Finite-blocklength performance of polar wiretap codes under a total variation secrecy constraint
We study the performance of polarizing codes over a degraded symmetric wiretap channel under a total variation distance (TVD) secrecy constraint. We show that the leakage can be bounded by the sum of the TVDs of the bit-channels corresponding to the …
Authors: Laura Luzzi, Valerio Bioglio
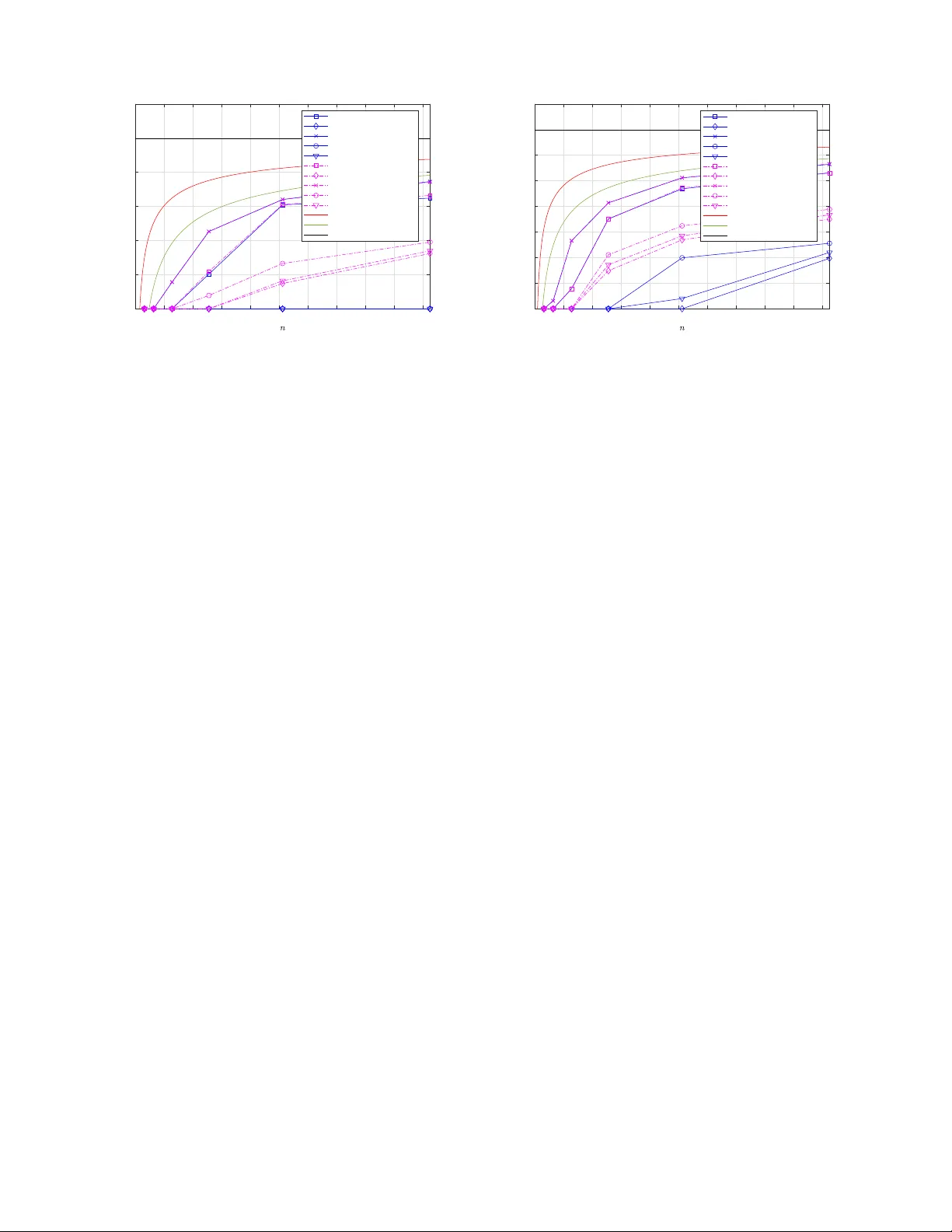
Finite-blocklength performance of polar wiretap codes under a total v ariati on s ecrec y constraint Laura Luzzi † ‡ , V alerio Bioglio ∗ † ETIS (UMR 8051 CY Cergy Paris Uni versit ´ e, ENSEA, CNRS), e-mail: laura.luzzi@ensea.f r ‡ ´ Equipe COSMIQ, Inria de Paris, e-mail: laura.lu zzi@inria.fr ∗ Dipartimento di Infor matica, Universit ` a d i T orino, e-mail: valerio.bioglio@un ito.it Abstract —W e study the p erf ormance of polarizing codes over a degraded symmetric wiretap channel und er a total variation distance (TVD) secrecy constraint. W e sho w that the leakage can be boun d ed b y the sum of the TVDs of the bit -channels corres ponding to the confidential and frozen bits. In the asymp- totic r egime, this giv es a new criterion to design wiretap codes with v anish ing TVD leakage. In finite bl ocklength, it allows us to compute lower bounds for the secre cy rate of d ifferent fa milies of polarizing wiretap codes ov er a bin ary erasure wiretap channel. Index T erms —Physical Lay er Security , Wiretap channel, Polar codes, Finite Bl ocklength, Information Leakage, T otal V ariatio n Distance I . I N T RO D U C T I O N W iretap co d ing allows c onfidential co mmunicatio n without secret keys in the presen ce of passive adversar ie s, as long as an asymm etry in the channel quality between the legitimate receiver and the adversary can be guaranteed [1 ]. W idely adopted metrics for the infor m ation leakage include the (nor- malized o r u nnorma lize d) mutu al inform ation (MI) and the TVD [2]. In the asymptotic setting where the blo c k length tends to infinity , secrecy c apacity-achieving cod ing schemes have been prop o sed, notably based on polar codes [ 3 ], which are an attractive solution since th ey are already pa r t o f the 5 G New Radio stand ard. Howe ver, for applications re quiring short packets or low laten cy , it is not possible in gene r al to guara n tee a vanishing in formation leak age; f or a target leakag e δ and error pro bability ǫ , the gap of the fin ite-blocklen gth secrecy rate from the secrecy c a pacity must b e taken in to acco unt. Building o n the finite-length channel cod in g rates analysis in [4], autho rs in [ 5] proved tigh t b o unds o n the optim al seco n d- order codin g rate over discrete mem oryless and Gaussian wire- tap ch a nnels un der a total variation (T V ) secrecy co nstraint. Recent work s hav e inv estigated the finite-length performanc e of pr actical wiretap codes. In [6], the eq uiv oca tion o f very short wiretap co des is qu antified over a b inary erasure chan nel (BEC); [ 7] prop osed a lgebraic meth o ds to compute exact equiv ocation in special cases. Au th ors in [8] consider rand om- ized Reed–M u ller code s for Gaussian wire ta p chann els; oth e r works have used deep learning to desig n wiretap codes [9–11]. L. Luzzi was supported in part by CY Initiat i ve of Excellence (ANR-16- IDEX-0008), the France 2030 ANR program “PEPR Networks of the Future” (ANR-22-PEFT -000 9) and by the Horizon Europe/JU SNS project R OBUST - 6G (GA no. 101139068). Howe ver, these app roaches ar e curren tly limited to very sho r t blockleng ths, due to the comp lexity o f estimatin g the leakage. W iretap Polar co des were consider ed in [12], which used a mo dified SC decode r to co mpute a lower b ound fo r the MI leakag e; [13] provid ed u pper and lower bo unds for the MI leak a ge of wir etap schemes b ased on polar cod es as a func tio n o f their finite-length scalin g ; [14] co mpared the perfor mance of polar an d Reed-Muller codes un der a T VD leakage constraint when the main chann el is error-free and the eav esdropp er’ s c hannel is a BEC; [1 5] extend ed this study to m ulti-kernel P A C codes. In this paper, we adopt the same viewpoint as [14], an d consider a TV secrecy co nstraint. While [14] on ly co nsidered the case where the m ain ch a nnel is error-free, we extend the approa c h to the ge neral degraded symm etric wir e ta p chann el. W e show tha t the TV infor mation leakage fo r po lar-like wiretap codes is up per bound ed by the sum of the TVDs of the b it-channe ls cor respondin g to th e co n fidential bits a n d th e frozen bits. In the asym ptotic regime, this allows to p ropose a variant of the strong secrecy scheme in [3] which is tailore d to the TV metr ic. For finite bloc klengths, o ur boun d provide s a simple cr iter ion to design wiretap codes fo r a given target leakage δ an d erro r proba bility ǫ with guaran te e d secrecy r ate. In th e case wh en the ma in chan nel and eavesdropper’ s chann el are BECs, we co mpute explicit lower bound s for the secrecy rates o f different families of polarizin g cod es — nam e ly Polar codes, Reed-Muller (RM) c odes [16], multi-kernel (MK ) po lar codes [17] and adjacent- bit swapped (ABS) codes [18]. I I . N O TA T I O N A N D P R E L I M I N A R I E S Notation: All loga rithms are in base 2 . W e use col- umn notation for vectors, a nd denote by x n the vector ( x 1 , . . . , x n ) t , and by x j i the subvector ( x i , x i +1 , . . . , x j ) t . Giv en A ⊆ J 1; n K , th e no tation x A refers to the projection of x n on the coordin a tes in A . W e denote the T VD between two d iscrete distributions b y V ( p, q ) = 1 2 k p − q k 1 . A. P r operties of the TVD o f symmetric channels W e recall Gallager’ s definitio n [ 1 9, p. 94 ] : Definition 1: A discre te channel W : X → Y is symmetric if there is a par titio n Y = Y 1 ∪ · · · ∪ Y r such that: 1) ∀ x, ¯ x ∈ X , there exists a per m utation π x ¯ x : Y → Y such that ∀ k ∈ J 1; r K , π x ¯ x ( Y k ) = Y k , and ∀ y ∈ Y , W ( y | x ) = W ( π x ¯ x ( y ) | ¯ x ) , 2) ∀ k ∈ J 1; r K , ∀ y , ¯ y ∈ Y k , there exists a per mutation π y ¯ y : X → X such that ∀ x ∈ X , W ( y | x ) = W ( ¯ y | π y ¯ y ( x )) . Definition 2 : Consider a symmetric ch annel W : X → Y with transition prob ability p Y | X . Given an inp ut distribution p X over X and the cor respondin g outp ut p Y = p Y | X ◦ p X , let T ( W , p X ) = X x ∈X ,y ∈Y | p XY ( x, y ) − p X ( x ) p Y ( y ) | = 2 V ( p XY , p X p Y ) . The TVD of the chann e l W is define d as T ( W ) = max p X T ( W , p X ) . The following result may b e of ind ependen t inter est: Lemma 1: For a symmetric channel W : X → Y with transition prob ability p Y | X , T ( W ) = T ( W , p ¯ X ) , where p ¯ X is th e uniform input distribution over X and p ¯ Y = p Y | X ◦ p ¯ X is the corre sp onding outpu t distribution. Sketch of p r oof: Recall tha t th e TVD V ( p, q ) cor responds to the f -div ergence D f ( p, q ) with f ( u ) = 1 2 | u − 1 | . T hus, T ( W , p X ) is the co rrespond ing f - informatio n [20, p. 1 3 4-135 ]. It follows from [21, L emma 3.2] that T ( W , p X ) is a con tinuous and con c a ve fun ction of p X . Note th a t althou gh f is not strictly conv ex, the sufficiency part of the second statemen t of [21, Theorem 3.2] still h olds. I f W is sy m metric, p ¯ Y is co nstant on each set Y k , k ∈ J 1; r K , an d V ( p Y | X = x , p ¯ Y ) takes the same value K for a ll x ∈ X . This implies that the info rmation radius R f ( W ) = inf p Y max x V ( p Y | X = x , p Y ) ≤ K . But by [21, Theorem 3.2] , R f ( W ) = max p X T ( W , p X ) = K . Example 1: For a binary erasure channel (BEC) W w ith erasure prob ability p , T ( W ) = 1 − p . Definition 3: A chan nel Q : X → Z is de graded with respect to a chan n el W : X → Z if there exists a ch annel P : Y → Z such th a t ∀ x ∈ X , ∀ z ∈ Z , Q ( z | x ) = P y ∈Y W ( y | x ) P ( z | y ) . I n th is ca se, we write Q 4 W . A pr oof o f the n ext pro perty can be f o und in [1 4, Lemma 2]. Lemma 2: If Q 4 W , then ∀ p X , T ( Q, p X ) ≤ T ( W , p X ) . The quality of a binary-inp u t chann el W : { 0 , 1 } → Y ca n be m easured by its Bhatta charyya p arameter Z ( W ) = X y ∈Y p W ( y | 0 ) W ( y | 1 ) ∈ [0 , 1] . The following inequ alities were proved in [22, A p pendix A]: Lemma 3: For any binary- input memory less symm etric channel (BMS) W , C ( W ) ≤ T ( W ) ≤ p 1 − Z ( W ) 2 . B. Ch a nnel po larization Let n = 2 m . A polar-like code of parameters ( n, k ) is specified by a p air ( G n , A ) , where G n is a n invertible n × n binary matrix, and A ⊆ J 1; n K is a set of information b its. Giv en an input M k ∈ { 0 , 1 } k , the encod er sets U A = M k and U J 1; n K \A = 0 n − k , and tran smits X n = G n U n . In the ca se of polar codes, G n = G ⊗ m 2 , where G 2 = 1 0 1 1 [22]. Giv en a BMS ch annel W : { 0 , 1 } → Y , ∀ i = 1 , . . . , n we define the i -th bit-chan nel W ( i ) n : { 0 , 1 } → Y n × { 0 , 1 } i − 1 with tra nsition p robabilities W ( i ) n ( y n , u 1 , . . . , u i − 1 | u i ) = X u i +1 ,...,u n 1 2 n − 1 W n ( y n | G n u n ) . T o simp lify notation, we will write W ( i ) instead of W ( i ) n when n is fixed. W e say that G n is po la rizing over W if the cap acities C ( W ( i ) ) are close to either 0 or 1 for almost all i ∈ { 1 , 2 , ..., n } a s n → ∞ [1 8]. C. P ola rization o f TVDs Channel po larization und er a TV metric was studied in [23], which showed that for a BMS channel W , given an i.i.d. process { B i } with Bern oulli(1/2) d istribution, if w e de fin e T 0 = T ( W ) , and ∀ m ≥ 0 , T m +1 = T ( W − m ) if B m = 1 , and T m +1 = T ( W + m ) if B m = 0 , where W + and W − denote Arikan’ s tra n sforms [22, eq. ( 17)-(1 8)], then T m is a bou nded supermartin gale in the in te r val [0 , 1] and co n verges alm ost surely to { 0 , 1 } [23, Proposition 5.2 ]. Namely , the TVDs of the bit-chan nels polarize. Mo r eover , T ( W − ) = T ( W ) 2 , T ( W − ) + T ( W + ) ≤ 2 T ( W ) an d P n i =1 T ( W ( i ) n ) ≤ nT ( W ) . Furthermo re, the following resu lt hold s [23, Propo sition 5 .8]: Pr oposition 1: For any BMS c hannel W , ∀ β ≤ 1 / 2 , lim m →∞ P { T m < 2 − 2 mβ } = 1 − C ( W ) . I I I . S E C R E C Y B O U N D S U N D E R A T V D M E T R I C A L I C E E N C O D E R p Y | X D E C O D E R B O B p Z | Y E V E M k X n Y n ˆ M k Z n Fig. 1: The degra ded wiretap chann el. W e consider the d egraded wiretap chan nel depicted in Figure 1. W e assume that Bob’ s cha n nel W b : X → Y and Eve’ s channel W e : X → Z , of transition p robabilities p Y | X and p Z | X respectively , are both BMS chan nels. The confiden tial message M k is a ssumed to be un iform over { 0 , 1 } k . A. S econd or d er bou nds for the secrecy rate W e con sider the average TVD S ( M k | Z n ) betwee n message M k and Eve’ s observation Z n as a measure of leakag e [5]: S ( M k | Z n ) = V ( p M k Z n , p M k p Z n ) . (1) For this mo del, the secr ecy cap acity is C s = C ( W b ) − C ( W e ) . In finite blocklen gth, [ 5, Th e orem 1 3] showed th a t fo r ǫ + δ < 1 , the maximal secrecy rate R ∗ ( n, ǫ, δ ) for block length n , and av erage er ror pr obability ǫ under the secrecy constrain t S ( M k | Z n ) ≤ δ (2) is u pper and lower bo unded by R ∗ ( n, ǫ, δ ) ≤ C s − r V c n Q − 1 ( ǫ + δ ) + O log n n , (3) R ∗ ( n, ǫ, δ ) ≥ C s − r V b n Q − 1 ( ǫ ) − r V e n Q − 1 ( δ ) + O log n n (4) where Q denotes the Q- function, V b and V e are the dispersion s of Bob and Eve’ s channels, and V c = X x ∈X p ¯ X ( x ) X y ,z p ZY | X ( z , y | x ) log p ZY | X ( z , y | x ) p Z | X ( z | x ) p Y | Z ( y | z ) 2 − D p ZY | X = x || p Y | Z p Z | X = x 2 ! , (5) provided that the u niform distribution p ¯ X is th e uniqu e distri- bution that maxim izes I ( X ; Y | Z ) [24]. B. W iretap co ding scheme W e consider the general wiretap co ding sch e me in [3]. The set J 1; n K is par titioned into three disjoint subsets A ∪ R ∪ B , where |A| = k and |R| = r . Intu iti vely , A co rrespond s to the indices of bit-chan nels th at are good f or Bob but b ad for Eve, B to bit-chan nels that are bad for both , and R to b it-channels that are g o od for b oth. Giv en th e confiden tial message M k ∈ { 0 , 1 } k and a vector V r of unifo r mly rando m bits, the wiretap encoder is defined by setting X n = G n U n , where U B = 0 n − k − r , U A = ( U i 1 , . . . , U i k ) = M k , U R = V r . (6 ) The secr ecy r ate of the wiretap cod e is R s = k / n . C. Bound fo r the a v erag e err o r p r obab ility Bob’ s blo ck e r ror pr o bability u nder SC deco ding is up per- bound ed by the sum of Bhattach a ryya parameters of Bob ’ s unfro zen b it-channels in G = A ∪ R [2 5, 26]: P e ≤ X i ∈A∪R Z ( W ( i ) b ) (7) Remark 1 : Bob does n ot decode th e bit-ch annels with in - dices greate r th an i max ( A ) = max { j ∈ A} , so that in ( 7), the sum can be taken over A ∪ R ′ , R ′ = { i ∈ R : i ≤ i max ( A ) } . D. B o unds for th e leakage First, we prove a prelimin ary lemm a ( see Bound 1 in [14]): Lemma 4: If M k is u niformly d istributed in { 0 , 1 } k , V ( p M k Z n , p M k p Z n ) ≤ k X i =1 V ( p M i Z n , 1 2 p M i − 1 Z n ) Pr oof: Letting f i ( m k , z n ) = 1 2 k − i p M i Z n ( m i , z n ) f or i = 0 , . . . , k , we can write V ( p M k Z n , p M k p Z n ) = 1 2 X m k ,z n f k ( m k , z n ) − f 0 ( m k , z n ) = 1 2 X m k ,z n k X i =1 ( f i ( m k , z n ) − f i − 1 ( m k , z n )) ≤ 1 2 k X i =1 X m k ,z n f i ( m k , z n ) − f i − 1 ( m k , z n ) = k X i =1 V ( p M i Z n , 1 2 p M i − 1 Z n ) . Lemma 5: Le t Z n be the ou tput o f the wiretap encod er with input U n giv en b y (6) throug h the eavesdropper ’ s chann el W e , and ¯ Z n the outpu t of the p o lar encode r with unifo r m inp u t ¯ U n , and let A ∪ B = { i 1 , . . . , i n − r } . Then th e following bounds hold f o r th e leakage in TVD: S ( M k | Z n ) ≤ 1 2 n − r X j =1 T ( p ¯ Z n ¯ U i 1 ¯ U i 2 ··· ¯ U i j − 1 | ¯ U i j ) (Bound 1) ≤ 1 2 X i ∈A∪B T ( W ( i ) e ) . (Bound 2) Pr oof: Let A ∪ B = { i 1 , . . . , i n − r } . W e have S ( M k | Z n ) = V ( p U A Z n , p U A p Z n ) ( a ) = V ( p U A∪B Z n , p U A∪B p Z n ) ( b ) ≤ V ( p ¯ U A∪B ¯ Z n , p ¯ U A∪B p ¯ Z n ) = 1 2 T ( p ¯ Z n | ¯ U A∪B ) ( c ) ≤ n − r X j =1 V p ¯ U i 1 ¯ U i 2 ··· ¯ U i j ¯ Z n , p ¯ U i j p ¯ U i 1 ¯ U i 2 ··· ¯ U i j − 1 ¯ Z n = 1 2 n − r X j =1 T ( p ¯ Z n ¯ U i 1 ¯ U i 2 ··· ¯ U i j − 1 | ¯ U i j ) , where (a) holds since the bits U B in (6) are fixed to zero, (b) hold s by Le m ma 1 since th e chann el Q n ( W e , R ) with transition probab ilities p ¯ Z n | ¯ U A∪B is sy mmetric provided that W e is sy mmetric [3, Propo sition 13], and (c) by Lemma 4. Assuming now that i 1 < i 2 < . . . < i n − r , we have 1 2 n − r X j =1 T ( p ¯ Z n ¯ U i 1 ¯ U i 2 ··· ¯ U i j − 1 | ¯ U i j ) ( d ) ≤ 1 2 X i ∈A∪B T ( p ¯ Z n ¯ U i − 1 1 | ¯ U i ) = 1 2 X i ∈A∪B T ( W ( i ) e ) . where (d) h olds sin c e the chan nel p ¯ Z n ¯ U J 1; i − 1 K ∩ ( A∪B ) | ¯ U i is degraded with r e spect to the ch annel p ¯ Z n ¯ U i − 1 1 | ¯ U i . Remark 2: Boun ds 1 an d 2 in Lem m a 5 can be seen as the TV analogu e of the upper boun ds in [3, eq. (77) ] and [1 3, Proposition 1] for M I . Howev er , it does n ot seem possible to prove a lower bou nd fo r the TVD lea k age analogo usly to [13, Proposition 3] due to the fact that TV do es no t tensor ize. I V . W I R E TA P C O D E D E S I G N A. W iretap cod e scheme with vanishing total v a riation leakage Using Lemm a 5 , we can ad apt the wiretap schem e in [3] in order to guar antee vanishing TV leakag e. Pr oposition 2: For β ∈ (0 , 1 / 2 ) and c 1 2 − n β < δ n = o (1 /n ) for some constant c 1 , define G n ( W b ) = { i ∈ J 1; n K : Z ( W ( i ) b ) < 2 − n β /n } , P n ( W e ) = { i ∈ J 1; n K : T ( W ( i ) e ) ≤ δ n } , and let R = J 1; n K \ P n ( W e ) , A = G n ( W b ) ∩ P n ( W e ) , B = P n ( W e ) \ G n ( W b ) . As n → ∞ , the wiretap sch eme ( 6) with p olarizing tran sform G n guaran tee s lim n →∞ S ( M k | Z n ) = 0 , lim n →∞ R s = C ( W b ) − C ( W e ) . Remark 3: Th e T V leak age constraint can be seen as intermediate between the weak secr ecy and th e stro ng secrecy constraint [2, Propo sition 1]. Altho ugh the stro ng secrecy scheme in [ 3] directly gu arantees vanishing TV leakag e by Pinsker’ s inequa lity , and the two schemes h ave the same asymptotic secrecy rate, th e d efinition of the set P n ( W e ) in Proposition 2 is less r estricti ve ( by Lemma 3), an d fo r finite n , the secrecy r ate will in gen e ral be larger . Sketch of pr o o f: Th e argu m ent is almost the same as for the strong secrecy sch e me in [3]. T h e vanishing o f the TV leakage follows fro m Bound 2 in Le mma 5 , since S ( M k | Z n ) ≤ X i ∈P n ( W e ) T ( W ( i ) e ) ≤ n δ n → 0 . Note th at R s = |A| n ≥ |P n ( W e ) | n − | J 1; n K \ G n ( W b ) | n . Recall that [3, The o rem 1] lim n →∞ | J 1; n K \ G n ( W b ) | /n = 1 − C ( W b ) . For β < α < 1 / 2 , de fin e P ′ n = { i ∈ J 1; n K : Z ( W ( i ) e ) ≥ 1 − 2 − n α } . By [3, Coro llary 19], lim n →∞ |P ′ n | /n = 1 − C ( W e ) . Fur- thermor e , by Lemma 3 , ∀ i ∈ P ′ n , T ( W ( i ) e ) ≤ 2 − ( n α − 1) / 2 . Therefo re, for large enough n , P ′ n ⊆ P n ( W e ) and lim n →∞ |P n ( W e ) | /n ≥ lim n →∞ |P ′ n | /n = 1 − C ( W e ) and lim n →∞ R s ≥ C ( W b ) − C ( W e ) . (8) Equality in (8 ) is proven similarly to [3, Propo sition 22] by noting th at G n ( W b ) ∩ P n ( W b ) = ∅ sinc e T ( W ) ≥ C ( W ) ≥ log 2 1+ Z ( W ) by [22, Proposition 1]. Note that similarly to the strong secrecy sche me in [3], we can’t guar antee vanishing err or pr obability for Bob, d ue to the existence of a sm a ll set of un r eliable and insecu re bits. Algorithm 1: W iretap co de d esign. Input : W e , W b , n , ǫ , δ Output: A ⊆ J 1; n K , G = A ∪ R ⊆ J 1; n K ; lower bound R s for the secrecy r at e // Find G = A ∪ R 1 Compute Z ( W ( i ) b ) for i = 1 , . . . , n ; 2 Sort Z ( W ( i ) b ) in i ncreasing order and store the vector of sorting i ndices I b ; 3 k b = max n k ∈ J 1; n K : P k j =1 Z W I b ( j ) b < ǫ o ; 4 G = { I b ( j ) | j = 1 , . . . , k b } ; 5 B = { I b ( j ) | j = k b + 1 , . . . , n } ; // Find A 6 Compute T ( W ( i ) e ) for i ∈ J 1; n K ; 7 Sort { T ( W ( i ) e ) } i ∈G in increasing order and store the vector of sorting indices I e of size k b ; 8 δ 0 = 1 2 P i ∈B T ( W ( i ) e ) ; 9 if δ 0 > δ then 10 k e = 0 ; 11 else 12 k e = max n k ∈ J 1; k b K : δ 0 + 1 2 P k j =1 T W I e ( j ) e < δ o ; 13 end 14 A = { I e ( j ) | j = 1 , . . . , k e } ; 15 R s = k e /n ; B. W iretap co de d esign in fin ite blo c klength In finite b locklength n , we consid e r a simple algo r ithm (Algorithm 1) to choose the sets A , R , B in the polar c o ding scheme so tha t P e ≤ ǫ an d S ( M k | Z n ) ≤ δ . First, the Bhattacharyy a par ameters for Bob’ s bit-ch annels W ( i ) b are computed an d sorted in increasing order; the set G = A ∪ R is cho sen as th e largest po ssible inform a tion set such that th e Bhattacharyy a boun d (7) on the error probab ility is smaller than ǫ . (Alternatively , a Mo nte-Carlo bou nd o n the error probab ility can be used if ǫ > 1 0 − 7 ). Subsequ e ntly , the TVDs for Eve’ s bit-ch annels W ( i ) e are comp uted a nd stored in increa sin g ord er; the set A is ch o sen as the largest p ossible subset of G such that the sum of the TVDs of the bit-c hannels in A ∪ B (Boun d 2 in Lemm a 5) is smaller than δ . V . N U M E R I C A L R E S U LT S A N D D I S C U S S I O N Although th e bou nds in Section II I are valid fo r gen eral BMS chann els, the co m putation o f the TVDs o f the bit- channels is pro blematic in gener al fo r most codes, since the cardin ality of the outp ut alp habet grows exponen tially (althoug h for standard polar c o des, they can b e u pper boun ded using T al and V ardy’ s algor ithm [27]). Therefo re, in order to test different families o f polarizing codes, w e focu s on the case where both W b and W e are BECs with erasu re pro babilities p b < p e . Due to the degradedn ess condition , without loss of generality W e can be seen as the concatenatio n o f W b with a BEC( p 0 ), wh ere p e = p b + (1 − p b ) p 0 . For this model, C s = p e − p b , V b = p b (1 − p b ) , V e = p e (1 − p e ) and the con stant in equ ation (5) is equ al to V c = (1 − p b ) p 0 − (1 − p b ) 2 p 2 0 = ( p e − p b )(1 − ( p e − p b )) . 100 200 300 400 500 600 700 800 900 1000 0 0.05 0.1 0.15 0.2 0.25 0.3 Rate bound 2 - RM bound 2 - Polar bound 2 - RLC bound 2 - MK-16 bound 2 - ABS bound 1 - RM bound 1 - Polar bound 1 - RLC bound 1 - MK-16 bound 1 - ABS Second order upper bound Second order lower bound Secrecy capacity (a) p b = 0 . 05 and p e = 0 . 3 100 200 300 400 500 600 700 800 900 1000 0 0.05 0.1 0.15 0.2 0.25 0.3 0.35 0.4 Rate bound 2 - RM bound 2 - Polar bound 2 - RLC bound 2 - MK-16 bound 2 - ABS bound 1 - RM bound 1 - Polar bound 1 - RLC bound 1 - MK-16 bound 1 - ABS Second order upper bound Second order lower bound Secrecy capacity (b) p b = 0 . 05 and p e = 0 . 4 Fig. 2: Lower secrecy-r ate boun ds for polarizing codes versus secon d-orde r b ounds (3) an d (4) over different degrade d binar y erasure wiretap chan n els with erro r prob ability con straint ǫ = 0 . 00 1 and secrecy constraint δ = 0 . 01 . A. Co m p utation of Bo unds 1 and 2 Note that if W e is a BEC, then all bit-chan nels W ( i ) e are also BECs with p arameters p e,i , and T ( W ( i ) e ) = 1 − p e,i . In this case, Bounds 1 and 2 can be computed b y Monte-Carlo simulation, similarly to [28], for any polarizin g kern el. Let ˜ U n be a permu tation of ¯ U n such that ˜ U n − k b 1 = U B , and ˜ U j = ¯ U I e ( j ) for j = 1 , . . . , k b , with ˜ G n being the cor respondin g column permutatio n of G n . W e want to estimate the erasure parameter ˜ p e,i of the ch annel p Z n ˜ U i − 1 1 | ˜ U i , w h ich is also a BEC for any linea r cod e [28]. Gi ven an erasure pattern E an d the set of unerased position s U = J 1; n K \ E , let ˜ Z U the (perm u ted) output of Eve’ s ch annel restricted to U and G U the r estriction of ˜ G n to th e rows corresp onding to unera sed p ositions. Then, ˜ Z U = ˜ G U , [ 1: n ] ˜ U n 1 = ˜ G U , [ 1: i − 1] ˜ U i − 1 1 + ˜ G U , [ i,n ] ˜ U n i . Supposing that the bits in ˜ U i − 1 1 have been deco ded, b it ˜ U i is unerased if it is p ossible to solve for ˜ U i in the linear system ˜ G U , [ i,n ] ˜ U n i = ˜ Z U ⊕ ˜ G U , [ 1: i − 1] ˜ U i − 1 1 , or equiv alently if r ank F 2 ( ˜ G U , [ i,n ] ) = rank F 2 ( ˜ G U , [ i +1 ,n ] ) + 1 . W e estimate ˜ p e,i by averaging over ma ny ra n dom BEC( p e ) erasure pattern s. Th e co de design is de scr ibed in Algorithm 1 for Bound 2; it can be mod ified fo r Bound 1 by rep lacing T ( W ( i ) e ) with ˜ p e,i in lin e s 8 and 1 2. B. P olarizing codes W e ev aluate our co ntruction for different families of polar- izing co des, namely Polar, Mu lti-kernel (MK), ABS, Reed- Muller (RM) and Rand om Linear (RL) cod es. RM codes h ave the same matrix G n of polar cod es, h owe ver the columns are reorder e d in inc r easing weight o r der; this leads to a faster polariza tion [16], but makes the decoding unfeasible f or mid- r ange rates. MK cod es are constructed by combinin g d ifferent kernels; in par ticular , we use the G 16 kernel in [29] in comb ination with Ar ikan’ s kernel G 2 . This larger kernel p ermits to ach iev e a better polariza tio n rate th an polar codes, ev en if n ot as good as the one o f RM co des, but entails a larger d ecoding com plexity than polar codes [30]. ABS cod es [1 8] rep resent a comp romise between po lar and MK cod es, having an intermed iate polarization rate b etween the two codes but decod ing complexity that is still man age- able. W e adap t ABS cod es to th e wiretap case by swapping bits i an d i + 1 in the r e c ursiv e construc tion o nly when it acceler a tes p olarization for b oth W b and W e , i.e. whe n T ( W ( i ) e ) ≥ T ( W ( i +1) e ) and C ( W ( i ) b ) ≥ C ( W ( i +1) b ) . Finally , RL co des, b a sed on a ran dom Berno ulli invertible matrix, up per-bound p olarizing code secr ecy with optimal polarization but impr a ctical deco ding [26]. C. Lower bounds o n the achievable secr ecy rates Figure 2 shows the lower bou nds on the secrecy rate R s computed u sing Bou nds 1 an d 2 fo r the po larizing co des introdu c ed previously . W e consider a fixed BEC( 0 . 05 ) fo r Bob, and we pr opose two scenarios f or Eve, n a m ely a BEC( 0 . 3 ) and a BEC( 0 . 4 ); in both cases, we imp ose an error prob a bility constraint ǫ = 0 . 001 and a secrecy con straint δ = 0 . 01 . Note that Bounds 1 and 2 are almo st the same f or RM and RL codes, due to the fact that the virtual bit-ch annels are m ostly or dered in reliability or der , an d th e set R u sually includes the last elemen ts o f J 1; n K . Moreover , RL codes achieve a better secrecy rate than RM code s, having a better polarization rate; their perfor mance co mes close to the lower bound (4) for the second order secrecy rate. W e c o njecture that th e lower boun d (4) is tighter th a n th e up per bou nd (3 ). On the other han d, ABS, Po la r and MK cod es exhibit a gap between Bound 1 an d 2 ; in this case, the r eorderin g of elemen ts in G for the calculation o f Bound 1 p ermits to slightly decr ease the TVD bou n ds for the elemen ts in A , allowing for the in troduction of b it-channels that were inclu ded in R f o r Bound 2. These re su lts suggest that ABS cod es strike a balan ce between achievable secrecy rate and deco ding complexity , o utperfor ming p olar code s while rem aining more practical than MK and RM co des. R E F E R E N C E S [1] A . D. W yner , “The wire-tap channel , ” B ell System T echni cal Journa l , vol. 54, pp. 1355–1387, Oct. 1975. [2] M. R. Bloch and J. N. Laneman, “Strong secrec y from channel resolv- abili ty , ” IEE E T rans. Inf. Theory , vol. 59, no. 12, Dec 2013. [3] H . Mahdav ifar and A. V ardy , “ Achiev ing the secrecy capacit y of wiretap channe ls using polar codes, ” IEEE T rans. Inf. Theory , vol. 57, no. 10, Oct 2011. [4] Y . Polyanskiy , H . V . Poor , and S. V erd ´ u, “Channel coding rate in the finite blockleng th regime, ” IEE E T ransacti ons on Information Theory , vol. 56, no. 5, pp. 2307–2359, 2010. [5] W . Y ang, R. F . Schaefe r , and H. V . Poor , “W iretap channels: Nonasymp- totic fundament al limits, ” IEEE T ransactions on Information Theory , vol. 65, no. 7, pp. 4069–4093, 2019. [6] J . P fi s ter , M. A. Gomes, J. P . V ilela, and W . K. Harrison, “Quantifying equi vocatio n for finite block length wiretap codes, ” in IEEE Internat ional Confer ence on Communicat ions (ICC) , 2017, pp. 1–6. [7] W . K. Har rison, “Exact equ i voca tion expr essions for wireta p coding ov er erasure channel models, ” IEEE Communicat ions Letter s , vol. 24, no. 12, pp. 2687–2691, 2020. [8] A . Nooraiepour , S. R. Aghdam, and T . M. Duman, “On s ecure commu- nicat ions over Gaussian wiretap channels via finite-len gth codes, ” IEEE Communicat ions Letters , vol. 24, no. 9, pp. 1904–1908, 2020. [9] R. Fritschek, R. F . Schaefer , and G. Wun der , “Deep learning based wiretap coding via mutual information estimati on, ” in Pr oceedings of the 2nd ACM W orkshop on W ireless Security and Machine L earning , 2020, pp. 74–79. [10] K. -L. Besser , P .-H. Lin, C. R. Janda, and E. A. Jorswieck, “Wi retap code design by neural net work autoe ncoders, ” IEEE T ransactio ns on Informatio n F orensics and Security , vol. 15, pp. 3374–3386, 2020. [11] V . Rana and R. A. Chou, “Short blockle ngth wiretap channel codes via deep learning : Design and performance e valuat ion, ” IEEE T ransaction s on Communications , vol. 71, no. 3, pp. 1462–1474, 2023. [12] K. T aleb and M. Benammar , “On the informat ion leaka ge of finite block-l ength wiretap polar codes, ” in IE EE Internatio nal Symposium on Information Theory (ISIT) , 2021, pp. 61–65. [13] H. Mahdav ifar and F . Abbasi, “Finite-le ngth ana lysis of polar secrecy codes for wiretap channels, ” in 2024 IEEE International Symposium on Informatio n Theory (ISIT) . IEEE, 2024, pp. 2951–2956. [14] M. Shakiba-He rfeh, L . Luzzi, and A. Chorti, “Finit e blocklength secrecy analysi s of polar and Reed-Mull er codes in BEC semi-determini stic wiretap channels, ” in IEEE Information Theory W orkshop (ITW) , 2021. [15] H. -Y . Lin, Y .-S. Su, and M.-C. Chiu, “ Achie ving optimal short- blockle ngth secr ecy rate using multi-k ernel P A C codes for the binary erasure wiretap channel , ” arXiv pre print arXiv:2409.00852 , 2024. [16] E . Abbe and M. Y e, “Reed-Mulle r codes polarize , ” IEEE T ransactions on Information Theory , vol. 66, no. 12, pp. 7311–7332, 2020. [17] V . Bioglio, F . Gabry , I. Land, and J.-C. Belfiore, “Mult i-ke rnel polar codes: Concept and design principles, ” IEEE T ransacti ons on Commu- nicati ons , vol. 68, no. 9, pp. 5350–5362, 2020. [18] G. L i, M. Y e, and S. Hu, “ Adjacent -bits-swa pped pola r codes: A new code construction to speed up polariz ation, ” IEEE T ransactions on Informatio n Theory , vol. 69, no. 4, pp. 2269–2299, 2022. [19] R. G. Gallager , Informatio n Theory and R eliabl e Communicati on . Wi - ley , 1968. [20] Y . Polyanskiy and Y . Wu, Informati on theory: F rom coding to learning . Cambridge Univ ersity Press, 2025. [21] I. Csisz ´ ar , “ A class of measures of informati vity of observ ation chan- nels, ” P eriodica Mathematica Hungarica , vol. 2, no. 1-4, pp. 191–213, 1972. [22] E . Arikan, “Channel polarizati on: a method for construct ing capacity- achie ving codes for symmetric binary-input memoryle s s channels, ” IEE E T rans. Inf. Theory , vol. 55, no. 7, pp. 3051–3073, 2009. [23] M. Alsan, “Re-provi ng channel polariza tion theorems: An ext remal- ity and robustne ss analysis, ” Ph.D. dissertat ion, ´ Ecole Polytechnique F ´ ed ´ erale de Lausanne, 2014. [24] S. L eung-Y an-Cheong, “On a special class of wiretap channe ls, ” IE EE T ransactio ns on Information Theory , vol. 23, no. 5, pp. 625–627, 2003. [25] E . Arikan and E . T elatar , “On the rate of channel polarizat ion, ” in IEEE Internati onal Symposium on Information Theory , 2009, pp. 1493–1495. [26] A. Faze li, H. Hassani, M. Mondelli , and A. V ardy , “Binary linea r codes with opti mal scaling: Polar codes wit h large k ernels, ” IEE E T ransactions on Information Theory , vol. 67, no. 9, pp. 5693–5710, 2020. [27] I. T al and A. V ardy , “Ho w to construct polar codes, ” IEEE T ransactions on Information Theory , vol. 59, no. 10, pp. 6562–6582, 2013. [28] A. Fazeli and A. V ardy , “On the scaling exponent of binary polarizatio n kerne ls, ” in 2014 52nd Annual Allerton Confer ence on Communicat ion, Contr ol, and Computing (Allerton) . IEEE, 2014, pp. 797–804. [29] H. Y ao, A. Faze li, and A. V ardy , “Explicit polar codes wit h small scali ng expo nent, ” in 2019 IEE E Internat ional Symposium on Informati on Theory (ISIT) . IEEE, 2019, pp. 1757–1761. [30] V . Bioglio, G. D. B. Rov ella, and M. Benammar , “Neural network decodin g of polar codes with large kernels, ” in 2025 13th Internation al Symposium on T opics in Coding (ISTC) , 2025, pp. 1–5.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment