The Secrecy Graph and Some of its Properties
A new random geometric graph model, the so-called secrecy graph, is introduced and studied. The graph represents a wireless network and includes only edges over which secure communication in the presence of eavesdroppers is possible. The underlying p…
Authors: Martin Haenggi
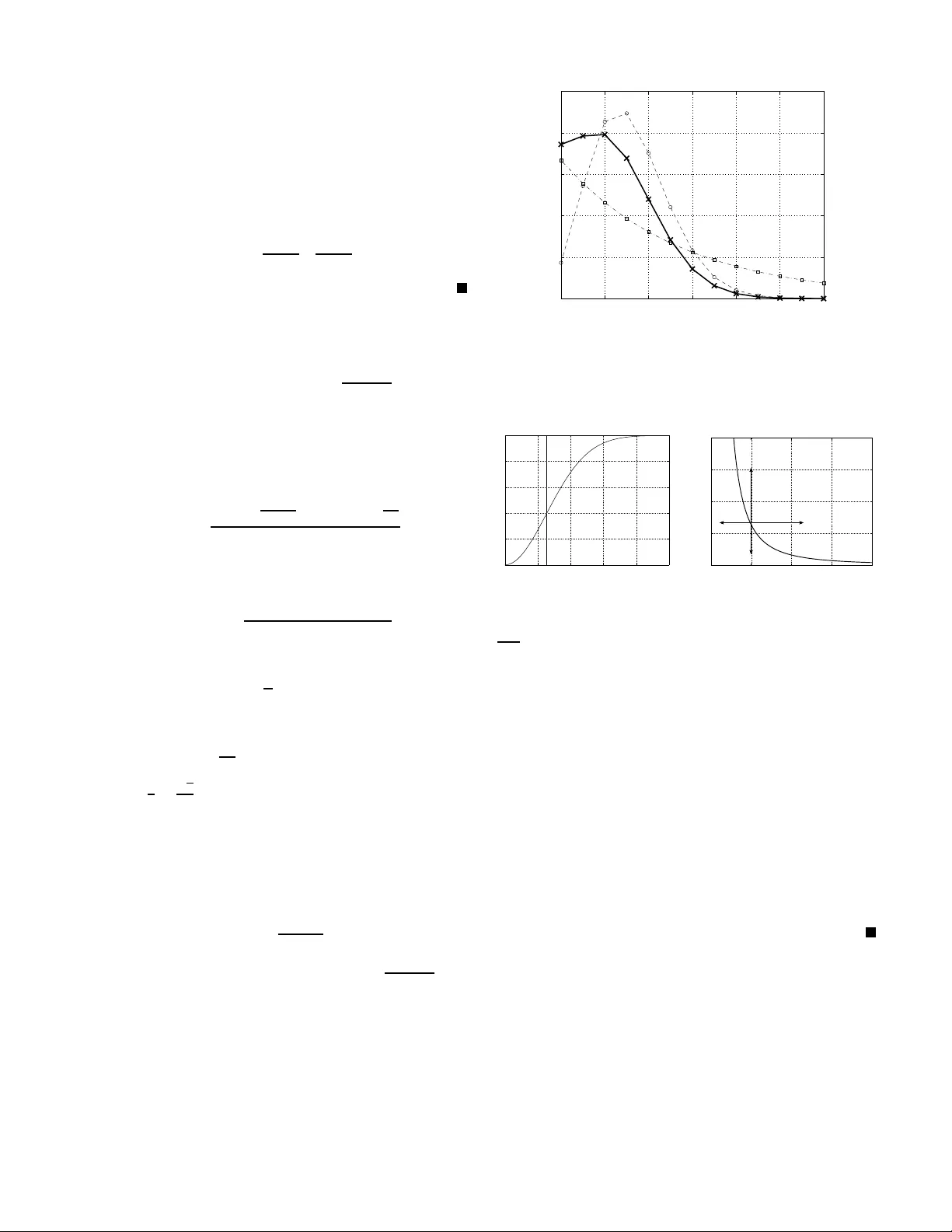
The Secrec y Graph and Some of its Properties Martin Haenggi Department of Electrical Engineering Univ ersity of Notr e Dame Notre Dame, I N 465 56, USA E-mail: mhaenggi@nd.e du Abstract —A new random geometric graph model, th e so-called secrecy graph , is introduced and stu died. Th e graph represents a wireless network and includes only edges ov er which secure communication in the pr esence of ea vesdroppers is possible. The underlying point process models considered a re lattices and Poisson point pro cesses. In the lattice case, analogies to standard bond and site percolation can be exploited to d etermine percolation thresholds. In the Poisson ca se, the node degr ees ar e determined and p ercolation is studied usin g analytical bounds and simulations. It turns out that a small density of ea vesdroppers already has a d rastic impact on the connectivity of th e secrec y graph. I . I N T RO D U C T I O N There has b een growing interest in infor mation-th eoretic secrecy . T o stud y the impact of the secre cy c onstraint on the co nnectivity of ad hoc networks, we introdu ce a new type of rand om geometric graph, the so-called secr ecy graph , that rep resents the network or co mmunic ation grap h in cluding only link s over which secure co mmunicatio n is possible. W e assume that a transmitter can choose th e rate v ery close to the capacity of the chan nel to the intended r eceiver , so that any eav esdropp er fur ther away than th e receiver canno t in tercept the m essage. Th is tran slates into a simp le geo metric con straint for secrecy which is reflected in the secrecy gr aph. In this initial investigation, we study some of the p roper ties of the secrecy gra ph. I I . T H E S E C R E C Y G R A P H Let ˆ G = ( φ, ˆ E ) be a ge ometric graph in R d , where φ = { x i } ⊂ R d represents th e locations o f th e n odes, also referred to as the “g ood guys”. W e c an th ink of this g raph as the unconstrain ed network graph that in cludes all possible edges over the good g uys could comm unicate if ther e were no secrecy con straints. T ak e an other set of po ints ψ = { y i } ⊂ R d representin g the locations o f the eavesdroppers o r “bad g uys”. These are assumed to be known to the go od guy s. Let D x ( r ) be the (closed) d -d imensional ball of rad ius r c entered at x , and let δ ( x, y ) = k x − y k be a distance metric, typ ically Euc lidean distance. Further, let φ ( A ) an d ψ ( A ) denote the number of points of φ or ψ falling in A ⊂ R d . Based o n ˆ G , we define the fo llowing secrecy graphs (SGs): The dir ected secr ecy graph: ~ G = ( φ, ~ E ) . Replace a ll edges in ˆ E b y two direc tional edges. Then r emove all edg es − − → x i x j for which ψ ( D x i ( δ ( x i , x j ))) > 0 , i.e. , th ere is a t least on e eav esdropp er in the ball. (a) Directed SG ~ G (b) B asic SG G (c) Enhance d SG G ′ Fig. 1. Example for s ecrec y graphs. T he dots are the good guys, the cross the eav esdropper . The underlyi ng graph is assumed to be fully conne cted so that the s ecrec y graphs include all edges along which secure communicati on is possible. From this directed graph , two undirected graphs are deriv ed: The basic secr ecy graph: G = ( φ, E ) , wh ere the (und i- rected) ed ge set E is E , { x i x j : − − → x i x j ∈ ~ E and − − → x j x i ∈ ~ E } . The en hanced secr ecy graph: G ′ = ( φ, E ′ ) , w here E ′ , { x i x j : − − → x i x j ∈ ~ E or − − → x j x i ∈ ~ E } . Clearly , E ⊂ E ′ . The difference is that edg es in E per mit secure bidir ectional commu nication w hile ed ges in E ′ only allow secure commu nication in one dir ection. However , this one-way link may be used to transmit a one-time pad so that the other no de can reply secretly . In d oing so, the lin k capacity would drop from 1 / 2 in each d irection to 1 / 3 . Fig. 1 shows an e xample in R 2 for the thr ee types of secrecy gr aphs. b ased on th e same und erlying fully connected gr aph ˆ G . One w ay to assess the im pact of the secr ecy req uiremen t is to dete rmine the secr ecy ratios η = | E | | ˆ E | = ¯ N ¯ ˆ N ; η ′ = | E ′ | | ˆ E | = ¯ N ′ ¯ ˆ N , (1) where ¯ N , ¯ N ′ > ¯ N , and ¯ ˆ N are th e average nod e degrees of the respective graphs. For η ≈ 1 , the impact of the secrecy requirem ent is negligib le while fo r small η it sev erely pr unes the gr aph. For the d irected graph , the mean in - an d o ut-degrees ar e equal, so we de fine ~ N , ¯ N out = ¯ N in = | ~ E | / | φ | . Since the edge sets of G and G ′ are a partitio n of th e edge set of the undirected m ultigraph con taining all edges in ~ G , th e fo llowing holds: Fact 1 The mean de g r e es are r ela ted b y ¯ N + ¯ N ′ = 2 ¯ N in = 2 ¯ N out . (2) Furthermore , the de gr ees of all nodes x ∈ φ ar e bo unded by N x 6 min { N in x , N out x } 6 ma x { N in x , N out x } 6 N ′ x 6 N in x + N out x . (3) In th e example in Fig. 1 , (2 ) yield s 10 / 9 + 2 2 / 9 = 3 2 / 9 . These grap hs b ecome interesting if the location s of the vertices are sto chastic point pro cesses. W e will use Φ and Ψ as the correspo nding random v ariables. Our g oal is to study the prop erties of the resulting rando m geometric grap hs, in cluding d egree d istributions and pe rco- lation thresholds. W e will con sider two cases, lattices and Poisson p oint p rocesses. A. Lattice model Let the u nderly ing g raph be the stand ard square lattice in Z 2 , i.e. , ˆ G = L 2 , where edge exists between all pair s of points with Eu clidean distance 1 . Let Ψ be obtained f rom ran dom indepen dent th inning of a regu lar point set whe re each po int exists with probab ility p , indep endently of all others. Let the correspo nding secrecy grap hs be denoted as ~ G p , G p , and G ′ p . Let θ ( p ) be the proba bility that th e componen t contain ing the origin is infinite 1 . T hen th e perc olation thresh old is defined as p c = inf { p : θ ( p ) = 0 } . (4) B. P oisson model Let the under lying grap h be Gilbert’ s disk gr aph ˆ G r [1], where Φ is a Po isson p oint pro cess (PPP) o f in tensity 1 in R 2 and two vertices are con nected if their distance is a t most r . Ψ is another, indep endent, PPP o f intensity λ . Deno te the secrecy graphs by ~ G λ,r , G λ,r , and G ′ λ,r . W ith θ ( λ, r ) b eing the pro bability th at the com ponen t containing the or igin (or any arb itrary fixed nod e) is infin ite, the p ercolation threshold radius for ˆ G r is r G , sup { r : θ (0 , r ) = 0 } ≈ 1 . 198 , (5) where th e subscript G indicates th at this is Gilbert’ s critical radius which is not known exactly but the bound s 1 . 19 79 < r c < 1 . 198 8 were established with 99 . 99% co nfidence in [2]. For radii larger than r G , we define λ c ( r ) , inf { λ : θ ( λ, r ) = 0 } , r > r G . (6) For the an alyses, we assume that there is a no de in Φ at the origin. This d oes not affect the d istributional prop erties of the PPP . The parameter r indicatin g the maximu m rang e of trans- mission can be related to standard communicatio n parameter s as f ollows: Assume a standard p ath lo ss law with attenua tion exponent α , a transmit p ower P , a no ise floor W , and a minimum SNR Θ for reliable com municatio n. Then r = P Θ W 1 /α . (7) 1 In the directed case, to be precise , we conside r oriented perco lation and let θ ( p ) be the probabili ty that the out-component is finite, i.e. , that there are direct ed paths from the origi n to an infinite number of nod es. Altern ati vel y (or in additio n) we could consider the in-component of the origin. I I I . P R O P E RT I E S O F T H E L AT T I C E S E C R E C Y G R A P H S Consider fir st the grap h G ′ p for th e c ase where a bad g uy is placed (with probab ility p ) in the midd le of each edge in L 2 , i.e. , Ψ = { x ∈ ( Z 2 + (1 / 2 , 0 )) ∪ ( Z 2 + (0 , 1 / 2 )) : U x < p } , ( 8) where U x is iid unif ormly d istributed in [0 , 1] . This case is analogou s to bond pe rcolation on th e two- dimensiona l square lattice [3], so: Fact 2 The per colation th r esh old fo r G ′ p is p c = 1 / 2 . For p = 1 / 2 , the den sity of bad guys is 1 , the same as the density of g ood guys. So the density of bad guys o nly needs to be a factor 1 − ǫ smaller than the density of goo d guy s, and the graph still perco lates, for any ǫ > 0 . Close to that threshold η ′ = 1 / 2 . If we pu t the b ad guys on the lattice po ints themselves (with probab ility p ) , the situation is analogou s to site perco lation o n L 2 , fo r which th e critical probab ility is unknown b ut estimated to be around 0.5 9, so p c ≈ 0 . 4 1 . In th is case the max imum density of bad guys is only 0.41 . So it seems having th e eavesdroppers at the lo cations indicated in (8) causes the least “dam age” to the co nnectivity of th e secrecy graph amo ng all regular Ψ . I V . P R O P E RT I E S O F T H E P O I S S O N S E C R E C Y G R A P H S A. Isolation p r oba bilities for r = ∞ Fact 3 The pr o bability th at th e origin o cann ot talk to an yone in ~ G λ, ∞ (out-isola tion) is P [ N out = 0] = λ λ + 1 . (9) In G λ, ∞ : P [ N = 0] = cλ cλ + 1 (10) wher e c = 4 3 + √ 3 2 π = 1 . 609 . For th e direc ted graph, this is simply the probability that the nearest n eighbo r in the combin ed pro cess Φ ∪ Ψ (of density 1 + λ ) is an eav esdropp er . I n the b asic graph, let x deno te the origin’ s nearest neighbor in Φ and let R = k x k . For N > 0 , we need D o ( R ) ∪ D x ( R ) to be fr ee of eavesdropper s. The area of the two inter secting disks is cπ R 2 for c = 4 / 3 + √ 3 / (2 π ) , a nd the prob ability density (pdf) of R is p R ( r ) = 2 π r e xp( − π r 2 ) (Rayleigh with mean 1/2) [4]. So P [ N > 0 ] = E R [exp( − λcπ R 2 )] = 1 cλ + 1 . (11) The prob ability of in-isolation P [ N in = 0] is smaller than P [ N out = 0] , since for each nod e x ∈ Φ \{ o } , ther e must b e at least one bad guy in D x ( k x k ) . Clearly , th is prob ability is smaller co mpared to (9) where o nly the nearest eav esdropp er matters. On the o ther han d, the in -degree is less likely than th e out-degree to be large since a significantly larger a rea needs to be free of bad guys. The isolation prob ability P [ N ′ = 0] is the smallest of all isolation pr obabilities. B. De gr e e distributions Proposition 4 Th e out-d e gr ee of o in ~ G λ, ∞ is geometric wit h mean 1 /λ . Pr oof: Con sider the sequ ence of near est neighb ors of o in the co mbined p rocess Φ ∪ Ψ . N out = n if the closest n a re in Φ an d the ( n + 1) -st is in Ψ . Since these are independ ent ev ents, P [ N out = n ] = λ 1 + λ 1 1 + λ n . (12) Alternatively , the distribution can be obtained as follows: Let R be the distance to the closest bad guy , i.e. , R = min y ∈ Ψ k y k . W e h av e P [ N out = n ] = E R exp( − π R 2 ) ( π R 2 ) n n ! , (13) where the pdf of R is p R ( r ) = 2 πr λ exp( − π λr 2 ) . For gener al r , we h av e: Proposition 5 Th e o ut-degr ee distribution of ~ G λ,r is P [ N out = n ] = λ 1 − Γ( n,a ) Γ( n ) + exp( − a ) a n n ! ( λ + 1) n +1 , ( 14) wher e a = π r 2 ( λ + 1) , and Γ( · , · ) is the u pper in complete gamma fun ction. The pr obability o f o ut-isolation is P [ N out = 0] = exp( − π r 2 ( λ + 1)) + λ 1 + λ , (15) and the mean out- and in-d e gr ees ar e E N out = E N in = 1 λ (1 − exp( − λπ r 2 )) . (16) The mean degr ee o f th e ba sic g raph G λ,r is E N = 1 cλ (1 − exp( − cλπ r 2 )) , (17) wher e c = 4 3 + √ 3 2 π . Pr oof: If there is no bad guy inside D x ( r ) — which is the case with p robability P 0 = exp( − λπ r 2 ) — th en the number is simp ly Poisson with mean π r 2 . If there is a b ad gu y at distance R , the num ber is Poisson with m ean π R 2 . So we have P [ N out = n ] = P 0 exp( − π r 2 ) ( π r 2 ) n n ! + (1 − P 0 ) E R n ] , the b ounds a/λ > E N > b/λ for the mean d egree fo llow . From (17) we alr eady know that E N = 1 / ( λc ) ≈ 0 . 6 2 /λ . Lastly , in this subsectio n, we c onsider the e nhanced gr aph. Proposition 6 Th e mean de g r e e E N ′ in the enhan ced graph G ′ λ,r is E N ′ = 2 λ (1 − exp( − λπ r 2 )) − 1 cλ (1 − ex p( − cλπ r 2 )) . (22) Pr oof: This follows by combining (2), (16), an d (17). C. S ecr ec y r atios Using the mean degree established in ( 17) we ob tain η ( λ, r ) = 1 − exp( − cλπ r 2 ) cλπ r 2 . (23) η ( λ, r ) is d ecreasing in both r and λ . η ′ ( λ, r ) follows fr om (22). Of in terest are also the relative edge d ensities of the enhanced an d basic grap hs: Fact 7 At least a fraction 3 π / (5 π + 3 √ 3) ≈ 0 . 4 5 o f the edges in th e enhan ced graph G ′ λ,r ar e present in th e basic graph G λ,r . The ratio E N/ E N ′ is 1 for small λr 2 and reaches its minimum as λr 2 → ∞ , where it is (2 c − 1) − 1 with c as in (17). The consequen ce is th at in some grap hs, mor e than 50% of the links can only be used securely in one d irection (unless one- time pad s a re used ). D. Edge leng ths W e con sider the d istribution of the len gth of the edges in ~ G λ, ∞ . For each no de, its nearest b ad gu y determin es th e maximum length o f an out- edge. So we intuitively expect the edge length d istribution to a pprox imately inherit the distribu- tion of the d istance to th e nearest bad g uy . Simulation stud ies reveal that indeed th e edge length d istribution is very close to Rayleigh with me an 1 / (2 √ λ ) , with o nly very slightly higher probab ilities for longer edg es—which is expected since nodes whose nearest b ad guy is far will have many lo ng edges o n av erage an d thu s skew the distribution. In th e power -limited regime, with r finite an d λ → 0 , th e edge length pdf conv erges to the usual 2 x/r 2 , 0 6 x 6 r . E. Oriented p er c olation o f ~ G λ,r W e ar e studying oriented out-p ercolation in ~ G λ,r , i.e. , the critical region in the ( λ , r ) -p lane for which ther e is a positi ve probab ility that the out-com ponen t containin g the or igin has infinite size. Fact 8 λ c ( r ) is monoton ically incr easing for r > r G , a nd we have 0 < lim r →∞ λ c ( r ) < 1 . (24) In o ther words, ther e exists a λ ∞ < 1 such that for λ > λ ∞ , G ′ λ,r does n ot pe r co late for any r . This fo llows from th e facts that fo r fixed r the m ean d egree is c ontinuo usly decreasing to 0 as a f unction of λ , and fo r λ < 1 , the mean degree is smaller than 1 ev en for r = ∞ , so percolation is impossible. W e will use λ ∞ to denote the limit in (2 4). For intensities smaller than that, we define r c ( λ ) , sup { r : θ ( λ, r ) = 0 } , λ 6 λ ∞ . (25 ) From the m onoton ic decrease of th e mean degre e in λ follows: Fact 9 The percolation r adius r c ( λ ) is mo notonica lly incr eas- ing with λ and h as a vertical asymptote at λ ∞ . Conjecture 10 r c ( λ ) is co n vex (and, consequ ently , λ c ( r ) is concave) : d 2 r c ( λ ) d λ 2 > 0 ∀ 0 6 λ < λ ∞ (26) It follows tha t r c ( λ ) > r G + cλ , wher e c , d r c ( λ ) d λ λ =0 . (27) Simulation r esults show that λ ∞ ≈ 0 . 14 99 with a standa rd deviation of 5 . 8 · 10 − 4 over 200 r uns. 0 0.2 0.4 0.6 0.8 1 0 0.02 0.04 0.06 0.08 0.1 0.12 0.14 0.16 Critical density log 10 (r) λ c (r) Simulation 0.15−exp(2sqrt(2)−4r) Fig. 4. The simula ted critical density λ c ( r ) vs. log 10 ( r ) toget her with a simple exponent ial app roximation. Each simulated point is the av erage of 30 runs. Since λ c ( r ) is concave and converges to a fin ite λ ∞ , we may conjec ture th at it can b e well ap prox imated by a function of th e form: λ c ( r ) ≈ λ ∞ − exp( a − br ) , r > r G , (28) where a and b are re lated thr ough a = log λ ∞ + br G . Indeed simulation results (see Fig. 4) reveal th at for b = 4 , λ ∞ = 0 . 1499 , and a = 2 √ 2 , we o btain an excellent approxima tion. Similarly , r c ( λ ) ≈ a b − 1 b log( λ ∞ − λ ) , λ < λ ∞ . (29) It follows that th e con stant c in Conj. 1 0 is c = ( bλ ∞ ) − 1 = 5 / 3 , an d the slope of λ c ( r ) at r = r + G is 3 / 5 . For th e critical graph ~ G λ,r c ( λ ) , it turns out that bo th P [ N = 0] and E N are increasing with λ . A g ood em pirically der iv ed appr oximation is P [ N out c = 0] ≈ 1 80 + 4 5 λ , λ < λ ∞ . (30) For the mean out-degree we h av e fr om ( 16) and (29) E N out c ( λ ) > π r 2 G + 11 4 λ . (31) E N out c ( λ ) is co n vex and reaches 1 /λ ∞ at λ = λ ∞ per Prop. 4. So percolation on the secr ecy graph requires a higher mean degree than Gilbert’ s disk graph. Since the disk graph was shown to req uire the hig hest mean degree amon g all ger m- grain r andom geom etric graphs [6]–[ 8], w e h av e established that: Fact 11 The secr ecy graph is not eq uivalent to any germ- grain random geome tric graph. V . C O N C L U D I N G R E M A R K S W e have introd uced a new class of rand om g eometric graphs that c aptures th e co ndition fo r secure commu nications in ad hoc networks. For th e lattice-based models, there exist direct analogies to bo nd and site p ercolation pro blems. In Poisson- based n etworks, we have derived the mean node degre es and, in some c ases, the d istribution. As a bypr oduct, a two- parameter distribution was fou nd that includ es the Po isson and the geometr ic distribution as special cases. Based on th e mean degree, we defin ed p ower - and secrecy-limited regions in the ( λ, r ) -plan e. The percolation region { ( r, λ ) : θ ( r, λ ) > 0 } was bound ed an d numerically determ ined. In conclusion, the pres- ence of eavesdroppers is r ather h armful in the ran dom case. A (relative) density of 0 . 15 is sufficient to make p ercolation impossible. Many inter esting problems remain o pen; we hope that this initial study sp arks fu rther investigations. A C K N O W L E D G M E N T S The author wishes to th ank A y lin Y ener for the discussions leading to the problem studied in this pap er . The suppo rt of NSF ( grants CNS 0 4-478 69, DMS 5056 24, and CCF 7 2876 3), and the DARP A/IPTO IT -MA NET program (gran t W91 1NF- 07-1- 0028) is g ratefully ac knowledged. R E F E R E N C E S [1] E. Gilbe rt, “Random plane netw orks, ” Journal of the S ociety for Industri al Applied Mathemat ics , v ol. 9, pp. 533–543, 1961. [2] P . Balister , B. Bollob ´ as, and M. W alters, “Cont inuum percolat ion with steps in the square of the disc, ” Random Structur es and Algorithms , vol. 26, pp. 392–403, July 2005. [3] G. Grimmett, P erco lation , vol. 321 of A Series of Comprehensi ve Studies in Mathemat ics . Springer , 2nd ed., 1999. [4] M. Haenggi, “On Distances in Uniformly Random Networks, ” IEEE T rans. on Informatio n Theory , vol. 51, pp. 3584–3586, Oct. 2005. A v ailabl e at http:/ /www .nd.edu/ ∼ mhaenggi/ pubs/tit 05.pdf. [5] D. Sto yan, W . S. K endall , and J . Meck e, Stochast ic Geometry and its Applicat ions . John W ile y & Sons, 1995. 2nd Ed. [6] P . Balister , B. Bollob´ as, M. Haenggi, and M. W alters, “Fast Transmission in Ad Hoc Networks, ” in IEEE International Symposium on Information Theory (ISIT’04) , (Chica go, IL), p. 19, June 2004. A v ailable at http: //www .nd.edu/ ∼ mhaenggi/ pubs/isit0 4bbhw .pdf. [7] M. Fra nceschet ti, L. Boot h, M. Cook, J. Bruck, and R. Mee ster , “Con- tinuum percolation with unreliable and spread out connecti ons, ” J ournal of Statisti cal Physics , vol. 118, pp. 721– 734, Feb . 2005. [8] P . Balister , B. Bollob ´ as, and M. W alters, “Cont inuum percolat ion with steps in an annulus, ” Annals of Applied Prob ability , vol. 14, no. 4, pp. 1869–1879, 2004 .
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment