Enabling End-to-End APT Emulation in Industrial Environments: Design and Implementation of the SIMPLE-ICS Testbed
Research on Advanced Persistent Threats (APTs) in industrial environments requires experimental platforms that support realistic end-to-end attack emulation across converged enterprise IT, operational technology (OT), and Industrial Internet of Thing…
Authors: Yogha Restu Pramadi, Theodoros Spyridopoulos, Vijay Kumar
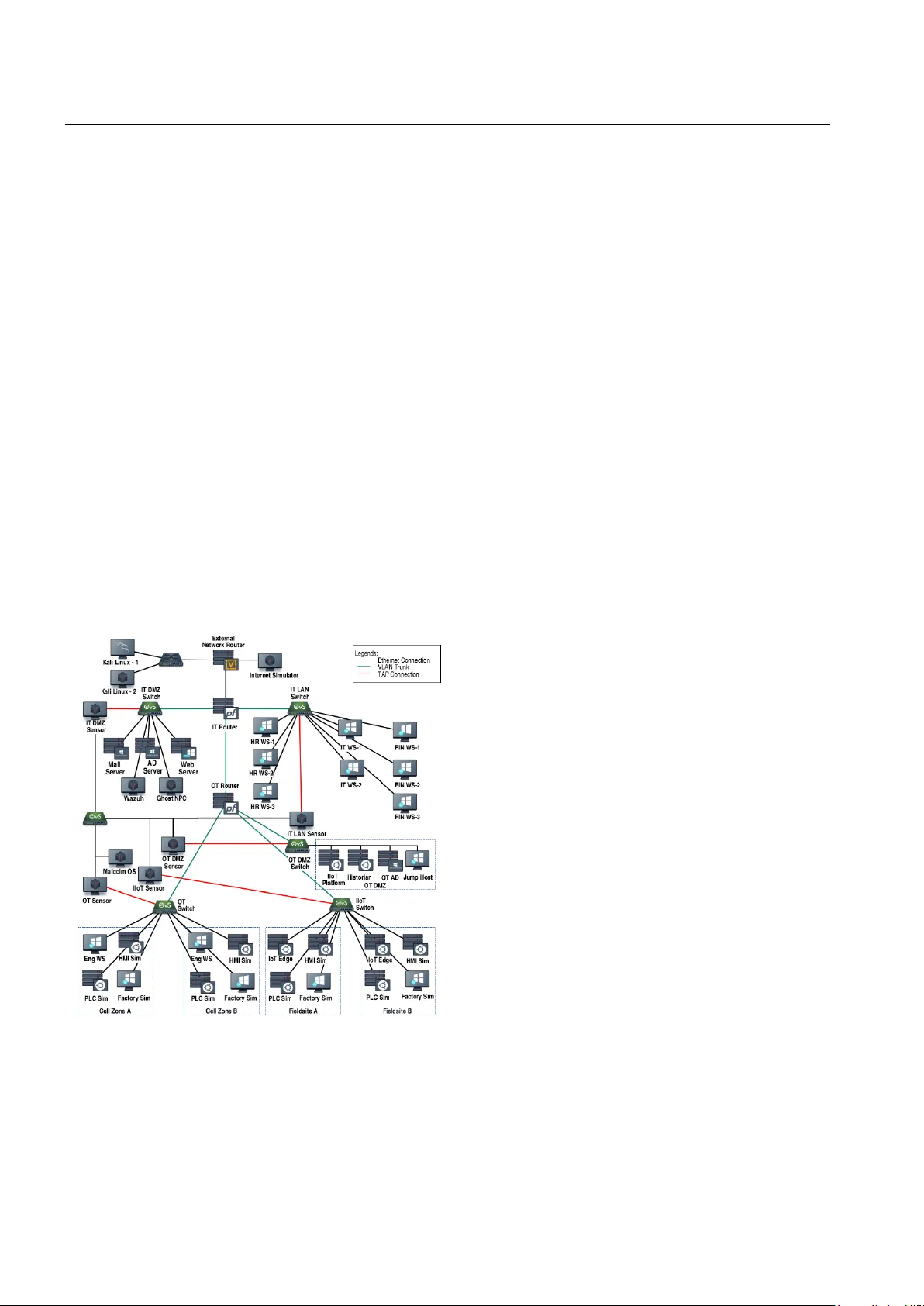
Enabling End-to-End APT Em ulation in Industrial En vironmen ts: Design and Implemen tation of the SIMPLE-ICS T estb ed Y ogha Restu Pramadi · Theo doros Sp yridop oulos · Vija y Kumar Abstract Research on Adv anced Persisten t Threats (APTs) in industrial environmen ts requires exp erimen- tal platforms that supp ort realistic end-to-end attac k em ulation across conv erged en terprise IT, op erational tec hnology (OT), and Industrial Internet of Things (I IoT) net works. How ever, existing industrial cyb ersecurit y test- b eds t ypically focus on isolated IT or OT domains or single-stage attacks, limiting their suitabilit y for study- ing multi-stage APT campaigns. This paper presen ts the design, implemen tation, and v alidation of SIMPLE- ICS, a virtualised industrial enterprise testbed that en- ables emulation of multi-stage APT campaigns across IT, OT, and I IoT environmen ts. The testb ed archi- tecture is based on the Purdue Enterprise Reference Arc hitecture, NIST SP 800-82, and IEC 62443 zoning principles and in tegrate s enterprise services, industrial con trol protocols, and digital t win–based process sim- ulation. A systematic metho dology inspired b y the V mo del is used to deriv e arc hitectural requirements, at- tac k scenarios, and v alidation criteria. An APT cam- paign designed to mimic the Blac kEnergy campaign is em ulated using MITRE A TT&CK tec hniques spanning initial en terprise compromise, creden tial abuse, lateral mo vemen t, OT netw ork infiltration, and process manip- ulation. The testb ed supp orts the sync hronised collec- tion of netw ork traffic, host-lev el logs, and op erational telemetry across all segments. The testb ed is v alidated on multi-stage attack trace observ ability , logging com- pleteness across IT, OT, and IIoT domains, and repeat- able execution of APT campaigns. The SIMPLE-ICS testb ed pro vides an exp erimen tal platform for studying end-to-end APT b eha viours in industrial enterprise net- Y.R. Pramadi · T. Spyridopoulos · V. Kumar School of Computer Science and Informatics Cardiff Universit y T el.: +44-29225-10176 E-mail: pramadiyr@cardiff.ac.uk w orks and for generating m ulti-source datasets to sup- p ort future researc h on campaign-level detection and correlation metho ds. Keyw ords Industrial Cyb ersecurit y · Critical In- frastructure Protection · Industrial Control Systems · Adv anced P ersistent Threats · Cyb ersecurit y T estb eds · IT/OT Conv ergence · Attac k Emulation 1 Introduction Industrial Control Systems (ICS) and Operational T ech- nology (OT) form the bac kb one of mo dern critical in- frastructure, supp orting essential services across sec- tors such as energy , manufacturing, water treatmen t, and transp ortation. These systems automate and opti- mise industrial processes to ensure operational contin u- it y , safety , and efficiency . The ongoing digitisation and in terconnectivity of ICS environmen ts enhance pro duc- tivit y and flexibilit y but also expand the attac k surface, increasing both the lik eliho o d and potential impact of cyb er inciden ts. Consequen tly , the resilience of these vital systems faces significant cyb ersecurit y c hallenges. Among the most sophisticated and p ersisten t threats to these en vironments are Adv anced P ersistent Threats (APTs). APTs are highly co ordinated systematic cam- paigns conducted by organised threat actors o ver ex- tended p eriods, typically with the aim of sab otage, es- pionage, or theft of intellectual property . Notable ICS- fo cused threat actors such as Sandw orm, Xenotime, and OilRig hav e demonstrated the capabilit y to cause ph ysical damage, disrupt critical operations, and com- promise safety systems through carefully orc hestrated m ulti-stage attacks. Unlike opp ortunistic cyb erattac ks, APTs are designed to ev ade conv entional security mech- anisms, maintaining stealth within a net work for pro- longed durations while gradually adv ancing tow ard strate- 2 Y ogha Restu Pramadi et al. gic ob jectives. Their m ulti-stage nature, p ersistence, and exploitation of zero-da y vulnerabilities mak e detec- tion particularly difficult. F urthermore, the increasing con vergence of Information T ec hnology (IT) and OT, accelerated by the Industrial Internet of Things (I IoT), allo ws an initial compromise in the IT domain to serv e as a pivot p oin t for lateral mov ement into the OT envi- ronmen t, posing direct risks to safety , pro cess integrit y , and av ailabilit y . OT systems differ fundamentally from IT systems, prioritising a v ailability , in tegrity , and op erational safet y o ver confiden tiality [1]. They often rely on legacy de- vices with outdated firm ware [2], lac k encryption [3], and use weak or ev en absen t authen tication mec hanisms [4]. Thes e characteristics, combined with extended sys- tem lifecycles and 24/7 op erational requirements, create an environmen t where traditional IT security measures are insufficien t or incompatible. T esting cyb ersecurit y mec hanisms or simulating complex APT campaigns on liv e industrial systems is impractical due to potential op erational disruptions, financial losses, and ph ysical hazards. T o ov ercome these constrain ts, realistic and recon- figurable testb eds hav e b ecome indisp ensable to ols for exploring, developing, and ev aluating cyb ersecurit y con- trols in ICS environmen ts without affecting live op er- ations [5, 6]. Suc h testb eds provide controlled settings for vulnerability analysis, taxonomy developmen t, and v alidation of no vel detection mec hanisms. How ever, a p ersisten t challenge lies in the scarcity of represen ta- tiv e datasets suitable for APT detection, particularly those capturing IT/OT/I IoT con v ergence and multi- domain correlations. Despite increasing research activ- it y in ICS cyb ersecurit y , publicly a v ailable datasets that supp ort the study of multi-stage APT campaigns in con verged IT-OT en vironments remain limited. Most existing datasets fo cus on isolated attack techniques, single net work domains, or short time windows, and often lac k the temp oral fidelit y , contextual detail, and co ordinated enterprise, net w ork, and operational tele- metry required to mo del stealth y , long-liv ed APT be- ha viour across heterogeneous industrial systems [7, 8]. As a result, researchers frequently rely on custom-built testb eds to generate exp erimen tal data tailored to sp e- cific threat mo dels and detection ob jectives. High-fidelity testb eds capable of pro ducing synchronised, cross-la y er telemetry across the full APT lifecycle are therefore critical for enabling rigorous analysis, repro ducible ex- p erimen tation, and systematic ev aluation of detection and defence mechanisms in con verged industrial en vi- ronmen ts. Despite this, few existing platforms enable the safe and reproducible study of APT campaigns spanning the full enterprise architecture from IT to OT and I IoT. Man y curren t testb eds fo cus on isolated domains, lack the arc hitectural complexit y of modern industrial net- w orks, or provide limited instrumen tation for cross-domain ev ent correlation. These constrain ts hinder the devel- opmen t and ev aluation of detection mec hanisms capa- ble of identifying the subtle, co ordinated activities that c haracterise adv anced threat actors as they mo ve lat- erally through segmented environmen ts. F urthermore, the proprietary nature and extensiv e customisation re- quiremen ts of most existing testbeds reduce their repro- ducibilit y and limit their adaptabilit y across differen t industrial sectors. This gap motiv ates the dev elopment of the proposed Sim ulated Industrial Multitier Platform for Lab- oratory Emulation of Industrial Con trol Systems (SIMPLE ICS) testbed, whic h enables systematic em- ulation of m ulti-stage APT campaigns and comprehen- siv e data collection in conv erged industrial environmen ts. The acronym SIMPLE reflects an aspirational design goal: while constructing a realistic industrial cyberse- curit y testb ed is inheren tly complex, this work aims to pro vide a repro ducible, mo difiable, and sector-agnostic platform that can b e adapted to diverse industrial con- texts with minimal effort. The SIMPLE ICS testb ed is designed as a mo del-based exp erimen tal environmen t to support the study of APT behaviours and the gen- eration of high-fidelity datasets for the ev aluation of detection and defence mechanisms in conv erged indus- trial netw orks. The main con tributions of this pap er are summarised as follows: – Integrated IT–OT–I IoT testb ed arc hitecture : W e present a sector-agnostic industrial cybersecu- rit y testb ed architecture that realistically mo dels mo dern enterprise en vironmen ts b y in tegrating IT, OT, and I IoT domains with lay ered netw ork seg- men tation, industrial protocols, and enterprise ser- vices aligned with the Purdue mo del. – End-to-end APT em ulation framew ork : W e in tro duce a reproducible methodology for em ulating m ulti-stage APT campaigns that tra verse en terprise IT, OT, and I IoT environmen ts, grounded in do c- umen ted threat actor behaviours (e.g., Sandw orm, Xenotime, OilRig) and MITRE A TT&CK for ICS. – Comprehensive, sync hronised data collection : W e establish a framework for sync hronised multi- mo dal data collection across net work, host, and pro- cess lay ers, forming a foundation for adv anced APT detection research aemulatednd providing a tem- plate for data set generation. – Systematic testbed dev elopmen t metho dol- ogy : W e adopt the V-Mo del design metho dology Design and Implementation of the SIMPLE ICS T estbed 3 to ensure traceabilit y from research requirements to implemen tation and v alidation, supp orting repro- ducibilit y and structured ev aluation of the prop osed testb ed. The remainder of this paper is structured as follo ws: Section 2 reviews related works and highlights existing gaps. Section 3 describes the adaptation of the V-Model metho dology to develop and v alidate the testbed. Sec- tion 4 discusses the progression of the APT attack in industrial en terprise netw orks and introduces a gener- alised APT scenario. Section 5 details the design and implemen tation of the SIMPLE ICS testb ed. Section 6 ev aluates its performance. Section 7 outlines limitations and future directions, and Section 8 concludes the pa- p er. 2 Related W orks The research landscap e surrounding industrial netw ork securit y against APT attacks has progressed signifi- can tly in recent years, largely driv en b y increasing threats and regulatory pressures. How ever, a crucial observ a- tion emerges: a dominant architectural trend -particularly in established testb eds- o v erwhelmingly focuses on repli- cating the OT or I IoT netw ork environmen t. While v aluable, this approach suffers a significant limitation: it largely neglects the significance of the IT infrastruc- ture in facilitating and enabling APT attacks within industrial settings. This section will review existing re- searc h, highligh ting the shortcomings of siloed ICS test- b eds and arguing for a more holistic, integrated ap- proac h. APTs in industrial en vironments are characterised b y multi-stage campaigns that tra v erse la yered netw ork arc hitectures while maintaining stealth during lateral mo vemen t. T raditional signature-based or single-stage anomaly detectors are insufficien t for identifying such threats, as they typically fo cus on isolated artefacts (e.g., anomalous flo ws or kno wn signatures) rather than correlated long-term b eha viours. [9] emphasised the need for detection metho ds that leverage multi-source corre- lation, temp oral context, and cyb er threat in telligence to capture campaign-level activities rather than discrete attac k even ts . A recen t literature review of APT detec- tion in ICS highlight challenges suc h as heterogeneous data sources, IT/OT in terconnectivity , and the absence of longitudinal datasets that represent the entire lifecy- cle of APT [10, 11]. T o address these challenges, researc hers ha ve em- plo yed m ultistage mo dels, such as the Cyber Kill Chain and MITRE A TT&CK, to correlate alerts across differ- en t phases of an attack. T echniques include probabilis- tic graphical mo dels [12, 13], sequence mining [14, 10], and graph-based or temp oral correlation frameworks [15]. These approaches enhance context-a wareness by linking seemingly disparate even ts into coherent attack traces. How ever, their effectiveness dep ends heavily on access to realistic, m ulti-stage, and well-labelled data- sets resources that remain scarce due to industrial con- fiden tiality and data sensitivity . Consequently , researc h increasingly relies on complex custom built testb eds to generate representativ e datasets [16]. Sev eral ICS cyb ersecurit y testb ed pro jects hav e de- v elop ed physical, virtual, or hybrid testb eds to supp ort the generation of data sets and the ev aluation of detec- tion tec hniques. Survey works ha ve catalogued such ef- forts [7], encompassing pro cess-con trol testb eds, smart grid sim ulators, w ater treatmen t facilities, hardw are-in- the-lo op (HIL), and digital twin platforms. How ever, the survey discussed that most of the testb eds fo cus on single attac ks (e.g., denial-of-service, command injec- tion) rather than the multi-stage, cross-domain nature of APT campaigns. Even when m ulti-phase attacks are included, they often remain confined within the OT do- main. In 2021, Al-Haw awreh and Sitnik o v a [17] presented Bro wn-I IoTb ed, a hybrid testb ed (using raspb erry pis and arduinos) fo cused on I IoT bro wnfield systems. The testb ed blends legacy system with mo dern I IoT and its architecture follows the three-tier architecture. The testb ed sho ws high fidelity as an I IoT testbed but it do es not follow an y cyb ersecurit y standard to provide baseline security . And the attack scenario implemen ted are non-APT cyber attac ks and assumes that the at- tac ker has gain a fo othold within the netw ork. Archi- tecturally , the testb ed is not designed to represent a full industrial enterprise netw ork with IT netw orks and common IT services. This mak es it not suitable to recre- ate certain attac ks suc h as lateral mov ement that ex- ploit A ctive Dir e ctory services that are common in APT attac ks. Ra vikumar et al. [18] presented a hybrid testb ed sp ecifically for Wide Area Monitoring, Protection and Con trol (W AMP A C), a net work commonly used in elec- trical pow er systems to control grid op erations. It used a real-time digital sim ulator (R TDS) hybridised with real industry-grade remote terminal units (R TU) and substation automation systems (SAS). The use of an R TDS makes the testb ed ac hieve a high degree of fi- delit y in process sim ulation and data while simulating a very large industrial net work, but at the same time these testb eds are not easy to recreate because of the high cost of these simulators, and sp ecial training is needed to use them. The cyb er attac ks implemented on the testbed co ver a specific scenario of attac ks targeting 4 Y ogha Restu Pramadi et al. p o wer grids, and not fo cused on adv anced multi-staged attac ks. Mubarak et al. [19], built a portable ph ysical testb ed designed to generate data sets for machine learning. The testb ed fo cused on the acquisition of real-time OT data and attacks that impact OT op erations, making its arc hitecture only limited to the OT netw ork. This also limits the attac ks that can be implemen ted, resulting in a dataset that only has representation of ICS hac king attac ks. Karc h et al. [20], presented CrossT est, a physical cyb ersecurit y-fo cused testb ed with miniaturised p o wer systems and a miniaturised man ufacturing process. The testb ed implemented a cross-la yer ICS testb ed that in- tegrates netw ork, host, and control-la yer monitoring to align with APT stages. Although this improv ed the ric hness of the data set, the testb ed remained limited to OT op erations, lacking the IT-to-OT breach vector. Kumar and Thing [21], taking inspiration from the Bro wn-I IoTb ed, presented a similar testb ed to detect APT attacks in the I IoT environmen t but with the ad- dition of using real PLC hardware as the controller. They presented three APT scenarios attacking I IoT with scenarios mimic king real-world APT attacks on industrial en vironment. Similarly , Ghiasv and et al. [22] also building up on Al-Ha w a wreh’s I IoT testbed, adopted the design for a pro v enance-based APT attac k detection approac h. The study implemen ted more than 20 APT attac k tec hniques. These testb ed also inheren t the short comings of the Brown-IIoTb ed. Simola et al. [23], dev elop ed a cyb erph ysical test- b ed to assess the effectiveness of SOCin critical infras- tructures. The pro ject w as designed with the fo cus on mobile technology such as 4G and WIFI in industrial settings and only fo cussing on the OT netw ork. The study briefly discusses the arra y of ICS centric cyber attac ks, but do es not discuss how it is implemented. Mikk elsplass and Jorgensen [24] introduced a phys- ical testb ed using a scaled-down factory mo del con- trolled b y a real PLC. Similarly to the previous w ork, the study in vestigates ho w effectiv e SOCs are in detect- ing cyb er attac ks in complex OT settings. The netw ork represen ts an ICS netw ork with an I IoT gatewa y with- out any representation of the IT netw ork and the other la yer of the I IoT arc hitecture which limits the scop e of attac ks. Lo et al. [25] presen ted a virtual testbed that utilises digital twin tec hnology (DT). The study used a fac- tory sim ulator in conjunction with an open-source PLC. The aim of the study is to generate time series oper- ational data for Deep Learning based detection. The study shows that DT can provide enough fidelit y to study the impacts of cyber attacks on the process lay er; nev ertheless, as with the other studies in this section, the scop e is limited on the OT netw ork. In summary , there remains a lack of repro ducible high-fidelit y testb eds that mo del the full Purdue en ter- prise architecture encompassing the IT, OT, and I IoT la yers. This limitation restricts adv ersary em ulation and hinders the study of end-to-end APT campaigns that tra verse en terprise IT to the operational domain and ul- timately impact ph ysical pro cesses. The ob jectiv es out- lined in Section 1 directly address these gaps. 3 Metho dology The developmen t of a cybersecurity testb ed for indus- trial net works is a complex undertaking that requires a metho dical and rigorous approac h. The credibility of an y researc h conducted on such a testb ed is in trinsically link ed to the credibilit y of the testbed itself, which in turn dep ends on the process used for its design and con- struction [26]. This section establishes the foundational principles for the testbed developmen t lifecycle, justi- fying the selection of metho dology used as the guiding framew ork. This research adopts the V-Mo del Design Metho d- ology [27], commonly used in system engineering pro- cesses and soft ware engineering [28, 29], to guide the de- v elopment of a testb ed for the detection and ev aluation of APTs in industrial en terprise net works. This model is characterised by a sequential developmen t pro cess in whic h each phase of sp ecification and decomp osition is mirrored by a corresponding phase of in tegration and v alidation. Figure 1 sho ws the mo del adapted for the study . Fig. 1: Prop osed V-Mo del Design Metho dology for cy- b ersecurit y testb ed developmen t Design and Implementation of the SIMPLE ICS T estbed 5 The left side of the ’V’, represen ting the decomp o- sition and sp ecification, mirrors the pro cess commonly used in the construction of ICS cyb ersecurit y testb eds [5]. It begins with the high-lev el Requiremen ts , whic h are analogous to the ov erarching researc h questions. Then these are decomposed in to a system Arc hitec- ture , which represents the high-level exp erimen tal de- sign. Finally , the Design phase specifies the concrete comp onen ts and configurations, defining the experimen- tal apparatus and pro cedures. The right side of the ’V’, representing in tegration and testing, mirrors the pro cess of exp erimen tal v eri- fication and hypotheses testing (v alidation). First, the T estb ed Use Case corresp onds to the defined testbed use cases that are deriv ed from the research gap that the research is trying to address . Next, the A ttack Scenario Analysis is based on the threat mo del or the threat scenario of real-world cyb erattac k scenar- ios, and the testbed architecture m ust be in line with the intended scenario it recreates. The last is the cy- b erattac k testing and data collection v alidation , where eac h important comp onen t of the designed test- b ed is tested for its functionalit y , sim ulating the attac k, testing data collection capability , and p erformance to ensure completeness and quality of the data. Finally , the tw o sides merge into the Implemen- tation phase. The testb ed is implemented, v alidated and verified by p erforming the APT attack simulation as sp ecified by the generalised APT scenario and ev al- uating the generated data. V alidating that the fully in- tegrated system, the testb ed, can successfully run the exp erimen ts needed to answer the initial research ques- tions. This parallel structure establishes clear and log- ical verification and traceabilit y from the highest-level researc h ob jectiv e down to the low est-level comp onen t test and back up to the final v alidation. The usage of the metho dology in this study is as follo ws: – The Requirement - T estb ed Use Case Phase: The methodology begins with the identification of the testb ed requirements based on a gap analysis of existing testbeds review of industrial APT inciden ts in the literature as discussed in 2. – The Architecture - APT Scenario Simulation Phase: The requirements and cyb ersecurit y stan- dards (e.g., NIST SP 800-82, IEC 62443) are then used to determine the architecture and v alidated b y realistic use cases form ulated that reflect known APT campaigns. Three attack scenarios are a gen- eralisation of prominent APT attacks in the indus- trial en vironment. These scenarios span the en tire APT lifecycle, from initial access to impact, and are mapp ed to MITRE A TT&CK tec hniques to guide the functionality of the testbed and the log require- men ts. The architecture can b e found in Subsection 5.1, and the attac k scenarios are detailed in Subsec- tion 4.1. – The Design - APT Attac ks & Corresp ond- ing Data Phase: The design sp ecifies comp onen t in terconnections, logging configurations, and attack sim ulation mec hanisms are discussed in Section 5.2. Both IT and OT-sp ecific telemetry sources are in- strumen ted, including PCAPs, OT proto col logs, Windo ws even t logs, and endpoint activity . The tele- metry are then mapped to their corresp onding at- tac ks and discussed in Section 4.2. – The Implemen tation Phase: The final implemen- tation is implemen ted in a virtualized environmen t using open source platforms suc h as OpenPLC, F ac- tory I/O, No de-RED, VirtualBo x, and Pro xmo x (de- tailed in Section 5.3. Infrastructure-as-Co de to ols (e.g. Ansible and T erraform) are used to enable re- pro ducible deplo ymen t. The testb ed supp orts the full execution of eac h selected APT scenario, pro- viding comprehensiv e logs and facilitating live moni- toring during red-team sim ulations. Implemen tation is v alidated through the phased execution of APT campaigns, confirming that eac h attack technique pro duces observ able evidence in the data la yer (Sec- tion 6). This systematic methodology ensures that the SIMPLE ICS testb ed is developed with rigour, traceability , and repro ducibilit y . 4 Developing the APT Threat Mo del This section aims to discuss the design of a detailed APT attack threat mo delling in the con text of indus- trial cyb er security studies. This is a crucial step in the study as it serves as the basis of the testb ed design and drives the v alidation and verification steps of the metho dology describ ed in Section 3. T o help achiev e this, the study devised an approach aimed at creating detailed APT attac k scenarios sp ecifically for cyb erse- curit y testb eds. The approac h is illustrated in Figure 2. The approach and its usage in this study is de- scrib ed in detail b elo w. Step 1: Scenario Analysis . The threat model sce- nario is developed b y taking in to accoun t t wo things, the research goals and the adversary ob jectives that the research is trying to inv estigate. The research goals mandate the main ob jective of the study , for exam- ple, ”generating a dataset of APT attacks with lateral mo vemen t from IT to OT”. This goal defines the t yp e 6 Y ogha Restu Pramadi et al. Fig. 2: The Approac h to Design a Detailed APT Sce- nario for Cyb ersecurit y T estb ed of adv ersary with a threat mo del that fits the study b est. F rom this example, the study fo cusses on detect- ing APT attac ks with later al movements , then c ho osing to mimic the Sandworm APT group for a scenario is a logical choice. F rom this, a high-level scenario threat mo del is dev elop ed, as can b e observ ed in Subsection 4.1 . Step 2: Scenario Detail Plan . In this step, the scenario from the first step is brok en do wn in to detailed attac k phases and mapp ed to MITRE A TT&CK TTPs. Once the detailed TTP map is finished, the telemetry that resp onds to the attac k is mapp ed to help the pro- cess of collecting data for each attac k. This step is used to guide Subsection 4.2. Step 3: A ttac k Flow Design . This step is crucial in relation to the implementation of the attack. Each attac k in the scenario has an execution flow to follo w in order for an attack to succeed. And the result of each attac k has an impact that ma y concern an y safet y issues to which the testb ed must adhere. This step creates conditional logic of the attack and the decisions that to ensure realism, fidelity , and the safety of the execution of the performed APT attac k scenario. Subsection 5.5 describ es this step in detail. This section is structured as follo ws. In the first sec- tion, the use case of the testb ed is deriv ed from the re- searc h gap; The second subsection describes the APT threat model in an industrial con text; And the last sub- section breaks down the APT scenario into a detailed attac k mapp ed to its. 4.1 A Generalised APT Scenario T argeting ICS T o help verify the second step in the v-mo del metho d- ology that we addopt, 3 The testb ed requirement requires it to support the sim ulation of APT attacks in industrial environmen ts. This means that the APT scenarios that it needs to sim ulate are APT campaigns that specifically target in- dustrial netw orks (e.g., ICS or IIoT) infrastructure as their primary ob jective, not just a minor component of broader IT attacks against organisations with industrial net works. This subsection discusses studies and rep orts on prominen t APT campaign analysis and presents a distillation of these APT campaigns in to a generalised APT scenario. A generalised APT scenario provides a rep eatable, explainable threat mo del to guide the testbed design: it defines the adv ersary goals, the stages or phases of the campaign, the detailed scenario of chain of attacks, and the stages where detection and mitigation con trols m ust op erate. T o effectiv ely describ e an APT scenario, it is cru- cial to break it down into sequential phases that il- lustrate the progression of an attack. APTs targeting industrial enterprise netw orks follow a structured at- tac k path, t ypically encompassing reconnaissance, ini- tial compromise, p ersistence, privilege escalation, lat- eral mo vemen t, command and control (C2), and final ob jectives such as op erational disruption or data ex- filtration. F ramew orks like the ICS Cyb er Kill Chain [30], the MITRE Attak for ICS [31] and the Mandian t A ttack Lifecycle [32] pro vide a structured approach to studying these threats. This study presen ts a generalised APT scenario (de- picted in Figure 3) that represents prominent APT cam- paigns. The scenarios are developed by analysing stud- ies such as [33, 32, 34, 35, 36]. The scenario presen ts an APT campaign with the mission of compromising a crit- ical pro cess in IT and OT. Inspired b y the 2016 and 2022 attacks on the Ukraine’s pow er grid by Sandw orm (APT 28). The scenario starts with a spear-phishing campaign for it’s initial access phase, then the attack tra verses the IT netw ork to the OT netw ork by using harv ested credential to access the jump host in the OT DMZ. In the OT DMZ the attack identifies industrial equipmen t in the OT and I IoT net work, and conducted an attac k causing disruption to a critical industrial pro- cess. A detailed pro cess of this scenario is shown in Fig- ure 3. Design and Implementation of the SIMPLE ICS T estbed 7 The APT scenario is dev elop ed to sim ulate an ad- v anced attack that targets mo dern OT net works that include IIoT netw orks. Although there is no single pub- licly documented APT campaign that demonstrated suc h an attack, this scenario is syn thesised from studies suc h as [21] and [22]. Phase 1 Initial Access APT operatives used the enterprise website to create a phising list They craft a spear-phising email impersonating a trusted industry partner An Employee opens a malicious attachment, unknowingly installing a backdoor Phase 2 IT Network Reconnaissance The backdoor established communication with the C2 Server Attacker use living-off-the-land techniques to avoid detection They map the network, identifying key servers and pivot points to OT Phase 3 Credential Harvesting Attacker deploy mimikatz to extract cached credentials They compromise the Domain Controller, to gain access to Active Directory Attacker identifies and harvest accounts with access to both IT and OT networks Phase 4 Lateral Movement to OT Attackers identify an Engineering WS (Jump Host) located in the Industrial DMZ Using the harvested credential, attackers access the Engineering WS The group installed additional tools on this pivotal machine Phase 5 OT and IIoT Network Infiltration From the Industrial DMZ, attackers scan the OT network, discovering that there is an II0T Network behind the OT DMZ Attackers identify SCADA servers, PLCs and HMIs controlling critical process in the OT network Attacker deploy a customised malware to disrupt the critical process Phase 6 Preparation for Attack The Malware established persistence in the OT and IIoT network Attackers map industrial process and identify critical control points They test small, reversible changes to verify their control Phase 7 Attack Execution On D Day , the attack is launched it sends malicous commands to controllers, causing malicious impact control systems are manually overridden, locking out engineers APT Attack Scenario: Attack Traversing IT to OT and IIoT Attackers identify an IIoT Gateway in the network and found the ssh certificate to login to the network at the Jump Host Fig. 3: A Generalisation of APT attac k scenarios in industrial environmen ts. 4.2 F rom Scenario to TTPs The APT attack scenarios from the previous section pro vides a high abstraction of series of correlated at- tac ks. T o mak e it actionable, complex attac k c hains in a scenario are translated in to discrete tactics, techniques, and procedures (TTP) [37]. MITRE A TT&CK [31] pro- vides a common vocabulary and taxonomy to describ e adv ersary behaviours to facilitate a clearer description of the attack in v olv ed. This subsection maps the gen- eralised attack campaign from the previous step of the study to TTPs, providing a clear blueprint for the de- sign phase of the testb ed to follo w. The pro cess of mapping the generalised scenarios in to the MITRE A TT&CK TTP framew ork is as fol- lo ws: 1. Understand the Scop e of the A ttack: The MITRE A TT&CK differentiate b et ween IT enterprise, ICS, Mobile, and Cloud matrices. F or IT/OT scenarios, the enterprise and ICS matrices are used. The sce- narios are reviewed and the attac k phase is defined within the IT and OT scop e. 2. Deconstruct the Scenario in to Atomic Attac ks: The phases of attac ks are then brok en do wn into steps of attac ks (tactics), and the the steps are detailed into the smallest action or ev en ts p ossible (techniques and subtechniques). The pro duced discrete attac k m ust follow the chronological flow and how one ac- tion enables the next. 3. Analyse Eac h Action Against A TT&CK T actics: The next step is to identify the corresp onding technique and sub-technique in the matrices for each discrete action and co dify them accordingly . 4. Refine and Organise the Mapping: The last step is to organise the iden tified TTPs according to the at- tac k phases describ ed in the scenario. The mapp ed scenarios must align with the progression of the at- tac k. T able 1 presents the mapping of the first scenario. The first column describ es the phase of the attack, the second column describ es the tactics, and the gran ular attac k tec hniques and subtechniques described in the last column. Note that in phase 1 to phase 5 the tactics and techniques use the enterprise matrices, and from phase 6 onw ards it uses the ICS matrices. The first five phases detail the atomic steps that the adv ersaries to ok in compromising the IT en terprise net work and mak e their wa y to the edge of the OT net w ork, and the next three phases detail the adv ersaries’ activit y in the OT net work up to the execution of the final ob jective. 5 T estb ed Arc hitecture, Design and Implemen tation This section discusses the arc hitecture, design, and im- plemen tation of the prop osed testb ed. 5.1 Architecture and Design of the T estbed In Section 2 w e ha v e discussed the gaps in ICS testb eds for APT research and dev elop ed a set of requirements to guide the architecture developmen t. T o fulfil the re- quiremen t of represen ting a mo dern industrial enter- prise net work that includes IT net work, OT net work, 8 Y ogha Restu Pramadi et al. T able 1: Detailed APT Scenario Phase TTP Mapping Asset T arget T elemetry Phase 1: Initial Access Initial Access (T A0001) – Sp earphishing Attac hment (T1566.001) IT user workstation, email gatewa y NIDS: Malware T ransfer, HIDS/EDR: process cre- ation, firewall logs Phase 2: IT Net work Re- connaissance Command & Control (T A0011) – Standard Application Lay er Proto col (T1071.001) Discov ery (T A0007) – System Information Disco very (T1082) – Network Service Discov ery (T1046) Defense Evasion (T A0005) – Impair Defenses (T1562) Active Directory servers, IT user workstation NIDS, Network Flow: C2, HIDS/EDR: sysmon even t logs, SIEM correlation Phase 3: Creden tial Har- vesting Credential Access (T A0006) – OS Credential Dumping (T1003) —- LSASS Memory (T1003.001) Discov ery (T A0007) – Account Discovery (T1087) —- Domain Account (T1087.002) – Network Share Discov ery (T1135) Active Directory servers, IT user workstation HIDS/EDR: Windows secu- rity logs (4624, 4625, 4672), LSASS memory access logs. Phase 4: Lateral Mo ve- ment to OT Lateral Movemen t (T A0008) – Remote Services (T1021) —- SMB Admin Shares (T1021.002) Execution (T A0002) – V alid Accoun ts (T1078) Jump servers, engineering workstations, file shares, OT gatewa y NIDS: netw ork scan,Authentication logs, SMB and RDP connection attempts, file transfer logs, Sysmon (Even t 3, 10), net- work flow Phase 5: OT and I IoT Netw ork Infiltration Discov ery (T A0008 ICS) – Device Discov ery (T0808) (ICS) – Pro cess Discov ery (T0813) (ICS) Execution (T A0007 ICS) – Command-Line Interface (T0807) (ICS) Persistence (T A0006 ICS) – Bo ot or Logon Autostart Execution (T1547) PLCs, HMIs, I IoT gateways, engineering stations PLC communication logs, Modbus/TCP network cap- tures, HMI command logs, OPC-UA telemetry , host startup logs Phase 6: Preparation for Attac k Collection (T A0100) – Monitor Pro cess State (T0801) Inhibit Resp onse F unction (T A0011 ICS) – Change Credential (T0892 ICS) SCADA servers, PLCs, process controllers, op erator HMIs NIDS:ICS anomaly detection logs, Operational logs, Pro- cess historian data Phase 7: A ttack Execu- tion Impair Pro cess Control (T A0009 ICS) – Mo dify Parameter (T0836 ICS) Impact (T A0010 ICS) – Manipulation of View (T0832 ICS) – Manipulation of Con trol (T0831 ICS) Field con trollers, actuators, sensors, safety systems PLC change logs, pro cess control commands, historian integrit y data, ICS alarms, safety PLC telemetry and I IoT netw ork, w e used the Purdue Enterprise Ref- erence Architecture (PERA) in conjunction with the Industrial In ternet Reference Architecture (I IRA) as a guide. T o provide baseline security , the IEC 64223 rec- ommendation is follo wed to implement security zones and no direct IT to OT comm unication is f ollow ed. Fig- ure 4. PERA pro vides a robust foundation due to the in- heren t la y ered approach, fo cusses on industrial pro cesses, and established applicabilit y across diverse industrial sectors [39, 40]. It is built around a six-lev el hierarc hical mo del, each representing increasing abstraction from the physical plant flo or to the enterprise level. Lev el s 0-1 (Physical Pro cess) represent the actual equip- men t, sensor, actuators, and controllers on the factory flo or. Lev el 2-3 (Control and Op erations) is where the supervisory con trol and data acquisition systems re- side, managing the physical pro cess underneath them. Lev els 4-5 (Business/En terprise) represent the IT en vironment in whic h the business applications and the corp orate net work reside. F or the IIoT portion of the design, I IRA provides a framework that allows in terop erabilit y betw een v ar- ious technologies in the industrial domain [17]. I IoT is characterised by a wide array of devices, proto cols, and platforms from differen t digital industrial genera- tions and vendors. The I IRA enables the modelling of the complex ecosystem b y utilising a lay ered abstrac- tion arc hitecture that are tailored to serv e sp ecific needs of industrial application. The framework is also data- cen tric with emphasis on data managemen t and analyt- ics, and it encourages the use of op en standards (e.g., MQTT, OPC UA, AMQP) for communication and data exc hange betw een lay ers. This allows for cyb ersecurit y Design and Implementation of the SIMPLE ICS T estbed 9 Purdue IEC 62443 IIC/ IIRA Enterprise DMZ Business Planning DMZ Operations/Control Controller Network Field I/O Enterprise DMZ DMZ Enterprise T ier DMZ Platform T ier Edge T ier Control Center Conduit BPCS SIS Conduit Conduit Conduit Fig. 4: Industrial Netw ork Architectures According to [38] exp erimen tation fo cused on data integrit y and pro cess- based anomaly detection. The testb ed design follows this framework by adopting the three-tier mo del. – I IoT Edge Tier: The edge tier represents the core OT environmen t devices and systems that handle the physical pro cess and the systems that trans- late and comm unicate data and con trol with the tier ab o ve it. – I IoT Platform Tier: This tier acts as a data ag- gregator, data storage, and data and con trol rela y b et ween the edge lay er and the en terprise lay er. – Enterprise Tier: The en terprise level is the la yer that consumes the op erational data and presents it to the business stak eholders to aid in monitor- ing and decision making. This tier can also provide direct control to certain physical devices enabling smart pro cessing control and remote maintenance. With the use of PERA and I IRA as a reference for the testb ed arc hitecture, a realistic representation of a contemporary industrial enterprise netw ork can b e ac hieved. NIST 800-82 and IEC 64223 also con tribute to the design b y providing baseline security measures and securit y data monitoring p oin ts to capture multimodal and high-fidelity security data. 5.1.1 Industrial Pr o c ess Design Ph ysical OT devices and ph ysical industrial processes on testb eds are desirable for their high fidelity , but of- ten create a barrier for the researcher to implement a testb ed for cyb er security researc h. F or certain re- searc h such as anomaly detection based on op erational data, using high-fidelity data from real physical devices and physical processes is the b est approach. This study will focus more on how APT attacks mov e and oper- ate within an industrial en terprise net work and create a defence mec hanism as early as possible. This do es not necessitate the need for a high-fidelity source of physi- cal process data. How ever, abstract mo dels or simplified represen tations of OT may lead to ov ersimplification. Ov ersimplification can cause the missing of critical data due to the lack of realistic interactions and interdepen- dencies. The integration of Digital Twin (DT) technology in to cyb ersecurit y testb eds has emerged as a transfor- mativ e approac h to mo delling and simulating complex cyb erattac k scenarios in virtual environmen ts. By cre- ating high-fidelit y virtual replicas of physical systems, DTs enable organisations to test and analyse cyb erse- curit y threats without risking real-w orld infrastructure. Digital Twins offer sev eral adv antages when in te- grated into cyb ersecurit y testb eds: – High-Fidelity Virtual Mo dels: DTs create detailed virtual replicas of physical systems, allowing for ac- curate sim ulations of cyb erattac k scenarios. F or ex- ample, in smart cities, DTs can mo del critical ur- ban infrastructure to simulate complex attacks [41]. Similarly , in industrial systems, DTs can replicate the b eha viour of industrial control systems (ICS) to ev aluate nov el cyb er-defence strategies [1]. – Cost-Effective and Safe T esting: Conducting cyb er- securit y tests in virtual environmen ts is safer and more economical than testing in real-world settings. F or example, in h ydro electric p o wer plan ts, DTs al- lo w for comprehensive securit y tests without risking op erational disruptions [42]. – Adv anced Threat Simulation: DTs enable the sim u- lation of v arious attac k scenarios, including sophisti- cated Adv anced P ersistent Threats (APTs). In smart man ufacturing, DTs can sim ulate the impact of v ar- ious threat scenarios to train deep learning models for threat detection [25]. With these b enefits, DT tec hnology is chosen as the approac h that the testb ed will use to represent the in- dustrial pro cess. 5.2 T estbed Design This section describes the design of the testb ed based on the arc hitectures discussed in the previous section. The design also m ust be able to accommodate the simu- lation of the APT scenarios defined in Section 4.1. This is done b y iden tifying the required netw ork segmen ts, services, and devices that the testb ed m ust hav e. T o facilitate a full attac k scenario sim ulation with scenar- ios that contain a piv ot of the attack from IT to OT, the test b ed is designed with six segments. The distinct net work segments are as follows: 10 Y ogha Restu Pramadi et al. 1. Internet Sim ulat or and Cyb er A ttack Plat- form (External Netw ork): a netw ork segment that is not part of the simulated industrial net work, but pla ys a vital role in pro viding in ternet service sim ulation (e.g. simulated DNS, web, and routing). This segmen t will also b e the origin of the attac ks that are conducted by the simulated APT. 2. IT DMZ (Demiliterized Zone): A buffer zone b et ween the IT LAN and external net works (e.g. the In ternet). It hosts services that require external ac- cess (e.g. Activ e Directory , email, w ebservices, and other general business applications) while protect- ing in ternal IT assets. In accordance with the I IRA arc hitecture, this segmen t also hosts the en terprise tier of the I IoT netw ork. 3. IT LAN: Represents the corp orate enterprise net- w ork, including typical office w orkstations. This seg- men t is the most exp osed to external threats and often serv es as the initial p oin t of compromise for APTs. 4. Industrial/OT DMZ: This critical buffer zone is p ositioned b etw een the IT and OT netw orks and is protected b y a firewall on b oth connections. It hosts devices that require interaction with b oth IT and OT environmen ts, such as data historians, data log serv ers, and v arious gatew ays, ensuring controlled data flo w and limiting direct IT-to-OT communi- cation. The OT DMZ serv es as a single, carefully con trolled p oin t of en try to the OT netw ork, often accessed via a jump host. 5. OT Netw ork: This segment houses the core in- dustrial con trol systems, including SCAD A systems, PLCs, HMIs, and other intelligen t devices resp onsi- ble for monitoring and managing ph ysical processes. This net work prioritises av ailabilit y and safety , us- ing sp ecialised industrial communication proto cols. Micro-segmen tation within the OT netw ork further isolates devices into functional zones, minimising impact of breach. 6. I IoT Net w ork: This infrastructure in tegrates IIoT devices that connect to the OT netw ork and the en terprise netw orks, facilitating op erational moni- toring and efficiency . These devices often lack ro- bust securit y protocols, making them p oten tial w eak links for lateral mo vemen t b et ween IT and OT. The I IoT net work design within the testb ed reflects its role as a p otential target for attack ers. T o b etter mimic real-world conditions, the testb ed is also designed with b est practices and cyb er security guidelines, such as NIST SP 800-82 [38] and IEC62443 [43]. These standards emphasise robust segemen tation and secure conduits to con trol traffic flow and minimise attac k surfaces. The arc hitectural design of the testb ed incorp orates m ultiple lay ers of defence. – Dual Firew alls: Strategic placemen t of firewalls at the edge of the IT netw ork and the OT netw ork, with the OT DMZ b et ween them, enforces access p olicies and con trols traffic flo w. These firewalls are configured to p erform pack et filtering and enforce micro-segmen tation rules within the OT and IIoT en vironment. – Netw ork Segmentation and VLANs: The en- tire sim ulated en terprise netw ork is divided in to dis- tinct IT and OT domains, with further segmen ta- tion in to Virtual Lo cal Net works (VLANs) within eac h domain. This allo ws for tailored securit y mea- sures and differen t access p olicies, reducing exp o- sure to unsophisticated attack vectors. – Access Control: A strict access con trols using tech- nology commonly used such as Access Directory . – Jump Hosts: A common security b est practice is to hav e a jump host or a bastion host. A jump host serv es as the p oin t of entry for external users to access devices on the OT net work from the IT net work. This minimises en try p oin ts and ensures that only authenticated and authorised p ersonnel can cross ov er into the OT domain. Figure 5 illustrates the design of the testb ed with its net work segments, net work devices, virtual machines, virtualised OT devices, and digital twins. 5.3 T estbed Implementation T o implement the testb ed, we follow the practical im- plemen tation guide presented by [26]. The study presen ts a building block of a cybersecurity testbed for indus- trial netw orks, the building blo c ks are the management la yer, the user lay er, the infrastructure bridge, and the exp erimen tal lay er. Providing these lay ers is a big task if it is done from scratch. Cyb er range platforms such as [44, 45, 46] pro vide the building blo c ks and tools re- quired to accelerate the building pro cess of a testb ed. F or this study , w e chose the DIA T eam cyber range [46]. The test b ed is implemen ted with mostly open source soft ware, with the proprietary softw are used being F ac- tory I/O, Microsoft Windows 10 Education and Mi- crosoft Windows Serv er. Figure 6 depicts the o v erall testb ed top ology implemen ted in the DIA T eam Cyb er- range. A brief description of the testbed implementa- tion is discussed as follows. Implemen ting the testbed starts with building the em ulated netw ork using op en source firew alls, routers, and switches. The main netw ork infrastructure is built with a VyOS router, tw o pfsense firew alls, and Design and Implementation of the SIMPLE ICS T estbed 11 Proximity Network Proximity Network Enterprise DMZ Mail Server Industrial DMZ IIoT Platform Tier IIoT Edge Tier Enterprise Authentication Server Web Server Engineering Workstation Data Historian Proxy & Software Update Data Transform Analytics & Operations Control Console Enterprise Workstation Enterprise Dashboard Business Data Business Dashboard Enterprise Tier Layer 3 - Manufacturing & Operations Layer 2 - Supervisory Control Layer 4 - Enterprise Layer 1 - Basic Control Internet HMI PLC Historian PLC Data Historian OT Authentication Server Remote Access Server HMI Historian Engineering Workstation Engineering Workstation Attacker Platform Layer 0 - Physical Process Digital T win Digital Twin IOT Edge IOT Edge Digital T win PLC HMI HMI PLC Digital T win SOC and Experimentation Experiment Data Storage Network and Log Capture Data Analytics Platform Legends: Ethernet Connection Network T AP Connection Fig. 5: The Prop osed T estbed Design, Guided by PERA and I IRA fiv e Op enVswitch virtual switches. The VyOS router serv es as a router to route outbound pac kets from the in ternal netw ork to the attack er platform and the in- ternet simulator. The first pfsense router acts as the p erimeter firew all with four net work interfaces, an in- terface for the IT DMZ, an in terface for the IT LAN, and an interface for the bac kb one that connects to the OT net work. The IT LAN interface on the firewall is configured to host in tranet VLANS. The second pfsense firew all acts as an OT firew all that regulates the traf- fic entering and leaving the OT netw ork. The OT fire- w all has four netw ork interface, an interface to the en- terprise backbone, and interface to the OT DMZ, an in terface to the OT net work, and an interface to the I IoT netw ork. The firew alls are configured to pro vide basic services suc h as DHCP , NA T (Net w ork Address T ranslation), and baseline segmentation security . Each firew all interface is connected to an Op enVSwitch vir- tual switch configured to forw ard pack ets to the first p ort for pac ket monitoring, and for the switches that serv es VLAN segmen tation, the switches interface are configured accordingly . The implementation of the External Net work Seg- men t is built with t w o main comp onen ts, the internet sim ulator and the attack platform. The internet simu- lator uses TOPGEN and Gr eyBox , we used the readily a v ailable O V A and conv erted it to a QCOW2 (QEMU Cop y-On-W rite) format. The VM is configured with a bridge interface that will b e the destination of traf- fic that is intended to b e directed to the internet, the Greyb o x emulates the internet backbone, while TOP- GEN pro vides functional equiv alents to p opular inter- 12 Y ogha Restu Pramadi et al. net services suc h as HTTP , DNS, and email. The attac k platform uses Kali Linux and Parr ot OS with Caldera along with other common hac king to ols configured to sim ulate APT attacks. F or the IT En terprise DMZ Segment , t wo Win- do ws Server are used. The first Windows Server VM serv es as the main Active Directory configured as the domain con troller (DC) of a domain (simpleics.lo cal). The AD is configured with vulnerabilities and miscon- figuration that enable lateral mov ement, taking inspi- ration from the Games of A ctive Dir e ctory (GOAD) pro ject. The implemented vulnerabilities are: Kerbr o ast- ing , ASREPR o asting , Unsecured SMB shares, and Golden Ticket persistence. The second server is installed with an email service and IIS to pro vide a platform for a vul- nerable web service and a platform to deliv er phishing emails. The IT LAN Segmen t implements multiple VMs using Windo ws 10 configured with the W azuh agen t and the Ghosts NPC human b eha viour agent. The VMs are authen ticated using the domain controller, and the hu- man b eha viour agen t runs a loop ed human behaviour scenario and APT victim scenarios. The human b e- ha viour simulation is describ ed further in section 5.4. Fig. 6: T estb ed Implementation on DIA T eam The OT DMZ Segment hosts an OT sub domain domain controller ( ot.simpleics.lo c al ) and tw o IIoT plat- form servers. The DC uses Windows Server 2019 , con- figured as a trusted c hild sub domain con troller. The I IoT platform is built with Ubuntu Serv er running the MING ( MQTT , InfluxDB , No de-RED , and Gr afana ) stac k. The MING stack serves as a broker with four main functions: firstly it receives published messages from the I IoT gatew a y and rela y them to the enterprise platform, secondly it receiv es con trol messages from the en terprise platform and forward them to the I IoT gate- w ays, thirdly it stores op erational telemetry data . The OT Segment implements tw o Windows 10 VMs and tw o Ubuntu Desktop 24.04. The first Win- do ws VM pla ys a role of an Engineering W orkstation with Op enPLC Editor installed, the second VM serves as a factory sim ulator using F actory IO. The Ubun tu Desktop VMs are dedicated to sim ulate industrial con- trol devices, the first VM servers as a PLC using Op en- PLC, and the second VM simulates an HMI using FUXA. The IIoT Segment is implemen ted similarly to the OT segmen t, the difference is that this segmen t uses the MING stack at the I IoT edge gatewa y instead of using Mo dbus. The MQTT service acts as a clien t that pub- lish operational messages to the I IoT platform in the OT DMZ and subscrib es to topics that control the fac- tory process. This enables remote con trol of the process from the I IoT Dashboard. The last segmen t to implement is the Exp erimen t/SOC Segmen t , this segment is implemented with a segre- gated netw ork using an Op enVSwitc h virtual switc h as the main netw ork hub of this segment. T o gather log data w e deplo yed fiv e Hedge Hog Linux VM as a net work sensor, one for each netw ork segmen t in the testb eds netw ork (not including the external segment). The netw ork sensor has tw o interface, one acts as the net work tap interface and the other is for connecting to the main SOC platform. The main SOC platform uses Malcolm OS to pro cess the gathered logs and pack ets from the net w ork sensors, it acts as a cen tral analysis platform of the exp erimen tal segment of the testb ed. T able 2 presents a list of applications, to ols, and op er- ating systems chosen for the testb ed. The SimpleICS implementation, configuration files, and scripts used in this study are publicly av ailable in our rep ository [47]. 5.3.1 Industrial Pr o c ess Simulation Implementation As discussed in the previous section, this study opted to use DT tec hnology to sim ulate factory processes mainly to facilitate deploymen t and repro ducibilit y while main- taining high fidelit y to the simulation of physical pro- cesses for cybers ecurit y researc h purp oses. F actory IO pro vides such a to ol at a relatively affordable price. T o aid in repro ducibilit y , the study used the readily av ail- able scenes in F actory IO. F or controlling and monitor- Design and Implementation of the SIMPLE ICS T estbed 13 T able 2: T ools and Comp onen ts. Segmen t Virtual Device T o ols Role External Netw ork VyOS – External netw ork routing P arrot OS and Kali VM MITRE Caldera Adv ersary simulator In ternet sim ulator VM T opGen, GreyBox In ternet simulator IT DMZ PFSense – IT enterprise firewall and routing Ope nVSwitc h – Virtual switch and netw ork tap Windo ws Server 2016 Activ e Directory Authen tication server, web serv er, and mail server Ubun tu Server MQTT, InfluxDB, No deRed, Grafana I IoT en terprise platform IT LAN Ope nVSwitc h – Virtual switch and netw ork tap Windo ws 10 Ghost NPC Emulates human b eha viour and serves as an attack piv ot p oin t OT DMZ PFSense – OT netw ork firewall and routing Windo ws Server 2016 Activ e Directory Authen tication server, web serv er, and mail server Ubun tu Server 24.04 MQTT, InfluxDB, No deRed, Grafana I IoT platform OT Netw ork Windo ws 10 F actoryIO F actory pro cess sim ulator Ubun tu Desktop 24.04 Op enPLC, FUXA Op en-source PLC and HMI I IoT Net work Ubun tu Server 24.04 MQTT, No deRed, In- fluxDB I IoT gatew ay Windo ws 10 F actoryIO F actory pro cess sim ulator Ubun tu Desktop 24.04 Op enPLC, FUXA Op en-source PLC and HMI SOC Netw ork Ope nVSwitc h – Virtual switch and netw ork tap Malcolm OS Open-source net work analysis to olset* Netw ork traffic analysis to ol suite HedgeHog Linux Open-source net work analysis to olset* Netw ork PCAP log * A detailed list of the op en-source toolset can b e seen in [48]. ing the pro cess, the study opted to use free op en source solutions, namely OpenPLC for the PLC simulator and FUXA for the HMI/SCADA simulator. The logic im- plemen ted for the scene is implemented using the IEC 611131-3 Ladder Diagram (LD) Standard. The imple- men tation of the industrial process for the OT and IIoT segmen ts is as follows: 1. The OT Segmen t Industrial Pro cess Imple- men tation: The industrial pro cess in this segment mimics a metal lid production line using the ”Pro- duction Line” scene from F actory IO. The pro cess in volv es loading metal slabs from a conv eyor belt to a CNC mac hine (computer numerical con trol) using a rob otic arm, lid pro duction control, pro duction progress monitoring, and transp ort to the end of the pro duction line with con vey or b elts. In the sim- ulation, there are tw o production lines that w ork in parallel, with the end of the con vey or merging in to one exit. The ladder diagram tak es input from the diffuse sensors for the con v ey or and the progress sta- tus of the production process. Then it controls the scene by sending a control signal to the conv eyor b elts and the CNC mac hine. The HMI implemen ts the monitoring of the pro cess, it displa ys every sta- tus of the conv eyor, counts the pro duced lids from eac h station, and implemen ts three manual controls (start, stop, and reset). The SCADA presen ts the same information and control with the addition of presen ting and storing the pro cess information ov er time (daily) to the historian database. 2. The I IoT Segment Industrial Pro cess Imple- men tation: This segment uses the ”Sorting b y W eight” scene, which simulates a b o xed pac k age sorting sys- tem that sort by the weigh t of the b o x. The pro- 14 Y ogha Restu Pramadi et al. cess starts b y sensing the weigh t of the box using a conv eyor scale and determines the weigh t of the b o x b y measuring the output voltage of the sensor (0 - 10 volts). The b o x will then be redirected to three differen t conv ey ors dep ending on the w eight of the box. The ladder diagram of this scene tak es input from diffuse sensors of the conv eyors to sense the position of the b o x; then it senses the voltage of the scale sensor, calculates the b o x’s w eigh t, and sends signals to the p op-up wheel sorter dep end- ing on redirecting the b o x to the intended con vey or. Similarly to the OT segment, the HMI and SCADA for the IIoT process displays every input and out- put of the pro cess, presen ts additional controls to manage the pro cess, and stores pro cess data to the historian. The sim ulated industrial pro cess uses the Mo dbus TCP/IP proto col, as this proto col is considered the de facto proto col for communication within ICS [49]. And for IIoT communication, the MQTT protocol is used for its ubiquitous adoption in IIoT due to its ligh tw eight and efficient nature that requires minimal resources to run [17]. In this setup, the F actory IO acts as a Modbus TCP/IP server, and Op enPLC, FUXA, and No de-Red act as the clients. T aking note of this configuration, to address the mo dbus outputs and inputs, it is necessary to follow the Op enPLC addressing space for a slave configuration: discrete outputs (%QX100.0-%QX199.7) and discrete inputs (% IX100.0-%IX199.7). Similarly in FUXA, the input needs to b e offset by 800 bits and the output offset by 800 bits. Figure 7a sho ws the ”Sorting b y W eight” scene used in the IIoT segmen t, and Figure 7b sho ws an example of the ladder diagram for the ”Sorting b y W eigh t” scene dev elop ed using the Op enPLC Editor. 5.4 Simulating User and Op erational Behaviour In a complex net w ork such as an industrial netw ork, normal b eha viour data can be divided in to three cate- gories: normal human activity b eha viour, normal op- erational b eha viour, and background noise. This re- quiremen t is vital for effective anomaly detection, where an y significant deviation from the established baseline can signal suspicious b eha viour or p oten tial compro- mise. The subsection co vers h uman b eha viour simula- tion tools for the testb ed, focussing on the Ghosts NPC to ol. Ghosts NPC is a to ol that automates the simula- tion of human b eha viour using agents (NPCs) and a cen tralised API to manage and monitor the b eha viour. They use game theory and concepts to animate the (a) F actory Simulation with F actory I/O (b) Ladder Diagram Fig. 7: The developed OT environmen t agen ts by giving the agen ts a p ersona that mimics com- plex human b eha viour. The latest iteration of the tool supp orts the use of generativ e AI to animate agen ts and will hav e a non-deterministic outcome. In this study , to sim ulate normal human / user b e- ha viour, the ”kno wledge horizon” of normal human ac- tivities is follo wed [50]. This means that to construct a normal user b eha viour in a testb ed we need to know what the role of the user is, identify what the user will realistically know and behav e, the timing of the actions of the user (when they will act and ho w long does it tak e), and the interaction b et ween users within an or- ganisation. IT and OT users will ha ve similarities in p erforming IT related tasks, and they will behav e dif- feren tly relative to their job roles. In addition to normal behaviour, the role of a user in an APT attac k scenario is also iden tified. This can be used to simulate users with low security aw areness clic k- ing a phishing link or unkno wingly activ ating a malw are [51]. As the study fo cusses on APT, the scenario in this study does not include any insider threat attac ks, but Design and Implementation of the SIMPLE ICS T estbed 15 it can b e done if necessary in the future, as the to ol used p ermits such use cases. The study implemen ted five roles, namely normal IT user, victim IT user, engineering department user, normal OT user, and victim OT user. An in teractiv e action b et ween the user, which in v olv es sending emails b et ween NPCs, is also defined in the script. The details of the roles, activities, actions, and rationale for the activities can b e seen in T able 3. 5.5 Implementing APT Scenarios This section describ es the practical implemen tation of the APT scenario that this study proposes, leveraging op en source offensiv e security to ols and the Caldera cyb ersecurit y framew ork. The goal is to emulate each phase of the attack lifecycle in an IT-OT conv ergence en vironment, allo wing empirical ev aluation of detection and correlation mechanisms. T o emulate the m ulti-phase scenario, we emplo y the MITRE Caldera adv ersary em ulation platform [52]. Cal- dera’s mo dular architecture enables the orchestration of A TT&CK-aligned attack campaigns via agents and abilities, supp orting repeatable, auditable exp erimen ts. Although Caldera do es not implement all techniques in the MITRE A TT&CK framew ork (esp ecially initial ac- cess tec hniques to a v oid being miss-used), it pro vides substan tial cov erage for enterprise and ICS TTPs b y installing the official OT proto col plugins [52]. F or tec h- niques that are not cov ered by Caldera’s abilities, the study implements manual attac ks. The metho dology in implementing attack scenarios with Caldera in this study is as follows: 1. Planning : This phase in v olv es planning the sim u- lated attack by analysing the scenarios’ TTPs against the testbed topology , determining the attac k path and the c hain of attacks of the simulated apt. W e iden tify the VMs that will be the victims, the vul- nerabilit y that will b e exploited on the system, and the tools that will b e used for the attac k. This c hain of TTPs will be implemen ted as a series of ”abilit y”. 2. Ability Selection and Creation : an abilit y in Caldera is an individual atomic technique that cor- resp onds to a specific attack tec hnique. Each abilit y is giv en a TTP id num b er that reflects the corre- sp onding MITRE A TT&CK TTP . Caldera comes with a set of default abilities . How ev er,as stated ab o ve, there are cases where the abilit y that needs to b e implemen ted is not in the library . In such cases, w e need to define a new ability; we can create them b y scripting a man ual command to execute an ex- ternal to ol. 3. Adversary Creation : an adversary in Caldera is a simulated threat actor that is created by selecting a series of abilities. The abilities is organised ac- cording to the phase of attacks do cumen ted in the scenario. 4. Attac k Implemen tation : After creating the ad- v ersary , the next phase is the attac k implemen tation phase. In a complex scenario, full automation of at- tac ks is difficult to achiev e. This complexit y arises from the in terdep endence of one abilit y on the re- sults of a preceding ability . The steps in implement- ing attacks include: (a) Agent Deplo yment: an agent is a light weigh t implan t that executes commands on b ehalf of the adversary . It serves as the remote agent to sim ulate APT action accross the attack. Agents need to be deploy ed in eac h victim in the sce- nario. Deploymen t t ypically sim ulates Inital Ac- cess (T A0001) by installing the agent on a com- promised host. (b) Op eration Execution: An Operation in Cal- dera is an orc hestrated, m ulti-step adv ersary em- ulation campaign. It c hains together individual abilities, executed b y agen ts on compromised hosts. T able 4 presents the adv ersary configuration for sce- nario 1. The scenario is successfully implemented with Caldera and it only requires manual interv ention for the sp earphishing eac h process. The Caldera mo dbus plugin is used for the final phase of the attack. The SimpleICS-APT dataset, including PCAPs, OT pro cess logs, and even t annotations, is av ailable at the follo wing rep ository: [53]. 6 V alidation and Ev aluation 6.1 F unctional and Performance Ev aluation The p erformance of the testbed was ev aluated across three critical communication pathw ays: intra-IT com- m unication, in tra-OT communication, and cross-segmen t comm unication. Performance measurements were col- lected o ver a 1-day p eriod under v arying op erational conditions to establish baseline c haracteristics and iden- tify p oten tial b ottlenec ks. T able 5 sho ws the p erformance. The netw ork la- tency , a verage bandwidth, and pack et loss measurements are performed ov er an hour to reveal the p erformance profiles b et ween the different netw ork segments. The net work latency and the av erage bandwidth of Intra-IT comm unications consistently show ed low latency and excellen t net w ork throughput performance with a mean resp onse time of 0.974 ms and an av erage bandwidth of 16 Y ogha Restu Pramadi et al. T able 3: Simulated User Beha viour. Role Activit y Actions & F requency Justification Normal IT User W eb browsing Accesses company intranet and online do cumen tation (5 times/day). Mimics common office tasks and pro vides baseline netw ork traffic. Do cumen t creation & edit- ing Creates and sav es do cu- ments in shared drives; edits existing files (3 times/day ). Represents typical pro ductivit y w orkflows and file I/O. Email communication Sends and receives emails (10 emails/day). Generates routine email traffic for baseline b eha viour. Victim IT User W eb browsing Same as Normal IT User, but clicks a phishing link when triggered. Acts as a precursor to compro- mise. Email communication Same as Normal IT User, but op ens malicious attac h- ments when present. Simulates susceptibility to social engineering. Engineering Department (Jump Host Access) System login & mainte- nance Logs into jump host via RDP for main tenance (2 times/day ). Reflects p eriodic maintenance tasks and establishes legitimate access patterns. Normal OT User (Engi- neer) PLC monitoring Uses SCADA/HMI to mon- itor PLC status and view sensor data (contin uous during working hours). Represents core industrial con- trol system op eration. Victim OT User (Engi- neer) PLC monitoring Same as Normal OT User but executes a compro- mised binary after compro- mise. In tro duces malicious code into OT environmen t. In teractive Action: Email Victim IT User → OT User Victim IT user accidentally forw ards a potentially mali- cious attachmen t to an OT user. Simulates accidental propaga- tion of malware/malicious con- ten t across trust b oundaries. T able 4: APT Emulation Implemen tation A ttack Phase A TT&CK T actics & T ec hniques Caldera Abilities & Plugins Initial Access T A0001 (T1566.001, T1133) Manual sp ear-phishing with a malicious attachmen t or link; initial script drop to install the sandcat agent enabling re- mote HTTP(S) C2. Reconnaissance & C2 T A0011, T A0007, T A0005 Run discov ery and environmen t-collection abilities such as whoami , systeminfo , net view , arp , netstat . Creden tial Harvesting T A0006 (T1003) Execute built-in mimikatz abilities to dump LSASS creden- tials; harvested credentials are stored as Caldera facts for subsequen t use. Lateral Mov ement T A0008 (T1021.*, T1078) Use psexec , smbexec and stockpile abilities to pivot lat- erally across IT hosts to the OT-Jumphost using v alid cre- den tials on remote-services. OT execution Prepa- ration T A0007, T A0002 Issue shell commands on the OT-Jumphost, enumerate in- terfaces, prob e OT subnets, and identify mo dbus targets. ICS Actions T A0010, T A0009, T0831 Use the Caldera-OT plugin to modify Mo dbus-TCP writes to impact PLC interactions. 9463 Kbps. In tra OT communication exhibits sligh tly higher latency at 1.29 ms with 9102 kbps throughput. The cross-segment net w ork latency from the IT net- w ork to the OT netw ork is measured as 3.695 ms and a Design and Implementation of the SIMPLE ICS T estbed 17 (a) Compromised Machines (b) Automation of Phase 2 (Reconnaissance) (c) Detected Attac ks on the Malcolm Dashboard Fig. 8: Adv anced A ttac k Sim ulation with Caldera: (a) Compromised Machines, (b) Automation of Scenario 1 – Phase 2 (IT Reconnaissance), (c) Detected Attac ks on the Malcolm Dashboard. T able 5: SIMPLE-ICS Performance Ov er One Hour Metrics In tra- IT In tra- OT Cross- Segmen t Avg. Netw ork Latency (ms) 0.974 1.29 3.605 Avg. Bandwidth (KB) 9463 9102 9012 Avg. Pac ket Loss (Normal) 0 0 0 Avg. Pac ket Loss (Stress) 0 0 0 throughput of 9012 Kbps. This shows that the netw ork p erformance is well within acceptable b ounds for ICS comm unications where submillisecond resp onse times are typically required for safety-critical operations, and the av erage bandwidth of the testb eds sho ws that test- b eds reliance on softw are defined net work (SDN) in a virtualised environmen t can provide a near true to the- oretical sp eed bandwidth (using gigabit Ethernet). Av- erage pack et loss was measured to see whether there are pac k et drops in the netw ork during normal load and during stress testing. F rom both measuremen ts, no pac ket loss w as detected, whic h sho ws that the platform has enough resources to accommodate the scenarios and that the netw ork devices were configured correctly . The use of testb ed resources w as ev aluated across m ultiple dimensions to assess efficiency and scalability . T able 6: SIMPLE-ICS OT Proto cols P erformance Over One Hour Metrics Result Avg. num b er of Mo dbus Pac kets 1,389,194 Avg. num b er of MQTT Pac kets 39,274 Avg. num b er of OPC UA Pac kets 33,045 The host system sp ecifications included t wo serv ers in- terconnected within the DIA T eam cyber-range virtual en vironment, eac h serv er housing an Intel Xeon Gold Pro cessor with a total of 48 cores and 4 TB of RAM and NVMe storage, representing a realistic industrial virtualisation platform. The CPU allo cation for the testb ed was 51 virtual mac hines using a total of 143 virtual pro cessors. And CPU usage during normal op erations w as av eraged 25%, with p eak usage reaching 37.9% during the sim ulation of the APT scenario. Memory consumption remained stable at 146 GB for no de 1( 6.5% of total capacit y), pro viding ample headroom for additional virtual ma- c hines or simulation complexit y . 6.2 Comparison with Similar T estbeds T able 7 compares SIMPLE ICS with contemporary test- b eds across five dimensions: architecture (IT/OT/I IoT co verage), ICS fidelit y (ph ysical, h ybrid, or digital t win), APT emulation supp ort, key characteristics (flexibil- it y , repro ducibilit y , cost-effectiveness, isolation, op en- ness [26]), and data logging capabilities (system, net- w ork, op erational logs). ICS Fidelity . Ph ysical tes tbeds [20, 19, 24] offer high realism but are costly , difficult to repro duce, and re- quire sp ecialized environmen ts. Hybrid testbeds [17, 23] balance realism with reproducibility , though sp ecial- ized comp onen ts like R TDS simulators [18] remain ex- p ensiv e. Digital twins [25, 54] now pro vide sufficient fi- delit y for cybersecurity researc h while maximizing re- pro ducibilit y and cost-effectiveness, motiv ating SIMPLE ICS’s design choice. Arc hitecture. Most testb eds fo cus either on I IoT [17, 34, 24, 22] or traditional OT [23, 18, 19] architectures. Critically , despite do cumen ted APT attac ks targeting traditional OT net works with IT infrastructure exploita- tion, no reviewed testb ed fully recreates both IT sys- tems (mail serv ers, Active Directory) and OT net works. SIMPLE ICS addresses this gap b y supp orting all three arc hitectures. APT Emulation. Only three testb eds explicitly supp ort APT attac ks. [34] and [20] simulate APT sce- narios but pro vide limited attack representations and 18 Y ogha Restu Pramadi et al. T able 7: SIMPLE ICS Comparison to other w orks identified in the literature T estb ed ICS Fidelit y Arc hitecture APT Characteristics Data Logs IT OT I IoT F R CE I O Sys Net Op Bro wnI IoTbed, 2021 [17] Hybrid ◗ ❍ ● - ✓ ✓ ✓ ✓ ✓ ✓ ✓ ✓ W AMP AC, 2021 [18] Hybrid ❍ ● ❍ - ✕ ✓ ✕ ✓ ✕ ✕ ✓ ✓ ICS Protable Cyber Kit, 2021 [19] Scaled Do wn Phy sical ❍ ● ❍ - ✕ ✓ ✕ ✕ ✕ ✕ ✓ ✓ Karc h et al., 2022 [20] Ph ysical ◗ ● ❍ - ✕ ✕ ✕ ✓ ✕ ✕ ✓ ✕ Simola et al., 2023 [23] Hybrid ❍ ● ◗ - ✕ ✓ ✕ ✓ ✕ ✕ ✓ ✕ Kumar and Thing, 2023 [21] Hybrid ◗ ❍ ● Campaign ✓ ✓ ✓ ✓ ✕ ✓ ✓ ✕ Mikk elsplass & Jor- gensen, 2023 [24] Phy sical test- b ed ❍ ❍ ● - ✕ ✓ ✓ ✕ ✕ ✕ ✓ ✕ Ghiasv and et al, 2024 [22] Hybrid ❍ ❍ ● Stages ✕ ✓ ✓ ✕ ✕ ✓ ✓ ✕ Lo et al., 2024 [25] Digital Twin ❍ ● ❍ - ✕ ✓ ✓ ✕ ✕ ✕ ✕ ✓ SIMPLE ICS Digital Twin ● ● ● Campaigns ✓ ✓ ✓ ✓ ✓ ✓ ✓ ✓ F: Flexibility R: Repro duce CE:Cost Effectiveness I: Isolation O: Openness ● : Implemented ◗ : Partially Implemen ted ❍ : Not Implemented ✓ : Supp orted ✕ : Not Supp orted no extensible framew ork. [22] fo cuses on individual attac k stages rather than complete campaigns. Other testb eds use discrete, unrelated attac ks that lack the sequen tial relationships c haracteristic of real APT cam- paigns. SIMPLE ICS provides a methodology and plat- form for emulating m ulti-stage APT campaigns with realistic attack chains from IT to OT/I IoT. Characteristics. Ph ysical testb eds lac k flexibility and op enness while incurring high costs. Hybrid ap- proac hes like [17] demonstrate goo d reproducibility and ha ve enabled deriv ative works [34, 22]. Digital twins of- fer sup erior flexibilit y , reproducibility , and cost-effectiv eness. Isolation is adequately addressed b y most testb eds through virtualization or air-gapping, though [19] and [22] lack explicit isolation do cumen tation. Data Logging. Netw ork logs are nearly univ ersal, but system and operational logs v ary significan tly . Only [17] and SIMPLE ICS capture all three log types. Sys- tem logs are essential for host-based detection but ab- sen t in most ph ysical testb eds. Op erational logs, critical for detecting attacks manifesting as ph ysical anomalies, are surprisingly omitted b y several IIoT-fo cused test- b eds. SIMPLE ICS’s comprehensiv e m ulti-source log- ging enables researc h on detection approac hes that lever- age correlated data across netw ork, host, and op era- tional domains. 7 Limitations and F uture Directions Although SIMPLE ICS aims to driv e adv ances in in- dustrial cyb ersecurit y testb ed capabilities, several lim- itations remain that present opp ortunities for future enhancemen t. – Currently , the testb ed’s device sim ulation relies pri- marily on soft ware-based industrial components, which, while functionally accurate, may not capture all the timing c haracteristics and ph ysical constrain ts of ac- tual industrial hardware. F uture w ork will explore h ybrid approaches that integrate hardware-in-the- lo op components to further increase realism. – The testbed’s current fo cus on traditional industrial proto cols, while comprehensive for most scenarios, could b e expanded to include emerging I IoT pro- to cols and edge computing arc hitectures that are increasingly prev alen t in mo dern industrial en viron- men ts. In addition, the integration of artificial in tel- ligence and machine learning comp onen ts for both attac k simulation and defence mechanisms repre- sen ts a promising research direction. – T o further enhance the framework’s research ca- pabilities, our immediate developmen t roadmap in- cludes the implementation of t wo additional APT attac k scenarios that will significantly expand the range of T actics, T ec hniques, and Pro cedures (TTPs) a v ailable for sim ulation. These new scenarios will complemen t our existing Sandworm, Blac kEnergy , Design and Implementation of the SIMPLE ICS T estbed 19 and F rost yGo op implementations b y targeting dif- feren t attack v ectors and industrial sectors, provid- ing researc hers with a more comprehensive represen- tation of the APT threat landscap e. Concurren tly , w e will generate a comprehensive APT attac k dataset from these expanded sim ulations, capturing net work traffic, system logs, and b eha vioural patterns across all implemen ted attack scenarios. This data set will serv e as a v aluable resource for the researc h comm u- nit y , enabling the developmen t and v alidation of ma- c hine learning-based detection systems, b ehavioural analysis algorithms, and threat intelligence frame- w orks sp ecifically tailored to industrial en vironmen ts. 8 Conclusions This pap er has presented SIMPLE-ICS (Simulated In- dustrial Multi-tier Platform for Lab oratory Em ulation of Industrial Control Systems), a testb ed framework designed to be easily reproduced b y cybersecurity re- searc hers. Through systematic design, implementation, and v alidation, we ha ve demonstrated that SIMPLE- ICS pro vides a realistic and extensible platform for sim- ulating Adv anced P ersistent Threat attac ks against mo d- ern industrial enterprise netw orks. The key contribu- tions of this work are as follo ws. Firstly , we introduced an adaptation of the V-Mo del design metho dology for testb ed dev elopment. Secondly , we presented a nov el m ultitier framew ork arc hitecture that seamlessly inte- grates IT, OT, and I IoT comp onen ts within a virtual- ized environmen t, allowing researchers to study cyber- ph ysical security interactions across the en tire indus- trial enterprise stack. The modular design, implemen ted on the DIA T eam cyb er range infrastructure with stan- dardised industrial proto cols (Modbus, OPC UA, and MQTT), ensures b oth realism and extensibilit y for di- v erse industrial scenarios. Third, we systematically recre- ate real-w orld APT attack campaigns that begin by de- v eloping a generic attack scenario distilled from promi- nen t APT attack inciden ts. W e then mo delled the at- tac k by mapping the scenario to the MITRE A TT&CK framew ork, and implemen ted the attack with the Cal- dera platform augmen ted by several manual attacks suc h as delivering the initial payload (initial access). By accurately mo delling the T actics, T echniques and Pro cedures (TTPs) of prominent threat actors includ- ing Sandw orm, Blac kEnergy , and F rostyGoop, SIMPLE ICS enables researchers to conduct realistic adv ersarial sim ulations that closely mirror actual industrial cyb er threats. This capabilit y addresses a significan t limita- tion in existing testb eds that often rely on simplified or theoretical attack scenarios. And last, we established a comprehensiv e v alidation framew ork that demonstrates our sim ulated industrial en vironments through net w ork b eha viour analysis, proto col communication v erification, and attack scenario v alidation. Our ev aluation results show that SIMPLE-ICS achiev es high realism in netw ork traffic patterns and industrial pro cess b eha viours while maintaining the flexibility needed for diverse research applications. SIMPLE-ICS is envisioned to become a collabora- tiv e ecosystem in whic h researchers and practitioners con tribute new attack scenarios, industrial configura- tions, and v alidation metho dologies. In conclusion, SIM- PLE ICS represents a step forw ard in the industrial cyb ersecurit y researc h infrastructure, providing an ex- tensible and realistic framework to adv ance our un- derstanding of cyb er threats to critical infrastructure. Through contin ued comm unit y collab oration and de- v elopment, w e anticipate that SIMPLE ICS will pla y a role in strengthening the cyb ersecurit y of industrial systems worldwide, ultimately con tributing to the pro- tection of critical infrastructure that underpins mo dern so ciet y . References 1. R. Cuorvo, N. d’Am brosio, D. Iorio, G. P errone, S.P . Ro- mano, in 2024 20th International Confer enc e on Network and Service Management (CNSM) (2024), pp. 1–7. DOI 10.23919/CNSM62983.2024.10814599. URL https:// ieeexplore.ieee.org/document/10814599 . ISSN: 2165- 963X 2. W. Hurst, N. Shone, in Management and En- gine ering of Critic al Infr astructur es , ed. by B. T ekinerdogan, M. Ak¸ sit, C. Catal, W. Hurst, T. Alsk aif (Academic Press, 2024), pp. 265–286. DOI 10.1016/B978- 0- 323- 99330- 2.00010- 6. URL https://www.sciencedirect.com/science/article/ pii/B9780323993302000106 3. Z.A. Shaikh, F. Ha jjej, Y.D. Uslu, S. Y ¨ uksel, H. Dın¸ cer, R. Alro obaea, A.M. Baqasah, U. Chinta, IEEE Ac- cess 12 , 7156 (2024). DOI 10.1109/ACCESS. 2024.3351485. URL https://ieeexplore.ieee.org/ abstract/document/10384336 4. M.R. Nosouhi, Z. Baig, R. Doss, D. Mahansaria, D. Prasad P ati, P . Gaurav aram, L. P an, K. So od, in Pr o- c e e dings of the 19th International Confer enc e on Avail- ability, Reliability and Se curity (A CM, Vienna Austria, 2024), pp. 1–11. DOI 10.1145/3664476.3671411. URL https://dl.acm.org/doi/10.1145/3664476.3671411 5. U.P .D. Ani, W. , Jeremy M., G. , Benjamin, C. , Barn- ab y , , J.R.C. Nurse, Journal of Cyb er Security T ech- nology 5 (2), 71 (2021). DOI 10.1080/23742917.2020. 1843822. URL https://doi.org/10.1080/23742917. 2020.1843822 . Publisher: T a ylor & F rancis eprin t: h ttps://doi.org/10.1080/23742917.2020.1843822 6. L.H. Fl ˚ a, C.A. Thieme, M.G. Jaatun, G.K. Hanssen, in Computer Se curity. ESORICS 2024 Interna- tional Workshops (Springer, Cham, 2025), pp. 425–438. DOI 10.1007/978- 3- 031- 82349- 7 27. URL https://link.springer.com/chapter/10.1007/ 978- 3- 031- 82349- 7_27 . ISSN: 1611-3349 20 Y ogha Restu Pramadi et al. 7. M. Con ti, D. Donadel, F. T urrin, IEEE Communications Surv eys & T utorials 23 (4), 2248 (2021). DOI 10.1109/ COMST.2021.3094360. URL https://ieeexplore.ieee. org/document/9471765 . Conference Name: IEEE Com- munications Surv eys & T utorials 8. A. Saxena, S. Mittal, in 2023 Se cond International Confer enc e on Informatics (ICI) (2023), pp. 1–6. DOI 10.1109/ICI60088.2023.10421181. URL https:// ieeexplore.ieee.org/document/10421181 9. S. Choi, J.H. Y un, S.K. Kim, in Critic al Infor- mation Infr astructur es Se curity , ed. by E. Luiijf, I. ˇ Zutautait ˙ e, B.M. H¨ ammerli (Springer International Publishing, Cham, 2019), pp. 154–166. DOI 10.1007/ 978- 3- 030- 05849- 4 12 10. M. Abu T alib, Q. Nasir, A. Bou Nassif, T. Mokhamed, N. Ahmed, B. Mahfo od, Computers & Security 122 , 102875 (2022). DOI 10.1016/j.cose.2022.102875. URL https://www.sciencedirect.com/science/article/ pii/S0167404822002693 11. A.A. Al-Kadhimi, M.M. Singh, M.N.A. Khalid, Ap- plied Sciences 13 (14), 8056 (2023). DOI 10.3390/ app13148056. URL https://www.mdpi.com/2076- 3417/ 13/14/8056 . Number: 14 Publisher: Multidisciplinary Digital Publishing Institute 12. G. Shen, W. W ang, Q. Mu, Y. Pu, Y. Qin, M. Y u, Wireless Communications and Mobile Com- puting 2020 , e8883696 (2020). DOI 10.1155/2020/ 8883696. URL https://www.hindawi.com/journals/ wcmc/2020/8883696/ . Publisher: Hindawi 13. N.H. Cuong, Z.L. Hua, C.D. Xuan, in 2023 RIVF Inter- national Conferenc e on Computing and Communic ation T e chnolo gies (RIVF) (2023), pp. 301–305. DOI 10.1109/ RIVF60135.2023.10471768. URL https://ieeexplore. ieee.org/document/10471768 . ISSN: 2473-0130 14. B. Bhattarai, H.H. Huang. Pro v2vec: Learning Pro ve- nance Graph Represen tation for Unsup ervised APT Detection (2023). URL 00843 . 15. A.S. AL-Aamri, R. Ab dulghafor, S. T uraev, I. Al- Shaikhli, A. Zeki, S. T alib, Sustainabilit y 15 (18), 13820 (2023). DOI 10.3390/su151813820. URL https://www. mdpi.com/2071- 1050/15/18/13820 . Number: 18 Pub- lisher: Multidisciplinary Digital Publishing Institute 16. S. Myneni, K. Jha, A. Sabur, G. Agraw al, Y. Deng, A. Chowdhary , D. Huang, Computer Netw orks 227 , 109688 (2023). DOI 10.1016/j.comnet.2023.109688. URL https://www.sciencedirect.com/science/article/ pii/S1389128623001330 17. M. Al-Ha wa wreh, E. Sitniko v a, IEEE Internet of Things Journal 8 (7), 5558 (2021). DOI 10.1109/JIOT.2020.3032093. URL https://ieeexplore. ieee.org/abstract/document/9233425?casa_token= jkcrnnN72kEAAAAA:ZVeDCNW2Df7NhF12Bmu9GzIHMk1Z_ wRys0ZxeJdY_gxb9FSqol3VhAD3TClUfqDwh56Cpypl3Q . Conference Name: IEEE Internet of Things Journal 18. G. Ra vikumar, B. Hyder, J.R. Babu, K. Khanna, M. Govindarasu, M. Parashar, in 2021 IEEE Power & Ener gy So ciety Gener al Me eting (PESGM) (2021), pp. 1–5. DOI 10.1109/PESGM46819.2021.9638183. URL https://ieeexplore.ieee.org/document/9638183 . ISSN: 1944-9933 19. S. Mubarak, M. Habaebi, M. Islam, A. Balla, M. T ahir, E. A, F. Suliman, Intelligen t Automation & Soft Comput- ing 31 (3), 1345 (2021). DOI 10.32604/iasc.2022.020801. URL https://www.techscience.com/iasc/v31n3/44856 . Publisher: T ec h Science Press 20. M. Karch, D. R¨ osch, K. Andr´ e, A. Meshram, C. Haas, S. Nicolai, in 2022 IEEE 27th International Confer- enc e on Emerging T e chnolo gies and F actory Automa- tion (ETF A) (2022), pp. 1–8. DOI 10.1109/ETF A52439. 2022.9921672. URL https://ieeexplore.ieee.org/ abstract/document/9921672 21. A. Kumar, V.L.L. Thing, in 2023 20th Annual Inter- national Confer enc e on Privacy, Security and T rust (PST) (2023), pp. 1–12. DOI 10.1109/PST58708. 2023.10320192. URL https://ieeexplore.ieee.org/ document/10320192 . ISSN: 2643-4202 22. E. Ghiasv and, S. Ray , S. Iqbal, S. Dadkhah, A.A. Ghor- bani. CICAPT-I IOT: A prov enance-based APT attack dataset for I IoT environmen t (2024). DOI 10.48550/ arXiv.2407.11278. URL 11278 . 23. J. Simola, R. Sav ola, T. F rantti, A. T ak ala, R. Lehko- nen, Europ ean Conference on Cyb er W arfare and Se- curit y 22 (1), 429 (2023). DOI 10.34190/eccws.22.1. 1362. URL https://papers.academic- conferences. org/index.php/eccws/article/view/1362 . Number: 1 24. S.A. Mikkelsplass, P .A. J¨ orgensen, in Pr oc ee ding of the 33r d Europ e an Safety and R eliability Con- fer enc e (Research Publishing Services, 2023), pp. 3422–3429. DOI 10.3850/978- 981- 18- 8071- 1 P564- cd. URL https://www.rpsonline.com.sg/proceedings/ esrel2023/html/P564.html 25. C. Lo, T.Y. Win, Z. Rezaeifar, Z. Khan, P . Legg, in 2024 29th International Confer enc e on Automation and Computing (ICAC) (2024), pp. 1–6. DOI 10.1109/ ICAC 61394.2024.10718749. URL https://ieeexplore. ieee.org/document/10718749 26. B. Green, R. Derb yshire, W. Knowles, J. Boorman, P . Ci- holas, D. Prince, D. Hutchison, (2020) 27. R.S. Pressman, Softwar e engine ering: a pr actitioner’s appr o ach , 7th edn. (McGra w-Hill, Dubuque, IA, 2010) 28. O. Do˘ gan, S. Bitim, K. Hızıro˘ glu, Sak arya Uni- v ersity Journal of Computer and Information Sci- ences 4 (1), 111 (2021). DOI 10.35377/saucis.04.01. 879905. URL http://saucis.sakarya.edu.tr/en/pub/ saucis/issue/59732/879905 . Number: 1 Publisher: Sak arya Univ ersity 29. M.S. Durmus, I. Ustoglu, R.Y. Tsarev, J. B¨ orcs¨ ok, Informatica 42 (4) (2018). DOI 10.31449/inf.v42i4. 2027. URL https://www.informatica.si/index.php/ informatica/article/view/2027 . Number: 4 30. M.J. Assante, R.M. Lee. The Industrial Control System Cyber Kill Chain (2021). URL https://www.sans.org/ white- papers/36297/ 31. O. Alexander, M. Belisle, J. Steele. MITRE A TT&CK ® for Industrial Con trol Systems: Design and Philosophy (2020). URL https://attack.mitre.org/docs/ATTACK_ for_ICS_Philosophy_March_2020.pdf 32. P . Maynard, K. McLaughlin, S. Sezer, Journal of Cy- bersec urit y 6 (1), ty aa020 (2020). DOI 10.1093/cybsec/ t yaa020. URL https://doi.org/10.1093/cybsec/ tyaa020 33. T. Alladi, V. Chamola, S. Zeadally , Computer Commu- nications 155 , 1 (2020). DOI 10.1016/j.comcom.2020.03. 007. URL https://www.sciencedirect.com/science/ article/pii/S0140366419319991 34. R. Kumar, R. Kela, S. Singh, R. T rujillo-Rasua, In ternational Journal of Critical Infrastructure Pro- tection 37 , 100521 (2022). DOI 10.1016/j.ijcip. 2022.100521. URL https://www.sciencedirect.com/ science/article/pii/S1874548222000129 Design and Implementation of the SIMPLE ICS T estbed 21 35. R. Khan, P . Maynard, K. McLaughlin, D. Lav erty , S. Sezer, (BCS Learning & Dev elopment, 2016). DOI 10.14236/ewic/ICS2016.7. URL https: //www.scienceopen.com/hosted- document?doi=10. 14236/ewic/ICS2016.7 36. B. Sto janovi ´ c, K. Hofer-Schmitz, U. Kleb, Computers & Security 92 , 101734 (2020). DOI 10.1016/j.cose. 2020.101734. URL https://www.sciencedirect.com/ science/article/pii/S0167404820300213 37. Y. Y ang, M. Zhang, in 2023 IEEE Eur op e an Symp o- sium on Security and Privacy Workshops (Eur oS&PW) (2023), pp. 336–344. DOI 10.1109/EuroSPW59978.2023. 00042. URL https://ieeexplore.ieee.org/document/ 10190669 . ISSN: 2768-0657 38. K. Stouffer, M. Pease, C. T ang, T. Zimmerman, V. Pil- litteri, S. Lightman, A. Hahn, S. Saravia, A. Sherule, M. Thompson, Guide to Op erational T echnology (OT) Security . T ec h. Rep. NIST Sp ecial Publication (SP) 800- 82 Rev. 3, National Institute of Standards and T ech- nology (2023). DOI 10.6028/NIST.SP .800- 82r3. URL https://csrc.nist.gov/pubs/sp/800/82/r3/final 39. H. Li, A formalization and extension of the Purdue En- terprise Reference Architecture and the Purdue Metho d- ology . Ph.D. thesis, Purdue Universit y , Indiana, United States (1994). URL https://docs.lib.purdue.edu/ dissertations/AAI9523390 40. D. Garton, National Petroleum Council Study on Oil and Natural Gas T ransportation Infrastructure (2019). URL https://www.energy.gov/sites/default/ files/2022- 10/Infra_Topic_Paper_4- 14_FINAL.pdf 41. S. Gulyamo v, A. Akhmedo v, S. Bazarov, A. Ubay- dullaev a, S. Musaev, A. Ro diono v, I. Odilkhujaev, in 2024 6th International Confer enc e on Contr ol Sys- tems, Mathematic al Mo deling, A utomation and En- er gy Efficiency (SUMMA) (2024), pp. 655–658. DOI 10.1109/SUMMA64428.2024.10803689. URL https:// ieeexplore.ieee.org/document/10803689 42. I. Erkek, E. Irmak, in 2024 12th International Confer enc e on Smart Grid (icSmartGrid) (2024), pp. 372–377. DOI 10.1109/icSmartGrid61824.2024.10578257. URL https: //ieeexplore.ieee.org/document/10578257 43. ISA/IEC 62443 Series of Standards - ISA. URL https://www.isa.org/standards- and- publications/ isa- standards/isa- iec- 62443- series- of- standards 44. Ludus. URL https://ludus.cloud/ 45. T. Liesk ov an, J. Ha jn´ y, in Pr o c e e dings of the 16th In- ternational Confer enc e on Availability, R eliability and Se curity (Asso ciation for Computing Machinery , New Y ork, NY, USA, 2021), ARES ’21, pp. 1–11. DOI 10.1145/3465481.3469188. URL https://dl.acm.org/ doi/10.1145/3465481.3469188 46. Cyb er Range p ow ered by Diateam | Thales Group. URL https://www.thalesgroup.com/en/ cyber- range- powered- diateam 47. Y. Pramadi. pramadiyr/simpleics. URL https:// github.com/pramadiyr/simpleics 48. Malcolm. URL https://malcolm.fyi/ 49. J.Y. Jhan, H.M. Sun. Enhancing Mo dbus TCP Pro- tocol Security with eBPF T ec hnology (2023). DOI 10.48550/arXiv.2312.05665. URL abs/2312.05665 . ArXiv:2312.05665 [cs] 50. D.D. Updyke, G.B. Dobson, T.G. P o dnar, GHOSTS in the Machine: A F ramework for Cyber-W arfare Exercise NPC Simulation. T echnical Report CMU/SEI-2018-TR- 005, Carnegie Mellon Universit y (2018) 51. V.D. V eksler, N. Buc hler, B.E. Hoffman, D.N. Cassen ti, C. Sample, S. Sugrim, F ron tiers in Psy- c hology 9 (2018). DOI 10.3389/fpsyg.2018.00691. URL https://www.frontiersin.org/journals/psychology/ articles/10.3389/fpsyg.2018.00691/full . Publisher: F rontiers 52. Caldera. URL https://caldera.mitre.org/ 53. Y. Pramadi, T. Spyridopoulos, V. Kumar. SIMPLE ICS Dataset 2025 (2025). DOI 10.5281/zenodo.17876512. URL https://doi.org/10.5281/zenodo.17876512 54. G. Lazaridis, A. Drosou, P . Chatzimisios, D. Tzo v aras, in 2023 IEEE Confer enc e on Standar ds for Communi- c ations and Networking (CSCN) (2023), pp. 265–270. DOI 10.1109/CSCN60443.2023.10453119. URL https: //ieeexplore.ieee.org/abstract/document/10453119 . ISSN: 2644-3252
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment