Physical Access Control Management System Based on Permissioned Blockchain
Using blockchain as a decentralized backend infrastructure has grabbed the attention of many startups entrepreneurs and developers. Blockchain records transactions permanently and protects them from undesirable tampering. It provides a reliable tampe…
Authors: Sara Rouhani, Vahid Pourheidari, Ralph Deters
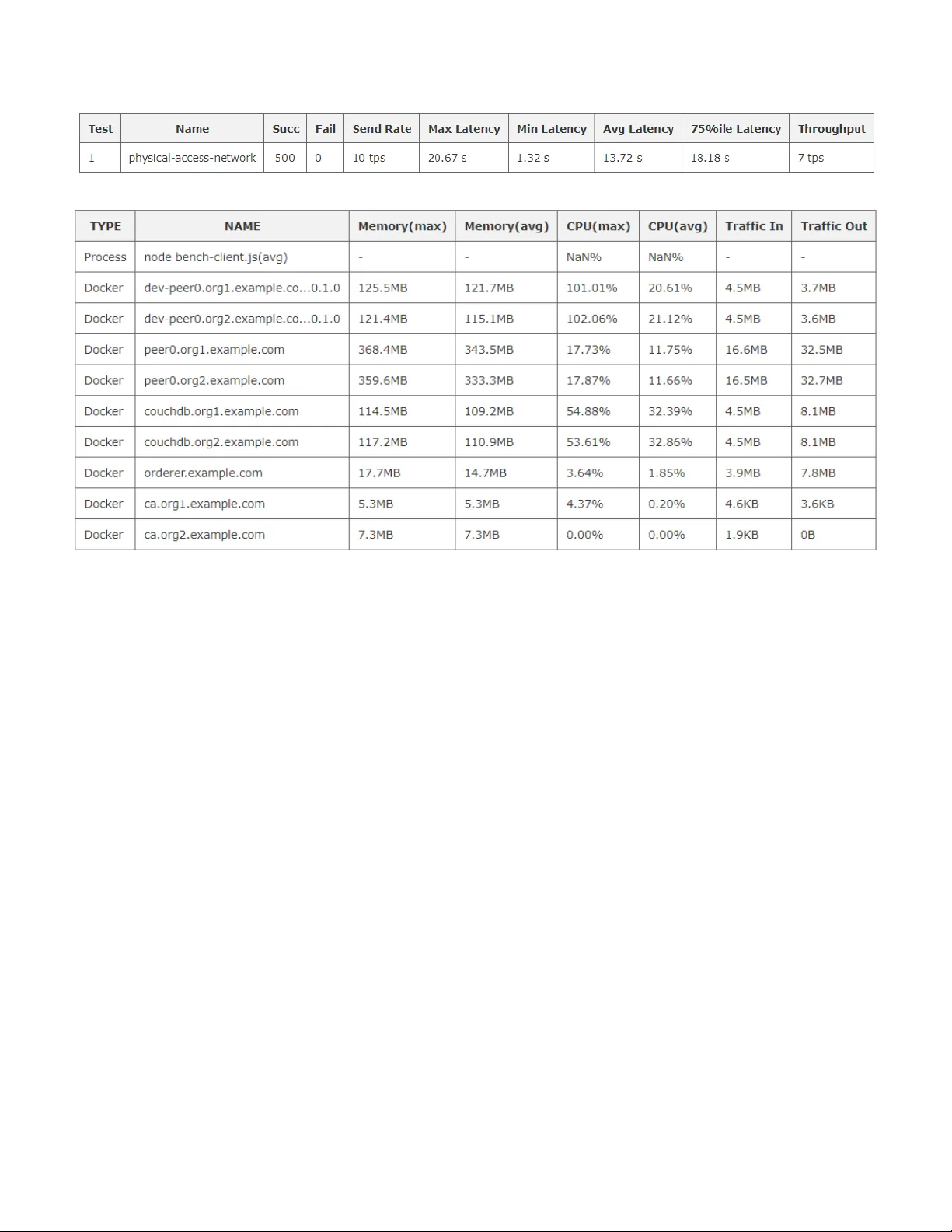
Physical Access Control Management System Based on Permissioned Blockchain Sara Rouhani Department of Computer Science University of Saskatchewan Saskatoon, Canada sara.rouhani@usask.ca Vahid Pourheidari Department of Computer Science University of Saskatchewan Saskatoon, Canada vahid.p@usask.ca Ralph deters Department of Computer Science University of Saskatchewan Saskatoon, Canada deters@cs.usask.ca Abstract — Using blo ckchain as a decentralized backend infrastructure has grabbed the attention of many startups entrepreneurs and developers. Blockchain records transactions permanently and protects them from undesirable ta mpering. It provides a reliable tamper-proof database w hich can be consider ed as a trustable source for tracking the previous sy stem state. In this paper , w e p resent our access control applica tion based on Hyperledger Fabric B lockchain and Hy perledger Composer to control access to physical pla ces. The system components and modular architecture are ill ustrated, and we have extracted m et adata include h istorian transactions ’ details arising fro m our de mo test. Finally, the performance metrics a nd resources consumption are provided using Hyperledger Caliper, a benchmark framework for measuring Hyperledger blockchains performance. Keywords — Blockchain, Smart Contracts, Access Co ntrol , Physical Access Control, Hyperledger I. I NTRODUCTI ON Access Control system s ar e applied in computer security to specify the conditi ons and implementation of granting or revoking access to logical or p hysical r esources. A pplyin g blockchain for access control sy stems is one of the in- demanding areas fo r usin g thi s new te chnology . B lockchain ’s unique characte ristics such as durability , immutabil ity , reliabil ity, auditabil ity, and security , made it a perfect soluti on for access contro l system s for a variety o f applications such as healthcar e sy stem s [1]. Block chain can be consider ed as a distribute d database to manage access co ntr ol and includes the permanen t hist ory of transactions which are tamper-proof and indelible . I n ad dition, blockc hain rem oves the thir d parti es ’ part fr om the sy stem and consequent ly it pr ovides privacy . There are two types of access control system s, Logical Access Control, and Physica l Access Control. Most of the studies on access control systems focus on logical access control, how ever, we have considered blockchain ’ s potential as an infras tructu re for access control managem ent software on the top of the physical access control system s . B lockcha in provides a tamper-pr oof solution for access con trol sy stem s which provides an auditable trail of transactions. There are tw o advantages of using blockch ain for physical access control system s . First the history of all recorde d transact ions stores o n a reliable tamper-pr oof d ataba se, hens significantly reduces the chance of collusion. S econd management of access rights perform s by a distribut ed approach, so the role o f the third party eliminates from the system and authorize d users can grant or revoke an other us ers’ access dire ctly. In this research study, we have implemen ted an access control applicati on based on Hyperledger Fabric permissioned blockchain . We have implem ented a simulated scena rio to test the a pplicat ion, and th e metadata h as been ext racted from the historian record of the su bmitt ed transacti ons. In the f ollowin g o f the paper in secti on tw o, w e overview the background related topics. We review the related works in section three. Secti on four pre sents our sys tem componen ts and architectu re model . Analy sis of our applicat ion availa ble in se ction five and finally , section six states summary and f utu re works. II. B ACKGROU ND A. B lockchain and Smart Contracts Blockchain initially introduced by bitcoin [2], a successful decentral ized sys tem for transferring digit al currencies di rectly . Blockchain is the new generation o f the distribut ed database system s and it is handled by the peer to peer network. It is the chain of chronological blocks of transacti ons which is submitted by untrusted parties and they co nfi rm with out any central authori ty. The chain starts with genesis block and it continuou sly grows when a new block links to the previous block through a hash value of the previous block. In ot her words, f or h ash value calculation of any n ew block, the hash value of the previous block is considere d as well. T hat feat ure makes blockchain tamper r esistant because if som eone attempts to make a change, the hashes for linked blocks will also change and this disru pts th e ledger st ate and this m akes the conflict between the copies of the shar ed ledger. T he concep t of sh ared ledger refers to th is p oint that every p eer on t he blockchain would have access to a copy of the whole ledger. After changing to the b lockc hain unique state, the process o f syncing starts and again every peer w ill access the updated state of th e bl ockchain. Auditability is one o f the key characterist ics o f the blockchain . After that each tran saction validated , it records on the current block with a timestam p and blockchain’s users are able to track the previous transactions and they can access the history o f all trans actions . T his feature is very interest ing from data management perspectiv e and the applications that are require d to access to tam per-proof log hist ory. Blockchain uses dif ferent consen sus algori thm s to reach agreem ent on the new state for the blockchain. T he main idea of using consensus algorithm is to use a group of people who are involved in the system for decision mak ing instead of usin g a trusted thir d party for making decisions. Proof of work (PoW), proof of stake (PoS) and Practical Byzantine Fault Toleranc e (PBF T) are th e most k now n cases of bl ockchain consensus algorith ms. These consensu s algo rithms are differ ent in identity managem ent mechanism, energy saving, and tolerating pow er of adve rsary [3]. Smart Contrac t is a set of programm able functions tha t store on the b lockcha in an d automatic ally enforce its ter ms without the need for trusted intermediaries . Smart contract’s functional ity is almost like traditi onal contra cts. As the traditi onal contracts include conditions that each of the parties is obligated to follow , blockchain smart contracts have been designed to automate the same task by automatic ally validati ng conditions and running the next steps automatical ly based on the result of the conditions. However, smart contracts automate transacti ons without the need for a central authority or legal system . By utilizing smart contracts , we can define more complex transaction tangled under specific conditions on the blockchain and as a result, we can develop applicati on beyo nd just transferring digital curren cies in more various are such as supply cha in, busin ess process m anagem ent, and health care. B. Pu blic and Private Blockchain Bitcoin is the first creation o f b lockchain and it is public. That means everybody with anonym ous i dentity can join to the blockchain , read the blockch ain, send transa ctions and be considere d as a mem ber of the consensus committee. Public blockchain s may seem interesting from some application perspectiv e since they are open to the world and their users’ identity is not kn own, however, the emergin g of priv ate blockchain s are tailored from intra organizati on perspective to rolling out block chain in to div erse pro ductions . In perm issioned or private blockch ain, the re is an additi onal permiss ion layer to authenticate users who want to join to the blockchain . So, the main difference between public and private blockchain is w ho can be part of the sy stem . In addition, it is worth to mention that there is a third type of blockchain known as consortium blockchain and it could be considere d as a hybrid type as only a selecte d of nodes can partici pate in decision making, and the access to read or wright on the bl ockchain could b e publi c or res tricted . [4 ]. Hyperledge r is a set of projects for open-source industrial blockchain framew orks such as Fabric, Saw tooth, Burrow, and Iroha hos ted by Linux Foundation . Hyperledge r Fabric provides modular architecture and includes Mem bership com ponent to create flexible permiss ioned b lockchain platform s. Fabric supports smart co ntracts called “ chaincode ” which is programm ing cod e for implem enting the applicati on logic and transaction functio ns. Fabric overcom es the proble ms of permissioned blockchain such as non-determ inistic execution of concurr ent transacti ons, execution on all nodes , non-flexib le trust model, hard-coded consensus and etc. by using execute-order-v alidate architecture instead of orde r-execute ar chitectu re [5]. Fabric ‘s ledger in cludes tw o components : World State and Transaction Log. T he World State addresses the current st ate of the ledger and the Transacti on log includes the history of all transacti ons. If a transacti on changes in any value already stored on the ledger or adding new data to the ledger, this is consider ed as new state for the blockchain an d it would be kept permanen tly, and it is not possible to reverse the previous state of the blockchain [6]. C. Access Control Systems and blockchain Access control refers to any action that restricts access to a physical pla ce or logic al resour ce. Physical Access C ontrol system s have three main c omponents: access control, surveillan ce, and testing. Physical access control investig ates solutions to regulate access t o phy sical p laces and phy sical resources for companies that want to manage access control over the ir p rivate an d sensit iv e phys ical resou rces. Su ch as using door lock restriction to access the important room s. Logical access control refers to managing access control for softw are system s and data . Current access control s ystem s o ften focus o n logical access control and they store data o n a centralize d server , which would be handled b y server ad minis trators , who have full access to everything and the access control processes are executed centralize d. As a result, tampering always threat data and history of t ransactions . Even for many systems , it is not possible to detect data modifi cation or data removal from the system . Using Physical access control implementation across a variety of organizati on is getting more popular every day and multiple companies are developing cutting-edg e technologi es to handle secu re phy sical acc ess cont rol technol ogy. For example, a physical Access Control system based on the smart card is composed of three elements : smart card, door reader to check the card validation and the door or gate, which would b e unlocked wh en the card is approved. However, behind the sc enes of this hardware equipmen t , there is a complex netw ork of data, servers , and softw are to authorize users and manag e access cont rol [1 1] . We found blockchain as a n improvement for storing and manag ing software layer of physical access co ntrol . Using blockchain enables us to manag e access control distri buted and be able to access to the truste d history logs permanen tly. This trust comes from the st rong and s ecure logic be hind of the blockchain architec ture in stead of non -logical trusting centralize d system administrat ors. Store perm ission and denial access transacti ons on blockch ain provided reliable transaction logs to refer at any point in the future. In this paper, we introduce ou r noble block chain based system to implem ent physical access control. Figure 1 shows how physical acce ss control softw are managem ent interacts with blockchain to request data from blockchain and read access permission s from blockchain . For access control method we have used b oth role-based access control and rule-base d ac cess control method. We have used R ole-Base d acc ess control m ethod to regu late u sers access based on their role in the system . Also , there are som e rules in the system that d efines who has the privilege to change other users access p ermis sions b y submitting transactions. All of the transacti ons r emain in blockchain database p erman ently, and nobody can d elete a record of it. For implementing role- based access control we have used ACL module of Hyperledger composer , b y defining participan ts d efault access permiss ions. Each participant represents a different role in the system . For dynamic access control, an authorized user who acces se s to submit grantAcc essContr ol or revokeAccessC ontro l trans actions su bmit appro priate transacti on and changes related user access permissions when the trans action has been confi rm ed. III. R ELATED WORK S Medrec [ 1] was one of the init ial studies which imple ment an ac cess control system for sharing medical d ata b ased on Ethereum Blo ckchain. T he system g ives th e a uthority of sharing medical data to the patients as the real owners of d ata. Medrec uses mining re ward solutions to motivate medical stakeholders to particip ate in the syste m and verify transactions a s miners. MeDShare [7 ] is a nother blo ckchain - based framework for sharing b ig medical data a mong clo ud services to achieve data p rovenance and auditing. [8] rep resents a blo ckchain based ac cess control application which uses a b itcoin p ublic blockchain to expr ess the rights e xchanges. Sinc e it uses p ublic blockchain everybody can see who has ac cess to which reso urce. It provides auditability and security while it is co mpromising privacy. [9 ] ar e blockchain-based access co ntrol studies which consider acces s control in IoT context . T heir decentralized solution ad dresses the security a nd privac y issue related to the data pro vided by IoT devices. IV. S YSTEM I MPLEMENTATIO N We used Hyperledger Composer framew ork [10] to implem ent our sy stem on the top of th e Hyperledger Fabric. All components can b e d efined by the compose r modular structure an d then it can be packed as one com ponent and deploy on the fabric blockchain. The main pa rts of th e composer m odule are set of m odel file, an Access Contro l Languag e file, Qu ery file and a set of Jav aScript files. In the m odel module, we hav e defined the part icipants , Assets, Transactions , and Even ts. All users who use the system such as administra tor users who define the access control policies and other authenticated users who need access to physical places have been defined as a partici pant in the model file. Defining p artici pants include the partici pant unique key and its attribu tes. We conside r p hysical places as an asset in our system which access to them will be managed through transaction processin g functions or smart cont racts and acc ess c ontrol file . F or example, in our applicati on, we consider a unique string ID which refers to the input door o f physical places wh ich secured by physical access control devices. It could include any other related attribute or map to any specific participant wh ich can manag e access poli cies over it. Transactions are subm itted to change the state o f the blockchain based on their pred efined c onditions. The att ribut es Figur e 1. Use r I nterf ace inter actio n wi th bl oc kchain of the transacti ons define in the model module, and their processing functions define in th e JavaScript f ile. In o ur applicati on, we have a transaction for granting access permiss ions and w e have an other transacti on to revoke acces s from users. In addition , there is a transacti on to delegate authority to other users, then they would be able to submit the grant access transa ction t o phy sical pla ces to other use rs. We have defin ed ou r access control policies in the Access Co ntrol Language (ACL) module . Here is the list of r ules we consider for o ur applicati on. These polici es include the follow ing item s. • Particip ants with specific roles have access to which resources by def ault • Particip ants w ith specific roles can sen d transact ions • System access pe rmissions • System administrat or role a ccess p ermissions • Particip ants with specific roles access p erm issions to read hist orian r ecords Composer ACL language d efines b y five different sets, a set of Participants , a set of Resources, a s et of Conditi ons, a set of Actions, and a set of Operations. Table one explains the meanin g of each notation . In the basic model, users can access to the resources based on their role defined in the system , so our access control model is based on role -based access control model [ 13 ]. In our Com poser model file, we have define d different type of participants which reflects different roles in the organizat ion and they have access to resources by default based on their roles an d condit ions. Ur ⊆ U × r is the set of user-role assignments and rR ⊆ r × R is the set of role-res ource as signm ents. TA BLE I . NOTA TI ONS M EANI NG Not ation Mean ing P Set of Par tic ipa nt R Set of Re sour ces C Set of Co ndit ions A Set of A ctio ns (Cre ate , Re ad, Upd ate and De le te) O Set of Ope ra tions (Al low and Deny ) A user u have access to the resour ce r if and only if there is a partici pant p defined in the model file and (u,p) Ur and (p,r) rR an d condi tion c is met. For a situati on that an authorize d user wants to change the access of any user, he or she can subm it a transac tion to cha nge user access control dynam ically and this is separate d from static AC L module definiti ons. Events are the important part of the system when they use alongside system queries. we have implem ented event modu le in order to query the transaction s inform ation logs. Log entries demonstrate the resu lts of th e events hav e been fi red fro m transacti onal processing function s. In addition, they can subscri be to an external application . For example, in ou r applicati on, we consider situa tion insisting on access request and rejecting request after several consecutive eff orts. As a result, a trigg er to the external appli cati on will be fired to apply necessary safety co nsidera tion s such as trigge ring intrus ion alarms to deter un authoriz ed access . Composer Transaction Processor functi ons are the part o f JavaScri pt files an d they transl ate to fa bric chain code, so i t can be conside red as smart contracts. T heir main task is to define the logic of each transacti on and the conditions that need to meet. T he Transaction Processor Functions are automatical ly called when the respective transaction is subm itted. Figure 2 explains the access permission proc edure bas ed on ACL module Composer Identity Managemen t main tasks inclu de create a partici pant and issue an identity for that p artici pant. Composer uses the concept of Card inspiring from real-world ID cards to issue an identity to a participan t . An ID card is access card to the chain and it inclu des identi ty data, a connecti on profile, and the certificate for chain access. Connection profile is used to connect composer n etw ork t o the runtim e Fa bric. These I D cards can map to real-world p hys ical access control smart cards. Query file includes the d eclarati on of queries. Queries based o n tamper-proof data. W e can be sure we q uery the data which h as not been modifi ed, alte red or delete d. Hyperledge r Com poser provides Historian record , w hich records successf ul transac tions with details includes transacti on’s info rmation an d partici pant w ho submitted the transacti on. Figu re 3 illu strates the hist orian tr ansacti on detail s. Figure 4 represents the architectu re model of our applicati on based on Hyperledge r Composer and Hyperledg er Fabric. I t includes Model , JavaScri pt, A ccess Cont rol, an d Figur e 2. Ac cess perm iss ion proce dure base d o n ACL mo dule query . All of these Modules merge into a Business Network Archive file and then the archive file (.bna) deploys on r unti m e Hyperledge r Fabric Blockchain and afterward users can interact with the blockchain through JavaScript API and user interface applicat ion. Althoug h the perform ance is o ne o f the main obstacles of blockchain- based appli ca tion s, advancing in blockch ain platform s b y co nsidering several factors promises a bright future for this issue [13]. I n this paper, we have used Hyperledge r Caliper [ 14 ] to test our applicati on and measure perform ance metrics. Hyperle dger Caliper is a fram ework to test differen t Hyperledge r blockchains such as Fabric, Sawtooth, Iroha, and Composer and get a report includes set of perform ance indicat ors. A test module for o ur applicat ion has been create d to generate and subm it transacti ons. Three main functions of our test module comprise init(), run(), and end() based o n Caliper requirem ent. The init function handle the initializati on phase of the test. The run function generates and subm its multiple transacti ons repeatedly in an asynchronous w ay. Finally , the end fun ction fin alizes th e end of the t est. V. A PPLICATION A NALYSI S In our model file , we have defined different participants which map to d ifferent roles in the sy stem and they have a differen t level of access such as managers and employees. W e considere d asset as the phy sical places and we categorized them into different d epartm ents, so access to each departm ent would be co ntrol by a dif ferent user (the CEO of the departm ent). User or participant instances and asset instances have defined in init function. Af terward, test Transactions have been fired through run function s . The test result indicat es that our application has worked 1 00% correctly during the test phase. Tables I and II present perfo rmance metrics and resource consumption reported by Hyperledger Caliper respective ly. VI. S UMM ARY A ND F UTURE W ORKS In centralized s ystems acces s to reso urce s co ntrol by third parties such as s ystem ad ministrators who have full control on system’s d ata and actio ns, a nd as a result they always suffer from security and trust issues. T his paper is the implementation o f a real- world ap plication using blo ckchain technology to explore per missioned blockchain app lications. By exploiting H yperledger Fa bric and Hyperledger Co mposer potential we have imple mented a ta mper-proof acces s co ntrol application b ased on p ermissioned blockchain for managing access permissions o n physical place s. The system provides a comprehensi ve transactions ’ log to query and it could be accessible through au thenticated and authorized users. In addition, the transaction history of the system is trustable si nce it is pr otected from undesira ble tampering. The anal ysis result reported by Hyperledg er Caliper illustrates s ystem stability a nd scalability include 100% successful tra nsaction r ate alo ng with accepta ble performance metrics. As a future w ork, we i ntend to continue our r esearch o n access control management using blockchain technology to integrate logical and physical access co ntrol and use for mal methods to analyze the security aspect a nd eliminate exploitable bugs. Figur e 3. His toria n Tr ansa ctio n Re cor d Figur e 4. Sys tem Arc hite ctu re TA BLE II . PERF OR MANCE MET RI CS TA BLE II I . RESO URC E CON SU MPTI ON R EFERENCES [1] A. Az aria, A. Ekblaw, T. Vieira, and A. Lippman, “MedRec : Using Blockchain for M edical Data Access and Permission Management,” in 2nd International Conference on Open and Bi g Data, OBD, Vienna, Austria, Aug. 2016, p p. 25 – 30. [2] S. Nakamoto, “Bitcoin: A peer - to - pe er electronic cash syste m ,” White Paper, 2008. [3] X Li, P Ji ang, T Ch en, X Luo, Q Wen, “A Surve y on the security of blockchain sy stems, ” Future G eneration Com puter Sy stems, 2017. [4] V Bu terin, “On public and private b lockc hains”, 2 015, https://blog.ether eum.org/2015/08/0 7/on-public-and-priv ate- blockchains/ [5] M. Vukoli, “Rethinking Per missione d Blockc hains,” In ACM Workshop on Blockchain, Cryptocurrencies a nd Contracts (BCC’17),2017 , pp. 3 – 7. [6] Hyperledger Fabric Documentation, http://hyperle dger- fabric.readthedocs .io/en/rele ase/ [7] Q. Xia, E. B. Sif ah, K. O. Asamoah, J. G ao, X. D u, M. G uizani, “ MeDShare : Trust-Less Medical Data Sharing Among Cloud Service Providers via Blockchain,” IEEE Access, vol. 5, 2017, pp. 14757 – 14767. [8] D. Di, F. M aesa, P. Mori, and L. Ricci, “Blockchain Based Access Control,” IFI P International C onfe rence on Distributed Applications and Inter operable Sy stems, vol. 1 ,2017, pp. 206 – 22 0. [9] A. Ouaddah, A. A. Elkalam , and A. A. Oua hman, “FairA ccess : a new Blockchain-based access c ontrol framework for the Internet of Things,” Security and c ommu nication networks, 2017, pp. 5943 – 5964. [10] Hyperledger Compo ser, https://hyper ledger.github.io/com poser/ [11] Smart Card Aliance , “Using Smart Cards for secure physical access”, Secure T echnology Aliance, 2003, https://www .securetechall iance.org/publica tions-secure-physical- access-report/ [12] R. S. Sandhu, E. J. Coy ne, H. L. Fe instein, C. E. Yo uman, “Rol e - based Acce ss control models, ” Comp uter, 1996, vol. 29, no. 2, pp. 38 - 47 [13] S. Rouhani and R. Deter s, "Perfo rmance analysis o f ethereum transactions in priv ate blockc hain," 2017 8th I EEE Inter national Conference o n Software Engineering and Se rvice Science (ICSESS), Beijing, 2017, p p. 70-74. [14] Hy perledger Caliper, https://git hub.com/hyper ledger/caliper/
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment