Decentralized Proof-of-Location for Content Provenance: Towards Capture-Time Authenticity
Reliable use of real-world data requires confidence that recorded evidence reflects what actually occurred at the moment of capture. In adversarial or incentive-misaligned cyber-physical settings, device-centric provenance and post-capture verificati…
Authors: Eduardo Brito, Fern, o Castillo
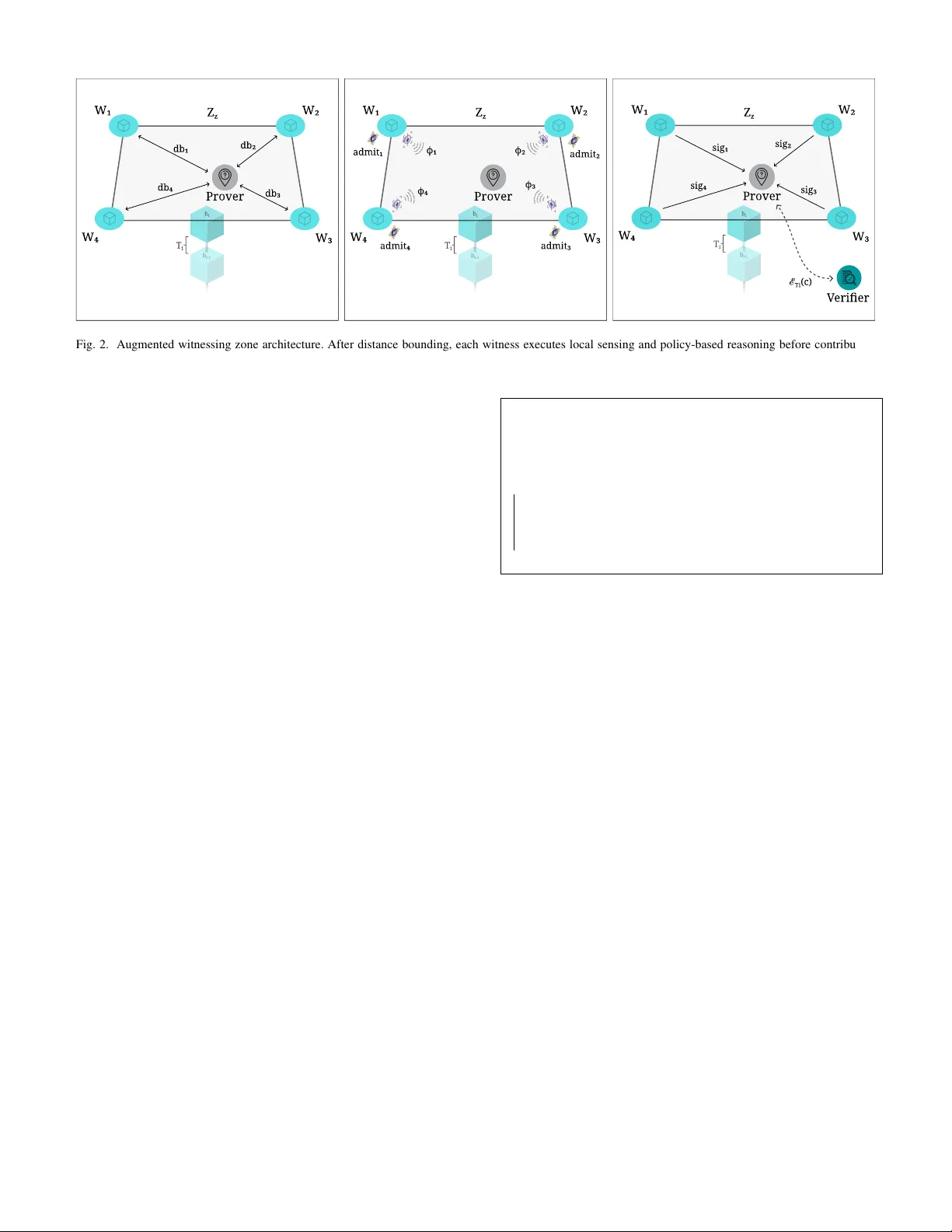
Preprint. This work has been accepted for publication at the 5th International W orkshop on Architect- ing and Engineering Digital T wins (AEDT 2026), to appear in the Companion Proceedings of the 23rd IEEE International Conference on Software Architecture (ICSA 2026). Decentralized Proof-of-Location for Content Pro v enance: T o wards Capture-T ime Authenticity Eduardo Brito ∗ † , Fernando Castillo ‡ , Amnir Hadachi † , Ulrich Norbisrath † , Jonathan Heiss ‡ ∗ Cybernetica AS, Estonia † Univ ersity of T artu, Estonia ‡ TU Berlin, Germany eduardo.brito@cyber .ee, { amnir .hadachi,ulrich.norbisrath } @ut.ee, { fc,jh } @ise.tu-berlin.de Abstract —Reliable use of r eal-world data requires confidence that recorded e vidence reflects what actually occurr ed at the moment of capture. In adversarial or incentive-misaligned cyber- physical settings, device-centric provenance and post-capture verification are insufficient to provide that guarantee. This paper builds on Proof-of-Location (PoL) as a baseline for establishing where and when e vents take place, and extends it with a witnessing-zone architecture in which multiple in- dependent observers collectively validate ph ysical events. The resulting approach produces auditable evidence artifacts that can support downstream systems in cyber -physical settings, without relying on centralized trust. Through representativ e scenarios and simulation-based evaluation, this paper shows how such architectur es impro ve sensor data trustw orthiness and r esilience to fabricated or staged events. Index T erms —Proof-of-Location; Content Pr ovenance; Capture-T ime Evidence; Cyber-Ph ysical Systems I . I N T R O D U C T I O N In distributed, multi-stak eholder cyber -physical settings with externally sourced observations, the question is not only whether data was recorded, but whether it can be trusted as a faithful account of what physically occurred. When incentives to misrepresent events exist, such trust cannot rest on a single device or party . This challenge is especially rele v ant for Digital T wins (DTs) that ingest externally sourced observations into state updates, analytics, and audit trails. Decentralized Proof- of-Location (PoL) systems provide a principled foundation. By combining distance-bounding protocols with Byzantine f ault- tolerant consensus among independently positioned witnesses, PoL architectures produce cryptographic proofs that a de vice was present within a bounded spatial region during a bounded temporal interval [1], [2]. These proofs establish time-and- space inte grity : verifiable evidence of where and when an ob- servation w as captured, grounded in physical-layer constraints. Howe v er , time-and-space integrity is insuf ficient when the content of a record must also be trusted. A de vice with a valid location proof can photograph synthetic imagery , record staged en vironments, or transmit misleading telemetry while satisfying all spatial and temporal constraints – an attack class we term scene spoofing . Single-device provenance frame works such as C2P A [3] provide post-capture chain-of-custody guar- antees, but inherit the device’ s un verified claim about what it observed, leaving scene spoofing unaddressed. This work was supported in part by the 2025/2026 Charlemagne Prize Academy Fellowship of the Charlemagne Prize Foundation. This paper introduces an augmented witnessing-zone ar - chitecture that extends decentralized PoL with capture-time evidence : attestations binding digital records not only to place and time, but also to physical context independently observed by a quorum of witnesses at capture time. The contribution is an architectural extension that adds multimodal witness sensing, policy-dri ven local reasoning, and a compact e vidence object that downstream systems can verify before accepting real-world data as input. In this model, a claim is admitted only when a quorum validates both spatio-temporal proximity and contextual coherence within a single interval. This trust layer is particularly relev ant for DTs when external observations influence twin-state e volution, but the architecture is intended for broader use across distrib uted, multi-stakeholder cyber - physical settings. W e motiv ate the design through three use- case domains – agri-commodity containerization, media prov e- nance, and smart mobility – and ev aluate it through domain- specific instantiation and discrete-event simulation quantifying admission rates, rejection of distance-fraud and scene-spoofing attempts, and boundary behavior under stochastic channel conditions. The remainder of the paper is as follows. Section II presents the use cases. Section III surve ys related work. Section IV specifies the baseline model. Section V introduces the augmented architecture. Section VI presents the e v aluation. Section VII discusses the paper and Section VIII concludes. I I . U S E C A S E S The follo wing three domains share a common structure: multiple parties with misaligned incentiv es must later agree on what occurred at a physical ev ent, based on digital records created at capture time. Physical environments are typically dense with ambient signals that collectively encode contextual state. Y et con ventional prov enance mechanisms bind records to a device, not to this surrounding sensory field. In each domain, time-and-space integrity alone leav es a gap that scene spoofing can exploit. a) Agri-Commodity Containerization: Due-diligence regimes such as the EU Deforestation Regulation require traceable linkages between farm-le vel geolocation and downstream events including lot sealing, warehouse ingress or e gress, and container loading [4]. Along this chain – of exporters, aggre gators, shipping agents, importers, and auditors – economic incenti ves div erge. Operational bottlenecks such as re-stows or subcontracted loading further complicate reliable recording of what was handled and when [5], [6]. A de vice proven to be at a loading bay during a sealing window does not establish which lot was inside the container , whether a seal photograph depicts the actual seal, or whether pallet sequences match the physical shipment. These scene-spoofing vectors satisfy proximity constraints while fabricating e videntiary content. Nearby infrastructure could sense BLE signatures of tagged pallets, ambient temperature, or short-range visual confirmation of seal presence, yet cannot verify sealed contents. Structural limits of third-party audits leav e such discrepancies undetected [7], [8]. Similar patterns arise under the U.S. DSCSA [9], EP A e-Manifest [10], and fisheries traceability regimes [11]. Because disputes may surface months later , records must remain self-contained and independently verifiable. b) Media Pr ovenance: In conflict covering, electoral, or breaking-news settings, creators, platforms, newsrooms, and subjects hold distinct stakes in whether footage is ac- cepted as authentic. Synthetic media reduces fabrication costs, while platform processing often strips metadata anchoring assets to specific times and locations [12]–[14]. The resulting “liar’ s dividend” benefits both fabricators and those dismiss- ing genuine evidence [15]. A camera with a valid location proof can still record a staged scene or a screen displaying synthetic content. Surrounding infrastructure could capture ambient audio fingerprints, visual scene descriptors, or RF en vironments to corroborate the presence of a real scene, but cannot attest to narrative truthfulness. Reactive forensics detection methods degrade under transcoding and adversarial adaptation [16], [17]. Whether verification occurs within hours or years, stakeholders require e vidence tied to physical scene conditions at capture, not merely to de vice provenance. c) Smart Mobility: Urban mobility gov ernance increas- ingly relies on where-when rules such as cordon charges, low- emission zones, and geofenced pickup areas. When contested, consequences di ver ge across drivers, fleet operators, munici- palities, and insurers. The evidentiary substrate is fragmented: fixed cameras hav e blind spots, GNSS drifts in urban canyons, and telemetry pipelines introduce synchronization inconsisten- cies [18], [19]. For pure presence queries – e.g., whether a vehicle entered a charge polygon during a billing interval – time-and-space integrity may suffice. Many disputes, howe ver , concern what occurred there: whether a vehicle was stationary or transiting, whether a pickup occurred at the designated curb, or whether a photographed plate matches the vehicle present. Incentiv es to misrepresent are direct. Roadside infrastructure may sense RF fingerprints, Doppler profiles, or image hashes, yet cannot establish driver identity or intent. Priv acy con- straints further limit persistent camera-based repositories [20], [21]. As appeals may arise weeks later, evidence must remain portable and verifiable across institutional boundaries. I I I . R E L AT E D W O R K a) Sensor- and Content-Level Authentication and Pr ove- nance: A wide range of techniques support authentication and prov enance across sensing modalities. De vice-side sign- ing embeds cryptographic credentials at capture, enabling later v erification of integrity and origin, as formalized by the Content Authenticity Initiativ e and C2P A standards [3], [22], [23]. W atermarking provides complementary , content- embedded signals but faces trade-offs between robustness and remov ability , as demonstrated by both resilient schemes and remov al attacks [17], [24], [25]. Reactive forensic methods, such as device fingerprints (e.g., camera PRNU), remain useful yet fragile against sophisticated adv ersaries [26], [27]. Collectiv ely , these approaches strengthen integrity guarantees but assume the capture de vice is trustworthy and that scene conditions were not spoofed. b) Threat Landscape: Generative Manipulation and Scene Spoofing: Advances in generati ve AI models have re- duced the cost of fabricating or altering sensor -deriv ed content, undermining confidence in digital evidence and amplifying the “liar’ s dividend, ” i.e., the strategic dismissal of genuine recordings as fake [12], [13], [28], [29]. As detectors improv e, adversaries adapt, rendering reacti ve forensics a moving tar get. This dynamic motiv ates proactive authenticity: binding acqui- sitions to verifiable spatial and temporal context at capture, so prov enance becomes cryptographic evidence rather than post- hoc probabilistic inference [17]. In particular , scene spoofing – e.g., recording staged en vironments or photographed screens – emerges as a first-class threat that single-de vice assurances cannot exclude. c) Cryptographic and Infrastructural Appr oaches to T rustworthy Sensing: Proactive authenticity increasingly com- bines cryptography with distributed infrastructure. Anchoring content hashes and manifests on distributed ledgers yields tamper-e vident, auditable records across capture and publica- tion, complementing CAI/C2P A and Project Origin [3], [30], [31]. Hardware-backed attestations, such as secure enclaves signing sensor outputs within capture pipelines, strengthen device integrity but still concentrate trust in a single end- point [23], [32]–[34]. T o address scene spoofing and coor- dinated relays, emerging work shifts tow ard collecti ve attesta- tion, where multiple independent devices corroborate the same ev ent, distributing trust across a witness set [1]. d) Pr oof-of-Location (P oL) Protocols and Arc hitectur es: Proof-of-Location (PoL) systems cryptographically establish where and when presence occurred. T ypical designs combine short-range distance bounding with signed witness attesta- tions, aggregated or ledger-anchored for immutability and auditability [2]. By fusing physical signal constraints with cryptographic commitments, PoL mitigates spoofing, relay , and replay attacks that af fect con ventional positioning sys- tems. Decentralized PoL distributes trust across quorum-based witness sets, preventing unilateral proof fabrication [1], [35]. This provides a natural substrate for grounding digital records in real-world spatio-temporal conditions. e) Bridging Spatial Pr oofs and Multimodal Pr ovenance: Extending PoL to sensor pro venance enables capture-time certificates coupling spatial, temporal, and en vironmental evi- dence. Nearby de vices may co-sign attestations incorporating ambient features – light, sound, radio context – forming multimodal proofs that bind content to its physical surround- ings [1], [36]. As sensor networks evolv e to ward reasoning- capable agents, they can validate contextual coherence across modalities, strengthening collectiv e attestations [36]. The ob- jectiv e is to make synthetic fabrications increasingly costly to reproduce coherently across independent observers, while genuine captures remain anchored to shared spatio-temporal state and auditable records [3], [30]. This con ver gence defines the foundation of the present work. I V . T H E W I T N E S S I N G Z O N E : B A S E L I N E M O D E L Follo wing adv ancements on decentralized PoL systems, we adopt the witnessing zone as the baseline architectural model for collective location attestation under timing and trust constraints [1], [2]. This section specifies the minimal structure and guarantees of a witnessing zone (Figure 1), excluding capture-time contextual sensing and local reasoning, which are introduced later . a) Zone Structure: A witnessing zone is a bounded, single-hop spatial region populated by a finite set of authenti- cated witnesses operating under a shared protocol. W itnesses are fixed-position nodes forming a fully connected, non- hierarchical mesh. Zone operation is discretized into fixed- length block intervals of duration T . All witness attestations are bound to a specific interval, and only attestations produced within the same interval are eligible for quorum formation, enforcing temporal soundness and replay resistance [2]. For each interval, witnesses e xecute a Byzantine fault-tolerant consensus protocol to finalize the set of claims admitted by quorum, defining a consensus round whose outcome is a finalized and hashed block b i , containing all claims admitted by quorum during that interv al, yielding a totally ordered, append-only , tamper-evident e vent log [1]. Each witness main- tains a local replica of this ordered log and associated zone configuration state. An operational information management layer governs zone membership, key rotation, configuration updates, and retention policies, and may optionally anchor block hashes or zone state commitments to an external public ledger for additional auditability . In standard two-dimensional deployments, zones are instantiated with four coplanar wit- nesses and a quorum threshold of k = 3 , tolerating one Byzantine witness. b) Interaction Model: W ithin each interval, a pro ver broadcasts a location claim. Each witness independently per- forms a time-critical physical-layer protocol with the prover , typically distance bounding, to deri ve an upper bound on physical proximity . Based on protocol v alidity and proximity alone, witnesses decide whether to attest. A claim is admitted if and only if at least k distinct witnesses produce v alid attestations within the same interv al. c) Identity Model: Each witness possesses a stable cryp- tographic identity represented by a pub l ic–priv ate key pair . W itness identities are established prior to operation and may be realized via PKI-based certification, consortium-managed i-1 Prover V erier Locatio Proof Locatio Attestation Zon Consensus Witnessin Zone Witness 1 Witness 4 Witness 3 Witness 2 Fig. 1. Baseline witnessing zone model. W itnesses form a synchronized mesh, attest to a prover’ s location, and collectiv ely produce a location proof verified by an external verifier . registries, or ledger-anchored identity records, provided iden- tities are authenticated and non-for geable. Provers are treated as untrusted and may be ephemeral; prover identity is not relied upon for correctness. All attestations are scoped to a unique zone id Z z , binding them to a specific witness set and configuration. d) Security Guarantees: The baseline witnessing zone provides spatio-temporal soundness, meaning that the proto- col admits only claims that satisfy time-and-space integrity: presence within a bounded spatial region during a bounded temporal interval. Distance bounding mitigates relay and re- play attacks, while quorum and Byzantine consensus ensure fault tolerance and global consistency under the assumption that fewer than k witnesses are compromised. The model does not assess semantic correctness of claims or en vironmental coherence; it proves that a claim was collectively accepted at a gi ven place and time, b ut not why beyond proximity and quorum. V . A U G M E N T E D W I T N E S S I N G Z O N E M O D E L Building on the baseline witnessing zone model, we aug- ment the witness role beyond proximity verification by incor- porating capture-time contextual sensing and local reasoning into the per-interv al witness decision process. The contribution is an architectural augmentation: it preserves the geomet- ric configuration, block-interval timing, identity assumptions, quorum thresholds, and Byzantine consensus foundations of the base PoL model while refining what each witness ev aluates before contributing to quorum. These additions operate at the lev el of the witness machine , i.e., the local decision logic ex- ecuted independently by each witness during a block interval. As a result, claims remain admitted through interval-bound quorum and consensus, but witness attestations now jointly reflect spatio-temporal proximity and contextual coherence ev aluated at capture-time (Figure 2). A. Capture-T ime Sensing and Local Reasoning Each block interval T i begins with the prover broadcasting a context-bearing claim c ∈ C , consisting of a structured b i T i Prover db4 db1 db2 db3 W1 W4 W3 W2 Z z b i T i Prover W1 W4 W3 W2 Z z ϕ 1 ϕ 4 admit4 admit3 admit2 admit1 ϕ 2 ϕ 3 b i T i Prover V erier Z z sig4 sig1 sig2 sig3 ℰ T i (c) W1 W4 W3 W2 Fig. 2. Augmented witnessing zone architecture. After distance bounding, each witness executes local sensing and policy-based reasoning before contributing to quorum formation. representation of the asserted e vent and an optional set of disclosed features ϕ P . Within the same interval, each witness ex ecutes the steps summarized in Algorithm 1. a) Distance Bounding and Sensing: Each witness w j engages in a time-critical exchange with the prover to deri ve an upper bound db j on physical distance. In parallel, the witness samples its configured sensing modalities (e.g., RF , visual, audio, inertial, ambient) and extracts feature descriptors ϕ j = { f ( m ) j } m , annotated with quality and freshness metadata. Feature descriptors are compact, policy-rele v ant representa- tions of raw sensor signals. For e xample, under a BLE- based policy , f ( BLE ) j may be a beacon fingerprint vector or similarity score, whereas under a visual policy , f ( vis ) j may be an embedding vector or perceptual hash used to compute a thresholded similarity . b) P olicy-Based Reasoning and Evidence Commitment: Each witness ev aluates a versioned policy predicate Admit v ( c, ϕ P , ϕ j , db j ) → { 0 , 1 } , which may encode deterministic rules, statistical thresholds, or learned comparison models. The internal computation need not be externally reproducible; ho wev er , all inputs influencing the decision are cryptographically committed. If the predicate ev aluates to admit j = 1 , the witness commits its local ex ecution state to a Merkle root R j and signs the tuple ( b i , c, R j , v , Z z ) . Quorum formation is strictly interval-bound: only signatures produced within the same block interval T i , anchored in block b i , are composable. If at least k witnesses produce valid signatures, the claim is admitted by the zone and passed to evidence assembly . B. Evidence Semantics and V erification Interface Once a quorum of at least k witnesses has produced valid signatures for the same claim c within interv al T i , the witnessing zone assembles a verifiable evidence object . This object is the sole e xternally visible artifact of the augmented protocol and serves as the unit of verification for downstream systems. Input: Claim c , disclosed features ϕ P , policy version v Deriv e distance bound db j via distance-bounding protocol; Sample sensors and extract features ϕ j ; admit j ← Admit v ( c, ϕ P , ϕ j , db j ) ; if admit j = 1 then Commit inputs and outputs to Merkle root R j ; sig j ← Sign j ( b i , c, R j , v , Z z ) ; Broadcast signature to zone; end Algorithm 1: W itness Machine Execution for Claim c in Block Interval T i The evidence object does not re-ex ecute or reinterpret witness reasoning. Instead, it binds the claim to the set of committed witness decisions and the policy under which they were made: E T i ( c ) := b i , c, { R j } j ∈ Q , σ Q , v , Z z , where Q denotes the quorum of admitting witnesses ( | Q | ≥ k ) and σ Q is the aggregated (threshold) signature. The semantics of E T i ( c ) assert that (i) the claim was ev aluated within a bounded execution window , (ii) a quorum of independent witnesses satisfied both distance-bounding constraints and the policy predicate, and (iii) each witness irrev ocably committed to the inputs and outputs of its local reasoning. V erification checks σ Q against the zone public keys and validates the policy version v . Depending on the trust model, verifiers may accept the e vidence object directly or request selecti ve opening of committed elements. This makes E T i ( c ) a compact interface for downstream consumers, including provenance services and DT data pipelines, to de- cide whether a real-world observation is admissible for state updates, analytics, or later dispute resolution. Figure 3 sum- marizes the interv al-bound interaction flow of the augmented witnessing zone. Fig. 3. Interval-bound interaction flow of the augmented witnessing zone. C. Deployment Profiles and P olicy Examples The augmented protocol generalizes across deployments with different operational constraints, sensing capabilities, and evidentiary requirements. In all cases, distance bounding remains the core spatio-temporal guardrail, while additional sensing and reasoning are applied only after proximity has been v alidated. W e highlight three representative profiles, Co- coa, Media, and Mobility , that illustrate ho w the architecture can be instantiated in practice. a) Cocoa (Supply Chain Sealing and Hand-off): In this scenario, the prov er is a container-mounted device at the point of sealing or custody transfer (e.g., at a port or cooperativ e facility), and the witnesses are fixed infrastructure nodes positioned at known locations near the hand-off point. The primary objecti ve is to bind a transfer ev ent to its physical location and time, ensuring that hand-offs occur in situ and are witnessed by multiple independent parties. • Sensors: BLE signal strength, ambient temperature, short-range ultrasonic chirps. • P olicy (v1): Admit if k -of- n (i) distance bounds are valid, and (ii) the BLE fingerprint matches the kno wn warehouse signature with similarity score abov e threshold τ BLE = 0 . 85 . b) Media (Content Pr ovenance in Public Envir onments): Here, the prov er is a user device (e.g., smartphone or bodycam) broadcasting a claim o ver media being recorded or streamed, and the witnesses are surrounding IoT nodes (e.g., streetlamps, kiosks, or vehicle-mounted sensors). The aim is to tie digital media to its spatial and environmental context at capture time, in order to produce v erifiable provenance certificates. • Sensors: visual scene sketches (e.g., pHash), ambient audio fingerprints, RF beacon en vironment. • P olicy (v2): Admit if k -of- n (i) distance bounds validate proximity , (ii) a vision-language model comparison be- tween the disclosed media frame and the witness snapshot yields similarity > τ vis = 0 . 70 , and (iii) ambient audio hashes match within tolerance. BLE beacon sets must also overlap. c) Mobility (Zone Entry/Exit in Urban T ransit): In mo- bility applications, the prover is typically a vehicle-mounted unit (e.g., in taxis or delivery v ans), and the witnesses are fixed roadside infrastructure. The goal is to produce non-repudiable records of zone crossings or regulated stops, even under GNSS denial or multipath environments. • Sensors: RF en vironment fingerprints, Doppler shift es- timation, IMU bursts, and image hash of nearby infras- tructure. • P olicy (v3): Admit if k -of- n (i) distance bounds vali- date proximity , (ii) IMU trajectory matches an expected crossing pattern, and (iii) RF fingerprints are consistent with the curbside beacon layout. Optional fallback to rule- based logic applies if visual sensors are unavailable. T o make policies concrete, we show a machine-readable ex- ample for the Media profile (Figure 4). It externalizes quorum and sensing thresholds, is v ersioned, and is cryptographically bound to the resulting e vidence object. policy: media_v2 zone_id: Z-17 interval: 2s quorum: k: 3 n: 4 requirements: distance_bound: max_distance: 20m visual_similarity: metric: vlm_embedding threshold: 0.70 audio_hash_match: true beacon_overlap: min_count: 2 on_fail: reject Fig. 4. Illustrati ve machine-readable admission policy for the Media deploy- ment profile. D. Security and T rust Properties The augmented witnessing protocol preserv es the spatio- temporal soundness of decentralized PoL systems [1]. Ad- mission still requires time-critical distance bounding with physically proximate witnesses and satisfaction of a k -of- n quorum within a fixed block interval T , ensuring that accepted claims correspond to bounded e vents in space and time ev en under partial collusion, delay , or transient faults. The augmentation introduces a second, orthogonal protec- tion layer based on v erification-time entropy , i.e. unpredictabil- ity of witness-local e valuation space conditioned on policy . Beyond proximity , a prover must satisfy contextual coherence checks independently ev aluated by multiple witnesses during the same interv al. These checks occur locally at capture time under a versioned policy v , prev enting the prov er from predicting which environmental features will be sampled or how they will be assessed. As a result, admissibility cannot be precomputed, and uncertainty is injected directly into the adversarial strategy space. This entropy derives from heterogeneous sensing modal- ities, policy e volution across zones and versions, and the natural variability introduced by spatially distributed ob- servers. Ev en identically equipped witnesses observe distinct en vironmental slices, making coherent spoofing across a quo- rum substantially more complex. Fabrication therefore requires not only defeating distance-bounding defenses b ut also in- ducing consistent en vironmental agreement across multiple independent observers within the same temporal window . This significantly increases the cost and complexity of adversarial strategies such as: • Relay attacks , in which the pro ver attempts to satisfy proximity constraints via hidden accomplices; • Scene spoofing , where synthetic or staged en vironments are constructed to deceive sensors; • Sensor spoofing , where adversaries attempt to replay or predict expected en vironmental signals; • Collusion , where compromised witnesses are used to fake quorum, mitigated by requiring div ersity and indepen- dence among participants. Accountability is preserved through commitment-based ev- idence construction. Each admitting witness signs a Merkle root binding its observations, intermediate results, and policy identifier; only such signed commitments participate in quo- rum formation. W itnesses are assumed to retain the committed descriptors and minimal supporting metadata for a bounded retention period sufficient to enable dispute resolution. The resulting e vidence object binds the claim, policy v ersion, and aggregated quorum signature into a verifiable artifact. Incorrect admissions can be challenged post hoc through selectiv e opening of committed elements or reference-policy re-ev aluation without disclosing full raw sensor streams or internal model state, maintaining auditability even when local reasoning is approximate or learned. In sum, the augmented protocol strengthens PoL by com- bining physical-layer guarantees with strate gically unpre- dictable, sensor-grounded verification while retaining decen- tralized trust assumptions. V I . I M P L E M E N TA T I O N A N D E V A L UA T I O N T o evaluate resilience against adversarial attempts (e.g., dis- tance fraud) and assess admission policies such as proximity- based and visual verification rules, we implemented a discrete- ev ent simulation using Python and SimPy 1 . This enables controlled analysis under stochastic en vironmental conditions and v alidates protocol behavior and adv ersarial robustness under an explicitly simplified environment model. A. Simulation Envir onment Model The simulation implements the witnessing zone model from Section V using discrete ev ents with SimPy . The main modules are: 1 https://simpy .readthedocs.io/en/latest/ • Cor e Models : 3D positioning ( Vector3 ), zone configuration ( ZoneConfig ), and the DistanceBoundingProtocol based on IEEE 802.15.4a [37] UWB channel models with 32-round exchanges. • En vironmental Sensing : Implements RfFingerprintSensor for RSSI-based beacon measurements and VisualSensor for scene object queries. • Consensus & P olicy : It manages WitnessNode voting with a configurable k -of- n threshold and ev aluates claims against modular poli- cies such as SupplyChainPolicy and VisualVerificationPolicy . The simulation models a single witnessing zone with a radius of R = 20 meters. The zone is monitored by N = 4 witness nodes positioned in a square geometry around the zone center . W e utilize a quorum threshold of k = 3 , requiring at least three witnesses to independently verify and v ote for a location claim before an attestation is issued. Each simulation experiment runs for a duration of T = 60 seconds. The prover broadcasts a ne w location claim ev ery 2 seconds, resulting in a total of 30 claims per e xperiment. The physical layer is modeled using a simplified IEEE 802.15.4a UWB channel model. T o account for en vironmental stochasticity , the path loss ( P L ) at distance d is modeled as: P L ( d ) = P L 0 + 10 γ log 10 d d 0 + X σ (1) where γ is the path loss exponent ( γ = 2 . 0 for LOS), and X σ ∼ N (0 , σ 2 ) represents shadowing effects ( σ = 3 . 0 dB). Ranging errors include a distance-dependent component (1%) and Gaussian multipath noise. B. Experimental Scenarios and Admission P olicies W e ev aluated the protocol using two policies: • Supply Chain Policy: A proximity-based policy that validates if the prov er is within a maximum distance ( 2 R ) of the witness and possesses an RF fingerprint similarity score above 0 . 5 . This represents standard logistics track- ing. • V isual V erification Policy: Extends the proximity check by requiring witnesses to visually confirm specific seman- tic queries (e.g., “Is there a red car?”). This policy fails if the quorum cannot agree on the visual scene description. Using the Supply Chain Policy , we tested four geometric cases, shown in Figure 5: 1) Baseline (4W/6W): An honest prov er is located at (5 , 5) , well within the zone boundaries. W e test with both 4 and 6 witnesses to ev aluate the impact of redun- dancy in the baseline. 2) Distance Fraud: An external attacker at (13 , 13) claims to be inside the zone. Since the distance to the farthest witnesses e xceeds the acceptance threshold, this scenario tests the protocol’ s ability to reject spoofed locations. Fig. 5. Admission probability heatmap of the simulation en vironment representing 4W and the theoretical effectiv e witness zone for d ≤ 20 and k ≥ 3 . 3) Edge Position: An honest prov er is placed at (9 . 28 , 0) , near the ef fectiv e witnessing boundary . This tests the protocol’ s sensiti vity to edge cases where geometric dilution of precision (GDOP) and shado wing might affect quorum consensus. C. P erformance Analysis W e conducted a Monte Carlo analysis with 1000 iterations for each scenario to measure the system’ s reliability in the presence of channel noise. T able I summarizes the perfor- mance across the four geometric scenarios 2 . The Baseline (4W) scenario demonstrates a 100% success rate for honest users within the zone. Increasing the number of witnesses to 6 ( Baseline (6W) ) maintained this performance, confirming that the witness configuration provides robust cov erage. D. Security Analysis The Distance Fraud scenario confirms the protocol’ s secu- rity . Attackers positioned outside the zone attempting to spoof closer positions were rejected in 100% of cases. The Edge Position scenario highlights the conserv ativ e nature of the protocol. Users located exactly at the zone boundary experience a significant drop in admission rate (35.9%), indicating that the system prefers to reject ambiguous edge cases rather than admit potential attackers. In addition to RF constraints, the V isualV erificationP olicy achiev ed a high admission rate when the required ”Red Car” object was present (97%) and dropped to 0% when the object was removed, showing that the witnessing consensus correctly enforced en vironmental prerequisites. 2 N/A as no positive instances exist (TP+FP=0, TP+FN=0). This ev aluation is intentionally limited to simulation and should be read as a feasibility check rather than operational proof. It does not measure hardware timing, field latency , ledger finality , or deployment-scale throughput. Relati ve to baseline decentralized PoL costs already analyzed in prior work [1], [2], the augmentation adds witness-local sensing, one commitment root per admitting witness, and policy- dependent computation whose cost scales mainly with the selected modalities and quorum size rather than with new global protocol rounds. T ABLE I C O MPA R A TI V E A NA L Y SI S O F S I M UL ATI O N S C E NA R I OS ( 1 0 00 I T ER ATI O N S ) Scenario Success Rate Precision Recall Admitted Baseline (4W) 1.000 ± 0.00 1.00 1.000 30.0/30 Baseline (6W) 1.000 ± 0.00 1.00 1.000 30.0/30 Distance Fraud 0.000 ± 0.00 N/A N/A 0.0/30 Edge Position 0.359 ± 0.09 1.00 0.359 10.8/30 V isual (V alid) 0.973 ± 0.08 1.00 0.973 29.2/30 V isual (Inv alid) 0.000 ± 0.00 N/A N/A 0.0/30 V I I . D I S C U S S I O N The augmented witnessing-zone architecture should be understood as a generalizable design pattern rather than a domain-specific solution. The core construct applies to settings where disputes concern not only where and when , but also what occurred. DT engineering is one natural beneficiary , since the e vidence object can serve as a verifiable admission layer for externally sourced observations before they influence twin state, automation, or audit records, but the same interface is rele v ant to other multi-stakeholder cyber-physical systems. Open questions remain around policy lifecycle management, cross-zone interoperability , e vidence portability for long-lived DTs, and adv ersarial behavior beyond single-zone distance fraud. The current ev aluation provides initial v alidation rather than operational proof, and priv acy remains a deployment trade-off [20]: although the evidence object exposes commit- ments rather than raw sensor streams, witnesses still observe local context and selectiv e opening may rev eal sensiti ve en- vironmental features. Hardware-in-the-loop experiments, field pilots, pri vac y-preserving policy verification, and scalability analysis across federated zone topologies are therefore natural next steps. V I I I . C O N C L U S I O N This paper addressed an important challenge for cyber- physical systems operating in distributed, multi-stakeholder settings with externally sourced observations: ensuring that such data is grounded in verifiable physical reality at capture time. Building on Proof-of-Location as a baseline for establish- ing where and when e vents occur , we introduced an augmented witnessing-zone architecture in which multiple independent observers collectively validate physical ev ents and produce auditable evidence objects for do wnstream verification. By extending spatio-temporal attestation with contextual witness agreement, the approach strengthens resistance to scene spoof- ing and other forms of fabricated or staged evidence at capture time. The result is an architectural building block for trustworthy data admission in settings where externally sourced observations influence system state, analytics, or audit records. The ev aluation shows that this can be achiev ed under the studied simulation assumptions without undermining operational predictability . R E F E R E N C E S [1] E. Brito, A. Hadachi, L. Kamm, and U. Norbisrath, “Decentralized Proof-of-Location systems for trust, scalability , and pri vac y in digital societies, ” Scientific Reports , vol. 15, no. 1, p. 19808, 2025. [2] E. Brito, F . Castillo, L. Kamm, A. Hadachi, and U. Norbisrath, “ A taxonomy and methodology for proof-of-location systems, ” in Interna- tional Conference on Enterprise Design, Operations, and Computing . Springer , 2025, pp. 228–244. [3] Coalition for Content P rovenance and Authenticity (C2P A), “C2P A technical specification v2.2, ” 2024, accessed 2025-10-07. [Online]. A vailable: https://spec.c2pa.org/specifications/specifications/1. 4/index.html [4] “Regulation (EU) 2023/1115 of the European Parliament and of the Council of 31 May 2023 on the making av ailable on the Union market and the export from the Union of certain commodities and products asso- ciated with deforestation and forest de gradation and repealing Regulation (EU) No 995/2010, ” https://eur- lex.europa.eu/eli/reg/2023/1115/oj/eng, May 2023, of ficial Journal L 150, 9.6.2023, pp. 206–247, text with EEA relev ance. [5] X. Li, L. Wu, H. Lang, Z. Jin, and P . He, “ A critical literature revie w on layout designs and handling technology in traditional and automated container terminals, ” Tr ansport Economics and Management , vol. 3, pp. 269–280, 2025. [6] L. Zhen, X. Jiang, L. H. Lee, and E. P . Chew , “ A revie w on yard man- agement in container terminals, ” Industrial Engineering & Management Systems , vol. 12, no. 4, pp. 289–304, 2013. [7] G. LeBaron and J. Lister, “Ethical audits and the supply chains of global corporations, ” Sheffield Political Economy Research Institute (SPERI), Univ ersity of Sheffield, T ech. Rep. 1, 2016, accessed 2026-03-24. [Online]. A vailable: https://eprints.whiterose.ac.uk/id/eprint/96303/ [8] C. Searcy , G. Michelson, P . Castka, and X. Zhao, “How auditor working conditions limit supply chain transparency , ” MIT Sloan Management Review , jul 2024, online article, Accessed 2026-03-24. [Online]. A v ailable: https://sloanreview .mit.edu/article/ how- auditor - working- conditions- limit- supply- chain- transparency/ [9] U.S. Food and Drug Administration, “Drug Supply Chain Security Act (DSCSA), ” https://www .fda.gov/drugs/drug- supply- chain- inte grity/ drug- supply- chain- security- act- dscsa, 2013, accessed 2025-10-18. [10] U.S. En vironmental Protection Agency, “Learn about the hazardous waste electronic manifest sys- tem (e-manifest), ” https://www .epa.gov/e- manifest/ learn- about- hazardous- waste- electronic- manifest- system- e- manifest, 2025, accessed 2025-10-18. [11] Food and Agriculture Organization of the United Nations (F AO), “Seafood traceability for fisheries compliance, ” 2024, accessed 2025-10-18. [Online]. A vailable: https://openknowledge.f ao.org/items/ 41d112ed- 0c69- 4740- b47d- a6d955fd565c [12] B. Chesney and D. Citron, “Deep fakes: A looming challenge for priv acy , democracy , and national security, ” Calif. L. Re v . , vol. 107, p. 1753, 2019. [13] R. T olosana, R. V era-Rodriguez, J. Fierrez, A. Morales, and J. Ortega- Garcia, “Deepfakes and be yond: A surv ey of face manipulation and f ake detection, ” Information Fusion , vol. 64, pp. 131–148, 2020. [14] International Press T elecommunications Council (IPTC), “Study e xposes social media sites that delete pho- tographs’ metadata, ” https://www .1854.photography/2013/03/ study- exposes- social- media- sites- that- delete- photographs- metadata/, 2013, accessed 2025-10-18. [15] K. J. Schiff, D. S. Schiff, and N. Bueno, “The liar’ s dividend: Can politi- cians use deepfakes and fake news to ev ade accountability , ” American P olitical Science Review , vol. 100, no. 1, pp. 1–20, 2022. [16] Defense Advanced Research Projects Agency (DARP A), “Se- maFor: Semantic forensics, ” https://www .darpa.mil/research/programs/ semantic- forensics, 2024, accessed 2025-10-18. [17] National Institute of Standards and T echnology, “Reducing Risks Posed by Synthetic Content (NIST AI 100-4), ” NIST , T ech. Rep., 2024. [Online]. A vailable: https://nvlpubs.nist.go v/nistpubs/ai/NIST .AI.100- 4. pdf [18] D. W eng, Z. Hou, Y . Meng, M. Cai, and Y . Chan, “Characterization and mitigation of urban GNSS multipath effects on smartphones, ” Measur ement , vol. 223, p. 113766, 2023. [19] Q. Liu, C. Gao, Z. Peng, R. Zhang, and R. Shang, “Smartphone posi- tioning and accuracy analysis based on real-time regional ionospheric correction model, ” Sensors , vol. 21, no. 11, p. 3879, 2021. [20] D. Bogdanov , E. Brito, A. Jaakson, P . Laud, and R.-M. Rebane, “Zero- knowledge proof-of-location protocols for vehicle subsidies and taxation compliance, ” in International Conference on Availability , Reliability and Security . Springer, 2025, pp. 343–360. [21] Transport for London (TfL), “Ultra low emission zone, ” 2025, accessed 2025-10-18. [Online]. A vailable: https://tfl.gov .uk/modes/ driving/ultra- lo w- emission- zone [22] Content Authenticity Initiative, “How Content Credentials W ork, ” 2025, accessed 2025-10-07. [Online]. A vailable: https://contentauthenticity . org/ho w- it- works [23] Coalition for Content Prov enance and Authenticity (C2P A), “ Attestations and Roots of T rust in C2P A, ” 2024, accessed 2025-10-07. [Online]. A vailable: https://c2pa.org/specifications/specifications/1.4/attestations/ attestation.html [24] Y . W en, J. Kirchenbauer , J. Geiping, and T . Goldstein, “Tree-ring watermarks: Fingerprints for diffusion images that are in visible and robust, ” arXiv preprint , 2023. [25] X. Zhao, K. Zhang, Z. Su, S. V asan, I. Grishchenko, C. Kruegel, G. Vigna, Y .-X. W ang, and L. Li, “Invisible image watermarks are prov- ably remov able using generativ e AI, ” Advances in neural information pr ocessing systems , vol. 37, pp. 8643–8672, 2024. [26] J. Lukas, J. Fridrich, and M. Goljan, “Digital camera identification from sensor pattern noise, ” IEEE T ransactions on Information F orensics and Security , vol. 1, no. 2, pp. 205–214, 2006. [27] F . Mart ´ ın-Rodr ´ ıguez, F . Isasi-de V icente, and M. Fern ´ andez-Barciela, “A stress test for robustness of photo response nonuniformity (camera sensor fingerprint) identification on smartphones, ” Sensors , vol. 23, no. 7, p. 3462, 2023. [28] Y . Mirsky and W . Lee, “The creation and detection of deepf akes: A survey, ” A CM computing surveys (CSUR) , v ol. 54, no. 1, pp. 1–41, 2021. [29] L. V erdoliv a, “Media forensics and deepfakes: an ov erview, ” IEEE journal of selected topics in signal pr ocessing , vol. 14, no. 5, pp. 910– 932, 2020. [30] A. Ramachandran and M. Kantarcioglu, “Smartprovenance: a dis- tributed, blockchain based datapro venance system, ” in Proceedings of the Eighth ACM Conference on Data and Application Security and Privacy , 2018, pp. 35–42. [31] Project Origin, “Building T rust at the Origin, ” 2025, accessed 2026- 03-24. [Online]. A v ailable: https://www .microsoft.com/en- us/research/ project/project- origin/ [32] A. Naveh and E. T romer , “Photoproof: Cryptographic image authen- tication for any set of permissible transformations, ” in 2016 IEEE Symposium on Security and Privacy (SP) . IEEE, 2016, pp. 255–271. [33] Y . Liu, Y . Nakatsuka, A. A. Sani, S. Agarwal, and G. Tsudik, “Vronicle: verifiable provenance for videos from mobile devices, ” in Proceedings of the 20th Annual International Conference on Mobile Systems, Appli- cations and Services , 2022, pp. 196–208. [34] M. Mesa-Sim ´ on, A. Escobar -Molero, B. S ´ aez-Mingorance, D. P . Morales, J. A. ´ Alvarez-Bermejo, and F . J. Romero, “Enabling Li ve V ideo Provenance and Authenticity: A C2P A-Based System with TPM-Based Security for Livestreaming Platforms, ” Author ea Preprints , 2025. [35] FOAM, “FO AM Whitepaper, ” 2018, accessed 2025-10-07. [Online]. A vailable: https://foam.space/publicAssets/FOAM Whitepaper .pdf [36] F . Castillo, O. Castillo, E. Brito, and S. Espinola, “Trustworthy de- centralized autonomous machines: A new paradigm in automation economy , ” in 2025 IEEE International Conference on Blockchain and Cryptocurr ency (ICBC) , 2025, pp. 1–7. [37] M. Poturalski, M. Flury , P . Papadimitratos, J.-P . Hubaux, and J.-Y . Le Boudec, “Distance bounding with IEEE 802.15.4a: Attacks and countermeasures, ” IEEE Tr ansactions on W ir eless Communications , vol. 10, no. 4, pp. 1334–1344, 2011.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment