Secure Short-Packet Transmission with Aerial Relaying: Blocklength and Trajectory Co-Design
In this paper, we propose a secure short-packet communication (SPC) system involving an unmanned aerial vehicle (UAV)-aided relay in the presence of a terrestrial passive eavesdropper. The considered system, which is applicable to various next-genera…
Authors: Milad Tatar Mamaghani, Xiangyun Zhou, Nan Yang
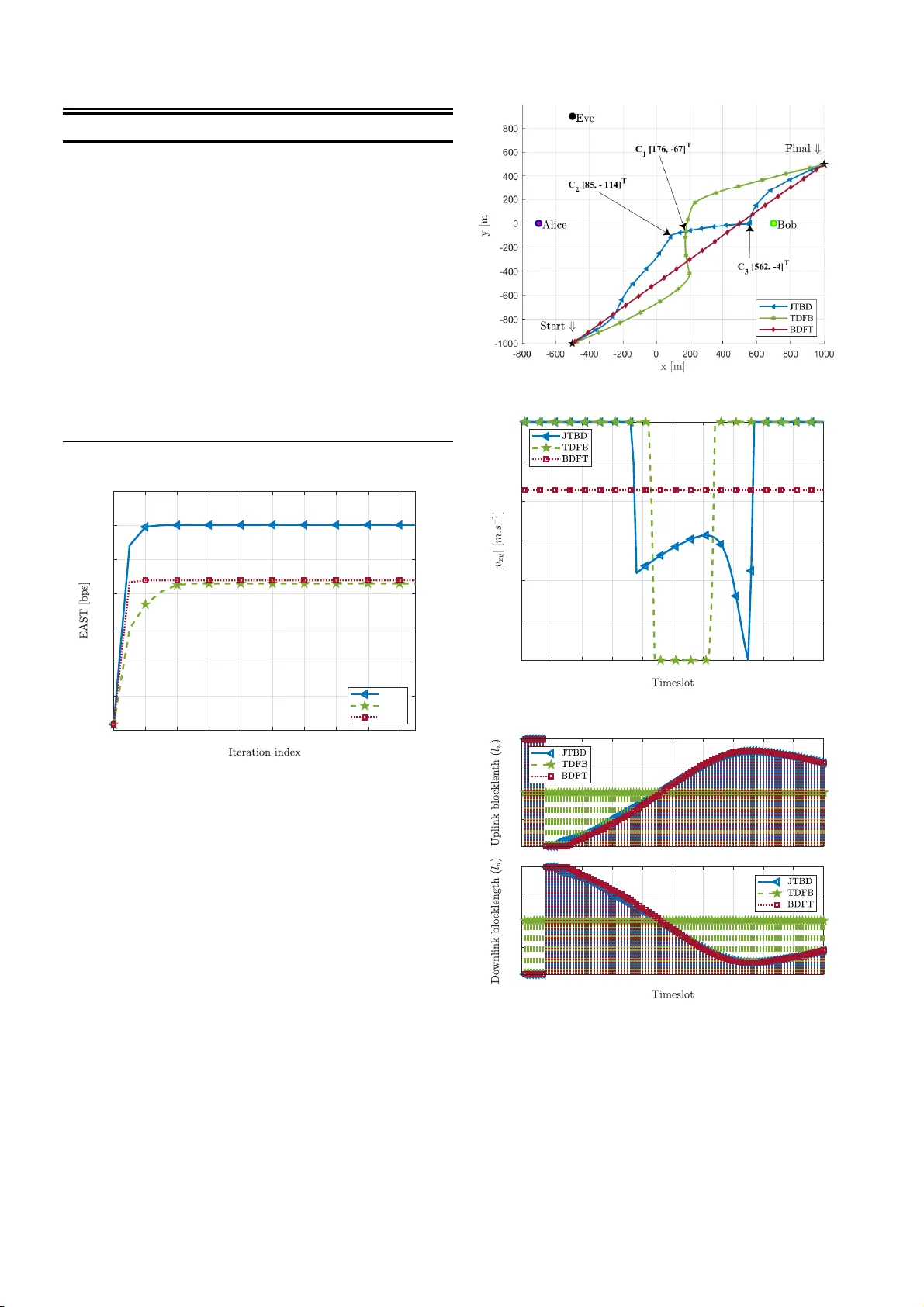
Secure Short-P ack et T ransmission with Aerial Relaying: Blocklength and T raj ectory C o -Design Milad T atar Mamaghani ∗ , Xiangyun Zhou ∗ , Nan Y ang ∗ , and A. Lee Swindlehurst † ∗ School of Engineerin g, Australian Nation al Un i versity , Canberra, A CT 2 6 01, Au stralia † Henry Samueli School of E n gineerin g, Uni versity o f Califo rnia, Ir v ine, CA 9 2697, USA Email: milad.tatarm amaghan i@anu.edu.au , xiang yun.zh ou@anu.ed u.au , nan.y ang@anu.e du.au , swindle@uci.ed u Abstract —In this paper , we pro pose a secur e short-packet communication (SPC) system in volving an unmanned aerial vehicle (U A V)-aided r elay in the presence of a terr estrial pas- siv e ea vesdro pper . Th e consid ered system, which is applicable to va rious next-generation Internet-of-Things (IoT) networks, exploits a U A V as a mo bile relay , facili t ating the re liable and secure exchange of intermittent short packets between a pair of remote IoT devices with strict latency . Our objective is to i mp ro ve the ov erall secrecy th roughput performa nce of the system by carefully designing key parameters such as the coding blocklengths and the U A V trajectory . Howe ver , this inherently poses a challenging optimization problem that is difficult to solve optimally . T o ad d ress the i ssue, we propose a low-complexity algorithm inspired by the block successive con vex approximation approach, where we divide the original problem into two sub problems and solve them alternately until con ver gence. Nu merical results demonstrate that the pro posed design achiev es significant performance impro vem ents relative to other benchmarks, and offer valuable insights into determining appropriate coding blocklengths and UA V trajectory . Index T erms —Beyond-5G networks, short-packet communi - cation, unmanned aerial vehicle, aerial r elaying, physica l-layer security , trajectory and blocklen gth optimization. I . I N T RO D U C T I O N Short-pac ket commun ication (SPC) is a cr itical compon e n t of emerging beyond-5G (B5G) wireless networks an d Inter net of Things (IoT) application s, wher e devices need to exchange short-packet data to fulfill low-latency and low-cost commu- nication requirem ents. On th e other ha nd, reduced cha n nel coding gain associated with short-packet tr a n smission poses a major hur d le to commu nication reliability in SPC. In addition, security issues such as eavesdropping in SPC-IoT networks are more pron ounced d ue to confide n tial an d sensiti ve SPC data that IoT ne twork s frequently need to share in an op en wireless en viron ment, particu lar ly for mission-cr itical scenar ios [ 1 ]– [ 3 ]. P hysical-lay er security (PLS) tech nolog y is a promising candidate for safeguarding SPC. PLS techniques exploit th e physical-lay er ch aracteristics of wireless channels or smart signaling for commu nication secrecy through wiretap cod- ing, without suffering from the high complexity of resour ce- demand in g key-based security metho d s [ 4 ]. This work was suppo rted by the Australia n Research Council’ s Discovery Project s funding scheme (project nu mber DP220101318). Nev ertheless, co n ventional PLS tech n iques adopt wiretap codes ba sed on the assumption o f infinite b lockleng ths. Sub- stantial stud ies h ave thus far been condu cted to secur e different wireless ne tworks working in the infinite blockleng th r egime (e.g., s ee [ 5 ], [ 6 ] an d reference s therein) . Ho wev er, SPC gen er- ally in volves the transmission of sho rt packets on the order of tens o f byte s as op posed to several kiloby tes in co nventional wireless systems. Consequently , PLS-based designs need to be me ticu lously revisited, as adopting the so-called Secrecy Capacity , i.e, a typica l perf ormance metric for conv ention a l PLS systems [ 7 ], is no longer applicab le for systems oper ating under SPC d ue to the finite blockleng th assumption. In light of th is, [ 8 ] f undam e n tally studied the attainab le secrecy rate (SR) in a wiretap channel with specific reliability and secrecy requirem ents u nder the finite blockleng th assumptio n. The authors in [ 9 ] and [ 10 ], developed PLS schemes for SPC assuming fading chan nels. The work in [ 11 ] holistically inves- tigated th e performance of secur e SPC in a mission -critical IoT system with an external adversary . Nevertheless, these s tudies have only considered system designs that inv olve stationary commun ication nodes an d adopted a fixed n umber of infor- mation bits per short-packet transm ission . C onsequ ently , th e approa c h es d ev eloped in [ 9 ]–[ 11 ] may not work well in h ighly dynamic scenarios or wh en the n umber of information bits generated for transmission by I oT devices varies. Unmanne d aerial vehicles (U A Vs), with their relati vely rapid on-dem and deployme nt, low-cost maintenance, and maneu- verability , can p otentially be used in a m yriad of wireless applications ran ging from serving as an aerial base station (BS) or mo bile relay f or rem ote sensing an d real- tim e mon ito ring in IoT networks [ 12 ]. Acco r dingly , it has been anticip ated that in- tegrating U A V technology in to forthco m ing B5G IoT systems is a cost-ef fective prom ising solution with sub stantial benefits. Due to their operation at r elativ ely high altitudes, U A Vs are particularly h e lpful in improving coverage b y redu cing signal attenuation in wire less links caused b y blockag e or shad owing. As a r esult, U A V -em powered wireless IoT systems, if prop erly designed, would req uire less power fo r tr a n smissions. This is specifically ben eficial for ene rgy -hung ry Io T networks since it expands their op erational lifetime. On the other han d, U A V - IoT scenarios are more susceptib le to eavesdropping attacks due to line-o f-sight (LoS)-domina nt air-groun d (AG) links [ 13 ]. Thus, securin g such systems presents significan t challenges, and of c o urse, requires f u rther r esearch. ©2023 IEEE. Personal use of t his material is permitted . Permi ssion from IE EE must be obtained for all other uses, in an y current or future media, including reprinti ng/republ ishing this material for a dverti sing or promotional purposes, creating ne w coll ecti ve wor ks, for resale or redistrib ution to servers or l ists, or reuse of any copyrigh ted component of this work in oth er w orks. Uplink transmiss ion Downlink transmission Uplink transmiss ion Downlink transmission Uplink transmiss ion Downlink transmission U A V - R e l a y E v e B o b A l i c e H H Uplink transmiss ion Downlink transmission U A V - R e la y UAV -Rela y Eve Bob Alic e H Fig. 1 : System mo del f or secure UA V -SPC rela y ing. T o ad dress the above-men tioned challenges, in this work we propo se a secure U A V -aided relayin g scheme with SPC, where sensiti ve short packets need to b e periodically transmitted from a remote IoT device to a designated receiver with a stringent latency re q uiremen t while combatin g passive eav es- dropp ing. W e form ulate a n ew optimizatio n problem for the considered UA V -aided SPC system un der security , re liab ility , latency , and mobility constraints. T he formulated problem is n o nconve x, and hence challeng ing to solve optim a lly . T o tackle the challen ging nonc o n vex problem , we apply the block succ essi ve conve x appro ximation (BSCA) approach to iterativ ely solve a sequ ence of conv ex subproblem s: coding blockleng th optimization and U A V trajectory design. W e then propo se a low-complexity algorithm combin in g these solutions to optim ize the system perf ormance . W e condu c t simulatio n s to draw som e u sef ul in sights in to the p e rforman ce of the propo sed jo int b lockleng th o ptimization and tr ajectory d esign, and highlight its secrecy p erform ance advantage compared to other competitive benchmark s. I I . S Y S T E M M O D E L A N D A S S U M P T I O N S As illustrated in Fig. 1 , we co nsider a UA V -aided IoT commun ication system with secure SPC, wherein a source (Alice) p e r iodically send s short p ackets containin g confidential informa tio n to a d esignated remote destination (Bob) via a mobile U A V -Relay (UR), while a p assi ve eavesdropper (Eve) attempts to overhe a r the ongoin g confidential transmissions. In practice, Alice perio d ically gen erates sh o rt-packet sensitive informa tio n from the environment and, if feasible, im m ediately transmits it to Bob with a stringent latency requir ement. W e assum e that a packet is generated at the beginning of each time slot and the p eriod o f each timeslot is δ t . W e also assume that Alice generates an d sends a v arying amount o f informa tio n bits durin g ea c h timeslot to han dle different task s such as monitorin g, contro llin g, or sensing. In this work , we assume that the d irect link between Alice and Bob is absen t du e to long distance o r b lockages, an d hence a U A V - mounted relay is employed to facilitate the end- to-end SPC. More over, we assum e that all the comm unication nodes are equ ipped with a single an tenna, as co m monly considered for low-cost and resource-constra ined IoT devices (see [ 14 ] and referen ces therein). In addition, the mobile relaying strat- egy adop ted by the UR is assumed to be the deco de-and - forward (DF) p rotocol with time division d uplexing (TDD), operating in a shared bandwidth W for both reception and transmission. W e assume that th e UR-aide d DF relaying for SPC occu rs at the b eginning of each timeslot δ t , which co nsists of two phases. I n the first phase (i.e., uplink transmission) in timeslot n , Alice gen erates a sho rt packet, containing sensiti ve informa tio n, and transmits the packet with fixed power p a to the UR over l u [ n ] chann el uses, where n = { 1 , 2 , · · · } denotes the ind ex of each timeslot, and then th e UR decode s the receiv ed signal to obtain the transmitted confiden tial message. In the second p hase (i.e., downlink transmission) in timeslot n , the UR encodes the o btained m essage fro m the first phase with a different co deboo k fo r secur ity pu rposes, forwarding the r esult to Bob over l d [ n ] ch annel u ses with fixed relaying power p r and Bob retrieves the original confiden tial informa tio n. While Eve wiretap s the ongoing transmissions in two p hases to obtain confid ential data, since the signals fro m both Alice and the UR ar e encoded with different codebooks, she c a n not explo it a div ersity co mbining strategy to imp rove her reception and po se stronger security threats. W e also note that the end-to -end SPC generally occupies much less time than one timeslot. Since the time taken f or o ne c h annel use is inversely prop o rtional to the av ailable ban dwidth, we have δ i [ n ] = l i [ n ] W ∀ n , where i ∈ { u, d } , an d δ i [ n ] indicates the time need ed for a finite blocklen g th SPC in e ither the uplink or downlink transmission. The three-dimen sio n al Cartesian coordina tes of Alice, Bob, and Eve are deno ted by q a = [ x a , y a , 0] T , q b = [ x b , y b , 0] T , and q e = [ x e , y e , 0] T , respectively , wher e [ · ] T represents the transpose operator . No te that all the commun ication node s are assumed to b e a pa r t of the same network; thu s, the location of the com munication nodes is perfectly known. Nonetheless, the in formatio n exch a nged between Alice and Bob sho u ld be kept secret fro m Eve for co nfidentiality purpo ses. W e a ssume that the UR’ s fligh t time ho rizon is set to T , and is split in to N timeslots such that T = N δ t . Sinc e the SPC duration is small, we assume that the UR’ s loc a tion o ver th e transmission ph ase in each timeslot remains approxim ately unch anged, but varies from o ne timeslot to another . Furthermo re, the altitude of the UR is fixed at H , which typically co rrespond s to the minimu m flying altitud e for bein g av oided by obstacles or mountaino us areas, establishing LoS-dom inant channel co mponen ts [ 14 ]. Therefo re, the UR’ s location in timeslot n can b e deno ted by q r [ n ] = [ x [ n ] , y [ n ] , H ] T . As such , the UR’ s continuou s trajectory ca n be appro ximated b y ( N + 1) waypo ints, i.e., { q r [ n ] } N n =1 . Assum ing that the UR’ s in itial and fin al loc ations are denoted by q i = [ x i , y i , H ] T and q f = [ x f , y f , H ] T , respectively , the following mobility constraints are imp osed on the UR tr a jectory: C 1 : q r [1] = q i , q r [ N ] = q f , (1a) C 2 : k q r [ n + 1] − q r [ n ] k ≤ v max δ t , n = 1 , · · · , N − 1 (1 b) where the constrain t C 2 limits the displacement o f the UR f or consecutive timeslo ts, and v max indicates the max imum flight velocity o f th e UR. The AG chan nels are a ssumed to be dominated by p ath-loss with negligible fading [ 6 ]. Thu s, for the Alice- UR lin k , the UR-Eve link, an d the UR-Bob link, d enoted as h r a [ n ] , h r e [ n ] , and h r b [ n ] ∀ n , respectively , we expr ess their Lo S-dominan t channel power gains as h r j [ n ] = β 0 k q r [ n ] − q j k 2 , ∀ n, j ∈ { a, e, b } (2) where β 0 denotes the p ath-loss at a r eference distanc e und e r omnidire ctional pr opagation . Furthermo re, since both Alice and Eve ar e terrestrial n odes, the ch annel mod e l fo r the Alice- Eve link constitute s both distance-de p endent attenuation and small-scale Ray le ig h fading [ 5 ], the power gain of which can be represente d as h ae [ n ] = β 0 k q a − q e k α ζ [ n ] , ∀ n (3) where ζ [ n ] is a unit-mean exponen tial ra n dom v ariable, and α is the corr espondin g en viron mental pa th-loss expo nent, with a typical range between 2 < α ≤ 4 . Delay tolera n ce in SPC is crucial as the co mmunicatio n system must deli ver sensitive infor m ation quickly to b e ef- fective. Thu s, for the con sid ered short-pa c ket delay -sensitiv e system, the requirement on delay tolerance can b e imposed b y constraining the num ber of total b lockleng th s p e r tr a nsmission to be less than the maximum allowable end -to-end d elay , expressed a s C 3 : X i l i [ n ] ≤ L max , l i [ n ] ∈ Z 0+ , i ∈ { u , d } , ∀ n (4) where L max denotes th e maximum latency toleran ce and Z 0+ represents the set of nonnegative integers. I I I . P RO B L E M F O R M U L A T I O N Let ε a n d η denote the network n ode’ s decoding err o r pr o ba- bility and infor mation leakag e, respectively . For simplicity , we also assume that the a d ditive white Gaussian n oise (A WGN) power at any no de is equal f o r all tim e slots and denoted by σ 2 . Consequen tly , we express the achievable av erage SR in bits per cha n nel use f or the short-p acket uplink transmission in timeslot n , ac cording to [ 8 ], as ˜ R sec u [ n ] = E ζ [ n ] n log 2 1 + γ r [ n ] 1 + γ ae [ n ] − s V ( γ r [ n ]) l u [ n ] Q − 1 ( ε ) − s V ( γ ae [ n ]) l u [ n ] Q − 1 ( η ) o , ∀ n (5) ( a ) ≈ log 2 1 + γ r [ n ] 1 + ¯ γ ae [ n ] − s V ( γ r [ n ]) l u [ n ] Q − 1 ( ε ) − s V ( ¯ γ ae [ n ]) l u [ n ] Q − 1 ( η ) ∆ = R sec u [ n ] , ∀ n (6) where E x {·} indica te s expec tation over the random variable x , and Q − 1 ( x ) is the in verse of th e complemen tary Gaussian cumulative distribution fun ction Q ( x ) , d efined as Q ( x ) = R ∞ x 1 √ 2 π e − r 2 2 dr . Moreover , γ r [ n ] and γ ae [ n ] , denoting the received signal-to- noise ratios (SNRs) at th e UR a nd Eve in timeslot n , ar e giv en re sp ectiv ely by γ r [ n ] = ρ a k q r [ n ] − q a k 2 , ∀ n (7) γ ae [ n ] = ρ a k q a − q e k α ζ [ n ] , ∀ n ( 8) Note that the appro ximation ( a ) in ( 6 ) follows from Jensen’ s inequality , and ¯ γ ae [ n ] = ρ a k q a − q e k α , where ρ a = p a β 0 σ 2 . Furthermo re, the fu nction V ( · ) indicates ch annel dispersion, which can b e mathematically expressed, accor d ing to [ 8 ], as V ( γ ) = lo g 2 2 ( e ) h 1 − (1 + γ ) − 2 i , ∀ n (9) Note that V ( γ ) is a monoton ically increasing functio n of the SNR γ . Like wise, the achievable SR for short-packet downlink transmission in timeslot n is g iv en by R sec d [ n ] = log 2 1 + γ b [ n ] 1 + γ r e [ n ] − s V ( γ b [ n ]) l d [ n ] Q − 1 ( ε ) − s V ( γ r e [ n ]) l d [ n ] Q − 1 ( η ) , ∀ n (10) where γ b [ n ] an d γ r e [ n ] deno te the received SNRs at Bob an d Eve in timeslot n , given respectiv ely by γ b [ n ] = ρ r k q r [ n ] − q b k 2 , ∀ n (11) γ r e [ n ] = ρ r k q r [ n ] − q e k 2 , ∀ n (12) with ρ r = p r β 0 σ 2 . Now , considering that Alice and the UR securely encod e the tr a n smit short-pa cket data in timeslot n to maintain th e desired reliab ility and secur ity r equiremen ts of the considered system ( ε, η ) , we d efine the secrecy thro u ghpu t metric a s the rate of the effecti ve num ber of secur e ly trans- mitted information b its in b its p er second (bps) as ¯ B s [ n ] = 1 − ε δ t h min( R sec u [ n ] l u [ n ] , R sec d [ n ] l d [ n ]) i + , ∀ n (13) where [ x ] + = max( x, 0) . Our objectiv e is to op timize the secr ecy perfo r mance of the p roposed U A V -SPC relaying system by d esigning the transmission blocklengths L = { l u [ n ] , l d [ n ] , ∀ n } , a nd th e UR traje c tory Q = { q [ n ] , ∀ n } . Th e resultin g optimization maximizes the Effectiv e A verage Sec r ecy Thro ughpu t ( EAST ) over the mission d uration, which is fo rmulated as ( P ) : max { L , Q } EAST = 1 N N X n =1 ¯ B s [ n ] s.t. C 1 − C 3 . (14) Note that ( P ) is a no nconve x optimizatio n problem d u e to the non conv ex objective fun ction with nonsmo oth operator [ · ] + , and highly coup led optimization variables. Thus, it is too challengin g to be solved optimally . First, we note that the nonsmoo thness of the objective f unction in ( P ) can be han dled since at the optim al point, ¯ B s [ n ] shou ld h old a nonnegative value. Otherwise, by setting l u [ n ] = 0 and /or l d [ n ] = 0 ( i.e., no transmission) in the given timeslot, one obtain s ¯ B s [ n ] = 0 , which violates the op timality . In light of this, we re m ove the nonsmoo thness oper ator from the ob jectiv e f u nction withou t impacting th e optimal solu tion. Here, introdu cing a slack variable vector τ τ τ = { τ [ n ] , ∀ n } , w e con vert ( P ) to a m ore tractable version, whose objective function is differentiable and serves as a lower bo und on that of the original problem: ( P 1) : max { L , Q , τ τ τ } 1 − ε T N X n =1 τ [ n ] s.t. C 1 − C 3 , (15a) R sec u [ n ] l u [ n ] ≥ τ [ n ] , ∀ n (15b) R sec d [ n ] l d [[ n ] ≥ τ [ n ] , ∀ n (15c) In the fo llowing, we p ropose a low-comp lexity iterative so- lution to solve ( P 1) based on the BSCA alg orithm, wherein we o ptimize each block of variables while keeping o thers unchan ged in an alternating m anner . Such an a lgorithm gen er- ally ap proach es a locally optimal s olution b ut with guaranteed conv ergence. I V . P RO P O S E D S O L U T I O N In this sectio n , we divide ( P 1) into two sub problem s: i) short-packet block le n gth op tim ization, and ii) UR tra je c tory optimization . Thereafter, we pro pose an ef ficient overall it- erative algor ith m. Note that in the seq uel, we om it the fixed multiplicative term 1 − ε T from the ob jectiv e functio n , which h as no impact o n the proposed solu tio n. A. S hort-pa ck et Blocklength Optimizatio n In this subsection, we optimize the block length vec- tors of both the uplink an d downlink SPC, i.e., L = { l u [ n ] , l d [ n ] , ∀ n } , while keeping other variables fixed. As such, the correspon ding subprob lem can be written as ( P 2) : max L , τ τ τ N X n =1 τ [ n ] s.t. C 3 , ( 15b ) , ( 15c ) . (16) Note that ( P 2) is a non linear integer pr o grammin g, which is in gene ral a challenging NP-hard problem. Ne vertheless, analyzing the objective function of ( P 2), we see that it is non-d ecreasing with respect to L , implying tha t the con straint C 3 shou ld b e satisfied with equality at the o ptimal point, i.e., l u [ n ] + l d [ n ] = L max ∀ n ; o therwise, inc reasing the blocklen g th leads to an incr ease in the ob jectiv e functio n, which v iolates the optim ality . Hence, we can solve ( P 2) v ia a simple 1D search over the discrete set L = { 0 , 1 , 2 · · · , L max } to obtain the optimal b lockleng th s for the u plink tr a nsmissions: l opt u [ n ] = arg max x ∈L ¯ B s [ n ] l u [ n ]= x,l d [ n ]= L max − x , ∀ n (17) Then, the optimal block lengths for the downlink tran smissions can be determined by l opt d [ n ] = L max − l opt u [ n ] ∀ n. B. UR T rajectory Op timization This subsection explores the joint optimiza tion of the UR’ s motion and altitude. In light of this, we recast ( P 1) to o p timize Q , while keeping the othe r variables fixed, which g iv es ( P 3) : max { q r , τ τ τ } N X n =1 τ [ n ] s.t. C 1 − C 2 , (18a) log 2 (1 + γ r [ n ]) − b 0 p 1 − (1 + γ r [ n ]) − 2 ≥ b 2 τ [ n ] + b 1 , ∀ n (18b) log 2 1 + γ b [ n ] 1 + γ r e [ n ] − c 0 p 1 − (1 + γ b [ n ]) − 2 − c 1 p 1 − (1 + γ r e [ n ]) − 2 ≥ c 2 τ [ n ] , ∀ n (18c) where b 0 = Q − 1 ( ε ) log 2 e p l u [ n ] , b 2 = 1 l u [ n ](1 − ε ) , b 1 = log 2 (1 + γ ae [ n ]) − s V ( γ ae [ n ]) l u [ n ] Q − 1 ( η ) , c 0 = Q − 1 ( ε ) log 2 e p l d [ n ] , c 1 = Q − 1 ( η ) log 2 e p l d [ n ] , c 2 = 1 l d [ n ](1 − ε ) . W e stress that ( P 3) is still a no nconve x op tim ization pr oblem due to no nconve x con stra ints ( 18b ) an d ( 18c ). In the follow- ing, we fo cus on tran sforming these constrain ts in to conve x approx imates to make the pr oblem tractable. 1) Con vex r eformulation of ( 18b ) : W e equiv alently write ( 18b ) in a more tractable way by introd ucing nonn egative slack variables λ λ λ = { λ 1 [ n ] , λ 2 [ n ] , ∀ n } and β β β = { β 1 [ n ] , ∀ n } , as log 2 (1 + λ 1 [ n ]) − b 0 β 1 [ n ] ≥ b 2 τ [ n ] + b 1 , ∀ n (19a) ρ a λ 2 [ n ] ≥ k q r [ n ] − q a k 2 , ∀ n (19b) λ 1 [ n ] λ 2 [ n ] ≤ 1 , ∀ n (19c) β 2 1 [ n ] ≥ 1 − (1 + λ 1 [ n ]) − 2 , ∀ n (19d) W e note that the con straints ( 19a ) and ( 19b ) are conve x, while the additiona l constrain ts ( 1 9c ) an d ( 19d ), introdu ced to en su re the smo othness of ( P 3), ar e no nconve x. W e stress that ( 19b )- ( 19d ) shou ld hold with eq uality at the op tim al p oint. Before proceed ing further, we pr esent a lemm a b elow . Lemma 1. Let f ( x, y ) = 1 xy with x, y > 0 . A t an y given poin t ( x 0 , y 0 ) in the domain of f , the following func tion serves as a global lower b ound on f ( x, y ) [ 15 ], i.e., f lb ( x, y ; x 0 , y 0 ) = − x y 0 + x 0 y − 3 x 0 y 0 x 0 2 y 0 2 ≤ f ( x, y ) . (20) Thus, at a given point ( q lo r , λ λ λ lo , β β β lo ) , the conve x approx i- mations of the constraints ( 19c ) an d ( 19d ) are 1 ≤ f lb ( λ 1 [ n ] , λ 2 [ n ]; λ lo 1 [ n ] , λ lo 2 [ n ]) , ∀ n (21a) ln( β 1 [ n ]) + ln(1 + λ 1 [ n ]) ≥ g ( λ 1 [ n ]; λ lo 1 [ n ]) , ∀ n (21b) where the conv ex function g ( x ; x 0 ) is defined as g ( x ; x 0 ) = A 0 ( x 0 ) + A 1 ( x 0 ) ( x − x 0 ) , with A 0 ( x ) and A 1 ( x ) being defined f or x > 0 as A 0 ( x ) = 1 2 ln ( x [2 + x ]) and A 1 ( x ) = x + 1 x ( x + 2) , respectively . Here, ( 21a ) follows f rom Lemma 1 and ( 21 b ) follows from the concavity of the logarithm function. 2) Con vex reformulation of ( 18c ) : Intro d ucing the non- negativ e slack variables ω ω ω = { ω 1 [ n ] , ω 2 [ n ] , ∀ n } , ψ ψ ψ = { ψ 1 [ n ] , ∀ n } , u = { u 1 [ n ] , ∀ n } , and v = { v 1 [ n ] , v 2 [ n ] , ∀ n } , we refo rmulate ( 18c ) into appr oximate conve x co nstraints, using Lemma 1 and [ 14 , Lem ma 3 ], as log 2 (1 + ω 1 [ n ]) − log 2 1 + u − 1 1 [ n ] ≥ c 0 ψ 1 [ n ] + c 1 v 1 [ n ] + c 2 τ [ n ] , ∀ n (22a) 1 ≤ f lb ( ω 1 [ n ] , ω 2 [ n ]; ω lo 1 [ n ] , ω lo 2 [ n ]) , ∀ n (22b) ρ r ω 2 [ n ] ≥ k q r [ n ] − q b k 2 , ∀ n (22c) ln( ψ 1 [ n ]) + ln(1 + ω 1 [ n ]) ≥ g ( ω 1 [ n ]; ω lo 1 [ n ]) , ∀ n (22d) ρ r u 1 [ n ] ≤ 2 q lo r [ n ] − q e T q r [ n ] + d lo 0 [ n ] , ∀ n (22e) ln( v 1 [ n ]) + ln(1 + v 2 [ n ]) ≥ g ( v 2 [ n ]; v lo 2 [ n ]) , ∀ n (22f) u 1 [ n ] ≥ v − 1 2 [ n ] , ∀ n (22g) where d lo 0 [ n ] = k q e k 2 − k q lo r [ n ] k 2 and ( q lo r , ω ω ω lo , ψ ψ ψ lo , v lo , u lo ) is the g iv en local point. W e n ow express the conv ex r eformu - lation of subprob lem ( P 3) as ( P 3 . 1) : max { q r , τ τ τ ,λ λ λ,β β β , ω ω ω , ψ ψ ψ, u , v } N X n =1 τ [ n ] s.t. C 1 − C 2 , ( 19a ) , ( 19b ) , ( 2 1 ) , ( 22 ) . (23) Since ( P 3 . 1) is con vex, it ca n b e efficiently solved by stan dard conv ex optimization tools such as CVX [ 16 ]. C. Overall Iterative Algo rithm In this subsection, w e propose an o verall iterativ e algorithm based on the seque ntial block o ptimization summ arized in Algorithm 1 . Algorithm 1 : Overall EAST optimization a lg orithm. 1: Initialize: Iter ation index i = 0 , choo se a feasible local p oint ( L ( i ) , Q ( i ) ); 2: Repeat: 2.1: Calculate EAST ( i ) , update i ← i + 1 ; 2.2: Solve ( P 2 ) via ( 17 ), th en u pdate L ( i ) = { l ( i ) u [ n ] , l ( i ) d [ n ] , ∀ n } ; 2.3: Gi ven L ( i ) , initialize slack variables λ λ λ lo , β β β lo , ω ω ω lo , ψ ψ ψ lo , u lo , v lo , and solve ( P 3. 1 ), then update Q ( i ) = { q ( i ) r [ n ] = [ x ( i ) r [ n ] , y ( i ) r [ n ] , H ] T , ∀ n } ; 2.4: Calcu la te E AST ( i ) at the new point L ( i ) , Q ( i ) ; 3: Until: k EAST ( i ) − EAST ( i − 1) k ≤ ǫ ; It can be proved that the proposed algorithm is guarante e d to c on verge to a local o ptimum com mencing from a feasible point. Mo reover , th e time comp lexity of Algo rithm 1 , b ased on the co mplexity of each co n vex subpro blem and the conv er- gence ac c uracy par a meter ǫ , can be ap proxim ately obtained as O N 3 . 5 log 2 ( 1 ǫ ) , where O ( · ) repr e sen ts big-O notation. The overall co mplexity o rder of Algo rithm 1 is polyno mial, and thus o u r prop osed approa ch can be reasonably imp lemented for energy-limited U A V - IoT scenar ios with SPC. V . N U M E R I C A L R E S U LT S A N D D I S C U S S I O N In this section, we d emonstrate the EAST enhan cement achieved by o ur pro posed optimizatio n algorithm fo r the considered U A V -aided SPC-IoT scenario. T o exhibit the ef- fectiveness of our join t trajectory a n d block length design in Algorithm 1 , labeled J TBD , we co mpare it with the fo llowing benchm a rk schemes: • T rajectory Design with Fixed B locklen g th ( TDFB ): With fixed cod ing block lengths, o nly the UR trajectory is optimized using ( P 3.1) in a sequential man n er . • Blocklength Design with Fixed T rajectory ( BDFT ): Keeping the UR tr ajectory fixed, o nly th e op tim ization of blocklength s is taken via solvin g ( P 2) using ( 17 ). T ab le I lists the system parameters used in this section, unless otherwise stated. Th ese p a r ameters are ma in ly a d opted in the literature such as in [ 2 ] and [ 14 ]. I n addition , th e initial f easible trajectory of the UR, Q (0) , is taken to be on a direc t line with fixed speed from the initial lo c ation to the final locatio n. The uplink and downlink tran smission blo cklength s p er timeslot are initialized as l (0) u [ n ] = l (0) d [ n ] = L max 2 ∀ n . Fig. 2 depicts the EAST perf ormance against th e iteration index for all sch emes to verify the quick co n vergence of Algorithm 1 and the v alidity of our an alysis, as well as to demonstra te the performan ce advantage o f our jo in t design . W e observe fro m the figure that th e EAST is non - decreasing T ABLE I: System parameters Simulati on parameter (notation) V alue Tra nsmit po wer ( p a ) 20 dBm Relay ing po wer ( p r ) 20 dBm Refere nce channel po wer gain ( β 0 ) − 70 dB T errestrial path-lo ss exp onent ( α ) 3 Channe l noise po wer ( σ 2 ) − 140 dBm Tra nsmission period ( δ t ) 1 s Maximum late ncy toleranc e ( L max ) 400 Mission time ( T ) 100 s U A V’ s altit ude ( H ) 60 m Maximum flying spee d ( v max ) 30 m/s U A V’ s initia l locat ion ( q i ) [ − 500 , − 1000 , 60] T m U A V’ s final loca tion ( q f ) [1000 , 500 , 60] T m Alice ’ s location ( q a ) [ − 700 , 0 , 0] T m Bob’ s location ( q b ) [700 , 0 , 0] T m Eve’ s locati on ( q e ) [ − 500 , 900 , 0] T m Decodin g error probabi lity ( ε ) 10 − 3 Informati on leakag e paramet er ( η ) 10 − 2 Con verge nce threshold ( ǫ ) 10 − 3 0 2 4 6 8 10 12 14 16 18 60 70 80 90 100 110 120 130 JTBD TDFB BDFT Fig. 2: EAST v s. iteration index. over the iteration index for all algo rithms, and that co n vergence occurs q uickly in just a few iteration s. Our prop osed JTBD ap- proach ach iev es the be st EAST perfo rmance among st all. For example, JTBD can reach up to 120 bps, appr oximately 14% more th an both the BDFT and TDFB designs, and nearly twice the EAST of the in itial feasible setting. Also, Fig . 2 shows that using the baseline trajector y and optim izing transmission blockleng ths is mor e imp ortant for SPC than optimizing the trajectory with fixed blo c klengths, while the joint design o f both is clearly pr eferable concern ing the EAST perfor mance metric. Fig. 3 illustrates the trajecto ry an d veloc ity pro files of the UR, as well as bo th the uplink and downlink short- p acket blockleng ths for the specific re a lization of the user location s based o n different d esign scen arios. W e observe from Fig s. 3 ( a ) and 3 ( b ) that in contrast to the other schem es, for (a) UR’ s trajectory profile. 0 10 20 30 40 50 60 70 80 90 100 0 5 10 15 20 25 30 (b) UR’ s velocity vs. timeslot. 0 100 200 300 400 100 200 300 400 0 10 20 30 40 50 60 70 80 90 100 (c) Blocklengths vs. timeslot. Fig. 3: Designed UR’ s tr ajectory and velocity profiles, and coding blockleng ths accord in g to different schemes. TDFB th e UR attem pts to fly with the max imum velocity while head ing tow ards a position between Alice and Bob lo - cated at th e coord inate C 1 = [176 , − 67 , 60] T m, and h overing at that point as long as possible, i.e., between T = 44 s and T = 62 s. This solution g reatly imp roves the EAST comp ared with the initial dir e ct-path trajectory with fixed veloc ity , but not as m u ch as BDFT and our proposed JTBD . W e also observe fro m Fig. 3 ( c ) that when th e UR is farther fro m Bob, larger d ownlink coding blocklengths are ad opted, and they red uce in length as the UR ap proach es Bob . As the UR flies away from Alice, the propo sed algor ith m efficiently increases the up link block length, which ultimately enh ances the EAST . Interestingly , th e blocklength designs o f both JTBD an d BDFT follow a very similar trend, even thoug h their corr espondin g trajectories are different. Nevertheless, when bo th the trajectory desig n and blockleng th optimiza tion are taken into acc o unt as in the p r oposed JTBD design , the UR demonstra te s effective navigation and ability to co n siderably enhance the EAST compared to oth er be n chmark s. Specifi- cally , the effecti ve trajecto r y for th e JTBD scheme requires the UR to fly with full speed from the initial location q i to the po sition m a rked as C 2 = [85 , − 114 , 60] T m, accord ing to the path illustrated in Fig. 3 ( a ). Then, a sharp velocity drop occurs at T = 3 6 s, enablin g the UR to move with relativ ely low sp eed from the position C 2 to a location with the coo rdinate C 3 = [5 6 2 , − 4 , 60] T m, for improvin g the overall E AST perfo rmance. Finally , the UR tra vels thro ugh an arc path tilted aw ay from Bob while maximally increasin g its velocity at timeslot T = 75 s and ma in taining this velocity so that th e last part o f th e mission fro m C 3 to the final location q f could be accomplished by the en d of the s pecified duration . Overall, th is observation reinforc es the significance of commu nication bloc klength an d trajector y co-design f or the secrecy perf o rmance improvement of aerial relay ing with SPC. V I . C O N C L U S I O N This work presented the d esign of a secur e and reliable U A V -I oT r elaying system with SPC. T o optimize the EAST perfor mance of the system, an ef fective joint design appro ach that inco rporates the U A V trajectory and bo th uplink an d downlink blocklengths was proposed , and was shown to achieve quick conver gence with low complexity . The ef ficacy of the pr o posed approach was e valuated through numerical simulations, and the r esults demonstrated th e superiority o f our J TBD scheme in term s of EAST co m pared to benchm arks that only co nsider either trajectory design or blo cklength optimization . Ou r r esults fu rther in dicated th a t both the uplink and downlink blocklen gths should be ad aptively ad justed accordin g to th e U A V location along the tra jec tory . R E F E R E N C E S [1] G. Durisi, T . K och, and P . Popovski, “T ow ard massiv e, ultrarel iable, and lo w-latenc y wireless communicati on with short packe ts, ” Proc. IEEE , vol. 104, no. 9, pp . 1711–1726, Sept. 20 16. [2] C. Feng and H. M. W ang, “Secure short-pack et communicat ions at the physical layer for 5G and beyond , ” IEEE Commun. Stand. Mag. , vol. 5, no. 3, p p. 96–102, Sept. 2021 . [3] M. Shirv animogha ddam et al. , “Short block-length codes for ultra- reliab le low latency communicati ons, ” IEEE Commun. Mag . , vol. 57, pp. 130–137, Feb. 2019. [4] N. Y ang, L. W ang, G. Geraci, M. Elkashlan, J. Y uan, and M. Di Renzo, “Safe guarding 5G wirel ess communication networks using physical layer security , ” IEEE Commun. Ma g. , vol. 53, pp . 20–27, Apr . 2015. [5] M. T atar Mamaghani, A. Kuhesta ni, and K.-K. W ong, “Secure two-way transmission via wire less-po wered untrusted relay and external jammer, ” IEEE T rans. V eh. T echnol. , vol. 67, pp. 84 51–8465, Sept. 2018. [6] M. T ata r Mamaghani and Y . Hong, “ Improving PHY -security of UA V - enable d transmission with wireless energy harvesti ng: Robust traject ory design and communications resource allo cation, ” IEEE T rans. V eh. T echn ol. , vo l. 69, pp. 8586– 8600, Aug. 2020. [7] H. V . Poor and R. F . Schaefer , “ Wi reless physical layer s ecurity, ” Pr oc. Natl. Acad. Sci. U .S.A. , vol. 114, no. 1, p p. 19–26, Ja n. 2017. [8] W . Y ang, R. F . Schaefer , and H. V . Poor , “W iret ap channels: Nonasymp- totic fundame ntal limits, ” IEEE T rans. Inf. The ory , vol. 65, pp. 4069– 4093, July 2019. [9] T .-X. Zheng, H.-M. W ang, D. W . K. Ng, a nd J. Y uan, “Physic al-laye r security in the finite blocklength regime ov er fadin g channe ls, ” IEEE T ran s. W ire l. Commun. , v ol. 19, no. 5, pp. 3405–3420, Ma y 2020. [10] C. Feng, H. M. W ang, and H. V . Poor , “Reliabl e and secure short-pack et communicat ions, ” IEE E T rans. W ir el. Commun. , vol. 21, pp. 1913 –1926, Mar . 2022. [11] H. -M. W ang, Q. Y ang, Z. Ding, and H. V . Poor , “Secur e short-pac ket communicat ions for mission-critica l IoT applica tions, ” IEE E T ran s. W irel. Commun. , vol. 18, p p. 2565–2578, Ma y 2019. [12] Q. W u et al. , “A comprehensi ve o vervi ew on 5G-and-be yond ne tworks with UA Vs: From communicat ions to sensing and inte lligenc e, ” IEE E J . Se l. A re as Commun. , vol. 39, pp. 29 12–2945, O ct. 2021. [13] H. M. W ang, X. Z hang, and J. C. Jiang, “U A V -in volv ed wireless physical -layer secure communication s: Ov ervie w and research direc- tions, ” IEEE W ir el. Commun. , v ol. 26, no. 5 , pp. 3 2–39, Oct. 2019 . [14] M. T atar Mama ghani and Y . Hong, “Joint trajecto ry and power allocati on design for secure artificial noise aided U A V communicatio ns, ” IEE E T ran s. V eh. T echnol. , v ol. 70, pp. 2850–2855, Mar . 2021. [15] S. Boyd and L. V andenber ghe, Con vex Optimizatio n . Cambri dge, U. K. : Cambridge Univ . Press, 2004. [16] M. Grant and S. Boyd, “CVX: Matlab Softwa re for Disciplined Con ve x Programming, V ersion 2.2, ” Jan. 2020 . [Online ]. A vail able: http:/ /cvxr .com/cvx
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment