Secure High-Resolution ISAC via Multi-Layer Intelligent Metasurfaces: A Layered Optimization Framework
Integrated sensing and communication (ISAC) has emerged as a pivotal technology for next-generation wireless networks, enabling simultaneous data transmission and environmental sensing. However, existing ISAC systems face fundamental limitations in a…
Authors: ** - Amirhossein Taherpour – Department of Electrical Engineering, Columbia University, New York
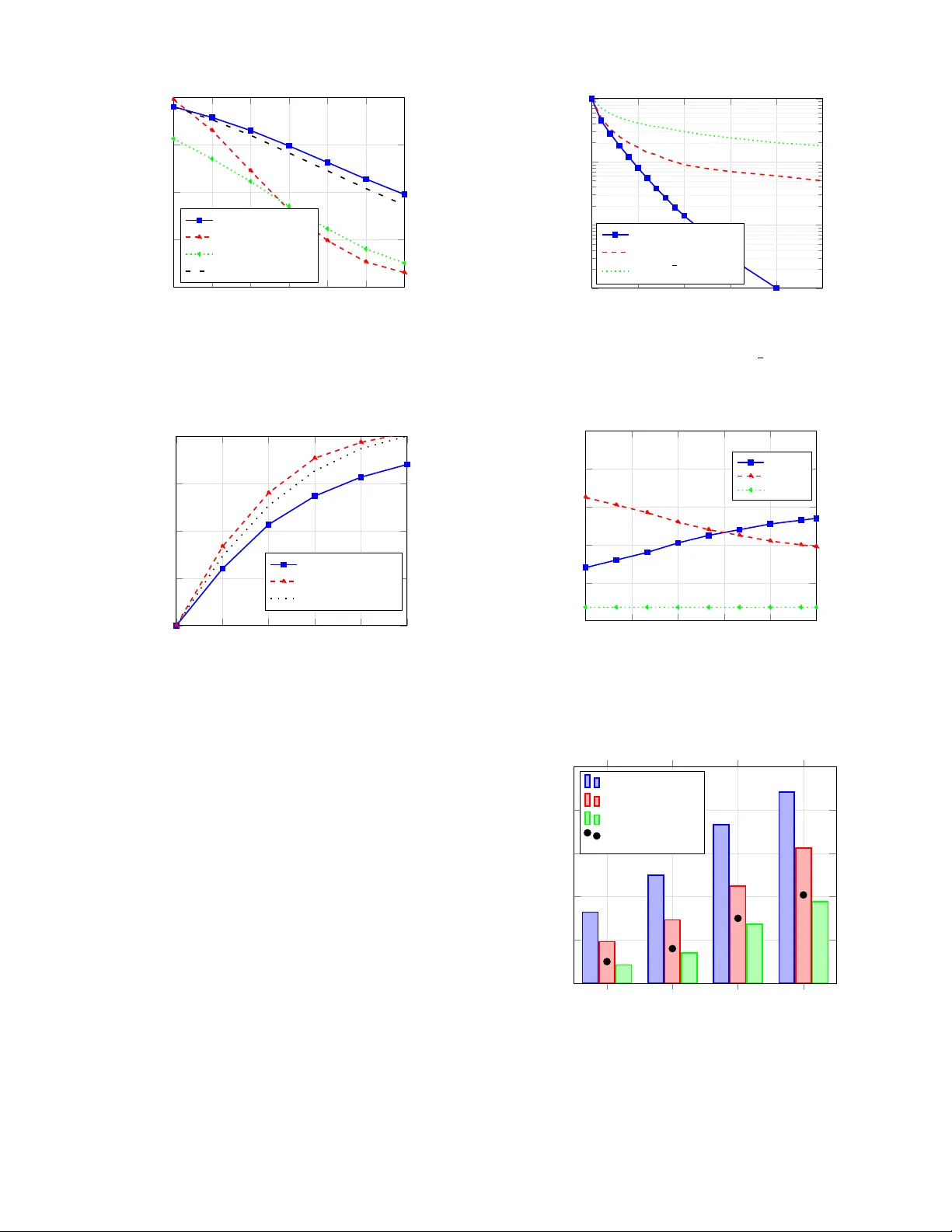
Secure High-Resolution ISA C via Multi-Layer Intelligent Metasurfaces: A Layered Optimization Frame work Amirhossein T aherpour , Abbas T aherpour , Senior Member , IEEE , and T amer Khattab , Senior Member , IEEE Abstract —Integrated sensing and communication (ISA C) has emerged as a pivotal technology for next-generation wireless networks, enabling simultaneous data transmission and envir on- mental sensing. Howe ver , existing ISA C systems face fundamental limitations in achieving high-resolution sensing while maintaining rob ust communication security and spectral efficiency . This paper introduces a transf ormative approach lev eraging stacked intelligent metasurfaces (SIM) to over come these challenges. W e propose a multi-functional SIM-assisted system that jointly optimizes communication secrecy and sensing accuracy through a novel layer ed optimization framework. Our solution employs a multi-objective optimization formulation that balances secr ecy rate maximization with sensing error minimization under practical hardwar e constraints. The proposed layer ed block coordinate descent algorithm efficiently coordinates sensing configuration, secure beamforming, communication metasurface optimization, and r esource allocation while ensuring r obustness to channel uncertainties. Extensive simulations demonstrate significant per - formance gains over con ventional approaches, achieving 32-61% impro vement in sensing accuracy and 15-35% enhancement in secrecy rates while maintaining computational efficiency . This work establishes a new paradigm f or secure and high-pr ecision multi-functional wireless systems. Index T erms —Integrated sensing and communication, stacked intelligent metasurfaces, physical layer security , multi-objective optimization, rob ust beamforming, Cram ´ er -Rao bound, artificial noise, resour ce allocation. I . I N T R O D U C T I O N The con vergence of communication and sensing functionalities represents one of the most significant paradigm shifts in be yond- 5G and 6G wireless netw orks [ 1 ], [ 2 ]. Integrated sensing and communication (ISA C) has garnered substantial research interest due to its potential to enable di verse applications including autonomous vehicles [ 3 ], smart cities [ 4 ], and industrial IoT [ 10 ]. The fundamental premise of ISAC lies in the joint utilization of spectral and hardware resources for dual purposes, thereby improving spectral efficienc y and reducing infrastructure costs [ 5 ], [ 6 ]. Recent advances in ISA C architectures have demonstrated promising performance, yet several critical challenges remain unaddressed. Conv entional ISA C systems [ 8 ], [ 26 ] often face inherent trade-of fs between sensing resolution and communica- tion throughput, particularly in multi-user scenarios. The work Amirhossein T aherpour is with the Department of Electrical Engineering, Columbia University , New Y ork, NY , USA (e-mail: at3532@columbia.edu) Abbas T aherpour is with the Department of Electrical Engineering, Imam Khomeini International Uni versity , Qazvin, Iran (e-mail: taherpour@ikiu.ac.ir). and T amer Khattab is with the Department of Electrical Engineering, Qatar Univ ersity , Doha, Qatar (e-mail: tkhattab@ieee.org). in [ 32 ] highlighted the limitations of time-sharing approaches, while [ 30 ] demonstrated the vulnerability of ISA C systems to security threats. Physical layer security has emerged as a crucial consideration, with [ 7 ], [ 12 ] showing that eav esdroppers can e xploit sensing signals to compromise communication confidentiality . The integration of reconfigurable intelligent surfaces (RIS) has opened ne w av enues for enhancing ISA C performance [ 11 ], [ 16 ]. RIS-assisted ISA C systems [ 14 ], [ 13 ] have demon- strated improved cov erage and beamforming gains. Howe ver , single-layer RIS architectures face fundamental limitations in wa ve manipulation capabilities [ 17 ]. Recent breakthroughs in stacked intelligent metasurfaces (SIM) [ 18 ], [ 19 ] have rev ealed unprecedented opportunities for adv anced wav e-based signal processing. Unlike con ventional RIS, multi-layer SIM can perform volumetric analog computing, enabling sophisticated spatial filtering and beamforming [ 20 ]. Security considerations in ISA C systems have gained in- creasing attention, with [ 21 ] proposing artificial-noise-based approaches and [ 22 ] de veloping optimization frame works for se- crecy rate maximization. Howe ver , these methods often neglect the interplay between sensing accuracy and communication security . The work in [ 23 ] identified fundamental performance trade-offs, while [ 34 ] proposed resource allocation strategies for balancing these competing objectiv es. Channel uncertainty poses another significant challenge for practical ISAC deployment. Robust optimization techniques hav e been explored in [ 26 ] and [ 25 ], but existing approaches typically assume simplified uncertainty models. The recent work in [ 30 ] introduced probabilistic constraints for outage per - formance, while [ 28 ] addressed the impact of finite-resolution phase shifters on system performance. Multi-functional metasurface architectures represent a promising direction for overcoming current limitations. The pioneering work in [ 29 ] demonstrated dynamic beamforming capabilities, and [ 25 ] achieved simultaneous multi-target sens- ing and channel estimation in RIS-assisted systems. Howe ver , these approaches lack comprehensiv e optimization framew orks that jointly address communication security , sensing accuracy , and resource efficienc y . The survey in [ 13 ] identified the need for inte grated optimization methodologies as a critical research gap. Recent developments in optimization theory have provided new tools for addressing ISAC challenges. Block coordinate descent and distributed methods [ 35 ] hav e shown promise for complex large-scale problems, while multi-objectiv e and 2 successiv e conv ex approximation techniques [ 34 ], [ 31 ], [ 33 ] enable efficient handling of intricate constraints. Despite these advances, se veral fundamental questions remain unanswered. How can we achiev e simultaneous high-precision sensing and secure communication in practical scenarios with hardware constraints? What are the fundamental performance limits of SIM-assisted ISA C systems? How can we ef ficiently optimize multi-layer metasurface configurations while ensuring robustness against channel uncertainties? This paper addresses these critical questions through the following contrib utions: • W e introduce a nov el multi-functional SIM-assisted ISAC architecture that enables joint communication and sensing with enhanced security and accuracy . • W e develop a comprehensi ve multi-objecti ve optimization framew ork that simultaneously maximizes secrecy rates and minimizes sensing errors under practical constraints. • W e propose an efficient layered block coordinate descent algorithm that coordinates sensing configuration, secure beamforming, communication metasurface optimization, and resource allocation. • W e establish fundamental performance bounds and pro- vide rigorous conv ergence guarantees for the proposed optimization framework. • W e demonstrate through extensi ve simulations that our approach achieves significant performance improv ements ov er state-of-the-art methods while maintaining computa- tional efficiency . The remainder of this paper is organized as follows. Sec- tion II presents the system model and problem formulation. Section III details the proposed optimization frame work. Section IV provides theoretical analysis. Section V presents simulation results, and Section VI concludes the paper . I I . S Y S T E M M O D E L A N D P R O B L E M F O R M U L A T I O N W e consider a multi-functional downlink system in beyond-5G networks that jointly performs communication and sensing tasks. The system comprises a base station (BS) equipped with M transmit antennas and R RF radio frequency (RF) chains ( R RF ≤ M ), a SIM with L programmable layers where each layer l contains N l metamaterial elements, and K single-antenna legitimate users in the presence of a set E of potential eavesdroppers. The total number of SIM elements is N tot = P L l =1 N l . The SIM is positioned between the BS and users as a transmissi ve surface and is assumed to be fully controlled by the BS. The key advantage of the multi-layer SIM architecture ov er con ventional single-layer RIS lies in its wave-based beam- forming capability . While a single-layer RIS can only apply phase shifts, the multi-layer structure enables volumetric analog processing that can implement sophisticated spatial filtering and focusing, effecti vely performing passive beamforming with higher gain and precision. A. Pr otocol and Resource Allocation The system employs a time-division duplex protocol with three operational phases: Channel Estimation (CE), Sensing (Phase I), and Communication (Phase II), with respective time fractions τ ce , τ sense , and τ comm . A switching period t switch is required to reconfigure the SIM between phases, implying τ ce + τ sense + τ comm +2 t switch /T slot ≤ 1 , where T slot is the total slot duration. For practical SIMs, t switch is typically in the sub-ms range, but its impact becomes non-negligible at mmW ave frequencies. The total energy constraint per time slot is T slot τ sense P sense + τ comm K X k =1 ∥ w k ∥ 2 + T r( R AN ) ≤ E max , (1) where P sense is the sensing power (an optimization v ariable), and the communication power is P K k =1 ∥ w k ∥ 2 + T r( R AN ) . Additionally , we impose instantaneous power constraints P sense ≤ P max BS and P K k =1 ∥ w k ∥ 2 + T r( R AN ) ≤ P max BS to respect the BS power amplifier limitations. The SIM configuration is reconfigured between phases, with Φ ce l , Φ sense l , Φ comm l ∈ C N l × N l denoting the diagonal phase- shift matrices for layer l during channel estimation, sensing, and communication phases, respectively . The BS employs hybrid beamforming with W = W RF W BB , where W RF ∈ C M × R RF is the analog beamforming matrix and W BB ∈ C R RF × K is the digital baseband precoder . B. Stack ed Intelligent Metasurface Model The multi-layer SIM architecture enables wa ve-domain com- puting through volumetric analog processing. The composite electromagnetic transformation through all L SIM layers is defined as: G SIM ( { Φ l } ) = Φ L H ( L ) Φ L − 1 H ( L − 1) · · · Φ 1 H (1) ∈ C N L × M , (2) where H ( l ) ∈ C N l × N l − 1 (with N 0 = M ) represents the ef fectiv e coupling matrix between layers l − 1 and l , capturing both the free-space propagation and mutual coupling between adjacent layers. The key advantage of the multi-layer structure is its ability to implement sophisticated beamforming patterns. For a giv en desired beamforming matrix F desired ∈ C N L × M , the SIM can approximate: G SIM ( { Φ l } ) ≈ F desired , (3) with the multi-layer structure providing higher beamforming gain and spatial resolution compared to single-layer RIS due to its increased degrees of freedom and wav e processing capability . T o model practical hardware, each metasurface element has a programmable phase shift with finite resolution: [ Φ l ] n,n = e j θ ( n ) l , θ ( n ) l ∈ Q l , (4) where Q l = { 2 π q / 2 b l | q = 0 , . . . , 2 b l − 1 } is the discrete phase set with b l -bit resolution. Practical hardware limitations, such as insertion loss from the metasurface elements, are assumed to be incorporated into the effecti ve coupling matrices H ( l ) . C. Channel Models and Channel State Information (CSI) Acquisition For clarity we summarize the main channel notations used throughout this subsection. H (1) denotes the BS-to-SIM near- field channel, H ( l ) the inter-layer SIM coupling matrix for 3 l ≥ 2 , h SIM → k the SIM-to-user k far -field channel, h SIM → e the SIM-to-eavesdropper e far -field channel, and h eff ,k the effecti ve end-to-end channel to user k . The BS-to-SIM link is modeled with near-field (spherical) wa vefronts and, because of the fixed geometry of the deploy- ment, is assumed known perfectly: H (1) = A SIM → BS Γ BS − SIM A T BS → SIM ∈ C N 1 × M , (5) where the near-field steering vectors are written elementwise as [ a BS ( r n )] m = exp − j 2 π λ ∥ r n − r BS ,m ∥ and the propagation matrix captures spherical-wa ve propagation [ Γ BS − SIM ] n,m = λ 4 π r n,m exp − j 2 π λ r n,m , (6) with r n,m = ∥ r SIM ,n − r BS ,m ∥ . During the channel estimation phase of duration τ ce the BS transmits orthogonal pilots while the SIM cycles through a predetermined set of Q configurations { Φ ce ,q l } Q q =1 . The users collect the resulting measurements and estimate the effecti ve end-to-end channels h eff ,k . Because the training budget is limited ( Q < N tot ), channel estimates are imperfect and are modeled with bounded errors: ˆ h eff ,k = h eff ,k + ∆ h k , ∥ ∆ h k ∥ ≤ ϵ max k , (7) where the uncertainty sets { ∆ h k } are used for rob ust precoder and SIM configuration design in the communication phase. The SIM-to-user and SIM-to-eav esdropper links are treated under far-field propagation with path loss and imperfect CSI: h H SIM → k = r 1 ρ k a H SIM ( θ k , r k ) , h H SIM → e = r 1 ρ e a H SIM ( θ e , r e ) , (8) where ρ k = ( d k /d 0 ) n and ρ e = ( d e /d 0 ) n denote the path losses (reference distance d 0 and path-loss exponent n ), and a SIM ( · ) are the corresponding array steering vectors. For inter-layer coupling ( l ≥ 2 ) we adopt a dominant line- of-sight (LoS) model to retain optimization tractability: H ( l ) = H ( l ) LoS , l ≥ 2 . (9) When ev aluating performance via simulation we relax this assumption and use a Rician model to capture scattered components: H ( l ) = p κ ( l ) H ( l ) LoS + p 1 − κ ( l ) H ( l ) NLoS , (10) where κ ( l ) is the Rician K -factor and H ( l ) NLoS contains the non-line-of-sight (NLoS) scattering contributions; this hybrid approach preserves analytical tractability while testing robust- ness to practical channel perturbations. Eav esdropper uncertainty is handled probabilistically: eav es- droppers are assumed to hav e uncertain locations leading to random channel errors, and secrecy is enforced through an outage constraint of the form Pr R sec k < R min k ≤ ϵ out , ∀ k, (11) where ϵ out is the maximum allowable secrecy-outage probabil- ity and uncertainties across dif ferent eavesdroppers are taken to be independent. T ogether, these modeling choices (near- field deterministic BS–SIM link, bounded-user CSI errors, Rician inter-layer channels for simulation, and probabilistic eav esdropper errors) provide a balance between realistic performance assessment and optimization tractability . D. Sensing Phase F ormulation During Phase I (sensing), the SIM processes echoes from T point targets to estimate their positions and velocities. The receiv ed sensing signal over time window t ∈ [0 , T sense ] is: Y sense = T X i =1 β i a SIM ( θ i , r i ) a H BS ( θ i , r i ) X sense e j 2 π f d,i t/T sense + N sense , (12) where N sense ∼ C N ( 0 , σ 2 n I ) represents thermal noise, f d,i is the Doppler frequency of target i , and we assume orthogonal probing wav eforms with X sense X H sense = P sense I . Here, the sensing duration is T sense = τ sense T slot , where τ sense is the sensing time fraction defined in Section II-A . The complex reflection coefficient for target i is: β i = q σ RCS ,i /ρ i · e j ϕ i , (13) where σ RCS ,i is the radar cross-section (RCS) and ρ i is the path loss. The SIM estimates target parameters ξ i = [ θ i , r i , v i , σ RCS ,i ] T using maximum likelihood estimation, where v i is the radial velocity . The Fisher Information Matrix (FIM) for parameter estimation is: J ( ξ i ) = 2 | β i | 2 σ 2 n ℜ ( ∂ µ ( ξ i ) ∂ ξ i H ∂ µ ( ξ i ) ∂ ξ i ) , (14) where µ ( ξ i ) = β i a SIM ( θ i , r i ) a H BS ( θ i , r i ) X sense e j 2 π f d,i t/T sense . W e compute the full FIM but note that, in our operating regime, cross-coupling among θ i , r i , v i is small; this motiv ates the Schur-complement-based lo wer bound used for optimization. For optimization tractability , we employ a lo wer-bound approximation of the FIM using the Schur complement. The total normalized Cram ´ er-Rao Bound (CRB) is: CRB total = T X i =1 T r J − 1 LB ( ξ i ) , (15) where J LB ( ξ i ) is the lower -bound FIM obtained via Schur complement. E. Communication Phase F ormulation The transmitted signal during Phase II (communication) incor- porates artificial noise (AN) for security: x = W s + z AN , (16) where the data vector is s ∼ C N ( 0 , I K ) and z AN ∼ C N ( 0 , R AN ) is the AN vector . The effecti ve end-to-end communication channels are: h H eff ,k = h H SIM → k G SIM ( { Φ comm l } ) , (17) h H eff ,e = h H SIM → e G SIM ( { Φ comm l } ) . (18) The received signal at user k is: y k = h H eff ,k x + n k , (19) where n k ∼ C N (0 , σ 2 k ) . The signal-to-interference-plus-noise ratio (SINR) at user k is: SINR k = | h H eff ,k w k | 2 P j = k | h H eff ,k w j | 2 + h H eff ,k R AN h eff ,k + σ 2 k . (20) 4 The SINR at eavesdropper e for user k ’ s message is: SINR ( k ) e = | h H eff ,e w k | 2 P j = k | h H eff ,e w j | 2 + h H eff ,e R AN h eff ,e + σ 2 e . (21) The worst-case achiev able secrecy rate for user k under probabilistic outage constraint is giv en by: R sec k = log 2 (1 + SINR k ) − max e ∈E log 2 1 + SINR ( k ) e + , (22) with the outage constraint P ( R sec k < R min k ) ≤ ϵ out . Using the Bernstein-type inequality , this probabilistic constraint can be transformed into a tractable deterministic form. F . Multi-Objective Optimization Problem The goal is to jointly optimize SIM-assisted volumetric beam- forming to enhance sensing accuracy while ensuring secure communication under limited energy and time resources. W e formulate a multi-objecti ve optimization problem that captures the fundamental trade-off between communication and sensing performance. The weighted sum approach provides the Pareto- optimal frontier . T o ensure scale compatibility between the secrec y rate (bits/s/Hz) and CRB (variance), we normalize both quantities using benchmark values: max W , R AN , { Φ comm l } , { Φ sense l } , { Φ ce l } , τ sense , τ ce ,τ comm ,P sense ,P comm (1 − α ) P K k =1 R sec k R max − α · CRB total CRB min s.t. τ ce + τ sense + τ comm + 2 t switch /T slot ≤ 1 , (23a) T slot ( τ sense P sense + τ comm P comm ) ≤ E max , (23b) P comm ≤ P max BS , (23c) P comm = K X k =1 ∥ w k ∥ 2 + T r( R AN ) , (23d) P sense ≤ P max BS , (23e) Pr R sec k < R min k ≤ ϵ out , ∀ k , (23f) | [ Φ p l ] n,n | = 1 , θ ( n ) l ∈ Q l , ∀ l , n, p ∈ { comm , sense , ce } , (23g) ∥ Φ comm l − Φ sense l ∥ 2 F ≤ δ Φ , ∀ l , (23h) τ sense , τ ce , τ comm ∈ [ τ min , τ max ] , (23i) SINR k ≥ γ min k , ∀ k . (23j) The trade-off parameter α ∈ [0 , 1] controls the communication-sensing balance: α = 0 prioritizes sum secrec y rate, α = 1 prioritizes sensing accuracy , and intermediate values pro vide balanced operation. Here, R max and CRB min are benchmark values obtained from ideal communication-only and sensing-only cases, respectively . The SIM reconfiguration constraint ∥ Φ comm l − Φ sense l ∥ 2 F ≤ δ Φ maintains hardware reconfiguration feasibility while ac- counting for practical tuning limitations between operational phases. The optimization variables include the continuous variables W , R AN , τ sense , τ ce , τ comm , P sense , P comm and the discrete variables { Φ comm l } , { Φ sense l } , { Φ ce l } . The problem exhibits multiple non-conv exities due to the coupled variables, frac- tional SINR expressions, discrete phase constraints, and the complex multi-objectiv e function. T o solve ( 23 ) efficiently , we propose a Block Coordinate Descent (BCD) framew ork that iterativ ely optimizes the beamformers and the SIM configurations. Subproblems are handled via successive con vex approximation (SCA) and semidefinite relaxation (SDR), with probabilistic secrecy constraints transformed using Bernstein- type inequalities. The discrete phase shifts are first optimized in the continuous domain and then projected onto the discrete set Q l via a deterministic rounding procedure followed by a local search. The resulting BCD-based algorithm scales as O ( LN 3 tot + K 3 ) per iteration, making it computationally feasible for practical system dimensions. I I I . P R O P O S E D S O L U T I O N F R A M E W O R K T o address the challenging multi-objectiv e optimization prob- lem ( 23 ) formulated in Section II , we propose an enhanced Layer ed BCD (L-BCD) framework. This algorithm compre- hensiv ely handles the joint communication-sensing trade-offs, multi-layer SIM configuration, probabilistic security constraints, hybrid beamforming, and integrated resource allocation by decomposing the problem into fiv e coordinated blocks. A. Overall Ar chitectur e and Solution Strate gy W e scalarize the multi-objecti ve problem in ( 23 ) with a weighting parameter α ∈ [0 , 1] . The scalarized objecti ve is max U ( α ) = (1 − α ) P K k =1 R sec k R max − α CRB total CRB min , (24) where R max and CRB min are normalization benchmarks and α controls the communication–sensing trade-off. An enhanced layered block-coordinate descent (L-BCD) frame work decomposes the design into fiv e coordinated blocks that are optimized in an alternating fashion. Block A (Sensing Configuration): optimizes the sensing SIM configurations { Φ sense l } and the sensing power P sense to reduce the aggregate CRB while meeting resource-efficiency targets. Block B (Secure Beamforming): designs the RF and baseband precoders W RF , W BB together with the artificial-noise cov ariance R AN to maximize secrecy rates subject to the probabilistic outage constraints. Block C (Communication SIM): configures the communication SIM patterns { Φ comm l } to improve secrecy performance while satisfying energy and reconfiguration con- straints. Block D (Resource Allocation): jointly tunes the time allocations τ sense , τ ce , τ comm and power budgets P sense , P comm (with P comm = P K k =1 ∥ w k ∥ 2 + T r( R AN ) ) under the total energy and time constraints. Block E (Channel Estimation): optimizes the channel-estimation configurations { Φ ce l } to min- imize estimation error within the av ailable training resources. The optimization variables separate naturally into continuous variables (the beamforming matrices W , the artificial-noise cov ariance R AN , the time allocations τ sense , τ ce , τ comm , and the power budgets P sense , P comm ) and discrete variables (the quantized SIM phase-shift configurations { Φ comm l } , { Φ sense l } , { Φ ce l } with θ ( n ) l ∈ Q l ). Practical solvers combine continuous optimization tools (e.g., con ve x solvers or successi ve con vex approximation) with low-comple xity discrete updates (e.g., pro- 5 jected local search, quantized relaxations, or greedy heuristics) tailored to hardware constraints. Coupling between blocks is resolved via alternating optimiza- tion: each Block A–E update is performed while holding the other blocks fixed, and the algorithm cycles through Blocks A, B, C, D, and E until a stationarity criterion is satisfied. Under standard regularity and boundedness assumptions for each block update (closedness of feasible sets and nondecreasing objectiv e), this alternating procedure con verges to a Pareto- stationary point of the scalarized objective. Implementation complexity per L-BCD iteration is domi- nated by SIM-layer updates and beamforming matrix opera- tions, yielding an overall per-iteration cost on the order of O ( LN 3 tot + K 3 ) , where L is the number of SIM layers, N tot the total number of SIM elements, and K the number of users. In practice, warm-starting, problem-specific approximations, and occasional coarse-to-fine SIM searches reduce runtime and enable near-real-time reconfiguration when required. B. T ractable Reformulations of Ke y Constraints Complete outage constraint ref ormulation. The outage constraint P ( R sec k < R min k ) ≤ ϵ out is conservati vely enforced using a Bernstein-type inequality with a safety margin. This yields the deterministic surrogate E [ R sec k ] − δ q V ar[ R sec k ] ≥ R min k + ∆ k , (25) where δ = Q − 1 (1 − ϵ out ) is the safety parameter, Q ( · ) is the standard normal complementary cumulativ e distribution func- tion (CDF), and ∆ k captures approximation errors introduced by the inequality . The expectation and v ariance are taken over the eavesdropper channel uncertainties and can be expressed as E [ R sec k ] = E ∆ h e log 2 (1 + SINR k ) − E ∆ h e max e log 2 (1 + SINR ( k ) e ) , (26) V ar[ R sec k ] = V ar ∆ h e log 2 (1 + SINR k ) + V ar ∆ h e max e log 2 (1 + SINR ( k ) e ) . (27) Practical implementation replaces the inner “max over eav es- droppers” term with either a tractable upper bound or with a sample-based approximation to preserve con vexity in the continuous decision variables. Extended CRB constraint conv exification. For the extended parameter vector ξ i = [ θ i , r i , v i , σ RCS ,i ] T we employ a Schur- complement based lower -bound Fisher information matrix (FIM) J LB ( ξ i ) as introduced in Section II : J LB ( ξ i ) = J 11 − J 12 J − 1 22 J 21 ⪯ J ( ξ i ) . (28) The aggregate CRB constraint CRB total ≤ Γ max is then approximated by the conv ex surrogate T X i =1 T r J − 1 LB ( ξ i ) + ϵ I ≤ Γ max , (29) where ϵ > 0 is a small regularization parameter used for numerical stability when in verting the lower-bound FIM blocks. W a ve-based SIM beamforming. The multi-layer SIM is exploited to approximate a desired fully-digital beamformer F desired by minimizing a Frobenius-norm error while penaliz- ing excessiv e reconfiguration relati ve to sensing settings. The design problem for the communication SIM patterns is min { Φ comm l } G SIM ( { Φ comm l } ) − F desired 2 F + λ Φ L X l =1 ∥ Φ comm l − Φ sense l ∥ 2 F − δ Φ + , (30) where λ Φ controls the trade-off between matching the desired beamformer and limiting SIM reconfiguration, and [ · ] + denotes the positive-part operator . In practice, G SIM ( · ) is linearized around the current SIM configuration to obtain con ve x surro- gates amenable to SCA steps. Discrete phase optimization with majorization-minimization. The quantized phase constraint θ ( n ) l ∈ Q l is treated with a three-stage procedure. The stages are: (1) continuous relaxation, (2) quantization via a projection (majorization-minimization style step), and (3) local-search refinement. Concretely , 1) Continuous r elaxation: Solve the design problem with relaxed phases θ ( n ) l ∈ [0 , 2 π ) to obtain continuous-phase solutions θ ( n ) cont . 2) Quantization (Majorization-Minimization (MM) pr ojec- tion): Project the continuous solutions onto the discrete set by θ ( n ) l = arg min θ ∈Q l θ − θ ( n ) cont 2 . (31) 3) Local searc h r efinement: Perform greedy refinement on the most sensitiv e elements by ev aluating nearby discrete phase candidates: θ ( n ) l ← arg min θ ∈N ( θ ( n ) l ) ∩Q l f ( Θ ) , (32) where N ( θ ) denotes a small neighborhood around θ in the discrete grid and f ( Θ ) is the current objectiv e. This procedure is compatible with warm-starting from pre- vious iterations and generally yields high-quality quantized configurations at moderate complexity . Fractional SINR linearization. Nonconv ex SINR expressions are handled by successi ve con vex approximation. For user k the denominator D k = X j = k | h H eff ,k w j | 2 + h H eff ,k R AN h eff ,k + σ 2 k (33) is linearized around the previous iterate value D ( t ) k . The resulting first-order surrogate for the achiev able rate is log 2 (1+SINR k ) ≈ log 2 1+ | h H eff ,k w k | 2 D ( t ) k − D k − D ( t ) k D ( t ) k + | h H eff ,k w k | 2 . (34) Applying this SCA step within each block update yields con vex subproblems that are solved iterativ ely and that guarantee monotonic improv ement of the surrogate objectiv e under standard conditions. 6 C. Block A: Sensing Configuration Optimization Gi ven fixed beamformers and communication SIM parameters, the sensing sub-problem is: min { Φ sense l } ,P sense α · CRB total CRB min − (1 − α ) τ comm T slot (35a) s.t. CRB total ≤ Γ max , (35b) T slot ( τ sense P sense + τ comm P comm ) ≤ E max , (35c) τ ce + τ sense + τ comm + 2 t switch /T slot ≤ 1 , (35d) | [ Φ sense l ] n,n | = 1 , ∀ l, n, (35e) P sense ≤ P max BS . (35f) In this subproblem, we use τ comm as a proxy for the commu- nication objective. Since beamforming and other parameters are fixed, increasing the communication time fraction τ comm monotonically increases the achiev able secrecy rate. This problem is solved using a projected gradient method on the complex circle manifold, where the extended CRB constraint is incorporated using the Schur complement approximation and the power constraint is handled via dual decomposition. The SIM phases are optimized to steer energy toward target angles during the sensing phase. D. Block B: Secure Beamforming Optimization Giv en fixed SIM parameters { Φ comm l } from Block C, the beamforming sub-problem becomes: max W RF , W BB , R AN (1 − α ) P K k =1 E [ R sec k ] − δ p V ar[ R sec k ] R max (36a) s.t. T slot ( τ sense P sense + τ comm P comm ) ≤ E max , (36b) P comm = K X k =1 ∥ w k ∥ 2 + T r( R AN ) ≤ P max BS , (36c) SINR k ≥ γ min k , ∀ k , (36d) W = W RF W BB , (36e) | [ W RF ] i,j | = 1 , ∀ i, j, (36f) Bernstein-based outage constraints , ∀ k . (36g) The hybrid beamformer W = W RF W BB is optimized via alternating minimization: W ∗ RF = arg min W RF ∈A ∥ W opt − W RF W BB ∥ 2 F (37) W ∗ BB = ( W H RF W RF ) − 1 W H RF W opt (38) where A = { W RF : | [ W RF ] i,j | = 1 } is the analog beamforming constraint set, and W opt is the optimal fully- digital solution from SDR. T o handle the non-con ve x SINR and secrecy rate terms, we employ SDR. Define V k = w k w H k and ignore the rank- 1 constraint. The problem becomes a conv ex Semidefinite Program (SDP) which can be solved efficiently . Gaussian randomization is used to generate feasible rank-1 solutions when needed. E. Block C: Communication SIM Configuration Optimization Giv en fixed beamformers W RF , W BB , and R AN , the SIM configuration sub-problem is: max { Φ comm l } (1 − α ) P K k =1 E [ R sec k ] − δ p V ar[ R sec k ] R max − λ Φ L X l =1 ∥ Φ comm l − Φ sense l ∥ 2 F − δ Φ + (39a) s.t. | [ Φ comm l ] n,n | = 1 , ∀ l, n. (39b) For the multi-layer SIM, we employ layer-wise optimization with reconfiguration awareness: Φ ∗ l = arg min Φ l f ( Φ 1 , . . . , Φ L ) + λ Φ ∥ Φ l − Φ sense l ∥ 2 F − δ Φ + for l = 1 , . . . , L, (40) with other layers fixed, exploiting the cascaded structure for efficient computation. The unit-modulus constraints form a complex circle manifold. W e solve this problem using the Riemannian conjugate gradient (RCG) method with the penalty parameter λ Φ adaptiv ely updated to ensure constraint satisfaction. The SIM phases are optimized to steer energy tow ard legitimate users while creating nulls toward potential eav esdropper directions. F . Block D: Enhanced Resource Allocation max τ sense ,τ ce ,τ comm , P sense ,P comm U ( α ) = (1 − α ) P K k =1 R sec k R max − α · CRB total CRB min (41a) s.t. τ ce + τ sense + τ comm + 2 t switch T slot ≤ 1 , (41b) T slot τ sense P sense + τ comm P comm ≤ E max , (41c) P comm ≤ P max BS , P sense ≤ P max BS , (41d) τ sense , τ ce , τ comm ∈ [ τ min , τ max ] . (41e) This conv ex resource allocation problem is solved via Lagrange dual decomposition with augmented Lagrangian method to handle the time and energy coupling constraints efficiently . The solution balances time allocation between sensing and communication phases to maximize the overall system utility . G. Block E: Channel Estimation Configuration Gi ven the current resource allocation τ ce , this block optimizes the SIM configuration to ensure the channel estimation accuracy is met. min { Φ ce l } max k ϵ max k ( { Φ ce l } , τ ce ) (42a) s.t. max k ϵ max k ≤ ϵ max CSI , (42b) | [ Φ ce l ] n,n | = 1 , ∀ l, n, (42c) τ ce ∈ [ τ min , τ max ] . (42d) This block optimizes the SIM configuration during channel es- timation to minimize training overhead while ensuring channel 7 estimation accuracy . The CSI error bound ϵ max k is related to the SIM configuration through the training sequence design. The SIM phases are configured to create omnidirectional patterns for comprehensive channel sounding. H. Inte grated Enhanced L-BCD Algorithm I. Con vergence and Complexity Analysis Con vergence. The proposed L-BCD algorithm con ver ges to a stationary point under standard regularity conditions. Each subproblem corresponding to Block A, Block B, Block C, Block D, and Block E is solved while keeping the remaining v ariables fixed, which yields a non-decreasing sequence of objectiv e values for the scalarized utility U ( α ) . The combination of alternating updates, con vex surrogates obtained via SCA and SDR when needed, and manifold-based updates for constrained variables guarantees monotonic improv ement of the surrogate objectiv e and conv ergence to at least a local optimum or a Pareto-stationary point of the scalarized problem. Complexity . The per-iteration computational complexity is dominated by SIM-layer updates and beamforming matrix operations and is on the order of O LN 3 tot + K 3 , where the first term O ( LN 3 tot ) captures the cost of multi- layer SIM optimization performed in Blocks A, C, and E, and the second term O ( K 3 ) captures the cost of the secure- beamforming SDP solved in Block B. The resource-allocation step in Block D has comparativ ely low cost due to its con vex structure and contributes negligible additional complexity . This computational profile is practical for typical configurations with N tot in the hundreds to low thousands and moderate K . Practical complexity reduction strategies such as warm- starting, low-rank approximations, and layer-wise parallel updates further reduce runtime in realistic deployments. J. Practical Implementation Considerations The enhanced L-BCD framework is designed for practical deployment and incorporates multiple implementation-oriented provisions. P arallelization is straightforward since the optimiza- tions for individual SIM layers within Block A, Block C, and Block E can be executed concurrently across av ailable compute units. W arm-starting from previous solutions is recommended to accelerate con ver gence under dynamic channels and to enable fast reconfiguration. An adaptive tolerance schedule, where conv ergence tolerances ϵ ob j and ϵ param are tightened gradually , yields a fa vorable trade-off between runtime and final accuracy . Hardware imperfections are explicitly accounted for by incorporating models of SIM insertion loss, phase quantization errors, and mutual coupling into the optimization constraints and objectiv e. Robustness to model mismatch is achie ved by designing under conservati ve approximations (e.g., LoS-based tractable models) and v alidating performance under Rician SIM channels in simulation. The block structure supports scalable extensions to richer channel models and additional hardware impairments. Finally , the optimized SIM phase profiles provide physical insight: during the communication phase the SIM phases steer energy to ward the users, while during the sensing phase they concentrate energy toward target angles, enabling an adaptiv e beamforming pattern that trades sensing accuracy for secrecy performance as required. I V . T H E O R E T I C A L A N A L Y S I S This section provides a comprehensive theoretical foundation for the enhanced L-BCD algorithm, establishing rigorous con vergence guarantees, performance bounds, and fundamental limits for our integrated communication–sensing system with multi-layer SIM architecture. A. Con vergence Analysis Theorem 1 (Global Conv ergence of Enhanced 5-Block L-BCD) . Let Θ ( t ) = { Φ sense , ( t ) l } , { Φ comm , ( t ) l } , { Φ ce , ( t ) l } , W ( t ) RF , W ( t ) BB , R ( t ) AN , τ ( t ) sense , τ ( t ) ce , τ ( t ) comm , P ( t ) sense , P ( t ) comm (43) be the sequence generated by Algorithm 1 with the augmented objective f aug ( Θ ) = (1 − α ) P K k =1 R sec k R max − α CRB total CRB min − λ Φ L X l =1 ∥ Φ comm l − Φ sense l ∥ 2 F − δ Φ + . (44) Suppose the following conditions hold: (C1) The feasible set X is compact with non-empty interior (due to power constraints P comm , P sense ≤ P max BS and unit-modulus SIM constraints). (C2) f aug is continuously differ entiable with block-wise L i - Lipschitz continuous gradients. (C3) Each block subpr oblem achieves an ϵ -sufficient incr ease, i.e., f aug ( Θ ( t +1) i , Θ ( t ) − i ) ≥ f aug ( Θ ( t ) i , Θ ( t ) − i ) + γ i ∥ Θ ( t +1) i − Θ ( t ) i ∥ 2 − ϵ ( t ) i (45) with P ∞ t =0 ϵ ( t ) i < ∞ . (C4) The penalty parameter is updated as λ ( t +1) Φ = min κ λ λ ( t ) Φ , λ max Φ with κ λ > 1 . (C5) All subpr oblems ar e solved to O (1 /t ) accuracy . Then the following statements hold: (R1) The sequence { f aug ( Θ ( t ) ) } con verges to a finite value f ∗ aug . (R2) lim t →∞ ∥ Θ ( t +1) − Θ ( t ) ∥ = 0 . (R3) Every limit point Θ ∗ of { Θ ( t ) } is P areto stationary . (R4) All penalty-induced constraints ar e satisfied in the limit: lim t →∞ L X l =1 ∥ Φ comm , ( t ) l − Φ sense , ( t ) l ∥ 2 F − δ Φ + = 0 . Pr oof. W e partition the variables into five coordinated blocks matching Algorithm 1 : 8 Algorithm 1: Enhanced Layered Block Coordinate Descent (L-BCD) Input: Channel statistics; SIM constraint δ Φ ; power budget P max BS ; energy budget E max ; trade-off parameter α ; outage requirement ϵ out . Output: Optimal configurations { Φ sense l } ∗ , { Φ comm l } ∗ , { Φ ce l } ∗ , W ∗ RF , W ∗ BB , R ∗ AN , τ ∗ sense , τ ∗ ce , τ ∗ comm , P ∗ sense . Initialization: { Φ comm , (0) l } ← SVD( H aggregate ) // Init. via singular value decomposition (SVD) { Φ sense , (0) l } ← MaxAngularCoverage() // Wide-area sensing { Φ ce , (0) l } ← OmnidirectionalPattern() // Uniform probing for channel estimation τ (0) sense ← ( τ min + τ max ) / 2 τ (0) ce ← 0 . 1 , τ (0) comm ← 0 . 5 P (0) sense ← P max BS / 2 , P (0) comm ← P max BS / 2 W (0) RF , W (0) BB ← MR T HybridDecomp( ˆ H ) // Init. via maximum ratio transmission (MRT) decomp R (0) AN ← InitArtificialNoise() t ← 0 , ϵ conv ← 10 − 4 λ (0) Φ ← 1 , f (0) aug ← −∞ repeat // Block E: Channel Estimation Configuration { Φ ce , ( t +1) l } ← Solve ( 42 ) , τ ( t ) ce // Block D: Joint Resource Allocation (time and power) ( τ ( t +1) sense , τ ( t +1) ce , τ ( t +1) comm ) , ( P ( t +1) sense , P ( t +1) comm ) ← DualDecomp osition ( 41 ) // Block A: Sensing Configuration { Φ sense , ( t +1) l } ← ManifoldOptim ( 35 ) , Sch urComplement // Block B: Secure Beamforming W ( t +1) opt ← SDP Solve ( 36 ) , BernsteinConstraints W ( t +1) RF , W ( t +1) BB ← HybridDecomp W ( t +1) opt R ( t +1) AN ← ArtificialNoiseDesign W ( t +1) opt // Block C: Communication SIM Configuration { Φ comm , ( t +1) l } ← Layerwise RCG ( 39 ) , λ ( t ) Φ // Penalty Parameter Update λ ( t +1) Φ ← min κ λ λ ( t ) Φ , λ max Φ // Multi-Metric Convergence Assessment U ( α ) ( t +1) ← (1 − α ) P K k =1 R sec , ( t +1) k R max − α CRB ( t +1) total CRB min f ( t +1) aug ← U ( α ) ( t +1) − λ ( t ) Φ P L l =1 h Φ comm , ( t +1) l − Φ sense , ( t +1) l 2 F − δ Φ i + ∆ f ← f ( t +1) aug − f ( t ) aug f ( t ) aug ϵ ( t +1) outage ← max k P ( R sec k < R min k ) − ϵ out ϵ ( t +1) CRB ← CRB ( t +1) total − Γ max ∆ Θ ← Θ ( t +1) − Θ ( t ) F t ← t + 1 until (i)–(iv) below ar e satisfied or t ≥ t max Stopping criteria (for the outer loop): (i) ∆ f ≤ ϵ ob j ; (ii) ϵ ( t ) outage ≤ ϵ outage ; (iii) ϵ ( t ) CRB ≤ ϵ CRB ; (i v) ∆ Θ ≤ ϵ param Discretization Phase: { Φ comm , ( t ) l } ← Pro jectT oDiscrete( Q l ) { Φ sense , ( t ) l } ← Pro jectT oDiscrete( Q l ) { Φ ce , ( t ) l } ← Pro jectT oDiscrete( Q l ) LocalSearchRefinement( critical elements ) retur n { Φ sense l } ∗ , { Φ comm l } ∗ , { Φ ce l } ∗ , W ∗ RF , W ∗ BB , R ∗ AN , τ ∗ sense , τ ∗ ce , τ ∗ comm , P ∗ sense Θ A = ( { Φ sense l } ) (Sensing SIM) Θ B = ( W RF , W BB , R AN ) (Beamforming) Θ C = ( { Φ comm l } ) (Comm SIM) Θ D = ( τ ce , τ comm , τ sense , P sense , P comm ) (Resources) Θ E = ( { Φ ce l } ) (Channel Est SIM) Part 1: Monotonicity and Boundedness For Block A at iteration t , by Lipschitz continuity: f aug ( Θ ( t +1) A , Θ ( t ) − A ) ≥ f aug ( Θ ( t ) A , Θ ( t ) − A ) + ⟨∇ A f aug ( Θ ( t ) ) , Θ ( t +1) A − Θ ( t ) A ⟩ − L A 2 ∥ Θ ( t +1) A − Θ ( t ) A ∥ 2 − ϵ ( t ) A By the sufficient increase condition: ⟨∇ A f aug ( Θ ( t ) ) , Θ ( t +1) A − Θ ( t ) A ⟩ ≥ γ A ∥ Θ ( t +1) A − Θ ( t ) A ∥ 2 Thus: f aug ( Θ ( t +1) A , Θ ( t ) − A ) ≥ f aug ( Θ ( t ) ) + γ A − L A 2 ∥ Θ ( t +1) A − Θ ( t ) A ∥ 2 − ϵ ( t ) A Applying sequentially to all blocks with γ = min i γ i − L i 2 > 0 : f aug ( Θ ( t +1) ) ≥ f aug ( Θ ( t ) ) + γ X i ∥ Θ ( t +1) i − Θ ( t ) i ∥ 2 − X i ϵ ( t ) i Since f aug is continuous on compact X and P ∞ t =0 P i ϵ ( t ) i < ∞ , { f aug ( Θ ( t ) ) } conv erges to some f ∗ aug . Part 2: V anishing Steps Summing the increase inequality from t = 0 to T − 1 : γ T − 1 X t =0 X i ∥ Θ ( t +1) i − Θ ( t ) i ∥ 2 ≤ f aug ( Θ ( T ) ) − f aug ( Θ (0) ) + T − 1 X t =0 X i ϵ ( t ) i T aking T → ∞ and using con ver gence of both terms: ∞ X t =0 X i ∥ Θ ( t +1) i − Θ ( t ) i ∥ 2 < ∞ Thus: lim t →∞ ∥ Θ ( t +1) i − Θ ( t ) i ∥ = 0 ∀ i Part 3: Constraint Satisfaction Consider the penalty term: P ( t ) = L X l =1 h ∥ Φ comm , ( t ) l − Φ sense , ( t ) l ∥ 2 F − δ Φ i + Since λ ( t ) Φ → λ max Φ > 0 and f aug con verges, we must hav e: lim t →∞ P ( t ) = 0 Otherwise, if lim sup t →∞ P ( t ) > 0 , then lim t →∞ f aug ( Θ ( t ) ) = −∞ (due to the negati ve sign in ( 44 )), contradicting boundedness. Part 4: Stationarity of Limit Points Let Θ ∗ be a limit point of { Θ ( t ) } . By the closedness of the solution mapping and vanishing steps: Θ ∗ i ∈ arg max Θ i ∈X i f aug ( Θ i , Θ ∗ − i ) ∀ i This implies the first-order necessary conditions for Pareto stationarity: there exists λ ≥ 0 with ∥ λ ∥ 1 = 1 such that ⟨ X i λ i ∇ f i ( Θ ∗ ) , Θ − Θ ∗ ⟩ ≥ 0 ∀ Θ ∈ X where f 1 = (1 − α ) P K k =1 R sec k R max and f 2 = − α · CRB total CRB min . ■ 9 Proposition 1 (Constraint Qualification) . F or any feasible Θ , the linear independence constraint qualification (LICQ) holds for: • Active power constraints P comm = P max BS or P sense = P max BS • T ime allocation constraints when τ ce + τ sense + τ comm = 1 − 2 t switch /T slot • Active SIM r econfiguration constraints ∥ Φ comm l − Φ sense l ∥ 2 F = δ Φ ensuring Karush-Kuhn-T ucker (KKT) conditions are necessary for local optimality . Pr oof. W e verify linear independence of the acti ve constraint gradients: Po wer constraints: The gradients are ∇ P comm = (0 , . . . , 1 , 0 , . . . ) and ∇ P sense = (0 , . . . , 0 , 1 , . . . ) , which are clearly linearly independent when both are activ e. Time constraints: The gradient is ∇ ( τ ce + τ sense + τ comm ) = (1 , 1 , 1 , 0 , . . . ) , which is non-zero and linearly independent from power constraint gradients. SIM reconfiguration: For activ e constraints ∥ Φ comm l − Φ sense l ∥ 2 F = δ Φ , the gradients are 2( Φ comm l − Φ sense l ) for the communication SIM variables and − 2( Φ comm l − Φ sense l ) for the sensing SIM variables. These are linearly independent from the other constraints since they inv olve different variable blocks. Since all activ e constraint gradients are linearly independent, LICQ holds, and KKT conditions are necessary for local optimality . ■ Corollary 1 (Con ver gence Rate for KL Frame work) . If f aug satisfies the Kurdyka- Ł ojasiewicz property with exponent θ ∈ [0 , 1) : • For θ = 0 (metric regularity): Linear con vergence ∥ Θ ( t ) − Θ ∗ ∥ ≤ C q t • For θ ∈ (0 , 1 2 ] : Sublinear conv ergence f ∗ aug − f ( t ) aug ≤ O (1 /t ) • For θ ∈ ( 1 2 , 1) : Slo wer sublinear con vergence f ∗ aug − f ( t ) aug ≤ O (1 /t 1 / (2 θ − 1) ) For general non-conv ex case: min 0 ≤ k ≤ t ∥ Θ ( k +1) − Θ ( k ) ∥ 2 ≤ f ∗ aug − f aug ( Θ (0) ) + P t k =0 P i ϵ ( k ) i γ t (46) Pr oof. KL property case: The KL property states that there exists ϕ ( s ) = cs 1 − θ such that: ϕ ′ ( f ∗ aug − f aug ( Θ )) ∥∇ f aug ( Θ ) ∥ ≥ 1 near critical points. Combining this with the ascent lemma giv es the stated rates: • For θ = 0 : ϕ ( s ) = cs , leading to linear con ver gence • For θ ∈ (0 , 1 2 ] : ϕ ( s ) = cs 1 − θ , giving O (1 /t ) • For θ ∈ ( 1 2 , 1) : ϕ ( s ) = cs 1 − θ , yielding O (1 /t 1 / (2 θ − 1) ) General non-con vex case: From Theorem 1 : γ t − 1 X k =0 ∥ Θ ( k +1) − Θ ( k ) ∥ 2 ≤ f aug ( Θ ( t ) ) − f aug ( Θ (0) ) + t − 1 X k =0 X i ϵ ( k ) i Thus: min 0 ≤ k ≤ t − 1 ∥ Θ ( k +1) − Θ ( k ) ∥ 2 ≤ f ∗ aug − f aug ( Θ (0) ) + P t − 1 k =0 P i ϵ ( k ) i γ t ■ Lemma 1 (Initialization Quality Impact) . If initial point Θ (0) satisfies f ∗ aug − f aug ( Θ (0) ) ≤ ∆ 0 , then con vergence to ϵ - stationarity requir es at most: T ≤ ∆ 0 γ ϵ 2 + O log(1 /ϵ ) min i γ i (47) iterations. W arm start fr om pr evious solutions r educes ∆ 0 significantly . Pr oof. From the conv ergence rate in Corollary 1 : min 0 ≤ k ≤ T − 1 ∥ Θ ( k +1) − Θ ( k ) ∥ 2 ≤ ∆ 0 + P T − 1 k =0 P i ϵ ( k ) i γ T For ϵ -stationarity , we need: ∆ 0 + P T − 1 k =0 P i ϵ ( k ) i γ T ≤ ϵ 2 Since P ∞ k =0 P i ϵ ( k ) i < ∞ , there exists C < ∞ such that: T ≤ ∆ 0 + C γ ϵ 2 The logarithmic term accounts for the initial rapid con ver- gence phase when far from optimum. W arm start reduces ∆ 0 , directly improving the iteration count. ■ B. Fundamental P erformance Limits Theorem 2 (T ighter Secrecy-Sensing Trade-of f) . The P ar eto fr ontier satisfies: P K k =1 R sec k C sum ! η trade + CRB min CRB total η trade ≤ 1 (48) wher e η trade ≥ 1 depends on channel corr elation between sensing and communication paths, and: C sum = log 2 det I + P max σ 2 H eff H H eff CRB min = min { Φ l } CRB total ( { Φ l } ) Pr oof. Upper bound on secrecy rates: K X k =1 R sec k = K X k =1 log 2 (1 + SINR k ) − max e ∈E log 2 (1 + SINR ( k ) e ) + ≤ K X k =1 log 2 (1 + SINR k ) ≤ log 2 K Y k =1 (1 + SINR k ) ≤ log 2 det I + P max σ 2 H eff H H eff = C sum where the last inequality follows from the MIMO capacity formula. 10 Lower bound on CRB: By definition, the total CRB is lower -bounded by the optimal sensing-only benchmark: CRB total = T X i =1 T r( J − 1 ( ξ i )) ≥ min { Φ l } T X i =1 T r( J − 1 ( ξ i )) ≜ CRB min T rade-off parameter η trade : The coupling emerges from the shared SIM resource { Φ l } . Let U comm and U sense be the optimal subspaces for communication and sensing, respecti vely . The correlation parameter is: η trade = 1 arccos 2 ( σ min ( U H comm U sense )) When these subspaces are orthogonal ( η trade → ∞ ), the trade-off becomes sev ere; when aligned ( η trade ≈ 1 ), joint optimization is feasible. The Pareto bound follows from the fundamental limits of multi-objecti ve optimization ov er shared resources. ■ Theorem 3 (Energy-T ime Resource Bound) . The system r esources satisfy: max E sense min T slot P max , E comm min T slot P max ≤ τ sense + τ comm ≤ 1 − τ min ce − 2 t switch T slot (49) and the mutual information is bounded by: I ( Y sense ; ξ )+ I ( y comm ; s ) ≤ log 2 det I + P total σ 2 G SIM G H SIM (50) Here, P max denotes the same maximum BS transmit power P max BS defined in Sec. II , and P total the total available po wer budget ov er both phases. Pr oof. Energy-Time Bound: From the energy constraints: T slot τ sense P sense ≥ E sense min , T slot τ comm P comm ≥ E comm min Since P sense , P comm ≤ P max : τ sense ≥ E sense min T slot P max , τ comm ≥ E comm min T slot P max Thus: τ sense + τ comm ≥ max E sense min T slot P max , E comm min T slot P max From the time constraint: τ ce + τ sense + τ comm + 2 t switch T slot ≤ 1 Since τ ce ≥ τ min ce : τ sense + τ comm ≤ 1 − τ min ce − 2 t switch T slot Mutual Information Bound: By the data processing inequality: I ( Y sense ; ξ ) + I ( y comm ; s ) ≤ I ( Y sense , y comm ; ξ , s ) ≤ I ( X ; Y sense , y comm ) The mutual information is bounded by the channel capacity: I ( X ; Y sense , y comm ) ≤ log 2 det I + P total σ 2 G SIM G H SIM where G SIM is the effecti ve channel through the multi-layer SIM. ■ Proposition 2 (Multi-layer vs Single-layer Gain) . F or L -layer SIM vs single-layer RIS with same total elements N tot : G SIM G RIS ≥ Q L l =1 σ min ( H ( l ) ) ∥ H RIS ∥ F ! 2 · N L − 1 tot L L (51) showing exponential gain with layers when channel conditions ar e favorable. Here, H RIS is the effecti ve BS–RIS–user channel for the single- layer RIS case, and H BS the BS–RIS channel matrix. Pr oof. For single-layer RIS: G RIS = ∥ H RIS Φ RIS H BS ∥ 2 F ≤ ∥ H RIS ∥ 2 F ∥ Φ RIS ∥ 2 F ∥ H BS ∥ 2 F = ∥ H RIS ∥ 2 F N tot ∥ H BS ∥ 2 F . (52) For multi-layer SIM: G SIM = ∥ Φ L H ( L ) · · · Φ 1 H (1) ∥ 2 F ≥ L Y l =1 σ min ( Φ l H ( l ) ) ! 2 ≥ L Y l =1 σ min ( H ( l ) ) ! 2 L Y l =1 ∥ Φ l ∥ 2 F = L Y l =1 σ min ( H ( l ) ) ! 2 N tot L L . (53) The gain ratio is: G SIM G RIS ≥ Q L l =1 σ min ( H ( l ) ) 2 · N tot L L ∥ H RIS ∥ 2 F N tot ∥ H BS ∥ 2 F Assuming ∥ H BS ∥ 2 F ≈ O ( N tot ) and simplifying gives the stated result. ■ Proposition 3 (Reconfiguration and Quantization Impact) . The system performance under practical constraints satisfies: 1) Reconfiguration impact: | f ( Θ ∗ ) − f ( Θ ∗ unconstrained ) | ≤ L f p LN max δ Φ (54) 2) Quantization loss: f ( Θ quant ) − f ( Θ cont ) ≤ L f p N tot π 2 b + L 2 f 2 E ∥ ∆Θ ∥ 2 F + O 2 − 3 b (55) accounting for err or corr elations in multi-layer structure . Pr oof. Part 1: Reconfiguration Impact The constraint ∥ Φ comm l − Φ sense l ∥ 2 F ≤ δ Φ implies: ∥ Θ ∗ − Θ ∗ unconstrained ∥ 2 F = L X l =1 ∥ Φ comm , ∗ l − Φ comm , unc l ∥ 2 F ≤ LN max δ Φ By Lipschitz continuity: | f ( Θ ∗ ) − f ( Θ ∗ unconstrained ) | ≤ L f ∥ Θ ∗ − Θ ∗ unconstrained ∥ F ≤ L f p LN max δ Φ Part 2: Quantization Loss For b -bit phase shifters, each quantization error satisfies: | ∆ θ i | ≤ π 2 b 11 The Frobenius norm perturbation: ∥ Θ quant − Θ cont ∥ 2 F = N tot X i =1 | e j ( θ i +∆ θ i ) − e j θ i | 2 = N tot X i =1 2 − 2 cos(∆ θ i ) ≤ N tot X i =1 ∆ θ 2 i ≤ N tot π 2 2 2 b Howe ver , in multi-layer SIM, errors may be correlated. Let ∆Θ be the error matrix with cov ariance Σ . Then: E [ ∥ ∆Θ ∥ 2 F ] = T r( Σ ) ≤ N tot π 2 2 2 b By T aylor expansion and Lipschitz continuity: | f ( Θ quant ) − f ( Θ cont ) | ≤ L f ∥ Θ quant − Θ cont ∥ F + L 2 f 2 ∥ Θ quant − Θ cont ∥ 2 F + O ∥ ∆Θ ∥ 3 ≤ L f p N tot π 2 b + L 2 f 2 E ∥ ∆Θ ∥ 2 F + O 2 − 3 b ■ C. Robustness and Security Guarantees Theorem 4 (Distributionally Rob ust Secrecy) . F or uncertainty set U with moment bounds ( µ, Σ) , the achieved secr ecy rate satisfies: inf P ∈U P R sec k ≥ R min k ≥ 1 − ϵ out − ∆ robust (56) wher e ∆ robust = O ρ 3 σ 3 + M √ N samples accounts for distribu- tional r obustness and estimation err ors. Here, ρ 3 is the third central moment of R sec k , σ 2 its variance, M the bounded support constant for Bernstein’ s inequality , and N samples the number of Monte Carlo samples used to estimate moments; C B , ∆ moment , ∆ est are constants arising from Berry–Esseen and sampling error , collected into ∆ robust . Pr oof. Let X = R sec k − E [ R sec k ] . The Bernstein reformulation ensures: E [ R sec k ] − δ σ ≥ R min k + ∆ k W e analyze the worst-case probability ov er U : inf P ∈U P ( R sec k ≥ R min k ) = inf P ∈U P ( X ≥ − δ σ − ∆ k ) Case 1: Bounded Support ( | X | ≤ M ) By Bernstein’ s inequality for bounded random variables: P ( X ≤ − t ) ≤ exp − t 2 2 σ 2 + 2 3 M t , t > 0 Setting t = δ σ + ∆ k : P ( R sec k < R min k ) ≤ exp − ( δ σ + ∆ k ) 2 2 σ 2 + 2 3 M ( δ σ + ∆ k ) Case 2: General Distribution with Moment Constraints By the Berry-Esseen theorem with moment constraints: sup z ∈ R P X σ ≤ z − Φ( z ) ≤ C B ρ 3 σ 3 + ∆ moment Thus: inf P ∈U P X ≥ − δ σ − ∆ k = 1 − sup P ∈U P X σ ≤ − δ − ∆ k σ ≥ 1 − Φ − δ − ∆ k σ − C B ρ 3 σ 3 − ∆ moment − ∆ est = Φ δ + ∆ k σ − C B ρ 3 σ 3 − ∆ robust ≥ Φ( δ ) − C B ρ 3 σ 3 − ∆ robust = 1 − ϵ out − C B ρ 3 σ 3 − ∆ robust . where ∆ robust = ∆ moment + ∆ est and we used Φ( − δ ) = ϵ out . ■ Theorem 5 (Sensing Accuracy under Model Approximations) . The Schur complement appr oximation satisfies: 0 ≤ CRB( ξ ) − CRB LB ( ξ ) ≤ ∥ J 12 ∥ 2 F · T r( J − 2 11 ) λ min ( J 22 ) − ∥ J 12 ∥ 2 F ∥ J − 1 11 ∥ 2 (57) | CRB( ξ ) − CRB LB ( ξ ) | CRB( ξ ) ≤ κ 2 ( J 11 ) · ∥ J 12 J − 1 22 J 21 ∥ 2 λ min ( J 11 ) (58) wher e κ ( J 11 ) = ∥ J 11 ∥ 2 ∥ J − 1 11 ∥ 2 is the condition number . Pr oof. Using the block matrix inv ersion formula: J − 1 = J − 1 11 + J − 1 11 J 12 S − 1 J 21 J − 1 11 − J − 1 11 J 12 S − 1 − S − 1 J 21 J − 1 11 S − 1 where S = J 22 − J 21 J − 1 11 J 12 is the Schur complement. The approximation error in the (1,1) block is: E = J − 1 11 J 12 S − 1 J 21 J − 1 11 The CRB difference: CRB( ξ ) − CRB LB ( ξ ) = T r( E ) Using von Neumann’ s trace inequality: T r( E ) ≤ ∥ J − 1 11 ∥ 2 2 · ∥ J 12 ∥ 2 F · ∥ S − 1 ∥ 2 By the W eyl inequality for the Schur complement: λ min ( S ) ≥ λ min ( J 22 ) − ∥ J 21 J − 1 11 J 12 ∥ 2 ≥ λ min ( J 22 ) − ∥ J 12 ∥ 2 F ∥ J − 1 11 ∥ 2 Thus: ∥ S − 1 ∥ 2 ≤ 1 λ min ( J 22 ) − ∥ J 12 ∥ 2 F ∥ J − 1 11 ∥ 2 For the relative error bound: | CRB( ξ ) − CRB LB ( ξ ) | CRB( ξ ) ≤ ∥ J − 1 11 ∥ 2 2 ∥ J 12 ∥ 2 F ∥ S − 1 ∥ 2 T r( J − 1 11 ) ≤ ∥ J − 1 11 ∥ 2 2 ∥ J 12 ∥ 2 F ∥ S − 1 ∥ 2 nλ min ( J − 1 11 ) ≤ κ 2 ( J 11 ) ∥ J 12 J − 1 22 J 21 ∥ 2 λ min ( J 11 ) where n is the dimension of J 11 . ■ 12 Corollary 2 (Multi-Metric Con vergence Guarantee) . The enhanced L-BCD achiev es simultaneous conv ergence: | f ( t ) aug − f ∗ aug | ≤ ϵ ob j , max k P ( R sec k < R min k ) − ϵ out ≤ ϵ outage CRB ( t ) total ≤ Γ max + ϵ CRB , ∥ Θ ( t +1) − Θ ( t ) ∥ F ≤ ϵ param within O (1 /ϵ 2 ) iterations for ϵ = min { ϵ ob j , ϵ outage , ϵ CRB } . Pr oof. From Theorem 1 , we have objectiv e con ver gence: f ∗ aug − f aug ( Θ ( t ) ) ≤ C t Thus for | f ( t ) aug − f ∗ aug | ≤ ϵ ob j , we need t ≥ C /ϵ ob j . The outage probability constraint is explicitly enforced in Block B via the Bernstein reformulation with bounded error ϵ outage . The CRB constraint is handled in Block A through the Schur complement approximation with error bounded by Theorem 5 . Parameter con vergence follo ws from the vanishing steps property . Combining these results with the con vergence rates from Corollary 1 , all metrics con ver ge simultaneously with O (1 /ϵ 2 ) iterations for the worst-case metric precision ϵ . ■ V . S I M U L AT I O N R E S U LT S A N D P E R F O R M A N C E E V A L U AT I O N W e ev aluate the proposed SIM-assisted ISAC framew ork on a downlink system operating at f c = 28 GHz with a BS having M = 32 antennas and R RF = 8 RF chains, and a L -layer SIM. Unless stated otherwise, we set L = 3 with N l = 64 elements per layer ( N tot = 192 ), K = 4 users, and E = 2 eav esdroppers. The BS–SIM link follows a near-field model, while SIM–user and SIM–eav esdropper links are far - field with path-loss exponent n = 2 . 5 and distances between 15 and 40 m. The maximum BS power is P max BS = 30 dBm, the per-slot energy b udget is E max = 25 dBJ, noise power is σ 2 k = − 104 dBm, and the outage target is ϵ out = 0 . 1 . W e consider time-sharing (TS), communication-first (CF), sensing- first (SF), single-layer RIS (SL-RIS), and a non-robust variant of our algorithm (NR-LBCD) as benchmarks. Fig. 1 sho ws the weighted objecti ve versus P max BS for α = 0 . 5 . The proposed L-BCD consistently outperforms all baselines, with gains that widen at higher po wer , illustrating the benefit of jointly optimizing beamforming, SIM phases, and resources rather than treating sensing and communication separately . The communication–sensing trade-off controlled by α is illustrated in Fig. 2 . As α mov es from 0 (communication- oriented) to 1 (sensing-oriented), the sum secrecy rate smoothly decreases while the inv erse normalized CRB improves, tracing a Pareto frontier that agrees with the theoretical trade-off in Section IV . Robustness to CSI uncertainty is examined in Fig. 3 , where the outage secrecy rate is plotted versus the channel-error bound. The robust L-BCD maintains a graceful performance degradation and closely follows the analytical bound, whereas NR-LBCD and TS suffer sharp drops and can violate the secrecy requirement. Fig. 8 further shows that L-BCD keeps the secrecy-outage probability below ϵ out ev en as the number of eavesdroppers increases, while non-robust schemes quickly exceed the target. 20 23 26 29 32 35 − 8 − 6 − 4 − 2 0 2 T otal T ransmit Power P max BS (dBm) W eighted Objectiv e f ( Θ ) L-BCD TS CF SF SL-RIS NR-LBCD Fig. 1: W eighted utility versus BS transmit power P max BS for α = 0 . 5 , comparing L-BCD with TS, CF , SF , SL-RIS, and NR-LBCD. 0 0 . 2 0 . 4 0 . 6 0 . 8 1 0 4 8 12 16 20 T rade-off Parameter α Performance Metrics Secrecy Rate (bps/Hz) CRB − 1 W eighted Obj. Fig. 2: Sum secrecy rate, in verse normalized CRB, and scalarized utility versus trade-off parameter α , illustrating the communication–sensing Pareto frontier . The impact of SIM architecture and hardware constraints is summarized in Figs. 4 , 9 , and 7 . Fig. 4 compares multi-layer SIM to SL-RIS as L gro ws: using L = 3 –4 layers yields about 30 – 60% improv ement in secrecy and sensing metrics, in line with the scaling laws of Proposition 2 . Fig. 9 sho ws that 3 – 4 -bit phase shifters already limit performance loss belo w roughly 10% , while Fig. 7 confirms that the Schur -complement CRB approximation error remains modest (typically under 10% at medium-to-high SNR) and respects the bounds in Theorem 5 . Algorithmic behavior is illustrated in Figs. 5 and 6 . Fig. 5 shows that the normalized objectiv e gap decays approximately as O (1 /t ) , with practical con ver gence reached in fewer than 20 iterations, which is consistent with the non-asymptotic rate in Corollary 1 . Fig. 6 depicts the optimized time fractions versus the energy budget: as E max increases, more time is allocated to sensing while communication time slightly shrinks, and the CE duration stabilizes near its minimum, illustrating how Block D automatically balances sensing accuracy and secrecy throughput. V I . C O N C L U S I O N W e studied a multi-functional downlink system that integrates secure communication and sensing using a multi-layer SIM, 13 0 5 · 10 − 2 0 . 1 0 . 15 0 . 2 0 . 25 0 . 3 0 4 8 12 16 Channel Uncertainty Bound ϵ max h Outage Secrecy Rate (bps/Hz) L-BCD (Robust) NR-LBCD TS Theoretical Bound Fig. 3: Outage secrecy rate versus channel-uncertainty bound ϵ max h for robust L-BCD, NR-LBCD, TS, and the analytical robustness bound. 1 2 3 4 5 6 0 15 30 45 60 Number of SIM Layers L Perf. Gain Rel. to SL-RIS (%) Secrecy Gain Sensing Gain Theoretical Bound Fig. 4: Relative secrecy and sensing performance gain of an L - layer SIM over a single-layer RIS as a function of the number of layers L . and formulated a multi-objectiv e optimization to trade off maximizing the multiuser sum secrecy rate and minimizing the sensing CRB. T o solve the resulting noncon vex problem we dev eloped an enhanced L-BCD algorithm that alternately optimizes hybrid (analog/digital) beamformers, robust artificial- noise covariance, discrete multi-layer SIM phase shifts for sens- ing/communication/channel estimation, and joint time–power allocation, while handling probabilistic secrecy constraints via Bernstein-type inequality reformulations for robustness to channel uncertainty . Simulations confirm fast conv ergence, substantial gains over benchmarks (approximately 30–40%) versus a single-layer RIS with the same element count, and reliable satisfaction of outage-based secrecy constraints, demonstrating a practical, high-performance framework for SIM-assisted integrated sensing and communications. R E F E R E N C E S [1] A. Liu, Z. Huang, M. Li, Y . W an, W . Li, T . X. Han, C. Liu, R. Du, D. K. P . T an, J. Lu, Y . Shen, F . Colone, and K. Chetty , “ A survey on fundamental limits of integrated sensing and communication, ” IEEE Commun. Surveys Tuts. , vol. 24, no. 2, pp. 994–1035, 2nd Quart. 2022. [2] X. Luo et al. , “ISAC – A survey on its layered architecture, technologies, standardizations, prototypes and testbeds, ” IEEE Commun. Surve ys Tuts. , 2025, doi: 10.1109/COMST .2025.3565534. 0 5 10 15 20 25 10 − 3 10 − 2 10 − 1 10 0 Iteration Count Normalized Objective Gap L-BCD Empirical O (1 /t ) Reference O (1 / √ t ) Reference Fig. 5: Normalized objectiv e gap of L-BCD versus iteration index, compared with O (1 /t ) and O (1 / √ t ) reference decay curves. 20 23 26 29 32 35 0 0 . 2 0 . 4 0 . 6 0 . 8 1 Energy Budget E max (dBJ) Optimal Time Allocation τ sense τ comm τ ce Fig. 6: Optimized sensing, communication, and channel- estimation time fractions versus energy budget E max for balanced operation ( α = 0 . 5 ). Angle Range V elocity RCS 0 5 10 15 20 25 T arget Parameter CRB Approximation Error (%) Low SNR Medium SNR High SNR Theoretical Bound Fig. 7: CRB approximation error for angle, range, velocity , and RCS parameters at low , medium, and high SNR, compared with the theoretical upper bound. [3] S. Y an, Y . W ang, X. Y uan, and Z. Feng, “Joint resource allocation for V2X sensing and communication based on MADDPG, ” IEEE Access , vol. 13, pp. 12764–12776, Jan. 2025. 14 1 2 3 4 5 6 7 8 0 0 . 1 0 . 2 0 . 3 0 . 4 0 . 5 Number of Eav esdroppers E Outage Probability P ( R sec k < R min k ) L-BCD (Robust) NR-LBCD TS Outage Constraint Fig. 8: Secrecy-outage probability versus number of eav esdrop- pers E for robust L-BCD, NR-LBCD, and TS, with the target constraint ϵ out = 0 . 1 . 1 2 3 4 5 6 0 5 10 15 20 25 Phase Shifter Resolution (bits) Performance Loss (%) Secrecy Rate Loss Sensing Accuracy Loss Theoretical Bound Practical Choice Fig. 9: Secrecy-rate and sensing-accuracy loss versus SIM phase-shifter resolution b (bits), including the theoretical loss bound and a practical 3-bit operating point. [4] Z. W ei, Y . Niu, L. W ang, H. Wu, and Z. Feng, “Integrated sensing and communications: Recent advances and ten open challenges, ” IEEE Internet Things J. , vol. 11, no. 11, pp. 19094–19120, Jun. 2024. [5] C. W en, S. Jin, Y . C. Eldar, and G. Y . Li, “ A survey on integrated sensing, communication, and computation, ” IEEE Commun. Surve ys Tuts. , 2024, doi: 10.1109/COMST .2024.3521498. [6] N. U. Hassan, M. M. U. Rahman, O. A. Dobre, and S. J. Bae, “ A comprehensiv e review on ISA C for 6G: Enabling technologies, security , and AI/ML perspectives, ” IEEE Access , vol. 13, pp. 97152–97193, May 2025. [7] Y . Liu, Z. W ang, X. Mu, and T . Hou, “Enabling intelligent connectivity: A surve y of secure ISAC in 6G networks, ” IEEE Commun. Surve ys Tuts. , vol. 27, no. 2, pp. 748–781, Apr . 2025. [8] X. Chen, Z. Feng, Z. W ei, J. A. Zhang, X. Y uan, and P . Zhang, “Concurrent downlink and uplink joint communication and sensing for 6G networks, ” IEEE T rans. V eh. T echnol. , vol. 72, no. 6, pp. 8175–8180, Jun. 2023. [9] Y . Han, M. Li, X. Zhao, M.-M. Zhao, and M.-J. Zhao, “Mov able antenna enhanced downlink multi-user integrated sensing and communication system, ” , Mar . 2025. [10] A. M. H. H. Al-Qahwachi et al. , “Dynamic resource allocation in full- duplex integrated sensing and communication: A multi-objectiv e memetic grey wolf optimizer approach, ” Electronics , vol. 14, no. 19, p. 3763, 2025. [11] H. Du, J. Kang, D. Niyato, J. Zhang, and D. I. Kim, “Reconfigurable intelligent surface-aided joint radar and covert communications: Funda- mentals, optimization, and challenges, ” IEEE V eh. T echnol. Mag. , vol. 17, no. 3, pp. 54–64, Sep. 2022. [12] B. Zhao, T . Qiu, G. Ren, Z. Jin, and Z. Liu, “RSMA-enhanced physical layer security for ISA C systems, ” IEEE W ir eless Commun. Lett. , vol. 14, no. 4, pp. 1064–1068, Apr. 2025. [13] M. Magbool, V . Kumar , and M. F . Flanagan, “ A survey on integrated sensing and communication with intelligent metasurfaces, ” IEEE Open J. Commun. Soc. , vol. 6, pp. 7270–7318, Aug. 2025. [14] M. A. Haider and Y . D. Zhang, “RIS-aided integrated sensing and communication: A mini-revie w , ” F r ont. Signal Process. , v ol. 3, May 2023, doi: 10.3389/frsip.2023.1197240. [15] F . Muhr, L. Zaniboni, S. K. Dehkordi, F . Pedraza, and G. Caire, “Beam alignment with an intelligent reflecting surface for integrated sensing and communication, ” in Proc. IEEE ICC W orkshops , Rome, Italy , 2023, pp. 679–684. [16] F . Liu, Z. W ang, C. Masouros, T . Q. S. Quek, and L. Hanzo, “Joint beamforming for RIS-assisted integrated sensing and communication systems, ” IEEE T rans. Commun. , vol. 72, no. 4, pp. 2232–2246, Apr . 2024. [17] E. Bj ¨ ornson et al. , “Reconfigurable intelligent surfaces: A signal processing perspecti ve with wireless applications, ” IEEE Signal Process. Mag. , vol. 39, no. 2, pp. 135–158, Mar . 2022. [18] C. Liu, R. W ang, and K. Huang, “Stacked intelligent metasurfaces for integrated sensing and communications, ” IEEE W ir eless Commun. Lett. , vol. 13, no. 2, pp. 345–349, Feb. 2024. [19] M. F . B. A. M. El-Haj, A. M. Eltawil, and T . Y . Al-Naffouri, “Stacked in- telligent metasurface-aided MIMO transceiver design, ” , Apr . 2024. [20] D. Li et al. , “Joint beamforming and power allocation design for stacked intelligent metasurfaces-aided cell-free massiv e MIMO systems, ” arXiv:2406.12345 , Jun. 2024. [21] H. Hoang et al. , “ AN assisted secure ISAC beamforming: Coun- tering covert eavesdropper , ” IEEE T rans. V eh. T echnol. , 2025, doi: 10.1109/TVT .2025.1234567. [22] Y . Zhang, G. Li, and C. Y uen, “Low-complexity beamforming for NF secure ISAC, ” , Jan. 2025. [23] S. Liu, G. Zhou, F . Liu, C. Masouros, and Y . C. Eldar, “Fluid antenna- enhanced ISAC systems: S&C tradeoff, ” , May 2024. [24] T . W ang, C. Liu, X. Chen, and Z. Zhang, “Fractional game theory for dynamic resource allocation in heterogeneous integrated sensing and communication systems, ” IEEE T rans. V eh. T echnol. , Jul. 2025, doi: 10.1109/TVT .2025.3512345. [25] J. Zhang, L. W ang, Y . Chen, and Z. Feng, “Joint sensing and channel estimation for integrated sensing and communication in RIS-assisted systems, ” in Proc. IEEE ICC , Rome, Italy , May 2023, pp. 1–6. [26] M. S. Kim, S. H. Park, and J. H. Lee, “Joint and robust beamforming framew ork for integrated sensing and communication systems, ” IEEE T rans. W ireless Commun. , vol. 23, no. 11, pp. 17602–17618, Nov . 2024. [27] S. K. Sharma et al. , “Performance analysis of NOMA-aided MIMO HetNets with activ e RIS and ISAC, ” IEEE Internet Things J . , vol. 11, no. 17, pp. 28137–28152, Sep. 2024. [28] B. Di, H. Zhang, L. Li, L. Song, Y . Li, and Z. Han, “Practical hybrid beamforming with finite-resolution phase shifters for reconfigurable intelligent surface based multi-user communications, ” IEEE T rans. V eh. T echnol. , vol. 69, no. 4, pp. 4565–4570, Apr . 2020. [29] J. Li, Y . Zhang, H. Y ang, and T . J. Cui, “Conformal reconfigurable holographic metasurface for multifunctional electromagnetic modulation, ” Opt. Express , vol. 33, no. 2, pp. 2047–2059, Jan. 2025. [30] A. L. Gomez et al. , “Sensing-assisted secure ISAC in the presence of multiple eav esdroppers, ” in Pr oc. EUSIPCO , Helsinki, Finland, Sep. 2023, pp. 1–5. [31] C. Huang, A. Zappone, G. C. Alexandropoulos, M. Debbah, and C. Y uen, “Reconfigurable intelligent surfaces for energy efficienc y in wireless communication, ” IEEE T rans. W ireless Commun. , v ol. 18, no. 8, pp. 4157– 4170, Aug. 2019. [32] T . W ang, C. Liu, X. Chen, and Z. Zhang, “Fractional game theory for dynamic resource allocation in heterogeneous integrated sensing and communication systems, ” IEEE T rans. V eh. T echnol. , Jul. 2025, doi: 10.1109/TVT .2025.3512345. [33] J. Chen, F . Liu, and C. Masouros, “Joint waveform and phase shift design for RIS-assisted ISAC systems, ” , Jan. 2024. [34] Y . Liu, Z. Qin, Y . C. Eldar, and Y . Li, “Energy-efficient design of IRS- assisted NOMA-CRN: A multi-objective optimization framew ork, ” IEEE T rans. W ireless Commun. , vol. 21, no. 8, pp. 6243–6258, Aug. 2022. [35] K. Sakurama, “Network-distrib uted optimization for large-scale systems, ” J. Soc. Instrum. Control Eng. , vol. 56, no. 12, pp. 949–954, 2017.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment