Automated Reencoding Meets Graph Theory
Bounded Variable Addition (BVA) is a central preprocessing method in modern state-of-the-art SAT solvers. We provide a graph-theoretic characterization of which 2-CNF encodings can be constructed by an idealized BVA algorithm. Based on this insight, …
Authors: Benjamin Przybocki, Bernardo Subercaseaux, Marijn J. H. Heule
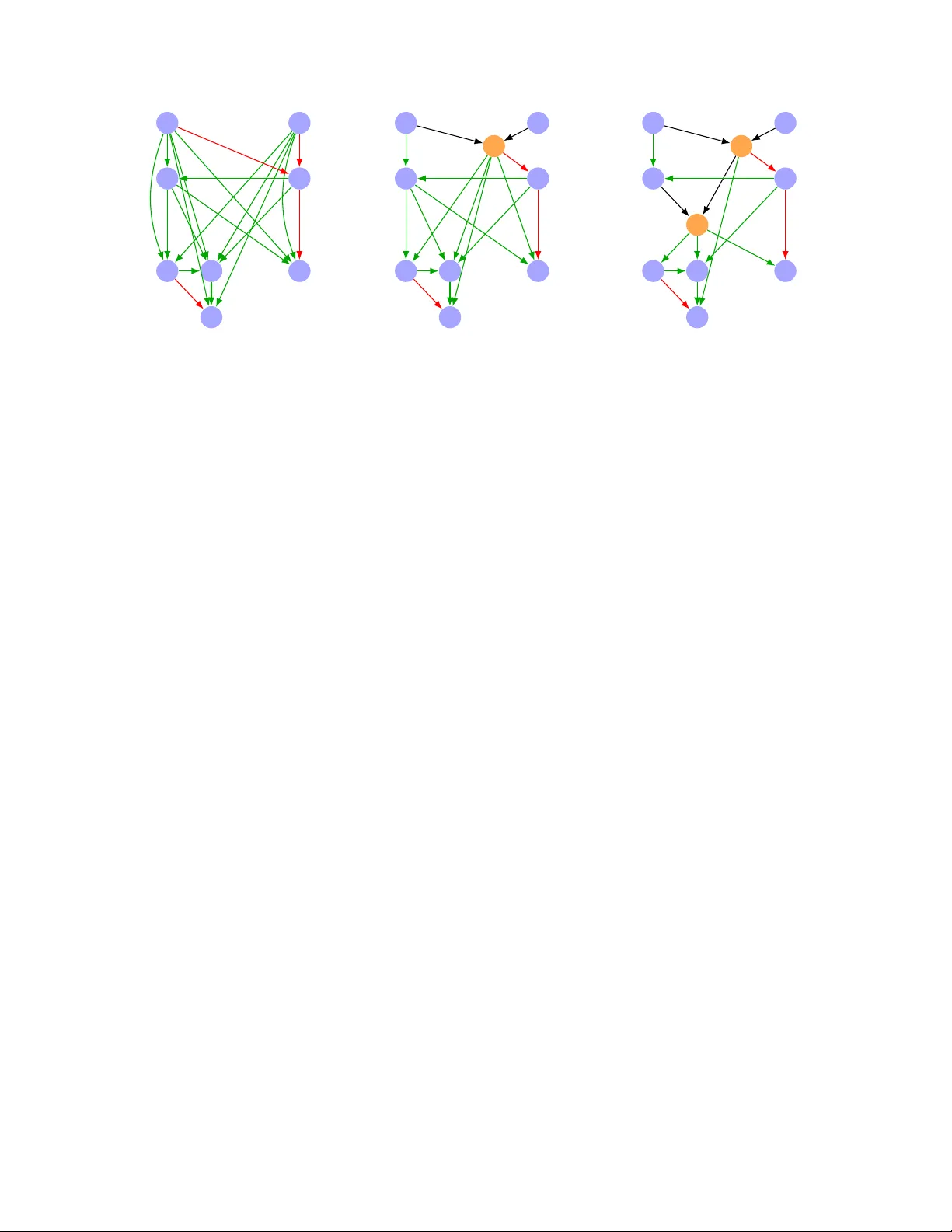
Automated Reenco ding Meets Graph Theory Benjamin Przyb ocki , Bernardo Sub ercaseaux , and Marijn J. H. Heule Carne gie Mel lon University [bpryzboc,bsuberca,mheule]@andrew.cmu.edu Abstract Bounde d V ariable A ddition (BV A) is a central prepro cessing metho d in mo dern state-of-the- art SA T solvers. W e pro vide a graph-theoretic c haracterization of which 2-CNF enco dings can be constructed by an idealized BV A algorithm. Based on this insigh t, w e prov e new results about the behavior and limitations of BV A and its interaction with other prepro cessing techniques. W e show that idealized BV A, plus some minor additional prepro cessing (e.g., equiv alent literal substitution), can reencode any 2-CNF form ula with n v ariables in to an equiv alen t 2-CNF formula with ( lg(3) 4 + o (1)) n 2 lg n clauses. F urthermore, we show that without the additional prepro cessing the constant factor worsens from lg(3) 4 ≈ 0 . 396 to 1, and that no reenco ding metho d can ac hieve a constan t b elo w 0 . 25. On the other hand, for the at-most-one constraint on n v ariables, we pro v e that idealized BV A cannot reenco de this constraint using few er than 3 n − 6 clauses, a b ound that we pro v e is achiev ed b y actual implementations. In particular, this shows that the product enco ding for at-most-one, which uses 2 n + o ( n ) clauses, cannot be constructed by BV A regardless of the heuristics used. Finally , our graph-theoretic c haracterization of BV A allo ws us to lev erage recen t work in algorithmic graph theory to develop a drastically more efficien t implementation of BV A that achiev es a comparable clause reduction on random monotone 2-CNF form ulas. 1 In tro duction Pro viding a satisfactory explanation for the remark able p erformance of SA T solv ers in practice is a ma jor theoretical challenge. Part of the difficult y of explaining this phenomenon, further detailed in the appropriately titled article “On the Unreasonable Effectiveness of SA T Solvers” b y V ardi and Ganesh [ 9 ], is that mo dern SA T solvers combine a v ariet y of heuristics, prepro cessing and inpro cessing tec hniques, data structures, and so on. W e p osit that, to make progress on the ov erall question, we ought to b etter understand the p o wer and limitations of each of these ingredien ts. In this pap er, we home in on one of these comp onen ts, namely , Bounde d V ariable A ddition (BV A) [ 20 ], a prepro cessing technique that in troduces auxiliary v ariables to reenco de an input form ula into an equisatisfiable form ula with fewer clauses. In 2023, a successor of BV A named Structur e d BV A (SBV A) [ 10 ], led the solv er SBV A-CaDiCaL , whose primary innov ation was to incorp orate SBV A as prepro cessing to the state-of-the-art solver CaDiCaL , to win the 1st place in the 2023 SA T Comp etition [ 4 ]. A t the 2024 SA T Comp etition, man y other solvers follow ed suit b y including some v arian t of BV A as a prepro cessing step, including the comp etition winner kissat-sc2024 [ 23 ]. BV A is no w incorp orated into the stable v ersions of CaDiCaL and Kissat under the name factor [ 6 ]. Ho w ever, despite its empirically demonstrated utility , little is known ab out BV A and its v arian ts from a theoretical p oin t of view. F or example, Biere, one of the authors of the original BV A pap er, commen ted [ 5 ]: 1 In [ 20 ], we alr e ady r e alize d that BV A r e enc o des [the dir e ct enc o ding of the at-most-one c onstr aint] into something b etter. R esults wer e only empiric al though and we did not analyze whether in principle BV A c an turn the dir e ct enc o ding into for instanc e the pr o duct or se quential c ounter enc o ding. In this paper, we develop a graph-theoretic framework for analyzing BV A, by means of which we can answer these and similar questions ab out the p o w er and limitations of BV A. F urthermore, our framew ork allo ws us to draw on recen t w ork in algorithmic graph theory to dev elop a drastically more efficien t implemen tation of BV A. Our Results W e fo cus on the b ehavior of BV A on 2-CNF subformulas. Man y formulas of interest, including, e.g., most SA T comp etition formulas, contain a large 2-CNF subformula that can b e reenco ded more compactly , leading to faster run times. In Section 6 , we justify in more detail why the 2-CNF fragmen t not only captures the most imp ortan t asp ects of the theoretical analysis but also explains most of BV A’s empirical success. Our primary result is a characterization of which reenco dings of a 2-CNF formula are achiev able b y BV A. Our c haracterization is in terms of r e ctifier networks [ 8 , 14 , 19 ], a graph-theoretic notion that has b een studied in the con text of circuit complexit y . Sp ecifically , we sho w in Theorem 5 that there is a corresp ondence b et w een reenco dings ac hiev able b y BV A and what we call strict p olarize d r e ctifier networks . Our c haracterization holds for an ide alize d v ersion of BV A that abstracts aw ay implemen tation-sp ecific heuristics. With this c haracterization in hand, we first study the class of 2-CNF formulas in general. By generalizing an old result of Nechiporuk [ 21 ] ab out rectifier netw orks, we prov e the follo wing: 1 Theorem 1 (Informal) . Ide alize d BV A c an r e enc o de every 2-CNF formula with n variables to one with at most (1 + o (1)) n 2 lg n clauses. Note that, without reenco ding, 2-CNF formulas can hav e Θ( n 2 ) clauses. W e also sho w that the b ound from Theorem 1 is sharp, in the sense that there is some 2-CNF form ula that idealized BV A reenco des with at least (1 − o (1)) n 2 lg n clauses. On the other hand, we describ e a simplification routine that one can run b efore BV A (“pre-prepro cessing”), which consists of equiv alent literal substitution and a weak er form of failed literal elimination [ 11 ], and this simplification step improv es the w orst-case p erformance of idealized BV A: Theorem 2 (Informal) . Ide alize d BV A with simplific ation c an r e enc o de every 2-CNF formula with n variables to one with at most ( lg(3) 4 + o (1)) n 2 lg n clauses. This b ound is also sharp. F urthermore, w e sho w that for every reenco ding metho d whose output is 2-CNF, there is some 2-CNF formula that it reenco des with at least ( 1 4 − o (1)) n 2 lg n clauses. Th us, with resp ect to w orst-case analysis, idealized BV A is optimal up to a constant factor. An imp ortan t subset of 2-CNF formulas is the monotone (or antitone) 2-CNF formulas. F or example, a direct enco ding for finding an indep enden t set in a graph G w ould include, for every edge { u, v } ∈ E ( G ), a clause ( x u ∨ x v ) . W e can actually impro v e the b ound from Theorem 1 for monotone 2-CNF formulas: Theorem 3 (Informal) . Ide alize d BV A c an r e enc o de every monotone 2-CNF formula with n variables to one with at most ( 1 4 + o (1)) n 2 lg n clauses. 1 All logarithms in this pap er are base 2 unless otherwise sp ecified. 2 This b ound is sharp, not merely for idealized BV A but for arbitrary reenco ding metho ds whose output is 2-CNF. Next, we study BV A’s p erformance on a particular class of 2-CNF formulas, namely the direct enco ding of the at-most-one constrain t on n v ariables: A tMostOne ( x 1 , . . . , x n ) : = ^ 1 ≤ i n , a truncation thereof. Within each blo c k B i , for each pair of v ertices { u, v } ∈ B i 2 create in R an auxiliary vertex z { u,v } , and create edges ( u, z { u,v } ) and ( v , z { u,v } ). Now, let r = ⌊ log 3 n − 3 log 3 log 3 n ⌋ , and partition as w ell V ( G ) in to parts P 1 , . . . , P ⌈ n/r ⌉ of size at most r ; sp ecifically , let P i = { v ( i − 1) · r +1 , . . . , v i · r } or, if i · r > n , a truncation thereof. F or eac h part P i and edge ( u, v ) ∈ E ( G ) ∩ ( P i × P i ), create in R a directed edge ( u, v ) with p ′ ( u, v ) = p ( u, v ). No w, for each part P i and each function S : P i → {− , 0 , + } , create in R an auxiliary vertex y S , and create a directed edge ( y S , v ) with p ′ ( y S , v ) = − for every v ∈ P i satisfying S ( v ) = − , and create a directed edge ( y S , v ) with p ′ ( y S , v ) = + for ev ery v ∈ P i satisfying S ( v ) = +. Giv en a vertex v ∈ V ( G ), let N ± ( v ) = { w ∈ V ( G ) | ( v , w ) ∈ E ( G ) and p ( v , w ) = ±} . Then, for each S : P i → {− , 0 , + } , let A ( S ) := { v ∈ P j | j < i, N − ( v ) ∩ P i = S − 1 ( − ) , and N + ( v ) ∩ P i = S − 1 (+) } . Finally , for each ∈ [ ⌈ n/q ⌉ ], let A ℓ ( S ) := A ( S ) ∩ B ℓ , and let a 1 , . . . , a k b e the elements of A ℓ ( S ) in an arbitrary order. Then, create in R directed edges ( z { a 2 j − 1 ,a 2 j } , y S ) for j ∈ [ ⌊ k / 2 ⌋ ], and if k is o dd, create the directed edge ( a k , y S ). If R con tains an y auxiliary vertices not b elonging to a v alid w alk, then delete them and their incident edges. This completes the construction of R . The full pro of in the app endix prov es that R is a strict rectifier net w ork for ( G, p ) and has at most lg(3) 4 + o (1) n 2 lg n edges. T ogether with the simplification from Prop osition 1 , we obtain the follo wing: Corollary 1. Every 2-CNF formula ϕ on n variables has a 2-CNF enc o ding ϕ ′ such that | ϕ ′ | ≤ ( lg(3) 4 + o (1)) n 2 lg n , and mor e over, such an enc o ding c an b e c ompute d in time O ( n 2 ) . Pr o of. It suffices to com bine Proposition 1 with Theorem 6 , and observe from the previous pro of that the construction can b e carried out in time O ( n 2 ). 3 4.2 Lo wer Bound for BV A With Simplification Using an information-theoretic argumen t, we now show that the b ound from Theorem 6 is sharp. W e start b y b ounding the num b er of 2-CNF form ulas with at most m clauses and the n umber of simple 2-CNF formulas on n v ariables. Lemma 2. The numb er of 2-CNF formulas with at most m clauses is at most 2 (1+ o (1)) m · lg m . 3 A similar construction, with pseudo code, app ears in [ 18 , Algorithm 1]. 10 Lemma 3. The numb er of simple 2-CNF formulas on n variables is at le ast 3 (1 / 2 − o (1)) n 2 . No w, w e can com bine these t w o lemmas to prov e the low er b ound: Prop osition 2. Ther e is a simple 2-CNF formula ϕ on n variables such that, for every ϕ ′ with ϕ ∼ ∼ ▷ BV A ∗ ϕ ′ , we have | ϕ ′ | ≥ lg(3) 4 − o (1) n 2 lg n . Pr o of. Let g ( m ) b e the n um ber of 2-CNF formulas with at most m clauses, and let h ( n ) b e the n um b er of simple 2-CNF formulas on n v ariables. By Lemmas 2 and 3 , lg g ( m ) ≤ (1 + o (1)) m · lg m and lg h ( n ) ≥ (lg (3) / 2 − o (1)) n 2 . If ϕ ∼ ∼ ▷ BV A ∗ ϕ ′ , then p erforming v ariable elimination (in the Da vis–Putnam sense) on the auxiliary v ariables in ϕ ′ yields ϕ . In particular, ϕ ′ has enough information to uniquely reconstruct ϕ . Th us, if for ev ery simple 2-CNF form ula ϕ on n v ariables, there is a 2-CNF formula ϕ ′ with at most m clauses suc h that ϕ ∼ ∼ ▷ BV A ∗ ϕ ′ , then g ( m ) ≥ h ( n ), and consequently lg g ( m ) ≥ lg h ( n ). If m ≤ ( r + o (1)) n 2 / lg n for some constant r , then lg m ≤ (2 + o (1)) lg n , and thus (lg(3) / 2 − o (1)) n 2 ≤ lg h ( n ) ≤ lg g ( m ) ≤ (1 + o (1)) m · lg m ≤ (2 r + o (1)) n 2 , from where r ≥ lg (3) / 4; that is, m ≥ ( lg(3) 4 − o (1)) n 2 / lg n . 4.3 Monotone F orm ulas The pro of of Prop osition 2 exploits the fact that idealized BV A reenco des distinct simple 2-CNF form ulas in to distinct enco dings. T o get a low er b ound for arbitrary reenco ding metho ds, whic h ma y not ha v e this prop ert y , w e fo cus on monotone 2-CNF form ulas: Prop osition 3. Ther e is a monotone 2-CNF formula with n variables whose smal lest 2-CNF enc o ding has at le ast ( 1 4 − o (1)) n 2 lg n clauses. In fact, idealized BV A can match this lo w er b ound: Theorem 7 (F ormal v ersion of Theorem 3 ) . F or every monotone 2-CNF formula ϕ on n variables, ther e is a 2-CNF formula ϕ ′ such that ϕ ∼ ∼ ▷ BV A ∗ ϕ ′ and | ϕ ′ | ≤ 1 4 + o (1) n 2 lg n . This strengthens a result of Sub ercaseaux [ 24 , Theorem 10], who prov ed that every monotone 2-CNF form ula has a 2-CNF enco ding with O ( n 2 / lg n ) clauses. Allen [ 2 ] prov ed the remark able result that almost all 2-CNF functions are monotone after p ossibly negating some input v ariables (i.e., unate ). T ogether with Theorem 7 , this implies that almost every 2-CNF function on n v ariables has a 2-CNF enco ding with at most ( 1 4 + o (1)) n 2 / lg n clauses, matc hing the low er b ound from Prop osition 3 . On this basis, w e conjecture that this b ound holds for al l 2-CNF functions, which would imply that there is a reenco ding metho d impro ving idealized BV A with simplification: Conjecture 1. Every 2-CNF formula ϕ on n variables has a 2-CNF enc o ding ϕ ′ such that | ϕ ′ | ≤ ( 1 4 + o (1)) n 2 lg n . 5 Enco dings for A tMostOne The previous section sho w ed that idealized BV A p erforms well from the p ersp ectiv e of worst-case analysis. But man y 2-CNF formulas that arise in practice are highly structured and can therefore b e enco ded with far fewer than Θ( n 2 / lg n ) clauses. Our framework also allows us to analyze the 11 op eration of idealized BV A on sp ecific 2-CNF formulas. W e demonstrate this b y studying enco dings of the most structured 2-CNF form ula of all, one which also frequently arises in practice, namely the at-most-one constraint: A tMostOne ( x 1 , . . . , x n ) : = ^ 1 ≤ i n , a truncation thereof. Within eac h blo ck B i , for eac h pair of v ertices { u, v } ∈ B i 2 create in R an auxiliary vertex z { u,v } , and create edges ( u, z { u,v } ) and ( v , z { u,v } ). No w, let r = ⌊ log 3 n − 3 log 3 log 3 n ⌋ , and partition as w ell V ( G ) in to parts P 1 , . . . , P ⌈ n/r ⌉ of size at most r ; sp ecifically , let P i = { v ( i − 1) · r +1 , . . . , v i · r } or, if i · r > n , a truncation thereof. F or eac h part P i and edge ( u, v ) ∈ E ( G ) ∩ ( P i × P i ), create in R a directed edge ( u, v ) with p ′ ( u, v ) = p ( u, v ). No w, for each part P i and each function S : P i → {− , 0 , + } , create in R an auxiliary vertex y S , and create a directed edge ( y S , v ) with p ′ ( y S , v ) = − for every v ∈ P i satisfying S ( v ) = − , and create a directed edge ( y S , v ) with p ′ ( y S , v ) = + for ev ery v ∈ P i satisfying S ( v ) = +. Giv en 22 a vertex v ∈ V ( G ), let N ± ( v ) = { w ∈ V ( G ) | ( v , w ) ∈ E ( G ) and p ( v , w ) = ±} . Then, for each S : P i → {− , 0 , + } , let A ( S ) := { v ∈ P j | j < i, N − ( v ) ∩ P i = S − 1 ( − ) , and N + ( v ) ∩ P i = S − 1 (+) } . Finally , for each ∈ [ ⌈ n/q ⌉ ], let A ℓ ( S ) := A ( S ) ∩ B ℓ , and let a 1 , . . . , a k b e the elements of A ℓ ( S ) in an arbitrary order. Then, create in R directed edges ( z { a 2 j − 1 ,a 2 j } , y S ) for j ∈ [ ⌊ k / 2 ⌋ ], and if k is o dd, create the directed edge ( a k , y S ). If R con tains an y auxiliary vertices not b elonging to a v alid w alk, then delete them and their incident edges. Correctness. Now, w e claim that R is a strict rectifier net w ork for ( G, p ). Supp ose ( u, v ) ∈ E ( G ). If u, v ∈ P i , then R con tains the edge ( u, v ) with p ′ ( u, v ) = p ( u, v ). Otherwise, let i, j ∈ [ ⌈ n/r ⌉ ] b e such that u ∈ P i and v ∈ P j ; then, i < j b y the topological ordering. Let S : P j → {− , 0 , + } b e such that u ∈ A ( S ); suc h an S is uniquely defined by the conditions S − 1 ( − ) = N − ( u ) ∩ P j and S − 1 (+) = N + ( u ) ∩ P j . Then, either there is a unique u ′ suc h that ( z { u,u ′ } , y S ) is a directed edge, in which case we hav e the v alid w alk ( u, z { u,u ′ } , y S , v ), or w e hav e the directed edge ( u, y S ), in which case we ha v e the v alid w alk ( u, y S , v ). Also, p ′ ( y S , v ) = p ( u, v ) by our c hoice of S . Th us, if ( u, v ) ∈ E ( G ), then there is a v alid w alk π from u to v with p ′ ( π ) = p ( u, v ) in R . Con v ersely , supp ose that R con tains a v alid walk π from u to v for some u, v ∈ B . Again, let i, j ∈ [ ⌈ n/r ⌉ ] b e such that u ∈ P i and v ∈ P j . If i = j , then the only possibility for the v alid walk is ( u, v ), whic h only happ ens if ( u, v ) ∈ E ( G ) and p ( u, v ) = p ′ ( u, v ) = p ′ ( π ). Otherwise, i < j , and the v alid w alk is either of the form ( u, z { u,u ′ } , y S , v ) or of the form ( u, y S , v ) for some u ′ ∈ B \ { u } and S : P j → {− , 0 , + } ; furthermore, it is imp ossible to hav e b oth v alid walks ( u, z { u,u ′ } , y S , v ) and ( u, y S , v ). W e mu st ha v e u ∈ A ( S ), so ( u, v ) ∈ E ( G ) with p ( u, v ) = S ( v ) = p ′ ( y S , v ) = p ′ ( π ). Th us, w e ha v e ( u, v ) ∈ E ( G ) if and only if there is a v alid walk π from u to v in R suc h that p ′ ( π ) = p ( u, v ), in whic h case π is the unique v alid walk b et w een u and v . Therefore, R is an SPRN realizing ( G, p ). Coun ting the edges. W e now sho w that R has at most lg(3) 4 + o (1) n 2 lg n edges. The num b er of edges of the form ( u, z { u,v } ) is at most ⌈ n/q ⌉ · q 2 ≤ n q + 1 · q 2 2 = nq 2 + q 2 2 ≤ n 2 2 log 2 3 n + n 2 2 log 4 3 n = o ( n 2 / lg n ) . The n um b er of edges of the form ( u, v ) for some i ∈ [ ⌈ n/r ⌉ ] and u, v ∈ P i is at most ⌈ n/r ⌉ · r 2 ≤ nr 2 + r 2 2 ≤ n log 3 n + log 2 3 n 2 = o ( n 2 / lg n ) . The num b er of edges of the form ( y S , v ) for some i ∈ [ ⌈ n/r ⌉ ], S : P i → {− , 0 , + } , and v ∈ S − 1 ( {− , + } ) is at most ⌈ n/r ⌉ · 3 r · r ≤ n r + 1 · n log 3 3 n · r = n 2 log 3 3 n + nr log 3 3 n = o ( n 2 / lg n ) . W e no w coun t the num b er of edges of the form ( z { a 2 j − 1 ,a 2 j } , y S ) for some i ∈ [ ⌈ n/r ⌉ ], S : P i → {− , 0 , + } , a 2 j − 1 , a 2 j ∈ A ℓ ( S ), and ∈ [ ⌈ n/q ⌉ ]. Fix i ∈ [ ⌈ n/r ⌉ ] and some S : P i → {− , 0 , + } . Then, for every ∈ [ ⌈ n/q ⌉ ] there are ⌊| A ℓ ( S ) | / 2 ⌋ edges of the form ( z { a 2 j − 1 ,a 2 j } , y S ). Since A ( S ) = S ℓ ∈ [ ⌈ n/q ⌉ ] A ℓ ( S ), for ev ery S w e ha v e P ℓ ∈ [ ⌈ n/q ⌉ ] ⌊| A ℓ ( S ) | / 2 ⌋ ≤ | A ( S ) | / 2 . No w, note that v can only 23 b elong to A ( S ), for S : P i → {− , 0 , + } , if v ∈ P j for some j < i ; furthermore, if j < i , then v ∈ A ( S ) for a unique S : P i → {− , 0 , + } . Th us, b y exc hanging summations, w e ha v e 1 2 X i ∈ [ ⌈ n/r ⌉ ] S : P i →{− , 0 , + } | A ( S ) | = 1 2 X v ∈ V ( G ) X i ∈ [ ⌈ n/r ⌉ ] S : P i →{− , 0 , + } 1 v ∈ A ( S ) = 1 2 X i ∈ [ ⌈ n/r ⌉ ] X j n , a truncation thereof. Within eac h blo c k B i , for each pair of vertices { u, v } ∈ B i 2 create in R an auxiliary vertex z { u,v } , and create edges ( u, z { u,v } ) and ( v , z { u,v } ). No w, let r = ⌊ lg n − 3 lg lg n ⌋ , and partition as well V ( G ) in to parts P 1 , . . . , P ⌈ n/r ⌉ of size at most r ; sp ecifically , let P i = { v ( i − 1) · r +1 , . . . , v i · q } or, if i · r > n , a truncation thereof. F or eac h part P i and edge ( u, v ) ∈ E ( G ) ∩ ( P i × P i ), create in R a directed edge ( u, v ) with p ′ ( u, v ) = p ( u, v ) = − . No w, for eac h part P i and eac h subset S ⊆ P i , create in R an auxiliary v ertex y S , and create a directed edge ( y S , v ) with p ′ ( y S , v ) = − for eac h v ∈ S . Then, for eac h S ⊆ P i , let A ( S ) := { v ∈ P j | j < i and N G ( v ) ∩ P i = S } . Finally , for eac h ∈ [ ⌈ n/q ⌉ ], let A ℓ ( S ) := A ( S ) ∩ B ℓ , and let a 1 , . . . , a k b e the elemen ts of A ℓ ( S ) in an arbitrary order. Then, create in R directed edges ( z { a 2 j − 1 ,a 2 j } , y S ) for j ∈ [ ⌊ k / 2 ⌋ ], and if k is o dd, create the directed edge ( a k , y S ). If R con tains an y auxiliary v ertices not b elonging to a v alid w alk, then delete them and their incident edges. The pro of that the construction is correct and the computation of the num b er of edges is v ery similar to the pro of of Theorem 6 . Theorem 10 (F ormal version of Theorem 1 ) . F or every 2-CNF formula ϕ on n variables, ther e is a 2-CNF formula ϕ ′ such that ϕ ∼ ∼ ▷ BV A ∗ ϕ ′ and | ϕ ′ | ≤ (1 + o (1)) n 2 lg n . Pr o of. Let the v ariables of ϕ b e x 1 , . . . , x n . W e can write ϕ = ϕ 1 ∧ ϕ 2 ∧ ϕ 3 ∧ ϕ 4 , where ϕ 1 := { ( x i ∨ x j ) | i < j and ( x i ∨ x j ) ∈ ϕ } ϕ 2 := { ( x i ∨ x j ) | i < j and ( x i ∨ x j ) ∈ ϕ } ϕ 3 := { ( x i ∨ x j ) | i < j and ( x i ∨ x j ) ∈ ϕ } ϕ 4 := { ( x i ∨ x j ) | i < j and ( x i ∨ x j ) ∈ ϕ } . It suffices to show that, for eac h i ∈ [4], there is a 2-CNF formula ϕ ′ i suc h that ϕ i ∼ ∼ ▷ BV A ∗ ϕ ′ i and | ϕ ′ i | ≤ 1 4 + o (1) n 2 lg n . By Theorem 7 , this is true for i = 1, and the case i = 4 is the same after negating the v ariables. A nearly identical construction to that of Theorem 7 (with p ′ ( u, v ) = + for eac h v ∈ V ( G ) rather than p ′ ( u, v ) = − ) w orks for i = 2, and the case i = 3 is the same after negating the v ariables. Lemma 15. The numb er of 2-CNF formulas on n variables is 4 n 2 − n . Pr o of. With n v ariables, there are 2 n literals. A clause consists of a pair of literals, the num b er of whic h is 2 n 2 = 2 n 2 − n . But, w e do not allow formulas to con tain tautologous clauses (i.e., those of the form ( x i ∨ x i )), the n um b er of which is n . Th us, there are 2 n 2 − 2 n clauses to c hoose from when constructing a 2-CNF formula, and any subset of these constitutes a 2-CNF formula, so the n um ber of 2-CNF form ulas on n v ariables is 2 2 n 2 − 2 n = 4 n 2 − n . Prop osition 4. Ther e is a 2-CNF formula ϕ on n variables such that, for every ϕ ′ with ϕ ∼ ∼ ▷ BV A ∗ ϕ ′ , we have | ϕ ′ | ≥ (1 − o (1)) n 2 lg n . 25 Pr o of. Let g ( m ) b e the n um ber of 2-CNF formulas with at most m clauses, and let h ( n ) b e the n um ber of 2-CNF formulas on n v ariables. By Lemmas 2 and 15 , lg g ( m ) ≤ (1 + o (1)) m · lg m and lg h ( n ) ≥ (2 − o (1)) n 2 . If ϕ ∼ ∼ ▷ BV A ∗ ϕ ′ , then p erforming v ariable elimination (in the Da vis–Putnam sense) on the auxiliary v ariables in ϕ ′ yields ϕ . In particular, ϕ ′ has enough information to uniquely reconstruct ϕ . Th us, if for ev ery 2-CNF form ula ϕ on n v ariables, there is a 2-CNF form ula ϕ ′ with at most m clauses suc h that ϕ ∼ ∼ ▷ BV A ∗ ϕ ′ , then g ( m ) ≥ h ( n ), and consequently lg g ( m ) ≥ lg h ( n ). If m ≤ ( r + o (1)) n 2 / lg n for some constant r , then lg m ≤ (2 + o (1)) lg n , and thus (2 − o (1)) n 2 ≤ lg h ( n ) ≤ lg g ( m ) ≤ (1 + o (1)) m · lg m ≤ (2 r + o (1)) n 2 , from where r ≥ 1; that is, m ≥ (1 − o (1)) n 2 / lg n . C Pro ofs from Section 5 Lemma 4. L et R b e an SPRN with m e dges r e alizing a diagr am G , and let y b e an auxiliary vertex. If the in-de gr e e or out-de gr e e of y is 1, then ther e is an SPRN r e alizing G with at most m − 1 e dges. Pr o of. W rite R = ( B , A, E , p ). Suppose first that y has in-degree 1. Let ( y ′ , y ) b e the unique incoming edge to y . Let R ′ = ( B , A \ { y } , E ′ , p ′ ) b e defined b y E ′ = ( E \ { e ∈ E | y ∈ e } ) ∪ { ( y ′ , z ) | ( y , z ) ∈ E } p ′ ( u, v ) = ( p ( y , v ) if u = y ′ and v ∈ B p ( u, v ) otherwise . Then, R ′ is an SPRN realizing G and has at most m − 1 edges. On the other hand, if y has out-degree 1, then let ( y , y ′ ) b e the unique outgoing edge from y . Let R ′ = ( B , A \ { y } , E ′ , p ′ ) b e defined b y E ′ = ( E \ { e ∈ E | y ∈ e } ) ∪ { ( z , y ′ ) | ( z , y ) ∈ E } p ′ ( u, v ) = ( p ( y , y ′ ) if v = y ′ ∈ B and ( u, y ) ∈ E p ( u, v ) otherwise . Then, R ′ is an SPRN realizing G and has at most m − 1 edges. Lemma 6. L et R b e an SPRN r e alizing K n with m e dges for some n ≥ 4 , and let x b e a b ase vertex. If the total de gr e e of x is exactly 1, then ther e is an SPRN r e alizing K n with at most m − 1 e dges. Pr o of. Let y b e the unique vertex adjacent to x in R . Then, y m ust b e an auxiliary vertex, or else there w ould b e no v alid w alk b et ween x and V ( K n ) \ { x, y } . Without loss of generality , supp ose ( x, y ) is the edge connecting these tw o vertices in R . W e claim that there is no base v ariable x ′ ∈ V ( K n ) \ { x } with a v alid walk from x ′ to y . Indeed, there is a v alid w alk ( x, y , . . . , x ′ ), so if there were a v alid walk ( x ′ , . . . , y ), we could construct the v alid walk ( x ′ , . . . , y , . . . , x ′ ), contradicting our assumption that R is an SPRN realizing K n . Since R is strict, it follo ws that y has in-degree exactly 1. By Lemma 4 , there is an SPRN realizing K n with at most m − 1 edges. 26 C.1 Ho w BV A Reenco des AtMostOne in Practice Here, w e pro v e that, using the heuristics for p erforming BV A steps describ ed in [ 20 ], BV A alw a ys reenco des AtMostOne ( x 1 , . . . , x n ) in to a form ula with 3 n − 6 clauses for n ≥ 3. T o pro v e this, w e must sp ecify ho w a BV A step is p erformed in practice. F ollowing the graph-theoretic lens w e ha v e been using, w e describ e the algorithm as it op erates on the diagram corresp onding to a simple 2-CNF form ula. Given a diagram G = ( V , E ) and v ∈ V , let N G ( v ) = { u | ( v , u ) ∈ E } ∪ { u | { v , u } ∈ E } . Then, a set of clauses of the form C D corresp onds in G to a complete bipartite subgraph ( L, R ), where R ⊆ N ( v ) for all v ∈ L ; we call this a biclique . Algorithm 1 is the algorithm for choosing a BV A step adapted from the original BV A pap er [ 20 ]. The algorithm, as we ha ve presen ted it, is nondeterministic since there ma y b e m ultiple c hoices of v in 1.1 and m ultiple iteration orders in 1.7 . Our result will apply to all p ossible executions of the algorithm, which means that it also applies to SBV A [ 10 ], which adds tie-breaking heuristics to the original BV A algorithm but still adheres to the sp ecification of Algorithm 1 . Algorithm 1: Heuristic-BV A-Step ( G ) Input: A diagram G = ( V , E ) Output: A biclique ( L, R ) found by one BV A step (or ⊥ if no improv ement) 1.1 c ho ose v ∈ V such that | N G ( v ) | is maxim um 1.2 L ← { v } // left side 1.3 R ← N G ( v ) // right side (current common neighborho od) 1.4 Q ← | L | · | R | − | L | − | R | // current biclique quality 1.5 while true do 1.6 ( v ⋆ , R ⋆ , Q ⋆ ) ← ( ⊥ , R, Q ) 1.7 foreac h w ∈ V \ L do 1.8 R w ← R ∩ N G ( w ) // new right side if w is added to L 1.9 Q w ← ( | L | + 1) · | R w | − ( | L | + 1) − | R w | // quality of ( L ∪ { w } , R w ) 1.10 if Q w > Q ⋆ then 1.11 ( v ⋆ , R ⋆ , Q ⋆ ) ← ( w , R w , Q w ) 1.12 if v ⋆ = ⊥ then 1.13 break // no vertex impro v es the quality // Accept the b est candidate and up date ( L, R ) 1.14 ( L, R, Q ) ← ( L ∪ { v ⋆ } , R ⋆ , Q ⋆ ) 1.15 if Q > 0 then 1.16 return ( L, R ) // biclique used for a BV A substitution 1.17 else 1.18 return ⊥ // no profitable biclique found Theorem 11. If the BV A algorithm, e ach step of which is chosen ac c or ding to Algorithm 1 , is applie d to the formula A tMostOne ( x 1 , . . . , x n ) for some n ≥ 3 , then the r esulting enc o ding has 3 n − 6 clauses. Pr o of. Note that K n is the diagram corresp onding to A tMostOne ( x 1 , . . . , x n ) for some n ≥ 3, so w e analyze how Algorithm 1 op erates on K n . F or n ≥ 3, let f ( n ) b e the n um b er of edges in the diagram resulting from repeatedly p erforming BV A steps according to Algorithm 1 starting with K n . The pro of is by induction on n . The base cases are when n ∈ { 3 , 4 } , in which case Algorithm 1 returns ⊥ . Th us, BV A do es nothing in these cases, so f ( n ) = n 2 = 3 n − 6. 27 No w supp ose that n ≥ 5. Throughout Algorithm 1 , w e ha ve | R | = n − | L | , so Q = | L | · ( n − | L | ) − | L | − ( n − | L | ) = n · | L | − | L | 2 − n . Algorithm 1 increments | L | so long as Q strictly increases, whic h happens until | L | = ⌊ n/ 2 ⌋ and | R | = n − | L | = ⌈ n/ 2 ⌉ . Without loss of generality , L = { x 1 , . . . , x ⌊ n/ 2 ⌋ } and R = { x ⌊ n/ 2 ⌋ +1 , . . . , x n } . Th us, the BV A step replaces the clauses { ( x i ∨ x j ) | i ∈ [ ⌊ n/ 2 ⌋ ] , j ∈ [ ⌊ n/ 2 ⌋ + 1 , n ] } b y the clauses { ( x i ∨ y ) | i ∈ [ ⌊ n/ 2 ⌋ ] } ∪ { ( y ∨ x j ) | j ∈ [ ⌊ n/ 2 ⌋ + 1 , n ] } . The resulting formula ϕ ( x 1 , . . . , x n , y ) can b e written as ϕ 1 ∧ ϕ 2 , where ϕ 1 := A tMostOne ( x 1 , . . . , x ⌊ n/ 2 ⌋ , y ) ϕ 2 := A tMostOne ( y , x ⌊ n/ 2 ⌋ +1 , . . . , x n ) . No w, w e claim that the next biclique found b y Algorithm 1 (if there is one) m ust b e en tirely within ϕ 1 or ϕ 2 . Indeed, for Algorithm 1 to not return ⊥ , w e must hav e | L | ≥ 2. If | L | ≥ 2, then x i ∈ L for some i ∈ [ n ]. If i ≤ [ ⌊ n/ 2 ⌋ ], then the biclique is entirely contained within ϕ 1 ; otherwise, it is en tirely con tained within ϕ 2 . Th us, f ( n ) = f ([ ⌊ n/ 2 ⌋ ] + 1) + f ([ ⌈ n/ 2 ⌉ ] + 1). The solution to this recurrence is f ( n ) = 3 n − 6, as desired. D Exp erimen tal Details Hardw are. W e ran all exp erimen ts on a MacBo ok Pro p ersonal computer, with 16 GB of RAM, an Apple M5 chip, and running macOS T aho e 26.2; all exp erimen ts were single-threaded. Co de. Our co de is av ailable at https://github.com/bsubercaseaux/BicliqueVA Instances. The form ulas for indep enden t sets of random graphs are created as follo ws. First, a graph G ∼ G ( n, p ) is sampled. Then, for eac h vertex v , out of n v ertices, is represen ted by a v ariable x v , and th us for every edge { u, v } w e add a clause ( x u ∨ x v ). Then, a cardinalit y constraint P v x v ≥ k is added, for which we use the sequential counter as implemen ted in PySA T [ 13 ]. Since the exp ected indep endence num b er of a G ( n, 1 2 ) is well-concen trated around 2 lg n , we consider b oth a satisfiable regime, for which we set k := 1 + ⌊ 1 . 2 lg n ⌋ , as well as an unsatisfiable regime for whic h w e set k := ⌊ 30 lg n ⌋ in order to keep the runtimes manageable (as k approac hes the critical threshold, the instances b ecome harder to solve). Since randomness is inv olved, all our results, b oth for clauses, v ariables, and runtimes, are av eraged ov er 5 indep enden t trials. The concrete num b ers corresp onding to the bar plots in Section 6 , whic h are for the satisfiable regime, are presented in T able 3 . On the other hand, T able 4 presents data on the unsatisfiable regime. 28 T able 3: Experimental results for the SA T regime, summarizing v ariables (b oth base and auxiliary), clauses, and computational time across differen t graph sizes. The b est of each group is highlighted in green, except for the num b er of v ariables, in which we do not consider the original enco ding. n Metho d # V ars # Clauses Reenc. Time (ms) Solv e Time (ms) T otal (ms) 600 Original 600 89671 — 364.60 364.60 BiV A 3713 44190 37.63 319.82 357.45 BV A 4847 32404 273.99 333.87 607.86 facto r 4551 32583 134.29 467.65 601.94 BiV A + BV A 6463 36719 99.39 308.18 407.57 BiV A + factor 6459 36700 66.52 310.99 377.51 1200 Original 1200 359732 — 1641.02 1641.02 BiV A 12582 156200 132.19 799.70 931.89 BV A 15862 117768 2433.71 439.00 2872.71 facto r 14731 118606 964.25 876.73 1840.98 BiV A + BV A 21870 128923 495.17 484.75 979.92 BiV A + factor 22028 128976 272.41 566.34 838.75 1800 Original 1800 809413 — 3684.32 3684.32 BiV A 18899 322931 306.63 827.77 1134.40 BV A 32074 251632 11811.92 362.26 12174.19 facto r 29706 253436 3244.75 352.23 3596.98 BiV A + BV A 39703 260504 1743.41 727.06 2470.47 BiV A + factor 39900 260705 754.32 430.94 1185.27 2400 Original 2400 1439527 — 8617.10 8617.10 BiV A 25200 548671 535.17 2599.50 3134.67 BV A 53234 431841 30201.91 1796.68 31998.60 facto r 48955 435083 7618.12 1384.92 9003.04 BiV A + BV A 61290 432518 5002.72 1901.01 6903.74 BiV A + factor 61463 432747 1546.71 1410.66 2957.37 3000 Original 3000 2249189 — 15724.21 15724.21 BiV A 54359 830189 867.49 2312.35 3179.84 BV A 78895 657162 63638.74 1526.34 65165.08 facto r 72535 662432 15205.77 1908.56 17114.34 BiV A + BV A 101018 668154 8617.16 849.28 9466.45 BiV A + factor 103489 669987 2398.41 570.11 2968.52 29 T able 4: Exp erimen tal results for the UNSA T regime, summarizing v ariables (b oth base and auxiliary), clauses, and computational time across different graph sizes. The b est of eac h group is highligh ted in green, except for the num b er of v ariables, in which w e do not consider the original enco ding. n Metho d # V ars # Clauses Reenc. Time (ms) Solv e Time (ms) T otal (ms) 500 Original 500 62255 — 129.47 129.47 BiV A 3078 31958 26.33 73.86 100.20 BV A 3572 23103 157.26 94.63 251.88 facto r 3379 23241 81.51 95.35 176.86 BiV A + BV A 4994 26825 65.48 74.49 139.96 BiV A + factor 4980 26834 43.59 74.80 118.39 1000 Original 1000 249714 — 2144.22 2144.22 BiV A 10408 113808 95.34 1670.44 1765.78 BV A 11576 83811 1329.48 1649.19 2978.67 facto r 10808 84326 568.98 1592.09 2161.07 BiV A + BV A 16854 94393 305.18 1686.26 1991.44 BiV A + factor 17019 94443 184.62 1679.89 1864.51 1500 Original 1500 562196 — 9075.38 9075.38 BiV A 15747 232248 213.32 7317.21 7530.53 BV A 23370 178873 5751.98 7535.59 13287.56 facto r 21608 180030 1944.58 7573.61 9518.19 BiV A + BV A 30273 189617 1003.89 7869.11 8873.00 BiV A + factor 30446 189677 479.09 7103.80 7582.88 2000 Original 2000 999401 — 69761.13 69761.13 BiV A 20982 392056 396.73 58099.24 58495.96 BV A 38593 306556 17114.92 63503.85 80618.77 facto r 35646 308821 4477.50 59651.54 64129.04 BiV A + BV A 46496 313607 2721.44 60768.45 63489.89 BiV A + factor 46671 313805 1013.76 57190.54 58204.30 30
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment