Towards Resilient UAV: Escape Time in GPS Denied Environment with Sensor Drift
This paper considers a resilient state estimation framework for unmanned aerial vehicles (UAVs) that integrates a Kalman filter-like state estimator and an attack detector. When an attack is detected, the state estimator uses only IMU signals as the …
Authors: Hyung-Jin Yoon, Wenbin Wan, Hunmin Kim
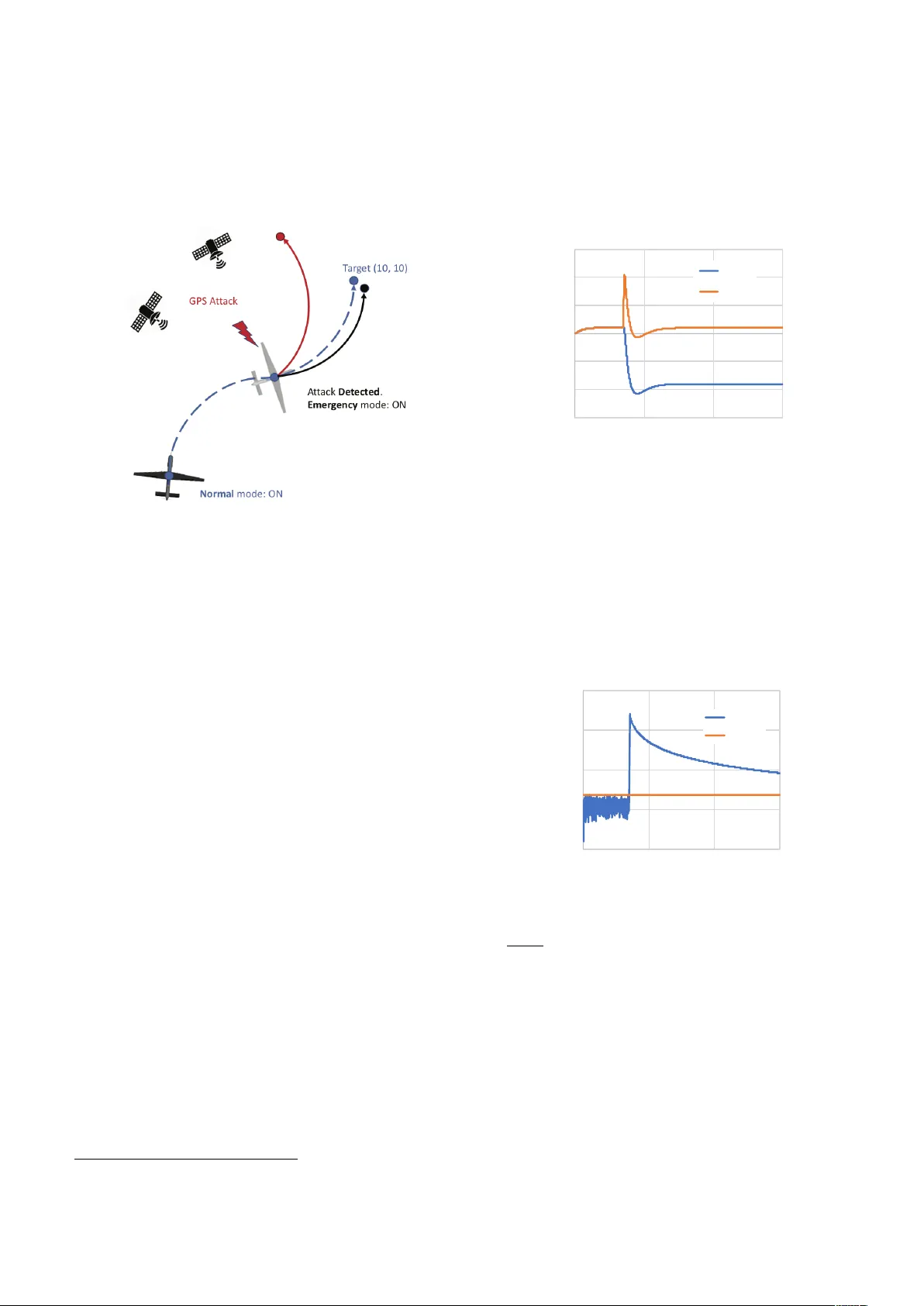
T o w ards Resilien t UA V: Escap e Time in GPS Denied En vironmen t with Sensor Drift ? Hyung-Jin Y o on, W en bin W an, Hunmin Kim, Naira Ho v akim y an ∗ Lui Sha ∗∗ , P etros G. V oulgaris ∗∗∗ ∗ Dep artment of Me chanic al Scienc e and Engine ering, ∗∗ Dep artment of Computer Scienc e, ∗∗∗ Dep artment of A er osp ac e Engine ering, University of Il linois at Urb ana-Champ aign (UIUC), Urb ana, IL 61801, USA. (email: { hyo on33, wenbinw2, hunmin, nhovakim, lrs, voulgari } @il linois.e du) Abstract: This pap er considers a resilien t state estimation framew ork for unmanned aerial v ehicles (UA Vs) that in tegrates a Kalman filter-like state estimator and an attac k detector. When an attac k is detected, the state estimator uses only IMU signals as the GPS signals do not con tain legitimate information. This limited sensor av ailabilit y induces a sensor drift problem questioning the reliabilit y of the sensor estimates. W e prop ose a new resilience measure, esc ap e time , as the safe time within which the estimation errors remain in a tolerable region with high probability . This pap er analyzes the stability of the prop osed resilien t estimation framew ork and quan tifies a low er bound for the escap e time. Moreo v er, sim ulations of the UA V mo del demonstrate the p erformance of the prop osed framew ork and pro vide analytical results. Keywor ds: Resilient estimation, Sto c hastic system, Unmanned aerial vehicle 1. INTR ODUCTION Unmanned aerial v ehicles (UA Vs) hav e b ecome p opular as commercial, industrial and educational platforms. The mec hanical simplicity and agile maneuverabilit y app eal to man y applications, such as media production, in- sp ection, and precision agriculture. In all these applica- tions, UA Vs need reliable state estimation (e.g. p osition, v elo cit y) to p erform v arious tasks. Most state estima- tion tec hniques for UA Vs use an inertial measurement unit (IMU) and a global p ositioning system (GPS) re- ceiv er. Ho w ever, GPS is vulnerable to sp oofing attac ks as demonstrated in W arner and Johnston (2003). In W arner and Johnston (2003), the V ulnerabilit y Assessment T eam at Los Alamos National Lab oratory demonstrated that GPS sp oofing attac ks can be easily implemen ted b y civil- ians using GPS satellite sim ulator. F urthermore, increas- ing applications of UA Vs extend the area of op eration to the urban areas, where GPS signals are w eak or denied due to other structures suc h as skyscrap ers, elev ated high wa ys, and bridges. Resilien t UA V na vigation requires timely attack detec- tion and mitigation. F rom controls p erspective, tradi- tionally the GPS sp oofing attac k has b een mo deled as a malicious signal injection. Attac k detection researc h against malic ious signal injection has b een studied ex- tensiv ely for the last several y ears. The attac k detection problem was formulated as an ` 0 / ` ∞ optimization prob- ? This work has b een supported by the National Science F ounda- tion (ECCS-1739732 and CMMI-1663460). lem in F a wzi et al. (2014); Pa jic et al. (2014). In Mo et al. (2014), an activ e detection scheme, by adding random disturbance signal to the optimal con trol input, w as prop osed to increase the detection rate trading off for optimalit y . In Mo et al. (2010), the authors iden tify maxim um deviations of the state due to the sensor at- tac ks, while remaining stealthy due to the detection. On the other hand, since the GPS signal injected by the attac ker w ould cause a discrepancy in the raw an tenna signal, the GPS sp oofing attack can b e detected b y examining the raw signal received by the antenna. F or example, the shap e of the GPS signal strength in p olar co ordinates w as used to detect the GPS attac k in McMilin et al. (2014). In Chen et al. (2013), an array of GPS an tenna w as used to detect the discrepancy compared to the normal situations. The metho ds using the ra w GPS signals in McMilin et al. (2014); Chen et al. (2013) ha v e the potential to detect the stealthy attacks defined in Mo et al. (2010). How ever, the metho ds using the raw antenna signals usually require mo difications of the hardw are or the low-lev el computing mo dules. Un biased state estimation in adv ersarial environmen ts can b e challenging, b ecause the estimator accumulates errors due to attac ks. In suc h cases, simple state detec- tion can b e a preferred metho d. Incomplete list of the related results includes Mo et al. (2010); P a jic et al. (2014); Y ong et al. (2015); Kim et al. (2017). In these efforts, the difference b et ween the measured output and the predicted output has b een used to detect attac ks and exclude corrupted sensor measurements. The rest of the uncompromised redundan t sensors are subsequen tly used for estimation. W e depart from this approach and consider limited sensor redundancy . In particular, the UA V mo del becomes undetectable in GPS-denied envi- ronmen ts. GPS denied state estimation has b een studied in F uke and Krotk o v (1996); Chung et al. (2001); Bevly and Parkinson (2007), wherein the fo cus is on estab- lishing the system output matrices that can b e used for standard (error state) Kalman filter for dead rec koning. Con tribution. This paper prop oses a resilien t estima- tion framework for UA Vs. The framew ork consists of an attac k detection mo dule and a state estimator that op erates in tw o mo des: (1) normal and (2) emergency . In the normal mo de, all av ailable sensor signals are used to estimate the state. In the emergency mo de, only IMU signals are fed to the state estimator. The limited sensor a v ailability leads to the sensor drift problem, and the estimates bec ome gradually unreliable. W e quantify a new resilience measure, the escape time, which is defined b y the safe time within which the estimation errors remain within a tolerable region with a high probabil- it y . W e analyze the stabilit y of the prop osed estimator and find a low er bound of the escape time. Sim ulations are conducted to show the effectiveness of the prop osed framew ork. The remainder of this pap er is organized as follows: In Section 2, we introduce the notation conv en tion in our pap er and the dynamic system model. In the same section, w e formulate the problem. In Section 3, w e prop ose a resilient state estimation and detection metho d for GPS attack detection. Section 4 presen ts the stabilit y analysis of the prop osed estimator, and studies escap e time to a void instabilit y . The significance of the escap e time and the p oten tial impact of it are described in Section 5. In Section 6, a numerical sim ulation of a UA V under GPS sp oofing attack is presented. 2. PRELIMINARIES This section discusses some preliminary notations/no- tions, system mo dels, problem formulation, and χ 2 at- tac k detector. 2.1 Notations W e use the subscript k of x k to denote the time index; R n denotes the n-dimensional Euclidean space; R n × m denotes the set of all n × m real matrices; A > denotes the transp ose of matrix A ; I denotes the identit y matrix with an appropriate dimension; k · k denotes the standard Euclidean norm for vector or an induced matrix norm; E [ · ] denotes the exp ectation op erator; × is used to denote matrix multiplication when the m ultiplied terms are in differen t lines. 2.2 System mo del W e use the follo wing linear mo del to consider the fligh t system dynamics and the attac ker mo del: x k = Ax k − 1 + Bu k − 1 + w k − 1 y G k = C G x k + d k + v G k y I k = C I ( x k − x k − 1 ) + v I k , (1) where x k ∈ R n , y G k ∈ R m G , y I k ∈ R m I are the state, the GPS measuremen t, and the IMU measurement, re- sp ectiv ely . IMU returns a noisy measurement of the state difference. The noise signals w k , v G k , v I k are assumed to b e indep endent and iden tically distributed (i.i.d.) Gaus- sian random v ariables with zero means and co v ariances E [ w k w > k ] = Σ w , E [ v G k ( v G k ) > ] = Σ G , E [ v I k ( v I k ) > ] = Σ I , resp ectiv ely . The vector d k ∈ R m G is the GPS spo ofing attac k, which is unkno wn to the defender. W e assume that the attac ker can inject any signal d k in to y G k . 2.3 Pr oblem formulation Giv en the system (1) with t wo sensors GPS and IMU, the defender aims to detect the GPS sp oofing attack and resilien tly estimate the state. F urthermore, the defender needs to analyze the reliability of the state estimates in the adv ersarial situation. 2.4 χ 2 attack dete ctor F or linear systems in (1) with Gaussian additiv e noises w k , v G k , and v I k , state estimations of the standard Kalman filter (KF) are Gaussian as w ell. Through this observ ation, the χ 2 statistical test is widely used in attac k detection, T eixeira et al. (2010); Mo et al. (2014); Guo et al. (2018), to distinguish whether the error is induced by statistical noises or attac ks. In particular, the χ 2 test has t wo hypothesis: H 0 : d k = 0 , H 1 : d k 6 = 0 . (2) By testing (2), we interpret the result as the following: (1) Rejecting H 0 (accepting H 1 ): there is significant evidence that the error is not zero and the error can b e due to the attack. (2) Keeping H 0 : we do not ha ve enough evidence to b eliev e that there is an attac k. 3. RESILIENT ST A TE ESTIMA TION DESIGN The prop osed estimation and detection system consists of the attack detector and the state estimator. The attack detector p erforms a statistical h ypothesis test to decide whether the GPS signal is b eing attack ed, based on output prediction error and error-cov ariance estimated b y the state estimator. Dep ending on the result of the hypothesis testing, the state estimation switches its mo de b et ween the normal mo de and the emer gency mo de . In the normal mo de, the state estimator uses b oth GPS and IMU to estimate the state and detect an attac k. If an attack is detected, the estimator switches to emergency mode, where IMU is used to estimate the state. If the attack detector determines that the GPS signals are clean, the state estimation can return to the normal mo de. 3.1 Normal mo de State estimation. The defender implemen ts an esti- mator and χ 2 detector to estimate the state and detect Fig. 1. A resilient state estimation framework consisting of GPS attack detection and tw o mo des (normal and emergency) state estimation. the GPS sp oofing attack. The follo wing KF-lik e state estimator is used to estimate the curren t state: ˆ x k = A ˆ x k − 1 + Bu k − 1 + K G k ( y G k − C G ( A ˆ x k − 1 + Bu k − 1 )) + K I k ( y I k − C I ( A ˆ x k − 1 + Bu k − 1 − ˆ x k − 1 )) P k = ( A − K k CA + K k DC ) P k − 1 ( A − K k CA + K k DC ) + ( I − K k C ) Σ w ( I − K k C ) > + K k Σ y K > k , f ( P k − 1 , K k ) , (3) where K k = [ K G k , K I k ], C = C G C I , Σ y = Σ G 0 0 Σ I , D = 0 0 0 I . The optimal gain K k can b e obtained by solving the follo wing problem: min K k tr ( P k ) , whic h is an uncon- strained conv ex optimization problem. By taking its deriv ativ e with resp ect to decision v ariable K k and set- ting it equal to zero, w e hav e ( A − K k CA + K k DC ) P k − 1 ( − CA + DC ) > − ( I − K k C ) Σ w C > + K k Σ y = 0 , and the solution is K k = ( AP k − 1 ( CA − DC ) > + Σ w C > ) × ( CA − DC ) P k − 1 ( CA − DC ) > + CΣ w C > + Σ y − 1 , g ( P k − 1 ) . (4) A ttack detection. W e implemen t χ 2 statistic test in (2) using CUSUM (CUm ulative SUM) algorithm, w hic h is widely used in change detection research Page (1954); Barnard (1959); Lai (1995). Before prop osing a detection algorithm, we consider some prop erties of attac k vector estimates. Since d k = y G k − C G x k − v G k , given the previous state estimate ˆ x k − 1 b y the state estimator, we estimate the attack v ector b y comparing the sensor output and the output prediction: ˆ d k = y G k − C G ( A ˆ x k − 1 + Bu k − 1 ) . The curren t estimate ˆ x k should not b e used, because it is correlated with the curren t output; i.e., E [ ˆ x k y G k ] 6 = 0. Due to the Gaussian noises w k and v k injected to the linear system in (1), the state estimates follo w Gaussian distribution, since an y finite linear combination of Gaussian distributions is also Gaussian. Similarly , ˆ d k is Gaussian as well, and thus the use of χ 2 test (2) is justified. The χ 2 test compares the normalized attac k v ector estimate ˆ d > k ( P d k ) − 1 ˆ d k with χ 2 d f ( α ): Accept H 0 if ˆ d > k ( P d k ) − 1 ˆ d k ≤ χ 2 d f ( α ) Accept H 1 if ˆ d > k ( P d k ) − 1 ˆ d k > χ 2 d f ( α ) , (5) where P d k , E [ ˜ d k ˜ d > k ] = C G ( AP k − 1 A > + Σ w )( C G ) > + Σ G , and χ 2 d f ( α ) is the threshold found in the Chi-square table. In χ 2 d f ( α ), d f denotes the degree of freedom, and α denotes the statistical significance level. The prop osed χ 2 CUSUM detector is characterized by the detector state S k ∈ R : S k = δ S k − 1 + ( ˆ d k ) > ( P d k ) − 1 ˆ d k , S 0 = 0 , (6) where 0 < δ < 1 is the pre-determined forgetting factor. The attac k detector will raise an alarm if S k > ∞ X i =0 δ i χ 2 d f ( α ) = χ 2 d f ( α ) 1 − δ . Remark 3.1. Comparing to standard CUSUM algo- rithm in P age (1954), the prop osed CUSUM detector has asymptotic b eha vior, where the impact of the attacks on the detector state S k deca ys asymptotically . 3.2 Emer gency mo de When an attack is detected, the defender switches emer- gency mode on. Let us denote k a the time when the attac k is detected, which satisfies S k a > χ 2 d f ( α ) 1 − δ . As w ell as normal mode, the state estimation and attac k detection contin ue in normal mo de. How ev er, the state estimation can only use the output measured by IMU in emergency mo de. Without GPS output, IMU based estimation accum ulates error and even tually diverges as w e analyze in the following section. State estimation. The state estimation algorithm (3) with K G k = 0 is used to recursively estimate the state ˆ x k and the error co v ariance P k . A ttack detection. At each time k , the CUSUM detec- tor (6) is used to up date the detector state S k and detect the attack. The corresp onding co v ariance can b e found b y P d k , E [ ˆ d k ˆ d > k ] = C G ( AP k − 1 A > + Σ w )( C G ) > + Σ G . If S k < χ 2 d f ( α ) 1 − δ , then it returns to the normal mo de. 4. ST ABILITY AND ESCAPE TIME This section presents analysis on stability of the state estimation and estimation error escap e time. 4.1 Stability analysis of state estimation In this section, we would like to discuss stability and instabilit y conditions of the prop osed estimator. T ow ard this end, we show that the estimator is stable in the normal mo de, and unstable in the emergency mo de. In particular, the state estimate ˆ x k obtained through observ er (3) is unbiased. Moreov er, its cov ariance is b ounded, if ( C G , A ) is detectable, as shown in the follo wing theorem. Theorem 4.1. Giv en E [ ˆ x 0 ] = x 0 , we ha ve E [ ˆ x k ] = x k for all k ≥ 0. If ( C G , A ) is detectable, then P k is b ounded. Pro of. State estimation error ˜ x k = x k − ˆ x k can be describ ed by ˜ x k = A ˜ x k − 1 + K G k ( A ˜ x k − 1 + w k − 1 + v G k ) + K I k ( C I ( A ˜ x k − 1 − ˜ x k − 1 + w k − 1 ) + v I k ) . Notice that E [ w k ] = 0, E [ v G k ] = 0, and E [ v I k ] = 0. Giv en E [ ˆ x 0 ] = x 0 , we ha ve E [ ˆ x 1 ] = x 1 b y (7). Assume E [ ˆ x k − 1 ] = x k − 1 , then E [ ˆ x k ] = x k b y (7). By induction, w e conclude that E [ ˆ x k ] = x k for ∀ k . Therefore, E [ ˆ x k ] = x k . Consider P k ( K G k , K I k ), where we emphasize the dep en- dency of P k on K G k , K I k . With K I k = 0, P k ( K G k , 0) is b ounded by Corollary 5.2 in Anderson and Moore (1981), b ecause ( C G , A ) is detectable. Since K k is chosen opti- mal, we hav e P k ( K G k , K I k ) ≤ P k ( K G k , 0). This completes the pro of. If the GPS signals are not av ailable for state estimation, the co v ariance of the state estimation is expected to b e unstable ov er time under Assumption 4.1. Let us first define necessary notations: ¯ C I , C I ( I − A − 1 ), ¯ A , ( I − L ¯ C I ) A and L , Σ w ( C I A − 1 ) > (( ¯ C I + ¯ C I A − 1 ) Σ w ( C I A − 1 ) > + Σ I ) − 1 . Assumption 4.1. Matrix A is in v ertible, and the pair ( ¯ C I , ¯ A ) is not detectable. Remark 4.1. Assumption 4.1 is satisfied with the dou- ble integrator mo del with IMU, whic h is widely used to design navigation con troller for UA Vs as in Kerns et al. (2014). In this case, ¯ C I = C I ( I − A − 1 ) = 0, and ¯ A = A , where A is not asymptotically stable. Then, the pair ( ¯ C I , A ) is not detectable and it fulfills Assumption 4.1. Theorem 4.2. Assume K G k = 0. Then, under Assump- tion 4.1, P k is increasing un b oundedly . Pro of. W e prov e the statemen t b y finding an equiv alen t Kalman filtering problem, and then use the existing stabilit y result for the KF in Anderson and Mo ore (1981). Giv en K G k = 0, the state estimation error up date law can b e obtained from (3): ˜ x k = A ˜ x k − 1 − K I k ( C I ( I − A − 1 ) A ˜ x k − 1 + C I w k − 1 + v I k ) = A ˜ x k − 1 − K I k ( C I ( I − A − 1 ) A ˜ x k − 1 + C I ( I − A − 1 ) w k − 1 + C I A − 1 w k − 1 + v I k ) . The abov e state estimation error up date is the Kalman filter solution of x k = Ax k − 1 + w k − 1 y k = ¯ C I x k + ¯ v I k , where ¯ v I k , C I A − 1 w k − 1 + v I k . How ev er, the pro- cess noise and the me asuremen t noise are coupled; i.e., E [ w k − 1 ¯ v > k ] = Σ w ( A − 1 ) > ( C I ) > 6 = 0. Then, the optimal gain is different from the Kalman gain used in the stan- dard KF. T o decouple the noises, it is a common practice to add zero term L ( y k − ¯ C I x k − ¯ v I k ) to the state equation ab o v e: x k = Ax k − 1 + w k − 1 + L ( y k − ¯ C I ( Ax k − 1 + w k − 1 ) − ¯ v I k ) = ( I − L ¯ C I ) Ax k − 1 + Ly k + ( I − L ¯ C I ) w k − 1 − L ¯ v I k = ¯ Ax k + ¯ u k + ¯ w k , where ¯ u k = Ly k , and ¯ w k − 1 = ( I − L ¯ C I ) w k − 1 − L ¯ v I k . The gain L is chosen such that the pro cess noise and measuremen t noise are decoupled: E [ ¯ w k ¯ v > k ] = ( I − L ¯ C I − L ¯ C I A − 1 ) Σ w ( C I A − 1 ) > − LΣ I = 0 , where the solution is L = Σ w ( C I A − 1 ) > (( ¯ C I + ¯ C I A − 1 ) Σ w ( C I A − 1 ) > + Σ I ) − 1 . No w, the state estimation error update la w (3) and its co v ariance up date law (3) with K G k = 0 are the Kalman filtering solution of x k +1 = ¯ Ax k + ¯ u k + ¯ w k y k = ¯ C I x k + ¯ v I k , where the pro cess noise and the measurement noise are decoupled from eac h other. Under Assumption 4.1, P k is unstable by Corollary 5.2 in Anderson and Moore (1981). This completes the pro of. Remark 4.2. Stabilit y with GPS (Theorem 4.1) and instabilit y without GPS (Theorems 4.2) are generalized in to a system with any relativ e sensors. This is b e- cause output mo del y I k in (1) can represent an y relative measuremen t sensor mo del regardless of their internal error state dynamic. This is a sharp contrast to existing analytical result. F or example, it is a common practice to in tro duce error state v ariables for IMU as in Bevly and P arkinson (2007). Using their specific system and output mo del, one can chec k detectability of the augmen ted system to guarantee stability/instabilit y . How ever, it is not generalized b ecause eac h system has different sys- tem/output(sensor) matrices. 4.2 Esc ap e time of the state estimation err or This section prop oses a new resilience measure, the es- cap e time, and analyzes the escap e time in the emergency mo de. It has b een rev ealed in Theorem 4.2 that the state estimation b ecomes less trustful, if GPS signals are compromised for a long time. Therefore, the UA V should escap e from the GPS spo ofer at a certain time before the estimation b ecomes unreliable. F ormally , we define the escap e time as follows. Definition 4.1. The escap e time k esc ≥ 0 is the time difference b et w een the attack time k a and the first time instance when the estimation error x k − ˆ x k ma y not b e in tolerable error distance ζ ∈ R n with the significance α , i.e. k esc = arg min k ≥ k a k − k a s . t . ζ > P − 1 k ζ < χ 2 d f ( α ) . Giv en the desired confidence level α , the degree of freedom d f , we hav e χ 2 d f ( α ). Since the optimal gains K k a , K k a +1 , · · · can b e found in adv ance at k = k a , the corresponding cov ariance matrices P k a , P k a +1 , · · · can also b e found b y the cov ariance up date la w in (3). Algorithm 1 presents escap e time calculation. Giv en k a , the state estimation errors ma y not remain in the tolerable region with the predetermined confidence α after k esc . Algorithm 1 Escap e time calculation Input: k a , α , d f , ζ ; R eturn: k esc ; 1: k = k a ; 2: while ζ T P − 1 k ζ > χ 2 d f ( α ) do 3: k = k + 1; 4: end while 5: k esc = k − k a . If ¯ C I = 0 as in Remark 4.1, then a low er b ound of the escap e time can also be found before actually operating the UA V as shown in Theorem 4.3. Let P denote the stationary p oin t of the co v ariance up date (3), i.e. P = f ( P , g ( P )) , where f ( · ) and g ( · ) were defined in (3) and (4) resp ec- tiv ely . Matrices used in the theorem are defined by ¯ Σ , ( I − K I k C I ) Σ w ( I − K I k C I ) > + K I k Σ I ( K I k ) > . Theorem 4.3. Assume ¯ C I = 0 and GPS spo ofing attac ks start after P k con verges to P . Then, a low er b ound of the escap e time can b e found by • F or k A k 6 = 1, k esc ≥ 1 log k A k 2 log k ζ k 2 χ 2 d f ( α ) + k ¯ Σ k k A k 2 − 1 k P k + k ¯ Σ k k A k 2 − 1 • F or k A k = 1, k esc ≥ ( k ζ k 2 /χ 2 d f ( α ) − k P k ) / k ¯ Σ k . Pro of. First, we derive an upp er b ound on k P k k . As- sume k a = 0 and P 0 = P without loss of generality . Giv en K G k = 0, the cov ariance up date law can b e ob- tained from (3): P k = AP k − 1 A > + ¯ Σ , P 0 = P , (7) where ¯ Σ is time-inv arian t b ecause the optimal K I k is time-in v ariant: K I k = Σ w ( C I ) > ( C I Σ w ( C I ) > + Σ I ) − 1 . Applying basic matrix norm prop ert y to (7), w e hav e k P k k ≤ k A k 2 k P k − 1 k + k ¯ Σ k , k P 0 k = k P k . By recursiv ely applying the b ound ab o v e, we hav e k P k k ≤ k A k 2 k k P 0 k + k ¯ Σ k k − 1 X i =0 k A k 2 i (8) No w, w e will apply the bound (8) to the χ 2 test equation. F or the p ositiv e definite matrices P k , w e hav e k P k k − 1 k ζ k 2 = λ min ( P − 1 k ) k ζ k 2 ≤ ζ > P − 1 k ζ , and th us the time k ∆ that v erifies ( k A k 2 k ∆ k P 0 k + k ¯ Σ k k ∆ − 1 X i =0 k A k 2 i ) − 1 k ζ k 2 = χ 2 d f ( α ) (9) is a low er b ound of the escape time k ∆ ≤ k esc . If k A k = 1, then k ζ k 2 /χ 2 d f ( α ) = k P 0 k + k ∆ k ¯ Σ k , whic h prov es the theorem. If k A k 6 = 1, by the sum of geometric series, equation (9) b ecomes k ζ k 2 /χ 2 d f ( α ) = k A k 2 k ∆ k P 0 k + k ¯ Σ k k A k 2 k ∆ − 1 k A k 2 − 1 . (10) By taking log on both sides, we hav e the desired result. 5. DISCUSSION As a new resilience measure, the escap e time provides a new criterion for optimal path planning with increasing uncertain ties. In this section, we discuss relev an t prob- lems. Landing position + + + k=0 k=2 k=1 k ≤ k esc Uncertainty To l e r a n c e Position est. … Fig. 2. Illustration of path planning problem considering the increasing uncertain ties Once an attack is detected, the UA V is exp ected to land on a secure p osition in the pre-calculated escap e time if p ossible. The path planning problem illustrated in Figure 2 can b e formulated as O ptimal path planning pr oblem s . t . x k esc = x landing position where the UA V should arriv e at the landing position b efore the escap e time. On the other hand, if a secure landing p osition is not a v ailable, the UA V is exp ected to escap e from the sp oofer within the escap e time. If the output p o w er of the GPS sp oofing signal is time inv ariant, the defender is able to sp ot the sp oofer through measuremen t of the GPS signal strength (e.g., signal-to-noise ratio) with corresp onding state estimates. Then, the problem of in terest b ecomes O ptimal path planning pr oblem s . t . P ( k x k esc − x spo ofer k > c safe ) > γ , where x spo ofer is the lo cation of the spo ofer, c safe is a pre- determined distance such that the GPS sp oofing signal cannot affect the UA V, and γ < 1 denotes the desired certain ty . 6. SIMULA TIONS W e sim ulate scenarios, where a UA V gets a GPS sp oofing attac k during a fligh t to a target p osition. In the first scenario, we simulate a system without attac k detector, where the UA V k eeps using the normal state estimator in Section 3.1 during the fligh t. In the second scenario, the UA V detects the attack and then switches to the emergency mo de as illustrated in Figure 3. Fig. 3. Illustration of the simulation scenario: (1) red line denotes the flight path with normal mo de under GPS attack; (2) black line denotes the path with emergency mo de. W e use a double in tegrator UA V dynamics under the GPS spo ofing attac k as in Kerns et al. (2014). The discrete time state vector x k considers planar p osition and v elo cit y at time step k , i.e. x k = [ r x k , r y k , v x k , v y k ] > , where r x k , r y k denote x, y p osition co ordinates, and v x k , v y k denote velocity co ordinates. With sampling time at 0 . 01 seconds, the double in tegrator mo del is discretized in to the follo wing matrices: A = 1 0 0 . 01 0 0 1 0 0 . 01 0 0 1 0 0 0 0 1 , B = 0 0 0 0 0 . 01 0 0 0 . 01 , and outputs y G and y I measure positions from GPS and IMU, resp ectiv ely , with the output matrices: C G = 1 0 0 0 0 1 0 0 , C I = 0 0 1 0 0 0 0 1 . The co v ariance matrices of the sensing and disturbance noises are c hosen as Σ w = 0 . 0001 I , Σ I = 0 . 001 I , Σ G = 0 . 001 I . In the scenarios, the UA V is mo ving to ward the target p osition with the co ordinates at (10 , 10) by using feed- bac k control 1 using the state estimate from the state estimator. The GPS attack happ ens at time step 700. The attac k signal is d = [100 , 100] > . 1 W e implemented a prop ortional-deriv ativ e (PD) like tracking controller, which is widely used for double integrator systems. 6.1 Standar d estimator (without attack dete ctor) As shown in Figure 4, the state estimation is deceived b y the GPS attack. The p osition co ordinate of the UA V actually conv erges tow ard ( − 90 , − 90), ho w ever, the state estimate sho ws it conv erges to the desired p osition at (10 , 10). -150 -100 -50 0 50 100 150 0 1000 2000 3000 X Coor dinate [m] Ti me St eps St at e Est imate Fig. 4. State and estimate under the GPS attack at k = 700. 6.2 Pr op ose d metho d The attack detector is able to detect the attack using the normalized attack vector as shown in Figure 5. In Figure 5, there is an evident spike of the detector state, whic h implies there is an attac k. Statistic significance of the attac k is tested using the CUSUM detector describ ed in (6) with the significance α at 1%. 1E-03 1E+00 1E+03 1E+06 1E+09 0 1000 2000 3000 Norm a liz ed A tta c k E s tim at e Ti me St eps St at i s t i c s Thresh ol d Fig. 5. Attac k detection: Statistics denotes S k defined in (6) of CUSUM detector. The threshold equals to χ 2 d f ( α ) 1 − δ with α = 0 . 01 and δ = 0 . 15. Based on the hypothesis test result, w e switch the system mo de to the emergency . As shown in Figure 6, the prop osed method mitigates the attack. Ho wev er, we also observ e the drift of estimate in Figure 6. The drift motiv ates us to estimate the b ounds of the drift. 6.3 Statistic al upp er b ound on err or and esc ap e time Using the cov ariance estimate P k and χ 2 test, we can calculate a confidence interv al as shown in Figure 7. The error magnitudes of 10 sample tra jectories are under the 99% confidence bound as shown in Figure 7. Note that 0 2 4 6 8 10 12 0 1000 2000 3000 X Coor dinate [m] Ti me St eps St at e Est imate Fig. 6. State and estimate with the attac k mitigation. the calculation of the confidence b ound is deterministic. Using Algorithm 1, we can calculate that it tak es 290 steps (escap e time) to reach the error threshold k ζ k = 2. Alternativ ely , we can calculate a lo wer bound of the escap e time according to Theorem 4.3. The low er b ound is at 257 steps whic h can b e v erified in Figure 7. Lower Boun d Esc a p i n g T i m e Threshold 700 Escape Time Lower Bound Fig. 7. The 99% confidence b ound with the prop osed metho d, i. e. q χ 2 d f ( α ) k P k k with α = 0 . 01, the upp er b ound calculated in Theorem 4.3, and 10 sample tra jectories ( gr ay colored) of k x k − ˆ x k k . 7. CONCLUSION This pap er studies resilient state estimation of UA Vs in GPS denied en vironmen t. The KF-like estimator has b een designed and χ 2 CUSUM algorithm is used to detect the attac k. In the presence of the attack, GPS signals are not used to estimate the state, because they do not contain v alid information. Due to the limited sensing device in the emergency mo de, the estimation suffers from the sensor drift problem. W e calculate a lo wer b ound of the escap e time, whic h is defined b y the safe time such that the estimation error remains in a tolerable region with a high probability . A simulation of the UA V demonstrates the results. REFERENCES Anderson, B. and Mo ore, J.B. (1981). Detectabilit y and stabilizability of time-v arying discrete-time linear systems. SIAM Journal on Contr ol and Optimization , 19(1), 20–32. Barnard, G.A. (1959). Con trol charts and sto c hastic pro cesses. Journal of the R oyal Statistic al So ciety. Series B (Metho dolo gic al) , 239–271. Bevly , D.M. and Parkinson, B. (2007). Cascaded k alman filters for accurate estimation of multiple biases, dead- rec koning na vigation, and full state feedback con trol of ground v ehicles. IEEE T r ansactions on Contr ol Systems T e chnolo gy , 15(2), 199–208. Chen, Y.H., Lo, S., Ak os, D.M., De Lorenzo, D.S., and Enge, P . (2013). V alidation of a controlled reception pattern antenna (CRP A) receiver built from inex- p ensiv e general-purp ose elements during sev eral liv e- jamming test campaigns. In Pr o c e e dings of the 2013 International T e chnic al Me eting of The Institute of Navigation, San Die go, California , 154–163. Ch ung, H., Ojeda, L., and Borenstein, J. (2001). Sen- sor fusion for mobile rob ot dead-reck oning with a precision-calibrated fiber optic gyroscope. In Pr o- c e e dings 2001 ICRA. IEEE International Confer enc e on R ob otics and Automation (Cat. No. 01CH37164) , v olume 4, 3588–3593. IEEE. F awzi, H., T abuada, P ., and Diggavi, S. (2014). Secure es- timation and control for cyb er-ph ysical systems under adv ersarial attacks. IEEE T r ansactions on Automatic Contr ol , 59(6), 1454–1467. F uke, Y. and Krotk ov, E. (1996). Dead rec koning for a lunar rov er on uneven terrain. In Pr o c e e dings of IEEE International Confer enc e on R ob otics and Au tomation , volume 1, 411–416. IEEE. Guo, P ., Kim, H., Virani, N., Xu, J., Zh u, M., and Liu, P . (2018). Rob oADS: Anomaly detection against sensor and actuator misb eha viors in mobile rob ots. In IEEE/IFIP International Confer enc e on Dep endable Systems and Networks (DSN) , 574–585. IEEE. Kerns, A.J., Shepard, D.P ., Bhatti, J.A., and Humphreys, T.E. (2014). Unmanned aircraft capture and control via GPS sp oofing. Journal of Field R ob otics , 31(4), 617–636. Kim, H., Guo, P ., Zh u, M., and Liu, P . (2017). Attac k- resilien t estimation of switched nonlinear cyb er- ph ysical systems. In Americ an Contr ol Confer enc e , 4328–4333. IEEE. Lai, T.L. (1995). Sequential changepoint detection in qualit y control and dynamical systems. Journal of the R oyal Statistic al So ciety. Series B (Metho dolo gic al) , 613–658. McMilin, E., De Lorenzo, D.S., W alter, T., Lee, T.H., and Enge, P . (2014). Single an tenna gps sp oof de- tection that is simple, static, instan taneous and back- w ards compatible for aerial applications. In Pr o c e e d- ings of the 27th international te chnic al me eting of the satel lite division of the institute of navigation (ION GNSS+ 2014), T amp a, FL , 2233–2242. Citeseer. Mo, Y., Chabukswar, R., and Sinop oli, B. (2014). De- tecting integrit y attacks on SCADA systems. IEEE T r ansactions on Contr ol Systems T e chnolo gy , 22(4), 1396–1407. Mo, Y., Garone, E., Casav ola, A., and Sinopoli, B. (2010). F alse data injection attacks against state estimation in wireless sensor net works. In IEEE Confer enc e on De cision and Contr ol , 5967–5972. P age, E.S. (1954). Con tinuous insp ection sc hemes. Biometrika , 41(1/2), 100–115. P a jic, M., W eimer, J., Bezzo, N., T abuada, P ., Sokolsky , O., Lee, I., and P appas, G.J. (2014). Robustness of attack-resilien t state estimators. In A CM/IEEE International Confer enc e on Cyb er-Physic al Systems , 163–174. T eixeira, A., Amin, S., Sandb erg, H., Johansson, K.H., and Sastry , S.S. (2010). Cyb er security analysis of state estimators in electric p o wer systems. In IEEE Confer enc e on De cision and Contr ol , 5991–5998. W arner, J.S. and Johnston, R.G. (2003). GPS spo ofing coun termeasures. Homeland Se curity Journal , 25(2), 19–27. Y ong, S.Z., Zhu, M., and F razzoli, E. (2015). Resilient state estimation against switching attacks on sto c has- tic cyb er-ph ysical systems. In IEEE Confer enc e on De cision and Contr ol , 5162–5169.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment