Hidden Elo: Private Matchmaking through Encrypted Rating Systems
Matchmaking has become a prevalent part in contemporary applications, being used in dating apps, social media, online games, contact tracing and in various other use-cases. However, most implementations of matchmaking require the collection of sensit…
Authors: Mindaugas Budzys, Bin Liu, Antonis Michalas
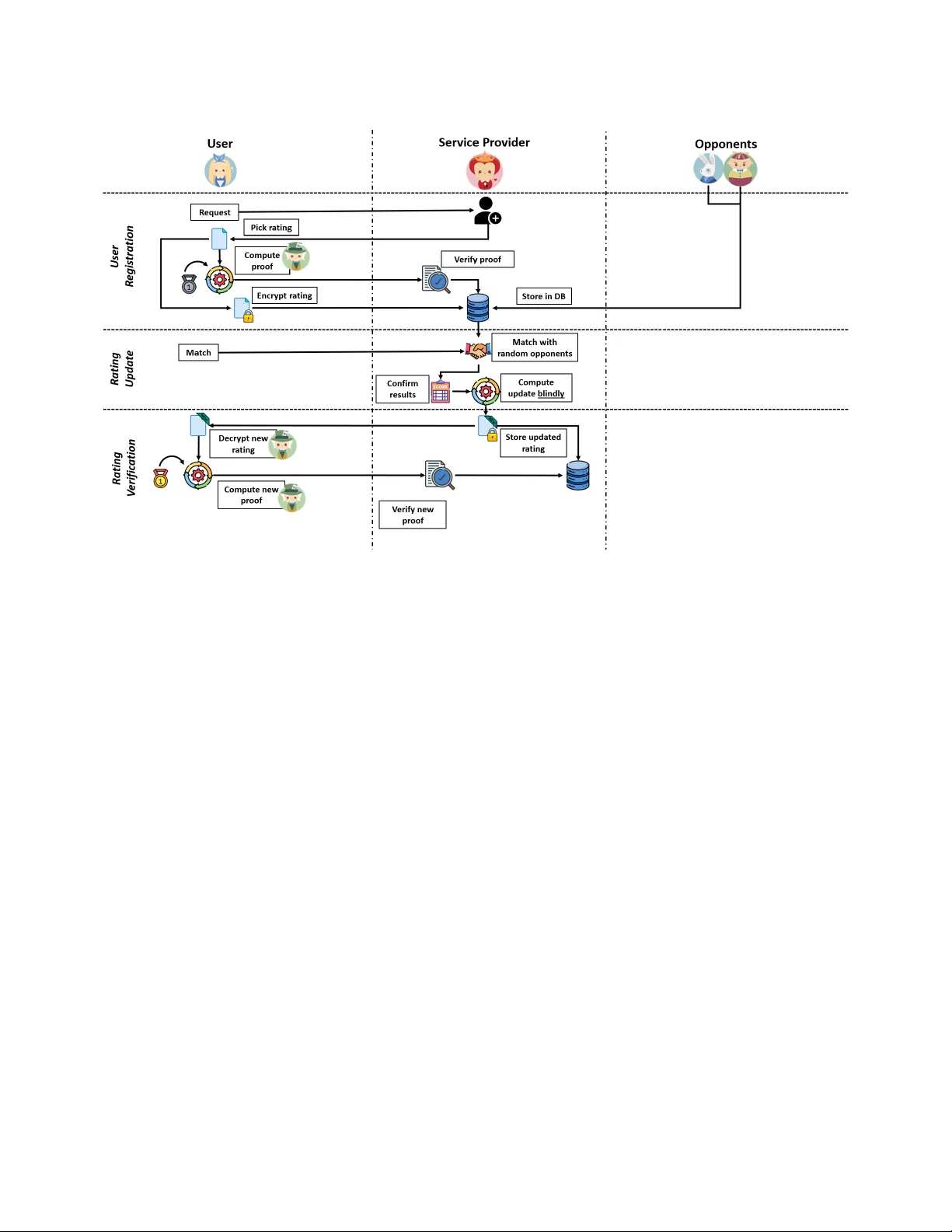
Hidden Elo: Private Matchmaking through Encrypted Rating Systems Mindaugas Budzys T ampere University T ampere, Finland mindaugas.budzys@tuni. Bin Liu ∗ T ampere University T ampere, Finland bin.liu@tuni.f i Antonis Michalas T ampere University T ampere, Finland antonios.michalas@tuni.f i Abstract Matchmaking has become a prevalent part in contemporary applica- tions, being used in dating apps, social media, online games, contact tracing and in various other use-cases. However , most implementa- tions of matchmaking require the collection of sensitiv e/p ersonal data for proper functionality . As such, with this work we aim to re- duce the privacy leakage inherent in matchmaking applications. W e propose H-Elo , a Fully Homomorphic Encryption (FHE)-based, pri- vate rating system, which allows for secure matchmaking through the use of traditional rating systems. In this work, we pro vide the construction of H-Elo , analyse the security of it against a capable adversary as well as benchmark our construction in a chess-based rating update scenario. Through our experiments we show that H-Elo can achieve similar accuracy to a plaintext implementation, while keeping rating values private and secure. Additionally , we compare our work to other private matchmaking solutions as well as cov er some future directions in the eld of private matchmaking. T o the b est of our knowledge we provide one of the rst private and secure rating system-based matchmaking protocols. CCS Concepts • Security and privacy → Public key (asymmetric) techniques ; Privacy-preserving pr oto cols . Ke y words fully homomorphic encryption, zer o-knowledge proofs, matchmak- ing, applied cryptography A CM Reference Format: Mindaugas Budzys, Bin Liu, and Antonis Michalas. 2026. Hidden Elo: Private Matchmaking through Encrypted Rating Systems. In Proceedings of the Sixteenth ACM Conference on Data and Application Security and Privacy (COD ASPY ’26), June 23–25, 2026, Frankfurt am Main, Germany . A CM, New Y ork, NY, USA, 16 pages. https://doi.org/10.1145/3800506.3803498 1 Introduction In the current digital era, a wide range of applications and commu- nications have moved to online spaces. As such, a larger emphasis is made on making professional or personal connections through online services. Notably , making conne ctions has b ecome easier ∗ Also with grchain.io. This work is licensed under a Creativ e Commons Attribution 4.0 International License. CODASPY ’26, Frankfurt am Main, Germany © 2026 Copyright held by the owner/author(s). ACM ISBN 979-8-4007-2562-3/2026/06 https://doi.org/10.1145/3800506.3803498 due to matchmaking services available on social media, dating apps or in online games. One of the ways, to implement matchmaking is by using a rating system, such as the Elo rating system [24]. In this case, players are matched with each other dep ending on their respective ratings. This form of matchmaking with rating systems have been used in a variety of zero-sum games, such as chess, traditional sports and e-sports. Additionally , the Elo system has been used in ecological studies [40] and articial intelligence evaluation [9]. In most applications, the rating is calculated by a server and revealed publicly to all parties. While this approach is convenient, it introduces some notable drawbacks and privacy concerns in matchmaking. Namely , in some cases the ratings are hidden from users and only the server has access to it, leaving users in the dark of their rating, such as in the case of the previous Tinder algorithm [46]. Additionally , rating systems have drawn criticism for b eing easy to e xploit for selective pairing [48], where a player can aim to sear ch for opponents wher e they maximize gains and minimize losses, especially when players can choose their o wn opponents. Alongside this, revealing the exact rating of a person can introduce ways for malicious parties to mon- itor specic user ratings and identify patterns in their behaviour . Due to these reasons, there is a clear need for securing rating cal- culations, allowing people to know their exact rating while being able to fairly match with opponents and avoid prying eyes. T o address these issues and encourage further research into pri- vate matchmaking through rating systems, we propose Hidden Elo ( H-Elo ) – a Fully Homomorphic Encryption (FHE)-based protocol for rating updates and verication. More specically , we make use of the Cheon-Kim-Kim-Song Residual Number System (CKKS- RNS) [15] FHE scheme (we explain our rationale for choosing CKKS- RNS in Appendix A) as well as Zer o-Knowledge Proofs (ZKPs) to implement a matchmaking protocol, which hides a user’s rating from other parties, while updating the rating correctly through a central ser vice provider . W e show that H-Elo allows for private rating-based matchmaking with reasonable accuracy by implement- ing and testing the rating update of our approach. Contributions. The main contributions of this paper can be sum- marized as follows: C1. W e pr op ose H-Elo , one of the rst private and secure rating system-based matchmaking protocols. W e achie ve this by mak- ing use of FHE to allow blind calculations of a rating update after a number of matches. Our construction uses lattice-based cryptography and therefore achieves post-quantum security . Additionally , our construction leverages ZKPs to reveal the minimum information needed to allow proper matchmaking, while keeping the actual ratings private. CODASPY ’26, June 23–25, 2026, Frankfurt am Main, Germany Mindaugas Budzys, Bin Liu, and Antonis Michalas C2. W e provide an extensive security analysis, which prov es, that H-Elo holds security notions for providing fair matchmaking as well as keeping the true rating hidden from a semi-honest adversary . C3. W e implement the FHE rating update of H-Elo and run bench- marks on the implementation. Through our evaluation we analyse the runtime and memory costs of H-Elo as well as compare the accuracy of the rating update to plaintext com- putations. W e show that our approach has reasonable run- time results for users using standard HE security parameters. Additionally , we show that our approach provides negligible deviation from the exact rating calculated on plaintext even after 10,000 consecutive updates. C4. Finally , we study existing w orks in the area of private match- making and identify that only Matchmaking Encryption (ME) [10] can be compared, in a meaningful and fair way , to this work. T o this end, we provide the rst systematic comparison between ME and an FHE-based, post-quantum-secure matchmaking protocol, highlighting dierences in trust assumptions, secu- rity guarantees, and performance. Organization. The rest of the paper is organized as follows. In Section 2 we cover the possible usecases of our approach covering the areas where H-Elo can be used. In Se ction 3 we cover the re- lated work in the eld, covering some of the rating systems that exist as well as private and secure matchmaking solutions currently available in literature. In Section 4 we introduce the cryptographic primitives which we make use of in our construction, and in Sec- tion 5 we pro vide the detailed construction of H-Elo . Afterwards, Section 6 covers the thr eat model and security analysis of H-Elo . W e implement our benchmarking usecase and cover the results in Section 7. Finally , we pro vide our conclusions and cover future work in Section 8. 2 Application Domain Matchmaking is a core system in the curr ent digital world, allowing two or more users to match with each other through common inter- ests in social media or by having similar skill levels in online games. Howev er , as these systems evolve and become more complex the inner workings of them become inaccessible or incomprehensible to users, all the while requiring large amounts of personal data or user activity to operate. As such, it is natural for people to want to protect sharing their private information with matchmaking services while retaining the functionality of these services. Through H-Elo , we aim to pr ovide similar functionality as the plaintext implementation by matching users with similar skill le vels based on rating systems, while keeping the rating secure on the client side. Consequently , such functionality w ould allow various real w orld usecases to b e implemented in a more privacy-conscious way . These use-cases could include: (i) implementing social media functionalities, such as forming professional or personal connec- tions with people, without directly sharing their personal data to the service provider; (ii) implementing online game matchmaking, where a user can know their true rating and hav e fair matchmak- ing by avoiding selective pairing; (iii) implementing reputations systems in marketplaces, where users and seller may vote on each others reputation without revealing the exact reputation but a gen- eralization of how the seller or buyer is perceived. 3 Related W ork 3.1 Elo and Traditional Rating Systems In the 1950s, Arpad Elo developed the fundamental theory , which eventually became the U.S. Chess Federations ( USCF) rating sys- tem. This version as well as a modication of it designed by Glick- man [24] is still used to this day in modern chess skill rating. This system adopted the name of the founder and is known as the "Elo rating system" [26]. The goal of the system is to calculate the likeli- hood of a player winning against their opponent and compare it to the actual result of the game . If a player with a lower rating wins against an opponent with a higher one , then the player "beat the odds" and gains a larger increase in their rating. On the other hand, the loss of rating is smaller if the likelihood to win was lower . In addition to the Elo rating system, other rating systems have also been adopted throughout history , such as Glicko [25], which introduce a variable for uncertainty in the player’s skill. More specically , uncertainty shows the possible deviation of the player’s skill, where a player with high uncertainty will lose or gain rating faster than those with low uncertainty . T o the best of our knowledge, ther e are no works analysing se- cure utilisation of rating systems, however there are works analysing how to perform secure matchmaking through Functional Encryp- tion (FE) constructions, such as Attribute-based Encr yption (ABE) and ME, or through Private Set Intersection (PSI) solutions. 3.2 Functional Encr yption (FE) FE refers to public-key encryption schemes, which allows a spe- cic function to be computed on a ciphertext through the use of a decryption key . This term was generalized by Boneh et al. [13] and ever since then, the eld has e xpande d to dierent function with the most notable ones being computing dot products with Inner- Product FE (IPFE) [1] and computing quadratic equations through Quadratic FE (QFE) [4]. More recently , there has b een a push by researchers to dev elop FE constructions that expand the function- ality of FE to allow qualitative analysis of encr ypted data [37] with selective, partial decryption. 3.2.1 Aribute-based Encryption (ABE). One typ e of FE construc- tions focused on ne-graine d access control on who would be able to decrypt a ciphertext. This initially started as Identity-Base d En- cryption (IBE) [45], which was later expanded to Ciphertext-Policy ABE (CP- ABE) by Sahai and W aters [44]. CP- ABE allowed identi- fying users not just through a string of characters like in IBE, but through a set of descriptive attributes. In turn CP- ABE associated these sets of attributes to a generated de cryption key which was then able to decrypt a ciphertext that had an equivalent access policy associated with it. Later on, researchers constructe d Key-Policy ABE (KP- ABE) [28] following an inverse construction than CP- ABE, namely where the decryption keys are associate d with the access policy , while the ciphertexts are associated with the encrypters attributes. In b oth KP- ABE and CP- ABE pow er is given to a single entity (users in CP- ABE or the trusted authority in KP-ABE) who denes who can access Hidden Elo CODASPY ’26, June 23–25, 2026, Frankfurt am Main, Germany what data. Additionally , in both methods a mismatch between the attributes and the policy rev eals them to the querier [11]. Due to this, Ateniese et al. proposed Matchmaking Encryption (ME) [10]. 3.2.2 Matchmaking Encryption. ME is a spe cial case of ABE, wher e both sender and receiver (who hav e individual attributes) can set their own required policies for a message to b e revealed. More specically , ME allows for both the sender and the receiver to set their o wn policies S and R , r espe ctively . Next, the sender associates his own attributes 𝜎 as well as policy S to the ciphertext 𝑐 . Then, a receiver with attributes 𝜌 and policy R are matched against S and 𝜎 in 𝑐 , if all attributes match the policies, then the receiver can decrypt 𝑐 , otherwise an error occurs and no one learns anything aside from the fact that there was a attribute mismatch. ME gives the ability for both sender and receiver to dene their attributes and their own policy . Through this, a ciphertext can be decr ypted only when a match occurs and both user attributes match each others policy . Additionally , ME addresses the issue of attribute/policy hiding and prevents this information leak when an attribute mismatch occurs during decr yption. While ME is a highly important step for providing a solution for secure matchmaking, it has noticeable drawbacks within it. Some of these include the strong assumptions required in constructing ME, making it impractical to implement. While these assumptions can be lowered to a weaker version, they r esults in a lowered security guarantee which can only support a bounded number of queries. This results in ME not being applicable to situations wher e users would wish to arbitrarily match with multiple users. 3.3 Private Set Intersection (PSI) PSI is a cryptographic method that enables parties to compute the intersection of their private input sets without revealing any information beyond the intersection [39]. In a PSI protocol, two or more parties can compute the intersection of their private input sets while ensuring that the elements not in the intersection remain private. PSI has a wide range of applications, including contact tracing [50] and matchmaking applications [30]. PSI has several variants, each dened by the inputs, outputs, and interactions among the parties involved. Each variant has specic requirements to consider when designing and implementing proto- cols. For instance, in traditional PSI, one or both parties learn the intersection of their input sets [39]. In contrast, some protocols may compute a function based on the intersection without revealing the intersection itself [22]. Additionally , specic protocols may require prior authorization for elements in the sets or impose a threshold on the intersection size before producing the output [35]. Several cryptographic techniques are commonly employed to enhance the eciency and se curity of PSI protocols. Examples of cryptographic techniques used include Hashing [38], Oblivious Transfer [41], Homomorphic Encr yption [19], Garbled Circuits [39] and Oblivious Pseudo-Random Functions [32]. Hashing improves eciency by mapping set items into bins, signicantly reducing computational overhead, though it requires car eful parameter selec- tion to avoid collisions. Oblivious Transfer (OT) enables secure two- party computation, allowing a receiver to obtain one of many data pieces without the sender knowing which was chosen. However , it may require multiple communication rounds [41]. HE allows com- putations on encrypte d data without decr yption, enabling complex secure operations at the cost of high computational overhead [19]. Garbled Circuits facilitate secure function evaluation on private inputs but can be less ecient than specialize d PSI protocols [39]. Finally , Oblivious Pseudo-Random Functions (OPRFs) securely gener- ate pseudo-random values for PSI, balancing eciency and security while requiring careful design to resist attacks. PSI protocols have ev olved since their initial introduction. Per- formance has been a central focus, as PSI protocols are known to be computationally intensive. Despite progr ess in performance, these protocols remain complex and require careful instantiation, con- sidering platform-specic characteristics like computation limits, bandwidth, or network delay . 4 Preliminaries 4.1 Elo Rating System The system aims to calculate the likelihood of a player winning against their opponent and compare it to the result of the game. Traditionally , a new rating in the Elo system is calculated as such: 𝑅 ′ = 𝑅 𝑝𝑟 𝑒 𝑣 + 𝐾 · ( 𝑆 𝑟 𝑒 𝑎𝑙 − 𝑆 𝑒 𝑥 𝑝 ) (1) where 𝑅 𝑝𝑟 𝑒 𝑣 and 𝑅 ′ refers to the player’s pr evious and new rating, respectively; 𝐾 is a K-factor , used for linear score adjustments; 𝑆 𝑟 𝑒 𝑎𝑙 and 𝑆 𝑒 𝑥 𝑝 are the real and expecte d outcome of the match for the player . 𝑆 𝑒 𝑥 𝑝 is calculated with the following equation: 𝑆 𝑒 𝑥 𝑝 = 1 1 + 10 ( 𝑅 𝑜 𝑝 𝑝 − 𝑅 𝑝𝑙 𝑎 𝑦𝑒 𝑟 ) / 400 (2) where 𝑅 𝑜 𝑝 𝑝 and 𝑅 𝑝𝑙 𝑎 𝑦𝑒 𝑟 are the Elo ratings of the opp onent and player , respectively . 4.2 Homomorphic Encr yption HE relies on the property of homomorphism, more specically “privacy homomorphism” . This property allows computation on encrypted data and was initially theorize d by Rivest, Adleman, and Dertouzos [42] for the RSA cryptosystem to allow p erforming arith- metic multiplications on ciphertexts. This type of encryption was further expanded into Fully HE (FHE) by Craig Gentry in 2009 [23] and allowed an unbound number of multiplications and additions on a ciphertext. However , due to the costs imposed by the bo otstrap- ping algorithm, researched turned towards limiting the numb er operations to avoid computing the bootstrapping step. This led to Levelled HE (LHE) schemes, such as BGV [14], B/F V [20], CKKS [17] and some FHE schemes, e.g. TFHE [18], to be pr op osed. The eld continued to be developed and allowed LHE schemes to be ex- panded into FHE schemes, such as in the case of CKKS-RNS [15], which allow e d bootstrapping on the CKKS scheme. While there are dierences between HE schemes, all of them rely on the same core algorithms, which can be dened as: Definition 1 (Homomorphic Encryption). Let HE for message space M , ciphertext space C and class of functions F : M 𝑛 → M , 𝑛 ∈ N ∗ , be a homomorphic encr yption scheme with a quadruple of PPT algorithms HE = ( KeyGen , Enc , Eval , Dec ) such that: CODASPY ’26, June 23–25, 2026, Frankfurt am Main, Germany Mindaugas Budzys, Bin Liu, and Antonis Michalas • HE . KeyGen ( 1 𝜆 ) – a probabilistic algorithm, that takes as input the security parameter 𝜆 , and outputs a public key pk , a private key sk , and an evaluation key evk . • HE . Enc ( pk , 𝑥 ) – a probabilistic algorithm, that takes as input the public key pk and a message 𝑥 ∈ M and outputs a ciphertext 𝑐 ∈ C , where 𝑥 is encoded into a polynomial representation. • HE . Eval ( evk , 𝑓 , 𝑐 1 , . . . , 𝑐 𝑛 ) – a probabilistic algorithm, that takes as input the evaluation key evk , a function 𝑓 , and a set of 𝑛 ciphertexts, and outputs a ciphertext 𝑐 𝑓 . • HE . Dec ( sk , 𝑐 ) – a deterministic algorithm, that takes as input the secret key sk and a ciphertext 𝑐 , and outputs a plaintext 𝑥 . Correctness : For all parameters 𝜆 ∈ N , 𝑛 ∈ N ∗ , ( pk , sk , evk ) ← $ HE . KeyGen 1 𝜆 , 𝑓 ∈ F and ciphertexts 𝑐 𝑖 ← $ HE . Enc ( pk , 𝑥 𝑖 ) , 𝑥 𝑖 ∈ M , 𝑖 ∈ [ 𝑛 ] , P [ HE . Dec ( sk , HE . Eval ( evk , 𝑓 , ( 𝑐 1 , . . . , 𝑐 𝑛 ) ) ) = 𝑓 ( 𝑥 1 , . . . , 𝑥 𝑛 ) + 𝛿 ] = 𝑛𝑒𝑔𝑙 ( 𝜆 ) where 𝛿 is a small value (or noise) that depends on the scaling factor ∆ ∈ N . If HE is such that 𝛿 always vanishes, HE is said to b e exact. Otherwise, it is called approximate. 4.2.1 Che on-Kim-Kim-Song (CKKS) Scheme. The CKKS scheme [17], proposed by Cheon et al. , is the rst HE scheme which enables en- crypted arithmetic computations on approximate numbers. Through the use of CKKS a user can encrypt real numbers ( 𝑥 ∈ R ) and per- form standard arithmetic, such as addition, subtraction and multipli- cation. Additionally , the construction allows for ciphertext rotations without necessitating de cryption. The scheme was a major advance- ment from previous HE schemes, such as BGV [14] and B/FV [20], which allowed the same operations only on integer plaintexts. Sim- ilarly as the aforementioned integer HE schemes, CKKS is based on the quantum-resistant, lattice-based Ring Learning with Error (RLWE) problem pr oviding security guarantees against quantum security threats. Also, with advances in CKKS bootstrapping [15], it allows high precision computations without having to rely on re-encryption to reduce noise while having lower latency than bootstrapping with the BGV scheme [5]. Similarly to other HE schemes, CKKS ciphertexts accumulate noise after each arithmetic op erations. As such, CKKS employs three techniques for noise management, namely modulus switch- ing, scaling and relinearization. Modulus switching is a technique that changes the modulo of a ciphertext 𝑐 𝑡 from 𝑞 to a value of 𝑞 ′ < 𝑞 . This avoids quadratic noise blowup and keeps the noise level constant after multiplications [31]. In addition to modulus switching, CKKS has to perform r escaling. Namely , as CKKS cipher- text are multiplied by a scale factor ∆ , this leads to multiplications of two cipherte xt increasing the factor e xp onentially . As this results in modulus overows and diminishes the precision, CKKS requires rescaling by dividing the ciphertext by 1 ∆ after each multiplica- tion [3]. Lastly , relinearization is a technique to reduce the degree of a ciphertext, namely multiplications increases the degree of the ciphertext from degree-1 to degr ee-2, which increases the size of the ciphertext making future operations mor e expensive [31]. Through relinearization this degree is once again r e duced to a lower value by using a relinearization key rlk . Another important functionality of CKKS is batching [29], which allows encrypting multiple data points with a single encryption (i.e . encrypting an array of data points) and performing computations on each point at the same time. With this functionality CKKS can utilize Single Instruction, Multiple Data (SIMD) parallelism, which increases the speed as multiple operations can be done simultane- ously . On the other hand, CKKS also supports sparse packing [16], which reduces the amount of slots available to encode plaintext values into a ciphertext. While this does not provide benets for reducing computation time as in the case of batching, ho wever , it reduces the memory footprint of the cr yptographic context. 4.3 Range Proof with Commitment-Ciphertext Consistency Zero-Knowledge Proofs (ZKPs) are cryptographic protocols, which allow a prover to convince a v erier that a statement is true without revealing any information beyond the validity of that statement. Since the seminal work of Goldwasser et al. in [27], ZKPs have become a cornerstone of mo dern cr yptography and are widely used in privacy-preserving authentication and identication [43], machine learning [49], and veriable computation [12] protocols. Classical ZKPs are interactive: the prover and the verier ex- change multiple messages. In many practical settings, particularly those require public veriability or verication in an asynchronous manner , such interaction is undesirable. This motivates the study of Non-Interactive Zer o-Knowledge Arguments 1 (NIZKs), in which a single proof is generated and can b e veried without interaction. NIZKs are commonly obtained by applying the Fiat-Shamir heuris- tic [21] to an interactive public-coin proof system, or designed directly in the common reference string (CRS) model. In this work, we require the NIZKs to be knowledge sound (extractable) and therefore the y are NIZK arguments of knowledge. For simplicity , we still use NIZK to denote such knowledge sound arguments. Let R ⊆ { 0 , 1 } ∗ × { 0 , 1 } ∗ be an NP relation and let L = { 𝑥 | ∃ 𝜔 : ( 𝑥 , 𝜔 ) ∈ R } be its corresponding language. Formally , a NIZK is dened as follows. Definition 2 (Non-Interactive Zero -Knowledge Argument, NIZK). A NIZK for a r elation R consists of a triplet of PPT algorithms NIZK = ( Setup , Prove , V erify ) , where: • NIZK . Setup (1 𝜆 , R ) → ( pk , vk ) : takes as input the se curity param- eter 𝜆 and the NP relation R , and outputs a proving key pk and a verifying key vk . • NIZK . Prove ( pk , 𝑥 , 𝜔 ) → 𝜋 : takes as input the proving key pk , a statement 𝑥 and a witness 𝜔 , and outputs a proof 𝜋 . • NIZK . V erify ( vk , 𝑥 , 𝜋 ) → { 0 , 1 } : takes as input the verifying key vk , a statement 𝑥 and a proof 𝜋 , and outputs 1 if the proof is valid for 𝑥 and 0 otherwise. Additionally , a NIZK argument system must satisfy the following properties: (1) Completeness. For all ( 𝑥 , 𝜔 ) ∈ R , an honest prov er using pk produces a proof 𝜋 such that the verier using vk accepts with probability 1 . (2) Zero-knowledge. There exists a PPT simulator , which given ( pk , vk ) but without access to witnesses, can generate proofs that are computationally indistinguishable from real proofs produced with witnesses. 1 When a proof system is only computationally sound, it is called an argument. Hidden Elo CODASPY ’26, June 23–25, 2026, Frankfurt am Main, Germany (3) Knowledge Soundness ( extractability). If any PPT adversary can produce a valid proof for a statement 𝑥 with non-negligible probability , then there exists an PPT extractor such that it is able to recover a valid witness for 𝑥 given access to the adversary except with negligible probability . Range proofs are a specialized class of ZKPs in which a prov er convinces a verier that a secret value, which may be presented in either commitment-based or encryption-based form, lies within a prescribed interval without revealing any additional information about the value itself. Such proofs are fundamental to privacy- preserving nancial applications, access control mechanisms and various consistency checks, where one needs to ensure the secret values respect some certain range. Although range proofs can be constructed in interactiv e form, in this work we only fo cus on the non-interactive setting, since our construction requires proofs that can be generate d once and subsequently veried without any further interaction. Accordingly , throughout this paper we invoke the standard NIZK algorithms di- rectly when employing range proofs in our protocols. Additionally , knowledge soundness guarantees that any prover that produces a valid proof must know a witness consistent with the relation. It is crucial for binding the underlying value of the ciphertext and the subsequent homomorphic computation over the ciphertext. In order to present the denition of range pr oofs, we rely on a commitment scheme Com = ( KeyGen , Commit , Open ) that is both binding and hiding . Definition 3 (Range Proof). Let ppc denote the commitment parameters and 𝑟 denote the randomness used for generating the com- mitment. Given integers 𝑎, 𝑏 , 𝑣 ∈ Z with 𝑎 ≤ 𝑣 < 𝑏 and a commitment scheme Com = ( KeyGen , Commit , Open ) , we dene the following NP relation: R range = { ( 𝑥 , 𝜔 ) | 𝑥 = ( ppc , 𝐶 , 𝑎, 𝑏 ) , 𝜔 = ( 𝑣 , 𝑟 ) , 𝐶 = Commit ppc ( 𝑣 ; 𝑟 ) ∧ 𝑎 ≤ 𝑣 < 𝑏 } . A (non-interactive) range proof is a NIZK argument for the relation R range . In addition to prove that a committed Elo value lies in a certain interval, w e still need to bind this value to the homomorphic cipher- text that the server will later update. Otherwise, a malicious user could present a valid range proof for some sp ecied value while providing a ciphertext that encrypts a dierent value to bypass the rank restrictions. Following the commitment and proof of equivalence paradigm in [34] but adapting it to our setting, w e dene the following NP relation R 𝑟 𝑐 𝑐𝑐 : Definition 4 (Range Proof with Commitment-Ciphertext Consistency). Let 𝑟 , 𝑟 ′ denote the randomness used for generating the commitment and encr yption, respectively . Given integers 𝑎, 𝑣 , 𝑏 ∈ Z with 𝑎 ≤ 𝑣 < 𝑏 , a commitment scheme Com = ( KeyGen , Commit , Open ) and an homomorphic encryption scheme HE = ( KeyGen , Enc , Eval , Dec ) , a non-interactive Range proof with Commitment Cipher- text Consistency is a NIZK argument for the NP relation R 𝑟 𝑐 𝑐𝑐 . R 𝑟 𝑐 𝑐𝑐 = { ( 𝑥 , 𝜔 ) | 𝑥 = ( ppc , pk , 𝐶 , 𝑐 , 𝑎, 𝑏 ) , 𝜔 = ( 𝑣 , 𝑟 , 𝑟 ′ ) , 𝐶 = Commit ppc ( 𝑣 ; 𝑟 ) ∧ 𝑎 ≤ 𝑣 < 𝑏 ∧ 𝑐 = Enc pk ( 𝑣 ; 𝑟 ′ ) } . Essentially , the NP relation dened above only rely on the en- cryption algorithm Enc and therefore could b e instantiated with an arbitrary public key encryption scheme. However , in our setting the ciphertext is not merely an encryption of the committed value and it could be involved in a sequence of homomorphic updates carried out by the ser ver . For this reason, we explicitly denote it as HE , even though the e valuation algorithm Eval is not involved in the relation. This choice ensures the minimal requirement: it only checks the consistency of the commitment and the ciphertext. 5 H-Elo Construction In this section we present the construction of our FHE-based match- making protocol using the Elo rating system. W e cover some addi- tional notation we use in Appendix B. A dditionally , we provide a high-level ov er view and a visualisation of the protocol in Figure 1. 5.1 System Mo del H-Elo consists of thr ee entities: (i) Ser vice Provider ( SP ), (ii) Clients ( U ), (iii) Trusted K ey Curator ( KC ). • Service Provider ( SP ) – SP hosts the matchmaking service. They dene the application and is responsible for initiating the match, verifying the outcome of a match and se curely calculating the rating of the users after the match. Additionally , the SP provides the initial rating of each client and registers them to the system. • Clients ( { 𝑢 1 , . . . , 𝑢 𝑛 } ∈ U ) – each client 𝑢 𝑖 ∈ U knows their rating and can prove their rank after a rating update. The clients wish to match with other similarly rated clients. • Trusted Ke y Curator ( KC ) – KC generates the public HE keys which are used by U in H-Elo . In this case, K C would decrypt and share the results with U after a rating update. The operations of the KC can be executed on a Trusted Execution Environment (TEE). 5.2 High-level Overview H-Elo is executed in three parts: (1) User Registration – is comprised of Algorithm 1 and Algo- rithm 2 and is run once by the parties. The Init algorithm gener- ates the respective keys and public parameters used thr oughout H-Elo . The Register algorithm allows 𝑢 𝑖 to choose their initial rating, encrypt it with HE and compute the proof of their rank and sends the proof and ciphertext to SP . If the pr o of is valid, then 𝑢 𝑖 is registered to the system and can match with other users 𝑢 𝑗 , otherwise the registration is aborted. (2) Rating Update – is done through Algorithm 3 and Algorithm 4. After 𝑢 𝑖 concludes 𝑛 matches, SP retrieves 𝑢 𝑖 ’s encrypted rating as well as the ratings of his 𝑛 opponents and computes the new rating homomorphically following Equation (1) by running the Update algorithm. The phase end by the KC re vealing the updated rating to 𝑢 𝑖 through the Announce algorithm. (3) Rating V erication – is comprised of Algorithm 5 and Al- gorithm 6. Upon receiving the new rating, 𝑢 𝑖 computes a new commitment and ciphertext through the V erifyNew algorithm, which are sent to KC . Afterwards, KC runs the Attest algo- rithm to open the commitment and verify if the commitment is consistent with its’ local record, then K C attests the cipher- text and commitment with a signatur e. Finally , 𝑢 𝑖 generates a CODASPY ’26, June 23–25, 2026, Frankfurt am Main, Germany Mindaugas Budzys, Bin Liu, and Antonis Michalas Figure 1: High-level Overview of H-Elo new proof and sends the pr oof to the SP . If SP can verify the proof, then he up dates the local r ecord and allo ws 𝑢 𝑖 to continue matchmaking with others. 5.3 Construction H-Elo is executed in three parts (i) User Registration , (ii) Rating Up- date , (iii) Rating V erication . The H-Elo protocol is constructed with six algorithms H-Elo = ( Init , Register , Update , Announce , Attest , V erifyNew ) , which can be dened as follows: Definition 5 ( H-Elo ). Let L denote a predened set of ranks, where each rank 𝑙 𝑖 ∈ L have a dened minimum 𝑙 𝑚𝑖𝑛 𝑖 ∈ Z and maxi- mum 𝑙 𝑚𝑎𝑥 𝑖 ∈ Z values required for the associated rank. Let HE dene a homomorphic encr yption scheme and 𝜆 dene the security parame- ter . Additionally , let NIZK dene a non-interactive zero-knowledge proving system, Com a commitment scheme and Σ a digital sig- nature scheme. Then H-Elo consists of a tuple of PPT algorithms H-Elo = ( Init , Register , Update , Announce , Attest , V erifyNew ) , where: • H-Elo . Init (1 𝜆 , R 𝑟 𝑐 𝑐𝑐 ) → ( vk KC , { 𝑝 𝑘 𝑖 } 𝑖 ∈ U , ppc , pk SP , vk SP ) – takes as input the se curity parameter 𝜆 and an NP relation R 𝑟 𝑐 𝑐𝑐 and outputs K C ’s verication key vk KC , the public HE keys 𝑝 𝑘 𝑖 of 𝑢 𝑖 , as well as the commitment public parameters ppc and proving pk SP and verication keys vk SP used for NIZK range proofs. • H-Elo . Register ( 𝑅 𝑖𝑛𝑖 𝑡 , 𝑙 𝑖𝑛𝑖 𝑡 , pk SP ) → 𝜋 𝑖 0 – takes as input the initial rating 𝑅 𝑖𝑛𝑖 𝑡 ∈ Z , and initial rank 𝑙 𝑖𝑛𝑖 𝑡 and outputs the initial proof 𝜋 𝑖 0 and registers 𝑢 𝑖 to the system. • H-Elo . Update ( 𝑐 𝑖 , 𝑐 𝑗 𝑜 𝑝 𝑝 , 𝑛, 𝑆 𝑟 𝑒 𝑎𝑙 , 𝐾 ) → 𝑐 ′ 𝑖 – takes as input 𝑢 𝑖 ’s en- crypted rating 𝑐 𝑖 , the number of matches 𝑛 > 2 , the encrypted ratings of 𝑢 𝑖 ’s opponents 𝑐 𝑗 𝑜 𝑝 𝑝 , wher e 𝑗 ∈ [0 , . . . , 𝑛 ] , summed match outcome 𝑆 𝑟 𝑒 𝑎𝑙 , and K-factor 𝐾 and outputs 𝑢 𝑖 ’s encrypted updated rating 𝑐 ′ 𝑖 . • H-Elo . Announce ( 𝑐 𝑖 , sk 𝑖 ) → 𝑅 ′ 𝑖 – takes as input the 𝑢 𝑖 ’s encrypted rating 𝑐 𝑖 , and the se cret key sk 𝑖 and output 𝑢 𝑖 ’s plaintext Elo value 𝑅 ′ 𝑖 . • H-Elo . Attest ( 𝑐 ′ 𝑖 , sk KC ) → 𝜎 – takes as input 𝑢 𝑖 ’s encrypted new rating 𝑐 ′ 𝑖 and the KC ’s signing key sk KC and outputs a signature 𝜎 on 𝑢 𝑖 ’s commitment. • H-Elo . V erifyNew ( 𝑖𝑑 𝑖 , 𝑅 ′ 𝑖 , 𝐶 ′ 𝑖 , 𝑟 , 𝑐 ′′ 𝑖 , 𝜎 ) → 𝜋 𝑖 – takes as input 𝑢 𝑖 ’s 𝑖𝑑 𝑖 , new rating 𝑅 ′ 𝑖 , the commitment 𝐶 ′ 𝑖 on 𝑅 ′ 𝑖 , the randomness 𝑟 used to generate 𝐶 ′ 𝑖 , current encrypted rating 𝑐 ′′ 𝑖 , the signature 𝜎 and outputs the proof 𝜋 𝑖 of 𝑢 𝑖 ’s rank. Algorithms. The User Registration phase involves generating the required keys for running H-Elo and registering a new user to the system. In Algorithm 1, K C generates vk KC and sk KC for Σ ( line 1). Then KC generates pk 𝑖 , sk 𝑖 and evk 𝑖 used for HE for each user 𝑢 𝑖 ∈ U (lines 2-3). SP generates the public parameters pp used in Com as well as pk SP and vk SP keys linke d to R 𝑟 𝑐 𝑐𝑐 used in NIZK (lines 4-5). All the public keys are shared to other entities ( line 6). In Algorithm 2, a new user is registered into the matchmaking system by SP dening an ID 𝑖𝑑 𝑖 for 𝑢 𝑖 and 𝑢 𝑖 obfuscates his rating 𝑅 𝑖 by some noise 𝛼 (lines 2-3) and generates the commitment 𝐶 𝑖 (line 4), ciphertext 𝑐 𝑖 (line 5) and proves that rating is within set bounds by the expe cted rank 𝑙 𝑖𝑛𝑖 𝑡 , which is shared to SP (lines 6-9). The SP veries the proof and publishes the user 𝑖𝑑 𝑖 and rank 𝑙 𝑖 (lines 10-14). If the verication fails SP aborts the registration (lines 15-16). Once 𝑢 𝑖 is registered, he may begin using the matchmaking Hidden Elo CODASPY ’26, June 23–25, 2026, Frankfurt am Main, Germany service and matching with 𝑢 𝑗 , where 𝑗 = 𝑖 . After each match cnt 𝑖 is incremented by one. Algorithm 1: H-Elo . Init Input: Security parameter 1 𝜆 and NP relation R 𝑟 𝑐 𝑐 𝑐 . Output: K C ’s verication key vk KC of digital signature scheme, public parameters of the commitment scheme ppc , pro ving key pk SP and verication key vk SP for the range proof. KC generates the key pair for the digital signature scheme as well as the Homomorphic Encryption scheme. 1 ( vk KC , sk KC ) ← Σ . KeyGen (1 𝜆 ) ; 2 for 𝑢 𝑖 ∈ U do 3 ( pk 𝑖 , sk 𝑖 , evk 𝑖 ) ← HE . KeyGen (1 𝜆 ) ; SP runs the setup algorithm of the commitment scheme and the range proof. 4 ppc ← Com . KeyGen (1 𝜆 ) 5 ( pk SP , vk SP ) ← NIZK . Setup (1 𝜆 , R 𝑟 𝑐 𝑐 𝑐 ) 6 return ( vk KC , { 𝑝 𝑘 𝑖 } 𝑖 ∈ U , pp c , pk SP , vk SP ) Algorithm 2: H-Elo . Register Input: Initial rating 𝑅 𝑖𝑛𝑖 𝑡 , initial rank 𝑙 𝑖𝑛𝑖 𝑡 , public parameters ppc , user 𝑢 𝑖 ’s public key pk 𝑖 , SP pr oving key pk SP . Output: Initial pr o of for 𝑢 𝑖 ’s 𝜋 𝑖 0 . SP assigns ID’s to the users who wish to r egister and sends them 𝑅 𝑖𝑛𝑖 𝑡 and their initial rank 𝑙 𝑖𝑛𝑖 𝑡 . 1 𝑖 𝑑 𝑖 ← Rand ( Z + ) ; The user adds some noise 𝛼 to the initial rating and proves that it stays inside the range of the initial rank 𝑙 𝑖𝑛𝑖 𝑡 . 2 𝛼 ← Rand ( Z ) ; 3 𝑅 𝑖 = 𝑅 𝑖𝑛𝑖 𝑡 + 𝛼 ; 4 𝐶 𝑖 ← Com . Commit ppc ( 𝑅 𝑖 ; 𝑟 ) ; 5 𝑐 𝑖 ← HE . Enc ( pk 𝑖 , 𝑅 𝑖 ; 𝑟 ′ ) ; 6 𝑥 𝑖 0 ← ( ppc , pk 𝑖 , 𝐶 𝑖 , 𝑐 𝑖 , 𝑙 𝑚𝑖𝑛 𝑖𝑛𝑖 𝑡 , 𝑙 𝑚𝑎𝑥 𝑖𝑛𝑖 𝑡 ) ; 7 𝜔 𝑖 0 ← ( 𝑅 𝑖 , 𝑟 , 𝑟 ′ ) ; 8 𝜋 𝑖 0 ← NIZK . Prove ( pk SP , 𝑥 𝑖 0 , 𝜔 𝑖 0 ) ; 9 return ( 𝑖𝑑 𝑖 , 𝑥 𝑖 0 , 𝜔 𝑖 0 , 𝜋 𝑖 0 ) ; On receiving ( 𝑥 𝑖 0 , 𝜋 𝑖 0 ) from 𝑢 𝑖 , SP v eries the proof and publishes the user and the rank if the proof is valid. 10 𝑏 ← NIZK . V erify ( vk SP , 𝑥 𝑖 0 , 𝜋 𝑖 0 ) ; 11 if 𝑏 == 1 then 12 cnt 𝑖 = 1 ; 13 SP r e cords ( 𝑖𝑑 𝑖 , 𝑙 𝑖 , 𝑐 𝑖 , cnt 𝑖 ) ; 14 return 𝑏 and publish 𝑖𝑑 𝑖 and 𝑙 𝑖 . 15 else 16 return ⊥ and abort the registration. The Rating Update phase consists of the Update algorithm, that runs when cnt 𝑖 == 𝑛 . The steps for updating 𝑢 𝑖 ’s rating are dened in Algorithm 3. In this case SP evaluates the expected result of each match up to 𝑗 == 𝑛 and creates a sum of all e xpe cted results 𝑐 𝑒 𝑥 𝑝 − 𝑠𝑢𝑚 (lines 1-7) as dened in Equation (2). Afterwards the up- date process follows Equation (1). It is imp ortant to note, that SP evaluates the bootstrapping cir cuit on the resulting cipherte xt after subtracting 𝑐 𝑒 𝑥 𝑝 − 𝑠𝑢𝑚 from 𝑆 𝑟 𝑒 𝑎𝑙 to refresh the accumulate d noise to an acceptable level (lines 8-9). The bootstrapping step is done here due to the plaintext values being the lowest at this point of the protocol, allowing the noise to be refr eshe d while retaining high precision. After the updated rating 𝑐 ′ 𝑖 (lines 10-11) is computed it is sent to KC to be announced to 𝑢 𝑖 as shown in Algorithm 4. Algorithm 3: H-Elo . Update Input: 𝑢 𝑖 ’s encrypted current rating 𝑐 𝑖 , opponents encrypted ratings 𝑐 𝑗 𝑜 𝑝 𝑝 , number of matches before an update 𝑛 , summed outcome of the matches 𝑆 𝑟 𝑒 𝑎𝑙 , K-factor 𝐾 . Output: 𝑢 𝑖 ’s encrypted update d rating 𝑐 ′ 𝑖 . The server homomorphically calculates the expected match results 𝑐 𝑒 𝑥 𝑝 − 𝑠𝑢𝑚 : 1 𝑐 1 ← HE . EvalMul ( 𝑐 𝑖 , 0 . 0025) ; ⊲ 1 400 = 0 . 0025 2 𝑐 𝑒 𝑥 𝑝 − 𝑠𝑢𝑚 = 0 ; 3 for 𝑗 < 𝑛 do 4 𝑐 2 ← HE . EvalMul ( 𝑐 𝑗 𝑜 𝑝 𝑝 , 0 . 0025) ; 5 𝑐 3 ← HE . EvalSub ( 𝑐 2 , 𝑐 1 ) ; ⊲ 𝑐 3 = ( 𝑐 2 − 𝑐 1 ) ÷ 400 6 𝑐 𝑒 𝑥 𝑝 ← HE . EvalPoly ( 𝑐 3 , 1 1+10 𝑐 3 ) ; 7 𝑐 𝑒 𝑥 𝑝 − 𝑠𝑢𝑚 ← HE . EvalAdd ( 𝑐 𝑒 𝑥 𝑝 − 𝑠𝑢𝑚 , 𝑐 𝑒 𝑥 𝑝 ) ; The server homomorphically calculates the updated rating and sends it back to the player . 8 𝑐 4 ← HE . EvalSub ( 𝑆 𝑟 𝑒 𝑎𝑙 , 𝑐 𝑒 𝑥 𝑝 − 𝑠𝑢𝑚 ) ; 9 𝑐 ′ 4 ← HE . EvalBootstrap ( 𝑐 4 ) ; 10 𝑐 5 ← HE . EvalMul ( 𝐾 , 𝑐 4 ) ; 11 𝑐 ′ 𝑖 ← HE . EvalAdd ( 𝑐 𝑖 , 𝑐 5 ) ; ⊲ 𝑐 ′ 𝑖 = 𝑐 𝑖 + 𝐾 · ( 𝑆 𝑟 𝑒 𝑎𝑙 − 𝑐 𝑒 𝑥 𝑝 − 𝑠𝑢𝑚 ) return 𝑐 ′ 𝑖 The nal phase in H-Elo is the Rating V erication , wher e 𝑢 𝑖 re- ceives his new ranking and must generate a ne w proof 𝜋 𝑖 of their rank 𝑅 ′ 𝑖 and have it attested by KC . In Algorithm 5, 𝑢 𝑖 generates a commitment 𝐶 𝑖 of his rating 𝑅 𝑖 (line 1), if KC can open the com- mitment, then KC attests the commitment and sends the signature to 𝑢 𝑖 , otherwise the attestation fails (lines 2-5). In Algorithm 6, 𝑢 𝑖 generates a ciphertext 𝑐 ′ 𝑖 of their rating and pro ves their rating with 𝜋 𝑖 following the same steps as in User Registration (lines 1-4). If SP can verify the proof, then the rank and ciphertext are updated, otherwise the verication is aborted ( lines 5-10). Algorithm 4: H-Elo . Announce Input: 𝑢 𝑖 ’s encrypted rating 𝑐 ′ 𝑖 , KC ’s decryption key sk 𝑖 . Output: 𝑢 𝑖 ’s rating 𝑅 𝑖 For every 𝑛 games, SP will send the latest encrypte d rating 𝑐 ′ 𝑖 for 𝑢 𝑖 to KC . On r e ceiving the encrypted contents, KC de crypts 𝑐 ′ 𝑖 with the use of sk 𝑖 and sends it to 𝑢 𝑖 . 1 𝑅 ′ 𝑖 ← HE . Dec ( sk 𝑖 , 𝑐 ′ 𝑖 ) ; 2 return 𝑅 ′ 𝑖 and record it for future attestation. 6 Security In this section, we formally present the security properties achieved by our construction H-Elo . Notably , we stress that the security of the underlying cryptographic primitives, such as the NIZK proof system and the homomorphic encryption scheme HE , is assumed to hold under their respective assumptions and is therefore out of the scope of this work. CODASPY ’26, June 23–25, 2026, Frankfurt am Main, Germany Mindaugas Budzys, Bin Liu, and Antonis Michalas Algorithm 5: H-Elo . Attest Input: 𝑢 𝑖 ’s rating 𝑅 ′ 𝑖 and the encrypted rating obtained from K C 𝑐 ′ 𝑖 , KC ’s signing key sk KC . Output: A signatur e 𝜎 on 𝑢 𝑖 ’s commitment. The user 𝑢 𝑖 computes the commitment 𝐶 𝑖 and sends ( 𝑖 𝑑 𝑖 , 𝑐 ′ 𝑖 , 𝐶 𝑖 ) to KC for attestation. 1 𝐶 𝑖 ← Com ppc . Commit ( 𝑅 ′ 𝑖 ; 𝑟 ) If 𝐶 𝑖 can be opened as valid on 𝑅 ′ 𝑖 , which is identical to KC ’s local record, and 𝑅 ′ 𝑖 ≥ 0 , KC attests 𝐶 𝑖 by generating a signature 𝜎 on ( 𝑖 𝑑 𝑖 , 𝑐 ′ 𝑖 , 𝐶 𝑖 ) 2 if Com ppc . Open ( 𝐶 𝑖 , 𝑅 ′ 𝑖 , 𝑟 ) == 1 then 3 return 𝜎 ← Σ . Sign ( sk KC , ( 𝑖𝑑 𝑖 , 𝑐 ′ 𝑖 , 𝐶 𝑖 )) . 4 else 5 return ⊥ and abort the attestation. Algorithm 6: H-Elo . V erifyNew Input: 𝑢 𝑖 ’s id 𝑖𝑑 𝑖 , new rating 𝑅 ′ 𝑖 , a commitment 𝐶 𝑖 on 𝑅 ′ 𝑖 with opening randomness 𝑟 , current encrypted rating 𝑐 ′′ 𝑖 for 𝑅 ′ 𝑖 , and a signature 𝜎 Output: 𝑢 𝑖 ’s proof of rank 𝜋 𝑖 . 𝑢 𝑖 nds out the expected rank 𝑙 𝑒 𝑥 𝑝 for 𝑅 ′ 𝑖 , then generates the range proof. 1 𝑐 ′ 𝑖 ← HE . Enc ( pk 𝑖 , 𝑅 ′ 𝑖 ; 𝑟 ′ ) 2 𝑥 𝑖 ← ( ppc , pk 𝑖 , 𝐶 𝑖 , 𝑐 ′ 𝑖 , 𝑙 𝑚𝑖𝑛 𝑒 𝑥 𝑝 , 𝑙 𝑚𝑎𝑥 𝑒 𝑥 𝑝 ) 3 𝜔 𝑖 ← ( 𝑅 ′ 𝑖 , 𝑟 , 𝑟 ′ ) 4 𝜋 𝑖 ← NIZK . Prove ( pk SP , 𝑥 𝑖 , 𝜔 𝑖 ) 𝑢 𝑖 sends ( 𝑐 ′′ 𝑖 , 𝑐 ′ 𝑖 , 𝐶 𝑖 , 𝜋 𝑖 , 𝜎 ) to SP . The SP veries the attestation and the proof. In the case that both are valid and 𝑐 ′′ 𝑖 is identical to the local record 𝑐 𝑖 , SP then updates 𝑐 𝑖 and 𝑙 𝑖 on record. 5 𝑏 ← NIZK . V erify ( vk SP , 𝑥 𝑖 , 𝜋 𝑖 ) ∧ Σ . V erify ( vk KC , 𝜎 , ( 𝑖𝑑 𝑖 , 𝑐 ′′ 𝑖 , 𝐶 𝑖 )) ∧ ( 𝑐 𝑖 == 𝑐 ′′ 𝑖 ) ∧ ( cnt 𝑖 == 𝑁 ) ; 6 if 𝑏 == 1 then 7 𝑐 𝑖 ← 𝑐 ′ 𝑖 , 𝑙 𝑖 ← 𝑙 𝑒 𝑥 𝑝 and cnt i ← 1 ; 8 return ( 𝑐 𝑖 , 𝑙 𝑖 ) 9 else 10 return ⊥ and abort the verication. W e begin by intr oducing two core security notions tailored to our setting: (1) N-round Fair Matchmaking. Each user’s rating is correctly and fairly updated for every 𝑁 rounds. It ensures that users ar e always matched within the correct rank interval; and (2) Hidden Elo. The ser vice provider learns no more ab out a user’s exact Elo value than what is implied by the validity of the range proofs. In earlier sections, we presented H-Elo core algorithms in min- imal form for simplicity , ho wever we expand our pr esentation in which local states are explicit and algorithm interfaces ar e asso ci- ated with the local states. W e stress that these changes are regarding presentation rather than semantic. Concretely , a user 𝑢 𝑖 ’s local state will become st 𝑢 𝑖 = ( 𝑖𝑑 𝑖 , 𝑙 𝑖 , 𝑅 𝑖 , 𝑐 𝑖 , 𝜎 ) , where 𝑖𝑑 𝑖 is its identity , 𝑙 𝑖 is its current rank, 𝑅 𝑖 is the Elo value, 𝑐 𝑖 is the encrypted Elo value and 𝜎 is the latest attestation obtained from KC . For simplicity we con- sider the randomness use d for generating the encr ypted Elo value is a part of 𝑅 𝑖 , but when it comes to value of 𝑅 𝑖 we just omit those ran- domness. Similarly , we also consider the commitment 𝐶 𝑖 as a part of 𝑐 𝑖 . Additionally , K C ’s local state st 𝐾 𝐶 = ( sk 𝐾 𝐶 , { st 𝑖 } 𝑢 𝑖 ∈ U , 𝑀 ) , where 𝑀 is a list (indexed by users) recording each user’s latest Elo value in plaintext form for future attestation. SP ’s local state contains a list L = { ( 𝑖𝑑 𝑖 , 𝑙 𝑖 , 𝑐 𝑖 , cnt 𝑖 ) } 𝑢 𝑖 ∈ U of per-user entries to record user’s current rank and the encrypte d Elo value. The counter cnt 𝑖 is used for tracking the numb er of matches since the last rank up date. Some of the protocol algorithms are then understoo d as sub-protocols that take the relevant local states as inputs and update the corre- sponding states. This modication makes the security denitions more general, since they are no longer hard-wire our concrete H-Elo construction. Our adversary model also becomes strictly stronger in an explicit way . Because up on an adaptive takeover of a user , the adversary should now learn about the session related information (e .g. the randomness for commitment and encr yption and the most recent attestation). W e rst formalise the security notion of N-round Fair Match- making . In a system wher e user ranks are refreshed every N games, rank updates should correctly reect the user’s curr ent Elo value. Under a semi-honest SP , this rank correctness condition suces to guarantee fair matchmaking, i.e., users are pair e d with opponents of the same rank whenever matchmaking is invoked between rank refresh ev ents. Let L denote the predened rank set, which is as- sumed to be valid in the sense that every admissible Elo value lies in exactly one rank interval. Let IsV alid be a predicate used by the experiment to reject invalid inputs, with IsV alid ( 𝑅 𝑖𝑛𝑖 𝑡 , 𝑙 𝑖𝑛𝑖 𝑡 ) = 1 in- dicates the initial Elo value and the rank are valid and IsV alid ( 𝑆 𝑟 𝑒 𝑎𝑙 ) = 1 indicates that the summed match outcome is valid. The security property is captured via the following game-based experiment in which an adversary attempts to make the ser ver record an incorrect rank for some user while the challenger ex- ecutes the protocol. The challenger runs Init with the security parameter 1 𝜆 and R 𝑟 𝑐 𝑐𝑐 , which is the range proof relation that en- forces commitment-ciphertext consistency . It also initialises three lists. The list L and 𝑀 mirror those in SP ’s and KC ’s local states, but are made explicit in the e xp eriment for clarity . Cr records the corrupted users. The challenger then hands the public parameters pp to the adversary A , who then interacts with the oracles shown in Figure 2 The registration oracle Register ( 𝑖 , st ∗ 𝑢 , 𝑅 𝑖𝑛𝑖 𝑡 , 𝑙 𝑖𝑛𝑖 𝑡 ) registers user 𝑢 𝑖 with the initial Elo 𝑅 𝑖𝑛𝑖 𝑡 and rank 𝑙 𝑖𝑛𝑖 𝑡 . If 𝑢 𝑖 is corrupted, the oracle runs Register using the lo cal state sp ecied by the adversar y st ∗ 𝑢 . Otherwise it uses the local state of 𝑢 𝑖 which is maintaine d by the experiment instead. Upon successful run, L is update d accordingly and the handle and r eturns 𝑢 𝑖 to indicate that. If 𝑢 𝑖 is corrupted, the oracle also releases the user’s updated local state to A . The update oracle Upda te ( 𝑖 , 𝑗 , 𝑆 𝑟 𝑒 𝑎𝑙 ) processes the released sum of match result 𝑆 𝑟 𝑒 𝑎𝑙 for the user 𝑢 𝑖 and 𝑢 𝑗 . If IsV alid ( 𝑆 𝑟 𝑒 𝑎𝑙 ) = 1 , each user’s game counter cnt is incremented by 1 and Update is run on their encrypted Elo values. Whenever either user r eaches the 𝑁 -th game, the oracle invokes Announce to let K C rev eal the latest Elo value to that user . The plaintext Elo value will be recorded in 𝑀 for future attestation and the counter is reset to 1 . Because both the KC and SP are semi-honest, their mutual interaction is reliable and outside the adv ersar y’s inuence, the announcement Hidden Elo CODASPY ’26, June 23–25, 2026, Frankfurt am Main, Germany is therefore modelled as part of Upda te . If either user is corrupt, the corresponding local-state update message is provided to A . The oracle VerifyNew ( 𝑖 , st ∗ 𝑢 ) allo ws the adversary to request for a rank refresh of a specied user 𝑢 𝑖 . The oracle runs V erifyNew on 𝑢 𝑖 ’s local state. If 𝑢 𝑖 is corrupted, it uses the local state provided by the adversary instead. Since V erifyNew works only when the counter cnt 𝑖 == 𝑁 , cnt 𝑖 will be reset to 1 on the successful run of the algorithm. After that, the VerifyNew returns the encrypted Elo value and the updated rank. If A queries Corrupt for taking over user 𝑖 , 𝑢 𝑖 will be added to the list Cr and the oracle returns the internal state of 𝑢 𝑖 . The adversar y wins by specifying a user 𝑢 𝑖 (and optionally a state st ∗ 𝑢 ). The challenger then executes V erifyNew using either the experiment’s local state for 𝑢 𝑖 or st ∗ 𝑢 if 𝑢 𝑖 is corrupted. On the successful run of the algorithm, a rank 𝑙 𝑖 can be derived from the outputs. If 𝑙 𝑖 is dierent from the actual rank of 𝑢 𝑖 , computed by applying the deterministic function rank ( · ) to the user’s current Elo value maintained by the game (stored in 𝑀 [ 𝑖 ] ), then the adversary is considered to win. Definition 6 (N-round Fair Ma tchmaking). A private and secure rating system-based matchmaking protocol Π is said to preserve 𝑁 -round Fair Matchmaking for a valid predened set of ranks L with a set of user U , for any probabilistic polynomial-time adversary A , the following holds: Adv N-fairness Π , A ( 𝜆 ) = Pr[ Exp N-fairness Π , A ( 𝜆 ) → 1] is a negligible function in 𝜆 , and the e xperiment Exp N-fairness Π , A is dened as follows: Exp N-fairness Π , A ( 𝜆 ) 𝑀 , L , Cr ← ⊥ ( st 𝑆 𝑃 , st 𝐾 𝐶 , { st 𝑢 𝑖 } 𝑢 ∈ U , pp ) ← $ H-Elo . Init (1 𝜆 , R 𝑟 𝑐 𝑐 𝑐 ) ( st ∗ 𝑢 , 𝑢 𝑖 ) ← $ A (1 𝜆 , pp : O 𝑓 ) If 𝑢 𝑖 ∈ U then return ⊥ If 𝑢 𝑖 ∈ Cr then st 𝑢 𝑖 ← st ∗ 𝑢 res ← $ H-Elo . V erifyNew ( st 𝑢 𝑖 , st 𝑆 𝑃 , pp ) If r es = ⊥ then Parse res as ( 𝑐 𝑖 , 𝑙 𝑖 ) If 𝑙 𝑖 = rank ( 𝑀 [ 𝑖 ]) then return 1 Else r eturn 0 W e now present the security notion of Hidden Elo , which en- sures that the server cannot learn a user’s exact Elo value beyond the rank to which that user belongs. This security property is de- ned by an indistinguishability-based game between the adversary A and a challenge that runs the protocol. As in the game that dened N-round fair Matchmaking, the adversary here is allowed to interact with the same suite of oracles modelling registration, updates, attestation, rank update, and user corruption (shown in Figur e 3). However , here the adv ersar y will be provided those information available to SP . This modication reects that SP is semi-honest, which means it faithfully follow the protocol specication but it records and inspects any message it receives and may collude with corrupt users. Additionally , the adversary is given access to a challenge oracle Challenge . Upon receiving a query specifying a target user and a pair of initial Elo values ( 𝑅 0 , 𝑅 1 ) of the same rank, the challenge selects one according to a random bit 𝑏 chosen at the b eginning of the game, and runs Register ( 𝑖 , st ∗ 𝑢 𝑖 , 𝑅 𝑖𝑛𝑖 𝑡 , 𝑙 𝑖𝑛𝑖 𝑡 ) If L [ 𝑖 ] = ∅ ∨ 𝑢 𝑖 / ∈ U then return ⊥ If ¬ IsV alid ( 𝑅 𝑖𝑛𝑖 𝑡 , 𝑙 𝑖𝑛𝑖 𝑡 ) then return ⊥ If 𝑢 𝑖 ∈ Cr then st 𝑢 𝑖 ← st ∗ 𝑢 res ← $ H-Elo . Register ( st 𝑢 𝑖 , pp ) If res == ⊥ then Return ⊥ Else Parse res as ( st 𝑢 𝑖 , 𝑖 𝑑 𝑖 , 𝑙 𝑖 , 𝑐 𝑖 , cnt 𝑖 ) L [ 𝑖 ] ← ( 𝑖𝑑 𝑖 , 𝑙 𝑖 , 𝑐 𝑖 , cnt 𝑖 ) If 𝑢 𝑖 ∈ Cr then Return st 𝑢 𝑖 Else return 𝑢 𝑖 A ttest ( 𝑖, st ∗ 𝑢 ) If 𝑢 𝑖 / ∈ U then return ⊥ If 𝑢 𝑖 ∈ Cr then st 𝑢 𝑖 ← st ∗ 𝑢 res ← $ H-Elo . Aest ( st 𝑢 𝑖 , sk 𝐾 𝐶 ) If res == ⊥ then return ⊥ Parse res as ( 𝑐 ′ 𝑖 , 𝜎 ) st 𝑢 𝑖 ← ( · , · , · , 𝑐 ′ 𝑖 , 𝜎 ) If 𝑢 𝑖 ∈ Cr then return st 𝑢 𝑖 Else return 𝑢 𝑖 Corrupt ( 𝑖 ) If 𝑢 𝑖 / ∈ U ∨ 𝑢 𝑖 ∈ Cr then return ⊥ Cr ← Cr ∪ { 𝑢 𝑖 } Return st 𝑢 𝑖 Upda te ( 𝑖, 𝑗 , 𝑆 𝑟 𝑒 𝑎𝑙 ) If 𝑢 𝑖 / ∈ U ∨ 𝑢 𝑗 / ∈ U then return ⊥ If ¬ IsV alid ( 𝑆 𝑟 𝑒 𝑎𝑙 ) then return ⊥ Parse L [ 𝑖 ] as ( 𝑖𝑑 𝑖 , 𝑙 𝑖 , 𝑐 𝑖 , cnt 𝑖 ) Parse L [ 𝑗 ] as ( 𝑖𝑑 𝑗 , 𝑙 𝑗 , 𝑐 𝑗 , cnt 𝑗 ) 𝑐 ′ 𝑖 ← $ H-Elo . Up date ( st 𝑆 𝑃 , pp , 𝑐 𝑖 , 𝑐 𝑗 ) 𝑐 ′ 𝑗 ← $ H-Elo . Up date ( st 𝑆 𝑃 , pp , 𝑐 𝑗 , 𝑐 𝑖 ) msg 𝑖 ← 𝑖 , msg 𝑗 ← 𝑗 For 𝑥 ∈ { 𝑖 , 𝑗 } : cnt 𝑥 ← cnt 𝑥 + 1 If cnt 𝑥 == 𝑁 then 𝑅 ′ 𝑥 ← $ H-Elo . Announce ( st 𝐾 𝐶 , 𝑐 𝑖 ) 𝑀 [ 𝑖 ] ← 𝑅 ′ 𝑥 If 𝑢 𝑥 ∈ Cr then msg 𝑥 ← 𝑅 ′ 𝑥 Return ( msg 𝑖 , msg 𝑗 ) VerifyNew ( 𝑖 , st ∗ 𝑢 ) If 𝑢 𝑖 / ∈ U then return ⊥ If 𝑢 𝑖 ∈ Cr then st 𝑢 𝑖 ← st ∗ 𝑢 res ← $ H-Elo . V erifyNew ( st 𝑆 𝑃 , st 𝑢 𝑖 , pp ) If res == ⊥ then return ⊥ Parse res as ( 𝑐 ′ 𝑖 , 𝑙 ′ 𝑖 ) cnt 𝑖 ← 1 ; L [ 𝑖 ] ← ( · , 𝑙 ′ 𝑖 , 𝑐 ′ 𝑖 , cnt 𝑖 ) If 𝑢 ∈ Cr then return ( 𝑐 ′ 𝑖 , 𝑙 ′ 𝑖 ) st 𝑢 𝑖 ← ( · , 𝑙 ′ 𝑖 , · , 𝑐 ′ 𝑖 , · ) Return 𝑢 𝑖 Figure 2: The oracles O 𝑓 that A has access to in Exp N-fairness Π , A . the registration algorithm. After that, it continues the protocol thereafter . Notice that the challenge oracle can be called on a user once, since any user in the system cannot register twice . At the end of the interaction, A outputs a guess 𝑏 ′ for the random bit. T o pre vent trivial wins, A is not allowed to take o ver any of the challenged users, since such a takeover would r eveal the underlying Elo value with the help of KC and thereby invalidate the intended security guarantee. The adversary wins the game if it guesses the bit correctly . Hidden Elo holds if any PPT adv ersar y’s advantage in this game is negligible in the security parameter . Definition 7 (Hidden Elo). A private and se cure rating system- based matchmaking protocol Π is said to preserve Hidden Elo for a valid predened set of ranks L with a set of user U , for any proba- bilistic polynomial-time adversary A , the following holds: Adv ind Π , A ( 𝜆 ) = | Pr[ Exp ind Π , A ( 𝜆 ) → 1] − 1 2 | is a negligible function in 𝜆 , and the experiment Exp ind Π , A is dened as follows: Exp ind Π , A ( 𝜆 ) 𝑏 ← $ { 0 , 1 } ; L , Cr , chall ← ⊥ ( st 𝑆 𝑃 , st 𝐾 𝐶 , { st 𝑢 𝑖 } 𝑢 ∈ U , pp ) ← $ H-Elo . Init (1 𝜆 , R 𝑟 𝑐 𝑐 𝑐 ) 𝑏 ′ ← $ A (1 𝜆 , pp : O ℎ ) Return ( 𝑏 ′ == 𝑏 ) Theorem 6.1. If the signature scheme Σ is EUF-CMA secure and the range proof NIZK is knowledge-sound, the construction H-Elo ensures N-round Fair Matchmaking. CODASPY ’26, June 23–25, 2026, Frankfurt am Main, Germany Mindaugas Budzys, Bin Liu, and Antonis Michalas Register ( 𝑖 , st ∗ 𝑢 𝑖 , 𝑅 𝑖𝑛𝑖 𝑡 , 𝑙 𝑖𝑛𝑖 𝑡 ) If L [ 𝑖 ] = ∅ ∨ 𝑢 𝑖 / ∈ U then return ⊥ If ¬ IsV alid ( 𝑅 𝑖𝑛𝑖 𝑡 , 𝑙 𝑖𝑛𝑖 𝑡 ) then return ⊥ If 𝑢 𝑖 ∈ Cr then st 𝑢 𝑖 ← st ∗ 𝑢 res ← $ H-Elo . Register ( st 𝑢 𝑖 , pp ) If res == ⊥ then Return ⊥ Else Parse res as ( st 𝑢 𝑖 , 𝑖 𝑑 𝑖 , 𝑙 𝑖 , 𝑐 𝑖 , cnt 𝑖 ) L [ 𝑖 ] ← ( 𝑖𝑑 𝑖 , 𝑙 𝑖 , 𝑐 𝑖 , cnt 𝑖 ) If 𝑢 𝑖 ∈ Cr then Return st 𝑢 𝑖 Else return ( 𝑙 𝑖 , 𝑐 𝑖 , cnt 𝑖 ) A ttest ( 𝑖, st ∗ 𝑢 ) If 𝑢 𝑖 / ∈ U then return ⊥ If 𝑢 𝑖 ∈ Cr then st 𝑢 𝑖 ← st ∗ 𝑢 res ← $ H-Elo . Aest ( st 𝑢 𝑖 , sk 𝐾 𝐶 ) If res == ⊥ then return ⊥ Parse res as ( 𝑐 ′ 𝑖 , 𝜎 ) st 𝑢 𝑖 ← ( · , · , · , 𝑐 ′ 𝑖 , 𝜎 ) If 𝑢 𝑖 ∈ Cr then return st 𝑢 𝑖 Else return 𝑢 𝑖 Challenge ( 𝑖 , 𝑅 0 , 𝑅 1 , 𝑙 ) If 𝑢 𝑖 / ∈ U ∨ 𝑢 𝑖 ∈ Cr then return ⊥ If 𝑢 𝑖 ∈ chall then return ⊥ If ¬ IsV alid ( 𝑅 0 , 𝑙 ) ∨ ¬ IsValid ( 𝑅 1 , 𝑙 ) Then return ⊥ If rank ( 𝑅 0 ) = rank ( 𝑅 1 ) then return ⊥ res ← $ H-Elo . Register ( st 𝑢 𝑖 , 𝑅 𝑏 , 𝑙 , pp ) If res == ⊥ then return ⊥ Parse res as ( st 𝑢 𝑖 , 𝑖 𝑑 𝑖 , 𝑙 𝑖 , 𝑐 𝑖 , cnt 𝑖 ) chall ← chall ∪ { 𝑢 𝑖 } Return ( 𝑙 𝑖 , 𝑐 𝑖 , cnt 𝑖 ) Upda te ( 𝑖, 𝑗 , 𝑆 𝑟 𝑒 𝑎𝑙 ) If 𝑢 𝑖 / ∈ U ∨ 𝑢 𝑗 / ∈ U then return ⊥ If ¬ IsV alid ( 𝑆 𝑟 𝑒 𝑎𝑙 ) then return ⊥ Parse L [ 𝑖 ] as ( 𝑖𝑑 𝑖 , 𝑙 𝑖 , 𝑐 𝑖 , cnt 𝑖 ) Parse L [ 𝑗 ] as ( 𝑖𝑑 𝑗 , 𝑙 𝑗 , 𝑐 𝑗 , cnt 𝑗 ) 𝑐 ′ 𝑖 ← $ H-Elo . Up date ( st 𝑆 𝑃 , 𝑐 𝑖 , 𝑐 𝑗 , pp ) 𝑐 ′ 𝑗 ← $ H-Elo . Up date ( st 𝑆 𝑃 , 𝑐 𝑗 , 𝑐 𝑖 , pp ) For 𝑥 ∈ { 𝑖 , 𝑗 } : cnt 𝑥 ← cnt 𝑥 + 1 If cnt 𝑥 == 𝑁 then 𝑅 ′ 𝑥 ← $ H-Elo . Announce ( st 𝐾 𝐶 , 𝑐 𝑖 ) Return ( 𝑐 ′ 𝑖 , 𝑐 ′ 𝑗 , cnt 𝑖 , cnt 𝑗 ) VerifyNew ( 𝑖 , st ∗ 𝑢 ) If 𝑢 𝑖 / ∈ U then return ⊥ If 𝑢 𝑖 ∈ Cr then st 𝑢 𝑖 ← st ∗ 𝑢 res ← $ H-Elo . V erifyNew ( st 𝑆 𝑃 , st 𝑢 𝑖 , pp ) If res == ⊥ then return ⊥ Parse res as ( 𝑐 ′ 𝑖 , 𝑙 ′ 𝑖 ) cnt 𝑖 ← 1 ; L [ 𝑖 ] ← ( · , 𝑙 ′ 𝑖 , 𝑐 ′ 𝑖 , cnt 𝑖 ) If 𝑢 ∈ Cr then return ( 𝑐 ′ 𝑖 , 𝑙 ′ 𝑖 ) st 𝑢 𝑖 ← ( · , 𝑙 ′ 𝑖 , · , 𝑐 ′ 𝑖 , · ) Return ( 𝑐 ′ 𝑖 , 𝑙 ′ 𝑖 ) Corrupt ( 𝑖 ) If 𝑢 𝑖 / ∈ U ∨ 𝑢 𝑖 ∈ Cr then return ⊥ If 𝑢 𝑖 ∈ chall then return ⊥ Cr ← Cr ∪ { 𝑢 𝑖 } Return st 𝑢 𝑖 Figure 3: The oracles O ℎ that A has access to in Exp ind Π , A . Proof Sketch. T o win the N-round Fair Matchmaking game, the adversary A must produce a valid range proof together with a valid attestation that jointly authenticate a user’s identier , an encrypted Elo value and the corresponding commitment bound to that value. There are only tw o possible ways in which the adversar y can succeed in doing so: (1) the adversary provides a valid attestation on an invalid Elo value, namely , a value that does not match the user’s current Elo value as that maintained by KC , or (2) the adversary presents a valid attestation, but provide it with a range proof that veries successfully for an invalid Elo value, even though this value is consistent with the commitment and ciphertext specied in the attestation. W e discuss these two cases separately . In the rst case, recall that KC is assumed to be semi-honest and therefore maintains an accurate record of each user’s current Elo value. By design, it only attests to commitments and ciphertexts that correspond exactly to those current values. Hence, it will never sign or attest to an inconsistent tuple ( 𝑖𝑑 𝑖 , 𝑐 𝑖 , 𝐶 𝑖 ) unless an adversary can forge a valid signature under KC ’s signing key . Consequently , any adversary that succeeds in this case can be used to construct a forger that breaks the EU-CMA security of the signature scheme. For the second case, A must produce a range proof that veries under the relation R 𝑟 𝑐 𝑐𝑐 for a ciphertext and commitment pair that does not encode a valid Elo value. Because the attestation in this scenario is valid, the only remaining violation w ould b ecome the ability to construct a convincing proof for a false statement in the underlying NIZK system. Therefore , any adversary that succe eds in this case can be transformed into an adversary that breaks the knowledge soundness property of the NIZK proof system NIZK . Bringing them together , these two reductions bound the adver- sary’s overall advantage in the N-r ound Fair Matchmaking game. Formally , there exists ecient adversaries B and C such that Adv N-fairness H-Elo , A ( 𝜆 ) ≤ Adv EU-CMA Σ , B ( 𝜆 ) + Adv soundness NIZK , C ( 𝜆 ) , where Adv EU-CMA Σ , B ( 𝜆 ) and Adv soundness NIZK , C ( 𝜆 ) denote the advantages in the signature scheme’s EU-CMA security game and the range proof ’s knowledge soundness game respectively . Thus, given that both primitives are secure, the construction H-Elo preserves the N-round Fair Matchmaking property . □ Theorem 6.2. The commitment scheme Com is computationally hiding, the range proof NIZK for the relation R 𝑟 𝑐 𝑐𝑐 is zero-kno wle dge, and the homomorphic encr yption scheme HE is IND-CP A secure, the construction H-Elo ensures Hidden Elo. Proof Sketch. Since the adversary receives precisely SP ’s view and also the corrupted users’ during the honest execution of the proto- col, we can narro w the leakage points of the protocol to see what can reveal information r egarding the exact Elo values. Recall that the SP observes commitments, ciphertexts, and range proofs for the relation R 𝑟 𝑐 𝑐𝑐 , while the information obtained fr om the corrupt users will not help the adversary to learn any information about the e xact Elo values of the challenged users. It should be notice that since the commitment is a part of the public statement of the range proof, the zero-knowledge property of the range pr oof itself do es not guarantee that no information about the associated Elo value is leaked through the commitment. Thus, information about an hon- est user’s precise Elo value can leak only through: (1) commitments, (2) ciphertexts, and (3) range pr o ofs. W e procee d the proof in the following sequence of games: Game 0 : The initial game is the original security game that denes Hidden Elo. Game 1 : In this game, w e replace the real proofs by simulated proofs for the same public statements. By the zero-knowledge property , the adversary’s view in Game 0 is indistinguishable from Game 1 . Game 2 : This game is identical to the previous one, e xcept that we replace each ciphertext generated in the registration algorithm to the encryption of a random Elo value 𝑅 ∗ of the same rank. Since all proofs in Game 1 are simulated and thus do not depend on any particular witness, replacing the original ciphertexts will not cause any problem. The IND-CP A se curity guarantees that this replace- ment is indistinguishable to the adversary . Notice that we only replace the ciphertext with those honestly generated by running the encryption algorithm on random Elo value of the same rank, so the public statement remains valid in the relation. Game 3 : Here, we r eplace each corresponding commitment by one computed from 𝑅 ∗ and a fresh randomness 𝑟 ∗ . Because the proofs are simulated and and the commitment scheme is hiding, the re- placement is valid and indistinguishable. Hidden Elo CODASPY ’26, June 23–25, 2026, Frankfurt am Main, Germany Now the adversar y’s view depends on 𝑅 ∗ and it is independent of the random bit 𝑏 . In such case, it can win the game with probability no better than a half. Thus, given that the commitment scheme is hiding, the range proof is zero-kno wle dge and the homomorphic encryption scheme is IND-CP A secure, our construction H-Elo preserves Hidden Elo. □ 7 Evaluation W e have not benchmarked the range proof separately . In our pr oto- col, the service provider performs many homomorphic evaluations per game, while the user generates at most one proof p er 𝑁 games. Accordingly , the amortise d online cost is expected to be dominate d by the FHE computation, although the precise trade-o depends on the instantiation. The NIZK considered here is a composed one, combining a commitment-based range proof with a proof that the FHE ciphertext encrypts the same value . It is most naturally instan- tiated via a lattice-native NIZK [36]. W e leave the instantiation and benchmarking of the range proof as future work. W e evaluate the usability of H-Elo by measuring the runtime, memory usage and accuracy of the FHE-based up date mechanism proposed in Algorithm 3 in a chess-based scenario. W e implement the algorithm with the OpenFHE library [6] and b enchmark it on a standard desktop machine with a 12th Generation Intel Core i7-12700@3.7GHz CP U, 32GB RAM, running Ubuntu 24.04.2 LTS. Runtime and memory usage experiments were performed 500 times ( single-thread) and the average results for each parameter set is provided in T able 1 and T able 2, r esp ectively . Accuracy r esults, provided in T able 3, are calculated after 10 000 consecutive rating updates on a randomly initiated rating. More specically , these results show the average dierence between the ne w rating approx- imated with CKKS-RNS using Algorithm 3 ( we provide details of the p olynomial approximation in Appendix D) and the same update computed on plaintext through Equation 1. The opponents’ ratings ( 𝑛 = 3 ) are sampled randomly from the same distribution as the player and the match outcomes are picked randomly between loss (0), draw (0.5) and win (1). Additionally , we cover the results of multi-threading in Appendix C. W e run our experiments on three parameter sets with dierent security levels: (1) security level 𝜆 ≈ 12 – a toy parameter set for showcasing the functionality of the implementation. (2) security level 𝜆 ≈ 80 – custom parameter set estimated to 𝜆 = 80 bits [8]. (3) security level 𝜆 ≈ 128 – standard 128-bit security level parame- ter set [7]. Open Science & Reproducible Research. T o support open and reproducible research, w e provide our source code on GitHub 2 . 7.1 Runtime Analysis T able 1 showcases the main runtime benchmarks: (i) key generation costs ( pk / sk , rlk , bsk ), (ii) individual operation costs, and (iii) one full update cost. The key generation costs consist of three parts: (1) Generate pk and sk – generates the public/private key pair ( pk / sk ) for homomorphic encryption and decryption. 2 H-Elo GitHub Repository T able 1: A verage runtime for each op eration in milliseconds (ms) over 500 iterations ( 𝑛 = 3 ). Operation Sec Lev el 𝜆 = 12 𝜆 = 80 𝜆 = 128 Generate pk and sk 12.413 204.368 418.347 Generate rlk 32.656 541.294 1120.767 Generate bsk 78.828 1534.842 3332.135 Encryption 2.396 45.868 99.446 Decryption 2.195 27.444 55.088 EvalMul (Constant) 0.087 1.722 4.438 EvalAdd 0.180 3.840 8.457 EvalSub 0.068 0.803 2.430 EvalPoly 59.853 1035.457 2171.868 Bootstrapping 328.714 7449.077 15785.967 Rating Update (RU) 497.483 11465.392 23247.823 RU w\o Bootstrapping 168.769 4016.315 7461.856 (2) Generate rlk – generates the relinearization key ( rlk ) for re- ducing the size of the ciphertext after multiplication and other operations. (3) Generate bsk – generates the b ootstrapping key ( bsk ) for re- freshing the noise of a homomorphic ciphertext. Moreover , the individual costs consist of algorithms used for computing a rating update: (i) encryption, (ii) decr yption, (iii) boot- strapping, (iv) polynomial appr oximation (details provided in Ap- pendix D), (v) multiplication, ( vi) addition, and (vii) subtraction. Following this, it can be observed that the largest computation costs for H-Elo are seen in the ke y generation (particularly "Gener- ate bsk ") as well as the Bootstrapping algorithms. The combined key generation algorithms are the second most computationally expensive algorithms in the scheme, just behind the Bootstrapping algorithm for all parameter sets. More specically , the combined time costs for key generation are 0.12s, 2.28s and 4.87s, respectively for each parameter set. How ever , key generation needs to be run only once during registration for the functionality of H-Elo . As such, these costs are reasonable in most scenarios as they will not introduce consistent latency for users of the application. On the other side, the bootstrapping algorithm is the most expen- sive part in H-Elo taking on average 15.79s to compute on security level 𝜆 = 128 and a full update takes 23.25s on average. While the computation time is considerably longer than a plainte xt alterna- tive (which takes a fraction of a second), the benets come in the additional se curity that is provided and keeps the rating secret from malicious users who aim to maximize their odds of obtaining a ben- ecial result. More importantly , the individual costs of computing a rating update without bootstrapping are low as even on the highest security level parameter set it takes approximately 7.46s to compute an update for a user . In practice, this computational cost would be divided into smaller parts, where SP could blindly compute part of the update after each match up to 𝑛 − 1 . In this case, 𝑢 𝑖 would only have to wait for the nal update to be computed after his latest CODASPY ’26, June 23–25, 2026, Frankfurt am Main, Germany Mindaugas Budzys, Bin Liu, and Antonis Michalas match. In our benchmarking scenario, that would hav e a latency of approximately 17.99s for 𝑢 𝑖 on security level 𝜆 = 128 (a single run of Algorithm 3, where 𝑗 == 𝑛 − 1 ), despite the 𝑛 value chosen as all previous updates up to 𝑛 − 1 could be computed after each match. Considerations. From these experiments, we can conclude that H-Elo does not allow for constructing use cases which would require instant access to the updated ratings. Ho wever , the costs are reason- able for implementing it in less time-sensitive applications, such as for online marketplace r eputation systems and online tournaments, where ratings are updated after the tournament concludes. 7.2 Memory Analysis T able 2: A verage memor y costs for each op eration in megabytes (MB) over 500 iterations ( 𝑛 = 3 ). Operation Sec Lev el 𝜆 = 12 𝜆 = 80 𝜆 = 128 Generate Context 5 . 70 82 . 80 165 . 55 Precompute Bootstrapping 2 . 14 28 . 06 55 . 42 Generate pk and sk 6 . 88 129 . 12 259 . 04 Generate rlk 12 . 68 197 . 79 395 . 36 Generate bsk 163 . 04 3538 . 72 7548 . 96 One Ciphertext 1 . 04 15 . 70 29 . 56 Encryption 0.00 0.00 0.00 Decryption 0.00 0.00 0.00 EvalMul (Constant) 0.32 0.00 0.00 EvalAdd 0.00 4.80 2.24 EvalSub 0.00 0.00 0.00 EvalPoly 3.80 33.90 81.21 Bootstrapping 32.17 21.14 20.10 Similarly to subsection 7.1, the memor y cost benchmarks pre- sented in T able 2 are divided into three parts: (i) context generation and precomputation memor y usage, (ii) key generation memor y usage, and (iii) individual operation memory usage. From these results, the core memory overhead of H-Elo is from setting up the parameter sets as well as generating the requir e d keys. More specically , the highest costs comes from generating and storing the b ootstrapping key ( bsk ) with the costs reaching approximately 7 549 MB (7.5 GB) of memory on the highest secu- rity level. While memor y costs for generating the cryptographic contexts and keys ar e high, they are manageable by SP . The keys can be serialized and stor ed securely on a database and only loaded into memory when a rating update is required for a user . With cur- rent capabilities of servers with terabytes of storage the approach is scalable to moderate user base sizes. Future improvements to HE key sizes, through bootstrapping key optimizations [2], would improve the scalability of the appr oach even further . Conversely , the memory costs of the individual op erations are negligible, varying between 0.00 MB and 0.081 MB throughout the individual operations for security level 𝜆 = 128 . In lower security levels the variation was even lower . Due to this, it is possible to conclude that the individual operations do not contribute to the memory usage. Considerations. The overall memory costs are comprised of preparing the parameter set and generating the needed keys for performing all computations. In view of these results, each appli- cation case needs to decide how to implement key management. With a smaller user bases, each user can generate their o wn keys while retaining proper functionality . Conversely , use cases with large user bases would require an alternative solution, such as hav- ing trusted, intermediate parties for key management (for example team managers who could reveal information to their play ers). 7.3 Accuracy T able 3: Rating dierence plaintext and HE computed up- dates over 10,000 consecutive updates ( 𝑛 = 3 ). Lower is better . Metric Sec Lev el 𝜆 = 12 𝜆 = 80 𝜆 = 128 Mean dierence 0 . 620 · 10 − 4 1 . 990 · 10 − 4 5 . 569 · 10 − 4 Standard deviation 0 . 463 · 10 − 4 1 . 601 · 10 − 4 4 . 631 · 10 − 4 Min dierence 0 . 0004 · 10 − 4 0 . 000 0 . 0004 · 10 − 4 Max dierence 2 . 715 · 10 − 4 12 . 94 · 10 − 4 34 . 92 · 10 − 4 CKKS is an approximate HE scheme, meaning arithmetic op- erations introduce noise to the r esult, which may deteriorate the precision of the underlying plaintext. A s H-Elo makes use of CKKS for rating updates, it is important to measur e this variance b etween plaintext and encrypted computations. Following this, T able 3 pro- vides four metrics to measure the deviation fr om plaintext results (the estimated precision is covered in Appendix E). Specically , the table contains: (i) mean dierence, (ii) standard deviation, (iii) min- imum dierence, and (iv ) maximum dierence. Our approach shows negligible deviation from plaintext r esults, as the mean dierence between the plaintext and encrypted results are only 5 . 569 · 10 − 4 with the maximum dierence b eing 34 . 92 · 10 − 4 on some rating updates. Additionally , these results wer e achieved without using more computationally e xp ensive approaches, such as iterative bootstrapping [33]. The standard deviation is equivalently low , resulting in a de viation of 4 . 631 · 10 − 4 after 10 000 consecutive rating updates. Additionally , the minimum dierence reached as low as 0.000 (result showed all zer o es from 8 digits in the fractional part) after 10,000 consecutive updates. As such, we can conclude that while CKKS does introduce some noise to the computations, the overall level of the noise remains low and do es not introduce any meaningful deviation from the exact plaintext results. While the rating is an approximation, a dierence of 5 . 569 · 10 − 4 on average would not aect the fairness of matchmaking even after 10 000 consecutive updates. Hidden Elo CODASPY ’26, June 23–25, 2026, Frankfurt am Main, Germany 7.4 Comparison to Other W orks Lack of Similar W orks as an Indicator of Novelty Comparing H-Elo with dierent private matchmaking techniques introduces unique diculties for fair compar- isons. For example, works on PSI [30, 19] focus on nding and revealing unique items which are the same between two individual sets, leading to a conceptually dierent ap- proach than H-Elo as in our work the fo cus is on keeping a single value (the rating) hidden ev en after nding a match. As such, there are few works – most notably Matchmaking Encryption [10] – with similar goals which would allow for a meaningful comparison with H-Elo . One work that we identied that can be used as a point of com- parison is ME [10]. ME aims to match two users who have individual attributes and can set their o wn policies for a ciphertext to be re- vealed only when an exact match o ccurs between the attributes and policies. While dierent from H-Elo , ME could be used to im- plement a matchmaking system b etween two similarly matched opponents following the same ow as H-Elo . Some of the main dierences between ME and H-Elo is the underlying primitives used, the trust assumptions and the performance. Firstly , H-Elo provides post-quantum security as FHE is con- structed with the quantum-r esistant RLWE assumption, conversely the proposed construction of ME relies on the Bilinear Die-Hellman (BDH) assumption, which is vulnerable to quantum attacks. Secondly , ME assumes the existence of a Trusted Authority (T A ) that can have access to each players p olicies and attributes and is responsible for generating the keys associated to them. H-Elo also makes use of a T A, howev er , the only function it performs is attesting that the ciphertext linked to a users new rating is generated correctly . Consequently , the trust assumptions required in ME are much stronger than those required by H-Elo . Lastly , looking at the p erformance of the tw o w orks, ME [10] out- performs H-Elo by a considerable margin e ven without taking into account the rating update computations as shown in T able 4. How- ever , this gap is something to b e expected as H-Elo makes use of RLWE, and therefore provides post-quantum security , while ME is implemented using BDH which makes the underlying construction more ecient but oers weaker security guarantees. Additionally , ME can run into the same issues as plaintext solutions since a play- ers rating can be kept hidden fr om them as only the T A needs to know the rating for attribute certication, resulting in a player being unsure of his exact rating, which H-Elo avoids. T able 4: Comparison b etween H-Elo and Matchmaking En- cryption. Computation time in miliseconds (ms) ME ( 𝜆 = 80 ) H-Elo ( 𝜆 = 80 ) Key Generation 7.867 16110.504 Encryption 7.012 45.868 Decryption 4.385 27.444 T o conclude, while H-Elo has considerably higher computational costs than ME, H-Elo provides stronger security guarantees and lowers the overall trust assumptions ne eded for implementing rating-based matchmaking. Naturally , a service provider would have to weigh their own capabilities and ne eds when choosing how to implement a private matchmaking solution and what privacy leakages are acceptable in their individual scenario. 8 Conclusion In this paper , we intr o duced H-Elo , a rating system-based match- making protocol by making use of HE and NIZK proving system. T o the best of our kno wledge, this is the rst work to tackle private and secure matchmaking through a rating system without obfuscating a users ratings from the user themselves. From our analysis we show that there is latency can conclude that our approach can be applied to real world scenarios without any noticeable latency for users. Additionally , w e prove H-Elo allows for fair matchmaking against a possible adversary . Future Directions. This paper provides the foundation for ex- ploring private matchmaking through rating system. W e believe that our work can further be expanded into other rating systems, such as Glicko and we leave this r esearch as a future work. Alterna- tive constructions could focus on p erforming the rating updates in a decentralized setting, namely instead of outsour cing the computa- tion to a CSP , the user could make the update locally and pr ove the correctness of the update process and output through zk-SNARKS. Further work could make use of scheme switching in HE to allow for simpler encoding for building an ecient range proof system. Acknowledgments This work was funded by the EU research project SW ARMCHES- TRA TE (No. 101135012). W e thank Dr . K aitai Liang for the discus- sions and his advice during the writing process. W e extend our gratitude to all the revie wers and the valuable feedback they pro- vided to improve this work. References [1] Michel Abdalla, Dario Catalano, Romain Gay, and Bogdan Ursu. 2020. Inner- product functional encryption with ne-grained access control. In Asiacrypt 2020-26th A nnual International Confer ence on the Theory and Application of Cryptology and Information Security . V ol. 12493. Springer, 467–497. [2] Rashmi Agrawal, Anantha Chandrakasan, and Ajay Joshi. 2024. Heap: a fully homomorphic encryption accelerator with parallelized bo otstrapping. In 2024 ACM/IEEE 51st Annual International Symposium on Computer Architecture (ISCA) . IEEE, 756–769. [3] Rashmi A grawal et al. 2023. High-precision rns-ckks on xed but smaller word- size architectures: theory and application. In Pr o ceedings of the 11th W orkshop on Encrypted Computing & A pplied Homomorphic Cryptography , 23–34. [4] Shweta Agrawal, Rishab Goyal, and Junichi T omida. 2021. Multi-input quadratic functional encryption from pairings. In Advances in Cr yptology–CRYPTO 2021: 41st A nnual International Cr yptology Conference, CRYPTO 2021, Virtual Event, August 16–20, 2021, Proceedings, Part I V 41 . Springer, 208–238. [5] Ahmad Al Badawi and Y uriy Polyakov. 2023. Demystifying bootstrapping in fully homomorphic encryption. Cryptology eprint ar chive . [6] Ahmad Al Badawi et al. 2022. Openfhe: open-source fully homomorphic en- cryption library. In Proceedings of the 10th W orkshop on Encr ypted Computing & Applied Homomorphic Cr yptography (W AHC’22). A ssociation for Computing Machinery , Los Angeles, CA, USA, 53–63. doi:10.1145/3560827.3563379. [7] Martin Albrecht et al. 2021. Homomorphic encryption standard. Protecting privacy through homomorphic encryption , 31–62. [8] Martin R Albrecht, Rachel P layer, and Sam Scott. 2015. On the concrete hardness of learning with errors. Journal of Mathematical Cryptology , 9, 3, 169–203. CODASPY ’26, June 23–25, 2026, Frankfurt am Main, Germany Mindaugas Budzys, Bin Liu, and Antonis Michalas [9] Amanda Askell et al. 2021. A general language assistant as a laboratory for alignment. arXiv preprint . [10] Giuseppe Ateniese, Danilo Francati, David Nunez, and Daniele V enturi. 2021. Match me if you can: matchmaking encr yption and its applications. Journal of Cryptology , 34, 1–50. [11] Nuttapong Attrapadung and Shota Y amada. 2015. Duality in abe: converting attribute based encryption for dual predicate and dual policy via computational encodings. In T opics in Cryptology—CT -RSA 2015: The Cryptographer’s T rack at the RSA Conference 2015 . Springer, 87–105. [12] Eli Ben-Sasson, Alessandro Chiesa, Michael Riabzev , Nicholas Spooner, Madars Virza, and Nicholas P War d. 2019. Aurora: transparent succinct arguments for r1cs. In Advances in Cryptology–EUROCRYPT 2019: 38th A nnual Interna- tional Conference on the Theory and A pplications of Cryptographic Techniques, Darmstadt, Germany, May 19–23, 2019, Procee dings, Part I 38 . Springer, 103–128. [13] Dan Boneh, Amit Sahai, and Brent W aters. 2011. Functional encryption: deni- tions and challenges. In Theory of Cryptography: 8th Theory of Cr yptography Conference, TCC 2011. Springer, 253–273. [14] Zvika Brakerski, Craig Gentry, and Vinod V aikuntanathan. 2014. (leveled) fully homomorphic encryption without bootstrapping. ACM Transactions on Computation Theory (TOCT) , 6, 3, 1–36. [15] Jung Hee Che on, K yoohyung Han, Andrey Kim, Miran Kim, and Y ongsoo Song. 2018. A full rns variant of approximate homomorphic encr yption. In International Conference on Selected Areas in Cr yptography . Springer, 347–368. [16] Jung Hee Che on, K yoohyung Han, Andrey Kim, Miran Kim, and Y ongsoo Song. 2018. Bootstrapping for approximate homomorphic encryption. In A n- nual International Conference on the Theor y and A pplications of Cr yptographic T echniques . [17] Jung Hee Cheon, Andrey Kim, Miran Kim, and Y ongsoo Song. 2017. Homo- morphic encryption for arithmetic of approximate numbers. In International Conference on the The ory and Application of Cr yptology and Information Security . Springer. [18] Ilaria Chillotti, Nicolas Gama, Mariya Georgieva, and Malika Izabachène. 2020. Tf he: fast fully homomorphic encryption over the torus. Journal of Cryptology . [19] Kelong Cong, Radames Cruz Moreno, Mariana Botelho da Gama, W ei Dai, Ilia Iliashenko, Kim Laine, and Michael Rosenb erg. 2021. Labeled psi from homomorphic encryption with reduced computation and communication. In Proceedings of the 2021 ACM SIGSAC Conference on Computer and Communica- tions Security , 1135–1150. [20] Junfeng Fan and Frederik V ercauteren. 2012. Somewhat practical fully homo- morphic encryption. Cryptology ePrint A rchive . [21] Amos Fiat and Adi Shamir. 1986. How to prove yourself: practical solutions to identication and signature problems. In CRYPTO . (Jan. 1986). [22] Gayathri Garimella, Payman Mohassel, Mike Rosulek, Saeed Sadeghian, and Jaspal Singh. 2021. Private set operations from oblivious switching. In IACR international conference on public-key cryptography . Springer, 591–617. [23] Craig Gentry . 2009. A fully homomorphic encr yption scheme . Stanford univer- sity . [24] Mark E Glickman. 1995. A comprehensive guide to chess ratings. American Chess Journal , 3, 1, 59–102. [25] Mark E Glickman. 2012. Example of the glicko-2 system. Boston University , 28. [26] Mark E Glickman and Albyn C Jones. 1999. Rating the chess rating system. CHANCE-BERLIN THEN NEW YORK - , 12, 21–28. [27] Sha Goldwasser, Silvio Micali, and Chales Racko. 2019. The knowledge complexity of interactive proof-systems. In Providing sound foundations for cryptography: On the work of sha goldwasser and silvio micali , 203–225. [28] Vipul Goyal, Omkant Pandey, Amit Sahai, and Br ent Waters. 2006. Attribute- based encryption for ne-graine d access control of encrypted data. In Proce ed- ings of the 13th ACM conference on Computer and communications security . [29] Shai Halevi and Victor Shoup. 2020. Design and implementation of helib: a homomorphic encryption library. Cr yptology ePrint A rchive . [30] Y uanyuan He, Xinyu T an, Jianbing Ni, Laurence T Y ang, and Xianjun Deng. 2022. Dier entially private set intersection for asymmetrical id alignment. IEEE Transactions on Information Forensics and Security , 17, 3479–3494. [31] Andrey Kim, Y uriy Polyakov, and Vincent Zucca. 2021. Revisiting homomor- phic encr yption schemes for nite elds. In International Conference on the Theory and Application of Cr yptology and Information Security . Springer. [32] Vladimir Kolesnikov, Ranjit Kumaresan, Mike Rosulek, and Ni T rieu. 2016. Ecient batched oblivious prf with applications to private set intersection. In Proceedings of the 2016 ACM SIGSAC Conference on Computer and Communica- tions Security , 818–829. [33] Joon- W oo Lee, Eunsang Lee, Y ongwoo Lee, Y oung-Sik Kim, and Jong-Se on No. 2021. High-precision bootstrapping of rns-ckks homomorphic encr yption using optimal minimax polynomial appro ximation and inverse sine function. In Advances in Cryptology–EUROCRYPT 2021: 40th Annual International Conference on the Theor y and Applications of Cr yptographic T echniques . Springer, 618–647. [34] Y ehuda Lindell and Ariel Nof. 2018. Fast secure multiparty ECDSA with practi- cal distributed key generation and applications to crypto currency custody . In Proceedings of the 2018 ACM SIGSAC Conference on Computer and Communica- tions Security CCS . ACM, 1837–1854. [35] Feng-Hao Liu, En Zhang, and Leiyong Qin. 2023. Ecient multiparty probabilis- tic threshold private set intersection. In Proceedings of the 2023 ACM SIGSAC Conference on Computer and Communications Security , 2188–2201. [36] V adim Lyubashevsky, Ngoc Khanh Nguyen, and Maxime Plançon. 2022. Lattice- based zero-knowledge proofs and applications: shorter , simpler , and more general. In Advances in Cryptology - CRYPTO 2022 - 42nd Annual International Cryptology Conference, Proceedings, Part II . Springer, 71–101. [37] C Nuoskala, H Abdinasibfar , and A Michalas. 2024. Spade: digging into se- lective and partial decryption using functional encryption. In The 20th EAI International Conference on Security and Privacy in Communication Networks (SecureComm’24) . EAI. [38] Benny Pinkas, Thomas Schneider , Christian W einert, and Udi Wieder. 2018. Ef- cient circuit-based psi via cuckoo hashing. In A nnual International Conference on the Theor y and Applications of Cr yptographic T echniques . Springer, 125–157. [39] Benny Pinkas, Thomas Schneider , and Michael Zohner. 2018. Scalable pri- vate set intersection based on ot extension. ACM Transactions on Privacy and Security , 21, 2, 1–35. [40] Ulrich Pörschmann, Fritz Trillmich, Birte Mueller, and Jochen BW W olf. 2010. Male reproductive success and its b ehavioural correlates in a polygynous mammal, the galápagos sea lion (zalophus wollebaeki). Molecular Ecology . [41] Peter Rindal and Mike Rosulek. 2017. Improved private set intersection against malicious adversaries. In A nnual International Confer ence on the Theor y and A pplications of Cr yptographic T echniques . Springer, 235–259. [42] Ronald L Rivest, Len Adleman, Michael L Dertouzos, et al. 1978. On data banks and privacy homomorphisms. Foundations of secure computation , 4, 11. [43] Michael Rosenberg, Jacob White, Christina Garman, and Ian Miers. 2023. Zk- creds: exible anonymous credentials from zksnarks and existing identity infrastructure. In 2023 IEEE Symposium on Security and Privacy (SP) . IEEE. [44] Amit Sahai and Brent W aters. 2005. Fuzzy identity-based encryption. In Ad- vances in Cryptology–EUROCRYPT 2005: 24th Annual International Conference on the Theory and A pplications of Cryptographic Techniques . [45] Adi Shamir. 1985. Identity-based cryptosystems and signature schemes. In Advances in Cryptology: Procee dings of CRYPTO 84 4 . Springer, 47–53. [46] Calvin Hartono Soemardi, Mario Indra Radityaputra, Raiza Rahman, Alexan- der Agung Santoso Gunawan, and Karen Etania Saputra. 2023. T esting how dating apps recommend a potential matches for user. In 2023 8th International Conference on Information T echnology and Digital A pplications (ICITDA) . IEEE. [47] Arisa T suji and Masato Oguchi. 2024. Comparison of f he schemes and libraries for ecient cryptographic processing. In 2024 International Conference on Computing, Networking and Communications (ICNC) . IEEE Computer Society. [48] Niki V eček, Matej Črepinšek, Marjan Mernik, and Dejan Hrnčič. 2014. A com- parison between dierent chess rating systems for ranking evolutionary al- gorithms. In 2014 Fe derated Conference on Computer Science and Information Systems . IEEE, 511–518. [49] Chenkai W eng, Kang Y ang, Xiang Xie, Jonathan K atz, and Xiao Wang. 2021. Mystique: ecient conversions for { zero-knowledge } proofs with applications to machine learning. In 30th USENIX Security Symposium (USENIX Security 21) . [50] Mingli Wu and T sz Hon Y uen. 2023. Ecient unbalanced private set interse c- tion cardinality and user-friendly privacy-preserving contact tracing. In 32nd USENIX Security Symposium ( USENIX Security 23) , 283–300. A Design Rationale T o implement H-Elo it was important to decide on the HE scheme we would utilise for the homomorphic op erations. The main schemes for consideration were (i) B/F V; (ii) BGV; (iii) CKKS; (iv) TFHE. A d- ditionally , the functionalities we required are as follo ws: (1) Ability to compute an Elo rating update, which consists of (i) two additions; (ii) two subtractions; (iii) two multiplications with a constant; (iv) a polynomial approximation of Equation 2. (2) Bootstrapping capabilities; (3) Allow values from 0 to 4000. Following our requirements we analysed the main HE schemes. Beginning with TFHE, while it is optimized to perform bootstrap- ping on sparsely packed ciphertexts, TFHE uses logic gates for ho- momorphic operations. Due to this, arithmetic op erations become more complex to implement compared to other schemes. Addition- ally , as TFHE performs b ootstrapping after each gate, the computa- tional and memory costs of TFHE grow rapidly for each arithmetic Hidden Elo CODASPY ’26, June 23–25, 2026, Frankfurt am Main, Germany 0 50 100 150 200 250 300 0 200 400 600 800 Users Runtime (s) 𝜆 = 12 𝜆 = 80 𝜆 = 128 (a) Runtime per Opponent Amount 0 50 100 150 200 250 300 0 2 , 000 4 , 000 6 , 000 8 , 000 Users Memory Usage (MB) (b) Memory Usage per Opponent Amount Figure 4: Opponent Number Cost Impact operation that is performed [47]. Additionally , the performance of TFHE is the best when the values are bound to 8-bit integers ( 2 8 ). While values upwards of 2 32 are possible, the performance of the scheme degrades and takes longer for the computations than other schemes [5, 47]. As such, we excluded TFHE as a choice . The remaining schemes are the exact HE schemes B/F V and BGV , as well as CKKS, an approximate HE scheme. Both exact schemes have similar capabilities for integer-based homomorphic operations and t our requirements. Howev er , the core reasoning for not choosing these schemes comes from performance, namely integer-based polynomial approximat ion of Equation 2 ends up being both costly and inaccurate, with the polynomial depth being limited and the result potentially becoming more inaccurate than CKKS. Additionally , another reason for cho osing CKKS was the cost of bootstrapping. While BGV does have better b ootstrapping capabilities in terms of performance for sparsely packed ciphertext (to a point), it shows lower precision of the resulting refreshed ciphertext than CKKS. This could introduce a more pronounced error b etween the plaintext and encrypted result. Additionally , following comparisons of CKKS and BGV , we can notice that BGV performs worse when bootstrapping is required [5] than CKKS. Due to these reasons, we choose CKKS over other HE schemes. B Notation W e denote the HE algorithms for key generation, encryption and decryption as we dened them in Denition 1. W e expand the evaluation algorithm into separate algorithms r espe ctive to their underlying function. More specically: • EvalAdd ( 𝑐 𝑥 , 𝑐 𝑦 ) – is the addition algorithm, which evaluates 𝑐 𝑥 + 𝑐 𝑦 ; • EvalSub ( 𝑐 𝑥 , 𝑐 𝑦 ) – is the subtraction algorithm, which evaluates 𝑐 𝑥 − 𝑐 𝑦 ; • EvalMul ( 𝑐 𝑥 , 𝑐 𝑦 ) – is the multiplication algorithm, which evaluates 𝑐 𝑥 · 𝑐 𝑦 ; • EvalPoly ( 𝑐 𝑥 , 𝑓 ) – is the polynomial approximation algorithm, which uses Chebyshev approximations to evaluate a specic function 𝑓 ( 𝑐 𝑥 ) . • EvalBootstrap ( 𝑐 ) – is the bootstrapping algorithm, which re- freshes the accumulated noise of a ciphertext 𝑐 to allow further computations. More sp ecically , it can be dened as homomorphi- cally evaluating the decryption circuit with an encr ypted secret key (also known as the bootstrapping key bsk = HE . Enc ( pk , sk ) ), namely HE . Bootstrap ( 𝑐 ) = HE . Eval ( evk , HE . De c ( · ) , bsk , 𝑐 ) . C Multi-threaded Results Increasing the number of matches required for a rating update in- creases the runtime costs linearly as can be seen in Figure 4a. The protocol execution can also be multi-threaded resulting in lower runtime for a rating update. In comparison, a single-threaded exe- cution takes approximately 799s, while a multi-threaded execution takes 297s (approximately 60% decrease in runtime), when 𝑛 = 300 and 𝜆 = 128 . Naturally , these r esults would continue to hold true as 𝑛 increases, but the eciency of multi-threading is r e duced when 𝑛 is reduced. It is important to note, that these results show the total time to fully compute the new rating after all matches con- cluded, however as noted previously , this would not be required in most applications, as the expecte d outcomes ( 𝑐 𝑒 𝑥 𝑝 and their sum in 𝑐 𝑒 𝑥 𝑝 − 𝑠𝑢𝑚 ) could be precomputed after each match to optimize the update time. So the practical latency w ould be simplied and reduced to a single run of algorithm 3, resulting in a true latency of about 18s before the new rating is obtained. Similarly to the runtime analysis, the memor y costs rise linearly as more matches (opponents) are required (see Figure 4b). Using the multi-thr eade d approach increases memory usage by about 35% , increasing fr om approximately 8 312 MB (8.3 GB) of memory usage to 11 240 MB (11.2 GB) of memory usage , when 𝑛 = 300 and 𝜆 = 128 . D Polynomial Approximation of Equation 2 W e utilised Chebyshev polynomials to approximate Equation 2 and decided upon the following parameters: T able 5: Polynomial approximation details of Equation 2 1 1+10 𝑥 Bound [ -5;+5] Polynomial Degree 50 Multiplicative Depth 7 W e analysed the potential b ounds for the function 1 1+10 𝑥 , where 𝑥 = ( 𝑅 𝑜 𝑝 𝑝 − 𝑅 𝑝𝑙 𝑎 𝑦𝑒 𝑟 ) / 400 . In this case, the bound will depends on the user rating and equivalently the range in each rank, so CODASPY ’26, June 23–25, 2026, Frankfurt am Main, Germany Mindaugas Budzys, Bin Liu, and Antonis Michalas if a single rank cov ers 500 rating p oints, then the b ound will be between the values [ -1.25;+1.25], naturally as the gap between ranks increases, the bound increases. T o simulate the capabilities of our scheme we choose to use a b ound of [ -5;+5], which corresponds to a maximum dierence of 2000 rating points between players. While this bound is not realistic, it acts as a stress test, sho wing that the scheme can remain accurate and functional even with large bounds. Following this, we picked the polynomial degree to be 50 as from our experiments this degr e e showed the b est accuracy and performance trade-o. Namely , this choice results in an approximate error of about 10 − 6 , from our testing this r esulte d in the best accuracy for a full update even with b ootstrapping, which tends to degrade the precision. W e provide the error curve in Figure 5. Figure 5: Polynomial Approximation Err or , when Bound = [ -5;+5] and Degree = 50. E Precision Bits Throughout most runs, the estimated pr e cision remained around 52-bits. Howev er , during certain updates it dropped to values be- tween 10-14 bits. W e showcase the change of the estimate d precision in Figure 6. Despite this, the drops did not have a major impact on the actual accuracy results on average as shown in T able 3. Figure 6: Precision bits after 10 000 consecutive updates, when 𝜆 = 128 .
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment