Spectral efficiency and optimal medium access control of random access systems over large random spreading CDMA
This paper analyzes the spectral efficiency as a function of medium access control (MAC) for large random spreading CDMA random access systems that employ a linear receiver. It is shown that located at higher than the physical layer, MAC along with s…
Authors: Yi Sun
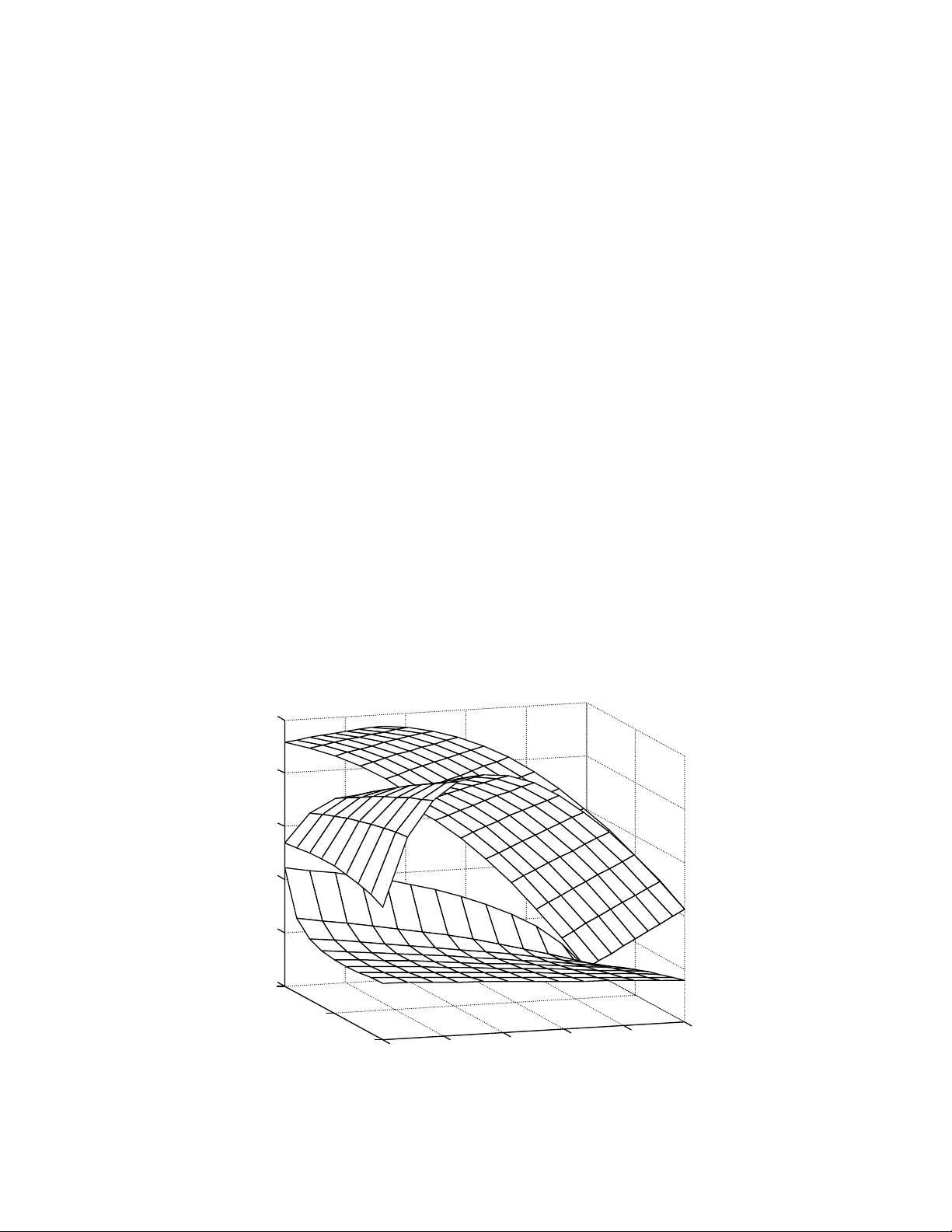
Spectral Efficiency and O ptimal Medium Access Control of Random Access Systems over Large Random Spreading CDMA Yi Sun 1 Abstract – This paper analyzes the spectral efficien cy as a fu nction of medium access control (MAC) for large random spreading CDMA random access systems that employ a linear receiver. It i s shown that located at higher than the physical layer, MAC along with sprea ding and power allocation can effectively perform spectral efficiency maximization and near-far mitigation. Index terms – CDMA, random access, spectral efficiency, medium access con trol I. I NTRODUCTION Random access is a medium access control (MAC) protocol for multiple users to access a basestation in probabilistic manor. Random access is conventionally opera ted over collision channels [1]-[4]. The stability region of a finite-user slotted random access system [2][3 ] is iden tical to the information theoretical capacity region of the collision channel without feedback [1] but an infinite-user random access syst em over the collision channel is always unstable [4]. Random access has also been applied to the channels capable of multipacket reception [5]-[10]. It turns out [5] that multipacket reception capability can stabilize an infinite-user system. Recent research in wireless communications has paid much attention to random access [6]-[10]. The throughputs of several symmetric wireless multiaccess systems where users have the same transmission rate and power ar e obtained in [8]. However, the stability region and the spectral efficiency of a CDMA random access system are unknow n in general. This is due partly to the fact that queues of all users are coupled by mutual interferenc e and then the system state is a high dimensional nonhomogeneous Markov chain which is difficult to analyze. However, recent studies showed [11]-[ 14] that in the large system limit of random spreading (LRS) CDMA with deterministic access, signal to interference ratio (SIR) of linear receivers is constant. This suggests that the queues in LRS-CDMA with random access be decoupled and analysis be feasible [9][1 0]. The spectral efficiency of LRS-CDMA with deter ministic access over frequency-flat fading channels is obtained in [17] with equal user power . By considering the on-off fadi ng that is equivalent to random access, the result in [17] can be applied to CDMA random access systems with equal user power but not an arbitrary power distribution. In this paper, for the random access system over LRS-CD MA with an arbitrary power distribution the SIR of the MMSE, decorrelator, MF is first shown to converge almost su rely to a constant that captu res effect of variations on traffic, spreading sequences and powers across users. The sp ectral efficiency is then obtained as a function of MAC, spreading, and power allocation, which therefore can join tly maximize spectral effici ency and mitigate near-far problem. In the high SIR regime MAC is m ore effective th an power control in near-far mitigation. The results are extended to an ordinary stable system whose stability region is identical to the informati on theoretical capacity region. 1 1 Yi Sun is with the Department o f Electr ical Engineering at the City College of C ity University of New York, New York, NY 10031 . E-mail: ysun@ee.ccny.cuny.edu . The obtained formulas provide a means for further study of CDMA rando m access systems with considerations of user collaboration, uncoded transmission, retr ansmission diversity, fairness, QoS, etc. The rest of the paper is organized as follows. Section II an alyzes the limit traffic load and SIR. Section III addresses the spectral efficiency, tradeoff of MAC, spreading and pow er, and extension to the ordinary system. All proofs are presented in the Appendix. II. L IMIT LINK CHANNEL A. Traffic load Consider that K users randomly access a basestation through a packet -switched symbol-synchronous CDMA channel. The total frequency bandwidth of the channel is W Hz and the symbol perio d is T s seconds, and then the spreading gain equals N = T s W second Hz. We first consider a dominating system where all users have sufficiently high packet arrival rates so that they always have packets in their buffe rs ready for transmission. T he result will be extended to an ordinary stable system where the probability for a buffer to be em pty is nonzero. Consider that user 1, the desired user, transmits a packet in a slot. In symbol period n of the slot, the chip MF at the basestation outputs an N -dimensional vector where the index of packet slot is omitted for notation brevit y, ) ( ) ( ) ( ) ( ) ( ) ( 2 1 1 1 n n b n p u n b n p n K i i i i i w s s r + + = ∑ = . ( 1 ) p 1 , s 1 ( n ), and b 1 ( n ) are the signal power, spreading sequence, and transm itted symbol for the desired user and p i , s i ( n ), and b i ( n ) for i ≥ 2 are for interference users where p i are time-invariant. w ( n ) ~ N ( 0 , σ 2 I ) are i.i.d. across symbol periods. The symbols take on real numbers with unit power Eb 2 [( ) ] 1 i n = and are independent for different users. A spreading sequence can be written as s where the chips s T iN n s )) ( ), " i i i n s n s n ( ), ( ( ) ( 2 1 = ij ( n ) take on 1 N ± ’s equiprobably and are i.i.d. As an indication function, u i = 1 if user i transmits, and u i = 0 otherwise. Being dependent on user’s power p i and independent of other events, the tran smission probability is equal to Pr( u i = 1) = θ ( p i ) ∈ (0,1]. Each function θ ( p ) that specifies transmission probabilities of all users determin es a MAC scheme for the system. Though here the MAC depends on the power distribution, the results are ready to be extended to an arbitrary MAC. Equation (1) can be written in matrix form ) ( ) ( ) ( ) ( ) ( ) ( 2 1 1 1 1 n n n n b n p n w b UP S s + + = r where U = diag( u 2 , …, u K ) and S ( n ), P , and b ( n ) are specified accordingly. A linear receiver l 1 ( n ) outputs an estimate of b 1 ( n ), 1 2 11 1 1 1 1 1 () () () () () () () () () TT T yn p n n b n n n n n n =+ + ls lS U P b l w . By taking expectation over symbols, we obtain the power of the desired signal and the power of interference and noise with interference power equal to . The signal to interference ratio (SIR) is P 1 2 1 1 )) ( ) ( ( ) ( p n n n P T s s l = ) ( ) ( ) ( 1 n n n P T v S l = 22 1 () | | () | | () in v Pn n P n σ =+ l ) ( ) ( 1 n n T l PUS s ( n )/ P in ( n ), which in general varies with n . We consider the LRS-CDMA channel where K and N → ∞ and K / N = α > 0. p k are upper bounded and their empirical distribution function converges to F . Moreover, MAC θ ( p ) is a function such that E [ θ ( p )] and E [ p θ ( p )] ex ist 2 with respect to F . The traffic demand is α (demanding users/s/Hz). The number of active users is K a = u 1 + … + u K and then the traffic load can be defined as ρ K = K a / N active users/s/Hz or transmitted symbols/s/Hz, which varies slot by slot since u k ’s do so. However, as K and N tend to infinit y, ρ K converges almost surely to a constant by the following lemma which can be proved b y following the proof of Lemma 2 in the Appendix. It implies that the traffic in the LRS-CDMA random access system behaves like that in the LRS-CDMA deterministic access system [11]- [16] but the active-user number is effectively reduced by a factor of E [ θ ( p )]. Lemma 1 : As K , N → ∞ and K / N = α , [( ) ] K E p ρ αθ → a.s. where the expectation is taken with respect to F . B. The limit link channel From the transmission of b 1 ( n ) to the estimate y 1 ( n ), there is an effective link channel. It is ready to obtain that the link channel is asymptotically memo ryless Gaussian and outputs 11 1 1 () () () yn p b n zn η =+ where z 1 ( n ) ~ N (0,1) are i.i.d. and η is the SIR when the received power is un it. The asymptotic Gaussianity of the link channel is obtained as an extension of th e asymptotic Gaussianity of an LRS-CDMA deterministic access syste m in [15][1 6]. By Le mma 1, K a / N converges alm ost surely to a constant α E [ θ ( p )] and the variation of traffic load due to the randomness of the number of active users vanishes. Therefor e, the LRS-CDMA random access system in each slot is almost surely an LRS-CDMA deterministic access system wh ere the interference of linear receiver output is Gaussian. Since spreading sequences are i.i.d. across n , the interferences in different sy mbol periods are independent. Hence, the limit link channel is Gaussian and memoryless. In what follows, the limit SIR η for the MMSE, decorrelator, and MF is obt ained in the almost sure convergence for the sample spreading sequences. The re sult is applicable to the com pletely random sequences in the sense of deterministic convergence. Theorem 1 : For the LRS-CDMA random access system, as K → ∞ and K / N = α , the unit-power SIR converges almost surely to η . For the MMSE, η uniquely solves 12 () 1 p p E p θ ησ α η − =+ + . ( 2 ) For the decorrelator, 2 1( ( ) ) E p α θ η σ − = ( 3 ) if α E [ θ ( p )] ≤ 1; otherwise, for the equal-power system with p i = p , θ i = θ , and Gaussian chips, 2 1 (1 ) 2 p α θ η αθσ αθ − = +− . ( 4 ) For the MF, 2 1 ( ()) E pp η σα θ = + . ( 5 ) 3 To each user, the SIR varies with spreading sequences and th e traffic load varies slot by slot. However, the SIR in the limit system is a constant. 1/ η is a notion of effective interference that cap tures the effect of variations in traffic, spreading sequences and user powers. It is an extension of the notion of effec tive interference [11] that captures only the effect of variant sequences and powers in a deterministic acce ss system. For the MMSE, the effect of θ ( p ) to a user is not to simply reduce its power by a factor of θ ( p ) though it is for the MF. If i ndependent of the power distribution, the MAC θ ( p ) for all the SIR’s is effective to reduce the active-user number by a factor of E [ θ ( p )] as it does for the traffic load α E [ θ ( p )]. However, when the MAC is determined by the power distribution, this is not true for the MMSE and MF. III. S PECTRAL EFFICIENCY AND OPTIMAL MAC A. Spectral efficiency Consider that a user with power p transmits a packet coded at a rate R ( p ) arbitrarily close to the link channel capacity (1/2)log 2 (1+ p η ) bits/symbol (or bits per channel use). The capacity of the effective link channel including the MAC is equal to 2 () ( () 2 ) l o g ( 1 ) p p Tp θ η =+ bits/symbol or T ( p )/( WT s ) bits/s/Hz. For the random access, the minim um bit energy per noise level N 0 = 2 σ 2 required for reliable communication is 2 0 () ( 2 () ) b E Np p T p θσ = or 2 02 log ( 1 ) b E p N p σ η = + ( 6 ) which compared with the deterministic access is decreased due to increased η . The spectral efficiency for the entire system equals 2 [( ) l o g ( 1 ) ] 2 CE p p α θ η =+ ( 7 ) bits/s/Hz. If the MAC is independent of the power distribution, CE 2 ( / 2) ( ) [log ( 1 )] E p α θη = + . Increase of transmission probabilities θ ( p ) can increase users’ link capacities but m ay not increase the spectral efficiency due to the increased interfe rence. This suggests existence of an optimal MAC that achieves the maximum spectral efficiency. In practice, a numerical opti mi zation algorithm can be used to search the optimal θ ( p ). For example, consider an M -class system where users of class i have the same power p i and therefore have the same transmission probability θ i . The expectation with respect to F ( p ) in (7) is simplified to the summation over the M classes. Optimization of MAC is th en to find the optimal set of M transmission probabilities θ i such that the spectral efficiency is maximized. Consider a two-class system where the users of class i have power p i , percentage of population q i , and transmission probability θ i for i = 1, 2. Then the spectral efficiency equals 2 2 1 log ( 1 ) 2 ii i i Cq p α θ η = =+ ∑ where η = [ σ 2 + αθ 1 p 1 q 1 /(1 + p 1 η ) + αθ 2 p 2 q 2 /(1 + p 2 η )] − 1 for the MMSE, η = [1 − α ( θ 1 q 1 + θ 2 q 2 )]/ σ 2 for α ( θ 1 q 1 + θ 2 q 2 ) ≤ 1 for the decorrelator, and η = ( σ 2 + αθ 1 p 1 q 1 + αθ 2 p 2 q 2 ) − 1 for the MF. Fig. 1 shows spectral efficiency versus MAC 4 θ ( p ) for a two-class system. The traffic demand is α = 0.95 users/Hz/s. The users of the first and the second classes have SNR = 10 dB and 30 dB, respectively. The ratio of the us er numbers of the first class to the second class is equal to q 1 / q 2 = 10. For the MMSE, C max = 1.2 is achieved by the MAC ( θ 1 , θ 2 ) = (1,1), which is control-free. For the decorrelator, C max = 0.97 is obtained by ( θ 1 , θ 2 ) = (0.65,1). For the MF, C max = 0.44 is attained by the MAC ( θ 1 , θ 2 ) = (1,0), which is unfair to the second class of users, though. B. Tradeoff between MAC, spreading, and power The spectral efficiency is a function of the number of demanding users K , spreading gain N (or bandwidth), power p i , and MAC. Optimization of these parameters can achieve the maximum spectral efficiency . K and p i are dynamic in wireless systems. Adjusting MAC c a n timely make up the change of K and p i to maintain the same spectral efficiency, which is the unique advantage of random access systems ove r deterministic systems. In the case when the MAC is independent of power distribution, if K is changed by a factor of γ , then adjusting the MAC to change E ( θ ) by a factor of 1/ γ can maintain the same spectral efficiency. To solve the near-far problem in wireless communication, pow er control is usually performed so that all users have about the same link capacity. As can be seen from η , reduction of transmission probabil it y is equivalent to reduction of their interference to other users. Moreover, the formula of T ( p ) shows that increase of transmission probabilit y can effectively increase their link capacities. It is clear that a proper MAC, even without power control, can achieve the goal of unifying link capacities. In practice, MAC and power control can be jointly applied. However, sensitivities of link capacity to transmission probability and to transmission pow er are different in different SIR regimes. In the low SIR regime such that η p << 1, the link capacity is ) 2 ln 2 ( ) ( η θ p p T ≅ . Both MAC and power control can effectively change the link capacity. On the other ha nd, in the high SIR regime such that η p >> 1, the link capacity is ) 2 ln 2 ( ) ln( ) ( η θ p p T ≅ . MAC is more effective than power control in change of link capacity. C. Extension to a stable system Now we extend the result from the dominating system to an or dinary stable system where the arrival rate is less than the service rate so that a user’s bu ffer is empty with a nonzero probability. A user with power p has a queue of packets in its buffer where new packet arrival rate is λ ( p ) packets/slot. The packet at the front end is transmitted with probability θ ( p ). Since packets are coded with an achievable rate, a transmitted packet is successfully decoded with probability one. Thus, the serv ice rate of the queue is equal to θ ( p ). We shall address, in the conventional terms of random access, the stability, probability distribution of queue length, and packet delay. This implies that the packet size is finite, seemly contradictor y to the fact that the size of packets coded with an achievable rate shall tend to infinity. Howeve r, the result is in the sense that if the packet size is sufficiently large, the system shall behave sufficiently cl ose to the result as the pack et size tends to infinity. A queue is stable if its length is finite with probabil ity one. If almost every queue in the system is stable as K → ∞ , then the system is stable. The stability re gion is the collection of sets of all user s’ arrival rates with which the system 5 is stable. In the LRS-CDMA syste m, the traffic load in each slot is equal to the constant E [ θ ( p )] and the interference to a user is the constant 1/ η both almost surely. Hence, the queue’s behavi or depends only on its arrival and service rates. It is clear that the queue is stable if λ ( p ) < θ ( p ), and unstable if λ ( p ) > θ ( p ). Moreover, it is notable that when λ ( p ) < θ ( p ), the probability that the queue is em pty is nonzero and then the interference power to other users is less than that in the dominating system. Hence, λ ( p ) < θ ( p ) for all p specifies the stability region. Furthermore, the information arrival rate satisfies () ()() ( ) s rp p R p W T λ = () l o g ( 1 ) ( 2 ) s p pW T θ η < + () ( ) s Tp W T = bits/s/Hz. Therefore, the stability region is identical to the information theoretical capacity region. Th e spectral effici ency (7) is the supreme of sum rate over the stability region. For a stable queue, the probability distribution q m that the queue has m packets in a slot is stationary. The rate of packets flowing from state m +1 to m is equal to the rate from m to m +1. That is, (1 10 ( ) ) ( ) ( ) p pq pq λ θλ −= and 1 (1 ( ) ) ( ) ( ) (1 ( ) ) mm p pq p p q λ θλ θ − −= − for m ≥ 2. Since ∑ , we obtain 1 0 = ∞ = m m q 0 1( ) qp ( ) p λ θ = − 1 0 () () [ ( 1 () ) () ] m m qq p p p p βλ λ θ − =− for m ≥ 1 where () [ ( 1 () ) () ] () ( 1 () ) p pp p p β λθ λ θ = −− . The probability that the queue is empty is q 0 > 0 due to λ (p) < θ ( p ). The packet delay is the average nu mber of slots from the slot of a packet arrival at the queue to the slot of its service. Since a packet is coded at an achievable rate, the packet delay is equal to the average length of the queue, 1 m m D mq ∞ = = ∑ () ( 1 () ) () ) ( () p pp p λ λθ λ = −− . It is clear that in each slot a user of power p transmits a packet with probability (1 − q 0 ) θ ( p ) = λ ( p ), which equals the arrival rate. This is due to the fact that in a stable system, the departure rate is equa l to the arrival rate. Hence, the MAC can serve to co ntrol λ ( p ). Then, replacing θ ( p ) by λ ( p ), all the formulas and results in the precedi ng subsections are applicable to the stable system. A PPENDIX Lemma 2 : Let { p i } be an upper bounded sequence and its em pi rical distribution function con verges to F , that is 1 lim ( 1 ) ( ) ( ) K i i K KI p x F = →∞ ≤= ∑ x and u i ’s be independent with Pr( u i = 1) = θ ( p i ) and Pr( u i = 0) = 1 − θ ( p i ). As K → ∞ , )) ( ( ) ( ) 1 ( 1 p E p K K i i θ θ → ∑ = where E is with respect to F . Then the empirical distribution functio n of { , } i i u p 1 () ( 1 ) ( ) K K i Hx K I p u x = = ∑ i i ≤ K + , converges almost surely to . 0 () 1 ( ( ) ) ( ) ( ) x Hx E p p d F p θθ =− + ∫ Proof : Since I ( u i p i ≤ x ) = I ( u i = 0) + I ( u i = 1) I ( p i ≤ x ), where 1 () ( 1 / ) ( 0 ) () K Ki i Hx K I u V x = == ∑ ∑ = ≤ = = K i i i K x p I u I K x V 1 ) ( ) 1 ( 1 ) ( . ( 8 ) The mean of V K ( x ) is 1 [( ) ] ( 1 / ) ( ) ( ) K Ki i i E Vx K p I p x θ = = ∑ ≤ , which converges to . Moreover, ∫ x p dF p 0 ) ( ) ( θ 44 4 1 1 [( ( ) ( ( ))) ] [( ( 1 ) ( )) ] ( ) K KK i i i i E Vx E Vx E I u p I p x K θ = −= = − ∑ ≤ 6 ∑∑ =≠ = ≤ ≤ − = − = + K i j K i j j i j j i i x p I x p I p u I E p u I E K 1, 1 2 2 4 ) ( ) ( ] )) ( ) 1 ( [( ] )) ( ) 1 ( [( 3 θ θ 2 33 13 ( 1 ) (1 ) K OK KK − ≤+ = . ( 9 ) By Chebyshev inequality, for each ε > 0, , and therefore it follows from the Borel-Cantelli lemma that V a.s. and then V 42 Pr{| ( ) ( ( )) | } /( ) KK Vx E Vx c K εε −> ≤ 0 )) → x ∫ x p 0 ) ( θ ( ( ) ( − V E x K K K ( x ) → a.s. Following the similar lines, we can show that H p dF ) ( K ( x ) − V K ( x ) → 1 − E [ θ ( p ) ] a . s . Proof of Theorem 1 : By ignoring a factor of positive constant, the MMSE receiver is l where ) ( ) ( ) ( 1 1 1 n n n s M − = 2 () () () T M nn σ =+ IS P U S n . The SIR equals 1 11 1 () () () () () T si n P n p n n n − = sM s Pn . Let Λ ( n ) = diag( λ 1 , …, λ N ) with λ i be the eigenvalues of S ( n ) PUS T ( n ) and Z ( n ) be the corresponding matrix of eigenvectors. Denote by G N the empirical distribution function of the eigenvalues. By [ 11] (Theorem 4.1), G N converges almost surely to G whose Stieltjes transform equals 1 0 { [ 1 () ] } ( ) } t t mz d H t α ∞ () { mz z − =− + + ∫ where H is the limit empirical distribution function of p i u i ’s. It follows from Lemma 2 that ∫ ∞ − = 0 ) ( 1 ) ( λ λ dG z z m ( 1 0 ) 0 1 {( ) [ 1 () ] } ( ) zp p p m z d F αθ ∞ = −+ + ∫ p . ( 1 1 ) For any U and N , S ( n ) PUS T ( n ) is nonnegative definite and therefore the spectral radius of M − 1 ( n ) is upper bounded by 1/ σ 2 . By [15] (Lemma B.1), 6 11 11 3 1 () () () t r ( () ) T c En M n n M n N N −− − ss ≤ . ( 1 2 ) It follows from the Chebyshev inequality and the Bor el-Cantelli lemma that ss a.s. Since (1/ 11 11 () () () ( 1 / ) t r ( () ) 0 T nM n n N M n −− −→ 1 )tr( ( )) NM n − = 21 (1 / ) t r [ ( ) ( ( ) ) ( ) ] T N nn σ − +Λ ZI Z n 2 1 ) 1 ( ) N i i (1 / N σ λ = =+ ∑ 2 0 1( ) ( ) N dG σ λλ ∞ =+ ∫ 2 0 1( ) ( ) dG σ λλ →+ ∞ ∫ a.s., we obtain ∫ ∞ − + = → 0 2 1 1 1 ) ( 1 ) ( ) ( ) ( λ λ σ η dG n n M n T s s a . s . ( 1 3 ) Letting z → − σ 2 in (10), the continuity of m ( z ) yields m ( z ) → η , which leads (11) to η . The decorrelator l 1 ( n ) of user 1 is the first column vector of [( where + denotes pseudoinverse. If s 1 ( ), ( ) ) ] T nn + sS U 1 ( n ) is not in the space spanned by S ( n ) U , then the decorrelator cancels out the interference signal and 7 11 () [ () ( () ) ] () nn n + =− lI S U S U s n . The SIR is 2 11 1 () () () [ () ( () ) ] () T si n P n p n n n n Pn σ + =− sI S U S U s () 1 () a Kn T ii i i n λ ′ = = ∑ z v ( ) a ′ () 1 1 a Kn T ii i i λ ′ +− = = ∑ v z () ( () ) nn + − IS U S U I . Let S ( n ) U be expressed in the singular value decomposition as SU where λ i ’s are Kn nonzero singular values. Its pseudo-inverse is (( and then . The spectral radius of I − S ( n ) U ( S ( n ) U ) ( ) a Kn ≤ () 1 a Kn i ′ = = − ∑ z ) ) n SU T ii z + is upper bounded by one. It foll ows from [15] (Lemma B.1) that { } 6 3 ( () ) ] / 11 () [ () ( () ) ] ( T ) ( 1 / ) t r [ () E nn n s I SU SU s n −− N + I SU n n c N − SU + ≤ . By the Chebyshev inequality and the Borel-Cantelli lemma, 11 1 ] () t r [ () ( n n () T [ () ( () ) nn n () ) ] 0 n N + −− s I SU + → − SU s a.s. By Lemma 1, I SU S U () ( ( ) ) a Kn N E p α θ → a.s. Suppose () 1 a Kn N < . By [18] (Proposition 2.1), the least singular value is alm ost surely greater than zero, and therefore S ( n ) U ( n ) has a full column rank (i.e., () () aa Kn Kn ′ = ) almost surely. It follows fro m Lemma 1 that () a Kn ( ( ) ) E p N α θ / ) [ ( ) ( ( ) ′ → a.s. and thus (1 ) ] 1 ( ( ) ) N tr n n − IS U S E αθ + → U p − a.s. The second part is obtained by following the lines in [13] [14] and noticing that the traffic load is () a Kn N ( ( ) ) E p α θ → 1 a.s. ) ( p n s = ) ( 1 n ) ( ) ( n n T s PUS 2 ) 1 ( α + || ) ( |||| |||| ) ( || || ) ( ) ( n n n n T T S PU S PUS S ≤ } { max ) 2 2 i K k p ≤ ≤ α 1 ( ≤ + } 6 3 () ) / T n c N ≤ U S ( ) ) 0 n → (1 / ) t r ( ( ) ( ) ) T Nn n = SP U S (1 / ) t r ( ( T ) ( ) ) N nn S PU ) ] k k n 2 (1 / ) K kk k S N pu = = ∑ () () p pdF p θ The MF is l 1 ( n ) = s 1 ( n ). The signal power equals P and the interference power equals . It is sufficient to show that P ) ( ) ( 1 n n P T v S s = v ( n ) → α E [ θ ( p ) p ] a.s. By [18] (Proposition 2.1), || ) ( ) ( || ≤ n n T S S a.s., and therefore || , which is upper bounded. Then the spectral radius of S ( n ) PUS T ( n ) is upper bounded in N . It follows from [15] (Lemma B.1) that { () ( 1 / ) t r ( () v E Pn N n − SP . In terms of the Chebyshev inequality and the Borel-Cantelli lemma, () v Pn − (1 / ) t r ( ( ) T Nn SP U S a.s. Moreover, 2 (1 / ) [ ( ) ( K T kk k Np u n = = ∑ SS , which by Lemma 2 converges almost surely to 00 () p dH p αα ∞∞ = ∫∫ . ( 1 4 ) T h i s c o m p l e t e s t h e p r o o f . References [1] J. L. Massey and P. Mathys, “The collision channel without feedback,” IEEE Trans. Inf. Theory , vol. 31, pp. 192 – 204, Mar. 1985. [2] V. Anantharam, “The stability region of the finite-user slotted ALOHA protocol,” IEEE Trans . Inf. Theory , vol. 37, pp. 535 – 540, May 199 1. [3] R. R. Rao and A. Ephremides, “On the stability of interacting queues in a m ultiple-access system,” IEEE Trans. Inf. Theory , vol. 34, pp. 918 – 9 30, Sept. 1988. [4] W. Rosenkrantz and D. Towsley, “On the inst ability of slotted ALOHA multiaccess algorithm,” IEEE Trans. Autom. Control , vol. 28, pp . 994 – 996, Oct. 1983. [5] S. Ghez, S. Verdú, and S. C. Schwartz, “Stability properties of slotted aloha with multipacket reception capability,” IEEE Trans. Automat. Control , vol. 33, no. 7, pp. 640-649, July 1988. 8 [6] L. Tong, Q. Zhao, and G. Mergen, “Multipacket r eception in random access wireless networks: from signal processing to optim al medium access control,” IEEE Commun. Mag. , pp. 108-112, Nov. 2001. [7] M. K. Tsatsanis, R. Zhang, and S. Banerjee, “Network -assisted diversity for random access wireless networks,” IEEE Trans. Signal Process. , vol. 48, pp . 702-711, M arch 2000. [8] D. Tuninetti and G. Caire, “The throughput of some wireless multiaccess systems,” IEEE Trans. Inf. Theory , vol. 48, pp. 2773 – 27 85, Oct. 2002. [9] X. Cai, Y. Sun, and A. N. Akansu, “Performance of CDMA random access systems with packet combining in fading channels,” IEEE Trans. Wireless Commum. , vol. 2, no. 3, p p. 413-419, May 2003. [10] Y. Sun and J. Shi, “Retransmission divers ity in large CDMA random access systems,” IEEE Trans. Signal Process. , vol. 55, no. 7, pp. 347 1-3483, July 2007. [11] D. N. C. Tse and S. V. Hanly, “Linear multiuser receivers: effective interference, e ffective bandwidth a nd user capacity,” IEEE Trans. Inf. Theory , vol. 45, pp. 641-657, Mar. 1999. [12] S. Verdú and S. Shamai (Shitz), “Spectral e fficiency of CDMA with random spreading,” IEEE Trans. Inf. Theory , vol. 45, no. 2, pp. 622-640, March 1999. [13] Y. C. Eldar and A. M. Chan, “On the as ymptotic performance of the decorrelator,” IEEE Trans Inf. Theory , vol. 49, no. 9, pp. 2309- 2313, Sept. 200 3. [14] Y. C. Eldar and A. M. Chan, “Correction to ‘On the as ymptotic performance of the decorrelator’ and ‘An optimal whitening approach to linear multiuser detection’,” IEEE Trans Inf. Theory , vol. 51, no. 1, pp. 421-4 21, Jan. 2005. [15] J. Zhang, E. K. P. Chong and D. N. C. Tse, “Output MAI distributions of linear MMSE multiuser receivers in DS-CDMA systems,” IEEE Trans. Inf. Theory , vol. 47, pp. 1128-1144, March 2001. [16] D. Guo, S. Verdú, and L. K. Rasmussen, “Asymp totic normality of linear multiuser receiver outputs,” I EEE Trans. Inf. Theory , vol. 48, no. 1 2, pp. 3080- 3095, De c. 2002. [17] S. Shamai (Shitz) and S. Verdú, “The impact of freque ncy-flat fading on the spectral efficiency of CDMA,” IEEE Trans. Inf. Theory , vol. 47, no. 4 , pp. 1302-132 7, May 2001. [18] S. Verdú, Multiuser Detection , Cambridge University Press, Ne w York, 1998. 0 0. 2 0. 4 0. 6 0. 8 1 0 0. 5 1 0 0. 2 0. 4 0. 6 0. 8 1 θ 1 θ 2 C ( bit s / Hz / s ec ond) Fig. 1. Spectral efficiency versus MAC ( θ 1 , θ 2 ) for a two-class system. From up to down are for the MMSE, decorrelator, and MF, respectively. 9
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment