Symbol-Aware Precoder Design for Physical-Layer Anonymous Communications
Physical-layer characteristics, such as channel state information (CSI) and transmitter noise induced by hardware impairments, are often uniquely associated with a transmitter. This paper investigates transmitter anonymity at the physical layer from …
Authors: Yu Li, Milad Tatar Mamaghani, Xiangyun Zhou
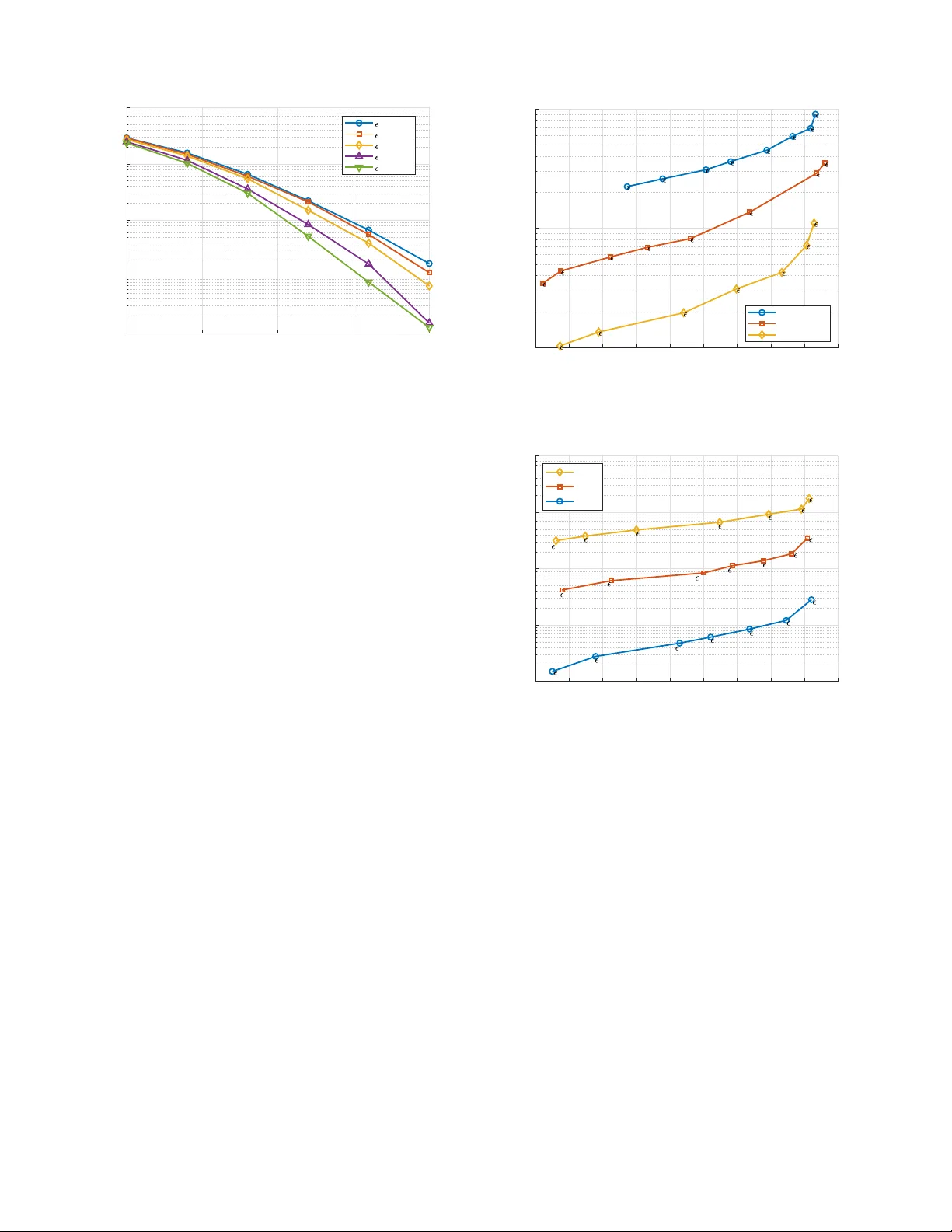
1 Symbol-A wa re Precoder Design for Physical-Layer Anonymous Communications Y u Li, Milad T atar Mamaghani, Xiangyun Zhou, F e llow , IEEE , and Nan Y ang, Senior Member , IEEE Abstract —Physical-lay er characteristics, such as channel state informa tion (CSI) and transmitter noise induced by hardware impairments, are often uniq uely associated with a transmitter . This paper inve stigates transmitter anonymity at the physical layer from a signal design p erspectiv e. W e consider an anony- mous communication problem where the recei ver should reliably decode the signal from the transmitter but shoul d not make use of the signal to infer the transmitter’s id entity . T ransmitter anonymity is quantified using a K u llback-Leibler div ergence (KLD)-based metric, which enables the f ormulation of explici t anonymity constraints in the precoder design. W e then propose an anonymous symbol-level precoding strategy that p reser ves re- liable communication under spatial multiplexin g while preve nting transmitter identification. T h e proposed framework empl oys a partitioned equal-gain combin ing (P-EGC) scheme that leverag es recei ver divers ity without requiring transmitter -specifi c CSI. Simulation results demonstrate anonymity-reliability t radeoffs acros s different signal-to-noise ratios (SNRs) an d nu mbers of data st reams. Moreov er , the results rev eal opposite trends of anonymity with respect to transmitter-dependent noise variations in the low-SNR and h igh-SNR regimes. Index T erms —Physical-layer an on ymous communications, symbol-lev el p recoding, MIMO, Kullback-Leibler diver gence I . I N T RO D U C T I O N T HE proliferation of next-generation wire less networks is reshapin g the lan dscape of co mmunicatio ns by en- abling a bro ad spectrum of Inter net of T hings (I oT) a p plica- tions, includin g vehicu lar network s, uncrewed aerial vehicle (U A V) comm unications, and bod y sensor systems [ 1 ]–[ 3 ]. While these advances offer un preceden ted connectivity , the broadc a st n ature of wir eless transmissions inheren tly exposes such systems to various secu rity threats such as eavesdrop- ping, jammin g, spoofing , an d traffic analysis [ 4 ]–[ 6 ]. Th e se vulnerab ilities are p articularly critical in human -centric IoT services, wh e re sensitive in formation , such as user id entities, locations, an d physiolog ical data, is rou tinely exchanged , and unautho rized disclosure may lead to severe priv acy violation s and safety r isks [ 7 ], [ 8 ]. Con ventional upper-layer secu rity mechanisms o f ten face practical limitations in I oT en vir o nments, due to stringent constraints o n power con su mption, compu tational cap ability , and latency [ 9 ]. In th is co ntext, physical- layer security (PLS) has em e rged as an effecti ve security e n hanceme n t by exploit- ing the in trinsic proper ties of wireless ch a nnels and transmit Y . Li, X. Z hou and N. Y ang are with the School of Engineering , the Australia n National Univ ersity , Canberr a, A CT 2601, Australia (e-mail: yu.li1@anu .edu.au; xiangyun.zhou@a nu.edu.au; nan.yang@anu.edu.au). Part of this work w as conducted while M. T atar Mamagh ani (e-mail: m i- lad.tat armamaghani @gmail.com) was previou sly with the Australian Nationa l Uni versity . T his work was supported by the Australian Research Council ’ s Discov ery Proje cts (DP220 101318). signals to provide lightweight and scalable protection, with out relying on computatio nally intensiv e and com plex crypto- graphic pr otocols. U n der th e gen eral um brella of PLS, two compleme n tary objectives can be identified: confi dentiality , which safeguards the transmitted content from u n authoriz e d access [ 10 ]–[ 12 ], a n d privacy , which p revents adversaries—or ev en legitimate parties—fro m infer ring sensitive user-related informa tio n, such as the iden tity o r even the existence of the transmitter, from the receiv ed signals. Priv acy-oriented tech - niques are gen erally de velope d under two different principles: anonymity a ims to conce a l th e transmitter ’ s id entity within a group of potential users [ 13 ], whereas u n observability seeks to hide the very existence of tr ansmissions, often th rough low- intercept-p robability commun ications su ch as covert commu- nications [ 14 ]. T r a nsmitter anonym ity is particularly critical in se veral emerging wireless applications. In vehicular systems, p eriodic beaconin g enab les safety-c r itical fu nctions, suc h as navigation and co llision av oidance, y et ro adside ad versaries can exp lo it physical-lay er signal ch a r acteristics to perf o rm p ersistent ve- hicle identification an d tr ajectory reconstru ction, even in the presence of pseud onym-based protoco ls [ 15 ], [ 16 ]. Similar vulnerab ilities ar ise in UA V comm unications, wh ere tran s- mitter id entification can expose mission-c r itical inform ation and en able trac king, jamm ing, or physical capture [ 17 ]–[ 19 ]. In b o dy a r ea networks, phy sical- layer identification by third - party b ase stations can further lin k sensitive p h ysiological data to individual users, leading to severe pr iv acy vio lations a n d potential commercial exploitation [ 20 ]. In these scenarios, th e physical-lay er signals often carry device-specific info r mation or location-d ependen t ch annel characteristics, which can be exploited for transmitter identification. There f ore, anonymity mechanisms oper ating above the ph y sical lay e r may n o longer be su fficient against adversar ies capable of exploiting ph ysical- layer feature s. This limitation motivates th e dev elopmen t of physical-lay er an onymity techniq ues that a im to mitiga te iden- tity leakage at the sign al level [ 21 ]. A. Related W orks In this work, we focu s on the analysis and design of physical-lay er anonymou s communication s. T his is a new topic of r esearch with only a hand ful of prio r works. The existing p hysical-layer a n onymity schem e s can be broad ly classified into st r ong- transmitter and str ong - r eceiver architec- tures, depending o n the relative number of tr ansmit an d receive antennas. In the strong -transmitter ca se, where the nu mber of transmit antennas exceeds that of the receiv e r, reliable 2 anonymou s commun ication can be achieved solely thr o ugh transmitter-side precod ing by exploiting the excess spatial degrees of freed om ( DoF) [ 22 ]. For this case, two classes of precod e r s have been developed: i) interfer ence-supp ression- based design s that employ transmitter-side pha se equ alization and ii) co nstructive-interference-b ased sy m bol-level preco d ers that steer signals into correct decision regions, thu s e liminating the need for explicit equalization at either the tr ansmitter or receiver . In con tr ast, the strong -receiver case, in w h ich receive antennas outnum ber tra nsmit a n tennas, r equires receiver - side combinin g to explo it the r eception diversity as the tr a nsmitter- side precoding alo ne is insu fficient to control the signal struc- ture across all r eceiv e antenn as [ 23 ], [ 24 ]. An early design for this case emp loyed ch annel-in depende nt equal-gain co mbining (EGC) with a single data stream to preserve anonymity un der heteroge n eous transmitter antenna configura tions [ 23 ]. More recently , [ 24 ] in vestigated the mu ltiplexing–diversity tradeo ff and in tr oduced alias-ch annel-b ased co mbiners to jointly ex- ploit spatial multiplexing and reception div ersity wh ile main - taining anonymity . Specifically , the combin e r was constructed from the av eraged channel responses of the true transmitter and multiple alias u sers, implicitly treating them as equally likely du ring receiver -side transmitter detectio n. While these works d iffer in transceiver stru cture an d signal processing design, they ad opt channel state informatio n (CSI) as the underly ing fe ature fo r transm itter identificatio n . Beyond CSI masking in [ 21 ]–[ 2 4 ], other ph ysical-layer character istics have been conside r ed. For in stance, join t ma sk ing of CSI and in - phase/quad rature (IQ) imbalan ce was explored as a means of enhancin g physical-layer an onymity in [ 25 ]. T o quantify physical-lay er an onymity , se veral perf o rmance metrics h av e b een e stablished in the literatur e. T he m ost common ly used metric is the detection erro r rate (DE R), which measures the probab ility that the recei ver fails to identify the activ e user . A larger DER indicates a higher lev el of anonymity . Complementarily , an onymity entropy was propo sed to characterize the receiver’ s u n certainty regard ing the transmitter id entity in a manner analo gous to Shanno n entropy [ 23 ], [ 26 ]. More gen eral analytical frameworks b ased on de te c tion-erro r expon e nts and di vergence-based measures were intr o duced in [ 13 ], while closed-f o rm DER expressions for specific systems were de riv ed in [ 24 ], [ 26 ], [ 27 ]. These metrics p rovide a pr incipled basis f or analy zing anonymity perfor mance an d the fu ndamen ta l trad e o ff between ano nymity and commun ication reliability . Despite the merits of the afor e mentioned works, two impor- tant limitation s still remain in the existing literatu re. First, to the best of our kn owledge, all existing anonym ous precodin g designs assume homogeneou s transmitter noise statistics across users, a nd hence n eglect user-dependent distortion due to hardware impairments, which creates user-dependen t noise statistics at the receiver that can be used f o r identification. Second, existing transmitter identification mod els are symbol- unaware , implicitly assuming that the adversar y does no t ex- ploit deco ded data symb ols wh e n performing id entification. In practice, howe ver , a receiv er capable of reliable decod ing can lev erage symbo l-depend ent statistics to significan tly enha nce identification perf ormance . The impact of such symb ol-aware transmitter id entification on anonymo us preco der d esign has not be e n systematically investi gated. Addressing the se limi- tations is essential for d ev eloping ph y sical-layer a n onymity mechanisms that r e main ro bust a gainst in formatio n-rich ad- versarial receivers. B. Our Contributions T o address the afor e m entioned limitations, this paper makes the f o llowing contributions: • W e intro duce a symbol-aware adversarial model for physical-lay er transmitter iden tification, in wh ich a re- ceiv er exploits all av ailable inf o rmation, including re- liably decoded data symbo ls, to en hance identification perfor mance. Unlike existing ph ysical-layer anonymity frameworks th a t rely on symbol-u naware detection mo d- els, we explicitly inco rporate symb o l-depen dent statistics into th e identification process and analyze their implica- tions f o r th e anonymou s p recoder design. • W e propo se a generalized physical-la yer anon y mity framework th at jointly accoun ts fo r CSI and transm itter noise statistics. By exp licitly modelin g heterogeneou s transmitter noise statistics in both the id entification m o del and the precod er d esign, th e p roposed fra mew o rk ad- dresses a critical and p r eviously overlooked so urce of identity le a kage and enables an onymity guaran tees in more g e n eral n etwork settings. • W e develop an an onymous symb ol-level precoding scheme f o r a multi-u ser multip le-input-m ultiple-ou tput (MU-MIMO) system tha t incorpora tes explicit anonymity constraints based on the Kullback-Leib le r di vergen c e (KLD) between tr ansmitter hypoth eses, while preservin g reliable spa tial mu ltiplexing perform ance u nder symb ol- aware iden tification. W e consider a strong-re c ei ver sce- nario and prop o se a pa rtitioned equa l- gain combining ( P- EGC) a r chitecture that ena b les re liab le multi-strea m re- ception witho ut requirin g tran smitter-specific CSI, alias- channel constructio n, or th e assumption o f e qual likeli- hood among the true and alias tran smitters. The proposed P-EGC depen ds o nly on the antenna configur ation an d the num ber o f data stre a ms, m aking it compatible with scenarios where u sers exhib it un equal detecta b ility at the receiver and r obust to he ter ogeneo us transmitter noise statistics. C. Or ga n ization an d Nota tion The rem ainder of this paper is organ ized as f o llows: Section II presents the system mo del. Section III intr oduces the trans- mitter detection strategy and the associated ano nymity metric s. Section IV focuses on the anonymous com munication design, including the pr oposed pr ecoder, combiner arch itectures, and the correspo nding optimization formu la tio n. Simulation results and d iscussions are pr ovided in Sectio n V , followed b y co n - clusions drawn in Section VI . Notation : Unless o therwise stated, the fo llowing notation is used through out the paper . Boldface lo wer case and u p- percase letter s denote vectors and matrices, respectively . The operator s ( · ) H , ( · ) † , k · k , an d k · k F denote the conju gate 3 transpose, Moore– Penrose pseud o-inv erse, Eu clidean n orm, and Fro benius n orm, respectively . T race and exp e ctation are denoted by tr( · ) and E[ · ] , respectively . The natural log a rithm is denoted by ln( · ) . In addition , C N ( 0 , Σ ) rep resents a circularly symmetric comp lex Gau ssian (CSCG) distribution with zer o mean and covariance matrix Σ , I n represents the n × n id entity matrix, O ( · ) represents the big -O notation, and ℜ{·} and ℑ{·} represent th e real an d im a g inary p arts, re sp ectiv e ly . I I . S Y S T E M M O D E L W e consider an up link MU- MIMO system com p rising K transmitting u sers and a single receiver acting as a central server . Each u ser is eq uipped with N t transmit anten nas, while the rece i ver em ploys N r receive antennas. W e assum e N r > N t , wh ich is a typic a l uplink scen ario an d is refe rred to as the strong- receiver scenar io in the literature of physical- layer anonymous comm unication s. The system o perates un d er a collision- free time division multiple access (TDM A ) pro to- col, su ch that o ne u ser is a c ti ve in each timeslot. In ou r c onsidered system, u ser sche duling is governed by an ano nymous access mech anism (e.g., ran domized conten tion or c oordin a tio n among tr ansmitters) [ 28 ], an d th e resulting scheduling infor m ation is not revealed to th e receiver . Conse- quently , althou gh exactly o ne u ser tran smits in each timeslot, the r e ceiv e r does no t know the identity of the active user, which is consistent with the standard physical- layer anony- mous commun ication setting [ 21 ]–[ 26 ]. W e ad opt a sem i-trustworthy receiver mode l, in which the receiver acts as a cu rious service provider that reliably decodes transm itted d ata wh ile simultaneo usly attemp ting to infer th e tr ansmitter’ s iden tity . The purp ose of p hysical-layer anonymou s com munication is to allow reliable dec oding while preventing the receiver from succ e ssfu lly inferring the trans- mitter’ s iden tity based on the received signal. As in [ 21 ]– [ 26 ], it is assumed that all com munication nodes have p e rfect knowledge of CSI. A. Signa l Repr esentation Let k ∈ K = { 1 , 2 , · · · , K } be the in d ex o f the sched uled user for transmission. W e adopt a blo ck-fading model in which the channel remains con stant throu ghout a transmission block and varies in depend ently across block s. W e d enote H k ∈ C N r × N t as the channel matrix from the k th user to the receiver an d W k ∈ C N t × N s as the associated prec o ding matrix, wh ere N s is the numb er o f data streams such that N s ≤ N t . The received signal corr espondin g to the k th user is ex- pressed as Y k = H k W k S + N k , (1) where S ∈ C N s × L is the transmitted symbol matr ix over a block of leng th L and N k ∈ C N r × L represents the aggr e- gated distor tion observed at the r eceiv er . Consistent with prior studies (e.g . , [ 29 ], [ 30 ]), th e comb ined effect of tran smitter- induced hardware impairmen ts an d r eceiv er n oise is m odeled as a u ser-dependent equiv alent Gaussian disturbanc e, i.e., N k ∼ C N ( 0 , σ 2 k I N r L ) , where σ 2 k denotes the effecti ve noise power associated with u ser k . Remark 1 . In practical systems, r esidual har dwar e impair- ments arising fr om non- ideal RF compo nents such as power amplifiers, IQ mod ulators, oscillators, and digital-to -analog converter s (D ACs), persist despite calibration an d compen - sation, and th eir severity ma y vary a cr oss devices [ 29 ]– [ 31 ]. These transmitter-originated d isto rtion s can have a non-n e g lig ible impa ct o n the received signal, pa rticularly in MIMO systems employing sensitive d etection schemes [ 32 ]. As a r esult, transmitter har d war e quality dir ectly influ ences the statistical p r operty of th e r e ceived sign a l a nd constitutes an importa n t sour ce of identity leakage in physical-layer anony mo us communicatio ns. I I I . T R A N S M I T T E R D E T E C T I O N S T R AT E G Y In this section, we investigate the receiver -side d etection mechanism used to evaluate transmitter ano nymity pe r for- mance. W e consider a scen ario in which the receiver seeks to id entify the active user b ased on the observed sign al Y and the kn own CSI of all u ser s. Since the tran smitter identity is anonym o us, the rece ived signal in ( 1 ) is deno ted by Y without a user -spe c ific subscript. The transmitter identification problem can be con sidered as a multip le-hypo thesis testing (MHT) formu la tio n, expressed as H 1 : Y = H 1 W 1 S + N 1 , H 2 : Y = H 2 W 2 S + N 2 , . . . H K : Y = H K W K S + N K , (2) where th e hyp othesis set H H H = {H 1 , H 2 , . . . , H K } represents K possible candid ates f or th e orig in ating transmitter and H i and W i denote the chan nel an d pr ecoder of user i ∈ K , respectively . T wo majo r me thodolo g ies exist for comp osite hyp o thesis testing: th e Bayesian ap proach and th e gen eralized likelihood ratio test (GLR T) [ 33 ]. For the MHT problem co nsidered here, we adop t the GLR T framework, as it does not req uire prior distributions on the unknown pr ecoding matrices and is there- fore more suitable an d robust for a n onymou s comm unication scenarios. The first step in GLR T is to ob tain the m aximum- likelihood estimate of th e unk nown para meters in th e lin e a r model given in ( 2 ). Since the o bjective of the ano nymous com- munication system is to guarantee transmitter ano nymity while preserving r e liable co mmunicatio n, the transmitted symbols must be correc tly d ecoded at the receiver . Consequ ently , when user identification is p erform ed after decod ing, the symb o l matrix S can b e treated as k n own. Under this assumption, the only remainin g unknown p arameter within e ach hyp othesis is the p recoding m a tr ix em ployed by the correspo nding user . If th e actua l transmitter is the k th user , then the hypothe sis H k is corr ect, and the actual tran sm itted signal is Y = H k W k S + N k . Under H k , the max imum-likelihoo d e stimate of th e precod er is c W k = H † k YS † , where H † k = ( H H k H k ) − 1 H H k and S † = S H ( SS H ) − 1 . Similarly , under incorrect hypo thesis H i , the estimated pre- coder b ecomes c W i = H † i YS † . Using these estimates, the 4 reconstruc ted receiv ed signals under the corre ct and incorrect hypoth eses are b Y k = H k c W k S = H k W k S + H k H † k N k S † S (3) and b Y i = H i c W i S = H i H † i ( H k W k S + N k ) S † S , (4) respectively . According ly , the probab ility de n sity function s (PDFs) of received signal Y un der each hyp othesis are given by H 1 : p ( Y ; c W 1 , H 1 ) = 1 ( π σ 2 1 ) N r L exp − 1 σ 2 1 k Y − b Y 1 k 2 F , H 2 : p ( Y ; c W 2 , H 2 ) = 1 ( π σ 2 2 ) N r L exp − 1 σ 2 2 k Y − b Y 2 k 2 F , . . . H k : p ( Y ; c W k , H k ) = 1 ( π σ 2 k ) N r L exp − 1 σ 2 k k Y − b Y k k 2 F . (5) Under th e GL R T framework, the receiver selects hypothesis H k if its likelihood p ( Y ; c W k , H k ) is the largest among all candidates. I n maximu m-likelihood estimation (ML E) and hypoth esis testing , it is com mon to employ the log -likelihood as the test statistic du e to its mo notonicity and numerical stability . Acco rdingly , we define T k = ln p ( Y ; c W k , H k ) as the test statistic und er th e hypoth esis H k such that the receiver decid es in fav o r o f the h ypothe sis associated with the maximal T k . A. Anon ymity Metric: Detection Err or Rate In this pap er , we ev aluate transmitter an o nymity thr ough the pro bability th at the receiver fails to cor rectly identify the active u ser . Con sistent with existing studies on ph ysical- layer anonymity ( e.g., [ 24 ], [ 26 ]), w e adopt th e DER as the anonymity metric. T o ch aracterize the DER, we exam ine the statistical beh avior of the d e tection test statistic T under the correct and inc orrect hypoth eses. Suppose the k th user is the actual tran smitter , implyin g that the tru e hyp othesis is H k , w h ile any H i ( ∀ i ∈ K an d i 6 = k ) represents an incorre c t hypo thesis. For ana lytical tractability , the cor respond in g log- likeliho od test statistics can be wr itten as T k = ln p ( Y ; c W k , H k ) = − N r L ln( π σ 2 k ) − 1 σ 2 k k b Y k − Y k 2 F (6a) and T i = ln p ( Y ; c W i , H i ) = − N r L ln( π σ 2 i ) − 1 σ 2 i k b Y i − Y k 2 F . (6b) Since the re c eiv er identifies the tra nsmitting user based on the largest test statistic, an incor rect detectio n occurs wh en T i > T k for some i 6 = k . T o char a cterize th is event, we introdu c e the dif fe r ence ran dom variable D i = T i − T k , which measures th e relative likelihoo d of an incorre c t h ypothe sis compare d with the true one . Theref o re, the DER can be equiv a lently written a s DER = 1 − Pr D i < 0 , ∀ i 6 = k . (7) Computing this pr obability require s the joint distribution of the set { D i } i 6 = k . Howe ver, the variables D i are mutually depend ent because each term inclu d es the com m on term T k . In add ition, the test statistics T k and T i are quad ratic form s of CSCG noise, and th us f o llow non-G a ussian generalized chi- square–ty pe d istributions. As a r esult, the joint c u mulative dis- tribution fu nction (CDF) inv olves high- dimensiona l integrals over dependent, non-Gaussian rando m variables, r endering an exact closed-fo rm expression for the DER analytically intractable. N evertheless, the DER metric can b e ev aluated numerically thr ough Monte-Carlo simulations. Remark 2. If we app r oximate T k and T i as Gaussian dis- tributed, then with both mean and variance specifi ed, the distributions would b e fully characterized, allowing a closed - form ap pr oximatio n of the ano nymity metric. In this case, for each n on-transmitting u ser i , the differ ence variab le D i = T i − T k would also be Ga ussian, and q uantities such as Pr( D i > 0) = 1 − P r( D i < 0) c o uld b e dir ectly evalu a ted via th e Gaussian CDF . If the variables { D i } i 6 = k wer e further assumed indepen dent, the overall ano nymity metric can b e expr essed as 1 − Q i 6 = k Pr( D i < 0 ) . However , this appr oa ch r elies o n sever al str ong assumptio ns and a ppr oxima tions. In practice, these assumptions in tr oduce a considerable g ap b etween the theo retical e stimate a n d the actual b e havior in o ur scena rio. k b Y k − Y k 2 F and k b Y i − Y k 2 F in test statistics, and c o nsequen tly D i , are n on-Ga u ssian because they involve quadratic forms of CSCG noise, and the variables { D i } i 6 = k ar e m u tually depend ent thr o ugh the sha r ed term T k . These issues make it imp ossible to obta in the joint distribution o f { D i } i 6 = k in closed form, making a closed- fo rm evaluation of DER analytica lly intractable. B. Anon ymity Metric: Information -theoretic Metric T o gain analytical insight into the factors influencing anonymity , we adopt an inf o rmation- theoretic perspe cti ve. Specifically , we examine the KLD [ 34 ] between the d istri- butions of the r eceiv ed signal Y und er the tru e h ypothesis p k , p ( Y ; c W k , H k ) and false hyp othesis p i , p ( Y ; c W i , H i ) , defined as D KL ( p k k p i ) = E ln p k ( Y ) p i ( Y ) = Z p k ( Y ) ln p k ( Y ) p i ( Y ) d Y , (8) where the expectation is taken with respect to ( w .r . t. ) the true distribution p k ( Y ) under hy pothesis H k . The KLD qu antifies how distinguishab le the received signals are between the two cases, i.e. , a larger KLD indicates th at the two distributions p k and p i are mo re d istinguishable, making cor rect detection easier for the receiver . In the following, we pre sent Lemma 1 to analy tically qu a ntify th e KLD in our anonym ous commu - nication system . 5 Lemma 1 . The KLD between the distributions p k and p i , defined in ( 8 ) , ad mits th e following closed -form expr ession: D KL ( p k k p i ) = E[ T k ] − E[ T i ] = N r L ln σ 2 i σ 2 k + 1 − σ 2 k σ 2 i ( N s N t − N r L ) + 1 σ 2 i h tr S H W H k H H k H k W k S − tr S H W H k H H k H i H † i H k W k S i . (9) Pr oof. See App endix A . Recalling that D i = T i − T k , the KLD in L emma 1 can be written as D KL ( p k k p i ) = − E[ D i ] . Thus, a larger expected value E[ D i ] corr e sponds to a smaller KL D, mea n ing that the two h ypothe ses become less distingu ish a ble. If we define each user other than the true transmitter as an alternativ e user , then the pairwise an onymity between the true tr ansmitter an d any alternative user i can be given by E [ D i ] . C. T ransmitter An onymity Constraint In this subsectio n, we quantif y an anonymity constraint for the transmitter d etection strategy . Here, we refer to the no n-transmittin g u sers (indexed by ∀ i 6 = k ) as the alias u sers who se ch annels are intentionally exploited by the transmitter to disguise the true transmission. W e first define the alias-cand idate set for the k th user as A cand k = { 1 , . . . , K } \ { k } , which con ta in s all non -transmitting users who se chann els m ay be explo ited fo r ano nymity . From the cand idate set A cand k , the transmitter selects a subset A ⊆ A cand k as the index set of the selected alias users, where |A| = a, 1 ≤ a ≤ K − 1 , represen ts the number of aliases considered by th e r e ceiv e r for transmitter detection . W e note that the rec e iver selects the user co rrespond ing to the largest test statistic T i . T o achieve pairwise ano nymity between the true user and each alias, the distribution o f the received sign al Y un der th e alias hypoth esis H i should closely re sem ble its distribution u nder the true hypothesis H k . From Lemma 1 , we see that the pairwise a n onymity c an b e q uantified b y the negative KL D between p k ( Y ) and p i ( Y ) . T o enhan ce anonymity , one can minimize th is divergence, which is equi v- alent to maximizin g its negati ve v alue, E[ D i ] = E[ T i ] − E[ T k ] . T o achieve this aim, E[ D i ] can be expressed as E[ D i ] = E const − 1 σ 2 i ∆ , (10) where E const = N r L ln σ 2 k σ 2 i + 1 − σ 2 k σ 2 i ( N r L − N s N t ) (11) and ∆ = tr S H W H k H H k H k W k S − tr S H W H k H H k H i H † i H k W k S . (12) It f ollows directly from ( 10 ) that maximizing the pair wise anonymity measure E[ D i ] is equivalent to minimizing th e trace-difference term ∆ , wh ich can be r ewritten as ∆ = tr S H W H k H H k ( I N r − H i H † i ) H k W k S (a) = tr S H W H k H H k ( I N r − H i H † i ) 2 H k W k S , (b) = k ( I N r − H i H † i ) H k W k S k 2 F . (13) where ( a ) follows fr om the idem potent pro perty of the pr o- jection matrix I N r − H i H † i and ( b ) follows from the iden tity tr( A H A ) = k A k 2 F . Since ∆ ≥ 0 , driving this term toward zero provides the most fa vorable co ndition for improving an onymity , as it minimizes the distinguisha bility between the true an d alias hypoth eses. Howe ver, enfor cing ∆ = 0 is overly restrictiv e and would impose a se vere constrain t on the precode r , com pro- mising com munication reliability . T o balan c e anonymity with commun ication q u ality , we introd uce a small relaxation p a- rameter ǫ to allow a con tr olled, non -zero trace-difference, with smaller values en forcing strong er anonymity . The anonymity constraint at the sy m bol level is thus giv en b y ( I N r − H i H † i ) H k W ℓ k s ℓ 2 2 ≤ ǫ, ∀ i 6 = k , ℓ (14) where s ℓ denotes th e tr ansmit symbol vector of the k th user at timeslot ℓ . Remark 3. The con d ition in ( 14 ) fo llo ws the theoretical definition of p airwise anon y m ity , which is fo rmulated w .r . t. any non-transmitting u ser ( ∀ i 6 = k ). This de finition specifi e s how pairwise ano n ymity is ensu r ed be tween th e tru e user and an arbitrary non- transmitting user , but does n ot requir e tha t the constraint be enforced fo r a ll such u sers in practice. Since imposing all K − 1 pairwise co n straints would overly r estrict the pr ec o ding space a n d noticeably d e g rade communica tion r eliab ility , the sub sequent design enfor ces this constraint only on a selected a lias subset A . I V . A N O N Y M O U S C O M M U N I C AT I O N D E S I G N In an anonymou s comm unication frame work, d espite being aware of the set of all CSI, the rec eiv e r must no t be able to associate the r eceiv ed signal with the chan nel of th e actual transmitter . T o en able user-agnostic signal comb ining an d reliable d emodulatio n, we em ploy a con structiv e-interfer ence (CI) precod er at the transmitter . The CI preco der pr e - aligns the transmitted symbo l ph ases so that, after spatial co mbining , the resulting received signal can be directly demo d ulated without requirin g any CSI-d e penden t equalization at the receiv er . In the following, we first r evie w the CI preco d ing pr inciples (see [ 35 ] and ref erences there in for f urther details) and then present our receiver com bining schem e an d anonym ous precod er design tailored fo r th e co nsidered system. A. Constructive Interfer en ce Precoder In conventional systems, phase equalization is essential f or exploiting spatial d iv e rsity in the sense that without alignin g the signal p hases ac r oss antennas, the received componen ts 6 cannot be coher e n tly combin e d. Howev er , in th e an onymous setting, the r eceiv er is not allowed to design a CSI-based equalizer to perf orm such ph ase alignment. Specifically , in the strong -receiver scenario ( N r > N t ), where the transmitter has limited spatial DoF , the transmitter canno t independ ently control the phase of each r eceiv e antenna. By pre-adju sting the transmitted signal phases, the CI pr ecoder fu lfills this role at the transmitter side, ensuring tha t the post-comb in ed received symbols for each data stream rem ain co rrectly alig ned for demodu lation while pr eserving user anonymity . In other words, the CI p recoding aims to actively shape the multi- stream in te r ference inasmuch as it reinfor ces, rath er than distorts, the d esired signal comp onents. Instead of suppr essing interferen ce, the precod er exploits the known symbo l phases and the av ailable CSI to steer the sup erimposed signal at the receiver to ward the constructive r egion of the constellation. As a result, the post-combine d received symbo ls are naturally aligned with their target dire ctions, enhan c ing de tection reli- ability without req u iring CSI-based phase equalization. This approa c h effectiv ely conv erts inter ference power into u seful signal energy , impr oving b oth en ergy efficiency an d no ise resilience. Th e r efore, the CI precod ing plays a crucial role in enabling ano nymous comm u nication un der the strong -receiver scenario ( N r > N t ). In th is work, we will design th e a p pro- priate CI preco der w .r .t. a new receiver comb iner structure , introdu c ed in the sequ el, f o r an onymous comm unication. B. P artitioned Equa l-Gain Combiner Con ventional com bining sch emes such as a maximum -ratio combiner, widely used in non-ano nym ous MIMO settings, are not suitable f or anonymous commun ications, becau se they inherently rely on user -specific CSI. In lig h t of this, we propo se a pa rtitioned equ al-gain combinin g (P-EGC) sch e me, which is ap plied at the receiver to exploit spatial diversity without relying on u ser-specific CSI. Spe c ifica lly , the k ey idea of o ur P-EGC schem e is to partition receive antenn as into se veral gro u ps accordin g to th e nu mber of transmitted d ata streams, then combine the signals rece ived within each grou p correspo n ding to the same data stream with equ al weig hts, while av oiding any com b ining across different antenna grou p s. This app roach enables the receiver to b enefit from spa tial div ersity in a u ser-agnostic man ner, without rely ing on the transmitter’ s identity or ch annel ch a racteristics. The detailed combin in g pro cess can be d e scribed as f ollows. For any arbitrar y num ber o f rec eiv e antenna s N r , the anten nas are divided into N s disjoint subsets such that N r > N s 1 . Let S m denote the subset of r eceiv e antennas assigned to the m th data stream with |S m | being its car dinality . W e denote y ℓ k,j as 1 Since N s data streams are sent using N t transmit antennas, in the simplest case ( N s = 1 ), where the transmitter sends only one data s tream, the recei ver natural ly achie ves full di versit y without the need to parti tion the recei ve antenna s into subsets. As such, the precoder essentially functions as a vector ( w k ∈ C N t × 1 ). Ho weve r , considering multiple xing gain at the transmit ter, the recei ver must partition the recei ve antennas into subsets based on the number of m ultipl ex ed da ta streams. If the number of recei ve antennas is not an in tege r multiple of th e number of streams, the antenna alloca tion among data streams may vary slightl y , b ut this does not affect our design process. the r e c eiv e d sign al at the j th antenna, wher e j ∈ S m , from the k th user at time slo t ℓ , wh ic h can b e expressed as y ℓ k,j = h k,j N s X n =1 w ℓ k,n s ℓ k,n + n ℓ k,j , (15) where h k,j ∈ C 1 × N t is the ch annel vector from the k th trans- mitter to the j th receive an te n na in S m , and w ℓ k,n ∈ C N t × 1 is the precoder f or the n th data stream at timeslot ℓ . Let s ℓ k,n ∈ C denote th e symbo l of the n th data stream tran smitted at timeslot ℓ an d n ℓ k,j ∼ C N (0 , σ 2 k ) d enote the noise in this received signal at th e j th receive antenna. Ap plying the P-E GC to all the r e ceiv e d sign als from S m , the c o mbined signa l can be expressed as r ℓ k,m = X j ∈S m y ℓ k,j = c k,m H k,m W ℓ k s ℓ + ˜ n ℓ k,m , ∀ k , m, ℓ, (16) where H k,m = h k,j j ∈S m ∈ C |S m |× N t is th e subm atrix of the full chan nel H k correspo n ding to antennas in S m , and c k,m ∈ C 1 ×|S m | denotes the equa l gain comb iner fo r the m th data stream, which is assumed to be an all-ones row vector , i.e., c k,m = 1 1 ×|S m | . I n add ition, W ℓ k = w k, 1 w k, 2 · · · w k,N s ∈ C N t × N s is th e precod e r for all data streams at timeslot ℓ , s ℓ denotes the transmit symbol vector a cross all data streams, and ˜ n ℓ k,m , c k,m n ℓ k,m indi- cates the agg r egated noise after c ombining , where n ℓ k,m = [ n ℓ k,j ] j ∈S m ∈ C |S m |× 1 is the noise vector correspondin g to the anten na subset S m . Each n ℓ k,j is modeled as an indepen d ent a n d iden tically distributed (i.i.d .) CSCG random variable. Thus, the effecti ve noise for each data stream follows ˜ n ℓ k,m ∼ C N (0 , σ 2 eff ) , such th at σ 2 eff = E( | ˜ n ℓ k,m | 2 ) = k c k,m k 2 2 σ 2 k = |S m | σ 2 k . For all N s data stream s, the P- EGC can be expressed in a compact b lock-diag onal form as C k = c k, 1 0 · · · 0 0 c k, 2 · · · 0 . . . . . . . . . . . . 0 0 · · · c k,N s , (17) where e a c h diagonal element is a row vecto r of all-o nes, representin g the com biner for th e sub set of receive anten nas for each data stream. The size o f these combiners de pends on the numbe r o f anten nas in each grou p. For example, fo r th e m th data stream, |S m | antennas are allocated for receptio n. Thus, th e overall com biner C k is a matrix of size N s × N r . Since the P-EGC dep ends only on the a n tenna group ing, C k does not vary with the timeslot index ℓ . As a result, b ased on the symbo l-lev el precoder W ℓ k , the po st-combined r eceiv ed signal vector at timeslot ℓ can be expr essed as ˜ r ℓ k = C k H k W ℓ k s ℓ + n ℓ k , ∀ k , ℓ, (18) where ˜ r ℓ k = [ r ℓ k, 1 , . . . , r ℓ k,N s ] T ∈ C N s × 1 is the post-co mbined outputs of all stre a m s a nd n ℓ k = [ n ℓ k, 1 , . . . , n ℓ k,N r ] T ∈ C N r × 1 is th e received noise vector . 7 Fig. 1. Illustration of CI precoding for QPSK modulation. The green area represent s the constructi ve decision region and the black points denote the referenc e constella tion symbols. The parameter γ indicates the mini mum in- phase distance from the origin. The blue point correspond s to a recei ved symbol x ℓ m on stream m at timesl ot ℓ , wi th s ℓ m denotin g the corresponding targ et constellat ion symbol. After rotating the point by the negat ive phase of the fi rs t-quadrant refere nce symbol, the rotated poin t lie s in the construct ive regi on if the ratio between its imagina ry and real components remains within the ± tan θ boundaries, where θ = 45 ◦ for QPSK. C. Ano n ymous Pr eco ding R e quir e m e n ts In this subsection , we specify the CI requ irement u sed in the anonymou s preco d er design . By comb in ing the CI principle with the P-EGC mod e l introd uced earlier, we expr ess the geometric cond itio n that the po st-combined received sym bol must satisfy in orde r to achieve constructive interf e rence, which will b e used as a constraint in the subsequen t design problem . In this w o rk, we consider th e quadrature phase shift keying (QPSK) modulatio n for the signal vector as a representa- ti ve exam ple o f con stellations com monly adopted in sym bol- lev el CI preco ding stud ies [ 22 ], [ 35 ]–[ 3 7 ]. In QPSK, each transmitted symbo l lies in one of th e fou r quad rants of the complex plane, an d the dec ision bou ndaries are the rea l and imaginary axes. The g oal o f CI precoding is to ensure th at the post-comb ined received signal of each data stream is pu shed deeper into th e correct qu adrant, away from these d e cision bound aries 2 . Follo wing our P-EGC receiver mo del, outlined in Section IV -B , the comb ined received signal ( 1 6 ) c a n be r ewritten as r ℓ k,m = α α α ℓ k,m s ℓ + ˜ n ℓ k,m , ∀ k , m, ℓ, (19) where α α α ℓ k,m , c k,m H k,m W ℓ k . T o e n sure cor rect detection, th e signal compon ent α α α ℓ k,m s ℓ (ignor in g th e noise) must lie within the dec ision region. Geometrically , for a QPSK sy mbol s ℓ k,m located on the un it circle with phase φ ℓ k,m , the constructive region corresponds to th e angular sector φ ℓ k,m ± θ , where θ = 2 Although our work specifically considers the QPSK modulation, the CI precodi ng framewo rk can be gen eraliz ed to higher -order constellat ions such as M-QAM and M-P AM, by redefining the construct i ve regi ons around constel lation point s [ 38 ], [ 39 ]. Such extension s are left as future w orks. π / 4 . In the CI scheme, the constellation is pro p erly rotated so that the desire d sym bol lies on the p ositiv e real axis. T h is c a n be equ i valently achieved b y multip ly ing the n o ise-less term α α α ℓ k,m s ℓ with the c o mplex-conju gate of the symbol, su bject to the f o llowing conditions: ℜ α α α ℓ k,m s ℓ ( s ℓ k,m ) ∗ ≥ γ , ∀ k , m, (20a) ℑ α α α ℓ k,m s ℓ ( s ℓ k,m ) ∗ ≤ tan θ ℜ α α α ℓ k,m s ℓ ( s ℓ k,m ) ∗ − γ , ∀ k , m, (20b) where γ > 0 deno tes the r equired minimum in-p hase dis- tance from the origin (a. k .a. c o nstructive margin , which is propo rtional to the Euclid ean decision margin), repr esenting the guaranteed constru ctiv e amplitude of the recei ved symbol. The real part in ( 20a ) cor responds to the in -phase p rojection of the rotated r eceiv ed symb ol, i.e., the comp onent that push e s the symbol away fr om th e decision bo undaries and thus contributes to reliab le de te c tio n. Meanwhile, ( 20b ) confines the symbol within the constru ctiv e angu lar sector . By no ting that the right-h and side of ( 20b ) is non negativ e o n ly when ℜ{·} ≥ γ , we find that ( 20a ) is satisfied wh e n ( 20 b ) ho lds. Therefo re, the two inequalities can b e com bined into a single constraint th at jointly captures bo th the I Q req u irements as ℑ n α α α ℓ k,m s ℓ ( s ℓ k,m ) ∗ o ℜ n α α α ℓ k,m s ℓ ( s ℓ k,m ) ∗ o − γ ≤ tan θ , ∀ k , m. (21) Constraint ( 21 ) ensures th at the p ost-comb in ed r eceiv ed sym- bol r ℓ k,m = α α α ℓ k,m s ℓ lies in the constructive region o f its target constellation p oint, hence forth turning m ulti-stream interferen ce into beneficial on e for detection perform ance improvement. An illustrativ e example o f the above CI precod ing applied to QPSK is provided in Fig. 1 . In this figu re, the blu e p oint represents a n example of the received symbol, de noted b y x ℓ m . The dash ed 45 ◦ line indica tes the dir ection of the refer ence constellation p oint in the first quadran t, along which CI aims to push the received symbol into the constructive region. After rotatin g the rece i ved signal by the n egati ve ph ase of the reference symbol, this 45 ◦ line a ligns with the real ax is. In this rotated do main, th e r e a l par t correspond s to the com ponent along the desired symb o l dir ection, whereas the imagina r y p art represents the deviation from that directio n. T o ensure that the received symbol lies within th e constru cti ve region, the geometric rela tio nship b etween its r eal an d imag in ary p arts must satisfy ( 2 1 ). W ith the CI constra int established, we now turn to h ow commun ication reliability is quantified under th is f r amew ork. Under the CI p recoding framework, multi-stream interferen c e is aligned with the desired symb ol direction and thus bec omes a usefu l power contribution. According ly , the post-co mbining signal-to-d isturbance ratio (SDR) fo r th e m th data stream of the k th user ca n be c a lculated as Γ k,m = k P j ∈S m h k,j ( P N s n =1 w ℓ k,n s ℓ k,n ) k 2 k P j ∈S m n ℓ k,j k 2 = k c k,m H k,m W ℓ k s ℓ k 2 |S m | σ 2 k , ∀ k , m. (22) 8 This expr ession charac terizes the resultin g post-co mbining reliability , whereas th e o ptimization is carried out w .r .t. th e guaran tee d threshold Γ th throug h the CI margin γ . Algorithm 1 Anonymou s Pr ecoding Algorithm Input: Chann e l set H = { H 1 , . . . , H K } , symbol m a trix S , transmitting user index k , total tr ansmit power p tot , noise variances { σ 2 i } K i =1 , number of alias channels a , an d relaxation parameter ǫ . 1: Construct the a lias-candidate set A cand k = { 1 , . . . , K } \ { k } . 2: Randomly select a users f r om A cand k to form the alias set A . 3: Compute the combinin g matrix C k using ( 17 ). 4: Construct the CI constraint according to ( 21 ). 5: Construct the anonymity constrain t using the relaxatio n parameter ǫ accordin g to ( 14 ). 6: Solve op timization pr oblem P 2 u sing CVX. Output: Precod ing matrix W k , co nstructive margin γ , and combinin g matrix C k . D. Design Pr oblem an d Solutio n Building on the pro posed P-EGC sch eme at th e rece i ver an d the CI p recoding at the transmitter, we now focus on d esigning anonymou s pr ecoders { W ℓ k } L ℓ =1 to jointly e n hance communi- cation reliability and enf o rce transmitter ano nymity . F o r eac h timeslot ℓ , we intro duce Γ ℓ as a common worst-str eam SDR guaran tee , i.e., the SDR of every data stream is constrained to be no smaller than Γ ℓ . T o ensure unifo rm pe rforman ce over time, we maximize th e w orst-timeslot guarantee, which yields the following max–min formulatio n: P0 : max { W ℓ k , Γ ℓ } L ℓ =1 , Γ Γ s.t. c k,m H k,m W ℓ k s ℓ 2 |S m | σ 2 k ≥ Γ ℓ , ∀ m, ∀ ℓ , (23a) ℑ c k,m H k,m W ℓ k s ℓ ( s ℓ k,m ) ∗ ≤ tan θ × ℜ c k,m H k,m W ℓ k s ℓ ( s ℓ k,m ) ∗ − q Γ ℓ σ 2 eff , ∀ m, ℓ , (23b) W ℓ k s ℓ 2 2 ≤ p tot L , ∀ ℓ, (23c) k ( I N r − H i H † i ) H k W ℓ k s ℓ k 2 2 ≤ ǫ, ∀ i ∈ A , ∀ ℓ, (23d) Γ ℓ ≥ Γ , ∀ ℓ. (23e) where ( 23a ) ensur es the SDR constrain ts fo r comm unication reliability , ( 23b ) enforces CI c o nditions at the symbo l level, ensuring that the re ceiv e d signals lie within th e constru cti ve region of the modulation con stellatio n , ( 23c ) impo ses the power budget for each symbol interval, where p tot is the total transmit p ower , and ( 23d ) inc o rporate s the transmission anonymity constraint, determined in ( 1 4 ). W e high light that problem P0 implements a tw o-level fairness criterio n, gua ran- teeing uniform ly reliable transmission across b oth data streams ∀ m and timeslots ∀ ℓ . Since a ll constraints in ( 23a )–( 23e ) are imp osed ind epen- dently per timeslot, and the p r ecoder W ℓ k appears only in constraints indexed b y the same ℓ , the prob lem P0 admits a per-timeslot decomp o sition. Accordingly , for a given timeslot ℓ , we can solve the following subprob lem ( dropp ing the index ℓ fo r n otational simp licity ): P1 : max W k , Γ Γ s.t. k c k,m H k,m W k s k 2 |S m | σ 2 k ≥ Γ , ∀ m, (24a) |ℑ { c k,m H k,m W k s ( s k,m ) ∗ }| ≤ tan θ × ℜ { c k,m H k,m W k s ( s k,m ) ∗ } − q Γ σ 2 eff , ∀ m, (24b) k W k s k 2 2 ≤ p tot L , (24c) k ( I N r − H i H † i ) H k W k s k 2 2 ≤ ǫ , ∀ i ∈ A . (24d) Let Γ ⋆ ℓ denote the op timal value o f pro blem P1 for timeslot ℓ . The optimal solution to the origin al prob lem P0 is then expressed as Γ ⋆ = min ℓ ∈{ 1 ,...,L } Γ ⋆ ℓ , (25) with W ℓ k selected as th e optim izer o f the cor respond in g per- timeslot p r oblem. Problem P1 is non-co n vex du e to the SDR constrain ts ( 24a ) and the CI co nstraints ( 2 4b ). T o obtain a tr a ctable d esign, we adopt 3 a stand a r d CI margin maximization ap proach [ 22 ]. Specifically , we define the (rea l) CI margin as γ , q Γ σ 2 eff , (26) and dir e c tly maximize γ , which en f orces a commo n lower bound on the in-phase constructive comp onent f or all streams. For QPSK, | s k,m | = 1 , and the CI con straint implies ℜ{ u m } ≥ γ , wher e u m , c k,m H k,m W k s ( s k,m ) ∗ . Therefo re, | u m | ≥ ℜ{ u m } ≥ γ , wh ich further y ields k c k,m H k,m W k s k 2 = | u m | 2 ≥ γ 2 = Γ |S m | σ 2 k , ∀ m , i.e., ( 24a ) is implied by th e CI co nstraints and can thus be o mitted. Consequently , we equ iv alently solve P2 : max W k , γ γ s.t. |ℑ { c k,m H k,m W k s ( s k,m ) ∗ }| ≤ tan θ ( ℜ { c k,m H k,m W k s ( s k,m ) ∗ } − γ ) , ∀ m, (27a) k W k s k 2 2 ≤ p tot L , (27b) k ( I N r − H i H † i ) H k W k s k 2 2 ≤ ǫ , ∀ i ∈ A . (2 7c) W e high light that prob lem P2 is conve x second-order cone progr amming (SOCP), du e to an affine o bjective function with linear an d second- order co ne (SOC) co n straints [ 40 ]. 3 Although problem P1 can be tackled via successi ve conv ex approxi- mation (SCA) [ 40 ], [ 41 ] by iterati vel y con vexifyi ng the nonco n vex SDR constrai nts, such approach es typical ly conv erge only to a stationar y point with initia lization-de pendent s olution and require an additi onal bisecti on/inner- loop procedure to handle √ Γ in the CI constraints. In contrast, the CI- margin reformul ation in P2 admits an SOCP representation and can be solved globall y; hence, we adopt P2 as a tractable surro gate for P1 . 9 The CI con straint in ( 27a ) is linear, since the absolute-value inequality can be rewritten as two affine ineq u alities. T he power constrain t in ( 27b ) an d the an onymity con straint in ( 27c ) are SOC constrain ts of the form k A x k 2 ≤ b . Hence , P2 can be efficiently solved by any con vex o ptimization tool. Algorithm 1 summarizes ou r p roposed anonym ous precodin g design. E. Complexity An alysis The p er-timeslot prob le m ( 27 ) is SOCP and can be solved using a primal– dual interior-point metho d (IPM). The worst- case complexity of conic program s with SOC a nd linear matrix inequality (LM I) con straints u sing a standard IPM scales as [ 22 ], [ 4 2 ] C = O ln 1 τ p β C form + C fact , (28) where τ > 0 denotes the target accu racy an d β is the bar rier parameter, gi ven by β = p X j =1 q j + 2 v , (29) with p deno ting the n umber of LMI co nstraints of sizes { q j } p j =1 , and v den oting the numb er of SOC constrain ts. The per-iteration compu tational co sts f or fo rming and factorizing the Newton system are u pper boun d ed by [ 42 ] C form = n v ar p X j =1 q 3 j + n 2 v ar p X j =1 q 2 j + n v ar v X j =1 u 2 j , C fact = n 3 v ar , (30) where n v ar is the n umber o f decisio n variables and u j is the dimension of th e j th SOC constraint. For p roblem P 2 , co nstraint ( 27a ) is equivalent to two affine ineq ualities per d ata stream, yieldin g 2 N s scalar linear constraints. The se can b e treated as 2 N s size-one LMIs, i.e., p = 2 N s and q j = 1 . Constraint ( 27b ) contributes one SOC con straint of size N t , and constraint ( 27c ) co ntributes |A| = a SOC co nstraints of size N r . Hence, v = 1 + a and β = 2 N s + 2(1 + a ) . In ad dition, since W k ∈ C N t × N s and γ ∈ R , the real- valued pro blem ha s n v ar = 2 N t N s + 1 d ecision variables. Su bstituting these q uantities yields the worst-case complexity of solvin g P2 per timeslot as C P2 = O ln 1 τ p 2 N s + 2(1 + a ) × 2 N s n 2 v ar + n v ar 2 N s + N 2 t + aN 2 r + n 3 v ar . (31) Since the pre coder is designed indepen dently acr oss L timeslots, the overall alg orithm complexity scales linearly with L . More over , since the Ne wto n-system factor iza tion term n 3 v ar is d ominan t in typ ical MIM O regimes, the total comp lexity can be ap proxim ated as C total ≈ O L ln 1 τ p 2 N s + 2(1 + a ) ( N t N s ) 3 . (3 2) 10 15 20 25 30 SNR (dB) 0.2 0.25 0.3 0.35 0.4 0.45 0.5 0.55 0.6 DER =1.0e-05 =1.0e-04 =1.0e-03 =5.0e-03 =1.0e-02 Fig. 2. DER vs. SNR under differe nt anon ymity rela xations ǫ . V . S I M U L A T I O N R E S U LT S In this section, we pr esent simulation results to ev a lu ate the detectio n p erform ance an d anonym ity beh avior o f the propo sed fr amew ork. I n each Monte Carlo trial, the ind ex o f the active user k is rando mly selected from all K can d idates to ensure statistical fairness. T h e alias u ser is then r andomly chosen from the remainin g K − 1 c andidates to form an alias set with size a = 1 . Unless otherwise specified, the fo llowing parameters are used through out the simulations: The total number of user s is K = 15 , th e num ber o f r eceiv e anten nas is N r = 12 , the number of tran smit antennas is N t = 8 , the n umber o f data streams is N s = 4 , and the block len g th is L = 30 . In addition , the n oise variance at any non-tran smitting user i 6 = k is modeled as a rando m per tu rbation ar ound that of th e true transmitter, gi ven b y σ 2 i = 1 0 β i / 10 σ 2 k , ∀ i 6 = k, (33) where { β i } are i.i.d. rand om variables un iformly distributed over [ − d, d ] , i.e., β i ∼ U [ − d, d ] , represen ting the relative deviation o f each user’ s noise variance fro m that of the tru e transmitter, an d d denotes the half-ran ge of no ise variation in the logarithmic domain. W e set d = 1 . 5 dB, which introdu ces moderate ra n domn e ss yet controlled h eterogene ity in the noise lev els. Finally , we clarify that all SNRs in this sectio n are defined as transmit SNRs. In this section , we d o not provid e performance comparison with existing precoders, as conv entional precoder designs (e.g., SVD/MMSE) provide n e ar-zero anonym ity in the con- sidered SNR r ange. M e a nwhile, re c ently proposed ph ysical- layer an onymous precode rs [ 22 ]–[ 24 ] r ely on fundame ntally different system assumptions and formulations (e.g., full- multiplexing without co mbiners, f ull-diversity single-stream transmission, or ho mogen e ous-noise closed-fo rm DER an al- ysis). Adaptin g them to our hetero geneou s-noise multiplex- ing–diversity framework would substantially alter their struc- ture and le a d to un fair or impra c tical compar iso n s. Fig. 2 shows the DER p e rforman ce as a functio n of the SNR f o r d ifferent anonymity constraint re laxation pa rameters 10 10 15 20 25 30 SNR (dB) 10 -4 10 -3 10 -2 10 -1 10 0 SER =1.0e-05 =1.0e-04 =1.0e-03 =5.0e-03 =1.0e-02 Fig. 3. A vera ge symbol e rror rate (SER) vs. SNR with differe nt ǫ . ǫ . Interestingly , the DER incr eases with the SNR, indicatin g that hig her transmit power enhan ces an o nymity . This be - havior can be explaine d by examining the expected d iffer- ence expression E[ D i ] in Lemma 1 . Sp e c ifically , the noise- variance-related constant ter m remain s essentially in depend ent of the SNR, wh ereas the signal- depend ent trace- difference term grows propor tionally with th e sign al power . Since the propo sed anonym ous precoder explicitly constrains this signal- depend ent compon ent, its re lati ve influence on th e test statistic becomes mor e pro nounce d at high SNRs, i. e ., degrad in g the receiver’ s identification capab ility and increasing th e DER. Moreover , smaller ǫ generally imposes tighter a n onymity con- straints an d consistently yields h igher DER. However , when ǫ b ecomes sufficiently small (e.g., below 10 − 3 ), the curves exhibit saturatio n, suggesting that further tighten in g provides negligible add itional anonym ity improvement. Fig. 3 illustrates the SER perform ance of th e considere d system ag ainst th e SNR for different anonymity relaxatio n s. As expec te d , increasing the SNR im p roves co mmunicatio n reliability f or all cases, r esulting in a m o notonic SER red uc- tion. In particular, for relatively high SNRs, the SER d rops to below 10 − 3 , which is a commonly accepted reliab ility threshold in c o mmunica tion systems. Mo reover , comp aring curves with different ǫ values r ev e a ls that looser anonymity constraints (larger ǫ ) achiev e lo wer SER, since the anonym ity precod e r has gre ater freedo m to optimize s ignal alignment for detection. Con versely , tigh ter anonymity e n forcem e nt restricts the feasible preco ding space an d slightly d egrades reliability . These results clearly demonstrate the inherent trad eoff between anonymity and comm unication perfo rmance. In addition , when the anonymity constraint beco mes sufficiently tight (e.g., 10 − 5 or ev en 10 − 4 ), furth er reductio n in ǫ brin g s negligible c h anges to the overall p erform ance, ind icating that reliability degrada- tion also exhib its a satu r ation effect similar to results in Fig . 2 . Fig. 4 illustrates th e SER-DER relationship acr oss dif fer ent transmit SNRs, wh ere each p oint on the c urves correspo nds to a different anonymity relaxation parameter ǫ . As ǫ decreases, i.e., the an onymity constra int b ecomes tighter (h igher DER), the SER increases, implying degraded co mmunica tion relia- 0 0.05 0.1 0.15 0.2 0.25 0.3 0.35 0.4 0.45 DER 10 -3 10 -2 10 -1 SER =6.0e-02 =5.0e-02 =4.0e-02 =3.0e-02 =2.0e-02 =1.0e-02 =5.0e-03 =5.0e-04 =5.0e-02 =4.0e-02 =3.0e-02 =2.5e-02 =2.0e-02 =1.0e-02 =1.0e-03 =1.0e-04 =2.0e-02 =1.5e-02 =1.0e-02 =7.0e-03 =4.0e-03 =1.0e-03 =1.0e-04 SNR = 16 dB SNR = 20 dB SNR = 24 dB Fig. 4. SER-DER tradeof f under dif ferent transmit SNRs a nd ǫ . 0 0.05 0.1 0.15 0.2 0.25 0.3 0.35 0.4 0.45 DER 10 -4 10 -3 10 -2 10 -1 10 0 SER =4.0e-02 =3.0e-02 =2.0e-02 =1.5e-02 =1.0e-02 =5.0e-03 =1.0e-04 =4.0e-02 =3.0e-02 =2.0e-02 =1.5e-02 =1.0e-02 =5.0e-03 =1.0e-04 =5.0e-02 =4.0e-02 =3.0e-02 =2.0e-02 =1.0e-02 =5.0e-03 =1.0e-04 N s = 5 N s = 4 N s = 3 Fig. 5. SER-DER tradeof f unde r differe nt number of data streams N s and ǫ . The SNR is set to 20 dB. bility . This SER-DER relationsh ip explicitly demon strates the cost of a nonymity in terms of detec tio n reliability . For all SNR le vels, the curves display a co nsistent mon otonic tradeoff pattern b etween anonymity and reliability . As an illustration at a fixed anonymity lev el (DE R ≈ 0 . 3 ), incr easing the SNR from 16 dB to 2 4 dB r e duces the SER from 3 . 6 × 1 0 − 2 to 3 . 1 × 10 − 3 , correspo n ding to nearly one ord er-of-magnitud e im provement in reliability . Nev e r theless, at higher SNRs, the suitable values of ǫ become smaller, indica ting that the system becomes mor e sensiti ve to ǫ . In particular, wh en ǫ becomes very small (e. g., below 10 − 3 ), the SER increases sharply while D E R improves only marginally , indicating diminishing anonymity return s. This also suggests that loosen ing anonymity requirem ents leads to significant reliability improvement in the tight ǫ region. Fig. 5 in vestigates th e impact of the numbe r of transmitted data streams N s on the an onymity-re liability tra d eoff, w h ere the SNR is fixed at 20 dB. W e see that increa sing N s enhances anonymity but degrade s comm unication reliability in terms of the SER. While all thre e curves follow the same overall 11 0 0.2 0.4 0.6 0.8 1 1.2 1.4 1.6 1.8 2 Noise variation half-range d (dB) 0.15 0.2 0.25 0.3 0.35 0.4 0.45 0.5 DER =1.0e-04 =1.0e-03 =5.0e-03 =1.0e-02 (a) SNR = 10 dB 0 0.5 1 1.5 2 Noise variation half-range d (dB) 0 0.1 0.2 0.3 0.4 0.5 0.6 DER =1.0e-04 =1.0e-03 =5.0e-03 =1.0e-02 (b) SNR = 20 dB Fig. 6. DER versus the noise-v ariation half-ra nge pa rameter d und er diff erent anonymity relaxation pa rameter ǫ . tradeoff p attern, the cur ve with lo w d ata stream (e.g., N s = 3 ) exhibits a larger DER v ariatio n ov er the same range of ǫ , and its slope is steep er compar ed with th e ca ses with higher N s . This indicates th a t the co nfiguratio ns with fe we r data streams are more sensitive to change s in the ano nymity co nstraint ǫ , and achieving th e same le vel of DER improvement requ ires a relativ ely larger increase in the SER. C onsequen tly , aggressive anonymity en forcemen t can lead to rapid reliability d egrada- tion in low-stream configur a tions. In Fig . 6 , we in vestigate how the hetero geneity of user- depend ent noise le vels affects the system’ s an o nymity perfor- mance. T o th is end , we plot the DER as a f unction of the log-do main no ise-variation half-r ange paramete r d . At the low SNR (Fig. 6 (a), 10 dB), the DER decreases as d increases, indicating reduce d ano nym ity . In this r egime, transmitter identification is p r imarily determ ined b y no ise statistics, and larger d isp e rsion in user noise v aria n ces makes the competing hypoth eses mor e distinguishable, wh ich enables more r e liab le detection. In contrast, at the high SNR (Fig. 6 (b), 20 dB), the trend reverses and the DER incr eases with d . Here, the signal- depend ent trace term contr o lled by th e anonymou s precod er dominates the likelihood metric, while the relative contribution of the n oise-depen dent constant beco mes seconda r y . Larger alias no ise v ariances redu ce th e norm a lized tr ace difference between hyp otheses, wh ich decr eases h y pothesis separab ility and conseq uently improves anonymity . These results d e m on- strate that the effect of hardware-in duced noise h eterogen eity on tr ansmitter id entification is strong ly depen dent on the operating SNR. Fig. 7 shows the noise-depe ndent constant term as a function of the n oise-variance ratio r . The curve is non- monoto nic and concave, intersecting zero at r = 1 an d at a secon d p oint r − < 1 . Co nsequently , the constant term is positi ve on ly within the narr ow interval r − < r < 1 , na m ely , when the alias user has a slightly smaller noise variance than the true user . Only in th is region c a n the alias hyp othesis produ ce a larger likelihood value and meaning fully degra d e transmitter identi- fication. For larger deviations in e ither d irection, the constant 0.8 0.9 1 1.1 1.2 1.3 1.4 -30 -25 -20 -15 -10 -5 0 5 Fig. 7. Noise-depende nt constant term E const vs. the noise-va riance rati o r = σ 2 i /σ 2 k . term becomes negative, which increases hy pothesis separabil- ity an d facilitates detection . W e clarify that this behavior high - lights the effect o f n oise h eterogen eity on anonym ity . Whe n noise statistics do minate, greater variance d isparity makes users more distinguishab le a n d redu ces DER. In contrast, when the signal-depen dent component dominates, larger alias noise variances attenuate th e n ormalized trace difference an d reduce separab ility , resu lting in improved an onymity . Thus, the influence of noise heterog eneity on the DE R dep ends o n which term g overns the test statistic. V I . C O N C L U S I O N W e studied p hysical-layer transmitter anonym ity in u plink multi-anten na systems, where we consider ed a sym bol-aware receiver perfor ming m u lti-hypo thesis transmitter identifica- tion using the known symbol m atrix, CSI, an d transmitter- depend ent h ardware noise statistics. T o enab le tractable de- sign, we intr oduced a KLD- based metric to q uantify pair w ise 12 anonymity between th e active and alias users an d der iv e d the correspo nding anonymity con straint. W e fu rther pr oposed the P-E GC to enh ance com munication r eliability at the r e- ceiv er and d ev eloped the corr e sponding a n onymous precodin g scheme und er spatial m ultiplexing. The overall design was formu late d as a co n vex optimization pro blem. Simulation re- sults, me a su red in terms of the DER and SER, sh owed that th e propo sed sche me significan tly im proves transmitter an onymity compare d with anonymity - unaware precod ing schemes while maintaining reliable commun ication performan ce. A P P E N D I X A P R O O F O F L E M M A 1 This appen dix de r iv e s the KLD between the d istributions of the r e c eiv e d signal Y und e r the true hy pothesis p k and a false hypoth esis p i , as follows: From ( 6 ), each test statistic consists of a linea r combination of a constant ter m an d a random term in volving the Frobenius norm. Hence, we define F k = k b Y k − Y k 2 F and F i = k b Y i − Y k 2 F . (A.1) Substituting the reconstru cted signals ( 3 ) and ( 4 ) into ( A.1 ) yields F k = H k H † k N k S † S − N k 2 F , F i = H i H † i YS † S − Y 2 F . (A.2) W e first compu te th e expectations o f F k and F i . Using the proper ties of the Fro benius nor m and that N k is zero-mean CSCG n oise with covariance σ 2 k I N r L , th e expec tation of F k is g iv e n by E[ F k ] = E H k H † k N k S † S − N k 2 F = E h tr ( H k H † k N k S † S − N k ) H ( H k H † k N k S † S − N k ) i = tr E[ N H k N k ] − tr E[ N k S † SN H k ] H k H † k = σ 2 k N r L − σ 2 k N t N s . (A.3) Similarly , th e expectatio n of F i is o btained as E[ F i ] = E H i H † i YS † S − Y 2 F = E h tr ( H i H † i YS † S − Y ) H ( H i H † i YS † S − Y ) i = tr E[ Y H Y ] − tr E[ Y H H i H † i Y ] S † S = σ 2 k N r L − σ 2 k N t N s + tr S H W H k H H k H k W k S − tr S H W H k H H k H i H † i H k W k S . (A.4) Consequently , the corresponding e xpectations of test statistics T k and T i follow directly by linearity of expectation as E[ T k ] = − N r L ln( πσ 2 k ) − ( N r L − N s N t ) , E[ T i ] = − N r L ln( πσ 2 i ) − σ 2 k σ 2 i ( N r L − N s N t ) − 1 σ 2 i tr S H W H k H H k H k W k S − tr S H W H k H H k H i H † i H k W k S . (A.5) W e n ext define p k ( Y ) , p ( Y ; c W k , H k ) a n d p i ( Y ) , p ( Y ; c W i , H i ) , such that T k = ln p k ( Y ) and T i = ln p i ( Y ) . When hy pothesis H k is tr u e, Y ∼ p k ( Y ) , and thus E[ T k ] = Z p k ( Y ) ln p k ( Y ) d Y , E[ T i ] = Z p k ( Y ) ln p i ( Y ) d Y . (A.6) T aking th eir difference yields E[ T i ] − E[ T k ] = Z p k ( Y ) ln p i ( Y ) − ln p k ( Y ) d Y = − Z p k ( Y ) ln p k ( Y ) p i ( Y ) d Y = − D KL ( p k k p i ) , (A.7) which implies that the KLD b etween p k and p i can be c o m- puted d irectly fro m the dif fer ence between th e expectation s of T i and T k , withou t requ ir ing the f ull d istributions of T k and T i . Finally , substituting ( A.5 ) into ( A.7 ) establishes th e result in Lem ma 1 . R E F E R E N C E S [1] D. C. Nguyen et al. , “6G Internet of Things: A comprehensi ve surve y, ” IEEE Internet Things J. , vol. 9, no. 1, pp. 359–383, J un. 20 22. [2] K. B. Letaief, W . Chen, Y . Shi, J. Zhang, and Y .-J. A. Zhang, “The roadmap to 6G: AI empowere d wirele s s netw orks, ” IEE E Commun. Mag . , vol. 57, no. 8, pp. 84 –90, Aug. 2019. [3] W . Saad, M. Be nnis, and M. Chen, “A visio n of 6G wi reless s ystems: Applica tions, trends, te chnologi es, and open research problems, ” IEEE Netw . , v ol. 34, no. 3, pp. 134–142, May/ Jun. 2020. [4] M. Mite v , A. Chorti, H. V . Poor , and G. P . Fettweis, “What physical layer s ecurit y can do for 6G security, ” IEEE Open J. V eh. T echnol. , vol. 4, pp. 375– 388, 2023. [5] V .-L . Nguyen, P . -C. Lin, B.-C. Cheng, R.-H. Hwang, and Y .-D. Lin, “Securi ty and priv acy for 6G: A survey on prospect i ve technologie s and chall enges, ” IEEE Commun. Survey s T uts. , vol. 23, no. 4, pp. 2384– 2428, 4th Quart., 2021. [6] G. T ripi, A. Iacobel li, L. Rini eri, and M. Prandini, “Securit y and trust in the 6G era: Risks and mitigation s, ” Electr onics , vol. 13, no. 11, p. 2162, 2024. [7] Y . Y ang, L. Wu, G. Y in, L. Li, and H. Zhao, “A surve y on security and pri vac y issues in Internet-o f-Things, ” IEE E Internet Things J . , vol . 4, no. 5, pp. 1250–1258, Oct. 20 17. [8] C. S andeepa, B. Siniarski , N. Kou rtelli s, S. W ang, and M. Liyanage , “A surve y on priv acy for B5G/6G: Ne w pri vac y challe nges, and research direct ions, ” J. Ind. Inf . Int egr . , vol . 30, p. 100405, Nov . 2022 . [9] P . Angueira et al. , “A s urve y of physical layer techn iques for secure wireless communication s in industry, ” IEEE Commun. Surve ys T uts. , vol. 24, no . 2, pp. 810–838, 2nd Quart., 2022. [10] M. Bloch and J. Barros, Physical-Layer Security: F r om Informat ion Theory to Security Enginee ring . Cambridge, UK: Cambridge Uni versity Press, 2011. 13 [11] X. Zhou, L. Song, and Y . Zhang, Physical Layer Securit y in W ir eless Communicat ions . Boca Ra ton, FL, USA: CRC Press, 2016. [12] M. T . Mamaghani , X. Z hou, N. Y ang, A. L. Swindlehurst, and H. V . Poor , “Performance analysis of finite blocklength transmissions over wiretap fa ding channels: An a verage informati on leakage perspe cti ve, ” IEEE T rans. W irel. Commun. , vol . 23, no. 10, pp. 13 252–13 266, Oc t. 2024. [13] Z. W ei, P . W ang, A. P . Petropulu, C. Masouros, and S. S un, “Physical layer anon ymous communications in trustworth y 6G: Fundamentals, recent adv ances, and future trend s, ” IE EE W irele ss Commun. , vol. 32, no. 2, pp. 26–32, Apr . 2025. [14] B. A. Bash, D. Goeck el, D. T owsle y , and S. Guha, “Hiding informatio n in noise: Fundamenta l limits of co vert wireless communi cation , ” IEEE Commun. Mag. , vol. 53, no. 12, pp. 26–31, Dec. 201 5. [15] S.-F . Tzeng, S. -J. Horng, T . Li, X. W ang, P .-H. Huang, and M. K. Khan, “Enhanci ng security and priv acy for identity-ba sed batch verificati on scheme in V ANETs, ” IEE E T rans. V eh. T echnol. , vol. 66, no. 4, pp. 3235–3248, Apr . 2017. [16] Z. Lu, G. Qu, and Z. Liu, “A surve y on recent adv ances in vehic ular netw ork securit y , trust, and priv acy, ” IEEE T rans. Int ell. T ransp. Syst. , vol. 20, no. 2, pp. 760–776, Feb. 2019. [17] P . T edeschi, F . A. Al Nuaimi, A. I. A wad , and E. Nata lizio, “Pri v acy- aw are remote ident ificati on for unmanne d aeri al vehicles: Current solutions, potential threats, and future directions, ” IE EE T rans. Ind. Informat. , vol. 20, no. 2, pp. 1069–1080, Feb. 2024. [18] A. Fotouh i et al. , “Su rve y on U A V cellular communicat ions: Practi cal aspects, standa rdization adv ancements, regulat ion, and securit y chal- lenges, ” IEEE Commun. Surve ys T uts. , vol. 21, no. 4, pp. 3417–3442, 4th Quart., 2019. [19] S. Pai et al. , “Confidential ity in sensor networks: Transact ional infor- mation, ” IEEE Secur . Privacy Mag . , vol . 6, no. 4, pp. 28 –35, Jul./Aug. 2008. [20] P . Gope and T . Hwang, “BSN-Care: A secure IoT -based modern health - care system using body sensor network, ” IEEE Sensor s J. , vol. 16, no. 5, pp. 1368–1376, Mar . 201 6. [21] Z. W ei, C. Masouros, H. V . Poor, A. P . Petropul u, and L. Hanzo, “Physica l layer anonymous precoding: T he path to priv acy-pre s erving communicat ions, ” IEEE W ir eless Commun. , vol. 29, no. 2, pp. 154–160, Apr . 2022. [22] Z. W ei, F . Liu, C. Masouros, and H. V . Poor , “Funda mentals of physica l layer anon ymous communicati ons: Sender detection and anonymous precodi ng, ” IE EE T rans. W irel. Commun. , vol. 21, no. 1, pp. 64–79, Jan. 2022. [23] Z. W ei, C . Masour os, P . W ang, X. Zhu, J. W ang, and A. P . Petropu lu, “Physica l layer anonymous preco ding design: From the perspect i ve of anon ymity entrop y, ” IEEE J. Se l. Areas Commun. , vol. 40, no. 11, pp. 3224–3238, Nov . 2022. [24] Z. W ei, C. Masouros, X. Zhu, P . W ang, and A. P . Petro pulu, “PHY layer anon ymous precodi ng: Sender detecti on performance and div ersity- multiple xing trade of f, ” IE EE T rans. W ir el. Commun. , vol. 23, no. 5, pp. 4531–4545, May 2024. [25] Y . Cui, Z. W ei, S. Sun, X. Zhu, C. Masouros, and A. P . Petropulu, “Phys- ical layer anonymous precod ing under CSI and hardware-imper fection s: A KLD-base d appro ach, ” IE E E T rans. W irel ess Commun. , v ol. 25, pp. 6225–6239, 2025. [26] Y . Cui, Z. W ei, C. Masouros, X. Zhu, and H. T ang, “On the closed-form detec tion error rate an alysis in physical laye r anon ymous communica- tions, ” IEEE T rans. V eh. T ech nol. , vol. 73, no. 8, pp. 12 195–12 200, Aug. 2024. [27] M. W ang, Z. W ei, C. Masouros, A. Guo, and N. Jia, “Closed-form detec tion error rate analysi s in PHY-anonymous MIMO MAC channel, ” IEEE T rans. V eh. T echnol. , 2025, early Access. [28] R. Song and H. T ang, “LAA: Link-layer anon ymous access for tactic al MANETs, ” in Proc. IEEE Military Communications Conf. (MILCOM) , Orlando, FL, USA, 2012, pp. 1–7. [29] C. Studer , M. W enk, an d A. Bur g, “MIMO transmission wi th residual transmit-R F impa irments, ” in Pr oc. Int. ITG W orkshop Smart A ntennas (WSA) , Bremen, Germany , 2010, pp. 189–196. [30] E. Bj ¨ ornson, J. Hoydis, M. Kou ntouris, and M. Debbah, “Hardware impairment s in large-sca le MISO systems: Ener gy effic ienc y , estimati on, and capacity limit s, ” in Proc. 18th Int. Conf. Digit. Signal Proce ss (DSP) , Santorin i, Greec e, 2013, pp. 1– 6. [31] X. Zhang, M. Matthaiou, E. Bj ¨ ornson, M. Coldre y , and M. Debbah, “On the MIMO capac ity with residual transcei ver hardware impairments, ” in Pr oc. IEEE Int. Conf. Commun. (ICC) , Sydney , Australia, 2014, pp. 5299–5305. [32] H. Suzuki, T . V . A. Tran, I. B. Collings, G. Daniels, and M. Hedle y , “Tr ansmitter noise effec t on the performance of a MIMO-OFDM hard- ware implemen tation achie ving improved co verag e, ” IEEE J. Sel. Areas Commun. , vol. 26, no. 6, pp. 867–876, Aug. 20 08. [33] S. M. Kay , F undamental s of Statistical Signal P r ocessing, V olume 2: Detect ion The ory . Prentice Hall, 1998. [34] T . M. Cov er and J. A. T homas, Elements of Informatio n Theory . John W iley & Sons, 199 9. [35] C. Masouros and G. Zheng, “Exploiting known interfe rence as green signal power for do wnlink beamforming optimiz ation, ” IEEE T rans. Signal Pro cess. , vol. 63, no. 14, pp. 3628–3640, Jul. 2015. [36] Z. W ei, C. Masouros, K.-K. W ong, and X. Kang, “Multi -cell interferenc e expl oitat ion: Enhancing the po wer efficien cy in cell coordinati on, ” IEE E T rans. W ire less Commun. , vol. 19, no . 1, pp. 54 7–562, Jan. 2020. [37] Z. W ei, C. Masouros, and F . Liu, “Secure directi onal modulation with fe w-bit phase shifters: Optimal and iterati ve-clo sed-form designs, ” IEEE T rans. Commun. , vol. 69, no. 1, pp. 486–500, Ja n. 2021. [38] A. L i, C. Masouros, B. V ucetic , Y . Li, and A. L. Swind lehurst, “Inter- ference exploit ation precoding for multi-le vel modulations: Closed-f orm solutions, ” IEEE T rans. Commun. , vol. 69, no. 1, pp. 291–308, Jan. 2021. [39] Z. W ei, J. W ang, C. Masouros, T . Xu, J. Che n, an d A. Li, “Su b-block le vel interference exploitat ion precoding in satellite communicatio ns, ” in Pr oc. Int. W irel ess Commun. Mobile Comput. Conf. (IWC MC) , Limassol, Cyprus, 2024, pp. 0537–0542. [40] S. Boyd and L. V anden bergh e, Con vex Optimizatio n . Cambridge , U.K.: Cambridge Uni v . Press, 2 004. [41] M. T . Mamaghani and Y . Hong, “Aerial intell igent reflecting surfac e- enable d terahertz cov ert communicati ons in beyo nd-5G Internet of Things, ” IE EE Internet Things J. , vol. 9, no. 19, pp. 19 012–19 033, Oct. 2022. [42] K.-Y . W ang, A. M.-C. So, T . -H. Chang, W .-K. Ma, and C. -Y . Chi, “Outage constrained robust transmit optimizat ion for multiuser MISO do wnlinks: Tractabl e approximat ions by conic optimization , ” IEEE T rans. Signal Proc ess. , vol. 62, no. 21, pp. 5690–5705, No v . 2014.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment