Multi-User Covert Communication in Spatially Heterogeneous Wireless Networks
This paper investigates an uplink multi-user covert communication system with spatially distributed users. Unlike prior works that approximate channel statistics using averaged parameters and homogeneous assumptions, this study explicitly models each…
Authors: Jinyoung Lee, Hyeonsik Yeom
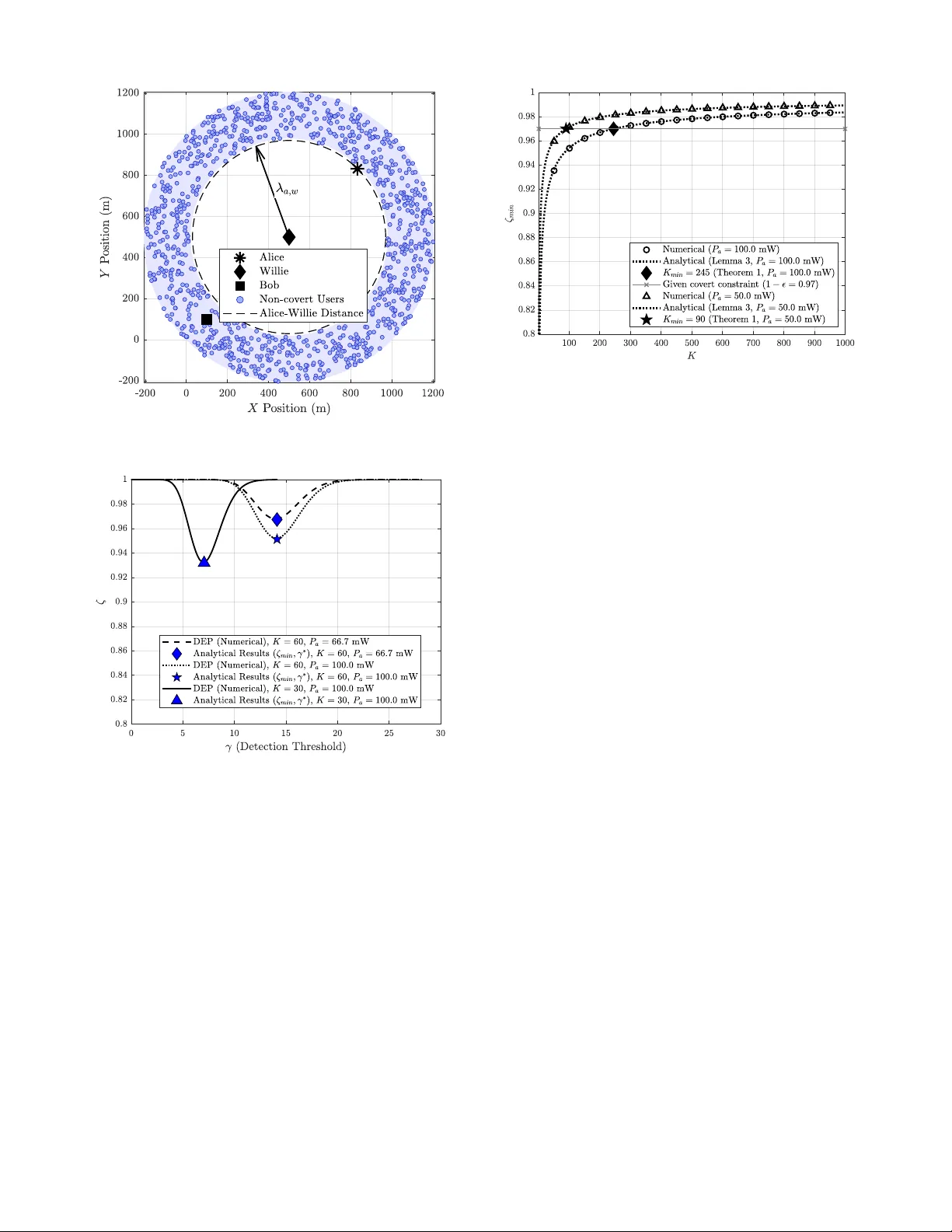
1 Multi-User Co v ert Communication in Spatially Heterogeneous W ireless Networks Jinyoung Lee, Hyeonsik Y eom Abstract —This paper in vestigates an uplink multi-user co vert communication system with spatially distributed users. Unlik e prior works that approximate channel statistics using av eraged parameters and homogeneous assumptions, this study explicitly models each user’s geometric position and corresponding user -to- Willie and user-to-Bob channel variances. This approach enables an accurate characterization of spatially heterogeneous covert en vironments. W e mathematically prove that a generalized on–off power control scheme, which jointly accounts for both Bob’s and Willie’s channels, constitutes the optimal transmission strategy in heterogeneous user configurations. Leveraging the optimal strategy , we deriv e closed-f orm expr essions f or the minimum detection error probability and the minimum number of coop- erative users required to satisfy a cov ert constraint. W ith the closed-form expressions, comprehensive theoretical analyses are conducted, which are validated by Monte-Carlo simulations. One important insight obtained fr om the analysis is that user spatial heterogeneity can enhance covert communication performance. Building on these findings, a piecewise search algorithm is proposed to achieve exact optimality with significantly reduced computational complexity . W e demonstrate that optimization considering user’s spatial heterogeneity achieves substantially impro ved covert communication performance than that based on the assumption of spatial homogeneity . Index T erms —Covert communication, physical layer security , piecewise optimization, spatial heterogeneity , wireless communi- cations I . I N T RO D U C T I O N W ith the explosiv e proliferation of wireless devices and the Internet of Things (IoT), modern wireless networks are required to manage enormous volumes of sensitiv e infor- mation. At the same time, the continuous gro wth in wire- less connectivity and device density increases the exposure of communication channels, making the wireless medium highly vulnerable to adv ersarial surveillance and eavesdrop- ping. T o address these threats, physical layer security (PLS) has emerged as a complementary paradigm to cryptography , exploiting the intrinsic randomness of wireless channel at the physical layer to provide confidentiality and resilience directly at the signal level. Among the v arious PLS techniques, co vert communication has recently attracted considerable attention for its unique objectiv e. Unlike con ventional cryptographic approaches that protect the content of a message, cov ert communication aims to conceal the existence of a transmis- sion from adversarial detectors, typically called W illie. In other words, the transmitter seeks to ensure an extremely J. Lee is with the Division of Electronics and Electrical Information Engineering, National K orea Maritime & Ocean Univ ersity , Busan 49112, South Korea, email: jylee120@kmou.ac.kr . H. Y eom is with the Defense ICT Conver gence Research Section, Elec- tronics and T elecommunications Research Institute (ETRI), Daejeon 34129, South Korea, email: hyeonsik@etri.re.kr . low probability that detectors can correctly decide whether a transmission is occurring, while simultaneously guaranteeing a desired data rate for the legitimate receiver . Such concealment capability is essential for di verse mission-critical and priv acy- sensitiv e applications, including military operations, secure IoT networks, and cov ert ad hoc communications [1]. Early covert transmission techniques, such as direct se- quence spread spectrum, frequenc y hopping, and chirp spread spectrum, were primarily implementation-driv en. Though they achiev ed practical covertness, the lack of theoretical analysis motiv ated a fundamental question on the limits of covert communication. In [2], Bash et al. introduced the squar e r oot law for additive white Gaussian noise (A WGN) channels. The law states that, under perfect channel knowledge at Willie, no more than O ( √ n ) bits can be transmitted reliably and cov ertly within n channel uses. Subsequent works [3]–[9] generalized this principle to other canonical channels such as binary symmetric, discrete memoryless, multiple access, broadcast, and interference models, thus establishing the the- oretical foundation of covert communication. Regrettably , strict adherence to the square root law dictates that the transmission rate must approach zero for a sufficiently large number of channel uses. Moti vated by this limitation, numerous studies hav e explored ways to achieve a positiv e cov ert rate by introducing uncertainty at W illie. Major ap- proaches to achiev e positiv e covert rates include exploiting channel uncertainty [10], [11], inducing interference via relays or jammers [12]–[17], and utilizing full-duplex receivers [18], [19]. Furthermore, recent hardware-assisted innovations hav e significantly enhanced covertness by lev eraging the inherent directionality of mmW a ve systems [20], the spatial reconfig- urability of movable antennas [21], and the mobility-enabled adaptability of UA V networks [22]–[24]. Meanwhile, beyond covert communication in single-user wireless networks, covert communication has also been exten- siv ely studied in multi-user wireless networks. These studies analyzed the impact of random user locations, interference, and spatial topology on covert performance. He et al. [25] analyzed a homogeneous Poisson point process network in which numerous transmitters act as uncoordinated interferers. Their analyses demonstrated that, in the interference-limited regime, the covert rate con verges to a finite bound regardless of the aggregate interference power , implying that background interference alone cannot indefinitely enhance cov ertness. Building upon this framew ork, Soltani et al. [26] introduced friendly nodes that intentionally generate artificial noise. By activ ating the node closest to each W illie, the legitimate parties maintain Willie’s detection error probability near one half and achieves improved covertness through artificial noise. 2 Although these studies provide valuable insights into the statistical behavior of large-scale stochastic networks, they rely on uncoordinated and statistically modeled interference. In particular , the interference sources are either naturally occur- ring, as in [25], or intentionally generated but still independent and non-cooperati ve, as in [26]. Consequently , these works do not in vestigate the potential of coordinated or jointly optimized user cooperation for activ ely enhancing cov ert performance. More recent studies focus on cooperative or active multi- user co vert communication, where legitimate users deliberately coordinate to confuse W illie [27]–[30]. Zheng et al. [27] proposed a distributed cooperativ e jamming scheme in which multiple friendly jammers are selected based on instanta- neous channel gains to maximize the covert rate. Although the analysis primarily relies on numerical methods, their results demonstrate that cooperativ e div ersity can significantly enhance covertness. Lee et al. [28] further elaborated the advantages of cooperative di versity in cov ert communication. In particular, they deriv ed closed-form expressions for the system performance that explicitly elucidate the relationships among system parameters, and proposed a low-comple xity algorithm that maximizes the cov ert rate by jointly optimizing the transmit po wers of the cooperati ve users and the cov ert message. Later , [29] incorporated channel correlation, rev eal- ing that the presence of correlation among users can actually improv e cov ertness, and proposed a scalable Q -learning based optimization algorithm. While these works have established the fundamental benefits of cooperation, they commonly as- sume homogeneous user configurations where all users are located at equal distances from both the legitimate recei ver and W illie. T o o vercome the fundamental limitations of existing analyses for uplink multi-user cov ert communication, Y eom et al. [30] in vestigated the cov ert communication performance in the uplink multi-user system where users are located at unequal distances from Bob . Although the users are spatially distributed, their mathematical analysis was deriv ed based on single average v alues for the distances from the users to Bob and from the users to W illie, which substantially simplifies the analytical deri v ations. Howe ver , this o versimplifying as- sumption does not allow the analysis to capture the impact of users’ spatial heterogeneity on the co vert communication performance. Motiv ated by this limitation, this work focuses on how heterogeneous spatial configurations among multiple users affect the covert communication performance. Unlike the existing works [28], [29], we consider an uplink multi-user cov ert communication network in which the user locations are spatially heterogeneous. In addition, we analyze the cov ert communication performance without relying on the ov ersimplifying assumption adopted in [30], thereby enabling us to capture how spatially heterogeneous users affect the cov ert communication performance. The major contrib utions are summarized as follows: 1) Optimal power allocation strategy f or covert com- munication: W e mathematically pro ve that the on–of f power allocation polic y that accounts for all channels between the legitimate parties and Willie is optimal. This result re veals that the relativ e strength between the channel gain from each user to Bob and the variance Wi lli e Bob , , fo r , , A li ce (C o v e r t u s e r ) E n cod e r Dec o d er E n cod e r , ( , ) , ( , ) Det ec t o r , ( , ) , ( , ) , ( , ) T h e c o v er t c h a n n el s o v er T h e no n c o v e rt c h a nne l s o v e r = 1 ,2 , … , (N o n - c o v e r t u se r s) Fig. 1. System model of multi-user cooperation for covert communication. of the channel from each user to Willie serves as a fundamental metric governing cooperati ve beha vior . By analytically characterizing this ratio within a spatially heterogeneous network, the proposed framew ork pro- vides the first geometric interpretation of how user locations influence the covert rate. 2) Closed-form expressions for the co vert communica- tion parameters: Closed-form analytical expressions are deri ved for key system parameters, including the minimum number of cooperativ e users and the activ ation threshold required to satisfy a conv ert constraint, and the cov ert rate. These results yield explicit design guide- lines and quantitativ e benchmarks for ev aluating and optimizing covert performance under realistic spatially heterogeneous conditions. 3) Algorithmic efficiency: By deri ving all ke y parameters in the analytical forms, the proposed framework es- tablishes explicit analytical relationships among system variables. Lev eraging these relationships, we propose an algorithm offering high computational efficiency while maintaining analytical optimality within the heteroge- neous multi-user framework. The subsequent sections of this work are detailed as follows. Section II introduces the system model and W illie’ s detection strategy . In Section III, the optimal transmit power profile for cooperativ e users is derived. Subsequently , Section IV deriv es closed-form expressions for the minimum number of cooperativ e users and the acti vation threshold required to satisfy the covert constraint. Building on these analyses, Section V proposes a piecewise search algorithm to efficiently search for the optimal covert message power . Finally , Section VI validates the theoretical findings with numerical results, followed by the conclusion in Section VII. I I . S Y S T E M M O D E L A N D P R O B L E M F O R M U L AT I O N A. System Model W e in vestigate uplink covert communication networks con- sisting of a cov ert user (Alice), M non-covert users, a base station (Bob), and a w atchful adv ersary (Willie), as illustrated in Fig. 1. W e assume that all users, including Alice and the non-cov ert users, communicate with Bob using frequency division multiple access. In particular , the m -th non-cov ert user , denoted by U m , and Alice transmit data symbols W m and W a through carrier frequencies f m and f a , respectively . A subset of non-covert users is selected as cooperativ e users 3 to assist in hiding Alice’s signal from detection at Willie by transmitting interference over f a . Hereafter , the term “users” refers to both the covert user and the non-covert users. W e assume that all nodes including users and Bob, and Willie are equipped with a single antenna. The channels are modeled as quasi-static Rayleigh fading, implying that the channel remains constant during a codeword transmission but v aries independently across code words. The channel from node x to node y at carrier frequency z is denoted by h z x,y ∼ C N (0 , λ x,y ) , x, y ∈ { a, b, m, w } , z ∈ { a, m } (1) where λ x,y indicates the large-scale fading coef ficient, and the indices a, b, m , and w represent Alice, Bob, U m , and W illie, respectiv ely . In this work, the large-scale fading coefficient is assumed to be in variant re gardless of the carrier frequenc y , and therefore the superscript indicating the carrier frequency is omitted from λ x,y . W e assume a single-slope path-loss model, and thus, the large-scale fading coefficient is expressed as λ x,y = β 0 d − α x,y , (2) where β 0 is the reference channel gain, α is the path-loss exponent, and d x,y denotes the Euclidean distances between nodes x and y . Unlike the homogeneous channel assumption in [28]–[30], where all users have a single large-scale fading coefficient, i.e., λ m,w = c for all m , this work considers on each user’ s distinct spatial position. Consequently , λ m,w = λ n,w for m = n , capturing the spatial heterogeneity that sets our analysis apart from prior works. Channel estimation process consists of two-phases. In the first phase, Bob broadcasts pilot signals o ver all frequency bands, i.e., f a and { f m | m ∈ { 1 , 2 , . . . , M }} . Based on the receiv ed pilot signals, each node estimates the channel from Bob to itself. In the second phase, each user transmits its own pilot signal over its allocated frequency band. For cov ert communication, each non-covert user transmits a secret orthogonal pilot signal ov er f a [2], [27], [31]. The use of secret orthogonal pilot signals by each non-covert user enables Bob to estimate the channel between the non-covert user and Bob, whereas Willie cannot. Note that we assume perfect channel estimation; hence, the ef fect of channel estimation errors is neglected. In addition, channel reciprocity is assumed to hold, i.e., h z x,y = h z y ,x for all x and y . The m -th non-covert user , U m , and Alice transmit code- words ¯ x ′ m and ¯ x a with length N ov er f m and f a , respectively , while each cooperati ve user also sends an interference se- quence ¯ x m ov er f a to help conceal ¯ x a . It is note worthy that the interference signal, ¯ x m , also acts as interference at Bob, which degrades the co vert communication performance. Therefore, the design of the interference power and the selection of cooperativ e users are of significant importance. Our main interest lies in co vert communication; hence, we only focus on the signal in f a , where the covert signal is transmitted. The receiv ed signal at Bob y [ t ] is giv en by y [ t ] = M X m =1 p P m h a m,b x m [ t ] + n b [ t ] , H 0 p P a h a a,b x a [ t ] + P M m =1 √ P m h a m,b x m [ t ] + n b [ t ] , H 1 , (3) where both x a [ t ] and x m [ t ] are assumed to be complex Gaussain random variables with zero-mean unit-v ariance. The parameters P a and P m represent the transmit power of Alice and U m , respecti vely , and n b [ t ] ∼ C N (0 , σ 2 b ) denotes A WGN at Bob . In addition, H 0 and H 1 indicate the hypotheses that Alice does not transmit or transmits a covert message, respectiv ely . Similarly , the receiv ed signal at W illie over f a is giv en by z [ t ] = M X m =1 p P m h a m,w x m [ t ] + n w [ t ] , H 0 √ P a h a a,w x a [ t ] + P M m =1 √ P m h a m,w x m [ t ] + n w [ t ] , H 1 , (4) where n w [ t ] ∼ C N (0 , σ 2 w ) stands for A WGN at W illie. B. Detection at W illie W illie infers the presence of covert data transmission from Alice based on his observation. As introduced in Section II-A, W illie is confronted with a binary hypothesis testing problem consisting of two hypotheses H 0 and H 1 . Under the con ventional equal prior assumption [16], [32], the detection error probability (DEP) can be defined to ζ ≜ P F A + P MD , (5) and the covert communication requirement is formalized through the constraint ζ ≥ 1 − ϵ , where ϵ > 0 is arbitrarily small [19], [28], [29]. Since a detection method employed by W illie has a signifi- cant impact on the DEP , it is necessary to specify the detection method assumed in the analysis of covert communication performance. According to the Neyman–Pearson Lemma [33], the likelihood ratio test (LR T) provides the optimal detection performance for the binary hypothesis test and is expressed as Q N t =1 f z [ t ]; H 1 Q N t =1 f z [ t ]; H 0 D 0 ≶ D 1 γ , (6) where f ( · ) represents the probability density function (PDF) and γ denotes the detection threshold. It is notew orthy that when the transmitted signals follow a Gaussian distribution, the recei ved ener gy , i.e., T w = P N t =1 | z [ t ] | 2 / N , serves as a sufficient statistic for the LR T [17], [27]. Consequently , the LR T can be equiv alently reduced to a test of the receiv ed energy , i.e., T w as follows: T w D 0 ≶ D 1 γ . (7) Since x a [ t ] , x m [ t ] and n w [ t ] are uncorrelated Gaussian random variables, the distrib ution of T w under both hypotheses follows a chi-square distribution, as gi ven by T w = M X m =1 P m | h a m,w | 2 + σ 2 w ! χ 2 2 N 2 N , H 0 M X m =1 P m | h a m,w | 2 + P a | h a a,w | 2 + σ 2 w ! χ 2 2 N 2 N , H 1 (8) 4 where χ 2 2 N denotes a chi-square random variable with 2 N degrees of freedom. When the length of codew ord, N , is sufficiently large, the ratio χ 2 2 N / (2 N ) conv erges to unity due to the strong law of lar ge numbers [34]. Accordingly , the test statistic T w can be characterized as T w = M X m =1 P m | h a m,w | 2 + σ 2 w , H 0 M X m =1 P m | h a m,w | 2 + P a | h a a,w | 2 + σ 2 w , H 1 . (9) Then, the DEP , ζ ( γ ) , for a giv en threshold γ is given by ζ ( γ ) = Pr( T w > γ | H 0 ) + Pr( T w ≤ γ | H 1 ) . (10) Note that ζ ( γ ) depends on the detection threshold γ . T o consider the w orst case, we assume that W illie chooses the threshold γ that minimizes the DEP , i.e., ζ min = min γ ζ ( γ ) . (11) It is shown in (9) that W illie faces uncertainty caused by (i) his access only to the statistical properties of the channel, | h m,w | 2 , and (ii) the randomness of the aggregated interference power from spatially distributed users, P M m =1 P m | h a m,w | 2 . Conse- quently , the spatial heterogeneity of user locations becomes a key factor determining covert communication performance. C. Optimization Pr oblem This work focuses on the transmit power optimization problem to maximize the achiev able rate while satisfying the cov ert constraint. The achiev able rate is defined as R = log 2 1 + P a | h a a,b | 2 P M m =1 P m | h a m,b | 2 + σ 2 b ! . (12) Then, the transmit po wer optimization problem can be formu- lated as ( P ∗ a , ¯ P ∗ ) = argmax P a , ¯ P R (13a) s.t. ζ min ≥ 1 − ϵ (13b) 0 ≤ P a ≤ P max (13c) 0 ≤ P m ≤ P max , ∀ m, (13d) where ¯ P ≜ ( P 1 , P 2 , . . . , P M ) is the transmit power profile for non-cov ert users, P max is the maximum transmit power , and ϵ is the tolerable covertness error . The covert constraint is given in (13b), and the transmit power constraints are given in (13c) and (13d), respectively . I I I . O P T I M A L T R A N S M I T P O W E R P R O FI L E In this section, the optimization problem in (13) is reformu- lated to a more tractable and simpler form by analyzing the optimal transmit power profile ¯ P for a giv en P a . Proposition 1. F or suf ficiently lar ge M , the optimal transmit power pr ofile for non-covert users under spatial heter ogeneity is an on–off scheme for a given P a , i.e., P ∗ m = P max , | h a m,b | 2 λ m,w ≤ τ 0 , otherwise . , (14) Pr oof. The proof is provided in Appendix A. Based on the on-off scheme presented in Proposition 1, we reformulate the original optimization problem in (13) as ( P ∗ a , τ ∗ ) = argmax P a ,τ R s.t. (13b) and (13c) . (15a) Note that the reformulated optimization problem in (15) has only two optimization v ariables, whereas the original opti- mization problem in (13) in volves M + 1 optimization vari- ables. Consequently , owing to Proposition 1, a much simpler optimization problem can be obtained. Remark 1. In this work, Bob optimizes the communication parameters, P a and ¯ P (or equivalently , the activation thr esh- old τ ), to maximize the achievable rate for the covert message while satisfying both the covert and power constraints, given the instantaneous c hannel gains {| h a x,b | : x ∈ { a, m }} and the larg e-scale fading coef ficients { λ x,b : x ∈ { a, m }} . The optimized parameters, i.e, P a and τ , ar e then br oadcast to users and W illie. Remark 2. Intuitively , increasing the activation thr eshold τ allows more non-covert users to transmit interference signals. This enhances the concealment of the covert message but simultaneously degr ades Bob’s communication performance due to the increased interfer ence power . In other words, ther e exists a fundamental trade-off between covertness and r eliable communication with r espect to τ . Consequently , the optimal thr eshold τ is selected as the minimum value that satisfies the covert constraint ζ min ≥ 1 − ϵ in (13b) ; that is, the optimal τ , denoted by τ ∗ , makes the covert constr aint hold with equality , i.e., ζ min ( τ ∗ ) = 1 − ϵ . Equivalently , since τ determines the number of cooperative users K through the condition | h a m,b | 2 /λ m,w ≤ τ , the optimal K is also c hosen as the minimum number of cooper ative users that satisfies the covert constraint. Remark 3. In the existing studies [28]–[30], it has been mathematically pr oven that the optimal power pr ofile fol- lows the on–off scheme that considers only the instantaneous channel gains between the non-covert users and Bob, i.e., | h a m,b | . In contrast, the on–off scheme pr oposed in this work takes into account not only | h a m,b | , but also the lar ge-scale fading coefficients between the non-covert user s and W illie, i.e., λ m,w . This r eveals a key distinction from the pre vious on- off scheme [28]–[30], which aim only to r educe interfer ence at Bob without accounting for W illie. In contrast, the on–off scheme pr oposed in this work explicitly incorporates Bob’s instantaneous channel gains, i.e., | h a m,b | , and W illie’s larg e- scale fading coefficients, i.e ., λ m,w , ther eby selecting cooper- ative users that r educe interference at Bob while increasing interfer ence observed by W illie. Remark 4. In this work, we adopt a worst-case adversary model for W illie. Specifically , W illie is assumed to have perfect knowledge of the on–off scheme and the total number of cooperative users K . Unlike [30], which assumes a single averag ed parameter ¯ λ = E [ λ m,w ] due to W illie’s incomplete knowledge of user locations, we assume that W illie knows the exact locations of all users. This enables him to compute the individual lar ge-scale fading coef ficients λ m,w for every 5 m , ensuring that his detection performance fully exploits the available spatial information. Such a worst-case modeling choice leads to a conservative and r obust secr ecy analysis. I V . A N A L Y S I S O F D E T E C T I O N A T W I L L I E In this section, we deriv e a closed-form expression of the minimum DEP and analyze its characteristics. In particular , we determine the optimal detection threshold γ ∗ that minimizes the DEP , resulting in the closed-form expression of ζ min . Furthermore, based on the closed-form expression of ζ min , we deriv e the minimum number of cooperative users and the corresponding activ ation threshold required to satisfy the cov ert constraint, i.e., ζ min ≥ 1 − ϵ , both in closed-form expressions. According to the on-of f scheme in Proposition 1, the coop- erativ e users transmit interference signals with P m = P max , while the other users do not transmit any interference signals, i.e., P m = 0 . Then, under the on-of f scheme in Proposition 1, the test statistic in (9) is expressed as T w = K X i =1 P max | h a m i ,w | 2 + σ 2 w , H 0 , K X i =1 P max | h a m i ,w | 2 + P a | h a a,w | 2 + σ 2 w , H 1 , (16) where m i ∈ { 1 , 2 , . . . , K } denotes the index of the i -th cooperativ e user sorted in ascending order of the ratio between the channel gain and the large-scale fading coefficient, i.e., | h a m i ,b | 2 /λ m i ,w ≥ | h a m j ,b | 2 /λ m j ,w for i ≥ j . Since each channel gain | h a m i ,w | 2 follows a Gamma distri- bution, and the sum of independent random variables is rep- resented by the conv olution of their distributions, the shifted test statistic T w − σ 2 w is expressed as T w − σ 2 w ∼ K ⊛ i =1 Γ(1 , λ m i ,w P max ) , H 0 , K ⊛ i =1 Γ(1 , λ m i ,w P max ) ∗ Γ(1 , λ a,w P a ) , H 1 , (17) where Γ( a, b ) represents a Gamma distribution with shape parameter a and scale parameter b , ∗ denotes the conv olution operator between PDFs of two random variables, and ⊛ K i =1 indicates the successi ve con volution of the PDFs of K random varaibles, i.e., ⊛ K k =1 A k = A 1 ∗ A 2 ∗ · · · ∗ A K . Based on the probabilistic distrib ution of T w − σ 2 w in (17), a closed-form expression for the DEP in (10) is deriv ed in Lemma 1. Lemma 1. W ith the on-off scheme, the closed-form expr ession for the DEP ζ ( γ ) is appr oximated as ζ ( γ ) ≈ 1 − exp − 2∆( ˆ γ − Ξ) − Σ 2∆ 2 Q − ∆( ˆ γ − Ξ) − Σ √ Σ ∆ , (18) wher e ˆ γ ≜ γ − σ 2 w , ∆ ≜ P a λ a,w , Ξ ≜ K P max M P M m =1 λ m,w , and Σ ≜ P 2 max " K M M X m =1 λ 2 m,w + K ( M − K ) M − 1 (19) × 1 M M X m =1 λ m,w − 1 M M X n =1 λ n,w ! 2 # . (20) Pr oof. See Appendix B The analytical form of the DEP in (18) enables one to obtain sev eral design parameters in closed-form. In particular , the optimal detection threshold γ ∗ , which minimizes the DEP , is deriv ed in closed-form and presented in Lemma 2. Lemma 2. The optimal detection thr eshold is given by γ ∗ = K P max M M X m =1 λ m,w + σ 2 w . (21) Pr oof. Starting from (18), the DEP is approximated as ζ ( γ ) ≈ 1 − c q exp − 1 2Σ ˆ γ 2 − 2Ξ ˆ γ + Ξ 2 | {z } ( a ) , (22) where the approximation follo ws from the fact that the Q - function can be approximated by an exponential function, i.e., Q ( x ) ≈ c q e − x 2 / 2 [28]. It is observed that the DEP expression in (22) is an exponential function of a quadratic term in ˆ γ . Since the exponential function is monotonically increasing function and the quadratic function with a negati ve quadratic coefficient, i.e., the term (a) in (22), attains its maximum v alue at the verte x ˆ γ = Ξ , the minimum DEP is achieved at ˆ γ ∗ = Ξ . Based on the definitions of ˆ γ and Ξ , the optimal detection threshold is given in (21). Using the optimal detection threshold in (21), the minimum DEP is obtained as presented in Lemma 3. Lemma 3. The minimum DEP at W illie is given by ζ min = 1 − √ π q Σ 2∆ 2 + q Σ 2∆ 2 + 4 π − 1 . (23) Pr oof. By substituting the optimal detection threshold γ ∗ in (21) into the DEP in (18), we obtain ζ min = 1 − exp Σ 2∆ 2 Q √ Σ ∆ ! = 1 − 1 2 exp Σ 2∆ 2 erfc √ Σ √ 2 ∆ ! ≈ (a) 1 − 1 2 exp Σ 2∆ 2 2 exp − Σ 2∆ 2 √ π q Σ 2∆ 2 + q Σ 2∆ 2 + 4 π = 1 − √ π r Σ 2∆ 2 + r Σ 2∆ 2 + 4 π !! − 1 , (24) where erfc( · ) indicates the complementary error function. The approximation in (a) follows from the fact that erfc( x ) ≈ 2 / √ π · exp( − x 2 ) / ( x + p x 2 + 4 /π ) is highly accurate for x ≳ 1 [35]. In our setting, the argument of the complementary error function is Σ / 2∆ 2 , and since the aggregate interference power Σ from the cooperativ e users is typically much larger than that of Alice’ s power ∆ , this approximation is well justified. As discussed in Remark 2, the number of cooperative users K is determined as the minimum integer value satisfying the 6 cov ert constraint ζ min ≥ 1 − ϵ . Based on this discussion, the minimum number of cooperative users, denoted by K min , is deriv ed in Theorem 1. Theorem 1. The minimum number of cooperative users is given by K min = & M ( E + V ) 2 V 1 − s 1 − 4 V C M ( E + V ) 2 !' , (25) wher e C = P 2 max / P 2 a λ 2 a,w c ϵ with c ϵ = (1 /ϵ 2 − 8+16 ϵ 2 ) / 2 π . In addition, E means the empirical mean of λ 2 m,w , which is defined by E ≜ E [ λ 2 w ] = 1 M M X m =1 λ 2 m,w , (26) and V r epr esents the empirical variance of λ m,w , which is expr essed by V ≜ V ar[ λ w ] = 1 M M X m =1 λ m,w − 1 M M X n =1 λ n,w ! 2 . (27) Pr oof. See Appendix C Although the expression for K min in (25) has a simple analytical form, it is somewhat challenging to directly observe how the communication parameters affect it. For this reason, we further analyze two special cases: 1) the asymptotic case, i.e., M ≫ 1 , in Corollary 1, and 2) the homogeneous user deployment case, i.e., λ m,w = λ n,w for m = n , in Corollary 2. Corollary 1. F or M ≫ 1 , K min is appr oximated as K min ≈ 1 C ( E + V ) = & ( P a λ a,w ) 2 c ϵ P 2 max E [ λ 2 w ] + V ar[ λ w ] ' . (28) Pr oof. Let us focus on the square-root term in (25). By apply- ing the first-order binomial expansion, i.e., √ 1 − x ≈ 1 − x/ 2 , the square-root term can be approximated as s 1 − 4 V C M ( E + V ) 2 ≈ 1 − 2 V C M ( E + V ) 2 . (29) Note that the first-order binomial expansion is accurate when x is small. In this work, x corresponds to the term 4 V / ( C M ( E + V ) 2 ) . When M increases, the values of C , E , and V do not scale with M , so the term 4 V / ( C M ( E + V ) 2 ) indeed becomes small for suf ficiently large M . This implies that when M is sufficiently large, the approximation in (29) is justified. Then, by substituting the approximation in (29) into (25), and performing some straightforward mathematical manipulations, we obtain the expression of K min presented in (28). From the approximation of K min presented in (28), we can obtain some insight into ho w the primary factors influence the required K min . In particular, the result indicates that K min is in versely proportional to E [ λ 2 w ] + V ar[ λ w ] , and increases quadratically with P a . In addition, K min increases on the order of ϵ − 2 as ϵ becomes small, because c ϵ itself scales as O ( ϵ − 2 ) as ϵ → 0 . This implies that as the covert constraint becomes tighter , that is, as ϵ decreases, the minimum number of cooperative users increases on the order of the inv erse square of ϵ . All these analyses are confirmed in Section VI-C. Corollary 2. Under homogeneous user deployment, wher e all non-covert users are located at appr oximately the same distance fr om W illie, i.e., λ m,w ≈ ¯ λ w for all m and thus V ar[ λ w ] ≈ 0 , but the Alice–W illie channel gain λ a,w may differ fr om ¯ λ w , the appr oximation expr ession of K min in Theorem 1 simplifies to K min ≈ & P 2 a c ϵ P 2 max λ a,w ¯ λ w 2 ' . (30) Pr oof. For simplicity , the ceiling function in (25) is omit- ted. Under homogeneous user deployment, the term V is very small; thus, using the first-order binomial approximation √ 1 − x ≈ 1 − x/ 2 for x = 4 V / ( C M ( E + V ) 2 ) in Theorem 1 yields a highly accurate approximation. After some straight- forward algebraic manipulation, K min can be written as K min ≈ 1 C ( E + V ) ≈ (a) 1 C E , (31) where (a) follows from V ≪ E in the homogeneous case. Finally , substituting C = P 2 max / ( P a λ a,w ) 2 c ϵ and applying E = ¯ λ 2 w , completes the proof. In this case, the minimum number of cooperati ve users is independent of the number of non-cov ert user M . In addition, when λ a,w = ¯ λ w , this result directly reduces to the result shown in previous works [28], [30], demonstrating that the proposed analysis encompasses these prior studies as special cases and therefore provides a more general characterization of the system. By utilizing the closed-form expression for K min in Theo- rem 1, the corresponding optimal activ ation threshold of the on-off scheme in Proposition 1 can be readily deriv ed, as presented in Theorem 2. Theorem 2. The optimal activation thr eshold τ ∗ is determined by τ ∗ = | h a K min ,b | 2 λ K min ,w . (32) Pr oof. By setting τ to the ratio | h a K min ,b | 2 /λ K min ,w , the K min - th weakest user in terms of | h a m,b | 2 /λ m,w becomes the acti- vation boundary , ensuring that exactly K min cooperativ e users participate, where K min is giv en in (25). V . O P T I M I Z AT I O N O F S Y S T E M P A R A M E T E R S In this section, we first reformulate the optimization problem in (15), which in volv es two optimization v ariables, into a simpler form with only a single optimization variable based on Theorems 1 and 2. Then, we propose an algorithm that efficiently solv es the reformulated optimization problem. A. Reformulation of the Optimization Pr oblem As discussed in Section III, adopting the on–of f scheme in Proposition 1 allo ws the original problem in (13) to be reformulated as (15), reducing the number of optimization variables from M + 1 , i.e., P a , P 1 , . . . , P M , to two, P a and τ . For a giv en P a , Theorems 1 and 2 characterize the 7 optimal number of cooperative users and the corresponding activ ation threshold. Consequently , the problem in (15) can be equiv alently rewritten as P ∗ a = argmax 0 ≤ P a ≤ P max R ( P a , K min ) , (33) where R ( P a , K min ) = log 2 1 + P a | h a a,b | 2 P K min m =1 P max | h a m i ,b | 2 + σ 2 b . (34) This optimization problem has only one optimization v ariable, i.e., P a , and is therefore much easier to solve than the original formulation of (13), which in volves M + 1 optimization variables. B. Optimization of T ransmit P ower for Alice Notably , as sho wn in Theorem 1 and Corollaries 1 and 2, K min is a function of P a . In particular , Corollaries 1 and 2 explicitly demonstrates that K min increases with P a . Intuitiv ely , a larger P a requires stronger interference, that is, a greater K min , to satisfy the co vert constraint. Therefore, the optimal P a in (33) is not simply the maximum allo wable value P max . In this work, we propose an algorithm that determines the optimal P a through a piecewise search for the optimization problem in (33). Meanwhile, it is notew orthy that K min in (25) includes a ceiling function. As a result, K min remains unchanged ov er certain ranges of P a . In such re gime where K min is constant, the optimal P a is the maximum value within that range. The maximum value of P a corresponding to a giv en K min = ¯ K can be obtained from Theorem 1 as P a ( ¯ K ) = P max √ c ϵ λ a,w r ( E + V ) ¯ K − V M ( ¯ K ) 2 . (35) Then, for a given K min = ¯ K , the optimal P a is defined as P ¯ K = min P max , P a ( ¯ K ) for ¯ K ∈ { 0 , . . . , M } . Thus, when performing a one-dimensional search for the optimal P a , it is sufficient to partition the feasible interval of P a according to the v alues of P ¯ K , which naturally leads to a piece wise search structure. This piece wise characterization eliminates the need to explore redundant regions of the search space, making the resulting piece wise search far more efficient and structure- aware than a con ventional exhausti ve one-dimensional search. The overall piece wise search is summarized in Algorithm 1. V I . N U M E R I C A L R E S U LT S In this section, comprehensi ve numerical e valuations are carried out to validate the theoretical analyses deriv ed in this work. In addition, we examine the performance of the proposed covert communication netw ork where users are spa- tially distributed and rev eal the interactions among key system parameters. Algorithm 1 Piecewise Search Input: h a a,b , { h a m,b } M m =1 , { λ m,w } M m =1 , P max , ϵ , σ 2 b Output: P ∗ a , K ∗ , τ ∗ 1: Compute C , E , V , and c ϵ , respectiv ely . 2: Set R temp ← 0 . 3: for ¯ K = 0 to M do 4: Compute P ¯ K and set P a ← P ¯ K . 5: Based on K min = ¯ K , compute R ( P a , ¯ K ) in (34). 6: if R ( P a , ¯ K ) > R temp then 7: R temp ← R ( P a , ¯ K ) , P ∗ a ← P a , and K ∗ ← K . 8: end if 9: end for 10: Set τ ∗ ← h a m K ∗ ,b 2 /λ m K ∗ ,w and return P ∗ a , K ∗ , τ ∗ . A. Simulation Setup For performance e valuations, we consider the large-scale fading channel model specified in the 3GPP TR 25.996 Urban Macrocell guideline [36]. The path loss (PL) at a distance d (in meters) is modeled as PL(dB) = 34 . 5 + 35 log 10 ( d ) , (36) which corresponds to the large-scale fading coefficient λ x,y = β 0 d − α x,y . Here, the path-loss exponent is set to 3.5, and the reference channel gain at d = 1m is gi ven by β 0 = − 34 . 5dB . The maximum transmit power of each user is set to P max = 200 mW (23 dBm) , and the noise variances at Bob and W illie are assumed to be identical, i.e., σ 2 b = σ 2 w = − 102 dBm . The spatial topology of the network is constructed over a circular region with a radius of approximately 707 m , rep- resenting the spatially adverse scenario illustrated in Fig. 2. W illie is placed at the center of the area, (500 , 500) , while Bob is located near the boundary at (100 , 100) . Alice is positioned at (831 , 831) such that her distance to W illie is d a,w ≈ 468 m . This layout intentionally enforces two defining characteristics of this adverse configuration. First, the distance from Alice to Bob is significantly lar ger than that to Willie ( d a,b ≫ d a,w ), forcing Alice to transmit with relatively higher power to sustain a reliable link, which simultaneously strengthens the receiv ed signal at the nearby adversary , i.e., W illie. Second, all M = 1000 non-cov ert users are uniformly distributed within an annular region satisfying d m,w > d a,w for every m ∈ { 1 , . . . , M } . Consequently , each non-covert users e xperiences a weaker channel to Will ie compared to Alice ( λ m,w < λ a,w ), minimizing the receiv ed interference power and imposing the most unfav orable conditions for covertness. Under this setting, the system must satisfy the co vert constraint using only these disadvantaged non-covert users, thereby providing a rigorous and conservati ve benchmark for the proposed scheme. B. W illie’ s Detection P erformance T o validate the theoretical results related to W illie’s detec- tion performance presented in Lemmas 1, 2, 3, and Theorem 1, we conduct Monte-Carlo simulations and compare the analytical results with the simulated ones. In Fig. 3, we present the DEP curves obtained from Monte- Carlo simulations using three different line styles, i.e., dashed, dotted, and solid line, for the combinations of ( K , P a ) = 8 Fig. 2. Spatial configuration of the spatially adverse scenario. Fig. 3. DEP ζ as a function of the detection threshold γ for various combinations of K and P a . (60 , 66 . 7 mW) , (60 , 100 mW) , and (30 , 100 mW) . The dia- mond, star , and triangle markers correspond to the theoretical results in Lemmas 2 and 3. Specifically , the x -coordinates represent the optimal detection threshold, γ ∗ , deri ved in Lemma 2 and the y -coordinates represent the minimum DEP , ζ min , obtained from Lemma 3, for the same three ( K, P a ) combinations. As observed in Fig. 3, the theoretical results for γ ∗ and ζ min closely match the Monte-Carlo simulation results for all considered ( K, P a ) combinations. This confirms the accuracy of our theoretical expressions in capturing the exact performance. This, in turn, validates the analytical framework established in Lemma 1, which serves as the fundamental basis for Lemmas 2 and 3. Meanwhile, in Fig. 3, comparing the dotted and solid curves rev eals that increasing the number of cooperative users (from K = 30 to K = 60 ) leads to a higher minimum DEP . This is attributed to the fact that a larger number of cooperative users generates stronger aggre gate interference at Willie, thereby Fig. 4. Minimum DEP ζ min versus the number of cooperative users K for different transmit po wers P a . hindering his detection performance. Furthermore, a com- parison between the dotted and dashed curves demonstrates that, for a fix ed K , increasing Alice’s transmit po wer from P a = 66 . 7 mW to 100 mW reduces the DEP across all values of γ . This occurs because a higher P a increases the SINR at W illie, which ef fectiv ely diminishes the impact of the interference and improves his detection capability . In Fig. 4, we plot the minimum DEP , ζ min , as a function of the number of cooperativ e users K under the on-of f scheme in Proposition 1 to validate the theoretical results presented in Lemma 3 and Theorem 1. The open markers, i.e., circle and triangle markers, represent the minimum DEP obtained via Monte-Carlo simulations for P a = 100 and 50 mW , respectiv ely . Specifically , the simulation results are determined through an exhausti ve search over the detection threshold, γ . The dotted curves correspond to the theoretical minimum DEP deri ved in Lemma 3, sho wing a precise match with the simulations. Furthermore, the filled star and diamond markers highlight the minimum number of cooperati ve users required to satisfy the cov ert constraint 1 − ϵ = 0 . 97 , as deriv ed in Theorem 1. The coordinates of the star and diamond mark ers correspond to the cases of P a = 50 mW ( K min = 90 ) and 100 mW ( K min = 245 ), respecti vely . This agreement confirms that Theorem 1 serves as a reliable and computa- tionally efficient guideline to determine the necessary number of cooperative users to meet a specified covert constraint. Moreov er , a comparison between the star and diamond mark- ers re veals the trade-off between Alice’ s transmit po wer and the required cooperati ve interference resources; specifically , a higher covert transmit po wer P a necessitates a larger number of cooperati ve users K min to satisfy the same co vert constraint, i.e., 1 − ϵ = 0 . 97 . This is because as P a increases, W illie’ s detection capability improves, requiring stronger aggregate interference generated by a large number of users to ef fectively conceal the signal and satisfy the desired cov ert constraint. C. Impact of Covertness Level and Spatial P arameters In this subsection, we in vestigate the impact of the cov ert constraint and the spatial heterogeneity of multiple users on 9 Fig. 5. Minimum number of cooperative users K min versus covert constraint 1 − ϵ for P a = 25 mW . the minimum number of cooperati ve users, K min . In addition, by comparing the theoretical result of this work with that of the existing literature, we validate through comprehensive simulations that the proposed scheme is significantly more efficient than con ventional approaches derived from prior work. In Fig. 5, we plot K min as a function of the covertness parameter , ϵ . The dotted curve represents the values of K min obtained from Monte-Carlo simulations. The circle, cross, and triangle markers indicate the theoretical results for K min deriv ed from Theorem 1, Corollaries 1, and 2, respecti vely . Fig. 5 illustrates that the theoretical results in Theorem 1 closely match the Monte-Carlo simulation results over the entire range of interest, 0 . 9 ≤ 1 − ϵ ≤ 0 . 99 , which corresponds to the practically relev ant region for cov ert communications. In addition, the close agreement between the cross markers of Corollary 1 and the circle markers of Theorem 1 confirms that the approximation holds well, indicating that the simulation is conducted in the regime of a sufficiently large number of users M . As discussed in Corollary 1, the figure also verifies that as ϵ decreases, K min increases according to the in verse-square scaling, i.e., K min ∝ O ( ϵ − 2 ) . In particular , for 1 − ϵ = 0 . 95 , we observe K min = 12 , whereas for a stricter constraint of 1 − ϵ = 0 . 975 , K min increases to 50. Finally , it is notable that there are significant discrepancies between the exact results (dotted curve) and the homogeneous approximation (triangle markers). In other words, the value of K min deriv ed under the homogeneous-channel assumption is significantly larger than the exact value. As mentioned earlier , Corollary 2 generalizes the existing results in [28]– [30], which correspond to the special case where ¯ λ w = λ a,w . Consequently , this comparison demonstrates that when users are spatially distributed, applying such homogeneous-based analyses leads to a substantial overestimation of K min , thereby failing to provide a proper estimation that reflects the critical characteristics of spatial heterogeneity . Fig. 6 illustrates how the spatial heterogeneity of non- cov ert users af fects K min . In particular , to represent the spatial heterogeneity of non-co vert users, Fig. 6 (a) uses the standard Fig. 6. The minimum number of cooperativ e users K min versus standard deviation for distances of non-covert users to W illie, σ d , and mean distances of non-covert users to W illie, µ d , for P a = 100 mW . deviation of their distances to W illie, i.e., σ d , and Fig. 6 (b) uses the mean distance, i.e., µ d . In addition, the circle and cross markers indicate the values of K min deriv ed from Theorem 1 and Corollary 1, and the dash-dot curv e denotes the K min obtained from Corollary 2. Consistent with the findings in Fig. 5, the baseline design deriv ed from Corollary 2, as observed in Figs.6 (a) and (b), leads to an overestimation of the minimum number of cooperative users. It is also observed in Fig. 6 (a) that as non-covert users become more spatially dispersed, i.e., as σ d increases, the minimum number of cooperati ve users decreases substantially . It is note worthy that, as σ d approaches zero, the gap between the proposed heterogeneous analysis in Theorem 1 and the homogeneous baseline in Corollary 2 vanishes. This con ver- gence confirms that our deriv ed model accurately subsumes the con ventional homogeneous scenario [28]–[30] as a special case, validating its consistency and generality . This observa- tion offers a v aluable design insight: increasing the spatial dispersion of non-covert users is beneficial for reducing the required minimum number of cooperativ e users, K min . Since a lower K min leads to reduced interference at Bob, it ultimately improv es the cov ert rate. Fig. 6 (b) sho ws that as all users mov e farther a way from Willie, i.e., as µ d increases, the required minimum number of cooperati ve users K min also increases. This is because a larger µ d weakens the aggreg ate interference power received at W illie, thereby necessitating more coop- erativ e users to satisfy the co vert constraint. Combining the results from Figs. 6 (a) and (b) yields a comprehensi ve design guideline: to maximize covert communication performance, non-cov ert users should be deployed as close to W illie as possible while maintaining a high degree of spatial dispersion. D. P erformance Comparison with Existing W ork In this subsection, we compare the covert communica- tion performance of the proposed method with that of the baseline method. In the proposed method, cooperati ve users are selected based on both the instantaneous channel gains between the users and Bob, and Willie’s large-scale fading 10 Fig. 7. Performance comparison between the proposed policy (Proposed) and the Bob-only policy (Baseline) versus the covert constraint 1 − ϵ . coefficients, as described in Proposition 1. In contrast, the baseline method selects cooperativ e users solely according to the instantaneous channel gains between the users and Bob [28]–[30]. In addition, when computing the optimal K ∗ , the proposed method considers the distinct distances between the users and W illie, while the baseline method assumes identical distances from users to Willie and Bob, respectively , despite the actual dif ferences, follo wing the assumption in [30]. T o validate the effecti veness of the proposed method, we compare the optimized results, i.e., P ∗ a , K ∗ , and R ∗ with respect to the the stringency of the cov ert constraint, 1 − ϵ . In Figs. 7 (a) and (b), we present the ratio of the optimized transmit power for the co vert message to the maximum trans- mit power , P ∗ a /P max , and the optimal number of cooperativ e users, K ∗ , respecti vely . It is observed that in the baseline method, a more stringent covert constraint, i.e., a smaller ϵ , is met primarily by increasing the number of cooperativ e users rather than decreasing Alice’ s transmit po wer . Meanwhile, the proposed method adopts a similar strategy when the co vert- ness requirement is moderate, i.e., 1 − ϵ < 0 . 93 . Howe ver , when the requirement becomes strict, i.e., 1 − ϵ ≥ 0 . 93 , the proposed method shifts its strategy by decreasing the transmit power for the covert message instead of further increasing the number of cooperativ e users. This strategic shift occurs because, in a spatially heterogeneous network, the interference effecti veness varies significantly among users. The proposed method exploits this spatial heterogeneity by selectiv ely utilizing only those users who effectiv ely interfere with W illie without excessi vely interfering with Bob . Beyond a certain point, adding more inefficient users yields diminishing returns, making power reduction the optimal choice. In con- trast, since the baseline method assumes homogeneous channel conditions, it incorrectly percei ves all users as equally effecti ve interferers, leading to a continuous and inefficient increase in the number of cooperativ e users. Fig. 7 (c) demonstrates that the proposed method improv es the cov ert rate compared with the baseline method. In particu- lar , as the cov ert constraint becomes more stringent, the perfor- mance gap between the proposed and baseline methods gro ws larger . This indicates that incorporating the distinct spatial locations of users into the optimization process substantially enhances cov ert performance, especially under stringent covert constraints, thereby highlighting the necessity of the proposed approach. Lastly , it is observed in Figs. 7 (a), (b), and (c) that when a stringent cov ert constraint is required, i.e., 1 − ϵ ≥ 0 . 97 , the baseline method fails to satisfy the cov ert constraint. In contrast, the proposed method is able to meet such a stringent cov ert constraint requirement. This implies that accounting for the distinct spatial locations of users broadens the range of achiev able cov ert constraint stringency . V I I . C O N C L U S I O N This paper in vestigated uplink multi-user cov ert commu- nication in which spatially distributed users assist the cov ert transmission. W e mathematically proved that, under the con- sidered system model, the on–off scheme is the optimal policy for designing the interference power transmitted by distributed users. With the optimal on–off scheme, closed- form expressions were deriv ed for the minimum number of cooperativ e users and the activ ation threshold required to satisfy a given cov ert constraint. Based on these expressions, we conducted a comprehensive analysis of the covert com- munication performance with respect to system parameters. In addition, we proposed an intelligent piecewise search al- gorithm to maximize the achie vable rate under both power and cov ert constraints, jointly optimizing the transmit power of the cov ert message and the interferences transmitted by spatially heterogeneous users. Crucially , we demonstrated for the first time that the spatial heterogeneity of distributed users acts as a fundamental advantage, significantly enhancing cov ert communication performance compared to con ventional homogeneous scenarios. A P P E N D I X A P RO O F O F P RO P O S I T I O N 1 Giv en a fixed P a , the optimization problem in (13) can be reformulated as ¯ P ∗ = argmax ¯ P P a | h a a,b | 2 P M m =1 P m | h a m,b | 2 + σ 2 b (37a) s.t. (13b) and (13d) . First, we analyze the minimum DEP associated with the cov ert constraint in (13b). T o deri ve the DEP , we employ a moment-matching based approximation technique, where the sum of Gamma-distributed random variables is approximated as another Gamma distribution with the same first and second moments. The feasibility and tightness of this approximation scheme hav e been extensi vely analyzed and v alidated in [37]– [39]. Thus, T w in (9) can be reformulated to T w − σ 2 w ∼ Γ ψ 2 Ψ , Ψ ψ , H 0 , Γ ( ψ + λ a,w P a ) 2 Ψ+( λ a,w P a ) 2 , Ψ+( λ a,w P a ) 2 ψ + λ a,w P a , H 1 , (38) where ψ = P M m =1 λ m,w P m and Ψ = P M m =1 λ 2 m,w P 2 m . F or sufficiently large M , the Gamma distribution con verges to a normal distribution [40], yielding T w − σ 2 w ∼ ( N ( ψ , Ψ) , H 0 , N ψ + λ a,w P a , Ψ + λ 2 a,w P 2 a , H 1 . (39) 11 Based on the probabilistic distribution of (39) and the defini- tion of the DEP in (10), the DEP can be calculated as ζ = Pr( T w > γ | H 0 ) + Pr( T w ≤ γ | H 1 ) = Q γ − ψ √ Ψ | {z } ( a ) + Q ( ψ + λ a,w P a ) − γ q Ψ + λ 2 a,w P 2 a | {z } ( b ) , (40) where Q ( · ) denotes the standard Gaussian Q -function. Assum- ing that the false alarm probability is set to α , i.e., P F A = α , the detection threshold γ can be obtained from result (a) in (40) as γ = √ Ψ Q − 1 ( α ) + ψ , (41) and with the result (b) in (40) and (41), the corresponding miss detection probability is given by P MD = Q λ a,w P a − √ Ψ Q − 1 ( α ) q Ψ + λ 2 a,w P 2 a . (42) Consequently , the DEP , as a function of α , can be expressed as ζ = α + Q λ a,w P a − √ Ψ Q − 1 ( α ) q Ψ + λ 2 a,w P 2 a . (43) It is noteworthy that ζ in (43) is a monotonically increasing function of Ψ for any 0 ≤ α ≤ 1 . Moreo ver , the minimum detection error probability ζ min also increases monotonically with Ψ . Suppose that for two v alues Ψ < ˆ Ψ , there exist optimal thresholds α ∗ and ˆ α minimizing ζ ( α, Ψ) and ζ ( α, ˆ Ψ) , respectiv ely . Then, by definition, ζ min (Ψ) = ζ ( α ∗ , Ψ) ≤ ζ ( ˆ α, Ψ) , and because ζ increases with Ψ for any fixed α , ζ ( ˆ α, Ψ) < ζ ( ˆ α, ˆ Ψ) = ζ min ( ˆ Ψ) . Therefore, ζ min (Ψ) is strictly increasing with respect to Ψ . By applying Sedrakyan’s Lemma [41], we obtain Ψ M 2 = 1 M M X m =1 λ m,w P m M 2 ≥ 1 M 3 M X m =1 λ m,w P m ! 2 , (44) where the inequality becomes tight as M grows large. Hence, for sufficiently large M , we hav e Ψ ≈ ψ 2 / M , and ζ min becomes a monotonically increasing function of ψ 2 / M . There- fore, the covert constraint can be equiv alently expressed as ψ = M X m =1 λ m,w P m ≥ δ, (45) where δ ≜ √ M ζ − 1 min (1 − ϵ ) . The optimization problem in (37) can be reformulated as ¯ P ∗ = arg min ¯ P M X m =1 P m | h a m,b | 2 + σ 2 b , (46a) s.t. M X m =1 λ m,w P m ≥ δ and (13d) (46b) T ABLE I F E AS I B L E S O LU T I O NS U N DE R T HE K K T C O N D IT I O N S ( N S: N O S O LU T I O N ) . | h a m,b | 2 λ m,w > ν ∗ | h a m,b | 2 λ m,w = ν ∗ | h a m,b | 2 λ m,w < ν ∗ ω ∗ m = 0 P ∗ m = 0 λ m,w P ∗ m = δ − P m ∈C P ∗ j NS ω ∗ m > 0 NS NS P ∗ m = P max Now , to solve the optimization problem in (46), we first deri ve the Karush–Kuhn–T ucker (KKT) conditions with Lagrange multipliers, i.e., { ϕ m , ω m , ν | m ∈ { 1 , 2 , . . . , M }} , as • Stationarity: | h a m,b | 2 − ϕ ∗ m + ω ∗ m + ν ∗ λ m,w = 0 , ∀ m . • Complementary slackness: ϕ ∗ m P ∗ m = 0 , ω ∗ m ( P ∗ m − P max ) = 0 , and ν ∗ ( P M m =1 λ m,w P m − δ ) = 0 . • Feasibility: 0 ≤ P ∗ m ≤ P max , P M m =1 λ m,w P ∗ m ≥ δ , and ϕ ∗ m , ω ∗ m , ν ∗ ≥ 0 . The feasible solutions, which correspond to the combinations of optimization variables and Lagrange multipliers satisfying the KKT conditions, are summarized in T able I. Thus, the optimal transmit power for each non-cov ert user is expressed as P ∗ m = P max , | h a m,b | 2 λ m,w < τ , 0 , | h a m,b | 2 λ m,w > τ , δ − P m ∈C P max λ m,w , | h a m,b | 2 λ m,w = τ , (47) where C denotes the set of selected cooperative users, i.e., C = { m ′ : | h a m ′ ,b | 2 /λ m ′ ,w < τ } and τ = ν ∗ . Note that if U m is a non-cov ert user satisfying | h a m,b | 2 /λ m,w = τ , the user cannot determine the transmit po wer from (47) since U m cannot have the kno wledge of the set C , i.e., the channels between the other users and Bob. Consequently , the optimal power profile is giv en by the following on–off scheme, as expressed in (48). P ∗ m = P max , | h a m,b | 2 λ m,w ≤ τ , 0 , | h a m,b | 2 λ m,w > τ . (48) A P P E N D I X B P RO O F O F L E M M A 1 By le veraging the moment-matching based Gamma approx- imation technique introduced in [37]–[39], the PDF of T w − σ 2 w in (17) can be approximated as T w − σ 2 w ∼ Γ θ 2 Θ , Θ θ , H 0 , Γ θ 2 Θ , Θ θ ∗ Γ (1 , λ a,w P a ) , H 1 , (49) where θ = P K i =1 λ m i ,w P max and Θ = P K i =1 λ 2 m i ,w P 2 max . Recall that a Gamma distribution con ver ges to a Gaussian distribution as its shape parameter increases [34], [42]. In our scenario, the suf ficiently large number of cooperative users, 12 K , results in a large shape parameter in (49). Consequently , the equation of (49) can be approximated to T w − σ 2 w ∼ ( N ( θ , Θ) , H 0 , N ( θ , Θ) ∗ Γ (1 , λ a,w P a ) , H 1 . (50) Practically , the set of selected users is unknown to Willie. Let S ⊂ { 1 , . . . , M } with |S | = K denote the (unkno wn) selection, drawn uniformly at random without replacement. Conditioned on S , the equation of (50) can be reformulated by T w − σ 2 w | S ∼ ( N ( θ S , Θ S ) , H 0 , N ( θ S , Θ S ) ∗ Γ (1 , λ a,w P a ) , H 1 , (51) where θ S = P m ∈S λ m,w P max and Θ S = P m ∈S λ 2 m,w P 2 max . As S is randomly drawn and unkno wn to W illie, the ov erall statistics of T w − σ 2 w must incorporate this selection induced randomness. Equiv alently , the mean and variance must be computed by av eraging the conditional moments with respect to the random user selection set S . By the la w of total expectation and variance [34], [42], the ov erall mean, Ξ and variance, Σ of T w − σ 2 w are obtained by av eraging the conditional mean θ S and variance Θ S ov er the random user selection S , yielding Ξ ≜ E S [ θ S ] = K M M X i =1 λ i,w P max , (52) and Σ ≜ E S [Θ S ] + V ar S [ θ S ] = P 2 max " K M M X i =1 λ 2 i,w + K ( M − K ) M − 1 × 1 M M X i =1 λ i,w − 1 M M X j =1 λ j,w 2 # , (53) where E S [Θ S ] is the expected conditional variance of the interference, and V ar S ( θ S ) is the v ariance of the conditional mean due to random user selection. The latter term, V ar S ( θ S ) , incorporates the finite population correction (FPC) [43], [44] since the users are sampled without replacement. Accordingly , the false-alarm probability , P F A , is defined as P F A = Pr T w − σ 2 w > ˆ γ H 0 ≈ Q ˆ γ − Ξ √ Σ , (54) where ˆ γ ≜ γ − σ 2 w . In addition, the miss-detection probability at W illie can be derived by P MD = Pr T w − σ 2 w ≤ ˆ γ ; H 1 = Pr( X + Y ≤ ˆ γ ) = Z ∞ −∞ 1 √ 2 π Σ exp − ( y − Ξ) 2 2Σ γ 1 , ˆ γ − y ∆ dy = Q − ˆ γ − Ξ √ Σ − exp − 2∆( ˆ γ − Ξ) − Σ 2∆ 2 × Q − ∆( ˆ γ − Ξ) − Σ √ Σ ∆ , (55) where X ∼ Γ(1 , ∆) with ∆ ≜ P a λ a,w and Y ∼ N (Ξ , Σ) . Combining (55) with (54) gives ζ ( γ ) = P F A + P MD = 1 − exp − 2∆( ˆ γ − Ξ) − Σ 2∆ 2 Φ ˆ γ − Ξ − Σ / ∆ √ Σ = 1 − exp − 2∆( ˆ γ − Ξ) − Σ 2∆ 2 Q − ∆( ˆ γ − Ξ) − Σ √ Σ ∆ , which matches (18). A P P E N D I X C P RO O F O F T H E O R E M 1 From (23), the condition ζ min = 1 − ϵ can be written as 1 − 1 √ π q Σ 2∆ 2 + q Σ 2∆ 2 + 4 π = 1 − ϵ, (56) which is equivalent to Σ 2∆ 2 = 1 − 4 ϵ 2 2 ϵ √ π 2 . (57) Let c ϵ ≜ 1 /ϵ 2 − 8+16 ϵ 2 2 π and recall ∆ = P a λ a,w . By substituting the marginal second-moment term Σ from (53) into (57), we obtain 1 ( P a λ a,w ) 2 P 2 max " K M M X m =1 λ 2 m,w + K ( M − K ) M − 1 · 1 M M X i =1 λ i,w − 1 M M X j =1 λ j,w 2 # = c ϵ . (58) Define the empirical mean-square and variance E ≜ E [ λ 2 w ] = 1 M M X i =1 λ 2 i,w and V ≜ V ar[ λ w ] = 1 M M X i =1 λ i,w − 1 M M X j =1 λ j,w 2 . Then (58) can be rearranged as P 2 max K P 2 a λ 2 a,w E + M − K M − 1 V = c ϵ . (59) For large M , M − K M − 1 ≈ M − K M = 1 − K M , so that E + M − K M − 1 V ≈ E + V − K M V . Introduce the constant, C ≜ P 2 max / ( P 2 a λ 2 a,w c ϵ ) , and re write (58) with equality at the threshold as C K E + V − K M V = 1 . Solving via the quadratic formula and simplifying gi ves K = M 2 V ( E + V ) ± r ( E + V ) 2 − 4 V C M ! . 13 Since we seek the minimum K , the physically relev ant solu- tion is the smaller root, K 1 = M 2 V ( E + V ) − r ( E + V ) 2 − 4 V C M ! . Consequently , considering the integer constraint on K , the minimum number of cooperativ e users is determined as K min = ⌈ K 1 ⌉ . This concludes the proof. R E F E R E N C E S [1] Y . Jiang, L. W ang, H.-H. Chen, and X. Shen, “Physical layer covert communication in b5g wireless networks—its research, applications, and challenges, ” Pr oceedings of the IEEE , v ol. 112, no. 1, pp. 47–82, 2024. [2] B. A. Bash, D. Goeckel, and D. T owsley , “Limits of reliable commu- nication with low probability of detection on A WGN channels, ” IEEE Journal on Selected Areas in Communications , vol. 31, no. 9, pp. 1921– 1930, 2013. [3] P . H. Che, M. Bakshi, and S. Jaggi, “Reliable deniable communication: Hiding messages in noise, ” in 2013 IEEE International Symposium on Information Theory , 2013, pp. 2945–2949. [4] M. R. Bloch, “Covert communication over noisy channels: A resolv- ability perspectiv e, ” IEEE T ransactions on Information Theory , vol. 62, no. 5, pp. 2334–2354, 2016. [5] L. W ang, G. W . W ornell, and L. Zheng, “Fundamental limits of communication with lo w probability of detection, ” IEEE T ransactions on Information Theory , vol. 62, no. 6, pp. 3493–3503, 2016. [6] K. S. K. Arumugam and M. R. Bloch, “Keyless covert communication over multiple-access channels, ” in 2016 IEEE International Symposium on Information Theory (ISIT) , 2016, pp. 2229–2233. [7] ——, “Covert communication over a k -user multiple-access channel, ” vol. 65, no. 11, pp. 7020–7044, 2019. [8] V . Y . F . T an and S.-H. Lee, “Time-di vision is optimal for covert communication ov er some broadcast channels, ” IEEE T ransactions on Information F orensics and Security , vol. 14, no. 5, pp. 1377–1389, 2019. [9] K.-H. Cho and S.-H. Lee, “T reating interference as noise is optimal for covert communication over interference channels, ” IEEE Tr ansactions on Information F orensics and Security , vol. 16, pp. 322–332, 2021. [10] S. Lee, R. J. Baxley , M. A. W eitnauer, and B. W alkenhorst, “ Achieving undetectable communication, ” IEEE Journal of Selected T opics in Signal Pr ocessing , vol. 9, no. 7, pp. 1195–1205, 2015. [11] K. Shahzad and X. Zhou, “Covert wireless communications under quasi-static fading with channel uncertainty , ” IEEE T ransactions on Information F or ensics and Security , vol. 16, pp. 1104–1116, 2021. [12] J. W ang, W . T ang, Q. Zhu, X. Li, H. Rao, and S. Li, “Covert commu- nication with the help of relay and channel uncertainty , ” IEEE Wir eless Communications Letters , vol. 8, no. 1, pp. 317–320, 2019. [13] R. Sun, B. Y ang, S. Ma, Y . Shen, and X. Jiang, “Cov ert rate maximiza- tion in wireless full-duplex relaying systems with power control, ” IEEE T ransactions on Communications , vol. 69, no. 9, pp. 6198–6212, 2021. [14] R. Sun, B. Y ang, Y . Shen, X. Jiang, and T . T aleb, “Covertness and secrecy study in untrusted relay-assisted d2d networks, ” IEEE Internet of Things Journal , vol. 10, no. 1, pp. 17–30, 2023. [15] J. Bai, J. He, Y . Chen, Y . Shen, and X. Jiang, “On covert communication performance with outdated csi in wireless greedy relay systems, ” IEEE T ransactions on Information F or ensics and Security , vol. 17, pp. 2920– 2935, 2022. [16] T . V . Sobers, B. A. Bash, S. Guha, D. T owsle y , and D. Goeckel, “Covert communication in the presence of an uninformed jammer , ” IEEE T ransactions on W ir eless Communications , vol. 16, no. 9, pp. 6193– 6206, 2017. [17] K. Li, P . A. K elly , and D. Goeckel, “Optimal po wer adaptation in covert communication with an uninformed jammer, ” IEEE T ransactions on W ireless Communications , vol. 19, no. 5, pp. 3463–3473, 2020. [18] K. Shahzad, X. Zhou, S. Y an, J. Hu, F . Shu, and J. Li, “ Achieving covert wireless communications using a full-duplex receiver , ” IEEE T ransactions on W ir eless Communications , v ol. 17, no. 12, pp. 8517– 8530, 2018. [19] J. Hu, S. Y an, X. Zhou, F . Shu, and J. Li, “Covert wireless commu- nications with channel in version power control in Rayleigh fading, ” IEEE T ransactions on V ehicular T echnology , v ol. 68, no. 12, pp. 12 135– 12 149, 2019. [20] J. Zhang, M. Li, M.-J. Zhao, X. Ji, and W . Xu, “Multi-user beam training and transmission design for co vert millimeter-wa ve communication, ” IEEE T ransactions on Information F orensics and Security , vol. 17, pp. 1528–1543, 2022. [21] H. Mao, X. Pi, L. Zhu, Z. Xiao, X.-G. Xia, and R. Zhang, “Sum rate maximization for movable antenna enhanced multiuser cov ert commu- nications, ” IEEE Wir eless Communications Letters , vol. 14, no. 3, pp. 611–615, 2025. [22] X. Jiang, Z. Y ang, N. Zhao, Y . Chen, Z. Ding, and X. W ang, “Resource allocation and trajectory optimization for uav-enabled multi-user covert communications, ” IEEE T ransactions on V ehicular T echnology , vol. 70, no. 2, pp. 1989–1994, 2021. [23] H. Lei, J. Jiang, I. S. Ansari, G. Pan, and M.-S. Alouini, “T rajectory and po wer design for aerial multi-user covert communications, ” IEEE T ransactions on Aer ospace and Electr onic Systems , vol. 60, no. 4, pp. 4574–4589, 2024. [24] J. Xu, L. Bai, X. Xie, and L. Zhou, “Collaborative secret and covert communications for multi-user multi-antenna uplink uav systems: De- sign and optimization, ” IEEE T ransactions on W ireless Communications , vol. 24, no. 7, pp. 6020–6035, 2025. [25] B. He, S. Y an, X. Zhou, and H. Jafarkhani, “Covert wireless communi- cation with a poisson field of interferers, ” IEEE T ransactions on W ireless Communications , vol. 17, no. 9, pp. 6005–6017, 2018. [26] R. Soltani, D. Goeckel, D. T owsley , B. A. Bash, and S. Guha, “Cov ert wireless communication with artificial noise generation, ” IEEE T rans- actions on Wir eless Communications , vol. 17, no. 11, pp. 7252–7267, 2018. [27] T .-X. Zheng, Z. Y ang, C. W ang, Z. Li, J. Y uan, and X. Guan, “Wireless covert communications aided by distrib uted cooperati ve jamming over slow fading channels, ” IEEE T ransactions on W ireless Communications , vol. 20, no. 11, pp. 7026–7039, 2021. [28] J. Lee, D. T . Dinh, H. Y eom, S.-H. Lee, and J. Ha, “Multiuser cooperation for covert communication under quasi-static fading, ” IEEE T ransactions on Information F or ensics and Security , vol. 18, pp. 4625– 4639, 2023. [29] J. Lee, H. Y eom, S.-H. Lee, and J. Ha, “Channel correlation in multi- user covert communication: Friend or foe?” IEEE Tr ansactions on Information F or ensics and Security , vol. 19, pp. 1469–1482, 2024. [30] H. Y eom, J. Lee, S.-H. Lee, and J. Ha, “Covert communication with multi-users cooperation at unequal distances, ” in 2024 IEEE Interna- tional Conference on Communications (ICC) , 2024, pp. 121–126. [31] T . Xu, L. Sun, S. Y an, J. Hu, and F . Shu, “Pilot-based channel estimation design in covert wireless communication, ” CoRR , vol. abs/1908.00226, 2019. [Online]. A vailable: http://arxiv .org/abs/1908.00226 [32] B. A. Bash, D. Goeckel, and D. T owsley , “Covert communication gains from adversary’s ignorance of transmission time, ” IEEE T ransactions on Wir eless Communications , vol. 15, no. 12, pp. 8394–8405, 2016. [33] J. Neyman and E. S. Pearson, “Ix. on the problem of the most efficient tests of statistical hypotheses, ” Philosophical T ransactions of the Royal Society of London. Series A, Containing P apers of a Mathematical or Physical Character , vol. 231, no. 694-706, pp. 289–337, 1933. [34] G. Casella and R. L. Berger , Statistical Inference , 2nd ed. Pacific Grove, CA, USA: Duxbury Press, 2002. [35] E. T . Whittak er and G. N. W atson, A Course in Modern Analysis . Cambridge University Press, 1990. [36] 3rd Generation Partnership Project (3GPP), “Spatial channel model for multiple input multiple output (mimo) simulations, ” 3GPP , T echnical Report TR 25.996. [37] A. M. Mathai, A Handbook of Generalized Special Functions for Statistical and Physical Sciences . Oxford University Press, 1993. [38] P . G. Moschopoulos, “The distribution of the sum of independent gamma random variables, ” Annals of Statistics , vol. 13, no. 1, pp. 365–372, 1985. [39] S. Covo, “ A novel single-gamma approximation to the sum of indepen- dent gamma random variables, ” Electr onic J ournal of Statistics , vol. 8, pp. 1274–1280, 2014. [40] A. Papoulis and S. U. Pillai, Pr obability , Random V ariables, and Stochastic Pr ocesses , 4th ed. New Y ork, NY , USA: McGraw-Hill, 2002. [41] N. Sedrakyan, “ About the applications of mean v alue theorems for analyzing inequalities, ” The Mathematical Gazette , vol. 81, no. 492, pp. 136–139, 1997. [42] S. M. Ross, Intr oduction to Pr obability Models , 12th ed. Amsterdam, The Netherlands: Academic Press, 2019. [43] W . G. Cochran, Sampling T echniques , 3rd ed. John Wile y & Sons, 1977. [44] S. L. Lohr , Sampling: Design and Analysis , 3rd ed. CRC Press, 2019.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment