Covert Routing with DSSS Signaling Against Cycle Detectors
This paper investigates covert multi-hop communication in wireless networks where an adversary employs a cyclostationary (cycle) detector to reveal hidden transmissions. The covert route employs direct sequence spread spectrum (DSSS) signaling to ens…
Authors: Swapnil Saha, Rahul Aggarwal, Fikadu Dagefu
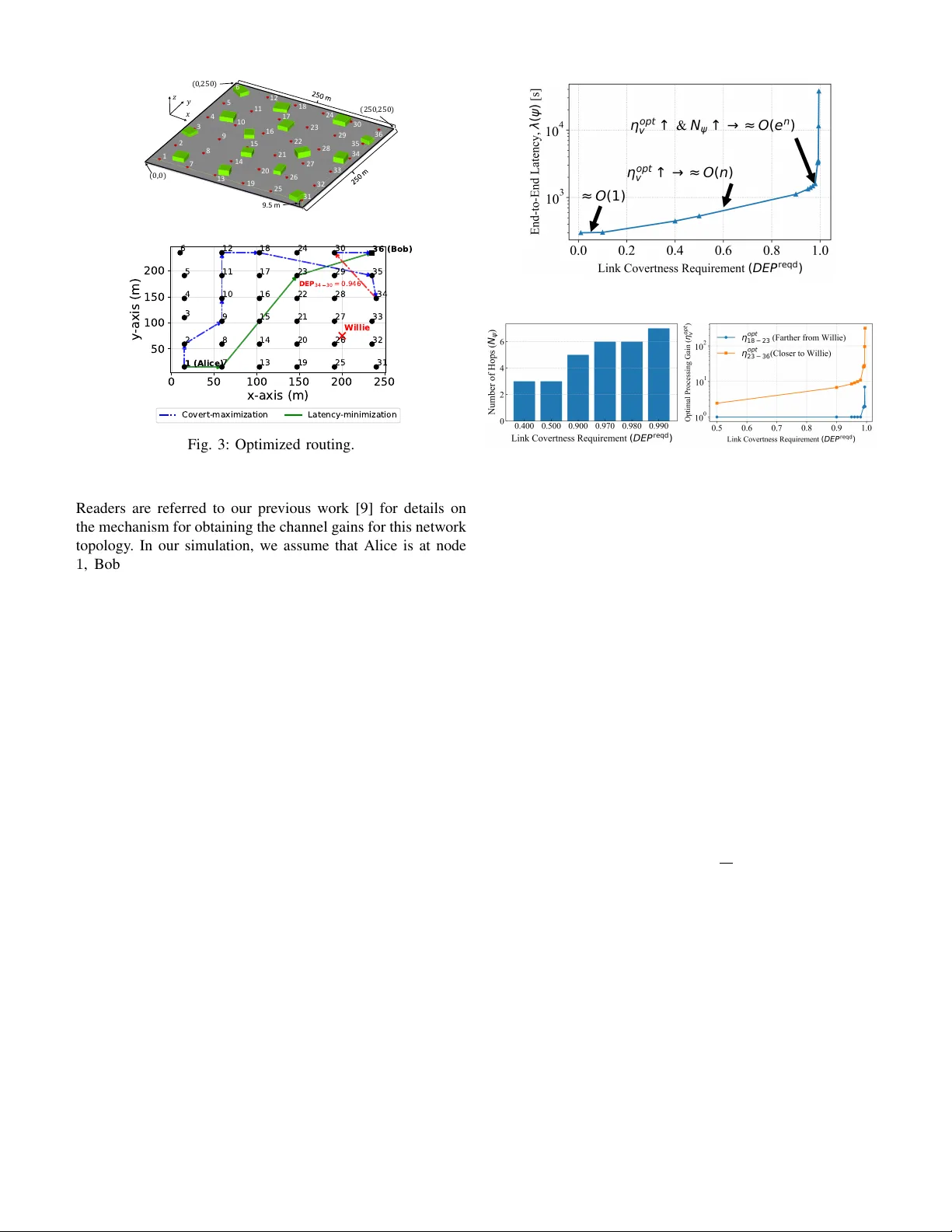
Co v ert Routing with DSSS Signaling Against Cycle Detectors Swapnil Saha ∗ , Rahul Aggarwal ∗ , Fikadu Dagefu † , Justin K ong † , Jihun Choi † , Brian Kim † , and Predrag Spasoje vi ´ c ∗ ∗ WINLAB, Rutgers Univ ersity , New Brunswick, NJ, USA † U.S. Army Combat Capabilities Dev elopment Command (DEVCOM) Army Research Laboratory , Adelphi, MD, USA Abstract —This paper in vestigates covert multi-hop communi- cation in wireless networks wher e an adversary employs a cyclo- stationary (cycle) detector to re veal hidden transmissions. The covert route employs direct-sequence spread spectrum (DSSS) signaling to ensur e either maximum end-to-end covertness max- imization or minimum latency minimization—under quality-of- service (QoS) and link budget constraints. Optimal bandwidth, transmit power , and spreading gain for each hop jointly sat- isfy reliability and either rate or covertness requir ements. W e show the equi valence between the covertness- and the detection SNR gain –based widest-path formulations and, hence, enabling efficient route computation. Numerical simulations in a realistic 3 D en vironment illustrate that ( i ) end-to-end latency increases exponentially with the cov ertness r equirement, ( ii ) the end-to-end latency increase is super -linear with the packet size M , and ( iii ) cycle and energy detectors impose different latency beha vior as a function of the message length and the covertness requirement. The proposed framework provides important insights into re- source allocation and routing design f or covert networks against advanced detection adversaries. Index T erms —cov ert communication, lo w probability of detec- tion (LPD), detection of error probability (DEP), direct sequence spread spectrum (DSSS), wireless routing, resource allocation I . I N T RO D U C T I O N Low probability of detection (LPD) or cov ert communica- tions [1] refers to a communication system that aims to hide its transmissions from a w atchful adversary . Intuitiv ely , reducing a wireless signal’ s transmission power and data rate lowers the likelihood of transmissions being detected by unintended observers. Multi-hop routing improves covertness by enabling reduced-power hop-by-hop transmission. In addition, Direct Sequence Spread Spectrum (DSSS) modulation is an ef fecti ve technique for achie ving covert communication, as it spreads the message signal across a wider bandwidth, thereby modulat- ing the signal to a level comparable to or exceeding the noise lev el and providing inherent covertness. Ne vertheless, the sta- tistical characteristics of the spreading codes typically exhibit characteristic features/patterns that an adversary can exploit to infer the presence of a transmitted signal [2]–[4]. Beyond security considerations, practical communication systems must also satisfy the Quality of Service (QoS) requirements [5], [6], such as low latency , high throughput, and reliability . In [7], authors take an information-theoretic approach to study communication covertness, an approach that does not consider the limitations of a practical detector . Authors in [7]– [10] study the covertness against an adversary employing an This material is based on work supported in part by the Army Research Office / Army Research Laboratory under Contract No. W911NF-23-2-0197. Fig. 1: System model of multi-hop network. Each hop uses DSSS signals to communicate with the next hop. energy detector . Adv ersary that exploits the signal’ s cyclosta- tionary properties (i.e., spectral correlations) has been studied extensi vely [5], [11]. W e refer to such an adversary as a cycle detector . The authors [2]–[4] identify dif ferent strategies that enhance covertness against cycle detectors. In [5], we compare the covertness of single link communication systems against energy and c ycle detectors under common communi- cation QoS requirements. Moti vated by the multi-hop routing cov ertness advantage, se v eral works optimize per-hop resource allocation and routing jointly [9], [12]–[14] ag ainst energy detectors. On the other hand, to the best of our kno wledge, no prior research has studied the covertness of multi-hop routing schemes against adversaries employing cycle detectors. In this paper , we examine a wireless covert routing prob- lem comprising Alice, Bob, multiple friendly relaying nodes, and a passi ve adversary , W illie (Fig. 1), employing a cycle detector . Alice transmits a confidential message with M bits, modulated by DSSS, to Bob . Alice prefers a lo wer probability of detection by W illie, with the help of relay nodes whose transmissions satisfy QoS constraints. The message generated by Alice is transmitted hop-by-hop to Bob . Direct communi- cation between Alice and Bob may require high transmitted power due to channel fading and QoS requirements, thereby rev ealing her communication to Willie. Con v ersely , multi- hop communications may provide more opportunities for the adversary to detect transmissions and/or increase end-to-end message-routing latency . K ey contributions are: • W e propose two nov el routing algorithms for cov ert multi-hop communication under a c ycle detector with QoS guarantees: a cov ertness-maximization and a latency-minimization approach. • W e validated the proposed approach in a realistic ( 3 D ) en vironment, re vealing that the end-to-end latenc y ex- hibits a sub-linear , linear , and and exponential with an increase in the covertness requirement. Additionally , with an increase in the message size M , the route latenc y ex- hibits super-linear and exponential growth under relaxed and stringent cov ertness requirements, respectiv ely . • W e also illustrate that, for latency maximization, the adversary may fav or the c ycle detector at low co vert requirements and the energy detector under stringent cov ert requirements. Section II giv es the legitimate network and signaling model. Section III introduces the per-hop cycle detector . Section IV formulates the optimization problems. Section V describes our proposed method. Section VI giv es the numerical results. I I . N E T W O R K & S I G N A L M O D E L A. Network Model As shown in Fig. 1, Alice can select multiple possible routes to transmit a message to Bob . W e define Ψ as the set of all possible routes. Let us denote ψ = ( v 1 , . . . , v N ψ ) ∈ Ψ as a route from Alice to Bob, where v i = ( T v i , R v i ) is the single- hop communication link between transmitter T v i and receiv er R v i , and N ψ is the number of hops of the route ψ . Here, T v 1 and R v N ψ are Alice and Bob, respectively . Alice generates a message of M bits, which is transmitted sequentially , hop by hop, along the selected route ψ until it reaches Bob . As the analysis of each hop communication is identical, we will drop the hop inde x i and use v to denote a single-hop communica- tion link. In the network, each of the transmitters { T v } along the path ψ adapti vely selects bandwidth Ω v and transmitted power P v based on the dynamic wireless environment, QoS requirements, and co vert requirements. There are multiple time slots between any transmitter T v and R v . Transmitter T v chooses one of the time slots randomly (discussed in Sec. III) and sends the message signal in DSSS format (described in Section II-B). W illie observes signals from the selected hops and decides whether Alice’ s transmission is present (W illie’ s detection mechanism is described in Sec. III-B). B. Single Hop T ransmission Model In our study , we consider that each node transmitter T v uses DSSS signals to send M bits to the recei ver R v as follo wing. x v ( t ) = p P v M − 1 X m =0 b m L v − 1 X l v =0 c l v p ( t − mT b v − lT c v ) , (1) where P v denotes the transmit power , { b m } is i.i.d. symbols with equal-probable v alue ± 1 , T b v is the bit duration, and { c l v } L v − 1 l v =0 is a bipolar spreading code of length L v . The chip duration is T c v = T b v /L v , and p ( t ) is a root raised cosine chip pulse with roll-off factor β = 1 and energy 1 /L v . The signal bandwidth is approximately Ω v = 1 T c v = L v T b v , and the uncoded data rate at hop v is D v = 1 /T b v bps. (For simplicity , in this study , we focus on the uncoded data rate.) The processing g ain is defined as η v ≜ Ω v D v = L v , implying that, under perfect despreading, the receiver achiev es an SNR gain of η v . W e assume that the intended receiv er R v knows the spreading code { c l v } L v − 1 l v =0 , whereas W illie does not. Accordingly , the SNRs are S N R v = P v | h T v ,R v v | 2 N 0 Ω v η v , S N R W v = P v | h T v ,W v | 2 N 0 Ω v . Here, N 0 / 2 denotes the po wer spectral density (PSD) of the additiv e white Gaussian noise. h T v ,R v v and h T v ,W v represent the channel gains between the transmitter T v and its intended receiv er R v , and between T v and W illie, respectively . Finally , the link reliability between T v and R v is quantified by the bit error rate (BER) B E R v = Q √ 2 × S N R v , where Q ( · ) is the complementary Gaussian distribution. I I I . C OV E RT N E S S A G A I N S T C Y C L E D E T E C T O R A. Backgr ound: Cycle Detector If a signal has an inherent periodic structure, the Degree of Cyclostationarity (DCS) [11] is an excellent feature for detecting the presence of the signal. The DSSS signal, with the same spreading code repeating, has a higher DCS v alue than the white noise signal. The DCS metric is calculated as follows. For a periodic autocorrelation function R y ( t, τ ) = E [ y ( t ) y ∗ ( t − τ )] with period T , the Cyclic Autocorrelation Function (CAF) is R α y ≜ 1 T R T / 2 − T / 2 R y ( t, α ) e − i 2 π αt dt where α = k T , for k = 1 , 2 , 3 .. are the c ycle frequencies. The Spectral Correlation Function (SCF) of y ( t ) , S α y ( f ) , is the Fourier T ransform of R α y ( τ ) . Then the DCS is defined as D C S y ≜ X α =0 R + ∞ −∞ | S α y ( f ) | 2 d f R + ∞ −∞ | S α =0 y ( f ) | 2 d f . (2) For a finite segment of signal y ( t ) , t ∈ (0 , T 0 )] , the SCF is estimated as follows ˆ S α Y ( f ) = Y T 0 f − α 2 Y ∗ T 0 f + α 2 , where Y T 0 ( t, f ) = R t + T 0 / 2 t − T 0 / 2 y ( u ) e − i 2 π f u du is time-varying finite-time complex spectrum [15]. Plugging the estimate SCF , ˆ S α Y ( f ) , in Eq. (2), we calculate the estimated DCS, [ D C S y . B. Single Hop Cycle Detection at W illie For single link transmission, at hop v , transmitter T v chooses to transmit or not with probability 1 / 2 . W e assume that W illie has the knowledge of when the transmission slots start and ends. This assumption corresponds to the worst-case scenario from the perspecti ve of co vertness. W illie selects one of the following two hypotheses: H 0 v : y W v ( t ) = n W v ( t ) , t ∈ (0 , T 0 ) , H 1 v : y W v ( t ) = h T v ,W v x v ( t ) + n w v ( t ) , t ∈ (0 , T 0 ) , where T 0 = M T b v is the slot duration; h T v ,W v is the channel gain form transmitter T v to W illie; H 0 v is the no transmission null hypothesis; and H 1 v denotes the alternate hypothesis when the transmission between T v and R v is present. T o detect the presence of the hop transmission, W illie estimates the strength of the cyclic feature by calculating the DCS value. The white noise does not have cyclic features, whereas the DSSS signal at Eq. (1) does. The strength of c yclic properties can be quantified via Degree of Cyclostationarity (DCS) [5], [16]. W illie compares the statistics [ D C S W v D 1 v ≷ D 0 v δ v , where [ D C S W v is the estimated DCS of y W v ( t ) and δ v is the decision threshold. D 0 v and D 1 v denote decisions in fa vor of H 0 v and H 1 v . The detection error probability (DEP) at W illie for link v is DE P v = ( P M D v + P F A v ) , where P MD v ≜ P D 0 v | H 1 v and P F A v ≜ P D 1 v | H 0 v are the probabilities of miss detection and false alarm, respectively . Further, we omit the prior probability factor . 5 without loss of generality . W illie’ s goal is to minimize each hop’ s detection error probability , D E P v , by selecting the optimum DCS threshold δ opt V . It selects the threshold [5] : δ opt v = arg max δ v D E P v ( S N R W v ) . where S N R W v is the SNR at Willie when the signal is present. Here, we assume that W illie has the perfect knowledge of all cycles in x v ( t ) , and the S N R W v (when present and when not) so that it can compute the DE P v (worst-case scenario from a cov ertness perspectiv e). Follo wing [5], the δ opt v is obtained via exhausti v e search due to the lack of an efficient analytical approach. In [5], we argue that D E P v ∝ 1 S N R W v , which is due to the f act that increased SNR at Willie both ensures increased distance between the two hypotheses measured via the DCS as well as an increased accuracy in estimating DCS. W e also show that DEP decreases with observ ation time, i.e., D E P v ∝ 1 M . In the above, ∝ indicates a monotonic non-decreasing relationship between parameters and statistics, which we exploit in this paper . I V . P E R F O R M A N C E M E T R I C S & P R O B L E M F O R M U L A T I O N W e aim to study two routing optimization problems in which Alice sends M bits to Bob . The first one is how cov ertly the M bits reach Bob from Alice; end-to-end covert maximization. The second one is how quickly M bits can be transferred to Bob, with a focus on minimizing end-to-end latency . For both routing optimization problems, we impose constraints to ensure QoS requirements. W e will first quantify the performance metrics for each problem and then provide an explicit description of our problem formulation. Here, for quantifying end-to-end co vertness, we assume that Willie has complete knowledge of the optimized route from Alice to Bob, ψ = ( v 1 , v 2 , . . . , v N ψ ) ∈ Ψ . This represents the worst-case condition for covert communication and the most fav orable case for W illie. A. P erformance Metrics End-to-end Covertness D E P ( ψ ) : W e define the end-to-end cov ertness of a route ψ as follo ws. Based on the definition of cov ertness in Sec. III-B, each hop’ s transmission is indepen- dent from others. If any hop v ∈ ψ is weak in cov ertness and cannot hide communication, the end-to-end cov ertness collapses, and W illie can detect Alice’ s transmissions. Thus, end-to-end covertness of the route ψ is constrained by the weakest link, i.e., D E P ( ψ ) = min v ∈ ψ D E P v . End-to-end Latency λ ( ψ ) : For a single hop v , we define the communication latency λ v as the expected time to send M bits to the ne xt hop, i.e., λ v = M D v where D v is the link data rate (uncoded). The end-to-end/total latency for the route ψ is the sum of all the link latencies, λ ( ψ ) = P v ∈ ψ λ v . W e note that this formulation provides a simplified estimate of o verall latency , as it ignores queuing delays and protocol ov erheads of hop-to-hop data transmission. B. End-to-End Covertness Maximization The end-to-end covertness can be maximized by maximiz- ing the weakest DEP in the route ψ : max P v ,η v ,ψ ∈ Ψ min v ∈ ψ D E P v , s.t. D ≥ D reqd , [ B E R v , Ω v , P v ] ⪯ [ B E R req d , Ω max , P max ] (3) Here, D req d is the (average) required link data rate; B E R req d , the bit error rate, ensures link reliability; Ω max and P max are the bandwidth and transmitted power budgets of a single link. C. End-to-End Latency Minimization W e minimize the ov erall latency min P v ,η v ,ψ ∈ Ψ X v ∈ ψ λ v , s.t. D E P v ≥ DE P reqd , [ B E R v , Ω v , P v ] ⪯ [ B E R req d , Ω max , P max ] (4) under the constraint that each link satisfies the common required covertness D E P req d as well as the above-mentioned QoS and link budget constraints. V . P R O P O S E D S O L U T I O N Based on the system model from Sec. II, metrics (and constraints) for each hop in a route are independent. Thus, end-to-end optimality can be achieved by first achieving link optimality , follo wed by optimum route selection. In the next section, we will first describe our approach for single-link optimization, followed by optimal route selection. A. Single Hop Covert Maximization max P v ,η v D E P v , s.t. D v ≥ D reqd , [ B E R v , Ω v , P v ] ⪯ [ B E R req d , Ω max , P max ] (5) Solution of (5) is detailed in our previous work [5]. Here, we summarize the results in the context of this study . Eq. (5) is maximized by the optimum spreading gain η opt = Ω max /D req d and the link transmission power P opt v = S N R req d | h T v ,R v v | 2 · N 0 Ω max η opt . both achie ved by selecting maximum bandwidth Ω opt v = Ω max and the minium required link rate D opt v = D req d . Here, SNR of Bob’ s received signal, S N R req d , ensures that the reliability constraint, B E R req d , common to all links, is satisfied with equality . The maximum D E P max v is achiev ed by the mini- mum detection SNR at W illie, S N R W,min v which maximizes the detection SNR gain θ v ≜ S N R v S N R W v and achieves θ max v = S N R req d S N R W,min v = | h T v ,R v v | 2 | h T v ,W v | 2 × η opt . B. Single Hop Latency Minimization Single-hop latency minimization requires min P v ,η v λ v , s.t. D E P v ≥ DE P reqd , [ B E R v , Ω v , P v ] ⪯ [ B E R req d , Ω max , P max ] . (6) The link co vertness and reliability requirements impose the op- posing SNR constraints S N R W v ≤ S N R W,max v and S N R v ≥ S N R req d v at Willie and Bob, respectively . T ogether they require that the link transmitted power P v satisfies S N R req v | h T v ,Rv v | 2 · D v ≤ P v N 0 Ω ≤ S N R W,max v | h T v ,W v | 2 . And, hence, λ v ≥ M S N R req v | h T v ,R v v | 2 P v N 0 ≥ M S N R req v S N R W, max v | h T v ,W v | 2 | h T v ,R v v | 2 1 Ω . (7) Hence, the maximum power and minimum link latency , P max,reqd v = SNR W, max v | h T v ,W v | 2 N 0 Ω max , λ min v = M SNR reqd v SNR W, max v | h T v ,W v | 2 | h T v ,R v v | 2 1 Ω max . ensure all constraints are satisfied. The following lemma directly follows the abov e discussion and inequality (7). 1 Lemma V .1. Let M be the packet size. The solution of (6) is the latency λ min v , ac hievable with bandwidth Ω max , tr ansmit power P max,req d v , and spreading gain η opt v = Ω max λ min v / M . Remark: The optimal transmit po wers are determined by the minimum detection SNR required for link reliability at Bob’ s, S N R req d v , and by the maximum SNR still ensuring link covertness at W illie’ s, S N R W,max v , for the covertness and latency optimization problems, respectiv ely . The optimal spreading gains are determined by the required link rate, D req d , and the minimum r eliable and covert latency , λ min v , for the cov ertness and latenc y optimization problems, respecti v ely . 1 For simplicity without loss of generality we assume that P max,req d v ≤ P max and that the spreading gain η v is not necessarily an integer . C. Covert Routes: Covertness vs Latency Optimization The route that maximizes covertness is the solution of: max ψ ∈ Ψ min v ∈ ψ D E P max v . (8) W e solve this problem using a Dijkstra-based widest path algorithm [17], which maximizes the minimum edge weight along the route by replacing the path-length metric with a bottleneck distance metric. Consequently , the edge with the lowest weight has to be found first. As mentioned in Sec. III-B, the D E P v computation is based on the empirical distributions under the null and alternativ e hypotheses obtained via Monte Carlo simulation. which is computationally intensi v e. Instead, here, we propose to solve the equi v alent problem max ψ ∈ Ψ min v ∈ ψ θ max v , (9) based on the detection SNR gain parameter θ v . Theorem V .2. The r outes (8) and (9) ar e equivalent. Pr oof. The proof relies on θ v ∝ DE P v in problem (5) (see [5] and V -A). The reliability constraint in (5) requires that the opti- mal detection SNR at Bob’ s is identical ( S N R ≡ v S N R req d ) for all links and, additionally , DE P v ∝ 1 S N R W v (see Sec. III-B). Consequently , D E P v is a non-decreasing function of θ v . Now , let ( v 1 , . . . , v N ) index the hops ordered according to DEP v 1 ≤ DEP v 2 ≤ · · · ≤ DEP v N . Then, the corresponding gains are ordered as θ v 1 ≤ θ v 2 ≤ · · · ≤ θ v N . Hence, the equiv alence of the two problems follo ws. The covert r oute that minimizes latency is the solution of min ψ ∈ Ψ X v ∈ ψ λ min v , and is solved using Dijkstra’ s shortest path algorithm. V I . N U M E R I C A L R E S U LT S In this section, we present numerical simulation results to validate the system’ s performance under our proposed solution 2 . W e perform our joint resource allocation and rout- ing within an emulated 3 D -propagation en vironment. Unless otherwise specified, all simulation results are obtained using the following parameter settings: maximum available band- width is Ω max = 10 M H z , the noise spectral density is N 0 = − 113 dBm / Hz , and message size M = 100 M b . W e choose B E R req d = Q ( √ 2 × 10) − → S N R req d = 10 dB as constraint for reliable communication. As a network topology (Fig. 2), we use an emulated 3 D en vironment (250 × 250 × 9 . 5) m 3 with 36 nodes (sho wn in red cones). The green cuboids indicate concrete b uildings. W e use a ray-tracing approach [18] to obtain channel data, assuming a center frequency of 900 M H z for the transmitted signal. 2 The simulation code is av ailable at https://github .com/swapnil-saha/Cov ert- Routing-with-DSSS-Signaling-Against-Cycle-Detectors.git 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 9.5 m 𝑧 𝑦 𝑥 ( 0 , 0 ) ( 0 , 250 ) ( 250 , 2 50 ) Fig. 2: Network topology . 0 50 100 150 200 250 x-axis (m) 50 100 150 200 y -axis (m) 1 (Alice) 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 (Bob) Willie D E P 3 4 3 0 = 0 . 9 4 6 Covert-maximization Latency -minimization Fig. 3: Optimized routing. Readers are referred to our previous work [9] for details on the mechanism for obtaining the channel gains for this network topology . In our simulation, we assume that Alice is at node 1 , Bob is at node 36 , and W illie is at the position between node 27 and node 26 (Fig. 3). A. Optimal Covert Routes Fig. 3 illustrates the optimized routing paths obtained from the solutions of (3) and (4). For the co vert maximization problem (3), each link’ s required throughput is set to D reqd v = 2 . 5 Mbps , while for the latency minimization problem (4), the required link cov ertness is fix ed at DE P reqd v = 0 . 85 . For the covertness- maximizing route, the link cov ertness v alues are [0 . 980 , 0 . 979 , 0 . 971 , 0 . 981 , 0 . 980 , 0 . 960 , 0 . 950 , 0.946 , 0 . 949] , yielding an end-to-end covertness of D E P ( ψ ) = 0 . 946 . For the latency-minimizing route, the total time to transmit a message of size M = 100 Mb is 30 s . T wo main observ ations can be drawn: (i) Transmitters located closer to W illie achie ve lower link cov ertness than those that are far aw ay: nodes 30 , 35 , and particularly 34 (the bottleneck hop sho wn by the red dotted link). (ii) The latency-minimizing route employs fewer hops and lies closer to W illie. This is intuitive: in the covertness-maximization formulation, the optimization prioritizes per -link cov ertness, whereas in the latency- minimization formulation, the relaxed covertness constraint permits higher transmit po wer , enabling longer transmission distances between hops and thus reducing end-to-end delay . Moreov er , optimizing routes of both problems (8) and (9) provides the same optimum routing (not sho wn in the figure), confirming the claim of Theorem V .2. (a) (b) (c) Fig. 4: End-to-end latency versus link covertness requirement, showing a transition from constant O (1) to linear O ( n ) and near-e xponential gro wth as stricter covert constraints force increases in both the hop number and processing gain. B. Impact of Link Covertness Requir ement on Route Latency Fig. 4 illustrates, for our netw ork topology and require- ments, the following results: for D E P req d < 0 . 1 , latenc y remains nearly constant; for 0 . 1 ≤ DE P < 0 . 97 , latency increases approximately O ( n ) ; and for D E P ≥ 0 . 97 , it exhibits exponential gro wth. The increase of route latency is triggered by two factors: increasing the required number of hops N ψ and increasing the optimal processing gain η opt v of hops close to W illie. The intuiti ve explanations of this behavior are as follows. A lo w cov ertness requirement allows higher transmission po wer at each node, thereby enabling near-direct communication between Alice and Bob with fewer hops (See Fig. 4b). At low covertness requirement, the optimal process- ing gain remains constant η opt v ≈ 1 , where hop v is closer to Alice (See Fig. 4c). Since D v ∝ 1 η v , latency also remains constant. The increase in the link covertness requirement has two significant effects. The optimized route requires more hops (with a closer proximity to Willie) and the required/optimum per hop processing gain η opt v increases. F or a moderate cov ert requirement, the latency exhibits approximately linear growth as the optimal transmission parameter η opt v increases (see Fig. 4c). Consequently , once a certain threshold DE P req d is crossed, the minimum achiev able latency grows exponentially . C. DCS vs Ener gy Metric Here, we quantitativ ely compare the energy and cycle detectors in the context of the latency minimization problem (Fig. 5). The energy detector implementation follows our (a) DE P req d = 10 − 2 (b) DE P req d = 0 . 8 Fig. 5: End-to-end latency of cycle and energy detectors versus message length under relaxed and stringent cov ert requirements. For low DE P , the cycle detector imposes routes with higher latency than the energy detector and vice versa. prior work [9]. W e vary two ke y system parameters: the link cov ertness requirement DE P req d and the message length M . The results reveal tw o main observations: ( i ) For latency minimization, the system performance decreases with the message length M ; ( ii ) T o maximize the best route’ s latency , W illie would select the cycle detector when Bob’ s covertness requirement is lo w and the energy detector when it is high. The explanation closely follo ws that of our prior study [5]. Since DE P v ∝ 1 M (Sec. III-B), the transmit power P v needs to decrease to guarantee the required link covertness as M increases. For the lower link covertness requirement (Fig. 5a), the optimal route follo ws an approximately direct path from Alice to Bob . For M ≤ 100 M bs , optimal processing gain is constant and η opt v ≈ 1 and, thus, latency increase is O ( M ) . For M > 1000 M bs , the processing gain increases in a linear fashion with M , and, consequently , the latency increase is roughly O ( M 2 ) . On the other hand, for a higher cov ertness requirement, due to both an increase in the required number of hops (Fig. 4b) and an increase in the η opt v the optimal route e xperiences exponential growth vs M . Different behavior of the energy and the cycle detector as a function of these two parameters is due to the dif ference in order of their respective statistics: energy detection relies on second- order statistics, whereas DCS is a fourth-order statistic, Eq. (2), making it more noise-sensitive (also see Fig. 1 in [5]). Hence, tightening the covertness requirement D E P req d reduces the required transmit power and degrades both signal estimation and detection, disproportionately affecting the cycle detector . For our network topology and QoS requirements, we found that the transition at which the c ycle degrades relati v e to the energy detector occurs at approximately D E P req d ≈ 10 − 1 . R E F E R E N C E S [1] A. O. Hero, “Secure space-time communication, ” IEEE Tr ansactions on Information Theory , vol. 49, no. 12, pp. 3235–3249, 2003. [2] C. Koumpouzi, P . Spasojevi ´ c, and F . T . Dagefu, “Improved lpd char - acteristics for qs-ds-cdma employing randomization techniques, ” IEEE T r ansactions on Information F orensics and Security , vol. 16, pp. 4762– 4771, 2021. [3] C. K oumpouzi, F . T . Dagefu, J. Choi, J. Kong, and P . Spasojevi ´ c, “Exploiting polarization di versity to improve cyclostationary-based lpd properties of cdma, ” IEEE W ireless Communications Letter s , v ol. 12, no. 1, pp. 6–10, 2022. [4] J.-B. Fraisse, P . Chev alier , R. Gautier , F . Delaveau, and S. Trav erso, “Power and second order cyclic covertness of chip-wise direct sequence spread spectrum faster-than-nyquist signaling, ” in MILCOM 2023 - 2023 IEEE Military Communications Conference (MILCOM) , 2023, pp. 522– 527. [5] R. Aggarw al, F . Dagefu, J. Kong, J. Choi, B. Kim, and P . Spasoje vi ´ c, “On covertness of dsss against energy and cycle detectors under link qos requirements, ” in 2025 IEEE 100th V ehicular T echnology Confer ence (VTC2025-Spring) . Oslo, Norway: IEEE, 2025. [6] J. Shi, Z. Dai, Z. Li, Z. T ie, and R. Chen, “User scheduling design for covert communication in cooperative cognitiv e radio system, ” IEEE sensors journal , vol. 23, no. 5, pp. 5459–5469, 2023. [7] B. A. Bash, D. Goeckel, and D. T owsley , “Limits of reliable communica- tion with lo w probability of detection on awgn channels, ” IEEE journal on selected areas in communications , v ol. 31, no. 9, pp. 1921–1930, 2013. [8] S. Y an, X. Zhou, J. Hu, and S. V . Hanly , “Low probability of detection communication: Opportunities and challenges, ” IEEE W ir eless Commu- nications , vol. 26, no. 5, pp. 19–25, 2019. [9] J. K ong, F . T . Dagefu, J. Choi, P . Spasoje vic, and C. K oumpouzi, “Co vert communications in low-vhf/microwa ve heterogeneous netw orks, ” in 2022 IEEE W ir eless Communications and Networking Conference (WCNC) , 2022, pp. 1970–1975. [10] R. Aggarwal, J. S. Kong, T . J. Moore, J. Choi, P . Spasojevic, and F . T . Dagefu, “Cov ert communications with simultaneous multi-modal transmission, ” in Pr oceedings of the 17th ACM Conference on Security and Privacy in W ireless and Mobile Networks , ser. WiSec ’24. New Y ork, NY , USA: Association for Computing Machinery , 2024, pp. 1–7. [Online]. A vailable: https://doi.org/10.1145/3643833.3656117 [11] W . A. Gardner and C. M. Spooner, “Signal interception: performance advantages of cyclic-feature detectors, ” IEEE T ransactions on commu- nications , vol. 40, no. 1, pp. 149–159, 1992. [12] M. Xie, J. Liu, H. T akakura, Y . Xu, Z. Li, and N. Shiratori, “Incentiv e routing design for covert communication in multi-hop decentralized wireless networks, ” in GLOBECOM 2022-2022 IEEE Global Commu- nications Confer ence . IEEE, 2022, pp. 49–54. [13] A. Sheikholeslami, M. Ghaderi, D. T owsley , B. A. Bash, S. Guha, and D. Goeckel, “Multi-hop routing in covert wireless networks, ” IEEE T r ansactions on W ir eless Communications , vol. 17, no. 6, pp. 3656– 3669, 2018. [14] B. Kim, J. Kong, T . J. Moore, and F . T . Dagefu, “Reinforcement learning based covert routing with node failure resiliency for heterogeneous networks, ” in MILCOM 2024-2024 IEEE Military Communications Confer ence (MILCOM) . IEEE, 2024, pp. 709–714. [15] W . A. Gardner and E. A. Robinson, “Statistical spectral analysis—a nonprobabilistic theory , ” 1989. [16] W . A. Gardner and C. M. Spooner, “Cyclic spectral analysis for signal detection and modulation recognition, ” in MILCOM 88, 21st Century Military Communications-What’ s P ossible?’. Confer ence r ecord. Mili- tary Communications Conference . IEEE, 1988, pp. 419–424. [17] D. Medhi and K. Ramasamy , Network r outing: algorithms, pr otocols, and ar chitectur es . Mor gan kaufmann, 2017. [18] EMA G T echnologies, Inc., “Emagtech — state-of-the-art radio- frequency system solutions, ” https://emagtech.com/, 2025, accessed: 2025-10-01.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment