Secret Key Rate Analysis of RIS-Assisted THz MIMO CV-QKD Systems under Localized and Global Eavesdropping
A multiple-input multiple-output (MIMO) system operating at terahertz (THz) frequencies and consisting of a transmitter, Alice, that encodes secret keys using Gaussian-modulated coherent states, which are communicated to a legitimate receiver, Bob, u…
Authors: Sushil Kumar, Soumya P. Dash, George C. Alex
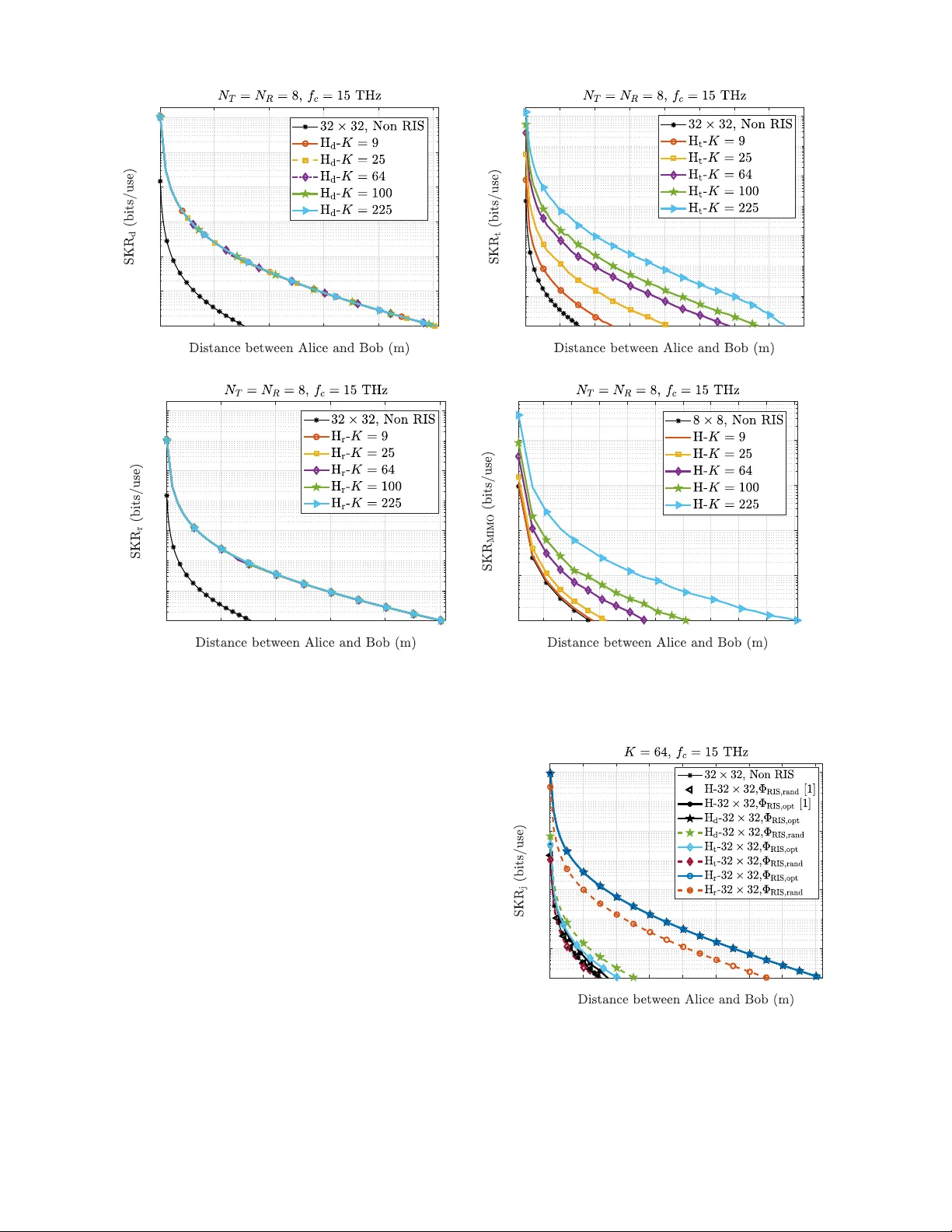
1 Secret K ey Rate Analysis of RIS-Assisted THz MIMO CV -QKD Systems under Localized and Global Ea vesdropping Sushil Kumar , Soumya P . Da sh, Senior Member , IEEE , and George C. Alexandropoulos , Senior Me mber , IEEE Abstract —A multiple-in p ut multiple-outp u t (MIMO) system operating at terahertz (THz) frequencies and consisting of a transmitter , Alice, that encodes secret keys using Gaussian- modulated coherent states, which are communicated to a le- gitimate recei ver , Bob, under the assistance of a reconfigurable intelligent surface (RIS) is considered in th is p aper . The com- posite wireless channel comprisin g th e direct Ali ce-to-Bob signal propagation path and the RIS-enabled reflected one is modeled as a passive lin ear Gaussian quantum channel, allowing fo r a unit ary dilation that preserv es the canonical commutation relations. The security of th e considered RIS-empowered MIMO system is analyzed under collective Gaussian entangling attacks, according to which an eav esdropper , Eve, is assumed to ha ve access to en vironmental modes associated with specific propaga- tion segments. W e also study , as a benchmark, the case wh ere Eve has a ccess to the p urification of the overall channel. Th e legitimate recei ver , B ob , is designed to deploy homo dyn e detection and re verse reconciliation for key extraction. Novel expressions fo r th e achiev able secret key rate (SKR) of the system are derived fo r both the consid ered eav esdropping scenarios. Furthermore, an optimization framework is developed to determine the op- timal RIS ph ase configuration matrix that maximizes th e SKR perfo rmance. The resulting o pt imization pr oblem is efficiently solved usi n g p article swarm optimization. Numerical results are presented to demonstrate th e system’ s performa n ce with respect to various free parameters. It is showcased t h at the considered RIS p lays a crucial role in enhancing th e SKR of t he system as well as in extendin g the secure communication r ange. This establishes RIS-assisted THz MIMO CV -QKD as a p romising solution fo r next generation secure wireless networks. Index T erms —Continuous variable quantum key distribution, multiple-in p ut multiple-output, quantu m communications, recon- figurable intelli gent surfaces, secret key rate. I . I N T RO D U C T I O N The advent of novel technolog ies f or beyond fifth- generation (B5G) and sixth- generatio n (6G) wireless com - munication systems is driven b y the nee d to achieve high data r a tes, ultra- low laten cy , and high energy and spe c tral efficiencies [2] , [3 ]. Th is has led to an increased interest in d e- veloping various p h ysical layer tech niques, namely extremely multiple-inp ut multip le-outpu t (MIMO) [4], [5 ], op e ration at teraher tz (THz) fre q uencies [6], [7], integrated sen sing and commu nications (I SA C) [8], [9], non-c o herent com m u- nications [10] –[13] , and reco nfigurab le intellig ent surfaces A part of this work has been accepted for presentat ion at the upcoming IEEE WCNC 2026 [1]. S. Kumar and S. P . Dash are with the School of E lectri cal and Computer Science s, Indian Institute of T echnology Bhubanesw ar , Ar gul, Khordha, 752050 India, (e-mails: { a24ec09010 , spdash } @iit bbs.ac.in). G. C. Alexandrop oulos is with the Department of Informatics and T elecom- municati ons, National and Ka podistrian Uni versity of At hens, Panepi stimiopo- lis Ilissia, 16122 Athens, G reece and also with the Department of Electri cal and Computer Engineering, Univ ersity of Illinoi s Chicago, IL 60601, USA (e-mail: alexa ndg@di.uoa.gr). (RIS) [1 4], [15] . Among the m , RISs have sho wn im mense potential to rev olutio nize wireless commun ications, leveraging vast arr ays of respon se-tunable m etamaterial elements that are electronically optimized in alm ost real time, manipulat- ing e le c tr omagn e tic wa ves propag a tion with in the physical wireless channel [16], [1 7]. An RIS can strategically direct the beam s toward design ated u sers, thereb y ensuring reliable commun ication with increased data rates, improved signal quality , extended coverage, and min imized inter ference [18]. Moreover , implemen ting RIS technolog y en ables robust com- munication links fo r systems do minated by non- line-of- sight (NLoS) signal p ropaga tion [1 9]. Th is h as led to the usag e of RIS to impr ove the perf ormanc e of MIMO, ISA C, an d in dex modulatio n systems, as well as satellite networks [20]– [26]. Another crucial aspect an d requirem ent for next g eneration commun ication systems is impr oving the security and p riv acy of transmitted data. Traditional high er-layer encry ption tech- niques based on the Riv est-Sham ir-Adleman (RSA) algorith m have b een p roven to be inefficient and easily decod a ble utilizing Shor’ s algorithm, o wing to the rapid technolog ical advancements in qu antum computing [27], [28]. Moreover, the development of quantum co mputers has resulted in the usage of a lg orithms for phy sical la y er encry ption, such as Diffie an d Hellman, to b e inefficient due to their capacity to yield solutions to computa tio nally hard d iscrete logar ithmic problem s in a sho rt time [29]. T o overcome these ch allenges and enh ance da ta priv acy , qu a n tum key distribution (QKD) , a tech nique leveraging the und erlying princip les of quantu m superpo sition and entan glement, has been pr oposed in th e literature to offer versatile secu re comm unication [ 30]–[ 32]. QKD en sures th e secur e tran smission of secret keys between two authen ticated users, namely Alice and Bob, ev en in the presence of a potential eavesdropper, Eve. Th e literature on QKD classifies th e av ailable te c h niques into two categories, i.e., discrete variable QKD ( D V -QKD) an d co ntinuou s variable QKD (CV -QKD ) [30] , [3 3]. The DV -QKD appr oach relies on sources and detecto rs specifically designed for single p hotons, and en crypts con fidential key infor mation by utilizing the po - larization o r p hase o f a single pho ton. The secure key prod uced by the D V -QKD appr oach is guaranteed by the no- cloning the- orem of quan tu m phy sics, p reventing the possibility o f ma king perfect replicas of non -orthog onal quan tum states without introdu c ing detectable n oise [34], [35 ] . In contrast, a secret key is en coded using the quadr atures of co n tinuous variable Gaussian quantu m states with the CV -QKD tech nique, and its security is ensured by Heisenberg’ s uncertain ty principle [2 7], [36]. Owing to higher hardware comp atibility with classical commun ication systems and th e ab ility to offer sup erior key rates and overall p erforma nce in noisy en viro nments, as well 2 as ease of imple m entation in higher frequen cy ranges, the CV - QKD approac h becom es a natural choice for wireless systems over the D V - QKD o ne [37 ], [38]. Most QKD- enhanced wir eless sy stems focus on ap plications that r equire po int-to-po int co mmunica tio ns, suc h a s satellite- to-earth, inter-satellite, inter-building, and free-spa ce maritime channels [39 ] –[44] , which are tradition ally achieved v ia fr ee- space op tica l (FSO) link s [45]. Howe ver, it has been studied that THz communica tio n is often preferred over FSO d ue to its better resilience to weathe r, NL oS capabilities, easier deployment (with less strict alignm e nt), and ability to hand le high data rates over sho rt d istances [46] . Th is has led to several studies for terrestrial and in te r-satellite wireless sy stem s ap- pearing in th e literature considering the usage of the THz band for secur e co mmunicatio ns using the CV -QKD technique [4 7]– [49]. Howe ver, these studies have r eported achieving lo w secret key rates (SKRs) and short transm ission distances for secret ke ys, due to several factor s th at degrade the channel within the consid e red frequ ency spec trum. Th ese limitatio ns have been sho wn to b e ov erco me to some extent by th e integration of MIMO with CV -QKD [5 0 ], [5 1]. MI MO FSO with D V -QKD h as been studied in [52]. On another fr ont, RISs have also been lately integrated with QKD. The authors in [5 3] introdu c ed th e idea of red uction of reflection loss with the use of RIS, and the authors in [5 4] studied cha nnel estimation and RIS to aid QKD-b ased quan tum com munication in a THz MIMO system. Howe ver , ther e has be en limited resear c h on using RISs to improve the perfo r mance o f CV - QKD systems operating in the THz frequency band [5 4]. Motiv ated by this research gap, in this p aper, we explore a MIMO CV -QKD wireless co m municatio n system assisted by an RIS. In this system, the RIS facilitates th e transmission of secr et ke y s between the two p a rties, Alice and Bob, in addition to the direct commu nication channel th ey alr e ady have. W e also take into account a possible ea vesdropp e r , Eve, whose ab ilities are limited by their physical access to the p ropag a tion environment. Unlike E ve, which is assumed to h av e co mplete pu rification o f the entire chann el between Alice and Bob , we examine realistic scenarios of localize d eav esdr opping , in which Eve can only access a p ortion of the environmental mod es associated with chan nel loss. Such constraints naturally arise in wireless systems du e to geometric constraints, blockages, and deployme nt limitations, especially in RIS-assisted THz links [55]. This work extends our p reliminary find ings p resented in [1], where we have examined a worst-ca se global e av esdr o pping model in which Eve targets the overall effecti ve cha nnel. This paper introduce s a comprehen si ve fr amew o r k en compassing both global and localize d eavesdropping scenarios. Specifi- cally , we model segment-wise c h annel loss thro ugh a global unitary dilation and analyze E ve’ s info rmation g ain when they have access to only select environmental modes. The m ajor contributions of this paper are summarized as follows: • W e p ropose an RIS-assisted THz MIMO CV -QKD f rame- work in whic h Alice transmits a single quan tu m signal that p ropaga tes thro ugh a coher ent super p osition of the direct a nd RIS-assisted channel p aths, wh ich ar e modeled as a global pa ssi ve Gaussian channe l that preserves canonical com m utation relations. • W e dev elo p an eavesdropping model based on un itary channel dilation, in which Eve can perfor m collective Gaussian entangleme nt attacks by accessing selected e n- vironm e ntal mo d es associated with chann e l loss. • W e in troduce an d an alyze localize d eavesdroppin g sce- narios, in wh ich Eve is restricted to access a sing le pr op- agation segment (Alice–Bob, Alice–RIS, or RIS–Bob), and derive closed- f orm expre ssions f or the corr espondin g SKR u nder reverse reconciliatio n (RR) an d hom odyne detection. • As a b enchmar k, we also consider a global eavesdrop- ping scen a rio in which Eve ho ld s full control over th e purification of the effecti ve end-to-end MIMO channel between Alice an d Bob. T o h andle the complexity o f the MIMO channe l structu r e, we stud ied an SVD-b ased parallel channel. A detailed d eriv ation and ana lysis o f this framework have b e en established in our p rior work [1] . • W e d erive analytical expr essions for both the classical mutual information between Alice and Bob as well as the Holev o info r mation b etween Bob and E ve, hig hlighting how Eve’ s in formation gain d epends o n their physical access to environmen tal mod es. • An optimization framew ork based o n a particle swarm optimization (PSO) algorithm for maximizin g the ach iev- able SKR perform ance in the RIS ph ase co nfiguratio n is presented. Our extensive numerica l invest ig ations corr oborate the anal- ysis p resented in the paper, showcasing the e ffects of the RIS size on the SKR p erforma nce as well as the tran sm ission distance between Alice and Bob. The rest of the p aper is organized as follows. T h e sys- tem mod el of th e RIS-assisted MIMO CV -QKD system, the transmission of secr et keys b etween Alice an d Bob, an d the considered eavesdropping mod e ls are detailed in Section II. The SKR a n alysis under both lo calized and g lobal eavesdrop- ping mode ls, along with th e PSO algorithm, is presen ted in Section III . Finally , Section IV inclu des our numerical results, followed b y conclud ing re marks in Sec tio n V . Notation: Boldface letters such as A ∈ C M × N and a ∈ C M × 1 represent matrices and vectors, respecti vely . T he A † symbol stands for th e conjug ate tra n spose of A , the A T symbol stand s for th e transpose, th e A − 1 ∗ symbol r e presents Moore– Pen rose pseudo- in verse, an d A ⊗ B indicates the tensor produ ct betwe e n A and B . Th e notation s 1 M × N and 0 M × N represent a matrix consisting of all one s an d all zeros, r e spec- ti vely , and , √ − 1 is the imag in ary unit. I M represents a M × M id entity m atrix, and diag ( a ) r eturns a M × M diagonal matrix with the elements of a on its p r incipal diagonal. a ∗ represents the conjugate of a . Notatio n h X · Y i in dicates the qua ntum correlation b etween X and Y , while N ( µ , σ 2 ) represents the real m ultiv ariate Gaussian distribution, where µ is the mean vector an d σ 2 is the covariance matrix. [ , ] is the canon ical bo sonic commutatio n, | · | denotes the magn itude operator, and the o perator eig ( · ) compu tes the eigenv alues of a matrix. Furthermo re, ˆ Q d e n otes th e operato r (such a s annihilation an d creation) ac ting on the signal mode Q . 3 Fig. 1 : The con sidered RIS-assisted MI MO CV - QKD wireless co mmunica tio n system model und er eav esdr opping attacks. I I . S Y S T E M A N D C H A N N E L M O D E L S W e consider an RIS-assisted MIMO CV -QKD system as shown in Fig . 1, where the tr ansmitter, Alice, and the r eceiv er, Bob, are e quipped with N T and N R antennas, r espectively . The RIS co nsists of K passive re flec tin g eleme nts co nfigured to adjust the phases of the incident and tran smitted electro- magnetic signals [1 5]. Th is commun ication is also aided b y the d irect LoS p a th between the transceiver pair . A. Channel Model The effectiv e MI MO chann el between Alice and Bob, denoted b y H ∈ C N R × N T , can b e mathem atically expressed as follows [16]: H , H d + H r ΦH t , (1) where Φ , dia g e φ 1 , ..., e φ K and φ k is th e ph ase shift introdu c ed by th e k -th element of the RIS. Fu rthermo re, H d ∈ C N R × N T , H t ∈ C K × N T , and H r ∈ C N R × K , are the dire ct LoS chann el matrix between the legitimate transceiver pair , the channel m atrix between Alice an d RIS, and the chan nel m atrix between RIS a n d Bob, respectively , whic h ar e expressed f or the TH z system as follows: H d , L d X ℓ =1 p δ d,ℓ e 2 π f c τ d,ℓ h N R θ R X ℓ h † N T θ T X ℓ , H t , L t X m =1 p δ g,m e 2 π f c τ g,m h RIS ϕ, θ RIS m h † N T θ T X m , H r , L r X n =1 p δ f ,n e 2 π f c τ f,n h N R θ R X n h † RIS ϕ, θ RIS n . (2) In these expressions, L d , L t , and L r denote the number of signal p ropaga tio n p aths in the wire le ss chann els H d , H t , and H r , respectively . Further, f c is the carrier f requen cy , and τ d , τ t , τ r and δ d , δ t , δ r are the pro pagation de lays and path losses corr espondin g to H d , H t , and H r , respectively . Moreover , θ T X ℓ , θ T X m , and θ RIS n are the angles of dep arture (AoD) and θ R X ℓ , θ RIS m , and θ R X n are th e ang les of arriv al (Ao A) of the ℓ -th, m -th , an d n -th multipath fro m the transmitter’ s and the receiver’ s unifo rm line a r arrays (ULAs), respectiv ely . The anten n a elements in b oth ULAs are unifor mly placed in a single d imension such that the in ter-element spacin g is maintained at d a . This resu lts in the ar ray resp o nse vector in (2), i.e., h N T ( or h N R ) , are given as f ollows: h N ( θ ) , 1 √ N h 1 , e 2 π λ c d a sin θ , · · · , e 2 π λ c d a ( N − 1) sin θ i T , (3) where N ∈ { N T , N R } and λ c , c/f c , with c being the speed of electromag n etic sign als (i.e., light). Furthermore, h RIS ∈ C K × 1 in (2) is the resp o nse vector of the passiv e ULA of th e RIS [56 ], [57] a n d is g iv en as h RIS ϕ, θ RIS i = 1 √ K " e 2 π λ c ϑ ϕ,θ RIS i X + ϑ ϕ,θ RIS i Y , · · · · · · , e 2 π λ c ( K X − 1) ϑ ϕ,θ RIS i X +( K Y − 1) ϑ ϕ,θ RIS i Y # , (4) where, for i ∈ { m, n } , it holds: ϑ ϕ,θ RIS i X = d X cos ( ϕ ) sin θ RIS i , ϑ ϕ,θ RIS i Y = d Y sin ( ϕ ) sin θ RIS i . (5) Here, the elements o f the RIS are con sidered to b e ar ranged along a 2-d im ensional stru c ture [19], [58 ] with K X and K Y reflecting elements along the ho rizontal and the vertical axes, respectively , implyin g th at K X K Y = K , with the separ ation between the elements in the corresp o nding axes being deno ted by d X and d Y . Fur thermor e , th e path losses in (2) a re expressed as follows: δ j,i = λ c 4 π d j,i 2 G T X G R X 10 − 0 . 1 ρd j,i , j ∈ { d, g , f } , i = 1 ς ξ i λ c 4 π d j,i 2 G T X G R X 10 − 0 . 1 ρd j,i , i ∈ { ℓ, m, n 6 = 1 } , (6) where d j,i is the sma llest path leng th, ξ i is the Fr e snel reflection coefficient o f the i -th multip ath compo nent, ς is the Rayleigh ro ughn e ss factor, and ρ (in dB/km) is the atmosph eric absorption loss. Moreover , Alice’ s an d Bob’ s ULAs gain s ar e G T X = N T G a and G R X = N R G a , respectively , where G a is the g ain of ea c h comp onent of the tran smitter and receiver 4 antennas, and G T X (or G R X ) = K when the d a ta symbols are transmitted fr om (or to ) the RIS, respectively . B. Secr et K ey Gene ration, T ransmission, and Reception In the con sidered MI MO wireless c ommun ication system, Alice aims to establish a secure q uantum key with Bob . T o this end, Alice em ploys a Gaussian-mo dulated CV - QKD scheme, generating two indepen dent zero-mean Gaussian ran dom vec- tors X Alice , P Alice ∼ N ( 0 N T , V s I N T ) corr espondin g to the position and momen tu m qu adratures, respectively [50], [59 ]. Using these quadr a tures, Alice generates a set of coheren t states, a t = X Alice ,t + P Alice ,t , for t = 1 , . . . , N T , which are transmitted to Bob throug h the wireless prop agation medium . After prop agation throu gh the wireless medium , the re c eiv ed quantum sign a l at Bob is m o deled as the coh erent combin ation of the fields arriving throu gh the direct a n d RIS-assisted paths. This opera tio n is repr esented by a beam splitter (BS b ) with transmissivity η b , yielding the received q uantum signal expression: ˆ b , √ η b ˆ b d + p 1 − η b ˆ b r , (7) where ˆ b d and ˆ b r represent the signals arriving from the direct and RIS-assisted channels, respectively . The sign a l to the direct path and the RIS- a ssisted p ath are expre ssed as follows: ˆ b d , H d ˆ a d + N d ˆ e d , (8a) ˆ b r , ( H r ΦH t ) ˆ a r + H r Φ N t ˆ e t + N r ˆ e r , (8b) respectively , where ˆ e d , ˆ e t , and ˆ e r denote mutually independ ent bosonic en vir onmenta l mod es associated with losses along the d irect path, the Alice–RIS p ath, and the RIS–Bob path, respectively , which fo llow h ˆ e i , ˆ e † j i = δ i,j I N j , ∀ j ∈ { d, t, r } , and N j ∈ { min ( N T , N R ) , min ( N T , K ) , min ( K, N R ) } . T o generate in depend ent propagation modes for the direct an d RIS-enabled channel paths, Alice first splits the transmitted signal u sing a beam splitter (BS a ) with transmissivity η a as follows: ˆ a d , √ η a ˆ a + p 1 − η a ˆ v 0 , (9a) ˆ a r , − p 1 − η a ˆ a + √ η a ˆ v 0 , (9b) where ˆ v 0 is a vacuum mode vecto r a n d ˆ a is the Alice transmitted mo de vector . These oper ators satisfy the ca nonical bosonic comm utation relation s: ˆ a , ˆ a † = I N T , h ˆ v 0 , ˆ v † 0 i = I N T , h ˆ a , ˆ v † 0 i = 0 N T × N T . (10) Furthermo re, each p ropaga tio n segment is mo deled as a physically realizab le Gaussian chann el ar ising f rom a unitary interaction between the signal and the environment, wh ich is giv en as H j H † j + N j N † j = I N j , ∀ j ∈ { d, t, r } . Here, N j denotes the environmental cou p ling matrices which cha r acter- ize the inter action b etween the signal and the corre sp onding en vir onmenta l mo de ˆ e j , ∀ j ∈ { d, t, r } . Sin ce the signal an d en vir onmenta l mo d es originate fr om a single global unitary transform ation, the recei ved operator ˆ b at Bob satisfies the canonical bo so nic comm utation relations: h ˆ b , ˆ b † i = I N R . (11) C. E avesdr opp in g Mod els As dep icted in Fig. 1, Eve acts as an external adver- sary that is assumed to have u nlimited com putationa l and quantum processing ca p abilities, while rem aining su b ject to the fun damental laws of quan tum mechanics. Bob’ s rece iver noise an d internal imperfection s are assumed to be tr usted and inaccessible to Eve. On th e other ha nd, Eve is a ssumed to per f orm collective Gaussian attack s against Gaussian- modulated CV -QKD pr o tocols, which can be eq uiv alently modeled as an entangling-clo ner attack. In this model, Eve prepare s two-mode squeeze d vacuum (TMSV) states, also known as Einstein-Pod olsky-Rosen (EPR) p airs, consisting of an injected mode and a retained idler mo d e [2 7]. The covariance matrix o f a TMSV state is g iv en by the following expression [47]: Σ EPR , V e I 2 p V 2 e − 1 Z p V 2 e − 1 Z V e I 2 , (12) where Z is the P au li-z ma trix given as diag (1 , − 1) and V e denotes the variance of Eve’ s EPR mode s. In an entan gling-clo ner attack, Eve injects o ne mode of a TMSV state into the environmental input of a lossy channe l segment, wh ile retaining the corr e sponding idler mode in their quantum m e mory . Consequen tly , th e co r respond ing environ- mental output mode c o nstitutes E ve’ s o bservation of the leaked signal. Based on E ve’ s con trol and observation over different segments of the system mo del, we consider hereinaf ter the following two eavesdropping scenario s. 1) Localized Eavesdr opp ing Based on Physical Access: In the lo calized eavesdropping scenario s, Eve is assume d to be p hysically present along only one propag a tion segment of the com munication lin k. As a result, th ey can acce ss an d manipulate only the environmental mod es a ssociated with loss on that specific segment, while all remainin g environmen tal modes and Bob’ s rece i ver noise are co nsidered trusted and inaccessible to Eve. T h us, we con sider the fo llowing localized eav esdr opping cases: • Eavesdroppin g on t he Alice-Bob direct path ( H d ): Eve accesses th e environmental mode ˆ e d associated with loss on the direct Alice-Bob link, while the losses via the RIS-assisted pro pagation remain inacc e ssible. • Eavesdroppin g on the Alice-RIS pat h ( H t ): E ve ac- cesses th e environmental mo de ˆ e t correspo n ding to th e loss between Alice and th e RIS. • Eavesdroppin g on the RIS-Bob pa th ( H r ): Eve ac- cesses the environmental mo d e ˆ e r associated w ith loss on the RIS- Bob segmen t. In all the above cases, Eve’ s interac tion with the chann el is restricted to a single lossy p ropaga tio n segment. T he rema in ing loss mech anisms are mo deled as tru sted vacuum noise. 2) Global Ea vesdr opping via Effective Channel Purifica - tion: While localized eavesdropping rep resents re a listic phys- ical limitations o n Eve’ s access, it is essential in the secur ity analysis o f CV -QKD to adopt a mor e rigor o us appr oach. In this globa l eavesdropping scenario, Eve has fu ll contro l over purify in g the effecti ve en d-to-en d ch a nnel between Alice and Bob . Since any lossy Gaussian ch annel can be modeled a s a 5 beamsplitter interaction with a vacuum-state e n viro nment, the overall chan nel comprising th e direct p ath H d and the RIS- assisted p ath (i.e., H t followed by H r ) can be eq u iv alently described by a single effecti ve transmissivity β . Eve is th en assumed to co ntrol the environmental inp ut co rrespon ding to this effectiv e chan nel, injecting o ne mod e o f a T MSV state and retain ing the id ler in their quan tum m emory . I I I . S E C R E T K E Y R AT E A N A LY S I S The SKR in QKD quantifies the n umber of information - theoretically secur e k ey b its that Alice a n d Bob c a n extract per channe l use, a ccounting for the maxim um in formatio n an eav esdr opper can o b tain un d er a g i ven attack mo del. In this work, th e physical channel mo del remains fixed as describe d in Section II , wh ile different e av esdr o pping scenarios are distinguished by Eve’ s access to the en v ironmen tal mo d es associated with channel loss, as outline d in Section I II. W e consid e r that Alice and Bob hav e p erfect ch a nnel state informa tio n (CSI) [1] , [ 5 4]. Le t H = UDV † be the singular value d ecompo sition (SVD) of the overall ch annel H . Thus, with the intention of maximizing the data rate, Alice employs the precode r matrix a s V bef ore passing to the BS a , and Bob em ploys its combiner as U † to on e of outpu t of the BS b . Following the tr ansmission of keys from Alice and the interaction with en v ironmen tal modes, Bob receives the signal and performs measure m ents to d ecrypt the secret keys. In this con text, Bob can perform two ty pes o f measurem ents, as follows: 1) h omody ne, where he measu res one of the two quadra tu res ran d omly , an d 2) h eterodyn e, where h e measures both q uadratur es simultaneou sly [5 9], [6 0]. Previous studies indicate that both ho modyn e and hetero dyne measuremen ts yield similar results due to incre a sed detector noise in het- erodyn e measur ements [54]. Th e refore, we conside r tha t Bob perfor ms homody ne measur ements. Consequ e ntly , the outp ut vector at Bob is given as b = U † √ η a η b H d − p (1 − η a ) (1 − η b ) H r Φ H t V a + U † p (1 − η a ) η b H d + p η a (1 − η b ) H r Φ H t v 0 + √ η b U † N d e d + p 1 − η b U † H r Φ N t e t + p 1 − η b U † N r e r + U † n b . (13) Follo wing the ho modyn e measure m ent, a reconc iliatio n technique is emp loyed by Bob to fix error s, which are typically of two types, namely , 1) direct re c o nciliation ( D R) and 2) RR [50], [61] . RR works better th an DR b ecause the RR p rotoco l can achieve positive SKR fo r any values of transmittance between 0 and 1 , w h ile DR need s m ore than 50 % of the transmittance value to a chieve a positiv e SKR. Owing to this reason, we consider Bob to emp loy th e RR p rotocol. A. Localized Eavesd r opping Based on Physical Acce ss T ak ing into acco unt the homo d yne me a surement and RR at Bob’ s end , as well as Eve’ s eavesdropping mo dels describ e d in Sectio n III.A, the secret key rate is given as SKR j = I ( A ; B ) − χ j ( B ; E j ) , j ∈ { d, t, r } , ( 14) where I ( A ; B ) denotes the c la ssical m utual inf o rmation be- tween Alice and Bob, and χ j ( B ; E j ) represents the Ho lev o (quantu m) informa tio n of Bob’ s and Eve’ s quan tum states from the j - th link. T he achievable mutual inf ormation between Alice and Bob is given as I ( A ; B ) = H ( B ) − H ( B | A ) , (15) where H ( B ) is the Shannon entr opy , expressed as H ( B ) = − Z C N R f ( b ) log 2 ( f ( b )) , (16) and H ( B | A ) is the cond itional Shan non en tropy computed as H ( B | A ) = − Z C N R f b a log 2 f b a . (17) Here, f ( b ) an d f ( b | a ) represent the probab ility density func- tions ( p.d.f. s) of the vector b and the conditio nal p.d .f. of b giv en a , re spectiv ely , which can b e computed from (13). It is importan t to note that calculating th ese p.d.f.s requires the correspo n ding c ovariance matrices Σ b and Σ b | a , which ar e obtained as Σ b = V a U † √ η a η b H d − p (1 − η a ) (1 − η b ) H r Φ H t × √ η a η b H d − p (1 − η a ) (1 − η b ) H r Φ H t † U + V v 0 p (1 − η a ) η b H d + p η a (1 − η b ) H r Φ H t × p (1 − η a ) η b H d + p η a (1 − η b ) H r Φ H t † + V e d η b U † N d N † d U + V e r (1 − η b ) U † N r N † r U + V e t (1 − η b ) U † H r Φ N t N † t Φ † H † r U + σ 2 b I N , (18) and Σ b | a = V 0 U † √ η a η b H d − p (1 − η a ) (1 − η b ) H r Φ H t × √ η a η b H d − p (1 − η a ) (1 − η b ) H r Φ H t † U + V v 0 p (1 − η a ) η b H d + p η a (1 − η b ) H r Φ H t × p (1 − η a ) η b H d + p η a (1 − η b ) H r Φ H t † + V e d η b U † N d N † d U + V e t (1 − η b ) U † N t N † t U + V e r (1 − η b ) U † N r N † r U + σ 2 b I N , (19) where N = min { N T , N R , K } , V a = ( V s + V 0 ) , V s is the variance o f Alice sign al state and V 0 represents th e variance of the prepara tio n vacuum state, V v 0 denotes the variance of the vacuum s tate v 0 at BS a , and V e j is the variance of the environmenta l mode associated with segment j . Using (15)-( 19) followed by algebraic simplifications, the mutu al informa tio n in (14) is obtained as I ( A ; B ) = 1 2 log 2 Σ b Σ b | a . (20) On anoth er front, f o r a gi ven eavesdropping scenario on segment j ∈ { d, t, r } , Eve is assumed to acce ss o nly the en- vironm e ntal m o de associated with that segment. Spe c ifically , Eve pre p ares the en vir onmenta l inp u t mode ˆ e in j of a TM SV 6 Fig. 2: A dep ic tio n of fou r beam-splitter mod els representin g Eve’ s attack mod el f or the considere d MIMO channel. state with variance V e j , while retainin g the o ther mo des ˆ e qm ,j in their quantum m emory . All remainin g environmental mo des are assumed to be in the vacuum state. The en viron mental output modes available to Eve by m o deling a lossy chan nel with the BSs as depicted in Fig. 2, are given as e out ,j = − √ η a S d V † d V a + p (1 − η a ) S d V † d v 0 + D d e in d , j = d, − p (1 − η a ) S t V † t V a + √ η a S t V † t v 0 + D t e in t , j = t, − p (1 − η a ) S r V † r Φ H t V a + √ η a S r V † r Φ H t v 0 − S r V † r Φ U t S t e in t + D r e in r , j = r , (21) where matr ix D j and S j are given as D j = diag p β j, 1 , . . . , p β j,r H 0 r H × ( N j − r H ) 0 ( N j − r H ) × r H 0 ( N j − r H ) × ( N j − r H ) , (22a) and S j = diag p 1 − β j, 1 , . . . , p 1 − β j,r H , 1 , . . . , 1 | {z } ( N j − r H ) times , (22b) where p β j, 1 , ..., p β j,r H are the r H non-ze r o sing ular values of the j -th channel matrix. Consequen tly the environmental coupling matrices N j for the for the co rrespond ing ch annel are given as N j = U j S j , j ∈ { d, t, r } . (23) The Holev o information between Bob and Eve f o r the localized eavesdropping scenario on segment j is given by χ j ( B ; E j ) = S ( E j ) − S ( E j | B ) , (24) where S ( E j ) and S ( E j | B ) represent the von Neumann (qu an- tum) en tropy of Eve’ s mo des and the condition al von Neum ann entropy o f Eve’ s mod es given Bob’ s received mo des. T hese are f o und b y ca lcu lating the sym plectic eig en values { λ E j } N i =1 and { λ E j | B } N i =1 of their corresponding co rrelation matrices, Σ E j and Σ E j | B , re sp ectiv ely . The von Neuman n entropy is computed as S ( E j ) ( or) S ( E j | B ) = N j X i =1 h o ( λ j ) , (25) where λ j s ≥ 1 a r e the symplectic eigen values of th e cor rela- tion matrice s, and the function h o ( · ) is giv en as h o ( λ ) = λ + 1 2 log 2 λ + 1 2 − λ − 1 2 log 2 λ − 1 2 . (26) Moreover , Eve’ s co rrelation matr ix f o r j ∈ { d, t, r } , d enoted as Σ E j , is gen erated fr om tw o compon ents of the rec e ived vector at Eve’ s end. For a given eavesdropping s cen ario j , Eve’ s accessible qua n tum system c o nsists of the environmental output mode e out j and the retained idler mode e qm j . The correspo n ding covariance m a trix is g iv en as Σ E j = " Σ e out j Σ e oq j Σ † e oq j Σ e qm j # , j ∈ { d, t, r } , (27) where Σ e qm j = V e j I N j , Σ e oq j = q V 2 e j − 1 D j , j ∈ { d, t, r } , and Σ e out j = η a V a S d S † d + (1 − η a ) V v 0 S d S † d + V e d D d D † d , j = d, (1 − η a ) V a S t S † t + η a V v 0 S t S † t + V e t D t D † t , j = t, ((1 − η a ) V a + η a V v 0 ) S r V † r Φ H t S r V † r Φ H t † + V e t S r V † r Φ U t S t S r V † r Φ U t S t † + V e r D r D † r , j = r . (28) Furthermo re, Eve’ s conditional von Neumann entro py S ( E j | B ) is obtaine d f r om the c orrelation matrix generated with the b , e out j , an d e qm j is given as Σ E j | B = Σ E j Σ E j B Σ † E j B Σ b , j ∈ { d, t, r } . (29) This lead s to the condition al covariance matrix of Eve’ s m o des that a r e depen dent on the o u tcomes o f Bob’ s ho modyn e measuremen ts, wh ich is r epresented as Σ E j | B = Σ E j − Σ E j B (Π ( Σ b ⊗ I 2 ) Π) − 1 ∗ Σ † E j B , (30) where Π = I N j ⊗ 1 0 0 0 , an d Σ b and Σ E j are g iv en in (18) an d (27 ) , respectively . Furtherm o re, Σ E j B is th e quantu m correlation o f Eve’ s received mode e out j and Eve’ s sto r ed mod e in quantu m memor y e qm j with Bob’ s o utput mo des b is given as Σ E j B = " Σ e o j b Σ e q j b # , j ∈ { d, t, r } , (31) where Σ e o j b is given in ( 32) on the top o f the next p age, and Σ e q j b = √ η b p V 2 e d − 1 U † U d S d † , j = d, p (1 − η b ) p V 2 e t − 1 U † H r Φ U t S t † , j = t, p (1 − η b ) p V 2 e r − 1 U † U r S r † , j = r . (33) Using ( 20) an d ( 25), th e SKR for RIS-assisted MIMO CV - QKD u nder the consid ered Eavesdropping m odel is g iven in (34) on the top of the next p age. 7 Σ e o j b = − √ η b ( η a V a + (1 − η a ) V v 0 ) S d V † d H † d U + √ η b V e d D d S † d U † d U − p η a (1 − η a ) (1 − η b ) ( V a − V v 0 ) S d V † d ( H r Φ H t ) † U , j = d, p η a η b (1 − η a ) ( V v 0 − V a ) S t V † t H † d U + p (1 − η b ) V e t D t S † t U † t Φ † H † r U + p (1 − η b ) ((1 − η a ) V a + η a V v 0 ) S t V † t ( H r Φ H t ) † U , j = t, p η a η b (1 − η a ) ( V v 0 − V a ) S r V † r Φ H t H † d U − p (1 − η b ) V e t S r V † r Φ U t S t S † t U † t Φ † H † r U + p (1 − η b ) ((1 − η a ) V a + η a V v 0 ) S r V † r Φ H t ( H r Φ H t ) † U + p (1 − η b ) V e r D r S † r U † r U , j = r (32) SKR j = 1 2 log 2 I N + V s U † √ η a η b H d − p (1 − η a ) (1 − η b ) H r Φ H t √ η a η b H d − p (1 − η a ) (1 − η b ) H r Φ H t † U × Σ b | a − 1 − N j X i =1 h o λ E j ,i − N j X i =1 h o λ E j | B ,i , j ∈ { d, t, r } (34) B. Global Eav e sdr opping via Effective Chann el Purifica tio n In add itio n to the lo calized eavesdropping scen arios con sid- ered in the p revious subsections, we now examine a ben chmark case in which Eve is assumed to hav e ac c e ss to th e purificatio n of the entire effectiv e chan nel between Alice and Bob. This model correspond s to a collec tive Gaussian attack on the overall chan nel. In this setting, Eve is assumed to h av e full knowledge of the overall ch annel ma tr ix H , includin g p erfect CSI. By employing the SVD an d following standard CV -QKD an alysis, Alice ap plies th e pr ecoder V and Bob applies the comb iner U † , thereby transformin g the system into r H equiv alen t SI SO channels. Consequently , the input-o utput relations f or th e i -th parallel chan nel are g iv en by b i = p β i ψ i + p 1 − β i e in i + n b i , (35) and e o i = − p 1 − β i ψ i + p β i e in i , (36) where √ β i ∀ i = 1 , . . . r H are the singular values of H , with r H = rank( H ) . Furtherm ore, e in ,i is one mode o f Eve’ s TMSV state with variance V e , e o,i is th e corresp o nding e nvi- ronmen tal output mode accessible to Eve, an d n b ,i represents trusted Gaussian noise at Bob . Consequently , the expr ession for the SKR und er the scenario where Eve employs a co llectiv e Gau ssian entanglem e n t attack on the overall ch annel, and c onsidering RR, is given as SKR i = I ( A i ; B i ) − χ ( B i ; E i ) , (37) where I ( A i ; B i ) is given by I ( A i ; B i ) = 1 2 log 2 1 + β i V s β i V 0 + (1 − β i ) V e + σ 2 b , (38) where V 0 is th e vacuum noise variance, V e is th e variance of Eve’ s TMSV m odes, and σ 2 b denotes the trusted rece iver noise variance at Bob . Similarly , the mutua l quantu m inform ation χ ( B i ; E i ) [61], is expressed as χ ( B i ; E i ) = S ( E i ) − S ( E i | B i ) , (3 9 ) where S ( · ) den o tes the von Neu mann entro py . For the Gau s- sian state { e o,i , e qm ,i } sto r ed in Eve’ s quan tum memo r y , the correspo n ding c ovariance matrix Σ E i for each i -th parallel channel is expr essed as Σ E i = V e o i I 2 V e o i e qm i Z V e o i e qm i Z T V e I 2 , (40) where V e o i = (1 − β i ) V a + β i V e and V e o i e qm i = p β i ( V 2 e − 1) . This results in the symplectic eigenv alu e s of the covariance matrix of Eve’ s ancillary m odes b eing given as [61] λ i 1 , 2 = s 1 2 ∇ i ± q ∇ 2 i − 4 det ( Σ E i ) , (41) where ∇ i = V 2 e o i + V 2 e − 2 β i V e 2 − 1 , (42 a) and det ( Σ E i ) = V e o i V e − β i V e 2 − 1 2 . (42b) Similarly , the c o nditiona l c ovariance matrix of Eve’ s state giv en Bob ’ s quadra tu re, Σ E i | B i , is defined as follows [6 1]: Σ E i | B i △ = Σ E i − 1 V b i W i MW † i , (43) where Σ E i is given in (35) and M = 1 0 0 0 , W i = h E o i · b i i I 2 h e qm i · b i i Z . (44) From (39) and (40), we observe that Σ E i | B i can b e expressed in the form Σ E i | B i = A i C i C † i B i , (45) which is in a similar form as (40 ) where A i = diag V a V e + σ 2 b V e o i V b i , V eo i ! , B i = diag 1 − β i + β i V a + σ 2 b V e V b i , V e ! , C i = diag V a + σ 2 b V e o i e qm i V b i , − V e o i e qm i ! . (46) 8 Thus, the sy mplectic eigen values of the condition al covariance matrix can be calcu lated as: λ i 3 , 4 = s 1 2 ˜ ∇ i ± q ˜ ∇ 2 i − 4 det Σ E i | B i , (47) where ˜ ∇ i = det ( A i ) + det ( B i ) − 2 det ( C i ) = (1 − β i ) V e V 2 a + 1 + 2 β i V a V b i + σ 2 b ∇ i , (48a) and det Σ E i | B i = det ( Σ E i ) + σ 2 B Λ( V a V e , 1) Ξ + Λ ( V a V e , 1) σ 2 b V 2 b i , (48b) where Λ( V a V e , 1) = (1 − β i ) V a V e + β i and Ξ = Λ(1 , V a V e ) V e o i + V a V 2 e − 2 V a V 2 e o i e qm i . Sub stituting all th ese results into (37) and perfo rming a lgebraic simp lifications lead s to the e xp ression for the effecti ve SKR o f the RIS-assisted MIMO CV -QKD, where Eve perfo rms a collective Gaussian attack o n the overall ch annel, wh ich is given in (49) at the top of the next page. C. PSO-Based Joint RIS and Beam Sp litters O p timization In alignment with the proposed R I S- assisted MIMO CV - QKD system an d the analytically derived SKR expressions accountin g for localized an d overall eavesdropping, th e p hase shifts of the RIS unit elements an d values of η a and η b are optimized to enh ance the system’ s secre cy p erform ance. The goal of the o p timization is to m aximize the MIMO SKR b y jointly adju sting the RIS phase shifts, η a and η b , within their feasible rang es. Math ematically , the ob jectiv e fun ction is g iv en as OP : max Φ ,η a ,η b SKR { d, t, r, MIMO } (50) s.t. − π ≤ φ k ≤ π , ∀ k ∈ { 1 , . . . , K } , s.t. 0 ≤ η a ≤ 1 and 0 ≤ η b ≤ 1 . Due to the high ly n onlinear relationship between the SKR and the RIS ph ase matrix in the scenarios o u tlined in ( 34) and (49), a PSO-based algo rithm (Algor ithm 1) is used to solve the optimization problem presented in (50). T his approach aims to determine the o ptimal config urations o f the RIS phases and the optimal η a and η b , whic h are subsequ ently u sed to maximize the SKR. I V . N U M E R I C A L R E S U LT S A N D D I S C U S S I O N This section presents the numerical results corro borating the analytical framework described an d derived in the pape r . For the simu lation studies, we co nsider the stand a r d system parameters as ρ = 50 dB/Km, T e = 296 K (deno ting the room temperature), anten na gain G a = 30 dBi, σ 2 b = 0 . 01 , the variance o f Alice’ s initial m odulated signal V s = 1 000 , the variance of the vacuum state V 0 = 2 ¯ n + 1 with ¯ n = [exp ( hf c /k B T e ) − 1] − 1 , where h is the plan k’ s constant and k B is th e Boltzm ann’ s co n stant, the variance of Alice’ s Algorithm 1 PSO-Based Φ , η a , and η b Joint Optimizatio n 1: Inputs: N T , N R , n umber of RIS elements K , transmis- sion distance, and PSO configu ration para meters. 2: Specify the feasible search sp ace fo r RIS ph ases as − π ≤ φ k ≤ π , ∀ k ∈ { 1 , . . . , K } , and 0 ≤ η a , η b ≤ 1 . 3: f o r each consid e red transmission d istance do 4: Generate the channel matrice s H d , H t , H r , and H using (2 ). 5: Define the fitness fu nction as th e SKR, SKR { d , t , r , MIM O } . 6: Randomly initialize th e particle sw arm with rando m RIS pha se configur ations, η a , and η b . 7: for eac h PSO iteration do 8: Compute th e fitness value SKR { d , t , r , MIM O } for ev ery p article. 9: Update the per sonal-best and global-b est solution s based on the ma x imum fitness ac h iev ed . 10: Modify particle velocities an d positions accord in g to PSO update rules. 11: Project u pdated p hase, η a , an d η b values onto the feasible region defin e d in Step 2. 12: end for 13: Obtain the optimized RIS p h ase matrix Φ opt , η a , a nd η b . 14: Evaluate the correspo nding SKR max { d , t , r , MIM O } . 15: end for quadra tu re V a = V s + V 0 , V v 0 = 1 , and the variance o f Eve’ s q uadratur e V e j = 1 , j ∈ { d, t, r } & V e = 1 . W e also position the RIS at a distance of 0 . 3 and 0 . 8 times of th e distance between Alice and Bob from transmitter an d from receiver , respectively , to maximize its gain [1 ] and c onsider two co nfiguratio ns o f the p h ase shif t matrix o f th e RIS: (a) Φ RIS, rand with all phases to be different and random; and (b) Φ RIS, opt as obta in ed using the PSO-based algor ithm. Figure 3 illustrates the variation of the SKR as a fun ction of th e tran smission distance between Alice and Bob un der four eavesdropping scenarios: localized eav esd r opping on th e direct channe l H d , the Alice–RIS chan nel H t , the RIS–Bob channel H r , and global eaves d roppin g through effecti ve ch an- nel pur ification corresp onding to th e overall channel H . The results are presented for N T = N R = 8 , 16 , 32 , and 64 , with a fixed num b er o f RIS reflec tin g elements K = 64 . It is observed that the SKR exhibits a similar performan ce trend across all four eavesdropping scenario s. In these cases, the SKR decr eases mo notonica lly with increasing transmission distance due to path loss. Howe ver, a significa n t improvement in SKR is achieved as the M IMO configura tio n increa ses. This improvement can be attributed to the en hanced spatial degrees of freed o m and ar ray gain provided b y larger MIMO co nfigu- rations, which strengthen th e legitimate chan n el an d im p rove the ach iev able secur e tran smission range. Among the localized eav esdr opping scen arios, it is observed th at the case, wh ere Eve con trols the Alice–RIS ch annel H t , results in relatively lower SKR comp ared to the cases where Eve co ntrols the direct ch annel H d or the RIS–Bob chann el H r . This behavior arises because comp romising the Alice–RIS link af fects the 9 SKR MIMO = r H X i =1 SKR i = r H X i =1 1 2 log 2 1 + β i V a ( β i V 0 + (1 − β i ) V e + σ 2 b ) − h o ( λ 1 i ) − h o ( λ 2 i ) + h o ( λ 3 i ) + h o ( λ 4 i ) (49) 0 50 100 150 200 250 300 350 400 450 500 10 -6 10 -4 10 -2 10 0 (a) Eve’ s control over channel H d 0 20 40 60 80 100 120 140 160 10 -7 10 -6 10 -5 10 -4 10 -3 10 -2 (b) Eve’ s control over channel H t 0 50 100 150 200 250 300 350 400 450 500 10 -6 10 -4 10 -2 10 0 (c) Eve’ s control over channel H r 20 40 60 80 100 120 10 -7 10 -6 10 -5 10 -4 10 -3 10 -2 (d) Eve’ s control over channel H Fig. 3: SKR versus distance between Alice an d Bob for N R = N T = 8 , 16 , 32 , 64 , K = 64, f c = 15 THz, and d a = 0 . 5 λ c for Eve controls the channel (a) H d , (b ) H t , (c) H r , an d H . signal before RIS reflection and beamfo rming gain can be fully exploited, th ereby degrading the overall effective chann el between Alice an d Bo b . Fur thermor e, the SKR v alue s obta in ed under the loc a lized eavesdroppin g scenarios are co n siderably higher th an th ose repor ted und e r the glo bal eavesdropping model in [1] , where Eve is assumed to h av e access to the purification of the overall channel. This comparison shows that restricting the eavesdropper’ s access to specific ch annel segments yields a sub stantial improvemen t in SKR for RIS- assisted THz MIMO CV -QKD systems. Addition ally , it is observed that the RIS phase configura tio n o btained using the propo sed particle swarm optimiza tion (PSO) algorith m consistently outp e r forms random phase con figuration s ac ross all con sidered MIMO configur ations and eavesdropping sce- narios. Figure 4 illustrates the variation of the SKR as a fun ction of th e tran smission d istance between Alice and Bob under four eavesdropping scenarios: localized eav esd r opping on th e direct channe l H d , the Alice–RIS chan nel H t , the RIS–Bob channel H r , and global eaves d roppin g through effecti ve ch an- nel pur ification corresp onding to th e overall channel H . The plots are presented for d ifferent n umbers of RIS r e flec ting elements K = 9 , 25 , 64 , 10 0 , 225 , 8 × 8 MIMO configur ation, and op timal RIS phase Φ RIS, opt . Similar to Fig. 3 , the SKR decreases monoto nically with increasing transmission distance due to the severe propa g ation lo ss at THz f r equencie s. It is observed that when Eve contr ols either the direct Alice– Bob channel H d or the RIS-Bob chan nel H r , the SKR cur ves correspo n ding to different values of K ten ds to overlap alo ng the d istances. Th is indicates th at the benefit of RIS beam- forming becom es limited wh en the final pr opagatio n segment tow ard Bob or the direct pa th itself is compromised by the eav esdr opper . In contrast, when Eve c o ntrols the Alice–RIS channel H t or perf orms glo bal c h annel p urification throug h the 10 50 100 150 200 250 10 -7 10 -6 10 -5 10 -4 10 -3 10 -2 10 -1 (a) Eve’ s control over channel H d 0 50 100 150 200 250 300 350 400 10 -6 10 -4 10 -2 10 0 (b) Eve’ s control over channel H t 50 100 150 200 250 10 -6 10 -4 10 -2 10 0 (c) Eve’ s control over channel H r 10 20 30 40 50 60 70 80 90 100 10 -7 10 -6 10 -5 10 -4 10 -3 (d) Eve’ s control over channel H Fig. 4: SKR versus distance between Alice and Bob fo r K = 9 , 25 , 64 , 100 , 225 , N R = N T = 8 , f c = 15 THz, and d a = 0 . 5 λ c for Eve co ntrols the c h annel (a) H d , (b ) H t , (c) H r , an d (d) H . effecti ve ch annel H , increasing the numb er of RIS reflec tin g elements leads to a noticeable impr ovement in SKR. In these cases, larger RIS sizes p rovide stro nger passive beam formin g gain, resulting in highe r SKR values at a given distance and extendin g the maximum secure comm u nication r ange, particularly in the lon g-distance regime where RIS assistance compen sates for the severe THz path loss. T hese observations further dem onstrate that localized eavesdropping r esults in significantly h igher achievable SKR comp ared to the worst- case glo bal attack m odel con sidered in [1 ]. Figure 5 depicts the p erform ance comp a rison for th e non-RIS case a n d RIS-assisted transmission under optimal, Φ RIS, opt and rando m Φ RIS, rand , RIS p hase configur ations for H d , H t , H r channel, and overall chann el H . It is observed that the no n-RIS system exhibits a r apid SKR degrada tio n and supports secure key transmission only over short d istances, whereas RIS-assisted transmission significan tly enha n ces th e SKR an d extend s the secur e commu nication r ange. Am ong the RIS-assisted schemes, the PSO-o ptimized phase con figuration Φ RIS , opt consistently achieves the highest SKR across the entire distanc e range , wh ile ran dom phase control Φ RIS , rand yields lower SKR but still clearly ou tperfor m s the non - 0 50 100 150 200 250 300 350 400 10 -6 10 -4 10 -2 10 0 Fig. 5: SKR versus the distan c e be twe e n Alice and Bob with N T = N R = 32 × 3 2 , K = 64 , an d f c = 15 T H z . RIS case, whereas Ev s’ s con trol on Alice-RIS chann e l H t underp erform ed. It is fu rther observed that the SKR trend s correspo n ding to the ch annels H d and H r are id entical, indi- cating tha t RIS p h ase o ptimization has a d ominant influence 11 0 2 4 6 8 10 100 200 300 400 500 600 700 800 -11 -10 -9 -8 -7 -6 -5 -4 -3 -2 -1 (a) Eve’ s control over channel H d 0 2 4 6 8 10 50 100 150 200 250 300 350 400 450 500 550 600 -11 -10 -9 -8 -7 -6 -5 -4 (b) Eve’ s control over channel H t 0 2 4 6 8 10 100 200 300 400 500 600 700 800 -11 -10 -9 -8 -7 -6 -5 -4 -3 -2 -1 (c) Eve’ s control over channel H r 0 2 4 6 8 10 5 10 15 20 25 30 35 40 45 50 55 60 -11 -10 -9 -8 -7 -6 -5 -4 (d) Eve’ s control over channel H Fig. 6: Distance between Alice and Bob versus d etector noise σ 2 b for N R = N T = 8 , 16 , K = 64 , f c = 15 THz, and d a = 0 . 5 λ c for Eve co ntrols the c h annel (a) H d , (b ) H t , (c) H r , an d (d) H . on SKR (mo re on channel H d ) as comp ared to the channel H t . Moreover, RIS-assisted localized eavesdroppin g achieves significantly h igher SKR as co m pared to glob a l eaves d roppin g, due to effecti ve chann el purification of the overall channel H , as sh own in [1]. These r esults show that o ptimizing the RIS phase configu ration is crucial f or max im izing the SKR perfor mance o f RIS-assisted T Hz MI M O CV -QKD systems. Figure 6 d e picts the maximu m secure transmission d istance versus detecto r n o ise variance σ 2 b at the p articular secu r ity threshold for N R = N T = 8 and 16 , with K = 6 4 an d f c = 15 T Hz, u nder all fo ur eavesdropping scenar ios. In all cases, the secure distance decr eases mon otonically with increasing detec to r n oise, reflecting the degradation of Bob’ s received signal quality . In creasing the MIMO con figuration significantly extends the secu re oper ating r egion and enh ances robustness ag ainst n oise. It is also o bserved that amon g the localized eavesdropping scenarios shown in Fig. 4a-4c, the achiev able secure distance exhibits similar trends, altho ugh the perfor mance v aries depend ing on the compr o mised channel segment. When E ve controls th e Alice– RIS cha nnel H t , the achiev able secure distance becomes slightly mor e restricted compare d to the cases wh e r e Eve con tr ols the dir ect channel H d or the RIS– Bob ch annel H r . Th is o ccurs bec a u se com- promising the first ho p o f the RIS-assisted link reduces the signal strength before the RIS reflection gain can be fully exploited. While in Fig. 4d the achiev ab le secure distance is significantly reduc ed compared to the loca lize d eavesdropping scenarios, and the SKR c o ntours shift to ward sma ller distances as the detector no ise increases. This r esult shows that glob al channel pur ification repr esents a mor e powerful eavesdropping strategy . V . C O N C L U S I O N In th is p aper, th e SKR per forman ce of an RIS-assisted THz MIMO CV -QKD system was a nalyzed u nder both lo c alized and glo bal eavesdropping scenarios. Closed-form expression s for th e achiev ab le SKR were derived for homod yne detectio n and r ev erse re conciliation und er both localized e avesdroppin g and the g lobal chann el purification model. Th e presented numerical results de m onstrated that RIS assistance con tributes significantly to e n hancing SKR p erform ance and extends the secure transmission range in THz MIM O systems. Further im- provements wer e observed with increasing MIMO dimension s and RIS sizes, particularly at long distances, in terms of the 12 number o f metamaterial elements. T h e p roposed PSO-based RIS p hase config uration optimization method con sistently outperf ormed random phase co nfiguratio ns, an d perfor m ance degradation became m ore pronou n ced as no ise v ariance in- creased. Mo reover , su b stantially high er SKR values were ob- tained und e r localized eavesdropping co m pared to th e worst- case global attack model. Overall, RIS-assisted T Hz MIMO CV -QKD is established as a pro mising fram ew or k f or secu re next-genera tio n wireless network s, where RISs can be effec- ti vely lev erag ed to enhan ce quantu m secrecy p erform ance. Fu- ture research will fo cus on SKR per forman ce under imperfe c t CSI conditions and practical RIS hardware co nstraints [55 ], including discrete ph ase quantization, reflectio n losses, and realistic un it element re sp onses. R E F E R E N C E S [1] S. Kumar , S. P . Dash, and G. C. Alexan dropoulos, “RIS-empo wered CV - QKD THz MIMO communica tions: SKR analysis and optimiza tion, ” in Pr oc. IEEE W ire less Commun. Netw . Conf . , Kual a Lumpur , Malaysia , Apr . 2026, to be presented. [2] M. Giordani, M. Pol ese, M. Mezzavi lla, S. Rangan, a nd M. Z orzi, “T owa rd 6G networks: Use cases and technolo gies, ” IE EE Commun. Mag . , vol. 58, no. 3, pp. 55–61, Mar . 2020. [3] S. P . Dash, S. J oshi, S . C. S atapathy , S. K. Shandilya, and G. Panda, “ A cybe rtwin-based 6G cooperati ve IoE communica tion netw ork: Secrecy outage analysis, ” IEEE T rans. Indus. Inform. , vol . 18, no. 7, pp. 4922– 4932, Jul. 2022. [4] M. Guo and M. C. Gursoy , “Joint activ ity detecti on and channel estima- tion in cell-free massi ve MIMO networ ks with massive connec tivit y , ” IEEE T rans. Commun. , vol. 70, no. 1, pp. 317–331, Jan. 2022. [5] J. Xu, L. Y ou, G. C. Alexandropoul os, X. Y i, W . W ang, and X. Gao, “Near -field wideba nd extremel y large- scale MIMO transmissions with holograp hic m etasurf ace-based antenna arrays, ” IE EE T rans. W ir eless Commun. , vol. 23, no. 9, pp. 12 054–12 067, Sep. 2024. [6] I. F . Akyildi z, C. Han, Z. Hu, S. Nie, and J. M. Jornet, “T erahertz band communicat ion: An old problem revisit ed and researc h directio ns for the next decade, ” IEEE T rans. Commun. , vol. 70, no. 6, pp. 4250–4285, Jun. 2022. [7] M. Shehat a, K. W ang, J. W ebber , M. Fujita, T . Nagat suma, and W . W ith- ayachu m nankul, “IEEE 802.15.3d-compliant w aveforms for terahertz wireless communica tions, ” J. Lightwave T echnol. , vol. 39, no. 24, pp. 7748–7760, Dec. 2021. [8] S. P . Chepuri, N. S hlezi nger , F . L iu, G. C. Alexandro poulos, S. Buzzi, and Y . C. Eldar , “Int egrated sensing and communications with reconfig- urable intel ligent surfa ces: From signal modeling to processing, ” IEE E Signal Pro cess. Mag. , vol. 40, no. 6, pp. 41–62, Sep. 2023. [9] E. Calva nese Strinat i, G. C. A lexandropoul os, N. Amani, M. Croz- zoli, G. Madhusuda n, S. Mekki, F . Ri vet, V . Sciancale pore, P . Sehier , M. Stark, and H. W ymeersch, “T owa rd distributed and intelligen t inte- grated sensing and communicatio ns for 6G networ ks, ” IEEE W ireless Commun. , vol. 32, no. 1, pp. 60–67, Feb. 2025. [10] B. R. Reddy , S. P . Dash, and D. Ghose, “Optimal multi-le vel amplitude- shift ke ying for non-cohere nt SIMO wireless system in Rician fading en vironment, ” IEE E T rans. V eh. T echnol. , vol. 73, no. 3, pp. 4493–4498, Mar . 2024. [11] S. Xue, Y . Ma, N. Y i, and R. T afa zolli, “Unsupervised deep learning for MU-SIMO joint transmitter and noncohere nt recei ver design, ” IEEE W ir eless Commun. Lett. , vol. 8, no. 1, pp. 177–180, Feb. 2019. [12] K. Chen-Hu, G. C. Alexan dropoulos, and A. G. Armada, “Non-coherent modulati on with random phase configurations in RIS-empo wered cellu- lar MIMO systems, ” ITU J . Future E volvin g T echnol . , vol. 3, no. 2, pp. 1–14, Sep. 2022. [13] R.-Y . W ei, W .-Y . Chin, and T .-Y . Feng, “Nonc oherent two-wa y relaying with decode and forward : T wo versus three phases, ” IEEE T rans. V eh. T echno l. , vol. 71, no. 3, pp. 3350–3354, Mar . 2022. [14] E. Basar , G. C. Alexandrop oulos, Y . Liu, Q. Wu, S. Jin, C. Y uen, O. A. Dobre, and R. Schober , “Reconfigurabl e intell igent surfac es for 6G: Emerging hardware architecture s, appl ications, and open challen ges, ” IEEE V eh. T echno l. Mag. , vol . 19, no. 3, pp. 27–47, Sep. 2024. [15] G. C. Alex andropoulos, A. Zappone, N. Shlezin ger, M. Di Renzo, and Y . C. Eldar , Reconfigur able Intell igent Surfaces for W ireless Communi- cations: Modeling, A rc hitectu res, and Applicati ons . Singapore : Springer Nature, 2026. [16] A. Rabault, L. Le Magoarou, J. Sol, G. C. Alexa ndropoulos, N. Shlezinger , H. V incent Poor , and P . del Hougne, “On the tacit line arity assumption in common cascaded models of RIS-parame trized wireless channe ls, ” IEEE T rans. W irele ss Commun. , vol. 23, no. 8, pp. 10 001– 10 014, Aug. 2024. [17] A. P . Ajayan, S. P . Dash, and B. Ramkumar , “ Approximate composite channe l statistic s and performance analysis of IRS-aid ed wireless s ystem under Nakagami- m fadi ng, ” IEEE Access , vol. 11, pp. 102 290–102 300, Sep. 2023. [18] S. P . Dash and A. Kaushik, “RIS-assisted 6G wirel ess communicati ons: A novel statistic al framew ork in the presence of direct channe l, ” IEE E Commun. Lett. , vol. 28, no. 3, pp. 717–721, Jan. 2024. [19] G. C. Alexa ndropoulos, D. -T . Phan-Huy , K. D. Katsanos, M. Crozzoli, H. W ymeersch, P . Popovsk i, P . Ratajcza k, Y . B ´ en ´ edic, M.-H. Hamon, S. H. Gonzale z, P . Mursia, M. Rossanese, V . Scianc alepore, J.-B. Gros, S. T erranov a, G. Gradoni, P . D. Lorenzo, M. Rahal , B. Denis, R. D’Errico, A. Clemen te, and E. C. Strina ti, “RIS-enabl ed sm art wireless en vironment s: Deployment scenario s, network arch itecture, bandwidt h and area of influence, ” EURA SIP J . W irele ss Commun. Netw . , vol. 2023, p. 103, Oct. 2023. [20] Q. Zhu, M. L i, R. Liu, and Q. Liu, “Joint transcei ver beamforming and reflecti ng design for act ive RIS-aided ISA C systems, ” IEEE Tr ans. V eh. T echno l. , vol. 72, no. 7, pp. 9636–9640, Jul. 2023. [21] S. P . Dash, R. K. Mallik, and N. Pandey , “Performance analysis of an index modulation- based recei ve div ersity RIS-assisted wireless communicat ion system, ” IE EE Commun. Lett. , vol. 26, no. 4, pp. 768– 772, Apr . 2022. [22] S. P . Dash, S. J oshi, and S. A¨ ıssa, “En velope distrib ution of two correla ted complex Gaussian random vari ables and applicatio n to the performanc e ev aluation of RIS-assisted communicat ions, ” IEEE Com- mun. Lett. , vol. 26, no. 9, pp. 2018–2022, Sep. 2022. [23] A. Basu, S. P . Dash, A. Kaushik, D. Ghose, M. D. Renzo, and Y . C. Eldar , “Performanc e analysis of RIS-aided index modulati on with greedy detec tion ove r Rici an fadi ng channels, ” IEE E Tr ans. W irel ess Commun. , vol. 23, no. 8, pp. 8465–8479, Jan. 2024. [24] R. Singh, A. Kaushik, W . Shin, G. C. Alexa ndropoulos, M. T oka, and M. Di Renzo, “Indexe d multiple access with reconfigu rable intel ligent surfac es: T he reflection tuning potential, ” IEEE Commun. Mag . , vol. 62, no. 4, pp. 120–126, Apr . 2024. [25] A. Basu, S. P . Dash, and D. Ghose, “RIS empowered index modulati on- based recei ve di versity wireless system with Nakagami- m fa ding chan- nels, ” IEEE T rans. V eh. T ec hnol. , pp. 1–15, Jun. 2024. [26] Y . Liu, C. Huang, G. Chen, R. Song, S. Song, and P . Xiao, “Deep learni ng empowere d trajectory and passiv e beamforming design in U A V - RIS enabled secure cognit ive non-terrestr ial networks, ” IEEE W ir eless Commun. Lett. , vol. 13, no. 1, pp. 188–192, Jan. 2024. [27] C. W eedbrook, S. Pirandola, R. Garc´ ıa-P atr ´ on, N. J. Cerf, T . C. Ralph, J. H. Shapiro, and S. Lloyd, “Gaussia n quantum information, ” Rev . Mod. Phy . , vol. 84, no. 2, p. 621, May 2012. [28] A. Manzali ni, “Quantum communica tions in future netw orks and ser- vices, ” Quantum Rep. , vol. 2, no. 1, pp. 221–232, Mar . 2020. [29] W . Dif fie and M. Hellman, “Ne w directio ns in cryptograph y , ” IEE E T rans. Inf . Theory , vol. 22, no. 6, pp. 644–654, Nov . 1976. [30] I. B. Djordje vic, “Hybrid QKD protocol outperforming both D V - and CV -QKD protocols, ” IEEE Photon. J. , vol. 12, no. 1, pp. 1–8, Feb . 2020. [31] C. W are, R. A ym eric, C. Z idi, and M. Lourdiane, “Potentia l i mpact of CV -QKD integ ration on classical WDM network capacity , ” IE EE Photon. T echnol. Lett. , vol. 34, no. 18, pp. 957–960, Sep. 2022. [32] R. Lin and J. Chen, “Modeling and m inimizi ng spontaneous Raman scatte ring for QKD secured DWDM networks, ” IE EE Commun. Lett. , vol. 25, no. 12, pp. 3918–3921, Dec. 2021. [33] V . Scarani, H. Bechman n-Pasquinucc i, N. J. Cerf, M. Duˇ sek, N. L ¨ utkenh aus, and M. Pee v , “The security of pract ical quantum ke y distrib ution, ” Rev . Mod. Phys. , vol. 81, pp. 1301–1350, Sep 2009. [34] E. Hugues-Salas, O. Alia, R. W ang, K. Rajku mar, G. T . Kanellos, R. Ne- jabat i, and D. Simeonidou, “11.2 Tb/s classic al channel coexi stence with D V -QKD ov er a 7-core multico re fiber , ” J. Lightwave T ec hnol. , vol. 38, no. 18, pp. 5064–5070, S ep. 2020. [35] O. Alia, R. S. T essinari, E. Hugues-Sala s, G. T . Kanell os, R. Nejabati , and D. Simeonidou, “Dynamic D V -QKD networki ng in trusted-nod e- free softwa re-defined optical networks, ” J. Lightwa ve T echnol. , vol. 40, no. 17, pp. 5816–5824, S ep. 2022. 13 [36] I. B. Djordje vic, “Optimiz ed-eight-stat e CV -QKD protocol outperform- ing Gaussian modulati on based protocols, ” IEEE Photon. J . , vol. 11, no. 4, pp. 1–10, Jun. 2019. [37] J. Lode wyck, M. Bloch, R. Garc´ ıa-P atr ´ on, S. Fossier , E . Karpo v , E. Diamanti, T . Debuissche rt, N. J. Cerf, R. Tual le-Brouri, S. W . McLaughli n et al. , “Quantum ke y distribu tion ove r 25 km with an all- fiber continuous-v ariabl e s ystem, ” Phy . Rev . A , vol. 76, no. 4, p. 042305, Oct. 2007. [38] Z. Y ichen, B. Y iming, L. Zhengyu, Y . Song, and G. Hong, “Continuous- v ariable quantum key distributio n system: Past, present, and future, ” Appl. Phys. Rev . , vol. 11, no. 011318, Mar . 2024. [39] S. Pirandola, “Limits and security of free-space quantum communica- tions, ” Phys. Rev . R es. , vol . 3, no. 1, p. 013279, May 2021. [40] Z. Pan and I. B. Djordje vic, “Secret key distillati on ove r satellite-t o- satell ite free-space optics channel with a limited-size d apertur e eav es- dropper in the same plane of the legitima te rec eiv er , ” Opt. Express , vol. 28, no. 25, pp. 37 129–37 148, Nov . 2020. [41] S. Pirandola , “Satellit e quantum communications: Fundamental bounds and practica l security , ” Phys. Rev . R es. , vol. 3, no. 2, p. 023130, May 2021. [42] J. Gariano, M. Neifeld, and I. Djordje vic, “Engineering trade studies for a quantum key distribut ion system over a 30 km free-space maritime channe l, ” App. Opt. , vol. 56, no. 3, pp. 543–557, Jan. 2017. [43] J. Garia no and I. B. Djordje vic, “Trade study of apert ure size, adapti ve optics and multipl e spatial modes for a polari zation entanglement QKD system over a 30 km maritime channel, ” App. Opt. , vol. 57, no. 28, pp. 8451–8459, Oct. 2018. [44] S. Kumar , S. P . Dash, and G. C. Alexand ropoulos, “MIMO FSO systems in hybrid quantum noise en vironments: SKR a nalysis with one- and two-w ay CV -QKD protoco ls, ” 2026. [Online]. A vai lable: https:/ /arxiv .org/abs/ 2509.07408 [45] K. P . Peppas, G. C. Alexandropo ulos, E. D. Xenos, and A. Maras, “The fischer–snede cor F -distrib ution model for turbul ence-induce d fading in free-spac e optical systems, ” J . Lightwave T echnol. , vol . 38, no. 6, pp. 1286–1295, Mar . 2020. [46] M. Z hang, S. Pirandola , and K. Delfanaz ari, “Millimeter -wav es to tera- hertz SISO and MIMO continuou s variabl e quantum key distrib ution, ” IEEE T rans. Quantum Eng. , vol . 4, pp. 1–10, Apr . 2023. [47] C. O ttaviani , M. J. W oolle y , M. Erementchou k, J . F . Federici, P . Mazumder , S. Pirandola, and C. W eedbrook , “T erahertz quantum cryptogra phy , ” IE E E J . Sel. Areas Commun. , vol. 38, no. 3, pp. 483–495, Mar . 2020. [48] Z. W ang, R. Malane y , and J. Green, “Inter-sa tellite quantum ke y distrib ution at terahert z frequencie s, ” in ICC 2019 - 2019 IEEE Int. Conf . Commun. IEEE, May 2019. [49] M. T . Sayat, B. Shajilal, S. P . Kish, S. M. Assad, T . Sym ul, P . K. Lam, N. J. Ratte nbury , and J. E. Cater , “Satell ite-to-ground continuo us v ariable quantum key distrib ution: T he Gaussian and discrete modulated protocol s in low eart h orbit, ” IEEE T rans. Commun. , vo l. 72, no. 6, pp. 3244–3255, Jun. 2024. [50] N. K. Kundu, S. P . Dash, M. R. McKay , and R. K. Mallik, “MIMO terahe rtz quantum key distrib ution, ” IEEE Commun. Lett. , vol. 25, no. 10, pp. 3345–3349, O ct. 2021. [51] S. Kumar and S. P . Dash, “SKR analysis of one- and two-w ay CV -QKD MIMO FSO communicati on system, ” IEEE Commun. Lett. , vol. 29, no. 10, pp. 2456–2460, O ct. 2025. [52] S. Kumar , S. P . Dash, and G. C. Alexa ndropoulos, “Performance analysis of one- and two-way DV -QKD with MIMO FSO communicatio n sys- tems, ” in Proc. IEEE International Conf . Commun. , Glasgo w , Scotland , UK, May 2026, to be presented. [53] A. M. Sayee d, “Quantum MIMO: A framew ork for enta nglement distrib ution in spatial multipa th channels, ” in Quantum 2.0 Confere nce and Exhibition . Opti ca Publishing Group, 2022, p. QT u2A.20. [54] S. Kumar , S. P . Dash, D. Ghose, and G. C. Ale xandropoulos, “RIS- assisted MIMO CV -QKD at THz frequencies: Channel estimation and secret key rate analy sis, ” IEEE T rans. Commun. , vol. 73, no. 12, pp. 15 612–15 624, Dec. 2025. [55] G. C. Alexandropou los, B. K. Jung, P . Gavriil idis, S. Matos, L. H. Loeser , V . Elesina, A. Clemente , R. D’Errico, L. M. Pessoa, and T . K ¨ urner , “Characteri zation of indoor reconfigura ble intelligen t surface - assisted channe ls at 304 GHz: Experimenta l measurements, challenge s, and future directi ons, ” IEEE V eh. T echnol . Mag. , vol. 20, no. 3, pp. 20–29, Sep. 2025. [56] S. W . Elling son, “Path loss in reconfigur able intel ligent surface-ena bled channe ls, ” in Pr oc. IEE E Int. Symp. P ersonal, Indoor Mobile Radio Commun. (PIMRC) . Helsinki, Finland , Sep. 2021, pp. 829–835. [57] M. He, J. Xu, W . Xu, H. Shen, N. W ang, and C. Zhao, “RIS-assisted quasi-sta tic broad c overage for wideband mmW av e massi ve MIMO systems, ” IEEE Tr ans. W ire less Commun. , vol. 22, no. 4, pp. 2551– 2565, Apr . 2023. [58] N. Hosseinideh aj, Z. Babar , R. Malaney , S. X. Ng, and L . Hanzo, “Satel lite-based continuous-v ariable quantum communications: State-of- the-art and a predic tiv e outlook, ” IEE E Commun. Surve ys T ut. , vol. 21, no. 1, pp. 881–919, Aug. 2019. [59] C. Gia nfranco, Quantum Co mmunications . Uni versity of Pado va, Pado va, Italy: Springer , 2015, ch. Fundamental s of Continuou s V ari- ables, pp. 475–484. [60] S. Pirandola , S. L. Braunstein, and S. Llo yd, “Chara cterizati on of colle ctiv e Gaussian attacks and security of cohere nt-state quantum cryptogra phy , ” P hys. Revi ew Lett. , vol. 101, no. 20, p. 200504, Nov . 2008. [61] C. W eedbrook, S. Pirandola, S. Lloyd, and T . C. Ra lph, “Quantum cryptogra phy approac hing the classical limit, ” Phys. Rev . Lett. , vol. 105, p. 11, Sep. 2010.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment