Grant, Verify, Revoke: A User-Centric Pattern for Blockchain Compliance
In decentralized web applications, users face an inherent conflict between public verifiability and personal privacy. To participate in regulated on-chain services, users must currently disclose sensitive identity documents to centralized intermediar…
Authors: Supriya Khadka, Sanchari Das
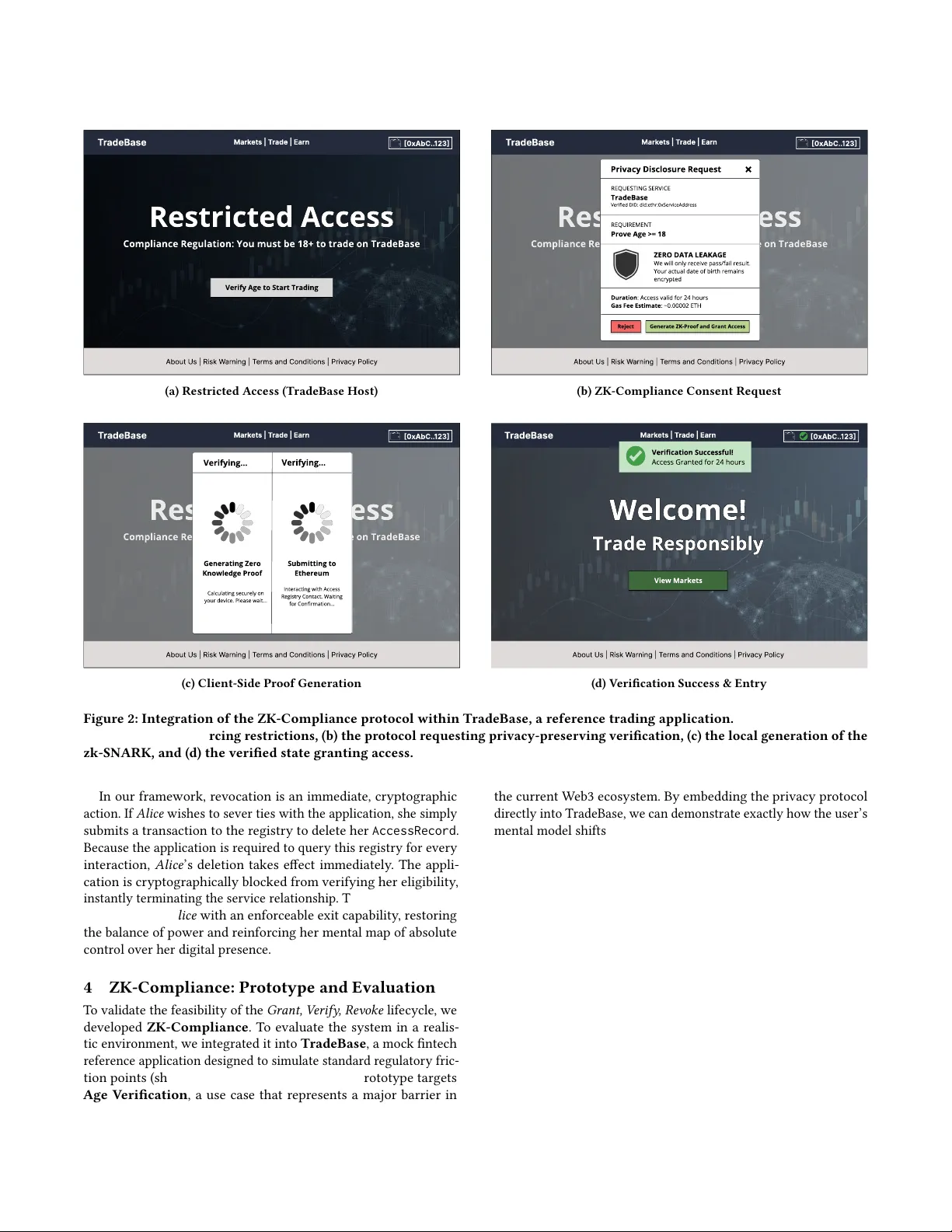
Grant, V erify , Rev oke: A User-Centric Paern for Blockchain Compliance Supriya Khadka George Mason University Fairfax, Virginia, USA skhadk@gmu.edu Sanchari Das George Mason University Fairfax, Virginia, USA sdas35@gmu.edu Abstract In decentralized web applications, users face an inher ent conict between public veriability and personal privacy . T o participate in regulated on-chain services, users must currently disclose sensi- tive identity documents to centralized intermediaries, permanently linking real-world identities to public transaction histories. This binary choice between total privacy loss or total exclusion strips users of agency and exposes them to p ersistent surveillance. In this work, we introduce a Selective Disclosure Framework designed to restore user sover eignty by decoupling eligibility verication from identity re velation. W e present ZK-Compliance , a prototype that leverages browser-based zero-knowledge proofs to shift the interaction model, enabling users to prove specic attributes (e .g., “I am over 18”) locally without r evealing the underlying data. W e implement a user-governed Grant, V erify , Rev oke life cycle that trans- forms the user’s mental model of compliance from a permanent data handover into a dynamic, r evocable authorization session. Our eval- uation shows that client-side proof generation takes under 200 𝑚𝑠 , enabling a seamless interactiv e experience on commodity hardware. This w ork pr ovides early evidence that regulatory compliance nee d not come at the cost of user privacy or autonomy . CCS Concepts • Human-centered computing → Systems and tools for in- teraction design ; • Se curity and privacy → Access control ; Usability in security and privacy . Ke ywords Blockchain, Privacy , Zero-Knowledge Proofs, User Agency , Self- Sovereign Identity A CM Reference Format: Supriya Khadka and Sanchari Das. 2026. Grant, V erify, Revoke: A User- Centric Pattern for Blo ckchain Compliance. In Extended Abstracts of the 2026 CHI Conference on Human Factors in Computing Systems (CHI EA ’26), A pril 13–17, 2026, Barcelona, Spain. ACM, New Y ork, N Y , USA, 6 pages. https://doi.org/10.1145/3772363.3798823 1 Introduction A fundamental tension exists between the W eb3 promise of self- sovereignty and the operational reality of radical transparency . While public blockchains enable trustless verication, the y force This work is licensed under a Creative Commons Attribution 4.0 International License . CHI EA ’26, Barcelona, Spain © 2026 Copyright held by the owner/author(s). ACM ISBN 979-8-4007-2281-3/2026/04 https://doi.org/10.1145/3772363.3798823 users into a hostile environment where every interaction is perma- nently recorded in a globally visible ledger [ 3 , 8 , 12 , 20 , 23 , 29 , 46 ]. As these platforms expand into regulated domains like nance and gaming, users face a structural conict between participation and privacy [ 35 , 48 ]. Currently , to satisfy identity-based controls such as Know Y our Customer (KYC) requirements [ 18 ], users are forced to rely on binary disclosure models that fail to capture the nuance of social trust [26, 42]. The core user experience challenge stems fr om the immutability of on-chain data. Because public blockchains cannot be redacted, users risk falling into a transparency trap where complying with a simple verication request ( e.g., pro ving age) permanently binds their real-world identity to their entire transaction histor y [ 3 , 10 , 34 ]. This linkage enables surveillance and proling that directly con- ict with data minimization principles [ 17 ]. Recent user-centered research argues that privacy must be instantiated as a controllable interaction mechanism rather than a static back-end policy [ 1 , 2 , 39 ]. Our framework adopts this stance, elevating sele ctive disclosure from a cryptographic possibility to a rst-class user capability . Currently , most applications address this tension by outsourc- ing verication to centralized interme diaries [ 4 , 32 ]. While this approach satises regulatory r e quirements, it reintroduces the very centralization risks that blockchain systems aim to avoid like data breaches and censorship [ 30 , 31 ]. Empirical studies conrm that this model generates signicant privacy discomfort , with users ex- pressing anxiety over unauthorized data retention and the lack of recourse against service denial [ 12 , 41 ]. This centralization eec- tively strips users of agency , r educing them to passive subjects of verication rather than active participants. T o address this, in this paper , we pr op ose a Selective Disclosure Framework that resolves the structural tension between compli- ance and user agency . W e argue that privacy should be an active capability of the user . The framework le verages Zero-Kno wledge Proofs (ZKPs), specically zk-SNARKs [ 6 ], to allow users to prove compliance predicates on-chain without revealing underlying iden- tity documents. Rather than treating identity as a monolithic ob- ject to be surrendered, our framework enforces ne-grained, user- controlled disclosure. W e instantiate this through ZK -Compliance , a prototype that enables privacy-preserving age verication via a client-side model. The system introduces an explicit Grant, V erify , Revoke lifecycle [ 26 ], reframing access authorization as a temp orary , revocable state rather than a permanent data transfer . This design restores user control while pr eserving the composability required by blockchain applications. CHI EA ’26, April 13–17, 2026, Barcelona, Spain Khadka and Das 2 The Agency Gap in W eb3 Identity Research on blockchain identity often bifurcates into transactional privacy protocols, decentralize d identity frameworks, and hardware- based controls [ 7 , 19 ]. W e analyze this landscape through the lens of Human-Computer Interaction (HCI), focusing on the cognitive load of compliance and the limitations of current trust models. Early privacy tools, such as Zerocash [ 38 ], focused on obfuscat- ing nancial metadata by hiding senders, recipients, and values. While eective for nancial condentiality , these “all-or-nothing” models fail to address identity-base d access control. From a user perspective, these tools lack granularity: a user cannot prove they are “ over 18” without either revealing their entire nancial history or nothing at all. This leaves users without the means to satisfy narrow eligibility predicates, for cing a choice between total trans- parency (compliance) and total opacity (non-compliance). Users require attribute-based mechanisms that separate eligibility veri- cation from nancial disclosure. Attempts to solve this through the Self-Sov ereign Identity (SSI) paradigm and W3C V eriable Credentials [ 45 ] have introduced sig- nicant interaction friction. SSI implementations often require users to navigate complex trust stacks involving Decentralized Identiers (DIDs) and specialized wallet software, creating a high barrier to entry [ 25 , 33 , 47 ]. This disconnect b etween the theoretical promise of self-sovereignty and the practical diculty of key management leads to “security fatigue , ” often causing users to r evert to custo dial solutions for convenience [ 40 ]. Critically , most SSI interactions act as “stateless events” , where once a user presents a credential, they typically lose control over how that data is stored or used [ 9 ]. This results in a one-way disclosure rather than a managed relationship. Finally , approaches using Trusted Exe cution Environments (TEEs) like Enigma [50] and Ekiden [11] attempt to bridge this gap by of- oading computation to secure hardware. How ever , these systems introduce a “black box” trust model, asking users to rely on opaque hardware guarantees ( e.g., Intel SGX) that they cannot audit or verify . This opacity complicates the user’s mental model of trust and introduces vulnerability to side-channel attacks [ 16 , 49 ]. In con- trast, our frame work minimizes reliance on external hardware trust, using lightweight cryptographic cir cuits that execute transpar ently within the user’s standard web bro wser . 3 System Design: A User-Centric Lifecycle W e propose a system architecture designed to align with the user’s mental model of temporar y permission rather than p ermanent sub- mission . T raditional compliance w orkows r ely on a custodial men- tal model: users hand over raw do cuments (like a passport) to a centralized server , losing all control over how that data is stored or when it is deleted [ 40 ]. Our architecture shifts this to a so vereign mental mo del. It coordinates three actors: User (Prover), Issuer (Trust Root), and V erier (Ser vice Provider ). The system enforces a strict separation between private attribute storage and public autho- rization state . T o operationalize this, we introduce a Grant, V erify , Revoke lifecycle. This model transforms the compliance process from a static data hand-o into a dynamic, re vocable session. The architecture is visualized in Figure 1. Phase 1: Grant (Sovereign Proving) . The life cycle begins with the user’s Identity V ault , a secure, client-side storage layer residing Alice’s Sovereign Domain (Client Side) Ethereum (Public State) Alice (User) Secure V ault Local ZK Prover (Browser Module) Ephemeral Proof (Anonymous T oken) V erifier Contract Access Registry TradeBase App 1. Grants Consent 2. Generates Proof (Locally) 3. Submits to Chain 4. Activates Session 5. V erify Status 6. Access Granted 7. Alice Triggers ’Kill Switch’ (Revoke) Figure 1: The Grant, V erify , Revoke lifecycle. (1-4) Grant: Al- ice actively generates a private proof locally to establish a session. (5-6) V erify: The application continuously checks this active, time-b ounded authorization. (7) Revoke: Alice retains a direct "Kill Switch, " allowing her to instantly sever the conne ction on-chain, bypassing the application entirely . entirely within the user’s br owser or device . Consider a standard usage scenario where Alice wants to access an age-restricted trading platform. In a traditional system, Alice would upload a photo of her ID card. In our system, the platform r e quests an eligibility check. The lo cal module retrieves her birthdate from her vault and executes the verication circuit lo cally . This phase is key for user agency as it shifts the moment of verication from a third-party server to the user’s own device. By generating the zero-knowledge proof locally , Alice acts as the sole custo dian of her data. The output is a cryptographic proof that asserts the truth of the pr edicate (e.g., “ Age > 18”) without revealing her actual birthdate. The network learns about the user without learning the user’s data. Phase 2: V erify (Ephemeral Authorization) . Alice then sub- mits this generated proof to the on-chain system. Up on successful verication, the registry creates an AccessRecord binding her ad- dress to the specic service. In a traditional custodial model, Alice ’s raw data would now reside indenitely on a corporate server , often without her visibility into its life cycle. In contrast, our system’s AccessRecord functions similarly to a transparent, time-bounded web session cookie stored on the blockchain. Crucially , when Alice generates the proof, the system enforces a strict expiry timestamp. From Alice ’s perspective, this transforms an open-ended data handover into a temporar y , predictable ses- sion. Even if she takes no further action, her permission naturally expires. This provides Alice with the p eace of mind that her au- thorization is ephemeral, eectively prev enting the accumulation of stale p ermissions that plague traditional identity systems. For developers, this abstracts cryptographic complexity into a simple logic check, ensuring they operate outside the scope of custodial data regulations like GDPR [17]. Phase 3: Revoke (The “Kill Switch”) . The most signicant de- parture from existing compliance workows is the introduction of a user-controlled “Kill Switch. ” If Alice decides to stop using a traditional service, her revocation mental model involves na vigat- ing complex settings menus or sending a formal deletion request to a support team, with no technical guarantee that her data will actually be purged. Grant, V erify , Revoke: A User-Centric Paern for Blockchain Compliance CHI EA ’26, April 13–17, 2026, Barcelona, Spain T r adeBase [0xAbC.. 123] Mark et s | T r ade | Earn About Us | Risk W arning | T erms and Conditions | Priv acy P olicy Restricted Access Compliance Regulation: You must be 18+ to trade on TradeBase Verify Age to Start Trading (a) Restricte d Access (TradeBase Host) T r adeBase [0xAbC.. 123] Mark et s | T r ade | Earn About Us | Risk W arning | T erms and Conditions | Priv acy P olicy Restricted Access Compliance Regulation: You must be 18+ to trade on TradeBase Verify Age via zk-AgeGuard Privacy Disclosure Request REQUESTING SERVIC TradeBas Veried DID: did:ethr:0xServiceAddress REQUIREMEN Prove Age >= 18 Duration: Access valid for 24 hour Gas Fee Estimate: ~0.00002 ETH ZERO DATA LEAKAG W e w ill o n l y receive p ass / fail resul t . Y our ac t ual da t e of b ir t h re m ai n s e n cr ypt ed Re j ect Generate ZK -Proof and Grant Access (b) ZK-Compliance Consent Request T r adeBase [0xAbC.. 123] Mark et s | T r ade | Earn About Us | Risk W arning | T erms and Conditions | Priv acy P olicy Restricted Access Compliance Regulation: You must be 18+ to trade on TradeBase Verify Age via zk-AgeGuard Verifying... Generating Zero Knowledge Proof Calculating securely on your device. Please wait... Interacting with Access Registry Contact. Waiting for Conrmation... Submitting to Ethereum Verifying... (c) Client-Side Proof Generation T r adeBase [0xAbC.. 123] Mark et s | T r ade | Earn About Us | Risk W arning | T erms and Conditions | Priv acy P olicy Welcome! Trade Responsibly View Markets Verication Successful Access Granted for 24 hours (d) V erication Success & Entr y Figure 2: Integration of the ZK-Compliance protocol within TradeBase, a reference trading application. The sequence shows: (a) the host app enforcing restrictions, ( b) the protocol requesting privacy-preser ving verication, (c) the lo cal generation of the zk-SNARK, and (d) the veried state granting access. In our framework, revocation is an immediate, cr yptographic action. If Alice wishes to sever ties with the application, she simply submits a transaction to the r egistry to delete her AccessRecord . Because the application is required to quer y this registry for every interaction, Alice ’s deletion takes eect immediately . The appli- cation is cryptographically blocked from verifying her eligibility , instantly terminating the service relationship. This tangible mecha- nism provides Alice with an enforceable exit capability , restoring the balance of power and r einforcing her mental map of absolute control over her digital pr esence. 4 ZK -Compliance: Prototype and Evaluation T o validate the feasibility of the Grant, V erify , Revoke lifecycle, we developed ZK-Compliance . T o evaluate the system in a realis- tic environment, we integrated it into T radeBase , a mock nte ch reference application designed to simulate standar d regulator y fric- tion points (shown in Figure 2). This full-stack prototype targets Age V erication , a use case that represents a major barrier in the current W eb3 ecosystem. By embe dding the privacy protocol directly into TradeBase, we can demonstrate exactly how the user’s mental model shifts when they are given cryptographic agency at a compliance gate. 4.1 Implementation: Architecture and Usability T o avoid reliance on trusted backends and to reduce user friction, we utilize bro wser local storage as a non-custodial Identity V ault. W e used Circom [ 5 ] and SnarkJS [ 24 ] to handle witness generation and proving entirely within the client’s JavaScript environment. From an interaction perspective, this means the user ne ver has to leave the application context or be redirected to a third-party portal to authenticate. This standardized tooling ensures the system is portable across any modern web browser without r equiring users to install specialize d wallet extensions or understand complex key management. The cryptographic heavy lifting is abstracted entir ely behind a familiar loading screen. A major usability challenge in CHI EA ’26, April 13–17, 2026, Barcelona, Spain Khadka and Das privacy systems is protecting simple data (like a birth year ) with- out burdening the user with e xtra steps [ 13 – 15 , 27 , 36 , 37 , 43 ]. T o protect low-entropy attributes from brute-for ce guessing, the sys- tem mathematically binds a local, high-entropy secr et to the data before generating the proof. Because this secret is generated and stored automatically within the local vault, the user is never asked to manage, memorize, or input it. This prevents attackers from reverse-engineering the attribute without physically compromising the user’s device [ 28 , 44 ], ensuring strong privacy guarantees are delivered through a frictionless, single-click interface. 4.2 Evaluation: Interaction Latency and Economic Feasibility For privacy to ols to achieve widespread adoption, latency is a crucial factor; high friction drives users toward insecure alternativ es. Prior work establishes that W eb3 usability hinges on the user’s ability to exercise eective control despite technical complexity [ 21 , 22 ]. Consequently , we prioritize d interaction latency (the delay between a user’s intent to prove eligibility and the cryptographic execution) as a primary design constraint. W e evaluated the system on standard consumer-grade hardware to ensure accessibility . The local circuit achieves client-side proof generation in under 200 ms . This result is signicant as it sho ws that cr yptographic privacy does not r e quire a trade-o with responsiveness. The delay is imp erceptible, allowing these privacy checks to b e integrated seamlessly into standar d login ows without degrading the user experience. Beyond performance, we analyzed on-chain verication costs to assess economic accessibility , as high fees can act as an exclusionary barrier . On the Ethereum Mainnet, this resulted in a prohibitiv e cost of approximately $15 at standard gas prices (using a representative gas price of 20 gwei and ETH ≈ $3 , 000 under typical network conditions). Howev er , based on current fee structures for Layer 2 scaling solutions (e.g., Optimism or Arbitrum), w e estimate that the cost for the same verication workload would drop to under $0 . 50 . This projection suggests that while the interaction model is sound, deploying on scalable infrastructure is a necessary prerequisite for democratizing access to privacy-preserving compliance tools. 5 Discussion: Enforcing Digital Rights W e analyze the proposed frame work not merely as a security proto- col, but as a mechanism for enforcing digital rights. By emb edding privacy protections directly into the interaction layer , the system addresses the structural power imbalances inherent in curr ent com- pliance workows. Minimization and Surveillance Defense. Standard verica- tion workows often create a “honey pot” risk by p ermanently recording sensitive attributes in centralized databases or immutable ledgers. Our system counters this by enforcing strict data mini- mization . By recording only a bo olean verication signal and an opaque cryptographic proof, we decouple access rights from iden- tity . This eectively instantiates a technical “right to be forgotten” even within an immutable ledger environment. T o further protect users from brute-for ce attacks on low-entr opy attributes (e.g., birth years), we mandate the inclusion of a high-entropy randomSalt (128 bits) within the user’s local vault. This salt is mathematically bound to the attribute before proof generation, ensuring that pri- vate data cannot be reverse-engineered via enumeration. This ar- chitecture fundamentally shifts the attack surface: in a centralize d model, a single breach compromises all users, whereas in our client- side model, an attacker would need to compromise individual user devices one by one to access raw attributes. This distributes risk to the edges, making mass surveillance and bulk data exltration economically impractical. Sovereign Revocation. A dening feature of our framework is the implementation of a user-controlled “Kill Switch” . In centralized systems, revocation is typically an administrative request: the user asks a server to delete their data, but must trust the provider to honor that request and purge cached credentials. In our framework, revocation is a cryptographic state change. When a user inv okes the rev ocation function, their specic AccessRecord is deleted from the on-chain registry . Because the application logic requires this record to proceed, the revocation takes immediate eect. The application cannot verify the user anymore, regardless of its internal policy . This enforces a non-coop erative revocation model where the user do es not need the service’s permission to terminate the relationship. The deletion of the on-chain state cryptographically invalidates the verication path, ensuring that the user’s decision to exit is nal, immediately eective, and globally consistent. 6 Future W ork and Limitations The current prototype has some limitations to address before be- coming a production-ready system. Its reliance on self-attestation restricts its utility in regulated sectors requiring facts from trusted authorities. Additionally , the system presents a se curity vulnera- bility b ecause verication proofs on the public network are not strictly bound to specic user identities, creating risks of intercep- tion and reused consent. The prototype also dep ends on a developer- controlled initialization process, which contradicts the principles of decentralized consensus. Finally , the cognitive load of navigating the Grant, V erify , Re voke compliance model and the users’ ability to condently exercise re vocation remain empirically untested. T o resolve these constraints, future w ork will focus on integrat- ing high-assurance credentials. This will allow users to seamlessly import authority-issued facts into local privacy vaults while crypto- graphically stripping all Personally Identiable Information b efore ledger submission. W e will also harden the protocol to bind eligibil- ity proofs tightly to user identities, ensuring actions are unforgeable and consent cannot be hijacked. Furthermore , we plan to transition to a transpar ent, community-driven initialization process governed by the users. Finally , we will conduct comprehensive empirical stud- ies to validate the human-centered security design and measure how eectively users navigate their privacy boundaries. 7 Conclusion The tension between regulatory compliance and user privacy in W eb3 envir onments requires a fundamental shift in how systems handle digital identity . In this paper , w e presented a Selective Disclo- sure Framework that shifts identity verication from a permanent data handover into a dynamic, user-controlled lifecycle . By utiliz- ing client-side Zero-Kno wle dge Proofs through our ZK-Compliance Grant, V erify , Revoke: A User-Centric Paern for Blockchain Compliance CHI EA ’26, April 13–17, 2026, Barcelona, Spain prototype, we demonstrated that users can satisfy strict eligibil- ity requirements without surrendering their underlying data. The introduction of the Grant, V erify , Revoke model, specically the cryptographic “Kill Switch, ” successfully restores user agency and enforces the principle of data minimization at the architectural level. Hence, this framework sho ws that radical transparency and regula- tory compliance do not have to come at the cost of self-sovereignty . As blo ckchain applications continue to integrate with regulated sectors, empowering users with cryptographic control over their own disclosures will be essential for building a truly secure and equitable decentralized web. Acknowledgments W e acknowledge the Data Agency and Se curity (DAS) Lab at George Mason University , where this study was conducted. W e also thank Dr . Xiaokuan Zhang for initial feedback on this work. This r esearch was supp orted in part by an unrestricted gift from Google. The opinions expressed in this work are solely those of the authors. References [1] Andrick Adhikari, Sanchari Das, and Rinku Dewri. 2025. Natural Language Processing of Privacy Policies: A Survey . arXiv e-prints 0 (2025), 1–27 pages. [2] Andrick Adhikari, Sanchari Das, and Rinku Dewri. 2025. PolicyPulse: Precision Semantic Role Extraction for Enhanced Privacy Policy Compr ehension.. In NDSS . Internet Society , San Diego, CA, USA, 18 pages. [3] Neha Agarwal, Ethan Mackin, Faiza Tazi, Mayank Grover , Rutuja More, and Sanchari Das. 2025. Systematic Literature Review of Vulnerabilities and Defenses in VPNs, T or , and W eb Browsers. In International Conference on Information Systems Security . Springer , Springer, Indore , India, 357–375. [4] Rafael Belchior , André Vasconcelos, Sérgio Guerr eiro, and Miguel Correia. 2021. A survey on blockchain interoperability: Past, present, and future tr ends. Acm Computing Surveys (CSUR) 54, 8 (2021), 1–41. [5] Marta Bellés-Muñoz, Miguel Isabel, Jose Luis Muñoz- T apia, Alb ert Rubio, and Jordi Baylina. 2022. Circom: A circuit description language for building zero- knowledge applications. IEEE Transactions on Dependable and Secure Computing 20, 6 (2022), 4733–4751. [6] Eli Ben-Sasson, Alessandro Chiesa, Eran Tromer , and Madars Virza. 2014. Succinct { Non-Interactive } zero knowledge for a von neumann architecture. In 23rd USENIX Security Symposium (USENIX Security 14) . USENIX, San Diego, CA, USA, 781–796. [7] J. B. Bernabé, J. L. Cánovas, J. L. Hernández-Ramos, R. T . Mor eno, and A. Skarmeta. 2019. Privacy-Preserving Solutions for Blockchain: Review and Challenges. IEEE Access 7 (2019), 164908–164940. doi:10.1109/ACCESS.2019.2952172 [8] Nikita Borisov and Claudia Diaz (Eds.). 2021. Financial Cr yptography and Data Security . Lecture Notes in Computer Science , V ol. 12675. Springer, Berlin, Heidel- berg. [9] Carl Magnus Bruhner , David Hasselquist, and Niklas Carlsson. 2023. Bridging the privacy gap: Enhanced user consent mechanisms on the web. In Proc. NDSS W orkshop on Measurements, Attacks, and Defenses for the W eb (MAD-W eb@ NDSS) . Internet Society , San Diego, California, USA, 17 pages. [10] Vitalik Buterin. 2016. Privacy on the Blockchain. https://blog.ethereum.org/2016/ 01/15/privacy- on- the- blockchain. Ethereum Foundation Blog. [11] Raymond Cheng, Fan Zhang, Jernej Kos, W arren He, Nicholas Hynes, Noah Johnson, Ari Juels, Andrew Miller, and Dawn Song. 2019. Ekiden: A Platform for Condentiality-Preserving, Trustworthy , and Performant Smart Contracts. In 2019 IEEE European Symp osium on Security and Privacy (EuroS&;P) . IEEE, Stockholm, Sweden, 185–200. doi:10.1109/eurosp.2019.00023 [12] Mauro Conti, E Sandeep Kumar , Chhagan Lal, and Sushmita Ruj. 2018. A survey on security and privacy issues of bitcoin. IEEE communications sur veys & tutorials 20, 4 (2018), 3416–3452. [13] Sanchari Das. 2024. Design of se cure, privacy-focused, and accessible e-payment applications for older adults. In 2024 Conference on Building a Secure & Empowered Cyberspace (BuildSEC) . IEEE, IEEE, Delhi, India, 74–78. [14] Sanchari Das, DongInn Kim, Jacob Abbott, and L Jean Camp. 2024. User-centered phishing detection through personalized edge computing. In Companion Publica- tion of the 2024 Conference on Computer-Supported Cooperative Work and Social Computing . ACM, San José , Costa Rica, 283–287. [15] Sanchari Das, Kapil Madathil, Josiah Dykstra, Prashanth Rajivan, Shubha Setty , James T McElligott, Jiovanne Hughart, and Daniel V otipka. 2022. Privacy and security of telehealth services. In Proceedings of the Human Factors and Ergonomics Society A nnual Meeting , V ol. 66. SAGE Publications Sage CA: Los Angeles, CA, SAGE Publications, Atlanta, GA, USA, 1524–1528. [16] Sanchari Das, Bingxing W ang, Andrew Kim, and L Jean Camp. 2020. Mfa is a necessary chore!: Exploring user mental models of multi-factor authentication technologies. In Procee dings of the 53rd Hawaii International Conference on System Sciences . Hawaii International Conference on System Sciences (HICSS), Hawaii, USA, 5441–5450. [17] European Parliament and Council of the European Union. 2016. Regulation (EU) 2016/679 (General Data Protection Regulation). Ocial Journal of the European Union. Article 5(1)(c): Data minimisation. [18] Financial Action T ask Force (F ATF). 2019. Guidance for a Risk-Base d Approach to Virtual Assets and Virtual Asset Service Providers. https://w ww .fatf- ga.org/ en/publications/Fatfrecommendations/Guidance- rba- virtual- assets.html. Estab- lishes KYC/AML obligations for virtual asset service providers. [19] Rodrigo Dutra Garcia, Gowri Ramachandran, Kealan Dunnett, Raja Jurdak, Caetano Ranieri, Bhaskar Krishnamachari, and Jo Ueyama. 2024. A Survey of Blockchain-Based Privacy Applications: An Analysis of Consent Manage- ment and Self-Sovereign Identity Appr oaches. arXiv:2411.16404 [cs.CR] https: //arxiv .org/abs/2411.16404 [20] Mayank Grover and Sanchari Das. 2025. SoK: a systematic review of privacy and security in healthcare robotics. In International Conference on Social Robotics . Springer , Springer , Naples, Italy , 212–234. [21] Maggie Y ongqi Guan, Y aman Yu, and K anye Y e Wang. 2025. Using Aordance to Understand Usability of W eb3 Social Media. In Proce edings of the 2025 CHI Conference on Human Factors in Computing Systems . ACM, Y okohama, Japan, 1–19. [22] Naman Gupta, Kate W alsh, Sanchari Das, and Rahul Chatterjee. 2024. " I really just leaned on my community for support": Barriers, Challenges, and Coping Mechanisms Used by Survivors of { T echnology-Facilitated } Abuse to Seek Social Support. In 33rd USENIX Security Symposium (USENIX Se curity 24) . USENIX Association, Philadelphia, P A, USA, 4981–4998. [23] Y ue Huang, Marthie Grobler , Lauren S Ferro , Georgia Psaroulis, Sanchari Das, Jing W ei, and Helge Janicke. 2025. Systemization of Knowledge (SoK): Goals, coverage, and evaluation in cybersecurity and privacy games. In Proceedings of the 2025 CHI Conference on Human Factors in Computing Systems . Association for Computing Machinery , Y okohama, Japan, 1–27. [24] iden3. 2025. snarkjs: zkSNARK implementation in JavaScript & W ASM. https: //github.com/iden3/snarkjs. Accessed: 2025-12-16. [25] Georgy Ishmaev . 2021. Sovereignty , Privacy , and Ethics in Blockchain-Based Identity Management Systems. Ethics and Information T echnology 23, 3 (2021), 239–252. doi:10.1007/s10676- 020- 09563- x [26] Supriya Khadka, Dhiman Goswami, and Sanchari Das. 2026. Poster: Privacy- Preserving Compliance Checks on Ethereum via Selective Disclosure. arXiv preprint arXiv:2602.18539 1 (2026), 3 pages. [27] Urvashi Kishnani, Isabella Cardenas, Jailene Castillo, Rosalyn Conry, Lukas Rodwin, Rika Ruiz, Matthew Walther , and Sanchari Das. 2024. T owards perceived security , perceived privacy, and the universal design of e-payment applications. arXiv preprint arXiv:2407.05446 1 (2024), 6 pages. [28] Urvashi Kishnani and Sanchari Das. 2025. Security and Privacy Assessment of US and Non-US Android E-Commerce Applications. In International Conference on Information Systems Security . Springer , Springer , Indore, Madhya Pradesh, India, 444–454. [29] Urvashi Kishnani, Srinidhi Madabhushi, and Sanchari Das. 2023. Blockchain in oil and gas supply chain: a literatur e review fr om user security and privacy perspective. In International Symposium on Human Aspects of Information Security and Assurance . Springer , Springer , Kent, United Kingdom, 296–309. [30] Urvashi Kishnani, Naheem Noah, Sanchari Das, and Rinku Dewri. 2022. Privacy and security evaluation of mobile payment applications through user-generated reviews. In Proceedings of the 21st Workshop on Privacy in the Ele ctronic So ciety . ACM, Los Angeles, CA, USA, 159–173. [31] Urvashi Kishnani, Naheem Noah, Sanchari Das, and Rinku Dewri. 2023. Assessing security , privacy , user interaction, and accessibility features in popular e-payment applications. In Proceedings of the 2023 European Symp osium on Usable Security . USENIX, Anaheim, CA, USA, 143–157. [32] Markus Klems, Jacob Eberhardt, Stefan T ai, Steen Härtlein, Simon Buchholz, and Ahmed Tidjani. 2017. Trustless intermediation in blockchain-based decentralized service marketplaces. In International Conference on Service-Oriented Computing . Springer , Springer , Malaga, Spain, 731–739. [33] Evan Krul, Hye-young Paik, Sushmita Ruj, and Salil S. Kanhere. 2024. SoK: Trusting Self-Sover eign Identity . Proceedings on Privacy Enhancing Technologies 2024, 3 (July 2024), 297–313. doi:10.56553/p opets- 2024- 0079 [34] Sarah Meiklejohn, Marjori Pomarole, Grant Jordan, Kirill Levchenko, Damon McCoy , Georey M V o elker , and Stefan Savage. 2013. A stful of bitcoins: characterizing payments among men with no names. In Proceedings of the 2013 conference on Internet measurement conference . ACM, Barcelona, Spain, 127–140. [35] Vinay Rishiwal, Udit Agarwal, Mano Yadav , Aziz Alotaibi, Preeti Yadav , and Sudeep Tanwar . 2024. Blockchain-secure gaming environments: A comprehensive survey . IEEE Access 12 (2024), 183466–183488. CHI EA ’26, April 13–17, 2026, Barcelona, Spain Khadka and Das [36] Suleiman Saka and Sanchari Das. 2024. Evaluating privacy measures in healthcare apps predominantly used by older adults. In 2024 conference on building a Se cure & Empowered Cyberspace (BuildSEC) . IEEE, IEEE, Delhi, India, 79–86. [37] Suleiman Saka and Sanchari Das. 2026. SoK: Reviewing T wo Decades of Security , Privacy , Accessibility , and Usability Studies on Internet of Things for Older Adults. In Proceedings of the 21st ACM Asia Conference on Computer and Communications Security (ASIA CCS) . ACM, Bangalore, India, 18 pages. doi:10.48550/arXiv.2512. 16394 [38] Eli Ben Sasson, Alessandro Chiesa, Christina Garman, Matthew Green, Ian Miers, Eran Tromer , and Madars Virza. 2014. Zerocash: De centralized anonymous payments from Bitcoin. In 2014 IEEE Symp osium on Security and Privacy . IEEE, IEEE, San Jose, California, USA, 459–474. doi:10.1109/SP.2014.36 [39] T anusree Sharma, Lin Kyi, Y ang W ang, and Asia J Biega. 2024. " I’m not con- vinced that they don’t collect more than is necessary": { User-Controlled } Data Minimization Design in Search Engines. In 33rd USENIX Security Symposium (USENIX Security 24) . USENIX, P hiladelphia, P A, USA, 2797–2812. [40] T anusree Sharma, Vivek C Nair, Henry Wang, Y ang Wang, and Dawn Song. 2024. “I Can’t Believe It’s Not Custodial!”: Usable T rustless Decentralized Key Management. In Procee dings of the 2024 CHI Conference on Human Factors in Computing Systems . ACM, Honolulu, Hawaii, USA, 1–16. [41] Janice Jianing Si, T anusree Sharma, and Kanye Y e W ang. 2024. Understanding user-perceived security risks and mitigation strategies in the web3 ecosystem. In Proceedings of the 2024 CHI Conference on Human Factors in Computing Systems . ACM, Honolulu, Hawaii, USA, 1–22. [42] T eck Ming Tan and Saila Saraniemi. 2023. Trust in blockchain-enabled exchanges: Future directions in blockchain marketing. Journal of the Academy of marketing Science 51, 4 (2023), 914–939. [43] Faiza T azi and Sanchari Das. 2024. Evaluating telehealth for women in mexico: Privacy , usability , and integration challenges in remote healthcare . Usability , and Integration Challenges in Remote Healthcare ( July 15, 2024) 1 (2024), 5 pages. [44] Otily T outsop, Sanchari Das, and Kevin K ornegay. 2021. Exploring the security issues in home-based Io T devices through denial of service attacks. In 2021 IEEE SmartW orld, Ubiquitous Intelligence & Computing, Advanced & Trusted Comput- ing, Scalable Computing & Communications, Internet of People and Smart City Innovation (SmartWorld/SCALCOM/UIC/A TC/IOP/SCI) . IEEE, IEEE, Atlanta, GA, USA, 407–415. [45] W orld Wide W eb Consortium (W3C). 2022. V eriable Credentials Data Model v1.1 . W3C Re commendation. W orld Wide W eb Consortium (W3C). https: //www.w3.org/TR/v c- data- model- 1.1/ [46] Kevin W erbach. 2018. Trust, but verify: Why the blockchain needs the law . Berkeley T echnology Law Journal 33, 2 (2018), 487–550. [47] Y aman Yu, T anusree Sharma, Sauvik Das, and Y ang W ang. 2024. "Don’t put all your eggs in one basket": How Cryptocurrency Users Choose and Secure Their W allets. In Proce edings of the 2024 CHI Conference on Human Factors in Computing Systems (Honolulu, HI, USA) (CHI ’24) . Association for Computing Machinery , New Y ork, NY, USA, Article 353, 17 pages. doi:10.1145/3613904.3642534 [48] Markos Zachariadis, Garrick Hileman, and Susan V Scott. 2019. Governance and control in distributed ledgers: Understanding the challenges facing blockchain technology in nancial services. Information and organization 29, 2 (2019), 105– 117. [49] Rui Zhang, Rui Xue, and Ling Liu. 2019. Security and privacy on blockchain. ACM Computing Surveys (CSUR) 52, 3 (2019), 1–34. doi:10.1145/3316481 [50] Guy Zyskind, Oz Nathan, and Alex Pentland. 2015. Enigma: Decentralized Computation Platform with Guaranteed Privacy . arXiv:1506.03471 [cs.CR] https: //arxiv .org/abs/1506.03471
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment