Synthesis of Orchestrations and Choreographies: Bridging the Gap between Supervisory Control and Coordination of Services
We present a number of contributions to bridging the gap between supervisory control theory and coordination of services in order to explore the frontiers between coordination and control systems. Firstly, we modify the classical synthesis algorithm …
Authors: Davide Basile, Maurice H. ter Beek, Rosario Pugliese
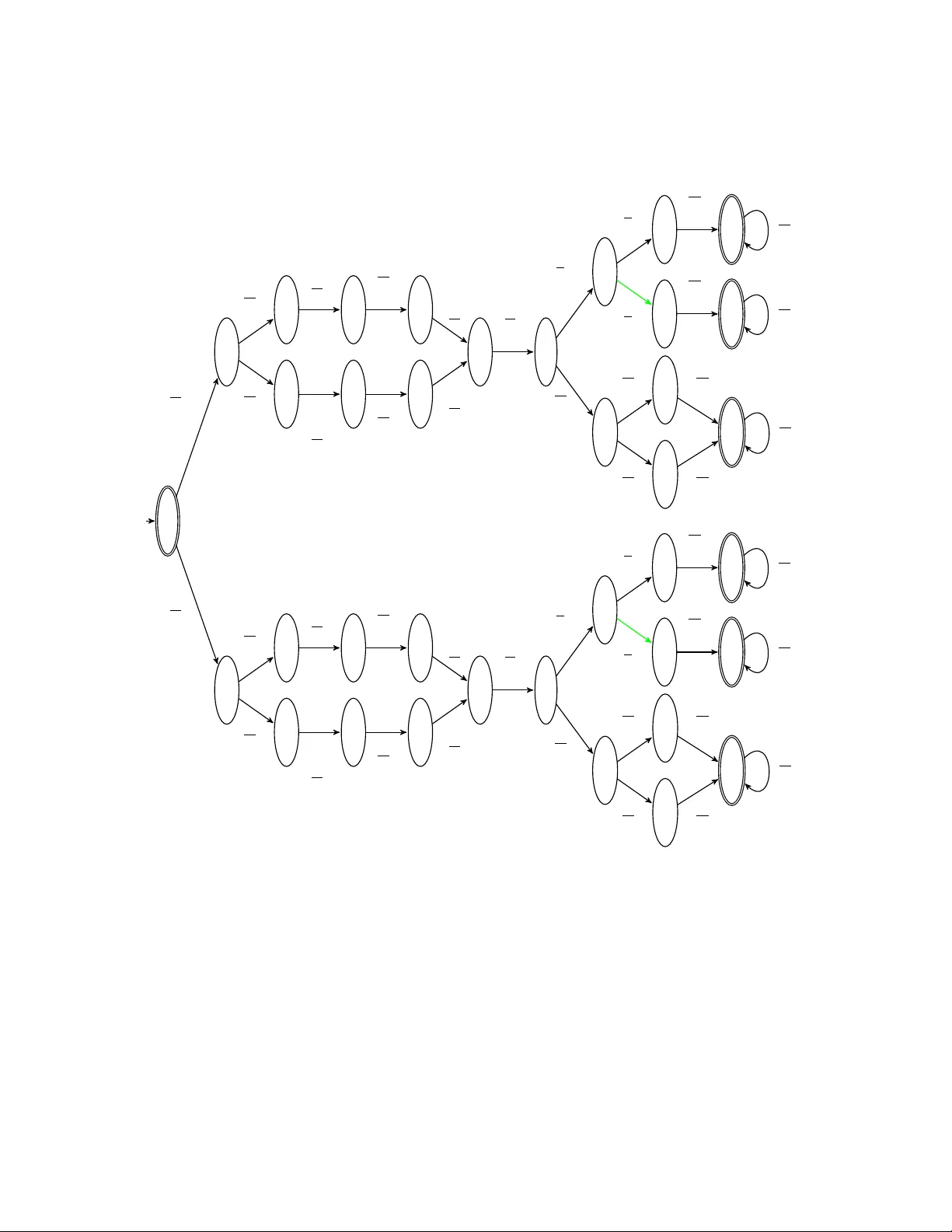
Logical Methods in Computer Science V olume 16, Issue 2, 2020, pp . 9:1–9:29 https://lmcs.episciences.org/ Submitted Oct. 05, 2019 Published Jun. 03, 2020 SYNTHESIS OF OR CHESTRA TIONS AND CHOREOGRAPHIES: BRIDGING THE GAP BETWEEN SUPER VISOR Y CONTR OL AND COORDINA TION OF SER VICES D A VIDE BASILE a , MA URICE H. TER BEEK a , AND ROSARIO PUGLIESE b a ISTI–CNR, Pisa, Italy e-mail addr ess : {da vide.basile,maurice.terb eek}@isti.cnr.it b Univ ersity of Florence, Italy e-mail addr ess : rosario.pugliese@unifi.it Abstra ct. W e presen t a n umber of con tributions to bridging the gap b et ween supervisory con trol theory and co ordination of services in order to explore the frontiers b etw een co ordination and control systems. Firstly , we mo dify the classical synthesis algorithm from sup ervisory control theory for obtaining the so-called most p ermissive controller in order to synthesise orchestrations and choreographies of service contracts formalised as contract automata. The key ingredien t to mak e this possible is a no v el notion of controllabilit y . Then, w e present an abstract parametric synthesis algorithm and sho w that it generalises the classical synthesis as well as the orchestration and choreograph y syntheses. Finally , through the nov el abstract synthesis, we show that the concrete syn theses are in a refinemen t order. A running example from the service domain illustrates our contributions. 1. Intr oduction Services are ubiquitous in to da y’s so ciety . Examples include finances, healthcare, and tourism (e.g. b o oking services). Service-oriented computing (SOC) is “the discipline that seeks to dev elop computational abstractions, arc hitectures, techniques, and to ols to supp ort services broadly” [ 16 ]. A ccording to this paradigm, services are w ell-defined, self-contained, and stand-alone soft w are modules that provide some standard business functionality . As suc h, services can serve as building blo cks for the rapid, lo w-cost developmen t of distributed applications in heterogeneous environmen ts. Services used in comp osite applications are not limited to new service implemen tations, but may also include adapted and wrapp ed fragmen ts of existing applications. The strength of SOC is comp osing multiple, distributed services in to more p ow erful applications. This reuse through comp osition provides businesses a means to reduce the cost and risks of dev eloping new applications. Service comp osition is th us a key c hallenge for the full realisation of the SOC paradigm. As suc h, it can b enefit from and con tribute to emerging research directions inspired b y cloud computing, IoT, so cial computing, and mobile computing, to name but a few. F or instance, Key wor ds and phr ases: Service Contracts, Con tract Automata, Controller Synthesis, Orchestration, Choreograph y . LOGICAL METHODS l IN COMPUTER SCIENCE DOI:10.23638/LMCS-16(2:9)2020 c D . Basile, M.H. ter Beek, and R. Pugliese CC Creative Commons 9:2 D. Basile, M.H. ter Beek, and R. Pugliese V ol. 16:2 the comp osition of cloud services requires the co ordination of hardware and softw are resources across v arious la yers. The IoT concept of smart cities concerns the large-scale comp osition of div erse and heterogeneous digital devices and services to pro vide multiple real-time, end user customised functionalities. Service comp osition based on relations in to day’s large so cial net w orks is challenging due to size and complexit y of the resultant big data. In mobile en vironmen ts, service comp osition is required to consider the in trinsic dynamicit y and its effect on QoS asp ects concerning securit y and reliability . T wo approac hes are widely adopted for co ordinating services by means of service comp o- sition: or chestr ation and chor e o gr aphy . In tuitiv ely , an orchestration yields the description of a distributed w orkflo w from “one part y’s p ersp ective” [ 41 ], whereas a choreograph y describ es the b ehaviour of the in v olv ed parties from a “global viewp oin t” [ 34 ]. In an orc hestrated mo del, the service comp onents are co ordinated by a sp ecial comp onent, the or chestr ator , whic h, by in teracting with them, dictates the w orkflo w at runtime. In a choreographed mo del, instead, the service comp onents autonomously execute and interact with eac h other on the basis of a lo cal control flow exp ected to comply with their role as sp ecified by the global viewp oin t. Ideally , a choreographed model is thought to b e more efficien t due to the absence of the ov erhead of communications with the orchestrator. An y choreograph y can trivially b e transformed in to an orchestration of services, b y adding an idle orchestrator. Similarly , b y explicitly adding an orchestrator and its in teractions with the service comp onents, and hence the relative ov erhead, an orchestration of services can b e transformed into a c horeograph y . Despite the k ey impact that SOC can hav e on other contemporary computing paradigms, as already men tioned before, the recent Service Computing Manifesto [ 16 ] p oin ts out that “Service systems hav e so far b een built without an adequate rigorous foundation that would enable reasoning ab out them” and that “The design of service systems should build up on a formal mo del of services”. Therefore, the principled design of service-based applications and systems is identified as a primary research challenge for the coming years. T o tackle this c hallenge, in [ 10 ], t w o orc hestrated and c horeographed automata-based mo dels of services, called c ontr act automata 1 and c ommunic ating (finite-state) machines , resp ectiv ely , are studied and related. The goal of b oth formalisms is to comp ose the automata such that eac h service is capable of reaching an accepting (final) state by sync hro- nous/async hronous one-to-one interactions with the other services in the comp osition. The main difference relies on the fact that con tract automata are oblivious of their partners and an orchestration is synthesis ed to driv e their interactions, whereas communicating mac hines name the recipient service of eac h interaction upfront and use FIF O buffers to in teract with eac h other. The mo del of con tract automata was further dev elop ed in [8]. The orchestration synthesis was b orro w ed from the synthesis of the most p ermissive con troller (mp c) from Supervisory Con trol Theory (SCT) [ 43 , 18 ], whose aim is to co ordinate an ensemble of (lo cal) comp onents in to a (global) system that functions correctly . In the con text of contract automata, this amoun ts to refining the comp osition of service contracts in to its largest sub-p ortion whose b eha viour is non-blo cking and safe (a notion of service compliance). The adaptation of the mp c syn thesis for synthesising an orchestration of services required the introduction of a no v el notion of semi-c ontr ol lability . Basically , the assumption of the presence of an unpredictable en vironmen t was dropped in fav our of a milder notion of predictable necessary service requests to b e fulfilled. 1 Not to b e confused with the acciden tally homonymous contract automata of [ 6 ], which were introduced to formalise legal con tracts among tw o parties expressed in natural language. V ol. 16:2 SYNTHESIS OF ORCHESTRA TIONS AND CHOREOGRAPHIES 9:3 In this pap er, w e con tribute to the researc h efforts on rigorously mo delling service orc hestration and choreograph y . More sp ecifically, building on [ 14 ], we report on the efforts to relate the mp c syn thesis and the orchestration syn thesis of contract automata through a p olished, homogeneous formalisation. The need for semi-con trollabilit y is sho w cased with in tuitiv e examples and its expressiv eness is ev aluated with resp ect to standard SCT notions of controllable and uncontrollable actions. Moreov er, we introduce a nov el choreograph y syn thesis algorithm and a nov el abstract synthesis algorithm. W e then show that each of the three synthesis algorithms can b e obtained through a differen t instan tiation of this abstract synthesis algorithm. This pap er extends [ 14 ] in several w a ys. W e include all pro ofs and as an additional contribution we demonstrate that the different instantiations of the abstract synthesis algorithm are related through a notion of refinement, which allows us to formally prov e that the orchestration synthesis is an abstraction of the mp c synthesis. F urthermore, w e illustrate each of the synthesis algorithms through a running example from the service domain. Finally , w e hav e also extended the prototypical to ol FMCA T 2 with the implemen tation of the nov el c horeograph y syn thesis algorithm and then used it to compute all the automata comp ositions and syn theses shown in our running example. The pap er is organised as follo ws. Section 2 contains background notions and results concerning contract automata and SCT, and introduces our running example. Section 3 and Section 4 in troduce the synthesis of orchestrations and the nov el syn thesis of c horeographies in the setting of (mo dal service) contract automata. Section 5 demonstrates that each of the in tro duced synthesis algorithms is an instantiation of a more abstract, parametric synthesis algorithm, and Section 6 shows that these differen t instan tiations are related. Section 7 discusses related w ork, while Section 8 concludes the pap er and pro vides some hints for future work. App endix A con tains the full pro ofs of t w o results only sketc hed in Section 5. 2. Ba ck gr ound In this section, we pro vide some background useful to b etter appreciate our contributions on the crossroads of supervisory control theory and co ordination of services formalised as modal service con tract automata. W e also introduce a running example from the service domain that will b e used throughout the pap er to illustrate our contributions. 2.1. Con tract Automata. A Contract Automaton (CA) represents either a single service (in whic h case it is called a princip al ) or a m ulti-part y comp osition of services p erforming actions. The num ber of principals of a CA is called its r ank . The states of a CA are vect ors of states of principals. In the following, ~ v denotes a v ector and ~ v ( i ) denotes its i th element. The transitions of CA are lab elled with actions, which are vectors of elements in the finite set of b asic actions L = R ∪ O ∪ {•} , with R ∩ O = ∅ and • 6∈ R ∪ O . In tuitiv ely , R is the set of r e quests (depicted as non-o v erlined lab els on arcs, e.g. a ), O is the set of offers (depicted as ov erlined lab els on arcs, e.g. a ) with O = { a | a ∈ R } , and • is a distinguished sym b ol represen ting the id le action. T o establish if a pair of a request and an offer are c omplementary , we use the involution function co : L → L defined as follows: ∀ a ∈ R : co ( a ) = a , ∀ a ∈ O : co ( a ) = a , and co ( • ) = • . By abusing notation, w e let co ( R ) = O and co ( O ) = R . 2 FMCA T is av ailable at https://github.com/davidebasile/FMCAT . A video-tutorial show casing the sp ecification, comp osition, and syn theses of the contract automata from our running example is av ailable at https://github.com/davidebasile/FMCAT/tree/master/demoLMCS2020 . 9:4 D. Basile, M.H. ter Beek, and R. Pugliese V ol. 16:2 An action is a v ector ~ a of basic actions with either a single offer, or a single request, or a single pair of request-offer that match, i.e. there exist i and j suc h that ~ a ( i ) is an offer and ~ a ( j ) is the complementary request (formally co ( ~ a ( i ) ) = ~ a ( j ) ); all other elemen ts of the v ector are • , meaning that the corresp onding principals remain idle. Such action is called r e quest , offer , or match , resp ectiv ely . A transition is said to b e a request, offer, or match according to its lab elling action. The goal of eac h principal is to reac h an accepting ( final ) state suc h that all its requests and offers are matched. In [ 11 ], CA are equipp ed with mo dalities , i.e. p ermitte d ( 3 ) and ne c essary ( 2 ), that are asso ciated to requests. Offers remain without mo dalities, i.e. they are interpreted as alw a ys p ermitted, like in the original CA formalism. Matc hes, on the other hand, inherit the mo dalit y of the in v olved request. The resulting formalism, called Mo dal Service Contract Automata (MSCA), is formally defined next. Differen tly from standard SCT, all transitions of MSCA are observable , since MSCA model the execution of services in terms of their requests and offers. Definition 2.1 (MSCA [ 11 ]) . Giv en a finite set of states Q = { q 1 , q 2 , . . . } , a Mo dal Servic e Contr act Automata (MSCA) A of rank n is a septuple h Q, ~ q 0 , A 3 , A 2 , A o , T , F i , with set of states Q ⊆ Q n , initial state ~ q 0 ∈ Q , set of p ermitted requests A 3 and of necessary request A 2 partitioning the set of requests A r ⊆ R , set of offers A o ⊆ O , set of final states F ⊆ Q , set of transitions T ⊆ Q × A × Q , where A ⊆ ( A r ∪ A o ∪ {•} ) n , partitioned in to p ermitte d transitions T 3 and ne c essary transitions T 2 , suc h that: (i) giv en t = ( ~ q , ~ a, ~ q 0 ) ∈ T , ~ a is either a request, or an offer, or a matc h; (ii) ∀ i ∈ 1 . . . n, ~ a ( i ) = • implies ~ q ( i ) = ~ q 0 ( i ) ; (iii) t ∈ T 3 if and only if ~ a is either a request, or a match on a ∈ A 3 , or an offer on a ∈ A o ; otherwise t ∈ T 2 . Remark ably , it follows that the set of transitions of an MSCA is finite. A princip al is an MSCA of rank 1 suc h that A r ∩ co ( A o ) = ∅ . Unless stated differently , w e assume that it is given an MSCA A = h Q A , ~ q 0 A , A 3 A , A 2 A , A o A , T A , F A i of rank n . Subscript A may b e omitted if no confusion may arise. A step ( w , ~ q ) ~ a − → ( w 0 , ~ q 0 ) o ccurs in A if and only if w = ~ aw 0 , w 0 ∈ A ∗ , and ( ~ q , ~ a, ~ q 0 ) ∈ T . Let → ∗ b e the reflexive and transitiv e closure of → . The language of A is L ( A ) = { w | ( w , ~ q 0 ) w − → ∗ ( ε, ~ q ) , ~ q ∈ F } . A step may be denoted as ~ q ~ a − → if w , w 0 , and ~ q 0 are irrelev ant, and as ~ q → ~ q 0 if w , w 0 , and ~ a are irrelev ant. Comp osition of services is rendered through the comp osition of their MSCA mo dels. This amoun ts to in terlea ving or matc hing the transitions of the comp onent MSCA, forcing the matc h whenever tw o comp onen ts are ready on their resp ective complemen tary request/offer actions. In the resulting MSCA, states and actions are vectors of states and actions of the comp onen t MSCA, respectively . The composition is non-asso ciative, i.e. pre-existing matc hes are not rearranged if a new MSCA joins the comp osition afterw ards. In a comp osition of MSCA, typically v arious prop erties are analysed. W e are esp ecially in terested in agr e ement and str ong agr e ement (whic h in the literature is also known as progress of interactions, deadlo ck freedom, compliance or conformance of contracts). In an MSCA in strong agreement, all requests and offers must be matc hed. Instead, the prop erty of agreement only requires matching all requests. An MSCA admits (strong) agreement if it has a trace satisfying the corresp onding prop erty , and it is safe if all its traces are suc h. The MSCA formalism has its origins in [ 8 ], where CA were first in tro duced, but in this pap er we build on the version with mo dalities from [ 11 ] to cater for controllable and V ol. 16:2 SYNTHESIS OF ORCHESTRA TIONS AND CHOREOGRAPHIES 9:5 c 0 c 1 c 2 c 3 c 4 c 0 0 c 0 1 c 0 2 c 0 3 c 0 4 qry 3 bst 3 ok 3 nok 3 qry 2 bst 3 ok 3 nok 3 Figure 1: MSCA Client (left) and PrivilegedClient (right) h 0 h 1 h 2 h 3 h 4 h 0 0 h 0 1 h 0 2 h 0 3 h 0 4 chk 3 rsp 3 bk 3 nbk 3 chk 3 rsp 3 bk 2 nbk 3 Figure 2: MSCA Hotel (left) and PrivilegedHotel (right) uncon trollable (and thus semi-con trollable) actions. The branc hing condition for CA from [ 10 ] will b e recalled in Section 4 as a condition for obtaining a choreograph y from an orchestration, and it is satisfied by construction by the output MSCA of the synthesis of the choreograph y . Example 2.2. W e introduce a running example that will b e used throughout the pap er to show case the synthesis of orchestration and choreograph y . W e an ticipate, as discussed in detail in Section 4, that a mo dified version of MSCA is used for the synthesis of a c horeograph y , in whic h offers can b e necessary whilst requests are only p ermitted. Figures 1, 3, and 2 show five MSCA of rank 1. These automata mo del an example of a hotel b o oking service, where clients and hotels interact by means of a broker for b o oking hotel ro oms. There are tw o t yp es of clien ts, Client and PrivilegedClient . Both clients can either terminate without interactions (final states are drawn as double circles), or they can engage in interactions with the broker to p ossibly b o ok a ro om. The first interaction is to ask for a ro om, by means of the offer qry (query). After this action, the clien ts receive the b est ro om option from the brok er, by means of the request bst (b est). Then, each clien t can either decide to accept (offer ok ) or refuse (offer nok ) the option offered by the broker. PrivilegedClient will b e used to show case a c horeograph y in Section 4. A ccordingly , PrivilegedClient only differs from Client with resp ect to the first offer qry , which is declared ne c essary . Basically , PrivilegedClient reac hes an agreement only if there exists a trace in which its offer is necessarily matched. All other actions are p ermitted. Similarly , there are tw o types of hotels, Hotel and PrivilegedHotel . Also b oth hotels can either terminate without interactions, or they can engage in interactions with the broker to p ossibly hav e their ro oms b ooked. The first interaction is to receive a request for a ro om, b y means of the request chk (c hec k). After this c hec k, a resp onse is sen t to the broker through the offer rsp (resp onse). Then, each hotel can either receiv e a b o oking or a no b o oking reply b y means of requests bk (b o ok) or nbk (no b o ok), resp ectively . PrivilegedHotel will b e used to show case an orchestration in Section 3. Accordingly , PrivilegedHotel only differs from Hotel with resp ect to the request bk , declared ne c essary . Basically , PrivilegedHotel admits non-empty orc hestrations only if there exists a trace in which one of its ro oms is b o ok ed (i.e. the necessary request is matched). All other actions are p ermitted. Finally , the Broker acts as an in termediary b etw een a client and at least tw o hotels. The broker starts by receiving a request for a ro om by a clien t through the request qry . A t this p oint, it starts to interact with the hotels to search for a p ossible option to prop ose to the client. This is done b y (twice) repeating the offer chk (sending a ro om enquiry) follow ed 9:6 D. Basile, M.H. ter Beek, and R. Pugliese V ol. 16:2 b 0 b 1 b 2 b 3 b 4 b 5 b 6 b 7 b 8 b 9 b 10 b 11 b 12 qry 3 chk 3 rsp 3 chk 3 rsp 3 chk 3 bst 3 ok 3 nok 3 bk 3 nbk 3 nbk 3 nbk 3 nbk 3 nbk 3 Figure 3: MSCA Broker b y the request rsp (receiving the ro om resp onse b y one hotel). Indeed, at least t w o hotels m ust b e enquired to sp eak of a b est offer. After that, the Broker can engage with further hotels, from state b 5 , or it can pro ceed with the b est offer bst to the client. At this p oint, it receiv es through the requests ok or nok either the acceptance or rejection, resp ectively , of its offer. If the offer is accepted, Broker pro ceeds to b o ok the ro om with offer bk to the selected hotel (abstracted aw ay in the con tract) and replying to all other hotels with a nbk offer. Otherwise, if the offer is rejected, Broker sends to all hotels waiting for a reply the offer nbk . All actions of Broker are p ermitted. 2.2. Sup ervisory Control Theory. The aim of Sup ervisory Con trol Theory [ 43 , 18 ] (SCT) is to provide an algorithm to synthesise a finite-state automaton mo del of a sup ervisory c ontr ol ler from given (comp onent) finite-state automata mo dels of the uncon trolled system and its requirements, themselves expressed as automata. The syn thesised sup ervisory controller, if successfully generated, is suc h that the controlled system, which is the comp osition (i.e. sync hronous pro duct) of the uncon trolled system and the sup ervisory controller, satisfies the requiremen ts and is additionally non-blo cking , c ontr ol lable , and maximal ly p ermissive . An automaton is non-blo cking if from each state at least one of the so-called marke d states (distinguished stable states representing completed ‘tasks’ [ 43 ], e.g. a final state) can b e reached without passing through so-called forbidden states , meaning that the system alw a ys has the p ossibility to return to an accepted stable state. The algorithm assumes that mark ed states and forbidden states are indicated for each component mo del. SCT distinguishes b etw een observable and unobservable , as well as c ontr ol lable and unc ontr ol lable actions, where unobserv able actions are also uncontrollable. Intuitiv ely , the sup ervisory controller cannot distinguish one unobserv able action from the other, whereas it can take observ able actions apart. Moreo v er, it is not p ermitted to directly blo ck uncon trol- lable actions from o ccurring; the controller is only allow ed to disable them by prev en ting con trollable actions from o ccurring. In tuitiv ely , controllable actions corresp ond to stimulatin g the system, while uncontrollable actions corresp ond to messages provided b y the environmen t, lik e sensors, which may b e neglected but cannot b e denied from existing. Finally , the fact that the resulting sup ervisory controller is maximal ly p ermissive (or least restrictiv e) means that as muc h b ehaviour of the uncon trolled system as p ossible remains present in the controlled system without violating neither the requirements, nor con trollabilit y , nor the non-blo cking condition. F rom the seminal work of Ramadge and W onham [ 43 ], we kno w that a unique maximally p ermissiv e sup ervisory controller exists, provided that all actions are observ able. This is called the most p ermissive c ontr ol ler ( mp c ); it co ordinates an ensem ble of (lo cal) comp onents in to a (global) system that works correctly . The syn thesis algorithm suffers from the same V ol. 16:2 SYNTHESIS OF ORCHESTRA TIONS AND CHOREOGRAPHIES 9:7 state space explosion problem as mo del c hec king [ 31 ]. Ho w ev er, SCT has successfully b een applied to industrial size case studies [29, 49]. In tuitiv ely , the synthesis algorithm for computing the mpc of a finite-state automaton A w orks as follo ws. The mp c is computed through an iterative pro cedure that at each step i up dates incrementally a set of states R i con taining the b ad states, i.e. those states that cannot preven t a forbidden state to b e even tually reac hed, and refines an automaton K i . The algorithm starts with an automaton K 0 equal to A and a set R 0 con taining all dangling states in A , where a state is dangling if it cannot b e reached from the initial state or cannot reach a final state. At each step i , the algorithm prunes from K i − 1 in a backw ards fashion transitions with target state in R i − 1 or forbidden source state. The set R i is obtained b y adding to R i − 1 dangling states in K i and source states of uncontrollable transitions of A with target state in R i − 1 . When no more up dates are p ossible, the algorithm terminates. T ermination is ensured since A is finite-state and has a finite set of transitions, and at eac h step the subsets of its states R i cannot decrease while the set of its transitions T K i cannot increase. Now, suppose that at its termination the algorithm returns the pair ( K s , R s ) . W e ha v e that the mp c is empty , if the initial state of A is in R s ; otherwise, the mp c is obtained from K s b y remo ving the states R s . W e rep ort b elow the standard syn thesis algorithm, but we homogenise the notation and simplify the formulation, to align the algorithm with those presented in the next sections. F or this purp ose, we assume the standard mp c synthesis to op erate on MSCA where necessary transitions ( T 2 ) are uncontrollable whilst p ermitted transitions ( T 3 ) are controllable. W e use h i to denote the empty automaton. A state q ∈ Q is said to b e dangling if and only if @ w suc h that q 0 w − → ∗ q or q w − → ∗ q f ∈ F . Let Dangling ( A ) denote the set of dangling states of A . Giv en tw o MSCA A and A 0 , w e say that A 0 is a sub-automaton of A , denoted b y A 0 ⊆ A , whenever the comp onents of A 0 are included in the corresp onding ones of A . Moreo v er, given t wo sets of states R and R 0 , we let ( A , R ) ≤ ( A 0 , R 0 ) if A 0 ⊆ A and R ⊆ R 0 . It is straightforw ard to sho w that ( MSCA × 2 Q , ≤ ) is a complete partial order (cp o). The algorithm to compute the mp c is now defined in terms of the le ast fixe d p oint of a monotone function on the cp o ( MSCA × 2 Q , ≤ ) . Definition 2.3 (Standard syn thesis, adapted from [ 43 ]) . Let A b e an MSCA, and let K 0 = A and R 0 = Dangling ( K 0 ) . W e let the synthesis function f : MSCA × 2 Q → MSCA × 2 Q b e defined as follows: f ( K i − 1 , R i − 1 ) = ( K i , R i ) , with T K i = T K i − 1 \ { ( ~ q − → ~ q 0 ) ∈ T K i − 1 | ~ q 0 ∈ R i − 1 ∨ ~ q is forbidden } R i = R i − 1 ∪ { ~ q | ( ~ q − → ~ q 0 ) ∈ T 2 A , ~ q 0 ∈ R i − 1 } ∪ Dangling ( K i ) Theorem 2.4 (Standard mp c, adapted from [ 43 ]) . The synthesis function f is monotone on the cp o ( MSCA × 2 Q , ≤ ) and its least fixed p oint is: ( K s , R s ) = sup( { f n ( K 0 , R 0 ) | n ∈ N } ) The mpc of A , denote d by K A , is: K A = h i if ~ q 0 ∈ R s h Q \ R s , ~ q 0 , A 3 , A 2 , A o , T K s , F \ R s i otherwise W e no w w an t to estimate an upp er b ound of the complexity of the mp c syn thesis algorithm as results from Definition 2.3 and Theorem 2.4. In the w orst case, deciding if a state is dangling requires to visit the whole state space. Th us, an upp er b ound of the 9:8 D. Basile, M.H. ter Beek, and R. Pugliese V ol. 16:2 complexit y of the pro cedure for deciding if a state is dangling is O ( | Q | ) , and the upp er-b ound complexit y for computing the set of dangling states is O ( | Q | 2 ) . At eac h iteration, in the w orst case, the algorithm either remov es a single transition from T or adds a single state to R , and each iteration requires to compute the set of dangling states. Thus, an upp er b ound of the complexity of the mp c synthesis algorithm is O (( | T | + | Q | ) × | Q | 2 ) . T o conclude, it is worth noticing that our analysis fo cusses on the abstract sp ecification of the algorithm while its implementation could b e optimised, for example by using parallelism and dedicated data structures, in order to p erform b etter than the complexit y sk etc hed ab ov e. Example 2.5. W e con tin ue the running example by discussing the synthesis of the mp c for the comp osition of t w o clients, the brok er, one normal hotel, and one privileged hotel, denoted as A 1 = Client ⊗ Client ⊗ Broker ⊗ Hotel ⊗ PrivilegedHotel The prop ert y to b e enforced is agreement: each request must b e matched by a corresp onding offer. Basically , this property is an inv arian t stating that all request transitions are forbidden. Since the synthesis works on forbidden states, we need to prepro cess A 1 accordingly . In particular, the algorithm starts from the automaton A 1 from whic h all p ermitted requests ha v e b een remov ed. F orbidden states are those featuring an outgoing ne c essary request. The resulting mp c only consists of the initial (and final) state ( c 0 , c 0 0 , b 0 , h 0 , h 0 0 ) , and its b eha viour is empty . Hence, agreement cannot b e enforced in A 1 using the standard syn thesis algorithm. This is an indication of the fact that standard mp c synthesis is not useful for the scop e of synthesising a correct service comp osition (i.e. in which agreemen t is satisfied). The reason is that necessary transitions are not to b e int erpreted as uncon trollable. The notion of uncon trollable transition stems from the necessit y of mo delling an unpredictable environmen t, whic h is not suitable to mo del necessary service requests. Basically , PrivilegedHotel has a necessary request that should b e matched in at le ast one trace of the comp osition. Ho w ever, b y interpreting suc h necessary request as uncontrollable, the syn thesis is enforcing the necessary requests to b e satisfied in every trace of the comp osition. In tuitiv ely , this would require that a client is not allow ed to refuse to b o ok a ro om. As will b ecome clear in the forthcoming sections, A 1 admits a non-empty orc hestration in which agreemen t is enforced, b ecause necessary transitions will not b e interpreted as fully uncon trollable. W e hav e used our to ol FMCA T to calculate the automaton A 1 and its mp c syn thesis. Their computation time and state-space dimension are rep orted in T able 1 (on page 17). 3. Synthesis of Orchestra tions In this section, we discuss how we revised the classical syn thesis algorithm from SCT to obtain the mp c (cf. Theorem 2.4) and synthesise orc hestrations of MSCA. Originally , MSCA were capable of expressing only p ermitted requiremen ts, corresp onding to actions that are controllable b y the orchestrator. Hence, in the syn thesis of the orchestra- tion, all transitions lab elled b y actions violating the property to be enforced were pruned, and all dangling states were remo v ed (cf. [8]). While p ermitted requests of MSCA are in one-to-one corresp ondence with controllable actions, in terestingly this is not the case for necessary requests and uncon trollable actions. A necessary (request) action is indeed a w eak er constrain t than an uncontrollable one. This stems from the fact that traditionally uncontrollable actions relate to an unpredictable V ol. 16:2 SYNTHESIS OF ORCHESTRA TIONS AND CHOREOGRAPHIES 9:9 · a 2 / / · · a 3 " " b 3 / / · a 3 / / · ( · , · ) ( a,a ) 2 " " ( • ,b ) 3 / / ( · , · ) ( a,a ) 2 # # . . . 7 3 Figure 4: T w o MSCA (left and middle) and a p ossible comp osition A of them (right) en vironmen t. How ever, the in terpretation of suc h actions as ne c essary service requests to b e fulfilled in a service con tract, as is the case in the setting of MSCA, implies that it suffices that in the synthesised orchestration at least one suc h sync hronisation (i.e. matc h) actually o ccurs. This is precisely what is mo delled by the notion of semi-c ontr ol lable actions, an ticipated in [11] and formally in tro duced in [12, 13], discussed next. The imp ortance of this nov el notion in the synthesis algorithm is show cased b y an in tuitiv e example. Consider the t wo MSCA in teracting on the necessary service request a depicted in Fig. 4 (left and middle), and their p ossible comp osition A depicted in Fig. 4 (righ t). Note that A mo dels tw o p ossibilities of fulfilling request a from the leftmost automaton b y matc hing it with a service offer a from the middle one. Note that a similar comp osition can b e obtained in other automata-based formalisms (suc h as, e.g., (timed) I/O automata [ 39 , 2 , 25 ]). No w assume that a m ust b e matched with a to obtain an agreemen t (i.e. it is ne c essary ), and that for some reason the b ad state 7 is to b e av oided in fav our of the suc c essful state 3 , i.e. in some sense we would lik e to express that a m ust b e matc hed at some p oint, rather than alwa ys. In most automata-based formalisms this is not allow ed and the resulting mp c is empt y . In the MSCA formalism, it is p ossible to orchestrate the composition of the t w o automata on the left in such a wa y that the result is the automaton A on the right, but without the state 7 and its inciden t transition. In fact, in the MSCA formalism, A depicts a comp osition in whic h the automata on the left can synchronise on a so-called semi-con trollable action a 2 either in their initial state or after the middle automaton has p erformed some other action b 3 , ignoring in this case whether a bad or a successful state is reached in the end. Indeed, the notion of semi-controllabilit y is indep enden t from b oth the sp ecific formalism b eing used and the requirement (e.g. agreemen t in case of MSCA) to b e enforced. As far as we know, we were the first to define a synthesis algorithm, in [ 13 ], that is capable of pro ducing a controller that guarantees that at le ast one of these tw o synchronisations actually o ccurs. Indeed, in the standard synthesis algorithm (cf. Theorem 2.4), action a can either b e c ontr ol lable and hence not necessary as we w an t, or unc ontr ol lable thus requiring that a m ust always b e matched, a stronger requirement than the one p osed by declaring a as necessary . T o formalise the intuitions ab o v e 3 , a semi-controllable transition t b ecomes controllable if in a giv en p ortion of A there exists a semi-con trollable match transition t 0 , with source and target states not dangling, suc h that in both t and t 0 the same principal, in the same lo cal state, do es the same request. Otherwise, t is uncontrollable. Definition 3.1 (Controllabilit y) . Let A b e an MSCA and let t = ( ~ q 1 , ~ a 1 , ~ q 1 0 ) ∈ T A . Then: • if ~ a 1 is an action on a ∈ A 3 ∪ A o , then t is c ontr ol lable (in A ) and part of T 3 ; • if ~ a 1 is a request or match on a ∈ A 2 , then t is semi-c ontr ol lable (in A ) and part of T 2 . 3 W e refer the interested reader to [12, 13] for more complete accounts. 9:10 D. Basile, M.H. ter Beek, and R. Pugliese V ol. 16:2 Moreo v er, given A 0 ⊆ A , if t is semi-controllable and ∃ t 0 = ( ~ q 2 , ~ a 2 , ~ q 2 0 ) ∈ T 2 A 0 in A 0 suc h that ~ a 2 is a matc h, ~ q 2 , ~ q 2 0 6∈ Dangling ( A 0 ) , ~ q 1 ( i ) = ~ q 2 ( i ) , and ~ a 1 ( i ) = ~ a 2 ( i ) = a , then t is c ontr ol lable in A 0 (via t 0 ); otherwise, t is unc ontr ol lable in A 0 . The algorithm for synthesising an orc hestration enforcing agreemen t of MSCA follows. The main adaptation of the mp c synthesis of Theorem 2.4 is that transitions are no longer declared uncontrollable, but instead they can b e either controllable or semi-controllable. More imp ortantly , a semi-controllable transition switc hes from con trollable to uncon trollable only after it has b een pruned in a previous iteration, in which case its source state b ecomes bad. Finally , in this case there are no forbidden states but rather forbidden transitions (i.e. requests, according to the prop ert y of agreemen t). Definition 3.2 (MSCA orchestration syn thesis, adapted from [ 11 ]) . Let A b e an MSCA, and let K 0 = A and R 0 = Dangling ( K 0 ) . W e let the or chestr ation synthesis function f o : MSCA × 2 Q → MSCA × 2 Q b e defined as follows: f o ( K i − 1 , R i − 1 ) = ( K i , R i ) , with T K i = T K i − 1 \ { ( ~ q − → ~ q 0 ) = t ∈ T K i − 1 | ( ~ q 0 ∈ R i − 1 ∨ t is a r e quest ) } R i = R i − 1 ∪ { ~ q | ( ~ q − → ) ∈ T 2 A is unc ontr ol lable in K i } ∪ Dangling ( K i ) Theorem 3.3 (MSCA orc hestration, adapted from [ 11 ]) . The or chestr ation synthesis function f o is monotone on the cp o ( MSCA × 2 Q , ≤ ) and its least fixed p oint is: ( K s , R s ) = sup( { f n o ( K 0 , R 0 ) | n ∈ N } ) The orc hestration K A of A is: K A = h i if ~ q 0 ∈ R s h Q \ R s , ~ q 0 , A 3 , A 2 , A o , T K s \ T 0 , F \ R s i otherwise wher e T 0 = { t = ~ q − → ∈ K s | t is c ontr ol lable in K s , ~ q ∈ R s } . W e now estimate the complexity of the orc hestration synthesis algorithm. In the synthesis of the mp c, deciding whether a transition is con trollable or uncontrollable has a complexity of O (1) . On the con v erse, for the orc hestration case, deciding whether a semi-con trollable transition is controllable or uncon trollable requires in the w orst case to chec k all transitions of the automaton. A ccordingly , the pro cedure for computing the set of uncontrollable transitions has an upp er-b ound complexity of O ( | T | 2 ) . Since this is the only difference with resp ect to the mp c synthesis, a first upp er b ound of the complexity of the orchestration syn thesis is O (( | T | + | Q | ) × | Q | 2 × | T | 2 ) . The computation of the set of dangling states and uncon trollable transitions could b e done in parallel through a single visit of the automaton. Th us, the upp er-b ound complexity of the orchestration syn thesis can b e lo w ered to b e the same as the complexit y of the mp c synthesis, i.e. O (( | T | + | Q | ) × | Q | 2 ) . Finally , w e w an t to underline that our complexity estimation refers to the abstract specification of the algorithm, resulting from Definition 3.2 and Theorem 3.3. As already observed for the mp c syn thesis, when implementing the algorithm further optimisations could b e achiev ed that can low er its complexit y . Example 3.4. W e further contin ue the running example by discussing the synthesis of the orc hestration for the comp osition A 1 = Client ⊗ Client ⊗ Broker ⊗ Hotel ⊗ PrivilegedHotel V ol. 16:2 SYNTHESIS OF ORCHESTRA TIONS AND CHOREOGRAPHIES 9:11 c 0 c 0 0 b 0 h 0 h 0 0 c 1 c 0 0 b 1 h 0 h 0 0 c 1 c 0 0 b 2 h 1 h 0 0 c 1 c 0 0 b 3 h 2 h 0 0 c 1 c 0 0 b 4 h 2 h 0 1 c 1 c 0 0 b 2 h 0 h 0 1 c 1 c 0 0 b 3 h 0 h 0 2 c 1 c 0 0 b 4 h 1 h 0 2 c 1 c 0 0 b 5 h 2 h 0 2 c 2 c 0 0 b 6 h 2 h 0 2 c 3 c 0 0 b 7 h 2 h 0 2 c 3 c 0 0 b 8 h 3 h 0 2 c 3 c 0 0 b 9 h 4 h 0 2 c 3 c 0 0 b 8 h 2 h 0 3 c 3 c 0 0 b 9 h 2 h 0 4 c 4 c 0 0 b 10 h 2 h 0 2 c 4 c 0 0 b 11 h 4 h 0 2 c 4 c 0 0 b 11 h 2 h 0 4 c 4 c 0 0 b 12 h 4 h 0 4 c 0 c 0 1 b 1 h 0 h 0 0 c 0 c 0 1 b 2 h 1 h 0 0 c 0 c 0 1 b 3 h 2 h 0 0 c 0 c 0 1 b 4 h 2 h 0 1 c 0 c 0 1 b 2 h 0 h 0 1 c 0 c 0 1 b 3 h 0 h 0 2 c 0 c 0 1 b 4 h 1 h 0 2 c 0 c 0 1 b 5 h 2 h 0 2 c 0 c 0 2 b 6 h 2 h 0 2 c 0 c 0 3 b 7 h 2 h 0 2 c 0 c 0 3 b 8 h 3 h 0 2 c 0 c 0 3 b 9 h 4 h 0 2 c 0 c 0 3 b 8 h 2 h 0 3 c 0 c 0 3 b 9 h 2 h 0 4 c 0 c 0 4 b 10 h 2 h 0 2 c 0 c 0 4 b 11 h 4 h 0 2 c 0 c 0 4 b 11 h 2 h 0 4 c 0 c 0 4 b 12 h 4 h 0 4 qry • qry • • 2 • • chk chk • 3 • • rsp rsp • 3 • • chk • chk 3 • • rsp • rsp 3 • • chk • chk 3 • • rsp • rsp 3 • • chk chk • 3 • • rsp rsp • 3 bst • bst • • 3 ok • ok • • 3 • • bk bk • 3 • • nbk • nbk 3 • • nbk • • 3 • • bk • bk 2 • • nbk nbk • 3 • • nbk • • 3 nok • nok • • 3 • • nbk nbk • 3 • • nbk • nbk 3 • • nbk • nbk 3 • • nbk nbk • 3 • • nbk • • 3 • qry qry • • 2 • • chk chk • 3 • • rsp rsp • 3 • • chk • chk 3 • • rsp • rsp 3 • • chk • chk 3 • • rsp • rsp 3 • • chk chk • 3 • • rsp rsp • 3 • bst bst • • 3 • ok ok • • 3 • • bk bk • 3 • • nbk • nbk 3 • • nbk • • 3 • • bk • bk 2 • • nbk nbk • 3 • • nbk • • 3 • nok nok • • 3 • • nbk nbk • 3 • • nbk • nbk 3 • • nbk • nbk 3 • • nbk nbk • 3 • • nbk • • 3 Figure 5: Orchestration of Client ⊗ Client ⊗ Brok er ⊗ Hotel ⊗ PrivilegedHotel The orchestration of A 1 is depicted in Fig. 5 and the time needed to compute it by using FMCA T is rep orted in T able 1 (on page 17). W e recall that the orchestration is the largest sub-p ortion of the comp osition that is in agreemen t, i.e. in whic h requests are matched by offers. F rom the initial (and final) state there are tw o p ossible ev olutions: either one of the clien ts is serv ed while the other one do es not interact. Without loss of generality , assume that the first client is served. The orc hestration contin ues with the brok er enquiring the hotels (in b oth p ossible orders). After these enquiries, the reac hed state is ~ q = ( c 1 , c 0 0 , b 5 , h 2 , h 0 2 ) . F rom ~ q , the brok er sends the b est offer received from one of the hotels to the client, and the clien t decides whether or not to accept this b est offer. The broker then communicates the selected 9:12 D. Basile, M.H. ter Beek, and R. Pugliese V ol. 16:2 c hoice to the hotels it interacted with. Note that in the orchestration it is p ossible that the clien t do es not b o ok an y ro om. W e now explain why the mp c is empty (cf. Example 2.5). First, note that ~ q m ust b e tra v ersed to reac h a final successful state. The composition A 1 (whic h is not displa y ed for space limitations) contains the transition t = ~ q ( • , • , • , • , bk ) 2 − − − − − − − − → ( c 1 , c 0 0 , b 5 , h 2 , h 0 3 ) . The state ~ q is then forbidden, since its outgoing transition t is uncontrollable and cannot b e pruned. It follo ws that all states trav ersed from the initial state to ~ q w ould even tually b ecome dangling during the mp c synthesis, and th us the mp c is empt y . On the con v erse, for the case of syn thesising the orc hestration, w e ha v e that t is semi- c ontr ol lable and it is c ontr ol lable via t 0 = ( c 3 , c 0 0 , b 7 , h 2 , h 0 2 ) ( • , • , bk , • , bk ) 2 − − − − − − − − − → ( c 1 , c 0 0 , b 8 , h 2 , h 0 3 ) . Th us, t is pruned by the orc hestration syn thesis algorithm. In tuitiv ely , in the orc hestration there exists a trace in whic h the necessary request bk is matched. This example sho ws that the notion of semi-con trollabilit y is b est suited for necessary requests of service con tracts. W e argue that semi-con trollability is not sp ecific to the con text of service con tracts; rather it is indep endent of the used formalism and can b e applied in other con texts as well. Semi-controllabilit y can b e interpreted as the ‘existentially quan tified’ coun terpart of the universally quan tified notion of uncontrollabilit y , originally stemming from Sup ervisory Control Theory , in m uc h the same wa y that Computation T ree Logic allows existen tial quan tification of paths that can only b e univ ersally quan tified in Linear T emp oral Logic. Ho w ev er, in the next section w e will see that the notion of semi-controllabilit y is to o relaxed for the case of c horeograph y , which th us demands a revisited version. 3.1. On enco ding semi-controllabilit y . W e no w show, b y means of an example adapted from [ 13 ], that the enco ding of an automaton A with semi-controllable actions into an automaton A 0 without, such that the same synthesised orchestrations are obtained, results in an exp onential blo w-up of the state space. More precisely , the enco ding is in tended to preserv e safet y: the orchestration of A equals that of A 0 . The enco ding is sketc hed in Fig. 6. Intuitiv ely , the enco ded automaton A 0 is obtained b y first applying the following construction to the automaton A from Fig. 4 (right): if the sync hronisation on a sp ecific semi-con trollable action a o ccurs in n different transitions in A (tw o in our example), then the enco ding creates an automaton A 0 that is the union of 2 n − 1 automata (three in our example), whic h are obtained by all p ossible com binations of pruning a subset of the n semi-con trollable transitions of A , min us the one in whic h all n semi- con trollable transitions are pruned; and then turning all semi-controllable transitions in to uncontrollable transitions. W e now explain wh y , without kno wing a priori the set of forbidden and successful states, it is imp ossible to pro vide a more efficient enco ding and refer to [ 13 , Theorems 3 and 4] for a formal account. Assume, b y contradiction, that there exists an enco ding that results in a ‘smaller’ automaton A 00 , in whic h one of the 2 n − 1 com binations of pruned transitions (sa y , P ) is discarded. It then suffices to specify as a counterexample a prop erty in A suc h that all source states of transitions in P are forbidden and all target states of the remaining semi-con trollable transitions are successful. The synthesis of A against suc h a prop erty would prune exactly the semi-con trollable transitions in P . Ho w ev er, in the syn thesis of A 00 suc h an orchestrati on would not b e present, a con tradiction. V ol. 16:2 SYNTHESIS OF ORCHESTRA TIONS AND CHOREOGRAPHIES 9:13 ( · , · ) ( · , · ) ( • ,b ) 3 / / ( · , · ) ( a,a ) 2 unc " " ( · , · ) ( a,a ) 2 unc " " ( • ,b ) 3 / / ( · , · ) ( a,a ) 2 unc " " ( · , · ) ( a,a ) 2 unc " " ( • ,b ) 3 / / ( · , · ) ( · , · ) ( · , · ) ( · , · ) ( · , · ) Figure 6: Automaton A 0 uses uncontrollable transitions to enco de automaton A from Fig. 4 4. Synthesis of Choreographies In the previous section, w e ha v e seen that the orc hestration of MSCA is similar to a most p ermissiv e controller. The orc hestrator is how ever implicit, in the sense that its in teractions with the principals are hidden. Basically , one could assume that b efore in teracting, each principal exp ects a message from the orchestrator and answers with an ackno wledgement after the interaction terminates. The main intuition b ehind switc hing from an orchestrated to a choreographic co ordination of contracts is that there is no longer the need for such ‘hidden’ interactions. Ideally , the principals moving autonomously are able to accomplish the b ehaviour foreseen b y the synthesis, whic h in this case acts as a global type. Differently from the traditional choreographic approach, where the starting p oint is a global t yp e, in MSCA the global type is syn thesised automatically . The requirements for ensuring that the synthesised automaton is a (form of ) choreograph y w ere studied in [ 10 , 37 ]. Roughly , they amoun t to the so-called br anching c ondition requiring that principals p erform their offers/outputs indep enden tly of the other principals in the comp osition. T o formalise this notion, w e let snd ( ~ a ) = i when ~ a is a matc h action or an offer action and ~ a ( i ) ∈ O . Definition 4.1 (Branc hing condition [ 10 ]) . An MSCA A satisfies the br anching c ondition if and only if the following holds for each pair of states ~ q 1 , ~ q 2 reac hable in A : ∀ ~ a match action . ( ~ q 1 ~ a − → ∧ snd ( ~ a ) = i ∧ ~ q 1 ( i ) = ~ q 2 ( i ) ) implies ~ q 2 ~ a − → . The branc hing condition is related to a phenomenon known as ‘state sharing’ in other co ordination mo dels (cf., e.g., [ 45 ]) according to which system comp onen ts can influence p oten tial synchronisations through their lo cal (comp onent) states ev en if they are not inv olved in the actual global (system) transition. In [ 10 ], it is prov ed that the syn thesised automaton corresponds to a well-behaving c horeograph y if and only if it satisfies the branc hing condition and is strongly safe. Notably , in case the tw o conditions are not satisfied, that pap er do es not provide an y algorithm for automatically synthesising a choreograph y; rather, the contracts ha v e to b e manually amended. Instead, in the remainder of this section, we introduce a no v el algorithm for automatically syn thesising a w ell-b eha ving choreograph y . Note that, differently from the orc hestration and the controller syn thesis, in this case there could b e more than one p ossible c horeograph y (cf. Example 4.6). The prop erty to b e enforced during the synthesis is strong agreement: all offers and requests hav e to b e matched, b ecause all messages ha v e to b e read (i.e. offers matc hed). Moreo v er, in the case of choreograph y , service contract requests are alwa ys p ermitted whereas 9:14 D. Basile, M.H. ter Beek, and R. Pugliese V ol. 16:2 ( q 0 , · , · ) ( a,a, • ) x x ( a, • ,a ) ' ' ... / / ( q 0 , · , · ) ( a,a, • ) & & 7 3 Figure 7: F ragmen t of a p ossible service comp osition service contract offers can b e necessary . That is, the roles of service requests and offers are sw app ed with resp ect to the case of orchestration. In principle, the synthesis could trivially introduce a co ordinator comp onen t and its in teractions to co ordinate the principals. How ever, this w ould reduce the c horeograph y to a cen tralised co ordination of contracts. T o preven t this, the syn thesis can only remov e and nev er add b eha viour. Hence, a choreograph y can only b e synthesised if all principals are capable of interacting on their own without resorting to a central coordinator. Similarly to orc hestration synthesis, indicating transitions as either controllable or uncon trollable do es not suffice for synthesising a c horeograph y . Moreov er, the notion of semi-con trollabilit y introduced for the orchestration case does not suffice for expressing necessary offers. Indeed, orchestration syn thesis do es not ensure the branc hing condition to b e satisfied by the syn thesised automaton, as the following example sho ws. Example 4.2. In Fig. 7, a fragmen t of a service comp osition is sho wn. T wo global states are depicted, and in b oth the first service, sa y A lic e , is in its initial lo cal state (say , q 0 ). A lic e p erforms an output (i.e. offer) a that can b e directed to either Bob (second service) or Car ol (third service), from the initial global state, or only to Bob from the other state. It is p ossible to reach either a successful ( 3 ) or a bad ( 7 ) state, left unsp ecified for the moment. Notably , the output of A lic e is neither controllable, nor uncontrollable, nor semi-con trollable b y the syn thesis. No w assume that the a is controllable and from the initial global state b oth interactions ev en tually lead to a bad state ( 7 ). In this case, those transitions are pruned by the syn thesis, and the resulting automaton is erroneously approv ed. Indeed, A lic e has no mean to understand when her output a is enabled, b ecause she has not changed state. The branching condition, whic h is necessary for obtaining a well-behaving c horeography , would b e violated. Note that this would happ en also if a w ere semi-controllable. In fact, to satisfy the branching condition, the synthesis should remov e all outputs a . Con v ersely , assume that the a is uncon trollable and that it is possible from the initial global state to reach a successful state ( 3 ) if the message a is received by Bob . In this case, it w ould not b e p ossible to prune the transition from the initial state leading to 7 , b ecause it is also uncontrollable. The synthesis w ould thus b e empt y , an erroneous rejection, b ecause a c horeograph y exists in which A lic e autonomously interacts with Bob . In conclusion, a necessary action is rendered neither as uncontrollabl e nor as semi- con trollable, and p ermitted actions require extra pruning op erations during the synthesis. A nov el notion of semi-controllabilit y for a necessary action is required, which is weak er than uncon trollable but stronger than the semi-con trollable notion used in the synthesis of orc hestration. Basically , for the c horeograph y syn thesis, a (semi-con trollable) necessary transition t = ( ~ q ~ a 1 − → ) ∈ T 2 is detected to b e uncontrollable if and only if no necessary transition V ol. 16:2 SYNTHESIS OF ORCHESTRA TIONS AND CHOREOGRAPHIES 9:15 t 0 = ( ~ q ~ a 2 − → ) ∈ T 2 exists from the same source state such that in b oth t and t 0 the same offer is pro vided by the same principal, but p ossibly with different receiv ers. W e now define this formally . Definition 4.3. Let A b e an MSCA and let t = ( ~ q , ~ a 1 , ~ q 1 0 ) ∈ T A . Then: - if ~ a 1 is an action on a ∈ A 3 , then t is c ontr ol lable (in A ); - if ~ a 1 is an offer or match on a ∈ A 2 , then t is semi-c ontr ol lable (in A ). Moreo v er, giv en A 0 ⊆ A , if t is semi-con trollable and ∃ t 0 = ( ~ q , ~ a 2 , ~ q 2 0 ) ∈ T 2 A 0 suc h that ~ a 2 is a matc h, ~ q , ~ q 2 0 6∈ Dangling ( A 0 ) , and ~ a 1 ( i ) = ~ a 2 ( i ) where i = snd ( ~ a 1 ) , then t is c ontr ol lable in A 0 (via t 0 ); otherwise, t is unc ontr ol lable in A 0 . Hence, again a necessary transition is a particular type of transition that switches from b eing controllable to uncon trollable in case a condition on the global automaton is not met. Note that this condition is stronger than the one required for the case of orchestration (semi- con trollabilit y), b ecause for the case of choreograph y transitions t and t 0 in Definition 4.3 share the source state. Moreov er, also in this case it can b e sho wn that the enco ding of this t yp e of semi-con trollable transition in to an uncon trollable one would result in an exp onen tial gro wth of the state space of the mo del. Similarly to the orchestration synthesis in Definition 3.2, when a semi-controllable transition previously remov ed b y the synthesis switches from controllable to uncon trollable, its source state is detected to b e bad. Apart from the different notion of semi-controllabilit y , another difference with resp ect to the orc hestration syn thesis is that the transitions violating the branching condition m ust also b e remo v ed. Depending on which transitions violating the branc hing condition are pruned at a certain iteration, different choreographies can be obtained (cf. Example 4.6). Indeed, a maximal choreograph y is not alwa ys guaranteed to exist (as is the case for the running example). A concrete implementation should fix the criterion under which transitions are selected for the set ˆ T K i ,R i (cf. Definition 4.4). Finally , according to the prop erty of strong agreemen t, b oth request and offer transitions are forbidden. The formalisation is pro vided next. Definition 4.4 (MSCA choreograph y synthesis) . Let A b e an MSCA, and let K 0 = A and R 0 = Dangling ( K 0 ) . W e let a chor e o gr aphy synthesis function f c : MSCA × 2 Q → MSCA × 2 Q b e defined as follows: f c ( K i − 1 , R i − 1 ) = ( K i , R i ) , with T K i = T K i − 1 \ ( { ( ~ q − → ~ q 0 ) = t ∈ T K i − 1 | ~ q 0 ∈ R i − 1 ∨ t is a r e quest or offer } ∪ ˆ T K i − 1 ,R i − 1 ) R i = R i − 1 ∪ { ~ q | ( ~ q − → ) ∈ T A is unc ontr ol lable in K i } ∪ Dangling ( K i ) where, at each iteration i , ˆ T K i ,R i ⊆ T bc = { ( ~ q 1 ~ a − → ) ∈ T K i | ∃ ~ q 2 : ( snd ( ~ a ) = j ∧ ~ q 1 ( j ) = ~ q 2 ( j ) ) ∧ ( ~ q 2 ~ a − → ) 6∈ T K i ∧ ~ q 1 , ~ q 2 6∈ R i } and whenever f c ( K i , R i ) = ( K i , R i ) then T bc = ∅ . Theorem 4.5 (MSCA c horeograph y) . A chor e o gr aphy synthesis function f c is monotone on the cp o ( MSCA × 2 Q , ≤ ) and its least fixed p oint is: ( K s , R s ) = sup( { f n c ( K 0 , R 0 ) | n ∈ N } ) A c horeograph y K A of A is: K A = h i if ~ q 0 ∈ R s h Q \ R s , ~ q 0 , A 3 , A 2 , A o , T K s \ T 0 , F \ R s i otherwise 9:16 D. Basile, M.H. ter Beek, and R. Pugliese V ol. 16:2 wher e T 0 = { t = ~ q − → ∈ K s | t is c ontr ol lable in K s , ~ q ∈ R s } . Mor e over, K A satisfies the br anching c ondition. Pr o of. The algorithm terminates b ecause at eac h iteration either some transition is pruned or a state b ecomes forbidden, and b oth sets of transitions and states are finite. W e now pro v e that the syn thesised automaton is (i) non-blo cking, (ii) con trollable, (iii) strongly safe, and (iv) satisfies the branching condition. In case K A = h i , the prop erties hold trivially , th us w e assume that the syn thesised con troller is non-empty . F or (i), trivially all dangling states are pruned, so it is alwa ys p ossible to reach a final state. Similarly , bad states (i.e. states in the set R s ) are never tra v ersed by construction, i.e. transitions with target in R s are pruned. F or (ii), by construction all uncontrollable transitions hav e source state in R s , and th us are not reachable. Note that by Definition 4.3 uncontrollable transitions are necessary requiremen ts that are not met and th us are alwa ys remov ed b y the synthesis. F or (iii), all transitions even tually violating strong safet y are requests or offers and are pruned by the syn thesis. F or (iv), the transitions violating the branc hing condition are { ( ~ q 1 ~ a − → ) = t ∈ T K A | ∃ ~ q 2 : ( snd ( ~ a ) = i ∧ ~ q 1 ( i ) = ~ q 2 ( i ) ) ∧ ( ~ q 2 ~ a − → ) 6∈ T K A } and these are pruned by definition. Returning to Example 4.2, the erroneously accepted case is remov ed b ecause, during the synthesis, the op eration of pruning the transitions leading to bad states causes the remo v al of the remaining transition. Th us, the obtained c horeograph y is empt y . Similarly , the erroneously rejected case is not p ossible b ecause, assuming that the output from the initial state is necessary , this necessary action is not rendered as uncontrollable as long as the output is matched b y some other principal from the same initial state. W e now estimate also the complexity of the c horeograph y syn thesis. With resp ect to the orc hestration synthesis, in the c horeograph y synthesis at each iteration a transition violating the branching condition can b e remov ed. In the w orst case, deciding if a transition violates the branc hing condition requires to c hec k all other transitions. Hence, an upp er b ound of the pro cedure for selecting a transition violating the branc hing condition is O ( | T | 2 ) . Note that, in the unlik ely even t that all transitions share the same source state, the upp er-b ound complexit y for computing the set of uncontrollable transitions is the same as in the case of orc hestration synthesis. Th us, a first upp er b ound of the complexit y of the choreograph y syn thesis algorithm is O (( | T | + | Q | ) × | Q | 2 × | T | 4 ) . W e can refine this first approximation to O (( | T | + | Q | ) × | Q | 2 ) . Indeed, similar to the case of orchestration synthesis, at each iteration in a single tra v ersal of the automaton it is p ossible to compute the set of dangling states, the set of uncontrollable transitions, and the set of transitions violating the branching condition. Also in this case, as for the other syn theses, our complexit y estimation refers to the abstract sp ecification of the algorithm resulting from Definition 4.4 and Theorem 4.5. The implementati on of the algorithm could b e optimised to p erform ev en b etter. Example 4.6. W e once more contin ue the running example by discussing the c horeograph y syn thesis of the running example for the comp osition A 2 = Client ⊗ PrivilegedClient ⊗ Broker ⊗ Hotel ⊗ Hotel The choreograph y of A 2 is depicted in Fig. 8 and the time needed to compute A 2 and its c horeograph y by using FMCA T is rep orted in T able 1. Note that differently from A 1 in V ol. 16:2 SYNTHESIS OF ORCHESTRA TIONS AND CHOREOGRAPHIES 9:17 c 0 c 0 0 b 0 h 0 h 0 0 c 0 c 0 1 b 1 h 0 h 0 0 c 0 c 0 1 b 2 h 1 h 0 0 c 0 c 0 1 b 3 h 2 h 0 0 c 0 c 0 1 b 4 h 2 h 0 1 c 0 c 0 1 b 5 h 2 h 0 2 c 0 c 0 2 b 6 h 2 h 0 2 c 0 c 0 3 b 7 h 2 h 0 2 c 0 c 0 3 b 8 h 3 h 0 2 c 0 c 0 3 b 9 h 3 h 0 4 c 0 c 0 4 b 10 h 2 h 0 2 c 0 c 0 4 b 11 h 4 h 0 2 c 0 c 0 4 b 12 h 4 h 0 4 • qry qry • • 2 • • chk chk • 3 • • rsp rsp • 3 • • chk • chk 3 • • rsp • rsp 3 • bst bst • • 3 • ok ok • • 3 • nok nok • • 3 • • bk bk • 3 • • nbk • nbk 3 • • nbk nbk • 3 • • nbk • nbk 3 Figure 8: Choreography of Client ⊗ PrivilegedClient ⊗ Brok er ⊗ Hotel ⊗ Hotel Num. states comp osition Time (ms) Num. states mp c Time (ms) Num. states orc hestration Time (ms) Num. states c horeography Time (ms) A 1 2934 65594 1 4070 37 715216 – – A 2 2934 66243 – – – – 13 459311 T able 1: Results of computing the comp ositions A 1 and A 2 and their syntheses. 4 Example 2.5 and Example 3.4, in A 2 there is a privileged client and no privileged hotel. Indeed, PrivilegedHotel is not a v alid con tract for the choreograph y case. The choreograph y do es not need the ov erhead of interactions with the orchestrator and, most importantly , the synthesis of choreograph y do es not introduce any additional b ehaviour. Indeed, with due adjustment of necessary transitions of PrivilegedClient and Hotel , the choreograph y could b e considered a sub-automaton of the orchestration. W e no w use the example to discuss the differences b et w een orchestration and c horeograph y , and in particular the requiremen t that the br anching c ondition is satisfied. In the orchestration, from the initial state either one of the tw o clients can in teract. This decision is internally tak en by the orc hestrator (whose communications are abstracted a w a y in the orc hestration). On the con v erse, in the c horeograph y only the PrivilegedClient is allow ed to interact. This is b ecause the clien ts are not able to decide on their o wn whic h one of them should start the in teractions. This can b e explained as follo ws. If b oth clien ts were allow ed to in teract, a deadlo ck could b e reac hed up on the following steps. Initially , PrivilegedClient offers qry . Afterwards, for the interactions to contin ue suc h offer m ust b e received by some principal (i.e. the underlining choreographed mo del is synchronous [ 10 ]). In this case, Broker receiv es the offer qry . At this p oin t, Client is allow ed to offer its qry message. The in teractions are now deadlock ed, b ecause Broker cannot receive such message, nor can any other con tract. This is an example of violation of the branching condition. Consider the initial state ~ q 0 = ( c 0 , c 0 0 , b 0 , h 0 , h 0 0 ) and state ~ q 1 = ( c 0 , c 0 1 , b 1 , h 0 , h 0 0 ) . In the orchestration, the branc hing condition is violated b ecause from state ~ q 0 the matc h ( qry , • , qry , • , • ) is allow ed, while it is not in state ~ q 1 , and in b oth states Client is in c 0 . During the c horeograph y syn thesis, the match ( qry , • , qry , • , • ) from state ~ q 0 is pruned. Likewise, in the choreograph y the brok er enquires the hotels in a fixed order, whereas in the orchestration all p ossible orders are allow ed, or else the branc hing condition would be violated. 4 The ev aluation was carried out on a machine with Pro cessor Intel(R) Core(TM) i7-8500Y CPU at 1.50 GHz, 1601 Mhz, 2 Core(s), 4 Logical Pro cessor(s) with 16 GB of RAM, running 64-bit Windo ws 10. 9:18 D. Basile, M.H. ter Beek, and R. Pugliese V ol. 16:2 Note that an alternative c horeograph y can b e obtained b y sw apping the order in whic h the hotels are enquired b y the brok er. Indeed, from state ~ q 1 the orc hestration allo ws both matc hes ( • , • , chk , chk , • ) and ( • , • , chk , • , chk ) . During the choreograph y synthesis, b oth these outgoing matches are violating the branching condition. By pruning one of them, the other is automatically amended, b ecause the states causing violation of the branc hing condition b ecome dangling. In particular, the syn thesis prunes the transition ( • , • , chk , • , chk ) in fav our of ( • , • , chk , chk , • ) . Finally , concerning semi-con trollabilit y , note that it is not p ossible to ha v e a choreograph y in whic h PrivilegedClient is not served in fav our of Client , b ecause the qry offer of PrivilegedClient is ne c essary and thus m ust b e matc hed. 5. Abstra ct Synthesis In Section 2, Section 3, and Section 4, w e ha v e presen ted three sligh tly different syn thesis algorithms, and in the previous section we ha ve illustrated their differences. As said b efore, to bridge the gap b et w een standard syn thesis and orchestration and choreograph y syntheses, the controllable and uncontrollable actions from SCT are related to p ermitted and necessary mo dalities, resp ectively , of MSCA. The main in tuition for this is that the SCT assumption of an unpredictable en vironmen t resp onsible for the uncon trollable transitions is not realistic in the case of co ordination of services whose b ehaviour is known and observ able. As a result, necessary actions are not in corresp ondence with uncontrollable actions, but rather require the in troduction of a milder notion of con trollabilit y . The condition under which a con trollable transition b ecomes uncon trollable v aries dep ending on the particular synthesis algorithm (orc hestration or choreograph y). Con v ersely , in the standard mp c syn thesis such information is lo cal, i.e. a transition is declared to b e uncon trollable. In this section, we discuss an abstract synthesis algorithm that generalises the previous algorithms by abstracting aw ay the conditions under which a transition is pruned or a state is deemed bad, th us encapsulating and extrap olating the notion of con trollabilit y and safet y . These tw o conditions, called pruning pr e dic ate ( φ p ) and forbidden pr e dic ate ( φ f ) are parameters to b e instantiated b y the corresp onding instance of the synthesis algorithm (e.g. orchestration or c horeograph y). Predicate φ p is used for selecting the transitions to b e pruned. Dep ending on the sp ecific instance, non-lo cal information ab out the automaton or the set of bad states is needed b y φ p . Therefore, φ p tak es as input the current transition to b e chec ked, the automaton, and the set of bad states. If φ p ev aluates to true, then the corresp onding transition will b e pruned. Predicate φ f is used for deciding whether a state b ecomes bad. The input parameters are the same as φ p . Ho w ev er, φ f only insp ects necessary transitions ( T 2 ). If φ f ev aluates to true, then the source state is deemed bad and added to the set R i . The abstract synthesis algorithm is formally defined b elow. Definition 5.1 (Abstract syn thesis) . Let A b e an MSCA, and let K 0 = A and R 0 = Dangling ( K 0 ) . Giv en t w o predicates φ p , φ f : T × M S C A × Q → Bo ol , we let the abstr act synthesis function f ( φ p ,φ f ) : MSCA × 2 Q → MSCA × 2 Q b e defined as follows: f ( φ p ,φ f ) ( K i − 1 , R i − 1 ) = ( K i , R i ) , with T K i = T K i − 1 \ { t ∈ T K i − 1 | φ p ( t, K i − 1 , R i − 1 ) = true } R i = R i − 1 ∪ { ~ q | ( ~ q − → ) = t ∈ T 2 A , φ f ( t, K i − 1 , R i − 1 ) = true } ∪ Dangling ( K i ) V ol. 16:2 SYNTHESIS OF ORCHESTRA TIONS AND CHOREOGRAPHIES 9:19 As in the previous cases, the mp c relative to the pair ( φ p , φ f ) is obtained b y computing the least fixed p oint ( K s , R s ) of f ( φ p ,φ f ) and removing the states R s from K s . Theorem 5.2 (Abstract controller syn thesis) . The abstr act synthesis function f ( φ p ,φ f ) is monotone on the cp o ( MSCA × 2 Q , ≤ ) and its least fixed p oint is: ( K ( φ p ,φ f ) s , R ( φ p ,φ f ) s ) = sup( { f n ( φ p ,φ f ) ( K 0 , R 0 ) | n ∈ N } ) The abstract con troller of A for pr e dic ates ( φ p , φ f ) , denote d by K ( φ p ,φ f ) A , is: K ( φ p ,φ f ) A = h i if ~ q 0 ∈ R ( φ p ,φ f ) s h Q \ R ( φ p ,φ f ) s , ~ q 0 , A 3 , A 2 , A o , T K ( φ p ,φ f ) s , F \ R ( φ p ,φ f ) s i otherwise Pr o of. The algorithm terminates b ecause at eac h iteration either some transition is pruned or a state b ecomes forbidden, and b oth sets of transitions and states are finite. W e now pro v e that the syn thesised automaton is (i) non-blo c king, (ii) con trollable, (iii) most-p ermissiv e, and (iv) safe. In case K ( φ p ,φ f ) A = h i , the prop erties hold trivially , th us w e assume that the syn thesised con troller is non-empty . F or (i), trivially all dangling states are pruned, so it is alwa ys p ossible to reach a final state. Similarly , bad states (i.e. states in the set R s ) are never tra v ersed by construction, i.e. transitions with target in R s are pruned. F or (ii) and (iv), the forbidden predicate φ f co difies exactly when controllabilit y or safety is violated by a state. By construction, it is never the case that such a state is reached. F or (iii), b y construction a state is deemed bad or a transition is pruned exactly when either forbidden or pruning predicates are satisfied, resp ectively . Thus, maximality follo ws b y the fact that eac h controller greater than the one synthesised will admit some forbidden state or transition. In the remainder of this section, w e show how to instantiate the abstract syn thesis function to the standard syn thesis function, to the orc hestration syn thesis function, or to the c horeograph y syn thesis function, and prov e their corresp ondences. Theorem 5.3 (Abstract mp c synthesis) . The standar d synthesis function of Definition 2.3 c oincides with the instantiation of the abstr act synthesis function of Definition 5.1 wher e, for a generic tr ansition t = ( ~ q , ~ a, ~ q 0 ) , pr e dic ates φ p and φ f ar e define d as fol lows: φ mp c p ( t, K , R ) = ( ~ q 0 ∈ R ) ∨ ( ~ q is forbidden ) φ mp c f ( t, K , R ) = ( ~ q 0 ∈ R ) Pr o of. Let K mp c A and K abs A b e the con trollers computed through Theorems 2.4 and 5.2, resp ectiv ely . The pro of pro ceeds by induction on the fixed p oint iterations and by case analysis. F or the base case, by definition K mp c 0 = K abs 0 = A and R abs 0 = R mp c 0 = Dangling ( K 0 ) . F or the inductive case, let i b e a fixed p oint iteration. Assuming K mp c i − 1 = K abs i − 1 and R mp c i − 1 = R abs i − 1 , we prov e K mp c i = K abs i and R mp c i = R abs i . The equiv alence K mp c i = K abs i follo ws b ecause at the i th iteration, φ mp c p detects exactly the same transitions that are pruned by the mp c synthesis algorithm. 9:20 D. Basile, M.H. ter Beek, and R. Pugliese V ol. 16:2 F or the equiv alence R mp c i = R abs i , we hav e R mp c i = R mp c i − 1 ∪ Dangling ( K mp c i ) ∪ { ~ q | ( ~ q , ~ a, ~ q 0 ) ∈ T 2 K mp c i , ~ q 0 ∈ R mp c i − 1 } and R abs i = R abs i − 1 ∪ Dangling ( K abs i ) ∪ { ~ q | ( ~ q a − → ) = t ∈ T 2 A , φ mp c f ( t, K abs i − 1 , R abs i − 1 ) = true } . Since K mp c i = K abs i , also the dangling states are equiv alent. It remains to prov e that { ~ q | ( ~ q , ~ a, ~ q 0 ) ∈ T 2 K mp c i , ~ q 0 ∈ R mp c i − 1 } = { ~ q | ( ~ q a − → ) = t ∈ T 2 A , φ mp c f ( t, K abs i − 1 , R abs i − 1 ) = true } . This equiv alence is straigh tforw ard by the definition of φ mp c f and the inductive hypothesis. Note that in Theorem 5.3 the predicates do not use an y non-lo cal information related to the parameter K . F or both orchestration and c horeograph y , tw o differen t semi-con trollabilit y conditions are used to decide whether a state has b ecome forbidden. These conditions are translated int o the corresp onding forbidden predicates. Theorem 5.4 (Abstract orc hestration syn thesis) . The or chestr ation synthesis function of Definition 3.2 c oincides with the instantiation of the abstr act synthesis function of Defini- tion 5.1 wher e, for a generic tr ansition t = ( ~ q , ~ a, ~ q 0 ) , pr e dic ates φ p and φ f ar e define d as fol lows: φ or c p ( t, K , R ) = ( t is a r e quest ) ∨ ( ~ q 0 ∈ R ) φ or c f ( t, K , R ) = @ ( ~ q 2 ~ a 2 − → ~ q 2 0 ) ∈ T 2 K : ( ~ a 2 is a match ) ∧ ( ~ q 2 , ~ q 2 0 6∈ Dangling ( K )) ∧ ( ~ q ( i ) = ~ q 2 ( i ) ) ∧ ( ~ a ( i ) = ~ a 2 ( i ) = a ) Pr o of (sketch). The pro of is analogous to that of Theorem 5.3 but relying on Theorem 3.2 instead of Theorem 2.4. The full pro of can b e found in the app endix. The pruning predicate of Theorem 5.4 do es not use any information coming from the global automaton K , whereas this is no longer the case for the forbidden predicate that indeed sp ecifies the semi-con trollabilit y condition for the necessary transitions of an orchestration (cf. Definition 3.1). Theorem 5.5 (Abstract c horeograph y syn thesis) . The chor e o gr aphy synthesis function of Definition 4.4 c oincides with the instantiation of the abstr act synthesis function of Defini- tion 5.1, wher e given a generic tr ansition t = ( ~ q , ~ a, ~ q 0 ) , the pr e dic ates φ p and φ f ar e define d as fol lows, wher e ˆ T K ,R is define d in Definition 4.4: φ c or p ( t, K , R ) = ( t is a r e quest or offer ) ∨ ( ~ q 0 ∈ R ) ∨ t ∈ ˆ T K ,R φ c or f ( t, K , R ) = @ ( ~ q ~ a 2 − → ~ q 2 0 ) ∈ T 2 K : ( ~ a 2 is a match ) ∧ ( ~ q , ~ q 2 0 6∈ Dangling ( K )) ∧ ( ~ a ( i ) = ~ a 2 ( i ) = a ) Pr o of (sketch). The pro of is analogous to that of Theorem 5.3 but relying on Theorem 4.4 instead of Theorem 2.4. The full pro of can b e found in the app endix. Notably , in Theorem 5.5 b oth predicates require global information on the whole au- tomaton. Similarly to Theorem 5.4, the forbidden predicate co difies the semi-controllabilit y condition of Definition 4.3. Moreov er, the pruning predicate remo v es all transitions violating the branching condition (cf. Definition 4.1). V ol. 16:2 SYNTHESIS OF ORCHESTRA TIONS AND CHOREOGRAPHIES 9:21 6. A P ar tial Order on Controllers In Theorem 5.3, Theorem 5.4, and Theorem 5.5, we hav e prov ed that the three previously presen ted syn thesis algorithms are instantiations of the abstract syn thesis algorithm of Definition 5.1. This abstraction prov ides us the mean to formally relate the v arious algorithms presen ted so far, as detailed in this section. T o b egin with, we define a partial order on predicates. In tuitiv ely , a pair ( φ p 2 , φ f 2 ) is greater than another pair ( φ p 1 , φ f 1 ) if and only if ( φ p 2 , φ f 2 ) is (pairwise) en tailed by ( φ p 1 , φ f 1 ) . Definition 6.1 (P artial order on predicates) . Let A b e an MSCA and let Pr b e the set of pairs of pruning and forbidden predicates of Definition 5.1 with ( φ p 1 , φ f 1 ) , ( φ p 2 , φ f 2 ) ∈ Pr . The partial order on predicates ( Pr , ≤ ) is defined as: ( φ p 1 , φ f 1 ) ≤ ( φ p 2 , φ f 2 ) iff ∀ i ∈ N . ( φ p 1 ( t, K 1 i , R 1 i ) ⇒ ( φ p 2 ( t, K 2 i , R 2 i ) ∨ t 6∈ K 2 i )) ∧ ( φ f 1 ( t, K 1 i , R 1 i ) ⇒ ( φ f 2 ( t, K 2 i , R 2 i )) ∨ ~ q ∈ Dangling ( K 2 i )) , where t = ( ~ q , ~ a, ~ q 0 ) . By Definition 5.1, w e know that suc h predicates are used to refine an MSCA during the syn thesis. Indeed, states and transitions are remo v ed when such predicates are satisfied by them. The partial order on predicates induces an ordering on the v arious abstract controllers, as the following result sho ws. Prop osition 6.2 (Ordering con trollers) . L et A b e an MSCA and let ( φ p 1 , φ f 1 ) , ( φ p 2 , φ f 2 ) ∈ Pr b e such that ( φ p 1 , φ f 1 ) ≤ ( φ p 2 , φ f 2 ) . Then: K ( φ p 2 ,φ f 2 ) A ⊆ K ( φ p 1 ,φ f 1 ) A Pr o of. By Definition 5.1, b oth K ( φ p 1 ,φ f 1 ) A and K ( φ p 2 ,φ f 2 ) A are sub-automata of A , and they only differ in the sets of states and transitions. By con tradiction, assume that there exists a transition t in T K ( φ p 2 ,φ f 2 ) A \ T K ( φ p 1 ,φ f 1 ) A . By Definition 5.1, let i b e the iteration where t is remo v ed from T K 1 i . By hypothesis, it holds that φ p 1 ( t, K 1 i , R 1 i ) ⇒ φ p 2 ( t, K 2 i , R 2 i ) ∨ t 6∈ K 2 i , hence by Definition 5.1, t m ust also hav e b een remo v ed from T K 2 i or it is not present, a contradiction. Similarly , assume that there exists a state ~ q in Q K ( φ p 2 ,φ f 2 ) A \ Q K ( φ p 1 ,φ f 1 ) A . By Definition 5.1, let i b e the iteration where ~ q is added to R K 1 i . By h yp othesis, it holds that φ f 1 ( t, K 1 i , R 1 i ) ⇒ φ f 2 ( t, K 2 i , R 2 i ) ∨ ~ q ∈ Dangling ( K 2 i ) , hence by Definition 5.1, ~ q m ust also hav e b een added to R K 2 i . Finally , Q K ( φ p 2 ,φ f 2 ) A = Q A \ R 2 s and R K 2 i ⊆ R 2 s , thus a con tradiction is reached. This result has an immediate application in p erforming abstraction of syntheses, in the sense that the lesser the pair of predicates the more abstract (in refinement terms) the corresp onding synthesised automaton. This can b e useful to p erform partial syntheses and skip unnecessary chec ks or even p otentially undecidable computations. F or example, if K ( φ p 1 , φ f 1 ) = h i , for a giv en pair ( φ p 1 , φ f 1 ) , then b y Prop osition 6.2 w e kno w that for all ( φ p i , φ f i ) such that ( φ p 1 , φ f 1 ) ≤ ( φ p i , φ f i ) it will hold that K ( φ p i , φ f i ) = h i . While the orchestration syn thesis of Definition 3.2 is enforcing agreemen t, the mp c syn thesis of Definition 2.3 is enforcing a generic predicate mo delled as forbidden states. Whenev er the mp c synthesis is also enforcing agreemen t, as an instantiation of Prop osition 6.2, w e can pro v e that the tw o syntheses are related. Moreo v er, agreemen t iden tifies forbidden 9:22 D. Basile, M.H. ter Beek, and R. Pugliese V ol. 16:2 transitions as those lab elled by requests. On the conv erse, the mpc syn thesis identifies forbidden states rather than forbidden transitions. Therefore, to enable a comparison of the mp c and the orchestration syn thesis, we need to (i) transform the automaton such that the predicate on forbidden transitions (i.e. agreemen t in this case) can b e expressed b y means of forbidden states and (ii) instantiate the generic predicate expressed by forbidden states. F or p oin t (i), the synthesis of the mp c is applied to the automaton A 0 obtained from the original automaton A b y erasing con trollable forbidden transitions. F or point (ii), forbidden states are those states that are sources of uncontrollable forbidden transitions. This is what the follo wing lemma states. Lemma 6.3 (Orc hestration vs. mp c synthesis) . Given an MSCA A , let A 0 b e obtaine d fr om A by r emoving al l c ontr ol lable r e quest tr ansitions and c onsidering as forbidden the states of A 0 with outgoing unc ontr ol lable r e quest tr ansitions. L et K or c A and K mp c A 0 b e the or chestr ation and mp c of Definitions 3.2 and 2.3, r esp e ctively. Then: K mp c A 0 ⊆ K or c A Pr o of. By Theorems 5.4 and 5.3, K or c A and K mp c A 0 are equiv alen t to K ( φ or c p , φ or c f ) A and K ( φ mp c p , φ mp c f ) A 0 , resp ectiv ely . Moreo v er, b oth con trollers are sub-automata of A , and they only differ in the sets of states and transitions. Recall that, given t = ( ~ q , ~ a, ~ q 0 ) , φ mp c p ( t, K mp c i , R mp c i ) = ( ~ q 0 ∈ R mp c i ) ∨ ( ~ q is forbidden ) , φ mp c f ( t, K mp c i , R mp c i ) = ( ~ q 0 ∈ R mp c i ) and φ or c p ( t, K or c i , R or c i ) = ( t is a request ) ∨ ( ~ q 0 ∈ R or c i ) , φ or c f ( t, K or c i , R or c i ) = @ ( ~ q 2 ~ a 2 − → ~ q 2 0 ) ∈ T 2 K or c i : ( ~ a 2 is a match ) ∧ ( ~ q 2 , ~ q 2 0 6∈ Dangling ( K or c i )) ∧ ( ~ q ( i ) = ~ q 2 ( i ) ) ∧ ( ~ a ( i ) = ~ a 2 ( i ) = a ) . W e pro ceed by induction on i . F or the base case, it holds that K A 0 0 ⊆ K 0 and Dangling ( K 0 ) ⊆ Dangling ( K A 0 0 ) . By hypothesis, φ or c p ( t, K or c 0 , R or c 0 ) is true. Then either t is a request or ~ q 0 ∈ Dangling ( K 0 ) . If t is a request, then t has been already pruned. Otherwise, ~ q 0 ∈ Dangling ( K 0 ) (or b oth), and so it is in Dangling ( K A 0 0 ) and the pruning predicate of the mp c is satisfied. Similarly , by h yp othesis φ or c f ( t, K or c 0 , R or c 0 ) is true. Since no transitions hav e b een pruned in K 0 , it must b e the case that the source state of t is in Dangling ( K 0 ) , and so it is in Dangling ( K A 0 0 ) . F or the inductiv e step, the implication on the pruning predicate is satisfied by noticing that R or c i − 1 ⊆ R mp c i − 1 . The implication on the forbidden predicate is satisfied b ecause trivially t 6∈ T 2 K or c i , and hence t 6∈ T 2 K mp c i , and this is b ecause either the target is dangling or the source is forbidden. In b oth cases the forbidden predicate of the mp c is satisfied. Th us, for example, given an MSCA A , from K or c A = h i w e can conclude that K mp c A = h i b y Lemma 6.3, without actually computing it. Example 6.4. Concluding the running example, one can observ e that the mpc of A 1 is a sub-automaton (formed of only the initial and final state) of the orchestration of A 1 . 7. Rela ted Work Our contributions to bridging the gap b etw een SCT and co ordination of services concern adaptations of the classical synthesis algorithm from SCT in order to synthesise orchestrations and c horeographies of service con tracts formalised as MSCA. In the literature, there exist man y formalisms for mo delling and analysing (service) contracts, ranging from b ehavioural V ol. 16:2 SYNTHESIS OF ORCHESTRA TIONS AND CHOREOGRAPHIES 9:23 t yp e systems, including b ehavioural contracts [ 21 , 1 , 36 ] and session types [ 17 , 32 , 27 , 20 , 40 ], to automata-based formalisms, including in terface automata [ 26 ] and (timed) (I/O) automata [ 39 , 2 , 25 ]. F oundational mo dels for service contracts and session t ypes are surv ey ed in [44, 7, 33]. The MSCA formalism used in this pap er differs fundamentally from these mo dels, whic h t ypically study notions of contract compliance inv olving only t w o parties, since MSCA primitiv ely supp ort multi-p arty compliance of contracts that c omp ete on offering or requesting the same service. F urthermore, the ab ov e models do not consider mo dalities of services whereas MSCA provide primitiv e supp ort for p ermitte d and ne c essary service actions, which resulted in the introduction of a nov el notion of semi-c ontr ol lability in the con text of SCT. Mo dal T ransition Systems (MTS) and their extensions [ 35 ], as adopted for instance in Soft w are Pro duct Line Engineering (SPLE [ 42 , 3 ]), like mo dal I/O automata [ 38 ] and MTS with v ariability constraints [ 47 ], do nativ ely distinguish ma y and m ust mo dalities, but the other differences remain. In particular, they cannot explicitly handle dynamic comp osition b y allo wing new services that join comp osite services to intercept already matc hed actions. W e are only aw are of tw o other applications of SCT to MTS. In [ 24 ], there is no direct relation b etw een may/m ust and controllable/uncon trollable, and the mo dal automaton (i.e. MTS with final states) is seen as a predicate that is satisfied if the plant automaton (i.e. the system to b e refined against the predicate) is a sort of alternate refinement of the predicate. Similarly , in [ 28 ], the con trol ob jectiv es (i.e. the predicate) is a mo dal automaton, non-blo c kingness is not considered, and another mo dal automaton describ es whic h actions are con trollable and which are uncontrollable in the plant automaton. In this pap er, the predicate is an inv arian t (i.e. forbidden states and forbidden transitions are given), the mo dal automaton (i.e. MSCA) is the plan t, and a necessary transition induces different notions of con trollabilit y according to the adopted co ordination paradigm. SCT w as first applied to SPLE in [ 48 ] b y showing how the CIF 3 to olset [ 50 ] can automatically synthesise a single (global, family) mo del represen ting an automaton for eac h of the v alid products of a pro duct line from (i) a feature constrain t with attributes (e.g. cost), (ii) b eha vioural comp onen t mo dels asso ciated with the features, and (iii) additional b eha vioural requirements lik e state in v ariants, action orderings, and guards on actions (reminiscen t of the F eatured T ransition Systems of [ 22 ]). The resulting CIF 3 mo del satisfies all feature-related constrain ts as w ell as all given b ehavioural requiremen ts. Since CIF 3 allo ws the exp ort of such mo dels in a format accepted by the mCRL2 mo del chec ker [ 23 ], the latter can be used to verify arbitrary b eha vioural prop erties expressed in the mo dal µ -calculus with data or its feature-orien ted v ariant of [46]. An imp ortant adv an tage is that b oth CIF 3 and mCRL2 can b e used off-the-shelf, meaning that no additional to ols are required. Differen tly from our approac h, all actions are con trollable and orchestration is not considered. In [9], the prototypical tool CA T supp orting orchestration synthesis for CA is presented. The only approach by others to bridge the gap betw een SCT and co ordination of services that w e are a w are of is that of [ 5 ], where services are formalised as so-called Service Lab elled T ransition Systems (SL TS), which are a kind of guarded automata with data. T o this aim, SCT is adapted to deal with conditions and v ariables as well as with a means to enforce services based on run time information. How ever, service comp osition through SL TS is based on the standard synchronous pro duct, whilst the con tract comp osition expresses comp eting con tracts. More imp ortan tly , in [ 5 ], input actions are considered uncon trollable whereas output actions are con trollable, in the standard view of a service interac ting with the en vironmen t. Our contribution induces no v el notions of controllabilit y to express necessary 9:24 D. Basile, M.H. ter Beek, and R. Pugliese V ol. 16:2 requiremen ts that are semi-controllable. The standard controller syn thesis algorithm is used in [ 30 ] to syn thesise adapters b etw een services. These adapters act like pro xies and are used to enforce prop erties such as deadlo ck-freedom. Compared to our work, the interactions b etw een services are driv en b y their con tracts rather than b y adapters. The standard controller syn thesis algorithm cannot b e applied to synthesise a correct comp osition of contracts. W e conclude this section by describing tw o recen t extensions of MSCA, developed for differen t purp oses, and for which we also defined adapted syn thesis algorithms. In [ 12 ], w e presen ted F eatured Mo dal Contract Automata (FMCA). T ec hnically , we extended MSCA with a v ariability mechanism concerning structural constrain ts that op erate on the service con tract, used to define different configurations. This reflects the fact that services are t ypically reused in configurations that v ary ov er time and need to dynamically adapt to c hanging environmen ts [ 51 ]. Configurations were c haracterised b y which service actions are mandatory and which forbidden. The v alid configurations w ere defined as those resp ecting all structural constrain ts. W e follo w ed the w ell-established paradigm of SPLE, whic h aims at efficien tly managing a product line (family) of highly (re)configurable systems to allow for mass customisation [ 42 , 3 ]. T o compactly represent a pro duct line, i.e. the set of v alid pro duct configurations, we used a so-called feature constraint, a prop ositional formula ϕ whose atoms are features [ 15 ], and w e identified features as service actions (offers as well as requests). A v alid pro duct then distinguishes a set of mandatory and a set of forbidden actions. Consequently , we defined an algorithm to compute the FMCA K A p as the mp c for a v alid pro duct p of an FMCA A . The main adaptation of the syn thesis algorithm for MSCA w as to consider as bad states also those that cannot preven t a forbidden action to b e even tually executed and to discard the transitions lab elled with actions forbidden by p . Moreo v er, if some action that is mandatory in p is unav ailable in the automaton that results from the fixed p oint iteration, then the mp c results empt y . In [ 12 ], we also presented an ev aluation of FMCA with the prototypical to ol FMCA T. Building on CA T [ 9 ], FMCA T can syn thesise the orchestration of an FMCA in terms of its mp c. The results clearly show the gain in expressiv eness due to the notion of semi-con trollabilit y , as well as the reduction of the n um b er of configurations needed to compute the orchestration due to the in troduction of a partial order of pro ducts of FMCA. This inspired us to consider semi-controllabilit y also in MSCA and to develop a partial order of controllers for MSCA in this pap er. In [ 13 ], we presen ted Timed Service Contract Automata (TSCA) as an extension of the FMCA from [ 12 ] with real-time constrain ts. F ormally , a configuration of a TSCA is a triple consisting of a recognised trace, a state, and a v aluation of clo c ks. The (finite) b eha viour recognised by a TSCA are traces of alternating time and discrete transitions, i.e. in a given configuration either time progresses (a silen t action in the languages recognised b y TSCA) or a discrete step to a new configuration is p erformed. Consequently , we defined an algorithm to compute the orchestration syn thesis of TSCA. T o resp ect the timing constraints, w e used the notion of zones from timed games [ 4 , 19 ]. The resulting synthesis algorithm resem bles a timed game, but it differs from classical timed game algorithms [ 4 , 19 , 25 ] by com bining t w o separate games, viz. r e achability games (to ensure that marked states must b e reachable) and safety games (to ensure that forbidden states are nev er tra v ersed). A TSCA migh t b e suc h that all bad configurations are unreachable (i.e. it is safe), while at the same time no final configuration is reachable (i.e. the resulting orchestration is empt y). V ol. 16:2 SYNTHESIS OF ORCHESTRA TIONS AND CHOREOGRAPHIES 9:25 8. Conclusion This pap er presents our recent efforts, originally published in [ 14 ], concerning bridging the gap b etw een the most permissive controller synthesis from Supervisory Control Theory with synthesis algorithms of orchestrations and c horeographies for a formal mo del of service con tracts called Mo dal Service Con tract Automata. This includes a nov el algorithm capable of syn thesising a safe non-blo c king comp osition of service contracts that is directly translatable in to a c horeographed formalism. A further contribution is an abstract syn thesis algorithm that generalises the synthesis of the choreograph y , as w ell as that of the orc hestration and that of the most p ermissive con troller. This pap er includes the pro ofs of all statemen ts from [ 14 ]. F urthermore, it con tains a formal demonstration that the different syn thesis algorithms are related through a notion of refinement, which allo ws us to formally pro v e that, under mild assumptions, the orchestration syn thesis is an abstraction of the mp c synthesis. Finally , the pap er includes an extensive running example from the service domain that illustrates our con tributions. The prop erties to b e enforced in the algorithms presen ted in this pap er are all inv arian ts sp ecified through either forbidden states or forbidden transitions. F uture w ork is needed to in v estigate the abstract syntheses under other non-in v arian t prop erties. Another av enue for future researc h is to in v estigate the differen t features of micro-services with respect to services, and to study what is needed to adapt the formalism of (timed/mo dal service) con tract automata and our results to deal with micro-services. A ckno wledgments W e ac kno wledge useful comments from the reviewers and funding from the MIUR PRIN 2017FTXR7S pro ject IT MaTT erS (Methods and T ools for T rust w orth y Smart Systems). References [1] L. Acciai, M. Boreale, and G. Zav attaro. Behavioural contracts with request-resp onse op erations. Sci. Comp. Pr o gr am. , 78(2):248–267, 2013. doi:10.1016/j.scico.2011.10.007 . [2] R. Alur and D. Dill. A Theory of Timed Automata. The or et. Comp. Sci. , 126(2):183–235, 1994. doi:10.1016/0304- 3975(94)90010- 8 . [3] S. Ap el, D. S. Batory , C. Kästner, and G. Saake. F e ature-Oriente d Softwar e Pro duct Lines: Conc epts and Implementation . Springer, 2013. doi:10.1007/978- 3- 642- 37521- 7 . [4] E. Asarin, O. Maler, A. Pnueli, and J. Sifakis. Controller Synthesis for Timed Automata. IF AC Pr o c. V ol. , 31(18):447–452, 1998. doi:10.1016/S1474- 6670(17)42032- 5 . [5] F. Atampore, J. Dingel, and K. Rudie. Automated Service Comp osition Via Sup ervisory Control Theory. In WODES , pages 28–35. IEEE, 2016. doi:10.1109/WODES.2016.7497822 . [6] S. Azzopardi, G. J. Pace, F. Schapac hnik, and G. Schneider. Contract automata: An op erational view of contracts b etw een in teractiv e parties. Artif. Intel l. L aw , 24(3):203–243, 2016. doi:10.1007/ s10506- 016- 9185- 2 . [7] M. Bartoletti, T. Cimoli, and R. Zunino. Compliance in Beha vioural Con tracts: A Brief Survey. In Pr o gr amming L anguages with Applic ations to Biolo gy and Se curity , volume 9465 of LNCS , pages 103–121. Springer, 2015. doi:10.1007/978- 3- 319- 25527- 9_9 . [8] D. Basile, P . Degano, and G. L. F errari. Automata for Sp ecifying and Orchestrating Service Con tracts. L o g. Meth. Comp. Sci. , 12(4:6):1–51, 2016. doi:10.2168/LMCS- 12(4:6)2016 . [9] D. Basile, P . Degano, G. L. F errari, and E. T uosto. Playing with Our CA T and Comm unication- Cen tric Applications. In FOR TE , v olume 9688 of LNCS , pages 62–73. Springer, 2016. doi:10.1007/ 978- 3- 319- 39570- 8_5 . 9:26 D. Basile, M.H. ter Beek, and R. Pugliese V ol. 16:2 [10] D. Basile, P . Degano, G. L. F errari, and E. T uosto. Relating tw o automata-based mo dels of orchestration and choreograph y . J. L o g. Algebr. Meth. Pr o gr am. , 85(3):425–446, 2016. doi:10.1016/j.jlamp.2015. 09.011 . [11] D. Basile, F. Di Giandomenico, S. Gnesi, P . Degano, and G. L. F errari. Sp ecifying V ariabilit y in Service Con tracts. In V aMoS , pages 20–27. ACM, 2017. doi:10.1145/3023956.3023965 . [12] D. Basile, M. H. ter Beek, P . Degano, A. Legay , G. L. F errari, S. Gnesi, and F. Di Giandomenico. Con troller synthesis of service contracts with v ariabilit y. Scienc e of Computer Pr o gr amming , 187, 2020. doi:10.1016/j.scico.2019.102344 . [13] D. Basile, M. H. ter Beek, and A. Legay . Timed service contract automata. Innovations Syst. Softw. Eng. , 2020. doi:10.1007/s11334- 019- 00353- 3 . [14] D. Basile, M. H. ter Beek, and R. Pugliese. Bridging the Gap Bet ween Sup ervisory Control and Co ordination of Services: Synthesis of Orchestrations and Choreographies. In COORDINA TION , volume 11533 of LNCS , pages 129–147. Springer, 2019. doi:10.1007/978- 3- 030- 22397- 7_8 . [15] D. S. Batory . F eature Mo dels, Grammars, and Prop ositional F ormulas. In SPLC , volume 3714 of LNCS , pages 7–20. Springer, 2005. doi:10.1007/11554844_3 . [16] A. Bouguetta ya, M. Singh, M. Huhns, Q. Z. Sheng, H. Dong, Q. Y u, A. G. Neiat, S. Mistry , B. Benatallah, B. Medjahed, M. Ouzzani, F. Casati, X. Liu, H. W ang, D. Georgakopoulos, L. Chen, S. Nepal, Z. Malik, A. Erradi, Y. W ang, B. Blak e, S. Dustdar, F. Leymann, and M. P apazoglou. A Service Computing Manifesto: The Next 10 Y ears. Commun. ACM , 60(4):64–72, 2017. doi:10.1145/2983528 . [17] R. Bruni, I. Lanese, H. C. Melgratti, and E. T uosto. Multiparty Sessions in SOC. In COORDINA TION , v olume 5052 of LNCS , pages 67–82. Springer, 2008. doi:10.1007/978- 3- 540- 68265- 3_5 . [18] C. G. Cassandras and S. Lafortune. Intr o duction to Discr ete Event Systems . Springer, 2006. doi: 10.1007/978- 0- 387- 68612- 7 . [19] F. Cassez, A. David, E. Fleury , K. G. Larsen, and D. Lime. Efficient On-the-Fly Algorithms for the Analysis of Timed Games. In CONCUR , volume 3653 of LNCS , pages 66–80. Springer, 2005. doi:10.1007/11539452_9 . [20] G. Castagna, M. Dezani-Ciancaglini, and L. Pado v ani. On Global Types and Multi-Part y Sessions. L o g. Meth. Comp. Sci. , 8(1:24):1–45, 2012. doi:10.2168/LMCS- 8(1:24)2012 . [21] G. Castagna, N. Gesb ert, and L. P adov ani. A Theory of Contracts for W eb Services. ACM T r ans. Pr o gr am. L ang. Syst. , 31(5):19:1–19:61, 2009. doi:10.1145/1538917.1538920 . [22] A. Classen, M. Cordy , P . - Y. Sc hobbens, P . Heymans, A. Legay , and J. - F. Raskin. F eatured T ransition Systems: F oundations for V erifying V ariabilit y-In tensiv e Systems and Their Application to L TL Model Chec king. IEEE T r ans. Softw. Eng. , 39(8):1069–1089, 2013. doi:10.1109/TSE.2012.86 . [23] S. Cranen, J. F. Gro ote, J. J. A. Keiren, F. P . M. Stapp ers, E. P . de Vink, W. W esselink, and T. A. C. Willemse. An Overview of the mCRL2 T o olset and Its Recent Adv ances. In T ACAS , volume 7795 of LNCS , pages 199–213. Springer, 2013. doi:10.1007/978- 3- 642- 36742- 7_15 . [24] P . Darondeau, J. Dubreil, and H. Marchand. Sup ervisory Control for Modal Sp ecifications of Services. IF AC Pr o c. V ol. , 43(12):418–425, 2010. doi:10.3182/20100830- 3- DE- 4013.00069 . [25] A. David, K. G. Larsen, A. Legay , U. Nyman, and A. Wąsowski. Timed I/O Automata: A Complete Sp ecification Theory for Real-time Systems. In HSCC , pages 91–100. ACM, 2010. doi:10.1145/1755952. 1755967 . [26] L. de Alfaro and T. Henzinger. Interface Automata. In ESEC/FSE , pages 109–120. ACM, 2001. doi: 10.1145/503209.503226 . [27] M. Dezani-Ciancaglini and U. de’Liguoro. Sessions and Session T yp es: An Overview. In WS-FM , volume 6194 of LNCS , pages 1–28. Springer, 2010. doi:10.1007/978- 3- 642- 14458- 5_1 . [28] G. F euillade and S. Pinchinat. Mo dal Sp ecifications for the Control Theory of Discrete Even t Systems. Discr ete Event Dyn. Syst. , 17(2):211–232, 2007. doi:10.1007/s10626- 006- 0008- 6 . [29] S. T. J. F orsc helen, J. M. v an de Mortel-F ronczak, R. Su, and J. E. Roo da. Application of sup ervisory con trol theory to theme park vehicles. Discr ete Event Dyn. Syst. , 22(4):511–540, 2012. doi:10.1007/ s10626- 012- 0130- 6 . [30] C. Gierds, A. J. Mooij, and K. W olf. Reducing A dapter Synthesis to Controller Synthesis. IEEE T r ans. Servic es Computing , 5(1):72–85, 2012. doi:10.1109/TSC.2010.57 . [31] P . Gohari and W. M. W onham. On the complexit y of sup ervisory control design in the R W framew ork. IEEE T r ans. Syst., Man, Cyb ern. B, Cyb ern. , 30(5):643–652, 2000. doi:10.1109/3477.875441 . V ol. 16:2 SYNTHESIS OF ORCHESTRA TIONS AND CHOREOGRAPHIES 9:27 [32] K. Honda, N. Y oshida, and M. Carbone. Multiparty Asynchronous Session T ypes. In POPL , pages 273–284. ACM, 2008. doi:10.1145/1328438.1328472 . [33] H. Hüttel, I. Lanese, V. T. V asconcelos, L. Caires, M. Carb one, P . - M. Deniélou, D. Mostrous, L. Pado v ani, A. Rav ara, E. T uosto, H. T orres Vieira, and G. Zav attaro. F oundations of Session Types and Behavioural Contracts. ACM Comput. Surv. , 49(1):3:1–3:36, 2016. doi:10.1145/2873052 . [34] N. Kav an tzas, D. Burdett, G. Ritzinger, T. Fletc her, Y. Lafon, and C. Barreto. W eb Services Choreogra- ph y Description Language v1.0. https://www.w3.org/TR/ws- cdl- 10/ , 2005. [35] J. Křetínský. 30 Y ears of Mo dal T ransition Systems: Survey of Extensions and Analysis. In Mo dels, Algorithms, L o gics and T o ols , v olume 10460 of LNCS , pages 36–74. Springer, 2017. doi:10.1007/ 978- 3- 319- 63121- 9_3 . [36] C. Laneve and L. Pado v ani. An algebraic theory for web service contracts. F orm. Asp. Comp. , 27(4):613– 640, 2015. doi:10.1007/s00165- 015- 0334- 2 . [37] J. Lange, E. T uosto, and N. Y oshida. F rom Communicating Machines to Graphical Choreographies. In POPL , pages 221–232. A CM, 2015. doi:10.1145/2676726.2676964 . [38] K. G. Larsen, U. Nyman, and A. Wąsowski. Mo dal I/O Automata for Interface and Pro duct Line Theories. In ESOP , volume 4421 of LNCS , pages 64–79. Springer, 2007. doi:10.1007/978- 3- 540- 71316- 6_6 . [39] N. Lynch and M. T uttle. An In tro duction to Input/Output Automata. CWI Q. , 2:219–246, 1989. URL: https://ir.cwi.nl/pub/18164/18164A.pdf . [40] J. Michaux, E. Na jm, and A. F an techi. Session types for safe W eb service orchestration. J. L o g. A lgebr. Pr o gr am. , 82(8):282–310, 2013. doi:10.1016/j.jlap.2013.05.004 . [41] C. P eltz. W eb Services Orchestration and Choreography. IEEE Comp. , 36(10):46–52, 2003. doi:10. 1109/MC.2003.1236471 . [42] K. Pohl, G. Böckle, and F. J. v an der Linden. Softwar e Pr o duct Line Engine ering: F oundations, Principles, and T e chniques . Springer, 2005. doi:10.1007/3- 540- 28901- 1 . [43] P . J. Ramadge and W. M. W onham. Sup ervisory con trol of a class of discrete even t pro cesses. SIAM J. Contr ol Optim. , 25(1):206–230, 1987. doi:10.1137/0325013 . [44] M. H. ter Beek, A. Bucchiarone, and S. Gnesi. W eb Service Composition Approaches: F rom Industrial Standards to F ormal Metho ds. In ICIW . IEEE, 2007. doi:10.1109/ICIW.2007.71 . [45] M. H. ter Beek, J. Carmona, R. Hennick er, and J. Kleijn. Communication Requiremen ts for T eam Automata. In COORDINA TION , volume 10319 of LNCS , pages 256–277. Springer, 2017. doi:10.1007/ 978- 3- 319- 59746- 1_14 . [46] M. H. ter Beek, E. P . de Vink, and T. A. C. Willemse. F amily-Based Model Checking with mCRL2. In F ASE , volume 10202 of LNCS , pages 387–405. Springer, 2017. doi:10.1007/978- 3- 662- 54494- 5_23 . [47] M. H. ter Beek, A. F antec hi, S. Gnesi, and F. Mazzanti. Mo delling and analysing v ariabilit y in pro duct families: Mo del chec king of mo dal transition systems with v ariabilit y constraints. J. L o g. A lgebr. Meth. Pr o gr am. , 85(2):287–315, 2016. doi:10.1016/j.jlamp.2015.11.006 . [48] M. H. ter Beek, M. A. Reniers, and E. P . de Vink. Sup ervisory Controller Synthesis for Pro duct Lines Using CIF 3. In ISoLA , volume 9952 of LNCS , pages 856–873. Springer, 2016. doi:10.1007/ 978- 3- 319- 47166- 2_59 . [49] R. J. M. Theunissen, D. A. v an Beek, and J. E. Ro o da. Impro ving evolv abilit y of a patien t comm unication con trol system using state-based sup ervisory control synthesis. A dv. Eng. Inform. , 26(3):502–515, 2012. doi:10.1016/j.aei.2012.02.009 . [50] D. A. v an Beek, W. J. F okkink, D. Hendriks, A. Hofk amp, J. Mark o vski, J. M. v an de Mortel-F ronczak, and M. A. Reniers. CIF 3: Mo del-Based Engineering of Sup ervisory Controllers. In T A CAS , volume 8413 of LNCS , pages 575–580. Springer, 2014. doi:10.1007/978- 3- 642- 54862- 8_48 . [51] Q. Yi, X. Liu, A. Bouguettay a, and B. Medjahed. Deploying and managing W eb services: issues, solutions, and directions. VLDB J. , 17(3):735–572, 2008. doi:10.1007/s00778- 006- 0020- 3 . Appendix A. Proofs W e pro vide the pro ofs of Theorem 5.4 and Theorem 5.5 only sk etc hed in Section 5. 9:28 D. Basile, M.H. ter Beek, and R. Pugliese V ol. 16:2 Theorem 5.4 (Abstract orc hestration syn thesis) . The or chestr ation synthesis function of Definition 3.2 c oincides with the instantiation of the abstr act synthesis function of Defini- tion 5.1 wher e, for a generic tr ansition t = ( ~ q , ~ a, ~ q 0 ) , pr e dic ates φ p and φ f ar e define d as fol lows: φ or c p ( t, K , R ) = ( t is a r e quest ) ∨ ( ~ q 0 ∈ R ) φ or c f ( t, K , R ) = @ ( ~ q 2 ~ a 2 − → ~ q 2 0 ) ∈ T 2 K : ( ~ a 2 is a match ) ∧ ( ~ q 2 , ~ q 2 0 6∈ Dangling ( K )) ∧ ( ~ q ( i ) = ~ q 2 ( i ) ) ∧ ( ~ a ( i ) = ~ a 2 ( i ) = a ) Pr o of. The pro of is analogous to that of Theorem 5.3 but relying on Theorem 3.2 instead of Theorem 2.4. The full pro of follo ws. Let K or c A and K abs A b e the con trollers computed through Theorems 3.2 and 5.2, resp ectively . The pro of pro ceeds by induction on the fixed p oint iterations and by case analysis. F or the base case, by definition K or c 0 = K abs 0 = A and R abs 0 = R or c 0 = Dangling ( K 0 ) . F or the inductive case, let i b e a fixed p oint iteration. Assuming K or c i − 1 = K abs i − 1 and R or c i − 1 = R abs i − 1 , we prov e K or c i = K abs i and R or c i = R abs i . The equiv alence K or c i = K abs i follo ws b ecause at the i th iteration φ or c p detects exactly the same transitions that are pruned b y the orchestration synthesis algorithm. F or the equiv alence R or c i = R abs i , w e hav e R or c i = R or c i − 1 ∪ { ~ q | ( ~ q − → ) ∈ T 2 A is un - c ontr ol lable in K or c i } ∪ Dangling ( K or c i ) , and R abs i = R abs i − 1 ∪ Dangling ( K abs i ) ∪ { ~ q | ( ~ q a − → ) = t ∈ T 2 A , φ or c f ( t, K abs i − 1 , R abs i − 1 ) = true } . Since K or c i = K abs i , also the dangling states are equiv alent. It remains to pro v e that { ~ q | ( ~ q − → ) ∈ T 2 A is unc ontr ol lable in K or c i } = { ~ q | ( ~ q − → ) = t ∈ T 2 A , φ or c f ( t, K abs i − 1 , R abs i − 1 ) = true } . This equiv alence is straightforw ard b y the definition of φ or c f , Definition 3.1, and the inductiv e h yp othesis. Theorem 5.5 (Abstract c horeograph y syn thesis) . The chor e o gr aphy synthesis function of Definition 4.4 c oincides with the instantiation of the abstr act synthesis function of Defini- tion 5.1, wher e given a generic tr ansition t = ( ~ q , ~ a, ~ q 0 ) , the pr e dic ates φ p and φ f ar e define d as fol lows, wher e ˆ T K ,R is define d in Definition 4.4: φ c or p ( t, K , R ) = ( t is a r e quest or offer ) ∨ ( ~ q 0 ∈ R ) ∨ t ∈ ˆ T K ,R φ c or f ( t, K , R ) = @ ( ~ q ~ a 2 − → ~ q 2 0 ) ∈ T 2 K : ( ~ a 2 is a match ) ∧ ( ~ q , ~ q 2 0 6∈ Dangling ( K )) ∧ ( ~ a ( i ) = ~ a 2 ( i ) = a ) Pr o of. The pro of is analogous to that of Theorem 5.3 but relying on Theorem 4.4 instead of Theorem 2.4. The full pro of follo ws. Let K c or A and K abs A b e the con trollers computed through Theorems 4.4 and 5.2, resp ectively . The pro of pro ceeds by induction on the fixed p oint iterations and by case analysis. F or the base case, by definition K c or 0 = K abs 0 = A and R abs 0 = R c or 0 = Dangling ( K 0 ) . F or the inductive case, let i b e a fixed p oint iteration. Assuming K c or i − 1 = K abs i − 1 and R c or i − 1 = R abs i − 1 , we prov e K c or i = K abs i and R c or i = R abs i . The equiv alence K c or i = K abs i follo ws b ecause at the i th iteration φ c or p detects exactly the same transitions that are pruned by the c horeograph y synthesis algorithm (and takes the same non-deterministic choices). V ol. 16:2 SYNTHESIS OF ORCHESTRA TIONS AND CHOREOGRAPHIES 9:29 F or the equiv alence R c or i = R abs i , w e hav e R c or i = R c or i − 1 ∪ { ~ q | ( ~ q − → ) ∈ T 2 A is un - c ontr ol lable in K c or i } ∪ Dangling ( K c or i ) , and R abs i = R abs i − 1 ∪ Dangling ( K abs i ) ∪ { ~ q | ( ~ q a − → ) = t ∈ T 2 A , φ c or f ( t, K abs i − 1 , R abs i − 1 ) = true } . Since K c or i = K abs i , also the dangling states are equiv alent. It remains to pro v e that { ~ q | ( ~ q − → ) ∈ T 2 A is unc ontr ol lable in K c or i } = { ~ q | ( ~ q − → ) = t ∈ T 2 A , φ c or f ( t, K abs i − 1 , R abs i − 1 ) = true } . This equiv alence is straightforw ard b y the definition of φ c or f , Definition 4.3, and the inductiv e h yp othesis. This work is licensed under the Creative Commons Attribution License. T o view a copy of this license, visit https://creativecommons.org/licenses/by/4.0/ or send a letter to Creative Commons, 171 Second St, Suite 300, San F rancisco , CA 94105, USA, or Eisenacher Strasse 2, 10777 Berlin, Germany
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment