iBEAMS: A Unified Framework for Secure and Energy-Efficient ISAC-MIMO Systems leveraging Bayesian Enhanced learning, and Adaptive Game-Theoretic Multi-Layer Strategies
Next generation ISAC networks operating in the mmWave and THz bands must provide physical layer secrecy against potential eavesdroppers (mobile and static) while coordinating distributed hybrid edge nodes under stringent power and QoS constraints. Ho…
Authors: Mehzabien Iqbal, Ahmad Y. Javaid
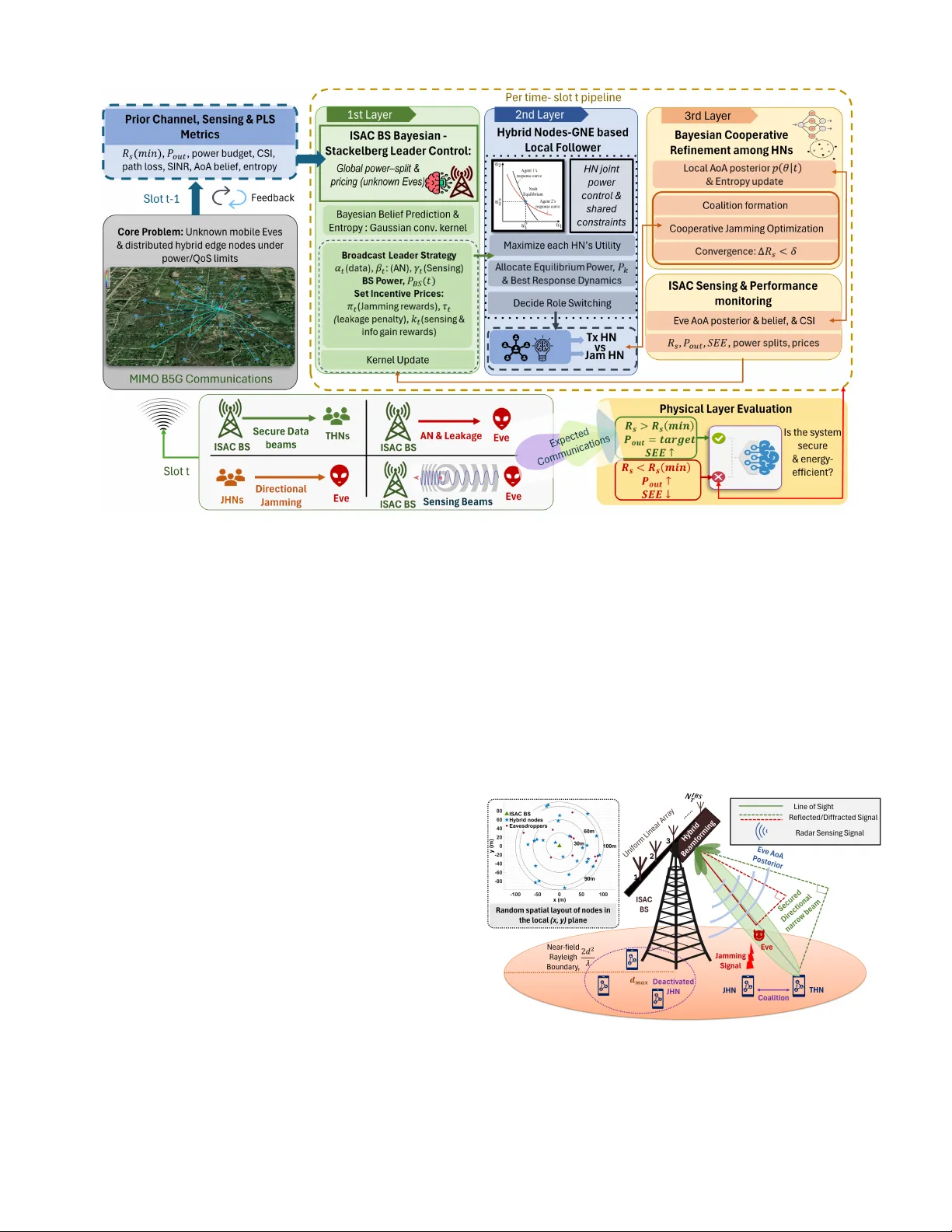
1 iBEAMS: A Unified Frame work for Secure and Ener gy-Ef ficient I SA C-MIMO Systems le v eraging B ayesian E nhanced Learning, and A dapti v e Game-Theoretic M ulti-Layer S trate gies Mehzabien Iqbal Graduate Student Member , IEEE , and Ahmad Y . Ja v aid Senior Member , IEEE Abstract —Next generation ISA C networks operating in the mm wav e and THz bands must provide physical layer secrecy against potential eav esdroppers (mobile and static) while coordinating distributed hybrid edge nodes under stringent power and Quality of Service (QoS) constraints. Howe ver , these r equirements ar e rarely addressed in a unified manner in existing ISA C physical layer security designs. This paper proposes iBEAMS , a hierarchi- cal Stackelberg–GNE–Bayesian framework f or secur e and energy efficient ISA C with distributed hybrid nodes. The pr oposed architectur e integrates: (i) a Stackelberg leader at the ISA C base station that jointly optimizes total transmit power , power splitting among confidential data, artificial noise, and sensing, and broadcasts incentiv e prices to shape follo wer utilities; (ii) a generalized Nash Equilibrium Game in which hybrid nodes select transmit powers and transmission versus jamming roles under coupled interfer ence constraints and base station imposed leakage penalties; and (iii) a Bayesian cooperativ e refinement layer that forms geometry aware jamming coalitions aligned with the posterior distrib ution of eav esdropper’ s Angle of Arrival (AoA). Simulations over carrier fr equencies from 28 GHz to 3 THz demonstrate hierarchical conver gence of both base station and hybrid node decisions with stable cooperativ e friendly jamming. iBEAMS attains approximately 4 . 4 – 4 . 7 bps/Hz average secr ecy rate, achieves about 2 × higher secrecy energy efficiency than fixed artificial noise ISA C, and delivers 30 – 70% higher Secrecy Energy Efficiency(SEE) than a Stackelberg decision based base- line, while maintaining zero outage at 28 GHz. Moreover , the posterior aligned jamming remains sharply directive and resilient under mobile eav esdroppers and increasing adversary density , indicating that iBEAMS can simultaneously act against static and mobile adversaries while coordinating hybrid edge nodes under limited power and QoS constraints. Index T erms —Integrated sensing and communication (ISA C), Physical Layer Security (PLS), secure beamf orming, cooperative jamming, Bayesian inference, Stackelberg Game, Generalized Nash equilibrium (GNE), Game Theory , Hybrid edge Nodes (HNs), mmW ave/THz communications, near -field MIMO, Se- crecy Energy Efficiency (SEE), eavesdr opper localization, adap- tive power allocation. I . I N T R O D U C T I O N T HE need for secure, energy-ef ficient, and sensing-aware wireless infrastructure is rapidly intensifying as beyond fifth-generation (B5G) and sixth-generation (6G) networks are en visioned to support safety-critical, autonomous, and immersiv e applications while still providing high-throughput data pipes [1], [2]. T o achie ve this vision, next genera- tion communications increasingly rely on millimeter-w av e (mmW ave) and terahertz (THz) bands to deliv er multi gigabit transmission in dense network deployments [3], [4]. How- ev er, the same highly directional beams, large bandwidths, and aggressiv e spatial reuse that enable these performance gains also intensify security exposure due to high propagation loss, beam leakage, reflections, and the inherently broadcast nature of wireless channels [5], [6]. Consequently , as wireless infrastructures increasingly inte grate autonomous, and Arti- ficial Intelligence(AI) driv en control, cyber -physical threats are becoming more sophisticated, adaptiv e, and context-aware, thereby creating a pressing need for frameworks that jointly account for security , performance, and situational awareness at the physical layer . Howe ver , existing approaches typically treat communication, sensing, and Physical Layer security (PLS) in isolation, or rely on static, far -field models and offline optimization, leaving the problem open of designing low-comple xity , cross-layer algorithms that can jointly secure and manage mmW a ve/THz systems under near-field operation, mobility , and imperfect channel knowledge. W ithin this context, Integrated Sensing and Communication (ISA C) has emerged as a key paradigm for future wireless systems. By unifying radar and communication functions, ISA C enhances PLS through joint exploitation of sensing and communication (S&C) metrics and information-theoretic limits (detection, estimation, efficienc y , and reliability), while improving spectral, energy , and hardware efficiency through spectrum sharing, hardware reuse, and integrated signal pro- cessing, in contrast to architectures that treat sensing and communication separately [7], [8]. Howe ver , ISA C operation in the mmW ave/THz re gime induces a tightly coupled commu- nication–sensing decision problem in the presence of strategic eav esdroppers and jammers, where legitimate nodes must act under incomplete and noisy knowledge of adversarial behavior [9], [10]. This challenge is especially critical for B5G/6G applications including vehicular and V2X networks, U A V swarms, industrial IoT , and mission-critical surveillance or defense systems where communication, sensing, and security are deeply intertwined, eventually failures can hav e immediate physical impact. In such scenarios, ISA C transceivers must continuously sense the environment, infer adversary behavior , and adapt beams, power , artificial noise, sensing effort, and jamming roles in an energy-ef ficient manner while satisfy- ing stringent latency and reliability requirements [7], [11], [12].Game theory has emerged as a po werful methodology for modeling and designing PLS strategies in ISA C-enabled 2 MIMO systems by capturing the strategic interactions among legitimate transceiv ers, eavesdroppers, and jammers, and pro- viding a rigorous frame work to define their performance and analyze stable operating points of the system [13], [14]. In parallel, Bayesian learning–based methods offer a principled way to update beliefs about unknown or time-varying ad- versaries from ISA C measurements and adapt transmission policies accordingly , enabling joint optimization of sensing, communication, and security decisions rather than treating them as isolated control variables under simplified, quasi-static models. A. Related W ork ISA C has become a key paradigm for B5G/6G since sharing radio resources for sensing and communication can improv e spectral and energy ef ficiency in dense deployments [15], [16]. Howe ver , practical operation in power , and interference- limited settings defines the impostance of security against strategic adversaries and energy-a ware resource allocation [14]. In this section, we present a detailed overvie w of the current state of the art of ISAC frameworks. Game-theoretic and sequential decision-making approaches are increasingly used to secure ISA C under uncertainty . Ac- cording to [17], a single ISAC base station and a mobile U A V eavesdropper are modeled as a Stackelberg game, where the U A V learns its trajectory through Deep Reinforcement Learning (DRL), and the base station optimizes beamform- ing and power to balance secrecy , sensing, and energy ef- ficiency . While effecti ve, this setting remains limited to a single BS–U A V interaction and does not jointly incorpo- rate Bayesian belief updates from ISA C measurements or support multi-node, equilibrium-consistent coordination. By contrast, iBEAMS addresses a broader MIMO-ISA C network with multiple le gitimate nodes and adversaries, combining Bayesian sensing-driven learning with Stackelberg and GNE formulations to jointly optimize beamforming, power split- ting, artificial noise, sensing effort, and hybrid-node jam- ming/relaying roles.In addition to this, [18] introduces only Bayesian game formulations to handle incomplete information about adversary locations or strategies, ensuring robust trans- mission policies in uncertain en vironments. In [19], secure hybrid beamforming for mmW ave ISAC is studied using a partially connected, dynamic sub-array architecture, where transmit power is minimized subject to secrecy-rate and sens- ing beampattern constraints under perfect or imperfect CSI (Channel State Information) through a two-stage design using SDR/SCA and the S-procedure. In contrast, iBEAMS gen- eralizes beyond scenario-specific beamforming by integrating Bayesian sensing-driv en belief updates with game-theoretic security modeling to support strategic-adversary awareness and scalable multi-agent, multi-layer PLS coordination with learning-enabled adaptation. At the system le vel, researchers hav e also inv estigated advanced enablers for secure ISA C, such as reconfigurable intelligent surfaces (RIS), near-field MIMO, and AI-driven optimization framew orks [20], [21]. Nonetheless, the dependence on static uncertainty sets and approximation-based optimization exposes a ke y limitation, as such methods lack the adapti ve, belief-driv en, and dynamically reconfigurable robustness that iBEAMS seeks to pro vide. Therefore, prior studies have established the potential of sensing aided beamforming, game theoretic PLS modeling, and system lev el enablers for secure ISAC. Howe ver , most existing designs remain largely static, optimize isolated objec- tiv es, and do not jointly capture adversarial uncertainty , coop- erativ e jamming, and entropy aware sensing ev entually secu- rity and energy efficienc y together . The key open problem is to co design base station power splitting, distributed node power and role control, and adaptive sensing to maximize secrecy and energy ef ficiency against mobile adversaries with partial or unknown CSI under strict power and QoS constraints. This motiv ates iBEAMS, which unifies Bayesian posterior learning, Stackelber g base station control, GNE based hybrid node interactions, and learning driv en policy optimization within a single three layer architecture for secure and ener gy efficient MIMO ISA C networks. B. Contrib utions Driv en by recent progress in ISA C, this work advances ISA C MIMO systems by addressing k ey challenges that jointly impact PLS, sensing quality , and energy efficiency . Fig. 1 summarizes the overall iBEAMS concept and key components of the proposed intelligent framework. The ke y contributions are as follows: • Primary contrib ution: iBEAMS as a unified hier - archical security and energy framework for ISA C W e propose iBEAMS , a unified three-layer Stackel- berg–GNE–Bayesian architecture for secure and energy- aware ISAC, where the base station acts as a Stackelberg leader , Hybrid Nodes (HN) as strategic followers, seeking to reach in a Generalized Nash Equilibrium (GNE), and a Bayesian refinement layer forms sensing-dri ven cooper- ativ e jamming coalitions. By iteratively updating beliefs and PLS metrics from ISA C measurements each slot, the framew ork jointly coordinates power , beamforming, sens- ing, and node role switching. T o the best our knowledge, this is the first ISAC–PLS architecture that integrates Stackelber g leadership, multi-agent GNE interaction, and Bayesian inference within a single hierarchical game theoretic model. • Layer 1: ISA C BS as Stack elberg leader with Bayesian belief feedback: In the first layer , the ISA C base sta- tion (BS) coordinates and broadcasts prior-channel PLS metrics and the eav esdroppers’ Angle-of-Arriv al (AoA) belief as part of a Stackelberg leader strategy . The ISA C BS jointly adapts its total transmit power and power split ratios for confidential data α , artificial noise (AN) β and sensing γ based on secrecy feedback and posterior entropy; sensing and AN are increased when secrecy degrades or uncertainty is high, and reduced when the posterior is confident that it will av oid excess RF con- sumption. In parallel, incentive prices ( π , τ , and ζ ) are broadcast to incorporate leakage and energy penalties into the HN utilities, resulting in an incentiv e-compatible and entropy-aware power and splitting policy aimed at maximizing SEE. 3 Fig. 1: Illustration of Unified Framework of iBEAMS leveraging Bayesian Learning, and Adaptive Game-Theoretic Multi-Layer Strategies of ISAC MIMO Systems • Layer 2: Hybrid-node GNE for distrib uted power and role selection: In the second layer, hybrid nodes operate as strategic followers and solve a Generalized Nash Equilibrium (GNE) under coupled interference and shared power constraints. Gi ven the leader’ s broadcast power splits and incentive prices, each node optimizes a local utility that trades of f secrecy benefit, transmit power cost, and leakage penalties. The resulting equilibrium yields a distributed power allocation and an initial role assignment (transmitting node - THN, vs. jamming node - JHN), providing an incenti ve consistent and energy efficient coordination mechanism. • Layer 3: Bayesian cooperative refinement f or geometry-aware jamming: In the third layer , HNs co- operate using the updated eav esdropper AoA posterior and its entropy to refine the jamming configuration. Coalitions are formed toward the most likely eavesdrop- per directions, prioritizing nodes that are geometrically aligned with these angles as focused jammers, while reallocating power to suppress redundant or low-impact jammers. The refinement iterates until the secrecy metric stabilizes, thus establishing a posterior -aligned, geometry- aware jamming strategy that concentrates energy where it is most effecti ve, preserves legitimate QoS, and improves SEE. C. Or ganization The remainder of this paper is organized as follows. Sec- tion II presents the iBEAMS system architecture. Section III formulates the core optimization problems underlying ISA C operation and PLS. Building on these formulations, and associ- ated constraints, section IV introduces the proposed iBEAMS architecture, which is described as a three-layer hierarchi- cal game-theoretic control framew ork. Section V details the simulation setup and pro vides the corresponding numerical ev aluation. Finally , Section VI concludes the article with key findings and outlines promising directions for future research. I I . S Y S T E M A R C H I T E C T U R E Fig. 2: System Model of Unified iBEAMS Frame work This section provides the rigorous system architecture and is or ganized as follows: Section II-A presents the network model; Section II-B details the antenna arrays and RF-chain configuration; Section II-C3 introduces the propagation chan- nel model, abd noise model; and Section II-D formulates the 4 energy-a ware power allocation and sensing model. In line with that, Figure 2 illustrates the proposed iBEAMS network architecture, which consists of an ISAC-enabled base station (IBS), a set of distrib uted hybrid nodes (HNs), and potential adversaries/ea vesdroppers (Eves). A. Network Model T o de velop a network model we consider , a single-cell ISA C network operating over a 5G NR style TDD do wnlink, where a single ISAC base station (IBS) serves multiple hybrid edge nodes (HNs) in the presence of eavesdroppers (Eves). The IBS is located at the center of a circular radius service region d max , with randomly distributed HNs and Eves may potentially appear near the IBS and to ward the cell edge (Fig. 2). In our network model, link formation and perfor- mance ev aluation are driv en by a 3GPP-compliant propagation and near-field channel construction. Specifically , large-scale propagation is generated using the 3GPP TR 38.901 model [22], [23], incorporating log-distance path loss and lognormal shadowing, while small-scale fading is modeled as Rician to reflect LOS-dominant mmW av e/THz links. Following is the detail about antenna design, channel model, signal model, and power and sensing model. B. Antenna Arrays, Steering V ectors, and Hybrid Precoding T o support highly directional mmW av e/THz transmission under practical RF-chain constraints, the ISA C base station employs a large-scale array with N IBS T transmit antennas and N RF RF chains using a partially connected hybrid-precoding architecture. The downlink precoder at slot t is modeled from [24], thus F ( t ) = F RF ( t ) F BB ( t ) , F RF ( t ) ∈ C N IBS T × N RF , F BB ( t ) ∈ C N RF × N s , N s ≤ N RF . (1) where F RF ( t ) is the analog RF precoder implemented through constant-modulus phase shifters, and F BB ( t ) is the lo w- dimensional digital baseband precoder for stream multiplex- ing, interference management, and power allocation [24], [25]. Under the partially connected structure, each RF chain driv es a dedicated sub-array , so F RF ( t ) is approximately block diagonal, achieving large array gain with substantially fewer RF chains than antenna elements. W ithin iBEAMS, RF precoding is realized through phase- only weights aligned with the instantaneous spatial channels of the scheduled HNs, consistent with practical hybrid beam- forming implementations that produce highly directive beams ov er the desired angular sector [26]. T o enhance PLS, AN is projected onto the approximate null-space of the aggregate legitimate channel to degrade eav esdropper reception while minimally affecting intended links [27]. Antenna Geometry and Array Response: T o character- ize the spatial response, standard 3D array-geometry models are adopted for both the IBS and HNs. Each transcei ver is equipped with a uniform linear array (ULA) with half- wa velength spacing, d = 0 . 5 λ , which suppresses grating lobes and enables well-conditioned beam steering. A narrowband plane wav e arriving from azimuth–elev ation ( α az , ϵ el ) is asso- ciated with the unit direction v ector . According to [28] u ( α az , ϵ el ) = cos ϵ el cos α az cos ϵ el sin α az sin ϵ el . (2) For a ULA of N elements oriented along the y -axis, the n th element location, r n can be expressed according to [29] r n = 0 nd 0 , n ∈ − N − 1 2 , . . . , N − 1 2 . (3) Let k 0 = 2 π /λ denote the free-space wa venumber . Under the narrowband assumption, the phase progression at element n is ϕ n ( α az , ϵ el ) = k 0 r ⊤ n u ( α az , ϵ el ) = π n cos ϵ el sin α az , (4) where the last equality follows from d = 0 . 5 λ . This phase progression directly links array geometry to angular selecti vity . Steering V ectors: Directional transmission and reception are described through array steering vectors. For a ULA with N elements, the steering vector has been defined from [24] a N ( α az , ϵ el ) = 1 √ N e j k 0 d ( − ( N − 1) / 2) cos ϵ el sin α az . . . e j k 0 dn cos ϵ el sin α az . . . e j k 0 d (( N − 1) / 2) cos ϵ el sin α az (5) Accordingly , the IBS and HN steering vectors are defined as a IBS ( α az , ϵ el ) = a N IBS T ( α az , ϵ el ) , a HN , tx ( α az , ϵ el ) = a HN , rx ( α az , ϵ el ) = a N HN ( α az , ϵ el ) (6) In addition, for a transmit beamforming vector w BS ∈ C N IBS T , the IBS array response and normalized power gain tow ard ( α az , ϵ el ) are A IBS ( α az , ϵ el ) = w H BS a IBS ( α az , ϵ el ) , G IBS ( α az , ϵ el ) = | A IBS ( α az , ϵ el ) | 2 . (7) Analogous expressions apply for the HNs using a HN , tx ( · ) and a HN , rx ( · ) . Coupled with the hybrid precoder in (1), these steering vectors constitute the fundamental building blocks for beam alignment and geometric channel characterization in mmW a ve/THz ISA C systems [19], [30], [31]. C. Pr opagation Model In this iBEAMS frame work, the link formation and perfor- mance ev aluation are driv en by a 3GPP-compliant propagation and near-field channel construction. Specifically , large-scale propagation is generated using the 3GPP TR 38.901 model [22], [23], incorporating log-distance path loss and lognormal shadowing, while small-scale fading is modeled as Rician to reflect LOS-dominant mmW a ve/THz links [32]. 5 1) Near -F ield Rician BS–HN and BS–Eve Channels: The proposed iBEAMS architecture is instantiated ov er a geometry-based, near-field MIMO channel model tailored to mmW ave/THz ISAC deployments. According to II-B, and [28], [33], [34], the effecti ve aperture, D ap , can be depicted when f c is the carrier frequency , λ = c/f c the wav elength, and an IBS equipped with a ULA of N IBS T antenna elements and inter-element spacing d ant as D ap = ( N IBS T − 1) d ant , (8) which induces a Fraunhofer distance, r F = 2 D 2 ap λ , that can be comparable to the cell radius at high carrier frequencies and large array sizes. As a consequence, ISAC BS–node channels are considered using spherical-wave phases. Therefore, The BS–HN link for the u th hybrid node (HN) is modeled as a near-field Rician vector where K R is the Rician K –factor . h BS ,u = r K R K R + 1 , h NLOS u, (9) Moreov er , the LOS (Line of Sight) component incorporates spherical-wa ve propagation: where d u is an ef fecti ve link distance, such as the a verage of { d n ( x u ) } ) and the NLOS component is modeled as spatially white Rayleigh fading model, [ h LOS u ] n = g ( d u ) exp − j 2 π λ d n ( x u ) q N IBS T , n = 1 , . . . , N IBS T , h NLOS u ∼ C N 0 , 1 N BS T I (10) In our system, HNs channels are fixed ov er the considered time horizon, capturing quasi-static large-scale propagation with a representativ e small-scale propagation. Howe ver , the BS–Eve channel to the e th eavesdropper in slot t follows the same near-field Rician structure b ut incorporates time v ariation in the scattered component: h BS ,e ( t ) = r K R K R + 1 h LOS e + r 1 K R + 1 h NLOS e ( t ) , (11) where h LOS e is determined by geometry through Fraunhofer distance, r f , while h NLOS e ( t ) is independently incorporated across slots to emulate mobility and fast fading. 2) Lar ge-Scale P ath Loss and Shadowing: Let r n ∈ R 3 denote the position of the n th BS antenna element and x ∈ R 3 the location of a node that can be an HN or an eav esdropper . The element-wise distances are d n ( x ) = ∥ r n − x ∥ 2 , n = 1 , . . . , N IBS T . (12) In addition, the free-space path-loss at is giv en by the Friis reference model is widely used in mmW av e and THz channel modeling [35] and in our iBEAMS framew ork, distance- dependent large-scale attenuation is captured by a log-distance model with lognormal shadowing, PL dB ( d ) = PL dB 1m + 10 n PL log 10 d 1 m + X σ , (13) where n PL is the path-loss exponent and X σ ∼ N (0 , σ 2 sh ) de- notes the lognormal shadowing term, consistent with standard large-scale fading models in cellular systems [35], [36]. The corresponding large-scale linear amplitude gain is then g ( d ) = 10 − PL dB ( d ) / 20 , (14) which directly links the stochastic path-loss model to the complex baseband channel coefficients used in the iBEAMS physical-layer simulations. 3) Signal Model and Secr ecy Metrics: Building on Sec- tion II-B and (1), we adopt a hybrid precoding architecture. At each slot t , the set of hybrid nodes (HNs) is partitioned into the transmitting/legitimate nodes U ( t ) (THNs) and the jamming nodes J ( t ) (JHNs), where U ( t ) ∩ J ( t ) = ∅ and U ( t ) ∪ J ( t ) spans all activ e HNs. This partition determines the effecti ve multiuser downlink signal model, namely the intended signal, multiuser interference, and artificial-noise/jamming leakage observed at legitimate HNs and at the eavesdroppers, based on which we define the instantaneous SINR and the corre- sponding secrecy-rate metrics. Noise Model: In our system, we have considered receiver noise accounts for thermal noise and front-end noise figure. W ith thermal noise power spectral density N 0 , dBm / Hz , system bandwidth B W , and recei ver noise figure, N F , the total noise power at the receiver front-end is σ 2 n = 10 N 0 , dBm / Hz +10 log 10 ( BW )+ N F − 30 10 [W] , (15) and the additiv e noise samples satisfy n u ( t ) ∼ C N ( 0 , σ 2 n I ) . Received Signal Repr esentation: Within each slot, the IBS allocates its transmit power across confidential data, AN, and sensing using fractions ( α t , β t , γ t ) from sensing model II-D. Thus, the IBS transmit signal in slot t is modeled as x ( t ) = Fs ( t ) + F AN z ( t ) , (16) where F AN is designed to approximately lie in the nullspace of the stacked legitimate channels [27], and s ( t ) contains the scheduled data streams and z ( t ) is the AN vector . Thereby , limiting AN leakage to ward THNs while intentionally degrad- ing eav esdropper reception. The recei ved baseband signal at HN, u ∈ U ( t ) under combining vector w u is y u ( t ) = w H u h H BS ,u x ( t )+ X v ∈J ( t ) ˜ h u ← v p P v ( t ) z v ( t )+ ˜ n u ( t ) , (17) where ˜ h u ← v denotes an effecti ve channel gain from jammer v to HN u , P v ( t ) is the jamming power of node v , and ˜ n u ( t ) is the effecti ve noise after combining. The corresponding Eve observation for decoding user u is defined analogously using h BS ,e ( t ) and an eavesdropper combiner w e . Instantaneous SINR and Secr ecy Rate: Let f u denote the effecti ve IBS beam associated with user u (the u th column of F ), and let P u ( t ) denote the po wer allocated to that stream (discussed in II-D). Therefore, the instantaneous SINR at legitimate HN u is SINR hn ,u ( t ) = P u ( t ) | g hn,u ( t ) | 2 P k = u P u ( t ) | g hn,u ( t ) | 2 + I J u ( t ) + I AN u ( t ) + σ 2 n , (18) where g hn,u ( t ) ≜ w H u h H BS ,u ( t ) f k ( hn ) , and I (J) u ( t ) captures the aggregate interference generated by cooperativ e jammers 6 and I (AN) u ( t ) accounts for residual AN leakage toward user u . Similarly , for an eavesdropper e , the SINR associated with decoding the stream intended for user u is SINR e,u ( t ) = P u ( t ) | g e,u ( t ) | 2 P k = u P u ( t ) | g e,u ( t ) | 2 + I J e ( t ) + I AN e ( t ) + σ 2 n (19) , where g e,u ( t ) ≜ w H e h H BS ,e ( t ) f u ( t ) , and I (J) e ( t ) and I (AN) e ( t ) denote, respectiv ely , the contributions of cooperative-jamming and AN in Eve e . In accordance with the proposed system architecture, we adopt a w orst-case leakage model by selecting the most detrimental eav esdropper in each slot: SINR max e ,u ( t ) = max e ∈E SINR ( e ) e ,u ( t ) , (20) The instantaneous secrecy rate then follo ws the standard Gaussian wiretap formulation [37], [38]: R s,u ( t ) = h log 2 (1 + SINR hn ,u ( t )) − log 2 (1 + SINR max e ,u ( t )) i + (21) , reflecting the fundamental physical-layer performance metric that is subsequently aggregated and fed back into the multi- layer iBEAMS control framew ork for power allocation, role selection, and sensing adaptation. D. Ener gy- Efficient P ower Allocation and Sensing Model In the proposed iBEAMS architecture, energy awareness is considered through a per–time-slot power -consumption model that accounts for both radiated transmit power and hardware- dependent overhead. Let P BS ( t ) denote the instantaneous transmit power of the ISAC BS in slot t , and let P u ( t ) denote the transmit po wer of HN. Therefore, the aggregate radiated power in slot t is P tx , tot ( t ) = P BS ( t ) + U HN X u =1 P u ( t ) , (22) Also, the corresponding total po wer consumption in slot t is modeled as P slot ( t ) = P cons + P tx , tot ( t ) η pa , (23) where P cons = N RF P rf + P bb accounts for the static power drawn by RF chains, P rf and baseband processing, P bb , and η pa ∈ [0 , 1] denotes the effecti ve power -amplifier efficienc y . This affine model is consistent with standard Secrecy Energy Efficienc y (SEE) formulations in secure MIMO systems [39], [40]. Thus, SEE in slot t is defined as the ratio between the aggregate secrecy throughput and the total po wer . SEE( t ) = X u ∈U ( t ) R s,u ( t ) P slot ( t ) [bits/Joule] , (24) Where, R s,u ( t ) is the instantaneous secrecy rate as giv en by (21), and U ( t ) denotes the set of HNs scheduled as legitimate receiv ers in slot t . The metric in (24) quantifies the fundamental trade-off between the enhancement, of secrecy and the expenditure of energy . In accordance with the ISA C signal model in Section II-C3, the BS transmit power in slot t is partitioned among confidential communication, AN, and sensing as P BS ( t ) = P comm BS ( t ) + P AN BS ( t ) + P sens BS ( t ) , (25) with P comm BS ( t ) = α t P BS ( t ) , P AN BS ( t ) = β t P BS ( t ) , P sens BS ( t ) = γ t P BS ( t ) (26) where ( α t , β t , γ t ) are nonnegati ve power -splitting coefficients satisfying α t + β t + γ t = 1 , ∀ t. (27) Here, α t controls the fraction of BS po wer dev oted to se- cure communications, β t specifies the AN power injected to mitigate eavesdroppers, and γ t regulates the power reserved for sensing beams used for AoA refinement and environment probing in line with ISA C operation. T o explicitly model the sensing functionality , a power-normalized sensing beam w S ∈ C N IBS T is steered to ward a candidate direction ( ϕ IBS , θ IBS ) , and the corresponding sensing response is characterized by R S ( ϕ IBS , θ IBS ) = w H S a IBS ( ϕ IBS , θ IBS ) 2 , (28) where a IBS ( · ) denotes the IBS array steering v ector . The sensing beam can be further shaped through a Hamming- tapered amplitude distrib ution to control the width of the main- lobe and the level of the side-lobe [24], w S ( τ , ϕ ) = [(1 − τ ) { N IBS T + τ h Hamming ] ⊙ a IBS ( ϕ ) , (29) where τ ∈ [0 , 1] is a taper-control factor , h Hamming denotes a normalized Hamming window across the array elements, and ⊙ represents the hadamard product [28], [41], [42]. Uniform weighting ( τ = 0 ) yields a wider beam with higher side lobes, whereas τ = 1 produces a narrower , high-gain beam with enhanced angular resolution. Equations (22), (29) thus provide a unified theoretical description of energy-a ware po wer allo- cation and sensing in iBEAMS. The numerical e v aluation in Section V directly instantiates these expressions to quantify SEE and sensing performance under realistic channel, and interference conditions. I I I . P RO B L E M F O R M U L A T I O N Con ventional ISA C designs often optimize communication or sensing in isolation under ideal CSI (Channel Sate Infor- mation) and static beam patterns. In contrast, secure ISAC requires joint power-limited co-design of confidential trans- mission and sensing, inducing fundamental tradeoffs among reliability , secrecy , sensing accuracy , and energy ef ficiency . This section formulates the underlying optimization problems and to show how iBEAMS addresses the tri-coupled optimiza- tion problems of secrecy , sensing , and ener gy efficiency . A. ISA C P ower-Coupled Decision Space and Constraints The BS power -splitting model in Section II-D and (25)–(27), the fractions α t , β t , γ t determine ho w P BS ( t ) is fractionated among secure data transmission, AN, and sensing. On the follower side, P k ( t ) denotes the transmit power of HN k in slot t , and U ( t ) is the set of scheduled legitimate receivers 7 (THNs). Thus, P BS ( t ) , α t , β t , γ t , P k ( t ) ∗ k constitutes the in- stantaneous power -allocation decision vector , from which the total radiated power P ∗ tx , tot( t ) and the consumed power in slots P slot ( t ) are obtained through (22)–(23), with P cons and η pa capturing the circuit overhead, and P A efficiency , respec- tiv ely . Ho we ver , these decisions are restricted by a coupled set of constraints. First, the power -simplex and feasibility con- straints in (27), (26) enforce non-negati vity and normalization of ( α t , β t , γ t ) , as well as minimum sensing and AN levels, while per-HN and network-wide power limits bound P k ( t ) and the friendly jamming (FJ) budget. Second, for the secrecy and sensing-entropy constraints, each activ e HN must achieve a secrec y rate above R th with bounded leakage and that the posterior entropy H ( p ) remains below H ∗ . Finally , CSI uncertainty is supposed to be captured through the bounded- error model, which defines an admissible channel set for rob ust operation. In this way , the decision space for iBEAMS is intrinsically coupled with po wer and constraints, an y change in the BS po wer or the split ( α t , β t , γ t ) simultaneously impacts the feasibility of HN transmit powers, FJ activ ation, secrecy guaranties and sensing reliability , providing the basis for the optimization of three-layers and game-theoretic control dev eloped in the next section IV. B. Leader -Level P ower -Allocation and Pricing Pr oblem In the first layer, the IBS chooses ( P BS ( t ) , α t , β t , γ t ) and a vector of incentive prices ( π t , τ t , κ t ) to analyze HN utilities. The leader’ s problem in each slot can be written as: max P BS , θ t SEE( t ) − λ sec ( R ⋆ s − R s ( t )) + − λ H ( H ( t ) − H ∗ ) + s.t. 0 ≤ P BS ( t ) ≤ P max BS , ( α t , β t , γ t ) satisfy (27) , π min ≤ π t ≤ π max , τ min ≤ τ t ≤ τ max , κ min ≤ κ t ≤ κ max , (30) where R s ( t ) is the average secrecy rate over served THNs in slot t , R ⋆ s is a target secrecy le vel, H ( t ) is the current sensing-entropy of the AoA posterior , and H ∗ is the allow able uncertainty bound. The penalty terms capture secrecy violation and excessi ve sensing uncertainty . In our framework, this problem is solved through an adaptiv e update of ( α t , β t , γ t ) and ( π t , τ t , κ t ) using the previous-slot secrecy , leakage, and entropy KPIs, thereby realizing a Stackelberg leader control in detail addressed in section IV, and Algorithm 1. C. F ollower-Level HN GNE P ower and Role Pr oblem Giv en the leader decisions ( P BS ( t ) , α t , β t , γ t , π t , τ t , κ t ) , each HN, u acts as a strategic follower that selects its transmit power P k ( t ) and role (transmitting node vs. jamming node) subject to local power constraints and shared interference coupling. Let A denote the set of activ e HNs, and E the set of potential eav esdroppers. Using the SINR expressions defined in Section II-C3, the secrecy rate for HN u ∈ A is R s ( u ) from (51) For each HN, a representativ e utility , U u deriv ed from Appendix A The follower -layer problem is thus to avail the best GNE: Find { P ⋆ u ( t ) } u ∈ P , U u P ⋆ u ( t ) , P ⋆ − u ( t ) ≥ U P u ( t ) , P ⋆ − u ( t ) , ∀ P u ( t ) ∈ P u , ∀ u. (31) where P u encodes local power constraints and P captures shared interference and ener gy b udgets. In our system, we hav e addressed this constraints through approximating the GNE through iterativ e best-response over a discrete power grid, addressed in SectionIV, and Algorithm 2. D. PLS and Secr ecy-Outage Metrics Pr oblem System-lev el security in con ventional ISA C designs is often characterized using either av erage secrecy rate or worst-case secrecy performance, typically under fixed power splits and static jamming strategies. Such models rarely capture how secrecy degrades probabilistically across users when eav es- droppers move, CSI is imperfect, and the sensing uncertainty persists. T o explicitly quantify this vulnerability , we ev aluate security in iBEAMS through per-slot secrecy-outage metrics ov er the activ e legitimate set A . Using (21), we define R min = min u ∈A R s ( u ) , (32) R = 1 |A| X u ∈A R s ( u ) , (33) P out = 1 |A| X u ∈A 1 { R s ( u ) < R th } , (34) where R th is the target secrecy rate, and R min captures the worst served legitimate user , R reflects the average secrecy lev el ov er all activ e HNs, and P out , outage probability quanti- fies the fraction of users that fail to meet the secrecy target in a giv en slot. The proposed iBEAMS framework explicitly seeks to control this secrecy-outage behavior so that P out remains below a prescribed reliability level while jointly maximizing SEE and enforcing the entropy-based sensing constraint. E. Sensing-Entr opy and Belief-Coupled Sensing Pr oblem Most existing models neither maintain an explicit belief ov er eav esdropper directions nor impose principled bounds on tolerable angular uncertainty before triggering sensing or beam adaptation. Consequently , secrecy decisions are often weakly quantified. In iBEAMS, the IBS explicitly maintains a poste- rior belief over the angular domain of potential eavesdroppers. Let Φ = { ϕ 1 , . . . , ϕ N ϕ } denote the discrete angle grid and p = [ p 1 , . . . , p N ϕ ] ⊤ the corresponding posterior with N ϕ X i =1 p i = 1 , p i ≥ 0 , ∀ i, (35) and quantify the residual directional ambiguity using Shannon entropy H ( p ) = − N ϕ X i =1 p i log 2 p i . (36) Therefore, a large H ( p ) indicates a dif fuse belief (high uncertainty in Eve’ s direction), whereas a small H ( p ) reflects 8 a concentrated belief and thus improv ed localization confi- dence.T o couple sensing explicitly with secrecy and power control, iBEAMS constrains the posterior uncertainty through H ( p ( t )) ≤ H ∗ , (37) where H ∗ is a design parameter determined by sensing resolution and acceptable situational-awareness lev els. Since this constraint may be violated in noisy or highly dynamic en vironments, it should be embedded into the optimization through a penalty term, thus, L H = λ H [ H ( p ) − H ∗ ] + , (38) with λ H > 0 and [ x ] + = max( x, 0) . Giv en sensing beamforming weights, w S from (29)used to illuminate different angular sectors, the belief-coupled sensing subproblem is then formulated following (35), and (37), min p , w S P sys out + λ H [ H ( p ) − H ∗ ] + , (39) thereby enforcing a joint design in which secrecy-outage reduction and bounded sensing uncertainty are optimized si- multaneously . In the iBEAMS implementation, those problems are addressed through Algorithm 1,and Algorithm 3 through (i) updating the AoA posterior from noisy sensing measurements, (ii) adapting the sensing power fraction γ t , and (iii) tuning the beam-taper parameter τ to widen or sharpen sensing beams as a function of the current entrop y le vel H ( p ) , described in more detail in section IV. F . F riendly-J amming (FJ) and Geometry-A war e Refinement Friendly-jamming schemes in secure wireless netw orks typically rely on pre-selected or static jammer sets, often ignoring (i) how jammer activ ation interacts with user secrecy rates under dynamic CSI and mobility , (ii) the geometric relationship between legitimate users and eav esdroppers, and (iii) the explicit energy cost of sustaining multi-node jamming. As a result, jamming resources are frequently ov er-provisioned as wasting po wer or poorly targeted with insufficient secrecy gain, and the resulting designs do not explicitly optimize SEE. T o address this problem, iBEAMS introduces a FJ optimization that is jointly dri ven by secrecy performance, network geometry , and power constraints. Each HN can act either as a legitimate transmitter or as a cooperativ e jammer . Let Jam ( u ) ∈ { 0 , 1 } denote the binary role of HN u , and n J = P u ∈A Jam ( u ) , the number of activ e jammers.Thus, a canonical FJ design problem can be written as min { Jam ( u ) } , g P sys out ( Jam , g ) , (40) s.t. Jam ( u ) ∈ { 0 , 1 } , ∀ u ∈ A , (41) P FJ = n J P max HN ≤ P max FJ , (42) P ( u ) leak ≤ ρ leak P max lu , ∀ u ∈ A . (43) where g is the aggregate jamming beamforming vector , P FJ is the total jamming power , and P ( u ) leak bounds interference leak- age to ward legitimate users. W ithin iBEAMS, this theoretical FJ problem is addressed in two tightly coupled stages, aligned with Algorithms 2, and 3. Algorithm 1 Layer 1: Bayesian-Stackelberg Leader Control at ISA C BS Require: Prior posterior distribution p t − 1 ( θ E ) of Eve’ s AoA; kernel bandwidth σ t ; historical secrecy KPIs: { R s ( t − 1) , P out ( t − 1) } ; BS power budget P BS ; incentiv e bounds ( π min , π max ) , ( τ min , τ max ) , ( κ min , κ max ) ; secrecy target R target s ; entrop y threshold H max . Ensur e: Adapti ve BS resource split ( α t , β t , γ t ) ; incentiv e prices ( π t , τ t , κ t ) ; predicted belief p − t ( θ E ) ; updated kernel σ t +1 . Step 1 : Bayesian Belief Pr ediction Predict the prior of Eve’ s AoA using a Gaussian con volution kernel: p − t ( θ ) = K ( σ t ) ∗ p t − 1 ( θ ) , and compute its entropy: H t = − Z p − t ( θ ) log p − t ( θ ) dθ . Step 2 : Entropy-A ware Sensing Allocation Determine sensing portion based on uncertainty: γ t = Γ( H t ) , Γ ′ ( · ) > 0 , Γ(0) = γ min , Γ( H max ) = γ max . Step 3 : Secrecy-Deficit-Driven AN Allocation Compute secrecy error relati ve to the tar get: e t = R target s − R s ( t − 1) . Update AN power: β t = limit ( β t − 1 + k s e t , 0 , 1 − γ t ) . Step 4 : Communication Power Adjustment Set the data power fraction: α t = 1 − β t − γ t . Step 5 : Incentive Price Design (Stackelberg Leader Action) Based on observed performance: π t = limit ( π t − 1 + k π ( I benefit jam ) , π min , π max ) , τ t = limit ( τ t − 1 + k τ (Ξ avg − Ξ target ) , τ min , τ max ) , κ t = limit ( κ t − 1 + k κ ( H t − H max ) , κ min , κ max ) , where, π t rew ards jamming contributions, τ t penalizes leak- age, and κ t rew ards sensing and information gain. Step 6 : Send Leader Strategy to Nodes Broadcast ( α t , β t , γ t ) and ( π t , τ t , κ t ) to all HNs. Step 7 : Kernel Update Adapt kernel width for next iteration: σ t +1 = σ t + η σ ( H t − H max ) . Return, ( α t , β t , γ t , π t , τ t , κ t ) and p − t , σ t +1 . I V . I B E A M S U N I FI E D G A M E T H E O R E T I C F R A M E W O R K Building on the coupled decision space and constraints in Section III, the proposed iBEAMS architecture is modeled as a three-layer hierarchical game-theoretic control framew ork. In each scheduling slot t , the IBS acts as a Stackelber g leader (Algorithm 1), HNs play a GNE game as strategic follo wers (Algorithm 2), and a Bayesian sensing and r efinement layer 9 Algorithm 2 Layer 2: GNE Response and Role Switching for HN Require: BS parameters ( α t , β t , γ t ) ; incenti ve prices ( π t , τ t , κ t ) ; channels { h u } ; po wer limits P max u ; secrec y thresh- old R min s ; network-wide coupling constraints (interference, leakage). Ensur e: Equilibrium powers p ⋆ u ; assigned roles role k ∈ { THN , JHN } . Step 1 : Initialization Initialize each HN power p (0) u and provisional role as THN. Step 2 : Utility Definition Each HN solves a self-interested utility maximization: U u = η u R s,u − c u p u − τ t Ξ u + π t J u + κ t I u , subject to shared constraints: g ( p 1 , . . . , p u ) ≤ 0 . Step 3: Best-Response Dynamics Repeat ∥ p ( i ) − p ( i − 1) ∥ 2 ≤ ϵ Update each node power: p ( i ) u = arg max 0 ≤ p u ≤ P max u U u ( p u , p ( i − 1) − u ) . i ← i + 1 Step 4: Equilibrium Identification Set p ⋆ ← p ( i ) ; if p ⋆ satisfies all coupling constraints, it constitutes a GNE Step 5: Role Switching Rule Assign the final role of each node: role k = ( JHN , R s,k ( p ⋆ ) < R min s , THN , otherwise . Step 6: F orward to Local Refinement Layer Pass THN/JHN sets and powers p ⋆ to Algorithm 3 Return p ⋆ , { role k } updates the AoA belief over potential ea vesdroppers and adjusts cooperative jamming coalitions (Algorithm 3). The standard game theoretical approach for wireless networks and PLS have taken from [43]–[45], where each game theoretical framew ork has been implemented separately . This three-layer structure directly implements the tri-coupled design objectiv es of secr ecy , sensing , and ener gy efficiency through addressing the power -simplex, secrecy-outage, sensing-entropy , and CSI- uncertainty constraints that has been mentioned in Section III. A. Hier ar chical Game Structure and Joint Decision V ariables This subsection formalizes the iBEAMS control architecture as a hierarchical game and specifies the key decision variables at each layer . In slot t , the leader (IBS) selects the control v ector , a t = ( P BS ( t ) , α t , β t , γ t , π t , τ t , κ t ) , (44) where ( π t , τ t , κ t ) are incentive prices broadcast to HNs that enter their utilities as jamming rewards, leakage penalties, and sensing/entropy rewards, respectively . On the follo wer side, each HN u selects a transmit power P u ( t ) and a mode role u ( t ) ∈ { THN , JHN } , yielding the follower action profile p t = { P u ( t ) , role u ( t ) } u ∈A ( t ) , (45) Algorithm 3 Layer 3: Bayesian Cooperativ e Refinement and Posterior-Aligned Jamming Require: Provisional THN/JHN sets from GNE; equilibrium powers p ⋆ k ; predicted posterior p − t ; sensing measurements { z ( θ ) } ; BS AN and data beam shapes. Ensure: Updated pos- terior p t ; refined jamming po wers; cooperati ve jamming field with THN-protectiv e nulls. Step 1 : Coalition Formation JHNs near dominant posterior peaks form jamming coalitions, and THNs with similar QoS form protection coalitions. Step 2 : Posterior Likelihood Update Compute pseudo-likelihood: L ( θ ) = z ( θ ) k eff . Update posterior: p t ( θ ) ∝ p − t ( θ ) L ( θ ) , normalize to unit mass. Step 3 : Cooperative Jamming Optimization For each jamming coalition C : { p new k } k ∈C = arg max { p k ≤ P max k } X u ∈ THN R s,u ( p k , p − k ) subject to: leakage constraints on THNs , posterior-weighted AN shaping . Step 4 : Posterior -Aligned Beam/Jamming Field Synthesis Construct AN lobes aligned with arg max p t ( θ ) , Insert deep nulls to ward THNs or protected angles, Adjust jamming phases coherently within each coalition. Step 5 : Stopping Rule T erminate cooperative refinement if: ∆ R sum s < δ. Return updated posterior p t , refined p k , and synthesized jam- ming field. where A ( t ) is the set of active HNs in slot t and J ( t ) ⊆ A ( t ) is the induced set of friendly jammers. The Bayesian sensing layer maintains a posterior belief over the discrete angular grid Φ = { ϕ 1 , . . . , ϕ N ϕ } : p ( t ) = [ p 1 ( t ) , . . . , p N ϕ ( t )] ⊤ , N ϕ X i =1 p i ( t ) = 1 , p i ( t ) ≥ 0 , (46) with entropy H ( p ( t )) = − N ϕ X i =1 p i ( t ) log 2 p i ( t ) , (47) constrained through H ( p ( t )) ≤ H ∗ as in (37). The aggregate radiated power and the total consumed power in slot t follow directly from the power model in section II-D, from (22) and (23), while the SEE( t ) is defined in (24). T ogether, these relations link the leader’ s decision variables, P BS ( t ) and { P u ( t ) } u ∈U ( t ) to the instantaneous energy cost and secrecy performance: any choice of the power -splitting frac- tions ( α t , β t , γ t ) , and BS power P BS ( t ) determines P tx , tot ( t ) 10 and P slot ( t ) through (22)–(23), and hence the SEE term in (24) that appears in the leader’ s objectiv e. In Stackelber g form, the IBS (leader) selects an action vector a t ∈ A lead (including P BS ( t ) , ( α t , β t , γ t ) , and prices ( π t , τ t , κ t ) ), anticipating the GNE response of followers p ⋆ t ( a t ) . The resulting hierarchical optimization in slot t can be written as max a t ∈A lead F ( a t , p ⋆ t ( a t ) , p ( t )) , (48) where F ( · ) embeds the SEE defined in (24) through P slot ( t ) from (23), together with secrecy and sensing–entropy penal- ties, and p ( t ) denotes the Bayesian sensing posterior that cou- ples the leader decisions to the belief-dependent constraints. B. Stac kelber g Leader Contr ol and Pricing At the leader layer, the IBS solv es a constrained power–allocation and pricing problem that respects the power–simple x and feasibility constraints in (26)–(27). Given the SEE, total transmit po wer, and slot–wise consumption defined in (24), (22), and (23), the leader’ s per–slot objective is described by F ( · ) in(48), which maximizes SEE while pe- nalizing secrecy-rate violations and excessi ve sensing entropy . Formally , the Stackelberg leader problem in slot t is max a t F ( a t , p ⋆ t ( a t ) , p ( t )) (49) (26) , (27) , π min ≤ π t ≤ π max , τ min ≤ τ t ≤ τ max , κ min ≤ κ t ≤ κ max , where a t is the leader action vector and p ⋆ t ( a t ) denotes the GNE follo wer response. Algorithm 1 implements a Bayesian–Stackelber g controller that approximates (49) on- line. In each slot, the IBS (i) predicts a prior AoA belief p − t ( θ ) for the eavesdropper through a Gaussian con volution, (ii) computes the predicted entropy H t and maps it to a sensing fraction γ t = Γ( H t ) , (iii) updates the AN fraction β t using the secrecy error e t = R target s − R s ( t − 1) , (iv) enforces the power simplex by setting α t = 1 − β t − γ t , and (v) adjusts the incentiv e prices ( π t , τ t , κ t ) through clipped affine updates driv en by jamming benefit, average leakage, and entropy deviation.Through this Bayesian–Stackelber g update, the IBS continuously reshapes the HN utilities and the resulting GNE so that the induced equilibrium is entropy , secrecy-aware, and explicitly oriented tow ard maximizing SEE, in direct correspondence with the second contribution item on adaptive BS power control. C. F ollower-Level GNE for P ower Contr ol and Role Switching Giv en the leader action v ector a t , the HNs interact on the mid-timescale through a GNE that captures power control and role selection under imperfect CSI. Thus, the composite BS- HN channel is modeled as H H N = b H H N + E H N , ∥ E H N ∥ 2 F ≤ ϵ H N , (50) where b H H N is the estimated channel and E H N denotes the bounded CSI error . Under this uncertainty model, the robust secrecy rate for an active HN u ∈ A ( t ) is giv en by (21) as R s ( u, t ) = " log 2 (1+SINR lu ( u, t )) − max e ∈E log 2 (1+SINR e ( u, e, t )) # + , (51) where SINR lu ( u, t ) and SINR e ( u, e, t ) depend on the BS communication and AN powers P comm BS ( t ) , P AN BS ( t ) , the HN powers { P k ( t ) } , and the induced multi-user interference pat- tern. Utility Design and Secrecy–Ener gy–Entr opy Pricing: T o align individual HN incentives with the system-le vel SEE objectiv e, the local payoff for HN u at slot t is de veloped from Appendix A U ( P u ( t ) , role u ( t ); a t , P − u ( t )) = η u R s ( u, t ) − c u P u ( t ) − τ t Ξ u ( t ) + π t J u ( t ) + κ t I ( t ) (52) where P − u ( t ) collects the powers of all other HNs. This utility can be interpreted as a priced, per-node SEE metric, the first term η u R s ( u, t ) reflects the secrecy throughput benefit when HN u acts as THN; the second term c u P u ( t ) penalizes its power consumption; Ξ u ( t ) measures secrecy leakage attributed to HN u and is weighted by the leakage price τ t ; J u ( t ) captures the effecti ve jamming contribution when u operates as a JHN and is rewarded by the jamming price π t ; and I ( t ) denotes the global information gain, and entropy reduction from sensing, shared among HNs and scaled by the entropy price κ t . In this way , the leader’ s prices ( π t , τ t , κ t ) imple- ment the “Secrecy–Ener gy–Entropy-a ware pricing” mecha- nism from the iBEAMS contributions, embedding ISA C BS priorities directly into follower payof fs. F easible Action Sets and Coupling Constraints: Each HN’ s power decision is constrained by both local hardware limits and network-wide coupling conditions. These con- straints can be expressed as 0 ≤ P u ( t ) ≤ P max u , ∀ u, (53) X u ∈A ( t ) P u ( t ) ≤ P max FJ , (54) Ξ u ( t ) ≤ Ξ max , ∀ u, (55) g ( P 1 ( t ) , . . . , P u ( t )) ≤ 0 , (56) where (53) enforces per-node power bounds, (54) limits the aggregate friendly-jamming power , (55) limits the secrecy leakage for each HN, and (56) compactly represents additional interference or sum-power/SINR feasibility constraints. Collecting these conditions, the global feasible set of power profiles is P ( t ) = n P ( t ) = ( P 1 ( t ) , . . . , P u ( t )) (53) – (56) combined o . (57) For a gi ven HN u , its admissible decisions are then given by the projection of P ( t ) onto the u -th coordinate: P u ( t ) = n P u ( t ) ∃ P − u ( t ) such that ( P u ( t ) , P − u ( t )) ∈ P ( t ) o . (58) 11 GNE F ormulation and Best-Response Appr oximation: Since utility , U depends on all other po wers through the secrecy rate, leakage, and jamming terms, the power profile { P ⋆ u ( t ) } u is a GNE if U ( P ⋆ u ( t ) , P ⋆ − u ( t )) ≥ U u ( P u ( t ) , P ⋆ − u ( t )) , ∀ P u ( t ) ∈ P u ( t ) , ∀ u. (59) taken together from A, that says no HN can unilaterally increase its utility while respecting all local and shared constraints. The Algorithm 2 implements an iterativ e best- response scheme to approximate this GNE on a discrete po wer grid. Starting from an initial power profile { P (0) k ( t ) } k , where all nodes provisionally treated as THNs, each HN repeatedly solves P ( i ) u ( t ) = arg max P u ( t ) ∈P u ( t ) U ( P u ( t ) , P ( i − 1) − u ( t )) , (60) until the updates satisfy ∥ P ( i ) u ( t ) − P ( i − 1) u ( t ) ∥≤ ϵ for all k . The resulting fixed point { P ⋆ u ( t ) } k provides an implementable approximation to the GNE defined in (59). Secr ecy-Based Role Switching and Energy-A war e Jam- ming: Once the equilibrium powers are obtained, iBEAMS maps each HN to a transmitting or jamming role using the secrecy-based rule role u ( t ) = ( JHN , R s ( u, t ) < R min s , THN , otherwise , (61) where R min s is the minimum acceptable secrecy rate for a legitimate transmission. HNs that cannot satisfy R min s under the current equilibrium are reconfigured as friendly jammers, thereby contributing additional interference tow ard eav esdrop- pers while incurring power , and leakage-related penalties in their utilities. The resulting equilibrium powers and roles, receiv ed from Algorithm 2 to the Bayesian refinement layer (Algorithm 3), determine the strategic HN role switching, and energy-a ware jamming contribution within a rigorous GNE framew ork, and couple naturally with the leader’ s entropy , and secrecy-a ware pricing policy . D. Bayesian Sensing , Entr opy Constr aint, and Geometry- A war e Refinement The Bayesian layer addresses the sensing-entropy and belief-coupled sensing problem in Section III-E. The IBS maintains the posterior p ( t ) as in (46), with entropy (47) constrained by 37 and the penalty by 38 which appears in the leader objectiv e (49) and the sensing subproblem (39). Algorithm 1 first predicts the AoA belief through p − t ( θ ) = ( K ( σ t ) ∗ p t − 1 )( θ ) , (62) where K ( σ t ) is a Gaussian kernel with bandwidth σ t modeling mobility and temporal evolution. Therefore, the predicted entropy H t = − Z p − t ( θ ) log 2 p − t ( θ ) dθ (63) is mapped to a sensing power fraction through γ t = Γ( H t ) with Γ ′ ( · ) > 0 , Γ(0) = γ min , and Γ( H max ) = γ max so that more power is devoted to sensing when uncertainty is high. Giv en p − t , and sensing measurements { z ( θ ) } , Algorithm 3 forms a pseudo-likelihood L ( θ ) = z ( θ ) k eff , (64) and computes the posterior as p t ( θ ) ∝ p − t ( θ ) L ( θ ) , (65) normalized to satisfy (46). The updated posterior feeds the Bayesian refinement mechanisms. This refinement mecha- nism, updated posterior belief p t ( θ ) subsequently driv es three bayesian refinement mechanisms that couple sensing, cooper- ation, and jamming. First, it induces belief-awar e coalition formation : JHNs whose angular sectors overlap with dominant posterior peaks, for example lar ge p t ( θ ) ) self-organize into jamming coalitions, while THNs with similar QoS and secrecy requirements form protection coalitions, thereby explicitly linking cooperati ve behavior to the belief state. Second, within each jamming coalition C , the cooperati ve jamming po wers { P k ( t ) } k ∈C are refined by conceptually maximizing the aggregate secrecy of the serv ed THNs subject to per -node po wer limits and bounded leakage, max { P u ( t ) ≤ P max u } u ∈C X u ∈ THN R s ( u, t ) s.t. Ξ u ( t ) ≤ Ξ max , ∀ u ∈ THN . (66) where the AN and jamming beams are shaped according to p t ( θ ) to concentrate energy along secrecy-critical directions while limiting leakage toward protected THNs. Third, the posterior is le veraged for posterior-aligned beam synthesis, the IBS steers AN/jamming beams to ward arg max θ p t ( θ ) and enforces nulls (or reduced gain) in directions associated with protected THNs; moreover , the phases of JHNs within each coalition are adjusted coherently so that their contributions add constructiv ely at the eav esdropper and destructi vely at legiti- mate receiv ers. In addition, the kernel bandwidth controlling belief prediction is adaptively updated as σ t +1 = σ t + η σ ( H t − H max ) , (67) which broadens the prediction when uncertainty is higher than desired and narrows it when the posterior is already sharp. Collectiv ely , these mechanisms instantiate the proposed bayesian cooperativ e refinement by ensuring that both sensing effort and cooperativ e jamming geometry are directly gov erned by the belief-entropy state. E. Cooper ative J amming Refinement (Layer 3): Giv en the updated posterior p t ( θ ) and the pro visional THN/JHN sets from Layer 2, iBEAMS performs a coalition- based refinement in which each jamming coalition C ⊆ J ( t ) updates only its local jamming powers while keeping non- coalition actions fixed. Concretely , the coalition powers are refined by maximizing the aggregate secrecy of the activ e THNs, { P new k ( t ) } k ∈C = arg max { 0 ≤ P k ( t ) ≤ P max k } k ∈C X u ∈T ( t ) R s ( u, t ; p C ( t ) , p −C ( t )) , (68) 12 subject to THN-protection (bounded leakage/interference tow ard legitimate users) and posterior-weighted shaping constraints that concentrate jamming energy along high- probability AoA directions and enforce nulls tow ard protected THNs. The detailed deriv ation and constraint instantiation of (68) are provided in Appendix C. F . Thr ee layer Utility designed: Combined we define the slot- t decision tuple x t ≜ ( a t , z t , b t ) , from B and the overall utility defined as J t ( x t ) ≜ from B. T aken together, the three layers of the iBEAMS framew ork jointly solve the coupled optimization problems of Section III within a single hierarchical game structure. At the top, the Stackelber g leader layer realizes secrecy , and entropy-aware BS po wer control and po wer splitting through the constrained optimization in (49) with the SEE-based objectiv e in (48), thereby enforcing the power -simplex, secrecy , and sensing- entropy constraints through explicit penalty terms. On the follower side, the GNE layer leverages the utility definition in (52) together with the feasibility conditions in (53)–(56) to embed energy cost, secrecy gain, leakage, and information gain into a unified payof f, and computes equilibrium transmit powers and roles using the best-response and role-switching rules in (60)–(61). Finally , the Bayesian layer evolv es the belief state through (62)–(65), and coalition-level refinement in (66), while shaping sensing beams and cooperati ve jamming fields according to the inferred geometry of the eavesdropper . In the next section, we e v aluate the performance of this integrated iBEAMS framework through detailed numerical simulations and compare its secrecy , energy-efficienc y , and sensing behavior against relev ant baselines. V . P E R F O R M A N C E E V A L UA T I O N A. Simulation Setup W e e v aluate the proposed iBEAMS frame work in a do wn- link ISA C cellular scenario spanning multiple carrier frequen- cies ( 28 GH Z − 3 T H Z ), while maintaining a fixed system bandwidth, as summarized in T able I. The ISA C base station (IBS) is modeled as ULA with half-wavelength spacing and a fixed location, and a set of HNs are considred with compact planar antenna arrays to support both data transmission and cooperativ e jamming. The propagation en vironment follows a distance-dependent large-scale loss model with log-normal shadowing and Rician small-scale fading, using the channel parameters in T able I. The receiv er noise is computed from the PSD thermal noise and noise figure listed in T able I. The transmission po wer is limited by the IBS and per-HN po wer budgets in T able I. At each slot, the IBS (leader) updates the power -splitting variables and Stackelber g incenti ve prices within the specified bounds (T able I), and the HNs (followers) update their strategies through a per-slot GNE best-response routine using the con vergence tolerance and iteration cap in T able I. In parallel, the Bayesian layer maintains a belief ov er the eav esdropper AoA on the discretized angular grid and refines it through a kernel-based prediction and measurement update, with kernel/measurement settings as giv en in T able I. T ABLE I: Key simulation parameters Parameter V alue Carrier , bandwidth, and noise Carrier frequency , f c 28 GHz to 3 THz System bandwidth, B W 100 MHz Thermal noise PSD, N 0 (at ≈ 290 K ) − 174 dBm / Hz Receiv er noise figure, NF 7 dB ISA C base station (IBS) array and geometry ISA C BS ULA antennas, N t 128 IBS position, p BS (m) [0 , 0 , 10] ⊤ Hybrid edge node (HN) array and geometry Number of HNs, K HN 25 HN array size, N t, HN 4 × 4 = 16 Large-scale and small-scale channel model Path-loss exponent, n PL 2 . 2 Shadowing, σ sh 3 dB Rician K -factor , K Ric 10 dB Power budgets Max BS power , P max BS 20 W / 43 dBm Initial BS power , P (0) BS 15 W / 41 . 76 dBm Max per-HN power , P max HN 1 . 5 W / 31 . 76 dBm Leader (Stackelberg) variables and bounds BS power split ( α, β , γ ) (data/AN/sensing) (0 . 6 , 0 . 2 , 0 . 2) Incentiv e prices ( π t , τ t , κ t ) (reward/penalty/info) (0 . 7 , 0 . 3 , 0 . 1) Bounds on π t , ( π min , π max ) (0 , 1) Bounds on τ t , ( τ min , τ max ) (0 , 1) Bounds on κ t , ( κ min , κ max ) (0 , 1) Eve AoA posterior tracking (Bayesian layer) AoA grid, θ [ − 90 , 90] ◦ Initial kernel width, σ (0) ker 10 ◦ AoA measurement noise std. dev ., σ meas 5 ◦ GNE / best-response settings GNE tolerance, ε GNE 10 − 3 Max Best-Response (BR) iterations per slot, I max 50 B. Numerical Analysis In this section, we discuss the simulation results to ev aluate the proposed approach of iBEAMS unified framew ork. T o begin with, Figures 3a – 3c validate the con vergence of the pro- posed three-layer iBEAMS control architecture across 28 GHz, 500 GHz, and 3 THz. At the leader layer (Algorithm 1, Fig. 3a shows that the BS control variables conv er ge in the sense of diminishing update magnitudes and sustained objectiv e tracking: the power -split triplet ( α t , β t , γ t ) and the Stackelber g prices ( π t , τ t , κ t ) undergo an initial transient and then ev olve around stable operating points depending on ISA C BS Bayesian-Stackelberg Leader . Simultaneously , the secrecy tracking error | e t | decreases tow ard a small steady regime while the leader (ISA C BS) residual | r 1 | remains bounded, indicating stable closed-loop behavior under time-varying fad- ing/mobility effects. At the follower layer (Algorithm 2), Fig. 3b demonstrates that the per-slot Best Response (BR) iterations required to satisfy the GNE tolerance decrease over time, consistent with best response dynamics and equilibrium power P u in HN joint power control, and shared contraints. Moreov er , the mean GNE gap decays rapidly with BR iter- ation, confirming contraction of the equilibrium gap within each slot, including the 3 THz case exhibits a higher initial gap and slower decay , reflecting stronger coupling and a more challenging equilibrium landscape at higher carrier frequen- cies. Finally , at the Bayesian-cooperative refinement layer (Algorithm 3), Fig. 3c shows that the posterior entropy H ( p ) decreases and plateaus, implying concentration of the AoA 13 (a) (b) (c) Fig. 3: Con ver gence beha vior of the proposed iBEAMS three-layer optimization across Algorithms 1–3.3a: Algorithm 1 (Leader) con vergence across frequency , 3b: Algorithm 2 GNE conv er gence across frequency , 3c:Algorithm 3 Bayesian-Cooperativ e refinement con ver gence across frequenc y posterior and stabilization of sensing-dri ven localization, while coalition scaling con ver ges to a steady band near unity . The cooperativ e power-update residual norm decays toward zero (log scale) and the total jammer po wer stabilizes, e videncing con vergence of cooperati ve refinements without destabilizing power escalation. Overall, these algorithm results confirm that iBEAMS achie ves hierarchical conv ergence: the leader stabilizes po wer split and incenti ves while tracking secrec y , the follower game reaches GNE efficiently with decreasing itera- tion b urden, and the Bayesian-cooperative layer con verges in uncertainty reduction and coalition/power coordination, with the THz regime requiring comparatively stronger and longer adaptation. Figure 4 jointly shows that iBEAMS conv er ges to a stable secure operating regime in which the leader’ s power -split and incentiv e prices settle to steady v alues while the distributed HNs perform sparse, event-triggered THN/JHN role switching that preserves high long-term utility and se- crecy . Firstly , Fig. 4a illustrates the leader-layer (Bayesian- Stackelber g) con ver gence by jointly tracking:(i) sensing uncer- tainty via the posterior entropy H ( p ) (left axis), and (ii) the leader’ s control variables as the BS power -split coefficients ( α t , β t , γ t ) and the incentiv e prices ( π t , τ t , κ t ) . Ov er time, the data power fraction α t monotonically increases and then saturates, indicating that the leader progressiv ely reallocates ISA C BS resources toward information-bearing transmission once a stable secrecy regime is established. In contrast, the artificial-noise share β t gradually decreases, while the sens- ing share γ t drops more sharply before settling at a small nonzero value, reflecting a transition from an exploration phase to an exploitation regime in which sensing is kept lightweight but persistent. The incenti ve prices exhibit clear saturation behavior consistent with conv ergence: the jamming rew ard π t rapidly ramps up to its upper bound, signaling that iBEAMS persistently incentivizes cooperative jamming under strong eav esdropping; the leakage penalty τ t decays tow ard zero as leakage is driven into an acceptable range; and the sensing/information reward κ t increases steadily , promoting continued Bayesian information acquisition even as the direct sensing power fraction γ t is reduced. Meanwhile, the entropy H ( p ) remains high b ut bounded, fluctuating within a narrow band. T aken together , the joint flattening of ( α t , β t , γ t ) ,and ( π t , τ t , κ t ) , along with bounded entropy dynamics, demon- strates that the iBEAMS leader layer attains a stable closed- loop operating equilibrium that consistently balances secrecy- (a) (b) Fig. 4: Leader (ISA C BS)–follower (HNs) co-ev olution in iBEAMS within time slot, t at 28 GHz driv en jamming incentiv es, leakage mitigation, and sustained yet low-ov erhead sensing support. Secondly , Fig. 4b charac- terizes the local-layer adaptation of iBEAMS through time- varying role assignment between THNs and JHNs. The top panel shows that the network operates predominantly in a jammer-dominant regime: most HNs are persistently selected as JHNs (orange), while only a small subset remain THNs (blue) in each slot. This reflects operation under strong (or worst-case) eavesdropping conditions, where the controller prioritizes secrecy by allocating the majority of edge resources to cooperative jamming, while maintaining a minimal set of 14 (a) (b) (c) Fig. 5: Comparativ e performance of the proposed iBEAMS unified framew ork versus baseline and multiple models: (a) power – secrecy trade-offs, (b) secrecy energy efficiency (SEE), and (c) outage probability and secrecy success rate within time slot, t at 28 GHz THNs to sustain data deliv ery . The middle panel highlights discrete role-switching ev ents (T → J and J → T) that occur sporadically in response to changes in the en vironment (ac- tiv e Eve location, secrecy-mar gin degradation, or proximity- based jammer selection), showing that role updates are event- driv en rather than continuous. Crucially , the bottom panel demonstrates that these switching events induce only transient perturbations in aggregate HN utility indicating at switching instants are followed by rapid recovery to a high, stable state. In parallel, the JHN fraction remains tightly constrained within a narrow band across slots, indicating conv er gence of the network-wide security posture to a steady operating point, with role adjustments acting as sparse correctiv e actions rather than a source of instability . In Figure 5, we examine a significant numerical comparison of the proposed iBEAMS architecture against the baseline and three benchmark models is depicted in Fig. 5a. In Fig. 5a, the baseline exhibits zero average secrecy rate over all slots as the system could not communicate data to legitimate users ov er worst-case and str onger eavesdr opper , despite operating the BS around 43 . 5 dBm, confirming that con ventional com- munications without cooperativ e jamming is unable to counter strong eavesdropping. Model 1 with conv entional communica- tions with injected fixed AN improves the average secrecy rate to roughly 2 – 2 . 5 b/s/Hz, while Model 2 (ISA C BS with Stack- elberg decision) further increases it to about 3 . 5 – 4 . 0 b/s/Hz; howe ver , both require comparable or higher BS po wer levels (around 42 – 43 dBm). Model 3 (ISA C BS with Stackelberg decision and HN with role switching roles) reduces the BS power from approximately 41 . 8 dBm to near 40 . 2 dBm o ver time, but at the cost of a relatively modest secrecy rate of ≈ 1 . 6 – 1 . 8 b/s/Hz. In contrast, iBEAMS stabilizes the average secrecy rate of THNs around 4 . 4 – 4 . 7 b/s/Hz while maintaining a nearly flat BS po wer trajectory close to 41 . 5 dBm. Hence, relativ e to the best benchmarks, iBEAMS deliv ers a roughly 15 – 25% higher secrecy rate with lower transmission power , demonstrating a strictly superior secrecy–power trade-off. The corresponding secrecy energy efficienc y (SEE) profiles in Fig. 5b reinforce this trend. The baseline again attains an SEE of zero bits/Joule, whereas Model 1 achie ves only ≈ 0 . 15 – 0 . 25 bits/J and Model 3 hovers around 0 . 25 – 0 . 32 bits/J. Although, Model 2 is more efficient, fluctuating mostly in the 0 . 35 – 0 . 55 bits/J range. By contrast, iBEAMS consistently operates near the upper en velope of all curves, sustaining SEE values between 0 . 55 and 0 . 63 bits/J for the majority of slots, with only occasional transient drops associated with role-switching events. Overall, iBEAMS of fers roughly a 2 × SEE gain over Model 1 and a clear margin on the order of 30 – 70% over Model 2, while simultaneously guaranteeing higher secrecy rates. Finally , Fig. 5c summarizes the reliability of secrecy in terms of outage probability and secrecy success rate. Conse- quently , the baseline e xperiences a 100% secrecy outage and thus 0% success rate at the chosen threshold, indicating that it nev er meets the required secrecy lev el. Model 1 reduces the outage probability to 32 . 5% , and 67 . 5% success, and Model 2 further improves to 12 . 5% outage ( 87 . 5% success). Both Model 3 and iBEAMS achiev e zero outage and 100% secrecy success across the simulated horizon; howe ver , when combined with the higher secrecy rates and substantially better SEE shown in Figs. 5a, 5b, iBEAMS clearly dominates Model 3. Therefore, the three metrics jointly demonstrate that iBEAMS attains outage-free, high-rate secrecy with markedly superior energy efficiency , thereby establishing a strong per- formance advantage over all baseline and benchmark designs. Figures 6a illustrate the dynamics of the AoA posterior p ( θ | t ) for four representativ e eavesdroppers (Eve 5, Eve 10, Eve 15, and Eve 20) under a static deployment. For all cases, the iBEAMS Bayesian layer rapidly concentrates the posterior around the true AoA and then maintains a narrow , high–confidence ridge over time. After an initial learning phase of roughly t ≈ 10 – 15 slots, the dominant mode of p ( θ | t ) stabilizes within a tight angular window of approximately ± 5 ◦ – ± 10 ◦ around the true direction, with the peak probability routinely exceeding 0 . 7 – 0 . 9 on the color scale. This behavior is consistent across all four network configurations (from 5 up to 20 Eves), demonstrating that the proposed sensing-and- learning mechanism is able to accurately infer and r etain the correct posterior ev en as the number of potential eav esdroppers increases. Similarly , Figures 6b demonstrates the AoA posterior p ( θ | t ) for the same set of representati ve Ev es when the ea vesdroppers are mobile. Here the heatmaps exhibit a sequence of distinct angular tracks rather than a single stationary ridge, reflecting 15 (a) (b) Fig. 6: Comparison of Eve AoA posterior heatmaps for the proposed iBEAMS framework under (a) quasi-static and (b) mobile eavesdropping scenarios at 28 GHz, where each panel reports the time-varying posterior p ( θ | t ) for four representati ve eav esdroppers changes in the dominant AoA se gment as the activ e Eve mo ves or as different Eves become most threatening. Importantly , at each segment the posterior still forms a sharply peaked lobe, with peak probabilities again reaching ≈ 0 . 8 – 0 . 9 , and the transition between segments occurs within a small number of slots. This indicates that iBEAMS is able to quickly diminish outdated directions and re–localize the activ e eav esdropper whenev er the channel geometry changes.Like wise, this be- havior is preserved across scenarios with 5, 10, 15, and 20 candidate Eves highlights the robustness of the hierar- chical Bayesian update: e ven when the pool of adversaries grows, the framew ork continues to deliver high–confidence, angle–selectiv e posteriors that track the true direction o ver time. Overall, figure 6 the comparison between the static, and mobile heatmaps confirms that iBEAMS not only learns an accurate static posterior , but also maintains reliable AoA tracking in highly dynamic environments, thereby enabling superior , geometry-aw are physical-layer security against both few and many eav esdroppers. Fig. 7: Normalized ULA beam pattern at 28 GHz for pos- terior–aware iBEAMS beamforming, showing the array gain versus angle for four representati ve mobile eav esdroppers within the ± 10 ◦ sector Figure 7 illustrates the normalized ULA jamming beam pattern synthesized by the proposed iBEAMS frame work when steering to ward four representati ve mobile eav esdroppers (Eve5, Eve10, Eve15, and Eve20) whose AoA posteriors are provided by the Bayesian leader layer . Across the angular window θ ∈ [ − 10 ◦ , 10 ◦ ] , all four traces exhibit a sharp main lobe with peak gain close to 0 dB around the posterior mean AoA, while neighboring directions are consistently attenu- ated by about 5 – 15 dB. In se veral angles the array forms deep nulls below − 25 to − 30 dB, demonstrating that the CSI–aware, posterior-dri ven precoder can shape pronounced spatial notches in unintended directions while concentrating power precisely along the estimated eavesdropper direction. The strong o verlap between the four curves indicates that, ev en as the activ e Eve index changes and the number of eaves- droppers increases or decreases, iBEAMS rapidly re-steers the jamming beam to the new posterior without sacrificing array gain or side-lobe suppression. Consequently , the beam pattern faithfully reflects the underlying near-field physical channel under CSI bounds and confirms that iBEAMS can maintain highly directiv e, mobile-Eve–aligned jamming beams, thereby strengthening physical-layer protection with minimal leakage tow ard benign directions. V I . C O N C L U S I O N S T o conclude, this research has introduced iBEAMS, a multi-layer hierarchical Stackelber g–GNE–Bayesian frame- work for secure and energy-efficient ISA C in networks pop- ulated by hybrid edge nodes. The architecture tightly couples a Bayesian–Stackelber g ISAC BS controller , a GNE-based hybrid-edge node’ s power and role-selection game, and a Bayesian cooperativ e refinement layer that shapes geometry- aware jamming. Numerical ev aluations from 28 GHz up to 3 THz demonstrate hierarchical con ver gence: the leader’ s power -splitting variables and incentiv e prices settle around stable operating points with small secrecy-tracking error , the follower game reliably attains a GNE with a diminishing equi- librium gap, and the cooperati ve layer dri ves the AoA posterior entropy , coalition scaling, and aggregate jammer power to ward steady regimes without destabilizing oscillations. Relativ e to con ventional communication, fixed-AN, and Stackelber g-only 16 or role-switching benchmarks, iBEAMS achiev es substan- tially higher secrecy rates (approximately 4 . 4 – 4 . 7 b/s/Hz at 28 GHz), about a 2 × improvement in SEE over fixed AN, and a 30 – 70% SEE gain ov er Stackelberg-only ISA C, while maintaining zero secrecy outage. The Bayesian layer further yields narrow , high-confidence AoA posteriors and sharply directiv e, posterior -aligned jamming beams in both static and mobile eav esdropping scenarios, enabling robust, geometry- aware physical-layer protection. Notwithstanding these benefits, se veral limitations remain. The current formulation is restricted to a single-cell ISAC BS with a moderate number of hybrid nodes and does not explicitly capture inter-cell coordination, multi-BS coupling, or ultra-dense deployments. Again, RF and wideband prop- agation effects are modeled at a simulation and theoretical lev el; a more faithful treatment of hardware impairments, beam alignment, phase-noise, and nonlinear front-end distortions is required for hardware-accurate design. Moreo ver , the algo- rithms further needs enhancement of a rigorous stability and robustness analysis under model mismatch, rapid mobility , and adversarial behavior . Finally , although computational and signaling overheads are quantified numerically , real-time val- idation on mmW a ve/THz ISAC testbeds and the dev elopment of lower -complexity of iBEAMS remain essential steps toward deployment. T aken together , the results indicate that iBEAMS offers a principled pathway for addressing the core challenge of securing mobile eavesdroppers in networks of distributed hybrid edge nodes under stringent power and QoS constraints. A P P E N D I X A F O L L O W E R U T I L I T Y A N D G N E F O R M U L A T I O N At slot t , each activ e HN u ∈ A ( t ) selects a transmit power P u ( t ) ∈ [0 , P max u ] and a role role u ( t ) ∈ { THN , JHN } in response to the leader broadcast a t = ( α t , β t , γ t , π t , τ t , κ t ) . T o align individual incentiv es with the system-le vel SEE objectiv e, the local utility of HN U is defined as U u ( P u ( t ) , role u ( t ); a t , P − u ( t )) = η u R s ( u, t ) − c u P u ( t ) − τ t Ξ u ( t ) + π t J u ( t ) + κ t I ( t ) , (69) where P − u ( t ) collects the powers of all other HNs. Here, η u R s ( u, t ) rew ards secrecy throughput (effecti ve when HN acts as a THN), c u P u ( t ) penalizes power expenditure, τ t Ξ u ( t ) penalizes secrecy leakage attributable to HN, π t J u ( t ) rewards effecti ve friendly-jamming contrib ution when HN acts as a JHN, and I ( t ) denotes the global entropy reduction or infor - mation gain from ISAC sensing shared among HNs, scaled by the information price κ t . Thus, ( π t , τ t , κ t ) implement the proposed secrecy-energy-entrop y aware pricing by embedding BS priorities into follower payoffs. In addition, HN deci- sions making and utility are constrained by local bounds and network-wide coupling conditions: 0 ≤ P u ( t ) ≤ P max u , ∀ u, (70) X u ∈A ( t ) P u ( t ) ≤ P max FJ , (71) Ξ u ( t ) ≤ Ξ max , ∀ u, (72) g ( P ( t )) ≤ 0 , (73) which define the global feasible set P ( t ) = { P ( t ) | (70)–(73) } and the individual feasible set P u ( t ) = { P u ( t ) | ∃ P − u ( t ) s.t. ( P u ( t ) , P − u ( t )) ∈ P ( t ) } . Because U u depends on P − u ( t ) and P u ( t ) is shaped by shared constraints, the follower interaction forms a GNE game. Thus, a power profile P ⋆ ( t ) is a GNE if, for every u , U u ( P ⋆ u ( t ) , P ⋆ − u ( t )) ≥ U u ( P u ( t ) , P ⋆ − u ( t )) , ∀ P u ( t ) ∈ P u ( t ) . (74) Algorithm 2 computes an implementable approximation through best-response iterations on a discrete grid): P ( i ) u ( t ) = arg max P u ( t ) ∈P u ( t ) U u ( P u ( t ) , P ( i − 1) − u ( t )) , (75) terminated when ∥ P ( i ) u ( t ) − P ( i − 1) u ( t ) ∥≤ ϵ for all u , yielding P ⋆ ( t ) used for subsequent role switching in Layer 2. A P P E N D I X B U N I FI E D T H R E E - L A Y E R U T I L I T Y T o summarize the three-layer iBEAMS loop in a sin- gle objectiv e form, we define the slot- t decision tuple x t ≜ ( a t , z t , b t ) , where (i) the leader variables are a t = ( P BS ( t ) , α t , β t , γ t , π t , τ t , κ t ) , (ii) the follower variables are z t = ( P ( t ) , ρ ( t )) with P ( t ) = { P u ( t ) } u ∈A ( t ) and roles ρ ( t ) = { role u ( t ) } u ∈A ( t ) , and (iii) the Bayesian belief state is b t ≜ p t ( θ E ) with entropy H ( b t ) . Now , the compact global utility that encounter secrecy , energy , and sensing uncertainty all together is J t ( x t ) ≜ SEE( t ) | {z } secrecy–energy objectiv e − λ sec R ⋆ s − R s ( t ) + − λ H ( H ( b t ) − H ⋆ ) + + λ I I ( t ) |{z} entropy reduction / information gain , (76) where R s ( t ) is a system secrecy statistic ( mean or minimum secrecy rate ov er active users), H ⋆ is the target entropy lev el, and I ( t ) denotes the sensing-driven entropy reduction or information gain (shared across HNs) used to couple the Bayesian layer to the resource-allocation loop. In addition, for the three-layer coupling and equilibrium response, given a t and b t , the follower layer computes a GNE response from (69) z ⋆ t ( a t , b t ) ∈ GNE( a t , b t ) , (77) under the local and coupling feasibility constraints. The Bayesian layer updates the belief state by an ISA C sens- ing/refinement operator b t +1 = B ( b t , a t , z ⋆ t ) , (78) which induces the entropy H ( b t +1 ) and the information gain I ( t ) . The overall three-layer control problem can therefore be expressed as the leader optimization max a t ∈A lead J t a t , z ⋆ t ( a t , b t ) , b t , (79) where A lead collects the leader feasibility constraints (po wer budget and power-splitting simplex for ( α t , β t , γ t ) , together 17 with the bounds on ( π t , τ t , κ t ) ). Equation (79) provides a single objective view of iBEAMS: the leader chooses a t to maximize SEE while penalizing secrecy deficit and excessiv e belief entropy , anticipating the distrib uted GNE response and the sensing-driv en belief e volution in (78). A P P E N D I X C C O O P E R AT I V E J A M M I N G O P T I M I Z AT I O N I N L A Y E R 3 In Layer 3, the posterior update p t ( θ ) identifies the most likely ea vesdropper directions and enables cooperativ e re- finement among jammer HNs. After the Layer 2 GNE, the THN/JHN roles and a feasible power profile P ⋆ ( t ) are av ail- able. Let C ⊆ J ( t ) denote a jamming coalition (a subset of JHNs) selected based on the dominant posterior peaks. In Layer 3, only the coalition po wers p C ( t ) ≜ { P k ( t ) } k ∈C are refined, while all other powers remain fixed at their current values: p −C ( t ) = p ⋆ −C ( t ) . a) Reduction fr om Network Secrecy Objective to Coali- tion Subpr oblem: A natural refinement criterion is to improve the aggregate secrecy of the currently served THNs under fixed leader parameters and fixed non-coalition actions. Using the standard secrecy-rate definition, R s , the coalition-level refinement is obtained by restricting the optimization variables to p C ( t ) while keeping all other decisions fixed. This yields the Layer 3 cooperative-jamming subproblem: p new C ( t ) = arg max p C ( t ) X u ∈T ( t ) R s ( u, t ; p C ( t ) , p −C ( t )) , (80) where T ( t ) denotes the THN set. Equation (80) is exactly the statement that Layer 3 performs a local impr ovement step on the network secrecy objectiv e conditioned on the equilibrium outcome of Layer 2 and the belief update of Layer 3. b) Leakag e Constraints towar d Pr otected THNs: Since friendly jamming may harm legitimate recei vers through resid- ual leakage, the refinement is performed under THN-protection constraints. A common leakage model is an interference- temperature bound at each THN u due to the coalition: Ξ u ( t ) ≜ X k ∈C P k ( t ) | h k → u ( t ) | 2 ≤ Ξ max , ∀ u ∈ T ( t ) , (81) where h k → u ( t ) is the (effecti ve) channel from jammer k to THN u (including beamforming gains if applicable). This constraint enforces QoS protection while allowing coalition power redistribution. c) P osterior-W eighted AN/J amming Shaping Constraint: T o ensure that refined jamming is aligned with the updated belief p t ( θ ) , a posterior-weighted shaping constraint is im- posed on the coalition radiation toward the angular grid Φ . Let g k ( θ ) ≥ 0 denote jammer k ’ s directional gain (beampattern) tow ard θ . The coalition jamming field is J C ( θ , t ) = X k ∈C P k ( t ) g k ( θ ) . (82) A belief-aligned shaping requirement can be expressed as a lower bound on posterior-weighted jamming energy , X θ ∈ Φ p t ( θ ) J C ( θ , t ) ≥ J min ( t ) , (83) or , equiv alently , by enforcing sufficient jamming on the dom- inant posterior support (e.g., for θ ∈ Φ peak ( t ) where p t ( θ ) is large). This ensures that refinement concentrates energy in secrecy-critical directions identified by sensing. d) F inal Cooperative J amming Optimization: Combining (80) with the local power limits, THN leakage protection, and posterior-weighted shaping yields the Layer 3 problem used in Algorithm 3: { P new k ( t ) } k ∈C = arg max { 0 ≤ P k ( t ) ≤ P max k } k ∈C X u ∈T ( t ) R s ( u, t ; p C ( t ) , p −C ( t )) s.t. X k ∈C P k ( t ) | h k → u ( t ) | 2 ≤ Ξ max , ∀ u ∈ T ( t ) , X θ ∈ Φ p t ( θ ) X k ∈C P k ( t ) g k ( θ ) ≥ J min ( t ) . (84) Problem (84) is generally noncon ve x due to the secrecy- rate structure, hence it is implemented in Layer 3 via low- complexity refinement (e.g., discrete-grid search, successive con vex approximation, or projected best-response updates) and terminated when the secrecy-impro vement criterion in Algorithm 3 is satisfied. R E F E R E N C E S [1] M. Z. Chowdhury , M. Shahjalal, S. Ahmed, and Y . M. Jang, “6g wireless communication systems: Applications, requirements, technolo- gies, challenges, and research directions, ” IEEE Open J ournal of the Communications Society , vol. 1, pp. 957–975, 2020. [2] I. F . Akyildiz, A. Kak, and S. Nie, “6g and beyond: The future of wireless communications systems, ” IEEE access , vol. 8, pp. 133 995– 134 030, 2020. [3] N. Su, F . Liu, and C. Masouros, “Sensing-assisted eav esdropper estima- tion: An isac breakthrough in physical layer security , ” IEEE T ransactions on Wir eless Communications , vol. 23, no. 4, pp. 3162–3174, 2024. [4] M. Iqbal, A. Y . Jav aid, and J. Kim, “ Antenna beamforming patterns of multimedia transmissions for nextg phy-security , ” in 2024 IEEE Interna- tional Symposium on Br oadband Multimedia Systems and Br oadcasting (BMSB) , 2024, pp. 1–6. [5] V . Petrov , H. Guerboukha, A. Singh, and J. M. Jornet, “W avefront hopping for physical layer security in 6g and beyond near-field thz communications, ” IEEE T ransactions on Communications , vol. 73, no. 5, pp. 2996–3012, 2025. [6] V . Petrov , D. Moltchanov , J. M. Jornet, and Y . Koucherya vy , “Exploiting multipath terahertz communications for physical layer security in beyond 5g networks, ” in IEEE INFOCOM 2019 - IEEE Confer ence on Computer Communications W orkshops (INFOCOM WKSHPS) , 2019, pp. 865–872. [7] F . Liu, Y . Cui, C. Masouros, J. Xu, T . X. Han, Y . C. Eldar, and S. Buzzi, “Integrated sensing and communications: T oward dual-functional wire- less networks for 6g and beyond, ” IEEE Journal on Selected Areas in Communications , vol. 40, no. 6, pp. 1728–1767, 2022. [8] Z. He, W . Xu, H. Shen, Y . Huang, and H. Xiao, “Energy efficient beamforming optimization for integrated sensing and communication, ” IEEE Wir eless Communications Letters , vol. 11, no. 7, pp. 1374–1378, 2022. [9] M. T . Mamaghani, X. Zhou, N. Y ang, and A. Lee Swindlehurst, “Secur- ing integrated sensing and communication against a mobile adversary: A stackelberg game with deep reinforcement learning, ” IEEE Journal on Selected Areas in Communications , pp. 1–1, 2025. [10] Y . Cui, F . Liu, X. Jing, and J. Mu, “Integrating sensing and communi- cations for ubiquitous iot: Applications, trends, and challenges, ” IEEE Network , vol. 35, no. 5, pp. 158–167, 2021. [11] A. Liu, Z. Huang, M. Li, Y . W an, W . Li, T . X. Han, C. Liu, R. Du, D. K. P . T an, J. Lu et al. , “ A survey on fundamental limits of integrated sensing and communication, ” IEEE Communications Surveys & Tutorials , vol. 24, no. 2, pp. 994–1034, 2022. [12] Y . Zhong, T . Bi, J. W ang, J. Zeng, Y . Huang, T . Jiang, Q. W u, and S. W u, “Empowering the v2x network by integrated sensing and com- munications: Background, design, adv ances, and opportunities, ” IEEE Network , vol. 36, no. 4, pp. 54–60, 2022. 18 [13] Y . Liu, B. Zhang, D. Guo, H. W ang, G. Ding, N. Y ang, and J. Gu, “ A game theoretical anti-jamming beamforming approach for integrated sensing and communications systems, ” IEEE T ransactions on V ehicular T ec hnology , vol. 73, no. 10, pp. 15 780–15 785, 2024. [14] L. W ang, W . Wu, M. Dai, and H. Zhang, “Game-theoretic approach for integrated sensing and computation offloading in vehicular edge networks: A utility maximization design, ” IEEE Internet of Things Journal , vol. 12, no. 13, pp. 23 694–23 708, 2025. [15] C. Ouyang, Y . Liu, H. Y ang, and N. Al-Dhahir, “Integrated sensing and communications: A mutual information-based framework, ” IEEE Communications Magazine , vol. 61, no. 5, pp. 26–32, 2023. [16] N. T . Hoa, D. V an T ung, H. T . Nguyen, N. C. Luong, and D. Niyato, “Fractional game theory for dynamic resource allocation in heteroge- neous integrated sensing and communication systems, ” IEEE T ransac- tions on V ehicular T echnology , vol. 74, no. 12, pp. 19 655–19 666, 2025. [17] M. T . Mamaghani, X. Zhou, N. Y ang, and A. L. Swindlehurst, “Securing integrated sensing and communication against a mobile adversary: A stackelberg game with deep reinforcement learning, ” arXiv preprint arXiv:2501.02271 , 2025. [18] J. W ang, J. He, G. Sun, Z. Xiong, D. Niyato, S. Mao, D. I. Kim, and T . Xiang, “Safeguarding isac performance in low-altitude wireless net- works under channel access attack, ” arXiv preprint , 2025. [19] S. Li, H. Dong, C. Shan, X. Fang, W . W u, and Z. Li, “Secure hybrid beamforming design for mmwav e integrated sensing and communication systems, ” IEEE T ransactions on V ehicular T echnolo gy , vol. 74, no. 7, pp. 10 622–10 638, 2025. [20] M. M. Kamal, S. Zain Ul Abideen, M. A. Al-Khasawneh, A. Alabrah, R. Sohail Ahmed Larik, and M. Irfan Marwat, “Optimizing secure multi- user isac systems with star-ris: A deep reinforcement learning approach for 6g networks, ” IEEE Access , vol. 13, pp. 31 472–31 484, 2025. [21] C. Jiang, C. Zhang, C. Huang, J. Ge, D. Niyato, and C. Y uen, “Ris- assisted isac systems for robust secure transmission with imperfect sense estimation, ” IEEE Tr ansactions on W ir eless Communications , vol. 24, no. 5, pp. 3979–3992, 2025. [22] Q. Zhu, C.-X. W ang, B. Hua, K. Mao, S. Jiang, and M. Y ao, “3gpp tr 38.901 channel model, ” in the wiley 5G Ref: the essential 5G refer ence online . W iley , 2021, pp. 1–35. [23] H. Poddar, D. Gold, D. Lee, N. Zhang, G. Sridharan, H. Asplund, and M. Shafi, “Overvie w of 3gpp release 19 study on channel modeling enhancements to tr 38.901 for 6g, ” arXiv pr eprint arXiv:2507.19266 , 2025. [24] M. Iqbal and A. Y . Javaid, “ A dual belief-driven bayesian-stackelberg framew ork for low-comple xity and secure near-field isac systems, ” arXiv pr eprint arXiv:2602.09754 , 2026. [25] O. E. A yach, S. Rajagopal, S. Abu-Surra, Z. Pi, and R. W . Heath, “Spatially sparse precoding in millimeter wave mimo systems, ” IEEE T ransactions on W ir eless Communications , vol. 13, no. 3, pp. 1499– 1513, 2014. [26] A.-A. A. Boulogeorgos, J. M. Jornet, and A. Alexiou, “Directional terahertz communication systems for 6g: Fact check, ” IEEE V ehicular T ec hnology Magazine , vol. 16, no. 4, pp. 68–77, 2021. [27] S. Goel and R. Negi, “Guaranteeing secrecy using artificial noise, ” IEEE T ransactions on W ir eless Communications , vol. 7, no. 6, pp. 2180–2189, 2008. [28] C. Balanis, Antenna Theory: Analysis and Design . W iley , 2016. [Online]. A vailable: ht tps://books.goog le.com/books?id =iFEBCgAAQB AJ [29] R. J. Mailloux, Phased array antenna handbook . Artech house, 2017. [30] F . Liu and C. Masouros, “Hybrid beamforming with sub-arrayed mimo radar: Enabling joint sensing and communication at mmwav e band, ” in ICASSP 2019 - 2019 IEEE International Conference on Acoustics, Speech and Signal Processing (ICASSP) , 2019, pp. 7770–7774. [31] D. Zhang, Y . W ang, X. Li, and W . Xiang, “Hybridly connected structure for hybrid beamforming in mmwav e massiv e mimo systems, ” IEEE T ransactions on Communications , vol. 66, no. 2, pp. 662–674, 2018. [32] S. R. Hadimani, G. S. GD, and P . Kumar , “Performance inv estigation of ris-assisted smart city communication system under log-distance path loss and rician fading effects, ” in 2025 3r d International Conference on Smart Systems for applications in Electrical Sciences (ICSSES) . IEEE, 2025, pp. 1–6. [33] H. Ni, M. Anjum, D. Mishra, and A. Sene viratne, “Energy- efficient near-field beamforming: A revie w on practical channel models, ” Energies , vol. 18, no. 11, 2025. [Online]. A vailable: https://www .mdpi.com/1996- 1073/18/11/2966 [34] E. Bj ¨ ornson, O. T . Demir , and L. Sanguinetti, “ A primer on near-field beamforming for arrays and reconfigurable intelligent surfaces, ” 2021 55th Asilomar Conference on Signals, Systems, and Computers , pp. 105–112, 2021. [Online]. A vailable: h t t ps : //api.semanticscholar .org/CorpusID:238743929 [35] T . S. Rappaport, R. W . Heath, R. C. Daniels, and J. N. Murdock, Millimeter W ave W ireless Communications . Pearson, 2015. [36] A. Goldsmith, W ireless Communications . Cambridge Univ ersity Press, 2005. [37] S. Shafiee and S. Ulukus, “ Achiev able rates in gaussian miso channels with secrec y constraints, ” in 2007 IEEE International Symposium on Information Theory , 2007, pp. 2466–2470. [38] A. D. W yner, “The wire-tap channel, ” Bell system technical journal , vol. 54, no. 8, pp. 1355–1387, 1975. [39] O. T aghizadeh, P . Neuhaus, R. Mathar, and G. Fettweis, “Secrecy energy efficienc y of mimome wiretap channels with full-duple x jamming, ” IEEE T ransactions on Communications , vol. 67, no. 8, pp. 5588–5603, 2019. [40] M. Hua, Y . W ang, Q. Wu, H. Dai, Y . Huang, and L. Y ang, “Energy- efficient cooperativ e secure transmission in multi-uav-enabled wireless networks, ” IEEE T ransactions on V ehicular T echnology , vol. 68, no. 8, pp. 7761–7775, 2019. [41] S. A. Doly , “ Adaptive waveform co-design for integrated sensing and communications (isac), ” Ph.D. dissertation, Arizona State Univ ersity , 2025. [42] L. Maman, S. Zach, and A. Boag, “Beam shaping by phase-only wa ve- form encoding for transmitting array antennas in radar applications, ” IEEE Open Journal of Antennas and Pr opagation , v ol. 6, no. 2, pp. 478–486, 2025. [43] N. Qi, W . W ang, F . Zhou, L. Jia, Q. Wu, S. Jin, and M. Xiao, “T wo birds with one stone: Simultaneous jamming and eavesdropping with the bayesian-stackelberg g ame, ” IEEE T ransactions on Communications , vol. 69, no. 12, pp. 8013–8027, 2021. [44] X. Zhu, J. Liu, L. Lu, T . Zhang, T . Qiu, C. W ang, and Y . Liu, “Enabling intelligent connectivity: A survey of secure isac in 6g networks, ” IEEE Communications Surveys & Tutorials , vol. 27, no. 2, pp. 748–781, 2025. [45] C.-K. Y u, M. van der Schaar, and A. H. Sayed, “Distributed learning for stochastic generalized nash equilibrium problems, ” IEEE T ransactions on Signal Pr ocessing , vol. 65, no. 15, pp. 3893–3908, 2017.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment