Cooperative Distributed State Estimation: Resilient Topologies against Smart Spoofers
A network of observers is considered, where through asynchronous (with bounded delay) communications, they cooperatively estimate the states of a Linear Time-Invariant (LTI) system. In such a setting, a new type of adversary might affect the observat…
Authors: Mostafa Safi
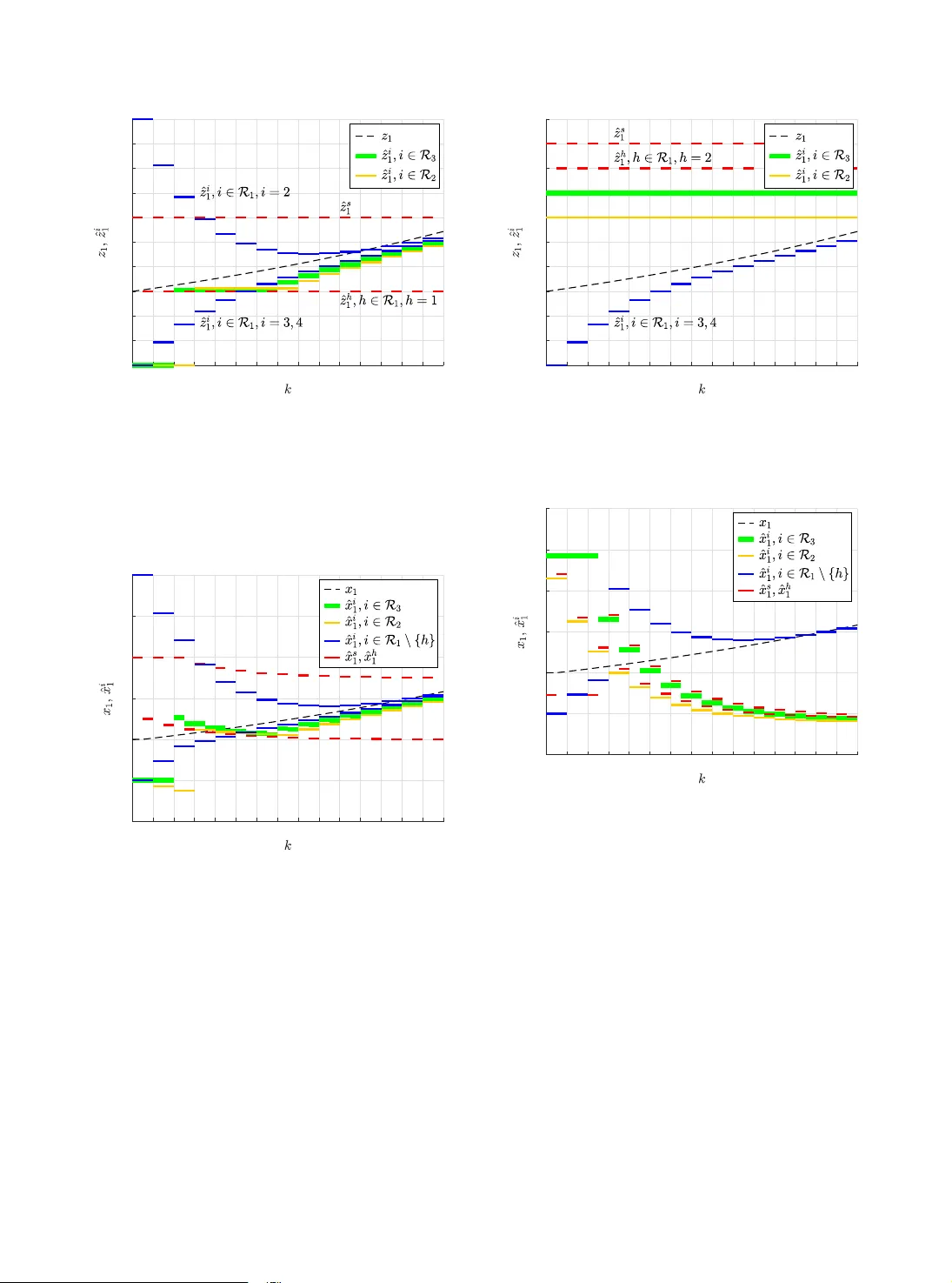
Springer Con trol Theory and T ec hnology Co op erativ e Distributed State Estimation: Resilien t T op ologies against Smart Sp o ofers Mostafa Safi 1* 1* Amirk abir Univ ersit y of T ec hnology , Hafez, T ehran, 424, T ehran, Iran. Corresp onding author(s). E-mail(s): halebi@aut.ac.ir ; Abstract A netw ork of observers is considered, where through asynchronous (with b ounded delay) com- m unications, they coop eratively estimate the states of a Linear Time-Inv ariant (L TI) system. In suc h a setting, a new type of adversary might affect the observ ation process by imp ersonating the identit y of the regular no de, which is a violation of comm unication authenticit y . These adv er- saries also inherit the capabilities of Byzantine nodes, making them more p o w erful threats called smart sp o ofers . W e show how async hronous netw orks are vulnerable to smart sp oofing attack. In the estimation scheme considered in this paper, information flo ws from the sets of source no des, whic h can detect a p ortion of the state v ariables each, to the other follow er no des. The regular no des, to a v oid b eing misguided b y the threats, distributively filter the extreme v alues received from the no des in their neighborho od. T op ological conditions based on strong robustness are prop osed to guaran tee the conv ergence. Two sim ulation scenarios are provided to verify the results. Keyw ords: Cyber-physical systems, smart spo ofing, distributed resilien t algorithm, secure observers 1 In tro duction Securit y is b ecoming an increasingly imp ortan t concern for the stabilit y and safety of netw orked con trol systems. Now ada ys, in large-scale con- trol systems, communication c hannels connecting v arious ph ysical comp onen ts for real-time mea- suremen t and control mostly mak e use of general purp ose cyb er-net works suc h as the Internet and wireless net w orks, whic h create vulnerabilities to adv ersarial in trusions. While conv entional net- w ork security-based measures may b e partially effectiv e, no vel resiliency methods explicitly tak- ing the dynamical nature of ph ysical comp onen ts in to account should b e developed as any failure in securit y of the cyb er components in suc h systems ma y turn into irrecov erable harms to the physical infrastructure. Securit y exp erts define v arious security goals including (i) Confidentiality , ensuring priv acy of imp ortan t data against outside ea vesdroppers; (ii) Inte grity , main taining fidelity of system signals; (iii) A vailability , capabilit y of timely ha ving access to the required signals; (iv) Authenticity , v erifying iden tit y of eac h signal; (v) Authorization , adjust- ing legitimacy of access by eac h comp onen t to other parts of the system; and (vi) A c c ountability , detection of an y potential attac ks and faults in the system [ 1 ]. In this paper, we consider masquer ading , sp o of- ing , or imp ersonation attack strategy on cyb er- ph ysical netw orked systems, which is a threat of authen ticit y . A broad range of wired and wire- less net works including sensor netw orks, in-vehicle net w orks, and In ternet-based net works are suscep- tible to be threatened by sp oofing. F or instance, 1 Springer Con trol Theory and T ec hnology 2 Sp o of-r esilient Distribute d Observers the reader can refer to [ 2 ] for satellite mobile comm unication netw orks, [ 3 ] for mobile ad ho c net w orks, and [ 4 ] for CAN-based net works. Spo of- resiliency techniques would b e essential for all of these netw ork setups to detect and/or mitigate the adv ersarial effects. How ever, mostly in literature, the sp o of-resilien t algorithms are studied for the in teractions b etw een only tw o agen ts: a sp o ofer and a normal [ 5 – 9 ]. F or example, [ 6 ] presen ts an application of spatial pro cessing metho ds for sp oofing detection and mitigation. Also, a GPS sp oofing scenario is form ulated as a constrained optimization problem and an effective solution is pro vided to compute the falsified GPS measure- men t of each time instant [ 7 ]. The false-data injec- tion attac k on unmanned vehicles is inv estigated in [ 8 ]. Although, this differs a little from sp oofing attac ks. The attack er masquerades as a distur- bance for control system of a vehicle and deviates its path smo othly . F urthermore, a game-theoretic approac h is dev elop ed in [ 9 ] to counteract sp oofing attac ks. How ever, a common p oin t all the ab o v e researc hes share is that there is no netw ork of agen ts. Only t wo-side in terplay scenarios are con- sidered, where the sp oofing or masquerading is the attac king metho d. Recen tly though, [ 10 ] and [ 11 ] fo cused on the sequels of sp oofing attack on the net w ork of agents. How ever, both of these refer- ences use physical fingerprints of comm unication signals to undo the attacks, whic h is a different approac h and cannot resist against onmniscient adv ersaries in practice. Despite [ 10 ], in our work, the attac k ers do not lea v e an y sign and th us the regular no des cannot iden tify them. Also, omni- scien t attack ers in our setup could break any type of signal encryption and p erform masquerading. P articularly , our emphasis is on the resiliency of a netw ork in terms of its top ology that is a more basic level of coun teraction to cyb er threats. More- o v er, in [ 10 ], attack ers cause an av ailability threat b y jamming the serv er with fak e iden tities, whic h is a sp ecial case of our adversarial mo del. W e com bine adv ersarial capabilities of the so-called Byzantine mo del, which is an in tegrity attack capable of sending inconsisten t erroneous signals to the receivers introduced and used in [ 12 , 13 ], with sp oofing, that is use of other no des’ identi- ties to send data on their b ehalf, and in tro duce a no v el and more p o werful adv ersarial mo del called smart sp o ofer . In [ 14 ], resiliency of synchronous net w orks is in vestigated against mobile Byzantine adv ersaries that are different from our adversarial mo del. In our setting, smart spo ofers can use the async hron y of netw ork communications to mislead the no des with impersonated identities. One of the targets of sp oofers in netw ork sys- tems w ould b e inserting erroneous v alues in to the distributed state estimations p erformed b y the no des. Distributed state estimation algorithms are extensively studied in the literature [ 15 – 18 ]. Ho w ev er, all these research w orks fo cused on the in teraction betw een dynamic system, observers and the graph topology . A minim um cost com- m unication graph whic h enables limited communi- cation for decen tralized estimation is in vestigated in [ 15 ] . The interpla y b etw een netw ork connec- tivit y , global observ ability , and system instabilit y is studied in [ 16 ]. Necessary and sufficient con- ditions for existence of distributed observ ers are studied in [ 17 ]. Also, [ 18 ] generalizes distributed observ er design for L TI systems with singular transition matrices. None of the abov e researc h w orks consider communication security among the ph ysical and cyb er la yers. The resilience of distributed observers against cyb er attac ks has recen tly receiv ed more atten tion. F or instance, the resiliency of L TI systems has been in v estigated in [ 19 , 20 ] against Byzan tine attac ks. Ho wev er, our adv ersarial model is more complex b y considering the impersonation capability of adversaries. W e also consider async hron y and dela ys in comm u- nications and prop ose a randomization strategy for relaxing the imp osed top ology constraints for secure distributed estimation problem. In the curren t pap er, w e consider imp erson- ation on a netw ork of distributed observ ers for an L TI system. Like the net work comm unica- tion settings in [ 21 , 22 ], the observ ers comm unicate with b ounded delays and asynchron y; how ever, they must deal with stronger attac ks, i.e. smart sp oofing. Similar to [ 19 ], the regular (un-attac ked) no des are partitioned to source no des and fol- lo w er no des, where source nodes can detect the corresp onding eigenv alues and via distributively constructing a directed acyclic graph (DA G), the asso ciated state estimates disseminate through the netw ork. In b oth DA G construction and esti- mation propagation, smart spo ofers in terfere to a v oid con v ergence. W e presen t a strategy based on lo cal filtering that is able to defend against smart sp oofing and define lo cal subgraphs to mimic the Springer Con trol Theory and T ec hnology Sp o of-r esilient Distribute d Observers 3 graph b ehavior for analysis of the estimation con- v ergence, turning in to sufficien t conditions on net- w ork top ology based on graph robustness that is a connectivity measure (see [ 13 , 23 ] for application of similar filtering algorithms in consensus prob- lem). Consistency of the defined sp oofing mo del with the netw ork security literature, consideration of dela ys, asynchron y , and accurate assumptions in netw ork communications mak e our prop osed algorithms, up date rule, and concluding results more practical in real world applications. In the dev elopmen t of our results and the pro ofs, we adopted the concept of motifs, the smallest p ossi- ble subgraphs of the original netw ork with certain prop erties, as a new pro of technique. W e analyze ho w the information is disseminated through the motifs. All in all, the main contributions of this pap er to the literature are: • In tro ducing, mo deling and formulating a new t yp e of cyb er attack in asynchronous net- w ork settings which inherits the prop erties of b oth Byzan tine adversaries and sp o ofing agen ts, called smart sp oofing. • Analyzing the vulnerabilit y of asynchronous net w orks to smart sp oofers and prop osing a resilien t distributed state estimation strategy for a class of L TI systems. • Using motifs, as the smallest possible repeat- ing patterns in a net work, to mathematically analyze the top ology constrain ts required for con v ergence of the distributed state estimation. • Presen ting a randomized up date rule to relax the sp o of-resilien t top ology constraint required for con vergence of the distributed state estima- tion. The paper is organized as follo ws. The prelimi- naries and problem statemen t come in section 2 . In section 3 , we take a look at the resilient distributed estimation scheme and the lo cal filtering-based algorithm that we used in this pap er. Our main results are presented in Section 4 . W e put forward the simulation results in Section 5 . Finally , w e con- clude the pap er and discuss the future tendency of the researc h in Section 6 . 2 Preliminaries and Problem Statemen t 2.1 Notations 2.1.1 Graph Theory A directed graph is represented by G = ( V , E ), where the set of no des and edges are represen ted b y V = { 1 , . . . , N } and E ⊆ V × V resp ectiv ely . An edge from no de j pointing to no de i implies data transmission from no de j to no de i and is denoted by ( j , i ). The neigh b ourhoo d of the i -th no de is defined by the set N i = { j | ( j, i ) ∈ E } . A no de j is said to b e an outgoing neighbour of no de i if ( i, j ) ∈ E . A spanning sub-graph for G is a sub-graph of G which con tains every v ertex of G . Consider no de v 1 to v p of G . A path is a sequence ( v 1 , v 2 , . . . , v p ) in which ( v i , v i +1 ) ∈ E for i = 1 , . . . , p − 1. The length of a path is measured by its n umber of edges. A cycle is a sequence ( v 1 , v 2 , . . . , v p , v 1 ) in whic h ( v i , v i +1 ) ∈ E for i = 1 , . . . , p − 1 and ( v p , v 1 ) ∈ E . A directed acyclic graph (DA G) is a directed graph which has no cycles. F or the consensus-based state estimation rule designed in this pap er, the critical top ological notion is graph robustness, whic h is a connectivity measure of graphs (see [ 24 ]). Definition 1 ( r -reac hable set) F or a graph G = ( V , E ) and a set C ⊂ V , we say that C is an r -reac hable set if there exists an i ∈ C suc h that |N i \ C | ≥ r , where r ∈ N + . Definition 2 (Strongly r -robust w.r.t. S ) F or a graph G = ( V , E ), a set of nodes S ⊂ V and r ∈ N + , w e say that G is strongly r -robust with respect to S , if for any non-empt y subset C ⊆ V \ S , C is r -reachable. 2.1.2 Linear Algebra The set of all eigen v alues of a matrix A is denoted b y σ ( A ). The set of all marginally stable and unstable eigenv alues of a matrix A is denoted by σ U ( A ) = { λ ∈ σ ( A ) || λ | ≥ 1 } . W e use a A ( λ ) and g A ( λ ) to denote the algebraic and geometric m ul- tiplicities, resp ectively , of an eigenv alue λ ∈ σ ( A ). An eigen v alue λ is said to b e simple if a A ( λ ) = g A ( λ ) = 1. Springer Con trol Theory and T ec hnology 4 Sp o of-r esilient Distribute d Observers Ph ysical La y er x [ k + 1] = Ax [ k ] Cyb er La yer R 3 R 5 R ¯ N R 1 s f s 3 s 2 R 2 R 4 s 1 Fig. 1 A typical cyb er-ph ysical system: In the physical lay er, the plant dynamic (maybe unstable in some mo des) propagates ov er time. In the cyb er la y er, the plant’s out- puts are monitored by a net work of distributed observ ers ( R 1 , R 2 , . . . , R ¯ N ) while only some of them are directly connected to the plan t. The netw ork is threatened by adversarial no des ( s 1 , s 2 , . . . , s f ). 2.2 System Dynamics and Distributed Observers Consider the follo wing discrete-time L TI system x [ k + 1] = Ax [ k ] , (1) where k ∈ N is the discrete-time index, x [ k ] ∈ R n is the state v ector and A ∈ R n × n is the system matrix. The system is observ ed b y an N -no de net- w ork G = ( V , E ). Access of the i -th node to the measuremen t of time instan t k is given by y i [ k ] = C i x [ k ] , (2) where y i [ k ] ∈ R r i and C i ∈ R r i × n . F or compu- tational or control purp oses, each no de needs to estimate the entire system state x [ k ]. Nodes of the net work G are called distribute d observers if they maintain and up date the estimates using only their own measurements and those received from their neighbors. Fig. 1 shows the la yout of a typical cyb er-ph ysical system threatened b y adv ersarial no des. Let ˆ x i [ k ] denote the state estimate of no de i at eac h time step k . The follo wing defi- nition describ es the ob jective of the distributed estimation sc heme. Definition 3 (Omniscience) Over the N -node net- w ork G , the distributed observ ers are said to achiev e omniscience if lim k →∞ | ˆ x i [ k ] − x [ k ] | = 0 , ∀ i ∈ { 1 , 2 , . . . , N } . 2.3 Adv ersarial Mo del W e consider an adversarial mo del that is able to threaten the following system protection ser- vices: authentic ation , authorization , c onfidential- ity , inte grity and availability . In what follows, we formally define the abilities of such an adv ersarial no de. Definition 4 (Smart Sp oofer) An adversarial node is called a smart sp oofer if it has the following capabilities: 1) The adversarial no de can hav e complete knowl- edge about the top ology , plan t dynamics, and information flow ov er the netw ork at all time steps. 2) The adversarial no de can refuse to p erform any preassigned algorithm and can send arbitrary v alues to eac h of its neigh b ors at the same time step. 3) The adversarial no de can send its data with in tended dela ys and async hron y . 4) The adversarial no de can imp ersonate other no des and send arbitrary data with their iden- tities. The first t wo actions are p erformed by Byzan- tine adv ersaries, while the last one is p erformed b y a threat called sp o ofing or masquer ading in [ 1 ] that directly threatens the authentication among systems’ protection services. In fact, the intro- duced adversarial mo del is an adv anced sp oofing threat with additional capabilities of Byzantine adv ersaries that we call smart sp o ofing . Note that w e use the terms “sp o of” and “imp ersonate” in terc hangeably in this pap er. It is apparen t that no distributed estimation algorithm w ould succeed if all the no des are adv er- sarial. So, the set of no des V is partitioned in to t w o subsets of regular no des and adversarial no des denoted b y R and A = V \ R , resp ectiv ely . In the literature of distributed fault-tolerant algorithms, a common assumption is to assign an upper b ound f to the total num b er of adversarial no des in the net w ork, whic h is kno wn as f -total adversarial mo del. T o consider a large n umber of adv ersaries in large scale netw orks, lo cally b ounded fault mo dels are used, as in [ 25 ], defined below. Springer Con trol Theory and T ec hnology Sp o of-r esilient Distribute d Observers 5 Definition 5 ( f -local smart sp oofer mo del) A set A of smart sp o ofers is f -locally b ounded if it contains at most f smart sp oofers in the neighbourho od of any of the regular no des, i.e. |N i ∩ A| ≤ f , ∀ i ∈ V \ A . Similarly , an y distributed estimation algo- rithm fails if a smart sp oofer can imp ersonate all the netw ork nodes. Th us, to tackle the problem, w e imp ose an upp er b ound for the num b er of no des that smart sp o ofers can send data on their b ehalf as follo ws. Definition 6 (Capacity of smart sp oofers) The max- im um num b er of no des that a smart sp o ofer can send data on their behalf at each time step, including itself, represen ts its capacity and is denoted by α ≥ 1. 2.4 Problem Statemen t W e aim to formulate the resilien t version of omni- science problem (Def. 3 ), where the netw ork is under smart sp oofers’ attack with tw o challeng- ing constraints on the netw ork communications, i.e. async hron y and delays. Accordingly , w e set the follo wing assumptions on the net work communi- cations proto col remarking the practical asp ects of our results. Assumption 1 All no des up date by a global clo c k. This means that the sampling time T is the same for all observers. Assumption 2 All no des communicate through serial links and hav e access to only the last data pack et they hav e received from neigh b or no des. Assumption 3 All no des make, at least, one up date within ¯ k steps and comm unication dela ys are upper- b ounded by ¯ τ . Referring to the introduced L TI dynamic sys- tem and the observ ation mo del of the netw ork, we put forth a more complicated v ersion of the stan- dard omniscience problem (Definition 3 ) in the follo wing definition. Definition 7 (Resilient Omniscience) Given a system dynamics of the form ( 1 ), a netw ork represen ted b y the graph G , and an observ er model at eac h node giv en b y ( 2 ), a state estimation design is said to achiev e r esilient omniscienc e if lim k →∞ | ˆ x i [ k ] − x [ k ] | = 0 , ∀ i ∈ R , regardless of the actions of any f -lo cally bounded set of smart sp o ofers. This pap er inv estigates the design of a dis- tributed estimation sc heme, proper to cop e with smart spo ofers threatening a given cyb er net work that is observing an L TI system. F or this pur- p ose, based on the assumptions on the netw ork comm unications proto col and the smart spo ofer adv ersarial mo del, we first presen t the distributed estimation scheme under a specific netw ork topol- ogy . Next, we analyze the required top ology con- strain ts whic h guaran tee resilien t omniscience of all regular nodes that up date their estimates using the prop osed estimation strategy . 3 Resilien t Distributed Observ ers Under Byzantine adversarial mo del introduced in [ 12 ], the netw ork ac hiev es omniscience by distributed observ ers prop osed in [ 19 ]. The design p erforms observ ation task by separating detectable and undetectable eigenv alues of the system and the related states. Here, w e use a sim- ilar scheme with a differen t distributed estimation rule, prop er for resilient omniscience defined in Definition 7 . T o this end, consider a Jordan canon- ical decomp osition of state transition matrix A with the following assumption on its eigen v alues. This assumption is made for sake of simplicity , is not restrictive, and can b e relaxed by some extra mathematical efforts and the techniques denoted in [ 19 ], whic h is not the fo cus of this paper. Assumption 4 Eigenv alues of A are real and simple. This assumption allows us to diagonalize A b y the co ordinate transformation matrix Ψ = [ ψ 1 , . . . , ψ n ], where ψ 1 , . . . , ψ n are n linearly inde- p enden t eigenv ectors of A . With z [ k ] = Ψ − 1 x [ k ], the system ( 1 ) is transformed in to the form z [ k + 1] = ¯ Az [ k ] , y i [ k ] = ¯ C i z [ k ] , ∀ i ∈ { 1 , . . . , N } , (3) Springer Con trol Theory and T ec hnology 6 Sp o of-r esilient Distribute d Observers where ¯ A = Ψ − 1 A Ψ is a diagonal matrix, and ¯ C i = C i Ψ. The eigen v alues of ¯ A (whic h are the same as those of A ) are denoted b y λ 1 , . . . , λ n . Eac h regular no de i distinguishes its detectable and undetectable eigenv alues by PBH test and divides them in to the sets D i and U i , resp ectively . Also, the set of regular no des are partitioned into sets of sour c e no des and fol lower no des as defined b elo w. Definition 8 (Source nodes and follo wer no des) F or eac h λ j ∈ σ U ( A ), the set of nodes that can detect λ j is denoted by S j , and is called the set of source nodes for λ j . The rest of the nodes are called follow er no des. Eac h regular node, dep ending on b eing a source no de or a follow er no de for λ j , adopts a differen t strategy for estimating the related states. 3.1 State Estimation by Source No des Referring to [ 19 ], each regular no de i relies on its o wn measurements and uses a lo cal Luen b erger observ er to estimate a patch of the states ˆ z D i asso- ciated to all λ j ∈ D i . T o this end, let Λ i ∈ R ρ i × ρ i (recall ρ i = |D i | ) b e a diagonal matrix consists of the detectable eigen v alues in D i and ¯ C D i ∈ R r i × ρ i stand for the columns of ¯ C i corresp onding to those eigen v alues. Then w e ha v e: ˆ z D i [ k + 1] = Λ i ˆ z D i [ k ] + L i ( y i [ k ] − ¯ C D i ˆ z D i [ k ]) , (4) where L j i ∈ R ρ i × r i is the observer gain matrix at no de i . Since the pair (Λ i , ¯ C D i ) is detectable, L i can be chosen in a w ay that (Λ i − L i ¯ C D i ) is Sc h ur stable, so lim k →∞ | ˆ z j i [ k ] − z j [ k ] | = 0 based on Assumption 4 . 3.2 Distributed State Estimation b y F ollow er No des A regular no de i cannot estimate a portion of the states asso ciated with its undetectable eigen v al- ues of the system. In fact, the regular no de i is a follo w er no de in estimating the sub-state related to the eigenv alues λ j ∈ U i and needs to receive information from its neighbors through a directed acyclic graph for each λ j (defined later) ro oted in the set of asso ciated source nodes. In what follo ws, we prop ose an updating rule for the fol- lo w er no de i accomplishing its estimation task in a net w ork with comm unication delays and p artial asynchr ony 1 . There is a ma jor difference b et ween resilient distributed state estimation rather than resilient consensus using local filtering presented in previ- ous research w orks such as [ 22 ]. Considering asyn- c hronous netw ork comm unications and observ abil- it y of dynamics of the physical la yer is a new c hallenge in design of the up date rule and leads to a totally different conv ergence analysis. Combin- ing the ideas behind the consensus up date rules in [ 19 ] and [ 22 ], we presen t a nov el up date rule with the follo wing algorithm based on lo cal fil- tering metho d for no de i to up date its own state estimate for λ j ∈ U i . 1) Eac h regular no de i , at each time step k when it w ants to up date its estimate, gathers the state estimate of z j [ k ] lastly received from only the nodes in N j i ⊆ N i ( N j i represen ts the set of neigh b ors in the D AG related to λ j that is selected by Algorithm 1 for eac h regular no de i , whic h will be proposed later) and arranges them from the largest to the smallest. 2) Node i drops the largest and smallest ( β + 1) f estimates ( β will b e defined later) and executes the follo wing up date rule: ˆ z j i [ k + 1] = λ j X ` ∈N j i ω j i` [ k ] ˆ z j ` [ k − e k i` [ k ] − τ i` [ k ]] , (5) where τ i` [ k ] is the time delay of the last data pac k et that no de i has received from node ` until time instan t k (it ma y be time-v arying), e k i` [ k ] is the time steps elapsed from the time that node i receiv es the pack et of the no de ` sen t the last time b efore time k up to the time it makes an up date ( e k i` [ k ] < ¯ k ), and ω j i` [ k ] is the w eigh t that the i -th node dedicates to the ` -th no de at the k - th time instant for the estimation of z j [ k ]. The w eigh ts are non-negativ e and c hosen to comply P ` ∈N j i ω j i` [ k ] = 1 , ∀ λ j ∈ U i . No de i remov es the ( β + 1) f largest and ( β + 1) f smallest estimates 1 The term p artial asynchrony refers to the case where nodes share some level of synchron y by having the same sampling times; how ever, they make updates at different times based on bounded information dela ys [ 26 ] Springer Con trol Theory and T ec hnology Sp o of-r esilient Distribute d Observers 7 from N j i b y setting their asso ciated w eights to 0. Note that dela ys ha ve an upp er b ound ( τ i` < ¯ τ ). In practice, each node i has a memory for each of its neighbors where stores the most recently receiv ed data. No de i uses the most recen t esti- mate v alues received from its neigb ours in N j i in up date rule ( 5 ), regardless of delays and asyn- c hron y in comm unications. 4 Main Results In this section, we pro vide the main results of the pap er giving the analysis of the sp o of-resilien t distributed estimation strategy and the top ology constrain ts under which our adopted algorithms and up date rule succeed. First, we consider ho w harsh the misb ehaviour effects of a smart spo ofer would b e in the netw ork. In Definition 6 , w e introduced the sp o ofing capac- it y in each time step. In the following lemma, we generalize capacity of smart sp oofers for a p erio d of time. Lemma 1 Let Assumption 3 hold and capacit y of a smart spo ofer be α . Then, each smart sp o ofer is able to send data on b ehalf of β = α ¯ k − 1 regular no des within each consecutive ¯ k steps. Pr o of According to Definition 6 , a smart sp oofer can send data on b ehalf of α nodes including itself at each time step. Also, according to Assumption 3 , all nodes ha ve to make at least one update within consecutive ¯ k steps (note that if a no de do es not follow this rule can b e detected as an adv ersarial node by the regular no des). Consider the time interv al k + 1 ≤ t ≤ k + ¯ k . Let the smart spo ofer choose to mak e an up date with its own identit y at t = k s , where k + 1 ≤ k s ≤ k + ¯ k . Considering eac h consecutive ¯ k steps, the smart sp oofer s has α − 1 capacity for imp ersonation at k s and α capacity in other ¯ k − 1 steps. Therefore, the smart sp o ofer is able to imp ersonate α ¯ k − 1 no des o verall within ¯ k steps, i.e. α − 1 + α ( ¯ k − 1) = α ¯ k − 1. In fact, Lemma 1 indicates that we cannot simply replace the smart sp o ofers and imp erson- ated nodes with Byzan tine nodes. Because the k ey question is that how many Byzantine no des hav e the same effect of a smart spo ofer with capac- it y α . This is what w e mathematically clarified in Lemma 1. Asynchron y lets the adversarial no des sp oof a sp ecific num b er of regular no des within eac h ¯ k time-steps. Besides, from adversarial no des’ p erspective, this sp oofing (and sending false data pac k ets) must b e contin ued for all the future time – in every ¯ k steps – in order to b e effectiv e. Th us, the distributed algorithms of regular no des mu st b e mo dified to b e resilient against the attack. In other words, netw ork providers need to b e aw are that in a netw ork with asynchron y (almost all the netw orks are practically async hronous), there is the p ossibility of stronger attac ks rather than Byzan tine attac ks. The following necessary con- dition on the net work communications formally states when a smart sp oofer can imp ersonate regular no des. Prop osition 1 Consider a netw ork of no des inter- connected by complete graph G , which contains smart sp oofer s ∈ N j i , where i ∈ R . Suppose that s is able to imp ersonate, at least, one regular no de within eac h consecutive ¯ k steps ( β > 0). Smart sp oofer s can imp ersonate a regular no de ` ∈ N j i ∩ R for node i at a time instant t > k only if the pack et which is broad- cast by no de ` at time instant t = k is received by no de i with delay e k i` [ k ] + τ i` [ k ] > 0. Pr o of W e pro ve b y con tradiction. Considering Assumption 1 , let node ` ∈ N j i broadcast a data pac ket at t = k and no de i ∈ R receives the pack et at the same time ( τ i` [ k ] = 0) and use it for its next up date at the same time ( e k i` [ k ] = 0). Also, supp ose that smart sp oofer s decides to impersonate node ` for no de i . There are tw o p ossibilities for the arriv al time of the pac ket sent by s to i . The pack et can arriv e either b efore or after the time t = k (the time instant t = k is excluded as it contradicts the Assumption 2 ). In case the pack et sent by s arriv es at any time t > k , the no de i has already accepted the last pac ket it receiv ed, that is, the pack et of no de ` receiv ed at t = k , and has already made an update. Otherwise, if the pac ket sent by s arriv es at an y time t < k , then i will receive the pac ket sent by no de ` at t = k and since, according to Assumption 2 , all nodes only access the last data pack et they receive. In either case, the smart sp oofer s fails to imp ersonate no de ` for no de i , whic h is a contradiction. This completes the pro of. Note that the necessary condition of Prop osi- tion 1 is indep endent of amoun ts of communica- tion delays. This is b ecause w e would lik e to deal with smart sp oofers that can imp ose arbitrarily Springer Con trol Theory and T ec hnology 8 Sp o of-r esilient Distribute d Observers b ounded amount of delays on their links to the regular nodes, that is, if a smart sp oofer w an ts to imp ersonate no de ` ∈ N j i , it can arrange to send the pack et to no de i after no de ` with appropriate dela y so that it will b e receiv ed after the pack et sen t by node ` . Then, no de i accepts a pack et sent b y s with iden tity of no de ` as it is the last pack et receiv ed. According to Prop osition 1 , the best case for the regular no de i is that both e k i` [ k ] = 0 and τ i` [ k ] = 0, so the smart spo ofers in the neigh- b orhoo d of i cannot imp ersonate neighbors of the no de i . How ever, even if w e supp ose that e k i` [ k ] = 0, i.e. no de i has not an y lag in up dat- ing its estimate using the last data receiv ed from no de ` , regular nodes cannot be sure ab out sp oof- ing attack. In practice, the regular no des cannot guess, before receiving a pack et, whether it will be receiv ed with dela y and, if so, how m uch the dela y will b e (although communication links’ delays in real net work systems are inevitable). Besides, as w e said, smart spo ofers can send data pac kets with in tended dela ys. So, the regular nodes must be a w are that all the comm unications may b e done with delays in each time step. Therefore, to con- sider the worst case, w e dev elop our further results on required top ology constrain ts b y assuming that the necessary condition on dela ys is satisfied for all time in the net w ork. 4.1 Sp o of-Resilient Mo de Estimation Directed Acyclic Graph (SR-MEDA G) Recall the lo cal filtering for resilient consen- sus based estimation law ( 5 ). Inspired by the algorithm presen ted in [ 19 ], for construction of directed acyclic graphs asso ciated with unde- tectable eigen v alues of an L TI system, we present a sp oof-resilient algorithm which is distributively executed by all the regular no des. The ov er- all distributed estimation sc heme constitutes the construction of these sub-graphs and the pre- scrib ed local filtering-based algorithm which are p erformed in parallel. In what follo ws, w e define the directed acyclic graphs that are paths for information flo w o v er the net w ork. Definition 9 (SR-MEDA G) F or eac h eigen v alue λ j ∈ σ U ( A ), the spanning sub-graph G j = ( V , E j ) of G Algorithm 1 SR-MEDA G Construction Algo- rithm 1: while k ≤ ¯ K j do 2: for λ j ∈ σ U ( A ) do c i ( j ) = 0 , N j i = ∅ . 3: 4: if i ∈ S j then 5: No de i up dates c i ( j ) to 1, sets N j i = ∅ and broadcasts a message 6: χ j (e.g. “110”) to its neigh b ors. 7: end if 8: if i ∈ V \ S j then 9: if ( c i ( j ) = 0, and node i has receiv ed m j from at least 2( β + 1) f + 1 distinct neigh b ors) then 10: No de i up dates c i ( j ) to 1 and stores the lab els of the 11: neigh b ors from whic h it received χ j to N j i . 12: end if 13: if c i ( j ) = 1 then 14: No de i broadcasts χ j to its neigh b ors. 15: end if 16: end if 17: end for 18: end while 19: Result : N j i , ∀ λ j ∈ σ U ( A ) is Sp oof-Resilient Mode Estimation Directed Acyclic Graph (SR-MEDA G) if it has the follo wing properties: 1) If i ∈ ( V \ S j ) ∩ R , then |N j i | ≥ 2( β + 1) f + 1. 2) There is a partition of R in to the sets L j 0 , L j 1 , . . . , L j ξ j , suc h that L j 0 = S j ∩ R , and N j i ∩ R ⊆ S m − 1 r =0 L j r for i ∈ L j m , where 1 ≤ m ≤ ξ j . Also, N j i ∩ R is the set of parent no des of no de i and L j m is the m -th lay er of G j . In fact, for each λ j , w e can organize the set of regular no des of the graph G as a directed acyclic graph G j . In G j , the set of regular source no des are denoted by L j 0 . Also, the set of regular nodes which hav e at least one path with length of m to L 0 are in the m -th lay er of G j denoted b y L m . Each regular no de in m -th lay er has at least 2( β + 1) f + 1 parent no des from the previous lay ers ( S m − 1 r =0 L j r ). Eac h regular node i ∈ R distributively exe- cutes the SR-MEDA G construction algorithm, Springer Con trol Theory and T ec hnology Sp o of-r esilient Distribute d Observers 9 presen ted as Algorithm 1 . The final result of the algorithm for node i is the set N j i asso ciated with ev ery undetectable eigenv alue λ j ∈ σ ( A ). By exe- cuting the algorithm at each time step k , no de i stores a coun ter v alue c i ( j ) and a list of indices N j i in p ersisten t memories for eac h undetectable eigen v alue λ j . The stored v alues in N j i ⊆ N i are the parent nodes’ indices of no de i in the SR- MED A G of λ j . Each regular no de i starts with c i ( j ) = 0 and N j i = ∅ . If node i was a source no de for λ j , i.e. i ∈ S j , it sets c i ( j ) = 1 and N j i = ∅ , then it b egins and k eeps broadcasting an arbitrary preset message χ j to its neigh b ors 2 for at least ¯ K j steps (later we pro ve that ¯ K j is b ounded). If no de i was a follo w er no de for λ j , i.e. i ∈ V \ S j , it waits until it receives χ j from at least 2( β + 1) f + 1 distinct neighbors. Then, it sets c i ( j ) = 1, sav es the indices of the neighbors from which it receiv ed χ j as N j i , b egins and keeps broadcasting χ j to its neighbors for at least ¯ K j steps. Finally , we say that SR-MEDA G c onstruc- tion algorithm terminates for no de i if the coun ter v alue c i ( j ) = 1, ∀ λ j ∈ σ U ( A ). Also, we sa y that SR-MED AG c onstruction phase terminates for λ j if the coun ter v alue c i ( j ) = 1, ∀ i ∈ R . In terestingly , it is not necessary for the regular no des to kno w ¯ K j (in that case, they ha v e to exe- cute the construction algorithm for all the future time not up to ¯ K j ). Indeed, eac h regular no de i can b egin up dating its state estimates in parallel as so on as it sets c i ( j ) = 1 for λ j although the SR-MED A G construction phase has not b een ter- minated y et. Ho wev er, we kno w that the construc- tion phase will be terminated at some time instan t in the future (b ounded b y ¯ K j ) when all regular no des will b e able to update their own state esti- mates corresp onding to each of the undetectable eigen v alues using the distributed consensus-based rule ( 5 ). In this regard, consider that delay and async hron y do not affect the output of the algo- rithm for eac h regular node i . Because no de i waits un til it receiv es the predefined message χ j from a sp ecified num b er of nodes regardless of the time it takes. Indeed, asynchron y and b ounded delays only p ostpone termination of the algorithm. F urthermore, one may concern that some of the regular nodes are exp osed to be impersonated 2 W e used the term bro adcast considering the case of wireless netw orks. Regular nodes ma y transmit the information to their known outgoing neighbors in wired netw orks. b y smart sp o ofers at any time while they are exe- cuting the construction algorithm. In fact, each smart sp oofer not only can imp ersonate regular no des (by sending arbitrary messages other than the true message χ j on b ehalf of them) but also can misb eha ve as follo ws: i) It chooses to transmit an y message different from the true message χ j from start to termi- nation of the construction phase. ii) It transmits the true message before the counter v alue is triggered b y a regular no de. iii) It c ho oses not to transmit a message at all. In the first case, regular nodes are able to iden tify the adversarial no de as it go es against the rules of Algorithm 1 . In the latter tw o cases, the adversar- ial no de is undetectable by regular no des relying just on local information. How ever, later w e dis- cuss constraints on the graph top ology so that adv ersarial no des fail to make an y problem neither for the construction algorithm nor the estimation pro cess. It is noteworth y that the upp er b ound for the parameter ¯ K j in Algorithm 1 is a function of the parameter β , which is the capacit y that async hron y provides for smart sp oofers to imp er- sonate regular nodes. This upp er bound would b e differen t if w e consider simply more Byzan- tine nodes instead of sp o ofers and imp ersonated no des. Actually , another con tribution of our paper with resp ect to [ 19 ] is the MED AG construction algorithm and its conv ergence time. In the case of sync hronous net works, eac h regular no de updates only once and go es to sleep, while, in asynchronous net w orks, regular no des hav e to contin ue updat- ing up to ¯ K j time-steps in order to complete the SR-MED A G construction. In the following theorem, we sho w that the sub-graphs distributively found by the regular no des, after termination of the construction phase, satisfy prop erties of the SR-MED AG. Theorem 1 If the SR-MED AG construction phase terminates for λ j ∈ σ U ( A ), there exists a sub-graph G j satisfying all the prop erties of an SR-MED AG. Pr o of First, w e prov e b y con tradiction that the span- ning sub-graph G j is a directed acyclic graph. Suppose there is a directed cycle iP i , where i and the no des in P b elongs to R . The path P originates from i which Springer Con trol Theory and T ec hnology 10 Sp o of-r esilient Distribute d Observers c hanges its counter v alue c i ( j ) from 0 to 1 and b egins transmitting χ j to its neigh b ors at a time instant t = k j i . Let the last node on the path P be ` . Clearly , no de i receiv es data from no de ` at a time instant t > k j i . As an edge from ` is p oin ting to node i , node i is supp osed to receive the message χ j from no de ` ev en when its counter v alue c i ( j ) is set to 1. This con- tradicts what no de i has to do according to Algorithm 1 . The same argumen t holds for every regular no de b elonging to G j . Next, w e associate the notion of path length, refer- ring to graph theory , to the found sub-graphs after the termination of the SR-MED AG construction phase to show that the set R in G j is partitioned to the sets L j 0 , L j 1 , . . . , L j ξ j . T o this end, let a regular no de i up date its counter v alue c i ( j ) from 0 to 1 at a time instan t t = k j i . Then, w e sa y that the node i belongs to L j m of G j if length of its longest path to a no de in S j b e m at k j i . Apparently , L j ξ j is set of the nodes which ha ve at least a path with maximum length (among all acyclic paths of G j ) to a no de in S j as 1 ≤ m ≤ ξ j . Accordingly , no de i b elongs to L j 0 of G j if i ∈ S j ∩ R . Now, supp ose that the SR-MEDA G construction phase terminates for λ j ∈ σ U ( A ). Since all the nodes up date their counter v alues from 0 to 1 at some time instan t, it is concluded that S ξ j r =0 L j r = R . Moreo ver, a regular no de in R cannot up date its coun ter v alue at t wo different time steps (the conv erse contradicts the rules of Algorithm 1 ). Thus L j r ∩ L j s = ∅ , ∀ r 6 = s . This completes the pro of according to the definition of the sets L j m (0 ≤ m ≤ ξ j ). Remark 1 Since the netw ork communications are async hronous and b ecause eac h regular no de does not kno w the comm unication dela ys b et ween other no des, regular no des in the sets L j 0 , L j 1 , . . . , L j ξ j do not up date their counter v alues in the same order as their lay er n umber. W e inten tionally used the minimum n umber of v ariables to b e communicated in SR-MEDA G so as to a void potential masquerading threats caused b y those v ariables. F or example, it is not p ossi- ble for regular no des to realize their lay er order in G j as they cannot identify which of their parent no des are sp oofed. T o clarify this, consider a reg- ular no de i in L j m . The regular node has to receive 2( β + 1) f + 1 incoming edges from the no des in S m − 1 r =0 L j r whic h broadcast their lay er num b ers so that the no de i can realize its own lay er n um b er b y sorting the receiv ed v alues and selecting the L j 0 L j 1 L j 2 i s q p 1 p 2 h Fig. 2 Motifs found in SR-MEDAG of G j for f = 1 and β = 1 with the regular no de i in L j 2 , three regular paren t nodes of i in L j 0 ( p 1 and p 2 are independent no des of the motifs and q is a common no de) and a parent no de in L j 1 which can b e impersonated by a smart sp oofer. Here, no de h is impersonated by the smart spo ofer s for the node i . maxim um as the previous lay er n umber. How ever, smart sp o ofers can imp ersonate some of these no des and send a wrong la yer num b er b ehind of them. Thus, the node i can b e deceived ab out the maxim um lay er num b er it received. In terestingly , in our metho d, there is no need that the regu- lar no des kno w their lay er orders since they only needs to kno w 2( β + 1) f + 1 of their paren t nodes to succeed in the estimation phase. Therefore, the construction algorithm can still b e executed dis- tributedly . Moreo ver, our strategy succeeds ev en if some of the source no des in S j are smart sp oofers. 4.2 Analysis of the Resilien t Distributed Estimation Strategy In this subsection, we in tro duce a rep eating pat- tern sub-graph whic h is used to simplify the anal- ysis of our distributed estimation sc heme. These sub-graphs are constructed and organized for eac h regular no de according to its incoming edges from smart sp oofers and other regular neighbors. Note that they ma y hav e o v erlaps in sp ecific no des and are defined as follo ws. Definition 10 (Motifs) Consider a regular no de i ∈ L j m at time instan t k and λ j ∈ σ U ( A ). Partition N j i in to subsets { q } , { p r } , r = { 1 , 2 , . . . , r } , and { h l } , l = { 1 , 2 , . . . , ¯ l } , where q and p r are the paren t nodes of no de i that are not impersonated and h l is a smart sp oofer in N j i or an imp ersonated paren t node of the Springer Con trol Theory and T ec hnology Sp o of-r esilient Distribute d Observers 11 no de i . Then, G j i ( l, r ) = V j i ( l, r ) , E j i ( l, r ) is a sub- graph of G j indicating the motif asso ciated with h l and p r around the no de i , where V j i ( l, r ) = { i, p r , q, h l } and E j i ( l, r ) = { ( p r , i ) , ( q, i ) , ( h l , i ) } . W e aim to associate eac h motif G j i to each no de i to ensure that a smart sp o ofer or an imp erson- ated node cannot deviate the estimation of the no de i . In fact, eac h motif is the smallest sub- graph of G j whic h is resilient against Byzantine attac ks. Note that imp ersonated regular no des are p oten tial Byzantine adversaries since smart sp oofers can use their identities to send arbitrary v alues to their neigh b ors. Definition 11 (Indep enden t and common no des) Consider ¯ γ motifs asso ciated with h l and p r around the regular node i denoted by G j i ( l, r ), r = 1 , 2 , . . . , ¯ γ . Let p γ b e a regular no de in the set V i j ( l, r ), r = γ . Then, p γ is an independent no de if p γ / ∈ V i j ( l, r ) ∀ r 6 = γ . A no de that is not independent is called common. The analysis strategy is to find the set of motifs around node i ∈ L j m suc h that they ha v e only one common no de. The follo wing lemma deter- mines the num b er of suc h motifs and inv estigates the p ossibility of this strategy (see Fig. 2 for an example). Lemma 2 Consider the netw ork G whic h con tains an SR-MED AG G j for each λ j ∈ σ U ( A ). There exist at least ( β + 1) f motifs around each regular node i ∈ L j m , where each motif has at least an independent no de. Pr o of F or each regular no de i ∈ L j m , referring to Def- inition 10 , consider partitioning of N j i in to subsets { q } , { p r } , r = { 1 , 2 , . . . , r } , and { h l } , l = { 1 , 2 , . . . , ¯ l } . Based on the first property of SR-MEDA G G j , we ha ve N j i ≥ 2( β + 1) f + 1. Under f -local smart sp o ofer mo del, there are at most f smart sp oofers around the no de i , i.e. |N j i ∩ R| ≥ (2 β + 1) f + 1. These regular no des are parent no des of i based on the second prop- ert y of SR-MEDA G G j . According to Lemma 1 , at most β f of these paren t no des may be imp ersonated b y the smart spo ofers. Th us, at most ( β + 1) f of the no des in N j i are whether smart spo ofers or imp erson- ated parent no des of the no de i whic h are partitioned as { h l } , l = { 1 , 2 , . . . , ¯ l } , i.e. ¯ l ≤ ( β + 1) f . W e can organize at least ( β + 1) f + 1 of the remaining parent no des, which cannot b e imp ersonated, to construct the motifs around the no de i . Based on Definition 10 and Definition 11 , w e pic k a paren t node q as a common no de and lea ve the rest in the set of indep endent par- en t no des { p r } , r = 1 , 2 , . . . , r , i.e. r ≥ ( β + 1) f . Since r ≥ ¯ l , w e can find at least ( β + 1) f motifs around the regular no de i suc h that all of them hav e one common paren t no de q and each asso ciated with an indep en- den t parent no de p r and a node h l . This completes the pro of. Fig. 2 exhibits t wo ov erlapping motifs. In this example, there is a smart sp oofer no de around the regular no de i , i.e. f = 1. Also, it is supp osed that β = 1. Th us, according to Lemma 2 , tw o motifs are found around node i . Note that smart sp oofer s can imp ersonate no de h , so a motif has to b e con- structed with the no de h as the adversarial node. Also, no de q is selected as the common node while p 1 and p 2 are the tw o independent parent no des of no de i . Next, w e use the notion of motifs to analyze estimation resilience of the net w ork G enhanced by the distributed estimation up date rule ( 5 ) at eac h no de against the adversarial no des in the pres- ence of communication delays and async hrony . W e start with regular no de i ∈ L j m and generalize our analysis to the whole net w ork afterw ards. Lemma 3 Consider the net work G which contains an SR-MEDA G G j for each λ j ∈ σ U ( A ). Supp ose that the state estimates of regular parent no des of no de i ∈ L j m , for the state related to λ j , conv erge to z j asymptotically . Then, the local filtering-based algorithm go verned b y up date rule ( 5 ) ensures that lim k →∞ | ˆ z j i [ k ] − z j [ k ] | = 0 in the presence of comm u- nication dela ys and async hrony under f -local smart sp oofer model. Pr o of Based on Lemma 2 , no de i has at most ( β + 1) f p oten tial threats and at least ( β + 1) f motifs around no de i such that they hav e one common no de. Con- sider the motifs around node i : G j i ( l, r ), r = 1 , 2 , . . . , r , l = 1 , 2 , . . . , ¯ l , where r ≥ ( β + 1) f and ¯ l ≤ ( β + 1) f . Let p r b e an indep endent parent node of the no de i , q the common paren t node, and h l the potential Byzantine adv ersarial no de in G j i ( l, r ), where the state estimation of p r and q conv erge to z j asymptotically for the state related to λ j . F or simplicit y of notations, w e define k i` = k − e k i` [ k ] − τ i` [ k ]. Note that τ i` [ k ] and e k i` are upp er b ounded by ¯ τ and ¯ k , thus k i` = k if k → ∞ . Therefore, for each node i , we calculate the asymptotic Springer Con trol Theory and T ec hnology 12 Sp o of-r esilient Distribute d Observers estimation err or of node ` ∈ N j i for z j [ k ] b y the last transmitted data to the no de i : e j ` [ k ] = ˆ z j ` [ k i` ] − z j [ k ], k → ∞ . Also, the asymptotic estimation error of the no de i for z j [ k ] is denoted by e j i [ k ] = ˆ z j i [ k ] − z j [ k ], k → ∞ . Then, subtracting z j [ k + 1] from b oth sides of ( 5 ) and noting that z j [ k + 1] = λ j z j [ k ] based on ( 3 ), w e derive Equation 6 from ( 5 ). Equation ( 6 ) represen ts that the estimation error of the no de i is a linear com- bination of the estimation errors of its neighbors whic h are group ed as motifs. Note that P ` ∈N j i ω j i` [ k ] = 1. F or the un-imp ersonated parent no des of no de i , we ha ve lim k →∞ e j q [ k ] = 0 and lim k →∞ e j p r [ k ] = 0, r = 1 , 2 , . . . , r . No w, consider the motifs G j i ( l, r ), l = r = 1 , 2 , . . . , ¯ l (note that r ≥ ¯ l ) for the adversarial no des h ` , l = 1 , 2 , . . . , ¯ l . In construction of the motifs, we arbitrarily pic k the common node q ; so we supp ose that ˆ z j p r [ k ] ≤ ˆ z j q [ k ], r = 1 , 2 , . . . , ¯ l . The following t wo cases are p ossible regarding the estimation v alues of the no des in the motif G j i ( l, r ): (i) ˆ z j h l [ k ] < ˆ z j p r [ k ip r ] or ˆ z j h l [ k ] > ˆ z j q [ k ], (ii) ˆ z j p r [ k ] ≤ ˆ z j h l [ k ] ≤ ˆ z j q [ k ]. In the former case, according to the lo cal filtering algo- rithm, v alues of the node h l will be remov ed b y setting ω ih l [ k ] = 0. F rom the latter case, w e infer that e j p r [ k ] ≤ e j h l [ k ] ≤ e j q [ k ]; the asymptotic estima- tion error of the adv ersarial node h l will be trapped b y the estimation errors of the parent nodes p r and q in motif G j i ( l, r ) at time step k and w ill be sandwic hed b y them o v er time as they con verge to 0 asymptotically . Therefor, we conclude that lim k →∞ e j h l [ k ] = 0. e j i [ k +1] = λ j X ` ∈N j i ω j i` [ k ] ˆ z j ` [ k i` ] − λ j X ` ∈N j i ω j i` [ k ] z j [ k ] = ¯ l X l = r =1 λ j ω j ip r [ k ] ˆ z j p r [ k ip r ] − λ j ω j ip r [ k ] z j [ k ] + λ j ω j ih l [ k ] ˆ z j h l [ k ih l ] − λ j ω j ih l [ k ] z j [ k ] + r X r = ¯ l +1 λ j ω j ip r [ k ] ˆ z j p r [ k ip r ] − λ j ω j ip r [ k ] z j [ k ] + λ j ω j iq [ k ] ˆ z j q [ k iq ] − λ j ω j iq [ k ] z j [ k ] = λ j ¯ l X l = r =1 ω j ip r [ k ] e j p r [ k ] + ω j ih l [ k ] e j h l [ k ] + λ j r X r = ¯ l +1 ω j ip r [ k ] e j p r [ k ] + λ j ω j iq [ k ] e j q [ k ] . (6) The same argument holds for all adv ersarial no des h l ∈ G j i ( l, r ), l = 1 , 2 , . . . , ¯ l . Therefore, the estimation error e j i [ k + 1], whic h is the linear combination of the estimation errors e j p r [ k ], r = 1 , 2 , . . . , r , e j h l [ k ], l = 1 , 2 , . . . , ¯ l and e j q [ k ], con v erges to 0 asymptotically , i.e. lim k →∞ e j i [ k ] = lim k →∞ | ˆ z j i [ k ] − z j [ k ] | = 0 , ∀ i ∈ L j m . No w, we analyze resilience of the estimation of all the follow er no des in the whole netw ork G with comm unication delays and async hrony against f - lo cal smart spo ofer model. Lemma 4 Consider the net work G which contains an SR-MEDA G G j for each λ j ∈ σ U ( A ). Then, for eac h regular no de i ∈ R and each λ j ∈ U i , the lo cal filtering-based algorithm gov erned b y up date rule ( 5 ) ensures that lim k →∞ | ˆ z j i [ k ] − z j [ k ] | = 0 in the pres- ence of comm unication dela ys and asynchron y under f -lo cal smart sp oofer model. Pr o of As G con tains an SR-MEDA G for each λ j ∈ σ U ( A ), the sets L j 0 , L j 1 , . . . , L j ξ j form a partition of the set R . T o pro ve, we use induction on the la yer n umber m . F or m = 0, b y definition of the set L j 0 , all the reg- ular nodes in L j 0 b elong to the set S j and can estimate z j [ k ] asymptotically . Then, consider the regular node i b elonging to the set L j 1 . Supp ose that the regular no de i has f incoming edges from adversarial no des. Then, according to Lemma 2 , w e can find at least ( β + 1) f motifs around no de i with each of them having an indep enden t regular source no de from the set L j 0 . Eac h smart sp oofer is able to imp ersonate at most β f paren t no des of i . So, there are at most ( β + 1) f Byzan- tine adversarial no des (including smart sp o ofers and imp ersonated regular no des) around no de i . How ev er, w e infer from Lemma 3 that the state estimate v alue of eac h adversarial no de is trapped and sandwic hed by one of the motifs according to the local filtering algo- rithm. Thus, the state estimate of no de i conv erges to z j asymptotically . Next, supp ose the result holds for the regular no des of all la yers from 0 to m (where 1 ≤ m ≤ ξ j − 1). By induction, it is concluded that the result holds for all the regular no des in L j m +1 as well based on the definition of SR-MED AG. Due to the linear dynamics of the lo cal Luen- b erger observers for source nodes and since the estimation error of each follow er no de is a linear com bination of its un-imp ersonated parents, we infer the follo wing corollary ab out the con v ergence rate of the follo w er no des’ estimation error. Springer Con trol Theory and T ec hnology Sp o of-r esilient Distribute d Observers 13 Corollary 1 Estimation conv ergence rate of all the follo wer nodes in the netw ork is exp onen tial as the estimation error of the source nodes conv erges to 0 exp onen tially . Theorem 2 Consider the netw ork G whic h con- tains an SR-MED AG for each λ j ∈ σ U ( A ). Then, the distributed estimation sc heme gov erned by the Luen b erger observers describ ed by ( 4 ), and the lo cal filtering-based algorithm gov erned by up date rule ( 5 ), ac hieves resilient omniscience in the presence of com- m unication delays and asynchron y under f -local smart sp oofer model. Pr o of Based on the observ able canonical decompo- sition represented by ( 3 ), for eac h regular node i , states of the dynamics system ( 1 ) are mapp ed and partitioned into tw o sub-states z D i [ k ] and z U i [ k ] corresp onding to the detectable and undetectable eigen v alues of the no de i , resp ectively . Using the designed Luenberger observers, ˆ z D i [ k ] con verges to z D i [ k ] asymptotically . As an SR-MEDA G exists for eac h λ j ∈ σ U ( A ), the result of Lemma 4 also holds. Consequen tly , no de i is able to estimate z U i [ k ] asymp- totically even in the presence of communication delays, async hrony and adv ersarial actions of smart sp oofers. Com bining these results, we infer that no de i can esti- mate the entire state z [ k ] which leads to resilien tly observing x [ k ] using the transformation x [ k ] = Ψ z [ k ]. This completes the pro of. 4.3 Sp o of-Resilient Graph T op ologies In this subsection, we characterize graph topolo- gies whic h ensures termination of the SR-MED AG construction phase for each λ j ∈ σ U ( A ) under misb eha vior of smart sp oofers. Lemma 5 The SR-MEDA G construction phase ter- minates for λ j ∈ σ U ( A ) if G is strongly 3( β + 1) f + 1 -robust w.r.t. S j . Pr o of Contradiction is used for the pro of. Consider an y λ j ∈ σ U ( A ) and let G be strongly 3( β + 1) f + 1 -robust w.r.t. the set of source nodes S j . If the SR- MED AG construction phase do es not terminate for λ j , there exists a set of regular nodes C ⊆ V \ S j whic h nev er up date their counter v alues c i ( j ) from 0 to 1 for i ∈ C . As G is strongly 3( β + 1) f + 1 -robust w.r.t. S j , it follo ws that C is 3( β + 1) f + 1 -reac hable, i.e., there exists a no de i ∈ C which has at least 3( β + 1) f + 1 neigh b ors outside C . Under the f -lo cal smart sp oofer mo del, at most f of these nodes are smart spo ofers whic h are able either to misbehav e themselves or to imp ersonate βf regular no des during the SR-MEDA G construction phase. So, at least, 2( β + 1) f + 1 of them are regular nodes with c i ( j ) = 1 which must hav e transmitted χ j to no de i . Th us, no de i must ha ve c hanged c i ( j ) from 0 to 1 at some p oin t of time, according to the rules of Algorithm 1 . This is a con- tradiction. Prop osition 2 Suppose that G is strongly 3( β + 1) f + 1 -robust w.r.t. S j , ∀ λ j ∈ σ U ( A ), and let the SR-MED AG construction phase starts at k = 0. Then, ¯ K j in Algorithm 1 is upp er b ounded by ¯ l j ( η + 1) ¯ k + ¯ τ + 1 where η = β b ( ¯ τ − ¯ k ) / ¯ k c and ¯ l is length of the longest path of G j . Pr o of Since G is strongly 3( β + 1) f + 1 -robust w.r.t. S j , according to Lemma 5 , each regular no de has at least 2( β + 1) f + 1 paren t no des which remain safe from sp oofing and transmit χ j at least once to the regular no de. Each of these parent no des has to make at least an up date within ¯ k consecutive steps. W e consider tw o separate cases: i) ¯ τ ≤ ¯ k and ii) ¯ τ > ¯ k . Let no de i b e in L j 1 of G j . In the first case, eac h smart spo ofer s ∈ N j i is able to impersonate at most β f parent nodes of no de i in each consecutive ¯ k steps. So, the other 2( β + 1) f + 1 parent nodes will remain safe and transmit χ j to node i . F or the second case, w e consider the w orst case where all these parent nodes p ostpone their up dates b y ¯ k − 1 steps and commu- nicate to their neighbors with ¯ τ steps dela y (because w e are seeking the maxim um time steps that a smart sp oofer can prev en t exactly 2( β + 1) f + 1 paren t no des to transmit χ j to their neighbors). As ¯ τ > ¯ k , the smart sp oofer has more η = β b ( ¯ τ − ¯ k ) / ¯ k c capacity after the first update to impersonate more parent nodes. Ho w- ev er, they cannot do it p ermanen tly , i.e. at some time the paren t no des will transmit χ j to node i . Supp ose that the smart sp oofer use this additional capacity to imp ersonate just one additional paren t no de. In fact, η up dates of this parent no de will b e sp oofed whic h tak es η ¯ k time steps. Considering the first ¯ k − 1 steps that the parent no de ma y p ostpone its first up date and ¯ τ steps delay of its last up date, the ov erall time that the spo ofed paren t no de succeeds to transmit χ j to no de i will be ( η + 1) ¯ k + ¯ τ + 1 steps. No w, consider the last node in the longest path of G j whic h is the last no de that up dates its counter v alue from 0 to 1. Let the length of the longest path of G j b e ¯ l j and each no de in this path updates its counter Springer Con trol Theory and T ec hnology 14 Sp o of-r esilient Distribute d Observers v alue from 0 to 1 after at most ( η +1) ¯ k + ¯ τ +1. Then the maxim um time needed for eac h regular node to keep transmitting χ j is b ounded b y ¯ l j ( η + 1) ¯ k + ¯ τ + 1 . Remark 2 The maximum time that is needed for eac h regular no de i ∈ L j m to keep transmitting χ j is b ounded by ( ¯ l j − m ) ( η + 1) ¯ k + ¯ τ + 1 . How ever, as the regular nodes cannot characterize their lay er num- b ers, they hav e to keep transmitting the message χ j up to ¯ K j steps. Finally , we propose the ov erall constraint on the netw ork top ology which mak es sure that the net w ork ac hieves resilien t omniscience despite of smart sp oofing actions. Theorem 3 Resilient omniscience of a netw ork with comm unication dela ys and asynchron y under f -lo cal smart sp o ofer mo del is ac hieved using the prop osed estimation sc heme if G is strongly 3( β + 1) f + 1 - robust w.r.t. S j , ∀ λ j ∈ σ U ( A ). Pr o of According to Lemma 5 , the SR-MEDA G con- struction phase terminates for every undetectable eigen v alue λ j if G is strongly 3( β + 1) f + 1 -robust w.r.t. S j , ∀ λ j ∈ σ U ( A ). Th us, based on Theorem 1 , as SR-MEDA G exists for every λ j ∈ σ U ( A ). Finally , from Theorem 2 , the existence of an SR-MEDA G for ev ery λ j ∈ σ U ( A ) leads to resilien t omniscience by using our prop osed distributed estimation scheme in a net w ork with comm unication delays and async hrony under f -lo cal smart spo ofer mo del. Remark 3 Suppose that smart spo ofers imp ersonate none of the regular no des during SR-MEDA G con- struction phase. Then, the sufficient constraint on the net work top ology to ac hieve resilient omniscience is strongly 2( β + 1) f +1 -robust w.r.t. S j , ∀ λ j ∈ σ U ( A ). Note that the presen ted sufficient conditions on the top ology will be the same as the case of Byzan tine attac ks, prop osed in [ 19 ], if we set the parameter β = 0. It means that the estimation will conv erge for all regular no des under a sim- pler top ology , i.e. strongly (3 f + 1)-robust w.r.t. S j , ∀ λ j ∈ σ U ( A ). This is consisten t with the most imp ortan t massage of our pap er whic h asserts that asynchronous netw orks are more suscepti- ble against cyb er attacks; asynchronous net works can b e threaten b y adversaries that are stronger than Byzan tine no des, i.e. smart sp o ofers, which can use free time-steps b et ween up dates of regu- lar no des to imp ersonate some of them in order to mislead the others. 4.4 Time-V arying Net works In the presented results so far, the observers o ver net w ork G were supp osed to b e fixed, that is, the edge set E was time in v ariant. W e now reconsider the results with a partially asynchronous time- v arying netw ork G [ k ] = ( V , E [ k ]) instead of the original time-inv ariant graph G earlier. T o this end, similar to what is presen ted in [ 21 ], w e define a join tly graph robustness measure as follo ws. Definition 12 (Jointly strongly r -robust w.r.t. S ) The time-v arying graph G [ k ] = ( V , E [ k ]) is said to be join tly strongly r -robust w.r.t. S if there exists a fixed ¯ µ ≥ 0 suc h that S ¯ µ µ =0 G [ k − µ ], k ∈ Z ≥ ¯ µ , is strongly r -robust w.r.t. S . Referring to Lemma 1 , the capacit y of smart sp oofers for imp ersonating regular no des is b ounded within eac h consecutive ¯ k steps b y β . Th us, the horizon parameter ¯ µ of time-v arying graph G [ k ] has to satisfy the following inequality: ¯ µ ≤ ¯ k . (7) Note that, otherwise, each smart sp oofer w ould ha v e extra capacity to impersonate more than β regular no des after eac h ¯ k steps. No w, the follo wing result states the extension of our main result (Theorem 3 ) for the case of time-v arying net w orks. Corollary 2 Resilient omniscience of a netw ork with comm unication dela ys and asynchron y under f -lo cal smart sp oofer mo del can b e achiev ed using the pro- p osed estimation scheme if G is jointly strongly 3( β + 1) f + 1 -robust w.r.t. S j , ∀ λ j ∈ σ U ( A ), under condition ( 7 ). Similarly , reconsidering the case where smart sp oofers do not imp ersonate any of the regu- lar no des during the SR-MEDA G construction phase, the follo wing result holds for time-v arying net w orks. Springer Con trol Theory and T ec hnology Sp o of-r esilient Distribute d Observers 15 Corollary 3 Supp ose that smart spo ofers imperson- ate none of the regular no des during SR-MEDA G construction phase. Then, the sufficient top ology con- strain t on the netw ork G [ k ] to ac hieve resilien t omni- science is jointly strongly 2( β + 1) f + 1 -robust w.r.t. S j , ∀ λ j ∈ σ U ( A ), with condition ( 7 ). These results follow Lemmas 3 to 5 as the time-in v arian t nature of the original graph G is not used in the pro ofs. 4.5 Randomized Up date Rule Consider the case that eac h regular no de, at eac h time instant, randomly decides whether to update its state estimate or not. That is, the follo wer no de i ∈ R up dates its state estimate at each time instan t k with the probabilit y of P i [ k ]. Note that with such updates, the algorithm remains fully distributed. Even the probabilities P i [ k ] need not b e identical. Intuitiv ely , this is in alignmen t with Assumption 3 as the regular no de will up date at least once within each consecutive ¯ k steps. With this strategy , the top ology constraint required for resilient omniscience can b e relaxed. This is b ecause the smart sp o ofers cannot predict the up date times in adv ance and need to use more of their spo ofing capacity to mak e sure that the reg- ular no des, at each time step, receive and accept false data with fake iden tities; they cannot imp er- sonate other nodes in a systematic manner in eac h consecutiv e ¯ k steps. In fact, regular no des uti- lized randomization in update times as a defensive means against smart sp oofers. What follows is the mo dification of Theorem 3 for the suggested net work with randomized up dat- ing strategy . Theorem 4 Resilient omniscience of a net work with comm unication dela ys and async hrony under the f - lo cal smart sp oofer mo del can b e achiev ed using the prop osed estimation sc heme if each follo wer node i ∈ R , at each time instant k , up dates using rule ( 5 ) with the probabilit y of P i ∈ (0 , 1] and if G is strongly 3( β 0 + 1) f + 1 -robust w.r.t. S j , ∀ λ j ∈ σ U ( A ), where β 0 = b β / ¯ k c + 1. Pr o of Referring to Lemma 1 , eac h smart sp oofer was able to imp ersonate at most β regular no des within R 3 R 2 s R 1 System Dynamics λ 1 λ 2 h Fig. 3 A sample netw ork that is 2( β + 1) f + 1 -robust w.r.t. λ j . No de h ∈ R 1 is imp ersonated by the smart spo ofer s for the nodes in set R 3 . ¯ k steps in case the smart sp o ofers knew when exactly eac h regular no de up dates its state estimate. Now, consider that each regular no de i make an up date at eac h time instan t k randomly with a probability of P i [ k ] ∈ (0 , 1]. Then, eac h smart sp oofer s ∈ N i can- not predict when exactly the no de i updates; so it has to imp ersonate the incoming neigh b ors of the node i for all the time steps within each consecutive ¯ k steps, that is ¯ k times. As a result, the smart sp oofers need to dedicate more capacit y to pro duce fault y data pack ets with the mimick ed identities of the neighbors of the no de i . Th us, the smart spo ofers will b e able to imper- sonate b β / ¯ k c regular no des for any of ¯ k steps and one regular no de for a limited num b er of time-steps, i.e. less than ¯ k . In this situation, to ensure that the smart sp oofers cannot impersonate an y extra regular no des, w e define β 0 = b β / ¯ k c + 1. Accordingly , similar to the pro of of Theorem 3 , the required top ology constrain t for omniscience based on the parameter β 0 is strongly 3( β 0 + 1) f + 1 -robust w.r.t. S j , ∀ λ j ∈ σ U ( A ). Remark 4 Based on Lemma 1 , w e hav e β 0 = b ( α ¯ k − 1) / ¯ k c . On the other hand, we kno w ¯ k ≥ 1. There- fore, it is concluded that β 0 = α − 1 in the case of a synchronous netw ork ( ¯ k = 1) and β 0 = α in an async hronous net work ( ¯ k > 1). 5 Sim ulation Results In this section, we present a simulation example to demonstrate how a smart sp oofer can misb eha ve and how it can be restrained in a given net w ork of distributed observ ers. In particular, we sho w why the constrain ts on the net work topology , prop osed in Theorems 2 and 3 , are critical for ac hieving resilien t omniscience under f -local smart sp oofer mo del in the presence of async hronous communi- cations and dela ys. Springer Con trol Theory and T ec hnology 16 Sp o of-r esilient Distribute d Observers 0 2 4 6 8 10 12 14 16 18 20 22 24 26 28 30 0 10 20 30 40 50 60 70 80 90 100 Fig. 4 Omniscience of the sample netw ork: the regular source no des in R 1 asymptotically estimate z 1 using Luen- berger observ ers. The follo wer no des in R 2 and R 3 can asymptotically estimate z 1 despite of the efforts smart spo ofer do es for misleading them by imp ersonating the node h ∈ R 1 . They also estimate z 2 since there is no spo ofing for λ 2 . 0 2 4 6 8 10 12 14 16 18 20 22 24 26 28 30 -2 0 2 4 6 8 10 Fig. 5 All the regular no des truly estimate x 1 while the smart sp o ofer s impersonates the no de h ∈ R 1 for the nodes in R 3 . T o this end, consider the net w ork illustrated in Fig. 3 . The directed edges of the graph represent all to one connections and edges p ointing in both directions represent all to all connections. The net- w ork has three sets of regular no des R 1 , R 2 , R 3 , and a smart spo ofer s ( f = 1). The capacit y of s is assumed to be α = 1 and all of the nodes are sup- p osed to mak e, at least, an up date within ¯ k = 2 steps. Thus, the parameter is set as β = 1. There are 2( β + 1) f no des in each of the sets R 1 and R 2 0 2 4 6 8 10 12 14 16 18 20 22 24 26 28 30 0 10 20 30 40 50 60 70 80 90 100 Fig. 6 The smart spo ofer s preven ts the follow er nodes for λ 1 in R 2 and R 3 to estimate z 1 by sending false estimate v alues on b ehalf of no de h ∈ R 1 to all the nodes in R 3 . 0 2 4 6 8 10 12 14 16 18 20 22 24 26 28 30 -2 0 2 4 6 8 10 Fig. 7 The regular nodes in R 2 and R 3 fail to estimate x 1 if the smart sp oofer s impersonates the no de h ∈ R 1 for the nodes in R 3 . and 2( β + 1) f + 1 no des in the set R 3 , where the no des within eac h set are not connected. F urther- more, comm unication dela ys o ver the net work are defined as follo ws: τ ij = 3 , if ( i ∈ R 3 and j ∈ R 2 ) 2 , if ( i ∈ R 2 and j ∈ R 3 ) or ( i ∈ R 3 and j ∈ R 1 ) 1 , if ( i ∈ R 1 and j ∈ R 3 ) or ( i ∈ R 3 and j = s ) 0 , if i = s and ( j ∈ R 1 or j ∈ R 2 ) Springer Con trol Theory and T ec hnology Sp o of-r esilient Distribute d Observers 17 Note that the smart sp oofer fully knows the dynamic system and the observ ation mo dels of the regular no des and calculates its o wn and the imp ersonated states estimations in a w ay that the targeting regular no des fail to reac h omniscience. Th us, to giv e a b etter intuition, w e deal with the transformed dynamic system and states in our sim ulations; the original system can b e analyzed accordingly . F or sake of simplicit y , we use the terms “send” and “receiv e” with ˆ z i 1 (or ˆ z i 2 ), while our purp ose is the original state ˆ x i 1 asso ciated to the ˆ z i 1 . The transition matrix of the original dynamic system and the initial state are assumed to b e A = 0 . 98 0 . 02 − 0 . 04 1 . 04 , x 0 = 2 5 , whic h, according to ( 3 ), are transformed b y Ψ = 0 . 1 1 0 . 2 1 in to the following diagonal system and initial state: ¯ A = 1 . 02 0 0 1 , z 0 = 30 − 1 . The first eigenv alue of the system ( λ 1 = 1 . 02) is unstable and the second one ( λ 2 = 1) is marginally stable. The observ ation model of the net work sys- tem is assumed to b e C i = [ − 10 10], ∀ i ∈ R 1 , C i = [2 − 1], ∀ i ∈ R 2 and C i = 0, ∀ i ∈ R 3 . The transformation of the observ ation mo del is given b y Ψ as ¯ C i = [1 0], ∀ i ∈ R 1 , ¯ C i = [0 1], ∀ i ∈ R 2 and ¯ C i = 0, ∀ i ∈ R 3 . This means that the no des in R 1 are source no des for λ 1 and follo wers for λ 2 as they can only detect λ 1 , the no des in R 2 are source no des for λ 2 and follow ers for λ 1 , and the no des in R 3 are follo wers for both λ 1 and λ 2 . Also, the no des in the set R 3 and the no de s up date at all time instants and the no des in R 1 and R 2 up date at time instan ts k = m ¯ k , m ∈ Z + . W e presen t the simulation results in tw o test scenarios. In b oth scenarios, the smart sp o ofer just imp ersonate only one node in R 1 and only for the state z 1 . Thus, all the no des of the net work will accurately estimate the state z 2 . In scenario 1, w e sho w that the follow er no des for λ 1 can asymptot- ically estimate z 1 ev en though the smart sp oofer s tries to mislead the follo wer no des but the net work finally ac hieves omniscience. Ho wev er, in scenario 2, the follow er no des cannot reach a true esti- mate of z 1 as the required top ology constraint for estimation (Theorem 2 ) is not satisfied. Scenario 1 The smart sp oofer sends the message χ s = 1 to all the no des in R 3 to pretend that it is a paren t no de for λ 1 . Although the smart sp o ofer can imp ersonate a regular no de during the SR-MEDA G construction phase, it decides not to do so and go es through the estimation phase. The initial estimates of z 1 for no des in R 1 are ˆ z i 1 [0] = 100, i = 1 , 2 and ˆ z i 1 [0] = 0, i = 3 , 4. Also, w e hav e ˆ z i 1 [0] = 0, i ∈ R 2 , and ˆ z i 1 [0] = 0 , i ∈ R 3 . Moreov er, eac h regular no de i ∈ R 1 uses a Luenberger observ er with the gain L 1 i = 0 . 5 to estimate z 1 . Starting the estimation phase, the smart sp oofer s sends tw o sequences of estimate v alues to all the nodes in R 3 in a w ay that the receiving esti- mate v alues from the no des in R 1 are eliminated in lo cal filtering: i) the estimate v alue ˆ z s 1 [ k ] = 60, where k = m ¯ k − 1 , m ∈ Z + , which keeps the smart spo ofer s among the accepted neighbors of the no des in R 3 as each no de has to send a data pack et at least in eac h consecutiv e ¯ k steps, ii) a false estimate v alue ˆ z h 1 [ k ] = 30, where k = m ¯ k , m ∈ Z ≥ 0 , on b ehalf of the no de h = 1 , h ∈ R 1 to the no des in R 3 . As shown in Fig. 4 , all the regular nodes can estimate z 1 although the smart spo ofer caused a deviation in the estima- tions of the nodes in R 3 (and accordingly the nodes in R 2 ) up to time instant k = 12. Note that the estimate v alue of ˆ z h 1 [ k ] will not b e filtered only if it conv erges to z 1 . In fact, referring to Lemma 3 , estimate v alues of the smart sp oofer are sandwiched b y estimate v alues of the regular parent no des, thanks to our prop osed rule ( 5 ) and the net work top ology constraint discussed in Theorem 2 . Scenario 2 Here, the smart sp oofer s sends a mes- sage χ s = 1 to the nodes in R 3 while it imp ersonates the no de p = 1 , p ∈ R 1 in the SR-MEDA G construc- tion phase b y setting the message χ p = 0, i.e. the no de p cannot b e a parent no de of the no des in R 3 for λ 1 . In other words, Algorithm 1 do es not termi- nate in the case of λ 1 for the no des in R 3 . In fact, the constrain t on the netw ork top ology is not satisfied for the estimation of z 1 since the no des in R 3 recognizes only 2( β + 1) f paren t nodes for λ 1 . Ho wev er, assume that the no des in R 3 decide to start the estimation regardless of the termination of the SR-MEDA G con- struction phase. As a result, the smart spo ofer is able to imp ersonate one more regular no de of the set R 1 this time in the estimation phase. The initial esti- mates of z 1 are giv en as ˆ z i 1 [0] = 10 , i ∈ R 1 , i = 2, ˆ z i 1 [0] = 0, i ∈ R 1 , i = 3 , 4, ˆ z i 1 [0] = 6, i ∈ R 2 , and ˆ z i 1 [0] = 7 , i ∈ R 3 . Again, the smart sp o ofer s sends Springer Con trol Theory and T ec hnology 18 Sp o of-r esilient Distribute d Observers t wo sequences of estimate v alues to the nodes in R 3 in a wa y that the estimate v alues of the no des i ∈ R 1 , i = 3 , 4, are eliminated in lo cal filtering: i) the esti- mate v alue ˆ z s 1 [ k ] = 8, where k = m ¯ k − 1 , m ∈ Z + , whic h keeps the smart sp oofer s among the accepted neigh b ors of the nodes in R 3 , ii) a false estimate v alue ˆ z h 1 [ k ] = 9, where k = m ¯ k , m ∈ Z ≥ 0 , on b ehalf of the no de h = 1 , h ∈ R 1 , to the no des in R 3 . Fig. 6 sho ws the consequence of spo ofing in the estimations. The initial estimate v alues of the no des in R 2 and R 3 remain constant for all the future time. It is notewor- th y that, not only the no des in R 3 are affected by the spo ofing, but the nodes in R 2 are also affected indirectly and none of them can reach omniscience for z 1 . While w e primarily analyzed the success or failure of the netw ork omniscience in the trans- formed dynamic system, the main results are v alid for the original dynamic system with different time histories of state v alues (Fig. 5 and Fig. 7 ). 6 Conclusion Com bining Byzan tine adv ersarial model and sp oofing as a misb ehaving technique, w e in tro- duced a new t yp e of cyber attack called smart sp oofing. Then, w e in v estigated the problem of distributed observer design for L TI systems in the presence of this attac k whic h uses the asyn- c hron y in communications to threaten the net- w ork. Using a tw o-step distributed mechanism, including a pre-executing algorithm for recogniz- ing the trusted neighbors and a lo cal-filtering algorithm for removing p ossible incorrect v al- ues induced by the adv ersarial nodes, the regu- lar no des can ac hieve resilient observ ation ov er so-called strongly robust graphs. W e prop osed resilien t top ology constrain ts on static and time- v arying netw orks under the prop osed adversarial threat. Numerical simulations with a sample net- w ork v alidate our analytic results. The prop osed designs are applicable to a v ast range of net work ed systems. In future studies, we consider resilient consensus problems prone to the smart sp oofing attac ks. Ac kno wledgements I offer m y sincerest gratitude to Dr. Sey ed Mehran Diba ji and Prof. Hideaki Ishii for the time they dedicated to me for useful discussions on the topic as well as their technical comments whic h signif- ican tly helped me to impro ve the quality of this pap er. References [1] Dasw ani N, Kern C, Kesa v an A. F oundations of securit y: what ev ery programmer needs to kno w. Dreamtec h Press; 2007. [2] Zheng G, Ma HT, Cheng C, T u YC. Design and logical analysis on the access authenti- cation scheme for satellite mobile communi- cation net w orks. IET Information Security . 2012;6(1):6–13. [3] Villalba LG, Matesanz JG, Canas DR, Orozco AS. Secure extension to the optimised link state routing proto col. IET Information Securit y . 2011;5(3):163–169. [4] Ueda H, Kurachi R, T ak ada H, Mizutani T, Inoue M, Horihata S. Securit y Authenti- cation System for In-V ehicle Netw ork. SEI T echnical Review. 2015;81:5–9. [5] Sun C, Hu C, Liu B. SA CK2: effective SYN flo od detection against skillful sp o ofs. IET Information Securit y . 2012;6(3):149–156. [6] Magiera J, Katulski R. Detection and mitiga- tion of GPS sp o ofing based on antenna array pro cessing. Journal of Applied Research and T echnology . 2015;13(1):45–57. [7] Su J, He J, Cheng P , Chen J. A stealth y GPS sp oofing strategy for manipulating the tra jec- tory of an unmanned aerial vehicle. Proc of IF AC W orkshop NECSYS. 2016;p. 291–296. [8] Dutta A, Langb ort C. Confiscating Fligh t Con trol System b y Stealthy Output Injection A ttac k. Journal of Aerospace Information Systems. 2017;14(4):203–213. [9] Zhang T, Zh u Q. Strategic Defense Against Deceptive Civilian GPS Sp o ofing of Unmanned Aerial V ehicles. Pro c of Int Con- ference on Decision and Game Theory for Securit y . 2017;p. 213–233. Springer Con trol Theory and T ec hnology Sp o of-r esilient Distribute d Observers 19 [10] Gil S, Kumar S, Mazumder M, Katabi D, Rus D. Guaran teeing sp o of-resilien t m ulti-rob ot netw orks. Autonomous Robots. 2017;41(6):1383–1400. [11] Renganathan V, Summers T. Spo of resilient co ordination for distributed multi-robot sys- tems. Proc of Int IEEE Symp osium on Multi- Rob ot and Multi-Agent Systems (MRS). 2017;p. 135–141. [12] Lync h NA. Distributed Algorithms. Morgan Kaufmann; 1996. [13] Diba ji SM, Safi M, Ishii H. Resilient Dis- tributed Averaging. Pro c of American Con- trol Conference. 2019;p. 96–101. [14] Bonnet F, D ´ efago X, Nguy en TD, Potop- Butucaru M. Tigh t b ound on mobile Byzan- tine Agreemen t. Theoretical Computer Sci- ence. 2016;609:361–373. [15] Alexandru AB, P equito S, Jadbabaie A, P ap- pas GJ. On the limited comm unication analysis and design for decentralized estima- tion. Pro c of IEEE Conference on Decision and Con trol. 2017;p. 1713–1718. [16] Khan UA, Kar S, Jadbabaie A, Moura JM. On connectivity , observ ability , and stabilit y in distributed estimation. Pro c of IEEE Conference on Decision and Con trol. 2010;p. 6639–6644. [17] P ark S, Martins NC. Design of dis- tributed L TI observ ers for s tate omniscience. IEEE T ransactions on Automatic Control. 2017;62(2):561–576. [18] W ang L, Morse A. A distributed observer for a time-inv ariant linear system. Pro c of American Control Conference. 2017;p. 2020– 2025. [19] Mitra A, Sundaram S. Resilient Distributed State Estimation for L TI Systems. arXiv preprin t arXiv:180209651. 2018;. [20] Mitra A, Sundaram S. Secure distributed state estimation of an L TI system ov er time- v arying netw orks and analog erasure chan- nels. Pro c of American Control Conference. 2018;p. 6578–6583. [21] Diba ji SM, Ishii H. Resilient consensus of second-order agent netw orks: Async hronous up date rules with delays. Automatica. 2017;81:123–132. [22] Diba ji SM, Ishii H, T emp o R. Resilien t ran- domized quan tized consensus. IEEE T rans- action on Automatic Con trol. 2017;. [23] Diba ji SM, Pirani M, Flamholz DB, Annasw am y AM, Johansson KH, Chakrab ortt y A. A systems and con trol p er- sp ectiv e of CPS security . Annual Reviews in Con trol. 2019;. [24] LeBlanc HJ, Zhang H, Koutsouk os X, Sun- daram S. Resilient asymptotic consensus in robust netw orks. IEEE Journal on Selected Areas in Comm unications. 2013;31(4):766– 781. [25] P elc A, Peleg D. Broadcasting with lo cally b ounded Byzantine faults. Information Pro- cessing Letters. 2005;93(3):109–115. [26] Bertsek as DP , Tsitsiklis JN. Parallel and Dis- tributed Computation: Numerical Methods. Pren tice Hall; 1989.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment