Trimmed Moebius Inversion and Graphs of Bounded Degree
We study ways to expedite Yates's algorithm for computing the zeta and Moebius transforms of a function defined on the subset lattice. We develop a trimmed variant of Moebius inversion that proceeds point by point, finishing the calculation at a subs…
Authors: Andreas Bj"orklund, Thore Husfeldt, Petteri Kaski (HIIT)
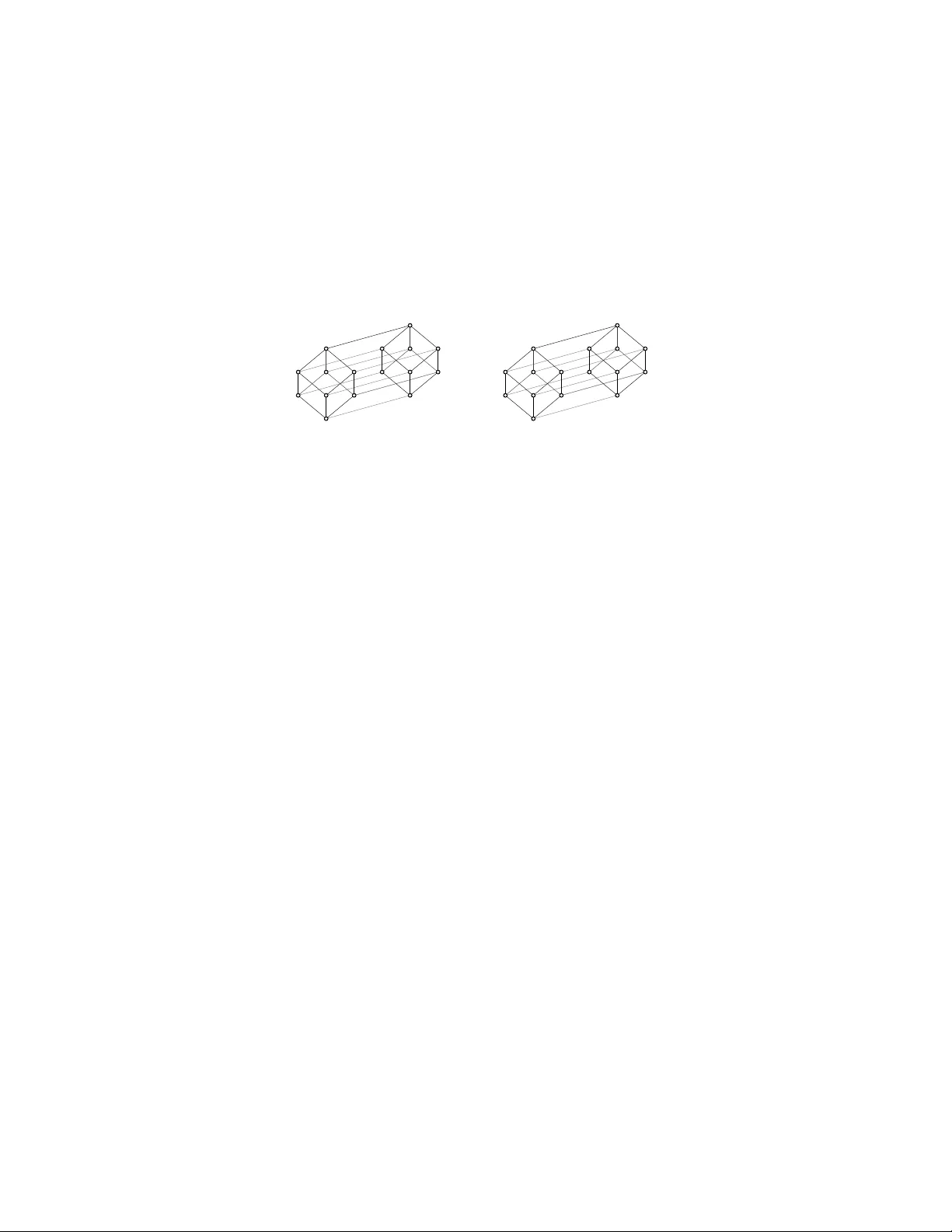
Symposium on Theoretical Aspects of Computer Science 2008 (Bordeaux), pp. 85-96 www .stacs-conf .org TRIMMED MOEBIUS INVERSIO N AND GRAPHS OF BOUNDED DEGREE ANDREAS BJ ¨ ORKLUND 1 , THORE HUSFELDT 1 , PETTE RI K ASKI 2 , AND M IK KO KOIVISTO 2 1 Lund Universit y , Departmen t of Computer Science, P .O.Bo x 118, S E- 22100 Lu n d, Sweden E-mail addr ess : andreas.b jorklund @logipard.com, thore.husfel dt @cs.lu.se 2 Helsinki In stitute for Information T ec hnology HI IT, Universit y of Helsinki, Department of Com- puter S cience, P .O.Bo x 68, FI-00014 Universit y of Helsinki, Finland E-mail addr ess : { pet t eri.k aski,mikk o.koivisto } @cs.hels ink i.fi Abstra ct. W e study wa ys to exped ite Y ates’ s algorithm for computin g t h e zeta and Moebius transforms of a function defined on the sub set lattice. W e develop a trimmed v arian t of Mo ebius inv ersion that pro ceeds p oint by p oint, finishing th e calculation at a subset b efore considering its sup ersets. F or an n -element un iverse U and a family F of its subsets, trimmed Mo ebius inv ersion allo ws us t o comput e th e number of packings, co verings, and p artitions of U with k sets from F in time within a p olynomial factor (in n ) of the num b er of sup ersets of th e members of F . Relying on an interse ction theorem of Chung et al. (1986) to b ound the sizes of set families, w e app ly th ese ideas to w ell-studied com b inatorial op t imisation problems on graphs of maxim um d egree ∆. I n particular, we sho w how to compute the Domatic Num b er in t ime within a p olynomial factor of (2 ∆+1 − 2) n/ (∆+1) and the Chromatic N umber in time within a p olynomial factor of (2 ∆+1 − ∆ − 1) n/ (∆+1) . F or any constant ∆, these b ounds are O ` (2 − ǫ ) n ´ for ǫ > 0 indep en dent of th e num b er of vertices n . 1. In tr o duction Y ates’s algorithm from 1937 is a kind of fast F ourier transform that computes f or a function f : { 0 , 1 } n → R and another function υ : { 0 , 1 } × { 0 , 1 } → R the v alues b f ( x 1 , . . . , x n ) = X y 1 ,...,y n ∈{ 0 , 1 } υ ( x 1 , y 1 ) · · · υ ( x n , y n ) f ( y 1 , . . . , y n ) . (1.1) sim ultaneously for all X = ( x 1 , . . . , x n ) ∈ { 0 , 1 } n using only O (2 n n ) op erations, instead of the obvious O (4 n n ). The algorithm is textb o ok material in many sciences. Y et, th ough it app ears in Knuth [13, § 3.2], it has receiv ed little atten tion in com binatorial optimisation. Recen tly , th e authors [3, 4] u sed Y ates’s algorithm in combinatio n with Moeb ius in v er- sion to giv e algorithms f or a n umb er of canonical com b inatorial optimisation problems su c h as Chromatic Num b er and Domatic Nu m b er in n -v ertex graphs, and n -terminal Minimum Steiner T r ee, in runnin g times within a p olynomial factor of 2 n . This researc h wa s supported in part by the Academy of Finland, Grants 117499 (P .K.) and 109101 (M.K.). c A. Bj ¨ orklun d, T . Husfeldt, P . Kaski, and M . Koivisto CC Creative Commons Attribution-NoDer ivs License 86 A. BJ ¨ ORKLUND, T . HUSFELDT, P . KASKI, AND M . KOIVI STO F rom th e wa y it is normally stated, Y ates’s alg orithm seems to face an inheren t 2 n lo w er b ound, up to a p olynomial factor, and it also seems to b e oblivious to the stru ctural prop er ties of the transform it computes. The motiv ation of the p r esen t in vesti gation is to exp edite the r unning time of Y ates’s algorithm for certain structur es so as to get runn ing times with a domin ating f actor of the form (2 − ǫ ) n . F rom the p ersp ectiv e of runn ing times alone, our impr ov emen ts are mo dest at b est, but apart from provi d ing evidence that the aesthetically app ealing 2 n b oun d from [4] can b e b eat en, the com b inatorial fr amew ork we pr esen t seems to b e new and ma y present a fr u itful direction for exact exp onentia l time algorithms. 1.1. Results In a graph G = ( V , E ), a s et D ⊆ V of v ertices is dominating if ev ery v ertex not in D has at least one neigh b our in D . The doma tic numb er of G is the largest k for wh ic h V can b e partitioned in to k dominating sets. W e sho w ho w to compute the domatic n umb er of an n -ve r tex grap h with maxim um degree ∆ in time O ∗ (2 ∆+1 − 2) n/ (∆+1) ; the O ∗ notation suppr esses factors that are p olynomial in n . F or constant ∆ , this b ound is alw a ys b etter than 2 n , though not by m uch: ∆ 3 4 5 6 7 8 · · · (2 ∆+1 − 2) 1 / (∆+1) 1 . 9344 1 . 9744 1 . 9895 1 . 9956 1 . 9981 1 . 9992 · · · The chr omatic numb er of a graph is the minimum k for whic h the v ertex set can b e co v ered w ith k indep en d en t sets; a set I ⊆ V is indep endent if no t wo ve rtices in I are neigh b ours. W e sho w ho w to compute the chromatic num b er of an n -v ertex graph with maxim um degree ∆ in time O ∗ (2 ∆+1 − ∆ − 1) n/ (∆+1) . This is sligh tly faster th an for Domatic Numb er: ∆ 3 4 5 6 7 8 · · · (2 ∆+1 − ∆ − 1) 1 / (∆+1) 1 . 8613 1 . 9332 1 . 9675 1 . 9840 1 . 9921 1 . 9961 · · · One n otes that eve n for mo d erate ∆, the improv emen t o ve r 2 n is min ute. Moreo v er, the colouring resu lts for ∆ ≤ 5 are not ev en the b est kno wn: by Bro oks’s Theorem [5], the c hromatic num b er of a connected graph is b ound ed b y its maxim um degree unless the graph is complete or an o dd cycle, b oth of whic h are easily recognised. It remains to decide if the chromatic n u mb er is 3, 4, or 5, and with algorithms from the literature, 3- and 4-colourabilit y can b e decided in time O (1 . 3289 n ) [1] and O (1 . 7504 n ) [6], resp ectiv ely . Ho w eve r , this app r oac h do es stop at ∆ = 5, since w e kno w n o o (2 n ) algorithm for 5- colourabilit y . O th er approac hes for colouring low-degree graphs are kn o wn via path width : giv en a path decomp ositi on of wid th w the k -colourabilit y can b e decided in time k w n O (1) [11]; for 6-regular grap h s one can fin d a decomp ositio n w ith w ≤ n (23 + ǫ ) / 45 for an y ǫ > 0 and sufficient ly l arge n [11], and f or graphs with m edges one can find w ≤ m / 5 . 769 + O (log n ) [12]. Ho w eve r , ev en these p athwidth based b ounds fall sh ort when k ≥ 5—w e are not aw are of an y previous o (2 n ) algorithm. F or the general case, it to ok 30 y ears and man y pap ers to impr o v e th e constant in the b ound for Chromatic Numb er from 2 . 4423 [14 ] via 2 . 4151 [9], 2 . 4023 [6], 2 . 3236 [2], TRIMMED M OEBIUS INVERSION AND GRAPHS OF BOUNDED DEGREE 87 Figure 1: T rimmed e v aluation. Or iginally , Y ates’s algorithm consider s the entire subset la ttice (left). W e trim the ev alation from b elow b y considering only the s up e r sets of ‘interesting’ p oints (middle), and from ab ov e by abando ning computation when we reach cer ta in p oints (rig ht). to 2 [4], and a similar (if less glacial) story can b e told for the Domatic Numb er. None of these approac hes w as sensitive to the d ensit y of the graph. Moreo ve r, w hat int erests us here is not so muc h the size of the constan t, but the f act that it is less th an 2, disp elling the tempting h yp othesis that 2 n should b e a ‘difficult to b eat ’ b oun d for compu ting the Chromatic Num b er for sparse graphs. In § 4 w e presen t some tailor-made v arian ts for whic h the run ning time improv emen t fr om applying the id eas of th e p resent pap er are more striking. Chromatic Num b er and Domati c Numb er are sp ecial cases of set partition pr oblems, where the ob jectiv e is to partition an n -elemen t set U (here, the vertic es of a graph) with mem b ers of a giv en family F of its sub sets (here, the indep enden t or d ominating sets of the graph). In fu ll generalit y , we sh o w ho w to compute the cov ering, pac king, an d partition n umb ers of ( U, F ) in time within a p olynomial factor of |{ T ⊆ U : there exists an S ∈ F su ch that S ⊆ T }| , (1.2) the num b er of su p ersets of the members of F . In the worst case, this b ound is not b ette r than 2 n , and the com binatorial c hallenge in applying the pr esen t ideas is to find go o d b ounds on the ab ov e expression. 1.2. T ec hniques The main tec hn ical contribution in this pap er, sk etc hed in Figure 1, is that Y ates’s algorithm can, for certain natur al c hoices of υ : { 0 , 1 } × { 0 , 1 } → R , b e trimmed b y considering in a b ottom-up f ashion only those X ∈ { 0 , 1 } n that we are actually interested in, for example th ose X f or which f ( X ) 6 = 0 and their sup ersets. (W e will understand X as a sub set of { 1 , . . . , n } w henev er th is is conv enien t.) Among the transforms th at are amenable to trimming are the zeta and Mo ebius transform s on the subs et lattice . W e use the trimmed algorithms for zeta and Mo ebius transform s to exp edite Mo ebius in version, a generalisation of the pr inciple of inclusion–exclusion, whic h allo ws us to compute the co v er, packing, and partition num b ers. T he fact that these num b ers can b e computed via Moeb ius in ve r sion w as already used in [2, 3, 4], an d those parts of the p resen t pap er con tain little that is n ew, except for a somewh at more explicit and streamlined p resen tation in the framewo rk of partial order theory . The fact that we can ev a luate b oth the zeta and Mo ebius transforms p oin t wise in s u c h a w ay th at w e are done with X b efore we pr o ceed to Y for ev ery Y ⊃ X also enables us to further trim compu tations from wh at is outlined ab o ve. F or in s tance, if we seek a minimum set p artition of sets from a family F of sub sets of U , then it suffices to fi nd the minim um partition of all X suc h that U \ X = S for s ome S ∈ F . In particular, w e need not consider ho w many sets it tak es to partition X for X ’s large enough for U \ X not to con tain an y set fr om F . The main combinatoria l con tribution in this p ap er is that if F is the family of m aximal indep en den t sets, or the f amily of dominating s ets in a graph, then we show how to b ound (1.2) in terms of the maximum degree ∆ using an in tersection theorem of Chung et al. [8] that go es bac k to S h earer’s Ent r opy Lemma. F or this we merely need to observe that 88 A. BJ ¨ ORKLUND, T . HUSFELDT, P . KASKI, AND M . KOIVI STO the in tersection of F an d the closed neigh b ourho o ds of the input grap h excludes certain configurations. In summ ary , via (1.2) th e task of b ounding th e runn ing time for (sa y) Domatic Number reduces to a combinato r ial statemen t ab out the in tersections of certain families of sets. Notation. Y ate s’s algorithm op erates on the lattice of su b sets of an n -elemen t u niv erse U , and we find it con v enient to wo r k with notation established in partial ord er theory . F or a family F of subsets of U , let min F (resp ectiv ely , max F ) denote the family of minimal (resp ecti vely , maximal) elemen ts of F with r esp ect to subset in clus ion. The u pp er closur e (sometimes called up-set or filter ) of F is d efined as ↑ F = { T ⊆ U : there exists an S ∈ F such that S ⊆ T } . F or a fun ction f d efi ned on su bsets of U , the supp ort of f is defined as supp( f ) = { X ⊆ U : f ( X ) 6 = 0 } . F or a graph G , w e let D denote the family of dominating sets of G and I the family of i ndep end ent sets of G . Also, f or a subset W ⊆ V of v ertices, w e let G [ W ] denote the subgraph indu ced by W . F or a p rop osition P , we us e I v erson’s brac ke t notation [ P ] to mean 1 if P is tru e and 0 otherwise. 2. T rimmed Mo ebius In v ersion F or a family F of sets from { 0 , 1 } n and a set X ∈ { 0 , 1 } n w e will consider k -tuples ( S 1 , . . . , S k ) with S i ∈ F and S i ⊆ X . Suc h a tu ple is disjoint if S i 1 ∩ S i 2 = ∅ for all 1 ≤ i 1 < i 2 ≤ k , and c overing if S 1 ∪ · · · ∪ S k = X . F rom these concepts we d efine f or fixed k (1) the c over numb er c ( X ), viz. th e num b er of co ve rin g tuples, (2) the p acking numb er p ( X ), viz. the num b er of disjoint tuples, (3) the p artition numb er or disjoint c over nu mb er d ( X ), viz. the num b er of tu ples th at are b oth d isjoin t and co v ering. In this s ection we sh o w how to compute these num b ers in time |↑ F | n O (1) , rather than 2 n n O (1) as in [3, 4]. The algorithms are concise but somewhat inv olv ed, and we c ho ose to present them here starting w ith an exp lanation of Y ates’s algorithm. Th us, the first t wo su bsections are primarily exp ository and aim to establish the new ingredient s in our algorithms. A t the h eart of our algorithms lie t wo transforms of fu n ctions f : { 0 , 1 } n → R on the subset lattice. The zeta transform f ζ is defined f or all X ∈ { 0 , 1 } n b y ( f ζ )( X ) = X Y ⊆ X f ( Y ) . (2.1) (The notatio n f ζ can b e r ead either as a formal op erator or as a pro duct of the 2 n - dimensional v ector f an d the matrix ζ with en tries ζ Y X = [ Y ⊆ X ].) Th e Mo ebius transform f µ is d efined for all X ∈ { 0 , 1 } n b y ( f µ )( X ) = X Y ⊆ X ( − 1) | X \ Y | f ( Y ) . (2.2) TRIMMED M OEBIUS INVERSION AND GRAPHS OF BOUNDED DEGREE 89 These transform s are eac h other’s inv erse in the sense that f = f ζ µ = f µζ , a fu ndament al com binatorial p rinciple called Mo ebius inversion . W e can (jus t barely) dr a w an example in four d im en sions for a function f give n by f ( { 4 } ) = f ( { 1 , 2 , 4 } ) = 1, f ( { 1 , 3 } ) = 2 and f ( X ) = 0 otherwise: 1 1 2 ζ − → µ ← − 1 1 1 1 2 3 3 2 2 4 Another example that we will use later is the connection b etw een the p ac king n umb er and the d isjoin t cov er num b er, p = dζ , (2.3) whic h is easy to v erify: By defin ition, ( dζ )( X ) = X Y ⊆ X d ( Y ) . Ev ery d isjoin t k -tuple ( S 1 , . . . , S k ) with S 1 ∪ · · · ∪ S k ⊆ X app ears once on the right hand side, n amely for Y = S 1 ∪ · · · ∪ S k , so this exp ression equals the p acking n umb er p ( X ). 2.1. Y ates’s algorithm Y ates’s algorithm [17] exp ects the transform in the form of a function υ : { 0 , 1 } × { 0 , 1 } → R and computes th e transformed v alues b f ( X ) = X Y ∈{ 0 , 1 } n υ ( x 1 , y 1 ) · · · υ ( x n , y n ) f ( Y ) . (2.4) sim ultaneously for all X ∈ { 0 , 1 } n . Here, w e let ( x 1 , . . . , x n ) and ( y 1 , . . . , y n ) denote th e binary representa tions (or, ‘incidence ve ctors’) of X and Y , so x j = [ j ∈ X ] and y j = [ j ∈ Y ]. T o obtain (2.1) set υ ( x, y ) = [ y ≤ x ] and to obtain (2.2) set υ ( x, y ) = [ y ≤ x ]( − 1) x − y . The direct ev aluation of (2.4 ) wo u ld tak e 2 n ev aluat ions of f for eac h X , for a total of O (2 n 2 n n ) = O (4 n n ) op erations. The zeta and Mo ebius transform s dep end only on Y ⊆ X , so they w ould require only P X 2 | X | = P 0 ≤ i ≤ n n i 2 i = 3 n ev aluat ions. Y ates’s algorithm is faster still and compu tes the general form in O (2 n n ) op er ations: Algorithm Y. ( Y ates’s algorithm. ) Computes b f ( X ) defined in (2.4 ) for all X ∈ { 0 , 1 } n given f ( Y ) for all Y ∈ { 0 , 1 } n and υ ( x, y ) for all x, y ∈ { 0 , 1 } . Y1: F or each X ∈ { 0 , 1 } n , set g 0 ( X ) = f ( X ). Y2: F or each j = 1 , . . . , n and X ∈ { 0 , 1 } n , set g j ( X ) = υ ([ j ∈ X ] , 0) g j − 1 ( X \ { j } ) + υ ([ j ∈ X ] , 1) g j − 1 ( X ∪ { j } ) . Y3: Output g n . The in tuition is to compute b f ( X ) ‘co ordin ate-wise’ b y fixing fewer and fewe r bits of X in the sense that, for j = 1 , . . . , n , g j ( X ) = X y 1 ,...,y j ∈{ 0 , 1 } υ ( x 1 , y 1 ) · · · υ ( x j , y j ) f ( y 1 , . . . , y j , x j +1 , . . . , x n ) . (2.5) 90 A. BJ ¨ ORKLUND, T . HUSFELDT, P . KASKI, AND M . KOIVI STO Indeed, the correctness pro of is a straightforw ard v erification (by induction) of the ab o v e expression. 2.2. T rimmed p oint wise ev aluation T o set the stage for our present con trib utions, observe that b oth the zeta and Mo ebius transforms ‘gro w u pw ards’ in the s ubset lattice in the sense that supp( f ζ ) , supp( f µ ) ⊆ ↑ supp( f ). Th u s, in ev aluating the t wo transforms, one ough t to b e able to trim off redu ndant parts of the lattice and w ork only w ith lattice p oints in ↑ supp( f ). W e w ould naturally lik e trimm ed ev aluation to o ccur in O ( |↑ supp( f ) | n ) op erations, in the sp irit of Algorithm Y. How ev er, to obtain the v alues at X in Step Y2 of Algorithm Y, at fi rst sigh t it app ears that we m u s t b oth ‘lo ok up’ (at X ∪ { j } ) and ’lo ok down’ (at X \ { j } ). F ortun ately , it suffices to only ‘lo ok down’. Ind eed, for th e zeta transform, setting υ ( x, y ) = [ y ≤ x ] and simp lifying Step Y2 yields g j ( X ) = [ j ∈ X ] g j − 1 ( X \ { j } ) + g j − 1 ( X ) . (2.6) F or the Mo ebius transform, setting υ ( x, y ) = [ y ≤ x ]( − 1) x − y and simp lifying yields g j ( X ) = − [ j ∈ X ] g j − 1 ( X \ { j } ) + g j − 1 ( X ) . (2.7) F urthermore, it is not necessary to lo ok ‘too far’ d o wn: for b oth transforms it is immediate from (2.5) that g j ( X ) = 0 holds for all X / ∈ ↑ sup p( f ) and j = 0 , . . . , n . (2.8) In wh at follo ws w e tacitly emplo y (2.8) to limit the scop e of (2.6) and (2.7) to ↑ sup p( f ). The next observ ation is that the lattice p oin ts in ↑ supp( f ) can b e ev aluated in order of their rank, using sets L ( r ) con taining th e p oin ts of rank r . Initially , the sets L ( r ) con tain only sup p( f ), but we add elemen ts from ↑ su pp( f ) as we go along. These obser v ations result in the follo win g algorithm for ev aluating the zeta trans f orm; the algorithm for ev a lu ating the Mo eb iu s transform is obtained by replacing (2.6 ) in Step Z3 with (2.7). Algorithm Z. ( T rimme d p ointwise fast zeta tr ansform. ) Computes the nonzero pa rt of f ζ g iven the nonzero part of f . The algorithm maintains n + 1 families L (0) , . . . , L ( n ) of subsets X ∈ { 0 , 1 } n ; L ( r ) contains only sets of size r . W e compute aux iliary v alues g j ( X ) for all 1 ≤ j ≤ n and X ∈ ↑ supp( f ); it holds that g n ( X ) = ( f ζ )( X ). Z1: F or each X ∈ supp( f ), insert X into L ( | X | ). Set the current rank r = 0 . Z2: Select a ny X ∈ L ( r ) and remov e it fro m L ( r ). Z3: Set g 0 ( X ) = f ( X ). F or e a ch j = 1 , . . . , n , set g j ( X ) = [ j ∈ X ] g j − 1 ( X \ { j } ) + g j − 1 ( X ) . [A t this p o int g n ( X ) = ( f ζ )( X ).] Z4: If g n ( X ) 6 = 0 , then o utput X and g n ( X ). Z5: F or each j / ∈ X , insert X ∪ { j } in to L ( r + 1). Z6: If L ( r ) is empt y then increment r ≤ n until L ( r ) is nonempty; ter mina te if r = n and L ( n ) is empty . Z7: Go to Z2. Observe that th e ev aluation at X is complete once S tep Z3 terminates, w h ic h en ab les further trimming of the lattice ‘fr om ab ov e’ in case the v alues at lattice p oin ts with higher rank are not requir ed. TRIMMED M OEBIUS INVERSION AND GRAPHS OF BOUNDED DEGREE 91 By symmetry , the presen t ideas wo rk just as well for transforms th at ‘gro w down w ards’, in whic h case one needs to ‘look up’. Ho w eve r , they d o n ot w ork for transforms that gro w in b oth directions, su c h as the W alsh–Hadamard transform. In the applications that no w follo w, f will alw ays b e the in dicator function of a family F . In this case having sup p( f ) quic kly a v ailable translates to F b eing efficien tly listable; for example, with p olynomial dela y . 2.3. Co vers The easiest application of th e trimmed Mo ebius inv ersion compu tes for eac h X ∈ ↑ F the co v er n umb er c ( X ). This is a p articularly straigh tforwa rd function of the zeta transform of th e indicator function f : sim p ly raise eac h elemen t of f ζ to the k th p o w er and transf orm the r esult bac k usin g µ . T o see this, obs erv e that b oth sides of the equation ( cζ )( Y ) = ( f ζ )( Y ) k (2.9) coun t the num b er of wa ys to c ho ose k -tuples ( S 1 , . . . , S k ) w ith S i ⊆ Y and S i ∈ F . By Mo ebius inv ersion, we can reco v er c by applying µ to b oth sides of (2.9) . Algorithm C. ( Cov er numb er. ) Computes c ( X ) for all X ∈ ↑ F given F . The sets L ( r ) and auxilia ry v alues g j ( X ) are as in Algo rithm Z; also requir ed ar e auxiliar y v alues h j ( X ) for Mo ebius transform. C1: F or each X ∈ F , insert X into L ( | X | ). Set the current r ank r = 0 . C2: Select a ny X ∈ L ( r ) and remove it fr o m L ( r ). C3: [Zeta tra nsform.] Set g 0 ( X ) = [ X ∈ F ]. F or each j = 1 , . . . , n , set g j ( X ) = [ j ∈ X ] g j − 1 ( X \ { j } ) + g j − 1 ( X ) . [A t this p o int it holds that g n ( X ) = ( f ζ )( X ).] C4: [Ev aluate zeta transform of c ( X ).] Set h 0 ( X ) = g n ( X ) k . C5: [Mo ebius tra nsform.] F or each j = 1 , . . . , n , set h j ( X ) = − [ j ∈ X ] h j − 1 ( X \ { j } ) + h j − 1 ( X ) . C6: Output X and h n ( X ). C7: F or each j / ∈ X , insert X ∪ { j } in to L ( r + 1). C8: If L ( r ) is empt y , then increment r ≤ n un til L ( r ) is nonempty; termina te if r = n and L ( n ) is empty . C9: Go to C2. 2.4. P artitions What mak es the partition p roblem sligh tly less transparent is the fact that w e need to use dynamic programming to assemble partitions from sets with different ranks. T o this end, we need to compute f or eac h rank s the ‘ranke d zeta transform’ ( f ζ ( s ) )( X ) = X Y ⊆ X, | Y | = s f ( Y ) . F or rank s , consider the num b er d ( s ) ( Y ) of tup les ( S 1 , . . . , S k ) with S i ∈ F , S i ⊆ Y , S 1 ∪ · · · ∪ S k = Y and | S 1 | + · · · + | S k | = s . Then d ( Y ) = d ( | Y | ) ( Y ). F urthermore, the 92 A. BJ ¨ ORKLUND, T . HUSFELDT, P . KASKI, AND M . KOIVI STO zeta-transform ( d ( s ) ζ )( X ) count s th e num b er of wa ys to c ho ose ( S 1 , . . . , S k ) with S i ⊆ X , S i ∈ F , and | S 1 | + · · · + | S k | = s . An other wa y to coun t the exact same quan tit y is q ( k , s, X ) = X s 1 + ··· + s k = s k Y i =1 ( f ζ ( s i ) )( X ) . (2.10) Th u s w e can reco v er d ( s ) ( Y ) from q ( k , s, X ) b y Mo ebius inv ersion. As it stands, (2.10) is time-consuming to ev aluate eve n given all the rank ed zeta trans- forms, bu t w e can compute it efficiently using dynamic programming b ased on the r ecurrence q ( k , s, X ) = ( P s t =0 q ( k − 1 , s − t, X )( f ζ ( t ) )( X ) , if k > 1 , ( f ζ ( s ) )( X ) , if k = 1 . This h app ens in Step D4. Algorithm D. ( Disjoint c over numb er. ) Computes d ( X ) for all X ∈ ↑ F g iven F . The sets L ( r ) are as in Algorithm Z; we also need auxiliary v alues g ( s ) j ( X ) and h ( s ) j ( X ) for all X ∈ ↑ F , 1 ≤ j ≤ n , and 0 ≤ s ≤ n ; it ho lds tha t g ( s ) n ( X ) = ( f ζ ( s ) )( X ) and h ( s ) n ( X ) = d ( s ) ( X ). D1: F or each X ∈ F , insert X into L ( | X | ). Set the current r ank r = 0 . D2: Select a ny X ∈ L ( r ) and remove it fro m L ( r ). D3: [Ranked zeta transfo rm.] F o r ea ch s = 0 , . . . , n , set g ( s ) 0 ( X ) = [ X ∈ F ][ | X | = s ]. F or each j = 1 , . . . , n and s = 0 , . . . , n , set g ( s ) j ( X ) = [ j ∈ X ] g ( s ) j − 1 ( X \ { j } ) + g ( s ) j − 1 ( X ) . [A t this p o int it holds that g ( s ) n ( X ) = ( f ζ ( s ) )( X ) for all 0 ≤ s ≤ n .] D4: [Ev aluate zeta tra nsform of d ( s ) .] F or each s = 0 , . . . , n , set q (1 , s ) = g ( s ) n ( X ). F or each i = 2 , . . . , k and s = 0 , . . . , n , set q ( i, s ) = P s t =0 q ( i − 1 , s − t ) g ( t ) n ( X ) . D5: [Ranked Mo ebius transform.] F or ea ch s = 0 , . . . , n , set h ( s ) 0 ( X ) = q ( k, s ). F or each j = 1 , . . . , n and s = 0 , . . . , n , set h ( s ) j ( X ) = − [ j ∈ X ] h ( s ) j − 1 ( X \ { j } ) + h ( s ) j − 1 ( X ) . [A t this p o int it holds that h ( s ) n ( X ) = d ( s ) ( X ) for all 0 ≤ s ≤ n .] D6: Output X a nd h ( | X | ) n ( X ). D7: F or each j / ∈ X , insert X ∪ { j } in to L ( r + 1). D8: If L ( r ) is empt y , then increment r ≤ n un til L ( r ) is nonempty; termina te if r = n and L ( n ) is empty . D9: Go to D2. 2.5. P ac kings According to (2.3), to compute p ( X ) it suffices to zeta-transform th e partition n umb er. This amounts to ru n ning Algorithm Z after Algorithm D. (F or a d ifferen t approac h, see [4 ].) TRIMMED M OEBIUS INVERSION AND GRAPHS OF BOUNDED DEGREE 93 3. Applications 3.1. The n umber of dominating sets in sparse graphs This section is p u rely com binatorial. Let D d enote the domin ating sets of a graph. A complete graph has 2 n − 1 dominating s ets, and sparse graphs can ha ve almost as man y: the n -star graph has 2 n − 1 dominating sets and a ve rage degree less than 2. Th us w e ask ho w large | D | can b e for graphs with b ounded maxim um degree. An easy example is provided b y the disjoint union of complete graphs of order ∆ + 1: eve ry v ertex su b set th at includes at least one v ertex from eac h comp onen t is dominating, so | D | = (2 ∆+1 − 1) n/ (∆+1) . W e shall sho w that this is in fact the largest p ossible D f or graphs of maxim um degree ∆ . Our analysis is based on the follo win g in tersection theorem. Lemma 3.1 (Chung et al. [8]) . L et U b e a finite se t with subsets P 1 , . . . , P m such that every u ∈ U is c onta ine d in at le ast δ subsets. L et F b e a family of subsets of U . F or e ach 1 ≤ ℓ ≤ m , define the pr oje ctions F ℓ = { F ∩ P ℓ : F ∈ F } . Then | F | δ ≤ m Y ℓ =1 | F ℓ | . Theorem 3.2. The numb e r of dominating sets of an n - vertex g r aph with maximum de gr e e ∆ is at most (2 ∆+1 − 1) n/ (∆+1) . Pr o of. Let G = ( V , E ) b e a graph with | V | = n and maximum d egree ∆. F or eac h v ∈ V , let A v b e the closed n eighb ou r ho o d around ve rtex v , A v = { v } ∪ { u ∈ V : uv ∈ E } . (3.1) Next, for eac h u ∈ V with degree d ( u ) < ∆, add u to ∆ − d ( u ) of the sets A v not already con taining u (it do es not matter wh ic h). Let a v = | A v | and note that P v a v = (∆ + 1) n . W e wa nt to apply Lemma 3.1. T o this end , let U = V and m = n . By constr u ction, ev ery u ∈ V b elongs to exactly δ = ∆ + 1 subsets A v . T o get a nontrivial b ound on D w e need to b ound the size of D v = { D ∩ A v : D ∈ D } . Eve r y D ∩ A v is one of the 2 a v subsets of A v , b ut none of the D ∩ A v can b e the empt y set, b ecause either v or one of its neigh b ours must b elong to the dominating set D . Thus | D v | ≤ 2 a v − 1. By Lemma 3.1, we ha ve | D | ∆+1 ≤ Y v (2 a v − 1) . (3.2) Since x 7→ log (2 x − 1) is concav e, J ensen’s inequ alit y give s 1 n X v log (2 a v − 1) ≤ log (2 P v a v /n − 1) = log (2 ∆+1 − 1) . T aking exp onen tials and com bin ing w ith (3.2) giv es | D | ∆+1 ≤ (2 ∆+1 − 1) n . 3.2. Domatic Num b er W e first obs er ve th at a graph can b e pac k ed w ith k dominating sets if and only if it can b e p ac k ed w ith k minimal d ominating sets, so we can consider k -pac kings from min D instead of D . Th is has the adv an tage that m in D can b e listed faster than 2 n . Lemma 3.3 (F omin et al. [10]) . Any n -vertex gr aph has at most O ∗ (1 . 717 0 n ) minimal dominating sets, and they c an b e liste d within that time b ound. 94 A. BJ ¨ ORKLUND, T . HUSFELDT, P . KASKI, AN D M . KOI VISTO Theorem 3.4. F or an n -vertex g r aph G with maximum de gr e e ∆ we c an de cide in time O ∗ (2 ∆+1 − 2) n/ (∆+1) whether G admits a p acking with k dominating sets. Pr o of. W e u se Algorithm D with F = min D . By the ab o ve lemma, we can complete S tep D1 in time O ∗ (1 . 717 0 n ). T he r est of th e algorithm r equires time O ∗ ( |↑ min D | ). S in ce ev ery sup erset of a dominating set is itself d ominating, ↑ min D is a sub-family of D (in fact, it is exactly D ), so Th eorem 3.2 b oun ds the total runn ing time by O ∗ (2 ∆+1 − 1) n/ (∆+1) . W e can do slightly b ette r if we mo dify Algorithm D in Step D7 to insert X ∪ { j } only if it excludes at least one ve rtex for eac h closed neigh b ourho o d. Put otherwise, w e ins ert X ∪ { j } only if the set V \ ( X ∪ { j } ) dominates the graph G . The graph then has Domatic Num b er at least k + 1 if and only if the algorithm rep orts some X for wh ic h d ( X ) is nonzero. The running time can again b e b ound ed as in Theorem 3.2 bu t no w D ∩ A v can neither b e the empty s et, nor b e equal to A v . Thus the app lication of Lemma 3.1 can b e strengthened to yield the claimed result. 3.3. Chromatic Number Our first argumen t for Chr omatic Number is similar; we giv e a s tr onger and sligh tly more complicated argument in § 3.4. W e consider the indep enden t sets I of a graph . An in dep en d en t set is not necessarily dominating, but it is easy to see that a maximal in d ep end en t set is dominating. Moreo ver, the Mo on–Moser b ound tells u s they are few, and Tsukiya ma et al. tell us ho w to list them with p olynomial dela y: Lemma 3.5 (Mo on and Moser [15]; Ts u kiy ama et al. [16]) . Any n -vertex gr aph has at most O ∗ (1 . 442 3 n ) maximal indep endent sets, and they c an b e liste d within that b ound. Theorem 3.6. F or an n -vertex g r aph G with maximum de gr e e ∆ we c an de cide in time O ∗ (2 ∆+1 − 1) n/ (∆+1) whether G admits a c overing with k indep endent sets. Pr o of. It is easy to see that G can b e co v ered with k ind ep enden t sets if and only if it can b e co vered with k maximal indep end en t sets, so we will use Algorithm C on max I . Step C1 is completed in time O ∗ (1 . 442 3 n ), and the rest of th e algorithm considers on ly the p oin ts in ↑ max I , which all b elo n g to D . Again, Theorem 3.2 b ounds th e total r unnin g time. 3.4. Chromatic Number via bipartite subgraphs W e can do somewhat b ette r b y considering the family B of verte x sets of induced bip artite subgraphs, th at is, the family of sets B ⊆ V for whic h the in d uced su b graph G [ B ] is bipartite. As b efore, the literature provides us with a nontrivial listing algorithm: Lemma 3.7 (Bysko v and Eppstein [7]) . Any n -vertex gr aph has at most O ∗ (1 . 772 4 n ) maximal induc e d bip artite sub gr aphs, and they c an b e liste d within that b ound. The family max B is more th an jus t d ominating, which allo ws u s to use Lemm a 3.1 in a stronger w a y . TRIMMED M OEBIUS INVERSION AND GRAPHS OF BOUNDED DEGREE 95 Theorem 3.8. F or an n -vertex g r aph of maximum de gr e e ∆ it holds that |↑ max B | ≤ (2 ∆+1 − ∆ − 1) n/ (∆+1) . Pr o of. Let G = ( V , E ) b e a graph w ith | V | = n and maxim um degree ∆. Let F = ↑ max B . Let A v b e as in (3.1). With the ob jectiv e of applying Lemma 3.1, we need to b ou n d the n umb er of sets in F v = { F ∩ A v : F ∈ F } . Assume first th at G is ∆-r egular. Let A v = { v , u 1 , . . . , u ∆ } . W e w ill r ule out ∆ + 1 candidates for F ∩ A v , n amely ∅ , { u 1 } , . . . , { u ∆ } / ∈ F v . (3.3) This then shows that | F v | ≤ 2 ∆+1 − ∆ − 1 and th us the b ound follo ws from Lemma 3.1. T o see th at (3.3) holds, observe that F ∈ F conta ins a B ⊆ F suc h that the induced subgraph G [ B ] is m aximal bipartite. T o r eac h a con tradiction, assume that there exists a v ∈ V with F ∩ A v ⊆ { u ℓ } . Since B ⊆ F , we hav e B ∩ A v ⊆ { u ℓ } , imp lying th at v d o es n ot b elong to B , and th at at most one of its n eigh b ours do es. Con s equen tly , G [ B ∪ { v } ] is also bipartite, and v b elongs to a partite set op p osite to any of its neigh b ours. This con tradicts the fact that G [ B ] is maximal bipartite. T o establish the non-r egular case, w e can pro ceed as in the pr o of of Th eorem 3.2, adding eac h u ∈ V with d ( u ) < ∆ to some ∆ − d ( u ) of th e sets A v not already including u . Note that by adding y new v ertices to A v originally con taining x v ertices, we get |{ F ∩ A v : F ∈ F }| ≤ 2 y (2 x − x − 1). Next, since 2 y (2 x − x − 1) ≤ 2 y + x − ( y + x ) − 1 for all non-negativ e inte gers y , x and log (2 x − x − 1) is a conca ve fu nction, the b ound follo ws as b efore via Jensen’s inequalit y . Theorem 3.9. F or an n -vertex g r aph G with maximum de gr e e ∆ we c an de cide in time O (2 ∆+1 − ∆ − 1) n/ (∆+1) whether G admits a c overing with k indep endent sets. Pr o of. When k is even, it is easy to see th at G can b e co v ered b y k indep enden t sets if and only if it can b e co vered b y k ′ = k / 2 maximal bipartite s ets, so we will use Algorithm C on max B and in vestig ate w hether c ( V ) 6 = 0. When k is o dd , we again use Algorithm C with k ′ = ( k − 1) / 2 maximal bipartite sets, but this time w e c hec k wh ether an X is output suc h that b oth c ( X ) 6 = 0 and V \ X is indep en den t in G . In b oth cases the runn ing time b ound f ollo w s from Theorem 3.8. 4. Concluding R emarks Since the presen ted impro vemen ts on runn in g time b oun ds are m o dest, one can ask whether this is b ecause of weak b ounds or b ecause of inh eren t limitations of the tec h nique. W e observ e that the run n ing time b ound s in Theorems 3.4, 3.6, and 3.9 are met b y a disjoint union of complete graphs of order ∆ + 1. Thus, either fur ther trimming or sp litting into connected comp onen ts is required f or impr ov ed algorithms in this con text. W e chose to demonstrate the tec h nique for Chr omatic and Domatic Number sin ce these are we ll-known and w ell-studied. T o briefly demonstr ate some fur ther application p oten tial, more artificial pr oblem v arian ts suc h as determining if a ∆-r egular graph has domatic n umb er at least ∆ / 2, or if the square of a ∆-regular graph has c hr omatic num b er at most 96 A. BJ ¨ ORKLUND, T . HUSFELDT, P . KASKI, AN D M . KOI VISTO 3∆ / 2, admit stronger b oun ds. F or example, if G has d omatic num b er at least d , d ev en, then its vertice s can b e partitioned in to tw o sets, b oth of whic h con tain d/ 2 dominating sets. Th is suggests the follo wing m eet-in-the-middle s tr ategy . Run Algorithm D with F equal to all d ominating sets and k = d/ 2 , bu t m o dify Step D7 to insert X ∪ { j } only if | A v \ ( X ∪ { j } ) | ≥ d/ 2 holds for all vertices v . A t termination, w e c hec k whether the algorithm has output tw o sets X and Y such that X ∪ Y = V and d ( X ) , d ( Y ) > 0. (F or example, one can c hec k f or d uplicates in a table with en try { X, V \ X } f or eac h outp u t X with d ( X ) > 0.) This algo rith m v arian t considers only sets with man y forbidden intersectio ns with th e neigh b ourho o ds of v ertices, wh ic h translates into s tronger b ounds via Lemma 3.1. References [1] R. Beigel and D. Eppstein, 3 -c oloring in time O (1 . 3289 n ), J. Algorithms 54 (2005), 168–2 04. [2] A. Bj¨ orklund and T. H usfeldt, Exact algorithms for exact satisfiability and numb er of p erfe ct matchings , Algorithmica, to app ear. Prelim. versi on in Pro c. 33rd International Colloquiu m on Automata, Lan- guages and Programming, Lect. Notes in Comp. S cience, V ol. 4051, Sp ringer, Berlin, 2006, p p. 548–559 . [3] A. Bj¨ orklu n d, T. Husfeldt, P . Kaski, and M. Koivisto, F ourier me ets M¨ obius: fast subset c onvolution , Proc. 39th ACM S ymp osium on Theory of Computing, Association for Computing Mac hinery , New Y ork, NY , 2007, pp. 67–74. [4] A. Bj¨ orklund, T. Husfeldt, and M. Koivisto, Set p artitioning via inclusion–exclusion , SI AM J. Comput., to app ear. Prelim. vers ions in Pro c. 47th IEEE Sy mp osium on F ound ations of Computer S cience, IEEE Computer Society , Los Alamitos, CA, 2006, pp. 575–582 , 583–590. [5] R. L. Brooks, O n c olouring the no des of a network , Pro c. Cam bridge Philos. So c. 37 ( 1941), 194–1 97. [6] J. M. Bysko v , Enumer ating maxi m al indep endent sets with applic ations to gr aph c olouring , Op er. R es. Lett. 32 (2004), 547–556. [7] , Exact algorithms f or gr aph c olouring and exact satisfiability , Ph.D. Thesis, Univ. Aarhus, 2004. [8] F. R . K. Chung, P . F rankl, R. L . Graham, and J. B. S hearer, Some interse ction the or ems for or der e d sets and gr aphs , J. Com bin. Theory Ser. A 43 (1986), 23–37. [9] D. Eppstein, Smal l maximal indep endent sets and faster exact gr aph c oloring , J. Graph Algorithms Appl. 7 (2003), 131–140. [10] F. V . F omin, F. Grandoni, A. V. Pyatkin, and A . A. Stepanov, Bounding the numb er of minimal dominating sets: a me asur e and c onquer appr o ach , Proc. 16th Intern. S ymp osium on Algorithms and Computation, Lect. N otes in Comp. Science, V ol. 3827, Springer, Berlin, 2005, pp . 573–582. [11] F. V. F omin, S. Gasp ers, S. S aurabh, and A. A. Stepan ov, On two te chniques of c ombini ng br anching and tr e ewidth , Algorithmica, to app ear. Rep orts in In formatics, n o. 337, Department of Informatics, Universit y of Bergen, 2006. [12] J. K n eis, D. M¨ olle, S. R ic hter, and P . Rossmanith, Algorithms b ase d on the tr e ewidth of sp arse gr aphs , Revised Selected Papers from the 31st I ntern. W orksh op on Graph-Theoretic Concepts in Computer Science, Lect. Notes in Comp. S cience, V ol. 3787, Sp ringer, Berlin, 2005, pp. 385–396. [13] D . E. Knuth, The Art of C omputer Pr o gr amming, V ol. 2: Seminumeric al Algorithms , 3rd ed., A ddison– W esley , Reading, MA, 1997. [14] E. L. Lawler, A note on the c omplexity of the chr omatic numb er pr oblem , Inform. Pro cess. Lett. 5 (1976), 66–67. [15] J. W. Moon and L. Moser, On cliques i n gr aphs , Israel J. Math. 3 (1965), 23–28 . [16] S . Tsukiyama, M. Ide, H. Ariyoshi, and I. Sh irak a wa, A new algorithm for gener ating al l the maxim al indep endent sets , SIAM J. Comput. 6 (1977), 505–517. [17] F. Y ates, The design and analysis of factorial exp eriments , T echnical Communicatio n 35, Common- w ealth Bureau of Soils, Harp en den, U .K., 1937. This wor k is license d und er th e Crea tive Commons Attr ibution-NoDer ivs License. T o view a copy of this license, visit http: //creativecommons.org/licens es/by-nd/3.0/.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment