Modification of Social Dominance in Social Networks by Selective Adjustment of Interpersonal Weights
According to the DeGroot-Friedkin model of a social network, an individual's social power evolves as the network discusses individual opinions over a sequence of issues. Under mild assumptions on the connectivity of the network, the social power of e…
Authors: Mengbin Ye, Ji Liu, Brian D. O. Anderson
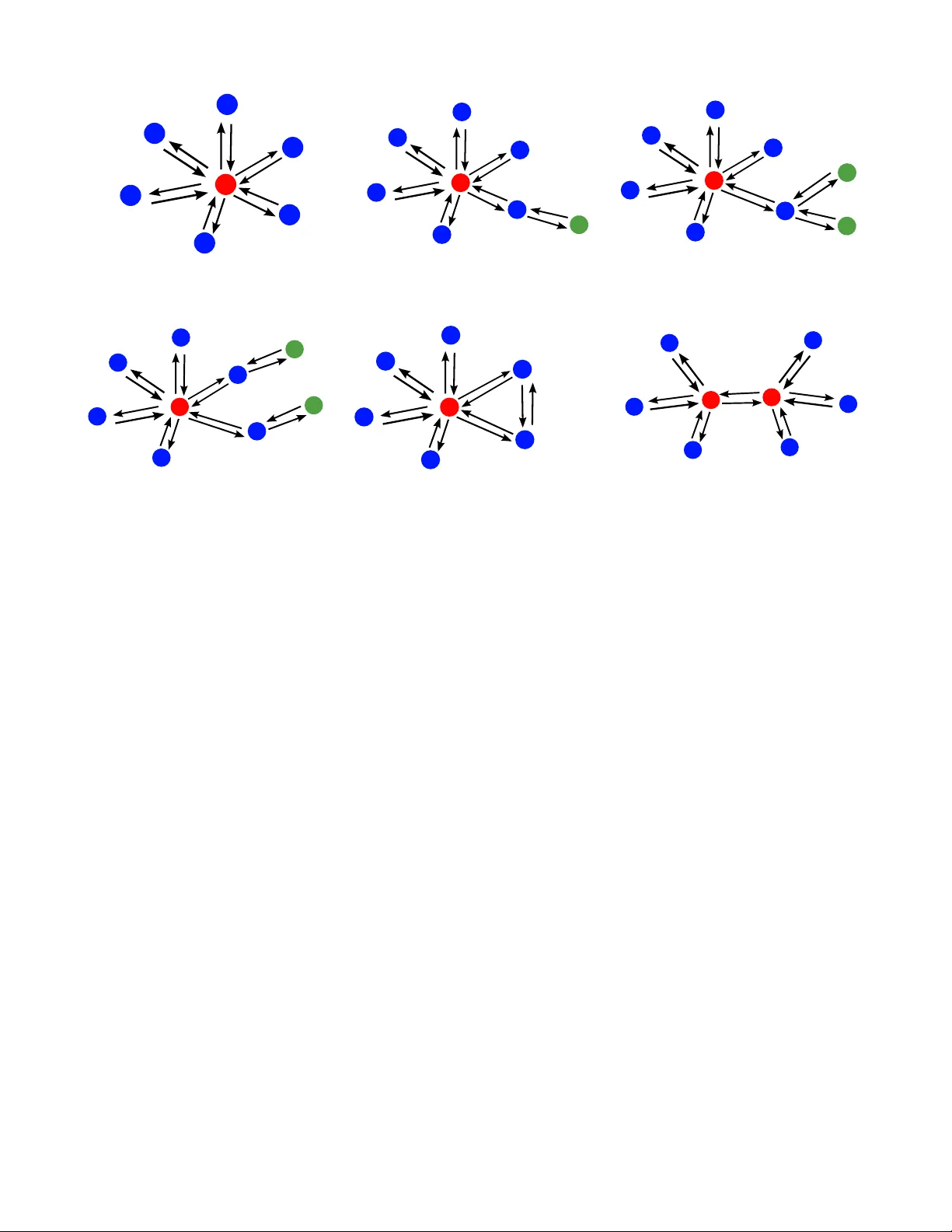
Modification of Social Dominance in Social Networks by Selecti ve Adjustment of Interpersonal W eights Mengbin Y e 1 , Ji Liu 4 , Brian D.O. Anderson 1 , 2 , 3 , Changbin Y u 1 , 2 , and T amer Bas ¸ ar 4 Abstract — According to the DeGroot-Friedkin model of a social network, an individual’ s social po wer evolv es as the network discusses individual opinions over a sequence of issues. Under mild assumptions on the connectivity of the network, the social power of e very indi vidual con verges to a constant strictly positive value as the number of issues discussed incr eases. If the network has a special topology , termed “star topology”, then all social power accumulates with the individual at the centr e of the star . This paper studies the strategic intr oduction of new individuals and/or interpersonal relationships into a social network with star topology to reduce the social power of the centre individual. In fact, several strategies are proposed. For each strategy , we deri ve necessary and sufficient conditions on the strength of the new interpersonal relationships, based on local information, which ensures that the centre individual no longer has the greatest social power within the social network. Interpr etations of these conditions sho w that the strategies are remarkably intuitive and that certain strategies are favourable compared to others, all of which is sociologically expected. I . I N T R O D U C T I O N In recent years, the systems and control community has turned to study of networked systems and multi-agent sys- tems in the context of social sciences. Of particular interest are social networks, where groups of people interact with acquaintances through interpersonal relationships . One problem of “opinion dynamics” has been of particular interest; how do the opinions of individuals for a given issue ev olv e as they discuss this issue in a social network? A recent survey on opinion dynamics is presented in [1]. An important aspect of opinion dynamics is social power , which in one sense can be considered as the weight/power/influence an individual has on the opinion discussion, relati ve to the weight/power/influence of the other individuals in the social network. This relativity arises due to interpersonal relation- ships and their strengths (which may be unidirectional). This concept is studied in the seminal works [2], [3]. The ev olution of social power is studied in [4]. The paper [5] studies the case where multiple, interdependent issues are simultaneously discussed. Selecting the most influential in- dividual in social dif fusion models is studied in [6]. A social network with stubborn individuals who remain attached to 1 M. Y e, B. D.O. Anderson and C. Y u are with the Research School of Engineering, Australian National University . 2 B. D.O. Anderson and C. Y u are with Hangzhou Dianzi Uni versity , Hangzhou, China. 3 B. D.O. Anderson is also with Data61-CSIRO (formerly NICT A Ltd.) in Canberra, A.C.T ., Australia. 4 J. Liu and T . Bas ¸ar are with the Coordinated Science Laboratory , Univ ersity of Illinois at Urbana-Champaign. This work was supported by the Australian Research Council (ARC) under grants DP-130103610 and DP-160104500, by the National Natural Science Foundation of China (grant 61375072), and by Data61-CSIRO. { Mengbin.Ye, Brian.Anderson, Brad.Yu } @anu.edu.au { jiliu, basar1 } @illinois.edu their initial opinions is studied in [7], [8]. The centralised DeGroot-Friedkin model for the ev olution of social power is proposed and analysed in [9]. Distributed discrete- and continuous-time DeGroot-Friedkin models are studied in [10] and [11] respectiv ely . According to French Jr . and Snyder in [12], “ leadership is the potential social influence of one part of the group ov er another . ” From the perspecti ve of opinion dynamics, a leader can therefore be seen as an individual or a group of individuals that has a disproportionate amount of control ov er the opinion discussion process. In the context of social power , one can therefore refer to a leader/leader group as the socially dominant individual/group of individuals. The fact that social power tends to accumulate with one individual or a subgroup of individuals in a social network is reported empirically in [4] and theoretically in [9]. This indi vidual or subgroup is defined explicitly by the interpersonal rela- tionships in the social network. Motiv ated by this concept of social dominance/leadership, and using the DeGroot-Friedkin model to describe the social network, we begin with network topologies which have a single socially dominant individual, and seek to study contr ol strate gies, including intr oduction of new individuals into the network and/or establishment of new interpersonal relationships, that will cause the social dominance to shift to another individual . W e now introduce the DeGroot-Friedkin model to better motiv ate the formal problem statement which follo ws in the sequel. In order to allow readers to quickly grasp the concepts of the new model and understand the motiv ations, in the following subsection, where possible we leav e out definitions and exact mathemat- ical results; these will be included in Section II. The terms “self-weight”, “individual social power” and “social power” will be used interchangeably . A. The DeGr oot-F riedkin Model The discrete-time DeGroot-Friedkin model comprises a consensus model for describing the opinion dynamics (details are gi ven below) and a mechanism for updating self-weights (the weight an individual applies to its own opinion value in the consensus process). W e define S = { 0 , 1 , 2 , . . . } to be the set of indices of sequential issues which are being discussed by the social netw ork. F or a given issue s , the social network discusses the issue using the discrete-time DeGroot consensus model (with constant weights throughout the discussion of the issue). At the end of the discussion (i.e. when the DeGroot model has ef fectiv ely reached steady state), each individual reflects upon, and judges its impact on the discussion. This mechanism is termed reflected self- appraisal, with “reflection” referring to the fact that adjust- ments to weights are made after discussion on an issue. The individual then updates its own self-weight and discussion begins on the next issue s + 1 (using the same consensus model but now with adjusted weights). W e now explain the mathematical modelling of the mechanism for updating opinions within an issue, and the updating of self-weights from one issue to the next. 1) DeGr oot Consensus of Opinions: For each issue s ∈ S , each individual updates its opinion y i ( s, · ) ∈ R at time t + 1 as y i ( s, t + 1) = w ii ( s ) y i ( s, t ) + n X j 6 = i w ij ( s ) y j ( s, t ) (1) where w ii ( s ) is the self-weight individual i places on its own opinion and w ij is the weight given by agent i to the opinion of its neighbour individual j . As will be made apparent in the sequel, P n j =1 w ij = 1 , which implies that individual i ’ s new opinion v alue y i ( s, t + 1) is a con vex combination of its own opinion, and the opinions of its neighbours at the current time instant. The opinion dynamics for the entire social network may be expressed as y ( s, t + 1) = W ( s ) y ( s, t ) (2) where y ( s, t ) = [ y 1 ( s, t ) · · · y n ( s, t )] > is the vector of opinions of the n + 1 agents in the network at time instant t . This model was studied in [3] with S = { 0 } (i.e. only one issue was discussed). The dynamics of (2), and the graphical conditions required for opinions to con ver ge, have been well studied. Next, we describe the model for the updating of W ( s ) (specifically w ii ( s ) via a reflected self- appraisal mechanism that occurs at the end of discussion of an issue s ). For simplicity , we assume that each individual’ s opinion, y i ( s, t ) , is a scalar . Kronecker products may be used if each individual’ s opinion state is a vector y i ∈ R p , p ≥ 2 . 2) F riedkin’ s Self-Appraisal Model for Determining Self- W eight: The Friedkin component of the model proposes a method for updating the self-weight (individual social power , self-confidence or self-esteem) of individual i , which is denoted by x i ( s ) = w ii ( s ) ∈ [0 , 1] (the i th diagonal term of W ( s ) ) [9]. Define the vector x ( s ) = [ x 1 ( s ) · · · x n ( s )] > as the vector of self-weights for the individuals of the social network, with starting self-weight 0 ≤ x i (0) ≤ 1 satisfying P i x i (0) = 1 . The self-weight vector x ( s ) is updated at the end of issue s as x ( s + 1) = ζ ( s ) (3) where ζ ( s ) > is the unique nonnegati ve left eigen vector of W ( s ) associated with the eigen v alue 1 , normalised such that 1 > n ζ ( s ) = 1 , see [9]. When indi vidual i adjusts its value of w ii ( s ) = x i ( s ) , it necessarily must adjust the weights w ij ( s ) , j 6 = i to maintain P n j =1 w ij = 1 . The precise structure of W ( s ) , and its properties giving rise to the existence of ζ ( s ) > , will be provided in the sequel. See Remark 1 in Section II-B for comments on the motiv ation for this update mechanism. Conv ergence properties will be presented in the sequel, but under mild assumptions on the social network topology , it is shown that lim s →∞ ζ ( s ) > = x ∗ where x ∗ is the constant vector of social power at equilibrium . B. Contributions In order to simplify the problem of achieving change of a socially dominant leader, we will only consider social power at equilibrium x ∗ in this paper . It was shown in [9] that if the social network has a specific topology termed the star topology , all social power at equilibrium accumulates with a single individual k as issues are sequentially discussed, in an “autocratic configuration”. In this paper , we show that by strate gic introduction of ne w individuals and/or new interpersonal relationships into the social network, not only is the autocratic configuration broken but if the new r elationship is sufficiently str ong, other identifiable individ- ual(s) will have social power at equilibrium greater than individual k . Specifically , we deriv e necessary and sufficient conditions based on local information for the relationship strength. This is in contrast to many control strate gies on networked systems which rely on global information [13], [14]. In fact, a number of different strategies are considered. W e also propose a strategy whereby two socially dominant individuals in separate networks can combine their networks and together remain socially dominant. While the results are initially presented mathematically as inequalities, we provide detailed analysis and interpretation. In doing so, we show that the strategies are remarkably intu- itiv e and precisely what one would expect when considered from a sociological context. The fact that the strategies affect the social power of individuals in a social network which is sequentially discussing issues implies that we hav e de vel- oped control strategies for affecting/influencing the opinion dynamics pr ocess . C. P aper Structure In Section II, we provide notations, an introduction to graph theory , and con vergence results for the DeGroot- Friedkin model. At the same time, a formal problem state- ment is giv en. The main results are presented in Section III. Simulations are presented in Section IV and conclusions are drawn in Section V. I I . B AC K G RO U N D A N D F O R M A L P RO B L E M S T A T E M E N T W e begin by introducing some mathematical notations used in the paper . Let 1 n and 0 n denote, respectiv ely , the n × 1 column vectors of all ones and all zeros. For a vector x ∈ R n , 0 x and 0 ≺ x indicate component-wise inequalities, i.e., for all i ∈ { 1 , 2 , . . . , n } , 0 ≤ x i and 0 < x i , respectiv ely . Let ∆ n denote the n -simplex, the set which satisfies { x ∈ R n : 0 x , 1 > n x = 1 } . The canonical basis of R n is gi ven by e 1 , . . . , e n . Define e ∆ n = ∆ n \{ e 1 , . . . , e n } and int (∆ n ) = { x ∈ R n : 0 ≺ x , 1 > n x = 1 } . For the rest of the paper , we shall use the terms “node”, “agent”, and “individual” interchangeably . A. Graph Theory The interaction between indi viduals in a social network is modelled using a weighted directed graph, denoted as G = ( V , E ) . Each individual agent is a node in the finite, nonempty set of nodes V = { v 1 , . . . , v n } . The set of ordered edges is E ⊆ V × V . W e denote an ordered edge as e ij = ( v i , v j ) ∈ E , and because the graph is directed, in general e ij and e j i may not both exist. An edge e ij is said to be outgoing with respect to v i and incoming with respect to v j . The presence of an edge e ij connotes that individual j learns of, and takes into account, the opinion v alue of individual i when updating its own opinion. The incoming and outgoing neighbour set of v i are respecti vely defined as N + i = { v j ∈ V : e j i ∈ E } and N − i = { v j ∈ V : e ij ∈ E } . The relativ e interaction matrix C ∈ R n × n associated with G has nonnegati ve entries c ij , termed “relative interpersonal weights” in [9]. The entries of C have properties such that 0 < c ij ≤ 1 ⇔ e j i ∈ E and c ij = 0 otherwise. It is assumed that c ii = 0 (i.e. with no self-loops), and we impose the restriction that P j ∈N + i c ij = 1 (i.e. that C is a row- stochastic matrix). A directed path is a sequence of edges of the form ( v p 1 , v p 2 ) , ( v p 2 , v p 3 ) , . . . where v p i ∈ V , e ij ∈ E . Node i is reachable from node j if there exists a directed path from v j to v i . A graph is said to be strongly connected if every node is reachable from every other node. The relativ e interaction matrix C is irreducible if and only if the associated graph G is strongly connected ( C is known in some literature as the weighted adjacency matrix). If C is irreducible then it has a unique (up to a scaling) left eigenv ector γ > , with all entries strictly positive, associated with the eigen value 1 (Perron- Frobenius Theorem, see [15]). Henceforth, we shall call this left eigen vector γ > the dominant left eigen vector of C and assume that γ > has been normalised such that it has the property γ > 1 n = 1 . B. Con ver gence Results for the DeGr oot-F riedkin Model W e now provide additional, specific details on the model. For a given issue, the influence matrix W ( s ) is defined as follows W ( s ) = X ( s ) + ( I n − X ( s )) C (4) where C is the relative interaction matrix associated with the graph G , and the matrix X ( s ) . = diag [ x ( s )] . From the fact that C is row-stochastic with zero diagonal entries, (4) implies that W ( s ) is a ro w-stochastic matrix. Note that ζ ( s ) > 1 n = 1 implies that x ( s ) ∈ ∆ n for all s . From (4) and the fact that C is constant, it is apparent that by adjusting w ii ( s + 1) = ζ i ( s ) , individual i also scales w ij ( s + 1) , j 6 = i by (1 − w ii ( s + 1)) in order to maintain the row-stochastic property of W ( s ) . Remark 1 (Social Power) . The pr ecise motivation behind using (3) as the updating model for x ( s ) is detailed in [9], but we pr ovide a brief overview her e in the inter est of making this paper self-contained. The definition of W in (4) ensur es that, for any given s , ther e holds lim t →∞ y ( s, t ) = ( ζ ( s ) > y ( s, 0)) 1 n . In other words, for any given issue s , the opinions of every individual in the social network r each a consensus value ζ ( s ) > y ( s, 0) equal to a con vex combination of their initial opinion values y ( s, 0) . The elements of w ( s ) > ar e the con vex combination coefficients, i.e. ζ i ( s ) repr esents pr ecisely the amount of weight/power that individual i had on the opinion discussion for issue s . F or a given issue s , ζ i ( s ) is a manifestation of individual i ’ s social power in the social network, as it is in effect the ability of individual i to contr ol the outcome of a discussion [16]. The reflected self- appraisal mec hanism ther efor e describes an individual 1) observing how much power it had on the discussion of issue s (the nonne gative quantity ζ i ( s ) ) and, 2) for the following issue s + 1 , adjusting its self-weight to be equal to this power , i.e. x i ( s + 1) = w ii ( s + 1) = ζ i ( s ) . As can be observed fr om (4) and because C is constant, adjusting w ii ( s + 1) also adjusts the interpersonal weights w ij ( s + 1) . It is shown in [Lemma 2.2, [9]] that the system (3) describing the update of self-weights, is equiv alent to x ( s + 1) = F ( x ( s )) (5) where the nonlinear vector-v alued function F ( x ( s )) is de- fined as F ( x ( s )) = e i if x i ( s ) = e i , for any i α ( x ( s )) c 1 1 − x 1 ( s ) . . . c n 1 − x n ( s ) otherwise (6) with α ( x ( s )) = 1 / P n i =1 c i 1 − x i ( s ) . Much of this paper will deal with scenarios where the underlying graph has a star topology or its variants, the definition and relev ance of which are now giv en. Definition 1 (Star topology) . A str ongly connected graph 1 G is said to have star topology if ther e exists a node i , which is called the centr e node, such that every edge of G is either to or fr om node i Note that the irreducibility of C implies that the star topology must include edges in both directions between the centre node v i and ev ery other node v j , j 6 = i . W e now provide a lemma and a theorem regarding the con ver gence of F ( x ( s )) as s → ∞ . Lemma 1 (Lemma 3.2, [9]) . Suppose that n ≥ 3 , and suppose further that G has star topology , which without loss of generality has centre node v 1 . Let C be the r ow-stochastic and irreducible adjacency matrix, with zero diagonal entries, associated with G . Then for all initial conditions x (0) ∈ e ∆ n , the self-weights x ( s ) con verge to the fixed point x ∗ = e 1 as s → ∞ . 1 While it is indeed possible to have a star graph that is not strongly connected, this paper similarly to [9] deals only with graphs which are strongly connected. Theorem 1 (Theorem 4.1, [9]) . F or n ≥ 3 , consider the DeGr oot-F riedkin dynamical system (5) with a r elative inter- action matrix C that is r ow-stochastic, irr educible, and has zer o diagonal entries. Assume that the digraph G associated with C does not have star topology and define γ > as the dominant left eigen vector of C . Then, (i) F or all initial conditions x (1) ∈ e ∆ n , the self-weights x ( s ) conver ge to x ∗ as s → ∞ . Here , x ∗ ∈ e ∆ n is the unique fixed point satisfying x ∗ = F ( x ∗ ) . (ii) Ther e holds x ∗ i < x ∗ j if and only if γ i < γ j , for any i, j , wher e γ i is the i th entry of the dominant left eigen vector γ . There holds x ∗ i = x ∗ j if and only if γ i = γ j . (iii) The unique fixed point x ∗ is determined only by γ > , and is independent of the initial conditions. An interpretation of Lemma 1 and Theorem 1 is given in below in Remark 2. C. F ormal Pr oblem Statement In this paper , we inv estigate how additional nodes and/or edges strate gically connected to a star topology can change the social power at equilibrium, x ∗ . T o that end, we begin first by providing definitions which will aid in describing our problem and discussing results obtained. Moreover , we are interested in comparing the social power of individuals within the network at equilibrium, i.e. when s → ∞ . W e will therefore refer to the equilibrium value x ∗ i as the social power of indi vidual i when there is no ambiguity (as opposed to the ev olving x i ( s ) when s < ∞ ). T o simplify the problem, we do not study the ev olution of the opinions y ( s, t ) . Under the assumption that C is irre- ducible, it is shown in [9] that, for any issue s , the opinions always conv erge as lim t →∞ y ( s, t ) = ( ζ ( s ) > y ( s, 0)) 1 n . As discussed above, we are interested in individual social power of the network. Definition 2 (Autocratic Network) . A social network is said to be an autocr atic configuration, with node v i being the autocrat, if x ( s ) = e i . Definition 3 (Social dominance/leadership) . Node v i is said to be the socially dominant/leader node in the network if x ∗ i > x ∗ j for all j 6 = i . In other words, at equilibrium, the social power of individual i is gr eater than the social power of any other individual in the social network. Remark 2 (Autocratic tendency) . Lemma 1 has an important social connotation. One can consider x i (0) as individual i ’ s estimate of its social power when the social network is first formed, before any issue discussion. F or any initial estimate x (0) ∈ e ∆ n (that is, no individual i believes x i (0) = 1 ), the star topology network tends to an autocratic configuration at equilibrium, x ∗ = e 1 . This implies that, for the first few issues, opinion discussion will occur with e veryone contrib ut- ing to the final consensus value. However , as more issues ar e discussed, the centr e individual incr easingly guides the outcome of discussions until, for s = ∞ , only the centr e individual’ s opinion value matters. Remark 3. In [9], the constant entries c ij of C ar e termed “r elative interpersonal weights”, and we will keep with this terminology . However , one can also consider c ij as the amount of “trust” individual i has for individual j or the str ength of “influence” individual j has on individual i . In other wor ds, c ij captur es the strength of a unidirectional r elationship (unidirectional since c ij 6 = c j i in general). For a giv en graph G with star topology , with centre node v 1 , let us call the other nodes subject nodes in the sense that they are subjects to the autocrat centre node. In Fig. 1, these are nodes v i , i = 2 , ..., 7 . W e are going to study ho w the autocracy can be disrupted by introduction of a perturbation to the star graph. This leads us to define a ne w type of node. An attacker node is a node v j which forms edges e j i , e ij with some node v i , i 6 = 1 , i.e. a subject node. In doing so, we modify the graph G to become ¯ G which is no longer a star . In Fig. 2, node v 8 is the attacker node, forming edges with node v 7 . W e call node v j an attacker node because, as will become apparent in the sequel, the weights c j i and c ij determine the social power x ∗ 1 of the autocrat node v 1 . In other words, v j attacks the social dominance of v 1 . Note that two edges, e j i , e ij must be formed to ensure that ¯ G remains strongly connected. Actually , there are a number of interesting ways to attack the social dominance of v 1 , and we list some of the most important/fundamental methods. For each topology v ariation we list below , we provide an example in the Figures 2-6. T opology V ariation 1 (Single Attack) . Suppose that n ≥ 4 . Suppose further that G has star topology , with v 1 being the centr e node, and with n − 2 subject nodes, v i , i = 2 , ..., n − 1 . A single attacker node v n attaches to subject node v n − 1 by forming edges e n − 1 ,n and e n,n − 1 . This forms the modified graph ¯ G T opology V ariation 2 (Coordinated Double Attack) . Sup- pose that n ≥ 5 . Suppose further that G has star topology , with v 1 being the centr e node, and with n − 3 subject nodes, v i , i = 2 , ..., n − 2 . T wo attack er nodes v n − 1 and v n attach to subject node v n − 2 by forming the set of edges { e n − 2 ,n − 1 , e n − 1 ,n − 2 , e n − 2 ,n , e n,n − 2 } . This forms ¯ G . T opology V ariation 3 (Uncoordinated Double Attack) . Sup- pose that n ≥ 5 . Suppose further that G has star topology , with v 1 being the centr e node, and with n − 3 subject nodes, v i , i = 2 , ..., n − 2 . One attack er node v n − 1 attaches to subject node v n − 3 with edges e n − 3 ,n − 1 , e n − 1 ,n − 3 . A second attack er node v n attaches to subject node v n − 2 with edges e n − 2 ,n , e n,n − 2 . This forms ¯ G . T opology V ariation 4 (T wo Dissenting Subjects) . Suppose that n ≥ 4 . Suppose further that G has star topology , with v 1 being the centr e node, and with n − 1 subject nodes, v i , i = 2 , ..., n . Ther e are no attacker nodes. Subject nodes v n − 1 and v n form edges e n,n − 1 , e n − 1 ,n , forming ¯ G . The following topology variation is motiv ated by the concept of a leadership gr oup where two leaders exist, and seek to maintain their collective social dominance. T opology V ariation 5 (Leadership group) . Suppose that G 1 and G 2 r espectively have n ≥ 3 and m ≥ 3 nodes, with node set V 1 = { 1 , ..., n } and V 2 = { n + 1 , ..., n + m } r espectively . Both G 1 and G 2 have star topology; the centre nodes for G 1 and G 2 ar e v 1 and v n +1 r espectively . Let ¯ G be the graph formed by merging G 1 and G 2 by insertion of the edges e 1 ,n +1 and e n +1 , 1 . Nodes v 1 , v n +1 form a leadership group with subjects v 2 , ..., v n , v n +2 , ..., v n + m . In the next section, we in vestigate the above topological variations of the star graph. Note that T op ology V ariations 1- 5 have modified graphs ¯ G which do not have star topology . From the properties of F ( x ( s )) established in [9] and detailed in Lemma 1 and Theorem 1, it immediately follows that x ∗ 1 < 1 for all T opology V ariations. In other words, v 1 is no longer the autocrat but if the perturbation from star topology (caused by the new edges) is small, one expects that v 1 remains socially dominant . What will we show is that if the interpersonal weights associated with these new edges exceed a giv en threshold, the socially dominant node changes from v 1 to some other node. It is worth emphasising at this stage that, in V ariations 1-3, it is useless for an attacker node v n to attach to the centre node v 1 instead of a subject node; the topology remains a strongly connected star, and there is no change in the autocratic nature of v 1 ’ s social dominance. Note that when new edges are introduced, we assume each individual i adjusts its weights c ij to ensure that the new C is ro w-stochastic. T ake T opology V ariation 5 as an example. Separately , the relative interaction matrix C 1 (respectiv ely C 2 ) associated with G 1 (respectiv ely G 2 ) is assumed to be row-stochastic. The relative interaction matrix ¯ C associated with ¯ G is also implicitly assumed to be row- stochastic with zero diagonal. That is, we assume that after the addition of edges e 1 ,n +1 and e n +1 , 1 , adjustments are made to the original weights c 1 ,j and c n +1 ,k to ensure ¯ C is row-stochastic. Remark 4 (Ordering of Social Power) . Although Theor em 1 states that x ∗ is uniquely determined by γ > , ther e ar e no r esults available which allow one to analytically compute the value of x ∗ given γ > . What is available is Statement (ii) of Theor em 1, which states that the or dering x ∗ i is consistent with the or dering of γ i . In this paper , we ar e ther efor e inter ested in the ordering of individual social power , as opposed to the pr ecise values of social power . This is r eflected in Definition 3. I I I . M A I N R E S U LT S In order to maintain the flow of this paper, and to place focus on discussion of the social connotations of each result, we place all proofs in the appendix. W e firstly present theorems and corollaries for each topological variation, and then discuss their social implications. A. T opology V ariation 1: Single Attack er Now , firstly consider T opology V ariation 1. The relativ e interaction matrix C ( β ) associated with ¯ G can be expressed as C ( β ) = 0 c 12 c 13 . . . c 1 ,n − 1 0 1 0 0 . . . 0 0 1 0 0 . . . 0 0 . . . . . . . . . . . . . . . . . . 1 − β 0 0 . . . 0 β 0 0 0 . . . 1 0 (7) where β = c n − 1 ,n ∈ (0 , 1) is the influence e xerted by the attacker node v n on subject node v n − 1 . The follo wing theorem details ho w the social po wer of each indi vidual changes as β changes. Theorem 2 (Single Attack) . F or a social network with T opology V ariation 1, with initial conditions x (0) ∈ e ∆ n , and described by the DeGr oot-F riedkin model, the following statements are true: (i) F or all values of β ∈ (0 , 1) , there holds x ∗ i < x ∗ 1 , for all i 6 = 1 , n − 1 , n and x ∗ n < x ∗ n − 1 (ii) Ther e holds 1) x ∗ 1 > x ∗ i , ∀ i 6 = 1 if and only if β < 1 − c 1 ,n − 1 = P n − 2 i =2 c 1 ,i , or 2) x ∗ n − 1 > x ∗ i , ∀ i 6 = n − 1 if and only if β > 1 − c 1 ,n − 1 . Ther e holds x ∗ 1 = x ∗ n − 1 > x ∗ i , ∀ i 6 = 1 , n − 1 if and only if β 1 = 1 − c 1 ,n − 1 (iii) Ther e holds x ∗ n > x ∗ 1 if and only if β > 1 / (1 + c 1 ,n − 1 ) . Corollary 1 (Generalised Placement of Single Attacking Node) . Suppose that instead of attac hing to subject node v n − 1 , attack er node v n can attach to any subject node v i , i ∈ { 2 , ..., n − 1 } by forming edges e n,i , e i,n . The lower bound on β = c n,i r equired to have x ∗ n − 1 > x ∗ 1 is minimised if v n attaches to v k wher e k = argmax j ∈{ 2 ,...,n − 1 } c 1 ,j . The above mathematical results can be interpreted in the following social context. From Statement (i), we conclude that individuals 2 to n − 2 , i.e. subject nodes v i , i ∈ { 2 , .., n − 2 } will ne ver have greater social power at equilibrium, x ∗ i than the centre individual v 1 with x ∗ 1 , regardless of ho w β changes. In addition, the attacker node will never hav e greater social power than the subject node v n − 1 which it is attached to. Recall from Remark 3 that c ij can be considered the trust le vel accorded to indi vidual j by indi vidual i . Then according to Statement (ii), centre individual v 1 r emains the socially dominant individual in the social network only if subject v n − 1 trusts attacker v n less than the total sum of trust accorded to subjects v i , i ∈ { 2 , ..., n − 2 } by centre node v 1 . In or der to become socially dominant, and to undermine the authority of the centr e node v 1 , individual v n − 1 must trust the attacker v n . Lastly , Statement (iii) re veals that the attacker can also obtain social po wer greater the centre indi vidual v 1 if β , i.e. the trust accorded to the attack er v n by subject node v n − 1 , is suf ficiently lar ge. W e therefore conclude that the leadership/social dominance within a social network with T opology V ariation 1 can be shifted from the original leader (centre node) to a subject via introduction of a single attacker and strengthening of the newly formed interpersonal relationships. 1 2 3 4 5 6 7 Fig. 1. Star T opology with red Centre Node v 1 , and blue subject nodes, n = 7 . 1 2 3 4 5 6 7 8 β 1 − β Fig. 2. T opology V ariation 1 (Single Attacker) with n = 8 , attacker nodes are green. 1 2 3 4 5 6 7 8 β 1 1 − β 1 − β 2 9 β 2 Fig. 3. T opology V ariation 2 (Coordinated Dou- ble Attacker) with n = 9 , attacker nodes are green. 1 2 3 4 5 6 7 8 β 1 1 − β 2 9 β 2 1 − β 1 Fig. 4. T opology V ariation 3 (Uncoordinated Double Attacker) with n = 9 . 1 2 3 4 5 6 7 β 2 β 1 Fig. 5. T opology V ariation 4 (T wo Dissenting Subjects) with n = 7 . 1 2 3 4 β 2 β 1 5 8 7 6 Fig. 6. T opology V ariation 5 (Leadership Group) with n = m = 4 . Corollary 1 delivers an intuiti ve and powerful, socially relev ant result. It states that the single attacker node v n should seek to form an interpersonal relationship with the subject node v k that centre node v 1 trusts the most . This will minimise the required amount of trust subject v k accords attacker v n before centre node v 1 loses social dominance. B. T opology V ariation 2: Coor dinated Double Attack Consider now T opology V ariation 2. Firstly , define β 1 = c n − 2 ,n − 1 ∈ (0 , 1) and β 2 = c n − 2 ,n = (0 , 1) as the two adjustable interpersonal weights. Note that because C is assumed to be row-stochastic, it is implied that β 1 + β 2 + c n − 2 , 1 = 1 which in turn implies β 1 + β 2 < 1 because c n − 2 , 1 > 0 . W e omit displaying the exact form of C ( β 1 , β 2 ) due to spatial limitations. Theorem 3 (Coordinated Double Attack) . F or a social network with T opology V ariation 2, with initial conditions x (0) ∈ e ∆ n , and described by the DeGr oot-F riedkin model, the following statements ar e true: (i) F or all β 1 , β 2 ∈ (0 , 1) , ther e holds x ∗ i < x ∗ 1 for all i 6 = 1 , n − 2 , n − 1 , n , and x ∗ n , x ∗ n − 1 < x ∗ n − 2 . (ii) Ther e holds 1) x ∗ 1 > x ∗ i , ∀ , i 6 = 1 if and only if β 1 + β 2 < 1 − c 1 ,n − 2 = P n − 3 i =2 c 1 ,i , or 2) x ∗ n − 2 > x ∗ i , ∀ , i 6 = n − 2 if and only if β 1 + β 2 > 1 − c 1 ,n − 2 . Ther e holds x ∗ 1 = x ∗ n − 2 if and only if β 1 + β 2 = 1 − c 1 ,n − 2 . (iii) Ther e holds x ∗ n > x ∗ 1 (r espectively x ∗ n − 1 > x ∗ 1 ) if and only if β 2 > (1 − β 1 ) / (1 + c 1 ,n − 2 ) (respectively β 1 > (1 − β 2 ) / (1 + c 1 ,n − 2 ) ). (iv) Ther e holds x ∗ n − 1 < x ∗ n or x ∗ n − 1 > x ∗ n if and only if β 1 < β 2 or β 1 > β 2 r espectively . If β 1 = β 2 , then x ∗ n − 1 = x ∗ n . Corollary 2 (Generalised Placement of Coordinated Double Attack) . Suppose that instead of attaching to subject node v n − 2 , attac ker nodes v n − 1 , v n can attac h to any subject node v i , i ∈ { 2 , ..., n − 2 } by forming the set of edges { e n − 1 ,i , e i,n − 1 , e n,i , e i,n } . The lower bound on β 1 + β 2 = c n − 1 ,i + c n,i r equired to have x ∗ n − 2 > x ∗ 1 is minimised if v n − 1 and v n attach to v k wher e k = argmax j ∈{ 2 ,...,n − 2 } c 1 ,j . Due to spatial limitations, we discuss social implications of Theorem 3 only if the conclusions differ significantly from the discussion in the previous subsection. The key result is Statement (ii), which indicates that the combined trust given to attackers v n − 1 and v n by subject node v n − 2 must exceed the combined trust giv en to subjects v 2 , ..., v n − 3 by centre node v 1 , in order for centre node v 1 to lose social dominance (and thus subject v n − 2 becomes the socially dominant individual). It is most interesting to note that it is only the sum of the trust/influence β 1 + β 2 that is rele vant, and ther e is no r equir ement on the individual magnitudes of β 1 , β 2 . Regarding Statement (iii), we observe that the inequality , which if satisfied ensures that attacker v n has social power greater than centre v 1 , is a function of β 1 , β 2 and c 1 ,n − 2 . As detailed in the proof in Appendix B, there always exists a β 1 , β 2 satisfying β 1 + β 2 < 1 which ensures both attacker nodes v n − 1 , v n hav e social power greater than the centre v 1 . C. T opology V ariation 3: Uncoor dinated Double Attack Define β 1 = c n − 3 ,n − 1 ∈ (0 , 1) and β 2 = c n − 2 ,n ∈ (0 , 1) . Theorem 4. F or a social network with T opology V ariation 3, with initial conditions x (0) ∈ e ∆ n , and described by the DeGr oot-F riedkin model, the following statements ar e true: (i) F or all values of β 1 , β 2 ∈ (0 , 1) , there holds x ∗ i < x ∗ 1 for all i ∈ { 2 , . . . , n − 4 } , and x ∗ n − 1 < x ∗ n − 3 and x ∗ n < x ∗ n − 2 . (ii) Ther e holds x ∗ 1 > x ∗ i for all i 6 = 1 if and only if β 1 < 1 − c 1 ,n − 3 and β 2 < 1 − c 1 ,n − 2 . If β 1 > 1 − c 1 ,n − 3 (r espectively β 2 > 1 − c 1 ,n − 2 ), then x ∗ n − 3 > x ∗ 1 (r espectively x ∗ n − 2 > x ∗ 1 ). (iii) F or i ∈ { 1 , 2 } , there holds x ∗ n − 2+ i > x ∗ 1 if and only if β i > 1 / (1 + c 1 ,n − 4+ i ) . (iv) Ther e holds x ∗ n − 3 > x ∗ n − 2 if and only if 1 − β 2 1 − β 1 > c 1 ,n − 2 c 1 ,n − 3 . Equivalently , x ∗ n − 3 > x ∗ n − 2 if and only if c 1 ,n − 3 c n − 3 , 1 > c 1 ,n − 2 c n − 2 , 1 The most interesting conclusion drawn from Theorem 4 is when we compare to Theorem 3 which concerns T opology V ariation 2. With T opology V ariation 2, for the centre indi- vidual v 1 to lose its social dominance we require the sum of the trust values β 1 + β 2 to exceed a lower bound, and there are no separate lower bounding inequalities for β 1 or β 2 . With T opology V ariation 3, centre individual v 1 loses social dominance if and only if either β 1 or β 2 exceed their respectiv e lower bounding inequalities. Importantly , these two lower bounding inequalities are independent of each other . This clearly points to the fact that a coordinated attack on the social dominance of the centre node is mor e desirable, an idea which is socially intuitive . From Statement (iii), both attacker nodes ha ve larger social power than the centre node if and only if β 1 > 1 / (1 + c 1 ,n − 3 ) and β 2 > 1 / (1 + c 1 ,n − 2 ) , which implies that β 1 + β 2 > 1 / (1 + c 1 ,n − 3 ) + 1 / (1 + c 1 ,n − 2 ) . From Statement (iii) Theorem 3, with T opology V ariation 2, both attacker nodes hav e larger social power than the centre node if and only if β 2 > (1 − β 1 ) / (1 + c 1 ,n − 2 ) and β 1 > (1 − β 2 ) / (1 + c 1 ,n − 2 ) , which implies that β 1 + β 2 > 2 / (2 + c 1 ,n − 2 ) . Since both 1 + c 1 ,n − 2 and 1 + c 1 ,n − 3 are smaller than 2 + c 1 ,n − 2 , it follows that 1 / (1 + c 1 ,n − 3 ) + 1 / (1 + c 1 ,n − 2 ) > 2 / (2 + c 1 ,n − 2 ) , which implies that a coordinated attack on the social dominance of the centre node is also mor e efficient for the attacker s . D. T opology V ariation 4: T wo Dissenting Subjects T opology V ariation 4 is different to the ones studied above in the sense that there are no attacker nodes. Instead, one can consider this variation as one where two subjects form a relationship in dissent from the leader . Firstly , let β 1 = c n − 1 ,n ∈ (0 , 1) and β 2 = c n,n − 1 ∈ (0 , 1) . Analysis yields the following result. Theorem 5 (T wo Dissenting Subjects) . F or a social network with T opology V ariation 4, with initial conditions x ( s ) ∈ e ∆ n , and described by the DeGr oot-F riedkin model, the following statements are true: (i) F or all β 1 , β 2 ∈ (0 , 1) , ther e holds x ∗ i < x ∗ 1 for all i 6 = 1 , n − 1 , n . (ii) Ther e holds x ∗ n > x ∗ 1 if and only if β 1 > (1 − c 1 ,n ) / ( c 1 ,n − 1 + β 2 ) with β 1 ∈ (0 , 1) . Ther e exists such a β 1 ∈ (0 , 1) only if β 2 > P n − 2 i =2 c 1 ,i . (iii) Ther e holds x ∗ n − 1 > x ∗ 1 if and only if β 2 > (1 − c 1 ,n − 1 ) / ( c 1 ,n + β 1 ) with β 2 ∈ (0 , 1) . Ther e exists such a β 2 ∈ (0 , 1) only if β 1 > P n − 2 i =2 c 1 ,i . (iv) Ther e holds x ∗ n < x ∗ n − 1 if and only if β 2 > β 1 c 1 ,n + c 1 ,n − 1 ( c 1 ,n − 1) or equivalently β 1 < ( β 2 + c n − 1 (1 − c 1 ,n )) Note that the inequality in statement (ii) can be rewritten as β 2 > (1 − c 1 ,n − β 1 c 1 ,n − 1 ) /β 1 with β 2 ∈ (0 , 1) which is satisfiable only if β 1 > (1 − c 1 ,n ) / (1 + c 1 ,n − 1 ) . Similarly , the inequality in statement (iii) is equiv alent to β 1 > (1 − c 1 ,n − 1 − β 2 c 1 ,n ) /β 2 with β 1 ∈ (0 , 1) which is satisfiable only if β 2 > (1 − c 1 , n − 1) / (1 + c 1 ,n ) . W e now interpret Statement (ii), which we believe is the key result of the theorem. A similar conclusion can be drawn for Statement (iii) but we omit this due to spatial limitations. In order to make centre node v 1 lose social dominance, the dissent subject nodes v n − 1 and v n must adopt a cooperative strate gy . From their definitions, we can interpret β 1 as the trust giv en by v n − 1 to v n while β 2 is the trust giv en by v n to v n − 1 . A necessary condition for individual v n to hav e social power greater than centre node v 1 is that β 2 > P n − 2 i =2 c 1 ,i . This means that not only must v n − 1 trust v n sufficiently (as giv en by the inequality β 1 > (1 − c 1 ,n ) / ( c 1 ,n − 1 + β 2 ) ), but individual v n must r ecipr ocate by ensuring that it trusts v n − 1 sufficiently ( β 1 > P n − 2 i =2 c 1 ,i ). Unless the two dissenting nodes build a cooperati ve and sufficiently strong bilateral relationship, centre node v 1 will remain socially dominant. E. T opology V ariation 5: Leadership Group W ith β 1 = c 1 ,n +1 ∈ (0 , 1) and β 2 = c n +1 , 1 ∈ (0 , 1) , the following result is obtained Theorem 6. F or a social network with T opology V ariation 5, with initial conditions x ( s ) ∈ e ∆ n + m , and described by the DeGr oot-F riedkin model, the following statements ar e true: (i) F or all β 1 ∈ (0 , 1) and for all β 2 ∈ (0 , 1) there holds x ∗ i < x ∗ 1 and x ∗ k < x ∗ n +1 for i ∈ { 2 , ..., n } and k ∈ { n + 2 , ..., n + m } . (ii) Ther e holds x ∗ 1 < x ∗ n +1 or x ∗ 1 > x ∗ n +1 if and only if β 2 < β 1 or β 2 > β 1 r espectively . If β 1 = β 2 , then x ∗ 1 = x ∗ n +1 . (iii) F or k ∈ { n + 2 , ..., n + m } there holds x ∗ k > x ∗ 1 if and only if c n +1 ,k ( β 1 /β 2 ) > 1 . F or i ∈ { 2 , ..., n } , holds x ∗ i > x ∗ n +1 if and only if c 1 ,i ( β 2 /β 1 ) > 1 . Statement (ii) shows that the ratio of β 1 /β 2 determines whether centre node v 1 or centre node v n +1 is socially dominant. Statement (iii) delivers a surprising and interesting result on how leaders can cooperatively protect themselves and maintain collectiv e social dominance. Let i ∈ { 2 , ..., n } and k ∈ { n + 1 , ..., n + m } . Consider from centre individual v 1 ’ s point of vie w . While x ∗ i < x ∗ 1 is guaranteed, in order to ensure that v 1 has greater social power than subject v k (i.e. subjects of centre individual v n +1 ), individual v 1 must ensure that c n +1 ,k ( β 1 /β 2 ) < 1 . This inequality al ways holds, regardless of the value of c n +1 ,k < 1 , if β 1 = β 2 . I.e. if the trust level v 1 accords to v n +1 is equal to the trust lev el v n +1 0 0.2 0.4 0.6 0.8 1 0 0.2 0.4 0.6 0.8 1 Value of x i at Equilibrium, x i * β 1 = c 78 Center Node v 1 Subject v 2 Subject v 7 Attacker v 8 Fig. 7. Simulation of T opology V ariation 1 with n = 8 . accords to v 1 , regardless of the magnitude of β 1 = β 2 , v 1 has greater social power than all subject nodes including the subjects of v n +1 . It can appear to be surprising because this holds even if c n +1 ,k >> β 1 , β 2 . Y et such a result is intuitive if we consider β 1 /β 2 as the ratio of the trust v 1 places on v n +1 (and indirectly the trust v 1 places on subject v k ) versus the trust v n +1 places on v 1 (and indirectly the trust v k places on v 1 ). I V . S I M U L A T I O N S In this section, we provide 2 short simulations to highlight some of our most interesting results. W e do not pro vide comprehensiv e simulations for each T opology V ariation due to spatial limitations. Firstly , we simulate T opology V ariation 1 as it is the fundamental strategy , with n = 8 . The top ro w of the matrix C is given by [0 , 0 . 15 , 0 . 15 , 0 . 2 , 0 . 05 , 0 . 15 , 0 . 3 , 0] . Figure 7 sho ws the social power at equilibrium x ∗ i , for selected indi viduals, as a function of β = c 78 . Centre v 1 loses social dominance when β > 0 . 7 as stated in Theorem 2. Next, we simulate T opology V ariation 4 to show the need for cooperation between two dissenting individuals in order to displace the centre node. The top row of C is [0 , 0 . 1 , 0 . 1 , 0 . 2 , 0 . 05 , 0 . 05 , 0 . 2 , 0 . 3] . Figure 8 shows the social power at equilibrium x ∗ i , for selected individuals as a function of β 1 = c 78 when β 2 = 0 . 49 (i.e. when β 2 < P n − 2 i =2 c 1 ,i ). In accordance with Theorem 5, Statement (ii), dissent subject v 8 nev er achie ves social power greater than centre v 1 because there does not exist a β 1 ∈ (0 , 1) satisfying the required inequality . Figure 9 shows the same simulation scenario but no w with β 2 = 0 . 55 > P n − 2 i =2 c 1 ,i . In accordance with Statement (ii) of Theorem 5, x ∗ 8 > x ∗ 1 when β 1 > 0 . 93 . V . C O N C L U S I O N S Social networks with a star topology conv erge to an autocratic configuration, with the centre individual holding all the social power , as the number of issues discussed tend tow ards infinity . This paper proposed a number of different strategies, in volving introduction of new individuals and/or new interpersonal relationships into the social network, in order to move social dominance from the centre individual to a subject individual. Necessary and sufficient conditions 0 0.2 0.4 0.6 0.8 1 0 0.2 0.4 0.6 0.8 1 Value of x i at Equilibrium, x i * β 1 = c 78 Center Node v 1 Subject v 2 Dissent Subject v 7 Dissent Subject v 8 Fig. 8. Simulation of T opology V ariation 4 with n = 8 , when β 2 < P n − 2 i =2 c 1 ,i . 0 0.2 0.4 0.6 0.8 1 0 0.2 0.4 0.6 0.8 1 X: 0.9306 Y: 0.3348 Value of x i at Equilibrium, x i * β 1 = c 78 Center Node v 1 Subject v 2 Dissent Subject v 7 Dissent Subject v 8 Fig. 9. Simulation of T opology V ariation 4 with n = 8 , when β 2 > P n − 2 i =2 c 1 ,i . are de veloped, and interpretation of these conditions showed the strategies are sociologically intuitive. Numerous future directions exist. Firstly , we wish to generalise the results on uncoordinated attack and coordinated attack to arbitrary numbers of attacker nodes. Different leadership groups, and dissent topologies will also be e xplored. W e also wish to in vestigate whether such straightforward strategies exist for more general topologies, and lastly we shall study strategies concerning social power for a subgroup of individuals. A P P E N D I X P R O O F S F O R S E C T I O N I I I In the following proofs, we make extensi ve use of The- orem 1, and in particular Statement (ii), which states that x ∗ i > x ∗ j ⇔ γ i > γ j and that x ∗ i = x ∗ j ⇔ γ i = γ j . A. Theor em 2 and Cor ollary 1 The e xpression γ > = γ > C , where C is gi ven in (7), allows us to obtain γ 1 = n − 2 X i =2 γ i + (1 − β ) γ n − 1 (8a) γ i = c 1 i γ 1 , ∀ i 6 = 1 , n − 1 , n (8b) γ n − 1 = c 1 ,n − 1 γ 1 + γ n (8c) γ n = β γ n − 1 (8d) Statement (i) is obtained from (8b), where we conclude γ i < γ 1 because c 1 i < 1 for all i 6 = 1 , n − 1 , n , and from (8d), which allows us to conclude that γ n < γ n − 1 for all β ∈ (0 , 1) . For Statement (ii), begin by substituting γ n from (8d) into (8c), which yields γ n − 1 = c 1 ,n − 1 γ 1 + β γ n − 1 . This is rearranged to obtain γ 1 = 1 − β c 1 ,n − 1 γ n − 1 (9) Recalling that 0 < c 1 ,n − 1 and 0 < β < 1 , it follows that γ 1 < γ n − 1 if and only if β > 1 − c 1 ,n − 1 . Similarly , one can obtain that γ 1 > γ n if and only if β < 1 / (1 + c 1 ,n − 1 ) , which prov es Statement (iii). Corollary 1 is a generalisation of Statement (ii) obtained by observing that ar gmin j (1 − c 1 ,j ) = argmax j c 1 ,j . B. Theor em 3 and Cor ollary 2 For T opology V ariation 2, the relativ e interaction matrix C is given by C ( β ) = 0 c 12 c 13 . . . c 1 ,n − 1 0 0 1 0 0 . . . 0 0 0 1 0 0 . . . 0 0 0 . . . . . . . . . . . . . . . . . . . . . 1 − ( β 1 + β 2 ) 0 0 . . . 0 β 1 β 2 0 0 0 . . . 1 0 0 0 0 0 . . . 1 0 0 (10) From γ > C = γ > , we obtain γ 1 = n − 3 X i =2 γ i + (1 − β 1 − β 2 ) γ n − 2 (11a) γ i = c 1 i γ 1 , ∀ i 6 = 1 , n − 2 , n − 1 , n (11b) γ n − 2 = c 1 ,n − 2 γ 1 + γ n − 1 + γ n (11c) γ n − 1 = β 1 γ n − 2 (11d) γ n = β 2 γ n − 2 (11e) Statement (i) is obtained from (11a) and (11d) and (11e), using the same arguments as the proof for Theorem 2. Regarding Statement (ii), substitute (11d) and (11e) into (11c) and rearrange to obtain γ n − 2 = c 1 ,n − 2 γ 1 / (1 − β 1 − β 2 ) . The statement is then straightforwardly obtained. For State- ment (iii), in regards to γ n , substitute γ n − 2 = c 1 ,n − 2 γ 1 / (1 − β 1 − β 2 ) into the right hand side of (11e) to obtain γ n = β 2 c 1 ,n − 2 γ 1 / (1 − β 1 − β 2 ) . It is straightforward to verify that β 2 > (1 − β 1 ) / (1 + c 1 ,n − 2 ) implies β 2 c 1 ,n − 2 / (1 − β 1 − β 2 ) > 1 , which in turn implies γ n > γ 1 . The inequality that ensures γ n − 1 > γ 1 can be similarly found. Observe that 1 − β 1 < 1 , 1 − β 2 < 1 and 1 < 1 + c 1 ,n − 2 . There must also hold β 1 + β 2 < 1 . This implies that for any value c 1 ,n − 2 , there always exist β 1 , β 2 which ensures γ n − 1 > γ 1 and γ n > γ 1 . Regarding Statement (iv), from (11d) and (11e), we have γ n − 1 /γ n = β 1 /β 2 . The statement is then straightforwardly obtained. Corollary 2 is a generalisation of Statement (ii) by observing that argmin j (1 − c 1 ,j ) = argmax j c 1 ,j . C. Theor em 4 The relative interaction matrix is giv en by C ( β 1 , β 2 ) = 0 c 1 , 2 · · · c 1 ,n − 3 c 1 ,n − 2 0 0 1 0 · · · 0 0 0 0 . . . . . . . . . . . . . . . . . . . . . 1 − β 1 0 · · · 0 0 β 1 0 1 − β 2 0 · · · 0 0 0 β 2 0 0 · · · 1 0 0 0 0 0 · · · 0 1 0 0 (12) and the equation γ > C = γ > yields the following equalities: γ 1 = (1 − β 1 ) γ n − 3 + (1 − β 2 ) γ n − 2 + n − 4 X i =2 γ i (13a) γ i = c i γ 1 , i ∈ { 2 , . . . , n − 4 } (13b) γ n − 3 = c 1 ,n − 3 γ 1 + γ n − 1 (13c) γ n − 2 = c 1 ,n − 2 γ 1 + γ n (13d) γ n − 1 = β 1 γ n − 3 (13e) γ n = β 2 γ n − 2 (13f) From (13b), since c 1 ,i ∈ (0 , 1) for all i ∈ { 2 , . . . , n − 4 } , it follows that γ i < γ 0 for all i ∈ { 2 , . . . , n − 4 } . From (13e) and (13f), since β 1 , β 2 ∈ (0 , 1) , it follows that γ n − 1 < γ n − 3 and γ n < γ n − 2 . Thus, statement (i) is true. From (13c) and (13e), we have γ n − 3 γ 1 = c 1 ,n − 3 1 − β 1 , which implies that γ 1 > γ n − 3 if and only if β 1 < 1 − c 1 ,n − 3 . Similarly , from (13d) and (13f), we have γ 1 > γ n − 2 if and only if β 2 < 1 − c 1 ,n − 2 . It is then straightforward to conclude that for i ∈ { 1 , 2 } , if β i > 1 − c 1 ,n − 4+ i , then x ∗ n − 4+ i > x ∗ 1 . Therefore, statement (ii) is true. From (13c) and (13e), we have γ n − 1 γ 1 = β 1 c 1 ,n − 3 1 − β 1 . It follows that γ n − 1 > γ 1 if and only if β 1 > 1 / (1 + c 1 ,n − 3 ) . Similarly , from (13d) and (13f), we hav e γ n > γ 1 if and only if β 2 > 1 / (1 + c 1 ,n − 2 ) . Thus, statement (iii) is true. Since γ n − 3 γ 1 = c 1 ,n − 3 1 − β 1 and γ n − 2 γ 1 = c 1 ,n − 2 1 − β 2 , it follows that γ n − 3 (1 − β 1 ) /c 1 ,n − 3 = γ n − 2 (1 − β 2 ) /c 1 ,n − 2 , which implies that γ n − 3 γ n − 2 = c 1 ,n − 3 (1 − β 2 ) c 1 ,n − 2 (1 − β 1 ) . Then, γ n − 3 > γ n − 2 if and only if 1 − β 2 1 − β 1 > c 1 ,n − 2 c 1 ,n − 3 . Therefore, statement (iv) is true. D. Theor em 5 For T opology V ariation 4, the relativ e interaction matrix C is expressed as C ( β 1 , β 2 ) = 0 c 12 c 13 . . . c 1 ,n − 1 c 1 ,n 1 0 0 . . . 0 0 . . . . . . . . . . . . . . . . . . 1 − β 1 0 0 . . . 0 β 1 1 − β 2 0 0 0 β 2 0 (14) where β 1 = c n − 1 ,n and β 2 = c n,n − 1 . The expression γ > C = γ > yields the following equalities γ 1 = n − 2 X i =2 γ i + (1 − β 1 ) γ n − 1 + (1 − β 2 ) γ n (15a) γ i = c 1 i γ 1 , ∀ i 6 = 1 , n − 1 , n (15b) γ n − 1 = c 1 ,n − 1 γ 1 + β 2 γ n (15c) γ n = c 1 ,n γ 1 + β 1 γ n − 1 (15d) Again, Statement (i) is obtained trivially from (15b). Substi- tute (15c) into (15d) and rearrange for γ n to obtain γ n = c 1 ,n + β 1 c 1 ,n − 1 1 − β 1 β 2 γ 1 (16) and it follows that γ n > γ 1 is implied by c 1 ,n + β 1 c 1 ,n − 1 > 1 − β 1 β 2 (17) β 1 > 1 − c 1 ,n c 1 ,n − 1 + β 2 (18) β 2 > 1 − c 1 ,n − c 1 ,n − 1 β 1 β 1 (19) Consider (18). Observe that (1 − c 1 ,n ) / ( c 1 ,n − 1 + β 2 ) ≥ 1 ⇔ 1 − c 1 ,n − c 1 ,n − 1 ≥ β 2 ⇔ P n − 2 i =2 c 1 ,i ≥ β 2 . Recalling that β 1 ∈ (0 , 1) , we conclude γ n > γ 1 is possible only if β 2 > P n − 2 i =2 c 1 ,i . Alternativ ely , one can consider (19) and similarly deriv e that γ n > γ 1 if β 2 > (1 − c 1 ,n − β 1 c 1 ,n − 1 ) /β 1 and β 1 > (1 − c 1 ,n ) / (1 + c 1 ,n − 1 ) . The inequality conditions for ensuring γ n − 1 > γ 1 are also deriv ed in similar manner and omitted due to spatial limitations. E. Theor em 6 The relative interaction matrix for T opology V ariation 5 is giv en by C ( β 1 , β 2 ) = 0 c 12 c 13 . . . β 1 0 . . . 0 1 0 0 . . . 0 0 . . . 0 . . . . . . . . . . . . . . . . . . . . . . . . 1 0 0 . . . 0 0 . . . 0 β 2 0 0 . . . 0 c n +1 ,n +2 . . . c n +1 ,n 0 0 0 . . . 1 0 . . . 0 . . . . . . . . . . . . . . . . . . . . . . . . 0 0 0 . . . 1 0 . . . 0 (20) And the expression γ > C = γ > yields the following equal- ities γ 1 = X 1
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment