Exploiting Liquidity Exhaustion Attacks in Intent-Based Cross-Chain Bridges
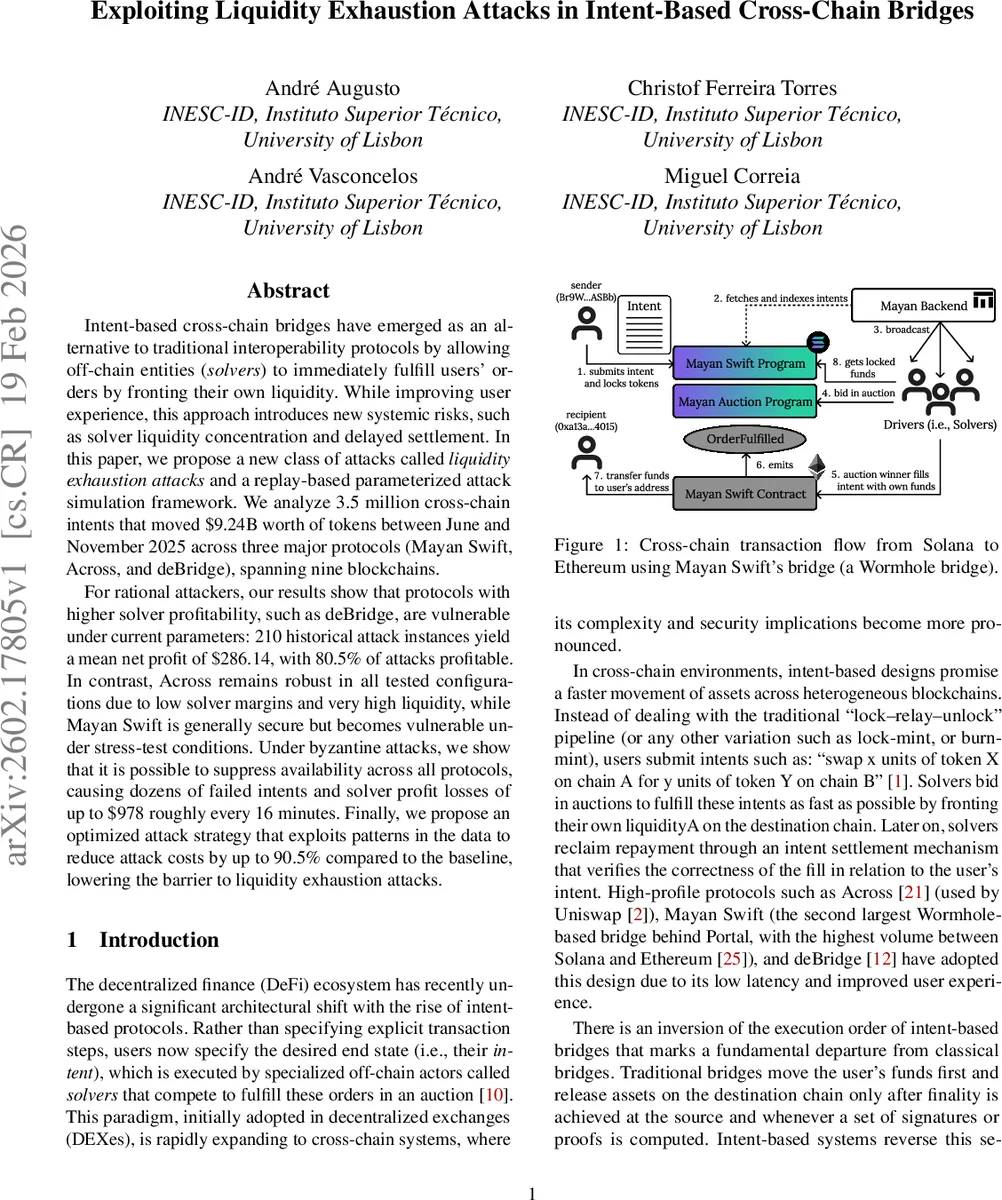
Intent-based cross-chain bridges have emerged as an alternative to traditional interoperability protocols by allowing off-chain entities (\emph{solvers}) to immediately fulfill users’ orders by fronting their own liquidity. While improving user experience, this approach introduces new systemic risks, such as solver liquidity concentration and delayed settlement. In this paper, we propose a new class of attacks called \emph{liquidity exhaustion attacks} and a replay-based parameterized attack simulation framework. We analyze 3.5 million cross-chain intents that moved $9.24B worth of tokens between June and November 2025 across three major protocols (Mayan Swift, Across, and deBridge), spanning nine blockchains. For rational attackers, our results show that protocols with higher solver profitability, such as deBridge, are vulnerable under current parameters: 210 historical attack instances yield a mean net profit of $286.14, with 80.5% of attacks profitable. In contrast, Across remains robust in all tested configurations due to low solver margins and very high liquidity, while Mayan Swift is generally secure but becomes vulnerable under stress-test conditions. Under byzantine attacks, we show that it is possible to suppress availability across all protocols, causing dozens of failed intents and solver profit losses of up to $978 roughly every 16 minutes. Finally, we propose an optimized attack strategy that exploits patterns in the data to reduce attack costs by up to 90.5% compared to the baseline, lowering the barrier to liquidity exhaustion attacks.
💡 Research Summary
The paper investigates a novel class of attacks—Liquidity Exhaustion Attacks—targeting intent‑based cross‑chain bridges, where off‑chain actors called solvers front liquidity to fulfill user intents instantly and are reimbursed only after an asynchronous settlement. By front‑loading liquidity, solvers become temporarily vulnerable; an adversary can submit a burst of high‑value intents to drain the available solver liquidity (the “Intent Flooding” stage) and then either profit by fulfilling their own intents (rational attack) or simply disrupt service (Byzantine attack).
The authors collected a comprehensive dataset covering June‑November 2025, comprising 3.5 million intents moving $9.24 billion across nine blockchains through three leading protocols: Mayan Swift, Across, and deBridge. Detailed on‑chain reconstruction yielded per‑solver liquidity, settlement delays, protocol fees, and profit margins. Key protocol characteristics emerged: deBridge exhibits extreme solver centralization (one solver handles 94 % of fills) and high profit margins (≈1.13 %); Across has many solvers, low margins (≈0.018 %), but long settlement windows (≈2 hours due to an optimistic oracle); Mayan Swift sits between the two, with moderate margins and a 20‑minute median settlement time.
The attack model formalizes costs (induction cost proportional to α·L(t)·F_prot plus gas, fill costs for gas and auction bids) and revenues (V_i·p_i per filled intent). Net profit is revenue minus all costs and an ε term for market impact. Simulations explore a range of exhaustion parameters α, gas price scenarios, and timing windows.
Results show that deBridge is highly vulnerable: 210 historical attack instances generated an average net profit of $286.14, with 80.5 % of attacks profitable. The high profit margin and the concentration of liquidity in a single solver make the attack cheap and effective. Across remains robust; its low margins and abundant liquidity render rational attacks unprofitable, though Byzantine attacks can still cause temporary denial‑of‑service by exploiting the 2‑hour fraud‑proof window. Mayan Swift is generally secure but becomes vulnerable under stress‑test conditions (elevated α, longer settlement delays).
The authors also present an optimized attack strategy that leverages observed temporal demand concentration (most volume occurs between 10 am–2 pm EST) and large‑intent clustering. By learning historical intent patterns, the attacker can schedule flooding to maximize α while minimizing capital outlay, reducing attack costs by up to 90.5 % compared with a naïve baseline.
Finally, the paper proposes mitigation measures: diversify solver participation to avoid centralization, shorten settlement windows or employ fast optimistic oracles, introduce insurance‑style reserve pools that automatically replenish drained liquidity, implement dynamic fee or spread adjustments that rise when solver liquidity drops, and enforce time‑of‑day or size caps on intents during peak periods. These guidelines aim to harden intent‑based bridges against both profit‑driven and disruptive liquidity exhaustion attacks.
Overall, the study provides the first empirical quantification of liquidity‑exhaustion risks in intent‑based cross‑chain bridges, demonstrates their practical feasibility, and offers concrete design and operational recommendations for the DeFi community.
Comments & Academic Discussion
Loading comments...
Leave a Comment