Secure Rate-Splitting and RIS Beamforming with Untrusted Energy Harvesting Receivers
We consider a reconfigurable intelligent surface (RIS)-assisted heterogeneous network comprising legitimate information-harvesting receivers (IHRs) and untrusted energy-harvesting receivers (UEHRs). A multi-antenna base station (BS) transmits confide…
Authors: Hamid Reza Hashempour, Le-Nam Tran, Duy H. N. Nguyen
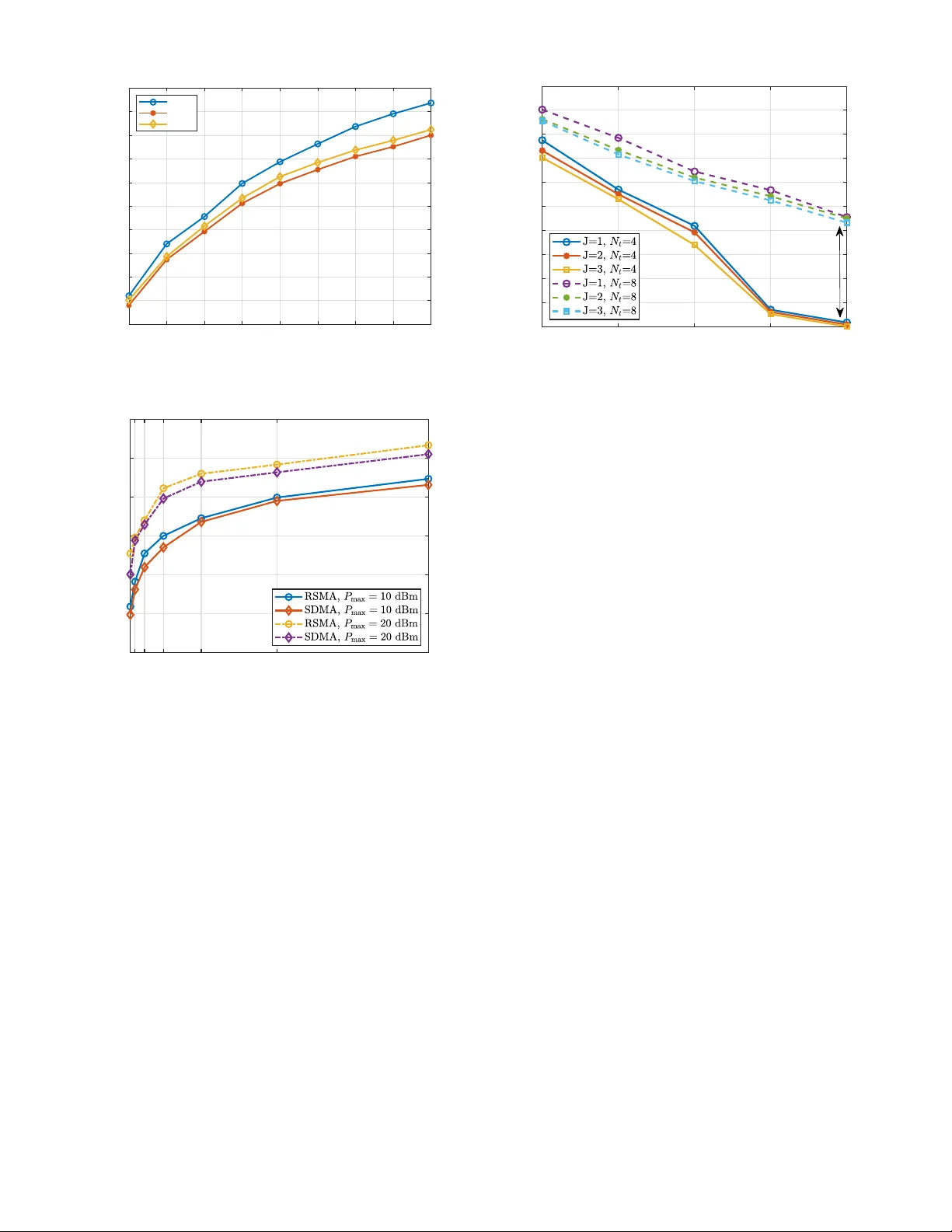
Secure Rate-Splitting and RIS Beamforming with Untrusted Ener gy Harv esting Recei v ers Hamid Reza Hashempour ∗ , Le-Nam T ran † , Duy H. N. Nguyen ‡ , and Hien Quoc Ngo ∗ ∗ Centre for W ireless Innov ation (CWI), Queen’ s Uni versity Belfast, U.K. † School of Electrical and Electronic Engineering, Univ ersity College Dublin, Dublin, Ireland. ‡ Department of Electrical and Computer Engineering, San Diego State Uni versity , San Diego, CA 92182, USA. { h.hashempoor , hien.ngo } @qub .ac.uk, nam.tran@ucd.ie, duy .nguyen@sdsu.edu Abstract —W e consider a reconfigurable intelligent surface (RIS)-assisted heterogeneous network comprising legitimate information-har vesting recei vers (IHRs) and untrusted energy- harvesting recei vers (UEHRs). A multi-antenna base station (BS) transmits confidential information to IHRs while ensuring suffi- cient energy transfer to UEHRs that may attempt eavesdropping . T o enhance physical-lay er security , we propose a secur e rate- splitting multiple access (RSMA) scheme aided by a U A V -mounted RIS. The objective is to maximize fairness-based secrecy energy efficiency (SEE). Owing to the non-conv exity of the formulated problem, we develop an alternating optimization framework that jointly designs the common message allocation, activ e precoders, and RIS phase shifts under transmit power and energy harvesting constraints, leveraging sequential con vex approximation (SCA). Simulation r esults demonstrate the scalability of the pr oposed algorithm and its superior SEE performance compared to space- division multiple access (SDMA) and non-orthogonal multiple access (NOMA) benchmarks. Index T erms —Rate-Splitting, secrecy energy efficiency , beam- forming, reconfigurable intelligent surfaces. I . I N T RO D U C T I O N Unmanned aerial vehicles (U A Vs) and reconfigurable intel- ligent surfaces (RISs) ha ve emer ged as promising enablers for cov erage extension, ener gy-efficient operation, and physical- layer security in beyond-5G networks [1], [2]. By repositioning U A V -mounted RISs, networks can establish fav orable cascaded links in blockage-rich deployments, thereby strengthening de- sired signals and mitigating interference. Recent studies have highlighted both the opportunities and challenges of securing U A V–RIS systems. For instance, [3] emplo ys deep machine learning to address malicious threats in UA V -assisted RIS net- works, while [4] in vestigate RIS-assisted secure communication where a U A V communicates with a ground user under the threat of eav esdropping, using time di vision multiple access (TDMA). Similarly , [5] proposes a RIS-assisted secure U A V communication scheme in the presence of activ e jammers and passiv e eav esdroppers. In parallel, rate-splitting multiple access (RSMA) has been recognized as a robust strategy that enhances spectral ef ficiency and interference management by splitting each user’ s message into common and priv ate parts [6]. Its flexibility makes RSMA particularly attractiv e for security- constrained wireless systems [6]–[8]. The work of H. R. Hashempour and H. Q. Ngo was supported by a research grant from the Department for the Economy Northern Ireland under the US- Ireland R&D Partnership Programme. Moreov er , radio frequency (RF) signals inherently deliv er both information and energy , motiv ating research on simulta- neous wireless information and power transfer (SWIPT). RIS- assisted SWIPT systems have been studied for energy harvest- ing (EH) recei vers [9], while secure SWIPT has drawn attention due to potential eavesdropping by untrusted EH receiv ers. For instance, [10] proposes artificial-noise-aided beamforming for full-duplex relays with untrusted EH receiv ers, and [11] studies RIS-assisted SWIPT in IoT networks. Recently , reinforcement learning has also been applied to maximize secrecy energy efficienc y (SEE) in RIS-assisted networks [12]. Motiv ated by these works, we study a secure multiuser multiple-input single-output (MISO) downlink, where a base station (BS) serves multiple legitimate information-harvesting receiv ers (IHRs) in the presence of untrusted energy-harvesting receiv ers (UEHRs). T o maximize fairness-based SEE while satisfying nonlinear EH constraints at UEHRs, we consider a RIS-assisted RSMA framework and jointly optimize the RSMA precoding, common message parameters, and RIS phase shifts. T o the best of our kno wledge, this joint design for SEE in RSMA-SWIPT systems has not been addressed before. The resulting non-con vex problem is solved via an alternating optimization (A O) algorithm, where the common rate allocation is obtained through linear programming, and the BS precoders and RIS phase shifts via sequential con vex approximation (SCA). Due to page limitations, the UA V -mounted RIS is assumed to be deployed at an ef fectiv e location, and U A V positioning optimization is not considered in this work. The main contributions of this work are summarized as follows: • W e study a secure RIS-assisted multiuser MISO do wnlink with SWIPT , where UEHRs can act as eav esdroppers, and fairness is ensured via a max–min SEE formulation. • W e propose an efficient A O-based solution using Dinkel- bach’ s transform and SCA to jointly optimize RSMA precoding, rate allocation, and RIS phase shifts under nonlinear EH constraints. • Numerical results demonstrate that RSMA provides better robustness and scalability than SDMA and NOMA across various system settings. The rest of the paper is organized as follows: Section II presents the system model and RSMA design. Section III formulates the fairness SEE problem and details the A O frame- BS RIS G b g k h j h bj 1 2 J 1 2 K Untrusted - EHRs IHRs Fig. 1. System model of UA V -assisted RIS-RSMA network. work. Section IV provides numerical results, and Section V concludes the paper . I I . S Y S T E M M O D E L Consider a downlink wireless communication system con- sisting of one U A V -assisted RIS, J non-colluding UEHRs, K legitimate users, and one BS. The set of K IHRs and J UEHRs are denoted by K = { 1 , . . . , K } and J = { 1 , . . . , J } , respectiv ely . Due to the presence of high obstacles, there exists no line-of-sight (LoS) channel between the BS and the users, as well as between the BS and the UEHRs. The U A V , equipped with a RIS, serves as a passive relay to assist communication between the BS and the users. The RIS is composed of M reflecting elements, and the phase shift of each element can be controlled by the UA V . The BS is equipped with N t antennas. All UEHRs, IHRs, and the BS are located on the ground. The horizontal coordinates of user k ∈ K , UEHR j ∈ J , and the BS are denoted by w I k = [ x I k , y I k ] T , w U j = [ x U j , y U j ] T , and w b = [ x b , y b ] T , respectiv ely . The UA V flies at a fixed altitude H and hovers to enhance communication. The system model is demonstrated in Fig. 1. The UA V horizontal coordinate is denoted by q = [ x, y ] T . The channel between the U A V and user k is g k = ˜ g k d − α k 2 k , ˜ g k = q K k K k +1 g LoS k + q 1 K k +1 ˆ g k , (1) where α k ≥ 2 is the pathloss exponent, ˆ g k ∼ C N ( 0 , I M ) , K k the Rician K -factor ( K k = 0 for Rayleigh fading), and d k = q ∥ q − w I k ∥ 2 + H 2 . Similarly , the U A V–UEHR j channel is h j = ˜ h j d − α j 2 j , ˜ h j = q K j K j +1 h LoS j + q 1 K j +1 ˆ h j , (2) where ˆ h j ∼ C N ( 0 , I M ) , K j is the Rician factor ( K j = 0 for Rayleigh fading), and d j = q ∥ q − w U j ∥ 2 + H 2 . W e define the RIS phase shift vector as s = [ s 1 , . . . , s M ] T , where each element is given by s m = e j θ m for all m ∈ { 1 , . . . , M } . The reflection-coefficient matrix of the RIS is then expressed as Θ = diag ( s 1 , . . . , s M ) ∈ C M × M , (3) where θ m ∈ [0 , 2 π ] denotes the phase shift applied by the m -th reflecting element. The channel matrix between the BS and the RIS is denoted by G b ∈ C M × N t , where [ G b ] m,n represents the channel coefficient between the n th transmit antenna at the BS and the m th reflecting element of the RIS. The distance between the BS and the U A V is d b = p ∥ q − w b ∥ 2 + H 2 . (4) As a worst-case assumption for secrecy analysis, we also consider a direct link between the BS and each of the UEHRs. The corresponding channel vector between the BS and the j - th UEHR is denoted by h bj ∈ C N t × 1 for all j ∈ J , where small-scale fading follows the same Rician model as above, with K bj = 0 for NLoS. For simplicity , we assume a common path loss exponent for all air-to-ground links, i.e., α b = α k = α j = α air = α . T o concurrently serve K users, we adopt the RSMA tech- nique throughout this paper . Accordingly , the transmitted signal x ∈ C N t × 1 at the BS is formulated as x = p c s c + K X k =1 p p k s p k , (5) where p c denotes the precoding vector for the common stream and p p k is the precoding vector for the priv ate stream of user k . The symbols s c and s p k represent the common and priv ate data symbols, respectively . Based on this transmission, the receiv ed signals at a le gitimate user k ∈ K and at the j -th UEHR, j ∈ J , are respectiv ely giv en by: y k = g H k ΘG b x + n k , y j = h H bj + h H j ΘG b x + n j , (6) where n k and n j denote the additi ve white Gaussian noise (A WGN) at user k and UEHR j , respecti vely . Based on (6), the receiv ed power at UEHR j ∈ J is expressed as P EH j = h H bj + h H j ΘG b p c 2 + K X k =1 h H bj + h H j ΘG b p p k 2 . (7) Accordingly , the harvested po wer at UEHR j can be modeled as [13] Ω( P EH j ) = ϕ k ′ 1 (1 + exp( − b 0 ( P EH j − b 1 ))) − k ′ 2 , (8) where Ω( · ) is a logistic function representing the non-linear energy harvesting model, and ϕ , k ′ 1 , k ′ 2 , b 0 , b 1 are posi- tiv e constants. According to RSMA principles, the signal-to- interference-plus-noise ratio (SINR) of the common stream receiv ed by user k ∈ K and UEHR acting as an eav esdropper j ∈ J can be expressed as γ c k = | g H k ΘG b p c | 2 K P l =1 | g H k ΘG b p p l | 2 + σ 2 , (9) γ c,e j = | ( h H bj + h H j ΘG b ) p c | 2 K P k =1 | ( h H bj + h H j ΘG b ) p p k | 2 + σ 2 . (10) where σ 2 is the noise po wer . Similarly , for the priv ate streams s p k , k ∈ K , the SINR at user k for decoding its own priv ate stream is giv en by γ p k = | g H k ΘG b p p k | 2 P l = k | g H k ΘG b p p l | 2 + σ 2 . (11) W e employ RSMA such that the UEHRs, regarded as poten- tial eavesdroppers, are unable to decode the common stream. Furthermore, we consider the scenario where UEHR j ∈ J attempts to decode the pri vate stream of user k . The corre- sponding SINR is expressed as γ p,e j,k = | u H j p p k | 2 | u H j p c | 2 + P l = k | u H j p p l | 2 + σ 2 . (12) where u j denotes the combined channel between the BS, RIS, and UEHR j , defined as u H j ≜ h H bj + h H j ΘG b . The transmission rate r c of the common stream at the BS should be designed such that all legitimate users are able to decode it successfully , while also ensuring robustness against the UEHRs. Therefore, the rate r c must satisfy the following condition log 2 (1 + max j ∈J γ c,e j ) ≤ r c ≤ log 2 (1 + min k ∈K γ c k ) . (13) By defining γ c E ≜ max j ∈J γ c,e j and γ p,k E ≜ max j ∈J γ p,e j,k , the secrecy rate of user k ∈ K can be expressed as R sec k = a k r sec c + r sec p,k , (14) where r sec c = [log 2 (1 + γ c ) − log 2 (1 + γ c E )] + (15) r sec p,k = h log 2 (1 + γ p k ) − log 2 (1 + γ p,k E ) i + (16) where [ x ] + ≜ max( x, 0) and γ c ≜ min k ∈K γ c k . Notably , a k adjusts the portion of the common message allocated to each user k , where P K k =1 a k = 1 . I I I . P RO B L E M F O R M U L A T I O N T o ensure perfect secrecy for all users, we define the mini- mum secrecy rate among all users as R sec = min k ∈K R sec k . (17) where R sec denotes the ov erall secrecy rate of the system. Our goal is to maximize the SEE by jointly optimizing transmit precoders and passive beamforming. The problem can be math- ematically formulated as max a , P , θ R sec ϱ T r ( PP H ) + P 0 (18a) s.t. r c ≤ min k ∈K log 2 (1 + γ c k ) , (18b) max j ∈J log 2 (1 + γ c,e j ) ≤ r c , (18c) X j ∈J P EH j ≥ Ω − 1 ( E h ) , (18d) K X k =1 a k = 1 , (18e) 0 ≤ a k ≤ 1 , ∀ k ∈ K , (18f) T r ( PP H ) ≤ P max , (18g) θ m ∈ [0 , 2 π ] , ∀ m ∈ { 1 , . . . , M } , (18h) where a = { a k } K k =1 , P = [ p c , p p 1 , . . . , p p K ] T , and θ = { θ m } M m =1 . Moreov er, E h denotes the minimum harvested en- ergy requirement at the set of UEHRs, ϱ is the reciprocal of the drain efficienc y of the power amplifier at the BS [14], and P 0 represents the circuit power consumption. The in verse function Ω − 1 ( x ) is defined as: Ω − 1 ( x ) = b 1 − 1 b 0 ln ϕ k ′ 1 ( x + k ′ 2 ) − 1 . (19) The optimization problem in (18) is nonconv ex, making the global optimum dif ficult to obtain. T o address this, we decom- pose it into subproblems and apply the SCA method. A. Optimal Allocation of Common Messag e Among IHRs For tractability , the problem in (18) is solved using the block coordinate descent (BCD) method. Giv en the precoding matrix P and RIS phase-shift matrix Θ , the optimal allocation of the common message among the IHRs is determined by solving the following subproblem max ζ , a ζ (20a) s.t. ζ ≤ a k r sec c + r sec p,k , ∀ k ∈ K , (20b) (18e) , (18f) . (20c) where ζ is an auxiliary variable introduced to represent a lower bound of the minimum secrecy rate R sec . Problem (20) is a stan- dard linear programming (LP) problem that can be ef ficiently solved using of f-the-shelf con vex optimization solvers. B. Optimization of Common and Private Pr ecoders For simplicity of notation, we set ϱ = 1 without loss of generality . The resulting subproblem becomes max ζ , P ζ T r ( PP H ) + P 0 (21a) s.t. (20b) , (18b) , (18c) , (18d) , (18g) . (21b) Problem (21) is a nonlinear fractional program. T o address its non-con ve xity , we apply Dinkelbach’ s algorithm [15], introduc- ing an auxiliary variable λ to transform the objectiv e into a more tractable form. The resulting problem is approximated as max ζ , P ζ − λ T r ( PP H ) + P 0 (22a) s.t. (20b) , (18b) , (18c) , (18d) , (18g) . (22b) The optimal value of λ can be iterativ ely updated using Al- gorithm 1 which is described later . Ho wev er , Problem (22) re- mains noncon vex due to the nonconv ex constraints in (22b). T o address this, we adopt an iterati ve approach that approximates the nonconv ex terms using their first-order T aylor expansions at each iteration. In the following, we analyze each noncon vex term individually and derive its conv ex approximation. W e reformulate the non-con vex constraints in (20b) using the epigraph technique. T o this end, we define two sets of auxiliary variables n f c E , f p,k E o , and { ρ c , ρ p k } . As a result, the secrecy constraint (20b) can be equi valently rewritten in terms of these auxiliary variables to enable con- ve x optimization. Using auxiliary variables and the first-order T aylor approximation, constraint (20b) for all k ∈ K can be equiv alently expressed as ζ ≤ a k [log 2 (1 + ρ c ) − f c E ] + [log 2 (1 + ρ p k ) − f p,k E ] , (23a) log 2 (1 + ρ p k ) ≥ f p,k E , (23b) log 2 (1 + ρ c ) ≥ f c E , (23c) ρ c ≤ min k ∈K γ c k , (23d) ρ p k ≤ γ p k , (23e) f c E ≥ log 2 (1 + max j ∈J γ c,e j ) , (23f) f p,k E ≥ log 2 (1 + max j ∈J γ p,e j,k ) . (23g) Proposition 1. The affine appr oximation of constraint (23d) and (23e) , ∀ k ∈ K ar e given by: K X ℓ =1 | v H p p ℓ | 2 + σ 2 − Ψ ( t ) ( p c , ρ c ; v ) ≤ 0 (24) X ℓ = k | v H p p ℓ | 2 + σ 2 − Ψ ( t ) ( p p k , ρ p k ; v ) ≤ 0 , (25) wher e v H ≜ g H k ΘG b and Ψ ( t ) ( u , x ; h ) ≜ 2 Re ( u ( t − 1) ) H hh H u x ( t − 1) − h H u ( t − 1) 2 x x ( t − 1) 2 is the first- or der T aylor appr oximations of | h H u | 2 x . Pr oof. Please refer to [8]. ■ T o handle the nonconv exity of constraints (23f) and (23g), we introduce auxiliary variables ρ c E and ρ p,k E satisfying ρ c E ≥ max j ∈J γ c,e j (26a) f c E ≥ log 2 (1 + ρ c E ) , (26b) ρ p,k E ≥ max j ∈J γ p,e j,k (26c) f p,k E ≥ log 2 (1 + ρ p,k E ) . (26d) Subsequently , the affine approximations of the constraints in (26) are deriv ed as follows | u H j p c | 2 ρ c E − X k Ψ ( t ) ( p p k , 1; u j ) − σ 2 ≤ 0 , (27a) | u H j p c | 2 ρ p,k E − X ℓ = k Ψ ( t ) ( p p ℓ , 1; u j ) − Ψ ( t ) ( p c , 1; u j ) − σ 2 ≤ 0 , (27b) 1 − Γ ( t ) ( f c E ) + ρ c E ≤ 0 , (27c) 1 − Γ ( t ) ( f p,k E ) + ρ p,k E ≤ 0 , (27d) where Ψ ( t ) ( p p k , ρ p k ; v ) and Ψ ( t ) ( p p k , 1; u j ) are the first-order T aylor approximations of | v H p p k | 2 ρ p k and | u H j p p k | 2 , respectively . Moreov er , Γ ( t ) ( x ) ≜ 2 x ( t − 1) 1 + ln(2) ( x − x ( t − 1) ) is the first- order T aylor approximation of 2 x . Follo wing the same approach as in Proposition 1, an affine approximation of constraint (18b) is giv en by r c ≤ log 2 (1 + ρ c ) , (28a) (24) . (28b) For the ea vesdroppers, constraint (18c) is reformulated as 1 − Γ ( t ) ( r c ) + ρ c E ≤ 0 , (29a) (27a) . (29b) Algorithm 1: Iterative Algorithm for Problem (21) Input: Initial values ζ (0) , P (0) , tolerance ε , t = 1 . 1 r epeat 2 Update λ ( t ) using (33); 3 Solv e the con vex subproblem (32); 4 Set t ← t + 1 ; 5 until ζ ( t ) − ζ ( t − 1) ≤ ε ; 6 r eturn P ( t ) ; Finally , the energy harvesting constraint (18d) can be reformu- lated as X j ∈J Φ ( t ) ( p c , u j ) + X j ∈J X k Φ ( t ) ( p p k , u j ) ≥ Ω − 1 ( E h ) , (30) where Φ ( t ) ( a , b ) denotes the first-order T aylor approximation of | a H b | 2 around b ( t − 1) , and is defined as Φ ( t ) ( a , b ) = 2 · Re n b ( t − 1) H aa H b o − a H b ( t − 1) 2 . (31) W ith these approximations, the original precoder optimiza- tion problem (21) can be reformulated into a con vex problem and solved iterati vely , as follows ζ ( t ) , P ( t ) = arg max ζ , P ζ − λ ( t ) T r ( PP H ) + P 0 s.t. (23a) – (23c) , (24) – (30) , (18g) . (32) where λ ( t ) is updated as λ ( t ) = ζ ( t − 1) T r ( P ( t − 1) P ( t − 1) H ) + P 0 . (33) The o verall iterative procedure for solving problem (21) is summarized in Algorithm 1. C. RIS Reflection Phase Optimization W e first note that, given the precoder vectors, the po wer consumption of the system is fixed. Thus, the fairness energy efficienc y maximization problem reduces to a fairness secrecy rate maximization problem. Accordingly , we can reformulate the following subproblem max Θ ,ζ ζ (34) s.t. (20b), (18b), (18c), (18d), (18h) . (35) For any arbitrary v ectors v and w we hav e: v H ΘG b w = t H s , where t = ( diag ( v H ) G b w ) ∗ . Therefore, by defin- ing t kc ≜ ( diag ( g H k ) G b p c ) ∗ , t j c ≜ ( diag ( h H j ) G b p c ) ∗ , t kp ≜ ( diag ( g H k ) G b p p k ) ∗ , t j p ≜ ( diag ( h H j ) G b p p k ) ∗ , t kpℓ ≜ ( diag ( g H k ) G b p p ℓ ) ∗ , t j pℓ ≜ ( diag ( h H j ) G b p p ℓ ) ∗ , we proceed to con ve xify the constraints of the RIS phase optimization subproblem. According to (23) we reformulate the constraint (20b) using the following proposition Proposition 2. An affine appr oximation of constraint (20b) , ∀ k ∈ K and ∀ j ∈ J is given by: K X ℓ =1 | t H kpℓ s | 2 + σ 2 − Ψ ( t ) ( s , ρ c ; t kc ) ≤ 0 , (36a) X ℓ = k | t H kpℓ s | 2 + σ 2 − Ψ ( t ) ( s , ρ p k ; t kp ) ≤ 0 , (36b) | h H bj p c + t H j c s | 2 ≤ Θ ( t ) ( ξ j p , ρ c E ) , (36c) ξ j p ≤ X k ϑ ( t ) ( h H bj p p k , t j p ; s ) + σ 2 , (36d) | h H bj p p k + t H j p s | 2 ≤ Θ ( t ) ( ξ j cℓ , ρ p,k E ) , (36e) ξ j cℓ ≤ X ℓ = k ϑ ( t ) ( h H bj p p ℓ , t j pℓ ; s ) + ϑ ( t ) ( h H bj p c , t j c ; s ) + σ 2 , (36f) (23a) − (23c) , (27c) , (27d) . (36g) wher e we have defined Θ ( t ) ( x, y ) ≜ 1 2 x ( t − 1) + y ( t − 1) ( x + y ) − 1 4 x ( t − 1) + y ( t − 1) 2 − 1 4 ( x − y ) 2 , for the linear appr oximation of the terms that in volve a pr oduct of two variables. Additionally , ϑ ( t ) ( c ; t ; s ) is the first-or der T aylor appr oximation of | c + t H s | 2 at iteration t : ϑ ( t ) ( c ; t ; s ) = 2 Re n c + t H s ( t − 1) H t H s o − c + t H s ( t − 1) 2 . (37) Pr oof. Please refer to [8]. ■ From the remaining constraints in problem (35), we replace (18b) with its af fine approximation in (28). Constraint (18c) is approximated by (29a), (36c), and (36d). Moreov er , (18d) can be rewritten as X j ∈J ϑ ( t ) ( h H bj p c ; t j c ; s ) + X j ∈J X k ϑ ( t ) ( h H bj p p k ; t j p ; s ) ≥ Ω − 1 ( E h ) . (38) Constraint (18h) is equiv alent to | s m | = 1 , ∀ m ∈ { 1 , . . . , M } . (39) Howe ver , (39) is still a non-con vex constraint. Hence, follo wing the penalty-based method in [16], we handle the unit-modulus constraint and rewrite the objective function as follows max ζ , s ζ + C ∥ s ∥ 2 (40a) s.t. (36) , (28) , (29a) , (36c) , (36d) , (38) , (40b) | s | ≤ 1 , (40c) where C is a lar ge positiv e constant, | s | denotes the element- wise magnitude of s , 1 is a vector of ones, and the inequality in (40c) is understood entry-wise. Note that the penalty term enforces | s m | 2 = 1 at the optimal solution. W e further ap- proximate the non-con ve x part, i.e., the penalty term in the objectiv e of (40). T ow ard this end, we directly linearize the quadratic term | s m | 2 around the point s ( t − 1) m using its first- order T aylor expansion. Accordingly , the penalty term can be approximated as C P M m =1 2 Re { ( s ( t − 1) m ) ∗ s m } − | s ( t − 1) m | 2 . Thus, the problem can be rewritten as max ζ , s ζ + C 2 Re ( s ( t − 1) ) H s − ∥ s ( t − 1) ∥ 2 (41a) s . t . (36) , (28) , (29a) , (36c) , (36d) , (38) , (40c) . (41b) Here, ( t − 1) denotes the previous iteration of the phase optimization subproblem in (41). Finally , the RIS phase op- timization can be summarized in Algorithm 2. By sequentially optimizing ( a , P , θ ), the joint optimization of the common message coefficient, BS activ e beamforming, and RIS phase shifts can be effecti vely solved using an A O scheme. The complete procedure is presented in Algorithm 3. Algorithm 2: Iterative Algorithm for Phase Optimiza- tion Problem Input: Initial values ζ (0) , Θ (0) , s (0) , tolerance ε . Output: Optimized phase shifts Θ ∗ . 1 Set t ← 1 ; 2 r epeat 3 Solv e the optimization problem in (41); 4 t ← t + 1 ; 5 until | ζ ( t ) − ζ ( t − 1) | ≤ ϵ ; 6 r eturn Θ ( t ) ; Algorithm 3: Proposed Algorithm for Fairness Secrecy Energy Ef ficiency Maximization Input: Initialize P (0) , Θ (0) , η (0) , tolerance ε for Algorithm 1, iteration index i ← 0 , and con ver gence accuracy ϵ . 1 r epeat 2 Obtain message allocation ratios a ( i +1) by solving (20) with giv en P ( i ) , Θ ( i ) . 3 Obtain RS precoders P ( i +1) via Algorithm 1 with giv en a ( i +1) , Θ ( i ) . 4 Obtain RIS phase shifts Θ ( i +1) via Algorithm 2 with giv en a ( i +1) , P ( i +1) . 5 Compute η ( i +1) = ζ ( i +1) P K k =1 ∥ p p ( i +1) k ∥ 2 + ∥ p c ( i +1) ∥ 2 + P 0 . 6 if η ( i +1) < η ( i ) then 7 Set Θ ( i +1) ← Θ ( i ) . 8 i ← i + 1 9 until η ( i ) − η ( i − 1) ≤ ϵ I V . S I M U L A T I O N R E S U LT S Unless otherwise stated, the setup is as follows. W e con- sider a 1500 × 3000 m 2 area with the BS at (0 , 0) and the U A V at (1000 , 0 , 100) m. The BS employs N t = 4 antennas, serving K = 2 le gitimate users and J = 2 UEHRs, ran- domly distributed within circles of radius 500 m centered at ( − 1000 , 1000) m and ( − 1000 , − 1000) m, respectiv ely . The U A V carries an RIS with M = 16 reflecting elements. Other parameters are: path-loss exponent α = 2 . 5 , circuit power P 0 = 1 W , and minimum harvested energy E h = 0 . 01 J. Noise power is normalized to 0 dBm and the minimum required transmission rate of the common stream is r c = 0 . 5 Bit/sec/Hz [8]. All results are av eraged ov er 100 channel realizations with con ver gence accuracy ϵ = ε = 0 . 01 . Figure 2 compares the SEE versus N t for the proposed RSMA scheme against SDMA and NOMA baselines, which are implemented as special cases of RSMA following the modeling approach in [6], with P max = 10 dBm. SEE increases with N t and then saturates, since extra antennas provide mainly array gains while secrecy rate grows only logarithmically . RSMA achiev es the highest SEE by fle xibly managing interference. SDMA slightly outperforms NOMA, as beamforming is more 2 3 4 5 6 7 8 9 10 Number of BS antennas (N t ) 3.5 4 4.5 5 5.5 6 6.5 7 7.5 8 8.5 Secrecy energy efficiency (bps/Hz/W) RSMA NOMA SDMA Fig. 2. SEE versus N t for P max = 10 dBm and M = 16 compared with NOMA and SDMA benchmarks. 2 4 8 16 32 64 128 Number of RIS elements (M) 0 2 4 6 8 10 12 Secrecy energy efficiency (bps/Hz/W) Fig. 3. SEE versus M for N t = 4 and different schemes. effecti ve than SIC in this scenario. Figure 3 shows the impact of RIS size M . Increasing M enhances SEE with a logarithmic trend, and higher P max further boosts performance. Notably , M = 128 with P max = 10 dBm achie ves almost the same SEE as M = 16 with P max = 20 dBm, demonstrating the RIS’ s energy-sa ving potential. Finally , Fig. 4 ev aluates scalability . As K increases, SEE decreases significantly due to higher eav esdropping probability , while more UEHRs cause only a slight drop. Increasing N t improv es spatial diversity and offsets the degradation. For instance, at K = 6 , raising N t from 4 to 8 yields more than a fourfold gain in SEE. V . C O N C L U S I O N S W e in vestigated a UA V -assisted RIS-RSMA system for se- cure and energy-efficient do wnlink transmission in the presence of UEHRs. An A O-based algorithm was proposed to jointly optimize message allocation, active precoders, and RIS phase shifts under power and EH constraints. Simulation results verified fast con vergence and demonstrated that the proposed scheme achie ves higher SEE compared to SDMA and NOMA baselines, highlighting the strong synergy between RSMA and RIS in U A V -assisted secure networks. 2 3 4 5 6 Number of IHRs (K) 1 2 3 4 5 6 7 8 9 10 Secrecy energy efficiency (bps/Hz/W) SEE improvement >4 Fig. 4. SEE versus number of legitimate users ( K ) and UEHRs ( J ) for P max = 20 dBm. R E F E R E N C E S [1] R. Kaur et al. , “ A survey on reconfigurable intelligent surface for physical layer security of next-generation wireless communications, ” IEEE Open J. V eh. T echnol. , vol. 5, pp. 172–199, 2024. [2] H. R. Hashempour et al. , “Power -efficient cooperative communication within IIoT subnetworks: Relay or RIS?, ” IEEE Internet Things J. , vol. 12, no. 9, pp. 12483–12500, May 2025. [3] U. A. Mughal et al. , “Deep learning for secure U A V -assisted RIS communication networks, ” IEEE Internet Things Mag. , vol. 7, no. 2, pp. 38–44, Mar . 2024. [4] S. Li et al. , “Rob ust secure U A V communications with the aid of reconfigurable intelligent surfaces, ” IEEE T rans. W ir eless Commun. , vol. 20, no. 10, pp. 6402–6417, Oct. 2021. [5] Y . Shang et al. , “RIS-assisted secure UA V communication scheme against activ e jamming and passive eavesdropping, ” IEEE T rans. Intell. T ransp. Syst. , vol. 25, no. 11, pp. 16953–16963, Nov . 2024. [6] H. Bastami et al. , “On the physical layer security of the cooperativ e rate- splitting-aided downlink in U A V networks, ” IEEE T rans. Inf . F orensics Secur . , vol. 16, pp. 5018–5033, 2021. [7] H. R. Hashempour and G. Berardinelli, “Secure rate splitting in ST AR- RIS assisted downlink MISO systems, ” in Proc. IEEE Int. Mediterranean Conf. Commun. Netw . (MeditCom) , Madrid, Spain, 2024, pp. 529–534. [8] H. R. Hashempour et al. , “Secure SWIPT in the multiuser ST AR-RIS- aided MISO rate-splitting downlink, ” IEEE Tr ans. V eh. T echnol. , vol. 73, no. 9, pp. 13466–13481, Sep. 2024. [9] B. Zhang et al. , “Performance analysis of RIS-assisted wireless commu- nications with energy harvesting, ” IEEE T rans. V eh. T echnol. , vol. 72, no. 1, pp. 1325–1330, Jan. 2023. [10] J. Ouyang et al. , “Secrecy energy efficienc y in full-duplex AF relay systems with untrusted energy harvesters, ” IEEE Commun. Lett. , vol. 25, no. 11, pp. 3493–3497, Nov . 2021. [11] M. Mohammadi, H. Q. Ngo, and M. Matthaiou, “Phase-shift and transmit power optimization for RIS-aided massive MIMO SWIPT IoT networks, ” IEEE T rans. Commun. , vol. 73, no. 1, pp. 631–647, Jan. 2025. [12] Y . Zhang et al. , “Deep reinforcement learning for secrecy energy efficienc y maximization in RIS-assisted networks, ” IEEE T rans. V eh. T echnol. , vol. 72, no. 9, pp. 12413–12418, Sep. 2023. [13] E. Boshkovska et al. , “Practical non-linear energy harvesting model and resource allocation for SWIPT systems, ” IEEE Commun. Lett. , vol. 19, no. 12, pp. 2082–2085, Dec. 2015. [14] L. D. Nguyen et al. , “Energy efficiency in cell-free massive MIMO with zero-forcing precoding design, ” IEEE Commun. Lett. , vol. 21, no. 8, pp. 1871–1874, Aug. 2017. [15] W . Dinkelbach, “On nonlinear fractional programming, ” Manage . Sci. , vol. 13, no. 7, pp. 492–498, Mar . 1967. [16] V . Kumar et al. , “ A novel SCA-based method for beamforming optimiza- tion in IRS/RIS-assisted MU-MISO downlink, ” IEEE Wir eless Commun. Lett. , vol. 12, no. 2, pp. 297–301, Feb . 2023.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment