Optimizing Entanglement Distribution Protocols: Maximizing Classical Information in Quantum Networks
Efficient entanglement distribution is the foundational challenge in realizing large-scale Quantum Networks. However, state-of-the-art solutions are frequently limited by restrictive operational assumptions, prohibitive computational complexities, an…
Authors: Ethan Sanchez Hidalgo, Diego Zafra Bono, Guillermo Encinas Lago
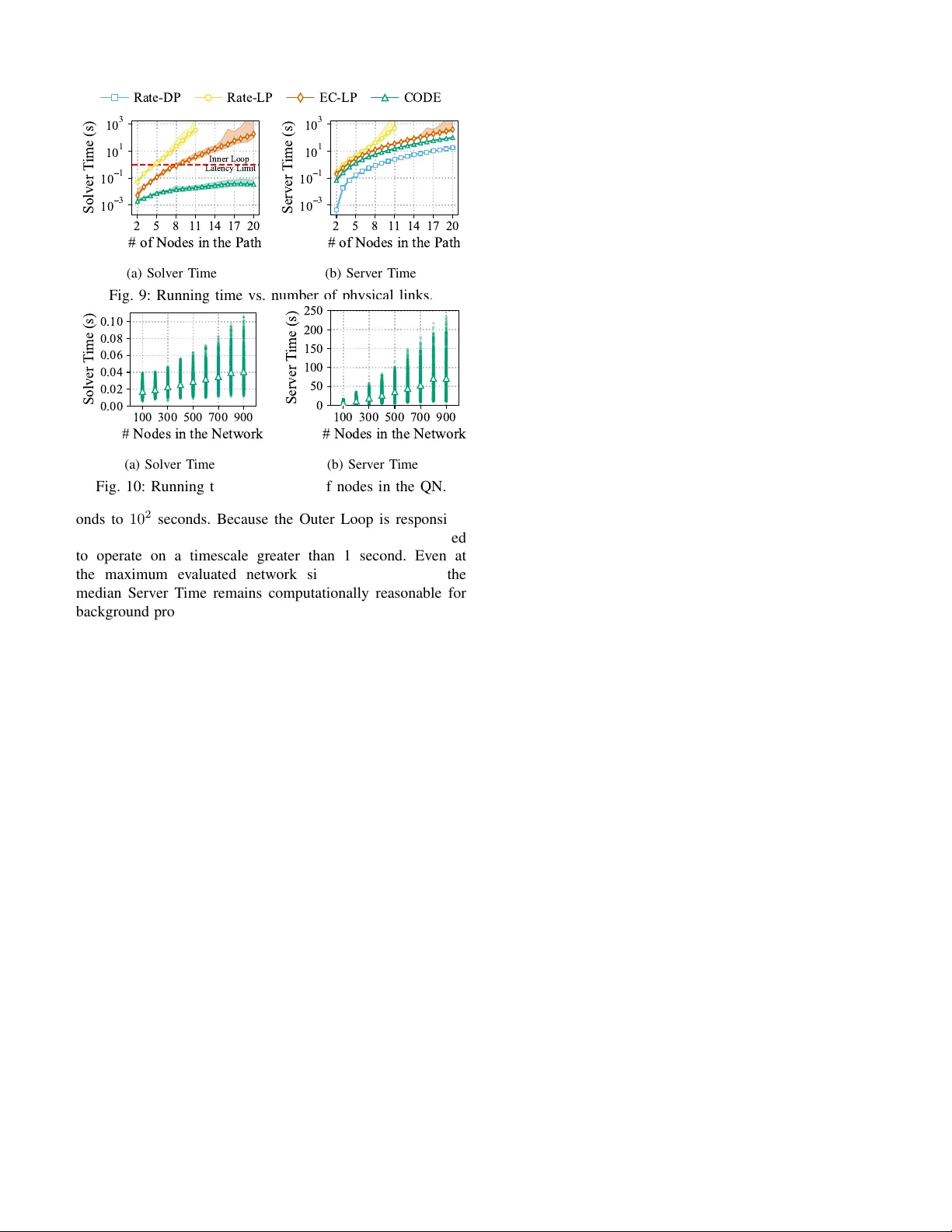
1 Optimizing Entanglement Distrib ution Protocols: Maximizing Classical Information in Quantum Networks Ethan Sanchez Hidalgo ∗ , Diego Zafra Bono, Guillermo Encinas Lago, J. Xa vier Salv at Lozano ∗ , Jose A. A yala-Romero, Xavier Costa Perez, Senior Member , IEEE This work has been submitted to the IEEE for possible publication. Copyright may be transferred without notice, after which this version may no longer be accessible. Abstract —Efficient entanglement distribution is the founda- tional challenge in realizing large-scale Quantum Networks (QNs). However , state-of-the-art solutions are frequently limited by restrictiv e operational assumptions, prohibiti ve computational complexities, and performance metrics that misalign with prac- tical application needs. T o overcome these barriers, this paper addresses the entanglement distribution pr oblem by introducing four pi votal advances. First, r ecognizing that the primary appli- cation of quantum communication is the transmission of private information, we derive the Ensemble Capacity (EC) , a novel metric that explicitly quantifies the secure classical information enabled by the entanglement distribution. Second, we pr opose a generalized mathematical formulation that remo ves legacy structural restrictions in the solution space. Our formulation supports an unconstrained, arbitrary sequencing of entangle- ment swapping and purification. Third, to efficiently navigate the resulting combinatorial optimization space, we intr oduce a novel Dynamic Programming (DP)-based hyper graph generation algorithm. Unlike prior methods, our appr oach avoids artificial fidelity quantization, preserving exact, continuous fidelities while proacti vely pruning sub-optimal trajectories. Finally , we encap- sulate these algorithmic solutions into CODE , a system-level, two-tier ed orchestration framework designed to enable near - real-time network responsiveness. Extensive evaluations confirm that our DP-driven architecture yields superior private classical information capacity and significant reductions in computational complexity , successfully meeting the strict sub-second latency thresholds required for dynamic QN operation. Index T erms —Quantum Network, Entanglement Distribution, Optimal Resource Allocation I . I N T RO D U C T I O N Quantum Networks are the next step in secure communi- cations, as they le verage the principles of quantum physics to securely transmit data using entangled particles—typically polarized photons of light transmitted through optical fibers. QNs enable the dev elopment of new applications such as Quantum Ke y Distrib ution (QKD) [1], Quantum Secret Shar- ing (QSS) [2] or Quantum Secure Direct Communication (QSDC) [3]. These applications rely on the ef ficient generation ∗ Corresponding authors. Ethan Sanchez Hidalgo and Diego Zafra Bono were with i2CA T Foundation, Barcelona, Spain (email: ethan.sanchez.hidalgo@gmail.com, diegozafrabono@gmail.com). Guillermo Encinas Lago is with i2CA T Founda- tion, Barcelona, Spain (e-mail: guillermo.encinas@i2cat.net). J. Xavier Salvat Lozano is with NEC Laboratories Europe GmbH, Heidelberg, Germany and Univ ersitat Autonoma de Barcelona (U AB), Bellaterra, Spain (e-mail: josep.xavier .salvat@neclab .eu). Jose A. A yala-Romero is with NEC Labora- tories Europe GmbH, Heidelber g, Germany (e-mail: jose.ayala@neclab.eu). Xavier Costa-Pérez is with NEC Laboratories Europe GmbH, Heidel- berg, Germany , i2CA T Foundation and ICREA, Barcelona, Spain (e-mail: xavier .costa@ieee.org). W ork supported by the European Commission through grants No. 101139270 (ORIGAMI) and SNS-JU-101192521 (Multi-X) and by the CERCA Programme. Destination Source (a) Max. EGR (F = 0.812) Max. Fidelity (F = 0.95) Max. bits (F = 0.886) 0 400 800 1200 1600 2000 # of E2E Entangled Pairs 0.80 0.85 0.90 0.95 1.00 Entangled Pairs Fidelity 0 40 80 120 160 200 E2E Information Bits Entangled Pairs Fidelity Information Bits (b) Fig. 1: Performance analysis of the proposed quantum net- work. (a) Schematic representation. (b) Comparison of differ - ent entanglement distribution strategies. and distribution of Entangled Pairs (EPs) across distant nodes to create and sustain reliable and priv ate end-to-end communi- cation links. Ho wever , distributing EPs across long distances is far from trivial. Optical fiber losses grow exponentially with distance [4], and unlike classical signals, quantum states cannot simply be amplified or regenerated as a consequence of the no-cloning theorem [5]. These constraints pose strict fundamental limits on direct data transmission over QNs, highlighting the need for specialized solutions. Quantum repeaters [6], [7] perform entanglement swap- ping [8], connecting shorter entangled segments to estab- lish entanglement o ver longer distances. Because repeater operations are imperfect, the fidelity the measure of an EP’ s proximity to its ideal reference staterapidly deteriorates. T o address this, repeaters perform entanglement purification [9], combining multiple low-fidelity pairs to distill fewer high- fidelity pairs. Swapping and purification operations are inher- ently interdependent: swapping extends communication range but degrades fidelity , while purification increases fidelity at the cost of reducing the number of av ailable EPs. As a result, QN performance depends heavily on link management strategies that determine which repeaters (and in what order) execute these operations to optimize end-to-end communication [10]– [12]. In this work, we address the Entanglement Distrib ution Pr oblem : the generation, transmission, and management of Entangled Pairs across a Quantum Network. A fundamental limitation of current entanglement distri- bution literature is its prev ailing focus on maximizing the raw Entanglement Generation Rate (EGR) subject to hard fidelity constraints. Optimizing raw generation rates does not intrinsically translate to the maximization of actual data trans- mission. Specifically , it fails to capture the classical private information capacity , which quantifies the volume of data that can be reliably transmitted over a quantum channel [13].T o 2 address this, we shift the optimization objective entirely . W e introduce classical priv ate information as the primary objectiv e and derive a novel performance metricthe Ensemble Capacity (EC) (see Sec. IV)which rigorously quantifies the actual secure classical bit rate enabled by distrib uted entanglement. Figure 1 demonstrates the critical flaw in rate- or fidelity- centric optimization using a 4-hop network topology . For simplicity , all links are assumed to have identical distance (70 km), generation budget (2760 Entangled pairs per second), and initial fidelity . A common approach in the literature is the maximization of the end-to-end EGR ( Max. EGR ) [11], [14]–[17]. While this method achiev es high pair volume, the resulting end-to-end fidelity is frequently compromised, sev erely restricting the transmission of priv ate information. Con versely , the Max. F idelity approach, as in [18], [19], starves the network (EGR reduced by a factor of 17x), b ut ensures a significantly higher state accuracy , enabling the transmission of nearly 5x the number of priv ate bits compared to the pre- vious approach. Finally , by directly optimizing the EC ( Max. bits ), our strategy strikes the optimal balance between rate and fidelity , achieving a 3x improv ement in secure information bits ov er standard approaches. T o the best of our kno wledge, this work is the first to consider this dimension in the entanglement distribution problem. Optimizing the Ensemble Capacity necessitates a fully generalized solution space that permits arbitrary sequencing of swapping and purification operations. Artificially forc- ing purification to occur strictly before swapping [20]–[22] leav es significant performance potential untapped. While un- constrained sequencing has been pre viously attempted using hypergraphs [14], these models relied on the strict discretiza- tion of continuous fidelity values to maintain computational feasibility , leading to inherent degraded state accuracy and sub-optimal operational decisions that compromise the end-to- end entanglement distribution performance. T o overcome these limitations, we introduce a Dynamic Programming (DP)-based hypergraph generation mechanism (Sec. VI-B). This method- ology pro vides two piv otal adv antages. First, it preserv es the exact, continuous fidelity of the distributed EPs, bypassing the deleterious effects of artificial quantization. Second, the algorithm guarantees a finite and tractable solution space by identifying and pruning low-performing operational sequences in advance. As validated by our ev aluation, this DP-driven approach achieves a significant reduction in computational complexity with almost negligible accuracy loss, yielding superior end-to-end performance compared to prior art. Howe ver , ev en an efficient hyper graph generation algo- rithm remains computationally heavy for the real-time-scale dynamics of a physical Quantum Network. T o bridge the gap between theoretical optimization and practical deploy- ment, we introduce a comprehensiv e system-le vel orches- tration framework termed CODE (Sec. VI-E), divided into two nested operational loops. The Outer Loop comprises the computationally intensi ve processing steps and operates on a coarse timescale (seconds to minutes), monitoring the network conditions and demands. Conv ersely , the Inner Loop operates on a finer timescale (10ms to 1s), lev eraging the pre-computed structures to handle rapid fluctuations in user demand and dynamically allocate resources in near -real-time. Our ev aluations confirm that, unlike existing benchmarks, our hierarchical design satisfies the stringent latency constraints imperativ e for near-real-time QN operation. T o the best of our knowledge, CODE provides the first system-level architecture designed to solve the Entanglement Distribution Problem for practical deployment. W e summarize the contrib utions of this work as follows: 1) Ensemble Capacity Metric: W e deriv e the Ensemble Capacity to directly quantify the volume of pri vate clas- sical information transmissible ov er a quantum channel. This shifts the fundamental optimization objecti ve from raw generation rates to actual secure data throughput. 2) Generalized Operational Sequencing: W e formulate a fully unconstrained mathematical model for entanglement distribution. By lifting restrictive structural constraints to accommodate the arbitrary sequencing of swapping and purification operations, our model unlocks pre viously unreachable regions of the optimization space. 3) Continuous-Fidelity DP Hypergraphs: W e introduce a Dynamic Programming-based hypergraph generation algorithm to tractably navigate this vast combinatorial space. By preserving exact continuous fidelities and sys- tematically pruning low-performing branches, we com- pletely eliminate the accuracy degradation inherent in artificial state discretization. 4) System-Level Orchestration Framework: W e encap- sulate our algorithmic solution into a practical, dual- loop network architecture. Rigorous benchmarking con- firms that by decoupling heavy background optimization from near-real-time execution, our framew ork success- fully meets the strict latency constraints required to manage real-world quantum networks. I I . R E L A T E D W O R K Previous research on entanglement distribution has mainly focused on two different directions. On the one hand, many studies aim to maximize the end-to-end EGR without purifi- cation operations, which results in poor end-to-end fidelity , often using EGR-based routing metrics to select paths [11], [15]–[17]. On the other hand, other works set a minimum end-to-end fidelity constraint to compute the best paths [12], [23], [24] but neglect purification. More recently , se veral works incorporated purification into path selection. The works [20]–[22] dev eloped different strategies to ensure a minimum per-link fidelity through purification before swapping. [25] formulates a joint routingpurification problem and designs algorithms for fidelity-guaranteed paths. In contrast, this work incorporates both entanglement swapping and purification op- erations. Critically , unlike prior studies that restrict purification to the initial step, our formulation allows purification to be applied at any stage of the operational sequence. By removing these constraints on the sequence of operations, our approach enables exploration of the full performance potential of QNs. More recently , the work more closely related to ours [14] considers both purification and swapping without constraints in the sequence of operations. This study aims to maximize 3 the EGR under fidelity constraints. Nev ertheless, the maxi- mization of the EGR does not necessarily correspond to the maximization of information transmission or classical private information , which quantifies how much priv ate information can be securely transmitted over a quantum channel [13]. In contrast to pre vious w orks, we consider the classical priv ate information maximization as the main objectiv e, as it directly quantifies the communication capabilities of the network. For that purpose, we derive a novel performance metric (Ensemble Capacity, see Sec. IV) that quantifies the priv ate classical bits of communication enabled by shared entanglement. Classical priv ate information has also been studied analyti- cally to bound secure key rates [26], [27]. These works provide theoretical limits deriv ed from simplified models of the net- works, which are not practical for de veloping or optimizing entanglement distrib ution protocols. The work in [10] is the first to optimize entanglement routing using distillable entan- glement, related to classical pri vate information. Howe ver , it is limited to symmetric topologies, short paths, and shallo w purification, providing a narrow perspective on the problem. I I I . B A C K G RO U N D Quantum communication in quantum networks builds upon the following key principles: 1) Quantum entanglement: Entanglement [28] is a phe- nomenon in quantum mechanics in which two or more parti- cles share a global state that cannot be described by their local states. Measurements on one particle instantaneously correlate with outcomes on its entangled counterpart, a feature known as quantum non-locality . Entangled pairs are the primary resource in QNs, which generate, maintain, and distribute them across spatially separated nodes. The quality of an Entangled Pair is quantified by the fidelity F , measuring the ov erlap between the actual state ρ and a target Bell state | Φ + i : F := h Φ + | ρ | Φ + i , (1) where F = 1 indicates a perfectly entangled pair , and v alues near 0 indicate near orthogonality . State-of-the-art techniques to generate entangled pairs include semiconductor quantum dots [29], nitrogen-v acancy centers in diamond [30], atomic ensembles [31], and nonlinear optical methods such as Spon- taneous Parametric Down Conv ersion [32]. 2) Quantum teleportation and Entanglement swapping: Quantum teleportation [33] is the fundamental mechanism for transferring a quantum state between distant parties without physical transmission, strictly respecting the no-cloning the- orem [5]. Operating within the Local Operations and Clas- sical Communication (LOCC) frame work, it requires a pre- shared Entangled Pair. The sender performs a joint Bell- state measurement (BSM) on the target qubit and their half of the entangled pair . Upon receiving the two-bit classical measurement outcome from the sender, the receiv er applies a conditional unitary operation to reconstruct the original state. Entanglement swapping [8] leverages this exact mecha- nism to establish long-distance communication by effecti vely teleporting entanglement itself. Given two independent pairs, ( A, B ) and ( C, D ) , an intermediate node holding particles B and C performs a local BSM on them. Once the in- termediate node relays the classical measurement outcome to the remote end nodes for local corrections, particles A and D become entangled despite never physically interacting, seamlessly bridging the tw o initial segments. 3) Entanglement purification: Entanglement purification or distillation [34], is a probabilistic process designed to enhance the fidelity of EPs. Purification extracts a smaller set of entangled pairs with higher fidelity from a large set of noisy or imperfectly entangled pairs [35]. I V . E N S E M B L E C A PAC I T Y : C L A S S I C A L P R I V AT E I N F O R M A T I O N A NA LY S I S In this section, we introduce a novel metric to ev aluate the performance of a QN: the Ensemble Capacity . While metrics such as the end-to-end fidelity of shared pairs [12], the end- to-end Entanglement Generation Rate (EGR) [11], the request fulfillment rate [36], and qubit utilization rate [37] provide valuable insights, the y do not directly quantify the network’ s data transmission capabilities. In contrast, Ensemble Capacity measures the volume of priv ate classical information bits that two end parties can securely exchange. This metric inherently captures the trade-off between the quantity of shared entangled pairs (i.e. where the aggregate count is directly proportional to the EGR) and their fidelity . T o address the entanglement distribution problem from a capacity-centric perspecti ve (see Sec. V) we first define the capacity of a single Entangled Pair (see Sec. IV -A) and then generalize this definition to a set of entangled pairs, formally defining the Ensemble Capacity (see Sec. IV -B). Finally , we discuss the uni versality of this met- ric, making the Ensemble Capacity applicable across diverse quantum applications (Sec. IV -C). A. Single Entangled P air Capacity W e define the capacity C of a single Entangled Pair ρ shared between a source s and destination d nodes as the amount of priv ate classical bits C ( ρ ) that can be securely transmitted from s to d using ρ assisted by adaptive Local Operations and Classical Communication (LOCC) operations. Let F denote the fidelity of an EP ρ modeled as a mixed two-qubit state (i.e., a W erner state modeling imperfect entanglement as a combination of a Bell state and white noise [38]). As established in [39], teleportation over noisy entangled states, is equiv alent to transmitting through a depo- larizing quantum channel E p of parameter p = 4(1 − F ) 3 , i.e. C ( ρ ) = C ( E p ) . Consequently , the capacity C ( ρ ) is bounded by k ( p ) − 3 p 4 log 2 (3) ≤ C ( ρ ) ≤ k ( p ) , (2) where k ( p ) := 1 − H 2 (3 p/ 4) , and H 2 is the binary Shannon entropy . These bounds are derived assuming arbitrary teleportation protocols; this generality holds because QKD- style protocols can be reformulated in terms of entanglement- based teleportation, as sho wn in [40]. 4 B. Multiple Entangled P airs Capacity T ransmitting information via a single pair alone is often inefficient. Instead, entanglement is typically generated in a parallel, producing multiple end-to-end pairs simultaneously . Therefore, we generalize the single-pair capacity to a network- lev el figure of merit: the Ensemble Capacity . W e define an ensemble as a set of Entangled Pairs { ρ i } n i =1 shared between a source s and destination d . The Ensemble Capacity (EC), denoted by C ( ⊗ n i =1 ρ i ) , is the number of pri vate classical bits that can be securely transmitted between s and d by using the ensemble { ρ i } n i =1 and adaptiv e LOCC operations. While this definition captures the theoretical maximum data- carrying potential, computing C ( ⊗ ρ i ) is generally intractable due to the complexity of ev aluating collectiv e operations over entangled resources. Consequently , following the fundamental bounds in [ 4], we adopt a conserv ativ e approximation by considering a lower bound on this quantity as the sum of individual pair capacities, P n i =1 C ( ρ i ) . By substituting p = 4(1 − F ) 3 into the lower bound of Eq. (2), we obtain the computable lower bound for the Ensemble Capacity: C ( ⊗ n i =1 ρ i ) = n X i =1 k 4(1 − F i ) 3 − (1 − F i ) log 2 (3) . (3) C. Ensemble Capacity as a Universal Metric The goal of quantum networks—regardless of the specific application—is always to maximize the number of shared high-fidelity entangled pairs in the least amount of time. Howe ver , the definition of “high-fidelity” varies across use cases. For example, QKD requires a minimum threshold of approximately F ≥ 0 . 8 [41], whereas distributed quantum computing typically demands fidelity exceeding 0 . 9 [42], [43]. This difference exposes a key limitation of the prev ailing optimization methodology , which typically maximizes the entanglement generation rate subject to a hard fidelity con- straint [12], [21], [25]. Choosing a fixed threshold hard-codes the target application into the network design, yielding solu- tions that are not comparable across use cases and collapsing the subtle pair quantity and fidelity trade-off into an arbitrary operating point. In contrast, Ensemble Capacity provides a use-case-agnostic objectiv e. It characterizes the aggreg ate end- to-end entanglement the network can deliver across all quality lev els, allowing the network to be optimized once for maximal provisioning capability while enabling specific applications to select their own operating regions. V . E N TA N G L E M E N T D I S T R I B U T I O N P RO B L E M F O R M U L A T I O N In this section, we present a mathematical frame work for the Entanglement Distribution Problem that maximizes the Ensemble Capacity between a source s and a destination d by optimizing the underlying sequences of purification and swapping operations. Our formulation introduces three fundamental advancements over existing literature. First, it generalizes the selection of a single sequence of operations along a path P . Instead, our formulation allows multiple sequences to ex ecute concurrently along the same path, gen- erating an ensemble of distinguishable end-to-end EPs [10], [22]. Second, it allows purification operations at any hop of the distribution sequence. This flexibility significantly expands the solution space, unlocking high-fidelity strategies that are inac- cessible to simpler models [20], [21]. Third, our formulation enables dynamic resource pooling across multiple, potentially ov erlapping paths. By jointly optimizing over non-disjoint paths, the model recognizes when entangled pairs on shared links are underutilized due to bottlenecks elsewhere in the network. Consequently , our approach reallocates these residual resources to co-existing operational sequences, ensuring that no entanglement is wasted when chaining operations across the infrastructure [16], [23]. A. Network Model and Notation A Quantum Network is mathematically modeled as a graph G = ( V , E ) , where the v ertex set V represents the quantum repeaters and the edge set E represents the physical links connecting adjacent nodes. Each edge e ∈ E is characterized by the tuple ( u, v , r e , f e ) , where u and v are two physically adjacent nodes, r e denotes the mean entanglement generation rate (in Hz) and f e represents the mean fidelity of the entangled pairs generated over the fiber-optic channel. W e define the accumulation window T w as the time interval during which entangled pairs are accumulated in quantum memories. W e assume T w is bounded by the quantum memory coherence time (see Sec. VII-C3). Let P s,d be the set of all simple paths between source s and destination d , where each path P ∈ P s,d is an ordered sequence of adjacent physical links. B. Sequences of oper ations T o establish an end-to-end entangled link between a source s and a destination d ov er a path P , P must be transformed into a single virtual link through a structured sequence of entanglement swapping and purification operations. Establish- ing end-to-end connectivity for a path of length k requires exactly k − 1 swaps and provides 2( k − 1) + 1 purification opportunities, as purification may be applied to the input links prior to each swap and to the terminal link. V alid sequences are defined by the specific allocation of purification rounds to these opportunities limited by the a vailable resource pool. 1) Entanglement Generation Pr otocols: W e define an En- tanglement Generation Protocol π as an ordered sequence of purification and entanglement swapping operations over the path P . The sequence of operations of a protocol π transforms the path P into a single virtual link generating an ensemble of indistinguishable entangled pairs ρ π resulting in an end-to- end generation rate R π (in Hz) and fidelity F π . A protocol π operates on the batch of entangled pairs accumulated during a window T w processing them during a time T π p . 2) Entanglement Distribution Schemes: An Entanglement Distribution Scheme S P is defined by a set of Entangle- ment Generation Protocols Π = { π 1 , . . . , π m } and a corre- sponding resource allocation v ector , enabling the concurrent ex ecution of multiple protocols across path P . Formally , 5 S P = { ( π j , R j ) } , where R j = ( R 1 π j , . . . , R k π j ) specifies the absolute resource consumption for protocol π j . Each R i π j denotes the raw EGR drawn from physical link e i ∈ P to support protocol π j . A distribution scheme S P effecti vely creates m distinct ensembles of entangled pairs (i.e. m distinct “flows") yielding a product state ρ S P = ⊗ m i =1 ρ π i ov er a path P . An empty scheme S P = ∅ indicates an idle path. C. Optimization F ramework An optimal solution for the Entanglement Distribution Prob- lem is rarely confined to a single sequence of operations ov er a single path. Since entanglement purification is a non- linear operation where inv esting additional resources yields diminishing returns, the optimal strategy often in volves a com- posite solution. Consequently , the Entanglement Distrib ution Problem must be optimized across multiple paths (utilizing disjoint or partially overlapping paths to aggregate capacity) and div erse Entanglement Generation protocols (executing heterogeneous sequences of operations). Thus, the challenge extends beyond simple shortest-path routing; it requires deter- mining the optimal configuration of schemes S P across the set of all simple paths P s,d between s and d to maximize resource utilization while strictly adhering to link capacity constraints. W e formulate the Entanglement Distribution Problem to maximize the aggregate capacity C between s and d as: max {S P } P ∈P s,d X P ∈P s,d C ( ρ S P ) (4a) subject to: Resource Constraint: X P : e ∈ P X π ∈S P R e π ≤ r e , ∀ e ∈ E . (4b) Non-negati ve Resource Consumption: R e π ≥ 0 ∀ e ∈ E , ∀ π ∈ S P . (4c) The objective function (4a) aggregates the capacities of all ensembles of entangled pairs generated across all active distribution schemes. The resource constraint (4b) ensures that the total physical consumption across all protocols using link e , denoted by R e π , does not exceed the available generation rate r e . Finally , constraint (4c) forces R e π to non-negati ve values. Note that, while quantum entanglement generation is a discrete process (counting individual pairs), our framework models R e π j as continuous variables. This relaxation is justified by the operational context of the network. As the system operates over a large number of synchronized accumulation windows T w , the discrete pair counts are aggreg ated into a long-term av erage throughput. Furthermore, the Ensemble Capacity C is an asymptotic metric defined over large en- sembles of states. Therefore, treating R as a continuous flow variable accurately represents the steady-state performance of the multiple distribution schemes. D. Pr oblem Har dness and Intr actability The joint optimization of path selection and protocol config- uration creates a nested combinatorial explosion that renders the problem intractable. First, the number of simple paths be- tween a pair of nodes in a graph scales exponentially with the network size (specifically , as O ( | V | !) in dense graphs [44]). Second, for each candidate path P of length k , the optimizer must configure a v alid Entanglement Generation Protocol π . On the one hand, the number of valid swapping opera- tions grows following geometric permutations (specifically , as O ( C k − 1 ) , where C is the Catalan number [45] and k is the number of links in the path), growing super-exponentially with path length. On the other hand, at each of the 2( k − 1) + 1 purification opportunities, we must assign a specific number of purification rounds. Third, since the purification strategy on one link changes the consumption requirements for all other protocols sharing that link, these decisions cannot be made in isolation. They are coupled globally via the link capacity constraints (Eq. (4b)). Finally , as established in Sec. IV, the capacity C is strictly con ve x with respect to fidelity . Howe ver , the physical process of purification dictates that fidelity F and av ailable rate R of entangled pairs are inv ersely related via a non-linear efficienc y curv e. T o increase F , one must non- linearly decrease R . Consequently , the interplay of massiv e combinatorial search spaces, globally coupled constraints, and non-linear physical dynamics renders exact optimization computationally infeasible. V I . C O D E : S O L U T I O N P RO P O S A L T o address the Entanglement Distribution Problem defined in the previous section, we propose a comprehensiv e opti- mization framework called called C apacity O ptimization for D istributed E ntanglement (CODE). T o manage the inherent computational intractability of the problem, CODE employs a hierarchical solution strategy . First, it extracts a subset of candidate paths, P ′ s,d ⊆ P s,d . Second, it determines the optimal configuration scheme, S P i , for every path P i ∈ P ′ s,d . The initial computation of P ′ s,d mitigates the factorial complexity of path enumeration by restricting the search space to the N -shortest paths. The rationale behind this design decision, alongside the specific algorithmic details, is discussed in Sec. VI-E. Furthermore, to navigate the super- exponential solution space associated with S P , we adopt a hypergraph-based formulation. This abstraction effecti vely maps the combinatorial sequencing of quantum operations into a structured resource flow problem, enabling the application of Linear Programming (LP) techniques. Constructing this hyper graph, ho wever , presents significant structural challenges. In Sec. VI-A, we introduce a standard hypergraph formulation prev alent in related literature, follo wed by a critical analysis of its limitations (Sec. VI-A4). Most notably , standard approaches rely on strict fidelity discretiza- tion to maintain a finite graph size. This coarse approximation introduces systemic inaccuracies and artificially degrades the achiev able end-to-end netw ork performance. T o overcome these fundamental bottlenecks, we pro- pose a nov el DP-based Hyper graph Generation Algorithm (Sec. VI-B). By lev eraging dynamic programming, this ap- proach efficiently generates a pruned hypergraph that circum- vents the deleterious effects of fidelity discretization. Building on this refined structure, Sec. VI-C formulates the corre- sponding LP , while Sec. VI-D provides a rigorous complexity 6 A B A B … A B T Π B C B C … B C start/en d swa p pu rify Hy per - edg es U V Hy per - ver tices C D C D … C D A C A C … A C B D B D … B D A D A D … A D Fig. 2: Example of the directed graph L P for a path of 4 nodes and 3 links (A-B-C-D). analysis. Finally , Sec. VI-E synthesizes these algorithmic components to present a complete overvie w of the CODE ar- chitecture, alongside practical system implementation details. A. Hyper graph F ormulation T o model the solution space, we build upon the state-of- the-art literature [12], [14] to construct a directed hypergraph L P = ( V , E ) that systematically encodes all feasible states of entanglement and the operational transitions between them. This abstraction maps the combinatorial complexity of the En- tanglement Distribution Scheme into a na vigable flo w graph. 1) Hyper-vertices (Entangled Links): The set of hyper- vertices V encodes the possible states of entangled links be- tween two specific nodes within a path P . Each hyper-verte x is a tuple ( u, v , f ) , representing an ensemble of indistinguishable EPs with fidelity f between nodes u and v on path P . If u and v are directly connected by an edge e u,v ∈ E in the physical topology , the entangled link is termed a physical link . Otherwise, we term it as a virtual link . Additionally , we define two auxiliary hyper -vertices: the source vertex ( ⊥ ) which represents the initial pool of raw resources ov er the path and the sink verte x ( t ) which represents the final successful distribution of end-to-end EPs. 2) Hyper-edges (Sequences of operations): The set of hyper-edges E models the transformation of a path P through a sequence of swapping and purification operations. W e define a hyper-edge ϵ ∈ E as a transition ( L, l out , h, r ϵ ) , where L ⊆ V is the set of input hyper-v ertices, l out is the output hyper-v ertex, and h ∈ { swap, purify , start, end } is the operation type and r is the continuous consumption rate (Hz). W e distinguish between primary operations (swapping and purification, | L | = 2 , denoted as l 1 , l 2 ), which transform the state of e xisting entangled links, and auxiliary operations (initialization and termination, | L | = 1 , denoted as l 1 ), which manage the flow of entanglement resources into and out of the quantum netw ork. W e mathematically formalize the primary operations as follows: 1) Swapping ( swap ): Combines two links sharing an inter- mediate node into one link between non-adjacent nodes. swap : V × V → V ( u, v , f 1 ) , ( v , w, f 2 ) 7− → ( u, w , f swap ( f 1 , f 2 )) (5) Flow conservation requires equal consumption rate r from both inputs. Residual rates on non-bottleneck links remain available in the resource pool for concurrent operations. 2) Purification ( purify ): Consumes two links between the same nodes to yield a single higher-fidelity link. purify : V × V → V ( u, v , f 1 ) , ( u, v , f 2 ) 7− → ( u, v , f pur ( f 1 , f 2 )) (6) Note that this formulation supports both symmetric (where input fidelities are identical, f 1 = f 2 ) and asym- metric purification (where f 1 6 = f 2 ). The explicit functional forms of f swap and f pur are deter- mined by the specific hardware implementation (see Sec. VII). Additionally , we formalize the two auxiliary functions to manage flow boundaries: 3) Initialization ( start ): Maps the source v ertex ⊥ to a set of physical link ( u, v , f 0 ) , representing raw entanglement generation: ( {⊥} , ( u, v , f 0 ) , start , r ) . 4) T ermination ( end ): Maps end-to-end links ( s, d, f ) to the sink vertex t , representing protocol fulfillment: ( { ( s, d, f ) } , t , end , r ) . 3) Hyper graph Structure: The directed hypergraph L P = ( V , E ) represents the operational solution space, where a connected sequence of hyper-edges from source ⊥ to sink t defines an Entanglement Generation Protocol ( π ). T o strictly model the physical constraints of entanglement swapping while ensuring that any spare capacity is preserved for other uses, we impose the follo wing restrictions on the hypergraph: Pair -wise Flow Conservation : A swapping hyper -edge consumes an identical flow rate r ϵ from both input vertices. This reflects the physical reality that the end-to-end rate is strictly bounded by the link with the lo wer EGR. Resource Pooling : Link vertices are modeled as cumulativ e resource pools. Multiple hyper -edges (representing distinct protocols) can draw from the same verte x. Physical v alidity is maintained by ensuring P r ϵ ≤ r e for each link. This mechanism prev ents the loss of “spare capacity” during asym- metric swaps, keeping residual EPs av ailable for additional purification or parallel operations. The Ensemble Capacity C for a protocol is then derived from the terminal flow r end and its associated fidelity f at the sink vertex t , follo wing the definition provided in Sec. IV. Fig. 2 depicts L P for a four-node path P = { A, B , C , D } . The source vertex ⊥ initiates entanglement distribution using physical links via the start operation. Dashed blocks repre- sent fidelity manifolds for specific node pairs; within these, purification hyper-edges transition resource flow r ( i,j ) pur tow ard higher-fidelity states. Swapping hyper-edges utilize r k u − v , swap resources to execute pair-wise combinations of adjacent links: flow from ( A, B ) and ( B , C ) generates virtual links in ( A, C ) , which can then be combined with ( C, D ) to establish the end- to-end link ( A, D ) . The ensemble capacity is computed as 7 the final flo w from the ( A, D ) block is directed to the sink verte x t through termination hyper-edges with EGR r end . This configuration models all operational sequences as traversable paths within a unified flow graph. 4) Hyper graph limitations: Modeling entanglement rates as continuous variables yields a continuous fidelity manifold f ∈ [0 . 5 , 1] , resulting in a hypergraph L P with an infinite verte x set. T o tackle this problem, related literature [14] only considers a discrete set of fidelity values F = { f 0 , . . . , f |F | } for ev ery entangled link in L P . They approximate the resulting link fidelity values f to the largest f i ∈ F s.t. f ≥ f i . This approximation poses severe limitations. First of all, discretizing continuous fidelity values into predefined lower bounds forces physically distinct entangled pairs to share an identical fidelity representation. This uncertainty diminishes the overall system performance; since the capacity of the end- to-end ensemble is highly sensitiv e to fidelity , any inaccuracy in its measurement leads to sub-optimal configurations of the swapping and purification operations. Second, discretization artificially degrades ensemble ca- pacity by collapsing continuous fidelities into lower -bound intervals, rendering models insensitive to qualitativ e dif fer- ences between paths. This creates a structural bias toward quantity o ver quality , where algorithms fav or the highest raw entanglement rates while discarding lower -rate paths with superior true fidelities. Such sub-optimality compounds ov er multiple hops, systematically eliminating high-capacity trajectories. Furthermore, any attempt to mitigate this loss by increasing the resolution of the discrete set F triggers a curse of dimensionality , reintroducing the very computational intractability the approximation sought to a void. B. DP-based Hypergr aph generation algorithm T o address the fundamental limitations of the standard hypergraph formulation, we propose a no vel hypergraph gen- eration mechanism based on Dynamic Programming (DP). In contrast to prior approaches that force continuous quantum states into discrete values, our formulation explicitly preserves the exact, continuous fidelity values of the entangled pairs. Specifically , our DP-based algorithm constructs a pruned hy- pergraph that encapsulates only the most promising sequences of operations in terms of performance. By systematically filtering out sub-optimal configurations early in the process, this strategy ef fectively circumvents the curse of dimension- ality , thereby substantially accelerating both the initial graph generation and the subsequent execution of the LP algorithm. Crucially , this architecture relies on a decoupled optimiza- tion paradigm. The DP phase is designed exclusiv ely to iden- tify the maximum theoretical potential of isolated protocols. The subsequent LP formulation then leverages this solution space to determine the actual e xecution rates, globally opti- mizing the distribution schemes based on concurrent network demands and physical resource a vailability . T o systematically identify a set of high-performance proto- cols, direct maximization of the ensemble capacity cannot be Algorithm 1 Hypergraph Construction via Dynamic Programming Input: Network path P , set of physical links V L , physical link Entanglement Generation Rates ( { r l } | P |− 1 l =1 ), discrete fidelity lev els F , L ′ P ← ∅ Output: Pruned Hypergraph L ′ P Notation: l i u,v : = ( u, v , f ( i ) ) , where f ( i ) ∈ [ f i , f i +1 ) 1: V ′ ← V ′ ∪ {⊥ , t} 2: for l ∈ V L do 3: V ′ ← V ′ ∪ l 4: E ′ ← E ′ ∪ ( {⊥} , l , start , r l ) 5: end for 6: for ∆ = 2 , . . . , | P | − 1 do 7: for u = 1 , . . . , | P | − ∆ do 8: v ← u + ∆ 9: for l i u,w , l j w,v ∈ V ′ do ▷ Perform Swap Operations 10: f new ← f swap ( l i u,w , l j w,v ) 11: r new ← min( r e l i u,w , r e l j w,v ) 12: Find k s.t. f new ∈ [ f k , f k +1 ] 13: if r new > r e l k w,v then 14: V ′ ← V ′ ∪ l new u,v 15: E ′ ← E ′ ∪ ( { l i u,w , l j w,v } , l new u,v , swap , r new ) 16: end if 17: end for 18: for l i u,v , l j u,v ∈ V ′ do ▷ Perform Purify Operations 19: f new ← f purify ( l i u,v , l j u,v ) 20: r new ← min( r e l i u,v , r e l j u,v ) · p succ 21: Find k s.t. f new ∈ [ f k , f k +1 ] 22: if r new > r e l k w,v then 23: V ′ ← V ′ ∪ l new u,v 24: E ′ ← E ′ ∪ ( { l i u,v , l j u,v } , l new u,v , purify , r new ) 25: end if 26: end for 27: end for 28: for f i ∈ F do 29: E ′ ← E ′ ∪ ( { l i s,d } , t , end , r l i s,d ) 30: end for 31: end for employed, as this metric fails to satisfy the optimal substruc- tur e pr operty required by the DP formulation 1 [46]. T o circumvent this fundamental limitation, we reformulate the DP objectiv e: rather than optimizing capacity directly , the algorithm maximizes the achiev able Entanglement Generation Rate (EGR), denoted by r , for a discrete set of minimum fidelities f ∈ F . This reformulation provides two piv otal advantages. First, it restores the requisite optimal substructure property , rendering a problem strictly solv able via DP . Second, it yields a diverse, Pareto-optimal frontier of high-performance solutions, as the algorithm naturally identifies the optimal 1 Consider an optimal end-to-end ensemble generated via a final purification step. The predecessor states (i.e., two lower -fidelity ensembles shared between the same nodes) are not necessarily optimal in terms of their indi vidual capacities. Consequently , a globally optimal capacity cannot be reliably constructed from locally optimal capacity subproblems, violating the optimal substructure property . 8 Entanglement Generation Protocol for every minimum fidelity tier defined in F . Specifically , we employ a “fidelity b ucket- ing” strategy . For each predefined fidelity interval [ f i , f i +1 ) (where f i and f i +1 are consecutive values in F ), the al- gorithm identifies the optimal state tuple ( u, v , f exact ) where f exact ∈ [ f i , f i +1 ) such as the associated EGR is the maximum within the interval [ f i , f i +1 ) . Crucially , unlike standard discretization techniques that systematically round continuous fidelities down to prede- fined thresholds, our fidelity-bucketing strategy retains the true continuous value, f exact , within each hyper-verte x. This ensures that all subsequent operations during the hyper graph construction lev erage precise physical parameters rather than pessimistic lo wer-bound approximations. Consequently , the algorithm rigorously preserves the most promising operational sequences while effecti vely pruning suboptimal trajectories, ultimately maintaining a finite and computationally manage- able graph without sacrificing the physical accuracy of the underlying quantum states. Algorithm 1 details the pseudocode for the proposed DP- based hypergraph generation framework. The procedure starts with an initialization phase (lines 15), wherein the physical links ( V L ) are mapped to the source vertex ⊥ through the start operation. Follo wing this, the algorithm systematically explores all combinations of sub-paths within path P via a set of nested iterations (lines 68). For each e valuated pair of nodes, the framework first considers entanglement swapping. It iterates over all a vailable pairs of physical or virtual links (line 9) to establish a new end-to-end connection across an intermediate node. Upon computing the effecti ve fidelity and EGR for a candidate swap (lines 1011), the algorithm ex ecutes the pruning step: if the candidate yields a strictly superior EGR for its specific fidelity interval, the newly generated virtual link is registered in the hyper-v ertex set V ′ (line 14), and its topological operation is appended to the hyper-edge set E ′ (line 15). Follo wing this, an analogous dynamic programming re- currence is ex ecuted to assess purification operations (lines 1826). This step ev aluates the distillation of available ensem- bles between the same node pairs, ensuring that all high- performing protocols are meticulously encoded into the final, computationally tractable hypergraph structure. T o conclude, the established end-to-end pairs are mapped to the end hyper- verte x t through the end operation (lines 28-30). By strictly restricting the graph topology to these optimal operational trajectories, our methodology achiev es a profound reduction in computational complexity . Specifically , the num- ber of hyper-edges is compressed from O ( | V | 3 |F | 2 ) -the scal- ing characteristic of standard, unpruned formulations found in prior literature-to an upper bound of O ( | V | 2 |F | ) . Crucially , this structural pruning is achie ved without information loss; the framework retains the exact, non-discretized fidelity pa- rameters strictly required for the accurate computation of the Ensemble Capacity . C. Linear Pro gramming F ormulation Using the previous pruned hypergraph L ′ P = ( V , E ) , we formulate the Entanglement Distribution Problem presented in Sec. V as a Linear Program (LP) optimization problem. For each hyper -edge ϵ = ( S, l out , h, r ϵ ) ∈ E , r ϵ is the decision variable associated to the number of Entangled Pairs generated by performing the corresponding operation h ∈ { sw ap, pur if y , star t, end } . Let ρ ϵ denote the quantum state of the EPs generated follo wing ϵ . Then, the LP formulation of the Entanglement Distrib ution Problem is: max r ϵ ,ϵ ∈E X ϵ ∈E end C ( ρ ϵ ) · r ϵ (7a) subject to: Flo w Conservation: ∀ l ∈ V \ {⊥ , t} , (7b) X ϵ ∈ in ( l ) \E pur r ϵ + 1 2 X ϵ ∈ in ( l ) ∩E pur p succ ( ϵ ) · r ϵ ≥ X ϵ ∈ out ( l ) r ϵ . Generation Limits: X ϵ ∈E start ( e ) r ϵ ≤ r e , ∀ e ∈ E . (7c) Non-negati ve Resource Consumption: r ϵ ≥ 0 , ∀ ϵ ∈ E . (7d) The objectiv e function (7a) maximizes aggregate end-to-end Ensemble Capacity by summing terminal assigned e xecution rates r ϵ weighted by their resulting state capacities C ( ρ ϵ ) . Flow conservation (7b) maintains entanglement balance for each verte x l ∈ V \ {⊥ , t} by requiring that total incoming entan- glement rate—comprised of non-purification flow ( in ( l ) \ E pur ) and purification yields ( in ( l ) ∩ E pur ) scaled by 1 2 p succ ( ϵ ) where p succ is the probability of successful purification— satisfies the total outgoing consumption in out ( l ) . This efficiency factor accounts for the physical sacrifice of two lo wer-fidelity pairs to produce one distilled pair . Generation limits (7c) enforce Resource Pooling by restricting the aggregate execution of initialization protocols in E start ( e ) to the hardware generation rate r e of physical link e . Finally , (7d) mandates non-negati ve ex ecution rates r ϵ to ensure physical feasibility . D. Complexity Analysis Related literature shows that a LP problems can be solved in polynomial time in the number of variables using interior-point methods [47]. Based on the formulation in (7), the number of variables in our approach corresponds to the edge count |E | of the graph L P . For an unpruned hypergraph L P , |E | is on the order of O ( | V | 3 |F | 2 ) , where | V | represents the number of vertices in the path and |F | denotes the number of discrete fidelity v alues (Fidelity Resolution). While applying the pruning strategy reduces the variable count to O ( | V | 2 |F | ) , it incurs a computational cost. The DP pruning algorithm is recurrent, operating on | V | 2 states represented by all possible pairs of link nodes. Each state ev aluates two branch types: "swap" and “purify”. The purify branch requires checking |F | 2 states, while the swap branch requires checking | V | · |F | 2 states. Consequently , the total complexity of the DP pruning algorithm is O ( | V | 3 |F | 2 ) . Despite the pruning algorithm having a complexity of O ( | V | 3 |F | 2 ) , this pre-processing step is computationally ad- vantageous. The runtime of LP solvers, denoted as C LP ( N ) , generally scales super-linearly with the number of v ariables N 9 (often O ( N 3 . 5 ) or higher for interior-point methods). Without pruning, the total cost is dominated by solving the LP with a large variable set: C LP ( | V | 3 |F | 2 ) . In contrast, our approach incurs the additiv e pruning cost of O ( | V | 3 |F | 2 ) b ut reduces the optimization step to C LP ( | V | 2 |F | ) . Since the solver’ s complexity C LP ( N ) grows significantly faster than linear time, the reduction in the dimensionality of the LP outweighs the ov erhead of the pre-processing algorithm. E. CODE: C apacity O ptimization for D istributed E ntanglement Having introduced the main building blocks of our solution, we unify the algorithmic components previously described into a cohesiv e orchestration frame work termed CODE: C apacity O ptimization for D istributed E ntanglement. T o ef fectiv ely manage the trade-off between the computa- tional cost of graph construction and the necessity for low- latency responsiv eness to user demands, CODE operates via a hierarchical control plane composed of two nested loops (see Alg. 2): the Outer Loop and the Inner Loop . This architectural separation ensures that computationally intensiv e tasks whose results can be stored and reused further, as long as the network state does not v ary too much, are decoupled from real-time time-sensitiv e decisions. 1) The Outer Loop: The Outer Loop operates on a coarse time scale (ranging from seconds to minutes) and serves as the network’ s topological manager . Its primary objectiv e is to monitor global network conditions—such as physical link av ailability , background noise lev els, and long-term traffic patterns—and update the routing tables accordingly . In this phase, the control plane ex ecutes the computationally heavy pre-processing steps: 1) Path Enumeration: It deploys a modified Dijkstra algo- rithm to e xtract a candidate set of the N -shortest paths, P ′ s,d ⊆ P s,d , for all active source-destination pairs ( s, d ) . 2) Protocol Optimization: It ex ecutes the DP-based hy- pergraph generation algorithm (Sec. VI-B, Algorithm 1) across all candidate path P ∈ P ′ s,d to identify the Pareto- optimal Entanglement Generation Protocols and ev aluate the corresponding Ensemble Capacities of each protocol. 3) T opological Pruning: It filters the candidate set by retaining only the top- K paths ( P K ⊆ P ′ s,d ). In particular , we select the K paths with the highest Ensemble Ca- pacity of their best performing Entanglement Generation Protocols, discarding the N − K underperforming paths. 4) Hypergraph Synthesis: It aggregates the DP-optimized operational sequences derived from the selected P K paths to construct and cache the global, multi-path pruned hypergraph, L ′ P K . 2) The Inner Loop: The Inner Loop operates on a fine time scale ( 10 ms to 1 s) and handles near -instantaneous user requests and rapid fluctuations in demand. Unlike the outer loop, which addresses structural optimization, the inner loop focuses purely on flow maximization. When a transmission request arrives, the Inner Loop retriev es the pre-computed pruned hypergraph L ′ P K and solves the LP to determine the optimal Entanglement Distribution Scheme. Algorithm 2 CODE: C apacity O ptimization for D istributed E ntanglement Input: Network topology G , noise sources (Sec. VII), traffic patterns, N (paths), K (top paths), T outer (Update period) Output: Optimal Entanglement Distrib ution Scheme 1: while Network is acti ve do ▷ Outer Loop 2: Monitor physical link availability 3: for each active source-destination pair ( s, d ) do 4: P N ← runModifiedDijkstra ( G, s, d, N ) 5: for each path p ∈ P N do 6: { C i } N i =1 ← EC estimation via DP (Sec. VI-B) 7: end for 8: P K ← selectT opKPaths ( P N , { C i } N i =1 , K ) 9: L ′ P K ← generatePrunedHypergraph ( P K ) 10: end for 11: Store L ′ P K for real-time access 12: while t current < T outer do ▷ Inner Loop 13: if Transmission request arrives then 14: Retriev e stored hypergraph L ′ P K 15: S P K ← runLP ( L ′ P K ) 16: Execute S P K 17: end if 18: end while 19: end while This hierarchical approach offers a distinct computational advantage. By relegating the O ( | V | 3 |F | 2 ) complexity of the DP-based pruning to the background Outer Loop, the critical path of the request processing is limited to solving the LP ov er a significantly reduced variable set. This ensures that the network can optimize entanglement distribution in near-R T without being bottlenecked by the combinatorial explosion of the full protocol space. V I I . E V A L UATI O N F R A M E W O R K This section details the building blocks of our ev aluation framew ork. This en vironment provides a unified reference to characterize how entanglement is generated and distributed across Quantum Networks. Developed in Python via the Net- Squid [48] library , the platform allows for the high-fidelity representation of scalable quantum networks. Unlik e simpli- fied models, our approach explicitly accounts for entanglement generation, swapping, and purification under realistic noise and hardware constraints. A. Quantum Network W e model each node of the quantum network as a quantum repeater equipped with a Spontaneous Parametric Down Con- version (SPDC) source capable of generating entangled polar- ized photons encoding qubits. Quantum nodes can store qubits in quantum memories and perform computing operations via quantum gates and measurements on them, enabling Bell-State Measurements for quantum teleportation. Adjacent quantum nodes are connected via fiber-optic channels that enable the exchange of entangled photon pairs to establish entanglement through shared entangled pairs, enabling quantum teleportation 10 Mid - p o i n t Stat i o n Beam Sp l i t t er Si n g l e Ph o t o n D et ect o rs (Sec. V I - B ) PM D / D ep o l ari zat i o n (Sec. V I - C3 ) Q u an t u m N o d e C Q u an t u m N o d e A Q u an t u m m em o ri es Mem o ry d eco h eren ce (Sec. V I - C3 ) Recei v ed i n fo rm at i o n b i t s SPD C s o u rce E n t an g l em en t g en erat i o n (Sec. V I - B & V I - C1 ) H i g h fi d el i t y E Ps E x t en d ed D E J MPS (Sec. V I - D2 ) BSM E n t an g l em en t s w ap p i n g Q u an t u m N o d e B SPDC s o u rce Mu l t i - h o p l i n k D i rect l i n k (Sec. V I - D1 ) Q u an t u m N o d e D E n t an g l em en t s w ap p i n g E n t an g l em en t p u ri fi catio n O p erat i o n N o i s e (Sec. V I - C2 ) G at es / Measu rem en t s E n t an g l em en t s w ap p i n g Fig. 3: Schematic representation of the Quantum Network system model used in the performance e valuation. of arbitrary states (Fig. 3 Dir ect link ). Non-adjacent nodes can become entangled via sequential swapping operations across intermediate nodes, extending communication o ver long dis- tances (Fig. 3 Multi-hop link ). All these operations are subject to imperfections and noise. T o mitigate any source of fidelity degradation, quantum nodes can also perform entanglement purification operations. Fig. 3 shows the different building blocks of our QN and the noise ef fects we have considered. 1) Or chestration and Control F rame work: A classical net- work ov erlaid on the QN interf aces with the quantum nodes using a centralized network controller . This controller enables the synchronization and coordination of quantum protocols. It is divided into two main control loops: ( i ) a Non-Real- T ime (non-R T) control loop that manages entangled resources and high-level policies (e.g. signaling link failures) with ex- ecution latencies exceeding 1s, and ( ii ) a Near-Real-T ime (near-R T) control loop which periodically reconfigures the quantum network and synchronizes the execution of differ - ent Entanglement Generation Protocols with response times ranging from 10ms to 1s. The controller ensures that the maximum processing time of all Entanglement Generation Protocols T π p is lower than the accumulation time window T w . Furthermore, it ensures that T π p + T w does not exceed the quantum memories’ coherence time (see Sec. VII-C3). B. Entanglement generation T o model entanglement generation, we adopt the mid- point link-lev el procedure presented in [49] and depicted in Fig. 3 under the direct link representation. Adjacent nodes store one photon from an SPDC-emitted pair and transmit the other to a mid-station. Successful entanglement is heralded by coincident detections after photons interfere at the mid- station’ s polarizing beam splitter . At each quantum node, we model the ef fectiv e local EGR at zero distance as r local . This parameter accounts local hardware efficiencies including the probabilities of single-photon emis- sion, memory-photon coupling and detector efficienc y [50]– [52]. Consequently , the effecti ve entanglement generation rate between adjacent nodes separated by a distance L is deter- mined by the fiber transmission loss as r link ( L ) = r local · e − αL/ 10 , (8) where α represents the optical fiber attenuation coefficient. W e used an attenuation coef ficient α = 0 . 21 dB/Km [48]. C. Entanglement Fidelity in Noisy En vir onments The quality of a shared entangled pair can be quantified using its fidelity , which measures ho w close the actual state is to a target Bell state (see Sec. III). Several noise sources contribute to the degradation of entanglement fidelity . 1) Initial F idelity of Generated Entangled P airs: The initial fidelity of a two-photon state, measured immediately after generation with respect to an ideal Bell state and denoted as F 0 , is typically observed to be slightly below unity due to imperfections in the generation process. Experimental results indicate that F 0 ' 0 . 98 is a conserv ative estimate for high- quality SPDC implementations [53], [54]. 2) Imperfect Local Operations and Measur ements: Local operations such as quantum gates and measurements inevitably introduce inaccuracies and noise degrading entanglement fi- delity and limiting communication performance. Also, these imperfections directly af fect entanglement swapping and pu- rification operations. W e model these imperfections adopting the approach introduced in [6]: • Quantum gate model : W e model a single-qubit gate noise using a parameter p 1 ∈ [0 , 1] , representing the lower bound on the probability of ideal operation. W ith probability 1 − p 1 , the noisy gate replaces the qubit with a maximally mixed state. Thus, the action of a noisy gate on a multi-qubit state ρ is described as: ρ 7→ p 1 O ideal 1 ρ | {z } Ideal operation + 1 − p 1 2 T r 1 { ρ } ⊗ I 1 | {z } Depolarizing noise , (9) where O ideal 1 is the single-qubit ideal quantum gate and I 1 is the maximally mixed state on the affected qubit. T wo-qubit gates are modeled analogously with reliability parameter p 2 , and the depolarized component is replaced by a maximally mix ed state on the inv olved qubits. • Measurement model : W e model imperfect quantum state measurements using Positiv e Operator -V alued Measures (PO VMs) [55] with an accuracy parameter η ∈ [0 , 1] , representing the probability of correctly identifying the 11 qubit state. For a single-qubit measurement in the compu- tational basis {| 0 i , | 1 i} , the noisy measurement operators are defined as: P η 0 = η | 0 ih 0 | | {z } Correct identification + (1 − η ) | 1 ih 1 | | {z } Misidentification , (10) P η 1 = η | 1 ih 1 | | {z } Correct identification + (1 − η ) | 0 ih 0 | | {z } Misidentification . (11) In quantum teleportation, Bell-State Measurements (BSMs) project two qubits onto one of the four Bell states. W e model BSMs using an imperfect two-qubit CNO T gate followed by a Hadamard operation and two noisy single-qubit mea- surements as defined above. Experimental works on quantum gates and measurement fidelities in superconducting and spin- based quantum hardware [52], [56]–[58] report reliability and accuracy parameters of η = p 1 = p 2 = 0 . 995 . 3) Decoher ence in Quantum Memories: En vironmental noise degrades the fidelity of stored quantum states in quantum memories via two processes [59]: ( i ) thermal decoherence (i.e. amplitude damping), characterized by the relaxation time T 1 , and ( ii ) dephasing, characterized by the coherence time T 2 . Quantum states are assumed to remain coherent and unaffected by noise up to a fix ed maximum storage time t cut , beyond which they are considered fully decohered [10], [12], [22]. This approximation is well-justified by the significant gap between the experimentally measured coherence durations [60], [61] ( T 1 = 3600 s, T 2 = 1 . 46 s) and typical quantum protocol execution times on the order of ∼ 10 − 2 seconds [6]. 4) Depolarization in Optical F iber: A polarization-encoded photon propagating through an imperfect optical fiber ex- periences a relativ e time delay denoted by τ PMD between orthogonal polarization states. This phenomenon is referred as Polarization Mode Dispersion (PMD) [50] and is the primary source of fidelity degradation. When τ PMD exceeds the photon’ s coherence time τ coh , polarization coherence is lost. W e model τ PMD as a normally distributed random variable [43], [50], τ PMD ∼ N ( D GD · √ L, D GD · √ L ) where the D GD is the differential-group delay in ps / √ Km and L is its length of the fiber in Km. Experimental works [50] estimate the D GD of a single-mode fiber to be around 0 . 1 ps / √ Km and a coherence time τ coh of 1 . 6 ps. D. Long-Distance Entanglement Distrib ution 1) Entanglement Swapping: Realistic swapping operations yield an entangled state of reduced fidelity due to imperfec- tions and noise. After N − 1 consecuti ve swapping operations across a N hops, the resulting fidelity F ′ of an EP is giv en by F ′ = 1 4 " 1 + 3 p 2 1 p 2 · 4 η 2 − 1 3 N − 1 N Y i =1 4 F i − 1 3 # , (12) where p 1 , p 2 , and η denote the reliabilities of the local oper - ations and measurements and F i denotes the fidelity after the i -th swapping operation [38]. (W e assume p 1 , p 2 and η equal for all network nodes in eq. (12)). This expression highlights A s y m m et ri cal D E J MPS D E J MPS Pro t o co l D E J MPS Ro u n d 1 In t erm ed i at e fi d el i t y In t erm ed i at e fi d el i t y D E J MPS Ro u n d 1 D E J MP S Rou n d 2 Fi n al fi d el i t y La rg e m em o ry r equi r em ent In i t i al Pai r Fresh Pair Pu m p i n g Ro u n d 1 In t erm ed i at e fi d el i t y Pu m p i n g Ro u n d 2 Fi n al fi d el i t y Sm a l l m em o ry r equi r em ent E n t an g l em en t p u ri fi cat i o n : Res o u rce Scal i n g Fres h Pai r Fig. 4: DEJMPS and Asymmetrical DEJMPS protocols. that unless each operation and link is performed with near- perfect accuracy , the final fidelity F ′ decays exponentially with the number of swaps, asymptotically approaching 1 / 4 . This emphasizes the need of purification operations at intermediate nodes to enable long-distance entanglement distrib ution. 2) Entanglement Purification: Entanglement purification is performed iteratively in discrete rounds, in which multiple low-fidelity pairs are combined to produce a smaller number of higher-fidelity pairs. Purification employs local quantum gates and measurements to decide whether the resulting pair is kept making the protocol inherently probabilistic. Fidelity gains diminish over successi ve rounds, asymptotically approaching a maximum attainable value F max ( p 1 , p 2 , η ) < 1 . In this work, we utilize the DEJMPS protocol [62], and extend it, via relaxing the identical-fidelity requirement, to an asymmetrical variant that allows for lower resource consumption. DEJMPS Protocol : The DEJMPS purification protocol [62] operates on pairs of shared entangled particles with identical fidelities between two nodes (i.e. a transmitter and a receiver). Both apply to the pair local unitary rotations, followed by CNO T operations and a local measurement of one shared qubit in the computational Z basis. Both nodes retain the remaining pair only if both parties obtain identical measure- ment outcomes. The protocol is fidelity-optimal for two copies of Bell diagonal states of rank up to three, achie ving the maximum possible output fidelity and success probability [63]. The protocol succeeds with probability (assuming p 1 , p 2 , and η equal for both nodes) p succ = 1 18 9 + (4 F 1 − 1)(4 F 2 − 1)(1 − 2 η ) 2 p 2 2 , (13) where F 1 and F 2 are the fidelities of the input pairs. The fidelity of the retained pair after successful purification is F ′ = 9 + p 2 2 (1 − 8 F 2 ) − 8 F 1 (6 η 2 + 6 η − 1) 72 · p succ + 16 p 2 2 F 1 F 2 (12 η 2 − 12 η + 5) 72 · p succ (14) DEJMPS’ s identical input fidelity constraint causes the ex- pected number of consumed pairs to grow exponentially , scaling as (2 /p succ ) k max for k max rounds. This exponential resource scaling (see Fig. 4) poses a limitation in scenarios with constrained qubit memory . 12 T ABLE I: Solution characterization across varying paths with capacity improvement relative to Rate-DP . Perf ormance Metrics Operational Metrics Capacity # Strategy EGR Fidelity Capacity Swaps Purif. Pairs Improv . 3 Rate-DP 2918.27 0.9266 1610.62 1.00 0.57 1.00 — Rate-LP 2920.20 0.9243 1584.53 1.20 1.70 1.20 -1.62% EC-LP 2920.20 0.9266 1614.89 1.78 1.24 1.78 +0.27% CODE 2920.20 0.9343 1738.62 1.80 1.41 1.80 +7.95% 5 Rate-DP 1902.40 0.8863 644.38 3.00 4.11 1.00 — Rate-LP 1971.85 0.8784 602.96 6.78 7.31 1.24 -6.43% EC-LP 2078.68 0.8800 666.59 9.46 6.16 3.19 +3.45% CODE 2163.37 0.8921 825.50 8.71 5.38 3.20 +28.11% 7 Rate-DP 704.13 0.8760 191.34 5.00 12.05 1.00 — Rate-LP 778.71 0.8701 185.70 19.41 21.78 1.01 -2.95% EC-LP 845.64 0.8678 194.29 18.99 19.05 3.36 +1.55% CODE 1117.58 0.8723 290.13 17.01 14.84 3.82 +51.63% 10 Rate-DP 276.11 0.8739 70.09 8.00 23.69 1.00 — Rate-LP 306.96 0.8700 72.60 39.67 51.99 1.00 +3.58% EC-LP 308.08 0.8709 73.21 38.11 48.74 3.50 +4.44% CODE 522.35 0.8721 127.15 28.99 35.36 3.90 +81.39% Asymmetrical DEJMPS : The asymmetrical v ariant is an adaptation of entanglement pumping [6] that relaxes the identical-fidelity requirement. It utilizes the same sequence of operations as the symmetrical case—and thus follows the same physical models for p succ and F ′ —but allows for F 1 6 = F 2 . T ypically , a high-fidelity "protected" pair is iterativ ely purified by consuming a fresh, lo wer-fidelity "source" pair . While the single-step performance is upper-bounded by the symmetrical case, the asymmetrical approach allo ws for linear scaling of memory resources relative to the number of rounds. V I I I . P E R F O R M A N C E E V A L UAT I O N This section evaluates CODE against state-of-the-art so- lutions (Sec. VIII-A, VIII-B). The analysis covers Ensem- ble Capacity performance (Sec. VIII-B1), operational opti- mization (Sec. VIII-B2), and scalability (Sec. VIII-B3). It assesses benchmark solution sensitivity to the minimum fi- delity lo wer bound (Sec. VIII-C), comparing optimal se- lections against CODE. Finally , it quantifies computational scalability (Sec. VIII-D), comparing CODE’ s execution times against benchmarks across v arying fidelity discretization (Sec. VIII-D1) set sizes, path lengths (Sec. VIII-D2), and network sizes (Sec. VIII-D3). Our solution and benchmarks results use the e v aluation framework described in Sec. VII. W e implemented CODE using Python, the ev aluation framework using NetSquid, and we used Gurobi as the main solver for any Linear Programming (LP) formulation. A. Solution Benchmarks State-of-the-art solutions to the Entanglement Distribution Problem do not optimize the Ensemble Capacity , rather they maximize the Entanglement Generation Rate (EGR) subject to minimum fidelity constraints. Thus, to f airly compare CODE against state-of-the-art solutions, we adapt them using a fixed fidelity lo wer-bound f LB and compute the resulting capacity using the end-to-end EGR. Selecting the optimal f ∗ LB is non-trivial due to the complex, non-linear trade-of fs between fidelity and generation rates (see Sec. VIII-B). W e compare CODE against the following three strategies: • Rate-DP : This solution is based on the Dynamic Pro- gramming (DP) formulation presented in [14]. It maxi- (a) Ensemble Capacity (b) Relativ e EC Gains Fig. 5: Comparison of the Ensemble Capacity and Relative Ensemble Capacity Gains as a function of the path length. mizes the EGR subject to a minimum fidelity constraint, restricted to entanglement pumping for purification. • Rate-LP : This solution is based on the Linear Program- ming (LP) formulation presented in [14]. It computes the hypergraph using the standard frame work presented in Sec. VI-A and maximizes the EGR subject to a minimum fidelity constraint. • EC-LP : This solution maximizes the Ensemble Capacity via the LP formulation presented in Sec. VI-C building a hypergraph using the standard framew ork presented in Sec. VI-A. This solution acts as an ablation study on the efficac y of DP-based hyper graph generation. In order to get meaningful operational insights, we ev al- uate CODE and the benchmark solutions ov er realistic net- work topologies from T opoHub [64]. This repository provides Gabriel graph models [65], characterizing the proximity-based connectivity inherent in fiber -optic deployments, alongside empirical topologies from The Internet T opology Zoo [66]. B. P erformance Benchmarking W e ev aluate CODE and the benchmark solutions using a 1000-node Gabriel graph from the T opoHub repository [64]. For each network link, distances are uniformly sampled from the range [20, 150] km. The local EGR at zero distance ( r local ) is set to 12k entangled pairs per second (EPs/s) [50] for all nodes. For the Rate-DP and Rate-LP solutions, we fix the fidelity lower bound at f LB = 0 . 87 (more details in Sec. VIII-C). T o ensure a fair comparison, all solutions were ev aluated over a discrete set of fidelity values of size |F | = 100 . W e e valuate the solutions of dif ferent approaches across 100 randomly selected node pairs for each path length (including both end nodes) of 3, 5, 7, and 10 nodes (corre- sponding to 2, 4, 6, and 9 hops, respectively). T able I summarizes the av eraged performance and opera- tional metrics. Performance metrics include the mean end- to-end EGR, mean fidelity , and a verage Ensemble Capacity . Operational metrics encompass the av erage number of entan- glement swaps and purification rounds required by the distri- bution scheme, alongside the mean number of distinguishable EPs produced. The final column reports the relative capacity improv ement compared to the Rate-DP benchmark. 1) Ensemble Capacity Optimization: The results presented in T able I sho w that CODE achie ves better Ensemble Capacity optimization across all path lengths. While it provides a 13 modest 7 . 95% improv ement in 3-hops paths, its improvement scales dramatically to a 81 . 39% capacity increase in 10-hop paths. Also, CODE achiev es the highest end-to-end EGR and top-2 fidelity across all path lengths. Since CODE utilizes the discretization set F as interv al boundaries, it accesses a richer search space of Entanglement Distribution Schemes, identi- fying high-potential solutions that standard methods would otherwise prematurely prune. On the other hand, EC-LP consistently deli vers higher EGR than both Rate-DP and Rate-LP as it aggressively uses residual resources to maximize the Ensemble Capacity . Con versely , despite optimizing a superset space of Rate-DP [14], Rate-LP unexpectedly underperforms Rate-DP in capacity for medium- to-short chains. In these scenarios, Rate-LP suffers from a “high-rate, lo w-fidelity” trade-off; the solver selects high EGR solutions that are undermined by poor end-to-end fidelity . 2) Operational Optimization: Operationally , CODE gener- ates a highly heterogeneous ensemble of end-to-end entangled pairs (EPs). By optimizing residual resources, it maximizes EPs yield while maintaining the number of swap and purifi- cation operations comparable to benchmark solutions. While EC-LP also produces high-utility heterogeneous ensembles, it achiev es lo wer total capacity than CODE. Con versely , as Rate- DP is constrained by a single distribution protocol, it limits purification opportunities and ties swap counts to path length. Rate-LP is operationally inefficient, performing additional swapping and purification operations that fail to increase the ensemble size significantly be yond Rate-DP levels. 3) Scaling with P ath Length: T o ev aluate solution scala- bility , we analyze performance as path length increases. W e now use the real link distances of the 1000-node Gabriel graph. Link distances range from 25 to 400 km with a mean 100 km. As pre viously established, we randomly select node pairs spanned by defined path lengths. Figure 5a presents the 95% confidence interval for Ensemble Capacity computed across 20 distinct paths per length size as a function of node count. T o isolate algorithmic ef ficiency from path-dependent variables (e.g., total length, Entanglement Generation Rate, and intermediate link fidelity), Figure 5b displays the Relative EC Performance. This secondary analysis normalizes each method against the EC-LP benchmark on a per-path basis. EC- LP serves as the 100% baseline due to its consistently superior performance among state-of-the-art methods. For Rate-LP solution we cannot use paths with more than length 10 as we exhaust our av ailable memory to run the solution. W e observe that the absolute Ensemble Capacity of all four solutions decreases as the path length grows. This behavior aligns with physical e xpectations: longer paths require more entanglement swapping and purification operations ine vitably leading to accumulated fidelity degradation and lo wer effecti ve EGR across the end-to-end connection. CODE consistently outperforms the other methods across all path lengths, yielding the highest overall capacity and exhibiting the most resilience to network scaling. While it shows a modest improv ement ov er the EC-LP at a 2-node configuration, its relati ve advantage scales steadily , achie ving ov er a 300% performance gain at 20 nodes path length. (a) Normalized EC f * L B (b) f ∗ LB Distribution Fig. 6: Impact of the f LB on network performance. C. F idelity Lower -Bound Sensitivity W e no w e valuate the sensiti vity of benchmark’ s results to fidelity lower bound constraint. Even though CODE does not depend on the fidelity lower bound constraint as it optimizes directly the Ensemble Capacity , it is helpful to study ho w sensitiv e state-of-the-art solutions are to this constraint as its value largely affect the quality of solutions. T o study this de- pendence, we resort to the Gabriel graph used in Sec VIII-B1, and run the CODE and the benchmark solutions for f LB values between 0.815 and 0.995 in 0.005 increments. W e analyze the results for 100 randomly selected pairs of nodes connected between a path with lengths between 2 to 10 hops. Fig. 6a plots the normalized Ensemble Capacity metric as a function of the centered fidelity lower-bound, f c LB = f LB − f ∗ LB where f ∗ LB = 0 . 87 maximizes the Ensemble Capacity for Rate- DP and Rate-LP . Centering the fidelity decouples intrinsic protocol performance from the path-dependent optimal oper - ating points of the benchmarks. Per-path normalization of the Ensemble Capacity (EC) values isolates topological variability , allowing for a fair cross-scenario comparison. Also, CODE’ s capacity defines the EC normalization baseline. As we observe in Fig. 6a, CODE directly optimizes the Ensemble Capacity without a fixed fidelity constraint, its performance is strictly in variant to f LB . EC-LP solution is the closest benchmark to CODE, achie ving approximately 65% of CODE’ s capacity while also remaining inv ariant to f LB . This performance gap highlights the limitations inherent in the standard hypergraph models utilized by EC-LP . By av oiding the rigid fidelity discretization characteristic of prior art, CODE accesses a richer search space of Entanglement Distribution Schemes, exploiting high-potential solutions that standard discretization methods prematurely prune. Con versely , the Rate-DP and Rate-LP approaches exhibit a distinct Gaussian-like sensiti vity to f LB . Their performance depends hea vily on the precise optimization of f LB , a non- trivial task dependant on multiple path-specific factors, includ- ing link count, link-level fidelities, and EGRs. Consequently , no single fidelity lower-bound is universally optimal across div erse network configurations. Figure 6b presents the distri- bution of optimal values ( f ∗ LB ) for the Rate-DP and Rate-LP solutions across multiple Gabriel topologies and path lengths. Although the f ∗ LB values are distributed within the interval (0 . 8 , 1 . 0) , benchmark performance e xhibits strong sensitivity to the exact selection of f LB . A marginal de viation of 0.02 from f ∗ LB yields up to a 20% de gradation in EC. 14 Fig. 7: Ensemble Capacity as a function of the Fidelity Resolution. (a) Solver Time (b) Server Time Fig. 8: Running time analysis as a function of the Fidelity Resolution. D. Computational Scalability Analysis Finally , we ev aluate the computational scalability of CODE against the stat-of-the-art solutions. W e analyze the execution time as a function of the fidelity resolution—defined as the dis- cretization set cardinality , |F | — and the total number of nodes in the path and network. Quantifying these computational trade-offs delineates the operational limits of the benchmark formulations and validates CODE’ s applicability for large- scale quantum network deployments. 1) F idelity Discr etization: T o begin with, we e valuate the sensitivity of the execution time of the different solutions to the fidelity resolution. As e xplained in Sec. VI |F | sets the size and precision of the state space during the hypergraph construction. A higher resolution allo ws for a more accurate tracking of entanglement states, which enables the discovery of higher -yield routing solutions. Howe ver , this comes at the cost of a larger state space, increasing the computational burden (see Sec. VI-D). W e ev aluate the impact of Fidelity resolution using a 1000-node Gabriel graph from T opoHub repository [64]. W e no w fix the path length to 6 nodes and study the effect of the fidelity resolution in the output EC. Figure 7 depicts the Ensemble Capacity as a function of Fidelity Resolution. As expected, all solutions exhibit an increase in capacity as the resolution becomes higher . The state-of-the-art benchmarks start with near-zero capacity at low resolution and require highly refined state spaces to identify viable entanglement distribution schemes. In contrast, CODE demonstrates remarkable algorithmic efficiency at low resolutions. It achiev es near-peak capacity at a resolution of just 10 2 , while the competing methods must scale toward 10 3 to reach comparable, albeit still inferior , performance levels. Fig. 7a presents the Solver Time which is time required for the LP solver to find the optimal solution while fig. 7b presents the Server T ime which is time required to construct the state space and optimization model. Both plots display the 1st, 50th, and 99th percentiles. Rate-DP is exclusi vely plotted in the Server Time figure as it lacks a distinct Solv er phase. Solver and Server T imes scale with increasing fidelity reso- lution, aligning with the theoretical predictions in Sec. VI-D. High-resolution operation ( |F | = 10 3 ) yields ex ecution times sev eral orders of magnitude longer than lo wer settings. This creates a se vere scalability bottleneck for the benchmark methods, which require high-resolution to achiev e meaningful Ensemble Capacity solutions. At these scales, benchmark Solver Times exceed quantum memory coherence times, ren- dering them unfeasible for responsi ve network management. Con versely , CODE bypasses this limitation by extracting near- optimal solutions at a coarser resolution ( |F | = 10 2 ). At this resolution, CODE’ s Solver Time remains near 10 − 2 s, keeping Server Time sufficiently low to enable rapid network updates. 2) P ath Length: Next, we evaluate how execution times change as a function of the number of nodes in a path. Using the previous section results, we fix |F | = 100 across all solutions and run them for paths lengths from 2 to 20 nodes using the same graph. Figure 9 presents the 99th, 50th, and 1st percentiles of both Server and Solver Time. As noted previously , Rate-DP appears only in the Serv er Time plot. From fig. 9b, we see that Rate-DP exhibits the fastest Server T ime among the four solutions. Howe ver , as previ- ously explained, this lower computational overhead comes at the expense of a significant performance de gradation (see Sec. VIII-A). Rate-LP exhibits the worst server time scal- ability; its computational cost compounds so aggressi vely that it mimics exponential scaling before becoming entirely unfeasible for path lengths higher than 11 nodes. CODE shows better Server Times than Rate-LP and EC-LP solutions. It demonstrates lo wer Server T imes than both, processing 20-node paths in approximately 10 2 seconds in the worst- case scenario. Since CODE meticulously constructs a pruned hypergraph via DP , its Server T ime absorbs an initial overhead that the standard LP approaches do not. The true impact of CODE’ s DP hypergraph generation can be clearly visualized in fig. 9a. CODE’ s solver time scales exceptionally well, remaining safely bounded between 10 − 3 and 10 − 1 seconds. Even at the maximum path length, it operates an order of magnitude belo w the quantum memory decoherence time and its inner loop latency limit of 1s. As both Rate-LP and EC-LP use an unpruned hypergraph, the y scale worse than CODE. Their Solver T ime increases rapidly , breaching the 1s operational latency limit at a path length of 5 nodes for Rate-LP and 8 nodes for EC-LP . 3) Network Size: Finally , we examine CODE’ s perfor- mance across networks of different network sizes. W e con- ducted e xtensiv e experiments using network topologies rang- ing from 100 to 900 nodes. For each topology , we e valuated 700 randomly selected source-destination pairs, selecting the top 3 shortest paths between them. Fig. 10 depicts the Server and Solver Times as scatter plots to illustrate the distribution of execution times with a marker in the median performance. CODE’ s Server T ime ranges from approximately 10 0 sec- 15 (a) Solver Time (b) Server Time Fig. 9: Running time vs. number of physical links. (a) Solver Time (b) Server Time Fig. 10: Running time vs. number of nodes in the QN. onds to 10 2 seconds. Because the Outer Loop is responsible for longer-term, structural network decisions, it is designed to operate on a timescale greater than 1 second. Even at the maximum ev aluated network size of 900 nodes, the median Serv er T ime remains computationally reasonable for background processing (peaking around < 10 2 seconds). This demonstrates that while the state space naturally gro ws with the underlying infrastructure, CODE’ s dynamic programming- based generation efficiently manages this expansion. The operational viability of CODE is v alidated by its exceptional Solver T ime performance in fig. 10a. Despite the network scaling up to 900 nodes, the LP execution time remains bounded below 0.10 seconds. In fact, the vast majority of instances, including the medians, cluster hea vily between 10 − 3 and 8 · 10 − 2 seconds. This remarkable stability highlights the core architectural advantage of CODE: by absorbing the complexity of state space e xploration into the non-R T Outer Loop, the Inner Loop is shielded from the combinatorial explosion typically associated with lar ge network topologies. I X . C O N C L U S I O N S In this work, we addressed the multifaceted challenges of the entanglement distrib ution problem by introducing four piv otal advances for the practical deployment of Quantum Net- works (QNs). First, we deriv ed the Ensemble Capacity metric to shift the optimization objectiv e toward maximizing the secure transmission of classical priv ate information. Second, we presented a generalized mathematical formulation that lifts legac y structural restrictions, enabling the arbitrary sequencing of entanglement swapping and purification. Third, we pro- posed a Dynamic Programming (DP)-based algorithm that circumvents artificial fidelity quantization, preserving exact continuous quantum states while efficiently pruning the com- binatorial space. Finally , we encapsulated these innov ations into CODE , a two-tiered orchestration framew ork enabling near-real-time network adaptivity . Evaluated under realistic physical hardware models, our methodology achiev es superior priv ate classical information capacity and drastically reduced computational overhead. By strictly satisfying dynamic latency constraints, this approach marks a substantial step toward the practical implementation of QNs. R E F E R E N C E S [1] M. Trav agnin, A. Lewis et al. , “Quantum key distribution in-field implementations, ” Publications Office of the Eur opean Union , 2019. [2] M. Hillery , V . Bužek, and A. Berthiaume, “Quantum secret sharing, ” Physical Revie w A , vol. 59, no. 3, p. 1829, 1999. [3] Z. Qi, Y . Li, Y . Huang, J. Feng, Y . Zheng, and X. Chen, “ A 15- user quantum secure direct communication network, ” Light: Science & Applications , vol. 10, no. 1, p. 183, 2021. [4] S. Pirandola, R. Laurenza, C. Ottaviani, and L. Banchi, “Fundamental limits of repeaterless quantum communications, ” Natur e communica- tions , vol. 8, no. 1, p. 15043, 2017. [5] M. Caleffi, A. S. Cacciapuoti, and G. Bianchi, “Quantum internet: From communication to distributed computing!” in Proceedings of the 5th A CM international confer ence on nanoscale computing and communication , 2018, pp. 1–4. [6] W . Dür, H.-J. Briegel, J. I. Cirac, and P . Zoller , “Quantum repeaters based on entanglement purification, ” Physical Review A , vol. 59, no. 1, p. 169, 1999. [7] W . J. Munro, K. Azuma, K. T amaki, and K. Nemoto, “Inside quantum repeaters, ” IEEE Journal of Selected topics in quantum electr onics , vol. 21, no. 3, pp. 78–90, 2015. [8] J.-W . Pan, D. Bouwmeester , H. W einfurter, and A. Zeilinger , “Exper- imental entanglement swapping: entangling photons that ne ver inter- acted, ” Physical r eview letters , vol. 80, no. 18, p. 3891, 1998. [9] J.-W . Pan, C. Simon, ˇ C. Brukner , and A. Zeilinger, “Entanglement purification for quantum communication, ” Natur e , vol. 410, no. 6832, pp. 1067–1070, 2001. [10] M. V ictora, S. Tserkis, S. Krastanov , A. S. de la Cerda, S. Willis, and P . Narang, “Entanglement purification on quantum networks, ” Physical Review Researc h , vol. 5, no. 3, p. 033171, 2023. [11] H. Gu, R. Y u, Z. Li, X. W ang, and F . Zhou, “Esdi: Entanglement scheduling and distribution in the quantum internet, ” in 2023 32nd International Conference on Computer Communications and Networks (ICCCN) . IEEE, 2023, pp. 1–10. [12] H. Gu, Z. Li, R. Y u, X. W ang, F . Zhou, J. Liu, and G. Xue, “Fendi: T ow ard high-fidelity entanglement distribution in the quantum internet, ” IEEE/ACM T ransactions on Networking , vol. 32, no. 6, pp. 5033–5048, 2024. [13] I. Devetak, “The private classical capacity and quantum capacity of a quantum channel, ” IEEE T ransactions on Information Theory , vol. 51, no. 1, pp. 44–55, 2005. [14] X. Fan, Y . Y ang, H. Gupta, and C. Ramakrishnan, “Distrib ution and purification of entanglement states in quantum networks, ” in 2025 International Confer ence on Quantum Communications, Networking, and Computing (QCNC) . IEEE, 2025, pp. 74–82. [15] M. Caleffi, “Optimal routing for quantum networks, ” Ieee Access , vol. 5, pp. 22 299–22 312, 2017. [16] M. Pant, H. Krovi, D. T owsle y , L. T assiulas, L. Jiang, P . Basu, D. En- glund, and S. Guha, “Routing entanglement in the quantum internet, ” npj Quantum Information , vol. 5, no. 1, p. 25, 2019. [17] E. Grant, “On the stochastic analysis of a quantum entanglement distribution switch, ” Science China Physics, Mechanics & Astr onomy , vol. 66, no. 5, p. 250301, 2023. [18] H. Gu, Z. Li, X. W ang, D. Y ang, G. Xue, and R. Y u, “Cost-aw are high-fidelity entanglement distribution and purification in the quantum internet, ” IEEE T ransactions on Networking , 2025. [19] X. Sun, T . Hu, H. Chen, T . Zhu, and X. Jiang, “High-fidelity entangle- ment distribution method for quantum communication network, ” in 2024 43r d Chinese Control Conference (CCC) . IEEE, 2024, pp. 6771–6776. [20] C. Li, T . Li, Y .-X. Liu, and P . Cappellaro, “Effecti ve routing design for remote entanglement generation on quantum networks, ” npj Quantum Information , vol. 7, no. 1, p. 10, 2021. [21] Y . Zhao, G. Zhao, and C. Qiao, “E2e fidelity aware routing and purification for throughput maximization in quantum networks, ” in IEEE INFOCOM 2022-IEEE Conference on Computer Communications . IEEE, 2022, pp. 480–489. 16 [22] L. Chen and Z. Jia, “On optimum entanglement purification scheduling in quantum networks, ” IEEE Journal on Selected Areas in Communica- tions , vol. 42, no. 7, pp. 1779–1792, 2024. [23] K. Chakraborty , F . Rozpedek, A. Dahlberg, and S. W ehner , “Distributed routing in a quantum internet, ” arXiv pr eprint arXiv:1907.11630 , 2019. [24] K. Chakraborty , D. Elkouss, B. Rijsman, and S. W ehner , “Entanglement distribution in a quantum network: A multicommodity flow-based ap- proach, ” IEEE T ransactions on Quantum Engineering , vol. 1, pp. 1–21, 2020. [25] J. Li, M. W ang, K. Xue, R. Li, N. Y u, Q. Sun, and J. Lu, “Fidelity- guaranteed entanglement routing in quantum networks, ” IEEE T ransac- tions on Communications , vol. 70, no. 10, pp. 6748–6763, 2022. [26] S. Bratzik, S. Abruzzo, H. Kampermann, and D. Bruß, “Quantum repeaters and quantum key distrib ution: The impact of entanglement distillation on the secret key rate, ” Physical Review AAtomic, Molecular , and Optical Physics , vol. 87, no. 6, p. 062335, 2013. [27] S. Pirandola, “End-to-end capacities of a quantum communication network, ” Communications Physics , vol. 2, no. 1, p. 51, 2019. [28] A. Einstein, B. Podolsky , and N. Rosen, “Can quantum-mechanical description of physical reality be considered complete?” Physical re view , vol. 47, no. 10, p. 777, 1935. [29] D. Huber, M. Reindl, Y . Huo, H. Huang, J. S. Wildmann, O. G. Schmidt, A. Rastelli, and R. Trotta, “Highly indistinguishable and strongly entangled photons from symmetric gaas quantum dots, ” Nature communications , vol. 8, no. 1, p. 15506, 2017. [30] I. Aharonovich, D. Englund, and M. T oth, “Solid-state single-photon emitters, ” Natur e photonics , vol. 10, no. 10, pp. 631–641, 2016. [31] L.-M. Duan, M. D. Lukin, J. I. Cirac, and P . Zoller , “Long-distance quantum communication with atomic ensembles and linear optics, ” Natur e , vol. 414, no. 6862, pp. 413–418, 2001. [32] B. J. Smith, P . Mahou, O. Cohen, J. Lundeen, and I. W almsley , “Photon pair generation in birefringent optical fibers, ” Optics expr ess , vol. 17, no. 26, pp. 23 589–23 602, 2009. [33] C. H. Bennett, G. Brassard, C. Crépeau, R. Jozsa, A. Peres, and W . K. W ootters, “T eleporting an unknown quantum state via dual classical and einstein-podolsky-rosen channels, ” Physical r eview letters , vol. 70, no. 13, p. 1895, 1993. [34] C. H. Bennett, D. P . DiV incenzo, J. A. Smolin, and W . K. W ootters, “Mixed-state entanglement and quantum error correction, ” Physical Review A , vol. 54, no. 5, p. 3824, 1996. [35] W . Dür and H. J. Briegel, “Entanglement purification and quantum error correction, ” Reports on Pr ogr ess in Physics , vol. 70, no. 8, pp. 1381– 1424, 2007. [36] Q. Zhang, N. Di Cicco, M. Ibrahimi, R. C. Almeida, A. Gatto, R. Boutaba, and M. T ornatore, “Link configuration for fidelity- constrained entanglement routing in quantum networks, ” in IEEE IN- FOCOM 2025-IEEE Conference on Computer Communications . IEEE, 2025, pp. 1–10. [37] S. Pouryousef, N. K. Panigrahy , and D. T owsley , “ A quantum overlay network for efficient entanglement distribution, ” in IEEE INFOCOM 2023-IEEE Conference on Computer Communications . IEEE, 2023, pp. 1–10. [38] M. F . Askarani, K. Chakraborty , and G. Castro do Amaral, “Entangle- ment distribution in multi-platform buffered-router -assisted frequency- multiplexed automated repeater chains, ” New Journal of Physics , vol. 23, no. 6, p. 063078, 2021. [39] G. Bowen and S. Bose, “T eleportation as a depolarizing quantum chan- nel, relative entropy , and classical capacity , ” Physical Re view Letters , vol. 87, no. 26, p. 267901, 2001. [40] C. H. Bennett, G. Brassard, and N. D. Mermin, “Quantum cryptography without bells theorem, ” Physical re view letters , vol. 68, no. 5, p. 557, 1992. [41] W . Kozlo wski, A. Dahlberg, and S. W ehner, “Designing a quantum network protocol, ” in Proceedings of the 16th international conference on emerging networking experiments and technolo gies , 2020, pp. 1–16. [42] H. Jacinto, É. Gouzien, and N. Sangouard, “Network requirements for distributed quantum computation, ” Physical Revie w Resear ch , v ol. 8, no. 1, p. 013205, 2026. [43] D. Pérez Castro, A. Fernández V ilas, M. Fernández V eiga, M. Blanco Rodríguez, and R. P . Díaz Redondo, “Simulation of fidelity in entanglement-based networks with repeater chains, ” Applied Sciences , vol. 14, no. 23, p. 11270, 2024. [44] P . Zhang and G. Chartrand, Intr oduction to graph theory . T ata McGraw- Hill New Y ork, 2006, vol. 2, no. 2.1. [45] S. Roman et al. , An introduction to Catalan numbers . Springer , 2015. [46] D. Bertsekas, Reinforcement learning and optimal contr ol . Athena Scientific, 2019, vol. 1. [47] R. J. V anderbei, “Linear programming: foundations and extensions, ” Journal of the Operational Research Society , vol. 49, no. 1, pp. 94– 94, 1998. [48] T . Coopmans, R. Knegjens, A. Dahlberg, D. Maier, L. Nijsten, J. de Oli veira Filho, M. Papendrecht, J. Rabbie, F . Rozp ˛ edek, M. Skrzypczyk et al. , “Netsquid, a network simulator for quantum information using discrete e vents, ” Communications Physics , vol. 4, no. 1, p. 164, 2021. [49] A. Zang, A. Kolar , J. Chung, M. Suchara, T . Zhong, and R. Kettimuthu, “Simulation of entanglement generation between absorptive quantum memories, ” in 2022 IEEE International Confer ence on Quantum Com- puting and Engineering (QCE) . IEEE, 2022, pp. 617–623. [50] H. Hübel, M. R. V anner, T . Lederer , B. Blauensteiner, T . Lorünser , A. Poppe, and A. Zeilinger , “High-fidelity transmission of polarization encoded qubits from an entangled source over 100 km of fiber , ” Optics Expr ess , vol. 15, no. 12, pp. 7853–7862, 2007. [51] A. Labay Mora, F . Ferreira da Silva, and S. W ehner, “Reducing hardware requirements for entanglement distribution via joint hardware-protocol optimization, ” Quantum Science and T echnolo gy , vol. 9, no. 4, p. 045001, 2024. [52] R. Barends, J. Kelly , A. Megrant, A. V eitia, D. Sank, E. Jeffrey , T . C. White, J. Mutus, A. G. Fowler , B. Campbell et al. , “Superconducting quantum circuits at the surface code threshold for fault tolerance, ” Natur e , vol. 508, no. 7497, pp. 500–503, 2014. [53] F . Steinlechner, P . Trojek, M. Jofre, H. W eier, D. Perez, T . Jennewein, R. Ursin, J. Rarity , M. W . Mitchell, J. P . T orres et al. , “ A high-brightness source of polarization-entangled photons optimized for applications in free space, ” Optics express , vol. 20, no. 9, pp. 9640–9649, 2012. [54] S. Magnitskiy , D. Frolovtse v , V . Firsov , P . Goste v , I. Protsenko, and M. Saygin, “ A spdc-based source of entangled photons and its char- acterization, ” J ournal of Russian Laser Researc h , vol. 36, no. 6, pp. 618–629, 2015. [55] C. W . Helstrom, “Quantum detection and estimation theory , ” Journal of statistical physics , vol. 1, no. 2, pp. 231–252, 1969. [56] J. P . Dehollain, J. T . Muhonen, R. Blume-Kohout, K. M. Rudinger, J. K. Gamble, E. Nielsen, A. Laucht, S. Simmons, R. Kalra, A. S. Dzurak et al. , “Optimization of a solid-state electron spin qubit using gate set tomography , ” New Journal of Physics , vol. 18, no. 10, p. 103018, 2016. [57] D. A. Rower , L. Ding, H. Zhang, M. Hays, J. An, P . M. Harrington, I. T . Rosen, J. M. Gertler, T . M. Hazard, B. M. Niedzielski et al. , “Suppressing counter-rotating errors for fast single-qubit gates with fluxonium, ” PRX Quantum , vol. 5, no. 4, p. 040342, 2024. [58] M. AbuGhanem and H. Eleuch, “Full quantum tomography study of googles sycamore gate on ibms quantum computers, ” EPJ Quantum T ec hnology , vol. 11, no. 1, p. 36, 2024. [59] P . W ang, C.-Y . Luan, M. Qiao, M. Um, J. Zhang, Y . W ang, X. Y uan, M. Gu, J. Zhang, and K. Kim, “Single ion qubit with estimated coherence time exceeding one hour , ” Nature communications , vol. 12, no. 1, p. 233, 2021. [60] M. H. Abobeih, J. Cramer , M. A. Bakker, N. Kalb, M. Markham, D. J. T witchen, and T . H. T aminiau, “One-second coherence for a single electron spin coupled to a multi-qubit nuclear-spin environment, ” Nature communications , vol. 9, no. 1, p. 2552, 2018. [61] C. E. Bradley , J. Randall, M. H. Abobeih, R. C. Berrev oets, M. J. Degen, M. A. Bakker , M. Markham, D. J. T witchen, and T . H. T aminiau, “ A ten- qubit solid-state spin register with quantum memory up to one minute, ” Physical Revie w X , vol. 9, no. 3, p. 031045, 2019. [62] D. Deutsch, A. Ekert, R. Jozsa, C. Macchiavello, S. Popescu, and A. Sanpera, “Quantum privac y amplification and the security of quantum cryptography ov er noisy channels, ” Physical r eview letters , vol. 77, no. 13, p. 2818, 1996. [63] F . Rozp ˛ edek, T . Schiet, L. P . Thinh, D. Elkouss, A. C. Doherty , and S. W ehner , “Optimizing practical entanglement distillation, ” Physical Review A , vol. 97, no. 6, p. 062333, 2018. [64] P . Jurkie wicz, “T opohub: A repository of reference gabriel graph and real-world topologies for networking research, ” SoftwareX , vol. 24, p. 101540, 2023. [65] E. K. Cetinkaya, M. J. Alenazi, Y . Cheng, A. M. Peck, and J. P . Sterbenz, “On the fitness of geographic graph generators for modelling physical lev el topologies, ” in 2013 5th International Congr ess on Ultra Modern T elecommunications and Contr ol Systems and W orkshops (ICUMT) . IEEE, 2013, pp. 38–45. [66] S. Knight, H. X. Nguyen, N. Falkner , R. Bowden, and M. Roughan, “The internet topology zoo, ” IEEE Journal on Selected Areas in Com- munications , vol. 29, no. 9, pp. 1765–1775, 2011.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment