Perimeter-defense Game on Arbitrary Convex Shapes
This paper studies a variant of multi-player reach-avoid game played between intruders and defenders. The intruder team tries to score by sending as many intruders as possible to the target area, while the defender team tries to minimize this score b…
Authors: Daigo Shishika, Vijay Kumar
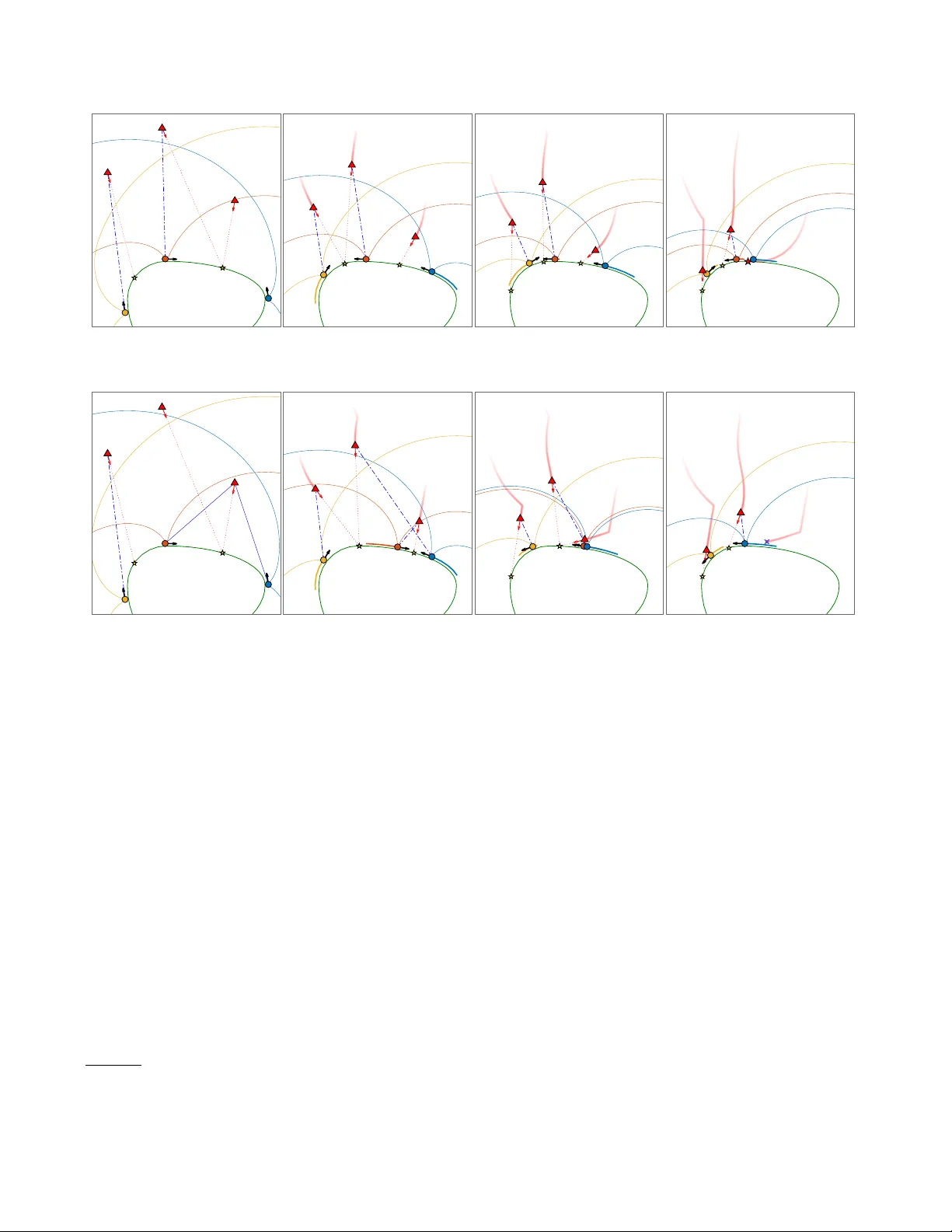
P erimeter-defense Game on Arbitrary Con v ex Shap es Daigo Shishik a a , Vija y Kumar b a Dep artment of Me chanic al Engine ering, Ge or ge Mason University, USA. b GRASP L ab, University of Pennsylvania, USA. Abstract This pap er studies a v ariant of m ulti-pla y er reach-a v oid game play ed b etw een intruders and defenders. The intruder team tries to score by sending as many intruders as p ossible to the target area, while the defender team tries to minimize this score b y intercepting them. Sp ecifically , we consider the case where the defenders are constrained to mov e on the perimeter of the target area. Since it is challenging to directly solv e the multi-pla yer game due to the high dimensionality of the join t state space, we leverage the solutions to smaller scale problems. First, we solve the one vs. one game, for which existing works either rely on numerical approac hes or make simplifying assumptions (e.g., circular p erimeter, or equal sp eed). This pap er accommo dates target areas with an y arbitrary conv ex shap es and provides analytical solution which lends itself to a useful geometric in terpretation. W e also provide a detailed discussion on the optimality of the derived strategies. Secondly , we solv e the tw o vs. one game to introduce a co op erative pincer maneuver, where a pair of defenders team up to capture an intruder that cannot b e captured by either one of the defender individually . Finally , we introduce how the aforementioned building blo c ks are used in three different assignment-based defense strategies. Key wor ds: Pursuit ev asion game, Reach av oid game, Co op erative control 1 In tro duction Main taining p erimeter surveillance and securit y is a complex problem giv en that it has b ecome practical to deplo y autonomous agen ts in large num b ers. V arious approac hes to counter intrusions by unmanned vehicles ha v e b een studied including patrolling strategy [34], in- trusion detection based on behavior rules [31], and GPS sp o ofing to manipulate the b ehavior of the agents [23]. When ev asive targets need to b e detected, intercepted, or surrounded, the scenarios are often form ulated as pursuit-ev asion games (PEGs) [8,17,43]. If it is formu- lated as a game of kind , we ask which initial configura- tion leads to capture (or ev asion), and what pursuit (or ev asiv e) strategy guaran tees that. If it is form ulated as a game of de gr e e , we find the optimal strategy for a given ob jectiv e function, e.g., time to capture. The game b ecomes more complex when the ev ader has another ob jective, such as to reach a target. A v ersion ? W e gratefully ackno wledge the supp ort of ARL grant ARL DCIST CRA W911NF-17-2-0181. Corresp onding au- thor: D. Shishik a. Email addr esses: dshishik@gmu.edu (Daigo Shishik a), kumar@seas.upenn.edu (Vija y Kumar). of this problem is called the target-attack er-defender (T AD) game [15,26,36]. In a T AD game the attac k er aims to capture the target while av oiding b eing captured by the defender, and the defender tries to defend the target b y intercepting the attack er. In [26] the defender could sa v e the target b y reaching it b efore the attac ker, whic h led to a rendezvous type strategy . Another formulation fo cuses on the case where the tar- get is a region in the game space and is no longer treated as an agen t. The tw o-play er v ersion of the game (one de- fender vs. one attack er) was first introduced by Isaacs as the target-defense game [22]. This game is also called the reac h-a void game [11,50,51], and it has b een stud- ied in man y differen t v ariants including m ulti-play er sce- nario [6,20,47,48,49] and coast-line guarding or b oarder defense [16,19,44]. This paper considers the p erimeter defense game, whic h is a v ariant of the reac h-a void game play ed b etw een in- truders and defenders [39,41]. The intruder team tries to score b y sending as man y in truders as p ossible to the target area, while the defender team tries to minimize this score by intercepting them. A sp ecific assumption made in this paper is that the defenders are constrained to mov e on the p erimeter. Suc h assumption is motiv ated b y the scenarios where the target region acts as an ob- stacle that the defenders cannot mo v e through ( e.g., de- fending a perimeter of a building using ground vehicles). V arious solution metho ds hav e b een prop osed to solve the PEGs introduced th us far. In general the approac hes can b e divided into t wo t yp es: the differential game for- m ulation and the explicit p olicy metho d [26]. The former obtains the strategies and the winning regions by solv- ing a Hamilton-Jacobi-Issacs (HJI) partial differen tial equation (PDE), while the latter analyzes the outcome of the game by prescribing a strategy to the play ers. The differential game formulation has b een successfully utilized for relativ ely simple problems that allo w analyt- ical solution to the HJI PDEs [3,22,29] and other prob- lems with lo w dimensional state space for whic h the HJI PDEs can b e numerically solved [6,12]. The strength of this approach is that the optimalit y of the deriv ed strate- gies are ensured by construction. The down side is the curse of dimensionality , which makes the HJI PDEs in- tractable for problems with large state space. There are sev eral pap ers on computing approximate optimal so- lutions for pursuit-ev asion games that also bypass the computational intractabilit y of solving HJI equations ex- plicitly [27,28,42]. The explicit p olicy metho d is widely used for multi- pla y er PEGs that require scalability in the n um b er of agen ts. F or scenarios inv olving m ultiple pursuers, sp e- cific con trol strategies hav e been prop osed with the anal- yses on their performance guarantees. Approaches based on V oronoi tessellation and area minimization can b e found in v arious works [21,35,52]. A v ariant of such w ork prop oses a so called rela y pursuit to improv e the ov erall efficiency by selecting one pursuer to actively go after the ev ader [2], and it has b een applied to a more com- plex scenario [38]. A b ehavior called the cyclic pursuit uses a chain of pursuers to encircle a target [4,24]. F or a non-adv ersarial scenario where there is no ev asive ma- neuv er, the problem is form ulated as the v ehicle-routing problem [1]. Ev asive maneuv ers hav e also b een consider in the scenario with one pursuer and multiple ev aders [14,37]. The problem b ecomes more challenging when there are m ultiple pursuers and multiple ev aders. The underly- ing question is “which pursuer should go after which ev ader?” In [35], a V oronoi-tessellation based approach w as used to directly obtain the desired direction of mo- tion. In [30], a task allo cation approach was prop osed, where the solution to the multiple pursuers vs. one ev ader problem w as used to assign a unique pursuer for each ev ader so that capture in minimum time is guaran teed. Sp ecifically for the reach-a void game pla yed b etw een m ultiple defenders and multiple attack ers, [6] approxi- mated the multi-pla yer game as a combination of tw o- pla y er games. In contrast to a more conv entional PEG that considers the time of capture, w e m ust consider whether the given pursuer can capture the attack er b e- fore it reaches the target. T o obtain this feasibilit y (cap- turabilit y) information, the solutions to the tw o play er games (strategies and winning regions) were obtained by n umerically solving the asso ciated HJI PDE [6,7]. As an adv an tage of using a numerical approach, the authors w ere able to handle complex environmen ts with obsta- cles. These solutions were used to formulate the design of defense p olicy as an assignment problem. F ollo wing the approach taken in [6,7], this pap er starts b y identifying the solution to the t w o-play er game: the game play ed betw een one defender and one in truder. Al- though the tw o-play er game has b een solv ed either nu- merically [6,7], or under restricted assumptions (circu- lar p erimeter or equal sp eed) [39], we analytically solve the problem for arbitrary con v ex shapes. This is enabled due to the constraint that the defender mov es on the p erimeter. Our analytical solution has several adv antages ov er the n umerical one. First, it lends itself to con venien t geomet- ric in terpretations such as appr o ach angle . In addition, while the n umerical approach requires us to compute the solution offline and store the data (i.e., a lo ok up table that gives control inputs from the current positions), an- alytical approach efficiently computes the control input online, and thus requires muc h less memory . In addition, the deriv ed solution exhibits an in terest- ing contrast to the solutions based on dominanc e r e gion , whic h was used in the original work by Isaacs [22] and also in [32]. The intruder-dominated region contains all the p oints that the in truder c an reach first regardless of the defender’s strategy [32]. One can conclude that the in truder can successfully reach the target/p erimeter if the intruder-dominated region intersects the target re- gion. How ever, our analysis shows that such condition is only sufficient and not necessary in the p erimeter de- fense game. W e also extend the existing assignment metho d by incor- p orating a co op erative defense p erformed b y tw o defend- ers. T o this end, we analytically solve the game play ed b et w een tw o defenders and one intruder. Then the so- lution to this tw o vs. one game is incorp orated in the extended assignment p olicy . The main con tributions of the pap er are (i) the solution to the one vs. one game; (ii) the solution to the t w o vs. one game that shows the benefit of defender coop eration; and (iii) the analysis on the optimalit y of the deriv ed strategies. These results are essential building blo cks to solv e the game play ed b et ween multiple defenders and m ultiple in truders [41]. Finally , we also presen t and dis- cuss three different assignmen t-based defense p olicies that utilize the aforementioned results. 2 In our previous w ork [39] the p erimeter-defense game w as solved on a circular p erimeter with a formulation that is not extensible to general shapes. This paper uses a formulation that can treat any con vex shap es including the circular perimeter. While the extension to p olygonal p erimeter was discussed in [39], the result w as limited to the case where the defender and the intruder hav e the same sp eed limits, which allo wed us to simplify the anal- ysis. This pap er fills the existing gap b y accommodating a more general case where the defender has any sp eed that is equal or higher than the intruder. Finally , the discussion of the pay off functions, for which the derived strategies are optimal, has not b een published b efore. The pap er is organized as follows. Section 2 formulates the problem. Section 3 solves the game play ed by one defender and one in truder. Section 4 in tro duces the co- op erativ e asp ect by solving the game play ed by tw o de- fender and one in truder. Section 5 prop oses the defender team strategy using the results of one vs. one and tw o vs. one games. Section 6 presents the numerical results. 2 Problem form ulation This section form ulates the reac h-a void game for de- fenders constrained on a p erimeter. The target T ⊂ R 2 is assumed to b e a conv ex region on a plane, and its p erimeter is giv en b y an arc-length parameterized curve γ : [0 , L ) → ∂ T , where L denotes the perimeter length. 1 W e use s ∈ [0 , L ) to denote the arc-length p osition on the curve measured in counter-clockwise (ccw) direction. The tangent vector of the curve at s is denoted by T ( s ) , d γ ( s ) ds . F or any t wo points/v ectors in R 2 w e denote the relative v ectors using x a ) b , x b − x a , and the unit v ectors using ˆ x = x k x k . The arc-length from p oin t s a to s b on the curve in ccw direction is denoted b y s a ) b , ( s b − s a ) mo d L, for example, s a ) b + s b ) a = L . The segment starting from s a and ending at s b in ccw direction is denoted by [ s a , s b ] , { s x | s a ) x ≤ s a ) b } . W e use ( s a , s b ) when the endp oin ts are not included. A set of N D defenders { D i } N D i =1 are constrained to mov e 1 In case the target is concav e, the results of this paper can b e applied by taking the conv ex hull of the original region and b y deplo ying defenders to protect this virtual target region. on the p erimeter. 2 The p osition of the i th defender is describ ed by s D i or x D i = γ ( s D i ). The defender’s con- trol input is the signed speed: ˙ s D i = ω D i or ˙ x D i = ω D i T ( s D i ) with the constraint | ω D i | ≤ 1. A set of N A in truders { A j } N A j =1 ha v e first-order integrator dynamics in R 2 . The control inputs are the v elo cities; ˙ x A i = u A i with the constrain t k u A i k ≤ ν . It is assumed that the defender is at least as fast as the intruder: 3 ν ∈ (0 , 1] . (1) This is a generalization of the case with ν = 1 studied in [39] and remov es some simplifications (see Sec. 3.4). W e assume that each play er has access to the current state and the sp eed ratio ν . Ho wev er, the pla yers do not kno w the instantaneous control action of the opp onent. In a microscopic view, an in truder A i scores if it reac hes the target ( x A i ∈ ∂ T ) without b eing captured by the defenders. W e use zero distance to define capture: i.e., k x A − x D k = 0, ho w ever, the extension to the case with non-zero capture radius is also straightforw ard [40]. The defender mov es on the p erimeter to either intercept the in truder or preven t it from scoring indefinitely . As the building blo cks to analyze the multi-pla yer game, w e solve the game play ed by one defender and one in- truder, and also by tw o defenders and one intruder. Problem 1: Find the b arrier surface [22] that divides the state space into intruder-winning and defender- winning configurations. In each region, what are the strategies to b e used by the play ers? In a macroscopic view, let Q ∈ N denote the num b er of in truders that reach the p erimeter. The intruder team maximizes Q while the defender team minimizes it. Problem 2: Giv en an initial configuration of the game and the sp eed ratio ν , what are the upp er and low er b ounds on the score Q , and what are the asso ciated team strategies to ensure that b ound? W e address these problems in the following sections. 2 This assumption is motiv ated b y v arious scenarios, for example, in which ground defenders are deplo yed to protect a building that they cannot mov e through. 3 The case with faster intruders (i.e., ν > 1) requires a separate treatmen t and is a sub ject of ongoing work. It is easy to see that if ν > 1, and also if the capture is defined b y zero distance, then the intruder can alwa ys win. 3 (a) (b) s tan,L AAACYnicbVDLahRBFK1pX7F9ZcxSF42D4EKG7iSgqxBw48JFBCcJTLfDrerbSZF6NFW3NUPR/+E2+Sv3fojVM7MwiRcKDueee+pweKukpzz/PUru3X/w8NHW4/TJ02fPX2yPXx572zmBM2GVdaccPCppcEaSFJ62DkFzhSf84tOwP/mBzktrvtGyxUrDmZGNFECR+u4XJeElBQLz/ku/2J7k03w12V1QbMCEbeZoMR4dlLUVnUZDQoH38yJvqQrgSAqFfVp2HlsQF3CG8wgNaPRVWMXus7eRqbPGuvgMZSv234sA2vul5lGpgc797d1A/m8376j5WAVp2o7QiPVHTacystnQQVZLh4LUMgIQTsasmTgHB4JiU2la1tiUugnl4Mybfk1wH0puVT0ksqpPb6YRIlbgo9TgT2G1BlOHsuPg+nlRRWRqdGtRdIlsmBR99IiNF7f7vQuOd6fF3nT36/7kcH/T/RZ7xd6wd6xgH9gh+8yO2IwJ5tgvdsWuR3+SNBknO2tpMtrc7LAbk7z+C5xgubE= s tan,R AAACYnicbVDLbtRAEJw1r2BeWXKEg8UKiQNa2UkkOEWRuHAMiE0irc2qZ9xORpmHNdOGrEb+D67wV9zzIRnv7oEktDRSqbq6plS8VdJTnv8dJffuP3j4aOtx+uTps+cvtscvj73tnMCZsMq6Uw4elTQ4I0kKT1uHoLnCE37xadif/EDnpTXfaNlipeHMyEYKoEh994uS8JICgXn/tV9sT/JpvprsLig2YMI2c7QYjw7K2opOoyGhwPt5kbdUBXAkhcI+LTuPLYgLOMN5hAY0+iqsYvfZ28jUWWNdfIayFfvvRQDt/VLzqNRA5/72biD/t5t31HysgjRtR2jE+qOmUxnZbOggq6VDQWoZAQgnY9ZMnIMDQbGpNC1rbErdhHJw5k2/JrgPJbeqHhJZ1ac30wgRK/BRavCnsFqDqUPZcXD9vKgiMjW6tSi6RDZMij56xMaL2/3eBce702Jvuvtlf3K4v+l+i71ib9g7VrAP7JB9ZkdsxgRz7Bf7zf6MrpI0GSc7a2ky2tzssBuTvL4GqAy5tw== s AAACVXicbVDLSsNAFJ3EqjU+WnXpJlgEVyXRgq5EcOOyglWhCWVmcqOD8wgzE6WEfIFb/TbxYwQnbRe+Lgwczj333jOHFJwZG0Ufnr/UWl5Zba8F6xubW53u9s6NUaWmMKKKK31HsAHOJIwssxzuCg1YEA635PGi6d8+gTZMyWs7LSAV+F6ynFFsHXVlJt1e1I9mFf4F8QL00KKGk23vLMkULQVISzk2ZhxHhU0rrC2jHOogKQ0UmD7iexg7KLEAk1Yzp3V44JgszJV2T9pwxn6fqLAwZiqIUwpsH8zvXkP+1xuXNj9NKyaL0oKk80N5yUOrwubbYcY0UMunDmCqmfMa0gesMbUunCBIMsgTkVdJs5nk9ZwgpkqI4lnjSPE6+OmGUheBcVIJz1QJgWVWJSXBuh7HqUMyAz0XuS2OrXpx7Xa4xOPf+f4FN0f9+Lh/dDXonQ8W2bfRHtpHhyhGJ+gcXaIhGiGKAL2gV/TmvXuffstfmUt9bzGzi36U3/kCnPK0+w== ( s ) AAACW3icbVDLSsNAFJ3GV41vxZWbYBF0U5Iq6EoENy4r2Ac0QWYmN3boPMLMRCkhH+FWv8yF/+Kk7cLXhYHDuefee+aQnDNjw/Cj4S0tr6yuNdf9jc2t7Z3dvf2+UYWm0KOKKz0k2ABnEnqWWQ7DXAMWhMOATG7r/uAZtGFKPthpDonAT5JljGLrqEGcj9mpOXvcbYXtcFbBXxAtQAstqvu417iOU0ULAdJSjo0ZRWFukxJryyiHyo8LAzmmE/wEIwclFmCScua3Ck4ckwaZ0u5JG8zY7xMlFsZMBXFKge3Y/O7V5H+9UWGzq6RkMi8sSDo/lBU8sCqoPx+kTAO1fOoAppo5rwEdY42pdRH5fpxCFousjOvNJKvmBDFlTBRPa0eKV/5PN5S6CIyTSnihSggs0zIuCNbVKEockinouchtcWzZiiq3wyUe/c73L+h32tF5u3N/0brpLLJvoiN0jE5RhC7RDbpDXdRDFE3QK3pD741Pb8nzvc251GssZg7Qj/IOvwAe0bYk s tan,L AAACYnicbVDLahRBFK1pX7F9ZcxSF42D4EKG7iSgqxBw48JFBCcJTLfDrerbSZF6NFW3NUPR/+E2+Sv3fojVM7MwiRcKDueee+pweKukpzz/PUru3X/w8NHW4/TJ02fPX2yPXx572zmBM2GVdaccPCppcEaSFJ62DkFzhSf84tOwP/mBzktrvtGyxUrDmZGNFECR+u4XJeElBQLz/ku/2J7k03w12V1QbMCEbeZoMR4dlLUVnUZDQoH38yJvqQrgSAqFfVp2HlsQF3CG8wgNaPRVWMXus7eRqbPGuvgMZSv234sA2vul5lGpgc797d1A/m8376j5WAVp2o7QiPVHTacystnQQVZLh4LUMgIQTsasmTgHB4JiU2la1tiUugnl4Mybfk1wH0puVT0ksqpPb6YRIlbgo9TgT2G1BlOHsuPg+nlRRWRqdGtRdIlsmBR99IiNF7f7vQuOd6fF3nT36/7kcH/T/RZ7xd6wd6xgH9gh+8yO2IwJ5tgvdsWuR3+SNBknO2tpMtrc7LAbk7z+C5xgubE= s tan,R AAACYnicbVDLbtRAEJw1r2BeWXKEg8UKiQNa2UkkOEWRuHAMiE0irc2qZ9xORpmHNdOGrEb+D67wV9zzIRnv7oEktDRSqbq6plS8VdJTnv8dJffuP3j4aOtx+uTps+cvtscvj73tnMCZsMq6Uw4elTQ4I0kKT1uHoLnCE37xadif/EDnpTXfaNlipeHMyEYKoEh994uS8JICgXn/tV9sT/JpvprsLig2YMI2c7QYjw7K2opOoyGhwPt5kbdUBXAkhcI+LTuPLYgLOMN5hAY0+iqsYvfZ28jUWWNdfIayFfvvRQDt/VLzqNRA5/72biD/t5t31HysgjRtR2jE+qOmUxnZbOggq6VDQWoZAQgnY9ZMnIMDQbGpNC1rbErdhHJw5k2/JrgPJbeqHhJZ1ac30wgRK/BRavCnsFqDqUPZcXD9vKgiMjW6tSi6RDZMij56xMaL2/3eBce702Jvuvtlf3K4v+l+i71ib9g7VrAP7JB9ZkdsxgRz7Bf7zf6MrpI0GSc7a2ky2tzssBuTvL4GqAy5tw== ( s ) AAACXXicdVBNT9tAEN2Y0lKXQoBDD1xWjSrRQyPbsQi9VEhcOAapAarYRbvrMVmxH9buulVk+Vf02v4wTvwV1iSVmqodaaWnN29m3j5aCW5dFN33go1nm89fbL0MX22/3tnt7+1fWl0bBlOmhTbXlFgQXMHUcSfgujJAJBVwRe/Ouv7VNzCWa/XZLSrIJblVvOSMOE99yao5//rhyL6/6Q+i4ceT4yQ9xtEwisZxEncgGaejFMee6WqAVjW52et9ygrNagnKMUGsncVR5fKGGMeZgDbMagsVYXfkFmYeKiLB5s2T4xa/80yBS238Uw4/sX9ONERau5DUKyVxc/t3ryP/1ZvVrjzJG66q2oFiy0NlLbDTuPs+LrgB5sTCA8IM914xmxNDmPMhhWFWQJnJssm6zbRslwS1TUa1KDpHWrThuhvGfATWSxV8Z1pKooomqykx7SzOPVIFmKXIb/FsM4hbv8Mn/jtW/H9wmQzj0TC5SAen6Sr7LXSI3qIjFKMxOkXnaIKmiCGJfqCf6FfvIdgMtoOdpTTorWYO0FoFbx4B+XO3Bw== + ( s ) AAACXXicbVDLSsNAFJ1G6yO+deHCTbAIilASFXQlghuXCtZWmlhmJjd2cB5hZqKUkK9wqx/myl9x0nbh68LA4dxz7z1zSM6ZsWH40fBmZptz8wuL/tLyyura+sbmnVGFptChiivdI9gAZxI6llkOvVwDFoRDlzxd1v3uM2jDlLy1oxwSgR8lyxjF1lH3cT5kD4f75mCw3grb4biCvyCaghaa1vVgo3Eep4oWAqSlHBvTj8LcJiXWllEOlR8XBnJMn/Aj9B2UWIBJyrHjKthzTBpkSrsnbTBmv0+UWBgzEsQpBbZD87tXk//1+oXNzpKSybywIOnkUFbwwKqg/n6QMg3U8pEDmGrmvAZ0iDWm1oXk+3EKWSyyMq43k6yaEMSUMVE8rR0pXvk/3VDqIjBOKuGFKiGwTMu4IFhX/ShxSKagJyK3xbFlK6rcDpd49Dvfv+DuqB0dt49uTloXJ9PsF9AO2kX7KEKn6AJdoWvUQRQJ9Ire0Hvj02t6y97qROo1pjNb6Ed52195YrbD s AAACVXicbVDLSsNAFJ3EqjU+WnXpJlgEVyXRgq5EcOOyglWhCWVmcqOD8wgzE6WEfIFb/TbxYwQnbRe+Lgwczj333jOHFJwZG0Ufnr/UWl5Zba8F6xubW53u9s6NUaWmMKKKK31HsAHOJIwssxzuCg1YEA635PGi6d8+gTZMyWs7LSAV+F6ynFFsHXVlJt1e1I9mFf4F8QL00KKGk23vLMkULQVISzk2ZhxHhU0rrC2jHOogKQ0UmD7iexg7KLEAk1Yzp3V44JgszJV2T9pwxn6fqLAwZiqIUwpsH8zvXkP+1xuXNj9NKyaL0oKk80N5yUOrwubbYcY0UMunDmCqmfMa0gesMbUunCBIMsgTkVdJs5nk9ZwgpkqI4lnjSPE6+OmGUheBcVIJz1QJgWVWJSXBuh7HqUMyAz0XuS2OrXpx7Xa4xOPf+f4FN0f9+Lh/dDXonQ8W2bfRHtpHhyhGJ+gcXaIhGiGKAL2gV/TmvXuffstfmUt9bzGzi36U3/kCnPK0+w== x A AAACbXicbVHLbtQwFPWEQssU6AOxoqosRghWo2SK1C6L2HQ5SEyn0iQa2Tc3rTV+RLYDjKJ8RLfwZXwFv1BnkgVtuZKlo3OPr4/P5aUUzsfxn0H0ZOvps+2d58PdFy9f7e0fHF46U1nAGRhp7BVnDqXQOPPCS7wqLTLFJc756kvbn39H64TR3/y6xEyxay0KAcwHap6qgv5cfl7uj+JxvCn6GCQ9GJG+psuDwTTNDVQKtQfJnFskcemzmlkvQGIzTCuHJYMVu8ZFgJopdFm98dvQ94HJaWFsONrTDfvvjZop59aKB6Vi/sY97LXk/3qLyhdnWS10WXnU0D1UVJJ6Q9vP01xYBC/XATCwInilcMMsAx8iGg7THIuQSJ22k3nRdAR3dcqNzFtHRvakgk4FLDD3/QGEUFzQafwBRimm8zqtOLPNIskC0jnaThTmBrYeJU2YEXaQPEz8MbicjJOT8eTrp9H5pN/GDnlL3pGPJCGn5JxckCmZESArckt+kd+Dv9Gb6Cg67qTRoL/zmtyr6MMdvyG9hQ== x A AAACbXicbVHLbtQwFPWEQssU6AOxoqosRghWo2SK1C6L2HQ5SEyn0iQa2Tc3rTV+RLYDjKJ8RLfwZXwFv1BnkgVtuZKlo3OPr4/P5aUUzsfxn0H0ZOvps+2d58PdFy9f7e0fHF46U1nAGRhp7BVnDqXQOPPCS7wqLTLFJc756kvbn39H64TR3/y6xEyxay0KAcwHap6qgv5cfl7uj+JxvCn6GCQ9GJG+psuDwTTNDVQKtQfJnFskcemzmlkvQGIzTCuHJYMVu8ZFgJopdFm98dvQ94HJaWFsONrTDfvvjZop59aKB6Vi/sY97LXk/3qLyhdnWS10WXnU0D1UVJJ6Q9vP01xYBC/XATCwInilcMMsAx8iGg7THIuQSJ22k3nRdAR3dcqNzFtHRvakgk4FLDD3/QGEUFzQafwBRimm8zqtOLPNIskC0jnaThTmBrYeJU2YEXaQPEz8MbicjJOT8eTrp9H5pN/GDnlL3pGPJCGn5JxckCmZESArckt+kd+Dv9Gb6Cg67qTRoL/zmtyr6MMdvyG9hQ== Fig. 1. Illustration of the tangent p oints and the approach angle. The segment S d is indicated with the solid line. (a) A contin uously differentiable p erimeter. (b) A p olygonal p erimeter. 3 One vs. One Game This section solves the game play ed betw een one de- fender and one intruder. The states of the system are [ s D , x A ] and the dynamics are [ ˙ s D , ˙ x A ] = [ ω D , u A ]. The terminal surface corresp onding to intruder’s win is { [ s D , x A ] | x A ∈ T and k x A − γ s D k > 0 } . The terminal condition for defender’s win is discussed later in Sec. 3.2. W e first introduce some relev an t geometries, and then solv e the game of kind to find the b arrier surface [22] that divides the game space into the intruder-winning and the defender-winning regions. W e also discuss the ob jectiv e functions for which the derived strategies are also optimal in the game of de gr e e . 3.1 Ge ometries Let s tan,R and s tan,L denote the p oin ts where the tan- gen t lines from x A touc h the p erimeter (see Fig. 1a). Considering the directions from the p ersp ective of a de- fender facing out ward from the perimeter, the subscript R corresp onds to the “righ t” or clockwise (cw) direction of motion, and L corresp onds to the “left” or counter- clo c kwise (ccw). W e use S d ( x A ) , [ s tan,R , s tan,L ] to denote all the p oints on the p erimeter that the in- truder can reach b y a straight-line path. Note that these geometries are indep enden t of the defender p osition. F or a giv en p oin t s B ∈ S d and s D / ∈ S d consider the follo wing quantit y 4 : J L ( s B ; s D , x A ) , s D ) B − k γ ( s B ) − x A k ν . (2) 4 The restriction s D / ∈ S d will b e remov ed after Remark 1. The first term is the ccw distance from the defender to s B , and k γ ( s B ) − x A k is the distance from the in truder to s B . Hence, recalling that the defender and the in truder has the sp eed 1 and ν resp ectiv ely , J L describ es how m uc h longer it takes for the defender to reach s B than it takes for the intruder, when the defender mov es ccw and the intruder mov es on a straight line path to w ards s B . The subscript L is used to highlight that w e assume the engagement in the “left” or ccw direction. Supp ose the game starts at t = 0 and the intruder reac hes s B at time t F b efore the defender do es. Then s D ) B ( t F ) = s D ) B (0) − t F ω D ≥ s D ) B (0) − t F = s D ) B (0) − k γ ( s B ) − x A (0) k ν . Therefore, a p ositive J L ( s B ) can also b e interpreted as the exp ected arc-length dis- tance b etw een the intruder and the defender when the in truder reaches s B . T o fo cus on the geometry , we defer the question of defender’s optimal direction of motion, and whether the intruder should employ a straight line path or not, to the later sections (e.g., Remark 3). Restricting ourselves to straight line paths for now, the in truder maximizes J L b y finding the optimal breac hing p oin t s B . The deriv ative is given by dJ L ds B = d ds B ( s B − s D ) − 1 ν d d γ k γ − x A k · d γ ( s B ) ds B = 1 − 1 ν γ ( s B ) − x A k γ ( s B ) − x A k · T ( s B ) , where the dot pro duct in the second term is related to the appr o ach angle defined in the following: Definition 1 Supp ose the intruder p osition x A is given. Then for s ∈ S d , we define the approac h angle to b e φ ( s ) , cos − 1 γ ( s ) − x A k γ ( s ) − x A k · T ( s ) ∈ [0 , π ] . (3) F or a p erimeter with disc ontinuous tangent ve ctor (e.g., p olygonal p erimeter), we use φ − ( s ) and φ + ( s ) to denote the appr o ach angles b efor e and after the disc ontinuity (in c cw dir e ction). Note that φ is non-increasing in ccw direction due to the con v exity of T , 5 and for a con tinuously differentiable p erimeter, we alwa ys hav e φ ( s tan,R ) = π and φ ( s tan,L ) = 0 (see Fig. 1b). Using the approach angle, the deriv ative is describ ed as: dJ L ds B = 1 − cos φ ( s B ) ν , 5 One can easily v erify this by observing that T ( s ) and γ ( s ) − x A rotate in ccw and cw direction resp ectively for increasing s ∈ S d . 4 whic h gives the following result: dJ L ds B = positiv e if φ ( s B ) > φ ∗ L 0 if φ ( s B ) = φ ∗ L neg ativ e otherwise , (4) where φ ∗ L = cos − 1 ( ν ) . (5) This result provides the critical breac hing p oint that maximizes J L as follows: Definition 2 We define left breaching p oint s L ( x A ) ∈ S d to b e the p oint that maximizes J L . F or a c ontin- uously differ entiable γ ( s ) , it is t he unique solution of φ ( s ) = φ ∗ L , i.e., s L ( x A ) = φ − 1 cos − 1 ν . (6) F or a p erimeter with disc ontinuous tangent ve ctor (e.g., p olygonal p erimeter), s L ( x A ) is a unique p oint that sat- isfies either of the fol lowing c onditions: ( φ ( s ) = φ ∗ L ( s L is on a c ontinuous p art), φ ( s ) + < φ ∗ L < φ − ( s ) ( s L is on a vertex) . (7) Due to the monotonicity of φ ( s ) on a conv ex p erimeter, s L is alwa ys unique, and it can b e found b y a simple searc h on a one-dimensional space. Note also that s L is obtained analytically for some sp ecial cases discussed in Sec. 3.4. Remark 1 (Limiting cases) If ν = 1 , then we always have s L = s tan,L , b e c ause φ ∗ L = 0 and φ ( s tan,L ) = 0 . When ν → 0 the optimal appr o ach angle b e c omes φ ∗ L → π 2 , in which c ase s L is e quivalent to the closest p oint on the p erimeter fr om x A . No w we consider all defender lo cations by remo ving the restriction s D ∈ S d . With this extension, the left breach- ing p oint s L do es not maximize J L if s D ∈ [ s tan,R , s L ], ho w ever, we will show in Sec. 3.2 that s L and its coun- terpart s R are the only p oints necessary in defining the optimal strategies. F or given p ositions s D and x A , we define the following function that gives the critical v alue of J L : J ∗ L ( s D , x A ) , J L ( s L ) = s D ) L − k γ ( s L ) − x A k ν . (8) Figure 2a shows the level sets of J ∗ L for a sp ecific v alue of s D . The discon tinuit y corresp onds to the manifold where s L ( x A ) = s D . -0.4 -0.3 -0.2 -0.1 -0.1 0 0 0 0.1 0.1 0.1 0.2 0.2 0.3 0.3 0.3 0.4 0.4 0.5 0.5 0.6 0.6 0.7 0.8 -0.4 -0.3 -0.2 -0.2 -0.1 -0.1 0 0 0 0.1 0.1 0.2 0.2 0.3 0.3 0.3 0.4 0.4 0.5 0.5 0.6 0.7 (a) (b) s D AAACWXicbVDLSsQwFE3ra6xvXbopDoKroR0FXYmgC5cKjgrTMiTprQbzKEmqDKHf4FY/TfwZ05lZ+LoQOJx77r0nh1ScGZskH0E4N7+wuNRZjlZW19Y3Nre2b42qNYUBVVzpe4INcCZhYJnlcF9pwIJwuCNP523/7hm0YUre2HEFucAPkpWMYuupgRm5i2a02U16yaTivyCdgS6a1dVoKzjNCkVrAdJSjo0Zpkllc4e1ZZRDE2W1gQrTJ/wAQw8lFmByN3HbxPueKeJSaf+kjSfs9wmHhTFjQbxSYPtofvda8r/esLblSe6YrGoLkk4PlTWPrYrbr8cF00AtH3uAqWbea0wfscbU+oCiKCugzETpsnYzKZspQYzLiOJF60jxJvrphlIfgfFSCS9UCYFl4bKaYN0M09wjWYCeivwWz7pu2vgdPvH0d75/wW2/lx72+tdH3bP+LPsO2kV76ACl6BidoUt0hQaIIoZe0Rt6Dz7DIOyE0VQaBrOZHfSjwp0vLxi1vQ== s D AAACWXicbVDLSsQwFE3ra6xvXbopDoKroR0FXYmgC5cKjgrTMiTprQbzKEmqDKHf4FY/TfwZ05lZ+LoQOJx77r0nh1ScGZskH0E4N7+wuNRZjlZW19Y3Nre2b42qNYUBVVzpe4INcCZhYJnlcF9pwIJwuCNP523/7hm0YUre2HEFucAPkpWMYuupgRm5i2a02U16yaTivyCdgS6a1dVoKzjNCkVrAdJSjo0Zpkllc4e1ZZRDE2W1gQrTJ/wAQw8lFmByN3HbxPueKeJSaf+kjSfs9wmHhTFjQbxSYPtofvda8r/esLblSe6YrGoLkk4PlTWPrYrbr8cF00AtH3uAqWbea0wfscbU+oCiKCugzETpsnYzKZspQYzLiOJF60jxJvrphlIfgfFSCS9UCYFl4bKaYN0M09wjWYCeivwWz7pu2vgdPvH0d75/wW2/lx72+tdH3bP+LPsO2kV76ACl6BidoUt0hQaIIoZe0Rt6Dz7DIOyE0VQaBrOZHfSjwp0vLxi1vQ== Fig. 2. Level sets of J ∗ L ( s D , x A ) (left) and J ∗ R ( s D , x A ) (righ t) for a sp ecific v alue of s D ( ν = 0 . 9). F or a similar analysis on the cw motion of the defender, consider the following function: J R ( s B ; s D , x A ) = s B ) D − k x A − γ ( s B ) k ν , (9) where the arc-length computation is now s B ) D . With the same pro cess, we define the right br e aching p oint , s R , to b e the solution to φ ( s R ) = φ ∗ R = π − cos − 1 ( ν ) . (10) W e define a function for the critical v alue as J ∗ R ( s D , x A ) , J R ( s R ) = s R ) D − k x A − γ ( s R ) k ν . (11) Next we use the tw o functions J ∗ L and J ∗ R to divide the game space in to “righ t side” and “left side” with respect to the p osition of the defender. Let s op D b e the farthest (opp osite) p oint from the defender on the p erimeter. The partitioning will be giv en by the singular surface defined in the following: Definition 3 Consider the surfac es define d by Γ ( s D ) = { x A | J ∗ L ( x A , s D ) = J ∗ R ( x A , s D ) } . (12) The one extending fr om s D is c al le d the affer ent sur- fac e , Γ aff , and the other extending fr om s op D is c al le d the disp ersal surfac e , Γ dis (se e Fig. 3a) [22]. The singular surfaces are defined in the three-dimensional state space, but for conv enience, we lo ok at the “tw o- dimensional slice” by considering a sp ecific v alue of s D . The singular surfaces divide the entire game space into t w o regions. W e define them as the left region , Ω L ( s D ), and the righ t region , Ω R ( s D ) (see Fig. 3a). As one can see from the definition, there will b e tw o equally go o d strategies when the states are on the singular surface. 5 -0.4 -0.3 -0.2 -0.2 -0.2 -0.1 -0.1 -0.1 -0.1 0 0 0 0 0 0.1 0.1 0.1 0.1 0.1 0.2 0.2 0.2 0.3 0.3 0.4 afferent dispersal R 1 L AAACZXicbVDLahRBFK1pX7E1ZqLixoWNg+Bq6E4CZiUBNy5cRHGSwHQ73Lp9OylSj6aqOjIU/SVu9aP8An/D6plZmMQDBYdzz711OLyVwvk8/z1K7ty9d//B1sP00ePtJzvj3acnznQWaYZGGnvGwZEUmmZeeElnrSVQXNIpv/wwzE+vyDph9Fe/bKlScK5FIxB8lBbjnVKBv0CQ4Uu/+PStWIwn+TRfIbtNig2ZsA2OF7uj92VtsFOkPUpwbl7kra8CWC9QUp+WnaMW8BLOaR6pBkWuCqvkffYmKnXWGBuf9tlK/XcjgHJuqXh0Djndzdkg/m8273xzWAWh286TxvVHTSczb7KhhqwWltDLZSSAVsSsGV6ABfSxrDQta2pK1YRVO7zp1wJ3oeRG1kMiI/v0ehrEWIGLVk3f0SgFug5lx8H286KKTNdk16Z4JaphUvTxRmy8uNnvbXKyNy32p3ufDyZHB5vut9hL9pq9ZQV7x47YR3bMZgxZx36wn+zX6E+ynTxPXqytyWiz84xdQ/LqL3HhugA= R 2 L AAACZXicbVDLahRBFK1pX7E1ZqLixoWNg+Bq6J4EdCUBNy5cRHGSwHQ73Lp9OylSj6aqWhmK/hK3+lF+gb9h9cwsTOKBgsO55946HN5K4Xye/x4lt27fuXtv53764OHuo73x/uMTZzqLNEcjjT3j4EgKTXMvvKSz1hIoLumUX74f5qffyDph9Be/aqlScK5FIxB8lJbjvVKBv0CQ4XO//Ph1thxP8mm+RnaTFFsyYVscL/dH78raYKdIe5Tg3KLIW18FsF6gpD4tO0ct4CWc0yJSDYpcFdbJ++xVVOqsMTY+7bO1+u9GAOXcSvHoHHK667NB/N9s0fnmbRWEbjtPGjcfNZ3MvMmGGrJaWEIvV5EAWhGzZngBFtDHstK0rKkpVRPW7fCm3wjchZIbWQ+JjOzTq2kQYwUuWjV9R6MU6DqUHQfbL4oqMl2T3ZjilaiGSdHHG7Hx4nq/N8nJbFocTGefDidHh9vud9hz9pK9ZgV7w47YB3bM5gxZx36wn+zX6E+ymzxNnm2syWi784RdQfLiL3PSugE= R 3 L AAACZXicbVDLahRBFK3p+IitMZMoblzYOAiuhu4koCsJuHHhIoqTBKbb4dbt20mRejRV1cpQ9Je41Y/yC/wNq2dmYRIPFBzOPffW4fBWCufz/Pco2bpz99797Qfpw0c7j3fHe/unznQWaYZGGnvOwZEUmmZeeEnnrSVQXNIZv3o/zM++kXXC6C9+2VKl4EKLRiD4KC3Gu6UCf4kgw+d+8fHr4WI8yaf5CtltUmzIhG1wstgbvStrg50i7VGCc/Mib30VwHqBkvq07By1gFdwQfNINShyVVgl77NXUamzxtj4tM9W6r8bAZRzS8Wjc8jpbs4G8X+zeeebt1UQuu08aVx/1HQy8yYbashqYQm9XEYCaEXMmuElWEAfy0rTsqamVE1YtcObfi1wF0puZD0kMrJPr6dBjBW4aNX0HY1SoOtQdhxsPy+qyHRNdm2KV6IaJkUfb8TGi5v93ianB9PicHrw6WhyfLTpfps9Zy/Za1awN+yYfWAnbMaQdewH+8l+jf4kO8nT5Nnamow2O0/YNSQv/gJ1w7oC s op D AAACZXicbVBNSxxBFOwdEzWTqKuGXHLIkCWQ0zKzCnoSIR5yNJBVYWeydPe80cb+GLrfqEszv8Rr8qPyC/wb9uzuIWoeNBT16lUXxWopHKbp31608ur16tr6m/jtu43Nrf72zpkzjeUw5kYae8GoAyk0jFGghIvaAlVMwjm7/tbtz2/AOmH0T5zVUCh6qUUlOMVATftbbupP2l85wh16U7fT/iAdpvNJXoJsCQZkOafT7d5RXhreKNDIJXVukqU1Fp5aFFxCG+eNg5rya3oJkwA1VeAKP0/eJl8CUyaVseFpTObsvxeeKudmigWlonjlnu868n+7SYPVYeGFrhsEzRcfVY1M0CRdDUkpLHCUswAotyJkTfgVtZRjKCuO8xKqXFU+75xZ1S4I5nzOjCy7REa28dM0nIcKXJBquOVGKapLnzeM2naSFQHpEuxCFFwC6wdZGzxC49nzfl+Cs9Ew2xuOfuwPjkfL7tfJR/KZfCUZOSDH5Ds5JWPCSUPuyW/yp/cQbUTvow8LadRb3uySJxN9egS8i7qo s D AAACWXicbVDLSsQwFE3ra6xvXbopDoKroR0FXYmgC5cKjgrTMiTprQbzKEmqDKHf4FY/TfwZ05lZ+LoQOJx77r0nh1ScGZskH0E4N7+wuNRZjlZW19Y3Nre2b42qNYUBVVzpe4INcCZhYJnlcF9pwIJwuCNP523/7hm0YUre2HEFucAPkpWMYuupgRm5i2a02U16yaTivyCdgS6a1dVoKzjNCkVrAdJSjo0Zpkllc4e1ZZRDE2W1gQrTJ/wAQw8lFmByN3HbxPueKeJSaf+kjSfs9wmHhTFjQbxSYPtofvda8r/esLblSe6YrGoLkk4PlTWPrYrbr8cF00AtH3uAqWbea0wfscbU+oCiKCugzETpsnYzKZspQYzLiOJF60jxJvrphlIfgfFSCS9UCYFl4bKaYN0M09wjWYCeivwWz7pu2vgdPvH0d75/wW2/lx72+tdH3bP+LPsO2kV76ACl6BidoUt0hQaIIoZe0Rt6Dz7DIOyE0VQaBrOZHfSjwp0vLxi1vQ== (a) (b) s op D AAACZXicbVBNSxxBFOwdEzWTqKuGXHLIkCWQ0zKzCnoSIR5yNJBVYWeydPe80cb+GLrfqEszv8Rr8qPyC/wb9uzuIWoeNBT16lUXxWopHKbp31608ur16tr6m/jtu43Nrf72zpkzjeUw5kYae8GoAyk0jFGghIvaAlVMwjm7/tbtz2/AOmH0T5zVUCh6qUUlOMVATftbbupP2l85wh16U7fT/iAdpvNJXoJsCQZkOafT7d5RXhreKNDIJXVukqU1Fp5aFFxCG+eNg5rya3oJkwA1VeAKP0/eJl8CUyaVseFpTObsvxeeKudmigWlonjlnu868n+7SYPVYeGFrhsEzRcfVY1M0CRdDUkpLHCUswAotyJkTfgVtZRjKCuO8xKqXFU+75xZ1S4I5nzOjCy7REa28dM0nIcKXJBquOVGKapLnzeM2naSFQHpEuxCFFwC6wdZGzxC49nzfl+Cs9Ew2xuOfuwPjkfL7tfJR/KZfCUZOSDH5Ds5JWPCSUPuyW/yp/cQbUTvow8LadRb3uySJxN9egS8i7qo s D AAACWXicbVDLSsQwFE3ra6xvXbopDoKroR0FXYmgC5cKjgrTMiTprQbzKEmqDKHf4FY/TfwZ05lZ+LoQOJx77r0nh1ScGZskH0E4N7+wuNRZjlZW19Y3Nre2b42qNYUBVVzpe4INcCZhYJnlcF9pwIJwuCNP523/7hm0YUre2HEFucAPkpWMYuupgRm5i2a02U16yaTivyCdgS6a1dVoKzjNCkVrAdJSjo0Zpkllc4e1ZZRDE2W1gQrTJ/wAQw8lFmByN3HbxPueKeJSaf+kjSfs9wmHhTFjQbxSYPtofvda8r/esLblSe6YrGoLkk4PlTWPrYrbr8cF00AtH3uAqWbea0wfscbU+oCiKCugzETpsnYzKZspQYzLiOJF60jxJvrphlIfgfFSCS9UCYFl4bKaYN0M09wjWYCeivwWz7pu2vgdPvH0d75/wW2/lx72+tdH3bP+LPsO2kV76ACl6BidoUt0hQaIIoZe0Rt6Dz7DIOyE0VQaBrOZHfSjwp0vLxi1vQ== ⌦ R AAACjXicfZHbahRBEIZ7J1HjeMjp0pshiyAiy0xU9EIkEEFvQhJxk4XtZanuqZk06cPQ3SMuw75EbuOL+Tb27M5CDmJBw89Xf1HVVaySwvk0/dOL1tYfPHy08Th+8vTZ882t7Z0zZ2rLcciNNHbEwKEUGodeeImjyiIoJvGcXR62+fOfaJ0w+oefVThRUGpRCA4+oBE9VljC9Pt0q58O0kUk90XWiT7p4mS63TM0N7xWqD2X4Nw4Sys/acB6wSXOY1o7rIBfQonjIDUodJNmMfA8eRlInhTGhqd9sqA3KxpQzs0UC04F/sLdzbXwX7lx7YuPk0boqvao+bJRUcvEm6T9fZILi9zLWRDArQizJvwCLHAfdhTHMc2xoMw1lBmZtxMYOV9CVTS07ceKFWAdYCvAl4BDW/MFw1osHgVwXKEFb+zrhoItFfyahzWV9E2r/mcUemUMKg4nyu4e5L442x9kbwf7p+/6B5+7Y22QF2SPvCIZ+UAOyDdyQoaEE0muyDX5HW1G76NPUeeNel3NLrkV0de/pdjJqg== ⌦ L AAACjXicfZHbahRBEIZ7J1HjeMjBS2+GLIKILDNR0QuRQAS9SEgCbrKwvSzVPTWTJn0YunvEZdiXyK2+mG9jz+4s5CApaPj56i+quopVUjifpn970dr6g4ePNh7HT54+e765tb1z5kxtOQ65kcaOGDiUQuPQCy9xVFkExSSes8uDNn/+E60TRv/wswonCkotCsHBBzSixwpLmB5Ot/rpIF1EcldkneiTLk6m2z1Dc8NrhdpzCc6Ns7TykwasF1ziPKa1wwr4JZQ4DlKDQjdpFgPPk1eB5ElhbHjaJwt6vaIB5dxMseBU4C/c7VwL/5cb1774NGmErmqPmi8bFbVMvEna3ye5sMi9nAUB3Iowa8IvwAL3YUdxHNMcC8pcQ5mReTuBkfMlVEVD236sWAHWAbYCfAk4tDVfMazF4lEAxxVa8Ma+aSjYUsGveVhTSd+26j6j0CtjUHE4UXb7IHfF2d4gezfYO33f3//SHWuDvCS75DXJyEeyT76TEzIknEhyRX6TP9Fm9CH6HHXeqNfVvCA3Ivr2D5kMyaQ= Fig. 3. Singular surfaces for ν = 0 . 9. (a) Left region (cyan) and righ t region (magenta). The left region is further parti- tioned into three regions. (b) Level sets of V . Ho w ever, we will later show that suc h non-uniqueness do es not prev en t us from iden tifying the barrier. Let S L = [ s D , s op D ] and S R = [ s op D , s D ] denote the seg- men ts of the p erimeter to the left and right of the de- fender. Whether the intruder is in the left region or not can b e tested using the lo cation of the breaching p oin ts ( s L and s R ), and the relation betw een the v alues J ∗ L and J ∗ R . If x A ∈ Ω L ( s D ), then x A is in one of the following three regions (see Fig. 3a): R 1 L = { x A | s L ∈ S L , s R ∈ S R , J ∗ L > J ∗ R } R 2 L = { x A | s L ∈ S L , s R / ∈ S R } (13) R 3 L = { x A | s L / ∈ S L , s R / ∈ S R , J ∗ L < J ∗ R } . If the states [ s D , x A ] satisfy none of the abov e three conditions, and if J ∗ L 6 = J ∗ R , then w e hav e x A ∈ Ω R ( s D ). Finally , w e merge the tw o ob jective functions as follo ws: V ( x A , s D ) = ( J ∗ L ( x A , s D ) if x A ∈ Ω L ( s D ) J ∗ R ( x A , s D ) otherwise . (14) Fig. 3b shows the level sets of V ( s D , x A ). 6 W e later sho w in Sec. 3.3 that this is the value of the game for some pay off functions. W e close this section b y providing an algorithm to com- pute s L for general ν ∈ (0 , 1). Note that in the sp ecial case where ν = 1 or ν → 0, s L is immediately obtained as discussed in Remark 1. The condition in line 4 is only necessary for p erimeters that are non-differentiable. It is sufficient to visit non- differen tiable vertices in the interv al S d , and test the condition (7). When there is no suc h critical point, then 6 The ev olution of these lev el sets with the defender p osition is illustrated in: https://youtu.be/h0_VqJbNsQc Algorithm 1 Finding left breaching p oin t s L 1: Input : x A , γ , and ν 2: Compute tangent points s tan,L and s tan,R 3: S d ← [ s tan,R , s tan,L ] 4: if ∃ a vertex s ∈ S d s.t. (7) is true then 5: s L ← s 6: else 7: s L ← arg min s ∈S d | φ ( s ) − cos − 1 ( ν ) | 8: end if 9: Return : s L s D AAACV3icbVDLSsNAFJ3EV42vVpdugkVwVZIq6EoEXbhUtCo0ocxMburgPMLMRCkhn+BWv82v0Unbha8LA4dzz733zCEFZ8ZG0YfnLywuLa+0VoO19Y3NrXZn+86oUlMYUMWVfiDYAGcSBpZZDg+FBiwIh3vydN70759BG6bkrZ0UkAo8lixnFFtH3ZjRxajdjXrRtMK/IJ6DLprX1ajjnSaZoqUAaSnHxgzjqLBphbVllEMdJKWBAtMnPIahgxILMGk19VqH+47Jwlxp96QNp+z3iQoLYyaCOKXA9tH87jXkf71hafOTtGKyKC1IOjuUlzy0Kmw+HmZMA7V84gCmmjmvIX3EGlPr4gmCJIM8EXmVNJtJXs8IYqqEKJ41jhSvg59uKHURGCeV8EKVEFhmVVISrOthnDokM9Azkdvi2Kob126HSzz+ne9fcNfvxYe9/vVR96w/z76FdtEeOkAxOkZn6BJdoQGiaIxe0Rt69z68T3/Zb82kvjef2UE/yu98ASTStbA= y A AAACV3icbVDLSsNAFJ3EV42vVpdugkVwVZIq6EoUNy4VrQpNKDOTmzo4jzAzUUrIJ7jVb/NrdNJ24evCwOHcc+89c0jBmbFR9OH5C4tLyyut1WBtfWNzq93ZvjOq1BQGVHGlHwg2wJmEgWWWw0OhAQvC4Z48XTT9+2fQhil5aycFpAKPJcsZxdZRN5PR+ajdjXrRtMK/IJ6DLprX1ajjnSaZoqUAaSnHxgzjqLBphbVllEMdJKWBAtMnPIahgxILMGk19VqH+47Jwlxp96QNp+z3iQoLYyaCOKXA9tH87jXkf71hafOTtGKyKC1IOjuUlzy0Kmw+HmZMA7V84gCmmjmvIX3EGlPr4gmCJIM8EXmVNJtJXs8IYqqEKJ41jhSvg59uKHURGCeV8EKVEFhmVVISrOthnDokM9Azkdvi2Kob126HSzz+ne9fcNfvxYe9/vVR96w/z76FdtEeOkAxOkZn6BJdoQGiaIxe0Rt69z68T3/Zb82kvjef2UE/yu98ASqxtbM= x A AAACV3icbVDLTsMwEHTCq4Rn4cglokLiVCUFCU4IxIUjCApITVTZzqZY+BHZDlBF+QSu8G18DThtD7xWsjSand0dDyk4MzaKPjx/bn5hcam1HKysrq1vbLa3bo0qNYU+VVzpe4INcCahb5nlcF9owIJwuCOP503/7gm0YUre2HEBqcAjyXJGsXXU9cvwbLjZibrRpMK/IJ6BDprV5bDtnSSZoqUAaSnHxgziqLBphbVllEMdJKWBAtNHPIKBgxILMGk18VqHe47Jwlxp96QNJ+z3iQoLY8aCOKXA9sH87jXkf71BafPjtGKyKC1IOj2Ulzy0Kmw+HmZMA7V87ACmmjmvIX3AGlPr4gmCJIM8EXmVNJtJXk8JYqqEKJ41jhSvg59uKHURGCeV8EyVEFhmVVISrOtBnDokM9BTkdvi2KoT126HSzz+ne9fcNvrxgfd3tVh57Q3y76FdtAu2kcxOkKn6AJdoj6iaIRe0Rt69z68T3/Rb02lvjeb2UY/ym9/ASi+tbI= Fig. 4. The barrier surface (depicted in red). The green cylinder depicts the p erimeter shape extruded v ertically . In- truder winning region is the interior of the barrier surface. the optimization in line 7 is p erformed. The simplest w ay to p erform this optimization is to discretize the interv al S d in to a finite set of p oin ts and ev aluate the righ t-hand side, which is practically fine since the complexit y of the search grows only linearly with the resolution. T o impro v e the efficiency , one can also use, for example, the bisection metho d [9]. The righ t breac hing p oint s R can be computed in a sim- ilar w ay . Once these breac hing p oints are found, J ∗ L and J ∗ R are immediately obtained using (2) and (9). 3.2 Winning R e gions This section pro v es that the barrier for the game of kind is given by the zero level set of V defined in (14). Fig. 4 depicts the surface V ( s D , x A ) = 0 in the three dimen- sional state space. F or con v enience, we p erform our anal- ysis using the t wo-dimensional slice at s D corresp onding to the lo cation of the defender. W e define the in truder winning region as R A ( s D ) = { x A | V ( s D , x A ) > 0 } . (15) W e first sho w that the intruder can guarantee its victory if it starts inside R A . Lemma 1 If the initial c onfigur ation is such that x A ∈ R A ( s D ) (i.e., V > 0 ), then r e gar d less of the defender 6 ⌫ =0 . 4 AAACW3icbVDLSsNAFJ3Gd3y1iis3wSK4KokWdaMIblwqWCs0QWYmN+3QeYSZiVJCPsKtfpkL/8VJ24WvCwOHc8+998whOWfGhuFHw1tYXFpeWV3z1zc2t7abrZ0HowpNoUcVV/qRYAOcSehZZjk85hqwIBz6ZHxd9/vPoA1T8t5OckgEHkqWMYqto/qxLC7CTvep2Q474bSCvyCagzaa1+1Tq3EZp4oWAqSlHBsziMLcJiXWllEOlR8XBnJMx3gIAwclFmCScuq3Cg4dkwaZ0u5JG0zZ7xMlFsZMBHFKge3I/O7V5H+9QWGz86RkMi8sSDo7lBU8sCqoPx+kTAO1fOIAppo5rwEdYY2pdRH5fpxCFousjOvNJKtmBDFlTBRPa0eKV/5PN5S6CIyTSnihSggs0zIuCNbVIEockinomchtcWzZjiq3wyUe/c73L3g47kQnneO7bvvqdJ79KtpHB+gIRegMXaEbdIt6iKIxekVv6L3x6S14vrcxk3qN+cwu+lHe3hd+RLXV ⌫ =0 . 8 AAACXHicbVDLSsQwFM3U8VXfCm7cBAfB1dCqqBtFcONSwdGBaZEkvdVgHiVJlaH0J9zqj7nxW0xnZuGoFwKHc8+99+TQQnDrouizFcy0Z+fmFxbDpeWV1bX1jc07q0vDoMe00KZPiQXBFfQcdwL6hQEiqYB7+nzZ9O9fwFiu1a0bFpBK8qh4zhlxnuonqjyLuqf4Yb0TdaNR4b8gnoAOmtT1w0brPMk0KyUoxwSxdhBHhUsrYhxnAuowKS0UhD2TRxh4qIgEm1YjwzXe80yGc238Uw6P2J8TFZHWDiX1Sknck/3da8j/eoPS5adpxVVROlBsfCgvBXYaN7/HGTfAnBh6QJjh3itmT8QQ5nxGYZhkkCcyr5JmM83rMUFtlVAtssaRFnU47YYxH4H1UgWvTEtJVFYlJSWmHsSpRyoDMxb5LZ6tOnHtd/jE49/5/gV3B934sHtwc9S5OJ5kv4B20C7aRzE6QRfoCl2jHmJIoDf0jj5aX0E7WApWxtKgNZnZQlMVbH8D65e2Aw== ⌫ =1 AAACWXicbVDLSsNAFJ3EV42vVpdugkVwVRIVdaMU3LhUsFpoQpmZ3OjgPMLMRCkh3+BWP038GSdtF74uDBzOPffeM4cUnBkbRR+ev7C4tLzSWg3W1jc2t9qd7TujSk1hQBVXekiwAc4kDCyzHIaFBiwIh3vydNn0759BG6bkrZ0UkAr8IFnOKLaOGiSyPI/H7W7Ui6YV/gXxHHTRvK7HHe8iyRQtBUhLOTZmFEeFTSusLaMc6iApDRSYPuEHGDkosQCTVlO3dbjvmCzMlXZP2nDKfp+osDBmIohTCmwfze9eQ/7XG5U2P0srJovSgqSzQ3nJQ6vC5uthxjRQyycOYKqZ8xrSR6wxtS6gIEgyyBORV0mzmeT1jCCmSojiWeNI8Tr46YZSF4FxUgkvVAmBZVYlJcG6HsWpQzIDPRO5LY6tunHtdrjE49/5/gV3h734qHd4c9ztn8yzb6FdtIcOUIxOUR9doWs0QBQx9Ire0Lv36Xt+yw9mUt+bz+ygH+XvfAFzqrVg Fig. 5. In truder-winning region under the constraint s L ∈ S L (cy an) and s R ∈ S R (magen ta), for v aried in truder speed ν . The dotted lines illustrate the corresponding in truder paths. (a) (b) s L AAACV3icbVDLSsNAFJ3EV42vVpdugkVwVZIq6EoENy5cKFoVmlBmJjd1cB5hZqKUkE9wq9/m1+ik7cLXhYHDuefee+aQgjNjo+jD8xcWl5ZXWqvB2vrG5la7s31nVKkpDKjiSj8QbIAzCQPLLIeHQgMWhMM9eTpv+vfPoA1T8tZOCkgFHkuWM4qto27M6HLU7ka9aFrhXxDPQRfN62rU8U6TTNFSgLSUY2OGcVTYtMLaMsqhDpLSQIHpEx7D0EGJBZi0mnqtw33HZGGutHvShlP2+0SFhTETQZxSYPtofvca8r/esLT5SVoxWZQWJJ0dykseWhU2Hw8zpoFaPnEAU82c15A+Yo2pdfEEQZJBnoi8SprNJK9nBDFVQhTPGkeK18FPN5S6CIyTSnihSggssyopCdb1ME4dkhnomchtcWzVjWu3wyUe/873L7jr9+LDXv/6qHvWn2ffQrtoDx2gGB2jM3SBrtAAUTRGr+gNvXsf3qe/7LdmUt+bz+ygH+V3vgA0WrW4 s R AAACV3icbVDLSsNAFJ3EV42vVpdugkVwVZIq6EoENy59VYUmlJnJTR2cR5iZKCXkE9zqt/k1Omm78HVh4HDuufeeOaTgzNgo+vD8hcWl5ZXWarC2vrG51e5s3xlVagoDqrjSDwQb4EzCwDLL4aHQgAXhcE+ezpv+/TNow5S8tZMCUoHHkuWMYuuoGzO6HrW7US+aVvgXxHPQRfO6HHW80yRTtBQgLeXYmGEcFTatsLaMcqiDpDRQYPqExzB0UGIBJq2mXutw3zFZmCvtnrThlP0+UWFhzEQQpxTYPprfvYb8rzcsbX6SVkwWpQVJZ4fykodWhc3Hw4xpoJZPHMBUM+c1pI9YY2pdPEGQZJAnIq+SZjPJ6xlBTJUQxbPGkeJ18NMNpS4C46QSXqgSAsusSkqCdT2MU4dkBnomclscW3Xj2u1wice/8/0L7vq9+LDXvzrqnvXn2bfQLtpDByhGx+gMXaBLNEAUjdErekPv3of36S/7rZnU9+YzO+hH+Z0vQAC1vg== s L AAACV3icbVDLSsNAFJ3EV42vVpdugkVwVZIq6EoENy5cKFoVmlBmJjd1cB5hZqKUkE9wq9/m1+ik7cLXhYHDuefee+aQgjNjo+jD8xcWl5ZXWqvB2vrG5la7s31nVKkpDKjiSj8QbIAzCQPLLIeHQgMWhMM9eTpv+vfPoA1T8tZOCkgFHkuWM4qto27M6HLU7ka9aFrhXxDPQRfN62rU8U6TTNFSgLSUY2OGcVTYtMLaMsqhDpLSQIHpEx7D0EGJBZi0mnqtw33HZGGutHvShlP2+0SFhTETQZxSYPtofvca8r/esLT5SVoxWZQWJJ0dykseWhU2Hw8zpoFaPnEAU82c15A+Yo2pdfEEQZJBnoi8SprNJK9nBDFVQhTPGkeK18FPN5S6CIyTSnihSggssyopCdb1ME4dkhnomchtcWzVjWu3wyUe/873L7jr9+LDXv/6qHvWn2ffQrtoDx2gGB2jM3SBrtAAUTRGr+gNvXsf3qe/7LdmUt+bz+ygH+V3vgA0WrW4 Fig. 6. Engagemen t when the game starts in a configuration with s L / ∈ S L and s R / ∈ S R . (a) Defender tak es a sub optimal strategy aiming at s L . (b) Intruder enters Ω R and switches its heading to s R . str ate gy, the intruder guar ante es its win using the fol low- ing fe e db ack str ate gy: u ∗ A = ( ν ˆ x A ) L if x A ∈ Ω L ( s D ) ν ˆ x A ) R otherwise , (16) wher e ˆ x A ) L = γ ( s L ) − x A k γ ( s L ) − x A k , and ˆ x A ) R = γ ( s R ) − x A k γ ( s R ) − x A k . 7 PR OOF. Supp ose x A ∈ Ω L ( s D ) without the loss of generalit y . W e consider tw o cases: (i) s L ∈ [ s D , s op D ], and (ii) s L ∈ [ s op D , s D ]. In either case, we know that the in- truder reaches s L first if the defender mov es ccw, b ecause J ∗ L = V > 0. In the first case when s L ∈ [ s D , s op D ], it is clear that the cw motion by the defender tak es longer time to reac h s L than the ccw motion since s L ) D > s D ) L . Therefore, the in truder can reach s L first regardless of the defender strategy . The set of all intruder positions corresp onding to the first case is shown as the shaded (cyan) region in Fig. 5. The second case where s L ∈ [ s op D , s D ] (corresp onding to the white region in Fig. 5) is more subtle since the 7 F or conciseness, we take the con ven tion that the intruder treats the singular surface as part of Ω R . On the singular surface, the tw o actions in (16) are equally go o d, and this c hoice is inconsequential tow ards the outcome of the game. defender ma y be tempted to mov e cw to reach s L b efore the intruder do es (e.g., see Fig. 6a). Supp ose the defender tak es this strategy: ω D = − 1 (cw motion). Then J ∗ L increases b ecause s D ) L in (8) increases. Now, there exists a time t 1 when x A ( t 1 ) ∈ Γ dis ( s D ( t 1 )), at whic h point w e ha v e V ( t 1 ) = J ∗ L ( t 1 ) = J ∗ R ( t 1 ) > J ∗ L ( t 0 ) = V ( t 0 ) > 0 . (17) If the defender contin ues in cw direction, the intruder en ters Ω R , and the strategy (16) switches the breac hing p oin t to s R . 8 The intruder will reach s R first b ecause J ∗ R ( t 1 ) > 0 (Fig. 6b). If the defender go es back to ccw motion, the intruder sta ys in Ω L and contin ues tow ards s L . The intruder will reach s L first b ecause J ∗ L ( t 1 ) > 0. Therefore, no matter what decision the defender makes at this p oint in time, V ( s D , x A ) stays p ositive through- out the rest of the game, and the intruder never leav es R A ( s D ) until it reac hes the p erimeter. Note that, for the defender, this configuration at t 1 is strictly “worse” than the initial one in the sense that V is now strictly larger than what it was at t 0 . Also note if x A ∈ Γ dis , and if the defender contin ues to switc h its heading (according to ω D = − 1 if x A ∈ Ω L , and ω D = 1 otherwise, which is the opp osite of (18)), there will b e a “chatter” due to infinitely frequent switch- ing in the heading. 9 The intruder will oscillate ab out Γ dis , and since it alwa ys has a velocity comp onen t to- w ards the p erimeter (due to its conv exity), the intruder slide along Γ dis to approach the p erimeter and even tually reac h s op D . Notice that the defender gains no adv antage in the azimuthal proximit y to the intruder, and thus a rational defender will in fact never use suc h a strategy . Remark 2 (Dominance region) F or the c onfigur a- tion in Fig. 6a, the analysis b ase d on the dominanc e r e gion [32] wil l not c onclude that the intruder c an win the game, b e c ause s L is not in the intruder-dominate d r e gion; i.e., the defender has a way to r e ach s L b efor e the intruder. Nevertheless, we have shown that the intruder c an win the game by employing a fe e db ack str ate gy (16) . The result mentioned in Remark 2 is a consequence of the following p oints: (i) the p erimeter acts as an obstacle, and (ii) the defender is protecting a region (and not a single p oint). Rather than moving tow ards the optimal breac hing p oint in the shortest path, the defender must maneuv er so that it do es not generate a breac hing p oint that is “w orse” (corresp onding to a higher V ), as was illustrated in Fig. 6. This is wh y the defender m ust trav el 8 The simulation video at https://youtu.be/h0_VqJbNsQc illustrates the engagement. 9 Suc h phenomena often arise in differential games [45,33]. The solution to a differen tial equation with discontin uous righ t-hand side (due to chattering) can b e provided in the sense of Filipp ov [10]. 7 a distance longer than L/ 2 (half of the p erimeter length) when the intruder is in the unshaded region in Fig. 5. Remark 3 (Straigh t line path) Consider the c ase x A ∈ Ω L . Noting that s L r emains c onstant if u A = ν ˆ x A ) L , and that s L is indep endent of s D , the str ate gy in (16) cle arly r esults in a str aight line p ath towar ds s L . Even if the defender b ehaves sub optimal ly, as exemplifie d in Fig. 6, the intruder’s p ath wil l stil l r emain pie c e-wise line ar. This observation c ombine d with the r esults of Se c. 3.3 justifies the r estriction of the intruder str ate gy to a set of str aight-line p aths. Lemma 1 only giv es a sufficient condition for the intruder to win. T o prov e that it is also a necessary condition, w e show that the defender wins if the game starts in a configuration x A / ∈ R A ( s D ). Recall that the defender wins the game b y either inter- cepting the in truder or preven ting it from reaching the p erimeter indefinitely . Related to the latter scenario, w e sho w that the defender is able to stabilize the system around the configuration x A ∈ Γ aff ( s D ). 10 Lemma 2 When x A ( t 0 ) ∈ Γ aff ( s D ( t 0 )) , then for any intruder c ontr ol str ate gy, the defender c an maintain the c ondition x A ( t ) ∈ Γ aff ( s D ( t )) for al l t > t 0 using the fol lowing c ontr ol: ω ∗ D ( s D , x A ) = ( 1 if x A ∈ Ω L ( s D ) − 1 otherwise . (18) PR OOF. In the neighborho o d of the surface Γ aff ( s D ), consider the error function e = J ∗ L − J ∗ R . Noting that e > 0 if x A ∈ Ω L ( s D ), and e < 0 otherwise, we can rewrite the con trol as ω ∗ D = sgn( e ). (Note, this ex- pression of control is only v alid in the neighborho o d of x A ∈ Γ aff ( s D ).) The time deriv ative of the squared error is given by d dt e 2 = 2 e ( ˙ J ∗ L − ˙ J ∗ R ), where ˙ J ∗ L is dJ ∗ L dt = ˙ s L − ˙ s D − ˆ x A ) L ν · ( ˙ s L T ( s L ) − u A ) = ˙ s L 1 − cos φ ( s L ) ν + ˆ x A ) L ν · u A − ω D = ˆ x A ) L ν · u A − ω D . (19) F rom the second to the third line, we used the fact that ˙ s L 1 − cos φ ( s L ) ν = 0, which we prov e in the following. Observ e that a small displacement in x A mo v es s L if it is on a con tinuously differen tiable part of the p erimeter, but s L will remain stationary if it is on a vertex (see (7)). 10 This stabilization is also demonstrated in the sim ulation video av ailable at https://youtu.be/h0_VqJbNsQc When s L is on a con tin uously differen tiable part, we hav e φ ( s L ) = φ ∗ L = cos − 1 ν , which giv es 1 − cos φ ( s L ) ν = 0. When s L is on a v ertex and not mo ving, we hav e ˙ s L = 0. With a similar computation on ˙ J ∗ R , the time deriv ative of the squared error is ν 2 d dt e 2 = e ( ˆ x A ) L · u A − ν ω ∗ D − ( ˆ x A ) R · u A + ν ω ∗ D )) = e (( ˆ x A ) L − ˆ x A ) R ) · u A − 2 ν ω ∗ D ) Recalling that ˆ x A ) L and ˆ x A ) R are unit vectors, no- tice that k ˆ x A ) L − ˆ x A ) R k ≤ 2, and the equalit y holds when ˆ x A ) L = − ˆ x A ) R , whic h can b e true only when x A is on the p erimeter. Therefore, we hav e the b ound | ( ˆ x A ) L − ˆ x A ) R ) · u A | < 2 ν , which gives ν 2 d dt e 2 = | e | sgn( e ) (( ˆ x A ) L − ˆ x A ) R ) · u A − 2 ν sgn( e )) < −| e | ( − 2 ν sgn( e ) + 2 ν ) ≤ 0 . Therefore, the error is stabilized around 0, implying that J ∗ L = J ∗ R , i.e., x A ∈ Γ aff ( s D ). Since the afferent surface extends from the defender’s p osition, the lemma sho ws that the intruder can only reac h the perimeter b y passing through the defender po- sition: i.e., it cannot reac h the p erimeter without getting captured. Therefore, w e extend the definition of capture from x A = γ ( s D ) to the condition x A ∈ Γ aff ( s D ), and use it as part of the terminal condition. Note that the former condition is contained in the latter. Lemma 3 L et R D ( s D ) denote the c omplement of R A ( s D ) . If the initial c ondition is x A ∈ R D ( s D ) , i.e., x A / ∈ R A ( s D ) , then r e gar d less of the intruder str ate gy, the defender wins the game of kind using ω ∗ D in (18) : i.e., the defender either c aptur es the intruder or pr events it fr om sc oring indefinitely. PR OOF. Supp ose the in truder never enters the win- ning region R A . Then, since R A con tains the entire p erimeter other than a single p oint s D (defender p osi- tion), the only en try p oint to the p erimeter is now s D . Ho w ever, entering the p erimeter from s D means capture. Therefore, for the intruder to win the game, it is neces- sary to en ter R A . The question is: can the in truder start outside of R A and enter it? Crossing the b oundary ∂ R A and entering R A requires V ( s D , x A ) to increase from negative to p ositive. How- ev er, this is imp ossible when x A ∈ Ω L ( s D ) b ecause ˙ V = ˙ J ∗ L = 1 ν ˆ x A ) L · u A − ω ∗ D ≤ 0 . (20) 8 W e similarly ha v e ˙ V ≤ 0 for x A ∈ Ω R ( s D ). Therefore, V ( s D , x A ) is non increasing, and so the intruder cannot en ter the region V > V ( t 0 ), implying that it cannot en ter R A . The results of this section is summarized in the following theorem: Theorem 1 The zer o level set of V ( s D , x A ) define d in (14) gives the b arrier of the game of kind. The result directly follows from Lemmas 1, 2 and 3. W e also provide the intruder and defender strategies in the algorithm form. The k ey step for b oth strategies is to determine whether the in truder is in the left region Ω L or in the righ t region Ω R . Imp ortantly , this question can b e answ ered without explicitly calculating the b oundaries of the regions: Algorithm 2 Determining region (1 vs. 1) 1: Input : s D , x A , γ , and ν 2: Compute s L and s R using Alg. 1 3: J ∗ L ← J L ( s L ; s D , x A ) using (2) 4: J ∗ R ← J R ( s R ; s D , x A ) using (9) 5: if any of the conditions in (14) is true then 6: is in Left ← T r ue 7: else 8: is in Left ← F al se 9: end if 10: Return : is in Left Giv en the information is in Left , we can immediately calculate the control input: Algorithm 3 In truder control (1 vs. 1) 1: Input : s D , x A , γ , and ν 2: Compute s L and s R using Alg. 1 3: Determine the region (i.e., is in left ) using Alg. 2 4: if is in left = T r ue then 5: u ∗ A ← ν ˆ x A/L 6: else 7: u ∗ A ← ν ˆ x A/R 8: end if 9: Return : u ∗ A Algorithm 4 Defender control (1 vs. 1) 1: Input : s D , x A , γ , and ν 2: Determine the region (i.e., is in left ) using Alg. 2 3: if is in left = T r ue then 4: ω ∗ D ← 1 5: else 6: ω ∗ D ← − 1 7: end if 8: Return : ω ∗ D 3.3 Optimality of the Str ate gies This section discusses ho w the strategy set ( ω ∗ D , u ∗ A ) de- fined in (18) and (16) forms an equilibrium also in the game of de gr e e for some ob jective functions. W e visit in truder-winning and defender-winning configurations separately . Supp ose the initial configuration is x A ∈ R A ( s D ). Then consider the following ob jective function: P 1 ( ω D , u A ) = min { s D ) B ( t F ) , s B ) D ( t F ) } , (21) where t F is the time the in truder breac hes the perimeter at p oin t s B . This quan tity P 1 describ es the safe distanc e at the time of breaching which the intruder maximizes and the defender minimizes. The min op erator is used to accoun t for b oth ccw and cw measure of the distance. Theorem 2 If the initial c onfigur ation satisfies x A ∈ R A ( s D ) , and if the players use P 1 in (21) as the obje ctive function, then u ∗ A in (16) and ω ∗ D in (18) form an e qui- librium, and the value of the game is V ( s D , x A ) in (14) : V = min ω D max u A P 1 ( ω D , u A ) = max u A min ω D P 1 ( ω D , u A ) . PR OOF. Supp ose x A ∈ Ω L without the loss of gener- alit y . Along the terminal surface { [ s D , x A ] | x A ∈ ∂ T } , w e ha ve x A = γ ( s B ) where s B ∈ S L from the sup- p osition. W e also hav e V = J ∗ L ( s D , x A ) = s D ) B since the term k γ ( s L ) − x A k in (2) is 0. Noting that s D ) B = min { s D ) B , s B ) D } for s B ∈ S L , we ha v e P 1 = J ∗ L along the terminal surface. Therefore, maximizing or minimiz- ing P 1 is equiv alent to maximizing or minimizing J ∗ L ( t F ) on the terminal surface. Recalling the time deriv ative in (19), we hav e 1 = arg min ω D max u A ˙ J ∗ L ( ω D , u A ) ν ˆ x A ) L = arg max u A min ω D ˙ J ∗ L ( ω D , u A ) and min ω D max u A ˙ J ∗ L ( ω D , u A ) = max u A min ω D ˙ J ∗ L ( ω D , u A ) = ˙ J ∗ L (1 , ν ˆ x A ) L ) = 0 . (22) The ab ov e results prov e the theorem. Remark 4 A similar r esult wil l b e obtaine d for any ob- je ctive function that is an incr e asing function of P 1 . F or example, let α : [0 , L/ 2) → [0 , ∞ ) b e a strictly incr e asing function. Then P 0 , α ( P 1 ) is a valid obje ctive function that has u ∗ A in (16) and ω ∗ D in (18) as the e quilibrium str ate gies. The value of the game is then V 0 = α ( V ) . The pr o of r elies on the fact that P 1 = V along the terminal 9 surfac e and ˙ V = 0 everywher e under the optimal str ate- gies. Remark 5 If the intruder’s obje ctive is to quickly r e ach the p erimeter, e.g., P 0 = − ( t F − t 0 ) , then the optimal intrusion str ate gy wil l b e differ ent. In this c ase, the in- truder wil l move str aight towar ds the closest p oint on the p erimeter whenever it avoids c aptur e. Otherwise, it wil l cho ose the br e aching p oint so that P 1 = ε , inste ad of maximizing the safe distanc e. Remark 6 The shortest p ath towar ds any s B / ∈ S d c on- sists of a str aight line towar ds the tangent p oint and the p ath along the p erimeter, which is e quivalent to br e ach- ing the p erimeter at the tangent p oint. Ther efor e, it is r e asonable for the intruder to cho ose s B ∈ S d . In the defender winning scenario, we can consider the follo wing quan tity which desc rib es the distance of the in truder from the barrier: d bar = min x ∈R A ( s D ) k x − x A k . (23) This quantit y can b e interpreted as a buffer / margin from the intruder winning configuration. The defender will wan t to maximize this buffer, whereas the intruder can minimize d bar hoping that an y “mistake” in de- fender’s behavior will let it p enetrate the barrier and en ter R A ( s D ). Let the terminal pa y off function to b e the negative of the distance from the barrier when the capture o ccurs at time t F : P 2 ( ω D , u A ) , − d bar ( t F ) < 0 . (24) Note that capture is defined by x A ∈ Γ aff ( s D ) (see the paragraph b efore Lemma 3). The defender tries to min- imize P 2 , while the intruder tries to maximize it. Theorem 3 If the initial c onfigur ation is x A / ∈ R A ( s D ) , and if the players use P 2 in (24) as the obje ctive function, then u ∗ A in (16) and ω ∗ D in (18) form e quilibrium str ate- gies, and the value of the game is V ( s D , x A ) in (14) : V = min ω D max u A P 2 ( ω D , u A ) = max u A min ω D P 2 ( ω D , u A ) . PR OOF. F ollowing the pro of of Theorem 2, it is suffi- cien t to show the following identit y: − d bar ( s D , x A ) = ( ν J ∗ L ( s D , x A ) if x A ∈ Ω L ( s D ) ν J ∗ R ( s D , x A ) otherwise . (25) In the following we prov e the case with x A ∈ Ω L ( s D ). x ⇤ AAACW3icbVDLSsQwFM3Ud30rrtwEB0FcDK0KuhLBjUsFxxGmVZL0VsPkUZJUHUo/wq1+mQv/xXRmFr4uBA7nnnvvyaGF4NZF0UcrmJqemZ2bXwgXl5ZXVtfWN26sLg2DLtNCm1tKLAiuoOu4E3BbGCCSCujRwXnT7z2BsVyrazcsIJXkQfGcM+I81Utkjl/u9u/X2lEnGhX+C+IJaKNJXd6vt06TTLNSgnJMEGv7cVS4tCLGcSagDpPSQkHYgDxA30NFJNi0Gvmt8a5nMpxr459yeMR+n6iItHYoqVdK4h7t715D/tfrly4/SSuuitKBYuNDeSmw07j5PM64AebE0APCDPdeMXskhjDnIwrDJIPcJ1IlzWaa12OC2iqhWmSNIy3q8KcbxnwE1ksVPDMtJVFZlZSUmLofpx6pDMxY5Ld4tmrHtd/hE49/5/sX3Bx04sPOwdVR++xokv082kY7aA/F6BidoQt0ibqIoQF6RW/ovfUZTAVhsDSWBq3JzCb6UcHWF/wDthQ= R T AAACYHicbVBNTxsxFHQWaMMCDWlvcLGIkLgQ7YZIcKqQeumRVoREilfI9r4FC3+sbG9RtNq/0Wv7t7j2l9Sb5MDXkyyN5s0bj4aVUjifJE+daGNz68PH7na8s7v3qbff/3zjTGU5TLiRxs4YdSCFhokXXsKstEAVkzBlD9/a/fQXWCeMvvaLEjJF77QoBKc+UOSUqAL/xIQ5fH27P0iGyXLwW5CuwQCt5+q23/lKcsMrBdpzSZ2bp0nps5paL7iEJiaVg5LyB3oH8wA1VeCyehm6wceByXFhbHja4yX7/KKmyrmFYkGpqL93r3ct+d5uXvniIquFLisPmq8+KiqJvcFtAzgXFriXiwAotyJkxfyeWsp96CmOSQ5FaKUmrTMrmhXBXE2YkXmbyMgmfpmG81CBC1INj9woRXVek4pR28zTLCCdg12Jgktg60HaBI/QePq637fgZjRMz4ajH+PB5XjdfRcdoiN0glJ0ji7Rd3SFJoijEv1Gf9Dfzr+oG/Wi/koaddY3X9CLiQ7+Azgtt4o= B AAACWXicbVDLSsQwFE3ra6xvZ+kmOAiuhlYFXYnoxuUIjgrTIkl6q8E8SpIqQ+k3uNVPE3/GdGYWvi4EDueee+/JoaXg1sXxRxDOzS8sLnWWo5XVtfWNza3tG6srw2DItNDmjhILgisYOu4E3JUGiKQCbunTRdu/fQZjuVbXblxCJsmD4gVnxHlqmMoCn99v9uJ+PCn8FyQz0EOzGtxvBadprlklQTkmiLWjJC5dVhPjOBPQRGlloSTsiTzAyENFJNisnrht8J5nclxo459yeMJ+n6iJtHYsqVdK4h7t715L/tcbVa44yWquysqBYtNDRSWw07j9Os65AebE2APCDPdeMXskhjDnA4qiNIfC51Gn7WZaNFOC2jqlWuStIy2a6KcbxnwE1ksVvDAtJVF5nVaUmGaUZB6pHMxU5Ld4tu4ljd/hE09+5/sX3Bz0k8P+wdVR7+xoln0H7aBdtI8SdIzO0CUaoCFiiKNX9Ibeg88wCDthNJWGwWymi35U2P0CPHa1Qg== s L AAACWXicbVDLSsQwFE3ra6xvXbopDoKroR0FXYngxoULBUeFaRmS9FaDeZQkVYbQb3Crnyb+jOnMLHxdCBzOPffek0MqzoxNko8gnJtfWFzqLEcrq2vrG5tb27dG1ZrCgCqu9D3BBjiTMLDMcrivNGBBONyRp/O2f/cM2jAlb+y4glzgB8lKRrH11MCM3GUz2uwmvWRS8V+QzkAXzepqtBWcZoWitQBpKcfGDNOksrnD2jLKoYmy2kCF6RN+gKGHEgswuZu4beJ9zxRxqbR/0sYT9vuEw8KYsSBeKbB9NL97Lflfb1jb8iR3TFa1BUmnh8qax1bF7dfjgmmglo89wFQz7zWmj1hjan1AUZQVUGaidFm7mZTNlCDGZUTxonWkeBP9dEOpj8B4qYQXqoTAsnBZTbBuhmnukSxAT0V+i2ddN238Dp94+jvfv+C230sPe/3ro+5Zf5Z9B+2iPXSAUnSMztAFukIDRBFDr+gNvQefYRB2wmgqDYPZzA76UeHOFz6otcU= s D AAACWXicbVDLSsQwFE3ra6xvXbopDoKroR0FXYmgC5cKjgrTMiTprQbzKEmqDKHf4FY/TfwZ05lZ+LoQOJx77r0nh1ScGZskH0E4N7+wuNRZjlZW19Y3Nre2b42qNYUBVVzpe4INcCZhYJnlcF9pwIJwuCNP523/7hm0YUre2HEFucAPkpWMYuupgRm5i2a02U16yaTivyCdgS6a1dVoKzjNCkVrAdJSjo0Zpkllc4e1ZZRDE2W1gQrTJ/wAQw8lFmByN3HbxPueKeJSaf+kjSfs9wmHhTFjQbxSYPtofvda8r/esLblSe6YrGoLkk4PlTWPrYrbr8cF00AtH3uAqWbea0wfscbU+oCiKCugzETpsnYzKZspQYzLiOJF60jxJvrphlIfgfFSCS9UCYFl4bKaYN0M09wjWYCeivwWz7pu2vgdPvH0d75/wW2/lx72+tdH3bP+LPsO2kV76ACl6BidoUt0hQaIIoZe0Rt6Dz7DIOyE0VQaBrOZHfSjwp0vLxi1vQ== (a) (b) ⇤ L AAACqnicZZFLb9QwEMe9KY8SXm05colYVUIIrZItEj1W6qUHDgWx20XrsLIdZ9eqH5E9KURRvgEnrvDF+DY4j0VlO5Klv38zY8+DFlI4iOM/o2Dv3v0HD/cfhY+fPH32/ODwaO5MaRmfMSONXVDiuBSaz0CA5IvCcqKo5Ff0+rz1X91w64TRn6EqeKrIWotcMAIeLXCxEV/frD6sDsbxJO4suiuSQYzRYJerw9EPnBlWKq6BSeLcMokLSGtiQTDJmxCXjheEXZM1X3qpieIurbuCm+jYkyzKjfVHQ9TR2xk1Uc5VivpIRWDjdn0t/Oc7vu1sUQHq+04BkJ+mtdBFCVyz/v+8lBGYqB1KlAnLGcjKC8Ks8C1EbEMsYeBHF2LNvzGjFNFZjbWxqlkmaY0lzwHLObcwTrAV6w1g296aMAxxxnNMXY2pkVnbiZFND1Ve47ZImm8BHQDdAtYDRrY5mX8oE66QpHJQddPtAm0f6Avy+0t2t3VXzKeT5GQy/fhufDYdNrmPXqJX6DVK0Ht0hi7QJZohhiT6iX6h38Hb4FPwJVj2ocFoyHmB/rMg+wv3vtZ4 T AAACp3icZZFLb9QwEMe94VXCq4Ujl4hVJbiskrYSHCtx4UaRutuV1lFlO5Ndq35E9gSIov0GSFzho/FtcB6LynYkS3//ZsaeB6+U9JimfybRvfsPHj46eBw/efrs+YvDo5cLb2snYC6ssm7JmQclDcxRooJl5YBpruCK33zs/FdfwXlpzSU2FeSarY0spWAY0Jxyn1xeH07TWdpbcldko5iS0S6ujyY/aGFFrcGgUMz7VZZWmLfMoRQKtjGtPVRM3LA1rII0TIPP277abXIcSJGU1oVjMOnp7YyWae8bzUOkZrjx+74O/vMd33Z2qEL9fa8ALD/krTRVjWDE8H9ZqwRt0k0kKaQDgaoJggknQwuJ2DDHBIa5xdTAN2G1ZqZoqbFOb1dZ3lIFJVK1AIfTjDq53iB13W0bxzEtoAyDbSm3qug6sWo7QF22tCuSlzvAR8B3QAxAsF1OER4qpK8Uazw2/XT7QDcEhoLC/rL9bd0Vi5NZdjo7+XI2PT8bN3lAXpM35C3JyHtyTj6RCzIngkjyk/wiv6N30edoES2H0Ggy5rwi/1nE/gLgmtUx d bar AAACrnicZZFLb9QwEMe94dESXi0cuUSsKnFaJQsSHCv1wrFI7LbSOlrZzmTXqh+RPQuNonwDzlzha/FtcB6LynYkS3//ZsaeB6+U9JimfybRg4ePHh8dP4mfPnv+4uXJ6aultzsnYCGssu6aMw9KGligRAXXlQOmuYIrfnPR+a++gfPSmq9YV5BrtjGylIJhQLRYU4RbbDhz7fpkms7S3pL7IhvFlIx2uT6d/KCFFTsNBoVi3q+ytMK8YQ6lUNDGdOehYuKGbWAVpGEafN70RbfJWSBFUloXjsGkp3czGqa9rzUPkZrh1h/6OvjPd3bX2aEK9e1BAVh+yhtpqh2CEcP/5U4laJNuMEkhHQhUdRBMOBlaSMSWOSYwjC+mBr4LqzUzRUONdbpdZXlDFZRI1RIcTjPq5GaL1HW3No5jWkBJuW8ot6roOrGqHaAuG9oVycs94CPgeyAGINg+pwgPFdJXitUe6366faAbAkNBYX/Z4bbui+V8lr2fzb98mJ7Px00ekzfkLXlHMvKRnJPP5JIsiCAV+Ul+kd9RGi2jPFoPodFkzHlN/rNo+xevNdjh @ R A AAACrnicZZFLb9QwEMe94VXCq4Ujl4hVJU6rZKkExyIuPRbEbiuto5XtOLtW/ZI9AaIo34Bzr+3X4tvgPBaV7UiW/v7Nw+MZaqXwkKZ/JtGDh48ePzl4Gj97/uLlq8Oj10tvKsf4ghlp3CUlnkuh+QIESH5pHSeKSn5Br750/osf3Hlh9HeoLc8V2WhRCkYgIIwtcSCITL6tP68Pp+ks7S25L7JRTNFo5+ujyW9cGFYproFJ4v0qSy3kTVeSSd7GuPLcEnZFNnwVpCaK+7zpm26T40CKpDQuHA1JT+9mNER5XysaIhWBrd/3dfCf7/ius0MW1K+9BqD8lDdC2wq4ZsP7ZSUTMEk3mKQQjjOQdRCEORG+kLAtcYRBGF+MNf/JjFJEFw3Wxql2leUNlrwELJfcwTTDTmy2gF13a+M4xgUvMfUNpkYW3U+MbAeoygZ3TdJyB+gI6A6wATCyyylCoUJ4K0ntoe6n2we6ITA0FPaX7W/rvljOZ9mH2fzryfR0Pm7yAL1F79B7lKGP6BSdoXO0QAxZdI1u0G2URssoj9ZDaDQZc96g/yza/gUVSNgr ⌫ s D ) L AAADZXicZVLLbtNAFJ0mPIqhtAXEAhZYRJXYNIrdSLCsBAsWLIpE2kqZKBqPrxMr87BmxjTWaCS+hi38Dl/AbzATu6hpr2TpzLnnXt9XVrFSm9Hoz06vf+/+g4e7j6LHT/ae7h8cPjvXslYUJlQyqS4zooGVAiamNAwuKwWEZwwustXH4L/4DkqXUnwzTQUzThaiLEpKjKfmB6+wqGM9t5+wVzV6KZUhSsmr+IubHwxGw9HG4rsg6cAAdXY2P+yd4FzSmoMwlBGtp8moMjNLlCkpAxfhWkNF6IosYOqhIBz0zG6acPGRZ/K4kMp/wsQb9maEJVzrhmdeyYlZ6tu+QP73Hd10BqoyfH2rAFN8mNlSVLUBQdv/FzWLjYzDoOK8VEANazwgVJW+hZguiSLU+HFGWMAVlZwTkVsspOJumswsZlAYzM5BmUGCVblYGqzCy0VRhHMocKYtziTLQyeSuZbkhcWhyKy4JrKOyK4J2hKUXMfkPlFe6oqRRptmM92NULVCX1C0XeT2fkO505OwnVYOzOJlJtcWq5rB1KfmsK4UDrsIWKQpNrA24Z0eD9PKNwaMrGd2kDg7HFfGOcxXoMTxmNddqjBRr7cTZ/05NM5yZ4XDbe92nDhvkT+z5PZR3QXn6TA5GaZfx4PTtDu4XfQavUXvUILeo1P0GZ2hCaLoB/qJfqHfvb/9vf6L/stW2tvpYp6jLeu/+QeJzSBK d bar AAACrnicZZFLb9QwEMe94dESXi0cuUSsKnFaJQsSHCv1wrFI7LbSOlrZzmTXqh+RPQuNonwDzlzha/FtcB6LynYkS3//ZsaeB6+U9JimfybRg4ePHh8dP4mfPnv+4uXJ6aultzsnYCGssu6aMw9KGligRAXXlQOmuYIrfnPR+a++gfPSmq9YV5BrtjGylIJhQLRYU4RbbDhz7fpkms7S3pL7IhvFlIx2uT6d/KCFFTsNBoVi3q+ytMK8YQ6lUNDGdOehYuKGbWAVpGEafN70RbfJWSBFUloXjsGkp3czGqa9rzUPkZrh1h/6OvjPd3bX2aEK9e1BAVh+yhtpqh2CEcP/5U4laJNuMEkhHQhUdRBMOBlaSMSWOSYwjC+mBr4LqzUzRUONdbpdZXlDFZRI1RIcTjPq5GaL1HW3No5jWkBJuW8ot6roOrGqHaAuG9oVycs94CPgeyAGINg+pwgPFdJXitUe6366faAbAkNBYX/Z4bbui+V8lr2fzb98mJ7Px00ekzfkLXlHMvKRnJPP5JIsiCAV+Ul+kd9RGi2jPFoPodFkzHlN/rNo+xevNdjh s L AAACWXicbVDLSsQwFE3ra6xvXbopDoKroR0FXYngxoULBUeFaRmS9FaDeZQkVYbQb3Crnyb+jOnMLHxdCBzOPffek0MqzoxNko8gnJtfWFzqLEcrq2vrG5tb27dG1ZrCgCqu9D3BBjiTMLDMcrivNGBBONyRp/O2f/cM2jAlb+y4glzgB8lKRrH11MCM3GUz2uwmvWRS8V+QzkAXzepqtBWcZoWitQBpKcfGDNOksrnD2jLKoYmy2kCF6RN+gKGHEgswuZu4beJ9zxRxqbR/0sYT9vuEw8KYsSBeKbB9NL97Lflfb1jb8iR3TFa1BUmnh8qax1bF7dfjgmmglo89wFQz7zWmj1hjan1AUZQVUGaidFm7mZTNlCDGZUTxonWkeBP9dEOpj8B4qYQXqoTAsnBZTbBuhmnukSxAT0V+i2ddN238Dp94+jvfv+C230sPe/3ro+5Zf5Z9B+2iPXSAUnSMztAFukIDRBFDr+gNvQefYRB2wmgqDYPZzA76UeHOFz6otcU= x A AAADUHicZVLLjtMwFPW0PIbwmoElm4hqJDZTNWklWA5iw3KQaDtSHVWOczON6kdkO0wjyx/BFv6KHX/CDuymRTOdK0U5Pvf4+r7ymlXajEa/j3r9Bw8fPT5+Ej199vzFy5PTVzMtG0VhSiWT6ionGlglYGoqw+CqVkB4zmCerz8F//wbKF1J8dW0NWScXIuqrCgxnppjXsab5cflyWA0HG0tvg+SHRignV0uT3tjXEjacBCGMqL1IhnVJrNEmYoycBFuNNSErsk1LDwUhIPO7DZfF595pohLqfwnTLxlb9+whGvd8twrOTErfegL5H/f2W1noGrDNwcJmPJDZitRNwYE7d4vGxYbGYeexEWlgBrWekCoqnwJMV0RRajxnYuwgBsqOSeisFhIxd0iySxmUBrMZqDMIMGqul4ZrMLJRVGECyhxri3OJStCJZK5juSlxSHJvNwT+Y7I9wTtCEr2dwofqKh0zUirTbvt7laoOqFPKLqbpB94q1dSGaKUvAnpLsZhOp0cmMWrXG4sVg2DhQ/NYVMrHGYRsEhTbGBjwjk9H6a1LwwY2WR2kDg7nNTGOczXoMT5hDe7UKGjXm+nzvp1aJ3lzgqHu9rtJHHeIr9myeFS3QezdJiMh+mXyeAi3S3cMXqD3qJ3KEHv0QX6jC7RFFG0Rt/RD/Sz96v3p/e3f9RJe7s/eo3uWD/6B9tHGWo= s D AAACWXicbVDLSsQwFE3ra6xvXbopDoKroR0FXYmgC5cKjgrTMiTprQbzKEmqDKHf4FY/TfwZ05lZ+LoQOJx77r0nh1ScGZskH0E4N7+wuNRZjlZW19Y3Nre2b42qNYUBVVzpe4INcCZhYJnlcF9pwIJwuCNP523/7hm0YUre2HEFucAPkpWMYuupgRm5i2a02U16yaTivyCdgS6a1dVoKzjNCkVrAdJSjo0Zpkllc4e1ZZRDE2W1gQrTJ/wAQw8lFmByN3HbxPueKeJSaf+kjSfs9wmHhTFjQbxSYPtofvda8r/esLblSe6YrGoLkk4PlTWPrYrbr8cF00AtH3uAqWbea0wfscbU+oCiKCugzETpsnYzKZspQYzLiOJF60jxJvrphlIfgfFSCS9UCYFl4bKaYN0M09wjWYCeivwWz7pu2vgdPvH0d75/wW2/lx72+tdH3bP+LPsO2kV76ACl6BidoUt0hQaIIoZe0Rt6Dz7DIOyE0VQaBrOZHfSjwp0vLxi1vQ== @ R A AAACrnicZZFLb9QwEMe94VXCq4Ujl4hVJU6rZKkExyIuPRbEbiuto5XtOLtW/ZI9AaIo34Bzr+3X4tvgPBaV7UiW/v7Nw+MZaqXwkKZ/JtGDh48ePzl4Gj97/uLlq8Oj10tvKsf4ghlp3CUlnkuh+QIESH5pHSeKSn5Br750/osf3Hlh9HeoLc8V2WhRCkYgIIwtcSCITL6tP68Pp+ks7S25L7JRTNFo5+ujyW9cGFYproFJ4v0qSy3kTVeSSd7GuPLcEnZFNnwVpCaK+7zpm26T40CKpDQuHA1JT+9mNER5XysaIhWBrd/3dfCf7/ius0MW1K+9BqD8lDdC2wq4ZsP7ZSUTMEk3mKQQjjOQdRCEORG+kLAtcYRBGF+MNf/JjFJEFw3Wxql2leUNlrwELJfcwTTDTmy2gF13a+M4xgUvMfUNpkYW3U+MbAeoygZ3TdJyB+gI6A6wATCyyylCoUJ4K0ntoe6n2we6ITA0FPaX7W/rvljOZ9mH2fzryfR0Pm7yAL1F79B7lKGP6BSdoXO0QAxZdI1u0G2URssoj9ZDaDQZc96g/yza/gUVSNgr x A AAADUHicZVLLjtMwFPW0PIbwmoElm4hqJDZTNWklWA5iw3KQaDtSHVWOczON6kdkO0wjyx/BFv6KHX/CDuymRTOdK0U5Pvf4+r7ymlXajEa/j3r9Bw8fPT5+Ej199vzFy5PTVzMtG0VhSiWT6ionGlglYGoqw+CqVkB4zmCerz8F//wbKF1J8dW0NWScXIuqrCgxnppjXsab5cflyWA0HG0tvg+SHRignV0uT3tjXEjacBCGMqL1IhnVJrNEmYoycBFuNNSErsk1LDwUhIPO7DZfF595pohLqfwnTLxlb9+whGvd8twrOTErfegL5H/f2W1noGrDNwcJmPJDZitRNwYE7d4vGxYbGYeexEWlgBrWekCoqnwJMV0RRajxnYuwgBsqOSeisFhIxd0iySxmUBrMZqDMIMGqul4ZrMLJRVGECyhxri3OJStCJZK5juSlxSHJvNwT+Y7I9wTtCEr2dwofqKh0zUirTbvt7laoOqFPKLqbpB94q1dSGaKUvAnpLsZhOp0cmMWrXG4sVg2DhQ/NYVMrHGYRsEhTbGBjwjk9H6a1LwwY2WR2kDg7nNTGOczXoMT5hDe7UKGjXm+nzvp1aJ3lzgqHu9rtJHHeIr9myeFS3QezdJiMh+mXyeAi3S3cMXqD3qJ3KEHv0QX6jC7RFFG0Rt/RD/Sz96v3p/e3f9RJe7s/eo3uWD/6B9tHGWo= R T 0 AAACkXicfZHdahRBEIV7x6jJ+JPEXOamcRFFZJmJAfVuUS8CIZhINglsL6G6p2bTpH+G7h5xGfY1vNXX8m3SszsLmogFDYevTtHFKV4p6UOW/e4l99buP3i4vpE+evzk6ebW9rMzb2sncCSssu6Cg0clDY6CDAovKoegucJzfv2p7Z9/Q+elNadhVuFEw9TIUgoIETGmS/qVMu7p6cvLrX42yBZF74q8E33S1fHlds+ywopaowlCgffjPKvCpAEXpFA4T1ntsQJxDVMcR2lAo580i6Xn9EUkBS2ti88EuqB/TjSgvZ9pHp0awpW/3Wvhv3rjOpTvJ400VR3QiOVHZa1osLRNgBbSoQhqFgUIJ+OuVFyBAxFiTmmasgLLmEjDuFVFu4FV8yXUZcPa/3i5ArwDfAXEEghoZz5jjMXhUQRfKnQQrHvdMHBTDd/nMaYpe9Oq/xmlWRmjSuOJ8tsHuSvO9gb528HeyX5/uN8da53skufkFcnJOzIkB+SYjIggFflBfpJfyU7yIRkmH5fWpNfN7JC/Kjm8AYXwyl8= Fig. 7. Proof of the identit y d bar = − ν J ∗ L . W e first show that the p oint x ∗ , which is the p oint in R A that is closest from x A , lies on the straight line from x A to γ ( s L ) (see Fig. 7). It suffices to sho w that x A ) L is p erp endicular to the tangent of the barrier ∂ R A at x ∗ , denoted by B . W e can treat s L as a parameter to express a p oin t, x bar , on the left barrier ∂ R A as follows: x bar ( s L ) = γ ( s L ) − ν s D ) L R T ( s L ) , where R ∈ R 2 × 2 denotes the matrix for ccw rotation b y φ ∗ L . The tangent is obtained by B , d x bar ds L = T − ν R T − ν s D ) L R T 0 , where T 0 = d T ( s L ) ds L denotes the normal vector of γ . The inner pro duct with ˆ x A ) L giv es B · ˆ x A ) L = T · ˆ x A ) L − ν R T · ˆ x A ) L − ν s D ) L R T 0 · ˆ x A ) L = cos( φ ∗ L ) − ν ( ˆ x A ) L · ˆ x A ) L ) − 0 = 0 , where from the first to second line we used R T = ˆ x A ) L and R T 0 · ˆ x A ) L = 0. No w, the distance b etw een x A and x ∗ is d bar = k x A ) L k − ν s D ) L = − ν J ∗ L . The case with x A ∈ Ω R can b e sho wn similarly . Unlik e the intruder strategy , it is easy to see that the defender strategy will stay the same even if the ob jectiv e is chosen to b e the minimum time capture. 3.4 Sp e cial Cases This section discusses how the results provided in the preceding sections accommo date the tw o sp ecial cases considered in [39]: circular p erimeter, and equal sp eed. 10 (a) D r AAAB+nicbVDLSgMxFM34rOOr6tJNsAiuykwRdFlw47IF+4DOUDLpnTY0yQxJRihjv8Ct/oA7cevPuPdDzLSz0NYDFw7n3Jvce6KUM20878vZ2Nza3tmt7Ln7B4dHx9WT065OMkWhQxOeqH5ENHAmoWOY4dBPFRARcehF07vC7z2C0iyRD2aWQijIWLKYUWKs1FbDas2rewvgdeKXpIZKtIbV72CU0EyANJQTrQe+l5owJ8owymHuBpmGlNApGcPAUkkE6DBfLDrHl1YZ4ThRtqTBC/X3RE6E1jMR2U5BzESveoX4nzfITHwb5kymmQFJlx/FGccmwcXVeMQUUMNnlhCqmN0V0wlRhBqbjesGI4gDEedB8XIUz10bi78awjrpNuq+V/fb17Vmowyogs7RBbpCPrpBTXSPWqiDKAL0jF7Qq/PkvDnvzseydcMpZ87QHzifPy6ak+Y= D A AAACqHicZZFLb9QwEMe9KdASXi0cuUSsKiEOq2SLBMciLhwXid0tWkcr23F2Tf2I7EkhivINOHBtv1m/Dc5jUdmOZOnv38zY86CFFA7i+HYUHDx4+Ojw6HH45Omz5y+OT14unCkt43NmpLEXlDguheZzECD5RWE5UVTyJb383PqXV9w6YfQ3qAqeKrLRIheMgEcLXDix/rQ+HseTuLPovkgGMUaDzdYno984M6xUXAOTxLlVEheQ1sSCYJI3IS4dLwi7JBu+8lITxV1ad+U20aknWZQb64+GqKN3M2qinKsU9ZGKwNbt+1r4z3d619miAtSvvQIg/5jWQhclcM36//NSRmCidiRRJixnICsvCLPCtxCxLbGEgR9ciDX/yYxSRGc11saqZpWkNZY8BywX3MI4wVZstoBte2vCMMQZzzF1NaZGZm0nRjY9VHmN2yJpvgN0AHQHWA8Y2eVk/qFMuEKSykHVTbcLtH2gL8jvL9nf1n2xmE6Ss8n06/vx+XTY5BF6jd6gtyhBH9A5+oJmaI4Y+oH+oGt0E7wLZsEy+N6HBqMh5xX6zwL6F3Zc1dw= R AAACo3icZZFLa9wwEMe17it1X0l67MV0WehpsbeF9hjopdBLErKbwMoEWR7viuhhpHFbY/wJ2mPz4fptKj+2pJsBwV+/mZHmkZVSOIzjP5PgwcNHj58cPA2fPX/x8tXh0fHKmcpyWHIjjb3KmAMpNCxRoISr0gJTmYTL7OZz57/8BtYJoy+wLiFVbKNFIThDj87Orw+n8TzuLbovklFMyWin10eTXzQ3vFKgkUvm3DqJS0wbZlFwCW1IKwcl4zdsA2svNVPg0qavtI1mnuRRYaw/GqOe3s1omHKuVpmPVAy3bt/XwX++2V1nh0pUP/YKwOJT2ghdVgiaD/8XlYzQRN00olxY4ChrLxi3wrcQ8S2zjKOfWUg1fOdGKabzhmpjVbtO0oZKKJDKFVicJtSKzRap7W5tGIY0h4JmrqGZkXnXiZHtAFXR0K7IrNiBbATZDvABcLbLyf1DuXClZLXDup9uH2iHQF+Q31+yv637YrWYJ+/ni7MP05PFuMkD8oa8Je9IQj6SE/KFnJIl4QTIT/Kb3Aaz4GtwHlwMocFkzHlN/rMg/QtMQtO0 ✓ AAACqHicZZFLj9MwEMfd8NglvHbhyCWiWglxqJKCBMeVuHAsEm0X1dHKdiatWT8ie8ISRf0GHLjCN+Pb4CQtWrojWfr7NzP2PHilpMc0/TOK7ty9d//o+EH88NHjJ09PTp8tvK2dgLmwyroLzjwoaWCOEhVcVA6Y5gqW/OpD519+A+elNZ+xqSDXbG1kKQXDgBYUN4Ds8mScTtLektsi24kx2dns8nT0gxZW1BoMCsW8X2VphXnLHEqhYBvT2kPFxBVbwypIwzT4vO3L3SZngRRJaV04BpOe3sxomfa+0TxEaoYbf+jr4D/f2U1nhyrU3w8KwPJ93kpT1QhGDP+XtUrQJt1IkkI6EKiaIJhwMrSQiA1zTGAYXEwNXAurNTNFS411ervK8pYqKJGqBTgcZ9TJ9Qap627bOI5pASXlvqXcqqLrxKrtAHXZ0q5IXu4B3wG+B2IAgu1zivBQIX2lWOOx6afbB7ohMBQU9pcdbuu2WEwn2ZvJ9NPb8fl0t8lj8oK8JK9IRt6Rc/KRzMicCPKV/CS/yO/odTSLltGXITQa7XKek/8s4n8B1K7WBg== ⌫ R AAACp3icZZFLj9MwEMfd8FrCaxeOXCKqleBSNQUJjitx4caCaLdSHa1sZ9Ja60dkT4AoyjdA4gofjW+D8yhauiNZ+vs3M/Y8eKmkx/n8zyS6dfvO3XtH9+MHDx89fnJ88nTlbeUELIVV1q0586CkgSVKVLAuHTDNFVzwq/ed/+IrOC+t+YJ1CZlmWyMLKRgGtKSmSj5fHk/ns3lvyU2RjmJKRju/PJn8oLkVlQaDQjHvN+m8xKxhDqVQ0Ma08lAyccW2sAnSMA0+a/pq2+Q0kDwprAvHYNLT6xkN097XmodIzXDnD30d/Oc7ve7sUIn6+0EBWLzLGmnKCsGI4f+iUgnapJtIkksHAlUdBBNOhhYSsWOOCQxzi6mBb8JqzUzeUGOdbjdp1lAFBVK1AofTlDq53SF13a2N45jmUFDuG8qtyrtOrGoHqIuGdkXyYg/4CPgeiAEIts/Jw0O59KVitce6n24f6IbAUFDYX3q4rZtitZilr2eLT2+mZ4txk0fkOXlBXpKUvCVn5AM5J0siiCQ/yS/yO3oVfYxW0XoIjSZjzjPyn0XsL/sc1Ts= ⇤ AAACqHicZZFLj9MwEMfd8FrCaxeOXCKqldAeqqQgwXElLhyLRNtFdVjZjtOa9Uv2BIiifAMOXOGb8W1wHkVLdyRLf/9mxp4HtVJ4SNM/k+jW7Tt37x3djx88fPT4yfHJ05U3lWN8yYw07oISz6XQfAkCJL+wjhNFJV/Tq3edf/2VOy+M/gi15bkiWy1KwQgEtMJ2Jz6fXR5P01naW3JTZKOYotEWlyeTH7gwrFJcA5PE+02WWsgb4kAwydsYV55bwq7Ilm+C1ERxnzd9uW1yGkiRlMaFoyHp6fWMhijva0VDpCKw84e+Dv7znV53dsiC+n5QAJRv80ZoWwHXbPi/rGQCJulGkhTCcQayDoIwJ0ILCdsRRxiEwcVY82/MKEV00WBtnGo3Wd5gyUvAcsUdTDPsxHYH2HW3No5jXPASU99gamTRdWJkO0BVNrgrkpZ7QEdA94ANgJF9ThEeKoS3ktQe6n66faAbAkNBYX/Z4bZuitV8lr2azT+8np7Px00eoefoBXqJMvQGnaP3aIGWiKEv6Cf6hX5HZ9EiWkefhtBoMuY8Q/9ZRP8CJ53VuQ== ↵ AAACqHicdZFLbxMxEMed5VWWVwtHLhZRJcQh2k2gTW+VuHAMEkmK4lVle72JqR8re7YQrfYbcOAK34xvg3c3QaUSI1n6+zcz9jxYqaSHJPk9iO7cvXf/wcHD+NHjJ0+fHR49X3hbOS7m3CrrLhj1Qkkj5iBBiYvSCaqZEkt29b71L6+F89KaT7AtRabp2shCcgoBLQhV5YZeHg6T0cnZeJK8w8koCTadBpEmZ5PJCU47kiRDtLPZ5dHgO8ktr7QwwBX1fpUmJWQ1dSC5Ek1MKi9Kyq/oWqyCNFQLn9VduQ0+DiTHhXXhGMAdvZlRU+39VrMQqSls/G1fC//6jm86W1SC/narACimWS1NWYEwvP+/qBQGi9uR4Fw6wUFtg6DcydAC5hvqKIcwuJgY8ZVbranJa2Ks080qzWqiRAFELYSDYUqcXG+AuPbWxHFMclEQ5mvCrMrbTqxqeqiLmrRFsmIP2A6wPeA94HSfk4eHculLRbcett10u0DXB4aCwv72S8L/F4vxKJ2Mxh/fDs/Hu00eoJfoFXqNUnSKztEHNENzxNEX9AP9RL+iN9EsWkaf+9BosMt5gf6xiP0BOcbWNQ== x A AAACbXicbVHLbtQwFPWEQssU6AOxoqosRghWo2SK1C6L2HQ5SEyn0iQa2Tc3rTV+RLYDjKJ8RLfwZXwFv1BnkgVtuZKlo3OPr4/P5aUUzsfxn0H0ZOvps+2d58PdFy9f7e0fHF46U1nAGRhp7BVnDqXQOPPCS7wqLTLFJc756kvbn39H64TR3/y6xEyxay0KAcwHap6qgv5cfl7uj+JxvCn6GCQ9GJG+psuDwTTNDVQKtQfJnFskcemzmlkvQGIzTCuHJYMVu8ZFgJopdFm98dvQ94HJaWFsONrTDfvvjZop59aKB6Vi/sY97LXk/3qLyhdnWS10WXnU0D1UVJJ6Q9vP01xYBC/XATCwInilcMMsAx8iGg7THIuQSJ22k3nRdAR3dcqNzFtHRvakgk4FLDD3/QGEUFzQafwBRimm8zqtOLPNIskC0jnaThTmBrYeJU2YEXaQPEz8MbicjJOT8eTrp9H5pN/GDnlL3pGPJCGn5JxckCmZESArckt+kd+Dv9Gb6Cg67qTRoL/zmtyr6MMdvyG9hQ== x A AAACbXicbVHLbtQwFPWEQssU6AOxoqosRghWo2SK1C6L2HQ5SEyn0iQa2Tc3rTV+RLYDjKJ8RLfwZXwFv1BnkgVtuZKlo3OPr4/P5aUUzsfxn0H0ZOvps+2d58PdFy9f7e0fHF46U1nAGRhp7BVnDqXQOPPCS7wqLTLFJc756kvbn39H64TR3/y6xEyxay0KAcwHap6qgv5cfl7uj+JxvCn6GCQ9GJG+psuDwTTNDVQKtQfJnFskcemzmlkvQGIzTCuHJYMVu8ZFgJopdFm98dvQ94HJaWFsONrTDfvvjZop59aKB6Vi/sY97LXk/3qLyhdnWS10WXnU0D1UVJJ6Q9vP01xYBC/XATCwInilcMMsAx8iGg7THIuQSJ22k3nRdAR3dcqNzFtHRvakgk4FLDD3/QGEUFzQafwBRimm8zqtOLPNIskC0jnaThTmBrYeJU2YEXaQPEz8MbicjJOT8eTrp9H5pN/GDnlL3pGPJCGn5JxckCmZESArckt+kd+Dv9Gb6Cg67qTRoL/zmtyr6MMdvyG9hQ== (b) Fig. 8. Circular p erimeter case. (a) States [ r, θ ] and the in- truder’s heading angle ψ A . (b) Computation of the approac h angle φ ∗ . When the p erimeter is a circle with radius R , the sym- metry allo ws us to reduce the state space to [ r , θ ], where r is the intruder’s radial distance from the p erimeter, and θ ∈ [ − π , π ] is the relative p olar angle b et ween the defender and the in truder with resp ect to the center of the circle. Whether the in truder is in the left region or the right region is determined b y the sign of θ : x A ∈ Ω L ( s D ) if θ > 0, and x A ∈ Ω R ( s D ) if θ < 0. The singular surfaces corresp ond to the lines θ = 0 and θ = ± π . The intruder con trol is parameterized by its sp eed v A and the heading ψ A as shown in Fig. 8a. Theorem 4 (from [39]) F or a cir cular p erimeter, the optimal str ate gies ar e ω ∗ D = sgn( θ ) , and (26) ( v ∗ A , ψ ∗ A ) = ν, sgn( θ ) sin − 1 ν R R + r , (27) and the value of the game is V ( r , θ ; ν ) = | θ | − F ( r ) + F (0) , (28) wher e F ( r ) = s R + r ν R 2 − 1 − cos − 1 ν R R + r . (29) The sign function accommo dates the switc hing betw een the left and the righ t regions. The in trusion strategy allo ws further geometric inter- pretation: the optimal path of the intruder is to mov e to w ards the tangent p oint of the circle with radius ν R (see Fig. 8b) [39]. T o verify this result with the strategy giv en in (16), we compute the approach angle as follo ws. The angle α in Fig. 8b is α = sin − 1 ν R R = sin − 1 ( ν ). The approach angle is φ ∗ = π − π 2 − α = π 2 − sin − 1 ( ν ), whic h gives the relation φ ∗ = cos − 1 ( ν ). Recalling the re- sults in (4), the circular case matches with our analysis in this pap er. The other sp ecial case is when the sp eed ratio is ν = 1. Notice that the ob jective function now has the form J ∗ L = s D ) L − k x A ) L k , in which case the level set V = 0 is generated by the locus of intruder p ositions where k x A ) L k = s D ) L (and similarly for the righ t breaching p oin ts). In addition, recalling Remark 1, the optimal breac hing points are s L = s tan,L and s R = s tan,R . These prop erties are sufficient to see that the barrier ∂ R A is giv en b y a curve called the involute — a lo cus of the tip of a taut string unw ound from the geometry . The left and the right part of the barrier corresp onds to unwinding the string in ccw and cw directions. 4 Tw o vs. One Game The next building blo ck is the game pla yed b et w een t w o defenders ( D i , D j ) and one in truder. The states of the system are no w [ s D i , s D j , x A ]. W e follo w the same struc- ture as the previous section and discuss b oth the game of kind and the game of degree. 4.1 Ge ometries A naive extension of the one vs. one game will conclude that the in truder will win if it is in the winning region against b oth defenders D i and D j , i.e., if x A is in R I , { x | V ( s D i , x ) > 0 and V ( s D j , x ) > 0 } . (30) The subscript I is used to reflect the fact that the games against D i and D j are indep endently considered. How- ev er, in reality , the optimal intrusion strategy and the winning regions cannot b e obtained by treating D i and D j separately , since the intruder must av oid b oth D i and D j sim ultaneously . Observ e that no w the game space is divided in to tw o parts by Γ aff ( s D i ) and Γ aff ( s D j ) (see Fig. 9a). W e show ed in Sec. 3.2 that the in truder cannot win if it reaches the afferent surface, so x A ∈ Γ aff ( s D i ) ∪ Γ aff ( s D j ) is a part of the terminal condition. Since x A cannot cross these surfaces, we focus our attention on the part of the game space that con tains the intruder (shaded region in Fig. 9a) and ignore the other. Without the loss of generalit y , we define D i to be the one on the cw side and D j to b e the one on ccw side (Fig. 9a). The opposite point s op D w as important in the one vs. one game b ecause it w as the farthest p oint from a single de- 11 irrelevant region R i AAACr3icZZFLb9QwEMe94VXCqy1HLhGrSpxWSUGix0pcemwrdrfSOiy24+xa9SPYE2hk5Rtw50o/Ft8GJ5tFZTuSpb9/M2PPg1ZSOEjTP6PowcNHj5/sPY2fPX/x8tX+weHMmdoyPmVGGntFieNSaD4FAZJfVZYTRSWf0+tPnX/+nVsnjP4MTcVzRVZalIIRCCjHisCaEekv26VY7o/TSdpbcl9kgxijwc6XB6OfuDCsVlwDk8S5RZZWkHtiQTDJ2xjXjleEXZMVXwSpieIu933VbXIUSJGUxoajIenp3QxPlHONoiGyq9Lt+jr4z3d019mhCtTNTgFQnuRe6KoGrtnm/7KWCZikm0xSCMsZyCYIwqwILSRsTSxhEOYXY81/MKMU0YXH2ljVLrLcY8lLwHLGLYwzbMVqDdh2tzaOY1zwElPnMTWy6Doxst1AVfp+8rTcAjoAugXMb3czkCI8VAhXSdI4aPrp9oF2ExgKCvvLdrd1X8yOJ9n7yfHFh/HpybDJPfQGvUXvUIY+olN0hs7RFDH0Df1Cv9FtlEXz6Ev0dRMajYac1+g/i8RfVsTZKA== R j AAACr3icZZFLb9QwEMe94VXCq4Ujl4hVJU6rpFSix0pceiwVu1tpHRbbcXZN/Qj2BIisfIPeuZaPxbfByWZR2Y5k6e/fzNjzoJUUDtL0zyi6d//Bw0d7j+MnT589f7F/8HLmTG0ZnzIjjb2kxHEpNJ+CAMkvK8uJopLP6dWHzj//zq0TRn+CpuK5IistSsEIBJRjRWDNiPQX7fLrcn+cTtLekrsiG8QYDXa+PBhd48KwWnENTBLnFllaQe6JBcEkb2NcO14RdkVWfBGkJoq73PdVt8lhIEVSGhuOhqSntzM8Uc41iobIrkq36+vgP9/hbWeHKlA/dwqA8iT3Qlc1cM02/5e1TMAk3WSSQljOQDZBEGZFaCFha2IJgzC/GGv+gxmliC481saqdpHlHkteApYzbmGcYStWa8C2u7VxHOOCl5g6j6mRRdeJke0GqtL3k6flFtAB0C1gfrubgRThoUK4SpLGQdNPtw+0m8BQUNhftrutu2J2NMneTY4+Ho9PT4ZN7qHX6A16izL0Hp2iM3SOpoihb+gXukG/oyyaR5+jL5vQaDTkvEL/WST+AlkD2Sk= R mid AAACunicZZHNbtQwEMe94aMlfG1B4sIlYlWJ0yppkeiBQyUuHAtit5XW0cp2nF1r/RHZE9rI5A14Cq7wQrwNTjaLynYkS//8ZhzPzJ9WUjhI0z+j6N79Bw8PDh/Fj588ffZ8fPRi7kxtGZ8xI429osRxKTSfgQDJryrLiaKSX9LNxy5/+Y1bJ4z+Ck3Fc0VWWpSCEQhoOX6FFYE1I9J/aZcY+A14JYp2OZ6k07SP5K7IBjFBQ1wsj0Y/cGFYrbgGJolziyytIPfEgmCStzGuHa8I25AVXwSpieIu9/0AbXIcSJGUxoajIenp7RueKOcaRUNl167bz3XwX+74drJDFaibvQagPMu90FUNXLPt+2UtEzBJt6SkEJYzkE0QhFkRRkjYmljCIKwyxppfM6MU0YXH2ljVLrLcY8lLwHLOLUwybMVqDdh2X20cx7jgJabOY2pk0U1iZLuFqvS9BbTcAToAugPM70waSBF+VAhXSdI4aPrt9oV2WxgaCv5l+27dFfOTaXY6Pfn8bnJ+Njh5iF6jN+gtytB7dI4+oQs0Qwx9Rz/RL/Q7+hDRSESbbWk0Gu68RP9FBH8BQ9zdnQ== s mid AAACrnicZZFLa9wwEMe17iOp+0raYy+mS6CnxU4DzTGQS48pdDeBlVkkebwrooeRZtsY42/Qc6/t1+q3qfzYkm4GBH/9ZkaaB6+U9JimfybRo8dPnh4cPoufv3j56vXR8ZuFt1snYC6ssu6GMw9KGpijRAU3lQOmuYJrfnvZ+a+/gfPSmq9YV5BrtjaylIJhQNSvKMIdNloW7epoms7S3pKHIhvFlIx2tTqe/KCFFVsNBoVi3i+ztMK8YQ6lUNDGdOuhYuKWrWEZpGEafN70RbfJSSBFUloXjsGkp/czGqa9rzUPkZrhxu/7OvjPd3Lf2aEK9d1eAVie54001RbBiOH/cqsStEk3mKSQDgSqOggmnAwtJGLDHBMYxhdTA9+F1ZqZoqHGOt0us7yhCkqkagEOpxl1cr1B6rpbG8cxLaCk3DeUW1V0nVjVDlCXDe2K5OUO8BHwHRADEGyXU4SHCukrxWqPdT/dPtANgaGgsL9sf1sPxeJ0ln2cnX45m16cj5s8JO/Ie/KBZOQTuSCfyRWZE0Eq8pP8Ir+jNFpEebQaQqPJmPOW/GfR5i/et9j7 A1 A2 s D i AAACqXicZZFLa9wwEMe1Ttuk7itJj72YLoFCYbHTQHMMNIceE+g+6MoskizvitXDSOO2xvgb9JJr+8n6bSo/tqSbAcFfv5mR5kELKRzE8Z9RcPDo8ZPDo6fhs+cvXr46PjmdOVNaxqfMSGMXlDguheZTECD5orCcKCr5nG4/tf75N26dMPoLVAVPFVlrkQtGwKO5W9XXK9GsjsfxJO4seiiSQYzRYDerk9FPnBlWKq6BSeLcMokLSGtiQTDJmxCXjheEbcmaL73URHGX1l29TXTmSRblxvqjIero/YyaKOcqRX2kIrBx+74W/vOd3Xe2qAD1Y68AyC/TWuiiBK5Z/39eyghM1M4kyoTlDGTlBWFW+BYitiGWMPCTC7Hm35lRiuisxtpY1SyTtMaS54DljFsYJ9iK9QawbW9NGIY44zmmrsbUyKztxMimhyqvcVskzXeADoDuAOsBI7uczD+UCVdIUjmouul2gbYP9AX5/SX723ooZueT5MPk/PZifHUxbPIIvUFv0TuUoI/oCn1GN2iKGNqiO/QL/Q7eB7fBIvjahwajIec1+s8C9hfd9tZ2 s D j AAACqXicZZFLa9wwEMe17it1X0l77MV0CRQKi50E2mOgOfSYQPdBV2aRZHlXXT2MNG5rjL9BLr0mn6zfpvJjS7oZEPz1mxlpHrSQwkEc/xkFDx4+evzk4Gn47PmLl68Oj17PnCkt41NmpLELShyXQvMpCJB8UVhOFJV8TrefW//8B7dOGP0VqoKniqy1yAUj4NHcreqL1fdmdTiOJ3Fn0X2RDGKMBrtcHY2ucWZYqbgGJolzyyQuIK2JBcEkb0JcOl4QtiVrvvRSE8VdWnf1NtGxJ1mUG+uPhqijdzNqopyrFPWRisDG7fta+M93fNfZogLUr70CIP+U1kIXJXDN+v/zUkZgonYmUSYsZyArLwizwrcQsQ2xhIGfXIg1/8mMUkRnNdbGqmaZpDWWPAcsZ9zCOMFWrDeAbXtrwjDEGc8xdTWmRmZtJ0Y2PVR5jdsiab4DdAB0B1gPGNnlZP6hTLhCkspB1U23C7R9oC/I7y/Z39Z9MTuZJKeTk6uz8fnZsMkD9Ba9Q+9Rgj6ic/QFXaIpYmiLfqMbdBt8CK6CRfCtDw1GQ84b9J8F7C/gNtZ3 s mid AAACrnicZZFLa9wwEMe17iOp+0raYy+mS6CnxU4D6TGQS48pdDeBlVkkebwrooeRZtsY42/Qc6/t1+q3qfzYkm4GBH/9ZkaaB6+U9JimfybRo8dPnh4cPoufv3j56vXR8ZuFt1snYC6ssu6GMw9KGpijRAU3lQOmuYJrfnvZ+a+/gfPSmq9YV5BrtjaylIJhQNSvKMIdNloW7epoms7S3pKHIhvFlIx2tTqe/KCFFVsNBoVi3i+ztMK8YQ6lUNDGdOuhYuKWrWEZpGEafN70RbfJSSBFUloXjsGkp/czGqa9rzUPkZrhxu/7OvjPd3Lf2aEK9d1eAVh+yhtpqi2CEcP/5VYlaJNuMEkhHQhUdRBMOBlaSMSGOSYwjC+mBr4LqzUzRUONdbpdZnlDFZRI1QIcTjPq5HqD1HW3No5jWkBJuW8ot6roOrGqHaAuG9oVycsd4CPgOyAGINgupwgPFdJXitUe6366faAbAkNBYX/Z/rYeisXpLPs4O/1yNr04Gzd5SN6R9+QDycg5uSCfyRWZE0Eq8pP8Ir+jNFpEebQaQqPJmPOW/GfR5i/dg9j3 (a) (b) a ↵ ( s D i ) AAACrHicfZHdahQxFMez41cdP7rVS28Gl0IVWWaqYC8LFvRGrNBtC5thOJM52YYmkyHJSJcwT+DTeKtP4tuY2Z2F2ooHQv78zjmc5H/KRgrr0vT3KLpz9979B1sP40ePnzzdHu88O7W6NQxnTEttzkuwKEWNMyecxPPGIKhS4ll5+aHPn31DY4WuT9yywVzBohZcMHABFeNdWmpZ2aUKF/0ISkFBHV45D5x3e7bwR4XoXhXjSTpNV5HcFtkgJmSI42JnpGmlWauwdkyCtfMsbVzuwTjBJHYxbS02wC5hgfMga1Boc7/6T5fsBlIlXJtwapes6PUOD8r2Tw6VCtyFvZnr4b9y89bxg9yLumkd1mw9iLcycTrpzUkqYZA5uQwCmBHhrQm7AAPMBQvjOKYVclpaf820bg0V97SfV/INKAdQbgBbAwZ9zxEGWwx+DuBLgwacNq89BbNQcNUFmxb0Ta/+VyjqTWFQcVhRdnMht8Xp/jR7O93/+m5yeDAsa4u8IC/JHsnIe3JIPpFjMiOMfCc/yE/yK5pGJ9E8ytel0WjoeU7+ioj/AVZP1p8= a ↵ ( s D j ) AAACrHicfZHdatRAFMdn41eNX1u99Ca4FKrIklTBXhYs6I1YodsWdkI4mZzZjp2PMDORLiFP4NN4q0/i2zjZzUJtxQPD/Pmdczgz/1PWUjifpr9H0a3bd+7e27ofP3j46PGT8fbTE2cay3DGjDT2rASHUmiceeElntUWQZUST8uL933+9BtaJ4w+9ssacwULLbhg4AMqxju0NLJySxUu+gGUgoJ6vPQtcN7tuqI9LL52L4vxJJ2mq0huimwQEzLEUbE9MrQyrFGoPZPg3DxLa5+3YL1gEruYNg5rYBewwHmQGhS6vF39p0t2AqkSbmw42icrerWjBeX6J4dKBf7cXc/18F+5eeP5ft4KXTceNVsP4o1MvEl6c5JKWGReLoMAZkV4a8LOwQLzwcI4jmmFnJauvWJat4aKt7SfV/INKAdQbgBbAwZ9zyEGWyx+CuBzjRa8sa9aCnah4LILNi3o6179r1DoTWFQcVhRdn0hN8XJ3jR7M9378nZysD8sa4s8Jy/ILsnIO3JAPpIjMiOMfCc/yE/yK5pGx9E8ytel0WjoeUb+ioj/AVhz1qA= s D j AAACjHicfZFtS9xAEMf3YmttrNaHl30Teggi5UisUKEIgiJ9U2qh5wmX45jdTM719iHsbopHyIfwrf1k/TZu7nLQaunAwp/f/IeZnaGF4NbF8e9OsPLi5eqrtdfh+puNzbdb2ztXVpeGYZ9poc01BYuCK+w77gReFwZBUoEDOj1r8oOfaCzX6oebFTiSMFE85wycRwM7rs7Ht/V4qxv34nlEz0XSii5p43K83dFpplkpUTkmwNphEhduVIFxnAmsw7S0WACbwgSHXiqQaEfVfN462vMki3Jt/FMumtM/KyqQ1s4k9U4J7sY+zTXwX7lh6fLjUcVVUTpUbNEoL0XkdNR8Psq4QebEzAtghvtZI3YDBpjzKwrDMM0wT6mtUqpF1kygRb2AMq/Sph/Nl4C2gC4BWwAGTc05+rUY/OrBtwINOG0OqhTMRMJd7dc0ST806n9GrpZGr0J/ouTpQZ6Lq8Ne8rF3+P2oe3rcHmuNvCPvyT5JyCdySr6QS9InjEzJPXkgv4LN4Cj4HJwsrEGnrdklf0Vw8Qg6Ysl7 s D i AAACjHicfZFtSxtBEMc319ra0/pQX/bN0SCIlHCnQgUpCJXSN0ULjRFyIczuzSVL9uHY3ZOG4z5E3+on89t0L7mA1dKBhT+/+Q8zO0MLwa2L44dO8OLl2qvX62/Cjc23W9s7u++urS4Nwz7TQpsbChYFV9h33Am8KQyCpAIHdPalyQ9u0Viu1U83L3AkYaJ4zhk4jwZ2XF2MeT3e6ca9eBHRc5G0okvauBrvdnSaaVZKVI4JsHaYxIUbVWAcZwLrMC0tFsBmMMGhlwok2lG1mLeO9j3Jolwb/5SLFvRxRQXS2rmk3inBTe3TXAP/lRuWLj8dVVwVpUPFlo3yUkROR83no4wbZE7MvQBmuJ81YlMwwJxfURiGaYZ5Sm2VUi2yZgIt6iWUeZU2/Wi+ArQFdAXYEjBoai7Qr8Xgdw8uCzTgtDmsUjATCb9qv6ZJ+rFR/zNytTJ6FfoTJU8P8lxcH/WS497Rj5Pu+Wl7rHXynnwgByQhn8g5+UauSJ8wMiO/yR25D7aCk+As+Ly0Bp22Zo/8FcHXPzg/yXo= Fig. 9. Regions in the tw o vs. one game. (a) Game space divided by the tw o afferent surfaces. (b) F urther division in to three regions based on the location of the left and righ t breac hing p oints. fender. The analogy in the tw o vs. one game is the mid- p oin t, s mid , b etw een the tw o defenders, which achiev es the maximum distance from the nearest defender. In deriving the in truder strategy , w e consider the follo w- ing quantit y: J ij = min { s D i ) B , s B ) D j } − 1 ν k γ ( s B ) − x A k , (31) where the subscript ij denotes the indices of the de- fenders. The interpretation is similar to J L and J R in Sec. 3. It is the expected safe distance assuming that (i) D i mo v es ccw, (ii) D j mo v es cw, and (iii) the intruder mo v es on a straigh t line path tow ards some breaching p oin t s B ∈ [ s D i , s D j ]. F or this function, w e can consider three cases depending on where s B lies in: J ij = J L ( s B ; s D i , x A ) if s B ∈ [ s D i s mid ) J R ( s B ; s D j , x A ) if s B ∈ ( s mid s D j ] J mid ( s D i , s D j , x A ) otherwise: i.e., s B = s mid , (32) where J mid , 1 2 s D i ) D j − 1 ν k γ ( s mid ) − x A k (33) describ es how muc h longer it takes for the defenders to reac h s mid than it do es for the intruder. The division describ ed abov e is possible because only D i ’s position is activ e in the calculation of J ij when the breaching p oint is in [ s D i , s mid ), and similarly only D j ’s p osition matters when s B ∈ ( s mid , s D j ]. F ollo wing the ab ov e decomp osition, the game space that con tains the intruder can b e further divided into three -0.2 -0.2 -0.2 -0.1 -0.1 -0.1 -0.1 -0.1 -0.1 0 0 0 0 0 0 0.1 0.1 0.1 0.1 0.2 0.3 s D i AAACbXicbZHNatwwEMe1btqmm34kLT0lBNOltKfF3gaSYyA99LiFbjawNos0Hidi9WEkuWERfohemyfLU+QVKq99aD4GBH9+89doNMMqwa1LkttB9Gzr+YuX26+GO6/fvH23u/f+3OraAM5AC20uGLUouMKZ407gRWWQSiZwzlZnbX7+G43lWv1y6wpzSS8VLzlQF9DcLv33JW+Wu6NknGwifizSXoxIH9Pl3mCaFRpqicqBoNYu0qRyuafGcRDYDLPaYkVhRS9xEaSiEm3uN/028edAirjUJhzl4g39/4an0tq1ZMEpqbuyD3MtfCq3qF15knuuqtqhgu6hshax03H7+bjgBsGJdRAUDA+9xnBFDQUXRjQcZgWWmSx91lZmZdMBZn3GtCjajrTooYTOBTSQ+/0BhKHY4FN4DVpKqgqf1YyaZpHmQakCTWcKdQP1o7QJNcIO0ocTfyzOJ+P023jy82h0Oum3sU32ySfylaTkmJySH2RKZgTIivwhf8nN4C76GB1Eh501GvR3PpB7EX35B59ZvfQ= s D j AAACbXicbZHbatwwEIa17indHpI05KqhmC6lvVrsbaG5DCQXudxCNxtYm0UajxN1dTCS3LIIP0Ru2yfLU+QVIq990RwGBD/f/BqNZlgluHVJcj2Injx99vzF1svhq9dv3m7v7L47s7o2gDPQQptzRi0KrnDmuBN4Xhmkkgmcs9Vxm5//RmO5Vj/dusJc0gvFSw7UBTS3S3+y/NUsd0bJONlE/FCkvRiRPqbL3cE0KzTUEpUDQa1dpEnlck+N4yCwGWa1xYrCil7gIkhFJdrcb/pt4k+BFHGpTTjKxRv6/w1PpbVryYJTUndp7+da+FhuUbvyMPdcVbVDBd1DZS1ip+P283HBDYIT6yAoGB56jeGSGgoujGg4zAosM1n6rK3MyqYDzPqMaVG0HWnRQwmdC2ggd/sDCEOxwafwD2gpqSp8VjNqmkWaB6UKNJ0p1A3Uj9Im1Ag7SO9P/KE4m4zTr+PJj2+jo0m/jS3ynnwkX0hKvpMjckqmZEaArMgV+Uv+DW6i/egg+tBZo0F/Z4/ciejzLaFdvfU= s mid AAACcnicbVHLahwxENSOncTZPPy6xZdxlkAOYZlZB5KjIZcc15C1DathkXp6bGE9BkljexHzG746v5X/yAdEszuH+NEgKKqrW0U1r6VwPsv+DJKNzRcvX229Hr55++799s7u3qkzjQWcgZHGnnPmUAqNMy+8xPPaIlNc4hm/+tH1z67ROmH0L7+ssVDsQotKAPORom5BPd76oETZLnZG2ThbVfoU5D0Ykb6mi93BlJYGGoXag2TOzfOs9kVg1guQ2A5p47BmcMUucB6hZgpdEVam2/RTZMq0MjY+7dMV+/9EYMq5peJRqZi/dI97Hflcb9746nsRhK4bjxrWH1WNTL1JuwTSUlgEL5cRMLAiek3hklkGPuY0HNISK6qqQLvNvGrXBHeBciPLzpGRPalgrQIWmYf+AGIoLuo03oBRiuky0IYz287zIiJdol2L4t7IhlHexh3xBvnjxJ+C08k4PxpPTr6Ojif9NbbIAflIPpOcfCPH5CeZkhkBUpM7ck9+D/4mH5LDpD9dMuhn9smDSr78AxM2wHU= s D i AAACbXicbZHNatwwEMe1btqmm34kLT0lBNOltKfF3gaSYyA99LiFbjawNos0Hidi9WEkuWERfohemyfLU+QVKq99aD4GBH9+89doNMMqwa1LkttB9Gzr+YuX26+GO6/fvH23u/f+3OraAM5AC20uGLUouMKZ407gRWWQSiZwzlZnbX7+G43lWv1y6wpzSS8VLzlQF9DcLv33JW+Wu6NknGwifizSXoxIH9Pl3mCaFRpqicqBoNYu0qRyuafGcRDYDLPaYkVhRS9xEaSiEm3uN/028edAirjUJhzl4g39/4an0tq1ZMEpqbuyD3MtfCq3qF15knuuqtqhgu6hshax03H7+bjgBsGJdRAUDA+9xnBFDQUXRjQcZgWWmSx91lZmZdMBZn3GtCjajrTooYTOBTSQ+/0BhKHY4FN4DVpKqgqf1YyaZpHmQakCTWcKdQP1o7QJNcIO0ocTfyzOJ+P023jy82h0Oum3sU32ySfylaTkmJySH2RKZgTIivwhf8nN4C76GB1Eh501GvR3PpB7EX35B59ZvfQ= s D j AAACbXicbZHbatwwEIa17indHpI05KqhmC6lvVrsbaG5DCQXudxCNxtYm0UajxN1dTCS3LIIP0Ru2yfLU+QVIq990RwGBD/f/BqNZlgluHVJcj2Injx99vzF1svhq9dv3m7v7L47s7o2gDPQQptzRi0KrnDmuBN4Xhmkkgmcs9Vxm5//RmO5Vj/dusJc0gvFSw7UBTS3S3+y/NUsd0bJONlE/FCkvRiRPqbL3cE0KzTUEpUDQa1dpEnlck+N4yCwGWa1xYrCil7gIkhFJdrcb/pt4k+BFHGpTTjKxRv6/w1PpbVryYJTUndp7+da+FhuUbvyMPdcVbVDBd1DZS1ip+P283HBDYIT6yAoGB56jeGSGgoujGg4zAosM1n6rK3MyqYDzPqMaVG0HWnRQwmdC2ggd/sDCEOxwafwD2gpqSp8VjNqmkWaB6UKNJ0p1A3Uj9Im1Ag7SO9P/KE4m4zTr+PJj2+jo0m/jS3ynnwkX0hKvpMjckqmZEaArMgV+Uv+DW6i/egg+tBZo0F/Z4/ciejzLaFdvfU= s mid AAACcnicbVHLahwxENSOncTZPPy6xZdxlkAOYZlZB5KjIZcc15C1DathkXp6bGE9BkljexHzG746v5X/yAdEszuH+NEgKKqrW0U1r6VwPsv+DJKNzRcvX229Hr55++799s7u3qkzjQWcgZHGnnPmUAqNMy+8xPPaIlNc4hm/+tH1z67ROmH0L7+ssVDsQotKAPORom5BPd76oETZLnZG2ThbVfoU5D0Ykb6mi93BlJYGGoXag2TOzfOs9kVg1guQ2A5p47BmcMUucB6hZgpdEVam2/RTZMq0MjY+7dMV+/9EYMq5peJRqZi/dI97Hflcb9746nsRhK4bjxrWH1WNTL1JuwTSUlgEL5cRMLAiek3hklkGPuY0HNISK6qqQLvNvGrXBHeBciPLzpGRPalgrQIWmYf+AGIoLuo03oBRiuky0IYz287zIiJdol2L4t7IhlHexh3xBvnjxJ+C08k4PxpPTr6Ojif9NbbIAflIPpOcfCPH5CeZkhkBUpM7ck9+D/4mH5LDpD9dMuhn9smDSr78AxM2wHU= c = ⌫ 2 s D i ) D j AAAD93icjVJNbxMxEHUbPsry0RSOXCyiSFwaZbeR4IJUCQ4ci0TaSuso8nq9yVLbu7K9bSLLv4AfwQ1x7bX8Ev4N42xUkRQkLO1q9s288Zu3k9WiNHY4/LWz27l3/8HDvUfR4ydPn+13D56fmqrRjI9ZJSp9nlHDRan42JZW8PNacyozwc+yi/chf3bJtSkr9dkuaz6RdKbKomTUAjTt9hl+h0mhKXNENd4lnlDNBFczO3cfpqWH1xc/7faGg+Hq4LtBvA56aH1Opge7NySvWCO5skxQY9J4WNuJo9qW0N1HpDG8puyCzngKoaKSm4lbzeNxH5AcF5WGR1m8Qv9kOCqNWcoMKiW1c7OdC+Dfcmlji7cTV6q6sVyx9qKiEdhWOJiD81JzZsUSAsp0CVoxm1Mwx4KFUURyXhBZOBI6Z4Vvgcw4klUiD4oqsQYla6sYBWRTH2NgioE6xa9YJSVVuSNNRrVP4wlEKue6LYK+gLpe7KFHH8N/XJp5pS3Vurra5G/mQqf0KBi+EqG5cP0IY0zmWbVwRDeCpyQvJV/UmgSPQ6yShFi+sOE7ORwktSVApItJEOAGo9p633aRF1yrw5Fs1v2Ci0ByY+/gXy+9k94pT1pD3AjkhwE251WlveTMpwlonFMYFXxdeD+Fy7aG6SV+yyyQdctd0f6LdbvXK6L5FyeKYNvj7d2+G5wmg/hokHwa9Y6T9d7voZfoFXqNYvQGHaOP6ASNEUNf0TW6QT87y863zvfOj7Z0d2fNeYE2Tuf6N8E+WKM= (a) (b) Fig. 10. (a) Level set of V ij . (b) Geometric construction of the zero level set of V ij . regions (see Fig. 9b): R i = { x A | s L ∈ [ s D i s mid ) } , R j = { x A | s R ∈ ( s mid s D j ] } , and (34) R mid = { x A | s L / ∈ [ s D i s mid ) , s R / ∈ ( s mid s D j ] } . If x A ∈ R i ( s D i , s D j ), the intruder can mov e tow ards s L to pla y optimally against D i without considering D j , since s D j will not b e active in J ij . Similarly when x A ∈ R j ( s D i , s D j ), the intruder can ignore D i and choose s R to play optimally against D j . How ever, when x A ∈ R mid , the intruder cannot simply choose one defender to play against b ecause the optimal b eha vior against D i mak es D j to b e the active defender and vice v ersa. A goo d compromise in this case is to approach s mid . No w we hav e a candidate intrusion strategy: u ∗ A = ν ˆ x A ) opt , (35) where ˆ x A ) opt = γ ( s opt ) − x A k γ ( s opt ) − x A k , and the optimal breaching p oin t is defined by s opt ( x A , s D 1 , s D 2 ) = s L if x A ∈ R i ( s D i , s D j ) s R if x A ∈ R j ( s D i , s D j ) s mid otherwise. (36) The asso ciated v alue (to b e pro ved in Theorem 6) is giv en as follows: V ij = J ∗ L ( s D i , x A ) if x A ∈ R i ( s D i , s D j ) J ∗ R ( s D j , x A ) if x A ∈ R j ( s D i , s D j ) J mid ( s D i , s D j , x A ) otherwise , (37) where the regions are defined in (34). Fig. 10a sho ws the lev el sets of V ij ( s D i , s D j , x A ). Each level set is a combi- nation of three curves: the tw o level sets from the one vs. one games and a circle cen tered at s mid . Sp ecifically , 12 the zero level set { x A | V ij ( s D i , s D j , x A ) = 0 } is a com- bination of the tw o barriers, and a circle with radius c = 1 2 ν s D i ) D j , (38) as shown in Fig. 10b. 4.2 Winning R e gions Analogous to the tw o-play er game, we define the intruder winning region to b e the sup erlev el set of V ij as follows: R C ( s D i , s D j ) , { x A | V ij ( s D i , s D j , x A ) > 0 } . (39) The subscript C is used to highlight the c o op er ative na- ture of the associated defense strategy . The follo wing lemma giv es a sufficien t condition for in truder’s victory: Lemma 4 If the initial c onfigur ation satisfies x A ( t 0 ) ∈ R C ( s D i ( t 0 ) , s D j ( t 0 )) , then r e gar d less of the defender’s str ate gy, the intruder wins the game of kind using u ∗ A define d in (35) . PR OOF. If the in truder starts in R i ∩ R C , then it wins against D i b y approaching s L since J ∗ L ( s D i , x A ) > 0. In this case, although s L is sub optimal against D j , the in truder still wins b ecause s L ) D j ( t 0 ) > s D i ) L ( t 0 ): D j is farther from s L than D i . With the same argumen t, the in truder wins if it starts in R j ∩ R C . Finally , if x A ∈ R mid ∩ R C , then the intruder can reac h s mid b efore either of the defenders b ecause J mid > 0. Observ e that the intruder-winning region R C is smaller than R I deriv ed from the one vs. one game analysis. The gap is generated by the co op eration b etw een the defenders. Definition 4 The p air e d-defense r e gion is define d by: R pair ( s D i , s D j ) = R I ( s D i , s D j ) − R C ( s D i , s D j ) . (40) The co op eration arises in the form of “pincer mo ve- men t,” whic h is a tactic where the tw o defenders ap- proac h the intruder from b oth cw and ccw sides at the same time. In our problem the corresp onding con trol in- put is [ ω D i , ω D j ] = [1 , − 1]. By considering this defender strategy , the next lemma sho ws that x A ∈ R C is also a necessary condition for the in truder to win the game of kind: Lemma 5 If the initial c onfigur ation satisfies x A ∈ R p air ( s D i , s D j ) , and if the defender p air uses a pin- c er movement, [ ω D i , ω D j ] = [1 , − 1] , then either x A ∈ R D ( s D i ) or x A ∈ R D ( s D j ) o c curs b efor e the in- truder r e aches the p erimeter: i.e., the defender p air wins. (a) (b) s mid AAACYHicbVDLThsxFHWGPtLpAwK7djNqVKmraCYg0VWFxKZLkBpAikeR7bkDFn6M7DvQyJrfYAu/1W2/pJ4kiwK9kqWjc889Pjq8UdJjnv8eJFsvXr56PXyTvn33/sP2zmj3zNvWCZgJq6y74MyDkgZmKFHBReOAaa7gnF8f9/vzG3BeWvMTlw2Uml0aWUvBMFLULyjCLwxaVt1iZ5xP8tVkz0GxAWOymZPFaPCdVla0GgwKxbyfF3mDZWAOpVDQpbT10DBxzS5hHqFhGnwZVqG77Etkqqy2Lj6D2Yr99yIw7f1S86jUDK/8011P/m83b7H+VgZpmhbBiPVHdasytFnfQFZJBwLVMgImnIxZM3HFHBMYe0pTWkFNdR1o78zrbk1wHyi3quoTWdWlj9MIESvwUWrgVlitmakCbTlz3bwoIzIVuLUoukQ2jIsuesTGi6f9Pgdn00mxP5meHoyPppvuh+QT+Uy+koIckiPyg5yQGRGkIXfknjwM/iTDZDsZraXJYHOzRx5N8vEvTGG5Gg== s mid AAACYHicbVDLThsxFHWGPtLpAwK7djNqVKmraCYg0VWFxKZLkBpAikeR7bkDFn6M7DvQyJrfYAu/1W2/pJ4kiwK9kqWjc889Pjq8UdJjnv8eJFsvXr56PXyTvn33/sP2zmj3zNvWCZgJq6y74MyDkgZmKFHBReOAaa7gnF8f9/vzG3BeWvMTlw2Uml0aWUvBMFLULyjCLwxaVt1iZ5xP8tVkz0GxAWOymZPFaPCdVla0GgwKxbyfF3mDZWAOpVDQpbT10DBxzS5hHqFhGnwZVqG77Etkqqy2Lj6D2Yr99yIw7f1S86jUDK/8011P/m83b7H+VgZpmhbBiPVHdasytFnfQFZJBwLVMgImnIxZM3HFHBMYe0pTWkFNdR1o78zrbk1wHyi3quoTWdWlj9MIESvwUWrgVlitmakCbTlz3bwoIzIVuLUoukQ2jIsuesTGi6f9Pgdn00mxP5meHoyPppvuh+QT+Uy+koIckiPyg5yQGRGkIXfknjwM/iTDZDsZraXJYHOzRx5N8vEvTGG5Gg== D i AAACV3icbVDLSsNAFJ3EV42vVpdugkVwVZIq6EoEXbhUtCo0ocxMburgPMLMRCkhn+BWv82v0Unbha8LA4dzz733zCEFZ8ZG0YfnLywuLa+0VoO19Y3NrXZn+86oUlMYUMWVfiDYAGcSBpZZDg+FBiwIh3vydN70759BG6bkrZ0UkAo8lixnFFtH3VyM2KjdjXrRtMK/IJ6DLprX1ajjnSaZoqUAaSnHxgzjqLBphbVllEMdJKWBAtMnPIahgxILMGk19VqH+47Jwlxp96QNp+z3iQoLYyaCOKXA9tH87jXkf71hafOTtGKyKC1IOjuUlzy0Kmw+HmZMA7V84gCmmjmvIX3EGlPr4gmCJIM8EXmVNJtJXs8IYqqEKJ41jhSvg59uKHURGCeV8EKVEFhmVVISrOthnDokM9Azkdvi2Kob126HSzz+ne9fcNfvxYe9/vVR96w/z76FdtEeOkAxOkZn6BJdoQGiaIxe0Rt69z68T3/Zb82kvjef2UE/yu98AREKtaY= D j AAACV3icbVDLSsNAFJ3EV43P6tJNsAiuSlIFXYmgC5eKVoUmlJnJTR2dR5iZKCXkE9zqt/k1Omm78HVh4HDuufeeOaTgzNgo+vD8ufmFxaXWcrCyura+sdneujWq1BT6VHGl7wk2wJmEvmWWw32hAQvC4Y48nTX9u2fQhil5Y8cFpAKPJMsZxdZR1+fDx+FmJ+pGkwr/gngGOmhWl8O2d5JkipYCpKUcGzOIo8KmFdaWUQ51kJQGCkyf8AgGDkoswKTVxGsd7jkmC3Ol3ZM2nLDfJyosjBkL4pQC2wfzu9eQ//UGpc2P04rJorQg6fRQXvLQqrD5eJgxDdTysQOYaua8hvQBa0ytiycIkgzyRORV0mwmeT0liKkSonjWOFK8Dn66odRFYJxUwgtVQmCZVUlJsK4HceqQzEBPRW6LY6tOXLsdLvH4d75/wW2vGx90e1eHndPeLPsW2kG7aB/F6Aidogt0ifqIohF6RW/o3fvwPv1FvzWV+t5sZhv9KL/9BRL7tac= R pair AAACenicbVFNa9tAEF2rX6n75aTHXkRMoaVgJCfQHgO99OiWOgl4hRmNRsmS/RC7qzZm0V/ptf1L/S89dGXr0CQdWHi8eTP7eFM2UjifZb9Hyb37Dx4+2ns8fvL02fMXk/2DU2dai7REI409L8GRFJqWXnhJ540lUKWks/LqY98/+0bWCaO/+k1DhYILLWqB4CO1nhxwheFLt+aern1oQNhuPZlms2xb6V2QD2DKhlqs90cLXhlsFWmPEpxb5VnjiwDWC5TUjXnrqAG8ggtaRahBkSvC1nyXvo5MldbGxqd9umX/nQignNuoMioV+Et3u9eT/+utWl9/KILQTetJ4+6jupWpN2mfRFoJS+jlJgJAK6LXFC/BAvqY13jMK6q5qgPvN5d1tyNKF3hpZNU7MnIgY4RbFUJkbvpDjKG4qNP0HY1SoKvA2xJst8qLiHRFdieKeyMbpnkXd8Qb5LcTvwtO57P8aDb/fDw9mQ/X2GOv2CF7w3L2np2wT2zBlgzZNfvBfrJfoz/JYfI2ebeTJqNh5iW7UcnxX5CDw1c= R C AAACd3icbVHLbtswEKTVRxI3bZzm2EOFGg1yMiS3QHsMkEuPTlAnAUzBIFerhAgfAkk1NQh9Sa/tR/VTegtl65BHFyAwmJ1dDmZ5LYXzWfZ3kDx7/uLl1vbO8NXu6zd7o/235840FnAORhp7yZlDKTTOvfASL2uLTHGJF/zmpOtf/EDrhNHf/arGQrErLSoBzEdqOdqjCsJZu6Qef/pw0i5H42ySrSt9CvIejElfs+X+YEZLA41C7UEy5xZ5VvsiMOsFSGyHtHFYM7hhV7iIUDOFrghr5236MTJlWhkbn/bpmr0/EZhybqV4VCrmr93jXkf+r7dofPW1CELXjUcNm4+qRqbepF0MaSksgperCBhYEb2mcM0sAx/DGg5piRVVVaDdZl61G4K7QLmRZefIyJ6M+a1VwCLz0B9ADMVFncZbMEoxXQbacGbbRV5EpEu0G1HcG9kwztu4I94gf5z4U3A+neSfJtPTz+PjaX+NbfKOfCBHJCdfyDH5RmZkToA05Bf5Tf4M/iXvk8PkaCNNBv3MAXlQSX4HNQTB0A== x A AAACbXicbVHLbtQwFPWEQssU6AOxoqosRghWo2SK1C6L2HQ5SEyn0iQa2Tc3rTV+RLYDjKJ8RLfwZXwFv1BnkgVtuZKlo3OPr4/P5aUUzsfxn0H0ZOvps+2d58PdFy9f7e0fHF46U1nAGRhp7BVnDqXQOPPCS7wqLTLFJc756kvbn39H64TR3/y6xEyxay0KAcwHap6qgv5cfl7uj+JxvCn6GCQ9GJG+psuDwTTNDVQKtQfJnFskcemzmlkvQGIzTCuHJYMVu8ZFgJopdFm98dvQ94HJaWFsONrTDfvvjZop59aKB6Vi/sY97LXk/3qLyhdnWS10WXnU0D1UVJJ6Q9vP01xYBC/XATCwInilcMMsAx8iGg7THIuQSJ22k3nRdAR3dcqNzFtHRvakgk4FLDD3/QGEUFzQafwBRimm8zqtOLPNIskC0jnaThTmBrYeJU2YEXaQPEz8MbicjJOT8eTrp9H5pN/GDnlL3pGPJCGn5JxckCmZESArckt+kd+Dv9Gb6Cg67qTRoL/zmtyr6MMdvyG9hQ== D i AAACV3icbVDLSsNAFJ3EV42vVpdugkVwVZIq6EoEXbhUtCo0ocxMburgPMLMRCkhn+BWv82v0Unbha8LA4dzz733zCEFZ8ZG0YfnLywuLa+0VoO19Y3NrXZn+86oUlMYUMWVfiDYAGcSBpZZDg+FBiwIh3vydN70759BG6bkrZ0UkAo8lixnFFtH3VyM2KjdjXrRtMK/IJ6DLprX1ajjnSaZoqUAaSnHxgzjqLBphbVllEMdJKWBAtMnPIahgxILMGk19VqH+47Jwlxp96QNp+z3iQoLYyaCOKXA9tH87jXkf71hafOTtGKyKC1IOjuUlzy0Kmw+HmZMA7V84gCmmjmvIX3EGlPr4gmCJIM8EXmVNJtJXs8IYqqEKJ41jhSvg59uKHURGCeV8EKVEFhmVVISrOthnDokM9Azkdvi2Kob126HSzz+ne9fcNfvxYe9/vVR96w/z76FdtEeOkAxOkZn6BJdoQGiaIxe0Rt69z68T3/Zb82kvjef2UE/yu98AREKtaY= D j AAACV3icbVDLSsNAFJ3EV43P6tJNsAiuSlIFXYmgC5eKVoUmlJnJTR2dR5iZKCXkE9zqt/k1Omm78HVh4HDuufeeOaTgzNgo+vD8ufmFxaXWcrCyura+sdneujWq1BT6VHGl7wk2wJmEvmWWw32hAQvC4Y48nTX9u2fQhil5Y8cFpAKPJMsZxdZR1+fDx+FmJ+pGkwr/gngGOmhWl8O2d5JkipYCpKUcGzOIo8KmFdaWUQ51kJQGCkyf8AgGDkoswKTVxGsd7jkmC3Ol3ZM2nLDfJyosjBkL4pQC2wfzu9eQ//UGpc2P04rJorQg6fRQXvLQqrD5eJgxDdTysQOYaua8hvQBa0ytiycIkgzyRORV0mwmeT0liKkSonjWOFK8Dn66odRFYJxUwgtVQmCZVUlJsK4HceqQzEBPRW6LY6tOXLsdLvH4d75/wW2vGx90e1eHndPeLPsW2kG7aB/F6Aidogt0ifqIohF6RW/o3fvwPv1FvzWV+t5sZhv9KL/9BRL7tac= R I AAACbXicbZHPbtQwEMa9gdKyFNpScQIhi1VVTqtki0SPlXqB24LYbqVNtLInk9Za/4lsB7SK8hC9wpP1KXiFOpscaMtIlj795vN4PMNLKZyP49tB9OTp1rPtnefDF7svX+3tH7y+cKaygDMw0thLzhxKoXHmhZd4WVpkikuc89V5m5//ROuE0T/8usRMsSstCgHMBzRPFdDvy6/L/VE8jjdBH4ukFyPSx3R5MJimuYFKofYgmXOLJC59VjPrBUhshmnlsGSwYle4CFIzhS6rN/029CiQnBbGhqM93dB/b9RMObdWPDgV89fuYa6F/8stKl+cZrXQZeVRQ/dQUUnqDW0/T3NhEbxcB8HAitArhWtmGfgwouEwzbFIVVGnbWVeNB3grk65kXnbkZE9VNC5gAVyvz+AMBQXfBp/gVGK6bxOK85ss0iyoHSOtjOFuoHWo6QJNcIOkocTfywuJuPkZDz59ml0Num3sUPekg/kI0nIZ3JGvpApmREgK3JDfpM/g7/Rm+hd9L6zRoP+ziG5F9HxHXxmvWQ= Fig. 11. Paired-defense region. (a) Intruder starts in R pair . Neither D i nor D j has a guarantee to win from the one vs. one game analysis because x A ∈ R I . (b) Pincer maneuv er by the defender pair pushes the intruder out from R pair , while also prev en ting it to enter R C . At this time, D j can guarantee its victory using one vs. one strategy since x A ∈ R D ( i ). PR OOF. Observe that R pair shrinks as the tw o defend- ers get closer, and it disapp ears when the t w o meet at the midp oint. Hence, the intruder will exit R pair in fi- nite time. There are only three w ays to exit R pair : en ter R D ( s D i ), enter R D ( s D j ), or enter R C ( s D i , s D j ). How- ev er, the in truder cannot enter R C b ecause its sp eed ν cannot exceed the rate at which the radius of the circle decreases: ˙ c = 1 2 ν d dt s D i ) D j = 1 2 ν ( − 1 − 1) = − ν . There- fore, x A en ters either R D ( s D i ) or R D ( s D j ). Recalling that x A ∈ R D ( s D i ) ∪ R D ( s D j ) trivially leads to capture based on the solution to the one vs. one game, the only region that the in truder can guaran tee its vic- tory is R C ( s D i , s D j ). Theorem 5 The zer o level set of V ij define d in (37) gives the b arrier of the game of kind playe d b etwe en two defenders and one intruder. The result directly follows from Lemmas 2, 5 and 4. Remark 7 The two vs. one sc enarios have also b e en studie d in r elate d but differ ent pr oblems. Co op er ative c aptur e in pursuit-evasion games have b e en studie d in [29,13,18]. Ther e ar e also works that c onsider two vs. one c o op er ation in b or der-defense typ e sc enarios [16,48]. 4.3 Optimality of the Str ate gies Consider the in truder winning configuration. The pa yoff function in (21) can b e mo dified to P 1 ( ω D i , ω D j , u A ) = min { s D i ) B ( t F ) , s B ) D j ( t F ) } , (41) whic h describ es the safe distance at the time of breac h- ing. 13 Theorem 6 If the initial c onfigur ation is x A ∈ R C ( s D i , s D j ) , and if the players use P 1 in (41) as the obje ctive function, then u ∗ A in (35) , (36) and the pinc er maneuver [ ω D i , ω D j ] = [1 , − 1] form e quilibrium str ate- gies, and the value of the game is V ij in (37) . PR OOF. Similar to the pro of of Theorem 2, we can see that P 1 = V ij along the terminal surface. Therefore, the increase (resp. reduction) in P 1 is equiv alent to the increase (resp. reduction) in V ij ( t F ). T o prov e the opti- malit y , we will show that ˙ V ij ( ω ∗ D , u A ) ≤ ˙ V ij ( ω ∗ D , u ∗ A ) = 0 ≤ ˙ V ij ( ω D , u ∗ A ) , (42) where ω D = [ ω D i , ω D j ], and ω ∗ D = [1 , − 1]. The ab ov e inequalit y indicates that an y unilateral change in the strategy will result in a sub optimal p erformance. Recall that V ij = J ∗ L when x A ∈ R i . In this case, the inequalit y is shown using the time deriv ative ˙ J ∗ L in the pro of of Theorem 2. The case with x A ∈ R j is simi- larly straightforw ard. How ever, the case x A ∈ R mid has not b een considered y et. F or example, can the defend- ers mo ve in the same direction ω ∗ D = [1 , 1] to mov e s mid a w ay from the intruder? W e will inv estigate this using the time deriv ative ˙ V ij = ˙ J mid : ˙ J mid = 1 2 ( ω D j − ω D i ) − ˆ x A ) mid ν · ( ˙ s mid T ( s mid ) − u A ) = 1 2 (1 − β ) ω D j − (1 + β ) ω D i + 1 ν ˆ x A ) mid · u A , where we used ˙ s mid = 1 2 ( ω D j + ω D i ) and defined β , ˆ x A ) mid · T ( s mid ) ν = cos φ ( s mid ) ν . F rom the conditions on s L and s R (see (34)), the ap- proac h angle at s mid satisfies φ ∗ L ≤ φ ( s mid ) ≤ φ ∗ R when x A ∈ R mid . Hence, w e hav e | cos φ ( s mid ) | < ν , or equiv- alen tly , | β | < 1 when x A ∈ R mid . Therefore, b oth 1 − β and 1 + β are p ositiv e, and we hav e [1 , − 1] = arg min ω D max u A ˙ J ∗ mid ( ω D , u A ) , ν ˆ x A ) mid = arg max u A min ω D ˙ J ∗ mid ( ω D , u A ) , and min ω D max u A ˙ J ∗ L ( ω D , u A ) = 0, whic h completes the pro of. F or the defender winning configuration, w e use the same pa y off P 2 in (24), with a modification on d bar as follo ws: d bar = min x ∈R C k x − x A k . (43) Theorem 7 If the initial c onfigur ation is x A / ∈ R C ( s D i , s D j ) , and if the players use P 2 in (24) as the obje ctive function, then u ∗ A in (35) and the pinc er ma- neuver [ ω D i , ω D j ] = [1 , − 1] form e quilibrium str ate gies, and the value of the game is V ij in (37) . PR OOF. Similar to the pro of of Theorem 3, it suffices to show that − d bar = ν V ij , since we already ha v e the result (42). The iden tit y for the case with x A ∈ R i or x A ∈ R j is already prov ed in Theorem 3. When x A ∈ R mid , it is easy to get the result B · x A ) mid = 0 recalling that the barrier ∂ R C in this p ortion is a circle whose cen ter is at s mid . The optimal b ehavior of the defender at s D i against an in truder at x A ma y b e different based on the existence of the third play er s D j . In a one vs. one game D i m ust decide betw een cw and ccw motion based on the location of x A with resp ect to the disp ersal surface Γ dis ( s D i ), and it is p ossible that the cw motion is optimal. On the other hand, in a tw o vs. one game D i (defined as the one on cw side) should alw ays mov e ccw. As was done for the one vs. one game, w e provide al- gorithms to obtain key quan tities necessary to compute the strategies. First, recall that a defender pair divides the game space into t wo parts (Fig. 9a). Given a pair of defenders s D 1 and s D 2 , we must first determine which acts as the cw-side defender ( D i ) and which acts as the ccw-side defender ( D j ). Algorithm 5 Relev ant region (2 vs. 1) 1: Input : s D 1 , s D 2 , x A , γ , and ν 2: Compute is in left1 with s D 1 using Alg. 2 3: Compute is in left2 with s D 2 using Alg. 2 4: if s D 1 ) D 2 < L 2 then 5: is in D1D2 ← is in left1 and ∼ is in left2 6: else 7: is in D1D2 ← is in left1 or ∼ is in left2 8: end if 9: Return : is in D1D2 Note: ∼ is a negation op erator If is in D1D2 = T r ue , then the defender at s D 1 tak es the role of D i as described in this section, but it will act as D j otherwise. The defender strategy is presented in Alg. 7. If one de- fender can guaran tee capture, then the b eha vior of the other defender is inconsequen tial. Therefore, we assign no action to that defender in this pap er. If a single de- fender cannot guarantee capture, i.e., x A / ∈ R D ( s D i ) ∪ R D ( s D j ), then the defenders perform pincer mo vemen t. Finally , note that the attack er’s curren t region identified with (34), together with the quantities s L , s R and s mid are sufficient to find V ij in (37) 14 Algorithm 6 In truder Control (2 vs. 1) 1: Input : s D 1 , s D 2 , x A , γ , and ν 2: Compute s L and s R using Alg. 2 3: Compute is in D1D2 using Alg. 5 4: if is in D1D2 = T r ue then 5: s D i ← s D 1 and s D j ← s D 2 6: else 7: s D i ← s D 2 and s D j ← s D 1 8: end if 9: Determine the region using (34) 10: if x A ∈ R i then 11: u ∗ A = ν ˆ x A ) L 12: else if x A ∈ R j then 13: u ∗ A = ν ˆ x A ) R 14: else 15: u ∗ A = ν ˆ x A ) mid 16: end if 17: Return : u ∗ A Algorithm 7 Defender Control (2 vs. 1) 1: Input : s D 1 , s D 2 , x A , γ , and ν 2: if x A ∈ R D ( s D 1 ) then 3: ω D 1 ← strategy from Alg. 4 4: ω D 2 ← 0 5: else if x A ∈ R D ( s D 2 ) then 6: ω D 1 ← 0 7: ω D 2 ← strategy from Alg. 4 8: else 9: Compute s L and s R using Alg. 2 10: Compute is in D1D2 using Alg. 5 11: if is in D1D2 = T rue then 12: [ ω D 1 , ω D 2 ] ← [1 , − 1] 13: else 14: [ ω D 1 , ω D 2 ] ← [ − 1 , 1] 15: end if 16: end if 17: Return : [ ω D 1 , ω D 2 ] Remark 8 (Computation) Imp ortantly, the c alcula- tion of the optimal str ate gies and the value (for b oth one vs. one and two vs. one) do not r e quir e any explicit c om- putation of the surfac es nor the r e gions. A numeric al se ar ch is p erforme d only in the first step when finding the br e aching p oints, which is also simple due to the mono- tonicity of the appr o ach angle φ ( s ) . Also note that nu- meric al metho ds pr op ose d in [6,7] r e quir es us to solve the HJI PDE offline and stor e the solution (i.e., c ontr ol in- puts c orr esp onding to al l p ossible states), so the players c an use this ‘lo okup table’ in the run time. Our metho d r e quir es less memory b e c ause c ontr ol inputs ar e c ompute d online. 5 Multipla yer Game This section discusses assignmen t-based defense p olicies when there are multiple play ers on b oth teams. These m ulti-agen t p olicies rely on the barriers or the winning regions derived in the previous sections. W e first review the assignment metho d (MM defense) prop osed b y Chen et al. [6,5] that only considers one vs. one defense. W e then propose an extension (MIS de- fense) that directly incorp orates coop erative t w o vs. one defense, which was first in tro duced in the conference ver- sion of this pap er [39]. W e also briefly in tro duce a co- op erativ e defense strategy (LGR defense) that has the strongest theoretical guarantees, whic h is presented in our separate publication [41]. Finally , w e provide a dis- cussion on the strengths and w eaknesses of each policy . The b ounds Q M M , Q M I S and Q LG that will b e intro- duced in this section provide solution to Prob. 2 p osed in Sec. 2. 5.1 Maximum Matching (MM) defense F or a giv en i nitial configuration { x A i } N A i =1 and { s D j } N D j =1 , the defender-winning regions can b e used to determine a set of in truders that eac h defender can win against: D j can be assigned to A i if x A i / ∈ R A ( s D j ), or equiv alently , x A ∈ R D ( s D j ). Again, the defender wins by either cap- turing the in truder or dela ying its intrusion indefinitely (see Sec. 3.2). One can generate a bipartite graph with intruders and defenders as t wo sets of nodes. Edges will b e drawn from eac h defender to all the intruders that it can capture. Matc hing in graph theory refers to finding a set of edges with no shared no des. Here, this restriction corresponds to the assumption that D j can only pla y an optimal t w o-play er game against at most one in truder at a time. Maxim um-cardinalit y matc hing (MM) algorithms (see references in [6]) give such an edge set with maximum cardinalit y . The edge set is use d to assign at most one unique de- fender to eac h intruder. If D j is assigned to A i , then D j selects its strategy to b e optimal against A i . The cardi- nalit y of the edge set, N cap MM , tells us that at least N cap MM in truders will b e captured. The upp er b ound on the in- truder score is then giv en b y Q ≤ Q MM = N A − N cap MM . (44) This metho d assumes that all defenders play indep en- den t games and ignores any coop eration with the team- mates. 5.2 Maximum Indep endent Set (MIS) defense No w we allow a defender pair to b e assigned to a single in truder. Let D ( i,j ) denote a pair ( D i , D j ). The match- ing algorithm needs to b e modified to a void conflicts. F or example, D i and a pair D ( i,j ) cannot b e treated as in- dep enden t no des and b e assigned to distinct intruders, b ecause D i ma y not b e able to mov e optimally against t w o intruders simultaneously . W e p ose the assignment 15 D1 A1 A4 A3 A2 D2 D3 D3,5 D4,5 1 2 3 4 5 6 7 8 9 1 2 3 4 5 6 7 8 9 D1 A1 A4 A3 A2 D2 D3 D3,5 D4,5 1 3 6 9 (b) (c) (d) A1 A2 A3 A4 D1 D2 D3 D4 D5 A1 A2 A3 A4 D1 D2 D3 D4 D5 possible assignment MIS assignment (a) (e) Fig. 12. (a) Example with 5 defenders and 4 intruders. (b) Eac h no de on the left represen ts a defender or a pair of de- fenders, and no des on the right represent intruders. Edges are dra wn when the defender or defender pair can win against the intruder. (c) Edges in (b) b ecome no des in the new graph. A maximum indep endent set is highligh ted in red. (d) An as- signmen t (not necessarily unique) that defends against max- im um n umber of intruders. (e) Assignment described in the original game space. problem into a maxim um indep endent set (MIS) prob- lem [25] as describ ed in the following: 1) Construct a bipartite graph with tw o sets of no des V D = { D i } N D i =1 ∪ { D ( i,j ) } i 6 = j and V A = { A i } N A i =1 . The no de set V D no w includes all p ossible defender pairs. 2) F or each D i , draw edges to all intruders, A k , such that x A k ∈ R D ( s D i ). 3) F or each pair D ( i,j ) , dra w edges to all A k suc h that x A k ∈ R pair ( s D i , s D j ) (see Fig. 11). Note that we ex- clude the intruders that are indep endently capturable b y either D i or D j . Figure 12a depicts a particular initial condition, and Fig. 12b shows the bipartite graph (nodes with no edges are omitted). 4) The edges in the graph are en umerated and b e- come the no des in the new graph representation (see Fig. 12c). 5) Draw an edge b etw een tw o no des (in the new graph) whenev er they share the same defender or in truder. 6) Find MIS, i.e., the largest subset of no des with no direct connection. Figures 12d-e illustrate the resultant assignments that giv e N cap MIS = 4 and Q ≤ Q MIS = N A − N cap MIS = 0. Note that the maximum-matc hing assignment only guaran- tees Q ≤ Q MM = 1 in this example. Since the MIS formulation considers paired defense in addition to all the individual defenses, it giv es equal or tigh ter upp er b ound for any initial configuration: i.e., Q ≤ Q M I S ≤ Q M M . (45) The ab ov e result is also straightforw ard noting that bi- partite matching problem can b e enco ded as a sp ecial case of the indep enden t set problem [25]. The downside of the ab ov e formulation is the fact that MIS cannot b e found efficiently [25]. While approxima- tion metho ds to solve MIS exist (e.g., [46]), they p oten- tially make the inequality (45) to no longer hold, which tak es a wa y the whole purpose of using the MIS strategy . A computationally efficient team p olicy that preserves the effectiveness of the co op erative defense is presented next. 5.3 L o c al Game R e gion (LGR) defense W e finally present an approach that gives us the strongest theoretical guarantees. The full detail of this p olicy is presented in our separate publication [41], and therefore we only provide a high-level idea here. The core concept we use for this strategy is called the Lo cal Game Region (LGR), whic h is defined by the in- truder winning region in the tw o vs. one game, with an addition of a degenerate case where the tw o defenders are iden tical. There are N D C 2 × 2 = N D ( N D − 1) ordered pairs and N D degenerate cases resulting in N 2 D regions in total. W e use k ∈ 1 , ..., N 2 D to denote the indices of the regions. F or each LGR, W e can define an intruder and a defender subteams by collecting all intruders and defenders in the region. Let n k A and n k D denote the num b er of agents in the k th intruder and defender subteams. Then we can define the numeric al advantage held by the intruder subteam as follows: q k = max { n k A − n k D , 0 } . (46) W e call this num b er the lo c al game sc or e . The signifi- cance of this quantit y is that we can prov e that the in- truder subteam can guaran tee to score at least q k p oin ts b y approac hing near the mid p oint b et w een the defender pair that defines this k th LGR [41]. No w considering the o v erall game, the in truders can maximize their score b y selecting the optimal decomp o- sition into subteams, i.e., a selection of a set of LGRs. W e sho w in [41] that this team selection can b e cast as 16 the following optimization problem: Q LG = max G X k ∈ G q k , (47) where G denotes a set of disjoin t LGRs, that do es not share any area. Con v eniently , the optimal disjoint set G ∗ and the v alue Q LG can b e obtained in O ( N 4 D ) time by recognizing (47) as an instance of the maximum weigh t indep endent set problem on a circular arc graph [39]. F or applications where it is critical to av oid an y intrusion, it is easy to test whether the intruders can guarantee a score of at least one: Q LG > 0 ⇔ ∃ q k > 0. By dividing the agents into subteams according to G ∗ , and by each subteam playing the t wo vs. one game against the corresp onding defender pair, the in truder team guarantees the following (see Theorem 1 in [41]): Q ≥ Q LG . (48) Note that such team strategy for the intruder and the score low er b ound are not giv en by either MM or MIS analyses. Note also that this score low er b ound is inde- p enden t of the defender strategy . F or the defender team strategy we also use the “inde- p enden t” intruder winning region, R I , defined in (30). W e define an extended v ersion of the lo cal game score: ˆ q k = q k + ˆ n k A , (49) where ˆ n k A denotes the num b er of in truders in the corre- sp onding paired-defense region R pair . The LGR defense p olicy developed in [41] takes the fol- lo wing steps: 1) Remov e/ignore Q LG uncapturable in truders from the game, so that the defenders can pla y a virtual game with Q LG = 0 (i.e., q k = 0 , ∀ k ). Iden tification of these in truders is presented as Alg. 2 in [41]. 2) F or eac h region with ˆ q k ≥ 1, assign corresp onding defender pair to one of the in truders in R pair . A greedy algorithm for this tw o vs. one assignments is presented as Alg. 3 in [41]. 3) Perform Maximum Matc hing to assign one vs. one de- fense for the remaining in truders and defenders (Alg. 4 in [41]). W e show in [41] that the ab ov e proce dure has polynomial time complexity . In addition, w e show that if ˆ q k ≤ 1 , ∀ k after the remov al of uncapturable intruders in the first step, then the LGR defense p olicy guarantees the fol- lo wing (Theorem 3 in [41]): Q ≤ Q LG . (50) T ogether with the previous low er b ound provided by the in truder team, this result prov es the optimality of this defense policy in a sense that it constitutes a saddle- p oin t equilibrium. As long as the intruder team sticks to their equilibrium strategy , the defender team cannot reduce the score by deviating from LGR defense p olicy . This optimality in- directly prov es the following result: Q ≤ Q LG ≤ Q M I S ≤ Q M M . (51) W e can in fact construct a case where Q LG < Q M I S as discussed in the simulation section. 5.4 Discussions W e discuss the strengths and weaknesses of the three approac hes introduced in this section: MM, MIS, and LGR defense p olicies. The MM assignment has the b est computational effi- ciency , and it is also the simplest approach to use. 11 The only necessary information from the agent-lev el game is the pair-wise win/loss information for all defender-in truder pairs. This simplicity allows us to use the MM assignment even when the defenders ha v e differen t sp eed limits or even different dynamics, since the analysis comes do wn to the individual p erformance. Therefore the MM approach is also the most extensible one as well. All of the ab o ve strengths come at the cost of sub optimal defender b ehavior, due to the absence of co op erative t w o vs. one defense. The MIS assignment impro v es the score b ound at the cost of computational complexit y . It is still simple to set up and extensible since we are only augmenting the one vs. one results with additional tw o vs. one results and p osing it as an existing combinatorial optimization prob- lem. Again, the biggest drawbac k is the computational complexit y , whic h mak es this approac h suitable only for small problems. The LGR approac h has t w o main strengths. First, the LGR defense p olicy giv es the tigh test score bound, as de- scrib ed in (51), and it actually constitutes a Nash equi- librium [41]. The second strength of the LGR analysis is that it also provides a low er b ound on the score: Q LG . This is in contrast to MM or MIS approaches that only pro vide score upp er b ounds. The intruder team strat- egy as w ell as the score lo wer b ound given by the LGR analysis are useful to ols in assessing the p erformance of defense systems. 11 Note that w e solely account for the m ulti-agent assignment asp ect and not the individual winning regions here. 17 Ev en with these strengths, the LGR algorithm is tractable in a sense that the complexit y grows p olyno- mially with the num b er of agen ts. The numerical com- parison of the score b ounds Q M M and Q LG is presen ted in [41]. Also, the time complexit y of all three approaches are pro vided in the App endix of [41]. The down side of the LGR approach lies in a relatively sophisticated for- m ulation related to the subteam definitions. In addition, the current theory only accommo dates defender teams with homogeneous speed limits, and the extension to higher-order dynamics will b e non-trivial. In summary , the MM defense strategy should b e con- sidered when simplicit y and extensibilit y are important. The LGR defense strategy should be used when optimal- it y is imp ortan t. Finally , if the intruder team strategy and/or score low er b ound are useful, the LGR analysis pro vides these information. 6 Sim ulation Examples This section demonstrates the theoretical results through numerical examples. All the examples use the p erimeter shap e parameterized as follows: [ x, y ] = [ a cos θ , b sin θ ], where [ a, b ] = [5 , 2] , [2 , 2] , [2 , 3] and [5 , 3] for the p olar angles θ ∈ [0 , π 2 ], θ ∈ [ π 2 , π ], θ ∈ [ π , 3 π 2 ], and θ ∈ [ 3 π 2 , 2 π ]. Note ho wev er that suc h parameteriza- tion is not necessary to apply the results of this pap er. The p erimeter curve maybe given as a series of sample p oin ts, or as a set of v ertices of a p olygon. The num b er of those data p oints linearly affect the ov erall compu- tational complexity through the search for the breach p oin t. 6.1 One vs. One Game W e v erify the results in Sec. 3 b y testing b oth opti- mal and sub optimal intrusion strategies. W e select the sp eed ratio to b e ν = 0 . 8 and start the game in the in truder-winning configuration. Fig. 13a shows the sim- ulation snapshots when the in truder takes the optimal strategy , whereas Fig. 13b and c sho w the cases when the in truder b eha v es sub optimally . The computation time of the strategies was 0.2 ms for an implementation in Matlab running on a laptop with a Core i7-7820HQ pro- cessor with 16 GB of memory . By insp ecting the right most column, we can compare the p erformance in terms of t w o metrics. First, the dis- tance b etw een the defender and the in truder at this time is the safe distanc e considered in Sec. 3.3. W e can see that the intruder ac hieves the largest safe distance with the optimal strategy in Fig. 13a. Next, notice the difference in the time the intruder reac hes the p erimeter. By sacrificing the safe distance, the closest-p oint strategy in Fig. 13b shows an improv ed t = 1 t = 200 t = 434 t = 1 t = 200 t = 385 t = 1 t = 200 t = 634 (a) optimal breaching point (b) closest point (c) tangent point Fig. 13. Simulation snapshots of one vs. one game with ν = 0 . 8. (a) Intruder b ehavior using the correct speed ratio. (b) Intruder b ehavior using ν = 0 . 01. (c) Intruder behavior using ν = 1. p erformance in terms of the arriv al time. This strategy also has the prop ert y of b eing op en-lo op type, since the closest p oin t on the p erimeter is completely indep enden t of the defender’s position or its b eha vior. Ho wev er, note that this strategy do es not alwa ys guarantee intruder’s win ev en if the game starts in the intruder winning con- figuration. Sp ecifically , when the intruder starts on the barrier, only the optimal strategy guarantees its win. The tangent-point strategy in Fig. 13c sho ws the opp o- site effect in the time of arriv al. By sacrificing the safe distance, this strategy delays the time the game ends, whic h may b ecome relev ant in a m ulti-play er game where it tries to keep the defender aw ay from other in truders. The result of this example highlights the fact that the optimal strategy will be differen t if the in truder’s ob jec- tiv e is to delay the capture as muc h as p ossible. W e omit the demonstration of the sub optimal defender strategy since it is already shown clearly with Fig. 6 in Sec. 3.2. 6.2 Multiplayer Game The example pro vided in Sec. 5 (Fig. 12a) sho wed a triv- ial case in which the MIS defense outp erforms MM de- fense, i.e., a case where Q MIS < Q MM . Here, we show 18 (a) (b) (c) (d) 1 2 3 1 2 3 t = 1 1 2 3 1 2 3 t = 105 1 2 3 1 2 3 t = 153 1 2 3 2 3 t = 284 Fig. 14. Sim ulation snapshots of MM defense. 1 2 3 1 2 3 t = 1 1 2 3 1 2 3 t = 105 1 2 3 1 2 3 t = 200 1 3 2 3 t = 285 (a) (b) (c) (d) Fig. 15. Sim ulation snapshots of MIS defense. an example where the tw o strategies initially hav e the same guarantee Q MM = Q MIS , but only MIS actually p erforms b etter than the initially provided b ound. Sim ulation snapshots of a three vs. three scenario are sho wn in Fig. 14 and 15 for MM defense and MIS defense resp ectiv ely . 12 The small yello w stars indicate eac h in- truder’s breaching p oint, the dash-dotted lines indicate the one vs. one assignments, and the solid blue lines in- dicate the tw o vs. one assignments. The intruders are p erforming indep endently greedy b e- ha vior: i.e., there is no team co ordination. 13 Eac h in- truder finds the closest pair of defenders that contains itself in the “relev ant region”, defined by the area b e- t w een the tw o afferent surfaces (see Fig. 9a). Then the in truder plays the tw o vs. one game against the pair. F or example, in Fig. 14a b oth A 1 and A 2 are lo cated in the relev an t region against the pair ( D 1 , D 2 ), and therefore mo v e tow ards the mid p oin t betw een the tw o defenders. 12 Also see https://youtu.be/h0_VqJbNsQc for the ani- mated version. 13 See [39] for a co ordinated team strategy of the intruders. Once the intru der conv erges on the afferen t surface of a defender, the relev ant region may start switching fre- quen tly . F or example, at time t = 105, the in truder A 2 is already on the afferent surface of defender D 2 . Dep end- ing on the side of a small deviation, the relev an t pair for A 2 switc hes b etw een ( D 1 , D 2 ) and ( D 2 , D 3 ). Such switc hing causes the in truder to follow a zigzag path to- w ards defender D 2 . T o av oid such degenerate b ehavior, w e add a small bias tow ards ccw direction when the in- truder selects the pair, whic h is why A 2 selects the pair ( D 2 , D 3 ). The kink in the path of A 3 (see Fig. 14d), is generated due to the switc hing from the midp oint b e- t w een ( D 2 , D 3 ) to the one b et w een ( D 3 , D 1 ). The MM assignment shown in Fig. 14, has tw o v alid edges giving N cap A = 2 and Q MM = N A − N cap A = 1. Since this MM assignment do es not sp ecify any b ehavior to the unassigned defenders, we also consider a secondary matc hing betw een the unassigned in truders and defend- ers. Defender D 1 gets this secondary assignmen t tow ards A 1 , which is why D 1 mo v es ccw. As the Q MM from the MM analysis exp ected, A 1 scores a p oin t (Fig. 14d). The MIS assignmen t sho wn in Fig. 15 also has N cap A = 2 at the b eginning, only guaranteeing Q ≤ Q MIS = 1. F or 19 this small problem, the computation time of the MIS defense strategy was 5 ms. The pair ( D 1 , D 2 ) initially pla ys the t wo vs. one game against A 1 . Ho wev er, at time t = 105, the in truder A 1 mo v es into R D ( D 2 ), whic h frees D 1 from the tw o vs. one game and allows it to p erform a one vs. one game against A 2 . A t this p oin t, the score upp erb ound has changed to Q MIS = 0, and the defender team guarantees that no intruder scores. Although the score b ound provided by Q MIS is tighter than Q MM (see Sec. 5), this example highlights that it ma y still not b e the smallest upp er b ound. Sp ecifically , the MIS analysis could not predict the outcome Q = 0 from the initial configuration. W e also note that the MIS assignmen t is non-unique; in fact, it could hav e selected the same edge set as the MM assignment in this ex- ample, b ecause they b oth ha v e the same cardinality . In other w ords, the tw o assignments are equally goo d in the instan taneous analysis. Ho wev er, only the assignment sho wn in Fig. 15 leads to the capture of all intruders. If we use the LGR defense strategy , we hav e q k = 0 for all the regions, and thus we ha ve Q LG = 0. This im- plies that all in truders will b e captured. The assignmen t will b e the same as the one in Fig. 15. How ever, what is imp ortan t is that the LGR strategy alwa ys makes this “correct” decision. This is one of the reasons b ehind the p erformance gap b etw een MIS and LGR defense strate- gies. In addition, unlike the MIS defense strategy , LGR analysis could predict Q = 0 from the initial configura- tion, showing that it is a more accurate estimate of the game outcome. 7 Conclusion W e study a v ariant of the reach-a void game with the defenders constrained to mov e on the p erimeter of the target region. The in truders try to score by breac hing the perimeter while the defender team tries to mini- mize the score by intercepting them. The one vs. one game is solv ed analytically for arbitrary con v ex shap es, whic h pro vides the in truder’s optimal breaching p oint and the defender’s optimal direction of motion. The de- riv ed strategies are at an equilibrium in terms of the safe distance (in the attack er-winning scenario) and the largest margin (in the defender-winning scenario). The t w o vs. one game is also solv ed analytically , and it high- ligh ts the b enefit of co op eration among the defenders. Sp ecifically , tw o defenders can team up to p erform a pincer maneuver to reduce the intruder-winning region. Finally , we introduce and discuss v arious team defense strategies that lev erage the results from one vs. one and t w o vs. one games. Ac knowledgemen ts W e gratefully ac knowledge useful discussions with Chris Kroninger, Ken Hay ashima, and Alexander V on Moll. References [1] Pushk arini Aghark ar and F rancesco Bullo. V ehicle routing algorithms to in tercept escaping targets. Pro c. A mer. Contr ol Conf. (ACC) , pages 952–957, 2014. [2] Efstathios Bakolas and Panagiotis Tsiotras. Relay pursuit of a maneuvering target using dynamic V oronoi diagrams. Automatic a , 48(9):2213–2220, 2012. [3] T amer Basar and Geert Jan Olsder. Dynamic Nonc oop er ative Game The ory, 2nd Edition . So ciety for Industrial and Applied Mathematics, 2011. [4] Shaunak D. Bopardikar, F rancesco Bullo, and Jo˜ ao P . Hespanha. A coop erative homicidal chauffeur game. Automatic a , 45(7):1771–1777, 2009. [5] Mo Chen, Zhengyuan Zhou, and Claire J. T omlin. A path defense approach to the m ultiplay er reach-a void game. IEEE Conf. De cis. Contr ol (CDC) , pages 2420–2426, 2014. [6] Mo Chen, Zhengyuan Zhou, and Claire J. T omlin. Multiplay er reach-a v oid games via lo w dimensional solutions and maximum matc hing. Pr oc. Amer. Contr ol Conf. (ACC) , pages 1444–1449, 2014. [7] Mo Chen, Zhengyuan Zhou, and Claire J. T omlin. Multiplay er reac h-av oid games via pairwise outcomes. IEEE T r ans. Autom. Contr ol , 62(3):1451–1457, mar 2017. [8] Timothy H Chung and Geoffrey A Hollinger. Search and pursuit-ev asion in mobile robotics. A uton. R ob ot. , 31(4):299– 316, 2011. [9] George Corliss. Which root does the bisection algorithm find? Siam R eview , 19(2):325–327, 1977. [10] Aleksei F edorovic h Filippov. Differ ential e quations with disc ontinuous righthand sides: contr ol systems , volume 18. Springer Science & Business Media, 2013. [11] Jaime F. Fisac, Mo Chen, Claire J. T omlin, and S. Shank ar Sastry . Reach-a void problems with time-v arying dynamics, targets and constraints. Pro c. 18th Int. Conf. Hybrid Sys. Comp. Contr ol (ACM) , pages 11–20, 2015. [12] Jaime F. Fisac and S. Shank ar Sastry . The pursuit- ev asion-defense differential game in dynamic constrained environmen ts. IEEE Conf. De cis. Contr ol (CDC) , pages 4549–4556, 2015. [13] M F oley and W Schmitendorf. A class of differential games with tw o pursuers versus one ev ader. IEEE T r ans. Autom. Contr ol , 19(3):239–243, 1974. [14] Zachariah E. F uchs, Pramo d P . Khargonek ar, and Johnny Evers. Coop erative defense within a single-pursuer, tw o- ev ader pursuit ev asion differential game. IEEE Conf. De cis. Contr ol (CDC) , pages 3091–3097, 2010. [15] Eloy Garcia, David W. Casb eer, Khanh Pham, and Meir Pac hter. Co op erative aircraft defense from an attacking missile. J. Guid. Contr ol Dyn , 38(8):1510–1520, 2015. [16] Eloy Garcia, David W Casbeer, Alexander V on Moll, and Meir Pac hter. Co op erative tw o-pursuer one-ev ader blo cking differential game. In Pr o c. A mer. Contr ol Conf. (A CC) , pages 2702–2709. IEEE, 2019. [17] Eloy Garcia, David W Casbeer, Alexander V on Moll, and Meir Pach ter. Multiple pursuer multiple ev ader differential games. IEEE T r ans. Autom. Contr ol , 2020. [18] Eloy Garcia, Zachariah E. F uchs, Dejan Milutinovic, David W. Casbeer, and Meir P ach ter. A Geometric Approach for the Cooperative Tw o-Pursuer One-Ev ader Differential Game. IF AC-Pap ersOnLine , 50(1):15209–15214, 2017. 20 [19] Eloy Garcia, Alexander V on Moll, David W Casbeer, and Meir P ach ter. Strategies for defending a coastline against multiple attack ers. In IEEE Conf. De cis. Contr ol (CDC) , pages 7319–7324, 2019. [20] Haomiao Huang, Jerry Ding, W ei Zhang, and Claire J. T omlin. A differential game approach to planning in adversarial scenarios: A case study on capture-the-flag. IEEE Int. Conf. R ob. Autom. (ICRA) , pages 1451–1456, 2011. [21] Haomiao Huang, W ei Zhang, Jerry Ding, Du ˇ san M. Stipanovi ´ c, and Claire J. T omlin. Guaranteed decentralized pursuit-ev asion in the plane with multiple pursuers. IEEE Conf. De cis. Contr ol (CDC) , pages 4835–4840, 2011. [22] Rufus Isaacs. Differ ential games: A mathematic al the ory with applic ations to warfar e and pursuit, c ontr ol and optimization . Courier Corporation, 1999. [23] Andrew J. Kerns, Daniel P . Shepard, Jahshan A. Bhatti, and T o dd E. Humphreys. Unmanned aircraft capture and con trol via GPS sp oofing. J. Field R ob. , 31(4):617–636, 2014. [24] T ae Hyoung Kim and T oshiharu Sugie. Co op erative con trol for target-capturing task based on a cyclic pursuit strategy. Automatic a , 43(8):1426–1431, 2007. [25] Jon Kleinberg and Ev a T ardos. A lgorithm design . Addison W esley , 2006. [26] Li Liang, F ang Deng, Zhihong P eng, Xinxing Li, and W enzhong Zha. A differential game for co op erative target defense. Automatic a , 102:58–71, 2019. [27] Shih-Y uan Liu, Zhengyuan Zhou, Claire T omlin, and J Karl Hedrick. Ev asion of a team of dubins vehicles from a hidden pursuer. In IEEE Int. Conf. R ob. Autom. (ICRA) , pages 6771–6776, 2014. [28] Shih-Y uan Liu, Zhengyuan Zhou, Claire T omlin, and Karl Hedrick. Evasion as a team against a faster pursuer. In IEEE Pr o c. Amer. Contr ol Conf. (ACC) , pages 5368–5373, 2013. [29] V enk ata Ramana Makk apati, W ei Sun, and P anagiotis Tsiotras. Optimal Ev ading Strategies for Two-Pursuer/One- Ev ader Problems. J. Guid. Control Dyn , 41(4):851–862, 2018. [30] V enk ata Ramana Makk apati and Panagiotis Tsiotras. Optimal Ev ading Strategies and T ask Allo cation in Multi- play er Pursuit–Ev asion Problems. Dynamic Games and Applic ations , pages 1–20, 2019. [31] Robert Mitchell and Ing Ray Chen. Adaptive in trusion detection of malicious unmanned air v ehicles using behavior rule sp ecifications. IEEE T rans. Syst. Man Cyb ern.: Syst. , 44(5):593–604, 2014. [32] Dav e W. Oyler, Pierre T. Kabamba, and Anouc k R. Girard. Pursuit-ev asion games in the presence of obstacles. Automatic a , 65:1–11, 2016. [33] Meir Pach ter, Alexander V on Moll, Eloy Garcia, David W Casbeer, and Dejan Milutino vi´ c. Singular tra jectories in the tw o pursuer one ev ader differential game. In 2019 International Conferenc e on Unmanned Air cr aft Systems (ICUAS) , pages 1153–1160. IEEE, 2019. [34] F abio P asqualetti, An tonio F ranchi, and F rancesco Bullo. On co operative patrolling: Optimal tra jectories, complexity analysis, and approximation algorithms. IEEE T r ans. Rob. , 28(3):592–606, 2012. [35] Alyssa Pierson, Zijian W ang, and Mac Schw ager. In tercepting rogue rob ots: An algorithm for capturing multiple ev aders with multiple pursuers. IEEE R ob. Autom. Lett. , 2(2):530– 537, 2017. [36] Sergey Rubinsky and Shaul Gutman. Three-Play er Pursuit and Ev asion Conflict. J. Guid. Contr ol Dyn , 37(1):98–110, 2014. [37] William L. Scott and Naomi E. Leonard. Optimal ev asive strategies for multiple interacting agents with motion constraints. Automatic a , 94:26–34, 2018. [38] Jhanani Selv akumar and Efstathios Bakolas. F eedback strategies for a reach-a v oid game with a single ev ader and multiple pursuers. IEEE T r ans. Cybern. , PP:1–12, 2019. [39] Daigo Shishik a and Vija y Kumar. Local-game decomp osition for multiplay er p erimeter-defense problem. In IEEE Conf. De cis. Contr ol (CDC) , pages 2093–2100, 2018. [40] Daigo Shishik a, James Paulos, Michael R Dorothy , M Ani Hsieh, and Vijay Kumar. T eam comp osition for perimeter defense with patrollers and defenders. In IEEE Conf. De cis. Contr ol (CDC) , pages 7325–7332, 2019. [41] Daigo Shishik a, James P aulos, and Vijay Kumar. Coop erative team strategies for multi-play er perimeter- defense games. IEEE R ob. Autom. L ett. , 5(2):2738–2745, 2020. [42] Ryo T akei, Richard Tsai, Zhengyuan Zhou, and Y anina Landa. An efficient algorithm for a visibilit y-based surveillance-ev asion game. Comm. in Math. Sci. , 12(7):1303– 1327, 2014. [43] Alexander V on Moll, David Casbeer, Elo y Garcia, Dejan Milutinovi ´ c, and Meir Pac hter. The multi-pursuer single- ev ader game. J. Intel. R ob. Syst. , 96(2):193–207, 2019. [44] Alexander V on Moll, Eloy Garcia, David Casb eer, M Suresh, and Sufal Chandra Sw ar. Multiple-pursuer, single-ev ader border defense differential game. J. A ero. Info. Syst. , pages 1–10, 2019. [45] Alexander V on Moll, Meir Pac hter, Eloy Garcia, David Casbeer, and Dejan Milutinovi ´ c. Robust p olicies for a multiple-pursuer single-ev ader differential game. Dynamic Games and Applic ations , 10(1):202–221, 2020. [46] Rui Y an, Xiaoming Duan, Zongying Shi, Yisheng Zhong, and F rancesco Bullo. Maximum-matc hing capture strategies for 3d heterogeneous multipla yer reach-a void games. arXiv pr eprint arXiv:1909.11881 , 2019. [47] Rui Y an, Zongying Shi, and Yisheng Zhong. Escape-av oid games with multiple defenders along a fixed circular orbit. In 13th IEEE Int. Conf. Control & Autom. (ICCA) , pages 958–963. IEEE, 2017. [48] Rui Y an, Zongying Shi, and Yisheng Zhong. Reach-a void games with tw o defenders and one attack er: An analytical approach. IEEE T r ans. Cyb ern. , 49(3):1035–1046, 2018. [49] Rui Y an, Zongying Shi, and Yisheng Zhong. T ask assignmen t for multipla yer reach–a void games in conv ex domains via analytical barriers. IEEE T r ans. R ob. , 36(1):107–124, 2019. [50] Zhengyuan Zhou, Jerry Ding, Haomiao Huang, Ryo T akei, and Claire T omlin. Efficien t path planning algorithms in reach-a void problems. Automatic a , 89:28–36, 2018. [51] Zhengyuan Zhou, Ryo T akei, Haomiao Huang, and Claire J T omlin. A general, op en-loop formulation for reach-a void games. In IEEE Conf. Decis. Control (CDC) , pages 6501– 6506, 2012. [52] Zhengyuan Zhou, W ei Zhang, Jerry Ding, Haomiao Huang, Du ˇ san M. Stipanovi ´ c, and Claire J. T omlin. Co op erative pursuit with V oronoi partitions. Automatic a , 72:64–72, 2016. 21
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment