A Partition-Driven Integrated Security Architecture for Cyber-Physical Systems
Emerging cyber-physical systems incorporate systems of systems that have functional interdependencies. With the increase in complexity of the cyber-physical systems, the attack surface also expands, making cyber-physical systems more vulnerable to cy…
Authors: Yahya Javed, Muhamad Felemban, Tawfeeq Shawly
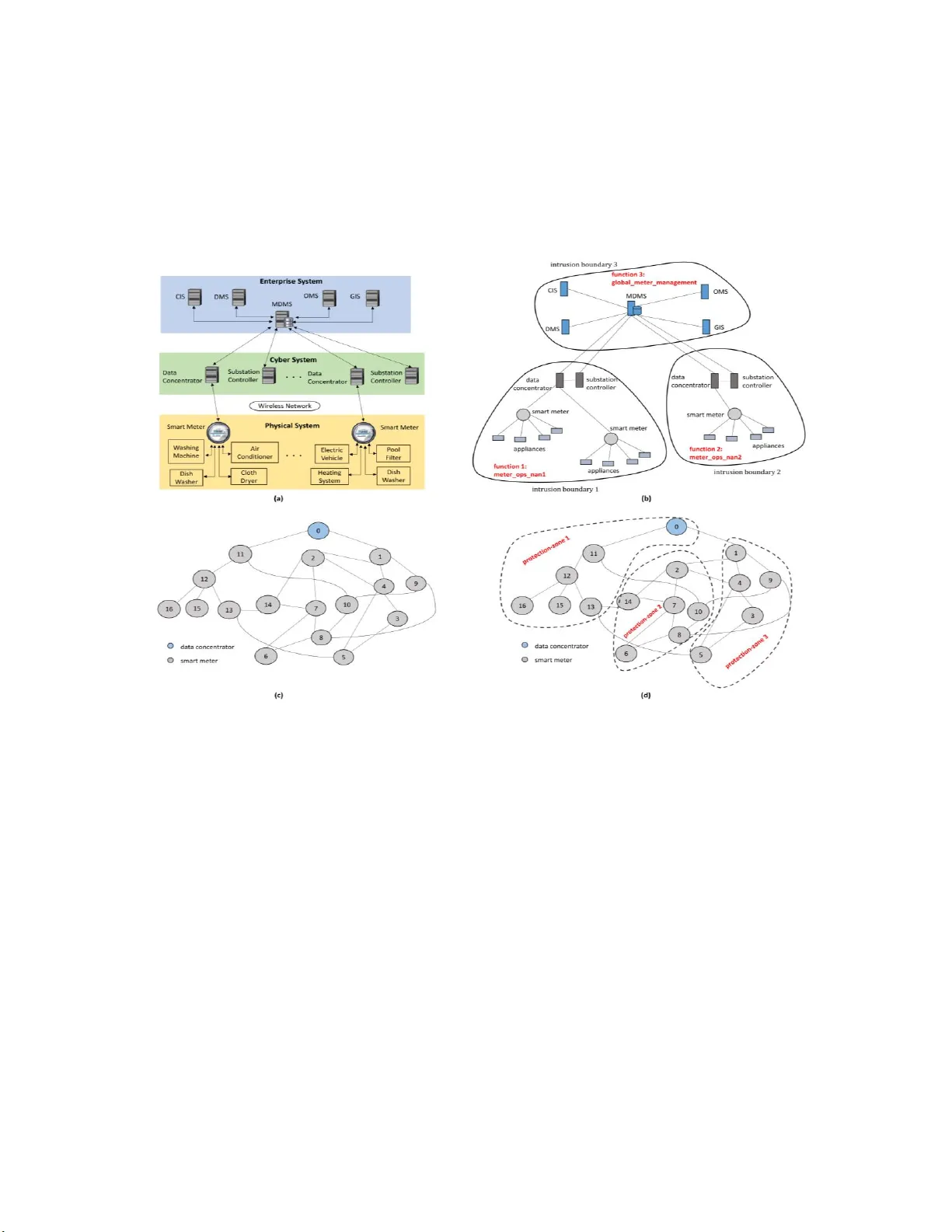
A Partition-Driv en Integrated Securi ty Architecture for Cy ber-Phy sical Systems Yahya Javed*, M uhamad Felemban* , Tawfeeq Shawly*, Jason Ko bes † and Arif Ghafoor* *School of Electrical and Computer Engineering, Purdue University, West Lafayette , IN † Northrop Grumm an Corporation, Wa shington, D.C. Emerging cyber-physical sy stems incorporate systems of systems that have functional interdepend encies. With the increase in complexit y o f th e cyb er- physical systems , the attack surface also expands, making c yber-physical systems more vulnerabl e to cyber-attacks. The functional interdependencie s exacerbate the security risk as a cyber-attack that compromise s one constituent system of a cyber-physical system can dissemin ate to others . This can result in a c ascade effect that can imp air the operability of the whol e cyber-physical system. In this article, we p resent a novel security architecture that localizes the cyber-attack in a timely manner, and simultaneously recovers the aff ected cyber -physical system functionality . We have e valuated the p erformance o f the ar chitecture for advan ced metering infrastructure- based pricing cyber-a ttacks scenario. The simulation r esults exhibit the effectiveness of the p ropo sed architecture in containing the attack in terms of system availability and its imp act on the electric load distribut ion in the power gr id . The increase in popularity of automated systems has made cy ber-ph ysica l systems (CPSs) find their application in many diverse domains, including electrical power grid, automotive systems, smarthome systems and he althca re systems. Emerging CPSs integrate heterogeneous s ystems that have functional interdependencies. These integrated heterogeneous systems effec tuate discrete functions and collaborate in an in tricate fashion to perform the overall functionality of th e CPSs. 1 Modern CPSs are co nnected to the internet and emplo y cloud-based infrastructure for their computational requirements. Moreover, the systems of a CPS sy stematically communicate with each other and the field devices of a CPS are commonl y p rovided with one or more int erfaces for maintenance purposes. 2 Now ada y s, CPSs are capable of performing multiple diverse functions as compared to the legacy s ystems. However, such capability can result in an increased s y stem complexity. From the s ystems engineering perspective , the increase in system complexit y makes it more challenging to provide service guarantees. Sim ilarly , from the security perspective, added complexit y widens the attack surface. 3 The functional interdependencies among the s y st ems of CPS further exacerbates the securit y risk. An attack that is initiated at o ne sub -sy stem of a CPS can disseminate to others. This can result in a cascade effect of compromi sing one s ystem after other and eventually impai ring the functionality of whole CPS in a short amount of time. Some CP S security frameworks mi tiga te the se curity risk by promptl y patching the system components for newl y discovered vulnerabilities, in addition to implementation of strict authentication protocols for communication with the CPS. 4 This solution based on the target hardening conce pt is provin g to be less effective as c y ber-attack incidents reported over the years indicate a continuous increase in their sophisti ca tion. Anothe r solution is based on the intrusion prevention approach, in which the sec urity framework employs an intrusion detection system (IDS) that generates al erts when it identifies an anomaly in the working of CPS components. On the other hand, intrusion preve ntion systems (IPSs), in addition to detection, can deplo y some countermeasure s, such as disconnecting the attacker’s communicatio n with the CPS , and halting the operation of affected CPS components. 5 The performance of I P Ss is tightly coupled with the I DS e fficiency. IDS is usua ll y evaluated in terms of false positive rate ( FPR), false negative rate (FNR) and detection delay time. High FPR indicates significant number of false alarms that can make the behavior of the I PS unpredictable while high FNR implies an ineffective IPS. Detection delay time is often meted with less im portance in eva luating th e performance of an I DS , but it has a significant effect on the operations performed b y the IPS. Considering a scenario in which the int ent of the attacker is to compromise as many components of th e CPS as possible. The attacker orchestrate the attack b y s y stematicall y compromising one component after the oth er. Th e average ti me taken by the attacker to compromise a component and move to compromise the next one corresponds to the attack propagation speed. On the other hand, the average time taken by the I DS to identif y if a component ha s been compromised corresponds to the detection s peed. If the attack propagation speed is more than the detection speed then the attacker can continue to compromise the CPS components while the IPS would try to catch-up unti l all of the tar ge t components are compromised. This “ catch-up ” process is evident when the strategy of the attacker is to outpace the response or defense mecha nism of the s y stem rather than evade detection. The contribution of our work is multifold. First, we present an integrated security architecture that combin es the concepts of intrusion prevention and reco ver y to mana g e cyber-attacks while maintaining high operational availability of CPS. Second, we propose a novel multi-level partitioni ng mechanism that partitions the CPS components based on their functionality and dama g e containment requirements . The partitions help to contain the damage b y localizing the c y ber-attack in the region of its inception . The re sponse mechanism of th e architecture effectively utiliz es the partitions to counte r attacks involving high attack propa gation speeds as well . Finall y , we have simulated advanced met ering infrastructure (AMI)-based pricin g c y ber-atta cks scenario, and demonstrate the performance of the p roposed architecture in terms of operational availability ( ω ), damage extent ( δ ) and average energy load (AEL) consumption. An Integ rated CPS Security A rchitec ture The proposed securit y architecture and it s interacti on with a g eneral CPS framework is depicted in Figure 1. The architec ture has four constituent s y stems : partition manager (PAM), intrusion re sponse system (IRES), intrusion recovery system (IREC) and performance monitor (PEM). The architecture utilizes the servic e of a n intrusion detection system (IDS) that generates alerts upon detect ion of a cyber-attack. The a rchitecture also uses the operational logs of CPS and a ssumes that the y a re updated in re altime with CPS component activities such as data flow between components with timestamp . We discuss the constituent sy stems of the architecture a nd their int erna l modules in detail starting with a discussion on the intrusion detection process. Intrusion De tection System Several intrusion d etection techniques corresponding to dif ferent threat models exist in literature. IDSs employ diverse methods to identify the anomalies in the operations of the systems they are designe d to protect. An IDS per forms two major operations: colle ction of data and an alysis of the data to detec t malicious activities. CPS centric I DSs collect data by monitoring component activities or b y observing CPS network traffic. The detection techniques are either signature-b ased or behavior-based. I n signature-based approach the IDS looks for malicious pattern to make detections. In behavior-b ased approach the I DS co mpares every new observation with normal sy st em be havior it ha s learnt during the data collection phase. 6 Some IDSs also provide limited I PS capabilities e.g. s nort 7 combined with firewall configuration fea ture can filter any malicious stream from a link. This technique of filtering out malicious traffic refers to as negative filtering. I t is also possible to do positive filterin g in which onl y tr affic meeting certain criteria is allowed. Fire walls are usually deployed on a central communication li nk to ensure only benign traffic flows through the li nk and it is not feasible to deploy th em on every communicat ion link of the system. For our proposed architecture, we assume that an IDS is available and works across all layers of the CPS. We assume that the IDS can report t he cyber-attack type , start time and detection time of c y ber-attack, a nd compromised components of CPS. We also assume that the firewalls can be deployed on certain communication links of the CPS. Figure 1. Proposed CPS security architec ture and its opera tions across all CPS layers. Partition Manage r PAM creates two levels of partitions for the CPS. The first level of partitioning involves demarcation of intrusion boundarie s ( I Bs). The objective of the I Bs is to contain dama g e propagation across IB s. The second level of partitioning involves the formation of protection-zones. The o bjective of p rotection-zones is that within an IB, components affected b y the attack needs to be isolated quickly so that the impact of the attack is confined to affected components only. Intrusion Bounda ry Demarcation The CPS components th at collaborate to provide a specific CPS function are included in the same IB. It is possible that a CP S component handles multiple functions while the same CPS component is shared among multip les IBs. An IB can encompass more than one functions as well. To create IBs, CPS topological structure and CPS component to functionality mappin g is used, and are assumed to be available to the architecture. Fi gure 2(a) shows advanced met ering inf rastructure (AM I) architecture and Figure 2(b) shows the division of AMI components in different IBs. The smar t meters th at are connected to the same data concentrator perform met er_ops_nan function, and form a neighborhood area network (NAN). Therefore, the y are part of the same IB. Sim ilarly , the AMI components at the enterprise system lay er such as meter data management s y stem (M DMS), consumer information system (CIS), outa ge management system (OMS), distribution management system (DMS) a nd geographic informati on s y stem (G I S) are mapp ed to global_meter_management function, and can be placed in the same I B. The idea behind IBs is that an attack inside an IB is fully contained in it by desi gn. The communication among different IBs is carried out by dedicated links or in some cases through shared components. The inter -IB communication can be ensured to be not malicious b y appl y ing a positive firewall filter policy on the inter- I B communication links or on the outgoing traffic from the shared c omponent. To minimize t he firewall deployment overhead, the number of inter-IB communication links should be minimum. To find an optimal IB configuration, an optimization problem similar to c lassical graph partitioning problem 8 can be formulated that minimizes the edge cut among IBs. Protection-zone Formation IB s can contain thous ands of CPS c omponents and an attack starting from a single component in an IB ca n potentiall y compromise all of the components in that IB due to functional dependencies. Figure 2(c) shows an example AM I topology enclosed in an I B. In order to contain the d amage within an IB , we introduce a second level of partitions known as protec tion-zones. The PAM groups CP S components of an IB in almost fixed- size protection-zones such that the chances of inter prot ection-zone damage propagation ar e minimized. The response s y stem of the architecture utilizes the protection-zone information to effectively localiz e the damage i n an IB. Th e protection-zone creation process is formulated as a sing le-objective multiple constraints optimization problem with the goal to minimize the inter protection-zone communication. The CPS components in an IB and the interconnections among them can be modeled as an unweighted non-direc tional graph , as shown in Figure 2(c). Let where is the set of vertices modeling CPS components and is the set of edges modeling the communication links between CPS components. Let be the i th subgraph, such that and . For each , let i.e. is the set of neighboring subgraphs that contain a vertex that is adjacent to whereas there exist an edge between and . The problem is to partition the graph into balanced subgraphs with minimum edge cut such that a vertex at the boundary of a subgra ph is a t most connected other subgraphs. Let i.e. i s the set of edges ex tending from one subgraph to another. The optimization problem is as follows. The objective function minimizes the number o f communication links between two different subgraphs or protection-zones. The damage propagates through the communication links betwee n CPS components, therefore minimizing the communication across protection-zones reduces the cha nces of inter protection-zone dama ge propagation. Moreover, the Constraint (2) balances the sizes of the partitions as small si zed partitions are unable to restrict the damage spread in one protection -zone and large siz ed partitions allow damage to propagate to a large number C PS components without any hindrance. Constraint (3) ensures that a CPS component in a protection-zone is at most connected to components in protection-zones. The intuition is that, if a component that is connected to components in man y different protection-z ones is attacked then damage could quickly propagate to oth er protection -zones. The parameters and are used to relax the constraints, the lower values of these pa rameters the better expected performance in terms damage containment, but usuall y i f the constraints are too tight then there might not be a feasible solut ion for a given CPS topol og ical structure. This g raph decomposition problem is similar to the classical uniform graph partitioning problem 8 and the PAM emplo y s a greedy algorithm to create protection-zones (partitions) of similar sizes. PAM maintains information about the respective member components of protection- zones and the boundary components of all protection-zones. A CPS component that has connections to components in other protection-zones is a boundary component. Figure 2(d ) shows the creation of protection-zones within an IB for AMI as an example CPS. Intrusion Response System IRES i s activated by the I DS upon detection of an intrusion. IRES generates response for the cy ber-attack by utilizing the in formation provided by the IDS, PAM and operationa l logs of CPS. The functionality of IRES is described as follows. Damage Assessment (D A). The DA module uses the protection-zone information provided by PAM to identify the protection-zones where damage has been spread. PAM shares two data structures with the DA module. The first one maps every CPS c omponent to a protection-zone and is named pz_component_list. The second data structure contains information about the boundary components of the protection-z ones and is nam ed pz_boundary_set. The IDS detects intrusions in the CPS and generates alerts that spec ifies the CPS components th at are compromised. The following pseudocode describes the damage assessment process. Input: pz_component_list, pz_boundary_set, ids_alert Output: response_set 1. for each ids_alert of a corrupted CPS component 2. use pz_component_list to find the protection-zone P to which the corrupted component belongs 3. identify the boundary components of P using pz_boundary_set 4. include the identified boundary components in response_set For each al ert received b y the DA module, response_set is computed. The components that need to be isolated from the rest of CP S are in the r esponse_set. I t is possible that b y the time I DS detects an i ntrusion the damage has alre ady spread to other pr otection-zones. In that case, the IDS keeps on generating alerts as more CPS c omponents get compromised and the DA module kee ps generating response_sets and provide them to the response manager module until the damage is contained. Figure 2. Partitioning process for AMI. ( a) Multi-layered system of systems AMI architecture. (b) Demarcation of IB s on a g iven AMI topol ogy. (c) A MI topolo gical structure in an IB. (d) P artitioning of the AMI topological structu re to form protection- zones. Response Manager. Response manager coordinates the operations of DA and int erfaces with the CPS control s y stem. Response manager starts its ope rations the mom ent it receives an alert from IDS. First, the response mana ger halts the operation of the compromised components. Subseque ntly, it sends instructions t o CPS control s y stem to disconnect the CPS components identified in response_set. The goal here is to stop inter protection-z one damage propagation. This action mi g ht temporarily halt certain CPS func tions, resulting in short- liv ed unavailability of those functions in ex change for the benefit of damage containment. Response manager continues this process until there are no more alerts from the IDS, indicating the damage has been successfully contained. Su bsequently, th e response manager activates I REC to start the recovery p roce ss. Additionally, response manager sends IRES operational information to PEM. Intrusion Recov ery System IREC recovers the s y st em in an automated fashi on by det ermining the exact extent of damage, and performin g corrective actions accordingl y . The architecture responds first and recovers a fterwards, because the re covery is a time consuming pro cess while response can be deployed quickly afte r the detection of the cyber-attack. We explain the functions of several IREC modules briefly. Recovery A n alysis (R A). RA modul e assesses the extent of damage by precisel y identifying the c ompromised components of CPS. For an IDS alert, the re covery process is initiated after completion of the response process. RA module ana l y z es op erational l ogs of the CPS that contains detailed information about the activities of CPS components. The activity of interest is usuall y the d ata flow information between CPS components. RA module uses th e IDS alert information to find the start time o f the cyber-attack (T s ) and the compromised CPS component. RA mo dule then starts anal y zin g th e CPS operational log to identify all of the components to which the compromised component communicated an d includes them in a data structure known as repair_se t. The RA process is described in the following pseudocode. Input: ids_alert, op_log Output: repair_set 1. for each ids_alert of corrupted CPS component 2. include compromised component in repair_set 3. for each new entry s in repair_set 4. identify components r in op_log that communicated with s after T s 5. include component c r in repair_set, if c repair_set It can be observed in the pseudocode that the RA module ge nerates the repair_set b y building causality relations hip between components using inter-component communication information. Recovery Protocol Know ledgebase (R PK). Once th e RA module identifies the compromised components, the RPK m odule dete rmines the recovery protocol to re cover them. R PK module maintains a knowledgebase that provides procedures that needs to be followed to recover the compromised CPS components. For example, if the data management serve r is compromised then the recove ry techniques mentioned in 9 can be employ ed. Similarly, if a field device is compromised then a r edundant device could be activated, if av ailable. Otherwise, if the device was providi ng essential data to a controller then instructions can be given to the controller to use simulated data till the device is restored manually. Recovery Manager. Similar to response manager, t he recovery manager interfaces wit h CPS control system. Recovery manager directs re covery instructions to the CPS controllers to take corrective a ctions based on the informatio n provided b y the RPK module, for a particular attack. Notice that recover y manager might not b e able to completely recover the CPS functionalit y in an automated manner due lim itations of the CP S infrastructure or unavailability of appropriate recovery protocol in RPK for a particular component. I n that case, the recovery manager onl y disables the corrupted component, and generates an alert to recover the s y stem manually. Once the rec overy process of the s ystem is complete, the normal communication of all the CPS components is restore d. Recove ry manager also records the activities of IREC and forwards this information to PEM. Performance Mon itor PEM provides an overvi ew of response and recovery s y stem performance by collectin g statistics from I RES and IREC, and calculating diff ere nt performance metrics. The performance monitor has two modules that we discuss briefly. Statistics Co llection. Information from dif ferent s y stems of the pro posed securit y architecture is collected and an aly zed by statistics collection module. The received information can be in the form of extensive log files, therefore this mod ule extracts useful data that is used by metrics calculation module. Metrics Calculation. We introduce ω as a m easure of servicea ble CPS functions, a nd derive δ from ω that reflects the impairment of CPS fun ctions caused b y an attack. The metrics are defined as follows. Op erational av ailability ( ω ): the available CPS functionalit y in terms of percentage of components unaffected in an attack for a CPS function. Damage extent ( δ ): the compromised CPS functiona lity in terms of percentage of components damaged in an attack for a CPS function. Note that these metrics co ncern a pa rticular CPS function . The overall CPS availabilit y a nd damage extent can b e fo und out b y averaging the metric for all C PS functions. Also note that we c an compute one metric from the other by subtracting the known metric value fr om 100. Simulations and Evaluation We have used AM I as the target CPS application to evaluate the performance of the proposed securit y arc hitectu re . We first discuss the threat model c oncerning AM I followed by a discussion on the simulation tool and implementation of proposed architecture. Finally, w e present our experimental setup and compare the performance of the proposed architecture with the commonly adapted intrusion prevention approach. Threat Mode l and Implementation We have employed the electricity pricing manipulation cyber-attacks on AMI 10 as the attack scenario in our experiments. The attacker tries to exploit access vulnerabilities of smart meters through a direct ph y sical link or through the AM I. Th e o bjective of the attacker in electricit y pric ing manipulation cyber-attack is to disrupt the distribution system of the power grid such t hat electric it y supply to the target ed re gions is suspended. The attacker maliciously ga ins access to a smart meter and usuall y injects a mal ware that could be propagated through t he network. In AMI, smart meters are connect ed to the data concentrator through a mesh network that forms a ne ighborhood ar ea netwo rk (NAN). The target of the malware is the guideline price information that is used by the smart controller to manage the usage o f differe nt appliances to reduce the electricity bill. The smar t controller when observes a lower price at a certain time of the day , schedules the usage of many appliances, resulting in the increase in energy consumption of that particular consumer. The consumers in a NA N are usu ally connected to the same b us used by the distribution s y stem o f the power grid. If the attacker suc ceeds to manipulate the pricin g information in a large nu mber of smart meters one after the other, the transmission line that delivers powe r to the bus ca n trip. This can cause the transmission system to reallocate the power distribution to other transmission lines connecting the bus, which i n turn can trip due to excessive load. This results in a cascading failure and the community conne cted to the bus can be out of power. This disruption in the distribution s y stem generally do esn’t stay within a communit y as from the generation system to the consumers, power flows through transmission lines linked to several buses as a result a total blackout can occur. In ord er to simulate thi s scenario we have used SecAMI 11 , an opensource simulator developed to stud y the impact of c y ber -attacks on AMI. SecAMI can be used to pe rform two operations: first an AMI topolog y involving smart meters and d ata concentrators can be created as an u ndirected graph, second an attack on the created top ology can be simulated that compromises one node (smart meter) after the other according to three simulation parameters – compromise time of a node (c t), hop time from one node to another (h t), and detection time of a compromised node (d t ). These parameters determi ne the attack propagation spe ed with respect to the detection sp eed in the simulation. W e have modified the SecAMI to imple ment the protection-zone aware response mechanism of th e architecture. To create protection-zones (partitions) for a given AMI topology (undirected graph), w e have built a partitioning m odule on top of SecAMI that takes a parameter k and a topology graph as inputs to create k protection-z ones of equal siz es. The partitioning module maintains information about the members of a protection-z one and boundary components of the created protection-zones. SecAMI uses a general response mechanism in which as a node is detec ted to be compromised, it is disconnected fr om the rest of the network. The proposed security architect ure’s response mechanism uses the protection - zone information to identify the protection-zones whose membe r nodes are detected to be compromised. Subsequentl y , it immediatel y halt s the communication of the boundar y nodes of the under attack protection-zones from the rest of the AMI topology. Experimentat ion and Res ults To evaluate the pe rformance of the proposed securit y architecture in t erms of damage containment, we have c onducted several experi ments. The variable par ameters in the experiments are: the size of the topology in ter ms of number of nodes (n), t he c ompromise to detection time ratio ( σ = ct /d t ) that specifies the attack propagation spe ed with respect to detection speed, and the partitioning parameter (k) that specifies the number of protection-zones for a given topolog y . The performance of the proposed architec ture is measured in terms of three metrics. The first two are aforementioned g eneral CPS damage containment evaluation metrics i.e. ω and δ . The third metric is AE L that is specific to AMI and power grid anal y sis . I n our experiments, we c onsider a ttacks on function 1: meter_ops_nan1 i.e. in intrusion boundary 1 in Figure 2(b) . Since onl y one function is considered, ω is the pe rcentage of components unaffected in the attack a nd δ is the percentage of components compromised in the atta ck. F or AEL we assume that each smart meter in the topol ogy is connected to a medium -sized household with standard appliances like washing machine, dish washe r etc. The smart controller o f each consume r schedules the ene rgy consumption for next 24h based on the guideline pricing inf ormation. The quadratic pricing model prese nted in 12 is e mployed to for m the norma l guideline price and energy consumption for a general household. The value of ω for different values of n with σ = 3 and k = 0, 8 is s hown in Figure 3(a) . It can be seen that the performance of the proposed partition -driven architecture (k=8) is considerably hi ghe r as compared to the non-partitioned system (k=0) e. g. at n=200, the value of ω is 84.5 for the parti ti oned system while its value is 7.4 for the non-partitioned system. Moreover, note that the value of ω increases as the value of n increases until 200 nodes after that it decreases. This is due to the fact that there ex ists an optimal protection- zone size that ma ximizes the benefit. If th e size of the p rotection-zone is too small, it is more likely that damage will propagate to other protection-zones. If the size is too big then many member nodes of the protection-zone can get corrupted without any hindrance. Figure 3(b) shows the val ues of δ for 200 node topolog y fo r different σ and k values. Notice that even when the attack propagation speed is hi gh i.e. lower v alues of σ , the pa rtitioned system (k>0) c an effectively contain damage relative to non-partitioned system (k=0). For higher σ v alues, there is ample time for the response mechanism to react and hence t he performance of the partition-driven architecture is significantly better. Figure 3(c) shows the manipulated guideline price va lues in a smart meter 10 . This change in g uideline price increases the energ y consumption of a consumer b y 1.3 kWh on average in our simulations . Figure 3(d) shows the increase in overall demand by all the customers corresponding to 200 node topology for non-partitioned (k=0) a nd partitioned systems (k=8). It can be noted that the partition-driven architecture efficie ntl y handles the attac k and correspondingl y the load on the transmission lines connected to the bus connecting 200 consum ers is not drastically increased in comparison to the non-partitioned sy stem. Figure 3. Proposed p artition-driven securit y architecture p erformance . ( a) Operational availability over topology size for σ = 3. (b) Damage extent over numbe r of protection- zones for n = 200. (c) G uideline electricity price in pricing manipulation cyber-attack. (d) Overall AEL consumption of a community for n = 200, σ = 3. The partition-driven securit y architecture presented in this article proposes a comprehensive s ecurity s olution for CPSs. The proposed arc hitecture is able to contain the damage propagation and recover the CPS automatically. However, there are several challenges that must be addre ssed to develop a robust sec urit y solution for CPSs . These include dealing with the performance of IDS and evaluation of the proposed securit y architecture for more complex attacks. References 1. I. Eusgeld, C. Nan, and S. Dietz, “Sytem - of -Systems Approach f or Interdependent Critical In f rastructures, ” Reliability Engineering and System Safety , vol. 96, no. 6, 2011, pp. 679-686. 2. “Framwork for Cyber -physcial Systems Releas e 1. 0”, NIST Cyber-physical systems Public Working Group, May 2016; pages.nist.gov/cpspwg. 3. M. Biro, A. Mashkoor, J. S am eti nger, and R. Seker, “Software Safet y and Security Risk Mitigation in Cyber - physical Systems,” IEEE Software , vol. 35, no. 1, 2017, pp. 24-29. 4. A. Humayed, J. Lin, F. Li, and B. Luo, “Cyber -Physical Systems Securit y —A Su rvey ,” IEEE Internet of Things Journal , vol. 4, no. 6, 2017, pp. 1802-1831. 5. S. Zonouz, H. Khurana, W. Sanders, and T. Yardley, “RRE: A Game - Theoretic Intrusio n Response and Recovery Engine,” IEEE Transactions on Parallel and Distributed Systems , vol. 25, no. 2, 2014, pp. 395-406. 6. R. Mitchell, and I. Chen, “A Survey of Intrusion Detection Techniques for Cyber -Physical Systems ,” ACM Computing Surveys , vol. 46, no. 55, 2014. 7. “Snort – network intrusion detection system,”; https:// www.snort.org. 8. B. Kernighan, a nd S. Lin, “An Eff icient Heuristic Pro cedure for Partitioning Graphs ,” T he Bell System Technical Journal , vol. 49, no. 2, 1970, pp. 291- 30 7. 9. P. Liu, “ Architectures for intrusion to lerant database systems, ” P roc. 18 th Annual Computer Security Applications Conference, 2002. 10. Y. Liu, S. Hu, and A. Zomaya, “The Hierarchical Smart Ho m e Cyberattack Detection Con sidering Power Overloading an d Frequency Distu rbance, ” IEEE Transactions on Industrial I nformatics, vol. 12, no. 5, 2016, pp. 1973-1983. 11. T. S haw ly, J. Liu, N. Burow, and S. Bagchi, “A Risk Assessment Tool f or Advanced Metering Inf rastructures,” Proc. 2014 IEEE Conference on Sm art Grid Communications , 2014. 12. L. Liu, Y. Liu, L . Wang, A. Zam aya, and S. Hu, “Econom ical and Balanced Energy Usage in the Sma rt Home Infrastructure: A Tutorial and New Re sults, ” IEEE Transactions on Emerging Topics i n Com puting , vol. 3, no. 4, 2015, pp. 556-570.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment