Telemetry-Based Server Selection in the Quantum Internet via Cross-Layer Runtime Estimation
The Quantum Internet will allow clients to delegate quantum workloads to remote servers over heterogeneous networks, but choosing the server that minimizes end-to-end execution time is difficult because server processing, feedforward classical commun…
Authors: Masaki Nagai, Hideaki Kawaguchi, Shin Nishio
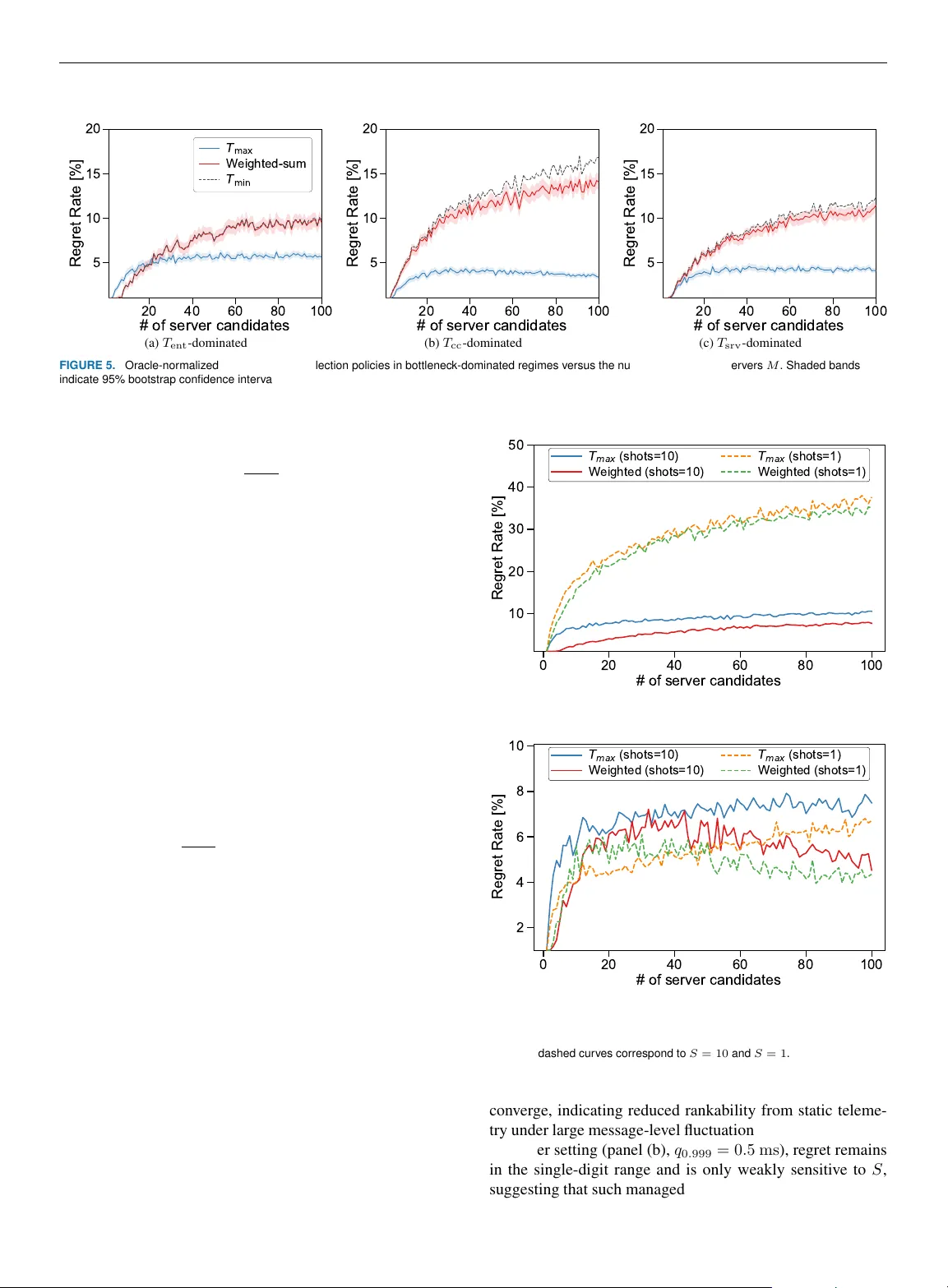
T elemetry-Based Server Selection in the Quantum Internet via Cross-La yer Runtime Estimation MASAKI NA GAI 1 , HIDEAKI KA W A GUCHI 1 , SHIN NISHIO 1,2 , and T AKAHIK O SA T OH 3 1 Graduate School of Science and T echnology, K eio Univ ersity , Y okohama, Kanaga wa 223-8522, Japan (email: masaki0818nagai@keio.jp, hikawaguchi@k eio.jp, shin.nishio@keio.jp) 2 Department of Physics & Astronomy , University College London, London, WC1E 6BT , United Kingdom 3 Faculty of Science and T echnology , Keio Uni versity , Y okohama, Kanagawa 223-8522, Japan (email: satoh@ics.keio.ac.jp) Corresponding author: Masaki Nagai (email: masaki0818nagai@keio.jp). This work was supported by JST Moonshot R&D Grant Number JPMJMS226C. SN was also supported by the Ne w Energy and Industrial T echnology Development Or ganization (NEDO) JPNP23003 and the JSPS Overseas Research Fello wship. TS was also supported by MEXT KAKENHI Grant Number 22K1978. ABSTRA CT The Quantum Internet will allo w clients to delegate quantum workloads to remote servers ov er heterogeneous networks, but choosing the server that minimizes end-to-end execution time is difficult because server processing, feedforw ard classical communication, and entanglement distrib ution can o verlap in protocol-dependent ways and shift the runtime bottleneck. W e propose T max , a lightweight runtime score that sums coarse telemetry from multiple layers to obtain a conservati ve ranking for online server selection without calibrating weights for each deployment. Using NetSquid discrete-ev ent simulations of a modified parameter-blind VQE (PB-VQE) w orkload, we e v aluate T max on pools of 10,000 heterogeneous candidates (selecting among up to 100 per decision) across crossover and bottleneck-dominated regimes, including temporal jitter scenarios and jobs with multiple shots. T max achiev es single-digit mean regret normalized by the oracle (belo w 10%) in both regimes and remains in the single-digit range under classical communication latency jitter for multi-shot jobs, while performance degrades for single-shot jobs under sev ere jitter . T o connect performance to deployment planning, we derive an operating map based on requirements relating distance and entanglement rate requirements to protocol le vel counts, quantify how simple multiuser contention shifts the crossover , and use Sobol global sensitivity analysis to identify regime- dependent bottlenecks. These findings suggest that simple cross-layer telemetry can enable practical server selection while providing actionable pro visioning guidance for emerging Quantum Internet services. INDEX TERMS Quantum Internet, Server Selection, Cross-Layer Optimization, Runtime Estimation I. INTRODUCTION Quantum computers are expected to outperform classical de- vices on specific problems [ 1 ], [ 2 ], and the Quantum Internet is emerging as a key enabler for distrib uted computation and secure applications [ 3 ]–[ 5 ]. The foundations of quantum networking were laid in the 1990s with quantum telepor- tation, enabling state transfer via shared entanglement and classical communication [ 6 ], and with quantum repeaters, which introduced entanglement swapping and purification for long-distance communication [ 7 ]. These breakthroughs established the basis for modern entanglement distribution and repeater-based netw orks. Recent experimental and theoretical adv ances hav e brought this vision closer to reality . Multi-node quantum networks have been realized over metropolitan fiber infras- tructures [ 8 ], marking ke y milestones toward scalable imple- mentations. In parallel, requirements for practical repeater deployment have been quantified both for processing-node architectures on real-world fiber grids [ 9 ] and for upgrading trusted-node links into long repeater chains [ 10 ]. At the application layer , clients must select among het- erogeneous remote quantum servers to minimize end-to- end runtime. This problem is central to practical Quantum Internet applications. In such applications, end-to-end run- time is determined not only by quantum processing b ut also by feedforward classical communication latency and entan- glement distribution, each of which can lie on the critical path. Since whether these components overlap is protocol- dependent and bottlenecks can switch across regimes as distance, entanglement distribution rate, and server -side per- formance vary , application-layer server selection must rely on a lightweight telemetry-based ranking metric rather than detailed per -candidate modeling, activ e probing, or online learning. Prior work has made substantial contributions from multi- ple directions. On the protocol side, blind quantum computa- 1 Nagai et al. : T elemetry Based Ser ver Selection in the Quantum Internet via Cross-Lay er Runtime Estimation tion (BQC) enables secure delegated computation with lim- ited client capabilities [ 11 ], [ 12 ]. In parallel, the v ariational quantum eigensolver (VQE) has emerged as the leading candidate for near-term applications, with demonstrations across platforms and extensi ve methodological studies [ 13 ]– [ 15 ]. P arameter-blind VQE (PB-VQE) has also been pro- posed to support secure and distributed use cases [ 16 ]. At the network and systems lev el, repeater architectures have been systematically compared to clarify distance-dependent performance trade-offs [ 17 ], while utility-based frame works connect netw ork resources to socio-economic value [ 18 ]. In parallel, concrete protocol-stack decompositions and link- layer abstractions have been proposed and e xperimentally validated to expose entanglement delivery as an application- facing service, motiv ating lightweight cross-layer telemetry for runtime-aware decisions [ 19 ]–[ 22 ]. These efforts underscore the rapid progress of the field. Nev ertheless, from the perspective of application-layer server selection, the literature still lacks a unified model that couples client, network, and server parameters to predict end-to- end runtime and guide server selection. In particular , three gaps persist: (i) the absence of a cross-layer runtime model capturing both computational and communication delays, (ii) the lack of a lightweight predictor that enables online ranking with minimal ov erhead, and (iii) an incomplete understand- ing of which physical and logical factors dominate end-to- end performance across operating regimes. T o address these gaps, we make three contributions. First, we formulate application-layer server selection as a cross- layer ranking problem under unknown o verlap between server processing, feedforward classical communication, and entanglement distribution, and define two e xtreme-overlap runtime estimates. Second, we propose a telemetry-only , tuning-free selection rule that ranks candidates by the con- servati ve serialized estimate T max . This conservati ve choice av oids making overlap assumptions and provides a simple ov erlap-agnostic score for online ranking. Third, using Net- Squid discrete-ev ent simulations [ 23 ] of an implementation- oriented PB-VQE benchmark at scale ( 10 , 000 -candidate pools and up to 100 candidates per decision), we quantify oracle-normalized regret across re gimes (including scenario- based jitter) and connect performance to deployment plan- ning via (i) a requirement-based ( d, R ) operating map that captures protocol-level counts, (ii) a simple multiuser con- tention scaling through R eff = R/U , and (iii) a regime map of dominant bottlenecks based on Sobol total-ef fect sensitivity analysis [ 24 ]. W e begin by re viewing the Quantum Internet setting and the delegated workload that motiv ates our focus on cross- layer delays (Sec. II ). W e then formalize latency components and define two extreme-ov erlap runtime estimates that lead to a robust server selection rule (Sec. III ). The proposed policy is ev aluated via NetSquid discrete-ev ent simulations across heterogeneous candidate sets and operating regimes, including robustness under temporal jitter (Sec. IV ). W e complement these results with a requirement-based operating map and global sensitivity analysis to identify dominant bot- tlenecks and extract deployment-rele vant priorities (Sec. V ). W e conclude with limitations and directions toward load- aware predictors for multiuser deplo yments (Sec. VI ). II. B A CKGROUND A. O VER VIEW OF THE QU ANTUM INTERNET The Quantum Internet, which distributes entanglement be- tween remote nodes, has emerged as a foundational infras- tructure for quantum cloud computing and secure quantum communication. Unlik e the classical Internet, which only transmits classical bits, the Quantum Internet employs quan- tum channels for state transfer and entanglement distrib ution in addition to classical communication [ 3 ]. A client with limited quantum capability can connect to multiple remote servers through the Quantum Internet, where both quantum and classical channels are indispensable for the application workflo w (Fig. 1 ). FIGURE 1. Client–network–ser ver schematic f or the server selection problem, instantiated for the PB-VQE w orkflow . T wo candidate servers (A and B) communicate with the client C ov er quantum channels through the shared Quantum Internet (QI). The quantum communication links (A–C and B–C) are annotated with the effectiv e entanglement distribution rate R , while the classical feedf orward communication latency t cc depends on the physical channel length d (propagation-limited model). Server nodes are par ameterized by the server-side processing time T srv , and the client node by T cli . P arenthesized symbols indicate the telemetry components used in the r untime decomposition ( T cli , T srv , T cc , T ent ) . B. BLIND QU ANTUM COMPUT A TION PRO T OCOLS Research on BQC has produced a range of protocols tailored to different client capabilities. Canonical examples include the BFK protocol [ 11 ], in which the client prepares single qubits with random rotations, and the MF protocol [ 12 ], in which the client only performs measurements. These pro- tocols ensure computational blindness, but can incur sub- stantial overhead on the client–server critical path, mak- ing end-to-end runtime sensiti ve to both netw ork latenc y and entanglement distribution. Complementary approaches explore alternativ e trust assumptions for secure delegation, such as quantum trusted ex ecution environments, which can reduce interaction ov erhead at the cost of different threat models [ 25 ]. 2 Nagai et al. : T elemetry Based Ser ver Selection in the Quantum Internet via Cross-Lay er Runtime Estimation C. P ARAMETER-BLIND V ARIA TIONAL QU ANTUM EIGENSOL VER The v ariational quantum eigensolver is a leading near-term algorithm, but in delegated use, its classical–quantum loop demands many shots. The parameter-blind VQE (PB-VQE) addresses pri v acy and communication overhead by fixing the server circuit while the client updates hidden parameters [ 16 ]. W e further enhance the PB-VQE protocol by integrating quantum teleportation, which increases rob ustness against channel loss. W e adopt PB-VQE as an implementation-oriented work- load for studying client–server execution ov er the Quantum Internet. Each shot combines a fixed server-side circuit with a small set of feedforw ard updates at the client, which makes the end-to-end runtime sensiti ve to both hardware and network conditions. The fixed circuit allows us to pa- rameterize serv er-side computational performance mainly by gate duration and readout, while the netw ork contrib ution is determined by classical communication latenc y over fiber and the entanglement distribution rate required to supply Bell pairs. W e use this workload because it exposes the cross-layer delays that dri ve end-to-end runtime while keeping protocol- lev el counts on the critical path fixed, and we provide proto- col details in Appendix A . III. PROBLEM FORMULA TION A. WORKFLO W AND LA TENCY COMPONENTS The end-to-end w orkflow of a Quantum Internet application is a network-mediated client–server interaction. The client prepares and submits a job, the network distributes entan- glement, and the server executes quantum operations while exchanging classical messages with the client (Fig. 2 ). The end-to-end execution time T exe reflects the combined delays of multiple layers, where the dominant bottleneck shifts across re gimes. This re gime-dependent beha vior necessitates a cross-layer runtime formulation. The end-to-end runtime can be decomposed into four latency components: serv er processing ( T srv ), client process- ing ( T cli ), classical communication ( T cc ), and entanglement distribution ( T ent ). W e formalize each component as follo ws: T srv = X t srv , (1) T cc = n cc t cc , (2) T ent = K R , (3) T cli = X t cli . (4) Here, T srv and T cli denote the critical-path execution time of the fixed server circuit under the assumed scheduling model (which can be exposed as coarse-grained telemetry or deriv ed from device specifications for a fix ed benchmark circuit). n cc is the number of one-way classical messages on the critical path, t cc is the one-way latency per message, and K is the number of Bell pairs consumed. T cc = n cc t cc captures the serialized feedforward delay along the critical path, and T ent = K /R uses the ef fecti ve end-to-end entanglement distribution rate R at the target fidelity . Appendix A pro vides the protocol-specific mapping for PB-VQE, including how ( n cc , K ) arise and ho w T srv is obtained for the benchmark circuit. In what follows, we model only the execution-phase la- tency that dif ferentiates candidate servers and omit one- time job setup and scheduling overheads. These overheads are implementation-dependent and are treated as constant across candidates in our ev aluation. Accordingly , we base the optimization on the end-to-end ex ecution time T exe . B. RUNTIME PREDICT OR The end-to-end execution time T exe of a Quantum Internet application is determined by multiple latency components across the client–server stack. T o obtain lightweight runtime estimates suitable for online server ranking, we consider tw o limiting ov erlap regimes and define: T max = T cli + T srv + T cc + T ent , (5) T min = max { T cli , T srv , T cc , T ent } . (6) Here, T max corresponds to a fully serialized ex ecu- tion, whereas T min corresponds to a perfectly ov erlapped, bottleneck-limited ex ecution. The y represent opposite e x- tremes of the ov erlap assumption. W e treat the T max -based policy as the proposed serv er selection method, while we use T min only as a reference baseline. In practice, the realized o verlap among these components is implementation- and load-dependent and is dif ficult to infer from coarse telemetry . W e therefore treat T max as a con- servati ve, monotonic score for online ranking, and validate its selection quality empirically in Sec. IV . As formalized in Sec. III-A , we decompose the workflow into client processing ( T cli ), server processing ( T srv ), classi- cal communication latency ( T cc ), and entanglement distribu- tion ( T ent ). These components do not compose additively in general. For e xample, feedforward dependencies can serial- ize a subset of T cc on the critical path, whereas T ent may proceed concurrently with local operations and ev en with parts of T cc when dependencies and resources permit. As channel length, entanglement distrib ution rate, and serv er- side computational performance differ across candidates, the dominant latency component can shift across operating regimes, making serv er ranking based on a single component inconsistent. C. SER VER SELECTION PROBLEM W e restrict attention to the subset of candidate servers that satisfy the application-lev el accuracy requirement. Let F acc denote the feasible candidate set after this offline filtering. Giv en a scoring function score i , the client selects i ∗ ∈ arg min i ∈F acc score i , (7) where F acc denotes the subset of candidates that satisfy the application-lev el accuracy requirement. In this w ork, we 3 Nagai et al. : T elemetr y Based Ser ver Selection in the Quantum Internet via Cross-Lay er Runtime Estimation FIGURE 2. Protocol diagram of a client–network–ser ver w orkflow over the Quantum Internet. Blue denotes classical operations/communication, and orange denotes quantum ones. Latency parameters T srv , T cli , T cc , T ent denote server processing, client processing, classical communication, and entanglement distribution, respectively . assume that feasibility is ev aluated offline and leave online accuracy estimation to future work. IV . PERFORMANCE EV ALU A TION A. EXPERIMENT AL SETUP Building on the runtime predictors in Sec. III , we ev alu- ate telemetry-based server selection policies via NetSquid discrete-ev ent simulations across heterogeneous channel length, entanglement distribution rate, and serv er-side com- putational performance. NetSquid is one of se veral simu- lation frameworks for Quantum Internet software and per- formance studies. Related tools include SimulaQron, Se- QUeNCe, and QuNetSim [ 26 ]–[ 28 ]. W e consider a setting where a client selects among M candidate servers with heterogeneous network conditions and serv er-side operation speeds. The client ranks candidates using the latenc y compo- nents T srv , T cc , and T ent under a fix ed client implementation. W e parameterize each candidate server by the three scalars ( κ, d, R ) , which map to the telemetry components ( T srv , T cc , T ent ) via Eqs. ( 1 )–( 3 ). Here, κ scales all server- side g ate and measurement durations (T able 1 ), d is the chan- nel length that determines classical communication latency , and R is the end-to-end entanglement distribution rate. The ev aluation procedure for each regime is as follows: 1) Generate a pool of 10 , 000 candidate servers by sam- pling ( d, R, κ ) independently on a logarithmic scale. 2) For each candidate-set size M ∈ { 1 , . . . , 100 } , draw 1 , 500 instances by sampling M servers from the pool. 3) For each instance, compute telemetry-based scores T srv , T cc , T ent for ev ery candidate, apply each selection policy , and simulate PB-VQE to obtain the realized runtime T exe of the selected server . 4) For e valuation only , define the oracle-selected server as arg min T exe within the instance and report oracle- normalized regret r = ( T ( policy ) exe − T ( oracle ) exe ) /T ( oracle ) exe . W e sample ( d, R, κ ) independently to model a heterogeneous candidate pool in which the effecti ve end-to-end entangle- ment service rate R can be decoupled from ph ysical distance d by provisioning choices and differing network architec- tures (e.g., repeater chains and routing over distinct paths). Sec. V -A later reintroduces the physical coupling between d and achie vable entanglement supply through a requirement- based operating map (Fig. 7 ). For ev aluation only , we obtain the oracle by simulating PB-VQE for all M candidates in each instance to compute arg min T exe . The oracle is not a vailable to the online polic y . W e benchmark the modified PB-VQE protocol on the H 2 molecular Hamiltonian [ 13 ], a standard test case for v ari- ational quantum algorithms. Each shot requires n cc = 5 classical messages on the critical path and consumes K = 5 Bell pairs. These counts are protocol-specific and problem- dependent. W e model the one-way classical communication latency as t cc = d/v fiber , where d is the channel length and v fiber ≈ 2 × 10 5 km / s is the effecti ve speed of light in optical fiber . Sub- stituting it into Eq. ( 2 ) yields T cc = n cc t cc = n cc d/v fiber . W e compute the entanglement distribution time from Eq. ( 3 ) as T ent = K /R , where R is the end-to-end entanglement distribution rate. W e approximate the three latency components in Eqs. ( 1 ) to ( 3 ) for a single shot of the PB-VQE benchmark as T srv , T cc , T ent ≈ 9 . 48 κ, 0 . 025 d, 5000 R ms (8) where gate durations are taken from recent trapped-ion ex- periments (IonQ Aria [ 29 ]) and κ is an operation-duration scaling factor . The prefactor 9 . 48 ms corresponds to the total duration of the fixed server -side circuit used in this bench- mark (Appendix A , Fig. 9 ). W e sample the channel length d 4 Nagai et al. : T elemetr y Based Ser ver Selection in the Quantum Internet via Cross-Lay er Runtime Estimation in km , the end-to-end entanglement distribution rate R in Hz , and the operation-duration scaling factor κ independently by drawing each parameter uniformly on a logarithmic scale to generate a regime-specific pool of 10 , 000 servers. In the Even regime, we sample ( d, R , κ ) over the ranges listed in T able 1 , which yields T srv , T cc , T ent ∈ [2 . 5 , 25] ms . W e choose the range of κ so that T srv spans the same order of magnitude as T cc and T ent in the Even regime, enabling balanced trade-of fs among the three components. T ABLE 1. Hardware parameters and variation ranges f or the Even regime. Parameter V alue 1-qubit gate duration 135 κ µ s 2-qubit gate duration 600 κ µ s Readout duration 200 κ µ s Operation-duration scaling factor κ 0 . 263 – 2 . 63 Entanglement distribution rate R 200 – 2000 Hz Channel length d 100 – 1000 km Unless otherwise stated, we set the shot count to S = 10 . Across the sweep ranges in T able 1 , this choice places T exe in the sub-second to few-second range. In the deterministic model, T srv , T cc , and T ent scale linearly with S , so the oracle ranking and the oracle-normalized regret change little with S . W e also report S = 1 in Sec. IV -D to test sensiti vity under temporal fluctuations. B. POLICIES AND O VERHEAD For online server selection, the client must make a selection with negligible decision overhead. W e characterize a selec- tion policy along three practical axes: (i) decision-time com- putation ov er M candidates, (ii) additional learning/tuning, and (iii) observation budget, i.e., the telemetry required to score each candidate. W e assume that { T srv , T cc , T ent } are av ailable as coarse-grained, periodically updated telemetry , rather than per-decision activ e measurements. Since the client and protocol are held fixed across candidates, T cli is constant across candidates and is omitted from the decision variable. W e e valuate the proposed T max -based policy against the following baselines. Each policy assigns a telemetry-based runtime estimate score i to candidate server i , and the client selects i ∗ = arg min i score i . The scores are defined as follows: ( T max ) score i = T srv ,i + T cc ,i + T ent ,i , (9) ( T min ) score i = max { T srv ,i , T cc ,i , T ent ,i } , (10) (Rank-sum) score i = X k ∈{ srv , cc , ent } rank( T k,i ) , (11) (W eighted-sum) score i = X k ∈{ srv , cc , ent } w k T k,i . (12) For W eighted-sum, we use Sobol-deriv ed weights (com- puted offline as described in Sec. V ). The weights w k are precomputed from the Sobol sensitivity analysis in Sec. V and then fixed across all instances. W e additionally include single-component indicators (serv er-side computational per - formance, classical communication latenc y , and entangle- ment distribution rate) and a random policy as simple ref- erence baselines. T able 2 summarizes the per-decision com- plexity and additional learning requirements. T ABLE 2. Decision-time complexity and additional learning for selection policies. M is the number of candidate ser vers . All policies assume access to { T srv , T cc , T ent } . Weighted-sum additionally requires offline calibr ation to obtain w . Policy per -decision complexity additional learning T min O ( M ) , linear scan none T max O ( M ) , linear scan none Rank-sum O ( M log M ) , sorting none W eighted-sum O ( M ) , linear scan weight calibration Practical ov erhead beyond per-decision comple xity T able 2 shows that both T max and W eighted-sum can be e val- uated in O ( M ) time at decision time. The practical differ - ence is that W eighted-sum requires an offline, deployment- specific calibration step to determine the weight v ector w (e.g., from assumed operating priors or from labeled runs), and the benefit of calibrated weights can diminish when the candidate population or network conditions shift (Sec. IV -D and Appendix D ). In contrast, T max uses coarse telemetry di- rectly with no per -deployment weight calibration, making it a robust default when operating conditions are heterogeneous or time-varying. Rationale f or T max Because the de gree of ov erlap among T srv , T cc , and T ent depends on protocol details and runtime conditions (e.g., scheduling and jitter), it is generally not predictable from coarse-grained telemetry alone. W e therefore use the fully- serialized proxy T max as a conservati ve, tuning-free ranking score: it is e xact under serialized ex ecution and remains monotone in each latency component, which makes it robust under bottleneck switching (Sec. IV -C ). In contrast, T min corresponds to a perfectly-overlapped optimistic extreme and is included only as a reference baseline. C. BO TTLENECK SWITCHING W e define two reference configurations using the endpoints of the baseline ranges in T able 1 . The light configura- tion is ( d min , R max , κ min ) , and the heavy configuration is ( d max , R min , κ max ) . From each reference configuration, we sweep one parameter at a time o ver a two-decade span (from 0 . 1 × the light endpoint to 10 × the heavy endpoint) while fixing the other two. W e report the execution time for a 10 - shot job . The sweeps in Fig. 3 show bottleneck switching in T exe . Increasing R reduces T ent = K /R until another component limits T exe (plateau) (Fig. 3a ). Increasing d raises T cc ∝ d , yielding a plateau-to-linear crosso ver once classical com- munication dominates (Fig. 3b ). Increasing κ raises T srv 5 Nagai et al. : T elemetr y Based Ser ver Selection in the Quantum Internet via Cross-Lay er Runtime Estimation 100 1000 10000 R [ H z ] 200 500 1000 2000 5000 T e x e [ m s ] Light configuration Heavy configuration (a) Entanglement distribution rate ( R ) 10 100 1000 10000 d [ k m ] 200 500 1000 2000 5000 T e x e [ m s ] (b) Distance ( d ) 0.1 1 10 200 500 1000 2000 5000 T e x e [ m s ] (c) Operation-duration scaling factor ( κ ) FIGURE 3. Bottleneck s witching in T exe illustrated by one-dimensional s weeps of R , d , and κ around the light/heavy ref erence configurations in T able 1 ( S = 10 shots). Plateaus and crossov ers indicate transitions among T ent , T cc , and T srv . and produces an analogous crossover when server execution dominates (Fig. 3c ). These crosso vers sho w that the dominant latenc y compo- nent shifts across operating conditions, so ranking based on any single component is not consistent across regimes. W e therefore ev aluate multi-component telemetry-based ranking in the following e xperiments. D . RESUL TS Even regime W e report mean oracle-normalized regret (Sec. IV -A ) over 1,500 instances for each M , with 95% bootstrap confidence intervals (CIs) o ver instances. In the Even regime, T srv , T cc , and T ent are of comparable magnitude, so no single component consistently dominates end-to-end runtime and the selection policy must trade off all three components. By construction, the Even-re gime ranges in T able 1 also straddle the classical–entanglement crossover T cc = T ent (Fig. 7 ), which induces bottleneck switching across candidates and makes ranking nontrivial. The W eighted-sum policy yields the lowest regret across M , with a mean re gret of about 6% (Fig. 4 ). The T max policy performs second best and maintains single-digit regret without weight calibration. Both T min and Rank-sum yield higher regret. Overall, the results confirm that explicitly combining the latenc y components is essential for robust selection in the Ev en regime. W e additionally confirm that T max is strongly rank- correlated with T exe in the Ev en-regime pool (Spearman ρ = 0 . 85 , Appendix B ). Bottleneck-dominated regimes T o probe bottleneck-dominated settings, we construct three regimes by scaling one parameter by a factor of 10 while holding the other two unchanged: we multiply κ by 10 (server-computation-dominated), multiply d by 10 (classical communication-dominated), and di vide R by 10 (entanglement-dominated). Regret across these regimes as a function of M is summarized in Fig. 5 . 0 20 40 60 80 100 N c a n d [ c o u n t ] 0 2 4 6 8 10 12 14 Regret Rate [%] T m a x W eighted-sum Rank-sum T m i n FIGURE 4. Mean oracle-nor malized regret of server selection policies in the Even regime as a function of the number of candidate servers M . Shaded bands indicate 95% bootstrap confidence intervals. The T max policy achiev es the lo west mean regret (about 5%) across the three bottleneck-dominated regimes. W eighted-sum and T min yield comparable regret but are consistently higher than T max . Notably , T max outperforms the regime-trained W eighted- sum policy in all three bottleneck regimes, despite the latter behaving almost identically to T min . While a 10 × scaling makes one component dominant on av erage, the top candi- dates often exhibit near-ties on the dominant term, so re gret is decided by the remaining delays. T max remains sensitive to these secondary contributions, whereas a bottleneck-focused scalarization can suppress them and misorder near-optimal servers. Robustness to tempor al fluctuations T o e valuate robustness, we augment the propagation-limited one-way latency in optical fiber with an additiv e per-message jitter term. F or each one-w ay classical message on the critical 6 Nagai et al. : T elemetr y Based Ser ver Selection in the Quantum Internet via Cross-Lay er Runtime Estimation 20 40 60 80 100 # of server candidates 5 10 15 20 Regret Rate [%] T m a x W eighted-sum T m i n (a) T ent -dominated 20 40 60 80 100 # of server candidates 5 10 15 20 Regret Rate [%] (b) T cc -dominated 20 40 60 80 100 # of server candidates 5 10 15 20 Regret Rate [%] (c) T srv -dominated FIGURE 5. Oracle-normalized regret of server-selection policies in bottleneck-dominated regimes v ersus the number of candidate servers M . Shaded bands indicate 95% bootstrap confidence intervals. F or visual clarity , we omit the Rank-sum baseline, whose regret is substantially larger and would compress the scale; the full curves including Rank-sum are repor ted in Appendix C (Fig. 11 ). path, we model t cc = d v fiber + J, (13) where d is the channel length, v fiber ≈ 2 × 10 5 km / s , and J ≥ 0 is resampled for ev ery message. W e use an exponential jitter model J ∼ Exp( µ J ) , (14) with mean µ J (i.e., Exp( µ ) denotes an exponential distribu- tion with mean µ ). W e parameterize µ J by the 0 . 999 -quantile q 0 . 999 of J : q 0 . 999 = µ J ln(1000) . (15) Let n cc denote the number of one-way classical messages on the critical path. F or an S -shot e valuation, the total jitter is J tot = N X i =1 J i for N = n cc S. (16) Under the e xponential model, the coef ficient of v ariation of J tot scales as 1 / √ n cc S , so increasing S reduces the relativ e impact of temporal v ariability on ranking under the same q 0 . 999 . W e consider two representativ e settings that reflect differ- ent operational conditions: (i) Lo w (managed control-plane), q 0 . 999 = 0 . 5 ms , and (ii) High (cross-domain and contended), q 0 . 999 = 20 ms . T emporal variability in classical communication latenc y degrades server selection performance, and the extent of the degradation depends on the shot count (Fig. 6 ). In the high-jitter setting (panel (a), q 0 . 999 = 20 ms ), W eighted-sum generally attains lower regret than T max for both S = 10 (solid) and S = 1 (dashed), while the gap remains modest and T max remains close to the W eighted- sum curve. Ho wev er , under the same high-jitter condition, the single-shot case ( S = 1 ) exhibits substantial degradation as M increases, reaching approximately 40% at M = 100 for both policies. In this failure regime, the two curves tend to 0 20 40 60 80 100 # of server candidates 10 20 30 40 50 Regret Rate [%] T m a x ( s h o t s = 1 0 ) W eighted (shots=10) T m a x ( s h o t s = 1 ) W eighted (shots=1) (a) High jitter ( q 0 . 999 = 20 ms ) 0 20 40 60 80 100 # of server candidates 2 4 6 8 10 Regret Rate [%] T m a x ( s h o t s = 1 0 ) W eighted (shots=10) T m a x ( s h o t s = 1 ) W eighted (shots=1) (b) Low jitter ( q 0 . 999 = 0 . 5 ms ) FIGURE 6. Oracle-normalized regret of T max and Weighted-sum under classical communication latency jitter versus the n umber of candidate ser vers M . Solid/dashed cur ves correspond to S = 10 and S = 1 . con ver ge, indicating reduced rankability from static teleme- try under lar ge message-le vel fluctuations. By contrast, in the low-jitter setting (panel (b), q 0 . 999 = 0 . 5 ms ), regret remains in the single-digit range and is only weakly sensitiv e to S , suggesting that such managed control-plane jitter has limited 7 Nagai et al. : T elemetr y Based Ser ver Selection in the Quantum Internet via Cross-Lay er Runtime Estimation impact on ranking. The pronounced S -dependence visible in panel (a) is consistent with the coef ficient-of-variation scaling 1 / √ n cc S of J tot under the exponential jitter model. W eight Calibration f or T elemetry-Based Ranking W eighted-sum T w = P k ∈{ srv , cc , ent } w k T k generalizes T max (uniform w ). Here w is derived from a Sobol sensitivity analysis from the assumed priors, computed of fline and fixed (see Appendix D for details). In the Even regime, W eighted- sum attains the lo west re gret ( ∼ 6%), while T max remains single digit without tuning (Fig. 4 ). In bottleneck-dominated regimes, where one component consistently dri ves the end- to-end latency , T max achiev es the lowest regret ( ∼ 5%; Fig. 5 ). Under high classical-communication latency jitter , W eighted-sum is only marginally better , and in a single shot, both degrade strongly (Fig. 6 ). Because the weights depend on the assumed priors, changes in operating conditions can reduce the benefit and may require recalibration. Thus, T max is the robust default, whereas calibrated weighting is an optional refinement. V . BOTTLENECK IDENTIFICA TION A. REQUIREMENT -BASED OPERA TING MAP AND DIST ANCE ENVELOPES The e valuation in Sec. IV -A samples ( d, R , κ ) independently to represent heterogeneous candidate servers and network- service conditions. T o connect these sweep ranges to deploy- ment scenarios and to generalize beyond a single benchmark instance, we deri ve a requirement-based operating map in the ( d, R ) plane using the protocol-level scalars ( n cc , K ) defined in Sec. III . In practical fiber links, the achiev able end-to-end entanglement supply rate generally decreases with distance due to loss and is constrained in the repeaterless setting by fundamental rate–loss tradeoffs [ 30 ], [ 31 ]. Repeater design and network planning tools provide complementary guid- ance on feasible operating regions [ 32 ], [ 33 ]. Because the latency components scale linearly with the shot count S when ( n cc , K ) are fixed per shot, the regime boundaries below are independent of S and apply to both S = 1 and multi-shot jobs. Classical–entanglement crossov er boundar y From Sec. III and the propagation-limited latency model in Sec. IV -A , the feedforward delay and entanglement distribu- tion time can be written directly as T cc = n cc d v fiber , T ent = K R . (17) The crossov er boundary T cc = T ent yields the required entanglement distribution rate R bal ( d ) = K v fiber n cc d . (18) Abov e this boundary ( R ≫ R bal ( d ) ), entanglement distri- bution is fast enough that feedforward latency tends to dom- inate. Below it ( R ≪ R bal ( d ) ), entanglement distribution 1 0 1 1 0 2 1 0 3 1 0 4 C h a n n e l l e n g t h d [ k m ] 1 0 1 1 0 2 1 0 3 1 0 4 E n t a n g l e m e n t d i s t r i b u t i o n r a t e R [ H z ] U = 1 : T c c = T e n t U = 5 : T c c = T e n t U = 2 0 : T c c = T e n t Even regime d = 3 7 9 R = 5 2 7 FIGURE 7. Requirement-based operating map in the ( d, R ) plane f or PB-VQE. The diagonal lines show the classical–entanglement crossov er T cc = T ent given b y R ( U ) bal ( d ) = U R bal ( d ) = U v fiber /d (here K = n cc = 5 ), for diff erent multiuser sharing lev els U under R eff = R/U ( U = 1 , 5 , 20 ). The red box indicates the Even-regime range (T able 1 ). The blac k dashed lines indicate the compute–network crossovers (Eqs . ( 22 ) – ( 23 ) ). The blac k dot marks the κ = 1 balance point where T srv ≈ T cc ≈ T ent . lies on the critical path. Equiv alently , for a network that can provide an end-to-end rate R , the distance at which the classical and entanglement components become comparable is d bal ( R ) = K v fiber n cc R . (19) B. PB-VQE INST ANTIA TION AND MUL TIUSER SCALING Operating map and PB-VQE instantiation Fig. 7 visualizes the resulting ( d, R ) operating map for PB- VQE and highlights how the ev aluation ranges (T able 1 ) and the Sobol priors (T able 3 ) cover distinct bottleneck re gimes. For our PB-VQE benchmark, K = n cc = 5 , hence R bal ( d ) = v fiber /d . W ith v fiber ≈ 2 × 10 5 km / s and d in km, R bal ( d ) ≈ 2 × 10 5 d Hz . (20) Notably , the Even-regime ranges in T able 1 ( d ∈ [100 , 1000] km and R ∈ [200 , 2000] Hz ) are centered around ( 20 ), intentionally straddling the T cc – T ent crossov er to stress- test selection under bottleneck switching. In our benchmark, the telemetry-based approximation in Eq. ( 8 ) yields the per- shot components T srv ≈ 9 . 48 κ ms , T cc ≈ 0 . 025 d ms , T ent ≈ 5000 R ms , (21) with d in km and R in Hz. These yield simple crosso ver conditions: T srv = T cc ⇒ d ≈ 379 κ km , (22) T srv = T ent ⇒ R ≈ 527 κ Hz . (23) 8 Nagai et al. : T elemetr y Based Ser ver Selection in the Quantum Internet via Cross-Lay er Runtime Estimation These relations provide a compact interpretation of when server -side acceleration (smaller κ ) versus network-layer provisioning (lar ger R or smaller d ) most ef fectiv ely reduces end-to-end runtime. These boundaries giv e quick deployment checks for PB-VQE: (i) compare R to R bal ( d ) to determine whether T ent or T cc lies on the critical path, and (ii) compute becomes limiting only when both network components are faster than the server , i.e., approximately d ≲ 379 κ and R ≳ 527 /κ . Multiuser contention and load balancing In a multiuser (multi-client) setting, shared resources effec- tiv ely rescale the parameters in the same operating map. As a simple contention model, if U clients share the entanglement distribution service along the rele vant path, we approximate the effecti ve rate per client as R eff = R/U . Under this model, the classical–entanglement crossover boundary scales linearly with concurrency , R ( U ) bal ( d ) = U R bal ( d ) , (24) which corresponds to a vertical shift of the boundary (cf. Fig. 7 ). Fig. 7 visualizes this shift: increasing U mo ves the T cc = T ent boundary upward by a factor of U , so an operat- ing point near the κ = 1 balance point (black dot) becomes effecti vely more entanglement-limited unless the provisioned rate R scales proportionally . Similarly , contention for server - side compute can be captured by an effecti ve slo wdown (e.g., an increased κ eff estimated from telemetry), which expands compute-limited regions. These scalings imply that load- aware telemetry (e.g., moving-av erage estimates of R eff and κ eff ) can be incorporated into the same T max score with low ov erhead, enabling load-aware server ranking without run- time retuning. This abstraction is consistent with the view that link-layer policies and scheduling determine the realized entanglement service rate under competing demands [ 19 ], [ 20 ], [ 34 ]. Conv ersely , if entanglement resources are pro- visioned per client (so R eff ≈ R ), compute contention on a shared server can dominate. This can be captured as an increased κ eff estimated from telemetry . C. REGIME MAP OF DOMINANT BOTTLENECKS AND DEPLO YMENT IMPLICA TIONS W e provides an analytic operating map that compares the two network-side components ( T cc and T ent ) in the ( d, R ) plane in Fig. 7 . Howe ver , end-to-end runtime depends jointly on ( κ, d, R ) and on implementation-dependent overlap among server e xecution and network processes. T o visualize regime-dependent sensitivity be yond the ana- lytic comparison, we estimate total-ef fect indices locally on the log-spaced grid used in Fig. 8 , ov er parameter ranges in T able 3 . Specifically , we partition the ( κ, d, R ) space into log- spaced cells and, for each cell, dra w Saltelli samples within the cell to estimate ( S T ,κ , S T ,d , S T ,R ) . Each color indicates the input with the largest total-ef fect index for runtime. The Sobol total-effect indices for runtime are summarized in Fig. 8 . Colors indicate the parameter with the lar gest total- T ABLE 3. Sobol sensitivity-analysis inputs (independent log-uniform pr iors) and the log-space discretization in Fig. 8 . We use e xpanded ranges der ived from the Even-regime endpoints in T able 1 b y scaling the lower (upper) endpoint by 0 . 1 ( 10 ). Parameter Range Operation-duration scaling factor κ 0 . 0263 – 26 . 3 Entanglement distribution rate R 20 – 20 , 000 Hz Channel length d 10 – 10 , 000 km effect inde x. The dominant constraint shifts across operating regimes. At short channel lengths, the runtime is primarily limited by the entanglement distribution rate R . At long channel lengths, classical communication latency T cc ov er fiber dominates. T cc scales with channel length d and the number of one-way classical communication messages n cc on the critical path, reaching tens to hundreds of ms for intercontinental links. d [km] R [Hz] 20 20000 200 2000 10 100 1000 10 0.0263 0.263 2.63 26.3 d [km] R [Hz] Dominant Facto r FIGURE 8. Dominant-factor map of Sobol total-eff ect sensitivity . Colors indicate the parameter with the largest total-eff ect index f or runtime. Axes are ( κ, d, R ) in log space over the ranges in T able 3 . In entanglement-limited regimes, the total-ef fect index for R dominates, as expected from T ent = K/R on the critical path. In this region, impro ving the entanglement distribu- tion service (larger R at the required fidelity) yields the largest runtime reductions. In long-haul regimes, the total- effect index for d dominates, consistent with feedforw ard latency T cc = n cc d/v fiber becoming limiting. In intermediate regimes where T srv becomes comparable, improving server- side execution (smaller κ ) and network-layer pro visioning (larger R or smaller d ) become substitutable levers. These regime-dependent priorities also help interpret why the additiv e score T max yields robust selection perfor - 9 Nagai et al. : T elemetr y Based Ser ver Selection in the Quantum Internet via Cross-Lay er Runtime Estimation mance in Sec. IV : the sum is monotone in each latency component and is dominated by the bottleneck term in bottleneck-dominated regimes, while still providing a simple, calibration-free scalarization of cross-layer trade-offs near crossov er boundaries. VI. CONCLUSION W e address application-layer server selection for Quan- tum Internet applications whose end-to-end runtime cou- ples server execution, feedforward classical latency , and entanglement supply , with protocol-dependent overlap and regime-dependent bottleneck switching. W e proposed the lightweight telemetry-based score T max for conservati ve on- line ranking and, using large-scale NetSquid discrete-ev ent simulations of an implementation-oriented PB-VQE bench- mark, showed that T max achiev es consistently low oracle- normalized regret across crossover and bottleneck-dominated regimes, including temporal jitter scenarios. Beyond selection accuracy , Sec. V -A deriv es a requirement-based operating map in the ( d, R ) plane and simple distance env elopes that relate network requirements to protocol-level counts, while Sec. V -B translates these regimes into provisioning implications: which telemetry matters most in each region and ho w multi-user contention shifts the classical–entanglement boundary via R eff = R/U . Finally , Sec. V -C complements the analytic map with a regime map of dominant bottlenecks (Fig. 8 ) via local Sobol total-effect indices, indicating which telemetry dimension ( d , R , or κ ) is the most ef fective lever in each operating re gion. T ogether, these results provide both a practical selection rule and interpretable deployment guidance for emer ging Quantum Internet services. LIMIT A TIONS AND OUTLOOK T o keep client-side decision overhead low , we assume ac- cess to coarse-grained telemetry on server-side computa- tional performance, classical communication latency , and entanglement-distribution rate. Our simulations focus on a single active client and omit queuing delays and multi-client contention. W e also treat the application-lev el accuracy con- straint as a precondition on the candidate set. An important direction for future work is to de velop probabilistic and load- aware predictors that capture temporal correlations, schedul- ing, and contention in multi-client deployments. . APPENDIX A IMPLEMENT A TION-ORIENTED PB-VQE This appendix specifies the modified PB-VQE benchmark used in Sec. IV , including the protocol-dependent counts ( n cc , K ) on the critical path. A. PRO T OCOL DESIGN The parameter-blind VQE (PB-VQE) protocol is a client– server v ariant of VQE, in which the server al ways ex ecutes a fixed, parameter-independent circuit. In contrast, the client updates the variational parameters based on measurement outcomes [ 16 ]. This ensures that the variational parameters remain hidden from the server , thereby achieving parameter blindness with significantly reduced communication com- pared to con ventional blind quantum computation (BQC) protocols such as BFK [ 11 ] or MF [ 12 ]. W e propose a modified PB-VQE protocol, tailored for implementation over the Quantum Internet. W e inte grate quantum teleportation to improve robustness against channel loss. W e add four ancilla-driv en computations to correct teleportation byprod- ucts and preserve parameter blindness (Fig. 9 ). This modi- fication increases the feasibility of the protocol in realistic, lossy network conditions. Ancilla-driv en (AD) decomposi- tion consumes one Bell pair and incurs one one-way feed- forward classical message (the Bell-measurement outcomes) per block, we have n cc = K = 5 per shot. Tracing the server - side critical path of the fixed circuit instance in Fig. 9 yields T srv ≈ 9 . 48 ms per shot. + + + + Ancilla-Driven ( ) Entanglement Distribution AD ( 0""""𝜋 ) Byproduct Correction AD ( 0""""𝜋 ) AD ( 0 ) AD ( 0""""𝜋 ) s1 s2 s3 s4 c1 s3 s4 c1 s2 Result info. 𝐵𝑃 𝐵𝑃 𝐵𝑃 or or or 𝐵𝑃 𝐵𝑃 𝐵𝑃 FIGURE 9. Modified parameter-blind VQE circuit (top) and ancilla-driven gate decomposition (bottom). Server qubits are labeled s1–s4, and c1 is a client ancilla for teleportation and byproduct (BP) correction [ 35 ]. Measurement labels θ and 0/ π denote the angles chosen at each step. B. MEASUREMENT UPD A TE POLICY In the modified PB-VQE protocol (Fig. 9 ), the server exe- cutes a fixed circuit AD( θ ) → AD(0/ π ) → AD(0/ π ) → AD(0) → AD(0/ π ), while the client updates the measurement angles and measures the ancilla after each block (labeled 1–5). At 0/ π stages, the angle is set to either 0 or π . Each ancilla- driv en step applies, conditioned on the ancilla outcome b , the operation ( X b ) H R z ( α ) to the register . Quantum teleportation produces two Bell-measurement bits ( z , x ) , which induce the Pauli byproduct Z z X x . The measurement angle is updated in the Pauli frame as α 7→ ( − 1) x α + z π (mo d 2 π ) . (25) This corresponds to the byproduct correction in Fig. 9 . For the fiv e ancilla-dri ven (AD) blocks, the measurement 10 Nagai et al. : T elemetr y Based Ser ver Selection in the Quantum Internet via Cross-Lay er Runtime Estimation angle θ t is set according to the gate type: θ t = θ for AD ( θ ) , π m for AD (0 /π ) , 0 for AD (0) , (26) where m ∈ { 0 , 1 } is the measurement outcome from the previous step. This explicit update rule ensures that byproducts are cor - rected consistently at ev ery stage. W ith these corrections in place, we analyze the blindness properties of the modified PB-VQE protocol. C. BLINDNESS PROPER TIES P arameter b lindness A single ancilla-dri ven circuit produces one classical bit m ∈ { 0 , 1 } . Conditional on m , the register under goes one of the two gates U 0 = H R z ( θ ) , U 1 = X H R z ( θ ) . (27) For the Fig. 9 ancilla-driven decomposition (ancilla initial- ized in | 0 ⟩ ), the register Kraus operators are K 0 = 1 √ 2 H R z ( θ ) , K 1 = 1 √ 2 H Z R z ( θ ) = 1 √ 2 X H R z ( θ ) , (28) so p ( m ) = T r( K m ρK † m ) = 1 2 and the server must av erage uniformly ov er the hidden m . Let ρ be the register state immediately before the ancilla-dri ven circuit step. From the server’ s point of view (the measurement outcome m is hidden), the post-measurement state is ρ srv = 1 2 U 0 ρU † 0 + U 1 ρU † 1 = 1 2 H R z ( θ ) ρ + Z ρZ R † z ( θ ) H † . (29) The prefactor 1 2 ( ρ + Z ρZ ) commutes with Z . Since R z ( θ ) = e − iθZ / 2 is generated by Z , it follows that R z ( θ ) ρ + Z ρZ R † z ( θ ) = ρ + Z ρZ, (30) ρ srv = 1 2 H ρ + Z ρZ H † . (31) is independent of θ , and no PO VM applied by the server can rev eal any information about the variational parameter . W e thus obtain parameter blindness. Output blindness Immediately before the final computational-basis measure- ment, we apply tw o consecuti ve ancilla-dri ven steps. Let E θ denote the ef fectiv e single-step channel in the server’ s reduced description, obtained by averaging over the unknown Pauli byproduct Z b with b ∈ { 0 , 1 } : E θ ( ρ ) = 1 2 H R z ( θ ) ρ + Z ρZ R † z ( θ ) H † . (32) For ρ of the form 1 2 ( I + r x X + r y Y + r z Z ) , we have E θ ( ρ ) = 1 2 H R z ( θ ) I + r z Z R † z ( θ ) H † = 1 2 I + r z X , (33) which is independent of θ . Applying the same channel once more giv es E θ ( E θ ( ρ )) = 1 2 H R z ( θ ) E θ ( ρ ) + Z E θ ( ρ ) Z R † z ( θ ) H † = I 2 . (34) Thus, two hidden steps implement the completely depolar- izing channel on each qubit from the server’ s perspectiv e. Applying this to all n qubits yields ρ final = I 2 n (35) for any input ρ in . Therefore, the server cannot distinguish the logical output or any intermediate branch of the computation, and output blindness holds. APPENDIX B V ALIDITY OF TELEMETR Y-BASED PREDICT ORS W e compute Spearman’ s rank correlation coef ficient between each telemetry-based estimate and the simulated ex ecution time T exe ov er the even-re gime pool. Spearman’ s rank cor- relation is ρ = 0 . 85 for T max and ρ = 0 . 79 for T min (Fig. 10 ). The higher coef ficient for T max suggests a stronger 1 0 2 1 0 3 Estimated runtime [ms] 1 0 2 1 0 3 S i m u l a t e d r u n t i m e T e x e [ m s ] T m a x T m i n y = x FIGURE 10. Spear man’ s rank correlation between telemetry-based runtime estimates and the simulated e xecution time T exe ov er 2000 server configurations sampled from the e ven-regime pool (T able 1 ). Both ax es are on logarithmic scales. The rank correlation is ρ = 0 . 85 for T max and ρ = 0 . 79 for T min . monotonic relationship with T exe in this setting. Selection performance is ev aluated directly in Sec. IV . APPENDIX C FULL BO TTLENECK-DOMINA TED REGRET CUR VES INCLUDING RANK-SUM In Fig. 5 , we omit the Rank-sum baseline for readability because its regret is substantially larger than the other poli- cies in bottleneck-dominated re gimes, which w ould other- wise compress the vertical scale and obscure the differences among T max , T min , and W eighted-sum. Fig. 11 reports the full curves including Rank-sum for completeness. 11 Nagai et al. : T elemetr y Based Ser ver Selection in the Quantum Internet via Cross-Lay er Runtime Estimation 20 40 60 80 100 # of server candidates 20 40 60 80 Regret Rate [%] T m a x W eighted-sum Rank-sum T m i n (a) T ent -dominated 20 40 60 80 100 # of server candidates 20 40 60 80 Regret Rate [%] (b) T cc -dominated 20 40 60 80 100 # of server candidates 20 40 60 80 Regret Rate [%] (c) T srv -dominated FIGURE 11. Oracle-normalized regret of server-selection policies in bottleneck-dominated regimes v ersus the number of candidate servers M . Shaded bands indicate 95% bootstrap confidence intervals. APPENDIX D SOBOL T O T AL-EFFECT INDICES W e identify bottlenecks using variance-based global sensitiv- ity analysis with Sobol indices [ 24 ]. W e use Sobol analysis as a screening tool and report total-ef fect indices, which provide a conservati ve ranking of influential inputs when the inputs are treated as independent. Let Y be the output metric and X = ( X 1 , . . . , X p ) the inputs. Denote by X ∼ i = ( X 1 , . . . , X i − 1 , X i +1 , . . . , X p ) the set of all inputs except X i . The total-ef fect index for X i is S T i = 1 − V ar X ∼ i ( E [ Y | X ∼ i ]) V ar( Y ) . (36) W e draw samples using the Saltelli scheme [ 36 ] with quasi-random sampling o ver the log-uniform ranges sum- marized in T able 3 . W e use N = 128 base samples in the Saltelli design. Each sample fixes the server-side operation- duration scaling factor κ , channel length d , and entanglement distribution rate R . For each configuration, we run PB-VQE and record runtime, then estimate S T i . W e set the output as the S -shot end-to-end runtime Y = T exe and choose the Sobol inputs as X = ( κ, d, R ) , which correspond directly to the three latency compo- nents ( T srv , T cc , T ent ) through the runtime decomposition in Sec. IV -A . W e interpret the corresponding total-ef fect indices as S T , srv , S T , cc , and S T , ent , and use them to form an offline- calibrated weight vector for the W eighted-sum baseline in Sec. IV -B : ( w srv , w cc , w ent ) = ( S T , srv , S T , cc , S T , ent ) S T , srv + S T , cc + S T , ent . (37) These weights are fixed across all instances to k eep the online decision-time ov erhead minimal. D A T A AND CODE A V AILABILITY All NetSquid simulation codes, configuration files, and anal- ysis notebooks are publicly accessible at https://github .com/ masakivv/Serv er- Selection- in- the- Quantum- Internet.git . REFERENCES [1] P . W . Shor, “ Algorithms for quantum computation: discrete logarithms and factoring, ” in Pr oceedings 35th annual symposium on foundations of computer science . Ieee, 1994, pp. 124–134. [2] L. K. Grov er, “ A fast quantum mechanical algorithm for database search, ” in Pr oceedings of the twenty-eighth annual ACM symposium on Theory of computing , 1996, pp. 212–219. [3] S. W ehner, D. Elkouss, and R. Hanson, “Quantum internet: A vision for the road ahead, ” Science , vol. 362, no. 6412, p. eaam9288, 2018. [4] H. J. Kimble, “The quantum internet, ” Nature , vol. 453, pp. 1023–1030, 2008. [Online]. A vailable: https://doi.org/10.1038/nature07127 [5] C. Simon, “T owards a global quantum network, ” Nature Photonics , vol. 11, pp. 678–680, 2017. [Online]. A vailable: https://doi.org/10.1038/ s41566- 017- 0032- 0 [6] C. H. Bennett, G. Brassard, C. Crépeau, R. Jozsa, A. Peres, and W . K. W ootters, “T eleporting an unknown quantum state via dual classical and Einstein-Podolsky-Rosen channels, ” Phys. Rev . Lett. , vol. 70, pp. 1895– 1899, 1993. [7] H.-J. Briegel, W . Dür , J. I. Cirac, and P . Zoller, “Quantum repeaters: The role of imperfect local operations in quantum communication, ” Phys. Rev . Lett. , vol. 81, pp. 5932–5935, 1998. [8] J.-L. Liu, X.-Y . Luo, Y . Y u, C.-Y . W ang, B. W ang, Y . Hu, J. Li, M.-Y . Zheng, B. Y ao, Z. Y an et al. , “Creation of memory–memory entanglement in a metropolitan quantum network, ” Nature , v ol. 629, no. 8012, pp. 579– 585, 2024. [9] G. A vis, F . Ferreira da Silva, T . Coopmans, A. Dahlberg, H. Jirovská, D. Maier, J. Rabbie, A. T orres-Knoop, and S. W ehner , “Requirements for a processing-node quantum repeater on a real-world fiber grid, ” npj Quantum Inf. , vol. 9, no. 1, p. 100, 2023. [10] F . F . da Silva, G. A vis, J. A. Slater, and S. W ehner , “Requirements for upgrading trusted nodes to a repeater chain over 900 km of optical fiber , ” Quantum Sci. T echnol. , v ol. 9, no. 4, p. 045041, 2024. [11] A. Broadbent, J. Fitzsimons, and E. Kashefi, “Universal blind quantum computation, ” in Proc. 50th Annu. IEEE Symp. F ound. Comput. Sci. (FOCS) . IEEE, 2009, pp. 517–526. [12] T . Morimae and K. Fujii, “Blind quantum computation protocol in which Alice only makes measurements, ” Phys. Rev . A , vol. 87, no. 5, p. 050301, 2013. [13] P . J. J. O’Malley , R. Babbush, I. D. Kivlichan, J. Romero, J. R. McClean, R. Barends, J. Kelly , P . Roushan, A. Tranter , N. Ding, B. Campbell, Y . Chen, Z. Chen, B. Chiaro, A. Dunsworth, A. G. Fo wler , E. Jef frey , E. Lucero, A. Megrant, J. Y . Mutus, M. Neeley , C. Neill, C. Quintana, D. Sank, A. V ainsencher , J. W enner, T . C. White, P . V . Coveney , P . J. Love, H. Ne ven, A. Aspuru-Guzik, and J. M. Martinis, “Scalable quantum simulation of molecular energies, ” Phys. Rev . X , vol. 6, no. 3, p. 031007, 2016. [14] A. Peruzzo, J. McClean, P . Shadbolt, M.-H. Y ung, X.-Q. Zhou, P . J. Love, A. Aspuru-Guzik, and J. L. O’brien, “ A variational eigenv alue solver on a photonic quantum processor , ” Nat. Commun. , vol. 5, no. 1, p. 4213, 2014. [15] J. T illy , H. Chen, S. Cao, D. Picozzi, K. Setia, Y . Li, E. Grant, L. W ossnig, I. Rungger, G. H. Booth et al. , “The variational quantum eigensolver: a 12 Nagai et al. : T elemetr y Based Ser ver Selection in the Quantum Internet via Cross-Lay er Runtime Estimation revie w of methods and best practices, ” Phys. Rep. , vol. 986, pp. 1–128, 2022. [16] Y . Shingu, Y . T akeuchi, S. Endo, S. Kawabata, S. W atabe, T . Nikuni, H. Hakoshima, and Y . Matsuzaki, “V ariational secure cloud quantum computing, ” Phys. Rev . A , vol. 105, no. 2, p. 022603, 2022. [17] S. Muralidharan, L. Li, J. Kim, N. Lütk enhaus, M. D. Lukin, and L. Jiang, “Optimal architectures for long distance quantum communication, ” Sci. Rep. , vol. 6, no. 1, p. 20463, 2016. [18] Y . Lee, W . Dai, D. T owsley , and D. Englund, “Quantum netw ork utility: A framew ork for benchmarking quantum networks, ” Proc. Natl. Acad. Sci. U.S.A. , v ol. 121, no. 17, p. e2314103121, 2024. [19] A. Dahlberg, M. Skrzypczyk, T . Coopmans, L. Wubben, F . Rozp ˛ edek, M. Pompili, A. J. Stolk, P . Pawełczak, R. Knegjens, J. de Oliv eira Filho, R. Hanson, and S. W ehner, “ A link layer protocol for quantum networks, ” in Pr oceedings of the A CM Special Interest Gr oup on Data Communication (SIGCOMM ’19) . A CM, 2019, pp. 159–173. [Online]. A vailable: https://doi.org/10.1145/3341302.3342070 [20] M. Pompili, C. D. Donne, I. te Raa, B. van der V echt, M. Skrzypczyk, G. Ferreira, L. de Kluijver , A. J. Stolk, S. L. N. Hermans, P . Pawełczak, W . K ozlowski, R. Hanson, and S. W ehner, “Experimental demonstration of entanglement delivery using a quantum network stack, ” npj Quantum Information , vol. 8, p. 121, 2022. [Online]. A vailable: https://doi.org/10.1038/s41534- 022- 00631- 2 [21] W . K ozlowski, A. Dahlber g, and S. W ehner , “Designing a quantum network protocol, ” in Pr oceedings of the 16th International Conference on Emerging Networking Experiments and T echnologies (CoNEXT ’20) . A CM, 2020. [Online]. A vailable: https://doi.org/10.1145/3386367. 3431293 [22] C. D. Donne, C. Dethier , R. V . Meter , and S. W ehner , “ An operating system for executing applications on quantum network nodes, ” Nature , vol. 639, pp. 321–328, 2025. [Online]. A vailable: https://doi.org/10.1038/s41586- 025- 08704- w [23] T . Coopmans, R. Knegjens, A. Dahlberg, D. Maier , L. Nijsten, J. de Oliveira Filho, M. Papendrecht, J. Rabbie, F . Rozp ˛ edek, M. Skrzypczyk et al. , “Netsquid, a network simulator for quantum infor- mation using discrete events, ” Communications Physics , vol. 4, no. 1, p. 164, 2021. [24] I. M. Sobol’, “On sensitivity estimation for nonlinear mathematical mod- els, ” Matematicheskoe modelir ovanie , vol. 2, no. 1, pp. 112–118, 1990. [25] Y . Ma, E. Kashefi, M. Arapinis, K. Chakraborty , and M. Kaplan, “Qenclav e - a practical solution for secure quantum cloud computing, ” npj Quantum Information , vol. 8, p. 128, 2022. [Online]. A vailable: https://doi.org/10.1038/s41534- 022- 00612- 5 [26] A. Dahlberg and S. W ehner, “Simulaqron—a simulator for dev eloping quantum internet software, ” Quantum Science and T echnology , vol. 4, no. 1, p. 015001, 2018. [Online]. A vailable: https://doi.or g/10.1088/2058- 9565/aad56e [27] X. Wu, A. K olar, J. Chung, D. Jin, T . Zhong, R. Kettimuthu, and M. Suchara, “Sequence: a customizable discrete-e vent simulator of quantum networks, ” Quantum Science and T echnology , vol. 6, no. 4, p. 045027, 2021. [Online]. A vailable: https://doi.org/10.1088/2058- 9565/ ac22f6 [28] S. DiAdamo, J. Nötzel, B. Zanger, and M. M. Be ¸ se, “Qunetsim: A software framework for quantum networks, ” IEEE T ransactions on Quantum Engineering , vol. 2, p. 2502512, 2021. [Online]. A vailable: https://doi.org/10.1109/TQE.2021.3092395 [29] IonQ, “IonQ Aria: Practical Performance, ” 2025, av ailable: https://ionq. com/resources/ionq- aria- practical- performance . Accessed: Sep. 30, 2025. [30] M. T akeoka, S. Guha, and M. M. Wilde, “Fundamental rate-loss tradeoff for optical quantum key distribution, ” Nature Communications , vol. 5, p. 5235, 2014. [Online]. A vailable: https://doi.org/10.1038/ncomms6235 [31] S. Pirandola, R. Laurenza, C. Ottaviani, and L. Banchi, “Fundamental limits of repeaterless quantum communications, ” Natur e Communications , vol. 8, p. 15043, 2017. [Online]. A vailable: https://doi.org/10.1038/ ncomms15043 [32] K. Azuma, S. Bäuml, T . Coopmans, D. Elkouss, and B. Li, “T ools for quantum network design, ” A VS Quantum Science , v ol. 3, no. 1, p. 014101, 2021. [Online]. A vailable: https://doi.org/10.1116/5.0024062 [33] K. Azuma, S. E. Economou, D. Elkouss, P . Hilaire, L. Jiang, H.-K. Lo, and I. Tzitrin, “Quantum repeaters: From quantum networks to the quantum internet, ” Reviews of Modern Physics , vol. 95, p. 045006, 2023. [Online]. A vailable: https://doi.org/10.1103/Re vModPhys.95.045006 [34] S. Khatri, “Policies for elementary links in a quantum netw ork, ” Quantum , vol. 5, p. 537, 2021. [Online]. A vailable: https://doi.or g/10.22331/q- 2021- 09- 07- 537 [35] J. Anders, D. K. Oi, E. Kashefi, D. E. Browne, and E. Andersson, “ Ancilla- driv en universal quantum computation, ” Phys. Rev . A , v ol. 82, no. 2, p. 020301, 2010. [36] A. Saltelli, P . Annoni, I. Azzini, F . Campolongo, M. Ratto, and S. T aran- tola, “V ariance based sensitivity analysis of model output. design and es- timator for the total sensiti vity index, ” Computer physics communications , vol. 181, no. 2, pp. 259–270, 2010. 13
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment