Robust Stabilization of Resource Limited Networked Control Systems Under Denial-of-Service Attack
In this paper, we consider a class of denial-of-service (DoS) attacks, which aims at overloading the communication channel. On top of the security issue, continuous or periodic transmission of information within feedback loop is necessary for the eff…
Authors: Niladri Sekhar Tripathy, Mohammadreza Chamanbaz, Rol
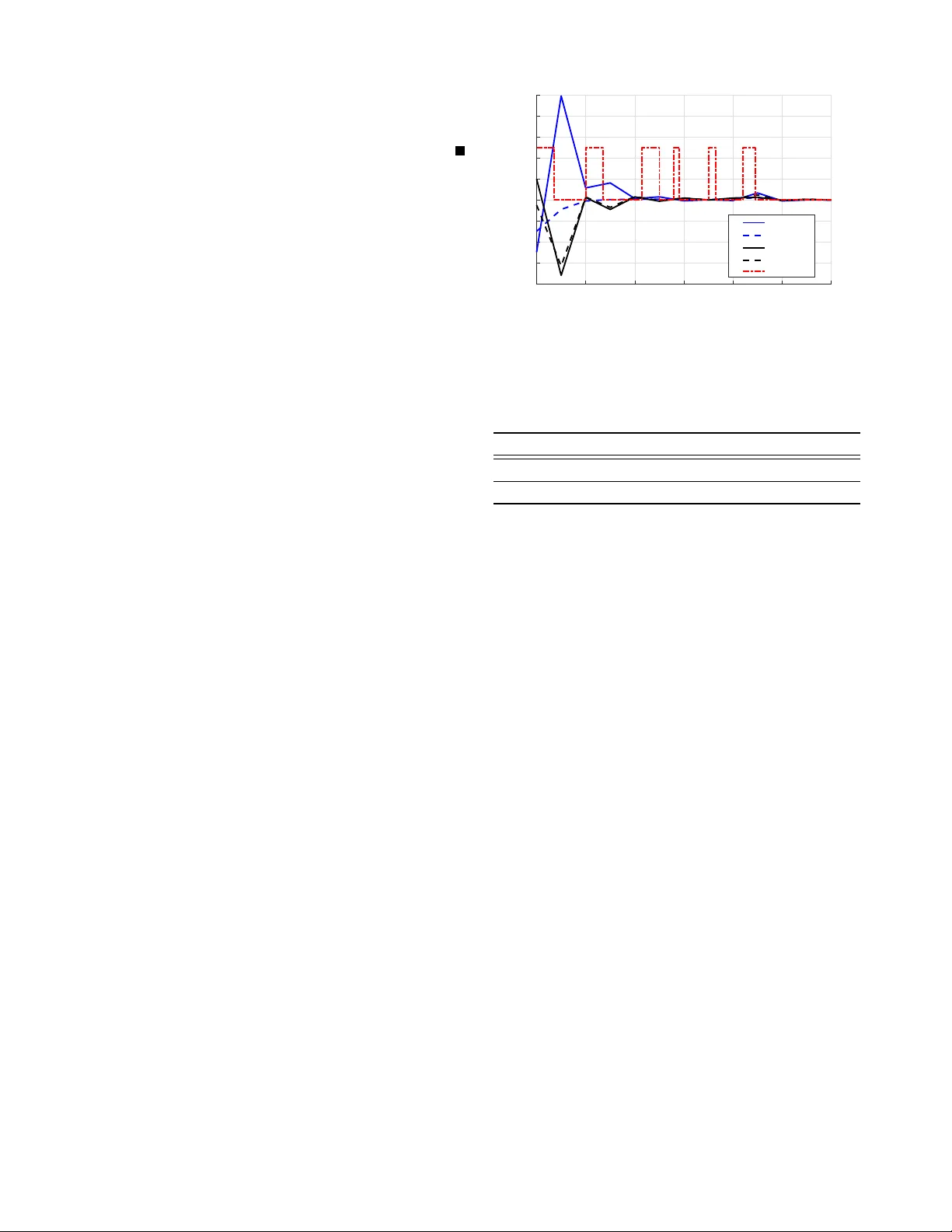
Rob ust Stabilization of Resource Limited Network ed Control Systems Under Denial-of-Service Attack Niladri Sekhar T ripathy , Mohammadreza Chamanbaz and Roland Bouf fanais Abstract — In this paper , we consider a class of denial-of- service (DoS) attacks, which aims at overloading the com- munication channel. On top of the security issue, continuous or periodic transmission of information within feedback loop is necessary for the effective contr ol and stabilization of the system. In addition, uncertainty—originating from v ariation of parameters or unmodeled system dynamics—plays a key role in the system’ s stability . T o address these three critical factors, we solve the joint control and security pr oblem f or an uncertain discrete-time Networked Control System (NCS) subject to lim- ited av ailability of the shared communication channel. An e vent- triggered-based control and communication strategy is adopted to reduce bandwidth consumption. T o tackle the uncertainty in the system dynamics, a robust control law is derived using an optimal control approach based on a virtual nominal dynamics associated with a quadratic cost-functional. The conditions for closed-loop stability and aperiodic transmission rule of feedback information ar e derived using the discrete-time Input-to-State Stability theory . W e show that the proposed control approach withstands a general class of DoS attacks, and the stability analysis rests upon the characteristics of the attack signal. The results are illustrated and validated numerically with a classical NCS batch reactor system. I . I N T RO D U C T I O N The range of applications of Cyber-Physical Systems (CPSs)—e.g. po wer systems, intelligent v ehicles, civil infras- tructure, aerospace, retail supply chains, connected medical devices—has vastly expanded beyond the realm of large- scale public infrastructures. The presence of a communi- cation medium combined with a tight integration of var - ious subsystems make most of these applications safety- critical. Therefore, both CPSs and Networked Control Sys- tems (NCSs) are broadly exposed to cyber -threats and cyber - vulnerabilities which may affect the functionality of physical processes at their core. These critical issues ha ve spurred new lines of research at the interface between cyber-security and control theory [1], [2]. For instance, the effects and containment of cyber -attacks on control systems, which affect the av ailability and integrity of sensor and actuator information ha ve been studied in [3], [4]. Recently , T eixira et. al. [4] described different characteristics of cyber -attacks and defined an attack space to analyze the effect of cyber-attacks Niladri Sekhar T ripathy , Mohammadreza Chamanbaz and Roland Bouff anais are with the Singapore University of T echnology and De- sign, Singapore 487372, e-mail: ( niladri.tripathy, chamanbaz, bouffanais@sutd.edu.sg ) This work was supported in part by the National Research Foundation (NRF), Prime Ministers Office, Singapore, under its National Cybersecurity R&D Programme (A w ard No. NRF2014NCR-NCR001-040) and adminis- tered by the National Cybersecurity R&D Directorate and MOE T ier 1 grant (T1MOE17001). on closed-loop dynamics. Cyber-attacks can be broadly clas- sified into two categories: Denial-of-Service (DoS) attacks and deception attacks [5]. This paper is concerned with DoS attacks and their effects on dynamical systems. DoS attacks primarily af fect the transmission medium within the feedback loop and cause irregular exchanges and losses of information [6], [7]. As this is one of the most reachable attack patterns in the attack space, man y researchers hav e studied its effects both theoretically and experimentally [8]– [11]. Beyond inherent security issues present in NCSs, the exchange of feedback information over the shared commu- nication channel, be it continuous or periodic, consumes a significant portion of the av ailable bandwidth. Recently , it has been shown that significant savings in the bandwidth and communication resources can be achie ved by switching from periodic or continuous sampling to aperiodic sampling [12], [13]. Specifically , ev ent-triggered control strategies have re- vealed drastic reductions in the use of network bandwidth within the feedback loop [14]–[18]. A central problem with classical event-triggered control is the need to have an accu- rate model of the system in order to devise appropriate ev ent- triggering rules. In practice, system modeling inevitably sim- plifies the actual system’ s operations, and thereby introduces a certain le vel of inaccurac y . Recently , T ripathy et al. [17] hav e dev eloped a robust ev ent-triggered control algorithm based on aperiodic feedback so as to deal with the presence of uncertainty . It is worth highlighting that there is a v ast breadth of problems related to the issue of ev ent-triggering control in the presence of DoS attacks, and with model uncertainty in NCSs. In event-triggered control, any new information is exchanged only when the stability criterion is violated, which implicitly assumes that the communication channel is av ailable at the time of event generation. It is clear that any factor or e vent affecting the av ailability of the interconnecting network, such as a DoS attack for instance, has the potential to seriously hinder the underlying physical processes and ov erall operations of the NCS. In light of this, it appears timely to de velop ne w ev ent-triggering control strategies capable of ensuring the stability of the closed loop system subjected to DoS attacks characterized by their frequency and duration, while accounting for uncertainty of the NCS model. In this paper , we propose an attack-resilient event-based robust control algorithm for discrete-time uncertain systems. Norm-bounded mismatched uncertainty is considered for the deriv ation of the robust control results. The primary goal of this work is to analyze the ef fect of DoS attacks on a discrete- time uncertain netw ork controlled system, and to characterize the relationship between frequency and duration of the attack signal and closed-loop stability . The Input-to-State Stability (ISS) theory is applied to deri ve the transmission rule and on/off periods of DoS attack signal. The key contributions of this paper are listed belo w: • W e deri ve and propose a resilient ev ent-based rob ust con- trol law , within the optimal control frame work, that is capable of dealing with both the occurrence of repeated DoS attacks and model uncertainty . • W e establish the upper bound of acceptable duration and frequency of DoS attacks, for which the ISS stability of the uncertain discrete-time systems is guaranteed with ev ent- triggered feedback. • The numerical results obtained with a NCS model for a batch reactor system provide an illustration of the proposed approach and also validate its effecti veness. Notations and Definitions: The Euclidean norm of a v ector x ∈ R n is denoted by k x k . The symbols I denote the identity matrix of appropriate dimension. The maximum (resp. minimum) eigen value of a symmetric matrix P ∈ R n × n is λ max ( P ) (resp. λ min ( P ) ). A continuous function f : R ≥ 0 → R ≥ 0 is said to be class K ∞ if it is strictly increasing, f (0) = 0 and f ( s ) → ∞ as s → ∞ . A function f : R ≥ 0 → R ≥ 0 is a class K function, if it is continuous, strictly increasing and f (0) = 0 . A continuous function β ( r , s ) : R ≥ 0 × R ≥ 0 → R ≥ 0 is a KL function, if it is a class K function with respect to r for a fixed s , and it is strictly decreasing with respect to s when r is fixed [19]. For any given time interval [0 , k ) where k > 1 , T off ( k ) denotes the total duration of DoS attack over [0 , k ) . The ratio T off ( k ) k represents the rate of unav ailability of the communication channel following the DoS attack. The variable N off ( k ) represents the frequenc y of DoS attack in the time interval [0 , k ) i.e. it means that N off ( k ) off-to- on transitions are present in the attack signal during which communication is impossible. The definitions detailed below are used to establish the theoretical results. Definition 1 (Input-to-State Stability [19]): A discrete-time system x ( k + 1) = Ax ( k ) + B u ( k ) , (1) is globally input-to-state stable (ISS) if it satisfies k x ( k ) k ≤ β ( k x (0) k , k ) + γ ( k u ( k ) k ) , (2) for all admissible inputs u ( k ) and for all initial values x (0) , with β a KL function, and γ a K ∞ one. Definition 2 (ISS Lyapunov Function [19]): Assume system (1) is at steady state at the origin, that is f (0 , 0) = 0 , ∀ k > 0 . A positi ve function V ( x ( k )) : R n → R is an Input-to-State L yapunov function for (1) if there exists class K ∞ functions α 1 , α 2 , α 3 and a class K function γ for all x ∈ R n and u ∈ R m satisfying the following conditions α 1 ( k x ( k ) k ) ≤ V ( x ( k )) ≤ α 2 ( k x ( k ) k ) , (3) V ( k + 1) − V ( k ) ≤ − α 3 ( k x ( k ) k ) + γ ( k u ( k ) k ) . (4) Controller Block System Block System Controller Actuator Sensor Event - monitoring uni t ZOH 𝒙(𝒌 𝒊 ) 𝒖(𝒌 𝒊 ) 𝒙(𝒌 𝒊 ) 𝒖(𝒌 𝒊 ) 𝒙 (k ) Comunicating Network Attacker Attacker Attacker Fig. 1. Block diagram of proposed control technique under DoS attack I I . P RO B L E M F O R M U L AT I O N A N D P R E L I M I N A R I E S A. Pr oblem description Consider a linear e vent-triggered system with model un- certainty mathematically represented by x ( k + 1) = A + ∆ A ( p ) x ( k ) + B u ( k i ) , ∀ k ∈ [ k i , k i +1 ) , i ∈ N , (5) u ( k i ) = K x ( k i ) = K { x ( k ) + e ( k ) } , (6) where x ( k ) ∈ R n and u ( k i ) ∈ R m are the system state and input vectors, respectiv ely . The symbol k i in (5) and (6) represents the i -th aperiodic sensing and actuation instant and e ( k ) = x ( k i ) − x ( k ) , ∀ k ∈ [ k i , k i +1 ) . The unknown matrix ∆ A ( p ) ∈ R n × n represents the uncertainty due to the bounded v ariations of the system’ s parameter p and its effects on the nominal system matrix A . The variations of p are bounded by a known and possibly uncountable set Ω . In general, the uncertainty is either matched or mismatched [21]. F or matched system, the uncertainty affects the system’ s dynamics via the input matrix, i.e. ∆ A ( p ) is in the range space of matrix B . This assumption does not hold for mismatched systems. In this paper , the unknown matrix ∆ A ( p ) is mismatched in nature and it is expressed as ∆ A ( p ) = B B + ∆ A ( p ) | {z } matched + ( I − B B + )∆ A ( p ) | {z } mismatched . (7) The matrix B + represents the left-pseudo in verse of input matrix B , i.e. B + = ( B T B ) − 1 B T . The unknown state perturbation matrix ∆ A ( p ) is bounded by a kno wn matrix F which is defined as ∆ A ( p ) T ∆ A ( p ) ≤ F 2 , (8) where the scalar is a design parameter . The block diagram of the proposed controlled system is shown in Fig. 1. According to (5), the control and sensing actions are ex ecuted at each ev ent-triggering instant k i . Howe ver , when DoS interruptions affect the communication medium, the control and sensing actions are pre vented from being executed. For simplicity , in this paper we assume that DoS attack equally affects the control and measurement channels. As expected, in the presence of DoS attacks, the data cannot be transmitted to or received from the communication channel. Problem Statement: Design robust ev ent-triggered state feedback control la w (6) that stabilizes system (5) in the presence of DoS attacks and mismatched uncertainty (7). Proposed Solution: A two-step solution to this control problem is proposed. First, a robust controller is designed to handle uncertainty and then, a transmission rule for sensing and actuation is deri ved to tackle DoS effects and limited av ailability of communication channel. T o derive the robust controller gain, an emulation-based approach is adopted from [17]. That means, the controller is designed excluding the influence of the network, and then some conditions are deriv ed to deal with netw ork constraints. In [17], Tripathy et. al. deri ved the robust controller gain matrices within the optimal control framework, which is discussed next. B. Optimal Contr ol Appr oach for Robust Contr oller Design The optimal control solution for a virtual system x ( k + 1) = Ax ( k ) + B u ( k ) + α ( I − B B + ) v ( k ) , (9) which minimizes a modified cost function J ( k ) = 1 2 ∞ X k =0 x ( k ) T ( Q + F ) x ( k ) + u ( k ) T R 1 u ( k ) + v ( k ) T R 2 v ( k ) , (10) is robust for the original systems (5) in the presence of uncertainty defined in (7). Here, α is a scalar and Q ≥ 0 , R 1 > 0 , R 2 > 0 are matrices. The system (9) has two control inputs u and v , which are denoted as stabilizing and virtual inputs respecti vely . The importance of virtual input v is discussed in Remark 1. T o design the robust controller gains for (5), the optimal control problem for (9) and (10) is solved adopting the method proposed in [17], [22] and results are presented as a Lemma belo w . Lemma 1: Suppose there exist a scalar > 0 and positiv e definite solution P > 0 of the follo wing Riccati equation A T P − 1 + B R − 1 1 B T + α 2 ( I − B B + ) R − 1 2 ( I − B B + ) T − 1 A − P + Q + F = 0 , (11) and ( − 1 I − P ) > 0 . (12) If the optimal control inputs u = K x and v = Lx for (9) and (10) are selected as K = − R − 1 1 B T P − 1 + B R − 1 1 B T + α 2 ( I − B B + ) R − 1 2 ( I − B B + ) T − 1 A, (13) L = − αR − 1 2 ( I − B B + ) T P − 1 + B T R − 1 1 B + α 2 ( I − B B + ) R − 1 2 ( I − B B + ) T − 1 A, (14) where the gain matrices K and L satisfy the following matrix inequality Q 1 = ( Q + K T R 1 K + L T R 2 L + M T P − 1 M ) − A T c P − 1 − I − 1 A c > 0 , (15) with A c = A + B K and M = { P − 1 + B R − 1 1 B T + α 2 ( I − B B + ) R − 1 2 ( I − B B + ) T } − 1 A, (16) then, the matrix K is the rob ust controller gain for (5). The detailed proof of Lemma 1 can be found in [17]. In the next section, the gain matrices K and L are used to derive the transmission instant. Remark 1: The virtual system (9) has two control inputs u = K x and v = Lx . The virtual input v is used for handling the mismatched uncertainty e ven though v is not used directly to stabilize the uncertain system (5). Ho wever , v indirectly helps to design the rob ust controller gain K by satisfying the inequality (15). I I I . M A I N R E S U LT S In this section, we consider a class of DoS attacks and present an event-triggering rule robustly stabilizing the closed loop system in the presence of model uncertainty and DoS attack. In particular , we assume that the DoS attack holds the following assumptions. Assumption 1: [DoS attack rate] There exist scalars η 1 , c 1 , c 2 ∈ R such that T off ( k ) k ≤ 2 ln( η 1 ) − ln( c 1 ) ln( c 2 ) − ln( c 1 ) , ∀ k > 1 . (17) where c 1 < η 1 < 1 and c 2 > 1 . Assumption 2: [DoS frequency] Let T a be the av erage time between two consecutiv e attacks and suppose scalar η 2 satisfies 1 > η 2 > η 1 . Then, the frequency of DoS attack for an interv al [0 , k ) is upper bounded by N off ( k ) k ≤ T a , (18) where T a = 2(ln( η 2 ) − ln( η 1 )) ln( λ max ( P ) /λ min ( P )) . Assumptions 1 and 2 imply some restrictions on the nature of the DoS attack in terms of duration and frequency of attack. For the sake of the analysis, we limit our study to the class of DoS signals satisfying both Assumptions 1 and 2. Owing to the occurrence of DoS attack disrupting the communication channel, the transmission of information at time instant k i may be influenced. T o pro ve the stability of the closed-loop system (5) and to design an event-triggering rule that can withstand model uncertainty in the presence of DoS attacks, the following two cases are considered. First, we establish the stability results and deri ve an event-triggering condition in the absence of any DoS attack. Second, to circumvent the DoS-related effects, we deri ve some conditions that the attack signal must satisfy for our event-triggering approach to be ef fecti ve. Before stating the main theorem, the following two lemmas adopted from [17], [20] are introduced which are instrumental to prov e the main results. Lemma 2: Suppose there exists a positiv e definite solution P > 0 of (11) and a scalar > 0 . Then if ( − 1 I − P ) > 0 , the follo wing holds ˆ X T P ˆ W + ˆ W T P ˆ X + ˆ W T P ˆ W ≤ ˆ X T ( − 1 I − P ) − 1 ˆ X + − 1 ˆ W T ˆ W , (19) where ˆ X and ˆ W are two matrices with appropriate dimen- sions. Lemma 3: Let P > 0 be a solution of (11) and the gain matrices K and L be computed using (13) and (14), respectiv ely . Using (13) and (14) the following holds A T ( P − 1 + B R − 1 B T + α 2 ( I − B B + ) R − 1 2 ( I − B B + ) T ) − 1 A = K T R 1 K + L T R T 2 L + M T P − 1 M , (20) where matrix M is defined in (16). The main results of this paper are stated in the follo wing theorem. Theor em 1: Suppose there exist scalars σ ∈ (0 , 1) and > 0 which satisfy (8) and (12) and let the controller gain matrices derived from (13) and (14). Consider any DoS signal for which Assumptions 1 & 2 hold. If (15) holds and the control input (6) is actuated based on the follo wing ev ent- triggering sequence k 0 = 0 , k i +1 = inf n k ∈ N | k ≥ k i ∧ ( µ k x k 2 − k e k 2 ) ≤ 0 o , (21) with µ = σ λ 2 min ( Q 1 ) 4 k ( A T c P B K ) k 2 + 2 λ min ( Q 1 ) k K T B T ( P − 1 − I ) B K k , (22) then, the ev ent-triggered control law (6) ensures the ISS of the system (5) in the presence of uncertainty (7) and DoS attacks. The proof of Theorem 1 is divided into two cases dis- cussed belo w . Case 1. No DoS attack has occurr ed: Here, we assume that the communication medium is perfect for data transmission, without any jamming within the channel. Therefore, any attempts in updating the control inputs will be successful. That means, whenev er an event is generated, the transmission of sensor and control information are not interrupted and the control law is actuated immediately . The stability criteria and aperi- odic transmission rule of information in the absence of any DoS attack are reported below for this particular case. Case 2. A DoS attack has occurred: Here, we suppose that the attacker successfully compromises the ef fectiv e- ness of the communication medium, thereby prev enting feedback loops from operating from time to time. If the channel is not av ailable to update the control actions, it may affect the closed-loop stability and sensing and actuation instants. In this case, we study the effect of attacks and model uncertainty in system’ s stability and propose a criterion guaranteeing the stability of the closed-loop system in the presence of DoS attacks satisfying Assumptions 1 and 2. Pr oof: [Proof of Theorem 1] Case 1. Let there exists an ISS L yapunov function V ( k ) = x T P x . Using (5), ∆ V = [ V ( k + 1) − V ( k )] is computed as ∆ V = x T [ A T c P A c + A T c P ∆ A + ∆ A T P A c + ∆ A T P ∆ A ] x + x T A T c P B K e + x T ∆ A T P B K e + e T K T B T P A c x + e T K T B T P ∆ Ax + e T K T B T P B K e − x T P x, where A c = A + B K . The above equality is simplified using Lemma 2 as ∆ V ≤ x T [ A T c ( P + P ( − 1 I − P ) − 1 P ) A c − P +2 − 1 ∆ A T ∆ A ] x + x T A T c P B K e + e T K T B T P A c x + e T K T B T ( P + P ( − 1 I − P ) − 1 P ) B K e. (23) Using matrix inv ersion lemma and solution of Riccati equa- tion from (11), inequality (23) is simplified as ∆ V ≤ x T [ A T c ( P − 1 − I ) − 1 A c − ( Q + F ) − A T ( P − 1 + B R − 1 B T + α 2 ( I − B B + ) R − 1 2 ( I − B B + ) T ) − 1 A + 2 − 1 ∆ A T ∆ A ] x + x T A T c P B K e + e T K T B T P A c x + e T K T B T ( P − 1 − I ) − 1 ) B K e. (24) Using (8) and applying Lemma 3 to (24), we arriv e at ∆ V ≤ x T [ A T c ( P − 1 − I ) − 1 A c − Q − K T R 1 K − L T R 2 L − M T P − 1 M ] x + ψ x T x + 1 ψ k A T c P B K k 2 k e k 2 + e T K T B T ( P − 1 − I ) − 1 ) B K e, where ψ is a positiv e scalar . Furthermore, using (15), we can simplify abov e inequality to ∆ V ≤ − x T Q 1 x + ψ x T x + 1 ψ k A T c P B K k 2 k e k 2 + k K T B T ( P − 1 − I ) − 1 ) B K kk e k 2 . Choosing ψ = λ min ( Q 1 ) 2 , the following is obtained ∆ V ≤ − ξ 1 k x ( k ) k 2 + ξ 2 k e ( k ) k 2 , (25) where matrix Q 1 is defined in (15) and ξ 1 = λ min ( Q 1 ) 2 and ξ 2 = 2( k A T c P B K k 2 λ min ( Q 1 ) + k K T B T ( P − 1 − I ) − 1 B K k . Using Definitions 1 and 2, the inequality (25) ensures the ISS of (5). In the absence of any DoS attack, the e vent-triggering condition (21) is also deriv ed using (25). In fact, the control inputs need to be actuated whenever the condition (21) is violated. The L yapunov function V ( x ) = x T P x satisfies (3) where α 1 ( k x k ) = λ min ( P ) k x k 2 and α 2 ( k x k ) = λ max ( P ) k x k 2 . No w applying the ev ent-triggering condition (21), the bound of ∆ V can be written as ∆ V ( x ) ≤ − ξ 1 λ min ( P ) (1 − σ ) V ( x ) ≤ − λ min ( Q 1 ) 2 λ min ( P ) (1 − σ ) V ( x ) , (26) where σ ∈ (0 , 1) regulates the transmission of information ov er the network. The information exchange ov er the net- work has inv erse relation with the selection of σ . This proves that the closed-loop system (5) is globally asymptotically stable with ev ent-triggered feedback and model uncertainty . Using (26), following yields V ( k + 1) ≤ c 1 V ( k ) (27) where c 1 = (1 − λ min ( Q 1 ) 2 λ min ( P ) (1 − σ )) and is always less than 1 as V ( x ) is decreasing. The following Remark describes the growth of error e in between two consecuti ve e vents. Remark 2: Inequality (26) signifies that the state of the uncertain system (5) will remain bounded. Since the state is bounded, the measurement error e ( k ) is also bounded. Here, the variable e ( k ) e volv es based on the following difference equation e ( k + 1) = x ( k i ) − x ( k + 1) , (28) = ( A + B K + ∆ A ) e ( k ) + ( I − ( A + ∆ A + B K )) x ( k i ) . The matrix ∆ A is also bounded as the condition (8) holds ∀ p ∈ Ω . This proves that the error growth remains bounded in between two consecutiv e events. Case 2: Suppose that a DoS attack occurs in the feedback channel at the instant a i ∈ [0 , k ) , where i ∈ { 0 , . . . , m } represents the i th attack e vent, and this attack lasts for the duration k a i time units. The scalar m represents the number of attacks during [0 , k ) . Now , within this time interv al k a i , if an ev ent is not generated then the requirement of feedback channel is unnecessary and the measurement error will grow according to (28). The problem is more sev ere if any ev ent occurs within k a i time duration. According to (21), a trig- gering e vent occurs only when the stability criterion (25) is violated. Therefore, the una vailability of the communication channel may destabilize the system. The ef fects of this DoS attack on the system’ s stability is considered and analyzed in what follows. W ithin the interval [0 , k ) , some transmission attempts are not successful due to jamming. In other words, for the time duration k − m X i =1 k a i ! , the channel is a vailable for communication and for the remaining time, the channel is unav ailable due to the DoS attack. The duration m X i =1 k a i is represented by T off ( k ) . Then, at a i , the growth of variable e is e ( k ) = x ( k i ( a i ) ) − x ( k ) , (29) where x ( k i ( a i ) ) represents the state of the system at the last successful control update up to a i . At the moment of the attack, the condition (25) holds. That means k e ( a i ) k ≤ √ µ k x ( a i ) k , x ( k i ( a i ) ) − x ( a i ) ≤ √ µ k x ( a i ) k . Using (29), the error e ( k ) can be expressed as k e ( k ) k ≤ (1 + √ µ ) k x ( a i ) k + k x ( k ) k . (30) The inequalities (30) and (25) can be used to compute ∆ V as ∆ V ≤ − ξ 1 k x ( k ) k 2 + ξ 2 ((1 + √ µ ) k x ( a i ) k + k x ( k ) k ) 2 ≤ γ max { V ( x ( k )) , V ( x ( a i )) } , (31) where γ = ξ 2 (1+ µ ) 2 λ min ( P ) . Let us consider the i th attack interval, i.e. ( a i , a i + k a i ) . Using the comparison principle for discrete-time system presented in [23, Proposition 1], for τ ∈ ( a i , a i + k a i ) , (31) reduce to V ( x ( τ )) ≤ c ( τ − k a i ) 2 V ( x ( a i )) , (32) where c 2 = (1 + γ ) > 1 . Now , consider the consecutive time interval without an y DoS attack, i.e. ( a i + k a i , a i +1 ) . Again, using comparison principle, [23, Proposition 1], for τ ∈ ( a i + k a i , a i +1 ) , (27) reduces to V ( x ( τ )) ≤ c ( τ − [ a i +1 − ( a i + k a i )]) 1 V ( x ( a i + k a i )) . (33) Therefore, whenev er DoS signal blocks the communication channel, the system dynamics follo ws (32) and in the absence of DoS signal, it is gov erned by (33). Recalling that the number of off to on transitions of DoS attack within the interval [0 , k ) is N off ( k ) . With these ingredients in mind and combining (32) and (33), we get the following bound on V ( k ) V ( k ) ≤ Ξ N off ( k ) c ( k − T off ( k )) 1 c T off ( k ) 2 V ( x (0)) (34) where Ξ = λ max ( P ) /λ min ( P ) . Now , using (34) and (3), we obtain the following upper bound for the system’ s state k x ( k ) k ≤ Ξ 1+ N off ( k ) 2 c ( k − T off ( k )) 2 1 c T off ( k ) 2 2 k x (0) k . (35) T o ensure the conv ergence of x ( k ) , the following two sub- cases are considered. Ξ = 1 : For a selection of Ξ = 1 , inequality (35) reduces to k x ( k ) k ≤ c ( k − T off ( k )) 2 1 c T off ( k ) 2 2 k x (0) k . Now assume that there exists a scalar 1 > η 1 > c 1 such that c ( k − T off ( k )) 2 1 c T off ( k ) 2 2 ≤ η k 1 . After simplification, the following is obtained T off ( k ) k ≤ 2 ln( η 1 ) − ln( c 1 ) ln( c 2 ) − ln( c 1 ) . (36) Ξ > 1 : For a selection of Ξ > 1 , (35) reduces to k x ( k ) k ≤ Ξ 1+ N off ( k ) 2 η k 1 k x (0) k . (37) Now , assume that there exists a scalar 1 > η 2 > η 1 which simplifies (37) as Ξ 1+ N off ( k ) 2 η k 1 ≤ η k 2 , (38) and thus k x ( k ) k ≤ η k 2 k x (0) k . The inequity (38) is used to deri ve the DoS frequency as N off ( k ) k ≤ 2(ln( η 2 ) − ln( η 1 )) ln(Ξ) = T a , where T a is T a = 2(ln( η 2 ) − ln( η 1 ))) ln(Ξ) , (39) which is defined in Assumption 2. From (35), if Assumptions 1 and 2 hold for the DoS attack signal, which are computed from (39) and (36), then k x ( k ) k in (35) is bounded. This completes the proof. I V . S I M U L A T I O N R E S U LT S This section validates the proposed robust control ap- proach in the presence of DoS attacks with uncertainty in the system’ s dynamics using a numerical example. F or the sake of numerical validation, we consider the classical networked control system corresponding to a batch reactor system [24] with two inputs and two outputs. T o realize a stabilizing control law , the feedback control loop is closed by means of a wireless communication network. The control input is designed to tackle the aperiodic av ailability of feedback information in the presence of mismatched uncertainty . W e deri ve a discrete-time linearized model of a batch reactor system in the form of (5) from a continuous model with a sampling period T = 0 . 05 . The matrices A and B are gi ven by A = 0 . 0690 − 0 . 0100 0 . 3355 − 0 . 2835 − 0 . 0290 − 0 . 2145 0 0 . 0338 0 . 0530 0 . 2135 − 0 . 3325 0 . 2945 0 . 0020 0 . 2135 0 . 0670 0 . 1050] , and B = 0 0 . 2840 0 . 0568 0 . 0568 0 0 − 0 . 1573 0 T . The matrix ∆ A is defined as ∆ A = pI where variable p is the uncertain parameter with variations in the unit interval. T o design the controller gains, the matrices Q = 4 I , R 1 = I , R 2 = I and v ariable = 0 . 01 are selected. The scalar parameter σ is chosen to be 0 . 1 . The simulation is carried out using MA TLAB for a run time of 6 seconds with the initial state x = − 0 . 5 − 0 . 3 0 . 2 − 0 . 05 T . The matrix F = 2 I and scalars η 1 = 0 . 3 and η 2 = 0 . 95 are selected such that the conditions (8), (15), (17) and (18) are satisfied. T o obtain the controller gain matrices K and L , the Riccati equation (11) is solved leading to K = − 0 . 0710 − 0 . 9309 − 0 . 0356 − 0 . 1008 1 . 4597 0 . 1990 1 . 0212 − 0 . 5773 , L = − 0 . 0092 0 . 0057 − 0 . 0053 0 . 0092 − 0 . 0144 0 . 0174 − 0 . 0072 0 . 0215 0 . 0220 − 0 . 0104 0 . 0131 − 0 . 0193 0 . 0007 − 0 . 0166 − 0 . 0016 − 0 . 0142 . Figure 2 shows the con ver gence of the state x in spite of system’ s uncertainty and DoS attack on the communication channel. The attack signal is represented with the red color . The degradation of the system’ s performance following DoS attacks is apparent in Fig. 2. T able I shows the efficac y of the proposed control algorithm. The symbol u total denotes the total number of transmissions of control inputs via the communication network. The quantities τ min and τ max represent the minimum and maximum duration of inter-e vent time respectively . The larger inter-e vent time, the improved 0 1 2 3 4 5 6 Time(sec.) -0.8 -0.6 -0.4 -0.2 0 0.2 0.4 0.6 0.8 1 States and DoS signal x 1 x 2 x 3 x 4 DoS signal Fig. 2. Conver gence of states in the presence of DoS attacks for p = 0 . 5 . T ABLE I C O MPA R IS O N O F E V E N T - T R IG G E RE D V S . P E R I OD I C F E ED BA C K C O N TR OL Control Strategy τ max (sec.) τ min (sec.) u total Periodic feedback control 0 . 05 0 . 05 120 Event-triggered control with DoS 0 . 93 0 . 05 37 savings in communication resources. The lo wer bound of attack duration, total DoS period and frequency are computed as T a = 0 . 1 sec., T off = 1 . 53 sec., N off = 12 . T o generate the DoS signal we hav e used these bounds. V . C O N C L U S I O N In this paper , we in vestigated the robust stabilization of discrete-time mismatched uncertain systems in the presence of DoS attack. The primary contribution of this paper is an explicit characterization of the attack signal, namely DoS duration and frequency under which the mismatched system remains input-to-state stable with e vent-triggered feedback. The aperiodic use of feedback information significantly reduces the communication ov erhead over the transmission network. T o handle the inherent uncertainty in the system’ s model, an optimal control approach based on a rob ust control technique has been considered. The proposed robust control approach translates the robust control problem into an optimal control one for a virtual system with a modified cost-functional. The optimal input for the virtual system is the robust solution for uncertain system. The proposed robust controller also ensures the stability of closed-loop system under a generic class of DoS attacks, for which the attack signal satisfies Assumptions 1 and 2. Beyond its effecti veness in ov ercoming the damaging effects of DoS attacks, the dev eloped e vent-triggered control technique leads to significant savings in the channel bandwidth. The proposed control algorithm is illustrated and validated numerically using the classical NCS batch reactor model. R E F E R E N C E S [1] Y . Mo, T . Kim, K. Brancik, D. Dickinson, H. Lee, A. Perrig, and B. Sinopoli, “Cyber-physical security of a smart grid infrastructure, ” Pr oc. IEEE , vol. 100, no. 1, pp. 195205, 2012. [2] A. C ´ ardenas, S. Amin, and S. Sastry , “Secure control: T owards surviv able cyber-physical systems, ” Int. Conf. Distrib. Comput. Syst. W orkshops , pp. 495-500, 2008. [3] S. Sundaram and C. N. Hadjicostis, “Distributed function calculation via linear iterati ve strategies in the presence of malicious agents, ” IEEE T rans. Autom. Control , vol. 56, no. 7, pp. 14951508, 2010. [4] A. T eixeira, D. Prez, H. Sandberg, and K. H. Johansson, “ Attack models and scenarios for networked control systems, ” in Pr oc. 1st Int. Conf. High Confidence Networked Systems, pp. 5564. 2012. [5] A. T eixeira, D. Prez, H. Sandberg, and K. H. Johansson, “ A secure control framew ork for resource-limited adversaries”, Automatica , vol. 51, pp.135-148, 2015. [6] W . Xu, K. Ma, W . Trappe, and Y . Zhang, “Jamming sensor networks: Attack and defense strategies, ” IEEE Network , vol. 20, no. 3, pp. 4147, 2006. [7] D. Thuente and M. Acharya, “Intelligent jamming in wireless networks with applications to 802.11b and other networks, ” in Proc. 25th IEEE Commun. Soc. Military Commun. Conf. , pp. 1075-1081, 2006. [8] M. Zuba, Z. Shi, Z. Peng, and J. Cui, ”Launching denial-of-service jamming attacks in underwater sensor networks, ” A CM Int. W orkshop on Underwater Networks , DOI: 10.1145/2076569.2076581, 2011. [9] H. Zhang, P . Cheng, L. Shi, J. Chen,“Optimal DoS attack scheduling in wireless networked control system”, IEEE T rans. Contr . Sys. T echn , vol.24, no. 3, pp. 843-852, 2016. [10] H. Zhang, P . Cheng, L. Shi, J. Chen, “Optimal denial-of-service attack scheduling with energy constraint”, IEEE T rans. Autom. Contr ol , vol. 60, no. 11, pp. 3023-3028, 2015. [11] C. D. Persis and P . T esi, “Input-to-State Stabilizing Control Under Denial-of-Service”, IEEE T rans. Autom. Control , vol. 60, no. 11, pp. 2930-2944, 2015. [12] L. Zhang and D. H. V arsakelis, “LQG control under limited commu- nication”, 44th IEEE Conf. on Decision and Control , pp. 185-190, 2005. [13] K. Astrom and B. Bernhardsson, “Comparison of Riemann and Lebesgue sampling for first order stochastic systems”, 41st IEEE Conf. on Decision and Control , pp. 2011-2016, 2002. [14] P . T abuada, “Event-triggered real-time scheduling of stabilizing control tasks”, IEEE T rans. on Autom. Control , vol. 52, no. 9, pp. 1680-1685, 2007. [15] S. Trimpe and R. D’Andrea, “Event-based state estimation with variance-based triggering”, 51st IEEE Conf. on Decision and Control , pp. 6583-6590, 2012. [16] W . P . M. H. Heemels, M. C. F . Donkers, and A. R. T ell,“Periodic ev ent- triggered control for linear systems, ” IEEE T rans. Autom. Contr ol , vol. 58, no. 4, pp. 847861, 2013. [17] N. S. Tripathy , I. N. Kar, and K. Paul, “Stabilization of uncertain discrete-time linear system with limited communication”, IEEE T rans. Autom. Contr ol , vol. 62, no. 9, pp. 4727-4733, 2017. [18] N. S. T ripathy , I. N. Kar , and K. Paul, “ An ev ent-triggered based robust control of robot manipulator”, International Conference on Contr ol Automation Robotics and V ision , pp. 425-430, 2014. [19] H. K. Khalil, Nonlinear Systems , Prentice Hall, 3rd Edition, Ne w Jersey , 2002. [20] G. Garcia, J. Bernussou, and D. Arzelier, “Robust stabilization of discrete- time linear systems with norm-bounded time v arying un- certainty”, Syst. Contr ol Lett. , vol. 22, pp. 327339, 1994. [21] I. R. Petersen, “Structural stabilization of uncertain systems: Necessity of the matching condition”, SIAM J. Contr ol Optim. , vol. 23, no. 2, pp. 286-296, 1985. [22] D. S. Naidu, Optimal Control Systems . CRC press, India, 2009. [23] G. Bitsoris, E. Grav alou, “Comparison principle, positive in variance and constrained regulation of nonlinear systems”, Automatica , vol. 31, no. 2, pp. 217-222, 1995. [24] D. Ne ˇ si ´ c, A. R. T eel, “Input-output stability properties of networked control systems”, IEEE T rans. A utom. Contr ol , vol. 49, no. 10, pp. 1650-1667, 2014.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment