Correct-by-construction requirement decomposition
In systems engineering, accurately decomposing requirements is crucial for creating well-defined and manageable system components, particularly in safety-critical domains. Despite the critical need, rigorous, top-down methodologies for effectively breaking down complex requirements into precise, actionable sub-requirements are scarce, especially compared to the wealth of bottom-up verification techniques. Addressing this gap, we introduce a formal decomposition for contract-based design that guarantees the correctness of decomposed requirements if specific conditions are met. Our (semi-)automated methodology augments contract-based design with reachability analysis and constraint programming to systematically identify, verify, and validate sub-requirements representable by continuous bounded sets – continuous relations between real-valued inputs and outputs. We demonstrate the efficacy and practicality of a correct-by-construction approach through a comprehensive case study on a cruise control system, highlighting how our methodology improves the interpretability, tractability, and verifiability of system requirements.
💡 Research Summary
The paper addresses a long‑standing gap in systems engineering: the lack of rigorous, top‑down methods for decomposing high‑level requirements into precise, verifiable sub‑requirements, especially in safety‑critical domains. While formal verification tools are abundant for bottom‑up validation of designs, they do not guarantee that the requirements themselves have been correctly partitioned. To fill this void, the authors propose a “correct‑by‑construction” requirement decomposition framework built on contract‑based design (CBD).
The core idea is to model a system as an input‑output relation over real‑valued vectors, where each variable is bounded within a continuous set. Requirements are expressed as assume‑guarantee contracts: an Assumption set A ⊆ X (acceptable inputs) and a Guarantee relation G ⊆ X×Y (acceptable input‑output pairs). Two fundamental contract conditions must hold: (C1) every input in A is accepted, and (C2) for each accepted input there exists at least one output in G.
The decomposition proceeds in three formally defined steps.
- Primary Refinement splits a top‑level contract f₀ into a collection of lower‑level contracts (e.g., f₁, f₂). The collection must collectively cover the original input space and its reachable output set must be a subset of the original guarantee. Formal inclusion properties (P1, P2) guarantee that the refinement does not weaken the original requirement.
- Secondary Refinement further refines each lower‑level contract into a functional contract gₖ: Xₖ×Pₖ → Xₖ×Yₖ, where Pₖ denotes bounded uncertain parameters (mass, friction, etc.). This step adds structure, turning relational contracts into deterministic functions while preserving the bounded uncertainty.
- Implementation maps each functional contract to a concrete implementation fₖ* (e.g., generated code or controller). An implementation satisfies its contract if, for every admissible input, the reachable output set lies inside the guarantee.
Automation is achieved by integrating two formal techniques. Reachability analysis computes over‑approximations of the set of states and outputs that a candidate implementation can achieve, enabling a check that the implementation’s output set is contained in the guarantee. Constraint programming encodes composability, realizability, and satisfiability conditions as a constraint satisfaction problem (CSP). Modern CSP solvers then search for parameter values and contract refinements that satisfy all constraints. The methodology is semi‑automated: designers define the high‑level contract and architectural decomposition; the tool automatically derives the refinement constraints, solves the CSP, and validates the resulting sub‑contracts.
Scalability is discussed in depth. The hierarchical nature of contracts naturally supports decomposition of moderately complex systems. However, deeper hierarchies increase CSP dimensionality. The authors argue that problem decomposition and efficient constraint propagation mitigate this issue, allowing the approach to scale to larger instances.
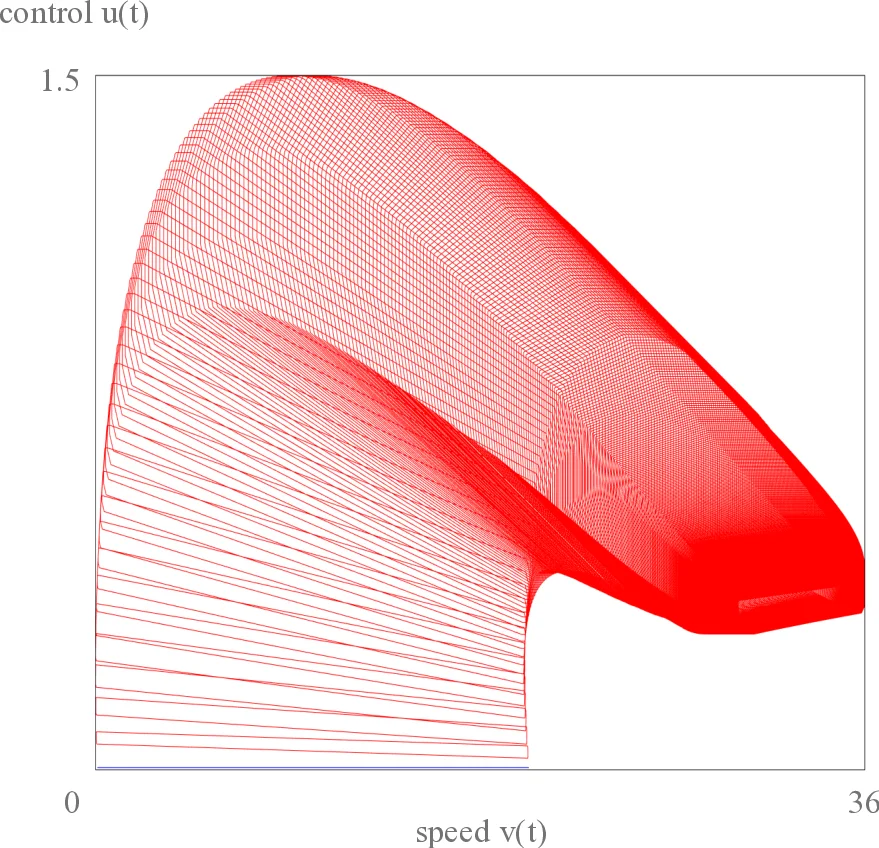
A comprehensive case study on a cruise‑control system illustrates the approach. The top‑level requirement (“maintain vehicle speed within 0‑150 km/h, respecting acceleration limits and external disturbances”) is encoded as contract f₀. It is refined into three sub‑contracts: speed‑maintenance, acceleration‑limit, and disturbance‑compensation. Each sub‑contract is turned into a functional contract with parameters such as vehicle mass, engine torque limits, road grade, and wind force. Reachability analysis confirms that for all admissible initial speeds and environmental conditions, the reachable speed trajectories remain within the top‑level guarantee. The CSP solver finds feasible parameter bounds that satisfy composability between the sub‑contracts. Finally, simulated controller code is verified against the contracts using a model‑checker, demonstrating that the implementations collectively satisfy f₀.
The paper acknowledges limitations. The current framework assumes that requirements can be expressed as continuous bounded sets; purely logical or discrete requirements (mode switches, event‑driven behavior) are not directly handled. Moreover, very deep contract hierarchies may cause exponential growth in the CSP search space, potentially limiting practicality for extremely large systems. Future work is proposed on hybrid discrete‑continuous contracts, automated contract generation, and distributed verification techniques.
In summary, the authors deliver a novel, mathematically grounded methodology that unifies top‑down requirement decomposition with bottom‑up formal verification. By guaranteeing that each sub‑requirement is a correct refinement of its parent, the approach eliminates a major source of design errors, improves traceability, and enhances the overall assurance case for safety‑critical systems. The cruise‑control example validates the practicality of the method and showcases its potential to reduce development cost and risk in real‑world engineering projects.
Comments & Academic Discussion
Loading comments...
Leave a Comment