A Physics-Based Attack Detection Technique in Cyber-Physical Systems: A Model Predictive Control Co-Design Approach
In this paper a novel approach to co-design controller and attack detector for nonlinear cyber-physical systems affected by false data injection (FDI) attack is proposed. We augment the model predictive controller with an additional constraint requir…
Authors: Mohammadreza Chamanbaz, Fabrizio Dabbene, Rol
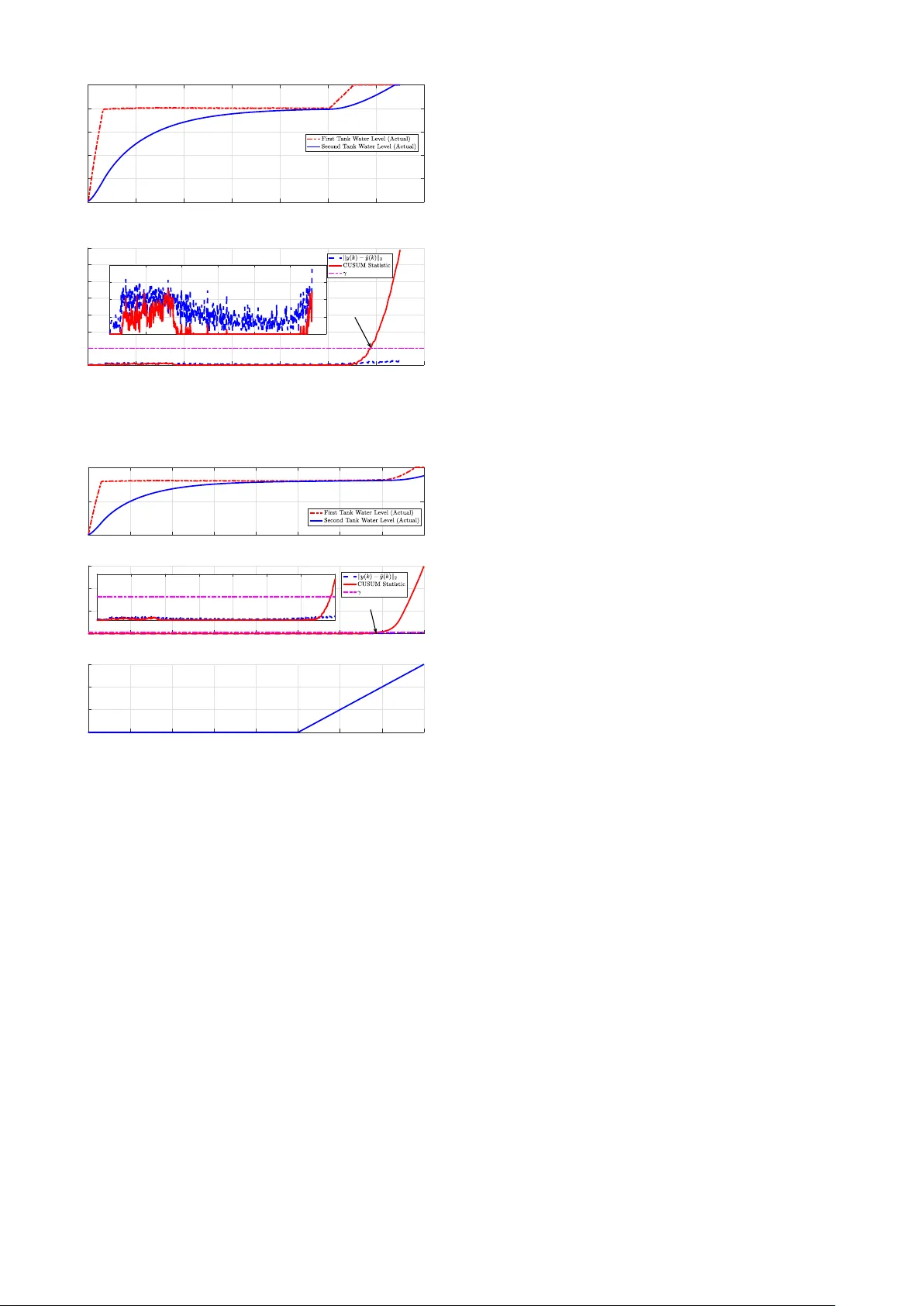
1 A Physics-Based Attack Detection T echnique in Cyber -Physical Systems: A Model Pr edictiv e Contr ol Co-Design A pproach Mohammadreza Chamanbaz, Fabrizio Dabbene and Roland Bouf fanais Abstract — In this paper a novel appr oach to co-design con- troller and attack detector for nonlinear cyber -physical systems affected by false data injection (FDI) attack is proposed. W e augment the model pr edictive controller with an additional con- straint requiring the future—in some steps ahead—trajectory of the system to remain in some time-in variant neighborhood of a properly designed refer ence trajectory . At any sampling time, we compare the real-time trajectory of the system with the designed refer ence trajectory , and construct a residual. The residual is then used in a nonparametric cumulativ e sum (CUSUM) anomaly detector to uncover FDI attacks on input and measurement channels. The effectiveness of the proposed approach is tested with a nonlinear model regarding le vel control of coupled tanks. I . I N T RO D U C T I O N Industrial c yber-ph ysical systems play a crucial rule in critical infrastructures and ev eryday life. Cyber-physical sys- tems (CPSs) are constituted of physical processes (plants) communication and computation. Some examples of CPS include power grids, intelligent transportation systems, water distribution systems, aerospace systems, retail supply chain, etc. which are all based on safety critical processes [3]. Both cyber and physical components of a CPS are vulnerable to malicious attacks. Security of CPSs is of paramount importance to societies and governments. This importance has fueled a considerable research in the recent past; see surve y papers [3], [4], [6], [7], [9], [20] and references therein. In general there are two possible approaches in attack detection: i) Information T echnology (IT) based methods, and ii) Physics-based (Control-based) methods. Due to the presence of physical components in CPS, the states of the system need to follow strict rules of nature, e.g. laws of physics. For instance, in a power grid, voltage of buses and current flo wing through lines need to follo w Kirchhoff ’ s circuit la ws. This important feature can be exploited to detect attacks in CPSs. In this paper , we focus on physics- based attack detection; hence, from no w onward by attack detection, we imply physics-based attack detection. Although attacks can be complicated from an IT vie wpoint, they tend to be rather na ¨ ıve or unsophisticated from a control prospecti ve [19]. Mohammadreza Chamanbaz and Roland Bouffanais are with the Sin- gapore University of T echnology and Design, Singapore 487372, e-mail: ( { chamanbaz, bouffanais } @sutd.edu.sg ) Fabrizio Dabbene is with CNR-IEIIT , Politecnico di T orino, Italy , email:( fabrizio.dabbene@ieiit.cnr.it ). This work was supported in part by the National Research Foundation (NRF), Prime Ministers Office, Singapore, under its National Cybersecurity R&D Programme (A ward No. NRF2014NCR-NCR001-040) and adminis- tered by the National Cybersecurity R&D Directorate. Most attack detection methods are observer-based tech- niques in which an observer is designed to estimate states of the plant. The estimated state is then compared against the actual value (measured by sensors) and a time-series residual is formed. Then, an anomaly detector is used to decide—based on the residual time series—on the presence of an adversary agent having access to the control signal and/or measurement output [1]. The observer can be static or dynamic; for instance, the phase angle estimator in power grids is a static estimator [10]. Attack detection strategies can be broadly divided into two categories: activ e and passiv e. Passi ve strategies are those in which the detection mechanism does not affect the system. On the other hand, activ e strategies affect the control system by sending some unpredictable control commands and observing if sensors react as predicted. In [15] a physical watermarking based detection mechanism is presented in which a random noise of kno wn distrib ution is injected to the plant and a stateful anomaly detector is used to detect attacks on the system. In most attack detectors, the control and attack detection designs are carried out independently: the controller is de- signed first and, subsequently , the detection mechanism is formulated. Contrary , in this paper we co-design these two critical components and propose a joint control and attack detection mechanism using elements from model predictive control (MPC). MPC is an optimization-based controller which can handle different state and control input constraints. The control signal at each sampling time is the solution of a constrained discrete-time optimal control problem [8], [14], [17]. For linear time-inv ariant systems, the resulting optimization problem is conv ex which can therefore be efficiently solved using standard solvers. If the dynamical systems is nonlinear—such as the one considered in this paper , the MPC optimization problem becomes nonconv ex. W e augment the standard MPC problem with an additional constraint which restricts the future state/output trajectory to remain within some time-in variant neighborhood of a carefully designed reference trajectory . The minimization of the MPC optimization problem in volv es the predicted states as well as inputs over the prediction horizon. The first component of the control vector is applied to the plant and the predicted outputs are used to construct the future reference trajectory . In fact, the reference trajectory at time k is the N th component of the predicted trajectory provided as the minimizer of the MPC problem at time k − N where N is the prediction horizon. The difference between actual real- time output and the reference output trajectory is stored in a residual time-series. The residual is used in a non-parametric 2 cumulativ e sum (CUSUM) anomaly detector to decide on the presence of attack in control signal or measurement output. A. Related Literatur e While the literature on attack detection is vast (see e.g. [16]) few works are based on a model predictive control design approach. In [2], the authors adopt a model-based approach in order to detect cyber -attacks in a linear system equipped with a model predictiv e controller . The problem is formalized as a binary hypothesis test. Ho we ver , the MPC structure is assumed to be giv en, and no co-design is considered. A recent and interesting line of research is the one based on the design of set-theoretic receding-horizon control schemes, see for instance [12], [13]. In these works, a specific control architecture is designed so as to be able to detect and mitigate c yber-attacks af fecting CPSs. In [22], an idea based on the concept of a receding-horizon control law is presented to mitigate replay attacks. In particular , stability is proved under some assumptions on the horizon length and the attack duration. The idea can also be used with false data injection attacks. An MPC-based attack detector using limit checking is introduced in [18]. A feasibility problem is solved online and if there does not exist a control vector being able to keep states within their safe limit during the predicted horizon, an attack is declared. W e remark that all revie wed approaches are applied to linear systems, while in this paper we consider a nonlinear setup. B. The sequel The remainder of this paper is or ganized as follows. In Section II we formulate the nonlinear MPC problem. The modified MPC problem along with proposed attack detec- tion methodology are presented in Section III. A numerical example of industrial cyber -physical systems is presented in Section IV and some concluding remarks are reported in Section V. Notations Lowercase letters are used for vectors and uppercase ones for matrices. The symbol X 0 (resp. X 0 ) is used to denote a positive (resp. positiv e semi-definite) matrix X . The set N > 0 denotes the set of positiv e integers. While y k denotes the measured output at time k , the output predicted ` steps ahead at time k is denoted as y ` | k . W e use u N | k to denote the sequence of length N of vectors u 0 | k , . . . , u N − 1 | k ; the same notation is used for output vector y N | k . The Minkowski sum of A and B is denoted by A ⊕ B = { a + b | a ∈ A, b ∈ B } . I I . P RO B L E M F O R M U L A T I O N Consider a nonlinear cyber -physical system (CPS) whose dynamics is governed by the nonlinear discrete-time system x k +1 = f ( x k , ( u k + u a k )) , (1a) y k = x k + y a k , (1b) where x k ∈ R n is the state v ector of the system at sampling time instant k , u k ∈ R m is the control signal to be applied to the system, u a k ∈ R m represents an attack signal applied to the input at time k , f : R n × R m → R n is a nonlinear map which assigns to a state vector x k and control vector u k the successor state x k +1 , y k is the measurement signal at time k , and y a k is the attack signal at the output. W e assume that all states are available for feedback. The controller is spatially distributed and the channels between controller-actuators and sensors-controller are established by some communication network, e.g. Internet or wireless, industrial Ethernet, Field- bus, etc. W e assume that malicious agents can gain access to these communication channels by compromising the security protocols, and as a consequence are able to inject their desired signals u a k and y a k to the system (1). The objectiv e is to design a model predictiv e controller for the system (1) to be able to detect any possible attack on the control input and measurement signals. In the MPC frame work, we usually restrict the output vector y k , ∀ k ∈ N > 0 to li ve in a set Y . This can be due to safety limitations; for example, the lev el of liquid in a tank needs to be within its high and low limits or furnace temperature should not exceed a predefined value. Similarly , the control signal u k , ∀ k ∈ N > 0 is also required to remain in a set U which is to prev ent any actuator saturation. The desired performance of the MPC controller is granted by the appropriate design of a cost function used in the optimization problem being solved at each sampling time. Assuming that 0 is the equilibrium point of the system—in fact if [ x T ∗ , u T ∗ ] T 6 = 0 is the equilibrium point of the system (1), we can replace f ( x k , u k ) by ( f ( x k + x ∗ , u k + u ∗ ) − x ∗ ) so to hav e 0 as the equilibrium point—the cost function ` ( x, u ) : Y × U → R > 0 penalizes the distance of the output y k and control input u k to the equilibrium point. A terminal cost is added to the cost function to ensure that the MPC policy stabilizes the system. W ith these ingredients in mind, we use the following finite-horizon cost to be minimized at time k ` N ( y N +1 | k , u N | k ) = N − 1 X j =0 y T j | k Qy j | k + u T j | k Ru j | k + V N ( y k + N ) , (2) where Q ∈ R n × n , Q 0 , R ∈ R m × m , R 0 and V N ( y ) is the terminal cost designed based on the L yapunov stability theory , see [8, Chapter 5] for further details. A terminal constraint of the form y N | k ∈ Y f is also included in the MPC optimization problem to guarantee stability . The terminal set Y f is designed to grant stability to the MPC policy . W ith these notations, in an attack-free scenario the MPC optimization problem being solved at time k is min y N +1 | k , u N | k ` N ( y N +1 | k , u N | k ) (3a) subject to: x j +1 | k = f ( x j | k , u j | k ) , x 0 | k = x k y k = x k y j | k ∈ Y , j ∈ [1 , N ] u j | k ∈ U , j ∈ [0 , N − 1] y N | k ∈ Y f . (3b) Denoting the minimizer of optimization problem (3) with 3 ( y ∗ 1 | k , . . . , y ∗ N | k , u ∗ 0 | k , . . . , u ∗ N − 1 | k ) , the MPC control law is u k = u ∗ 0 | k , meaning that only the first element of the optimal control signal is applied to the system. The formulated MPC problem (3) is for an attack-free scenario, i.e. u a k = y a k = 0 , ∀ k ∈ N > 0 . In the next section, we propose a modified MPC problem along with a detection criterion which is able to detect possible attacks on system (1). I I I . A T T AC K D E T E C T I O N A L G O R I T H M W e first discuss the class of attacks considered in this paper , and then present the modified MPC controller and, finally the detection procedure. Here, we specifically con- sider the class of False Data Injection Attacks (FDI). In an FDI attack, an attacker augments control and measurement signals with his/her desired arbitrary data by manipulating u a k and y a k . Re garding the FDI attack we make the follo wing assumption. Assumption 1: The attacker can modify control and mea- surement signals by injecting its desired signals u a k , y a k ; howe ver , it cannot access both control and measurement channels at the same time, i.e. @ k : ( u a k 6 = 0)&( y a k 6 = 0) . Assumption 1 is important because if the attacker has access to the model of the system and is able to modify both control and measurement signals, he/she can design attack signals u a k and y a k such that the attack remains covert, see [19] for further details. A. Modified MPC Algorithm Attack detection algorithms reported in the literature are usually independent from the controller design process. T yp- ically , the controller is designed first, and subsequently the detection algorithm is formulated. In this paper, howe ver , we take a nov el approach by co-designing the detection algorithm and the controller . T o this end, at each time k we consider a future reference trajectory ˜ y j | k , j ∈ [1 , N ] . This constitutes a key ingredient of our approach, and is formally defined later . Next, we add an extra constraint to the MPC optimization requiring the actual output trajectory y j | k , j ∈ [1 , N ] to remain within a specified time-inv ariant neighborhoods of the reference trajectory y j | k ∈ ˜ y j | k ⊕ E , j ∈ [1 , N ] . (4) Therefore, the modified MPC problem to be solved at each time k reads as min y N +1 | k , u N | k ` N ( y N +1 | k , u N | k ) (5a) subject to: x j +1 | k = f ( x j | k , u j | k + a j + k ) , x 0 | k = x k y j | k ∈ Y , j ∈ [1 , N ] y j | k ∈ ˜ y j | k ⊕ E , j ∈ [1 , N ] u j | k ∈ U , j ∈ [0 , N − 1] y N | k ∈ Y f . (5b) The motiv ation behind forcing the real-time output to re- main within some time-in variant neighborhood of a reference trajectory originates from the distributed model predictiv e control literature, and in particular , [5]. In [5] authors con- sider a distributed scenario where states and control inputs of each node of the network af fects the neighboring nodes. Specifically , each node of the network enforces its real-time trajectory to stay within some time-in variant neighborhood of a reference trajectory . Nodes of the network receiv e the predicted state and control input of their neighbors and solve their local MPC problem by relying on the predicted trajectories. Solution of the optimization problem defined in (5), i.e. ( y ∗ 1 | k , . . . , y ∗ N | k , u ∗ 0 | k , . . . , u ∗ N − 1 | k ) , inv olves pre- dicted outputs ( y ∗ 1 | k , . . . , y ∗ N | k ) . This information can be used as the predicted reference trajectory ˜ y j | k . In fact, the refer- ence trajectory at time k + N , ˜ y k + N is the N th component of the predicted output trajectory provided as the minimizer of the MPC problem (5) at time k , y ∗ k + N | k ˜ y k + N = y ∗ k + N | k . Therefore, by solving the MPC optimization (5), we gradu- ally construct the reference trajectory . The set E defines the closeness of the actual trajectory to the future reference trajectory . Requiring the two trajectories to be very close may result in a conserv ative control strat- egy with poor performance. There is therefore trade-of f in selecting the set E . Selecting a very small E compromises the performance of the MPC control strate gy while very large E leads to poor security . B. Anomaly Detector Anomaly detectors construct a series of residuals based on which they decide on the occurrence of an attack on dynamical systems. In observer-based anomaly detectors, the residual is the difference between the actual states (or outputs) and the estimated ones. In this paper, on the contrary , we use as residual the dif ference between real- time output y k and the reference output trajectory ˜ y k . T wo types of detector are usually adopted in the literature: i) stateless, and ii) stateful. In a stateless test, if the residual r k . = k y k − ˜ y k k exceeds some threshold γ , an attack is declared. Contrary , in a stateful test, which is a statistical test, a new statistic S k is constructed, which keeps track of the residuals. There are a number of stateful anomaly detectors in the literature, such as simple averaging ov er a time window , exponential weighted moving a verage and, non-parametric cumulativ e sum known as CUSUM. In this paper , we adopt CUSUM statistic due to its popularity and effecti veness. The CUSUM statistic S k is defined recursiv ely as S 0 = 0 and S k +1 = max(0 , S k + r k − δ ) , where δ is chosen such that it pre vents the CUSUM statistic to grow constantly in an attack-free scenario. An attack is declared if S k exceeds the threshold γ . Then, the CUSUM statistic is restarted, i.e. S k +1 = 0 . The threshold γ is usually selected by performing extensi ve simulations. In fact, a small threshold may result in frequent false positiv es while a large v alue of γ can lead to a detecting mechanism ignoring attacks. The control and attack detection algorithm is reported in Algorithm 1. At each sampling time, we first receiv e the actual measurement y k from the plant and construct the 4 Algorithm 1 Control and Anomaly Detection Algorithm 1: Input: f , N , E , γ , δ, y 0 2: Output: attack Initialization: 3: Construct a feasible reference trajectory ˜ y 1 | 0 , . . . , ˜ y N | 0 and set k = 0 , attack = 0 , S 0 = 0 Evolution: 4: while attack == 0 do 5: Receiv e y k from the plant 6: S k +1 = max(0 , S k + k y k − ˜ y k k − δ ) 7: if S k +1 > γ then 8: Set attack = 1 9: retur n attack 10: end if 11: Solve the modified MPC problem (5) 12: Set ˜ y k + N = y ∗ k + N | k 13: Set u k = u ∗ 0 | k and transmit u k to the plant 14: end while CUSUM statistic S k +1 . If S k +1 exceeds a carefully chosen threshold γ , an attack is declared. Next, the modified MPC problem (5) is solved, the reference trajectory is constructed ˜ y k + N = y ∗ k + N | k and, the control signal u k = u ∗ 0 | k is transmitted and applied to the plant. I V . N U M E R I C A L S I M U L AT I O N S W e ran extensiv e simulations to check the effecti veness of the presented approach. In particular , we tested the algorithm on a nonlinear system re garding level control of tw o coupled tank systems. A. Level Contr ol of Coupled T anks The schematic diagram of this system is shown in Fig. 1. The fluid is pumped form a reservoir into the top tank. There is an opening at the bottom of the tank which allo ws the drainage of the fluid to the second tank. Similarly , due to the opening in the second tank, the fluid returns back into the reserv oir . The goal is to control the fluid level in both tanks by manipulating the pump that connects the reservoir and T ank 1. The system dynamics can be computed using the conserv ation of mass and Bernoulli’ s equation dh 1 dt = c 1 ρA 1 u − c 2 ρA 1 p h 1 , (6) dh 2 dt = c 2 ρA 2 p h 1 − c 2 ρA 2 p h 2 , where h = [ h 1 , h 2 ] T is the state vector containing the level of liquid in the first and second tank respecti vely , ρ is the density of the fluid, A 1 , A 2 are the cross-sectional area of tanks 1 and 2 respectiv ely , c 1 , c 2 are coef ficients related to the tanks opening, and, u is the pump rate. There are a number of ways to discretize the continuous model (6). Here, we use the first-order forward Euler approximation to construct a discrete-time model. T o this end, selecting a ℎ " ℎ # Reservoir T ank 1 T ank 2 Control ler & Atta ck Detector 𝑢 Fig. 1. Schematic diagram of the two coupled tanks system. The exchange of information between sensors/controller and controller/actuator are subject to false data injection attack. Lev els of the two tanks are sensed and transmitted to the controller using level transmitters. The control signal is computed in the controller and then transmitted to the flow control valve to regulate the flow of liquid. desired sampling time T , the discretized model is h 1 ( k + 1) = h 1 ( k ) + T α 1 u ( k ) − α 2 p h 1 ( k ) , (7) h 2 ( k + 1) = h 2 ( k ) + T α 2 p h 1 ( k ) − p h 2 ( k ) , where—assuming identical tanks— α 1 = 1 . 75 and α 2 = 0 . 1544 . W e remark that more sophisticated discretization method such as Runge–Kutta can be used which results in a more complex discrete dynamics and consequently a more complex MPC optimization problem, see [8, Chapter 11]. The objectiv e is to design an MPC controller to control the lev el of tank 2 at 0 . 95 . The saturation level of flow control valv e is set to 1 which means the following constraint on the control signal should hold all the time 0 ≤ u ( k ) ≤ 1 , ∀ k ∈ N > 0 . In order to prevent any overflo w in both tanks, we require the fluid level h ( k ) to remain below 1 . Hence, the follo wing state constraint should be respected all the time 0 0 ≤ h ( k ) ≤ 1 1 , ∀ k ∈ N > 0 . The MPC framew ork formulated in Section II is for regu- lation problems. T o consider a tracking problem, the cost needs to be modified as ` N ( h N +1 | k , u N | k ) = N − 1 X j =0 ( h j | k − ¯ h j | k ) T Q ( h j | k − ¯ h j | k )+ u T j | k Ru j | k + V N ( h k + N ) , 5 0 10 20 30 40 50 60 70 Time (sec) 0 0.2 0.4 0.6 0.8 1 Liquid Levels 0 10 20 30 40 50 60 70 Time (sec) 0 0.2 0.4 0.6 0.8 1 1.2 Liquid Levels Attack Fig. 2. Scenario in which the reading form the level sensor reporting liquid level in T ank 1 is compromised starting from time t = 50 sec. The top figure shows both the actual, as well as the deceived liquid levels in T ank 1. The bottom figure presents the liquid level at T ank 2. A simple false data injection attack causes both tanks to o verflo w . where ¯ h j | k is a reference signal that output h j | k has to follo w . The constraint (4) in this example is chosen to be k h j | k − ˜ h j | k k 2 < 0 . 01 , j ∈ [1 , N ] . (8) In fact, the real-time trajectory at time k is required to remain in an ` 2 -ball of radius 0 . 01 centered at the the reference trajectory at time k . Other measures such as the infinity norm can also be used. The non-conv ex MPC optimization problem is formulated in Y ALMIP [11] and solved using the interior point algorithm embedded in the fmincon solver [21]. W e first consider data injection attack on sensors. In particular , we assume that attacker has access to the level sensor installed at T ank 1. W e assume that the attacker’ s goal is to decei ve the controller to inject too much fluid in the two tanks causing them to overflo w . T o this end, the attacker can subtract a positive v alue from the sensor reading to encourage the controller injecting more fluid into the system leading to an overflo w . T o show that if no detection mechanism is used, the attacker can easily lead the system to an unsafe region, we consider an FDI attack shown in Fig. 2. Assuming that both tanks are empty at time k = 0 , i.e. h 1 (0) = h 2 (0) = 0 , the objecti ve of MPC controller is to fill T ank 2 and keep its liquid lev el at 0 . 8 . W e remark that at this stage the proximity constraint (8) is not incorporated in the MPC optimization problem. The attacker starts sending f alse data at time k = 500 —corresponding to t = 50 sec—which deceiv es the controller forcing it to inject more fluid into the system and e ventually causes both tanks to overflo w . This simple scenario rev eals that the system without a detection mechanism is vulnerable to FDI attacks. T o sho w the effecti veness of the proposed approach, we add the proximity constraint (8) to the MPC optimization problem and use the anomaly detector reported in Section III to detect the attack. In particular , we use the CUSUM 0 10 20 30 40 50 60 70 Time (sec) 0 0.2 0.4 0.6 0.8 1 Liquid Levels 0 10 20 30 40 50 60 70 Time (sec) 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 Detection Metric 0 10 20 30 40 50 60 0 0.005 0.01 Attack Detected Fig. 3. Scenario in which the reading from the level sensor reporting liquid level in T ank 1 is compromised starting from time t = 50 sec. The top figure shows the actual level of both tanks. The bottom figure shows the residual k y ( k ) − ˜ y ( k ) k 2 as well as CUSUM statistic. Once the CUSUM statistic exceeds 0 . 1 , the attack is detected in the system. The inset shows a zoomed-in vie w of both residuals and CUSUM from t = 0 to t = 5 . 6 sec. It is clear that the residual does not exceed γ = 0 . 01 meaning that constraint (8) is respected in the absence of attack. anomaly detector S 0 = 0 , S k +1 = max(0 , S k + k y ( k ) − ˜ y ( k ) k 2 − 0 . 01) , where y k is the (decei ved) sensors measurement at time k and ˜ y k is the predicted value of the le vels at time k . Figure 3 shows both residual k y ( k ) − ˜ y ( k ) k 2 as well as CUSUM statistic. W e remark that the same FDI attack scenario as the one reported in Fig. 2 is used to ev aluate the effecti veness of the detection mechanism. The detection threshold—the parameter γ in Algorithm 1—is selected to be 0 . 1 . As it can be seen from the inset in Fig. 3, the residual k y ( k ) − ˜ y ( k ) k 2 remains bello w 0 . 01 meaning that the proximity constraint (8) is respected in the absence of any attack. Starting from t = 50 sec, the residual starts to increase resulting in an increase in the CUSUM statistic. At t = 5 . 92 sec, the CUSUM statistic e xceeds 0 . 1 and the FDI attack is detected. Any sensor measurement inevitably carries some noise. T o see the effect of noise on the performance of the proposed detection mechanism, we add a white Gaussian noise with zero mean and 0 . 002 standard de viation to the sensor mea- surement from both T anks 1 and 2. The simulation reported in Fig. 4 shows that the presence of noise does not hav e a negati ve ef fect on the performance, hence confirming the robustness to noise of the proposed approach. W e next consider an FDI attack on the control input u . A simulation reporting an attack on the control signal is shown in Fig. 5. The attacker compromises the control signal applied to the system and augment the actual control signal u ( k ) with an attack signal u a ( k ) —sho wn in the bottom graph in Fig. 5. W e remark that a smaller attack signal cannot bring the system to an unsafe region and hence is automatically rejected using the MPC controller . Specifically , if the attack signal on the control input is small, the MPC controller is 6 0 10 20 30 40 50 60 70 Time (sec) 0 0.2 0.4 0.6 0.8 1 Liquid Levels 0 10 20 30 40 50 60 70 Time (sec) 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 Detection Metric 0 10 20 30 40 50 60 0 0.005 0.01 0.015 0.02 Attack Detected Fig. 4. Same scenario as the one in Fig. 3, but in the presence of added white Gaussian noise. The performance of the controller/detector is not affected by noise. 0 10 20 30 40 50 60 70 80 Time (sec) 0 0.5 1 Liquid Levels 0 10 20 30 40 50 60 70 80 Time (sec) 0 2 4 6 Detection Metric 0 10 20 30 40 50 60 70 80 Time (sec) 0 0.2 0.4 0.6 Attack Signal 0 10 20 30 40 50 60 70 0 0.1 0.2 Attack Detected Fig. 5. Scenario in which the control input signal is compromised. In particular , the actual control signal u ( k ) is replaced with u ( k ) + u a ( k ) where u a ( k ) is the attack signal showed in the bottom graph. The attack signal is started at t = 50 sec and detected at t = 6 . 9 sec. able to reject it by manipulating its designed control signal u ( k ) and hence the attack signal will not hav e an adverse effect on the performance of the controlled system. V . C O N C L U S I O N An approach to co-design a controller controlling the system and an attack detector to detect false data injection attacks in control inputs and measurements is reported in this paper . In a model predictiv e controller framework, we consider a nonlinear system and require the future trajectory of the outputs to remain in some time-in v ariant neighborhood of a reference trajectory . Deviation of the real-time trajectory form the reference trajectory—at any point in time—is con- sidered as a residual and used in a non-parametric cumulati ve sum (CUSUM) anomaly detector to detect attacks. Future research considers extending the proposed ap- proach to distributed industrial control systems. R E F E R E N C E S [1] C. Bai and V . Gupta. On kalman filtering in the presence of a compromised sensor: Fundamental performance bounds. In 2014 American Contr ol Confer ence , pages 3029–3034, 2014. [2] A. Barboni, F . Boem, and T . Parisini. Model-based detection of cyber -attacks in networked MPC-based control systems. In 10th IF AC Symposium on F ault Detection, Supervision and Safety for T echnical Pr ocesses SAFEPR OCESS 2018 , pages 963 – 968, 2018. [3] A. Cardenas. Cyber-physical systems security knowledge area. In The Cyber Security Body Of Knowledge (cybok) . 2019. [4] D. Ding, Q.L. Han, Y . Xiang, X. Ge, and X.M. Zhang. A surve y on security control and attack detection for industrial c yber-physical systems. Neurocomputing , 275:1674–1683, January 2018. [5] M. Farina and R. Scattolini. Distributed predictive control: a non- cooperativ e algorithm with neighbor-to-neighbor communication for linear systems. Automatica , 48(6):1088–1096, 2012. [6] J. Giraldo, E. Sarkar, A. A. Cardenas, M. Maniatakos, and M. Kantar- cioglu. Security and Priv acy in Cyber-Physical Systems: A Surve y of Surveys. IEEE Design T est , 34(4):7–17, 2017. [7] J. Giraldo, D. Urbina, A. Cardenas, J. V alente, M. Faisal, J. Ruths, N.O. Tippenhauer , H. Sandberg, and R. Candell. A Survey of Physics- Based Attack Detection in Cyber-Physical Systems. ACM Comput. Surv . , 51(4):76:1–76:36, 2018. [8] Lars Gr ¨ une and J ¨ urgen Pannek. Nonlinear model predicti ve control. In Nonlinear Model Predictive Contr ol , pages 45–69. Springer , 2017. [9] H. He and J. Y an. Cyber-physical attacks and defences in the smart grid: a survey . IET Cyber-Physical Systems: Theory & Applications , 1(1):13–27, December 2016. [10] Y . Liu, P . Ning, and M.K. Reiter. False data injection attacks against state estimation in electric power grids. In Pr oceedings of the 16th ACM Conference on Computer and Communications Security , CCS ’09, pages 21–32, New Y ork, NY , USA, 2009. A CM. [11] J. L ¨ ofberg. Y almip : A toolbox for modeling and optimization in matlab . In In Proceedings of the CACSD Confer ence , T aipei, T aiwan, 2004. [12] W . Lucia, B. Sinopoli, and G. Franze. Networked constrained cyber- physical systems subject to malicious attacks: a resilient set-theoretic control approach. In arXiv preprint – , 2016. [13] W . Lucia, B. Sinopoli, and G. Franze. A set-theoretic approach for secure and resilient control of cyber-ph ysical systems subject to false data injection attacks. In 2016 Science of Security for Cyber-Physical Systems W orkshop (SOSCYPS) , pages 1–5, 2016. [14] D.Q. Mayne. Model predictive control: Recent de velopments and future promise. Automatica , 50(12):2967–2986, December 2014. [15] Y . Mo, S. W eerakkody , and B. Sinopoli. Physical authentication of control systems: Designing watermarked control inputs to detect counterfeit sensor outputs. IEEE Contr ol Systems Magazine , 35(1):93– 109, Feb 2015. [16] F . Pasqualetti, F . Dorfler, and F . Bullo. Attack detection and identi- fication in cyber -physical systems. IEEE T ransaction on Automatic Contr ol , 58(11):2715–2729, 2013. [17] J.B. Rawlings. Model pr edictive contr ol: Theory and design . [18] A. Rosich, H. V oos, Y . Li, and M. Darouach. A model predictive approach for cyber-attack detection and mitigation in control systems. In 52nd IEEE Conference on Decision and Control , pages 6621–6626, 2013. [19] R.S. Smith. Covert Misappropriation of Networked Control Systems: Presenting a Feedback Structure. IEEE Contr ol Systems , 35(1):82–92, 2015. [20] S. Sridhar , A. Hahn, and M. Govindarasu. Cyber-Physical System Security for the Electric Power Grid. Proceedings of the IEEE , 100(1):210–224, 2012. [21] R.A. W altz, J.L. Morales, J. Nocedal, and D. Orban. An interior algorithm for nonlinear optimization that combines line search and trust region steps. Mathematical Pro gramming , 107(3):391–408, Jul 2006. [22] M. Zhu and S. Martnez. On the performance analysis of resilient networked control systems under replay attacks. IEEE Tr ansactions on Automatic Contr ol , 59(3):804–808, 2014.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment