Girth Approximations in the CONGEST Model
This paper advances the state of the art in girth approximation within the CONGEST model. Manoharan and Ramachandran [PODC '24] provided the first significant improvement in girth approximation in over a decade. We build on this momentum and make pro…
Authors: Shiri Chechik, Gur Lifshitz, Doron Mukhtar
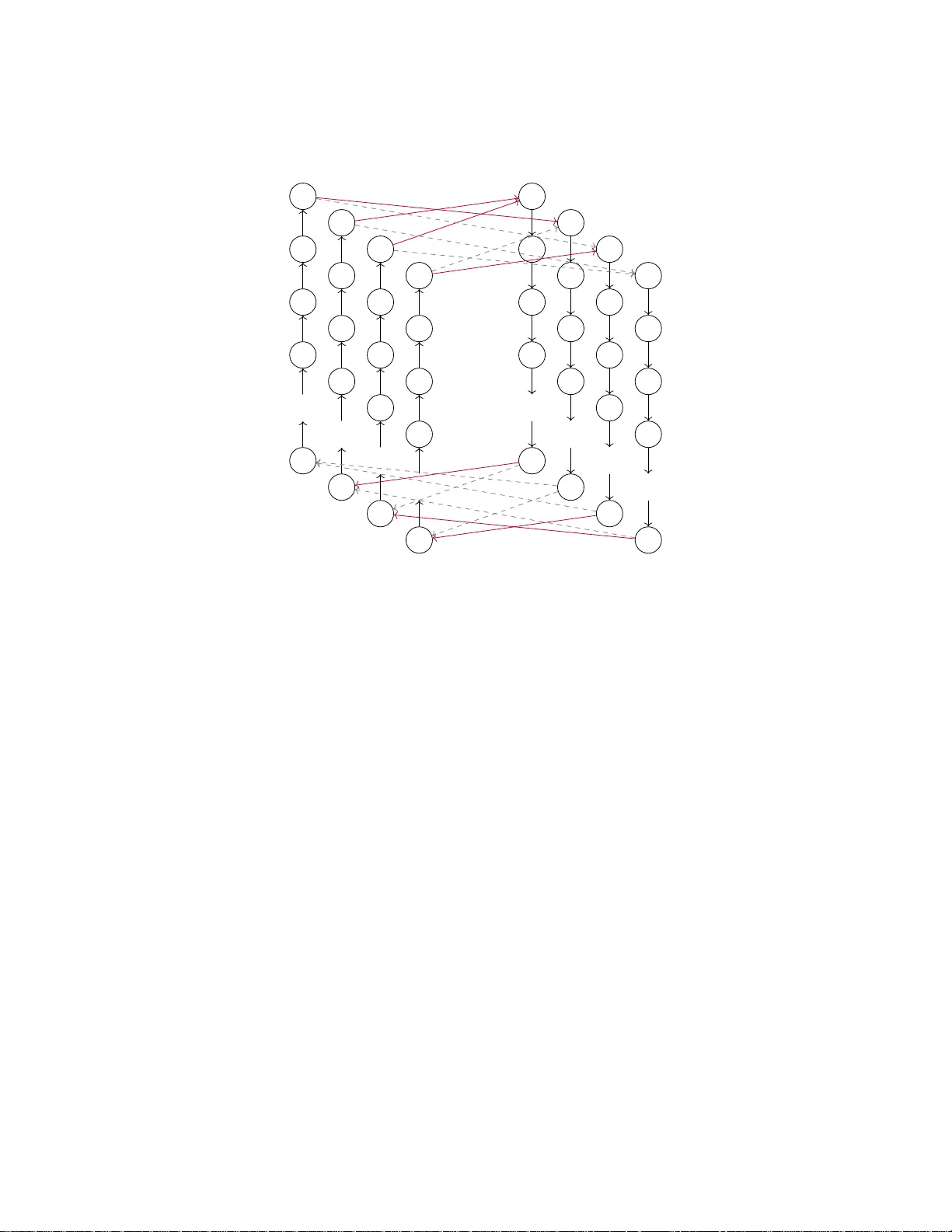
Girth Appro ximations in the CONGEST Mo del Shiri Chec hik ∗ Gur Lifshitz ∗ Doron Mukh tar ∗ Abstract This pap er adv ances the state of the art in girth approximation within the CONGEST mo del. Manoharan and Ramac handran [ PODC ’24 ] pro vided the first significant impro vemen t in girth approximation in o ver a decade. W e build on this momen tum and mak e progress on all fron ts: w e pro vide a unified family of algorithms yielding girth approximation–round tradeoffs for undirected netw orks; w e obtain impro ved b ounds for directed netw orks; and w e establish b etter low er b ounds for directed and undirected weigh ted net works. T ogether, these results substan tially narrow the remaining complexity gaps across all settings. Sp ecifically , for netw orks with n nodes and hop-diameter D , we show that one can compute, with high probabilit y: (1) An f -appro ximation for un weigh ted undirected girth in ˜ O ( n 1 /f + D ) rounds, for every constan t integer f > 2. (2) A (2 k − 1 + o (1))-approximation for w eighted undirected girth in ˜ O ( n ( k +1) / (2 k +1) + D ) rounds, for ev ery constant integer k > 1. (3) A 2-approximation for directed unw eighted girth, and a (2 + ε )-appro ximation for directed w eighted girth, b oth in ˜ O ( n 2 / 3 + D ) rounds. W e also pro ve new lo wer b ounds for directed netw orks and for undirected weigh ted net works: for ev ery integer k > 2 and ε > 0, assuming the Erd˝ os-Simono vits’ even cycle conjecture (and unconditionally for k ∈ { 3 , 4 , 6 } ), any ( k − ε )-appro ximation for the girth requires ˜ Ω( n k/ (2 k − 1) ) rounds, ev en when D = O (log n ). Keywor ds : girth appro ximation, distributed algorithms. 1 In tro duction Researc h in distributed computing has primarily fo cused on designing algorithms for computing imp ortan t prop erties of the netw orks on whic h they op erate. One such prop ert y is the girth of the netw ork, the length of its shortest cycle, or more generally , the weigh t of its lightest cycle (if the netw ork is weigh ted). Being a fundamental prop erty , there is a natural need to estimate it efficien tly . This, how ev er, is far from b eing a trivial task, esp ecially in mo dels that heavily restrict the comm unication b et ween the no des. In this pap er, we fo cus on the CONGEST mo del [23] of distributed computing. According to it, we represent a communication netw ork b y an n -no de graph G , such that eac h no de corresp onds to a device and each edge to a bidirectional communication c hannel. The netw ork may b e w eigh ted ∗ T el Aviv Universit y , Israel ( shiri.chechik@gmail.com , gur.lifshitz@gmail.com and doron.muk@gmail.com ). 1 and/or directed. In this case, we assume that each no de initially knows the w eights and/or the directions of its incident edges, and that this information do es not affect communication in any w ay . Computation pro ceeds in discrete rounds, following a predefined algorithm designed to solve a sp ecific task. In eac h round, every node receives the messages that w ere previously sen t to it, p erforms a lo cal computation, and then sends O (log n )-bit (p ossibly different) messages to its neigh b ors. W e also assume that each no de has the ability to flip coins and use their outcomes during the computation. An algorithm that utilizes this ability is called randomized; otherwise, it is deterministic. A randomized algorithm is said to succeed with high probability if the probability of failure (tak en ov er all coin flips) is at most 1 /n c for an arbitrary constan t c ≥ 1. Our goal is to design an algorithm that enables each no de to compute a go o d approximation of the girth in as few rounds as p ossible. Prior work has ac hieved steady progress on this and related problems, yielding b oth exact and approximation algorithms, which we briefly review. Un w eighted Netw orks F or unw eigh ted netw orks, whether directed or not, we can compute the girth exactly in O ( n ) rounds using a deterministic all-pairs shortest paths algorithm [15, 19, 20]. When the edges are directed, this b ound is nearly optimal, as ˜ Ω( n ) rounds are required for any constan t approximation factor b elo w 2, even when the netw ork’s hop-diameter D is constant [20]. In contrast, for undirected netw orks, the tightness of this result remains unclear, as the b est kno wn lo wer b ound for an y such approximation factor is ˜ Ω( √ n + D ) [13]. The landscap e of girth approximation in suc h netw orks is more complicated. F or directed net works, Manoharan and Ramachandran [21] presented an algorithm that, with high probability , computes a 2-approximation in ˜ O ( n 4 / 5 + D ) rounds, and established that ˜ Ω( √ n + D ) rounds are necessary for any constan t approximation factor at least 2. F or undirected netw orks, they show ed [20, 21] that (2 − 1 /g )-appro ximation (where g is the netw ork’s girth) can b e computed with high probabilit y in ˜ O ( √ n + D ) rounds, while ˜ Ω( n 1 / ( f +1) + D ) rounds are required for an y constant appro ximation factor less than f + 0 . 5 (for an y fixed integer f > 1). W eigh ted Net w orks F or netw orks with p ositiv e integer w eights bounded b y a p olynomial in n , the girth can b e computed exactly in ˜ O ( n ) rounds with high probabilit y , regardless of whether the net work is directed or not [20, 2]. Moreov er, [21] sho ws that for any constant ε > 0, a (2 + ε )- appro ximation can b e obtained with high probabilit y in ˜ O ( n 4 / 5 + D ) rounds for directed net works and in ˜ O ( n 2 / 3 + D ) rounds for undirected netw orks. On the lo wer-bound side, it is known [20, 21] that, indep enden t of edge orien tation, any constant-factor approximation b etter than 2 requires ˜ Ω( n ) rounds, while ac hieving a factor of 2 or more requires ˜ Ω( √ n + D ) rounds. Related W ork A closely related problem is the q -cycle detection, whic h asks to determine whether a giv en netw ork contains a cycle of length exactly q . Detecting undirected cycles of a fixed length q has a complexity of ˜ Θ( n ) for o dd q ≥ 5; for ev en q ≥ 4, the complexity lies b et ween ˜ Ω( √ n ) and ˜ O ( n 1 − 2 /q ) [10, 17, 12]. T riangles can b e detected in ˜ O ( n 1 / 3 ) rounds, even in directed net works [7, 20]. Detecting longer directed cycles, ho wev er, requires ˜ Ω( n ) rounds [20]. The girth problem has b een also studied in the Congested Clique mo del, where it can b e computed exactly in O ( n 0 . 157 ) 1 rounds for un weigh ted graphs [6], and approximated within an additiv e error of one in a constant n umber of rounds for undirected, unw eigh ted graphs [5]. 1 The actual running time is ˜ O ( n 1 − 2 /ω + ε ) where ω is the matrix m ultiplication exp onen t and ε > 0 is an arbitrarily small constant. 2 Although considerable progress has b een made on the girth problem, significan t gaps remain b et w een the known upp er and lo wer b ounds. In this work, w e make an imp ortan t step tow ard closing these gaps and obtain the follo wing results: Un w eighted Undirected Net works W e presen t new trade-offs betw een the round complex- it y and the approximation quality of the girth in unw eigh ted, undirected netw orks. Specifically , w e introduce a new algorithm that, with high probabilit y , computes an f -appro ximation to the girth in ˜ O ( f n 1 /f + f D ) rounds, for an y p ositiv e integer f . This nearly matches the low er b ound of ˜ Ω( n 1 / ( f +1) + D ) established in [21]. Previously , suc h trade-offs w ere b eliev e d to be imp ossible due to a published lo wer b ound, whic h w e hav e disco vered to b e fla wed: Manoharan and Ramac handran [21] claimed a stronger low er b ound of ˜ Ω( n 1 / 4 ) for any constant appro ximation factor α ≥ 2 . 5, which holds ev en for netw orks of diameter Θ(log n ). This claim app ears as Theorem 2.B in [21] building on a low er b ound for w eighted undirected net w orks established in the pro of of Theorem 3.A. Their approac h attempts to adapt the construction b y replacing each weigh ted edge with an unw eighted path of equal length. Ho wev er, this transformation ov erlo oks a critical consequence – it increases the netw ork’s diameter from O (log n ) to ˜ Ω( n 1 / 4 ), undermining the claim. W eigh ted Undirected Netw orks W e obtain new trade-offs for w eighted and undirected net works. More precisely , w e show that, with high probability , one can compute a (2 k − 1 + ε )- appro ximation of the girth in ˜ O ( kn ( k +1) / (2 k +1) + k D ) rounds, for an y integer k > 1 and constant ε > 0 (assuming p ositiv e in tegral edge weigh ts that are p olynomially b ounded in n ). Directed Netw orks W e devise new randomized algorithms that, in ˜ O ( n 2 / 3 + D ) rounds, com- pute a 2-appro ximation to the girth in directed un weigh ted netw orks, and a (2 + ε )-appro ximation (for an y constan t ε > 0) in directed weigh ted net works (again, with p ositiv e in tegral w eights p oly- nomially b ounded in n ). Thus, achieving a p olynomial improv emen t ov er the previously known upp er b ounds [21]. Lo w er Bounds W e complement our new upp er b ounds for directed netw orks and for undi- rected weigh ted netw orks with relative lo wer b ounds. F or every in teger k > 2 and ε > 0, we sho w that under the Erd˝ os-Simono vits’ even cycle conjecture [11] (and unconditionally for k ∈ { 3 , 4 , 6 } ), an y ( k − ε )-approximation algorithm for the girth in suc h net w orks requires ˜ Ω( n k/ (2 k − 1) ) rounds, ev en when the hop-diameter D is O (log n ). Our result yields a p olynomial impro vemen t ov er the previously known ˜ Ω( √ n ) low er b ound of [21], and for the first time makes the lo wer b ound explicitly depend on the appro ximation factor. T o illustrate the tightness of our results, observ e that for w eighted undirected net works our upp er and lo wer b ounds essentially match: for example, we obtain a (3 + o (1))-appro ximation in ˜ O ( n 3 / 5 + D ) rounds, while (3 − o (1))-approximation requires ˜ Ω( n 3 / 5 + D ) rounds. 2 Preliminaries All logarithms are base tw o, and all graphs are simple. F or a cycle C in a graph G , we denote by V ( C ) its set of v ertices, b y E ( C ) its set of edges and b y | C | the size of E ( C ). If G is weigh ted, w e let w G ( C ) denote the w eight of C in G . F or tw o vertices s and t in G , w e write d G ( s, t ) for the 3 distance from s to t in G . Giv en an additional non-negativ e in teger h , we let d h G ( s, t ) denote the h -hop distance from s to t in G . F or a cycle C and a vertex s in G , w e define the distance from s to C as d G ( s, C ) = min { d G ( s, v ) | v ∈ V ( C ) } . When the graph G is clear from context, we may omit the subscript G from an y of these notations. Throughout, we assume that each v ertex v in an n -no de comm unication net work is assigned a unique O (log n )-bit iden tifier I D ( v ), initially known only to v itself. If the netw ork is weigh ted, edge w eights are are assumed to lie in { 1 , 2 , ..., c · n k } for some constants c, k ≥ 1. W e also assume that eac h vertex initially knows the n umber of v ertices n , the maximum edge w eight W (when applicable) and a constan t-factor approximation of the net work’s hop-diameter D . (All these v alues can b e computed deterministically in O ( D ) rounds using standard techniques; see, e.g., [19, 23].) 3 Un w eigh ted Undirected Net w orks In this section, w e present new randomized algorithm for approximating the girth of un w eighted, undirected net works. 3.1 Ov erview W e fundamentally refine the girth approximation framework of [20, 21] b y replacing their uniform sampling approach with a multi-scale exploration scheme that systematically trav erses the net work from a progressively smaller set of sources. This new multi-la yered approach, combined with a careful analysis, enables us, for the first time, to obtain an appro ximation to the girth in muc h less than ˜ Θ( √ n ) rounds. W e now provide a high-level ov erview of the approac h. As in previous w ork, we leverage the fact that a partial BFS tree rooted at a vertex s allo ws one to approximate the girth g whenever the vertices of a shortest cycle C b elong to it. Concretely , the girth can b e estimated as the minimum of d ( s, x ) + d ( s, y ) + 1 o ver all crossing edges { x, y } , yielding an additiv e approximation with error at most 2 d ( s, C ). In tuitively , applying this pro cedure from sev eral sources and taking the minim um o ver all es- timates can lead to a smaller additiv e error, as we may hit a closer source. Manoharan and Ramac handran [20, 21] exploit this idea as follows. First, they construct partial BFS trees from all v ertices so that each one participates only in the trees of its O ( √ n ) closest vertices, and compute an initial estimate. (This can b e done in O ( √ n + D ) rounds by using a source-detection algorithm [19].) If the vertices of a shortest cycle C are fully contained in the partial BFS tree ro oted at some v ertex of C , then the girth is computed exactly . Otherwise, there must b e Ω( √ n ) v ertices whose disance from C is at most g / 2. Consequently , b y sampling each v ertex indep enden tly with probabilit y ˜ Θ( n − 1 / 2 ), one of them is selected with high probabilit y . Th us, construting full BFS trees from the sampled sources and estimating again yields a 2-approximation to the girth. This tak es another ˜ O ( √ n + D ) rounds, as there are ˜ O ( √ n ) sampled sources with high probabilit y . W e further extend this idea and show that one can trade approximation quality for running time b y p erforming several suc h estimations at differen t sampling scales. Sp ecifically , w e p erform f estimations, where in the i -th estimation vertices are sampled indep enden tly with probability ˜ Θ( n − i/f ), and partial BFS trees are constructed from the sampled sources such that eac h v ertex participates only in the trees of its ˜ O ( n 1 /f ) closest sampled sources. (This takes ˜ O ( n 1 /f + D ) rounds.) By generalizing the previous argumen t, we can show that for some i ∈ { 0 , ..., f − 1 } , there exists a sampled vertex x in this lay er whose distance to a shortest cycle C is at most ( g / 2) · i , and 4 suc h that x b elongs to the set Q i +1 ( v ) of the O ( n ( i +1) /f ) closest vertices of eac h v ertex v in C . Since eac h vertex is c hosen indep enden tly with probability p i = ˜ Θ( n − i/f ), it follows with high probabilit y that Q i +1 ( v ) contains p i · | Q i +1 ( v ) | = ˜ O ( n 1 /f ) sampled vertices for every v in C . Consequently , all v ertices of C participate in the partial BFS tree ro oted at x , yielding an ( i + 1) ≤ f appro ximation in ˜ O ( f · n 1 /f + f · D ) rounds. The rest of this section is organized as follows. W e first formalize and generalize the estimation pro cedure that app ears implicitly in earlier w ork. W e then show how to incorp orate this pro cedure in to a complete girth-approximation algorithm, thereby ac hieving the claimed tradeoff b et ween appro ximation quality and running time. 3.2 The Estimation Pro cedure Let G = ( V , E ) b e an undirected netw ork with girth g and diameter D . Let S ⊆ V be a set of sources and k b e a natural num b er. W e sa y that a v ertex v ∈ V is closer to u ∈ V than w ∈ V , if either d ( u, w ) > d ( u, v ), or d ( u, w ) = d ( u, v ) and I D ( w ) > I D ( v ). F or each v ertex v ∈ V , w e let U ( S , k , v ) b e the set of the k closest v ertices to v from S , or simply S if | S | ≤ k . W e say that a cycle C in G is co v ered by S , if there is a source s ∈ S that cov ers it, i.e., s ∈ U ( S, k , v ) for all v ∈ V ( C ). In this case, w e denote b y d ( S, C ) its distance from a closest source that cov ers it, that is, d ( S, C ) = min { d ( s, C ) | s ∈ S is a source that cov ers C } . Let C b e the set of all the shortest cycles in G that S cov ers. In the case where C is nonempty , we define d ( S ) to b e the smallest distance in G b et w een a shortest cycle and a source that cov ers it, i.e., d ( S ) = min { d ( S, C ) | C ∈ C } . Our goal in this section is to describ e a deterministic algorithm that computes in O ( k + D ) rounds a v alue M known to every vertex, such that M ≥ g alw ays holds, and 2 d ( S ) + g ≥ M holds when C is not empty . T o achiev e this, we use the source dete ction algorithm [19, Theorem 1.2], whic h allows us to do the following: Lemma 3.1. F or an unweighte d and undir e cte d network G = ( V , E ) with diameter D , a set of sour c es S ⊆ V and a natur al numb er k , p artial BFS tr e es r o ote d at the sour c es c an b e determin- istic al ly c onstructe d in O ( k + D ) r ounds, such that e ach vertex p articip ates only in the tr e es of its min( k , | S | ) closest sour c es. A t the end, e ach vertex v knows the set U ( S, k , v ) , along with the c orr esp onding distanc es d ( s, v ) and p ar ent p ointers p ( s, v ) , for al l s ∈ U ( S, k , v ) . W e now describ e the pro cedure for computing M , which internally uses the source detection algorithm of Lemma 3.1. Pro cedure Estimate( G, S, k ) Input: An undirected and unw eigh ted netw ork G = ( V , E ), a set of sources S ⊆ V and a natural num b er k , where each vertex initially kno ws k and whether it b elongs to S . 1 The v ertices run the source detection algorithm on ( G, S, k ). 2 Eac h vertex v broadcasts the set { ( s, d ( s, v ) , p ( s, v )) | s ∈ U ( S, k , v ) } to its neigh b ors. 3 Ev ery vertex y performs the following internal computation: 4 M y ← ∞ 5 foreac h neighbor x a nd source s ∈ U ( S, k, y ) ∩ U ( S, k , x ) do 6 if p ( s, x ) = y and p ( s, y ) = x then M y ← min( M y , d ( s, x ) + d ( s, y ) + 1) 7 The v ertices compute M = min { M v | v ∈ V } by conv ergecasting (see, e.g., [23]). 5 The follo wing lemma establishes the correctness of the procedure by sho wing that the computed v alue M satisfies the required b ounds. Lemma 3.2. F or an undir e cte d and unweighte d network G = ( V , E ) with girth g , a set of sour c es S ⊆ V and a natur al numb er k , pr o c e dur e Estimate ( G, S, k ) c omputes a glob al ly known value M satisfying g ≤ M , and M ≤ 2 d ( S ) + g whenever C is nonempty. Pr o of. W e start by showing that M ≥ g . F or this w e ha v e to show that d ( s, x ) + d ( s, y ) + 1 ≥ g holds for ev ery edge { x, y } = e ∈ E and every source s ∈ U ( S, k , x ) ∩ U ( S, k , y ) that satisfy the condition at line 6. Fix suc h e = { x, y } and s . As p ( s, x ) = y , there is a path p of length d ( s, x ) from s to x suc h that y is not the parent of x in p . W e claim that y do es not app ear in p at all. Indeed, if it w as, then it would b e at distance at least 2 from x in p , but then we could replace this subpath by the edge { x, y } and get a shorter path, in contradiction. By a symmetric argumen t, there is a path q of length d ( s, y ) from s to y suc h that x do es not app ear in it. Let u b e the closest v ertex to y in q that also app ears in p (such a vertex m ust exists as s is a common v ertex). Let p ′ and q ′ b e the subpaths of p and q from x to u and from u to y , respectively . It is easy to see that C = p ′ ◦ q ′ ◦ ( y , x ) is a cycle of length at most d ( s, x ) + d ( s, y ) + 1, and so d ( s, x ) + d ( s, y ) + 1 ≥ | C | ≥ g . Assume no w that C is not empty , and let C ∈ C b e such that d ( S ) = d ( S, C ). Let s ∈ S b e a source that cov ers C such that d ( S, C ) = d ( s, C ). Since s co vers C , we hav e s ∈ U ( S , k , v ) ∩ U ( S, k , u ) for every edge { u, v } in C . Moreov er, at least one of these edges e = { x, y } m ust satisfy the condition at line 6 with respect to s , as C is a cycle. Thus, for s and x , we hav e M x ≤ d ( s, x ) + d ( s, y ) + 1. Let v b e a v ertex in V ( C ) such that d ( s, C ) = d ( s, v ). Note that d ( S ) = d ( S, C ) = d ( s, C ) = d ( s, v ). By the triangle inequality we know that d ( s, x ) ≤ d ( s, v ) + d ( v , x ) and d ( s, y ) ≤ d ( s, v ) + d ( v , y ). It follo ws that M x ≤ 2 d ( s, v ) + d ( v , x ) + d ( v , y ) + 1. As d ( v , x ) + d ( v , y ) + 1 cannot b e more than the length of C , we get that M ≤ M x ≤ 2 d ( s, v ) + | C | = 2 d ( S ) + g . The next lemma establishes an upp er b ound on the round complexity of the pro cedure as a function of k and D . Lemma 3.3. Pr o c e dur e Estimate ( G, S , k ) runs in O ( k + D ) r ounds on any undir e cte d, unweighte d network G of diameter D . Pr o of. The source detection algorithm tak es O ( k + D ) rounds (Lemma 3.1), broadcasting the set in line 2 takes O ( k ) rounds, and computing M takes O ( D ) rounds. Thus, O ( k + D ) rounds in total. 3.3 The Approximation Algorithm Let f b e a p ositiv e integer, and c ≥ 1 a constant. W e describ e a randomized algorithm that, with probabilit y at least 1 − n − c , computes in ˜ O ( f · n 1 /f + f · D ) rounds, an f -approximation to the girth of an y undirected netw ork G = ( V , E ) with n > 0 v ertices and diameter D . 6 Algorithm 1: Approximating the girth in unw eighted undirected netw orks // Let A 0 be V and k be ⌈ 12( c + 3) n 1 /f log n ⌉ . 1 if n ≤ f then 2 M ← Estimate( G, A 0 , n ). 3 else 4 M 0 ← Estimate( G, A 0 , k ). 5 for i ← 1 to f − 1 do 6 Eac h vertex samples itself with probability p i = min(( c + 3) n − i/f log n, 1). 7 M i ← Estimate( G, A i , k ), where A i is the sampled set. 8 Eac h vertex lo cally computes M = min( M 0 , ..., M f − 1 ). Next, w e establish the correctness of the algorithm and provide a thorough analysis of its running time. Correctness. If n ≤ f then the algorithm computes the girth exactly (as, in this case, any v ertex in a shortest cycle cov ers it). So assume that n > f . F or each i ∈ { 1 , ..., f } and each vertex v ∈ V , let Q i ( v ) b e the set of the ⌈ n i/f ⌉ closest vertices to v in G 2 . W e sa y that the sampling is go od, if the follo wing tw o even ts o ccur: (1) for every i ∈ { 1 , ..., f − 1 } and ev ery v ∈ V , the set Q i ( v ) con tains a v ertex from A i , and (2) for ev ery i ∈ { 0 , ..., f − 1 } and every v ∈ V , the set Q i +1 ( v ) con tains at most ⌈ 12( c + 3) n 1 /f log n ⌉ vertices from A i . W e start by proving that the sampling is go od with high probability . Claim 3.1. The sampling is go o d with pr ob ability at le ast 1 − n − c . Pr o of. By the union b ound, it is enough to sho w that each of the ev ents fails to o ccur with proba- bilit y at most n − c − 1 . (1) F or a given i ∈ { 1 , ..., f − 1 } and v ∈ V , the probability that Q i ( v ) do es not con tain any vertex from A i is (1 − p i ) | Q i ( v ) | = ( 0 , if p i = 1 (1 − ( c + 3) n − i/f log n ) ⌈ n i/f ⌉ ≤ e − ( c +3) log n ≤ n − c − 3 , otherwise th us, by the union b ound ov er all the v ertices and all the indices, w e get that the ev ent fails to o ccur with probability at most n − c − 1 . (2) Let i ∈ { 0 , ..., f − 1 } and v ∈ V . If i = 0, then Q 1 ( v ) can contain at most | Q 1 ( v ) | = ⌈ n 1 /f ⌉ ≤ ⌈ 12( c + 3) n 1 /f log n ⌉ v ertices from A 0 , so the probabilit y that the ev ent do es not o ccur is 0. Otherwise, the exp ected num b er of vertices X i v in Q i +1 ( v ) that b elong to A i is | Q i +1 ( v ) | · p i ≤ ⌈ n ( i +1) /f ⌉ · ( c + 3) n − i/f log n ≤ 2( c + 3) n 1 /f log n th us, by Chernoff b ound, w e hav e P ( X i v ≥ 12( c + 3) n 1 /f log n ) ≤ 2 − 12( c +3) n 1 /f log n ≤ n − c − 3 and so b y the union bound ov er all the v ertices and indices, we get that the ev ent fails to o ccur with probabilit y at most n − c − 1 . 2 Recall that a vertex x ∈ V is said to b e closer to v than a vertex y ∈ V , if either d ( v , x ) < d ( v , y ), or d ( v , x ) = d ( v , y ) and I D ( x ) < I D ( y ). 7 No w, we will show that when the sampling is go o d, the algorithm finds an f -approximation. Let g b e the girth of G . If it is not finite, then all the appro ximations will return ∞ . Otherwise, G has a shortest cycle C . W e pro ve the following key prop ert y: Claim 3.2. Ther e exist an index i ∈ { 0 , ..., f − 1 } and a vertex x ∈ A i such that d ( x, C ) ≤ ( g / 2) · i , and x ∈ Q i +1 ( u ) for al l u ∈ V ( C ) . Pr o of. F or the sake of contradiction, supp ose that the claim is false. W e will pro ceed by induction on i to show that for each i ∈ { 0 , ..., f − 1 } there exists a vertex x ∈ A i suc h that d ( x, C ) ≤ ( g / 2) · i . This will imply that for i = f − 1 there is a v ertex x ∈ A f − 1 suc h that d ( x, C ) ≤ ( g / 2) · ( f − 1), and so that there is a vertex u ∈ V ( C ) such that x ∈ Q f ( u ), which is imp ossible, as Q f ( u ) = V by definition. The base case ( i = 0) is trivial as for any vertex x ∈ V ( C ) ⊆ V = A 0 , we hav e d ( x, C ) = 0 ≤ ( g / 2) · i . Assume that the claim is true for 0 ≤ i < f − 1, and prov e it for i + 1. By the induction h yp othesis, there exists a vertex y ∈ A i suc h that d ( y , C ) ≤ ( g / 2) · i . As we assumed that the claim do es not hold, there must b e a v ertex u ∈ V ( C ) suc h that y ∈ Q i +1 ( u ). As the sampling is go o d, there is a v ertex x ∈ A i +1 ∩ Q i +1 ( u ). As y ∈ Q i +1 ( u ) and x ∈ Q i +1 ( u ), we hav e d ( u, x ) ≤ d ( u, y ). Let z ∈ V ( C ) be such that d ( y , z ) = d ( y , C ). By the triangle inequalit y , d ( u, y ) ≤ d ( u, z ) + d ( z , y ), and so d ( x, C ) ≤ d ( x, u ) ≤ d ( u, y ) ≤ d ( u, z ) + d ( z , y ) = d ( u, z ) + d ( y , C ) ≤ g / 2 + g i/ 2 = ( g / 2) · ( i + 1) In the next claim, w e use this prop ert y to sho w that the algorithm returns a go od appro ximation: Claim 3.3. Ther e exists i ∈ { 0 , ..., f − 1 } such that M i ≤ g ( i + 1) Pr o of. By Claim 3.2, there exist i ∈ { 0 , ..., f − 1 } and x ∈ A i suc h that d ( x, C ) ≤ g i/ 2, and x ∈ Q i +1 ( u ) for all u ∈ V ( C ). As the sampling is go od, w e know that for each u ∈ V ( C ), the set Q i +1 ( u ) contains at most k = ⌈ 12( c + 3) n 1 /f log n ⌉ vertices from A i . This implies that Q i +1 ( u ) ∩ A i ⊆ U ( A i , k , u ) for all u ∈ V ( C ). In particular, we ha ve x ∈ U ( A i , k , u ) for all u ∈ V ( C ). It follo ws that x cov ers C , and so M i ≤ 2 d ( A i ) + g ≤ 2 d ( x, C ) + g ≤ g ( i + 1). W e conclude that the v alue M = min( M 0 , ..., M f − 1 ) that the algorithm returns is alwa ys in the range [ g , f · g ]. Complexit y . When n ≤ f , we compute one appro ximation that tak es O ( f + D ) rounds. Otherwise, we compute f approximations, each takes O ( n 1 /f log n · c + D ) rounds. Th us, the complexit y is ˜ O ( f · n 1 /f · c + f · D ). 4 W eigh ted Undirected Net w orks In this section, we present a randomized algorithm that achiev es new trade-offs for approximating the girth of w eighted, undirected netw orks. 8 4.1 Ov erview A primary b ottlenec k in the framew ork of Manoharan and Ramac handran [21] is the Θ( | S | 2 ) rounds required to compute appro ximate distances from a set of sources S (used to estimate the weigh t of certain cycles), via a pro cedure that relies on an exhaustiv e broadcast of all-pairs distances within S as an intermediate step. W e ov ercome this limitation by demonstrating that such dense dissemination is not an inheren t requiremen t. By substituting the full broadcast w ith a strategically constructed spanner, we effectively reduce the communication cost. This technique breaks the quadratic dep endency on | S | , effectively accelerating the girth estimation pro cess at the cost of a marginal decrease in appro ximation quality , which remains close to optimal. W e no w provide a more detailed o verview of this approach. The first observ ation of [21] is that the appro ximation algorithm for un weigh ted net w orks can b e adapted to weigh ted ones by simulating eac h edge of weigh t w as an un weigh ted path of length w . This transformation allows one to compute a 2-approximation to the girth in weigh ted undirected net works, but may require as many as Ω( W D ) rounds, where W is the maxim um edge weigh t and D is the hop-diameter. T o mitigate this, they limit the depth of the BFS scans to at most h hops, whic h yields the following result [21, Corollary 12]: Lemma 4.1. Given a weighte d undir e cte d network G and a natur al numb er h , we c an, with high pr ob ability, c ompute in ˜ O ( √ n + h + D ) r ounds an appr oximation M to the weighte d girth g such that g ≤ M and M ≤ 2 g whenever g ≤ h . Next, they used a scaling technique [22] to mov e from an approximation for b ounded w eight to one for b ounded hop. Sp ecifically they construct O (log hW ) v ersions of G , where in the i -th v ersion G i , the weigh t of each edge e is set to ⌈ 2 hw ( e ) /ϵ 2 i ⌉ . By an analysis similar to that of [22, Theorem 3.3], we can show that if G con tains a minimum w eight cycle C with at most h edges, then there exists an index i such that w G i ( C ) = O ( h ), and ( ϵ 2 i / 2 h ) · w G i ( C ) ≤ (1 + ϵ ) w ( C ). Th us, in voking Lemma 4.1 on G i giv es an approximation M i suc h that M i ≤ 2 w G i ( C ), and so ( ϵ 2 i / 2 h ) · M i ≤ (2 + 2 ϵ ) w ( C ). Applying this pro cedure to all graphs and taking the minimum ov er the resulting v alues yields a 2(1 + ϵ )-approximation for the minimum w eight cycle with hop b ound h in ˜ O ( √ n + h + D ) rounds. This approac h giv es a go o d running time when h is relativ ely small. T o obtain an approximation for larger v alues of h , they use a direct sampling technique aimed at hitting a minim um-weigh t cycle. Sp ecifically , if G con tains a cycle C with at least h vertices, then selecting eac h v ertex independently with probabilit y ˜ Θ(1 /h ) ensures that, with high probability , at least one vertex of C is selected. Th us, computing (1 + ϵ )-apro ximate distances from the selected set S , and computing an estimation for all non-tree’s edges, gives us a (1 + ϵ )-appro ximation to the minim um-weigh t cycle. Computing these distances takes ˜ O ( h + D + | S | 2 ) rounds, e.g. [21, Algorithm 1]. Since | S | = ˜ O ( n/h ) with high probabilit y , the total running time is ˜ O ( h + ( n/h ) 2 + D ). Setting h = Θ( n 2 / 3 ) yields a running time of ˜ O ( n 2 / 3 + D ) for appro ximating cycles with Ω( n 2 / 3 ) edges. The rest can be approximated with the previous pro cedure in another ˜ O ( n 2 / 3 + D ) rounds. The critical ov erhead of this approach lies in the approximation pro cedure for cycles with Ω( n 2 / 3 ) hops, as it requires to compute appro ximate distances from | S | = ˜ Θ( n/h ) sources using a procedure that takes Ω( h + D + | S | 2 ) rounds. This pro cedure op erates by first computing appro ximate h - hop distances from all sources, then constructing an o verla y netw ork on the set S , and finally broadcasting all edges of this net work, enabling eac h vertex to appro ximate its distance from each source. Here, we show that broadcasting the entire netw ork (which may take Ω( | S | 2 ) rounds) 9 can b e av oided b y constructing an appropriate spanner and broadcasting only it, thereby trading appro ximation quality for improv ed running time. The remainder of this section is organized as follo ws. W e first describ e our new distance appro ximation pro cedure, whic h relies on spanner construction. Next, we integrate this pro cedure in to the girth-approximation algorithm and reanalyze it. 4.2 Multi-Source Distance Approximation Let G = ( V , E , w ) be a weigh ted undirected net work with n > 0 vertices and hop-diameter D , and let h and k b e t wo natural num b ers. The goal of this section is to describ e an axuliary pro cedure that giv en a sampled set of sources S ⊆ V , obtained by choosing each vertex with probabilit y ˜ Θ(1 /h ), computes a (2 k − 1)(1 + ϵ )-approximation to the distances from all S . W e b egin by briefly describing t wo to ols that w e will use in our algorithm. Appro ximating Bounded Hop Distances. W e rely on the follo wing kno wn result on multi- source h -hop distance approximation [22, Theorem 3.6], whic h we summerize in the follo wing lemma: Lemma 4.2. Ther e exists a r andomize d algorithm that, given a weighte d undir e cte d network G = ( V , E , w ) with hop-diameter D , a set of sour c es S ⊆ V , an inte ger hop p ar ameter h ≥ 1 , and an appr oximation p ar ameter ϵ > 0 , c omputes distanc e estimates ˜ d ( s, v ) for al l ( s, v ) ∈ S × V , such that with high pr ob ability d ( s, v ) ≤ ˜ d ( s, v ) ≤ (1 + ϵ ) d h ( s, v ) wher e ˜ d ( s, v ) is known to v . The algorithm runs in ˜ O ( h/ϵ + | S | + D ) r ounds. Construction of Spanners on Overla y Netw orks. W e say that a weigh ted undirected graph H = ( V H , E H , w H ) is an overlay network (or equiv alently , a virtual network ) on a comm uni- cation net work G = ( V G , E G , w G ) if V H ⊆ V G and eac h vertex v ∈ V G kno ws whether it b elongs to V H , and if it do es, it also knows the set of edges incident to it in H . It is known that for ev ery weigh ted undirected netw ork on n vertices and every natural num b er k , a (2 k − 1)-spanner of size O ( kn 1+1 /k ) can b e deterministically computed in ˜ O ( kn 1 /k ) rounds in the Broadcast Congested Clique [1, Corollary 5.1]. This algorithm consists of O ( k ) iterations in eac h of whic h ev ery v ertex broadcasts ˜ O ( n 1 /k ) bits, resulting in a total communication of ˜ O ( n 1+1 /k ) bits p er iteration. F or an ov erla y netw ork H with n vertices ov er a real netw ork with hop-diameter D , eac h suc h iteration can b e simulated in ˜ O ( n 1+1 /k + D ) rounds (by standard casting op erations, e.g. [23]), whic h gives the following result: Lemma 4.3. F or any natur al numb er k and an overlay network H = ( V H , E H , w H ) over G with hop-diameter D , a (2 k − 1) -sp anner of size O ( k | V H | 1+1 /k ) c an b e deterministic al ly c ompute d in ˜ O ( k | V H | 1+1 /k + k D ) r ounds. Next, w e describ e the appro ximation algorithm, provide a pro of of its correctness, and analyze its running time. 10 Pro cedure DisAppro x( G, S, h, k , ϵ ) Input: An undirected weigh ted net work G = ( V , E , w G ), a set of sampled sources S ⊆ V (obtained by c ho osing each vertex with probability min(( c + 2) log n/h, 1), for some natural n umber h ), a natural num b er k and an approximation parameter ϵ > 0. Eac h vertex initially knows k , ϵ and whether it b elongs to S . 1 The v ertices compute (2 h )-hop distance approximation ˜ d from S b y using Lemma 4.2. /* Let H be the overlay network whose vertex set is S , with an edge between every pair of sources that have a finite estimated distance, and where the weight of each edge equals the corresponding distance estimate ˜ d . Note that H is implicitly constructed in step 1. */ 2 The v ertices construct a (2 k − 1)-spanner H ′ for H using Lemma 4.3, and broadcast it. 3 Eac h vertex v locally computes: 4 foreac h s ∈ S do 5 d out ( s, v ) ← min { d H ′ ( s, s ′ ) + ˜ d ( s ′ , v ) | s ′ ∈ S } Lemma 4.4. With high pr ob ability, the c ompute d distanc es appr oximate the true distanc es within a factor of (2 k − 1)(1 + ϵ ) . Pr o of. The pro of follo ws a fairly standard argumen t. F or eac h vertex pair ( u, v ) with a shortest path of h v ertices in G , choose one suc h path π ( u, v ), and let Π denote the set of all the chosen paths. W e say that S hits Π if every path in Π con tains at least one v ertex from S . Observe that S hits Π with high probability: for any path π ∈ Π, the probability that it contains no vertex from S is at most e − ( c +2) log n ≤ n − ( c +2) , and as | Π | ≤ n 2 , it follows by the union b ound that S fails to hit Π with probability at most n − c . The rest of the pro of establishes that, whenever S hits Π, the pro cedure yields the correct approximation. Consider a pair ( s, v ) ∈ S × V , and let p b e a shortest path from s to v in G . W e partition p in to m consecutiv e subpaths p 1 , ..., p m , eac h containing h vertices, except p ossibly the last, which contains at most h vertices. Without loss of generality , we may assume that each path in { p 2 , ..., p m − 1 } b elongs to Π, and so eac h such p i con tains a vertex s i ∈ S . Let ( x 1 , ..., x t ) denote ( s, s 2 , ..., s m − 1 , v ), and note that for each t wo consecutive v ertices in it, there exists a shortest path containing at most 2 h edges. Th us, with high probability , w e hav e ˜ d ( x i , x i +1 ) ≤ (1 + ϵ ) d 2 h G ( x i , x i +1 ) = (1 + ϵ ) d G ( x i , x i +1 ) for all i ∈ { 1 , ..., t − 1 } . It follo ws that d H ( x 1 , x t − 1 ) ≤ (1 + ϵ ) P t − 2 i =1 d G ( x i , x i +1 ), and so d H ′ ( x 1 , x t − 1 ) ≤ (2 k − 1) d H ( x 1 , x t − 1 ) ≤ (2 k − 1)(1 + ϵ ) P t − 2 i =1 d G ( x i , x i +1 ). W e conclude that d out ( s, v ) ≤ d H ′ ( x 1 , x t − 1 ) + ˜ d ( x t − 1 , x t ) ≤ (2 k − 1)(1 + ϵ ) P t − 1 i =1 d G ( x i , x i +1 ) = (2 k − 1)(1 + ϵ ) d G ( x 1 , x t ). Lemma 4.5. The pr o c e dur e takes ˜ O ( h/ϵ + k | S | 1+1 /k + k D ) r ounds for any network whose hop- diameter is D . Pr o of. Step 1 takes ˜ O ( h/ϵ + | S | + D ) rounds, and step 2 takes ˜ O ( k | S | 1+1 /k + k D ) rounds. Thus, ˜ O ( h/ϵ + k | S | 1+1 /k + k D ) rounds, in total. 4.3 The Approximation Algorithm Let k > 1 b e an integer, and ϵ > 0 b e a constan t. W e describ e a randomized algorithm that, with high probability , computes in ˜ O ( kn ( k +1) / (2 k +1) + k D ) rounds, a (2 k − 1 + ϵ )-appro ximation of the 11 girth for an y undirected weigh ted net work G with n > 0 vertices and hop-diameter D . Algorithm 2: Approximating the girth in weigh ted undirected netw orks Input: An undirected weigh ted net work G = ( V , E , w ), a natural num b er k > 1 and an appro ximation parameter ϵ > 0. Each vertex initially knows k and ϵ . 1 Eac h vertex sets h ← ⌈ n k +1 2 k +1 ⌉ and samples itself with probabilit y min(( c + 2) log n/h, 1). // Compute an estimation for long cycles ( S is the set of sampled vertices) 2 The v ertices call DisApprox( G, S, h, k , ϵ ) to compute distance estimations d ′ , where during its execution, eac h vertex v also keeps trac k of its parent p ( s, v ) along the estimated path from eac h s ∈ S . 3 Eac h vertex v broadcasts the set { ( d ′ ( s, v ) , p ( s, v )) | s ∈ S } to its neigh b ors. 4 Ev ery vertex v locally computes: 5 M v ← ∞ 6 foreac h neighbor x a nd source s ∈ S do 7 if p ( s, x ) = v and p ( s, v ) = x then M v ← min( M v , d ′ ( s, v ) + d ′ ( s, x ) + w ( v , x )) 8 The v ertices compute M l = min { M v | v ∈ V } by conv ergecasting [23]. // Compute an estimation for short cycles 9 Eac h vertex sets h ∗ ← (1 + 2 /ϵ ) · h . 10 for i ← 1 to ⌈ log hW ⌉ do 11 Eac h v ertex lo cally adjusts the weigh ts of its incident edges so that eac h edge e ∈ E has w eight ⌈ 2 hw ( e ) /ϵ 2 i ⌉ . // Denote by G i the resulting graph 12 The vertices compute an h ∗ -limited 2-approximation of G i ’s girth M i using Lemma 4.1. 13 Eac h vertex lo cally computes M s = min i { ϵ 2 i M i / 2 h } . // Compute the final estimation 14 Eac h vertex lo cally computes M = min( M s , M l ). W e pro ve that the algorithm correctly computes the claimed appro ximation and analyze its running time. Correctness. Let C b e a minimum weigh t cycle in G . W e first show that w ( C ) ≤ M s and, if C contains < h edges then M s ≤ (2 + ϵ ) w ( C ). F or each i ∈ { 1 , ..., ⌈ log hW ⌉} , the weigh t of any cycle C ′ in G i is X e ∈ E ( C ′ ) ⌈ 2 hw ( e ) /ϵ 2 i ⌉ ≥ (2 h/ϵ 2 i ) X e ∈ E ( C ′ ) w ( e ) = (2 h/ϵ 2 i ) w ( C ′ ) ≥ (2 h/ϵ 2 i ) w ( C ) It follo ws that M i ≥ (2 h/ϵ 2 i ) w ( C ), and so ϵ 2 i M i / 2 h ≥ w ( C ). Th us, M s ≥ w ( C ). Assume no w that C con tains less than h edges. Let i ∈ { 1 , ..., ⌈ log hW ⌉} b e such that 2 i − 1 ≤ w ( C ) < 2 i . The weigh t of C in G i is w G i ( C ) = P e ∈ E ( C ) ⌈ 2 hw ( e ) /ϵ 2 i ⌉ < P e ∈ E ( C ) (2 hw ( e ) /ϵ 2 i + 1) = (2 h/ϵ 2 i ) w ( C ) + | E ( C ) | , whic h is at most (2 /ϵ + 1) h = h ∗ . This implies that M i ≤ 2 w G i ( C ), and so M s ≤ ϵ 2 i M i / 2 h ≤ 2 · ϵ 2 i w G i ( C ) / 2 h ≤ 2( w ( C ) + ϵ 2 i − 1 ) ≤ 2(1 + ϵ ) w ( C ). No w, w e show that w ( C ) ≤ M l and, if C contains ≥ h edges then M l ≤ (1 + ϵ )(2 k − 1) w ( C ). F or proving the first condition, we hav e to show that d ′ ( s, v ) + d ′ ( s, x ) + w ( v , x ) ≥ w ( C ) holds for 12 ev ery edge { v , x } that satisfies the condition in line 7. This is true b ecause there alwa ys exists a cycle passing through { v , x } whose w eight do es not exceed the computed estimate. No w, if C contains at least h edges, then with high probability , there is a vertex s ∈ S ∩ V ( C ). As C is a cycle, there m ust b e an edge { v , x } that satisfies the condition in line 7. Thus, we hav e M l ≤ d ′ ( s, v ) + d ′ ( s, x ) + w ( v, x ) ≤ (1 + ϵ )(2 k − 1)( d ( s, v ) + d ( s, x ) + w ( v, x )) ≤ (1 + ϵ )(2 k − 1) w ( C ). As (2 k − 1)(1 + ϵ ) ≥ 2(1 + ϵ ), w e conclude that M ≤ (2 k − 1)(1 + ϵ ) w ( C ). Complexit y . Step 2 takes ˜ O ( h/ϵ + k | S | 1+1 /k + k D ) rounds by Lemma 4.5. Step 3 takes O ( | S | ) rounds. Step 8 tak es O ( D ) rounds. The lo op at line 10 runs for O (log n ) iterations, each tak es ˜ O ( n 1 / 2 + h ∗ + D ) = ˜ O ( n 1 / 2 + h + h/ϵ + D ) rounds b y Lemma 4.1. Thus, the total is ˜ O ( h + h/ϵ + n 1 / 2 + k | S | 1+1 /k + k D ) rounds. As, with high probability , we hav e | S | = ˜ O ( n/h ) = ˜ O ( n k/ (2 k +1) ), w e get that the running time is ˜ O (( k + 1 /ϵ ) · n ( k +1) / (2 k +1) + k D ). 5 Directed Net w orks W e now fo cus on the directed setting and presen t an improv ed randomized algorithm for approx- imating the girth of un weigh ted, directed net works. Extension to weigh ted directed netw orks is discussed in a later subsection. 5.1 Ov erview W e significan tly improv e the girth appro ximation framew ork of [21] for approximating the girth in directed netw orks. As in previous w ork, cycles are divided into long , whic h are likely to in tersect a suitably sampled v ertex set through which the cycles are computed exactly , and short , whic h are handled via restricted BFS explorations of carefully defined lo cal neighborho o ds. Our main tec hnical con tribution is a global approac h to handling congestion: instead of controlling congestion during the execution of restricted explorations (as w as done in [21], and required an excessive n umber of rounds), w e isolate and pro cess highly congested v ertices in adv ance, enabling a cleaner analysis and an impro ved round complexity of ˜ O ( n 2 / 3 + D ). Throughout this section, let G = ( V , E ) b e a directed un weigh ted graph with | V | = n and hop-diameter D . The algorithm maintains, for each vertex v , a v alue µ v represen ting the length of the shortest directed cycle through v discov ered so far. The final output is µ = min v ∈ V µ v . The algorithm is divided in to t w o phases. The first phase is similar in spirit to the corresp onding phase of [21], and w.h.p. exactly detects the length of any cycle with hop-length at least h = n 2 / 3 . The second phase computes a 2-approximation for the remaining cycles, whose hop-length is at most h . 5.2 Computing approximate for long MWC The algorithm sets h = n 2 / 3 and samples a set S ⊆ V of size | S | = ˜ Θ( n 1 / 3 ) with high probability , b y including each vertex indep enden tly with probability ˜ Θ(1 /h ). Next, the algorithm p erforms tw o multi-source exact directed BFS computations, one from the v ertices in S and one to the v ertices in S . As a result, eac h v ertex v ∈ V learns all distances d ( s, v ) and d ( v , s ) for every s ∈ S . This step tak es O ( p n | S | + D ) = ˜ O ( n 2 / 3 + D ) rounds with high 13 probabilit y [21, Theorem 4]. F or ev ery edge ( v , s ) ∈ E , the algorithm then lo cally up dates µ v = min { µ v , d ( s, v ) + 1 } . Let C b e a minimum weigh t cycle in G . If the hop-length of C is at least h , then with high probabilit y the sampled set satisfies C ∩ S = ∅ . In this case, for every vertex v ∈ C the algorithm has computed d ( v ⇆ s ) for some s ∈ C ∩ S , and therefore sets µ v = d ( v ⇆ s ). Finally , for every pair s, s ′ ∈ S , the algorithm broadcasts the distance d ( s, s ′ ). This step takes O ( | S | 2 + D ) = ˜ O ( n 2 / 3 ) rounds and concludes the first phase. The full pseudo-co de is giv en in Algorithm 3. Algorithm 3: 2-Approximation Algorithm for Directed Unw eighted MWC Input: Directed un weigh ted graph G = ( V , E ) Output: µ , a 2-appro ximation of the minimum weigh t cycle in G 1 Let h = n 2 / 3 ; 2 Initialize µ v ← ∞ for all v ∈ V ; 3 Sample a set S ⊆ V by including eac h vertex indep enden tly with probability Θ log 3 n h ; 4 Compute distances d ( s, v ) for all s ∈ S , v ∈ V using m ulti-source directed BFS; /* Detect all cycles passing through sampled vertices */ 5 foreac h s ∈ S do 6 foreac h inc oming e dge ( v , s ) ∈ E do 7 µ v ← min { µ v , d ( s, v ) + 1 } ; 8 Broadcast all distances { d ( s, t ) } s,t ∈ S to all v ertices; 9 In vok e Algorithm 4; /* the short-cycle procedure that processes cycles of hop-length < h . */ 10 Return µ ← min v ∈ V µ v computed b y a conv ergecast. 5.3 Computing approximate for short MWC The first phase ”handles” long MW C, meaning that the MW C hop-set it at least h = n 2 / 3 . In this section we presen t a new metho d for appro ximating the MW C if its hop distance is less than h . W e assume that each v ertex v ∈ V knows all d ( v , s ) , d ( s, v ) for all s ∈ S , and all d ( s, s ′ ) for all s, s ′ ∈ S . This subsection describ es the construction of a vertex neighborho o d P ( v ) for eac h v ∈ V , and a small elimination set R ( v ) ⊆ S that controls the size of P ( v ). Informally , the neighborho o d P ( v ) is defined so that (i) it contains all short cycle s through v whenever the minim um cycle through v a voids the sampled set S and is muc h smaller then the minimal d ( s ⇆ v ) o ver all s ∈ S , and (ii) it is small enough to supp ort a restricted exploration in sublinear time. Elimination predicate. W e rely on the following elimination rule (cf. Lemma 5.1 in [8]). F or a fixed v ertex v , a vertex t ∈ S is said to eliminate a v ertex y ∈ V if 2 d ( v , t ) + d ( t, y ) ≤ 2 d ( v , y ) + d ( y , t ) . (1) Lemma 5.1 in [8] states that whenever (1) holds, the minimum cycle through v and t provides a 2-appro ximation for the minimum cycle through v and y , and since cycles through sampled v ertices are already handled in the first phase, the v ertex y can b e excluded from the neighborho od of v . 14 Definition of P ( v ) giv en R ( v ) . Giv en any subset R ( v ) ⊆ S , define P ( v ) = n y ∈ V ∀ t ∈ R ( v ) , 2 d ( v , y ) + d ( y , t ) < 2 d ( v , t ) + d ( t, y ) o . (2) Equiv alently , P ( v ) contains exactly those vertices not eliminated b y any t ∈ R ( v ). Construction of R ( v ) . Fix β = ⌈ log n ⌉ . P artition the sampled set S into β disjoint groups S 1 , . . . , S β of (almost) equal size. 3 The set R ( v ) is constructed iteratively , adding at most one represen tative from each group. In iteration i , consider the subset of v ertices in S i that do not eliminate the current neigh b orho od, and select one suc h vertex (e.g. uniformly at random) to add to R ( v ). By construction, | R ( v ) | ≤ β = O (log n ). Manoharan and Ramachandran show the exact algorithm to compute that directly , so we will later assume that we hav e R ( v ) for every v ∈ V . Lemma 5.1 (Size b ound) . Assume | S | = Ω(log n · n 1 / 3 ) . Then for every fixe d v ∈ V , the set P ( v ) define d by (2) using the ab ove c onstruction of R ( v ) satisfies | P ( v ) | < n 2 / 3 with high pr ob ability in n . Pr o of sketch. The pro of follows the argument of Chechik and Lifshitz after substituting h = n 2 / 3 and | S | = Ω(log n · n 1 / 3 ). The key p oin t is that each iteration adds one sampled vertex t ∈ R ( v ) dra wn from a fresh group S i , and the elimination predicate (1) remo ves a constant fraction of the remaining vertices from the candidate neighborho o d (unless the remaining neighborho o d is already of size at most ˜ O ( n/ | S | )). After β = Θ(log n ) iterations, a standard multiplicativ e shrink age argumen t implies | P ( v ) | = ˜ O ( n/ | S | ) = ˜ O ( n 2 / 3 ) w.h.p. If the algorithm can compute the neighborho o d P ( v ) for any vertex v ∈ V within ˜ O ( n 2 / 3 + D ) rounds, then the remaining steps are straigh tforward. Once P ( v ) is kno wn, the algorithm can lo cally compute the minimum directed cycle through v con tained in P ( v ), up date the v alue µ v accordingly , and broadcast this v alue to the rest of the graph. A final con vergecast then yields µ = min v ∈ V µ v , completing the computation. It therefore suffices to show how to compute P ( v ) efficien tly . Since | P ( v ) | < n 2 / 3 with high probabilit y (Lemma 5.1), computing P ( v ) up to hop-distance h = n 2 / 3 can b e done in ˜ O ( n 2 / 3 ) rounds: Restricted BFS. The k ey idea is that the algorithm computes P ( v ) on the fly , without explicitly constructing it in adv ance. The algorithm p erforms a BFS pro ceeding for exactly h steps, and at eac h step a message is forwarded only to neighbors that satisfy the membership condition of Definition 2. T o test whether an intermediate vertex y b elongs to P ( v ) b efore propagating the BFS, the algorithm uses the distances b et ween sampled vertices that are already known from the first phase, together with the information defining R ( v ), which is carried in the BFS message. Since | R ( v ) | = O (log n ), the BFS message contains only O (log n ) distance v alues and therefore fits within the CONGEST bandwidth constrain ts. As a result, the restricted BFS explores exactly the vertices of P ( v ) up to hop-distance h , and completes in ˜ O ( n 2 / 3 ) rounds. The problem b ecomes when trying to compute all P ( v ) simultane- ously . 3 The partition can b e fixed globally using public randomness, or locally using a shared hash function. 15 Congestion measure. F or a subset U ⊆ V and a v ertex u ∈ V , define P − 1 ( u, U ) = { v ∈ U | u ∈ P ( v ) } , p − 1 ( U ) = max u ∈ V | P − 1 ( u, U ) | . In tuitively , P − 1 ( u, U ) measures ho w man y neighborho ods P ( v ), for v ∈ U , contain the vertex u , and p − 1 ( U ) captures the maxim um congestion induced by the family { P ( v ) } v ∈ U . Computing neighborho o ds under b ounded congestion. Manoharan and Ramachandran sho wed that, b y introducing random delays and carefully sc heduling restricted BFS explorations, one can compute all neighborho o ds P ( v ), v ∈ U , in time that depends linearly on the maxim um congestion parameter p − 1 ( U ), up to p olylogarithmic factors. Adapting their scheduling tec hnique to our setting yields the follo wing guarantee. Lemma 5.2. L et U ⊆ V and let h = n 2 / 3 . Then the r estricte d h -hop BFS explor ations r o ote d at al l vertic es v ∈ U c an b e exe cute d in ˜ O p − 1 ( U ) + h r ounds in the CONGEST mo del. Pr o of sketch. Eac h vertex v ∈ U p erforms an h -hop BFS restricted to P ( v ), as describ ed ab o v e. T o con trol congestion, the algorithm assigns eac h suc h BFS a random start delay dra wn from a suitable range, ensuring that BFS messages originating from differen t sources are sufficiently spread out ov er time. With high probabilit y , no vertex u is required to pro cess messages from more than ˜ O ( p − 1 ( U )) sources sim ultaneously . Since eac h restricted BFS pro ceeds for h = n 2 / 3 steps, the total running time is ˜ O ( p − 1 ( U ) + h ). F or con venience, w e refer to this procedure as SchedRBFS ( U, h ), and use it as a blac k b o x in the remainder of the algorithm, in voking Lemma 5.2 whenever its running time is needed. Second phase: intuition. The algorithm do es not need to compute the neighborho o ds P ( v ) for all vertices simultaneously . In fact, it suffices to compute P ( v ) for a single vertex v on any directed cycle C whose weigh t is less than half of the smallest v alue µ v found so far. Thus, the goal of the second phase is to ensure that at least one v ertex on every such short cycle can b e pro cessed. If the congestion parameter satisfies p − 1 ( V ) = O ( n 2 / 3 ), then the algorithm can inv oke the pro- cedure SchedRBFS ( V , h ), and compute all neigh b orho ods P ( v ) and terminate. The main challenge arises from v ertices that b elong to to o many neighborho o ds P ( v ), whic h would cause excessive congestion. The k ey idea is therefore to iden tify and pro cess highly congested vertices first, remov e them from the graph, and then recurse on the remaining v ertices. Handling congested vertices. W e define, for each U ⊆ V and u ∈ U , p − 1 ( u, U ) := | P − 1 ( u, U ) | . A v ertex u is called overflowing with resp ect to U if p − 1 ( u, U ) > 2 n 2 / 3 . 16 Let B 0 := V . Assume first that no vertex is ov erflo wing with resp ect to B 0 . Then p − 1 ( B 0 ) = O ( n 2 / 3 ), and the algorithm can in vok e SchedRBFS ( B 0 , h ) and compute Otherwise, define B 1 = { u ∈ V : p − 1 ( u, B 0 ) > 2 n 2 / 3 } to b e the set of ov erflowing vertices with respect to B 0 . Our goal is to pro cess the vertices in B 1 first and then remo ve them from the graph. The algorithm could do that if p − 1 ( B 1 ) = O ( n 2 / 3 ) - but that could not b e the case also. F or i ≥ 1, giv en B i , let B i +1 = { u ∈ V : p − 1 ( u, B i ) > 2 n 2 / 3 } . This pro cess contin ues un til | B τ | < 2 n 2 / 3 , b ecause after that B τ +1 = ∅ . Shrinking of congestion lay ers. The following lemma shows that this p eeling pro cess termi- nates quic kly . Lemma 5.3. F or al l i ≥ 0 : (1) B i +1 ⊆ B i and (2) | B i +1 | ≤ 1 2 | B i | . In p articular, the pr o c ess terminates after at most O (log n ) iter ations. Pr o of sketch. (1) If u ∈ B i +1 , then u b elongs to P ( v ) for more than 2 n 2 / 3 v ertices v ∈ B i . Since B i ⊆ B i − 1 b y induction, this implies u ∈ B i . (2) Eac h v ertex v ∈ B i can con tribute to at most | P ( v ) | ≤ n 2 / 3 v ertices u for whic h v ∈ P − 1 ( u, B i ). Consequen tly , X u ∈ V p − 1 ( u, B i ) ≤ | B i | · n 2 / 3 . On the other hand, b y definition, every vertex u ∈ B i +1 satisfies p − 1 ( u, B i ) > 2 n 2 / 3 . Therefore, X u ∈ V p − 1 ( u, B i ) ≥ X u ∈ B i +1 p − 1 ( u, B i ) > | B i +1 | · 2 n 2 / 3 . Com bining the tw o b ounds yields | B i +1 | · 2 n 2 / 3 < | B i | · n 2 / 3 , and hence | B i +1 | ≤ 1 2 | B i | . Ideally , the algorithm w ould explicitly compute the la yers B 0 , . . . , B τ , and once | B τ | < 2 n 2 / 3 , compute all neighborho o ds P ( v ) for v ∈ B τ , up date the v alues µ v , remo ve B τ , and contin ue with B τ − 1 , B τ − 2 , . . . . After removing B i +1 , there are no o verflo wing v ertices an ymore with resp ect to B i , so computing SchedRBFS ( B i , h ) on G \ B i +1 tak es ˜ O ( h ) time. The difficult y is that the algorithm cannot afford to compute these la yers exactly . Determining whether a vertex u b elongs to B 1 requires knowing the exact v alue of p − 1 ( u, V ), whic h in turn dep ends on the neigh b orho ods P ( v ) for many sources v . Instead, the algorithm relies on approxi- mate congestion information: given an approximation ˜ B i of B i , we show that b y sampling ˜ Θ( n 1 / 3 ) v ertices from ˜ B i , the algorithm can construct a go od approximation of B i +1 . 17 5.4 Second Phase: Algorithm Ov erview The second phase approximates the minimum w eight cycle among cycles of hop-length at most h = n 2 / 3 that av oid the sampled set S . It consists of t wo stages: Constructing a sequence of appro ximate congestion la yers V = ˜ B 0 ⊇ ˜ B 1 ⊇ ˜ B 2 ⊇ · · · ⊇ ˜ B τ , and processing these la yers from ˜ B τ up to ˜ B 0 , computing restricted neigh b orho ods and up dating the v alues µ v . Constructing the appro ximate lay ers ˜ B 1 , . . . , ˜ B τ . The construction pro ceeds iterativ ely . Set ˜ B 0 := V . At iteration i ≥ 0, the algorithm first computes | ˜ B i | via a standard conv ergecast on a BFS tree in O ( D ) rounds and chec ks whether | ˜ B i | > 0. If so, the construction terminates and we set τ := i − 1. Otherwise, the algorithm samples a set S i ⊆ ˜ B i b y including each vertex indep enden tly with probabilit y p := c log n h for a large enough constan t c , and in vok es SchedRBFS ( S i , h ). As a result, ev ery vertex u ∈ ˜ B i can compute the exact v alue p − 1 ( u, S i ). Using this information, the algorithm defines the next appro ximate lay er as ˜ B i +1 = { u ∈ ˜ B i | p − 1 ( u, S i ) > 3 c log n } , and pro ceeds to the next iteration. Pro cessing the lay ers. Once the sequence ˜ B 0 , ˜ B 1 , . . . , ˜ B τ has b een constructed, the algorithm pro cesses the lay ers in rev erse order. Starting from ˜ B τ and con tinuing up to ˜ B 0 , the algorithm in vok es SchedRBFS ( ˜ B i \ ˜ B i +1 , h ), computes the restricted neighborho o ds P ( v ) for all v ∈ ˜ B i \ ˜ B i +1 , and up dates the v alues µ v accordingly . After pro cessing a lay er ˜ B i , its vertices are excluded from all subsequen t calls to SchedRBFS (conceptually removing them from the graph). 18 Algorithm 4: SecondPhase : Handling short cycles via approximate congestion lay ers Input: Directed graph G = ( V , E ); hop b ound h = n 2 / 3 ; access to mem b ership test for P ( v ) via R ( v ); blac k b o x SchedRBFS ( U, h ). Output: Up dated v alues µ v for all v ∈ V (hence µ = min v µ v after con vergecast). /* Stage 1: Construct approximate congestion la yers */ 1 ˜ B 0 ← V , i ← 0; 2 while | ˜ B i | ≥ 0 do /* Compute | ˜ B i | using standard methods in O ( D ) time */ 3 Sample a set S i ⊆ ˜ B i b y including each vertex with probability c log n h ; 4 In vok e SchedRBFS ( S i , h ); /* Each vertex u can now compute p − 1 ( u, S i ) exactly */ 5 ˜ B i +1 ← { u ∈ V | p − 1 ( u, S i ) > 3 c log n } ; 6 i ← i + 1; 7 τ ← i − 1; /* Stage 2: Pro cess la yers in rev erse order */ 8 for i ← τ to 0 do 9 U i ← ˜ B i \ ˜ B i +1 ; /* Compute restricted neighborhoods for sources in the current layer */ 10 SchedRBFS ( U i , h ); 11 Up date µ v for ev ery v ∈ U i ; 12 Exclude U i from subsequen t iterations (conceptually remov e it from G ). 5.5 Analysis W e now present details of the pro of of correctness and round complexit y of Algorithm 3. Lemma 5.4. Algorithm 3 c omputes a 2 -appr oximation of the minimum weight cycle in a dir e cte d unweighte d gr aph G = ( V , E ) with high pr ob ability in n . Pr o of. Let C b e a minimum weigh t cycle in G , and let g := | C | denote its hop-length. If the hop-length of C is at least h = n 2 / 3 , then with high probabilit y the sampled set S in tersects C in the first phase. In this case, the algorithm computes the exact length of C b y com bining distances from and to the sampled vertex, and therefore returns the correct v alue. W e henceforth assume that the hop-length of C is less than h . If after the first phase there exists a vertex v with µ v ≤ 2 g , then the algorithm has already found a v alid 2-approximation and w e are done. Otherwise, consider the execution of the second phase. Since C do es not in tersect S , Lemma 5.1 of [8] implies that for every v ertex v ∈ C , the entire cycle C is con tained in the neigh b orho od P ( v ). Let v ∈ C be the first vertex on C that is pro cessed by the algorithm during the la yered p eeling pro cedure of the second phase. A t the time v is pro cessed, all other vertices of C hav e not yet b een remov ed, and therefore the restricted BFS ro oted at v explores the en tire cycle C within h hops. Consequently , the algorithm discov ers the exact length of C during this exploration and sets µ v = g . 19 W e no w b ound the round complexity by sho wing that the appro ximate lay ers shrink geometri- cally . Lemma 5.5. Fix an iter ation i and a vertex u ∈ ˜ B i . 1. If p − 1 ( u, ˜ B i ) ≥ 4 h , then P [ u / ∈ ˜ B i +1 ] ≤ n − Θ( c ) . 2. If p − 1 ( u, ˜ B i ) ≤ 2 h , then P [ u ∈ ˜ B i +1 ] ≤ n − Θ( c ) . Pr o of. Recall that ˜ B i +1 consists of all v ertices u satisfying p − 1 ( u, S i ) ≥ 3 c log n . Note that p − 1 ( u, S i ) ∼ Bin p − 1 ( u, ˜ B i ) , c log n h , and let µ := E [ p − 1 ( u, S i )] = c log n h · p − 1 ( u, ˜ B i ). (1) If p − 1 ( u, ˜ B i ) ≥ 4 h , then µ ≥ 4 c log n . By a Chernoff b ound, P [ u / ∈ ˜ B i +1 ] = P p − 1 ( u, S i ) < 3 c log n = P p − 1 ( u, S i ) < 3 4 µ ≤ n − Θ( c ) . (2) If p − 1 ( u, ˜ B i ) ≤ 2 h , then µ ≤ 2 c log n . By a Chernoff b ound, P [ u ∈ ˜ B i +1 ] = P p − 1 ( u, S i ) ≥ 3 c log n ≤ n − Θ( c ) . Lemma 5.6. Assume | P ( v ) | ≤ h for al l v ∈ ˜ B i . with high pr ob ability in n , for al l iter ations i ≤ ⌈ log n ⌉ , | ˜ B i +1 | ≤ 1 2 | ˜ B i | . Conse quently, τ = O (log n ) with high pr ob ability. Pr o of. Fix an iteration i . By double counting, X u ∈ V p − 1 ( u, ˜ B i ) = X v ∈ ˜ B i | P ( v ) | ≤ | ˜ B i | · h. Hence, the n umber of vertices u satisfying p − 1 ( u, ˜ B i ) > 2 h is at most | ˜ B i | / 2. By Lemma 5.5(2), eac h v ertex u with p − 1 ( u, ˜ B i ) ≤ 2 h is included in ˜ B i +1 with probability at most n − Θ( c ) . T aking a union b ound ov er all v ertices u ∈ V , with probabilit y at least 1 − n − Θ( c )+1 , no suc h vertex is included in ˜ B i +1 . Condition on this ev ent. Then every vertex in ˜ B i +1 satisfies p − 1 ( u, ˜ B i ) > 2 h , and therefore | ˜ B i +1 | ≤ 1 2 | ˜ B i | . Finally , taking a union b ound ov er all iterations i ≤ ⌈ log n ⌉ and choosing c sufficiently large completes the pro of. Lemma 5.7 (Round complexit y of the second phase) . Algorithm 4 c ompletes in ˜ O ( h + D ) = ˜ O ( n 2 / 3 + D ) r ounds with high pr ob ability in n . 20 Pr o of. Stage 1 (constructing lay ers). In iteration i , the algorithm first computes | ˜ B i | by a standard aggregation (con vergecast and broadcast) on a BFS tree, which costs O ( D ) rounds. Next, it samples S i b y including each v ertex with probability p = c log n h and in vok es pro cedure SchedRBFS ( S i , h ). By Lemma 5.2, this costs ˜ O p − 1 ( S i ) + h rounds. By Lemma 5.6, with high probability in n w e hav e | ˜ B i +1 | ≤ 1 2 | ˜ B i | for all i ≤ ⌈ log n ⌉ , and hence the n umber of iterations in Stage 1 is τ = O (log n ). Moreo ver, for ev ery i ≤ τ the sampling is p erformed from ˜ B i (eac h vertex outside ˜ B i is irrele- v ant), so E [ | S i | ] = p · | ˜ B i | ≤ c log n h · n = O ( n 1 / 3 log n ) , and a Chernoff b ound implies | S i | = ˜ O ( n 1 / 3 ) for all i ≤ τ with high probability . Therefore, p − 1 ( S i ) ≤ | S i | = ˜ O ( n 1 / 3 ) deterministically , and Lemma 5.2 giv es that each call SchedRBFS ( S i , h ) runs in ˜ O ( h ) rounds w.h.p. Summing o ver τ = O (log n ) iterations, Stage 1 takes ˜ O ( h ) + O ( D ) · O (log n ) = ˜ O ( h + D ) rounds with high probabilit y . Stage 2 (pro cessing la yers). F or each i = τ , . . . , 0, the algorithm inv ok es SchedRBFS ( U i , h ) where U i = ˜ B i \ ˜ B i +1 , and the sets U i form a partition of V . W e claim that for ev ery i , p − 1 ( U i ) = O ( h ) with high probabilit y . Fix i and a v ertex u ∈ U i . Since u ∈ ˜ B i but u / ∈ ˜ B i +1 , Lemma 5.5(1) implies that, except with probabilit y n − Θ( c ) , p − 1 ( u, U i ) < 4 h. Applying Lemma 5.2 giv es that each call SchedRBFS ( U i , h ) completes in ˜ O ( h ) rounds. T aking a union b ound o ver all i ≤ τ and choosing c sufficiently large, all these b ounds hold simultaneously with high probabilit y . Hence Stage 2 takes ˜ O ( h ) rounds in total. 5.6 Extension to W eigh ted Net works W e use the same transformation as Manoharan and Ramac handran [21]. W e run the unw eighted algorithm on weigh ted netw orks by sim ulating each directed edge of weigh t w as an un weigh ted directed path of length w ; that is, eac h BFS step of the original algorithm is sim ulated by a sequence of steps along a virtual path. T o preven t the running time from getting to o big, w e limit all BFS executions on the virtual net w ork to a given depth h ∗ . This approac h guaran tees a 2-approximation whenev er the girth has weigh t O ( h ∗ ), and ac hieves a running time of ˜ O ( n 2 / 3 + h ∗ + D ). Next, w e apply the same scaling that w e used in Algorithm 2. Namely , we construct O (log h ∗ W ) v ersions of G . In the i -th version G i , the w eight of eac h edge e is set to ⌈ 2 h ∗ w ( e ) /ε 2 i ⌉ . By an iden tical reasoning to that in Algorithm 2, if G contains a minim um-weigh t cycle C with at most h ∗ edges, then there exists an index i suc h that w G i ( C ) = O ( h ∗ ), and ( ε 2 i / 2 h ∗ ) · w G i ( C ) ≤ (1 + ε ) w ( C ). 21 Therefore, applying the abov e pro cedure to all graphs and taking the minimum yields a (2 + ε )- appro ximation for a minim um-weigh t cycle with hop b ound h ∗ in ˜ O ( n 2 / 3 + h ∗ + D ) rounds. In particular, for h ∗ = Θ( n 2 / 3 ), the running time b ecomes ˜ O ( n 2 / 3 + D ). T o handle longer cycles, w e sample a set S of ˜ Θ( n 1 / 3 ) v ertices by selecting each v ertex inde- p enden tly with probabilit y ˜ Θ( n − 2 / 3 ). W e then compute (1 + ε )-appro ximate distances ˜ d from all S in time ˜ O ( p | S | n + D ) = ˜ O ( n 2 / 3 + D ) [21, Theorem 4], and compute the estimation min v min { ˜ d ( s, v ) + w ( s, v ) | s ∈ S is an ingoing neigh b or of v } by con vergecasting in O ( D ) rounds. If there exists a minimum-w eight cycle C of length at least n 2 / 3 , then with high probability at least one of its v ertices is sampled, and so we get a (1 + ε )-appro ximation. 6 Lo w er Bounds In this section w e presen t new lo wer bounds for distributed girth appro ximation in the CONGEST mo del. Our main low er b ound concerns the directed, un weigh ted setting and sho ws that appro xi- mating the girth within any factor strictly smaller than 3 requires ˜ Ω( n 3 / 5 ) rounds, even on graphs of (undirected) diameter O (log n ). W e later extend this result to any in teger appro ximation factors α , as w ell as to the undirected weigh ted setting. Before presen ting the lo wer b ound constructions, we recall a standard notions from extremal graph theory . Let F b e a family of graphs. A graph is called F -free if it con tains no cop y of a graph in F as a subgraph. A cornerstone of e xtremal graph theory is the study of the T ur an numb er ex ( n, F ), the maximum num b er of edges in an F -free graph on n vertices. Define the Zar ankiewicz numb er z( n, F ) to b e the maxim um num b er of edges in an F -free bipartite graph on n v ertices. Let C k denote a cycle of length k , and let C 0 ) r e quir es ˜ Ω(min( q , m )) r ounds. Pr o of. Alice and Bob lo cally construct their resp ectiv e parts of G according to E A and E B , and sim ulate the girth-approximation algorithm. By Claim 6.1, if E A ∩ E B = ∅ then girth( G ) = 2 q , whereas if E A ∩ E B = ∅ then girth( G ) ≥ 6 q . Since (3 − ε ) · 2 q < 6 q , 25 an y (3 − ε )-appro ximation distinguishes the tw o cases, and hence decides whether E A ∩ E B = ∅ . Th us the algorithm yields a randomized protocol for Set Disjointness with the same round complexit y . By the black-box lo wer b ound applied to the underlying undirected communication net work, an y such proto col requires ˜ Ω(min( q , m )) rounds. W e hav e q = n 2 a . Substituting in to ˜ Ω(min { q , m } ) and using m = Θ( a 3 / 2 ) giv es ˜ Ω min n n a , a 3 / 2 o . Balancing n a = a 3 / 2 yields a = n 2 / 5 , and hence the lo wer b ound is ˜ Ω( n 3 / 5 ). 6.1 The Undirected W eigh ted Construction W e now extend the construction to the undirected weigh ted setting. The vertex set and edge set remain exactly as in the directed case, except that all edges are made undirected and assigned w eights. In this setting, girth( G ) denotes the minimum total weigh t of a cycle. Let ε > 0. W e assign weigh ts as follo ws: • Ev ery pip e edge has w eight 1. • Ev ery input-dep enden t edge has weigh t q ε . • Ev ery shortcut-tree edge (including pip e-to-leaf edges) has w eight 6 q ε . Claim 6.2. 1. If E A ∩ E B = ∅ , then girth( G ) = 2 q ε (1 + ε ) . 2. If E A ∩ E B = ∅ , then girth( G ) ≥ 6 q ε . Pr o of. In tersecting inputs. As in the directed case, if ( l , r ) ∈ E A ∩ E B , there exists a cycle using t wo pip es and t wo input-dep enden t edges. Its total weigh t is 2 q · 1 + 2 · q ε = 2 q ε (1 + ε ) . Disjoin t inputs. Assume E A ∩ E B = ∅ , and let C b e a minim um-weigh t cycle. If C uses any shortcut-tree edge, then w ( C ) ≥ 6 q ε and w e are done. Otherwise, C consists only of pip e and input-dep enden t edges. As in the directed case, pro- jecting C on to H yields a cycle in H . Since H has girth at least 6, C m ust contain at least six input-dep enden t edges. Therefore, w ( C ) ≥ 6 · q ε = 6 q ε . 26 The reduction to a (3 − 3 ε )-appro ximation algorithm follows exactly the same argument as in the directed un weigh ted case, and w e therefore only sketc h it. Assume there exists a (3 − 3 ε )-approximation algorithm for weigh ted girth. By Claim 6.2, in the Yes -instance girth( G ) = 2 q ε (1 + ε ) , while in the No -instance girth( G ) ≥ 6 q ε . Since (3 − 3 ε ) · 2 q ε (1 + ε ) = 6 q ε (1 − ε 2 ) < 6 q ε , suc h an algorithm distinguishes the tw o cases, and the comm unication low er b ound follows as in the directed case. 6.2 General girth approximation The previous construction extends naturally to larger approximation factors. Let k ≥ 2, and let H 2 k = ( L ∪ R, E 2 k ) be a bipartite graph with | L | = | R | = a that con tains no cycle of length less than 2 k and maximizes the num b er of edges. Assuming the Erd˝ os–Simono vits even cycle conjecture, m := | E 2 k | = Θ( a 1+1 / ( k − 1) ) . W e construct the graph G exactly as b efore, replacing H with H 2 k . Cycle structure. In the Yes -instance there exists a directed cycle trav ersing t wo pip es, of length 2 q . In the No -instance, any directed cycle pro jects to a cycle in H 2 k , and therefore must con tain at least 2 k input-dep enden t edges. Hence it trav erses at least 2 k pip es and has length at least 2 k q . Th us distinguishing the tw o cases requires a ( k − ε )-approximation. Optimizing the parameters. The graph contains n = 2 aq vertices, and the low er b ound is ˜ Ω(min( q , m )). Balancing q = m and using m = Θ( a 1+1 / ( k − 1) ) giv es n a = a 1+1 / ( k − 1) Solving yields a = Θ n k − 1 2 k − 1 , q = Θ n k 2 k − 1 W e obtain the following theorem. Theorem 6.2. L et k ≥ 3 and ε > 0 . Assuming the Er d˝ os–Simonovits even cycle c onje ctur e (or unc onditional ly for k ∈ { 3 , 4 , 6 } ), any ( k − ε ) -appr oximation algorithm for girth in the CONGEST mo del r e quir es ˜ Ω n k 2 k − 1 r ounds, even when the (undir e cte d) diameter is O (log n ) . This holds for dir e cte d gr aphs and for undir e cte d weighte d gr aphs. 27 Ev en without assuming the Erd˝ os–Simono vits conjecture, we can plug in the b est known explicit constructions of C 2 k -free bipartite graphs due to Lazebnik–Ustimenko–W oldar [18]. These yield z( a, C 2 k ) = Ω( a 1+ γ k ) for an explicit γ k > 2 3 k . Substituting this b ound into our reduction gives an unconditional round low er b ound ˜ Ω( n 1 / 2+ β k ) for an explicit exp onent β k > 1 6 k , thus strictly impro ving ov er the previously kno wn ˜ Ω( √ n ) b ound. References [1] Rub en Beck er, Sebastian F orster, Andreas Karrenbauer, and Christoph Lenzen. Near-optimal appro ximate shortest paths and transshipment in distributed and streaming mo dels. SIAM J. Comput. , 50(3):815–856, 2021. [2] Aaron Bernstein and Danupon Nanongk ai. Distributed exact w eighted all-pairs shortest paths in near-linear time. In Pr o c e e dings of the 51st A nnual A CM SIGA CT Symp osium on The ory of Computing (STOC ’19) , pages 334–342, 2019. [3] J.A Bondy and M. Simonovits. Cycles of ev en length in graphs. Journal of Combinatorial The ory, Series B , 16(2):97–105, 1974. [4] W. G. Brown. On graphs that do not con tain a thomsen graph. Canadian Mathematic al Bul letin , 9(3):281–285, 1966. [5] Keren Censor-Hillel, Orr Fischer, Tzlil Gonen, F ran¸ cois Le Gall, Dean Leitersdorf, and Rotem Oshman. F ast distributed algorithms for girth, cycles and small subgraphs. In Pr o c e e dings of the 34th International Symp osium on Distribute d Computing (DISC ’20) , pages 33:1–33:17, 2020. [6] Keren Censor-Hillel, P etteri Kaski, Janne H. Korhonen, Christoph Lenzen, Ami Paz, and Jukk a Suomela. Algebraic metho ds in the Congested Clique. Distribute d Comput. , 32(6):461–478, 2019. [7] Yi-Jun Chang, Shang-En Huang, and Hsin-Hao Su. Deterministic expander routing: F aster and more versatile. In Pr o c e e dings of the 43r d ACM Symp osium on Principles of Distribute d Computing (PODC ’24) , pages 194–204, 2024. [8] Shiri Chec hik and Gur Lifshitz. Optimal girth approximation for dense directed graphs. In Pr o c e e dings of the 32nd Annual A CM-SIAM Symp osium on Discr ete Algorithms (SODA ’21) , pages 290–300, 2021. [9] A tish Das Sarma, Stephan Holzer, Liah Kor, Amos Korman, Dan up on Nanongk ai, Gopal P andurangan, David P eleg, and Roger W attenhofer. Distributed verification and hardness of distributed appro ximation. In Pr o c e e dings of the F orty-Thir d Annual ACM Symp osium on The ory of Computing , STOC ’11, page 363–372, New Y ork, NY, USA, 2011. Asso ciation for Computing Mac hinery . [10] Andrew Druck er, F abian Kuhn, and Rotem Oshman. On the p ow er of the Congested Clique mo del. In Pr o c e e dings of the 33r d ACM Symp osium on Principles of Distribute d Computing (PODC ’14) , pages 367–376, 2014. 28 [11] P ´ eter Erd˝ os and Mikl´ os Simonovits. Compactness results in extremal graph theory . Combi- natoric a , 2(3):275–288, September 1982. [12] Pierre F raigniaud, Ma¨ el Luce, F r´ ed´ eric Magniez, and Ioan T o dinca. Deterministic ev en-cycle detection in Broadcast CONGEST. In Pr o c e e dings of the 52nd International Col lo quium on A utomata, L anguages, and Pr o gr amming (ICALP ’25) , pages 80:1–80:19, 2025. [13] Silvio F risc hknech t, Stephan Holzer, and Roger W attenhofer. Ne t works cannot compute their diameter in sublinear time. In Pr o c e e dings of the 23r d A nnual ACM-SIAM Symp osium on Discr ete Algorithms (SODA ’12) , pages 1150–1162, 2012. [14] Zoltan F ¨ uredi, Assaf Naor, and Jacques V erstra¨ ete. On the tur´ an num b er for the hexagon. A dvanc es in Mathematics , 203(2):476–496, 2006. [15] Stephan Holzer and Roger W attenhofer. Optimal distributed all pairs shortest paths and ap- plications. In Pr o c e e dings of the 31st ACM Symp osium on Principles of Distribute d Computing (PODC ’12) , pages 355–364, 2012. [16] Bala Kalyanasundaram and Georg Schnitger. The probabilistic communication complexit y of set in tersection. SIAM J. Discr et. Math. , 5(4):545–557, 1992. [17] Janne H. Korhonen and Jo el Rybic ki. Deterministic subgraph detection in Broadcast CON- GEST. In Pr o c e e dings of the 21st International Confer enc e on Principles of Distribute d Sys- tems (OPODIS ’17) , pages 4:1–4:16, 2017. [18] F elix Lazebnik, V. Ustimenk o, and Andrew W oldar. A new series of dense graphs of high girth. Bul l. AMS , 32, 12 1994. [19] Christoph Lenzen, Boaz Patt-Shamir, and Da vid Peleg. Distributed distance computation and routing with small messages. Distribute d Computing , 32(2):133–157, 2019. [20] Vignesh Manoharan and Vijay a Ramachandran. Near optimal b ounds for replacement paths and related problems in the CONGEST mo del (brief announcemen t). In Pr o c e e dings of the 41st A CM Symp osium on Principles of Distribute d Computing (PODC ’22) , pages 369–371, 2022. [21] Vignesh Manoharan and Vija ya Ramachandran. Computing minimum w eight cycle in the CONGEST mo del. In Pr o c e e dings of the 43r d ACM Symp osium on Principles of Distribute d Computing (PODC ’24) , pages 182–193, 2024. [22] Dan up on Nanongk ai. Distributed appro ximation algorithms for weigh ted shortest paths. In Pr o c e e dings of the 46th Symp osium on The ory of Computing (STOC ’14) , pages 565–573, 2014. [23] Da vid Peleg. Distribute d Computing: A L o c ality-Sensitive Appr o ach . So ciet y for Industrial and Applied Mathematics (SIAM), 2000. [24] Alexander A. Razb oro v. On the distributional complexit y of disjointness. The or. Comput. Sci. , 106(2):385–390, 1992. 29
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment