The Decentralisation Paradox in Digital Identity: Centralising Decentralisation with Digital Wallets?
Digital identity is shifting from service- and network-centric approaches toward user-centric ones that promise users increased control over their data. Despite their decentralised design, such approaches often reintroduce centralised components in d…
Authors: Ioannis Konstantinidis, Ioannis Mavridis, Evangelos K. Markakis
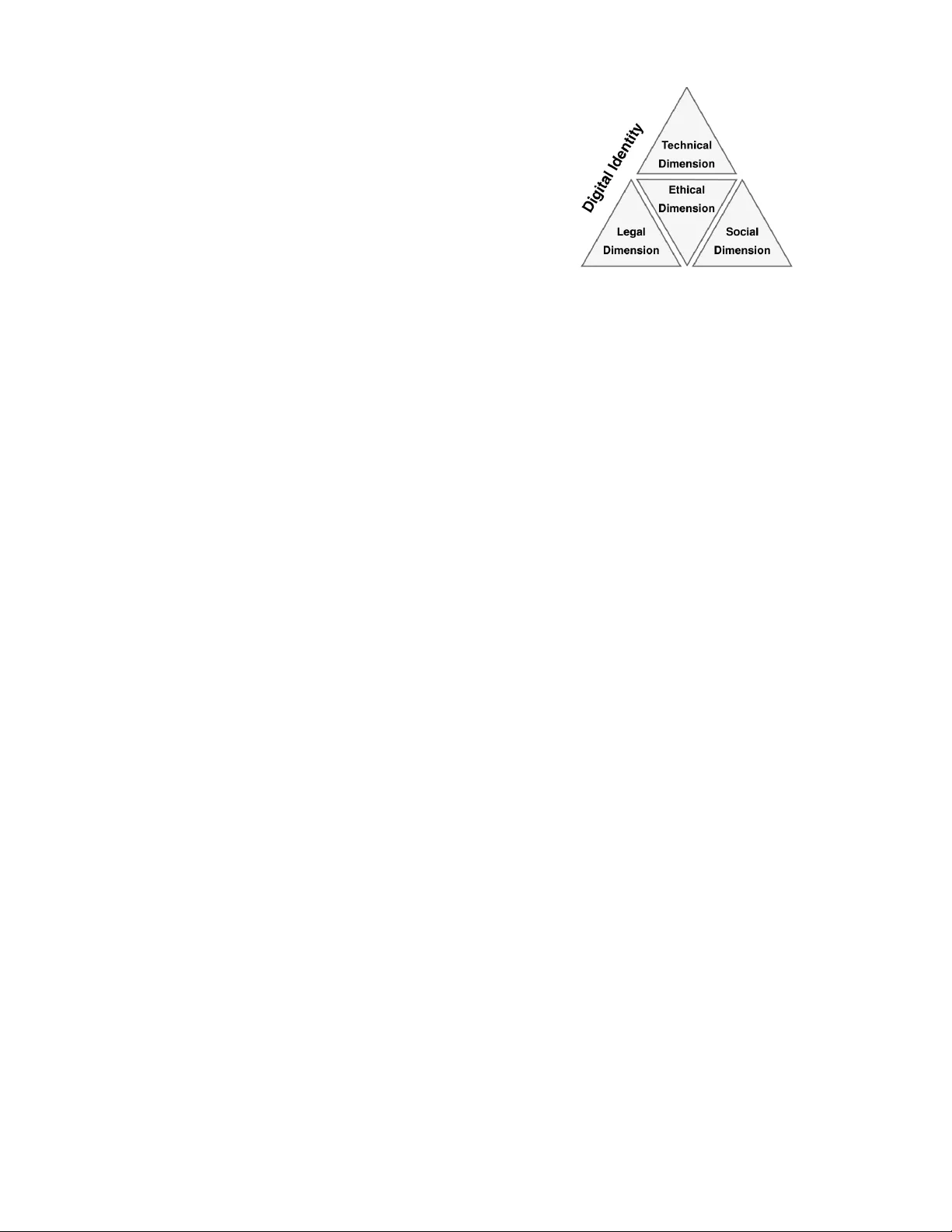
PREPRINT SUBMITTED TO ARXIV 1 The Decentralisation P aradox in Digital Identity: Centralising Decentralisation with Digital W allets? Ioannis K onstantinidis, Ioannis Ma vridis, and Ev angelos K. Markakis Abstract —Digital identity is shifting from service- and network-centric approaches toward user-centric ones that promise users increased control over their data. Despite their de- centralised design, such approaches often reintroduce centralised components in differ ent f orms. This resear ch explores this ten- sion, i.e., the decentralisation paradox, and argues that user - centric architectures tend to redistrib ute rather than eliminate centralisation. Based on Critical Systems Thinking (CST), digital identity is framed as a ”wicked problem” that spans across the technical, legal, social and ethical dimensions. The paper argues that understanding all these interdependencies is essential f or designing reliable architectures and ensuring the next generation of digital identity goes beyond superficial decentralisation. Index T erms —Digital identity , decentralised identity , self- sover eign identity , digital wallets, decentralisation paradox. I . I N T RO D U C T I O N Who o wns digital identities? In user-centric digital iden- tity architectures, including decentralised identity and Self- Sov ereign Identity (SSI), users hold and control their creden- tials in digital wallets and decide when and with whom to share them [1] [2] [3]. Howe v er , research indicates an ongoing tension, i.e. a “decentralization paradox” embedded in such approaches; the more they aim to eliminate intermediaries, the more they lean tow ard different forms of co-ordination and control while reintroducing centralised components [4] [5] [6]. As a consequence, rather than eliminating centralisation, user-centric approaches often redistribute it. Despite the promise of user -centric architectures in fostering innov ation and enhancing priv acy and data protection, they are constrained by a number of coordination-related challenges [4] [6] as well as fragmented standards [7] [8] [9]. The literature suggests that decentralisation operates along a continuum, i.e., architectures are decentralised in some aspects and centralised in others [1] [9] [10] [11]. In particular , in user -centric approaches, gov ernmental entities and institutions reassert a central position ev en on top of decentralised components [12] [6] [10] [13]. Thus, the decentralisation paradox challenges researchers to examine not only the technical dimension of digital identity , but also the legal, social and ethical ones [14]. Giv en the multi-dimensional complexities of digital identity [15], this paper aims to problematise the established perspec- tiv es within the field. It adopts Critical Systems Thinking (CST) [16] as the methodological approach which encourages a holistic examination of complex systems; this is often ov er - looked in technical or legal analyses. Based on CST [17], this Ioannis K onstantinidis and Ioannis Mavridis are with the Department of Applied Informatics, University of Macedonia, Thessaloniki 54636, Greece. Evangelos K. Markakis is with the Department of Electrical and Computer Engineering, Hellenic Mediterranean Univ ersity , Heraklion 71410, Greece. research conceptualises digital identity as a “wicked problem” that spans multiple dimensions and resists simple solutions. The exploration of the decentralisation paradox in digital identity leads to the following research questions: RQ1: How does digital identity ev olve from service-centric and network-centric to user-centric approaches, and what factors influence this paradigm shift? RQ2: How do the technological, legal, social, and ethical di- mensions of digital identity interact to shape the mani- festation of the decentralisation paradox? RQ3: How do digital wallets and their surrounding architectural components operate as new intermediaries within user- centric digital identity architectures, and how does this reinforce the decentralisation paradox across the techni- cal, legal, social and ethical dimensions? The contribution of this research is both analytical and conceptual. It offers a critical perspectiv e that identifies the hidden forces of centralisation in user-centric architectures and introduces the “Digital Identity T etrahedron” as a framew ork for examining these forces. As such, the paper adv ances a theoretical problematisation to deepen the understanding of the decentralisation paradox and inform more context-aw are design choices in the future dev elopment of such architectures. I I . E VO L U T I O N O F D I G I TA L I D E N T I T Y ( R Q 1 ) A. Service-, Network- and User-Centric Approac hes Digital Identities are understood as sets of attributes that represent entities within a specific context [18] [19] [20]. They ev olved from service-centric (centralised) to network- centric (federated) approaches, and no w lean to wards user - centric ones [11] [13] [21] that often incorporate the concepts of decentralised identity or SSI. This reflects a paradigm shift in how digital identities are created, managed and used. In service-centric approaches, digital identities are managed in a centralised manner where a single Identity Provider (IdP) issues credentials and manages data within its own environ- ment. Although, these approaches suf fer from a number of limitations [22] [23], including credential proliferation and password fatigue. As a response, network-centric approaches, including Federated Identity Management (FIM) and Single Sign-On (SSO) [24], establish trust relationships among IdPs and Service Providers (SPs) and enable users to access multi- ple SPs with the same set of credentials. While these network- centric approaches offer a consistent experience and ease-of- use, they still re volv e around a number of IdPs [11] [22] [25]. As a consequence, trust and control remain centralised and render these architectures as single points of failure. PREPRINT SUBMITTED TO ARXIV 2 Fig. 1. An illustration of a user-centric architecture that depicts the issuer , user , verifier and the underlying trust mechanism. W ith the emergence of Distributed Ledger T echnology (DL T), user-centric approaches support users with managing their own credentials through cryptographic mechanisms and blockchain-based registries [13] [21] [26]. A cornerstone of these approaches are digital wallets, i.e., applications that hold the users’ credentials and cryptographic keys. Figure 1 indicates the three main actors in such architectures: a) issuers that issue credentials to users, b) users who store credentials in their digital wallets and c) verifiers that make decisions based on the presented credentials [1] [9]. As credentials are portable and under the users’ possession, it is possible to use one credential across multiple SPs or combine data from different credentials [27] [28] into a single presentation to SPs. Proponents often argue that decentralisation eliminates the before-mentioned single points of failure. Moreover , the re- duction of centralised IdPs could mitigate the risk of mass data breaches and surveillance [6] [11] [21] [26]. Howe ver , these promises face significant challenges in the real world. Even when there are standardised protocols, the deployment of such user-centric architectures at a national or even a global scale is subject to multiple technical, legal, social and ethical considerations [5] [6] [10] [11] [21] [23] [25] [29] [30] [31] [32] [33]. It is not sufficient to dev elop a digital wallet or a credential verification mechanism; one also needs to establish framew orks, unified standards and adoption strategies for an architecture to work [1] [14] [22]. This is where the decen- tralisation paradox becomes evident: to replace intermediaries, additional forms of agreements and components are required. B. T rust and Co-or dination in User-Centric Appr oaches Both trust and co-ordination are foundational elements. When an SP relies upon a credential, there is an implicit trust that it is valid, it belongs to the legitimate user and the issuer of that credential is authoritative [6] [34]. In service-centric or network-centric approaches, establishing trust is straightfor- ward, since the IdP serves as the trust anchor . Whereas, in user - centric approaches, trust is established through a combination of technical components (e.g., cryptographic mechanisms) and governance frameworks (e.g., policies, certification and ov ersight mechanisms) [12] [35]. In fact, the concept of a “trust framew ork” is often used to denote a set of agreements, standards and roles that enable trust. In user-centric approaches, trust frame works take on dif- ferent forms, including the notion of “trustlessness” [6] [26] which differs from Public Ke y Cryptography (PKI)-based approaches [34]. In this sense, trustlessness intends to elimi- nate reliance on intermediaries [36], although such technical trustlessness does not eliminate the social and le gal dimensions of trust [37]. One must still trust that issuers are authoritative and issue genuine credentials and that the overall framew ork is not compromised. In reality , what is often described as trustlessness is better characterised as ”trust minimisation”. The literature discusses two main approaches: • W eb of T rust [22] [25] [38]: Each verifier decides which issuers to trust in an independent manner, often through bilateral or community-based relationships. While decen- tralised, this approach becomes impractical at a large scale, as it lacks a common baseline of trust and could lead to fragmentation or uncertainties. • Trust Anchors [1] [6] [38]: T rust registries co-ordinate and formalise trust relationships. In practice, these often require foundations, consortia or governmental entities to establish rules (e.g., requirements for issuers) and maintain lists of trusted issuers. Although credentials are still exchanged in a peer-to-peer manner , this approach reintroduces a centralised point of co-ordination. In this context, assurance is an important requirement [23] [39]. For example, the eIDAS Regulation defines three Levels of Assurance (LoAs) [39] [40], i.e., Low , Substantial or High. Likewise, NIST SP 800-63-3 specifies three Identity Assurance Le vels (IALs) [41]. In essence, a higher LoA or IAL implies stringent identity proofing and verification processes (e.g., in-person appointments and/or biometric recognition). This is where decentralisation faces friction once more. In practice, such requirements also lead to the establish- ment of certification schemes. These are centralised, e ven if implemented through a network of auditors or authorities [34] [42]. The paradoxical outcome is the re-distrib ution of trust, i.e., users do not depend on a single IdP but still depend on a centralised mechanism [1] [38]. As the next section outlines, the real-world implementations of user-centric approaches at scale reveal important contradictions. C. Real-W orld Implementations of User-Centric Appr oaches A number of national and international implementations of user-centric approaches draw on principles from decentralised identity and SSI. These approaches emphasise that users hold credentials in digital wallets and control the disclosure of their identity data. In practice, howe ver , sev eral state-backed and government-led implementations incorporate centralised elements for trust, co-ordination, assurance and gov ernance; this again reflects the broader decentralisation paradox. In the European Union, the European Digital Identity W allet (EUDI W allet) is a prominent example under the eIDAS 2.0 Regulation [43]. Its architecture [44] [45] incorporates a number of open standards such as ISO/IEC 18013-5, ISO/IEC 23220-2, OID4VP , OID4VCI and IETF SD-JWT VC. In particular , the EUDI W allet operates on a PKI-based trust mechanism [34] [46] and each member-state maintains trusted lists of entities (e.g., wallet providers). Although this set- up contributes to assurance and interoperability , it also re- introduces centralised components. Furthermore, the current PREPRINT SUBMITTED TO ARXIV 3 design raises concerns about unlinkability and observ abil- ity [47] [48]. This means that while selectiv e disclosure is theoretically supported, the credential presentations could be correlated across SPs. In effect, the EUDI W allet reflects an implementation where the appearance of user control coexists with strong institutional ov ersight; this raises questions about the actual degree of decentralisation of such architectures. In the United States, mobile Driving Licences (mDLs) are av ailable in several states [49] [50] [51] [52] [53]. These are provisioned to smartphone wallets and signed by each state’ s issuing authority . In parallel, the Transportation Security Ad- ministration (TSA) accepts mDLs in lieu of physical IDs at a number of airports [54]. While the interface is user-centric, the underlying trust mechanism remains centralised. Furthermore, in certain implementations, there are additional dependencies: Apple W allet and Google W allet support mDLs but introduce a degree of proprietary integration into a public trust infras- tructure [49] [55]. Despite the rhetoric of user control, the architecture rev olves around centralised issuance, verification and governance as seen in network-centric approaches. What emerges is a user-centric interface on top of an institutional framew ork which also raises questions about the depth of decentralisation and the practical limits of user control. In Bhutan, the National Digital Identity (NDI) [56] [57] supports a range of credentials such as national identification documents, permits and certificates [58] using W3C DIDs and W3C VCs. In principle, NDI also supports selectiv e disclosure and aligns with SSI in terms of user control and data minimisation. Its trust anchor is DL T -based, as it relies on Hyperledger Indy with a planned migration to Polygon [59]. Nev ertheless, ev en NDI reflects the decentralisation para- dox, as it relies on centralised trust registries and rev ocation mechanisms despite its decentralised infrastructure [58]. A national legal framework (i.e., the NDI Act [60]) defines the gov ernance-related parameters, including which issuers are trusted and under what conditions credentials are rev oked. Thus, Bhutan’ s NDI exemplifies how SSI-aligned approaches are still dependent on centralised components, e ven on top of decentralised infrastructures. In Buenos Aires, Argentina, QuarkID [61] [62] allows users to self-manage multiple categories of credentials, including civic records, licenses and certificates. It is also possible for them to self-issue credentials (albeit with limited recognition) [63]. QuarkID’ s blockchain-based infrastructure is anchored across zkSync, Ethereum, Polygon and Rootstock; it aligns with the Trust Over IP F oundation (T oIP) model [64] which details the requirements for trust and interoperability across multiple layers. Y et, despite its emphasis on decentralisa- tion and alignment with the principles of SSI, QuarkID is dependent on municipal authorities [63]. This re veals that decentralised technical components could still be constrained, thereby exemplifying the decentralisation paradox. Japan’ s My Number Card [65] reflects a contrasting ap- proach which is less decentralised (by design) but still relev ant to user -centric paradigms. It functions as an of ficial identity document that contains the user’ s attributes and a unique 12- digit identifier [66] which can, in turn, point to tax, social security or health records. A smartphone integration allows Fig. 2. The Digital Identity T etrahedron: A conceptual model that illustrates the technical, legal, social and ethical dimensions of digital identity . users to enrol their My Number Card into Apple iOS or Google Android [67]. Despite these user-centric features, the o verall approach remains centralised [68] [69]. All identity data reside in gov ernment-managed databases, while the physical card or the mobile device functions as an access token. Moreover , the smartphone integration introduces dependencies on proprietary components [67] and further reinforces the centralisation. As such, Japan’ s case emphasises that digitisation and user-centric approaches do not necessarily in volv e decentralisation; by default, there could be reinforced centralised components. All these real-world implementations reflect that user- centric digital identity constitutes a broader superset that encompasses distributed, decentralised and ev en SSI-aligned approaches. A consistent observation is that ev en the most decentralised architectures depend on forms of centralised gov ernance or trust co-ordination. This again underscores the decentralisation paradox: user-centric approaches do not elim- inate the inv olvement of authorities but rather redistribute and reframe it. In fact, governmental entities or other institutional actors continue to curate registries, trust lists or blockchains that anchor trust [12] [34]. Thus, e ven as users obtain increased control over their identity data, the surrounding infrastructure remains dependent on centralised components. I I I . M U LTI - D I M E N S I O N A L A N A L Y S I S O F D I G I TA L I D E N T I T Y ( R Q 2 ) T o understand the decentralisation paradox, it is useful to conceptualise digital identity through a ”Digital Identity T etrahedron” that reflects its multiple dimensions (Figure 2): (a) T echnical Dimension [21] [37] [38]: It concerns the ar - chitectural components, protocols, mechanisms and data structures that enable the identification, authentication, authorisation and management of digital identities. (b) Legal Dimension [35] [39] [70]: It relates to the princi- ples, frameworks and le gal requirements that define the recognition and governance of digital identities. (c) Social Dimension [12] [29] [71]: It reflects the patterns of trust, user behaviour , accessibility and the factors that influence adoption and digital inclusion or exclusion. (d) Ethical Dimension [25] [36] [72]: It concerns the moral and normativ e considerations related to fairness, priv acy , autonomy and power distribution. PREPRINT SUBMITTED TO ARXIV 4 A. T echnical Dimension From a technical point-of-view , user-centric approaches rely upon cryptographic mechanisms, distributed ledgers and stan- dardised protocols. The specific design choices determine the lev el of decentralisation and interoperability of an architecture. The technical components in such approaches often include: • Identity Data and Credential Structures: W3C Decen- tralised Identifiers (DIDs) [73] are independent of cen- tralised registries and can be anchored on blockchains, distributed ledgers or peer -to-peer networks. In addi- tion, W3C V erifiable Credentials (VCs) [27] and IETF Selectiv e Disclosure JSON W eb T oken (SD-JWT) VCs [28] describe credentials that contain identity data in a priv acy-preserving manner . For specific use-cases, there are additional specifications such ISO/IEC 18013-5 and 18013-7 for mDLs [74] [75] and ICA O Doc 9303 for Digital Tra vel Credentials (DTCs) [76] [77]. • Credential Exchange and T rust Protocols: There are mul- tiple examples such as Decentralised Identifier Commu- nication (DIDComm) [78], OpenID for V erifiable Cre- dential Issuance (OID4VCI) [79], OpenID for V erifiable Presentation (OID4VP) [80] and Self-Issued OpenID Provider (SIOPv2) [81] that support the issuance, presen- tation and verification of credentials across architectures. • Digital W allets: These serve as the user interfaces for managing credentials and cryptographic keys [2] [21] [82]. Their design determines how users store, manage and present identity data. In practice, wallets need to be intuitiv e to use [7] [21] [23] [82], resilient against com- promise [22] [31] [32] [83] and equipped with recov ery options [10] [84]. Ideally , a well-designed wallet should enable users to control their data with confidence. Beyond technical specifications, the success or failure of user-centric approaches depends on a series of legal and social enablers. On one hand, institutions and regulators shape the ecosystem through laws, trust framew orks and compliance requirements. On the other hand, human factors such as trust, usability and institutional acceptance are equally important [71]. Even if an architecture includes decentralised technical components, users could find it difficult to adopt or v erifiers could refuse to accept credentials without a central guarantor . B. Legal Dimension The question of governance was amongst the first to expose the tension between decentralisation and accountability in SSI [12] [34] [84]. For instance, the Sovrin network created their gov ernance framew ork that detailed who could run network nodes, how issuers were on-boarded and how compliance with legislation was handled [15]. While not part of formal law , such framew orks often assume a quasi-legal character . In parallel, the Decentralized Identity Foundation (DIF) [85] and the T oIP Foundation [64] [86] defined governance models and sets of rules. Hence, all these dev elopments reflected that a trustless architecture cannot fulfil the real-world requirements In practice, in service- or network-centric approaches, there are well-defined roles and responsibilities, e.g., gov ernmental entities issue passports and maintain their integrity , and finan- cial institutions validate their customers’ identities according to Kno w-Y our-Customer (KYC) and Anti-Money Laundering (AML) le gislation [15] [35]. Howe ver , such requirements become difficult to fulfil in user-centric approaches [3] [39], as legal frameworks need to further detail the duties of issuers, users and verifiers. Consequently , decentralisation in digital identity faces pressure for accountability [84] which, in turn, prompts the introduction of centralised governance-related processes [12]; the decentralisation paradox re-appears. C. Social Dimension Besides the technical and legal dimension, the success or failure of user -centric approaches depends on whether users trust and adopt them. The paradox is reflected here as well: centralisation often fosters mistrust (e.g., fear of monopolisation or surveillance) but decentralisation could also appear chaotic or insecure [7] [25] [72]. Meanwhile, the public remains sceptical of digital identity and fears the loss of ci vil liberties, re gardless of an architecture’ s design and capabilities. Moreov er , there are persistent usability and inclusion-related challenges. Not all users are capable or willing to manage cryptographic keys or secure their own wallets [71] [82]. Therefore, sev eral user-centric approaches incorporate social recov ery mechanisms [10] [84] which, in fact, re-introduce forms of delegated trust. In state-backed user-centric imple- mentations, gov ernmental entities might pro vide backup mech- anisms; which could increase conv enience but also recentralise control in case of inappropriate safeguards. Another behavioural observation is that users often equate con venience with trust. The well-documented “priv acy para- dox” [2] [29] [71] phenomenon reflects that users express concern about priv acy and data protection but trade them for ease-of-use. In the context of digital wallets, users might over - disclose personal data if the interface makes it easy (or appears secure by design) without understanding the potential impli- cations. Paradoxically , this could lead to greater data exposure than in service-centric or network-centric approaches, as the wallet might make everything look secure and trustworthy . Thus, transparency , user education and responsible interface design are essential [71] [84]. D. Ethical Dimension Is it ethical to shift a number of technical complexities to users (e.g., managing credentials and cryptographic keys), knowing that mistakes will happen? The ethical dimension rev olves around the redistribution of responsibilities, mitiga- tion of vulnerabilities and maintenance of control. As control mov es to each user , so does the burden of managing risk. For example, the theft of a device (with a digital wallet) could lead to the loss of access to essential credentials (e.g. educational qualifications). Even mechanisms such as mnemonic-based or social (shared) recovery come with challenges, e.g., by requir- ing trusted contacts or third parties [10] [21] [84]. Therefore, the decentralisation paradox appears again, as the initial effort to eliminate intermediaries creates additional dependencies. PREPRINT SUBMITTED TO ARXIV 5 Another ethical concern is digital inclusion [82]. Despite the existence of population groups who lack smartphones or digital literacy , user-centric approaches often assume both access to and competence with digital solutions [72]. An ethical design would require alternati ve options (e.g., card- based credentials, dele gated access or support through commu- nity centres) to ensure participation from e veryone, including people with cognitive impairments or disabilities [10] [37] [84]. Meanwhile, gov ernmental entities and institutions need to refrain from treating people differently or denying access to services if they do not possess a wallet. Fundamentally , digital identity is meant to expand choice rather than restrict it. Furthermore, there are persistent priv acy and surveillance- related risks [7] [25] [72]. Even decentralised technical com- ponents could be repurposed to control users rather than empower them. For instance, a user-centric architecture cannot guarantee protection against coercion or misuse, as malicious actors or intermediaries might still track, profile or exclude users [31] [32] [48]. The technical dimension alone cannot ensure ethical outcomes; and if the legal frame work lacks strength or clarity , ethics become the final safeguard. This is where the ”identity monopolies” [22] [25] phe- nomenon becomes evident. In practice, decentralisation redis- tributes (but does not remov e) the centres of power [25]. This is evident when a handful of technological solutions or wallet providers hold a dominant position. Therefore, ethical design requires a critical aw areness of ho w ev en open standards could, in practice, be gov erned by a limited set of powerful actors. Overall, the ethical dimension underscores that decentrali- sation is not virtuous by default. For instance, a digital identity ecosystem in the hands of an abusi ve government could still be used to profile or even discriminate against people. Like wise, a technical design could protect against surveillance by SPs but what if the underlying technology itself is subverted [32] (e.g., a wallet with hidden tracking capabilities)? As such, a truly ethical design needs to strike the right balance between autonomy , security , innovation and accountability . I V . D I S C U S S I O N : D E C E N T R A L I S A T I O N P A R A D OX I N D I G I T A L I D E N T I T Y ( R Q 3 ) The analysis through the Digital Identity T etrahedron exem- plifies the decentralisation paradox. Even with a user-centric approach, a degree of centralised gov ernance and oversight remains necessary . Y et an excessi ve redistribution of power would undermine the core benefits of decentralisation. Hence, trust requires calibration: users need to trust a solution before adoption and this, in turn, necessitates strong safe guards. It is a delicate balance that requires a multidisciplinary collaboration; not only among cryptographers and engineers, but also jurists, sociologists and ethicists from the earliest stages of design. A. A Single P oint of Con ver gence and Exposure Digital wallets promise a unified point of conv ergence for personal data. This enhances con venience b ut also concentrates a lot of data on the user’ s device. T echnically , wallets risk becoming high-value targets, as a single compromise could expose multiple credentials at once [31] [32] [33]. In effect, the wallet’ s strength as a one-stop solution is also its greatest weakness and constitutes a single point of failure. A key promise of digital wallets is data minimisation which enables users to disclose the minimum amount of data for specific purposes [25] [70]. In theory , minimisation also limits profiling [36] and restricts issuers or verifiers from tracking when and ho w credentials are used. Ho wever , researchers highlight that certain design choices could still lead to expo- sure and undermine the principle of unlinkability [47] [48] [70] [72], e.g., through collusions between issuers and verifiers. As a consequence, this raises the spectre of different forms of profiling [32]: a wallet that knows everything about users could impose unprecedented impacts on their liv es if misused. This is where the paradox resurfaces; a user-centric approach reduces reliance on siloed IdPs but aggre gates personal data within the users’ wallets and increases their exposure. B. A Single Authority that Anchors T rust In effect, in national implementations, governmental entities and institutions remain the ultimate trust anchors. The state authorities (or their appointed providers) issue credentials that all other parties need to recognise. Moreover , user -centric approaches introduce further centralised dependencies; ev en though identity data exist on the users’ devices, their security often depends on specific components such as Trusted Execu- tion Environments (TEEs) or Secure Enclaves (SEs) [9] [22] [83]. This reinforces the decentralisation paradox: e ven when the wallet empowers users at the edge, it meanwhile restricts them to a centralised trust mechanism and an oligopoly of actors for specific functionalities [38] [87]. Overall, the legal and ethical implications of such an arrangement would be significant. When trust is anchored in government-back ed infrastructures, authorities retain the power to withdraw , revok e or in validate credentials. If a malicious actor decides to unilaterally inv alidate a user’ s credentials, it could disrupt that user’ s access to multiple services and ef fecti vely cut them off from society . This il- lustrates how user-centric architectures could still reproduce structural power asymmetries; it also raises serious concerns about accountability , due process and democratic safeguards. C. A F or gotten User: Cognitive Overload and Exclusion Amid the excitement that surrounds digital wallets, there is a risk of forgetting the users these solutions are meant to empower . The literature indicates that wallets often impose additional cognitiv e burdens and complexities that undermine their intended benefits [23] [71] [88]. In addition, the absence of transparent user interfaces could reflect an illusion of control [71] and fail to provide adequate protection. In f act, the inherent cognitiv e overload could render a solution frustrating or ev en intimidating to the av erage user [38]. As such, the decentralisation paradox highlights a deeper concern: ignoring these realities could increase digital inequalities. An ev en starker challenge is digital e xclusion [7] [72]. It cannot be assumed that everyone possesses a smartphone or the digital literacy to use one in a confident manner . If digital wallets become the default mode of identification and PREPRINT SUBMITTED TO ARXIV 6 authentication, those who lack devices or skills could be left behind [72]. Even if alternative solutions are of fered (e.g., physical cards), they might be treated as second-class users. Thus, user-centric approaches run the danger of becoming exclusionary by design. The for gotten user is the one for whom a wallet represents exclusion instead of empowerment. D. A Responsibility Shift Disguised as Empowerment As noted earlier , the introduction of digital wallets imposes a number of obligations [6] [32] that users might struggle with. While they are expected to keep their credentials safe and use them correctly , the legal frame works might nevertheless presume a failure in their duty (e.g., in cases of fraud or compromise). In this sense, user empowerment becomes an illusion: a series of relev ant risks are shifted downward onto users without adequate support or recourse. The decentralisation paradox also raises ethical questions: Do we empower users or do we shift responsibilities and call it empowerment? Also, what happens if verifiers pressure users into rev ealing their credentials or demand additional data? This is where the introduction of new intermediaries (e.g., custodians) could emerge to manage and protect the users’ wallet on their behalf [6] [37]; but then this would once again undermine the autonomy that user-centric approaches promise. V . C O N C L U S I O N The future of user-centric approaches depends on careful design choices at the intersection of the technical, legal, social and ethical dimensions. As these ev olve, there is an urgent need to dev elop a rich conceptual framework for digital identity: one that focuses on who holds power , who absorbs risk and how technological solutions serve the public good. The recognition of the decentralisation paradox is the first step toward addressing it. W ithout critical reflection, there is a real risk of rev erting to centralised architectures that are disguised as user empo werment. As such, researchers and practitioners need to work across disciplines to bend the arc of implementation toward pragmatic user empowerment. This requires a delicate balance to reconcile the promise of decentralisation with the practical realities of re-centralisation. It is crucial to ensure the next generation of digital identity fulfils its promises in practice rather than merely in rhetoric. Finally , it is important to question the true meaning of user empowerment. Is it measured by the amount of identity data users control, or by the level of understanding and confidence they hav e in managing their data? If the latter , then it might be time to rethink uniform wallet solutions and consider more adaptiv e, inclusive and supportive approaches that match the users’ real-world expectations and capabilities. R E F E R E N C E S [1] ˇ S. ˇ Cu ˇ cko, ˇ S. Be ´ cirovi ´ c, A. Kamisalic, S. Mrdovic, and M. T urkanovi ´ c, “T owards the Classification of Self-Sov ereign Identity Properties, ” IEEE Access , vol. 10, pp. 88 306–88 329, 2022. [2] M. Babel, L. Willb urger, J. Lautenschlager, F . V ¨ olter , T . Guggenberger , M.-F . K ¨ orner , J. Sedlmeir, J. Str ¨ uker , and N. Urbach, “Self-Sovereign Identity and Digital W allets, ” Electronic Markets , vol. 35, p. 28, 2025. [3] J. Sedlmeir, R. Smethurst, A. Rieger , and G. Fridgen, “Digital Identities and V erifiable Credentials, ” Business & Information Systems Engineer- ing , vol. 63, pp. 603–613, 2021. [4] K. L. T an, C.-H. Chi, and K.-Y . Lam, “Survey on Digital So vereignty and Identity: From Digitization to Digitalization, ” ACM Computing Surveys , vol. 56, no. 3, p. 61, 2023. [5] K. Degen and T . T eubner, “W allet W ars or Digital Public Infrastructure? Orchestrating a Digital Identity Data Ecosystem from a Government Perspectiv e, ” Electr onic Markets , vol. 34, p. 50, 2024. [6] E. Krul, H. young Paik, S. Ruj, and S. S. Kanhere, “SoK: Trusting Self- Sovereign Identity, ” Pr oceedings on Privacy Enhancing T echnologies , vol. 2024, no. 3, pp. 297–313, 2024. [7] S. H. Supangkat, H. S. Firmansyah, I. Rizkia, and R. Kinanda, “Challenges in Implementing Cross-Border Digital Identity Systems for Global Public Infrastructure: A Comprehensiv e Analysis, ” IEEE Access , vol. 13, pp. 42 083–42 098, 2025. [8] S. Lips, N. V inogradova, R. Krimmer , and D. Draheim, “Re-Shaping the EU Digital Identity Framework, ” in Proceedings of the 23rd Annual International Confer ence on Digital Government Resear ch . Association for Computing Machinery , 2022, pp. 13–21. [9] H. Y ildiz, A. K ¨ upper , D. Thatmann, S. Gondor , and P . Herbke, “T oward Interoperable Self-Sovereign Identities, ” IEEE Access , vol. 11, pp. 114 080–114 116, 2023. [10] A. Satybaldy , M. S. Ferdous, and M. Nowostawski, “A T axonomy of Challenges for Self-Sovereign Identity Systems, ” IEEE Access , vol. 12, pp. 16 151–16 177, 2024. [11] P . Manimaran, T . Garrett, L. Jehl, and R. V itenberg, “Decentralization T rends in Identity Management: From Federated to Self-Sov ereign Identity Management Systems, ” Computer Science Review , vol. 58, p. 100776, 2025. [12] R. B. Gans, J. Ubacht, and M. Janssen, “Gov ernance and Societal Impact of Blockchain-Based Self-Sov ereign Identities, ” P olicy and Society , vol. 41, no. 3, pp. 402–413, 2022. [13] M. Alizadeh, K. Andersson, and O. Schel ´ en, “Comparative Analysis of Decentralized Identity Approaches, ” IEEE Access , vol. 10, pp. 92 273– 92 283, 2022. [14] L. W eigl, T . Barbereau, and G. Fridgen, “The Construction of Self- Sovereign Identity: Extending the Interpretive Flexibility of T echnology T owards Institutions, ” Government Information Quarterly , vol. 40, no. 4, p. 101873, 2023. [15] R. A. Pav a-Diaz, J. Gil-Ruiz, and D. A. Lopez-Sarmiento, “Self- Sovereign Identity on the Blockchain: Contextual Analysis and Quan- tification of SSI Principles Implementation, ” F rontiers in Blockchain , vol. 7, p. 1443362, 2024. [16] M. C. Jackson, Critical Systems Thinking and the Management of Complexity . W iley , 2019. [17] ——, Critical Systems Thinking: A Practitioner’ s Guide . Wile y , 2024. [18] International Organization for Standardization (ISO), “ISO/IEC 24760- 1:2025 – Information Security , Cybersecurity and Privac y Protection – A Framew ork for Identity Management, ” 2025, accessed: 2025-11-25. [Online]. A vailable: https://www .iso.org/standard/24760- 1 [19] International T elecommunication Union (ITU), “ITU-T Recom- mendation X.1252 – Baseline Identity Management T erms and Definitions, ” 2021, accessed: 2025-11-25. [Online]. A vailable: https://www .itu.int/rec/T - REC- X.1252- 202104- I/en [20] National Institute of Standards and T echnology, “NIST SP 800-63: Digital Identity Guidelines, ” 2024, accessed: 2025-11-25. [Online]. A vailable: https://pages.nist.gov/800- 63- 4/sp800- 63.html [21] D. Schumm, K. O. E. M ¨ uller , and B. Stiller , “ Are we there yet? a study of decentralized identity applications, ” IEEE Access , vol. 13, pp. 125 232– 125 259, 2025. [22] R. Soltani, U. T . Nguyen, and A. An, “A Survey of Self-Sovereign Identity Ecosystem, ” Security and Communication Networks , vol. 2021, 2021. [23] F . Schardong and R. Cust ´ odio, “Self-sovereign identity: A systematic revie w , mapping and taxonomy , ” Sensors , vol. 22, no. 15, p. 5641, 2022. [24] National Institute of Standards and T echnology, “NIST SP 800-63C: Federation and Assertions, ” 2024, accessed: 2025-11-25. [Online]. A vailable: https://pages.nist.gov/800- 63- 4/sp800- 63c.html [25] G. Ishmae v , “Sovereignty , Priv acy , and Ethics in Blockchain-Based Identity Management Systems, ” Ethics and Information T echnology , vol. 23, pp. 239–252, 2021. [26] ˇ Spela ˇ Cu ˇ cko and M. T urkanovi ´ c, “Decentralized and Self-Sov ereign Identity: Systematic Mapping Study, ” IEEE Access , vol. 9, pp. 139 009– 139 027, 2021. PREPRINT SUBMITTED TO ARXIV 7 [27] W orld Wide W eb Consortium (W3C), “V erifiable Credentials Data Model v2.0, ” 2025, accessed: 2025-11-25. [Online]. A vailable: https://www .w3.org/TR/vc- data- model- 2.0/ [28] O. T erbu, D. Fett, and B. Campbell, “Selectiv e Disclosure for JWT -Based V erifiable Credentials (SD-JWT VC), ” Internet Engineering T ask Force (IETF), 2025, accessed: 2025-11-25. [Online]. A vailable: https://datatracker .ietf.org/doc/draft- ietf- oauth- sd- jwt- vc/ [29] J. Lockl, N. Thanner, M. Utz, and M. R ¨ oglinger , “The Paradoxical Impact of Information Priv acy on Privac y Preserving T echnology: The Case of Self-Sovereign Identities, ” International Journal of Innovation and T echnology Management , vol. 20, no. 04, p. 2350025, 2023. [30] N. Martin and F . M. Metzger, “The Chimera of Control: Self-Sovereign Identity , Data Control, and User Perceptions, ” Human T echnology , vol. 20, no. 2, pp. 183–223, 2024. [31] D. P ¨ ohn, M. Grabatin, and W . Hommel, “ Analyzing the Threats to Blockchain-Based Self-Sovereign Identities by Conducting a Literature Survey , ” Applied Sciences , vol. 14, no. 1, 2024. [32] A. Sharif, Z. E. Ansaroudi, G. Sciarretta, D. P ¨ ohn, M. Mollaeefar , W . Hommel, and S. Ranise, “Protecting Digital Identity W allet: A Threat Model in the Age of eIDAS 2.0, ” in Risks and Security of Internet and Systems , S. Collart-Dutilleul, S. Ouchani, N. Cuppens, and F . Cuppens, Eds. Cham: Springer Nature Switzerland, 2025, pp. 89–106. [33] L. Ziegler , M. Grabatin, D. P ¨ ohn, and W . Hommel, “Designing a Secu- rity Incident Response Process for Self-Sovereign Identities, ” EURASIP Journal on Information Security , vol. 2025, no. 12, 2025. [34] R. Ramos Fern ´ andez, “Evaluation of T rust Service and Software Product Regimes for Zero-Knowledge Proof Development under eIDAS 2.0, ” Computer Law & Security Review , vol. 53, p. 105968, 2024. [35] A. Giannopoulou and F . W ang, “Self-Sovereign Identity, ” Internet P olicy Review , vol. 10, no. 2, 2021. [36] G. Ishmaev and Q. Stokkink, “Identity Management Systems: Singular Identities and Multiple Moral Issues, ” Fr ontiers in Blockchain , vol. 3, p. 15, 2020. [37] ˇ S. ˇ Cu ˇ cko, V . Ker ˇ si ˇ c, and M. T urkanovi ´ c, “T owards a Catalogue of Self- Sovereign Identity Design Patterns, ” Applied Sciences , vol. 13, no. 9, p. 5395, 2023. [38] F . Ghaffari, K. Gilani, E. Bertin, and N. Crespi, “Identity and Access Management using Distributed Ledger T echnology: A Survey , ” Interna- tional Journal of Network Management , vol. 32, no. 2, p. e2180, 2022. [39] J. Andrasko and M. Mesarcik, “Those Who Shall be Identified: The Data Protection Aspects of the Legal Framework for Electronic Identification in the European Union, ” T alT ech Journal of European Studies , vol. 11, no. 2, pp. 3–24, 2021. [40] European Commission, “Commission Implementing Regulation (EU) 2015/1502 of 8 September 2015 Setting Out Minimum T echnical Specifications and Procedures for Assurance Lev els for Electronic Identification Means Pursuant to Article 8(3) of Regulation (EU) No 910/2014, ” 2015, accessed: 2025-11-25. [Online]. A vailable: https://eur- le x.europa.eu/eli/reg impl/2015/1502/oj/eng [41] National Institute of Standards and T echnology, “NIST SP 800- 63A: Enrollment and Identity Proofing, ” 2024, accessed: 2025-11-25. [Online]. A vailable: https://pages.nist.gov/800- 63- 4/sp800- 63a.html [42] European Commission, “Certification and Risk Management – European Digital Identity W allet Architecture and Reference Frame work v2.7.3, ” 2025, accessed: 2025-11-25. [Online]. A vailable: h tt p s : //eudi .de v/2.7 .3/archite cture- and- re ference- fr amework- mai n/#7- certifi c ation- and- risk- management [43] European Parliament and Council of the European Union, “Regulation (EU) 2024/1183 of the European Parliament and of the Council of 11 April 2024 Amending Regulation (EU) No 910/2014 as Regards Establishing the European Digital Identity Framework, ” 2024, accessed: 2025-11-25. [Online]. A vailable: h ttps://eur- lex.europ a.eu/eli/reg/2 024/ 1183/oj [44] European Commission, “EUDI W allet Ecosystem – European Digital Identity W allet Architecture and Reference Framework v2.7.3, ” 2025, accessed: 2025-11-25. [Online]. A vailable: https://eudi.dev/2.7.3/archite cture- and- reference- framework- main/#3- eudi- wallet- ecosystem [45] ——, “2. EUDI W allet Functionalities – Architecture and Reference Framew ork v2.3.0, ” 2025, accessed: 2025-11-25. [Online]. A vailable: https ://eudi .de v/2. 7.3/arch itecture- and- refer ence- fra mework- ma in/#2- e udi- wallet- functionalities [46] ——, “T rust Model – European Digital Identity W allet Architecture and Reference Framework v2.7.3, ” 2025, accessed: 2025-11-25. [Online]. A vailable: http s://eud i.dev/2.7 .3/arch itectur e- and- re ferenc e- frame work - main/#6- trust- model [47] C. Baum, O. Blazy , J. Camenisch, J. Hoepman, E. Lee, A. Lehmann, A. L ysyanskaya, R. Mayrhofer , H. Montgomery , N. K. Nguyen, B. Preneel, A. Shelat, D. Slamanig, S. T essaro, S. E. Thomsen, and C. T roncoso, “Cryptographers’ Feedback on the EU Digital Identity’ s ARF, ” 2024, accessed: 2025-11-25. [Online]. A vailable: http s://gi thub.co m/eu- di gital- i dentit y- wallet /eudi- doc- arc hitectu re- and - reference- framework/issues/200 [48] I. A. Alvarez, P . Holzmer , and J. Sedlmeir, “Priv acy Evaluation of the European Digital Identity W allet’ s Architecture and Reference Frame- work, ” Computers & Security , vol. 160, p. 104707, 2026. [49] Apple, “ID in W allet — Supported U.S. States, ” 2025, accessed: 2025-11-25. [Online]. A vailable: https://learn.wallet.apple/id#states- list [50] A. D. of Transportation, “Arizona Mobile Driv er License (mDL), ” 2025, accessed: 2025-11-25. [Online]. A vailable: http s://azdo t.gov/mv d/mobile- driver - license [51] C. D. of Motor V ehicles, “California Mobile Dri ver License (mDL), ” 2025, accessed: 2025-11-25. [Online]. A vailable: h tt p s: //www .dmv .ca.gov/portal/california- mdl/google- wallet/ [52] G. D. of Dri ver Services, “Georgia Digital Dri ver’ s License and ID, ” 2025, accessed: 2025-11-25. [Online]. A vailable: h tt p s: //dds.georgia.gov/georgia- licenseid/ga- digital- id [53] I. D. of T ransportation, “Iowa Mobile ID App, ” 2025, accessed: 2025-11-25. [Online]. A vailable: https ://iowad ot.gov/d ri vers- l icenses- i ds/mobile- id/iowa- mobile- id- app [54] U.S. Transportation Security Administration (TSA), “TSA – Partici- pating States and Eligible Digital IDs, ” 2025, accessed: 2025-11-25. [Online]. A vailable: https://www .tsa.gov/digital- id/participating- states [55] Google, “Store Y our Digital ID on Y our Phone – Google W allet, ” 2025, accessed: 2025-11-25. [Online]. A vailable: h ttps://wallet.g oogle/ intl/en us/digitalid/ [56] Bhutan NDI, “Bhutan NDI (National Digital Identity), ” 2025, accessed: 2025-11-25. [Online]. A vailable: https://www .bhutanndi.com/ [57] United Nations Dev elopment Programme (UNDP), “Kingdom of Bhutan: Digital Development and Transformation Strategy, ” 2024, accessed: 2025-11-25. [Online]. A vailable: https:/ /www .un dp.or g/bhuta n/pub lication s/kingdom - bhutan- d igital- devel opment- a nd- transf ormatio n- strategy [58] P . Sharma and E. Drury , “Bhutan NDI (National Digital Identity) & T oIP Digital Trust Ecosystems, ” 2024, accessed: 2025-11-25. [Online]. A vailable: ht tps:/ /trus tover ip.or g/wp- co ntent /uplo ads/ Case- S tudy- Bh u tan- NDI- Na tional- Digital- Id entity- ToIP- Digita l- Trust- Ecosyste ms- V1. 0- 2024- 05- 21.ext .pdf [59] Bhutan NDI, “Press Release – DHI Announces Bhutan NDI’ s Migration to the Polygon Blockchain for Enhanced User Experience and Scalability, ” 2025, accessed: 2025-11-25. [Online]. A vailable: htt ps:/ /www .bh utan ndi.c om/a rtic le/pr ess- r eleas e- dh i- ann ounc es- b huta n- ndi- s - migration- t o- the- polygon - blockchain- for- en hanced- user- exper ience- and- scalability 82080061- 7100- 468b- 803e- 7fde59205f6b [60] Parliament of Bhutan, “National Digital Identity Act of Bhutan 2023, ” 2023, accessed: 2025-11-25. [Online]. A vailable: h t t p s : //tech.gov.bt/wp - content/uploads/2024 /09/National- Digital- I dentity- Act - of- Bhutan- 2023.pdf [61] Government of the City of Buenos Aires – QuarkID, “QuarkID – A Self-Sovereign Digital Identity, ” 2025, accessed: 2025-11-25. [Online]. A vailable: https://quarkid.org/ [62] QuarkID, “QuarkID Architecture, ” 2025, accessed: 2025-11-25. [On- line]. A vailable: https://docs.quarkid.org/en/Arquitectura/arquitectura/ [63] ——, “Self-Sovereign Identity: Basis of a New Decentralized Digital Ecosystem (QuarkID Whitepaper), ” Whitepaper, 2022, accessed: 2025- 11-25. [Online]. A vailable: https://github.com/ssi- quarkid/WhitePaper [64] Trust Over IP Foundation (T oIP), “Design Principles for the Trust over IP Stack, ” 2021, accessed: 2025-11-25. [Online]. A vailable: http s://tru stoverip .org/wp - conten t/uploa ds/Desi gn- Princ iples- fo r- the- T oIP- Stack- V1.0- 2022- 11- 17.pdf [65] The Japan Agency for Local Authority Information Systems, “Individual Number Card (My Number Card), ” 2025, accessed: 2025-11-25. [Online]. A vailable: https://www .kojinbango- card.go.jp/en/ [66] Digital Agency , Government of Japan, “My Number (Indi vidual Number) Scheme / My Number Card, ” 2025, accessed: 2025-11-25. [Online]. A vailable: https://www .digital.go.jp/en/policies/mynumber [67] ——, “Smartphone My Number Card, ” 2025, accessed: 2025-11-25. [Online]. A vailable: h ttps ://ww w .di gita l.go. jp/e n/po licie s/my numbe r/s martphone- certification [68] ——, “Japanese Public Key Infrastructure (JPKI), ” 2025, accessed: 2025-11-25. [Online]. A vailable: ht tps:// www .d igital. go.jp/ en/pol icies/ mynumber/private- business/jpki- introduction [69] ——, “Common Infrastructure and General-Purpose T ools for My Number Card Use, ” 2025, accessed: 2025-11-25. [Online]. A vailable: PREPRINT SUBMITTED TO ARXIV 8 https://www .digital.go.jp/en/policies/mynumber/local- government/platfo rms- and- generic- tools- for- jpki [70] E. Podda, P . Holzmer, A. Amard, J. Sedlmeir, and G. Fridgen, “The Impact of Zero-Knowledge Proofs on Data Minimisation Compliance of Digital Identity W allets, ” Internet P olicy Review , vol. 14, no. 3, pp. 1–29, 2025. [71] M. T euschel, D. P ¨ ohn, M. Grabatin, F . Dietz, W . Hommel, and F . Alt, “Don’t Annoy Me With Priv acy Decisions! Designing Priv acy- Preserving User Interfaces for SSI W allets on Smartphones, ” IEEE Access , vol. 11, pp. 131 814–131 835, 2023. [72] A. Kaplane, “The European Digital Identity W allet: A New Human Right Unlocked?” Nordic Journal of Human Rights , vol. 43, no. 3, pp. 304– 316, 2025. [73] W orld Wide W eb Consortium (W3C), “Decentralized Identifiers (DIDs) v1.0: Core Architecture, Data Model, and Representations, ” 2022, accessed: 2025-11-25. [Online]. A vailable: ht tps:/ /www.w3.o rg/TR/ di d- 1.0/ [74] International Organization for Standardization (ISO), “ISO/IEC 18013- 5:2021 – Personal Identification: ISO-Compliant Dri ving Licence – Part 5: Mobile Driving Licence (mDL) Application, ” 2021, accessed: 2025- 11-25. [Online]. A vailable: https://www .iso.org/standard/69084.html [75] ——, “ISO/IEC TS 18013-7:2025 – Personal Identification: ISO- Compliant Driving Licence – Part 7: Mobile Driving Licence (mDL) Add-On Functions, ” 2025, accessed: 2025-11-25. [Online]. A vailable: https://www .iso.org/standard/91154.html [76] International Ci vil A viation Organization (ICA O), “Machine Readable T rav el Documents T echnical Report: Guiding Core Principles for the Dev elopment of Digital Trav el Credential (DTC), ” 2023, accessed: 2025-11-25. [Online]. A vailable: h ttps://www2023. icao.int/Securi ty/F A L/TRIP/Pu blishingImages/Pages /Publications/IC AO%20GUIDING%20 CORE%20PRINCIPLES%20DTC Draft%20v4.8.pdf [77] ——, “Machine Readable Trav el Documents T echnical Report: Digital T rav el Credentials (DTC) Physical Component and Protocols, ” 2022, accessed: 2025-11-25. [Online]. A vailable: ht tps://www2 023.icao.i nt/S ecu rity/ F A L/TRI P/Pub lishi ngIm ages/ Pages/ Publi catio ns/I CAO%2 0TR %20- %20Digital%20T ravel%20Credentials%20PC.pdf [78] S. Curren, T . Looker, and O. T erbu, “DIDComm Messaging v2.1, ” Decentralized Identity Foundation (DIF), 2023, accessed: 2025-11-25. [Online]. A vailable: https: //identity.foundation/didcomm- messaging/spe c/v2.1 [79] T . Lodderstedt, K. Y asuda, and T . Looker , “OpenID for V erifiable Credential Issuance 1.0, ” OpenID Foundation, 2025, accessed: 2025- 11-25. [Online]. A vailable: htt ps://o penid. net/sp ecs/o penid- 4 - verif iabl e- credential- issuance- 1 0.html [80] O. T erbu, T . Lodderstedt, K. Y asuda, D. Fett, and J. Heenan, “OpenID for V erifiable Presentations 1.0, ” OpenID Foundation, 2025, accessed: 2025-11-25. [Online]. A vailable: https://openid.net/specs/openid- 4- verif iable- presentations- 1 0.html [81] K. Y asuda, M. Jones, and T . Lodderstedt, “Self-Issued OpenID Provider v2, ” OpenID Foundation, 2023, accessed: 2025-11-25. [Online]. A vailable: ht tps://openid.net/specs/openid- connect- self- is sued- v2- 1 0 .h tml [82] B. Lukkien, N. Bharosa, and M. D. Reuv er, “Barriers for Developing and Launching Digital Identity W allets, ” in Proceedings of the 24th Annual International Confer ence on Digital Government Resear ch . Association for Computing Machinery , 2023, pp. 289–299. [83] Z. E. Ansaroudi, G. Sciarretta, A. D. Maria, and S. Ranise, “Navigating Secure Storage Requirements for EUDI W allets: A Revie w Paper , ” EURASIP Journal on Information Security , vol. 2025, no. 2, pp. 1–24, 2025. [84] J. Xian, L. Y ou, Q. Y i, J. W ang, and G. Hu, “A Surve y on Decentralized Identity Management Systems, ” Computer Science Review , vol. 58, p. 100811, 2025. [85] Decentralized Identity Foundation, “About Decentralized Identity Foundation – Gov erning Documents, ” 2025, accessed: 2025-11-25. [Online]. A vailable: https://identity.foundation/governance/about [86] Trust Over IP Foundation (T oIP), “Principles of SSI, ” 2021, accessed: 2025-11-25. [Online]. A vailable: https ://trusto v erip.o rg/wp- con tent/upl oads/2021/10/ToIP- Principles- of- SSI.pdf [87] C. Lepore, R. Laborde, and J. Eynard, “Aligning eIDAS and Trust Over IP: A Mapping Approach, ” in Pr oceedings of the 19th International Confer ence on A vailability, Reliability and Security . Association for Computing Machinery , 2024, p. Article 186. [88] D. P ¨ ohn, M. Grabatin, and W . Hommel, “eID and Self-Sovereign Identity Usage: An Overview, ” Electronics , vol. 10, no. 22, p. 2811, 2021.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment