Reversible Data Hiding in Encrypted Images Using MSBs Integration and Histogram Modification
This paper presents a reversible data hiding in encrypted image that employs based notions of the RDH in plain-image schemes including histogram modification and prediction-error computation. In the proposed method, original image may be encrypted by…
Authors: Ammar Mohammadi
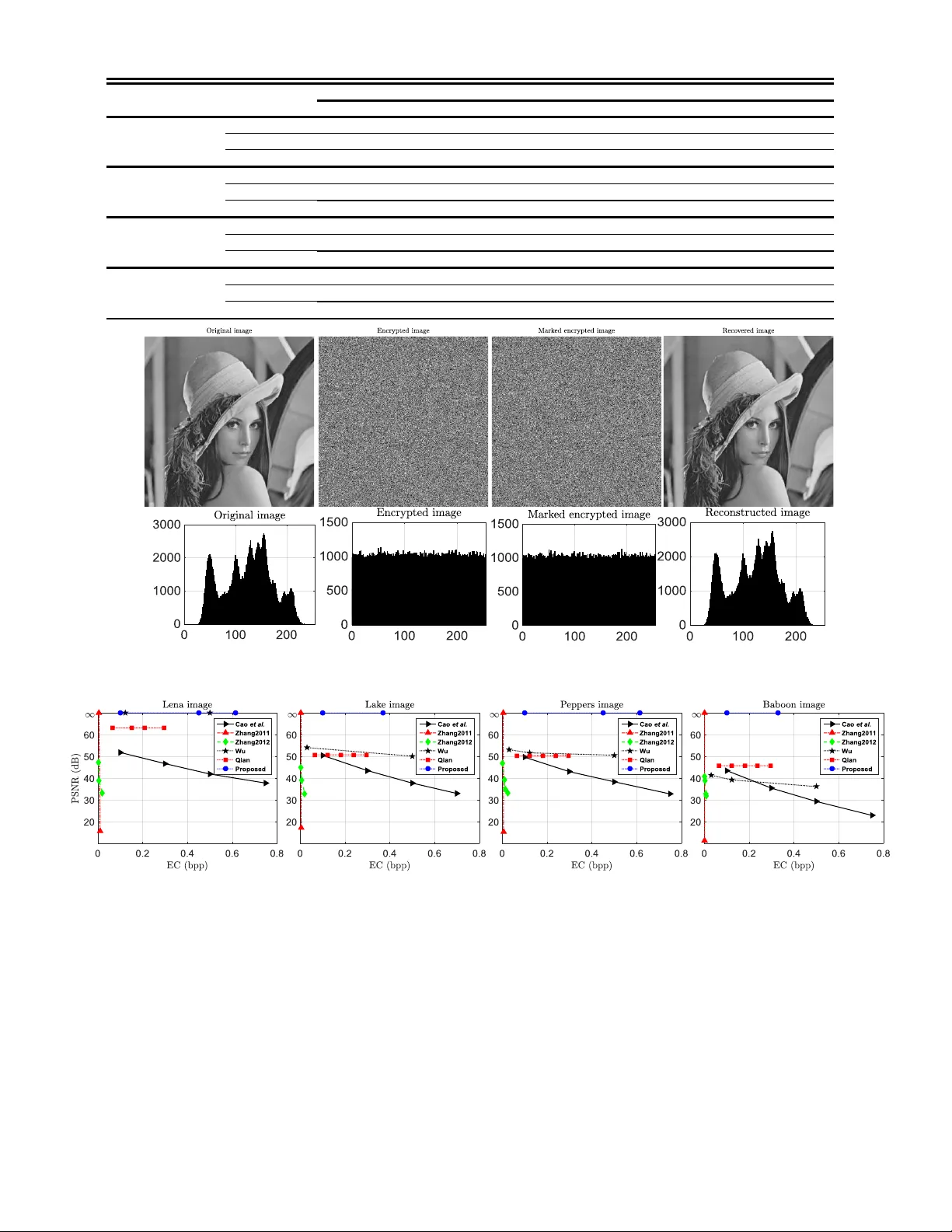
Abstract — This paper presents a r eversible data hiding in an encrypted image that employs based no tions of reversible data hiding ( RDH ) in a plain-image including histogram modification and prediction-error c omputation. In the proposed method, the original image may be encrypted by an arbitrary stre am cipher . The most significant bit (M SB) of encrypted pix els are integrated to va cate room for em bedding data b its. The in tegrated MSBs will be more robust a gainst failure of recon struction if they are modified fo r data e mbedding. At the recipient, w e e mplo y chess- board predictor for lossless reconstruction of the original image thanks to prediction-error analysis . Co mpar ing to existent RDHEI algorithms, not only a se parable method for data extraction is proposed, but also the content-o wner may atta in a perfect reconstruction of the original image w ithout having data hider ’s key. E x perimental r esults confirm that the propo sed method outperforms state of the art methods. Index Terms — Histogram modification, prediction-errors, reversible data hiding, vacating room after encryption. I NTRODUCTI ON eversible data hiding in plai n-image (RDH PI ) is drastica lly developed by many researchers in recent years [1]. In RDHPI, secret d ata is imperceptibly embedded in a p lain-image in a way that the original image can be lo sslessly recover ed after error-free secret data extraction. More presented papers in RDHPI drive from three main notions, namely d ifference expansion, histogram modification and lossless compressio n pioneered b y [2] , [3] and [4], respec tively. Some d eveloped studies also employ pr ediction-erro r to improve hiding capacit y in a determined le vel of distortion. Attaining more accurate prediction, there exists sharpe r histog ram of error s that can be modified to e mbed secret data. For example, schemes in [ 5] and [6] exp loit gradient-adj usted predictio n (GAP) and median edge detec tor ( ME D) predictors introduced in [7] and [8] , respectively. Tsai [9] present a predictor , may be denoted as local dif ference (LD) predictor, that co mputes d ifference between pixels intensities in a local area of the image and the most ce ntral one to bring ou t prediction-erro rs. T hey e mbed secret data via histogram modification o f the p rediction-erro rs. Sachnev further pr esent cross- dot predicto r that divides an image into t wo “cross” and “ d ot” sets [10] . Dot set may be predicted using cross o ne and vice versa. T he cross-do t predictor is also employed as a chess -board ( CB) predictor in [11]. Besides RDHPI, reversible d ata hiding in encr ypted image (RDHEI) is a solution to preserve privac y for cloud computing/storage ser vices . I n RDHEI, there are three p arties: image-owner, data hider and recipient. An i mage-owner may not trust a channel ad ministrator (or inferior assistant) ; consequently, the image-owner encrypts the image b efore uploading to cloud server whereas he/she is not motivated to compress h is/her original-content before encryption . On the other side, data hider , i.e. the channel ad ministrator, is not allowed to have the original-co ntent but authorized to embe d some handy data in the encrypted image . Therefore, the approach should guarantee lossless original image reconstruction and error -free data extraction at the recipient . Th ese challenges are th e cause of developing R DHEI. Schemes introduced in R DH EI may b e classified into three categor ies namely: i) reserving room before encryption (RRBE) [12 -19] , ii) vacating roo m b y e ncryption (VRBE) [20- 26] and iii) vacating room after encr yption ( VR AE) [27- 32] . In RRBE schemes, t here ex ists a p re-processin g before encryption that enables data hider to embed data bit s in the encrypted i mage. T hus, in most RRBE sche mes, data hider is not ab solutely blind to the ori ginal content. O n the ot her hand, most notions in VRBE are realized by encrypting some p ixels intensities in a local area of the image using the same cip her byte . T his ap proach pr eserv es co rrelation bet ween pixels employed to embed d ata bits . T hus, so me information remai ns disclosed in VRBE. Except [17], the schem e s present ed in RRBE and VRBE are separable, which means extraction of the data bits at the recipient is not t ied to decr ypted information. On the other hand, in joint ones data extraction can be per formed just using the d ecrypted marked image. In VRAE proced ure, data hider is co mpletely blind to original information. Af ter image encryption, data h ider vacates room to embed d ata bits w it hout any knowledge of the original- content. Some m ethods in VRAE ar e j oint [ 28, 30, 31 ] while some others are separable [27, 2 9]. In [32], two different joint and separab le procedure s are introduced. T he separab le schemes in VRAE are m o re functio nal than joint VRAE schemes; in fact, they are even more functional than RRBE and VRBE schemes . Since data hider is absolutely blind to th e original-content, sep arable VR AE methods p reserve t he content-owner privacy more than the others. Neverthele ss , achieving high embedding ca pacity is more challengeable in separable VRAE tha n the other s . From using secret keys point of view, Chen et al. [15 ] classify three di fferent schemes namely shared independent Ammar Moham madi, Mohamm ad Ali Akhaee and Mansor Nak hkash Reversible Data Hiding in Encrypted Images Using MSBs Integration and Histogram Modification R (Corresponding author: Ammar Mohammadi.) and Mansor Nakhkash are with the Departme nt of Electrical Eng ineering, Yazd U niversity, Yaz d 89195 - 741, Iran (e-mail: mohammadi_a@st u.yazd.ac.ir and nakhkash@y azd.ac.ir ). M. A. Akhaee is with the Department of Electrical and C omp uter Engineering, College o f Eng., Univer sity of Tehran, Tehran, Iran, 1458889694 (e -mail: akhaee@ut.ac. ir ). secret keys (SIK), shared one key (SOK) [15] and shared no secret keys (SNK) [12, 17]. In SIK, there exist two d ata hider ( ) and image-o wner ( ) keys that are s hared with rec ipient independently while in SO K, there exists just o ne key. In SN K there exists no key to be shared. M ost schem es in RDHEI, including the pr oposed one, emplo y SIK to manage secret keys. Generally, similar to RDHPI, most scheme s in RDHEI use the correlation o f neighboring pixels i n an image a nd further employ main notio ns of RDHP I such as histogr am modification, difference expansion, and prediction-erro r computation. For example, schemes [1 5, 17] exploit differe nce expansion while Xiang and Luo emplo y histogram modification of the prediction-errors to reserve room bef ore encryption [12] . Huang et al. present a new framework in RDHE I that makes it possible to u se the most notions o f RDH in the p lain-image for the encrypted one [24]. In this self-contained sc heme, any kind of prediction technique including GAP, MED, C B and L D may be used to esti mate prediction-er rors. Schemes [19 ] and [2 0] use the based id ea of LD predicto r to embed data in the encrypted image. They rea lize a lossless reconstruction (LR ) of the original i mage and error-free extraction of data bit s. Qian and Z ha ng emplo y local co rrelation of n eighboring pixels as well to reconstruct the original pixel at the recipient [29]. Using ME D pred ictor, Yin et al. allocate some label s for al most all p ixels before e ncryption [14] . T hese labels are co mpressed via H uffman coding and are embedded along w ith data bits. They improve [19] and [20] naturally thanks to the source coding algorit hms. Fallahpour a nd Sedaaghi present a RDHPI m e thod that ap ply the sc heme of [3] in non-overlapped blocks of the plain-image to embed data using histogra m modificatio n of p ixels in a block [3 3]. In the same appro ach, Ge et al. introduce a RDHEI method that employs histo gram modificati on ([ 3] ) in non-overlapped blocks of the encrypted image to v acate roo m for data embedding [2 5] . As discussed, there exi st several schemes in R DHEI that employ based notio ns of R DHPI to embed d ata in the en crypted image. Here, we present a new schem e o f separable VRAE that uses idea of histogram modification to vacate room after encryption. In VRAE procedure, after a standard image e ncryption, data hider vacates room for data embedding without any knowled ge of the original-co ntent, i.e. data hider is completely blind to original infor mation. At the recipient side, when the scheme o f VRAE is separab le, the extraction o f data bits is not tied to decrypted i mage . Design and impleme ntation o f a separ able VRAE is more challengeable but more f unctional th an th e other approaches because d ata hider is blind to original -content in both embed ment and extraction sides. Her e, w e have improv ed other separable VRAE schemes than ks to histogram modification a nd MSB integration. T he CB predictor is also exploited to per fect reconstruction of the original i mage at the recipient. Indep endent secret keys, and are used to encrypt the original i mage and data bits, resp ectively. The rest of the paper is organized as follows. Related works are discussed i n section II. The prop osed m ethod is p resented in section III including b oth e mbedding a nd er ror-fr ee extraction of data bits and lossless reconstruction of the original image. Section IV demonstrat es the experimental results. Finally, section V co ncludes the pap er. R ELAT ED WORKS For more clarificatio n of the pro posed method, w e are goin g to explain the details of histogra m modification, CB predictor and prediction-erro r analyzing in the following. A. Histogram modification As discussed, Ni [3] present a RDHP I scheme using histogram modification of the original image. In this scheme , they embed data b its in the peak point o f the histogram that is the most frequent p ixel i n t he image. Accordingly, t hey vacate room by histogram modification for data e mbedding . In this way, reversible r econstruction of the or iginal image is possible. For instance , the peak p oint in the histogram of the Lena im age (Fig. 1a ) is “155”. Thus, to vacate room , all intensities of the image more than “155 ” are add ed by 1 (Fig. 1b) . In our proposed procedure, we apply the idea of histogram modification to vacate roo m in the e ncrypted image ( Fig. 6) . B. Black and white prediction Fig. 2 . P art of an imag e, whose p ixels are div ided into white and black sec tions. In this section, we present two predictors related to the CB predictor [10] . As described in Fig. 2, pixels of the i mage can be divided to three groups, white target pixe ls (WT Ps), black target pi xels (BT Ps) and b lack refere nce pi xels (BRPs) that respectively denoted by , (a) (b) Fig. 1. (a) Histog ram of the Lena ima ge. (b) Vacating room to embe d data bits. and . Data is embedded in target p ixels and reference pixels re main intact during e mbedding process. Predictio n of a white p ixel , , i s do ne by averagi ng o f its neighboring black ones , { } , (1) that d enoted white plus pred iction, WP P. T he prediction-error , is computed by In addition, a target black pix el ( ) can be p r edicted by averaging of its nei ghboring black ones (3) that denoted black cross prediction (BCP) . In (1) and (3), is the r ound function. Similarly, the pr edictio n-error is calculated by (4) C. Prediction-error an alysis According to (2) or (4), having a prediction -error and a predict ed value of an original pixel , the original pixel can be definitely reconstructed. For more explanation, let u s assume a predictio n -error that is co mputed from subtracting the original p ixel ( ) and its predicted value ( ) as: (5) A s proved in [19 ], even by having a r ange of prediction - errors , some signi ficant b its of the original pi xel will be retrieved if the y substit ute by data bits . I n one data bit embedment , t he M SB of the p ixel “ ” would be retrievable if (6 ) To gain a better insight, assume a pixel, , describing eig ht bits including th e LSB, , to the MSB, . Having (6), may be replaced by a data bit in a way that it can be agai n retrieved at the recipient. Employing more efficie nt pr edictor leads to sharp er histogram of the prediction-error s and accordingly provides the more pixels in the image t hat their pred iction-errors satis fy (6). Thus, there e xist more MSB s of the pi xels to be modified for data embedding. In Fig. 3 , the histograms o f predictio n-errors pr ovided by WPP, BCP, MED and GAP predictors are d emonstrated for Baboon . As shown, WPP provides sensibly a sharper histogram of the pr ediction-errors tha n the others . In addition, it see ms GAP makes sharper histogram than MED and BCP . If (6) is n ot satisfied, pixe ls whose prediction -errors are greater than or equal to 64 are not s uitable for data embedding . Let us denote “ ” as the number of pred iction-errors which do no t satis fy (6) and “ ” as the all pr ediction-errors i n an image. Accordingly, we de fine (7) as a p robability o f failure in reco nstructing the refor med MSB Fig. 4. Process o f data embedme nt. Fig. 3. Histograms o f prediction-erro rs provided by predictors of WP P, BCP , MED and GAP f or Baboon image. of a pixel r andomly picked u p . Using (7), w e ha ve , and for Baboon . Althou gh is significantly less tha n t he others, there still exists a pr obability of failure in reconstructi ng the original pixel s. As a so lution, we integrate several MSBs of target p ixels in ord er to mitigate the ri sk of failure . Therefore, -MSBs, as extracted features of target pi xels, are i ntegra te d using an i ntegration model, ( Fig. 5), and the integrated value is used to convey a data bit . The amount of co mputed depends not only upon the kind o f the employed predictor , but the type o f a host image . The lower the entropy of an image, the lower the probability of the failure can be attained i n the re c ov er y process . General ly, smoother images have less ; for instance, Lena and F16 images result in despite images like Baboo n. As a co nsequence , we employ the best p redictor, WPP, in our proposed sche me along with BCP . T HE PROPOSED SCHEME We introduce the propo sed scheme and its stages includi ng image encryption , e mbedding and extractin g data bits , and recovering the origi nal image. A. Image encryption The encrypted image is achieved using bitwise “exclusi ve or” of the original one w ith a strea m cipher provides by an encryption algorithm w ith an input secret k ey ( ). L et us classify pixel s forming encrypted image into three groups, namely encrypted white target pixels , , encrypted b lack target pixels , , and encrypted black r eference pixels , . Encrypted BRPs remain intac t d uring data embedding process and are used to reconstruct the black or white target pi xels at the recipient. B. Embedding data bits We describe em bedding process in Fig. 4 . Let set = { ,…, ,…, } be the a ssorted subsets of sources employed to convey data bits. The framework consi st of se veral steps, namely, feature extractio n, integratio n, vacati ng roo m , data embedment, disinte gration and forming marked sources . 1) Integration Integration model is demonstrated in Fig. 5 for a subset of , . Here , is a set of en crypted target pixels divided into subset of pixels, , . MSB of a pixel is taken as the feature. Therefore, is a set of extracted features, MSBs, of corresponding pixel s in . Integration is done by (8) is integration parameter of a source . Employing integration, -MSBs must b e changed instead of just one MSB to e mbed data bit that provides more rob ustness agains t fail ure in the reconstruction pro cess. 2) Vacating room by histog ram modification Regarding t he nature of a n en crypted image, the histogra m of the integrated features, , would have t he un iform distribution. E mploying the h istogram modification , we vac ate room in integrated feat ures. Note that, is a whole number less tha n . T he approach is a shrinking p rocess that shi fts each to a less one t hat has the most bitwise mutation than ; in other word s, is rep laced with its 1’s complement. At the result, t he shrunken a mounts, , , is achieved using Algorithm 1. 3) Data embedment Having ro om , -bits o f encrypted data, , encr ypted b y , may be embed ded in e mploying Algorithm 2 that results in marked features, . In this al gorithm, to e mbed an encr ypted data bit with value “1” in , it is r eplaced by its 1 ’s complement and to embed value “0” it is re mained intact. 4) Disintegration and fo rming marked sou rces In order to create a marked encrypted image, first, t he set has to be disintegrated using , (9) Substituting in the MSB of th e e ncrypted pixels, , marked sources , are made. Let us d emonstrate the embedding pro cess with an example. Suppose w e have 27 MSBs of the encr ypted pixels, , and . By inte gration, there exist nine w h ole nu mbers less than eight, . Employing Algorithm 1, vacat ing room is done by histogram modification, . Adapt values between 4 and 7 Fig. 5. Propose d model of integration. Fig. 6. The histogram o f an example of and sets. to smaller ones, room is vacated to embed ={1, 1 ,0 , 1 ,0, 0 ,1, 0 ,1}. E ventually, exploiting Algor ithm 2, the marked set , is attained. The histogram o f , and are depicted in Fig. 6. In disintegration, we have . C. Data extraction At the r ecipient, for data ex traction, we j ust need data hider key, . MSBs of pixels in are extracted to bring o ut . Considering inte gration mode l, to achieve , subsets of are integrated b y (8) w here is replaced by . Note that, = . Having , extracting data bits are done employing Algorithm 3. In Algorithm 3, ’th bit of the e ncrypted data, , is extracted using . Encr ypted bits are decrypted usin g to bring out . D. Recovering the original ima ge Reconstructing the or iginal image may b e initiated b y decryption of the marked encrypted image using . Let be the decrypted marked pixel s. B y replacing t he MSB of the decr ypted marked pixels w it h their 1’s complement values, an alternative set, , is formed. T herefore, there exist two candidates and , one of them is nominated as retr ieved s ubset , , that drive s fro m a decision process is shown in F ig. 7 . These two candidates are individually integrated using pr oposed integration model (Fig. 5) when feat ure set is prediction-error s. E mploying neighbor ing pixel of a source pixel, pred iction-errors may be calculated by WPP or BCP de pends on po sition of sou rce pixels can b e white or black, resp ectively. For subsets of , pr ediction-errors are computed. Therefore and ar e pr ediction-errors of corresponding pixels in and , respectivel y. Employing integration functio n that d efines the summatio n of absolute values of the features (1 0) we compute and . In an alternative notatio n, integration may be denoted by related sources of the features , and , respectively. As shown in Fig. 7, for decision, the source prov ides less integrated predictio n-errors nominated as reco vered source, , . In eq ual integrated pred iction-errors , is taken; nevertheless we probably have failure in recon struction . If and are close to each other, it will be a high risk in realizing LR . Therefore, the risk of failure in reconstruction ca n be analyzed by computing the di fference between and . (11) The larger , the lo wer risk would be obtained and vice versa. Employing and in Algorithm 4 , w e can define four class es of risk namely: h igh risk ( ) median risk ( ), low risk ( ) and very lo w risk ( ). Therefore, in each subset of -pixels, we have a risk anal ysis. The bigger is chosen, the more accurate eval uation of the ri sk would b e realized. E. Overall view of the proposed method In Fig. 8 a, we depict the g eneric block diagra m o f the Fig. 7 . Proced ure of making decision to recover or iginal set. Algorithm 1: Shrinking the value of to . for to do if then end if end for Algorithm 2: Embedding data bits for to do if then end if end for Algorithm 3: Extracting data bits for to do if then else end if end for Algorithm 4: Ris k of failure in reco nstruction if then else if then else if then else end if proposed scheme. T here exist two sources of encrypted target pixels e mployed to embed data bits. Data bits at first are embedded in the encr ypted white target pi xels, , and then in t he encrypted black target pixels , , a s demonstrated in Subsection III -B by their own integration parameters and . After e mbedding, the marked encrypted image, including the marked target pixels, and , is created. Meanwhile, BRPs are just encrypted w it hout any more modification. They will be employed to reconstruct other pixels at the recipient. The y form 25% of the image. Now, assuming an o riginal image has the size of , and regarding i ntegration p arameters of { }, embeddin g capacity ( EC ) can be achieved by (12) Thus, b y choosing { }, the most po ssible EC that is would be achieved. As sho wn i n Fig. 8b, extracting data bits and reconstruction of the original image are separatel y accomplished . Data extraction is de monstrated in S ubsection III- C . It is performed for the marked source s, and . Reconstructing the original image is initiated b y decryption of the marked encrypted im age using . Therefore, BRPs , , are co mpletely recovered just by decryption. Ha ving , BTPs may be retrieved in a pro cedure described in Subsection III - D , where . Havin g and , WT Ps are recovered in similar proced ure when . BPP and WPP predictor s are used to compute p rediction -errors of and , respectivel y. The risk of failure is included in t he retrieval process as well. If the encr ypted target pixels are used sequentially for integration, the MSBs o f pixels in rougher regions are considered as a set of integrat ed MSBs that rises possibilit y of failure in the reconstruction process . Thus, b y scr ambling the encrypted target pixels, w e can mitigate the risk at the recipie nt. E XPERI M ENTAL R ESULT The perform ance of the proposed separ able VRAE algorithm is evaluated by conducting several experi ments. Twelve grayscale images F16 , Lena, Spla sh, House, Boa t, Elaine, Lake, Peppers, Baboon , Stream, Aerial and APC from the US C-SIP I database are used as our test images. Also, BOWS2 o riginal database, including 1 0000 greyscale images, are employed to confirm that th e proposed algorithm c an provide LR o f the original image and error -free extrac tion of data b its. The s ize of all test i mages are 5 12×512 . In experiments, the first and t he last two ro ws and columns o f the ima ge are ignored in data embedding process. T he p eak signal- to -noise ratio (PSNR) is used to estimate the quality of the recovered image. PSNR means LR of the original i mage. Choosing integration parameters, , is somewhat relevant to entropy of an image. T he greater the entrop y o f t he image, the greater value o f must be selected for LR. However, the lar ger is c hosen, the s maller EC w o uld Fig. 9. Efficiency evaluation of the propose d scheme using 10000 test images of Bows2 d atabase in different integration parameters, . We just exploit to restore t he original images. The sy mbol is the failure rate. ( a) ( b ) F i g . 8 . T h e g e n e r i c b l o c k d i a g r a m o f t h e p r o p o se d s c h e me . ( a ) Emb e d d i n g d a t a a n d f o r m i n g t h e m a r k e d e n c r y p t e d i mag e . ( b ) Ex t r a c t i n g d a t a a n d r e c o v e r i n g t h e o r i g i n a l i mag e . T ABLE I P ERFORMANCE ANALYSIS OF THE PROPOSED SCHEME EMP LOYING 12 T EST IMAGES . Items images F16 Lena Splash House Boat Elaine Lake Peppers Baboon Stream Aerial APC EC (bits) 161290 161290 161290 161290 86021 193548 96774 161290 86021 80645 86021 96774 1 1 1 1 2 1 2 1 2 2 2 2 2 2 2 2 3 1 2 2 3 4 3 2 PSNR Retrieving 4 0 0 0 0 0 0 8 5 0 0 0 136 80 4 163 44 27 2 161 1052 182 130 4 Retrieving 0 0 0 0 0 1 0 0 13 0 0 0 37 9 1 33 68 40 93 35 885 25 103 11 T ABLE II S IX IMAGES OF BOWS2 DATABASE THAT HAVE THE MOST NUMBE R OF H I R FOR EMBEDDING DATA I N . Items Images (.pgm ) 6502 6501 6537 6498 6514 9373 Retrieving 15 11 10 6 4 4 947 923 778 943 415 460 Retrieving 1 1 2 1 0 2 285 259 413 415 60 170 PSNR 52.39 49.38 52.39 55.4 The number o f deforme d MSBs 6 12 0 6 3 0 be ac hieved. In Table I, the precise for LR of the test images is tabulated. By taking for the Elain e image, the most po ssible EC in t he prop osed method that is 193548 bits, is achieved. On the other hand , the S tream i mage provides the lo west EC. In this image, the lowest possible integration para meters for LR are . Also, in Table I , the risk of failure i n reconstruction is evaluated by computing the number of subset that take either HiR or Me R. Although F16 , Pepper s and Baboon images are reconstruct ed perfectly, they include 4, 8 and 5 hig h risk subset s of -pixels , respectively. Also, in r econstructing the s ubsets of -pixels, Baboon and Elaine images ta ke 1 3 and 1 sub sets o f high ri sk, respectively. Accounti ng the num ber of HiR and MeR, Baboon is more suscepti ve to failure in reconstructio n ; nonetheles s, by choosing { , } for d ata embedding in Babo on , no sub set of H i R is le ft. It is obtained by pa ying the cost of reducing EC to 5 5913 bits. In our sc heme, w e assume that data hider is completely blind to the original-content; thus, we ca nnot find ou t the le ast possible precise f or LR. Ne vertheless , in the n ext subsection, it is con firm ed th at a set of m ay be always found out for LR. It is worth mentioning that in the p roposed scheme, error -free e xtraction o f data b its is realized for all test images under any circumstanc es. A. Lossless retrieval In Fig . 9 , w e de monstrate the performance of the pro posed scheme in LR and error- fr ee extraction of data b its using 10 000 test images of B OWS2 database. As shown, for various , we accomplished t he proposed algorithm to result in the number o f fail ure in reconstruction. For example, in , from 1 0000 test i mages, t here exist 11 images t hat are not per fectly reconstructed and co nsequen tly the failure rate is . As can be seen, the more is preferred , th e less E C and definitel y the less failure rate would be achieved. I n , is zero. Therefore, there exists per manently a set o f to pro vide LR for all 1 0000 test images . As s hown in Fi g. 9, m o difying affects EC and m ore than As an insta nce, in increasing from two to three d ecreases E C and as much as bits and 0.02 49, respectively; while in , the i ncrement of has no noticeable impact on EC and . Implementing the proposed algorithm for , we sort all 10 000 reconstructed i mages in a descending order by the nu mber of their subsets w hic h are HiR in retrieving . The first six sor ted images ar e listed in T able II. In t his tab le, PSNR de monstrates four i mages that are not reconstructed lo sslessly and t hus, four out o f all 11 failures, i.e. Fig. 9 for , include in t he fir st si x sorted i mages. It confirms that the risk analy sis is a proper assessment for evaluating LR , i.e. all 11 failures are included in the first 50 sorted i mages. In any f ailure, there exist some defor med MSB s that cannot be recovered correctly. The number of defor med M SBs are demonstrated in Tab le II for various images. The maximu m one is just 12 bits for 650 1.pgm image; thus, there is not much b it error rate when LR does not realized. B. A visual demonstration of the proposed scheme Fig . 10 is a visual demonstratio n o f t he pr oposed scheme including the origi nal, encrypted, marked encrypted and reconstructed i mages with their dep icted histograms , respectively. We optionally e mploy AES in t he cou nter mode, i.e. a stream cipher procedure, to encrypt the Len a test image. As shown in Fi g. 10 b, af ter encryption there exist no kno wledge of the original content . Due to u sing a standard en cryptio n algorithm like AES, as can be observed , the histo gram o f the encrypted image is uni formly distributed which guarantees the security of the propo sed algorithm. Since in t he propo sed scheme, data hider is co mpletely blind to the original -content , it absolutely preserves the content -owner privacy. Fig. 10c is a description of the marked encrypted image. The histogram still has a u niform distribution. The original image is losslessly reconstructed as shown in Fig . 10 d. C. Comparison with other scheme s In Table III, the pro posed scheme i s compared with other separable VRAE sc hemes. After i mage e ncryption , the proposed scheme vacate s room by “ histo gram modification o f the integrated MSBs ” (HMIM SB). Beside s, schemes [27] and [29] vacate room b y “ co mpressing t he least significant bits ” (CLSB) and “ encoding using LDPC code ” (ELDP C) , respectively. Mea nwhile, they ad opt some para meters to make a tradeoff bet ween embedding capac ity and lossless r ecovery . Their functionality is similar to the integration par ameters of the proposed sch eme . For a fair com p arison between HMIMSB and those of CLSB and E LDPC, we employ these para meters in such a w a y that all test i mages are p erfectly reconstructed. In this approach, we apply parameters , for CLSB , ELDPC and for HMIMSB . Note that by choosing less and , bo th EC and the ri sk of failure in reconstructi on ar e i ncreased, for all three schemes . In ELDPC, for LR at the recip ient, some infor mation is need ed that ca n be available just by having . T herefore, as demonstrated in Table III, for this scheme just a h igh quality version of t he or iginal image can be retrieved without having while in the pro posed scheme t he o riginal image ca n be reconstructed p erfectly just b y having . B esides, HM IMSB can achieve more EC tha n ELDPC . As described in T able III, in comparison to CLSB, the embedding capacity is significantly improved . Similar to ELDPC, their algorithm is dep endent on having for LR of the original image. In Wu’s sc heme [32], using data h ider key, they select some target pixels in the encr ypted image to e mbed data bits and employ altered CB predictor t o reco nstruct the o riginal i mage. Their methods do not guarantee LR . In the experiment, their algorithm fails to perfect ly r econstruct the orig inal image for five test images out of nine ones. As illustrated in T able III, we improve their algorit hm by designing a proced ure to guarantee LR by employing histogra m modification and MSBs integration. However, we pay the cost by less EC. All d iscussed schemes a s well as the proposed scheme provide an error -free data bits extraction while the pro posed scheme is the only one that makes possible LR of the original image just by having the secret key ( ). In Fig . 11 , the proposed schem e is co mpared to [16] , [27] , [29], [30] and [32] in terms of the quality of the reconstructed image. In this experi ment, sche mes [3 0] and [32] have both encryption and data hider keys while others just have encryption key. I n Zhang’s method [30], the reco nstruction of the o riginal image and extraction of d ata bits are j oint while in our sche me it is separab le. I n this case, we improve n ot only E C but also the image quality. To embed data bits, Cao’s scheme reserves ro om before encryptio n usin g patch -level spar se representation [16]. Generally, the embedd ing capac ity of t he proposed scheme is comparable with the Cao’s method . A preprocessing is allo wed b efore encryption in Cao ’s scheme wh ile the prop osed scheme is absolutely blind to the origin al- content. As shown in Fig. 11 , ELDPC outper forms CLSB a nd the Cao ’s scheme in ter m of P SNR. From LR point o f view, our proposed scheme outperfor ms ELDPC . In comparison with Wu’s scheme, f or Peppers and Len a images, w e r each to hig her EC. In Lake , Peppers and Baboon images, the y ac hieve the PSNR o f les s than 55 dB even b y usin g both keys while in o ur scheme LR is perfor med just by . TABLE III E FFIC IENCY COMPARISON BETW EEN THE PROPOS ED SCHEME AND O THE R SEPARABLE VRAE ONES FOR NINE TEST IMAGES. Schemes Items images F16 Lena Splash House Boat Elaine Lake Peppers Baboon Zhang2012 [27 ] (CLSB) EC (bits) 1920 1920 1920 1920 1920 1920 1920 1920 1920 LR Pass Pass Pass Pass Pass Pass Pass Pass Pass LR just by Fail Fail Fail Fail Fail Fail Fail Fail Fail Wu [32] EC (bits) 130050 130050 130050 130050 130050 130050 130050 130050 130050 LR Pass Pass Pass Fail Fail Pass Fail Fail Fail LR just by Pass Pass Pass Fail Fail Pass Fail Fail Fail Qian [29] (ELDPC) EC (bits) 77376 77376 77376 77376 77376 77376 77376 77376 77376 LR Pass Pass Pass Pass Pass Pass Pass Pass Pass LR just by Fail Fail Fail Fail Fail Fail Fail Fail Fail Proposed Scheme (HMIMSB) EC (bits) 86021 86021 86021 86021 86021 86021 86021 86021 86021 LR Pass Pass Pass Pass Pass Pass Pass Pass Pass LR just by Pass Pass Pass Pass Pass Pass Pass Pass Pass (a) (b) (c) (d) Fig. 10 . A visu al demo nstration of the pro posed scheme . (a) Original image. (b) Encry pted image. (c) Marked en crypted ima ge, i.e. 161290 bits. ( d) Reconstructe d image, . Histog ram of the images is also de scribed. Fig. 11. PSNR compar i son of the proposed scheme and other sc hemes such as Cao [16], Zhang2 011[30], Zhang 2012 CLSB [27], Qian ELD PC [29], and Wu [32] for four te st images. C ON CLUSION In this paper, b y comparing different pred ictors, it is demonstrated that WPP is a better choice to reduce the probability of fa ilure i n rec onstructi ng t he or iginal i mage. Moreover, BCP predictor is e mployed to increase the embedding capacit y. By pred iction-erro r analysis, we just choose the MSB of t he encrypted target pixels for data embedding. T hese MSB s ar e integrated to be more robust against failure of reconstruct ion when they are m od ified to embed data bits. Employing histogram modificatio n of t he integrated MSB s, we vacate ro om for data em bedding. At the recipient, data bits are faultlessly extracted and t he original image is losslessly reconstruc ted b y separate p rocedures . We employ the risk analysis evaluatin g LR. T he pr oposed m eth od improves other separab le VRA E schemes t hanks to using MSBs integration and histogra m modification. As a futu re work, we are willing to improve the e mbedding capacity. R EFERENCES [1] Y. -Q. Shi, X. Li, X. Zhang, H.- T. Wu, and B. Ma, “Reversible d ata hiding: Advances in the past t wo decades,” IEEE Access, vol. 4, p p. 3210-3237, 2016. [2] J. Tian, “Reversible data e mbedding using a differe n ce expansion,” IEEE Transactions on Circuits and Systems fo r Vi deo Tec hnology, vol . 13, no. 8, pp. 890-896, A ug. 2003. [3] Z. Ni, Y.- Q. Shi, N. Ansari, and W. Su, “Reversible data hiding,” IEEE Transactions on Circuits and Systems fo r Vi deo Tec hnology, vol . 16, no. 3, pp. 354-362, Mar . 2006. [4] T. K alker, and F . M. W i llems, “Capacity b ounds and constructions for reversible da ta - hiding,” in Proc. Internatio nal Conference on Digital Signal Processin g , Santorini, G reece, Greece, 2002, pp. 71-76. [5] X. Li, W. Zhang, X. Gui, and B. Yang, “A novel r eversible data hiding scheme based o n two-dimensional difference-histogram modifica tio n,” IEEE Transact ions on Inform ation Forensics and Secur ity, vol. 8, no. 7 , pp. 1091-1100, Jul. 2013. [6] D. M. Thodi , and J. J . Rodríguez, “Expa nsion embe dding techni ques for reversible w atermarking,” IEEE Transactions on Ima ge Pr ocessing, vo l. 16, no. 3, pp. 7 21-730, Mar. 2007. [7] X. Wu, and N. M emon, “Context -based, adaptive, lossle ss image coding,” IEEE Tra nsactions on Com munications, vol. 45, no. 4, pp. 437 - 444, Apr. 19 97. [8] M. J. W einberger, G. Seroussi, and G. Sapiro, “The LOCO -I l ossless image compre ssion algorithm: P rinciple s and s t andardizat ion into JPEG- LS,” IEEE Tr ansactions on Im a ge processi n g, vol. 9, no. 8, pp. 1309- 1324, Aug. 200 0. [9] P. Tsai, Y.-C. Hu, and H.- L. Yeh, “Reversible image h iding scheme using predictive coding and histog r am shifting,” Signal Process i ng, vol. 89, no. 6, pp. 1 129-1143, Jun. 200 9. [10] V. Sachnev, H. J. Kim, J. Nam, S. Suresh, and Y. Q. Shi, “Reversible watermarking algorithm using sorting and prediction,” IEEE Transactions on Circuits and Systems fo r Vi deo Technol ogy, vol . 19, no. 7, pp. 989-999, Jul. 2009. [11] A. Mohammadi, and M. Nakhkash, “Sor ting methods and adaptive thresholding for histogram based reversible data hiding,” Multimedia Tools and App lications, Sep. 20 20 . [12] S. Xiang, and X. Luo, “Revers ible d ata h iding in h omomorph ic encrypted domain by mirroring ciphe rtext group,” IEEE Transactions on Circuits and S ystems for Video Technology, vol. 2 8, no. 11, pp. 3099 - 3110, Nov. 201 8. [13] K. Ma, W. Zhang, X. Zhao, N. Yu, and F . Li, “Re versible data hi ding in encrypted images by rese r ving room befo re encry pt ion,” IEEE Transactions on Information Forensi c s and Sec urity, vol. 8, no. 3, pp. 553-562, Mar. 2013. [14] Z. Yin, Y. Xiang, and X. Zhang, “Re v ersible data h iding in encry pt ed images based on multi-M SB prediction and Huffman coding,” IEEE Transactions on M u ltimedia , vol . 22, no. 4, pp. 874-884, Apr. 20 20 . [15] Y. -C. Chen, T.-H. Hung, S.-H. Hsieh, and C.- W. Shiu, “A new reversible data hiding in e ncrypted i mage based on multi-secret sharing and lightwe ig ht c ryptogr aphic algorithms,” IEEE Tr a nsactions on Information Forensics and Sec u rity, v ol. 14, no. 1 2, pp. 3332-3343, Dec. 2019. [16] X. Cao, L . Du, X. Wei, D. Meng, and X. G uo, “High ca p acity rev ersible data hiding in encrypted images by patch-level sp arse representation,” IEEE Transactions on Cybernetics, vol. 4 6, no. 5 , pp. 1132-1143, May 2016. [17] C. -W. Shiu, Y.- C. Chen, and W. Hong, “Encrypted i mage -based reversible data hiding with public key cryptography from difference expansion,” Signal Processi ng: I mage Co mmunic ation, vol. 39, pp. 226- 233, Nov. 2015. [18] P. Puteaux, and W. Puech, “An efficient MSB prediction -based method for h igh- capacity reversible d ata hiding i n encrypted images,” IEEE Transactions on Information Forensics and Security, vol. 13, no. 7, pp. 1670-1681, Jul. 2 018. [19] A. Mohammadi, M. Nakhkash, and M. A. Akhaee, “A hi gh -capacity reversible dat a hiding in encry p ted images employing local difference predictor,” IEEE Transactions on Circuits and Sy stems for Video Technology , vol. 30 , no. 8, pp. 2366-2376 , Aug. 20 20 .. [20] S. Yi, and Y. Zhou , “Separable and reversible data hiding in encry pted images using parametric binary tree labeling,” IEEE Transactions on Multimedia, vol. 21, no. 1, pp. 51-64, Jan. 2019. [21] D. Xu, and R. Wang, “Separable and error -free reversible data hiding in encrypted im ages,” Signal Processi n g, vol. 123, pp. 9-2 1, Jun. 2016. [22] Z. Yin, B. Luo, a nd W. Hong, “Separ able and error -free r eversible data hiding in encrypted image with high payload,” Th e Scientific Wo rld Journal, vol. 2014, A pr. 2014. [23] W. Zhang, K. Ma, and N. Yu, “Re versibility improved data hiding in encrypted images,” Signal Processing, vol. 94, n o. 1 , pp. 118-127, Jan. 2014. [24] F. Huang, J. Huang, an d Y.- Q. Shi, “New framework for reve rsible data hiding in encrypted domain,” IEEE Transact ions on Informa tion Forensics and Sec u rity, vol. 11, no. 12, pp. 2777-2789, De c . 2016. [25] H. Ge, Y. Chen, Z. Qian, and J. Wang, “A high capaci ty multi-lev el approach for reve rsib le data hiding in encry pted images,” IEEE Transactions on Circuits and Systems fo r Vi deo Tec hnology, vol . 29, no. 8, pp. 2285 - 2295, Aug. 2019. [26] X. Zhang, “Commutative re versible data hiding and encry p tion,” Security and C ommunicat ion Networks, vol. 6, no. 11, pp. 1396 -1403, 2013. [27] X. Zhang, “Separable reversible data hiding in encrypted image,” IEEE Transactions on Information Forensi c s and Sec urity, vo l. 7, no. 2, pp. 826-832, Apr. 2 012. [28] J. Z hou, W . Sun, L. Dong, X. Liu, O. C. Au, a nd Y. Y. Tang, “Secure reversible image data hiding ov er encrypted domain via key modulation,” IEEE T ransactions on Circuits and Systems for Video Technology, vol . 26, no. 3, pp. 4 41-452, Mar. 2016. [29] Z. Qian, and X. Zh ang, “ Reversible data hiding in e ncrypted images with distributed source encoding,” IEEE Transactio ns on Circuits and Systems for V ideo Technology, vol . 26, no. 4, pp. 63 6-646, Apr. 2016. [30] X. Zhang, “Reversible data hiding in encry p ted image,” IEEE Signal Processing Letters, vol. 18, no. 4, pp. 255-258, Apr. 2 011. [31] W. Hong, T.-S. Chen, and H.- Y. Wu, “An i mprove d reversible d ata hiding in encrypted i mages u sing side match,” IEEE Signal Processing Letters, vol. 19, no. 4, pp. 199-202, Apr. 201 2. [32] X. Wu, and W. Sun, “High -capacity reversible data hiding in encrypted images b y prediction error,” Signal Pro cessing, vol . 104, p p. 387-400, Nov. 2014. [33] M. Fallahpour, and M. H. Sedaaghi, “High capacity lossless data hiding based on histogram modificat ion,” IEICE Electr o nics Express, vol. 4, no. 7, pp. 205-210, 20 07.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment