Centrality-Based Security Allocation in Networked Control Systems
This paper addresses the security allocation problem within networked control systems, which consist of multiple interconnected control systems under the influence of two opposing agents: a defender and a malicious adversary. The adversary aims to ma…
Authors: Anh Tung Nguyen, Andreas Hertzberg, André MH Teixeira
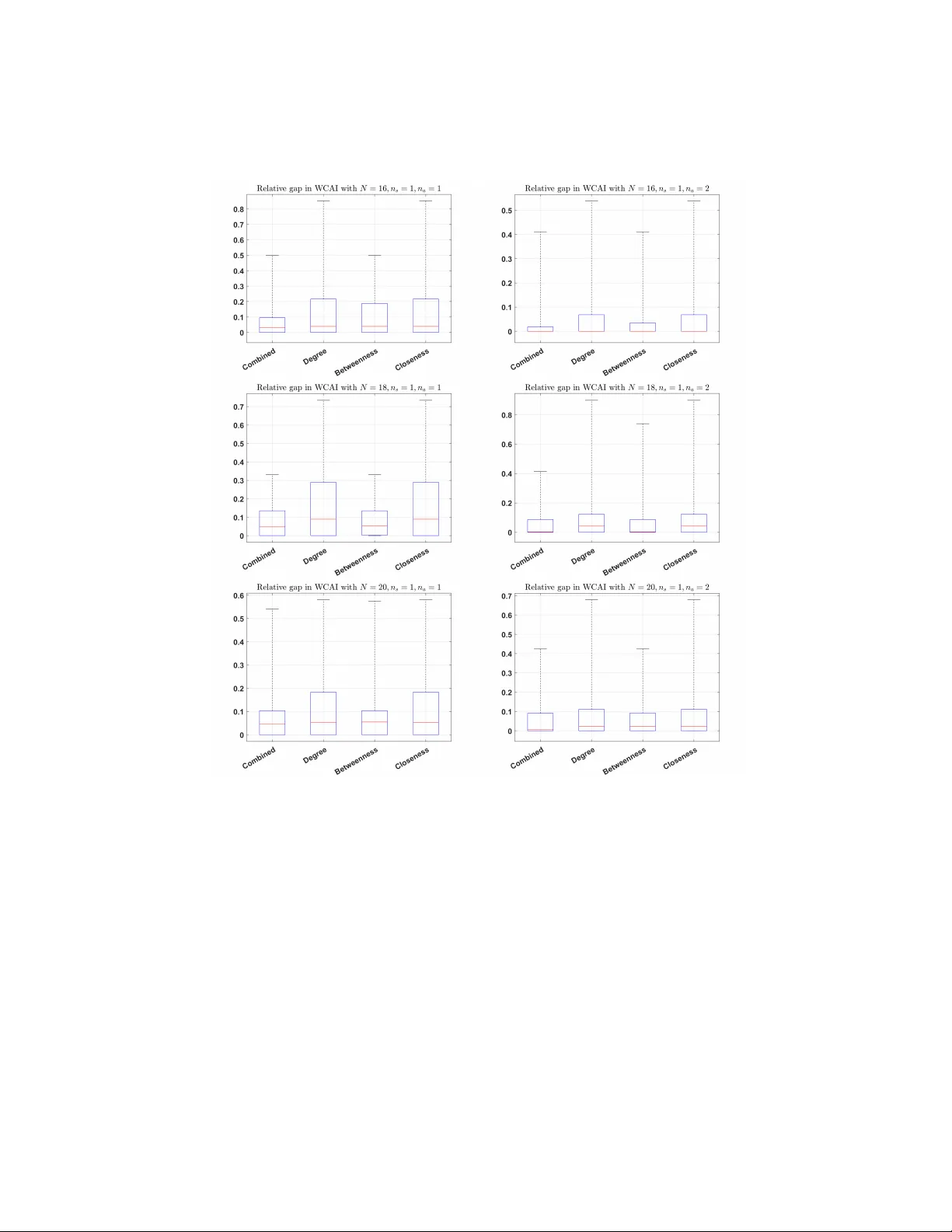
Cen tralit y-based Securit y Allo cation in Net w ork ed Con trol Systems Anh T ung Nguy en [0000 − 0001 − 9316 − 233 X ] , Andreas Hertzb erg, and André M. H. T eixeira [0000 − 0001 − 5491 − 4068] Departmen t of Information T echnology , Uppsala Universit y , PO Box 337, SE-75105, Uppsala, Sweden anh.tung.nguyen@it.uu.se andreas.hertzberg.0811@student.uu.se andre.teixeira@it.uu.se Abstract. This paper addresses the security allo cation problem within net work ed con trol systems, whic h consist of m ultiple interconnected con- trol systems under the influence of t wo opp osing agents: a defender and a malicious adv ersary . The adversary aims to maximize the w orst-case attac k impact on system performance while remaining undetected by launc hing stealthy data injection attacks on one or sev eral in terconnected con trol systems. Con versely , the defender’s ob jective is to allo cate secu- rit y resources to detect and mitigate these worst-case attacks. A no vel cen trality-based approach is prop osed to guide the allocation of securit y resources to the most connected or influential subsystems within the net- w ork. The methodology inv olves comparing the w orst-case attack impact for both the optimal and cen trality-based security allo cation solutions. The results demonstrate that the centralit y measure approach enables significan tly faster allo cation of security resources with acceptable levels of p erformance loss compared to the optimal solution, making it suit- able for large-scale netw orks. The prop osed method is v alidated through n umerical examples using Erdős–Rényi graphs. Keyw ords: Securit y metric · net work ed con trol systems · cen tralit y measures · stealthy attacks · cyb er-ph ysical security . 1 In tro duction Net work ed con trol systems are in tegral to mo dern infrastructure, whic h are prominen tly featured in p ow er grids, transp ortation netw orks, and water distri- bution systems. These systems lev erage op en and widely-used information and comm unication technologies, including the public Internet and wireless commu- nication [3, 8, 24]. Ho wev er, using unprotected wireless communication channels ma y exp ose them to cyb er threats, w hic h can lead to severe financial losses and so cietal disruptions. Notable examples include the Iranian industrial con trol sys- tem, which suffered from the Stuxnet malware in 2010 [3], and the Ukrainian p o w er grid, whic h w as compromised b y the Industro y er malw are in 2016 [8]. 2 Anh T ung Nguyen et al. These incidents underscore the critical imp ortance of bolstering securit y mea- sures within control systems to protect against suc h p oten tially dev astating cyb er attac ks. The issue of cyb ersecurit y has garnered significan t attention from researc hers within the Information T echnology communit y . Solutions in this area are critical for maintaining the core principles of the Confidentialit y , Integrit y , and A v ailabil- it y (CIA) triad for data and IT services. These principles are defined as follo ws: 1) Confidentialit y: ensures that data stored, transmitted, and pro cessed remains priv ate and accessible only to authorized individuals; 2) Integrit y: ensures that data is reliable and cannot b e mo dified by unauthorized means; and 3) A v ail- abilit y: ensures that the system provides timely access to data when requested. Among these, integrit y is particularly emphasized, as any breach directly im- pacts system p erformance [24]. In exploring p otential threats to control systems, Zhang et al. [30] in tro duced the concept of controlled inv ariant subspace, derived from geometric control theory , whic h remains independent of system outputs and nonlinear functions, to prop ose a cov ert attack on certain classes of nonlinear systems. Addressing nonlinear systems presen ts considerable c hallenges, requir- ing attac kers to gain deep system kno wledge and intercept real-time transmitted data. Rather than fo cusing on nonlinear system mo dels, P ark et al. [21] exam- ined p otential threats in linear systems with uncertain ties. By thoroughly ana- lyzing system dynamics and con ven tional anomaly detection mechanisms, these sophisticated stealthy data injection attac ks significan tly disrupt control systems without b eing detected. This highlights the n eed for more adv anced detection metho ds. Least squares-based fusion tec hniques are widely employ ed to identify and mitigate the harmful effects of false data injection attacks on state estima- tion [10, 11]. Physical watermarking, initially designed to detect replay attacks, has b een adapted to signal the presence of false data injection attacks [15]. Re- cen t adv ancements ha ve further reduced the av erage detection delay time [16]. Ho wev er, physical watermarking can increase control costs and reduce actuator lifespan in con trol systems. Multiplicative watermarking [4, 5, 25] offers an effec- tiv e solution to these challenges. A dditionally , reallo cating defensive resources can help mitigate the adverse effects of attack ers [1], enhancing the system’s re- silience against stealthy false data injection attac ks. Nev ertheless, it is imp ortan t to ac knowledge that con temp orary in telligent adversaries can learn and adapt to these mitigation strategies, refining their attack metho ds to maintain stealth. Therefore, this pap er emphasizes the need for a comprehensive inv estigation of net work ed control systems under the influence of stealthy false data injection attac ks. Up on review of the abov e existing studies [1, 4, 5, 10, 11, 15, 16, 21, 25, 30], it b ecomes evident that the literature has primarily fo cused on secure estimation and control from the viewp oin t of either the defender or the adversary . Ho w- ev er, it is imp ortan t to ac knowledge that b oth parties encoun ter simil ar chal- lenges. While the defender confronts resource limitations in countering malicious activities, the adversary also faces energy constrain ts during attac k execution. Therefore, it is highly p ertinen t to address this matter within a comprehensive Cen trality-based Securit y Allo cation 3 framew ork that encompasses both the defender and the adversary . F ortunately , the security allo cation problem b et ween the defender and the malicious adver- sary fits w ell within the framework of game theory , which is one of the most efficien t frameworks addressing the challenge of optimal decision-making among non-co operative parties [2]. In an attempt to apply game theory to deal with the securit y allo cation problem, the authors in [9] seek the Stack elb erg equilibrium b y form ulating the optimization problems in [9, Theorem 3.3] where all the at- tac k scenarios are considered in their constraints. T o solve those optimization problems in [9, Theorem 3.3], the authors use a linear mapping from action space to the game pa yoff (see more in [9, Section II I.B]), remo ving the complexity of computing game pay off. In the same line with [9], the authors in [29] also s eek the Stack elb erg equilibrium b y considering all the attac k scenarios in [29, The- orem 1]. The study in [22] has a similar game setup to ours where the defender and the adversary hav e discrete action spaces. They also conduct the traditional bac kward induction to find the Stac kelberg equilibrium [22, Algorithm 1]. T o b e able to proceed with the algorithm, the authors in [22] need to inv estigate all the p ossible action scenarios shown in [22], resulting in a v ery high computa- tional cost [22, Section V]. Although not considering a Stack elberg game setting, the authors in [14, 27] tackle an analogous problem. The authors in [27] find the Ba yesian game equilibrium through solving an optimization problem [27, Section VI.A] where the game pay off matrix is employ ed in its constrain t. Clearly , build- ing up the game pay off matrix enumerates all the action scenarios [27, T ables 1 and 2]. Although the problem in [14] is not clearly form ulated as a game b et ween a defender and an adv ersary , the authors discuss the m utual formulation betw een theirs and a zero-sum game setting in [14, Section IV.B]. The authors in [14] find the optimal action for the operator, who has the same role as the defender in our w ork, through solving an optimization problem in [14, Section I I I.C] where they consider all the p ossible actions in disc rete action spaces. F urther, many other concepts of games describing netw ork ed systems sub jected to cyb er attac ks such as matrix games [17–19, 22, 27], dynamic games [7], and sto chastic games [13] ha ve b een studied. In summary , the consideration of all the action scenarios re- mains in recent studies [9, 14, 22, 27, 29]. P articularly , the authors in [9, 14, 29] deal with security problems by solving a single large optimization problem that addresses all the action scenarios. As a consequence, the computation in those existing studies is considerably hea vy . W e aim to address such an issue in this study . In this pap er, we consider a contin uous-time netw ork ed control system, asso- ciated with an undirected connected graph, inv olving tw o strategic agen ts: a de- fender and a malicious adv ersary . The system consists of m ultiple interconnected subsystems, referred as to vertices. The aim of the adv ersary is to maximally disrupt the global p erformance of the netw ork without b eing detected by the defender. Meanwhile, the defender selects several monitor vertices to measure their outputs with the purp ose of alleviating the attack impact. T o assist the defender in allo cating the defense resources, we adopt centralit y measures in- cluding degree, b etw eenness, and closeness cen trality measures to seek the most 4 Anh T ung Nguyen et al. p oten tial monitor v ertices. This approach enables us to solve less complicated optimization problems, massiv ely alleviating the computational cost compared to finding the optimal solution. Notation: the set of real p ositiv e num bers is denoted as R + ; R n and R n × m stand for sets of real n -dimensional vectors and n -ro w m -column matrices, re- sp ectiv ely . A v ector with the i -th elemen t set to one and the other elemen ts set to zero is denoted e i ∈ R n . A p ositiv e definite matrix A and a p ositiv e semi- definite matrix B are denoted as A ≻ 0 and B ⪰ 0 , resp ectively . The notations A ≺ 0 and B ⪯ 0 stand for − A ≻ 0 and − B ⪰ 0 , resp ectiv ely . The space of square-in tegrable functions is defined as L 2 ≜ f : R + → R | ∥ f ∥ 2 L 2 [0 , ∞ ] < ∞ and the extended space be defined as L 2 e ≜ f : R + → R | ∥ f ∥ 2 L 2 [0 ,T ] < ∞ , ∀ 0 < T < ∞ . The notation ∥ x ∥ 2 L 2 is used as shorthand for the norm ∥ x ∥ 2 L 2 [0 ,T ] ≜ 1 T R T 0 ∥ x ( t ) ∥ 2 2 d t if the time horizon [0 , T ] is clear from the con- text. Let G ≜ ( V , E , A ) b e an undirected graph with the set of N v ertices V = { 1 , 2 , ..., N } , the set of edges E ⊆ V × V , and the adjacency matrix A = [ a ij ] . F or an y ( i, j ) ∈ E , i = j , the element of the adjacency matrix a ij is p ositiv e, and with ( i, j ) / ∈ E or i = j , a ij = 0 . The degree of v ertex i is denoted as ∆ i = P n j =1 a ij and the degree matrix of graph G is defined as ∆ = diag ∆ 1 , ∆ 2 , . . . , ∆ N , where diag stands for a diagonal matrix. The Laplacian matrix is defined as L = [ ℓ ij ] = ∆ − A . F urther, G is called an undi- rected connected graph if and only if matrix A is symmetric and the algebraic m ultiplicity of zero as an eigenv alue of L is one. The set of all neighbours of v ertex i is denoted as N i = { j ∈ V | ( i, j ) ∈ E } . 2 Problem Description In this section, we present the mathematical description of a netw orked control system under cyb er attac ks. Then, the purposes and resources of the adversary and the defender are in tro duced. 2.1 Net work ed control systems under false data injection attac ks Consider a netw orked con trol system asso ciated with an undirected connected graph G ≜ ( V , E , A ) with N vertices where every vertex i is describ ed by the one-dimensional state-space mo del: ˙ x i ( t ) = u i ( t ) , i ∈ { 1 , 2 , . . . , N } , (1) where x i ( t ) ∈ R represents the state v ariable of vertex i , and u i ( t ) ∈ R denotes the con trol input for the same vertex. The state of the en tire netw ork will b e denoted as x ( t ) ≜ [ x 1 ( t ) , x 2 ( t ) , . . . , x N ( t )] ⊤ ∈ R N . The con trol la w for eac h v ertex is: u i ( t ) = X j ∈ N i a j i ( x j ( t ) − x i ( t )) , ∀ i ∈ V . (2) Cen trality-based Securit y Allo cation 5 By applying the con trol law (2) to the state-space mo del (1) for the en tire net work, one obtains the following closed-lo op mo del (3) without attacks: ˙ x ( t ) = − Lx ( t ) , (3) where L is a Laplacian matrix represen ting the graph G . When the system is in the presence of a malicious adversary , w e assume that the adversary selects a set of vertices to launch false data injection attacks (says ζ ( t ) ). Let the set of attack v ertices b e denoted as A ≜ { a 1 , a 2 , . . . , a n a } for a giv en attac k budget n a = |A| . It is worth noting that there is no benefit of c ho osing fewer attack v ertices than the budget and therefore we ignore the case of |A| < n a . The N -dimensional binary v ector B ( A ) ∈ { 0 , 1 } N stands for the c hosen attac k v ertices where its i -th elemen t B ( A ) i = 1 if i -th v ertex is attack ed and B ( A ) i = 0 otherwise. Then, the netw ork ed con trol system (3) under false data injection attac ks can b e rewritten as follo ws: ˙ x ( t ) = − Lx ( t ) + B ( A ) ζ ( t ) . (4) Let us mak e use of the following assumption. Assumption 1 The networke d c ontr ol system (4) is at its e quilibrium x e = 0 b efor e b eing affe cte d by attack signals. In the following parts, the netw ork p erformance and the purp oses of the adver- sary and the defender will b e describ ed in more detail. 2.2 Net work p erformance and monitoring In the net work ed control system, the ov erall p erformance of the system is the col- lectiv e p erformance of all vertices in the system. Consequently , the cost function for the system p erformance can b e denoted as: J = X i ∈ V ∥ y i ∥ 2 L 2 , (5) y i ( t ) = e ⊤ i x ( t ) , ∀ i ∈ V . (6) The securit y challenge against the malicious adversary stems from the assumed budget limitation within the system, making it necessary to select a subset of v ertices to monitor for the residual signal since it is not feasible to monitor all v ertices. This security resource constrain t enforces the defender chooses a subset of the v ertex set V to serv e as the monitor set M = { m 1 , m 2 , . . . , m n s } for a given sensor budget n s = |M| . The outputs of the monitor vertices can b e written as follo ws: y m k ( t ) = e ⊤ m k x ( t ) , ∀ m k ∈ M . (7) By monitoring outputs (7), the defender can notify the presence of the adversary if the energy of the monitor outputs crosses a given alarm threshold δ , i.e., ∥ y m k ∥ 2 L 2 > δ. (8) 6 Anh T ung Nguyen et al. Remark 1 In this p ap er, we assume that the alarm thr eshold δ is given by the op er ator, which c annot b e alter e d by the defender. Ther efor e, the pr oblem of cho osing the alarm thr eshold is not c onsider e d in this study. Inste ad, the defender is al lowe d to cho ose vertic es, which have their given c orr esp onding alarm thr esh- olds, to monitor their outputs with the purp ose of dete cting malicious activities. 2.3 The purp oses of adv ersary and defender In the following, we first present the purp ose of the adv ersary . Then, the purpose of the defender defender is in tro duced. The purp ose of the malicious adv ersary is to maximize the negativ e im- pact on the system p erformance, i.e., the adversary seeks to maximize the cost function J in (5). F urthermore, there are strong arguments as to why the ma- licious adv ersary simultaneously would seek to remain stealth y to the defender, (see the discussion in [27, Section II-E]). One can assume that the defender w ould quickly mitigate the attack when detected b y shutting down the mali- ciously affected communication channels. This means there will b e no pay off for the adversary , additionally one can assume that the malicious adv ersary has in- v ested resources to obtain system kno wledge and to infiltrate the system, which will most likely b e lost when detected. Therefore, to a v oid losing the inv est- men t the adversary has made, this pap er considers that the malicious adversary conducts stealth y data injection attacks, which will be defined in the following. Let us consider the netw ork ed control system under cyb er attacks (4) and the monitor outputs (7). The false data injection attack ζ ( t ) in (4) is called a stealth y false data injection attac k if, and only if, the monitor outputs ∥ y m k ∥ 2 L 2 < δ for all m k ∈ M . If at least one monitor vertex m k ∈ M do es not satisfy this, the attac k from the malicious adversary is detected. A dditionally , a realistic assumption is that the adversary has finite resources not only in the n umber of attack vertices but also in the energy of the attack signals. In more detail, let us denote a positive num ber A e as the maxim um attac k energy of the attack signal ζ ( t ) for a given time horizon [0 , T ] , i.e. ∥ ζ ∥ 2 L 2 [0 ,T ] ≤ A e . (9) The purp ose of the defender is to allo cate securit y resources given the p oten tial existence of a malicious adversary that seeks to negatively impact the system’s p erformance. How ev er, a realistic assumption is that the defender is unable to foresee the action of the adversary . Therefore, the defender needs to form ulate a defense strategy without knowing the attack strategy . An approach that has not b een considered in existing literature, is the utilization of centralit y measures to select monitor v ertices in the netw orked control system. This ap- proac h will b e utilized and presen ted more thoroughly in the following sections. 3 Risk analysis and ev aluation Giv en the netw orked control system under cyb er attacks outlined in (4), the net work performance (5), and the monitor outputs (7), the attack set A , and Cen trality-based Securit y Allo cation 7 the monitor set M , the worst-case attack impact (WCAI) on the netw ork per- formance is form ulated as follows: J ( A , M ) = sup ζ ∈ L 2 e X i ∈ V ∥ y i ∥ 2 L 2 s.t. ∥ y m k ∥ 2 L 2 < δ, ∀ m k ∈ M , ∥ ζ ∥ 2 L 2 ≤ A e , (4) , (6) , (7) , x (0) = 0 . (10) The following theorem presents the boundedness of the non-conv ex optimization problem (10) and its computation. Theorem 1 The worst-c ase imp act of ste althy FDI attacks is always b ounde d and c ompute d by the fol lowing semi-definite pr o gr amming (SDP) pr oblem. J ( A , M ) = min P = P ⊤ ⪰ 0 , β > 0 , γ m k > 0 A e β + δ X m k ∈ M γ m k (11) s.t. − LP − P L P B ( A ) B ( A ) ⊤ P − β + X i ∈ V e ⊤ i 0 e i 0 − X m k ∈ M γ m k e ⊤ m k 0 e m k 0 ⪯ 0 . ◁ Pr o of. The net work ed control system (4) is stable due to the fact that matrix − L is negativ e semi-definite. Meanwhile, the attac k input ζ has bounded energy . As a result, the output p erformance y i also has b ounded energy for all i ∈ V , leading to the b oundedness of (10). Next, the computation of (10) is shown. Let us consider the dual form of (10) describ ed in the following: inf γ k > 0 , β > 0 sup ζ ∈ L 2 e X i ∈ V ∥ y i ∥ 2 L 2 + X m k ∈M γ k δ − ∥ y m k ∥ 2 L 2 + β A e − ∥ ζ ∥ 2 L 2 (12) s.t. (4) , (6) , (7) , x (0) = 0 . The dual form (12) is b ounded if, and only if, X i ∈ V ∥ y i ∥ 2 L 2 − X m k ∈M γ k ∥ y m k ∥ 2 L 2 − β ∥ ζ ∥ 2 L 2 ≤ 0 , ∀ ζ ∈ L 2 e , x (0) = 0 . (13) As a result, the dual form can b e rewritten as follows: J ( A , M ) = inf γ k > 0 , β > 0 δ X m k ∈M γ k + A e β (14) s.t. X i ∈ V ∥ y i ∥ 2 L 2 − X m k ∈M γ k ∥ y m k ∥ 2 L 2 − β ∥ ζ ∥ 2 L 2 ≤ 0 , (4) , (6) , (7) , x (0) = 0 . 8 Anh T ung Nguyen et al. Recalling the key results in dissipativ e system theory for linear systems [26] with a non-negative storage function V ( x ) = x ( t ) ⊤ P x ( t ) where P = P ⊤ ⪰ 0 and a supply rate s ( · , · ) = P m k ∈M γ k ∥ y m k ∥ 2 L 2 + β ∥ ζ ∥ 2 L 2 − P i ∈ V ∥ y i ∥ 2 L 2 , the optimization problem (14) can b e computed by the SDP (11). ■ Giv en that the adversary seeks to maximize the worst-case attack impact on the system, the defender selects a monitor set to minimize the worst-case attack impact. In practice, the defender seldom foresees when the adv ersary attacks the system. Thus, the defender should make a decision on their defense strategy b efore the adversary do es. As a result, the optimal security allo cation can b e form ulated as the following minimax optimization problem: min M , |M| = n s max A , |A| = n a J ( A , M ) . (15) The ab o v e optimal security allo cation can b e rewritten as follows: min M , |M| = n s Q s.t. J ( A , M ) ≤ Q, ∀ A , |A| = n a . (16) In the next section, we discuss how to compute (16) and its approximate solution based on cen trality measures. 4 Securit y Allocation This section outlines the metho dology employ ed in this pap er, encompassing all metho ds and approaches utilized to deriv e the results. The nov el approac h of selecting the monitoring set M utilizing centralit y measures, and the approach of assessing monitoring sets. 4.1 Optimal security allo cation Inspired b y our previous w ork [20, Proposition 1], the defender is able to find the optimal security allo cation by solving the combinatorial problem (16). The follo wing theorem states the computation of the optimization problem (16). Theorem 2 F or e ach attack set A , let us denote a tuple variable ( ¯ z A , P A ) ∈ R N × S N c orr esp ondingly. Denote an N -dimensional binary ve ctor z M ∈ { 0 , 1 } N as a r epr esentation of the monitor set M wher e m -entry of z M b eing e qual to 1 indic ates that m -th no de b elongs to M . Supp ose that the adversary finds an attack set A such that it maximizes the worst-c ase imp act of ste althy FDI attacks (10) . Then, the optimal se curity al lo c ation (16) is determine d by z ⋆ M which is the solution to the fol lowing mixe d-inte ger SDP pr oblem: min ¯ z A ∈ R N , z M ∈{ 0 , 1 } N , P A = P ⊤ A ⪰ 0 , β > 0 , Q > 0 Q (17) s.t. 1 ⊤ N z M = n s , δ 1 ⊤ N ¯ z A + A e β ≤ Q, 0 ≤ ¯ z A ≤ ˜ M z M , |A| = n a , − L ⊤ P A − P A L P A B ( A ) B ( A ) ⊤ P A − β A + diag I 0 − diag ¯ z A 0 ≤ 0 , ∀ A , Cen trality-based Securit y Allo cation 9 wher e 1 N is an N -dimensional al l-one ve ctor, n s is the sensor budget, n a is the attack budget, δ is the given alarm thr eshold, A e is the maximum attack ener gy, and ˜ M is a given lar ge p ositive numb er, also c al le d a “big M" [ ? ]. Pr o of. The pro of directly follows [20, Proposition 1]. ■ 4.2 Cen trality-based securit y allo cation The methodology of selecting monitor sets based on the cen trality measures in- cluding degree, b etw eenness, and closeness centralit y relies on the idea that the most connected or influential v ertices in the graph would b e the most suitable monitor vertices. Therefore, we create all p ossible monitor sets for eac h cen tral- it y measure giv en the monitor budget n s . Then, we deriv e the total centralit y for eac h monitor set by summing up the calculated centralit y measure for eac h ver- tex. Finally , we select the monitor set with the highest total centralit y according to the sp ecific centralit y measure. Given the sensor budget, this ensures that the v ertices with the highest cen trality are selected as the monitor set. This pro cess, while straigh tforward, often results in duplicate solutions where different monitor sets may hav e the same total centralit y . F or example, if the sensor budget is tw o and there are three vertices with the highest and identical centralit y , there must b e multiple monitor sets with the same highest total centralit y . In these cases, all monitor sets are ev aluated by solving (11) and selecting the monitor set with the smallest WCAI. This metho d is applied to all three centralit y measures whic h are degree cen trality , closeness cen trality , and b et weenness centralit y measures. Let us make use of the following definition of the ab o ve-men tioned centralit y measures. Definition 1 (Cen tralit y measures [6]) Given a gr aph G ≜ ( V , E , A ) and d ( i, j ) as the shortest p ath fr om no de i to no de j , the de gr e e c entr ality me asur e of no de i ∈ V , denote d as C D ( i ) , is the total numb er of c onne ctions b etwe en no de i and its neighb ors, i.e., C D ( i ) ≜ ∆ i = X j ∈ N i a ij . (18) The closeness c entr ality me asur e of no de i ∈ V , denote d as C C ( i ) , is the inverse- aver age shortest p ath length fr om the vertex to al l the other vertic es, i.e., C C ( i ) ≜ N − 1 P j = i d ( i, j ) . (19) The b etwe enness c entr ality me asur e of no de i ∈ V , denote d as C B ( i ) , is the numb er of shortest p aths that p ass thr ough vertex i of inter est among al l shortest p aths b etwe en p airs of vertic es in the gr aph, i.e., C B ( i ) ≜ X s = i = t σ st ( i ) σ st , (20) wher e σ st is the total numb er of shortest p aths fr om vertex s to t and σ st ( i ) is the numb er of shortest p aths fr om vertex s to t that p ass thr ough vertex i . 10 Anh T ung Nguy en et al. Moreo ver, a combined centralit y measure approach is considered where the three monitor sets (obtained from the respective centralit y metrics) are first compared to each other, and the one with the smallest W CAI is selected and then compared with the optimal solution. The combined method allows us to ascertain if utilizing only one of these centralit y measures would generally give a larger gap to the optimal solution than using all three and alw ays picking the b est one. Let us denote the set of monitoring vertices founded b y degree centralit y mea- sure as z d M , closeness centralit y measure as z c M , b et weenness centralit y measure as z b M , combined centralit y measure as z o M . After we obtain the set of moni- toring vertices that has the highest centralit y measures, denoted z † M ∈ { 0 , 1 } N where † ∈ { d, c, b, o } , we can compute the worst-case impact of stealthy FDI attac ks b y replacing the kno wn v alue z † M with the binary v ariable z M in (17). It is worth noting that the optimization problem (17) with z † M is an SDP problem and can b e solved muc h faster than the mixed-integer version presented in (17) with z M as a binary v ariable. 5 Results This section describ es the empirical resu lts of centralit y measure-based security allo cation in net work ed control systems. In the first part, we show exp erimen tal results on Erdős–Rén yi random graphs where an edge is included to connect t wo vertices with a probability of 0.5. In the second part, w e present how the cen trality measure assists the securit y allo cation in an IEEE benchmark for p o w er systems (IEEE 14-bus system). 5.1 Erdős–Rén yi random graphs All the exp erimen ts w ere p erformed using Matlab 2023b with Y ALMIP 2021 [12] and MOSEK solver on a p ersonal computer with 2.9-GHz, 8-core In tel i7-10700 pro cessor and 16 GB of RAM. Due to the limited hardware, the size of netw orks is restricted from 10 to 20 . It is w orth noting that not only the size of the netw ork influence the complexity of the security allo cation problem (17), but the attack scenarios also significantly contribute to its complexity . More specifically , giv en the attac k budget n a , the n umber of attack scenarios is computed b y N n a , significan tly scaling up with the netw ork size and the attack budget. Therefore, w e limit our exp erimen t to the netw ork size N = { 10 , 12 , 14 , 16 , 18 , 20 } , the attac k budget n a = { 1 , 2 } , and the monitor budget n s = 1 . F or each net work size, w e did the exp erimen t with 30 Erdős–Rényi random graphs. The exp erimen tal results are shown in Figures 1-2 for the relative gaps in W CAI and Figures 3-4 for the relative gaps in solving time. As seen in Figure 1, monitor sets chosen based on com bined centralit y and b et weenness centralit y measures perform v ery w ell where their median and 75 p ercentile v alues are k ept under 10%. In particular, 75 p ercentile v alues of the combined cen trality Cen trality-based Securit y Allo cation 11 measure in case of 2 attac k budget stay at zero. Regarding solving tim e in Fig- ure 3, security allo cation based on com bined cen trality measures reduces around 70% solving time while the other centralit y measures decrease approximately 90% solving time compared with solving the optimal v alue. When we increase the size of the netw ork up to 20 depicted in Figure 2, the relative gaps in WCAI increase in all cen trality measures, particularly degree and closeness ce n tralit y measures. Ho wev er, the num b ers for combined centralit y and b et weenness cen- tralit y measures are still kept under 15%. The relative gaps in solving time are almost the same in the case of smaller netw orks (see Figure 4). 12 Anh T ung Nguy en et al. Fig. 1: Relative gap of the w orst-case attack impact b et ween the optimal v alue and the v alue given by choosing monitor vertices based on centralit y measures. The netw ork size N = { 10 , 12 , 14 } , the attac k budget n a = { 1 , 2 } , and the monitor budget n s = 1 . F or eac h netw ork size, 30 Erdős–Rén yi random graphs where an edge is included to connect t wo vertices with a probabilit y of 0.5. Cen trality-based Securit y Allo cation 13 Fig. 2: Relative gap of the w orst-case attack impact b et ween the optimal v alue and the v alue given by choosing monitor vertices based on centralit y measures. The netw ork size N = { 16 , 18 , 20 } , the attac k budget n a = { 1 , 2 } , and the monitor budget n s = 1 . F or eac h netw ork size, 30 Erdős–Rén yi random graphs where an edge is included to connect t wo vertices with a probabilit y of 0.5. 14 Anh T ung Nguy en et al. Fig. 3: Relativ e gap of the solving time betw een the optimal v alue and the v alue giv en b y c ho osing monitor v ertices based on centralit y measures. The netw ork size N = { 10 , 12 , 14 } , the attack budget n a = { 1 , 2 } , and the monitor budget n s = 1 . F or each netw ork size, 30 Erdős–Rén yi random graphs where an edge is included to connect t wo vertices with a probability of 0.5. 5.2 IEEE 14-bus system In this part, we did an exp eriment on an IEEE b enc hmark of p o wer systems whic h is the IEEE 14-bus system, depicted in Figure 5. The system includes 14 buses and 20 transmission lines. The b eha vior of a bus i ∈ { 1 , 2 , . . . , 14 } can b e Cen trality-based Securit y Allo cation 15 Fig. 4: Relativ e gap of the solving time betw een the optimal v alue and the v alue giv en b y c ho osing monitor v ertices based on centralit y measures. The netw ork size N = { 16 , 18 , 20 } , the attack budget n a = { 1 , 2 } , and the monitor budget n s = 1 . F or each netw ork size, 30 Erdős–Rén yi random graphs where an edge is included to connect t wo vertices with a probability of 0.5. describ ed by the so-called swing equation [23]: I i ¨ θ i ( t ) + D i ˙ θ i ( t ) = − X j ∈N i P ij ( t ) , (21) where I i and D i are the inertia and damping co efficien ts, resp ectiv ely , and P ij is the active p o w er flo w from bus j to bus i . Considering that there are no pow er 16 Anh T ung Nguy en et al. losses and V i = | V i | e j p i ( j 2 = − 1) and θ i b e the complex v oltage and the phase angle of the bus i , resp ectiv ely . The activ e p o w er flo w P ij ( t ) from bus j to bus i is giv en by P ij ( t ) = − ℓ ij sin( θ i − θ j ) , (22) where − ℓ ij ∈ R + is the susceptance of the p o wer transmission line conn ecting bus i with bus j . Those parameters consisting of line susceptance − ℓ ij , inertia I i , and damping D i can b e found at [28] and are listed in T able 1. Since the phase angles usually are close, w e can linearize (22) and rewrite the dynamics (21) of bus i as follo ws I i ¨ θ i ( t ) + D i ˙ θ i ( t ) = X j ∈N i ℓ ij θ i ( t ) − θ j ( t ) , (23) whic h can b e rewritten as follo ws: d d t ˙ θ ( t ) θ ( t ) = 0 I − I − 1 L − I − 1 D ˙ θ ( t ) θ ( t ) , (24) where ˙ θ ( t ) = [ ˙ θ 1 ( t ) , ˙ θ 2 ( t ) , . . . , ˙ θ N ( t )] ⊤ , θ ( t ) = [ θ 1 ( t ) , θ 2 ( t ) , . . . , θ N ( t )] ⊤ . F urther, L is a Laplacian matrix representing the netw ork, I = diag ( I i ) , and D = diag ( D i ) . By applying the computation of centralit y measures in the previous section, w e found that the bus n umber 4 alwa ys has the highest v alue. Ho wev er, the optimal v alue computed b y (17) giv es us the optimal bus n umber 2 . Next, we compare the WCAI of all the monitor buses depicted in Figure 6. W e observ e that the relative gap in W CAI of the bus num ber 4 compared to the optimal bus 2 is under 2%, an acceptable v alue. Meanwhile, the other buses provide muc h higher relativ e gaps, for example, bus 8 gives us 10% relative gap. Cen trality-based Securit y Allo cation 17 Fig. 5: IEEE 14-bus system. Susceptance Inertial Damping − ℓ 12 = 8 . 2838 I 1 = 1 . 060 D 1 = 0 − ℓ 15 = 31 . 2256 I 2 = 1 . 045 D 2 = 4 . 98 − ℓ 23 = 27 . 7158 I 3 = 1 . 010 D 3 = 12 . 72 − ℓ 24 = 24 . 6848 I 4 = 1 . 019 D 4 = 10 . 33 − ℓ 25 = 24 . 3432 I 5 = 1 . 020 D 5 = 8 . 78 − ℓ 34 = 23 . 9442 I 6 = 1 . 070 D 6 = 14 . 22 − ℓ 45 = 5 . 8954 I 7 = 1 . 062 D 7 = 13 . 37 − ℓ 47 = 29 . 2768 I 8 = 1 . 090 D 8 = 13 . 36 − ℓ 49 = 77 . 8652 I 9 = 1 . 056 D 9 = 14 . 94 − ℓ 56 = 35 . 2828 I 10 = 1 . 051 D 10 = 15 . 10 − ℓ 6 , 11 = 35 . 2828 I 11 = 1 . 057 D 11 = 14 . 79 − ℓ 6 , 12 = 35 . 8134 I 12 = 1 . 055 D 12 = 15 . 07 − ℓ 6 , 13 = 18 . 2378 I 13 = 1 . 050 D 13 = 15 . 16 − ℓ 78 = 24 . 6610 I 14 = 1 . 036 D 14 = 16 . 04 − ℓ 79 = 15 . 4014 − ℓ 9 , 10 = 11 . 8300 − ℓ 9 , 14 = 37 . 8532 − ℓ 10 , 11 = 26 . 8898 − ℓ 12 , 13 = 27 . 9832 − ℓ 13 , 14 = 48 . 7228 T able 1: P arameters of the IEEE 14-bus system. 18 Anh T ung Nguy en et al. Fig. 6: Relative gap of the w orst-case attack impact b et ween the optimal v alue and the v alue giv en b y choosing a monitor v ertex based on centralit y measures (blue dot at bus 4). 6 Conclusion In conclusion, w e explored the securit y allo cation problem within a netw orked con trol system featuring tw o opp osing agents: a defender and a malicious adver- sary . The adv ersary aims to maximize the WCAI on the net work p erformance while remaining undetected, by launching stealth y data injection attac ks. Con- v ersely , the defender’s ob jective is to allo cate security resources to minimize the W CAI. The prop osed approac h was centralit y measures-based securit y allo cation using degree, betw eenness, and closeness centralit y , in addition to a combined cen trality measure approach using all three. The conclusion one can draw from this study is that the com bined approac h, although it could only perform as w ell as the b est monitor set derived using the three cen trality measures for eac h graph, outp erformed them on av erage across the 30 Erdős–Rén yi random graphs (a probability of 0.5) with 10 to 20 vertices considered in this pap er. This ap- proac h can b e utilized for securit y allo cation in net works if the relative gap of 10% in terms of W CAI to the optimal solution is acceptable. W e can also con- clude that b ecause the solver times are significantly shorter for the combined cen trality measure approac h than computing the optimal solution, this method is adv antageous when hardw are capabilities are limited. A dditionally , among the three centralit y measures in vestigated, the b et w eenness centralit y p erformed the b est. Similar to the com bined cen tralit y measure approac h, w e can conclude that b et weenness cen trality can b e utilized for the security allo cation in net- w orks derived using Erdős–Rényi random graphs (a probability of 0.5) with 10 to 20 vertices. Moreov er, the solver time for only using b et weenness centralit y is a third or shorter than the com bined approach. A ckno wledgmen ts. This work is supp orted by the Swedish Research Council under the grant 2021-06316 and b y the Sw edish F oundation for Strategic Research. Cen trality-based Securit y Allo cation 19 References 1. Anand, S.C., T eixeira, A.M.H., Ahlén, A.: Risk assessment and optimal allo cation of security measures under stealth y false data injection attac ks. In: 2022 IEEE Conference on Control T echnology and Applications (CCT A). pp. 1347–1353. IEEE (2022). https://doi.org/10.1109/CCTA49430.2022.9966025 2. Başar, T., Olsder, G.J.: Dynamic nonco operative game theory . SIAM (1998) 3. F alliere, N., Murc hu, L.O., Chien, E.: W32. stuxnet dossier. White pap er, Symantec Corp., Security Resp onse 5 (6), 29 (2011) 4. F errari, R.M.G., T eixeira, A.M.H.: A switching multiplicativ e watermarking sc heme for detection of stealthy cyb er-attac ks. IEEE T ransactions on Automatic Con trol 66 (6), 2558–2573 (2020). https://doi.org/10.1109/TAC.2020.3013850 5. Gallo, A.J., Anand, S.C., T eixeira, A.M.H., F errari, R.M .: Design of multiplica- tiv e watermarking against cov ert attac ks. In: 2021 60th IEEE Conference on De- cision and Con trol (CDC). pp. 4176–4181. IEEE (2021). https://doi.org/10. 1109/CDC45484.2021.9683075 6. Golb ec k, J.: Netw ork structure and measures. In: Analyzing the Social W eb, c hap. 3, pp. 25–44. Newnes (2013) 7. Gupta, A., Langb ort, C., Başar, T.: Dynamic games with asymmetric information and resource constrained play ers with applications to security of cyb erphysical systems. IEEE T ransactions on Con trol of Net work Systems 4 (1), 71–81 (2016). https://doi.org/10.1109/TCNS.2016.2584183 8. Kshetri, N., V oas, J.: Hac king p ow er grids: A current problem. Computer 50 (12), 91–95 (2017). https://doi.org/10.1109/MC.2017.4451203 9. Li, Y., Shi, D., Chen, T.: F alse data injection attacks on net work ed control systems: A stack elberg game analysis. IEEE T ransactions on Automatic Control 63 (10), 3503–3509 (2018). https://doi.org/10.1109/TAC.2018.2798817 10. Li, Z., Mo, Y.: Secure distributed dynamic state estimation against sparse in tegrity attac k via distributed conv ex optimization. IEEE T ransactions on Automatic Con- trol 69 (9), 6089–6104 (2024). https://doi.org/10.1109/TAC.2024.3397158 11. Li, Z., Nguy en, A.T., T eixeira, A.M., Mo, Y., Johansson, K.H.: Secure state esti- mation with async hronous measurements against malicious measuremen t-data and time-stamp manipulation. In: 2023 62nd IEEE Conference on Decision and Control (CDC). pp. 7073–7080. IEEE (2023). https://doi.org/10.1109/CDC49753.2023. 10383571 12. Lofb erg, J.: Y almip: A to olbox for modeling and optimization in matlab. In: 2004 IEEE In ternational Conference on Robotics and Automation (IEEE Cat. No. 04CH37508). pp. 284–289. IEEE (2004). https://doi.org/10.1109/CACSD. 2004.1393890 13. Miao, F., Zh u, Q., Pa jic, M., P appas, G.J.: A hybrid sto c hastic game for secure con trol of cyb er-ph ysical systems. Automatica 93 , 55–63 (2018). https://doi. org/10.1016/j.automatica.2018.03.012 14. Milošević, J., Dahan, M., Amin, S., Sandb erg, H.: Strategic monitoring of net- w orked systems with heterogeneous security levels. IEEE T ransactions on Control of Net work Systems 11 (3), 1165–1176 (2023). https://doi.org/10.1109/TCNS. 2023.3333392 15. Mo, Y., Chabuksw ar, R., Sinop oli, B.: Detecting in tegrity attacks on scada sys- tems. IEEE T ransactions on Control Systems T echnology 22 (4), 1396–1407 (2013). https://doi.org/10.1109/TCST.2013.2280899 20 Anh T ung Nguy en et al. 16. Naha, A., T eixeira, A., Ahlén, A., Dey , S.: Quick est physical watermarking-based detection of measurement replacemen t attacks in netw ork ed control systems. Euro- p ean Journal of Control 71 , 100804 (2023). https://doi.org/10.1016/j.ejcon. 2023.100804 17. Nguy en, A.T., Anand, S.C., T eixeira, A.M.: A zero-sum game framework for opti- mal sensor placement in uncertain netw ork ed control systems under cyber-attacks. In: 2022 IEEE 61st Conference on Decision and Control (CDC). pp. 6126–6133. IEEE (2022). https://doi.org/10.1109/CDC51059.2022.9992468 18. Nguy en, A.T., Anand, S.C., T eixeira, A.M., Medvedev, A.: Optimal detector place- men t in net work ed con trol systems under cyb er-attac ks with applications to p o wer net works. IF AC-P apersOnLine 56 (2), 1820–1826 (2023). https://doi.org/10. 1016/j.ifacol.2023.10.1896 19. Nguy en, A.T., T eixeira, A.M.H., Medvedev, A.: A single-adversary-single-detector zero-sum game in netw ork ed con trol systems. IF AC-P apersOnLine 55 (13), 49–54 (2022). https://doi.org/j.ifacol.2022.07.234 20. Nguy en, A.T., T eixeira, A.M., Medvedev, A.: Securit y allo cation in net work ed con trol systems under stealthy attacks. IEEE T ransactions on Control of Netw ork Systems (2024). https://doi.org/10.1109/TCNS.2024.3462546 21. P ark, G., Lee, C., Shim, H., Eun, Y., Johansson, K.H.: Stealthy adversaries against uncertain cyb er-ph ysical systems: Threat of robust zero-dynamics attack. IEEE T ransactions on Automatic Control 64 (12), 4907–4919 (2019). https://doi.org/ 10.1109/TAC.2019.2903429 22. Sh ukla, P ., An, L., Chakrab ortt y , A., Duel-Hallen, A.: A robust stack elb erg game for cyb er-securit y inv estmen t in netw orked con trol systems. IEEE T ransactions on Con trol Systems T echnology 31 (2), 856–871 (2022). https://doi.org/10.1109/ TCST.2022.3207671 23. T egling, E.: F undamental limitations of distributed feedback control in large-scale net works. Ph.D. thesis, KTH Roy al Institute of T echnology (2018) 24. T eixeira, A., Shames, I., Sandb erg, H., Johansson, K.H.: A secure control frame- w ork for resource-limited adversaries. Automatica 51 , 135–148 (2015). https: //doi.org/10.1016/j.automatica.2014.10.067 25. T eixeira, A.M.H.: Optimal stealthy attacks on actuators for strictly prop er systems. In: 2019 IEEE 58th Conference on Decision and Control (CDC). pp. 4385–4390. IEEE (2019). https://doi.org/10.1109/CDC40024.2019.9029171 26. T rentelman, H.L., Willems, J.C.: The dissipation inequality and the algebraic Ric- cati equation. Springer (1991) 27. Umsonst, D., Sarıtaş, S., Dán, G., Sandberg, H.: A bay esian nash equilibrium- based moving target defense against stealth y sensor attacks. IEEE T ransactions on Automatic Con trol 69 (3), 1659–1674 (2024). https://doi.org/10.1109/TAC. 2023.3328754 28. UW-EE: Ieee 14-bus test case (1993), labs.ece.uw.edu/pstca/pf14/ieee14cdf. txt 29. Y uan, H., Xia, Y., Zhang, J., Y ang, H., Mahmoud, M.S.: Stack elb erg-game-based defense analysis against adv anced persistent threats on cloud control system. IEEE T ransactions on Industrial Informatics 16 (3), 1571–1580 (2019). https: //doi.org/10.1109/TII.2019.2925035 30. Zhang, K., Keliris, C., Parisini, T., Polycarpou, M.M.: Stealthy integrit y attacks for a class of nonlinear cyb er-ph ysical systems. IEEE T ransactions on Automatic Con trol 67 (12), 6723–6730 (2021). https://doi.org/10.1109/TAC.2021.3131656
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment