On Adversary Robust Consensus protocols through joint-agent interactions
A generalized family of Adversary Robust Consensus protocols is proposed and analyzed. These are distributed algorithms for multi-agents systems seeking to agree on a common value of a shared variable, even in the presence of faulty or malicious agen…
Authors: David Angeli, Sabato Manfredi
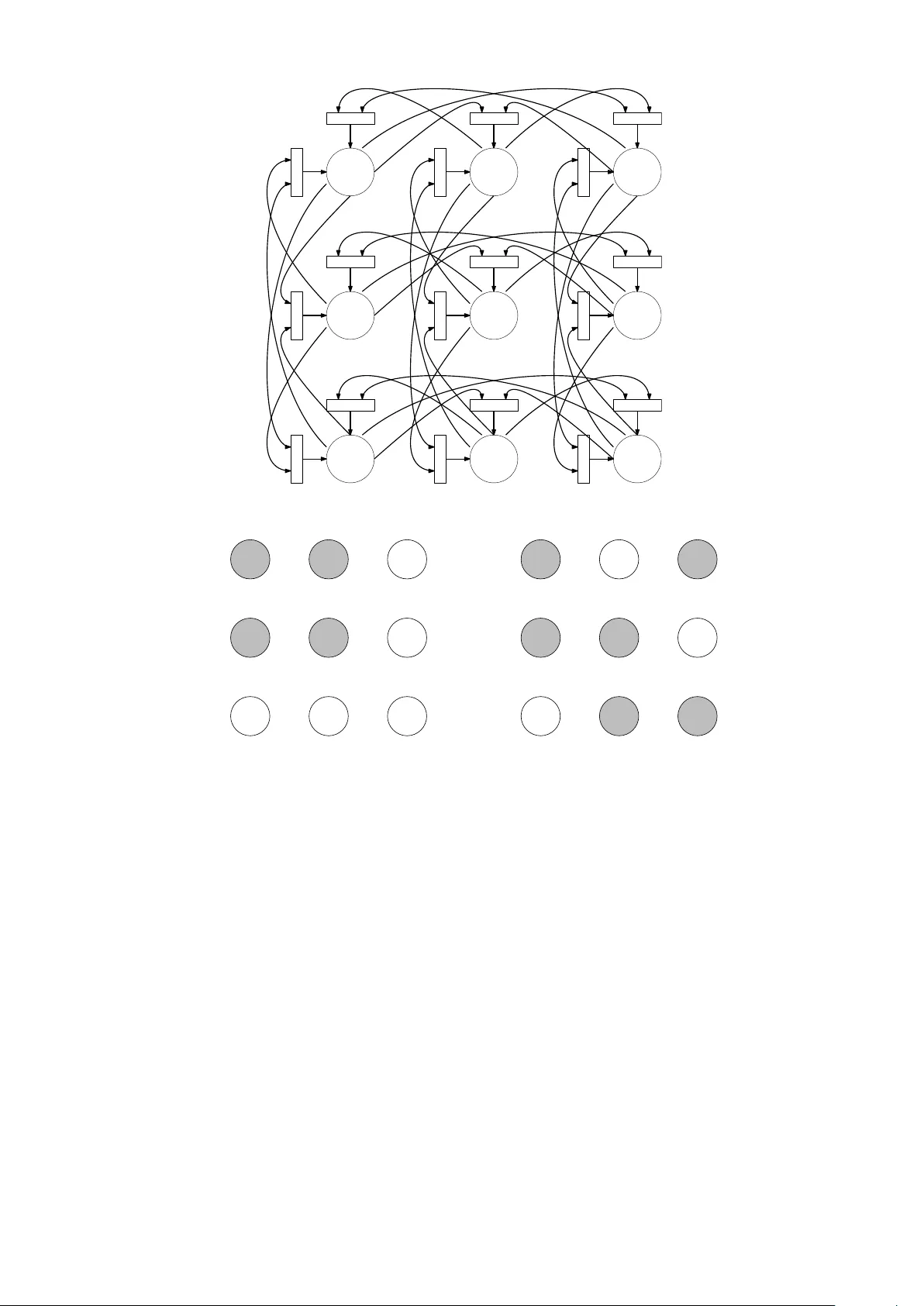
On Adv ersary Robust Consensus proto cols through join t-agen t in teractions Da vid Angeli and Sabato Manfredi Decem b er 20, 2024 Abstract A generalized family of Adversary Robust Consensus proto cols is proposed and analyzed. These are distributed algorithms for m ulti-agents systems seeking to agree on a common v alue of a shared v ariable, ev en in the presence of faulty or malicious agents whic h are up dating their lo cal state according to the proto col rules. In particular, we adopt monotone joint-agen t interactions, a very general mechanism for pro cessing lo cally a v ailable information and allowing cross-comparisons b etw een state-v alues of multiple agen ts sim ultaneously . The salien t features of the prop osed class of algorithms are abstracted as a Petri Net and con vergence criteria for the resulting time evolutions form ulated b y employing structural inv arian ts of the net. 1 In tro duction and motiv ations Algorithms for consensus w ere introduced in [17] a few decades ago, in the con text of distributed optimization, a topic whic h remains of great interest still to da y , [18]. The role pla yed by propagation of information in achieving consensus among interacting agents, was first high- ligh ted in the seminal paper [6]. Therein, authors form ulated tight and explicit graph-theoretical requiremen ts for asymptotic consensus in time-v arying linear up date proto cols, by abstracting the netw ork of agents’ in terac- tions and its underlying dynamics as a graph. This sparked a considerable interest of the scientific communit y in adv ancing and applying consensus proto cols for multi-agen t systems (see i.e. [3, 4, 5] and references therein). Subsequen t developmen ts in the theory of nonlinear consensus proto cols ha ve formalized and clarified the role of information spread along the graph of agents’ in teraction for more general situations, including second and higher order agents dynamics, or agents’ states evolving on manifolds [21] or nonlinear interactions [10, 11]. More recently , graph theoretical criteria hav e been similarly dev elop ed to encompass asymmetric confidence, as in the case of unilateral interactions [12], or join t-agent interactions, [1]. The latter, in particular, account for situations where individual agents impose “filtering thresholds” up on neigh b ours’ influences by cross-v alidating their opinions through mutual comparisons that only allow for con- sisten t infuences (either from ab o ve or b elo w) of tw o or more neighbouring agen ts to b e enacted up on. In this regard, unlik e the ma jority of existing consensus proto cols that implicitly assume ‘additive’ dynamics and exhibit v ariation rates as a disjunctive com bination (sum) of neighbors influences, joint-agen t interactions allo w the form ulation of conjunctiv e influences, and, respectively , of their additiv e com bination. It is worth stressing that complex contemporary so cial and engineering systems often need to deal with selfish or malicious users, no de faults and attacks ([22]- [26]). In this resp ect the ev aluation of individual and group reputation pla y a fo cal role for the safety of such systems. In the last y ears differen t (centralised and distributed) algorithms hav e b een proposed to deal with online reputation estimation of b oth individual ([27]- [32]) and group (clustering all users according to their rating similarities - [33, 34]) to pro viding incentiv es to users acting responsibly and coop eratively . Within this line of inv estigation, the problem of Adversary Robust Consensus Proto cols (ARC-P) w as for- m ulated in [7], follo wing earlier seminal results in [35]. Therein, Leblanc and cow ork ers prop ose and analyze a discrete time proto col which allows n co operating agents to conv erge to wards a consensus state, within a complete all-to-all net work, ev en when a subset of agents (of cardinality up to b n/ 2 c ) is malicious or faulty , namely it evolv es in a completely arbitrary w ay , with the sole constraint of broadcasting its own state to all remaining agents. The prop osed proto col simply orders state v alues in ascending (or descending order) and remo ves F top and low est v alues from the ordered list, where F is an apriori fixed b ound to the num b er of malicious agen ts. Then, the av erage among the remaining v alues is computed and a standard linear consensus up date equation is applied. 1 Subsequen t analysis has b een dev oted in [9] to the imp ortan t topic of relaxing the all-to-all topology require- men t and inv estigating sufficient conditions for Adversary Robust Consensus on the basis of lo cal information only , or in the presence of so called Byzantine agents [8], who ma y , either inten tionally or due to faulty con- ditions, communicate different state v alues to different neigh b ours. A related line of in vestigation assumes the presence of trusted no des, [2]. The interconnection top ology is interpreted, in such con text, as a sp ecific type of switc hing (time-v arying) linear consensus, arising through the application of the so called sorting function, its comp osition with the r e ducing function (resp onsible for discarding highest and low est v alues) and finally by a veraging the entries of the v ector obtained. It turns out, ho wev er, that similar types of agents interactions can also b e recast within the framew ork of join t-agent interactions. The formalism of joint-agen t interactions is, in this respect, even more flexible and ma y , for instance, allo w to partition neighbours of every agen t in several subgroups, to b e suitably sorte d, r e duc e d and aver age d while adding (p ossibly with differen t weigh ts) the influences resulting from distinct subgroups as a final step. This t yp e of rules for processing lo cal information results in consensus proto cols which allow different levels of trust attributed to different set of neigh b ors and, generally sp eaking, break the simmetry implicit in the use of a single sorting and reducing function. The extended class of intrinsically nonlinear consensus proto cols afforded by the use of joint-agen t inter- actions can b e conv eniently describ ed and characterized, from a top ological p oin t of view, as bip artite gr aphs , and more specifically P etri Nets. It turns out that structural notions, developed in the con text of Petri Nets to ascertain their liveness as Discrete Even t Systems, pla y a crucial role in characterizing the abilit y of a net work of agen ts to reac h consensus regardless of initial conditions [1]. The sp ecific details of the conditions needed for this to happ en will b e illustrated in a subsequen t Section. Nev ertheless, it is in tuitiv e that if, on one hand, application of conjunctiv e filtering conditions among neigh b our- ing agents limits the spread of information across the netw ork (and therefore, if not done carefully ma y preven t consensus from happ ening at all), on the other, it only allows “trustw orth y” information to b e propagated, and therefore may result (if carefully deploy ed) in Adv ersary Robust Consensus proto cols. In this pap er we address the issue of when a netw ork of agents, with arbitrary (and p ossibly asymmetric) interconnection top ology (al- lo wing for instance differen tiated trust levels among neigh b o ors) exhibits the ability to reac h consensus despite a subset of its agen ts b eing either faulty or malicious , viz. able to influence other no des according to their individual state-v alue but, in fact, upgrading their p osition in a completely arbitrary fashion. Just to illustrate the p otential of the approac h, w e presen t below simulations referring to an all-to-all net work of 5 agents, inv olving linear interactions, or a similar netw ork entailing joint-agen t interactions. Our theory allo ws to prov e that, in the latter net work, robustness can b e achiev ed allowing an y set of 2 out of 5 agen ts to b e malicious or faulty , and still guaran teeing the remaining health y agen ts will retain the ability to reac h exact consensus. In particular, w e simulate the following linear netw ork: ˙ x i = X j 6 = i a ij ( x j − x i ) , i, j ∈ { 1 . . . 5 } , (1) for some a ij > 0 and compare it with the following nonlinear all to all net work: ˙ x i = X J ⊂{ 1 ... 5 }\{ i } : | J | =3 f J → i ( x ) (2) where the function f J → i : R n → R is defined below: f J → i ( x ) = max j ∈ J min { x j − x i , 0 } + min j ∈ J max { x j − x i , 0 } . W e pic k the initial condition [35 , 10 , 5 , 15 , 20] 0 and run the tw o consensus proto cols assuming that agents 4 and 5 are fault y and follo w the apriori fixed time evolutions: x 4 ( t ) = 15 + cos(3 t ) − 1 9 + t sin(3 t ) 3 + t 3 150 x 5 ( t ) = 20 + sin(2 t ) 4 + t 2 sin( t ) 2 − 1 2 . These agents effectively act as exogenous disturbance inputs for the remaining 3 agents, and, from the practical p oin t of view, may b e regarded as faulty agen ts or malicious agents trying to disrupt the consensus. In the 2 Figure 1: Linear consensus protocol sub ject to faulty agents 4 and 5 case of equation (1), as it is exp ected due to linearity and addivity of in teractions, the exogenous disturbances x 4 and x 5 are able to spread their influence to the remaining agents and effectively preven t the remaining agen ts to asymptotically reach consensus (see Fig. 1). In the case of equation (2), instead, nonlinear joint-agen t in teractions allo w the three“healthy” agen ts, 1 , 2 , 3 to asymptotically reach agreement within the con vex-h ull of their initial v alues, regardless of x 4 and x 5 , (see Fig. 2). In other words, while the faulty agents ma y , to a certain exten t, affect the final consensus v alue reac hed, they are unable to disrupt it. 2 Problem form ulation The aim of this note is to derive necessary and sufficien t conditions to c haracterize when net works of agents implemen ting joint-agen t interactions may b e able to achiev e r obust consensus in the presence of p ossibly malicious or faulty agents. In particular, w e study netw orks describ ed by the following class of nonlinear finite-dimensional differen tial equations: ˙ x = f ( x ) (3) where x ∈ R n is the state vector, and f : R n → R n is a Lipschitz continous function, describing the up date la ws of each agent as a function of its o wn and neighbours’ state v alues. F or conv enience we ask that f j b e monotonically non-decreasing with resp ect to all x i ( i 6 = j ) so that the resulting flo w is monotone with resp ect to initial conditions, once the standard order induced by the p ositive orthan t is adopted. This assumption, while not essen tial, can to a certain exten t simplify the analysis and the definition of in teraction among agen ts. Man y authors, in recent years, hav e elab orated conditions under which solutions of (3) asymptotically conv erge to wards equilibriums of the follo wing form: lim t → + ∞ ϕ ( t, x 0 ) = ¯ x 1 (4) for some ¯ x ∈ R , where 1 is the v ector of all ones in R n . When this o ccurs for all solutions, and regardless of initial conditions, w e sa y that system (3) achiev es glob al asymptotic c onsensus . In this note, how ever, w e consider a more general situation in which the state vector x is partitioned in to tw o subv ectors, x H and x F , asso ciated to he althy and faulty agents resp ectiv ely . Accordingly , w e denote f ( x ) = [ f H ( x ) 0 , f F ( x ) 0 ] 0 and wish to characterize under what assumptions solutions of ˙ x H = f H ( x H , x F ) (5) asymptotically con verge to equilibria of the t yp e: lim t → + ∞ x H ( t ) = ¯ x 1 H 3 Figure 2: Joint-Agen t consensus proto col sub ject to faulty agen ts 4 and 5 for all initial conditions x H (0) and all exogenous input signals x F ( · ). A formal definition follo ws. Definition 1 We say that network (3) achieves r obust c onsensus in the fac e of faults in F ⊂ N , if, p artitioning the state ve ctor ac c or ding to F and H := N \ F yields: lim t → + ∞ ϕ H ( t, x H (0) , x F ( · )) = ¯ x 1 H for al l x H (0) , and al l uniformly b ounde d exo genous input x F ( · ) , (wher e ϕ H ( t, x H (0) , x F ( · )) denotes the solution of (5) at time t fr om initial c ondition x H (0) and input x F ( · ) ). In practice, for a giv en net, we will b e in terested in considering sev eral p ossible com binations of fault y agen ts (corresp onding to sev eral c hoices of F ) and, for each one of them, v erify conditions for asymptotic conv ergence to wards consensus of the remaining he althy agents H . In order to characterize the flow of information needed for achieving suc h kind of b ehaviour, w e recall the notion of joint agent inter action , as proposed in [1]. Definition 2 We say that a gr oup of agents I ⊂ N jointly influenc es agent j ∈ N \ I if for al l c omp act intervals K ⊂ R ther e exists a p ositive definite function ρ , such that, for al l x I , x j ∈ K it holds: sign ( x I − x j ) f j ( x j 1 + ( x I − x j ) e I ) ≥ ρ ( | x I − x j | ) . (6) We denote this by the fol lowing shorthand notation: I → j . Notice that influence from I to j , denoted as I → j , is monotone (in its first argumen t I ) with resp ect to set-inclusion. In particular, if j ∈ N \ ˜ I we hav e: I → j and I ⊂ ˜ I ⇒ ˜ I → j. F or this reason, it is normally enough to consider minimal influences alone. W e say that I influences j and that this influence is minimal if there is no ˜ I ( I such that ˜ I → j . 3 Relev an t P etri Net bac kground Our goal is to derive c haracterizations of a graph theoretical nature regarding the ability of netw orks with join t-agent in teractions to exhibit robust consensus, in the face of faults or malicious attacks. W e adopt, to this end, the formalism introduced in [1]. In particular, w e represent multiagen t net works as P etri Nets. These 4 A 1 A 2 A 3 A 1 A 2 A 3 A 4 A 5 Figure 3: Petri Nets asso ciated to netw ork of in teractions (7) and (8) are a type of bipartite graph, used to mo del Discrete Even t Systems, and can b e conv eniently adopted in the presen t study . In fact, a rich literature on structural in v ariants for P etri Nets already exists, including softw are libraries to compute them as well as complexity analysis of the a v ailable algorithms. An (ordinary) Petri Net is a quadruple { P , T , E I , E O } , where P and T are finite sets (with P ∩ T = ∅ ) re- ferred to as plac es and tr ansitions , resp ectively . These are nodes of a directed bipartite graph. In fact, directed edges are of t wo types: E I ⊂ T × P connecting transitions to places and E O ⊂ P × T connecting places to transitions. In our context places represent agents while transitions stand for interactions among them. More closely , to eac h agen t i ∈ N there exists a unique asso ciated place p i ∈ P . F urthermore, if agen ts in J ⊂ N jointly influence agen t i , this is denoted as J → i and, provided this in teraction is minimal, it is represented graphically b y a single transition t ∈ T , with edges ( p j , t ) ∈ E O for all j ∈ J and a single edge ( t, p i ) in E I . Notice that ev ery transition can b e assumed to only afford exactly one outgoing edge, unlike in general Petri Nets. As an example, w e sho w in Fig. 3 the graphical represen tation of the P etri Nets associated to the list of interactions { 1 } → 2 , { 1 , 2 } → 3 , (7) and, next to it, for a kind of ring top ology with 5 agents and the follo wing list of minimal join t agen t in teractions: { 1 , 2 } → 3 , { 2 , 3 } → 4 , { 3 , 4 } → 5 , { 4 , 5 } → 1 , { 5 , 1 } → 2 . (8) The next concepts will b e crucial in characterizing, from the top ological p oin t of view, netw orks that guarantee asymptotic con vergence tow ards consensus. The set of input tr ansitions for a place p , is denoted as I ( p ) = { t ∈ T : ( t, p ) ∈ E I } , and, similarly for a set of places S ⊂ P , its input transitions are: I ( S ) = { t ∈ T : ∃ p ∈ S : ( t, p ) ∈ E I } . Simmetrically , output transitions are denoted as: O ( S ) = { t ∈ T : ∃ p ∈ S : ( p, t ) ∈ E O } . Definition 3 A non-empty set of plac es S ⊂ P is c al le d a siphon if I ( S ) ⊂ O ( S ) . A siphon is minimal if no pr op er subset is also a siphon. Informally , in a group of agents that corresp ond to a siphon, any influence needs to come (at least in part) from within the group. In [1], a c haracterization of the ability of agents to asymptotically conv erge tow ards consensus (regardless of their initial conditions) is provided. This feature, called structur al c onsensuability , is sho wn to b e equiv alent to the requirement that an y pair of siphons in the asso ciated Petri Net ha ve non-empty in tersection. T o address robustness questions, within the same set-up of joint agen t interactions, an externsion of the concept of siphon is needed. The follo wing is, to the b est of our knowledge, an original definition: Definition 4 A non-empty set of plac es S ⊂ P is an F -c ontr ol le d siphon, if: I ( S ) ⊂ O ( S ) ∪ O ( F ) . 5 Notice that Definition 4 b oils do wn to the standard notion of siphon for F = ∅ . Union of F -controlled siphons is again an F -con trolled siphon and, in particular, if a set is an F 1 -con trolled siphon it is also a n F 2 -con trolled siphon for all F 2 ⊇ F 1 . W e call the set F the switch of siphon S . Informally , this terminology is adopted as malicious agents in F may prev ent health y agents in S from increasing (or decreasing) their own state v alues. This is indeed ac hiev able by malicious agen ts simply broadcasting v alues which are either b elo w the minim um or, respectively , ab o ve the maximum of all v alues within the siphon. The follo wing notions are appropriate to characterize o ccurrence of robust consensus. Definition 5 We say that a Petri Net fulfil ls r obust c onsensuability with r esp e ct to faults in F ⊂ N if H := N \ F is a siphon and for al l p airs of c ontr ol le d siphons S 1 , S 2 and asso ciate d switches F 1 , F 2 ⊂ F , we have the fol lowing: S 1 ∩ S 2 = ∅ ⇒ F 1 ∩ F 2 6 = ∅ . (9) It is worth p oin ting out that robust consensuabilit y , when F = ∅ , boils do wn to structur al consensuabilit y as defined in [1]. Also, a direct comparison with previously existing conditions for consensuability in netw orks where all influences are single-agen t influences is not p ossible, as the condition w ould nev er be fulfilled. It is in fact use of joint-agen t in teractions and cross v alidations that make adversary robust consensus achiev able. On the other hand, we b elieve that our conditions boil down to those prop osed in [9] when only interactions obtained through a sorting and reducing function are allow ed. 4 Main result and pro ofs In the following Section we state the main result and clarify the steps of its pro of. T o this end, in order to allo w dynamical prop erties of a m ultiagent system to b e derived on the basis of structural conditions fulfilled b y the associated P etri Net, it is important to establish a closer link betw een the considered equations and the asso ciated Petri Net. F or any transition t ∈ T , denote by: I ( t ) := { p ∈ P : ( p, t ) ∈ E O } and by j ( t ) the unique place such that ( t, j ( t )) b elongs to E I . In particular, for a given P etri Net { P , T , E I , E O } w e consider non-decreasing lo cally Lipsc hitz functions F i : R | I ( p i ) | → R , with F i (0 , 0 , . . . , 0) = 0, and such that F i is strictly increasing in each of its arguments in 0. These are emplo yed to define netw orks of equations: ˙ x i = F i ( f I ( t 1 ) → i ( x ) , f I ( t 2 ) → i ( x ) , . . . , f I ( t | O ( p i ) | ) → i ( x )) , O ( p i ) = { t 1 , . . . t | O ( p i ) | } . (10) A typical example arises when F i ( f ) = P k α k f k , for some choice of co efficients α k > 0. Equation (10) is, ho wev er, more general and allows non-additive agents’ infuences. As an example of a non-additive function F i , one ma y consider for instance the map F i ( f ) = min k ∈{ 1 ,..., | O ( p i ) |} f k + max k ∈{ 1 ... | O ( p i ) |} f k . Comp osition of the ab o ve maps with monotonic increasing functions, such as saturations or (o dd) p o wers are also legitimate c hoices, i.e. F i ( f ) = P k α k sat( f k ) or F i ( f ) = ( P k α k f k ) 3 . W e are now ready to state our main result and, later, to discuss the technical steps of its deriv ation. Theorem 1 Consider a c o op er ative network of agents as in (3) and let N b e the Petri Net asso ciate d to its set of minimal joint agent inter actions. Consider a p artition of N into two disjoint sub gr oups F , H ⊂ N , which r epr esent the F aulty and the He althy agents (r esp e ctively), along with the pr oje cte d dynamics, (5). Then, r obust c onsensus is achieve d among the agents in H pr ovide d N fulfil ls r obust c onsensuability with r esp e ct to faulty agents in F . It is w orth pointing out that the result assumes fault y agents are follo wing arbitrary contin uous ev olutions and that these are reliably broadcast to all neighbouring agen ts. This h yp othesis cannot mo del the situation in whic h malicious agents in tentionally comm unicate different ev olutions to different neigh b ors. Agents with this abilit y are usually referred to as Byzan tine agen ts, and Byzan tine consensus protocols exhibit robustness to such kind of threats. Notice that the ability of malicious agen ts of differen tiating the information sen t to neigh b ors ma y disrupt consensus even when robust consensuability is fulfilled. An example of this situation is later shown in Section 5. W e start the tec hnical discussion b y generalizing Prop osition 11 in [1]. Lemma 1 L et H b e a siphon of N . Consider a network of e quations (10) and let x H denote the state ve ctor of agents in H , along with the c orr esp onding e quations ˙ x H ( t ) = f H ( x H ( t ) , x F ( t )) (11) 6 as intr o duc e d in (5). Then, for any c ∈ R , the sets: ¯ X c := { x H ∈ R | H | : x H ≤ c 1 H } , X c := { x H ∈ R | H | : x H ≥ c 1 H } ar e r obustly forwar d invariant for any b ounde d input signal x F ( · ) . Pro of Let x F ( · ) tak e v alue in the compact set K and h ∈ H b e any agent whose asso ciated state v alue fulfills x h = c . T o pro ve inv ariance of ¯ X c w e need to show f h ( x H , x F ) ≤ 0 for all x F ∈ K . This condition, in fact, amoun ts to f ( x H , x F ) ∈ T C x ( ¯ X c ) for all x H ∈ ∂ ¯ X c and all x F ∈ K . This, in turn implies forward inv ariance of ¯ X c b y Nagumo’s Theorem. Let O ( p h ) = { t 1 , t 2 , . . . , t | O ( p h ) | } . Since h is a siphon, for all t i in O ( p h ) there exists ˜ h ∈ I ( t i ) ∩ H . Hence: f I ( t i ) → h ( x ) ≤ f I ( t i ) → h ( ¯ x H 1 H , x F ) = 0 . By monotonicit y of F h then: ˙ x h = F h ( f I ( t 1 ) → h ( x ) , f I ( t 2 ) → h ( x ) , . . . , f I ( t | O ( p h ) | ) → h ( x )) ≤ F h (0 , 0 , . . . , 0) = 0 . This completes the pro of of the Lemma. The rest of the Section is dev oted to illustrate the main technical steps of the pro of. Pro of Let x F ( t ) b e an arbitrary bounded, con tinuous signal. Assume, in particular, that x F ( t ) ∈ K for some compact set K ⊂ R | F | . Pick any initial agent distribution x H (0) and define the evolution of health y agents in H according to the equation (5). In particular, we denote the solution x H ( t ) := ϕ H ( t, x H (0) , x F ( · )), for all t ≥ 0. Moreov er, w e let: ¯ x H := max h ∈ H x h x H := min h ∈ H x h . Since H is a siphon, by Lemma 1, we see that for all t 2 ≥ t 1 ≥ 0: x H ( t 1 ) ∈ ¯ X ¯ x H ( t 1 ) ⇒ x H ( t 2 ) ∈ ¯ X ¯ x H ( t 1 ) . In particular then, ¯ x H ( t 1 ) ≥ ¯ x H ( t 2 ), viz. ¯ x H is monotonically non-increasing. As exp ected, a symmetric argumen t shows that x H ( t ) is monotonically non-decreasing. Therefore x H ( t ) is uniformly b ounded and the limits ¯ x ∞ H := lim t → + ∞ ¯ x H ( t ) x ∞ H := lim t → + ∞ x H ( t ) , (12) exist finite. F or future reference, it is con venien t to define the conv ex-v alued differential inclusion given b elow: ˙ z ∈ F H ( z ) := co [ x F ∈ K { f H ( z , x F ) } ! . (13) Due to compactness of K , and Lipschitz con tinuit y of f H , F H is a Lipschitz contin uous set-v alued map. In particular, x H ( t ), is also a (b ounded) solution of (13). Consider next the asso ciated ω -limit set, which, by b oundedness of x H ( t ), is non-empt y and compact: Ω H := x ∈ R | H | : ∃ { t n } + ∞ n =1 : lim n → + ∞ t n = + ∞ and x = lim n → + ∞ x H ( t n ) . (14) Notice that, b y definition, for an y z H ∈ Ω H w e ha ve ¯ z H = ¯ x ∞ H and z H = x ∞ H . As is w ell kno wn, Ω H is a w eakly in v ariant set for the differen tial inclusion (13). Selecting any element ˜ z H in Ω H , there exists at least one viable solution ˜ z H ( t ) of (13), such that ˜ z H ( t ) ∈ Ω H , for all t . Notice that, b y Lipsc hitzness of F H , the sets M ( t ) := { h ∈ H : ˜ z h ( t ) = ¯ x ∞ H } , and m ( t ) := { h ∈ H : ˜ z h ( t ) = x ∞ H } are monotonically non-increasing with resp ect to set-inclusion and, trivially , non-empt y for all t ≥ 0. Hence, there exists some finite τ ≥ 0 such that M ( t ) = M ( τ ) and m ( t ) = m ( τ ) for all t ≥ τ . Moreo ver, for all such v alues of t , w e see that: ˙ ˜ z h ( t ) = 0 ∀ h ∈ M ( τ ) , (15) and similarly ˙ ˜ z h ( t ) = 0 ∀ h ∈ m ( τ ) . (16) 7 T o prov e asymptotic consensus, we need to show M ( τ ) ∩ m ( τ ) 6 = ∅ . T o this end, we claim that there exists F M ⊂ F such that M ( τ ) is an F M con trolled siphon, as w e argue next b y con tradiction. Should this not happ en, at least some h would exist in M ( t ) and I ⊂ N such that I → h and still I ∩ ( M ( t ) ∪ F ) = ∅ . In particular then, ¯ ˜ z I ( t ) := max i ∈ I ˜ z i ( t ) < ¯ x ∞ H and this violates (15) b y virtue of definition (6) as for all x F ∈ K : f h ( ˜ z H ( t ) , x F ) ≤ f h ( ¯ x ∞ H 1 H + ( ¯ ˜ z I ( t ) − ¯ x ∞ H ) e I , x F ) ≤ − ρ ( ¯ x ∞ H − ¯ ˜ z I ( t )) < 0 . A similar argumen t can be used to sho w that m ( t ) is an F m con trolled siphon. Consider next an y switch pairs F M , F m ⊂ F such that M ( τ ) and m ( τ ) are, resp ectiv ely , an F M and F m con trolled siphon. Assume, without loss of generality , F M and F m minimal with resp ect to set inclusion (among similar siphons’ switc hes). In the following we argue by contradiction considering the case M ( τ ) ∩ m ( τ ) = ∅ . By structural consen- suabilit y this implies F M ∩ F m 6 = ∅ and w e may pic k ¯ f ∈ F M ∩ F m . By minimality of F M and F m , moreov er, taking out ¯ f from them violates the definition of controlled siphon, viz. there exist h M ∈ M ( τ ) and h m ∈ m ( τ ) (distinct from eac h other), suc h that for some joint interactions I M → h M and I m → h m w e see that I M ∩ ( M ( t ) ∪ ( F M \{ ¯ f } )) = ∅ , (17) and, similarly , I m ∩ ( m ( t ) ∪ ( F m \{ ¯ f } )) = ∅ . (18) Since H is a siphon, how ev er, f h M ( z , x F ) ≤ 0 for all z ∈ Ω H and all x F ∈ K . Moreov er condition (17) yields: x ¯ f < ¯ x ∞ H ⇒ f h M ( ˜ z H ( t ) , x F ) ≤ − ρ ( ¯ x ∞ H − max { ¯ ˜ z I M ( t ) , x ¯ f } ) < 0 . Similarly , f h m ( z , x F ) ≥ 0 for all z ∈ Ω H and all x F ∈ K . In addition, x ¯ f > x ∞ H ⇒ f h m ( ˜ z H ( t ) , x F ) ≥ ρ (min { ˜ z I m ( t ) , x ¯ f } − x ∞ H ) > 0 . Notice that, whenev er x ∞ H < ¯ x ∞ H , w e ha ve ( −∞ , ¯ x ∞ H ) ∪ ( x ∞ H , + ∞ ) = R and therefore, f h M ( ˜ z H ( t ) , x F ) − f h m ( ˜ z H ( t ) , x F ) ≤ − ρ (min ¯ x ∞ H − max { ¯ ˜ z I M ( t ) , ( x ∞ H + ¯ x ∞ H ) / 2 } , min { ˜ z I m ( t ) , ( x ∞ H + ¯ x ∞ H ) / 2 } − x ∞ H ) . As a consequence: ( e h M − e h m ) 0 F H ( ˜ z H ( t ) , x F ) ≤ − ρ (min ¯ x ∞ H − max { ¯ ˜ z I M ( t ) , ( x ∞ H + ¯ x ∞ H ) / 2 } , min { ˜ z I m ( t ) , ( x ∞ H + ¯ x ∞ H ) / 2 } − x ∞ H ) < 0 for all x F ∈ K . This, how ever, con tradicts either (15) or (16). Notice that, in the pro of of Theorem 1, it is crucial that the p osition communicated by malicious agents to all of its neighbors are consistent. If not, malicious agents could more easily preven t consensus by sending differen tiated signals to individual agents, and a corresp ondingly stronger notion of structural consensuabilit y w ould b e needed. 5 Examples and Sim ulation W e consider next an example with 9 agen ts arranged in a 3 × 3 grid. Each agent is denoted b y an (ordered) pair of in tegers in { 1 , 2 , 3 } := N . In particular then N = N × N . W e consider the following interconnection top ology . F or all ( i, j ) ∈ N × N , we ha ve tw o join t-agent interactions: ( N \{ i } ) × { j } → ( i, j ) { i } × ( N \{ j } ) → ( i, j ) . The asso ciated Petri Net is shown in Fig. 4. Notice that, by construction, whenever an agent belongs to a siphon, someb ody from the same column and row also needs to b e within the siphon. Let, for a set Σ ⊂ N × N , Σ i denote the elemen ts of Σ b elonging to { i } × N and, by Σ j the elements of Σ in N × { j } . W e see that Σ 8 1 , 1 1 , 2 1 , 3 2 , 1 2 , 2 2 , 3 3 , 1 3 , 2 3 , 3 Figure 4: Petri Net asso ciated to joint-agen t in teractions (a) 1 , 1 1 , 2 1 , 3 2 , 1 2 , 2 2 , 3 3 , 1 3 , 2 3 , 3 (b) 1 , 1 1 , 2 1 , 3 2 , 1 2 , 2 2 , 3 3 , 1 3 , 2 3 , 3 Figure 5: Siphons of minimal support (gra y) (non-empt y) is a siphon if and only if | Σ i | ≥ 2 for all i ∈ N such that | Σ i | > 0 and | Σ j | ≥ 2 for all j ∈ N suc h that | Σ j | > 0. In particular, minimal siphons fulfill the equalit y rather than the strict inequalit y and are essentially of tw o kinds, as shown in Fig. 5. It is straightforw ard to see that, despite ha ving siphons of cardinalit y strictly smaller than half of the size of the group (4 < 9 / 2 ), still their la yout ensures that tw o siphons will alwa ys share at least one element. Therefore, structural consensuabilit y is fulfilled and asymptotic consensus is guaran teed in the absence of faulty agents for all initial conditions. Next w e inv estigate the p ossibilit y of achieving robust consensus in the presence of a single faulty agent. Due to the simmetry of the netw ork w e ma y c ho ose any agent to b e faulty , and the corresponding analysis will apply to an y other p ossible agen t after some p erm utations. F or ease of graphical represen tation we c ho ose the fault y agent to b e (2 , 2). First of all it is easily seen that N × N \{ (2 , 2) } is a siphon. Moreo ver, any siphon of the full Petri Net that do es not con tain (2 , 2) is also a ∅ -con trolled siphon when F = { (2 , 2) } . Next, we look for (2 , 2)-controlled siphons. These are siphons for which agent (2 , 2) acts as a switch. It can b e seen that Σ is a (2 , 2) controlled siphon if (and only if ) Σ ∪ { (2 , 2) } is a siphon. This direct implication is true for all Petri Nets, but the conv erse need not hold in general. In particular, then, only tw o types of controlled siphons can b e iden tified (up to p erm utations), as sho wn in Fig. 6. Because of this, for any pair of ∅ or (2 , 2) con trolled siphons Σ 1 , Σ 2 , with associated switc hes F 1 , F 2 it is true that (Σ 1 ∪ F 1 ) ∩ (Σ 2 ∪ F 2 ) 6 = ∅ . 9 (a) 1 , 1 1 , 2 1 , 3 2 , 1 2 , 2 2 , 3 3 , 1 3 , 2 3 , 3 (b) 1 , 1 1 , 2 1 , 3 2 , 1 2 , 2 2 , 3 3 , 1 3 , 2 3 , 3 Figure 6: (2 , 2)-controlled siphons of minimal support (gray) (a) 1 , 1 1 , 2 1 , 3 2 , 1 2 , 2 2 , 3 3 , 1 3 , 2 3 , 3 (b) 1 , 1 1 , 2 1 , 3 2 , 1 2 , 2 2 , 3 3 , 1 3 , 2 3 , 3 Figure 7: { (2 , 2) , (3 , 3) } -controlled siphons of minimal support (gray) And, since b y definition Σ i ∩ F i = ∅ , then the following is true: Σ 1 ∩ Σ 2 = ∅ ⇒ F 1 ∩ F 2 6 = ∅ . Hence, robust structural consensuabilit y is fulfilled and one ma y expect the 8 healty agents to reac h asymp- totic consensus despite the exogenous disturbance coming from agent (2 , 2). As previously remarked, this is still true for all p ossible selections of a single fault y agent. Next w e explain why this netw ork is not able, in general, to withstand more than a single faulty agent. If t wo faulty agents occur, either in the same ro w or column, then the set of healt y agents will exhibit a row or a column with a single agent. This implies that the set of healthy agen ts is not a siphon. Hence robust structural consensuabilit y is not fulfilled. Indeed, the t wo agents ha ve the ability to influence the agent within the same column (or ro w) and disrupt its ability to reach asymptotic consensus. Consider next the case of tw o faulty agents that are not in the same ro w or column. F or instance agen ts (2 , 2) and (3 , 3). Let F = { (2 , 2) , (3 , 3) } . As w e already c haracterized s ∅ con trolled siphons and siphons con trolled b y switc h of cardinalit y one, w e need only look for F -controlled siphons. An y set Σ suc h Σ ∪ F is a siphon is also an F -controlled siphon. In addition, the netw ork exhibits tw o types of F -con trolled siphons that do not fulfill suc h condition. These are shown in Fig. 7. Notice that, { (2 , 3) } is an F -controlled siphon. On the other hand, the set { (1 , 1) , (1 , 2) , (3 , 1) , (3 , 2) } is an ∅ -con trolled siphon. These t wo con trolled siphons and their asso ciated switches ha ve both empt y in tersection. Hence, robust structural consensuabilit y do es not hold for this c hoice of faulty agents. Indeed agents in F ha ve the ability to preven t consensus b et ween the agents in the siphons describ ed ab o ve. F or instance, one ma y take initial conditions x 1 , 1 (0) = x 1 , 2 (0) = x 3 , 1 (0) = x 3 , 2 (0) = 1. F or a ∅ -controlled siphon this results in solutions fulfilling x 1 , 1 ( t ) = x 1 , 2 ( t ) = x 3 , 1 ( t ) = x 3 , 2 ( t ) = 1 for all t . At the same time, one ma y let the malicious agen ts fulfill x 3 , 3 ( t ) = x 2 , 2 ( t ) = 0 so that, an y solution with x 2 , 3 (0) = 0 w ould result in x 2 , 3 ( t ) = 0 iden tically , th us preven ting consensus. A similar issue arises, letting agen ts x 1 , 1 , x 1 , 2 , x 3 , 1 , x 3 , 2 b e initialized with negative v alues, while x 2 , 2 and x 3 , 3 oscillate at some higher v alues as sho wn in Fig. 8. Due to simmetry of the considered netw ork, it follows that selection of any tw o faulty agen ts result in the conditions for robust consensuability to b e violated. W e emphasize that the considered netw ork is not robust with resp ect to Byzantine malicious agents. In particular, in the simulation we show the result of agent (2 , 2) broadcasting higher v alues to agents (1 , 2), (2 , 1) than the one broadcast to agents (3 , 2), (2 , 3). The Byzan tine agent is initialized with x 2 , 2 (0) = 0 and does not 10 Figure 8: Malicious agen ts (2 , 2) and (3 , 3) disrupt consensus. Figure 9: Byzantine agent (2 , 2) disrupts consensus. c hange his p osition, while it sends the v alue +2 and − 2 to its neighbors, th us disrupting consensus as sho wn in Fig. 9. It is w orth p oin ting out that if the agen t had consisten tly sent the same information to all his neigh b ours robust consensus w ould ha ve b een ac hieved. 6 Comparison with AR C-P proto cols Adv ersarily Robust Consensus was first in tro duced by LeBlanc and co w orkers in [7]. This is proposed, initially , for all-to-all netw orks and later extended in [9] to net works with more ge neral top ologies. W e start this Section b y highlighting how the all-to-all top ology considered in [7] can b e seen as a sp ecific type of symmetric joint- agen t interaction. Similar considerations apply when the set of neighbours of each agent is a prop er subset of { 1 , 2 , . . . , n } but, for the sak e of simplicit y , this is not illustrated in detail. Let ¯ σ k ( x ) denote the k -th largest en try in x and, similarly , σ k ( x ) the k -th smallest en try in x . W e see that, ¯ σ k ( x ) = max J ⊂N : | J | = k min k ∈ J x k σ k ( x ) = min J ⊂N : | J | = k max k ∈ J x k . 11 Moreo ver, ¯ σ k ( x ) = σ n +1 − k ( x ), and therefore for any integer F with n − F ≥ F + 1 we see n − F X k = F +1 ¯ σ k ( x ) = n − F X k = F +1 σ k ( x ) . Consider next the proto col described by the following se t of equations: ˙ x i = − x i + P n − F k = F +1 ¯ σ k ( x ) n − 2 F . (19) This is, essen tially , a contin uous-time version of the algorithm prop osed in [7], where each agen t is directed to wards the av erage of the n − 2 F agents’ opinions of intermediate v alue (as achiev ed in [7] by using the sorting and reducing maps). It is easy to see that (19) is a monotone coop erative netw ork, moreov er, w e claim that for all J of cardinality F + 1 and any agent i it holds J → i . T o this end, let J b e a subset of cardinality F + 1 and let x J > x i b e the common v alue associated with agents in J . All agen ts not in J , including agent i ha ve v alue x i , instead. Clearly ¯ σ k ( x ) = x J for all k = 1 . . . F + 1 and ¯ σ k ( x ) = x i for all k = F + 2 . . . n . In particular, then: ˙ x i = − x i + x J + ( n − 2 F − 1) x i n − 2 F = x J − x i n − 2 F , whic h pro ves a joint influence of agen ts in J tow ards i from ab o ve. Similar results hold when x J < x i . Moreov er, J → i is a minimal influence. In fact, an y prop er subset of J consists of at most F elemen ts and therefore, assuming their v alue is x J while x i is the v alue of other agents, a simple computation shows that ˙ x i = − x i + ( n − 2 F ) x i n − 2 F = 0 . th us ruling out the possibility of joint-influences for sets of agen ts of cardinality F or low er. Similar computations can b e carried out when the netw ork is not of all-to-all t yp e, and each agent has a sp ecific set of neighbours that get sorted, reduced and av eraged up on. 7 Conclusions This pap er has explored tight necessary and sufficient conditions for contin uous-time Adversary Consensus Proto cols of net works with join t-agent interactions of arbitrary topology . This captures, as a particular case, the notion of AR C consensus studied in the discrete-time case b y Leblanc and co-w orkers, using sorting and sele ction maps. Consensus is a c hieved in the face of agents that b eha ve as arbitrary b ounded disturbances, and are only constrained to broadcasting the same information to all of the neigh b ours they ha ve an influence up on. In this respect, the problem of Byzantine consensus, where agents may maliciously or unintenionally send differen t information to distinct neighbours is an interesting op en question for further research. Conditions are form ulated in the language of Petri Nets, in particular making use of the notion of c ontr ol le d siphon , in which fault y agen ts play the role of a ‘switch’ capable of disabling some influences by suitably positioning itself ab o ve or b elo w the v alue of agents within the same joint-agen t in teraction. An example is presented to illustrate the applicabilit y of the considered results. This does not fall within the class of netw orks considered in [9] since eac h agent is only has t wo distint group of neighbours (vertical and horizon tal ones in the picture) which are treated separately when cross-v alidating information in joint-agen t in teractions). In particular, the equations considered can nev er be achiev ed b y means of sorting and selection functions. References [1] D. Angeli and S. Manfredi, On consensus proto cols allowing join t-agent interactions, IEEE Conf. on De- cision and Contr ol submitted. [2] W. Abbas, Y. V orob eychik and X. Koutsoukos, Resilient Conse nsus Proto col in the Presence of T rusted No des, 7th International Symp osium on R esilient Contr ol Systems , Denv er (CO), U.S., August 2014. [3] R. Olfati-Sab er, J.A. F ax and R.M. Murray , Consensus and Coop eration in Netw orked Multi-Agent Sys- tems, Pr o c e e dings of the IEEE , vol . 95, N. 1, pp. 215-233, 2007. [4] J. M. Hendrickx and J. N. Tsitsiklis. Conv ergence of t yp e-symmetric and cut-balanced consensus seeking systems. IEEE T r ansactions on Automatic Contr ol, 58, 1, 2013 . 12 [5] S. Martin, J. M. Hendrickx, Con tinuous-time consensus under non-instantaneous recipro city , in IEEE T r ansactions on Automatic Contr ol, 61, 9, 2484 -2495, 2016 . [6] L. Moreau. Stability of m ultiagent systems with time-dep endent communication links. IEEE T r ansactions on Automatic Contr ol, 50, 2, 2005 . [7] H. LeBlanc and X. Koutsoukos, Consensus in Netw orked Multi-Agen t Systems with Adversaries, Pr o c. of HSCC’2011 , Chicago, IL, USA, 2011. [8] H. LeBlanc and X. Koutsoukos, Lo w Complexity Resilient Consensus in Netw orked Multi-Agen t Systems with Adv ersaries, Pr o c. of HSCC’2012 , Beijing, China, 2012. [9] H. LeBlanc, H. Zhang, S. Sundaram and X. Koutsoukos, Consensus of Multi-Agen t Net works in the Pres- ence of Adv ersaries Using Only Lo cal Information, Pr o c. of HiCoNS’12 , Beijing, China, 2012. [10] Z. Lin, B. F rancis, and M. Maggiore. State agreemen t for con tin uous time coupled nonlinear systems. SIAM J. Contr., 46, 1 , 2007. [11] S. Manfredi, D. Angeli. A criterion for exp onen tial consensus of time-v arying non-monotone nonlinear net works. IEEE T r ansactions on Automatic Contr ol, 62, 5, 2483–2489, 2016 . [12] S. Manfredi, D. Angeli. Necessary and Sufficien t Conditions for Consensus in Nonlinear Monotone Net works with Unilateral In teractions. A utomatic a, 77, 51 - 60 , 2017. [13] Y. D. Zhong, V. Sriv astav a and N. E. Leonard. On the Linear Threshold Mo del for Diffusion of Innov ations in Multiplex Social Netw orks. T o app e ar in Pr o c. IEEE Confer enc e on De cision and Contr ol , 2017. [14] M. A. Jav arone. So cial Influences in Opinion Dynamics: the Role of Conformity . Physic a A: Statistic al Me chanics and its Applic ations , 2014. [15] C. Als-F errer, S. Hugelsc hfer and J. Li. Inertia and Decision Making. F r ontiers in Psycholo gy, V olume 7 , 2016. [16] M. Baddeley Herding, so cial influence and economic decision-making: so cio-psyc hological and neuroscien- tific analyses. Phil. T r ans. R. So c. B, 365, 281-290 , 2016. [17] D.P . Bertsek as and J.N. Tsitsiklis, Par al lel and Distribute d Computation: Numeric al Metho ds , Pren tice Hall, 1989. [18] S. Bo yd, N. P arikh, E. Chu, B. Peleato and J. Ec kstein, Distribute d Optimization and Statistic al L e arning via the Alternating Dir e ction Metho d of Multipliers , F oundations and T rends in Mac hine Learning, V ol. 3, N.1., p. 1-122, 2010 [19] C. Altafini, Consensus problems on netw orks with antagonistic in teractions, IEEE T r ansactions on Auto- matic Contr ol, V ol. 58, No. 4, 2013 . [20] S. Manfredi, D. Angeli. F rozen state conditions for exp onen tial consensus of time-v arying co operative nonlinear net works. Automatic a, 63, 182 – 189, 2016 . [21] A. Sarlette and R. Sepulchre, Consensus Optimization on manifolds, SIAM Journal on Contr ol and Opti- mization , V ol. 48, N.1, pp. 56-76, 2009. [22] P . Resnic k, K. Ku wabara, R. Zeckhauser, E. F riedman, R eputation systems , A CM 43, 12, 4548., 2000 [23] S.-R. Y an, X.-L. Zheng, Y. W ang, W.W. Song, W.-Y. Zhang, A gr aph-b ase d c ompr ehensive r eputation mo del: Exploiting the so cial c ontext of opinions to enhanc e trust in so cial c ommer c e, Inform . Sci. 318, 5172, 2015 [24] X.-L.Zheng,C.-C.Chen,J.-L.Hung,W.He,F.-X.Hong,Z.Lin, A hybrid trust-b ase d r e c ommender system for on- line c ommunities of pr actic e , IEEE T ransactions Learn. T echnol. 8, 4, 345356, 2015. [25] B. Mortaza vi, and G. Kesidis, Cumulative R eputation Systems for Pe er-to-Pe er Content Distribution, Pro ceeding NOSSDA V ’03 Pro ceedings of the 13th in ternational w orkshop on Netw ork and op erating systems support for digital audio and video 144-152, 2003 [26] A. Jsang, R. Ismail, and C. Bo yd. A survey of trust and r eputation systems for online servic e pr ovision. Decision Support Systems, 43, 2, 618-644, 2007 13 [27] W.Jiang, J.W u, F.Li,G.W ang, H.Zheng, T rust evaluation in online so cial networks using gener alize d flow , IEEE T ransactions Comput. 65,3, 952963, 2016 [28] K. F ujimura, T. Nishihara, R eputation r ating system b ase d on p ast b ehavior of evaluators , in: Pro ceedings of the 4th ACM Conference on Electronic Commerce, EC03, A CM, New Y ork, NY, USA, 246247, 2003 [29] X.-L. Liu, Q. Guo, L. Hou, C. Cheng, J.-G. Liu, R anking online quality and r eputation via the user activity , Ph ysica A 436, 629636, 2015 [30] Liao H, Zeng A, Xiao R, Ren Z-M, Chen D-B, Zhang Y-C R anking R eputation and Quality in Online R ating Systems . PLoS ONE 9, 5: e97146, 2014 [31] S. Kamv ar, M. Sc hlosser, and H. Garcia-Molina. The Eigen- T rust algorithm for r eputation management in P2P networks . In Pro ceedings of the Twelwth International W orld-Wide W eb Conference (WWW03), pages 446458, 2003. [32] M. Kinateder and K. Rothermel. Ar chite ctur e and algo- rithms for a distribute d r eputation system. In Pro- ceedings of T rust Managemen t: First International Conference (iT rust 2003), LNCS, pages 116. Springer- V erlag, May 2003. [33] J.Gao,Y.-W.Dong,M.-S.Shang,S.-M.Cai,T.Zhou, Gr oup-b ase d r anking metho d for on line r ating systems with sp amming attacks , Europh ys. Lett.110, 2, 28003, 2015 [34] Jian Gao, T ao Zhou, Evaluating user r eputation in online r ating systems via an iter ative gr oup-b ase d r anking metho d, Physica A 473, 546560, 2017 [35] M. Pease, R. Shostak and L. Lamport, Reaching Agreemen t in the Presence of F aults, Journal of the ACM , V ol. 27, N. 2, pp. 228-234, 1980. 14
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment