Enhanced IoV Security Network by Using Blockchain Governance Game
This paper deals with the design of the secure network in an Enhanced Internet of Vehicles by using the Blockchain Governance Game (BGG). The BGG is a system model of a stochastic game to find best strategies towards preparation of preventing a netwo…
Authors: Song-Kyoo Kim
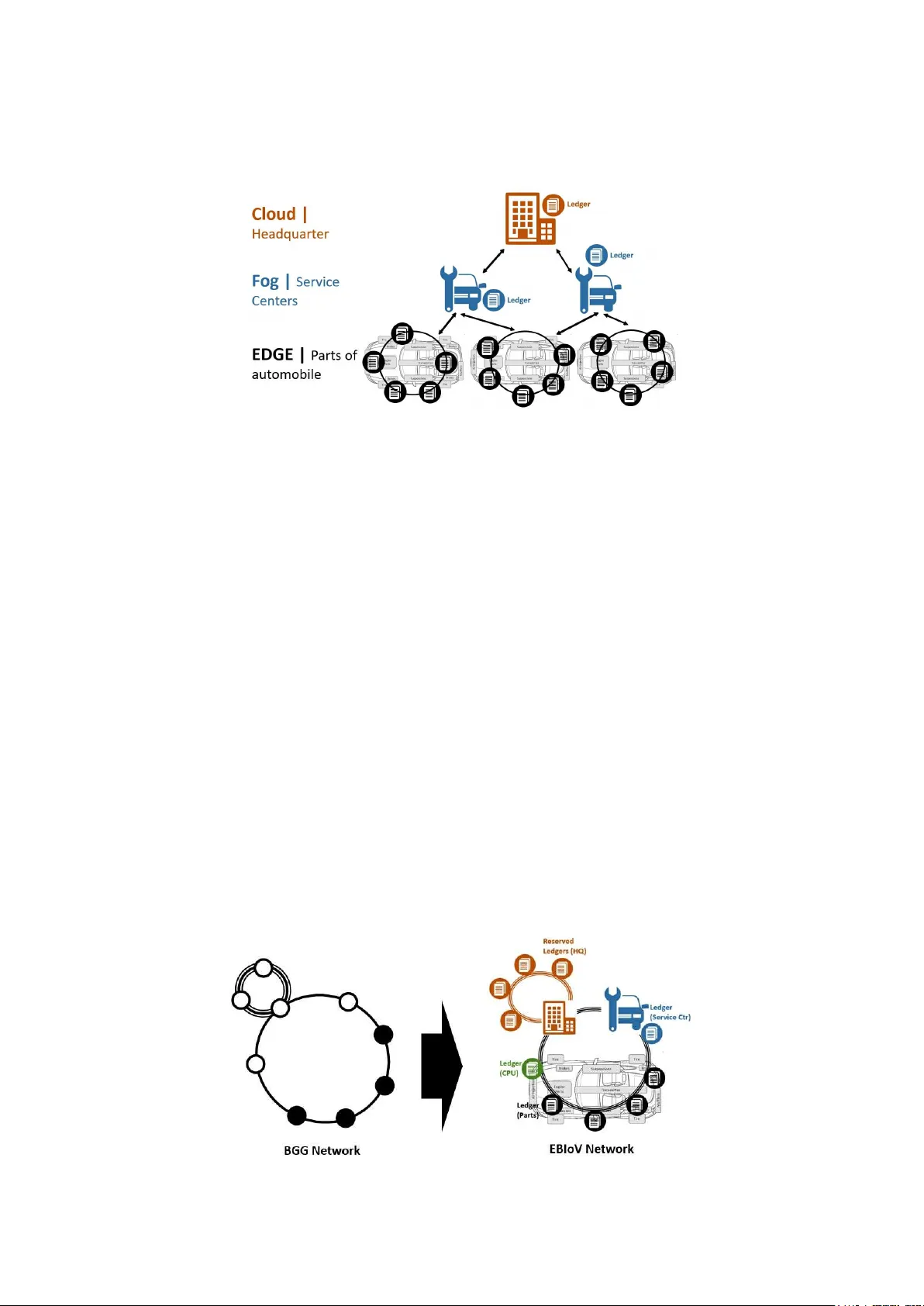
1 Enhanced Io V Security Netwo rk by Using Blockchain Governanc e Gam e * S K K ONG- YOO IM A BSTRACT This paper deals with the design of the secure network in an Enhan ced I nternet of Vehicles by using the Blockchain Gove rnance Game (BGG). The BGG is a system mo del of a stochastic game to find best strategies towards preparation of preventing a network ma lfunction by an attacker and the paper applies this g ame model into the connected vehicle security. Analy tically tractable results for decision-making para meters enable to predict the moment for safety operations and to del iver the optimal combination of the number of reserved nodes wi th the acceptance probability of backup nodes to protect a connected car. This research helps for whom considers the enhanced secure IoV architecture with the BGG within a decentralized network. Keywords: I oT security ; Internet of Vehicles; I oV; connect ed car, Blockchain Governance Game; mix ed game; stochastic model; fluctuation theory ; 51 percent attack I. I NTRODUCTION The Enhanced BI oV (EBIoV) network [1] is emphasized in this paper. The EBI oV is the I oV network architecture based on t he Edge Computi ng [ 2-3] with enabling the Blockchain Governance Game (BGG) [4] for improving the network security [ 1]. Aty pical BI oV could be applied t o trace the provenance of spare parts back through every step in the supply chain to its original manufacture date and l ocation [1, 5]. Car manufacturers concern that service centers and garages are knowingly fitting counterfeit spare parts to their vehicles of customers [2] . Iden tifying geniality of car parts by using the EBI oV has been introduc ed in the previ ous research [6] and it suggests that the network within car components is considered as the Edge network * This pap er is the abrid ged summ ary of the accepted pa per. 2 and the mo nitoring equipment in car servi ce centers are Fog level and the database in the headquarter (HQ) is the level of the cloud network (see Fig.1) [2-3 , 7]. Fig 1. Ado pting Fog Computing in Auto Services in Blockchain [1] This paper provides the mathematical functional of th e EBIoV network architecture for enhancing the securitie s from attackers. The EBIoV security regarding counterfeits of the car parts already has been studied [1] and this research is focused on avoiding aty pical IoV attack in a decentralized ne twork (i.e., the 51 percent attack). In the BGG [4], an attacker and a defender compete each other by buil ding blocks in private and public chains as the sequence of stages to generate ledgers. The his torical strategies and the proba bilistic stage transitions can be observed by both an attacker and a defender. Hence, the intera ction between the attacker and the defender can be modeled as a stochastic game [4, 8]. II. S G F BI V N S TOCHASTIC AME OR O ETWORK ECURITY The Blockchain Governance Game (BGG) [ 4] has been tried to be adapted the BI oV network architecture to defend against the attacks. This sy stem model consists of one attacker (i.e., t he miner which inte nds t o fork a private chain) and one defender (the miner whic h honestly mines on the public chain) [ 8]. This explicit functio n (Theorem BGG-1) from the BGG (Blockchain Governance Game) gives the predicted mo ment one step bef ore the 51 percent attac k [4]. The propose d BI oV network structure is considered and the components in a vehicle, the equipment of a service center and [1] the HQ database are hooked up as one Blockchain (see F ig. 2). Fig 2. Ada pting BGG for the EBI oV architecture [ 1] 3 Each car component bes ide the CPU (smart control ler) generates t he value based on its mechanical action and the genera ted values are sharing with all other components including assigned service centers and a company headquarter. Each numb er from a car component is unique and randomly genera ted. Unlike conventional Blockchain networks, th e EBI oV network does not have any reward sy stem whic h re quires a heavy computational power for being a miner to g enerate ledgers. The Verifiable Random Function (VRF) is applied to select the node for generating ledgers [9] and it is a cry ptographic primitive that maps inputs to verifiable pseudorandom outputs [ 10- 11]. One Blockchain company has pioneered for using th e VRF to pe rform secret cry ptogra phic solut ion t o select committe es to run the consensus protocol [9] . By apply ing the VRF, all nodes will have an equal chance to become a miner for gener ating le dgers without requiring a heavy computati onal power. The mechanism for protecting the Blockch ain is exactly same as the B GG. To apply t he BGG in to the BIoV network structure, the a ntagonistic game of two play ers (called "A" and "H") are introduced to describe the Blockchain network i n a connected car as a defender and an attacker. Both play ers compete to build the blo cks either for honest or false ones. Let ( , , be probabilit y space be independent -subalgebras . This game is a st ochastic process describing the evolution of a conflict between players A and H known to an observation process = The game is ended when on the -th observation epoch , the collateral building blocks to pl ay er H (or A) exce eds more than the ha lf of t he tota l nodes in the regular operation or player A exceeds more than nodes under the safety mode. T o further formalize the gam e, the is exit in dex introduced: inf 1 inf 2 where is th e number of the reserved honest nodes from a headquarter (HQ) which is depends on the availa bility from the HQ. The joint functional of the BI oV network model is as follows: 3 where indicates th e to tal number of nodes (or ledgers) in the BI oV network for each car (see Fig. 2). III. B G G S & LOCKCHAIN OVERNANCE AM E TRATEGY O P PTIMIZATION RACTICE Let us consider a two-person mi xed strategy game, and play er H (i.e., a car company ) is the person who has two strategies at the observation mom ent, one step before 4 attackers complete to generate alternative chains with dishonest transactions. Pla y er H has the following strategies: . Play ers: 4 A . Strategy sets: " " " " NotBurst Burst " " " " Regular Safety Based on the above condi tions, the general cost matrix at the prior time to be burst could be composed as follows: Table 1. Cost matrix NotBurst Burst Regula r Safety where is the probabilit y of bursting blockchain network (i.e., an attacker wins the game) an d it depends on the strateg ic decision of play er H: Regular Safety 5 I t is noted th at the cost for the reserved nodes (i.e., the cost of " " operation Safety strategy by player H) should be sma ller th an t he other strategy . T he tota l number of reserved nodes that a company owns depends on the cost function and the optima l number of reserved nodes which supported by the HQ. Similarly, the optimal value is the success probability when the reserved honest nodes are supported from the HQ. The best combination could be found as follows: inf Reg Safe 6 The governance in the Blo ckchain is followed by the decision ma king parameter and it also means no action until the time . An attacker still has the chance th at all nodes are governed by an attacker if the atta cker catches more than the half of nodes at (i.e., . If the attacker catches the less th an half of all node s at (i.e., , then the defender could run the safety mode to avoid the attack at The total cost for developing the enhanced B IoV network is as follows: 7 Total Safe Reg < where 5 . 8 Recall from (5), the probability of bursting Bloc kchain network (i.e., an attacker wins the game) under the memory less properties becomes the Poisson compound process: Regular Safety 9 where 10 A network security in a BIoV network for each car is considered in this subsection. The strategy for prote cting the EBIoV is for supporting the addit ional node s to give the less chance th at an attacker cat ches blocks with false control requests. Si nce, the model of the BGG in the EBIoV net work has been analy tically solved, the values for the cost function and the ca lculatio ns of the probability distributions are straight forward. However, it sti ll requires the software implementation by using a progra mi ng languag e. Based on th e above conditi ons, the L P (Linear Programing) mo del could be described as follows from (3.7) an d (3.4): Objective minimizing 11 Total Subject to 12 From (7), the total cost is as follows: Total 13 Total The total cost could be min imized by given and the parameter set Total is t he optima l combination of the reserved nodes which are supported by th e HQ. T he below illustration in Fig. 3 is atypical graph of an optimal result by using the BGG based BI oV (E BIoV) net work based on the given conditions in Table I . 6 Fig. 3. Optimization Example for the EBIoV The moment of requesti ng the additi onal nodes will be the tim e when is one step prior than the tim e when an attacker c atches more th an half of the whole blocks (i.e., ). V. C ONCLUSION This paper establishes t he enhanced Blo ckchain ba sed IoV network architecture by bringing a theore tical model in stochastic m odeling. The Enhanced Blockchain enabled I nternet of Vehicles (EBIoV) is an adva nced secure IoT network architecture for protecting a connected car from attackers. This new architecture ha s been desig ned for a decentralized network by adapting the Blockchain Governance Game (BGG) to improve the connected car security . The BGG is a mathematically proven game model to develop opti mal defense strategies to protect systems from attackers. The practical case in the paper demonstrates how an EBIoV network could be implemented for connected car securities. The EBIoV networ k is the first research that applies a BGG model into th e I oV security domain. T he BGG m odel sha ll be ex tended to various Blockchain based cy bersecurity areas including IoT security and secured decentralized service network desig n. R EFERENCES [1] S.-K. Kim, C. Y. Yeun, E. D amiani, Y. Al-Ham madi and N.-W. Lo, New Blockchain Adoptation For Automotive Security by Using Sy stematic Innovation, The 2 019 IE EE Tr ansportation Electrification Conference and E xpo Asia-Pacific, Jej u, South Korea, 8 -10 May, 2019, p p. 1 -4. [2] J. Baker, E dge Computing -- The N ew F ro ntier of the Web, r etrieved from https://hackernoon.com/edge-computing -a-beginners-g uide-8976 b6886 481 , 2017 . [3] ERP INNEW, Fog computing vs edge c omputing, retrieved from https://erpinnew s.com/fog- computing- vs-edge-com puting, 2017 . [4] S. -K. Kim, Bloc kchain Governance Game, Comp. & Indust. Eng. 136 (201 9), pp . 373-38 0 7 [5] M. J ones, Blo ckchain for Autom otive: spar e parts and warranty, retrieved from https://w ww .ibm.com/blogs/internet-of- things/iot-blockchain- automotive-industry /, 20 17. [6] M. Co noscenti and et al., "Bloc kchain for the Internet of Things: A sy stematic literature review", in Proce edings of the 13th IEEE/ACS International Conference o f Com puter Systems and Applications, AICCSA 20 16, IEE E, Agadir, Moro cco, Dec ember 2016. [7] F. B onomi, R. Milito and et a l., Fog computing and its role in the internet of things, Proceed ings of the first edition of the MCC workshop on Mobile c loud computing, Helsinki, Fin land, August 17, pp. 13-16, 2 012. [8] Z. Liu, N. C. Luong and et al., " A Survey on A pplic ations of Game Theory in Blockchain", retrieved fro m h ttps://arxiv.org/ab s/1902.10 865 , 2019 . [9] S. Mi cali, M. Rabin and e t al., " Verifiable rando m fun ctions". Pr ocee dings of the 40th IEEE Sym posium on Foundations of Comput er Scie nce. pp. 1 20-130, 1999. [10] S. Gorbunov, Algorand Releases First Ope n-Source Code: Verifiable Ra ndom Fun ction, re trieved from https://m edium.com/algorand/, 2018. [11] Y. Dodis and A. Yampolskiy, "A Verifiable Random Function w ith Short Pr oofs and Keys", Lecture Notes in Computer Science 338 6, pp. 416-431 , 2005 .
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment