Closed-Form Expressions for Secrecy Capacity over Correlated Rayleigh Fading Channels
We investigate the secure communications over correlated wiretap Rayleigh fading channels assuming the full channel state information (CSI) available. Based on the information theoretic formulation, we derive closed-form expressions for the average s…
Authors: ** Xiaojun Sun, Ming Zhao, Jiang Ming (국가 모바일통신연구실
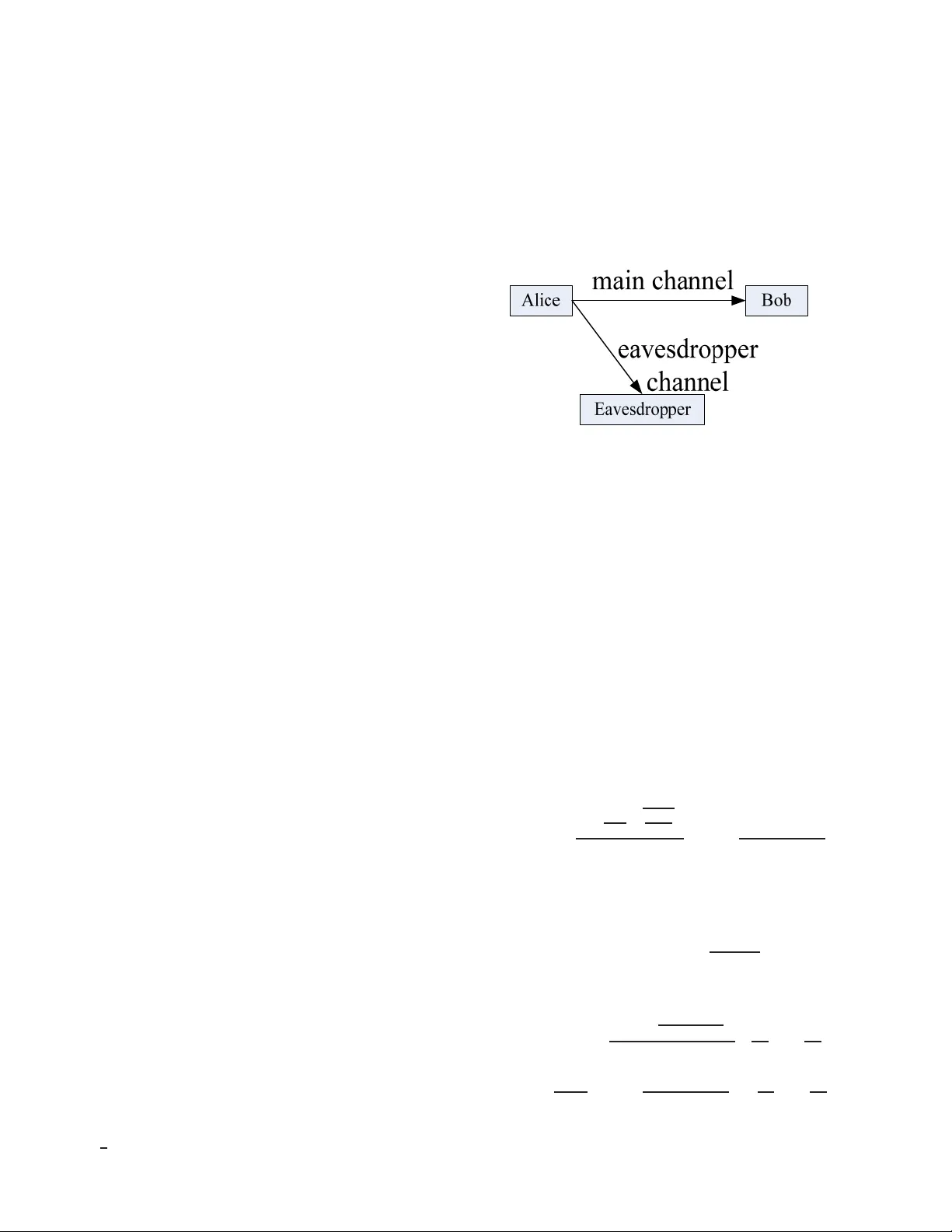
1 Closed-F orm Expressions for Secrec y Capacity o v er Correlate d Rayleigh Fading Channels Xiaojun Sun, Chunming Zhao , Member IEEE, and Ming Jian g, Member IEEE, Abstract —W e in vestigate the se cure communications o ver cor - related wiretap Rayleigh fading channels assumin g the full chan- nel state informa tion (CSI) av ailable. Based on the information theoretic formulation, we deri ve closed-f orm expre ssions for t he a verag e secre cy capacity and the outage p robability . Simulation results confirm our analytical expressions. Index T erms —Infor mation-theoretic security , wiretap channel, secrecy capacity , corre lated Rayleigh fading. I . I N T R O D U C T I O N Because wireless communica tions are susceptible to ea ves- dropp ing, traditional security mechanisms mainly rely on cryp- tograph ic protoco ls. Recently , poten tial benefits of deriving secure information from physical lay er ha ve bee n reported in [1]. In [2 ], the infor mation-th eoretic secrecy capacity was introdu ced b y using the p hysical properties of chann els. The basic pr inciple of informa tion-theo retic security has been widely accepted as the strictest notion of security , which guaran tees that th e sent massages can not be decoded by a malicious eavesdropper [1]. W yn er introd uced wiretap channel model to ev alu ate secure transmissions at the physical layer [2], where Alice transmits confiden tial data to Bob and Eve eav esdrop s the data. Csiszar et. al. and Leung-Y a n-Cheong et. al. gen eralized it to br oadcast chan nels and basic Gau ssian channels, respecti vely in [3] and [ 4]. W ei Kang e t. al. stud- ied secure comm unication s over two-user semi-d eterministic broadc ast channels [5 ]. T he secre cy capacity is defined as th e difference between the main ch annel capacity (Alice to Bob) and the eaves drop ping’ s chan nel capacity (Alice to Eve) [4]. Barros et. al. and Gop ala et. al. generalized this Gaussian wiretap channel model to wireless quasi-static fading channels [6]-[8]. The secur e MIMO systems are studied in [9]-[10]. Motiv ated by emerging wireless a pplications, there is a grow- ing in terest in exploiting th e be nefits of relay an d co operative strategies in order to guar antee secure transmissions [11]-[13]. In this paper, we consider the secure communicatio ns within W y ner’ s corr elated wiretap chann el by b uilding on th e detailed technique in [7]. Similar w o rk studied in [14] gives the limiting value of the average secrecy capacity , which only converges into the secrecy cap acity at th e h igh signal-to-n oise ratio (SNR). W e der iv e the clo sed-form expressions of the a verag e secure communicatio n capacity and the o utage probab ility un- der the assum ption of the full chann el state inf ormation (CSI) av ailab le. Simulation results verify our analytical expr essions. Nationa l Mobile Communicat ions Research Laboratory , Southeast Uni versi ty , Na njing 210096, CHIN A. E-m ail: { sunxiaojun, cmzha o, jiang ming } @seu.edu.c n Fig. 1. Fading wir etap cha nnel model. I I . S Y S T E M M O D E L Fig. 1 sho ws a fadin g wiretap channel mod el considered in this paper . Here, the source Alice transmits confidential informa tion to the destination Bob . A third party (Eve) is able of eav esdrop ping on th e transmissions. The received signals at Bob and Eve are gi ven by y = h sd x + n d (1a) z = h se x + n e (1b) where h se and h sd are co mplex Gaussian random variables (R V) with zero -mean. N d and N e denote zero-m ean comp lex Gaussian noise R Vs with unit-variance. The instantan eous SNRs α = | h sd | 2 and β = | h se | 2 are expone ntially distrib ute d. The average value is λ 1 and λ 2 , respectively . Since α and β are correlated variables, the joint PDF is expressed as [14][1 5] f ( α, β ) = I 0 2 1 − ρ q αβ ρ λ 1 λ 2 (1 − ρ ) λ 1 λ 2 exp − α/λ 1 + β /λ 2 1 − ρ (2) where ρ is the correlation between h se and h sd . I 0 ( · ) is the zeroth-o rder modified Bessel fun ction of the first kind. Using the infinite-series repr esentation of I 0 ( x ) [ 16] I 0 ( x ) = 1 + ∞ X k =1 x 2 k 4 k ( k !) 2 W e can re write the joint PDF as f ( α, β ) = ∞ X k =0 c k exp − α/λ 1 + β /λ 2 1 − ρ λ 1 λ 2 α λ 1 k β λ 2 k = ∞ X k =0 c k 1 λ 1 λ 2 exp − α/λ 1 + β /λ 2 1 − ρ α λ 1 k β λ 2 k = ∞ X k =0 c k f k ( α, β ) (3) 2 where c k = ρ k ( k !) 2 (1 − ρ ) 2 k +1 . In this study , we assume that Alice has access to CSI on both the main channel and th e eavesdropper’ s ch annel. For instance, Eve may b e not a covert eavesdropper, but simply another user [6][7 ]. Alice wants to transmit some con fidential data to Bob which Alice d oes not wish Eve kn ow . So, Alice can estimate the CSI of the eavesdropper’ s channel [6][7]. I I I . S E C U R E C O M M U N I C AT I O N S OV E R C O R R E L A T E D R AY L E I G H FA D I N G C H A N N E L Start with the technique detailed in [7], which introduces the secrecy capacity over fading chann el. A similar introd uction was presented in [8]. Recalling the results of [7] fo r the Rayleigh fading wiretap channel, the secrecy capacity fo r one realization can be wr itten as C s ( α, β ) = ( ln ( 1 + α ) − ln (1 + β ) , if α > β 0 , if α 6 β (4) where ln (1 + α ) is the rate of the m ain ch annel, and ln (1 + β ) den otes the rate of th e eav esdropp er’ s channel. A. avera ge secr ecy cap acity The average secrecy cap acity over co rrelated chann els is derived as fo llows. Theor em 1: The a verage secrecy c apacity is av eraged over all chann el realizations C s = Z ∞ 0 Z ∞ 0 C s ( α, β ) f ( α, β ) dαdβ = ∞ X k =0 c k k ! (1 − ρ ) k +1 F λ 1 , k , 1 1 − ρ − k ! k X m =0 ( λ 1 /λ 2 ) m m ! (1 − ρ ) k +1 − m F λ 1 , k + m, 1 + λ 1 /λ 2 1 − ρ − k ! k X m =0 ( λ 2 /λ 1 ) m m ! (1 − ρ ) k +1 − m F λ 2 , k + m, 1 + λ 2 /λ 1 1 − ρ (5) where fu nction F ( λ, k , µ ) can be recur si vely e valuated or computed by using popular symbolic software like MA TLAB. After integration by parts, we get F ( λ, k , µ ) = Z ∞ 0 ln ( 1 + λx ) exp ( − µx ) x k dx = λ µ F k + k µ F ( λ, k − 1 , µ ) (6) where F k is defin ed by [16, 3.3 53.5] F k = Z ∞ 0 x k 1 + λx e − µx dx = 1 λ " − 1 λ k exp µ λ E 1 µ λ + k X m =1 Γ ( m ) ( − λ ) m − k µ m # . Function F ( λ, 0 , µ ) = 1 µ E 1 µ λ exp µ λ . E 1 ( x ) = R ∞ 1 e − xt t dt is the expon ential-integral functio n [16]. Γ ( · ) is the gam ma function [16]. Pr oof: Th e integral in (5) is re-expr essed as C s = ∞ X k =0 c k Z ∞ 0 Z α 0 ln (1 + α ) f k ( α, β ) dαdβ − Z ∞ 0 Z ∞ β ln ( 1 + β ) f k ( α, β ) dαdβ = ∞ X k =0 c k Z ∞ 0 Z λ 1 u/λ 2 0 ln (1 + λ 1 u ) f k ( u, v ) du dv − Z ∞ 0 Z ∞ λ 2 v/λ 1 ln ( 1 + λ 2 v ) f k ( u, v ) du dv = ∞ X k =0 c k R 1 k − R 2 k The integral R 1 k can be evaluated b y[16, 3.38 1.1] R 1 k = Z ∞ 0 ln (1 + λ 1 u ) exp − u 1 − ρ u k du × Z λ 1 u/λ 2 0 exp − v 1 − ρ v k dv = Z ∞ 0 (1 − ρ ) k +1 ln (1 + λ 1 u ) exp − u 1 − ρ u k × γ k + 1 , λ 1 u λ 2 (1 − ρ ) du (7) where γ ( · , · ) is th e inco mplete gamma functio n d efined by [16] γ ( n + 1 , x ) = n ! − n ! e − x n X m =0 x m m ! Further with some ma nipulation s, R 1 k can be rewritten as R 1 k = Z ∞ 0 k ! (1 − ρ ) k +1 ln (1 + λ 1 u ) exp − u 1 − ρ u k du − k ! k X m =0 ( λ 1 /λ 2 ) m m ! Z ∞ 0 (1 − ρ ) k +1 − m ln (1 + λ 1 u ) × exp − 1 + λ 1 /λ 2 1 − ρ u u k + m du (8) Using (6), we can e valuate the integral R 1 k = k ! (1 − ρ ) k +1 F λ 1 , k , 1 1 − ρ − k ! k X m =0 ( λ 1 /λ 2 ) m m ! (1 − ρ ) k +1 − m F λ 1 , k + m, λ 1 /λ 2 1 − ρ (9) Similarly , we e valuate R 2 k by using the complem entary incom- plete gamma fu nction Γ ( n + 1 , x ) = n ! e − x n P m =0 x m m ! [16]. It yields R 2 k = k ! k X m =0 ( λ 2 /λ 1 ) m m ! (1 − ρ ) k +1 − m F λ 2 , k + m, 1 + λ 2 /λ 1 1 − ρ (10) 3 B. outage pr o bability of secr ecy cap acity The secrecy capa city can also be char acterized in ter ms of the outage pro bability for a target secrecy rate. The o utage probab ility can be calculated accor ding to P out ( R ) = 1 − P r ( C s ( α, β ) > R ) = 1 − P r α > e R (1 + β ) − 1 Theor em 2: Similarly in voking again the in finite-series rep - resentation of I 0 ( x ) , the ou tage proba bility is equiv a lent to P out ( R ) = 1 − exp − y 1 − ρ ∞ X k =0 c k k ! k X m =0 1 m ! µ 1 − ρ m × m X n =0 n m ! y µ m − n 1 − ρ 1 + µ k + n +1 Γ ( k + n + 1) (11) where y = e R − 1 /λ 1 and µ = e R λ 2 /λ 1 . At this point in this study , the closed-fo rm expressions of secrecy capacity have been d erived f or a c orrelated Rayleig h fading channel. In all cases of practical significa nce, the infi- nite series representation s c an be truncated without sacrificing numerical accuracy . W e also note that th e results in [7] are a special case o f our result by assum ing indepen dent channels. I V . S I M U L A T I O N R E S U LT S In Fig. 2, we plot the secr ecy capacity versus SNR over correlated fading chann els in the case of the scenar io that the SNR of ma in channel and eavesdropper’ s channel are equal. It is c learly shown that th e co rrelation b etween the m ain and the eavesdropper’ s chann el reduce the secrecy capacity . For co mparison , th e limiting value given in [14 ] also is depicted in Fig 2 . The secrecy capacity converges into the limit of the secrecy capacity [14] at h igh SNRs. However , the limiting value is far away form the secrecy capacity at low and mod erate SNRs. V . C O N C L U S I O N In this paper, we in vestigate the secure co mmunica tion over co rrelated Rayleigh fadin g W yner’ s wiretap channel. The closed form expressions for av erage secrecy cap acity an d outage probability are derived assuming th e full chann el state informa tion available. A C K N O W L E D G M E N T This work is supported by Natio nal Science Found ation of China under Gran t 6 08020 07 and supported by the Research Fund of National Mob ile Communications Research Labora- torySouth east Uni versity 200 9A10. R E F E R E N C E S [1] U. Maure r , “Sec ret k ey agreement by public disc ussion from common informati on, ” IEEE T rans. Info.Theory . , vol.39 , pp. 733-7 42, May . 1993. [2] A. D.W yner , “The wire-t ap channel , ” Bell Syst. T ec h. J . , vol .54, no.5, pp.1355-1367, Oct . 1975. [3] I. Csisz ´ ar and J. K ¨ orn er , “Broa dcast channels with confide ntial mes- sages, ” IEEE T rans. Inf o. Theory . , vol .24, no.3, pp. 339-348, May 1978. [4] S. K. Leung-Y an-Ch eong and M. E. Hellman, “The Gaussian wire-tap channe l, ” IEEE T rans. Inf . Theory . , v ol.24, no.4, pp. 451-456, Jul 1978. 5 10 15 20 25 30 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 SNR(dB) Secrecy Capacity (in nats) ρ =0 ρ =0.1 ρ =0.5 ρ =0.9 Fig. 2. The av erage secrecy capaci ty versus SNR ov er the corr elated fading channe ls. The a vera ge SNR of main channe l and ea vesdrop per’ s channel are equal. The solid li nes indica tes the limiti ng val ue gi ven i n [14]. [5] W ei kang and Nan Liu, “The Secrecy Capacit y of the Semi-det erministic Broadca st Cha nnel, ” in Pro c. IEEE ISIT . , Seoul, K orea, Jun. 2009, pp. 2767-2771. [6] J. Barros and M. R. D. Rodri gues, “Sec recy capacit y of wireless channe ls, ” in Pr oc. IEE E ISIT . , Seattl e, W A, Jul. 2006, pp. 356 -360. [7] Mat thieu Bloch, J o ˜ ao Barros, Migue l R. D. Rodrigues and Ste ven W . McLaughli n, “Wire less Information-Theoreti c Security , ” IEEE T rans. Info.Theory . , vol.54, no.6, pp. 2515-2534, May 20 08. [8] P . K. Gopala, L . Lai, and H. E. Gamal, “On the secrec y capa city of fadi ng chan nels, ” IEEE T rans. Info.Theory . , vol .54, no.10, pp. 4687- 4698, Oct 2008. [9] Z. Li, W . Tra ppe and R. Y ates, “Secre t communicatio n vi a multi antenna transmission, ” in Pr oc. 41st Confer ence on Informati on Science s and Systems. , Mar 2007. [10] S. Shafiee and S. Ulukus, “ Achie va ble ra tes in Gaussian MISO channels with sec recy constra ints, ” in Pr oc. IEEE ISIT . , Jun 2007, pp. 2466 - 2470. [11] L. Lai and H. El Gamal , “The relay-ea vesdrop per channel: coop eration for secre cy , ” IEEE T rans. Inf. Theo ry . , vol.54, no.9, pp. 4005 - 4019, Sept 2008. [12] L. Dong, Z . Han, A. Petropulu and H. V . Poor , “Secure wireless communicat ions via coope ration, ” in Proc. 46th A nnual Allerton Conf . Commun., Contro l, and Comput ing. , Sep t 2008, pp.1132 - 1138. [13] L. Dong, Z. Han, A. Petropu lu and H. V . Poor , “ Amplify-and-forw ard based coop eration for secure wirele ss communicati ons, ” in P r oc. IEEE ICASSP . , Apr 2009, pp.261 3 - 2616. [14] H. jeon, N. Kim, M. Kim, H. Lee and J. Ha“Sec recy capacity over correla ted ergodic fadi ng channel, ” in Proc. IEEE Mili tary Comm. , 2008. [15] Ma rvin K. Simon, Pr obability Distributio ns In volvin g Gaussian Random V ariables. , Sprin ger Press, 2006. [16] I. S. Gradshte yn and I. M. Ryzhik , T able of Inte grals, Series, and Pr oducts,6th ed . , San Diego:CA, Aca demic press, 2000.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment