On Compression of Cryptographic Keys
Any secured system can be modeled as a capability-based access control system in which each user is given a set of secret keys of the resources he is granted access to. In some large systems with resource-constrained devices, such as sensor networks …
Authors: Aldar C-F. Chan
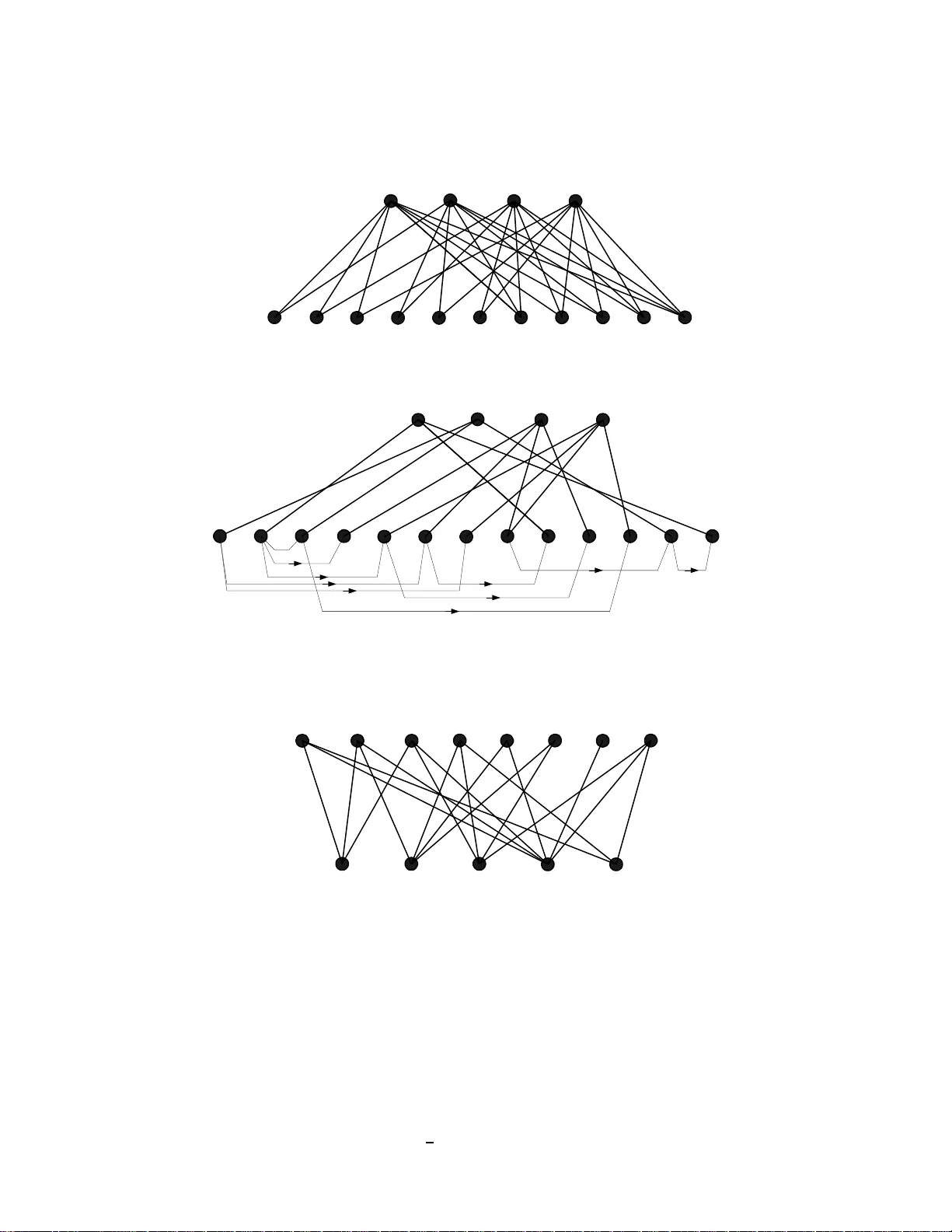
1 On the Compression of Cryptographic Keys Aldar C-F. Chan National Univ ersit y of Singap ore Abstract Any secured system can b e mod eled as a capability-b ased access contro l system in which each u ser is given a set o f secret keys of the resources h e is gra nted access to. In som e large systems with resource -constrained devices, such as sensor networks and RFID systems, the design is sensitiv e to memo ry or key storage co st. W ith a goal to minimize the m aximum users’ key storag e, key compr ession based on key lin king, that is, deriving one ke y from an other without compromising security , is studied. A lower bou nd on key storage neede d for a gen eral access stru cture with key d eriv ation is der iv ed. Th is bou nd demo nstrates the th eoretic limit of any systems which do not trade off secu rity and ca n be tr eated as a negative resu lt to p rovide groun d for designs with security tradeoff. A concr ete, provably secure key linking scheme b ased on pseudor andom fun ctions is gi ven. Using the key lin king framework, a num ber of key pre- distribution schemes in the liter ature are analyze d. I . I N T RO D U C T I O N In any comp uter sys tem o f fering s ecurity-related se rvices, it is a ba sic ne cess ity that its users have access to some priv ate information to give them lev erage over an a dversary . The se secret pieces of information are commonly known a s (cryptographic) keys. The key is usually used as input to p rotocols o r algorithms for identification, secrecy an d authentication purpos es. Nearly all suc h systems can b e modeled as a cap ability-based access system in which eac h resource is assigne d a s ecret key an d a use r granted with a cces s right to the resource would be gi ven its key . For example, in secure grou p co mmunication [3], each co nference g roup is assigned a c onference key which is giv en to all users belong ing to the group so that the communica tion of the group could be kept s ecret and messa ge authen tication c an be achieved within the group. Ideally , the sec urity req uirement of a typica l system (not limited to secu re group c ommuni- cation) is that all users o utside a particular group or no t granted acce ss to a resou rce should not be able to obtain or compu te the key for it even by co llusion. For instance , in se cure g roup communication, it is nece ssary to ensure that all u sers outside a c ertain conferenc e group (whose key is treated as a resou rce key) should not be able to derive the group key from their keys. In most ca ses, the storage ne eded at each u ser could be too large to be practical. For example, in a typica l a ccess control system, if a us er has a high level of privil ege, his device may nee d to store a conside rable number of keys. Since the cost o f the tamper-r esistant storage for the keys increases linearly with the size of the key storage, it is thus worthwhile to study tec hniques to generate all these keys from a smaller seed or comp ress the key materials. There is a similar problem facing eme r ging applications like se nsor n etworks and RFID tags. Desp ite the dropp ing cost o f secu re storag e, key storage is s till a b ig conce rn in these app lications, in volving low cos t embedde d devices which have to store a c onsiderable amount of sec ret keys. C ompressing key materials is ess ential to the s calability o f such designs. T o ens ure co rrectness of the op eration of all cryp tographic algorithms, the key c ompression needs to b e loss less. Besides, to p rotect a reso urce from una uthorized acces s by collusion o f compromised u sers, the key compression should n ot le ak information that ca n e ase un authorized acces s to any res ource key n ot g i ven to the co mpromised use rs. Th is paper studies technique s to create depend ency between res ource keys (to derive one key from anothe r) so as to reduc e the 2 storage requirement on each user device. In other words, we exploit the redunda ncy in privileged group membersh ips for key compress ion. The goal is to minimize the max imum of us er key storage over all users. T o link keys togethe r , we n eed to conside r the access memberships of all the resource s in the system to av oid compromising the secu rity of some resources. 1 W e in vestigate the li mit of this k ey deriv a tion approach by deri ving a bound on maximum compress ion achiev able without compromising the security of any resource key . Due to their simplicity , existing work in the literature suc h as [10], [20], [7] on ly cons iders monotonic acce ss structures. Wherea s, this pa per considers a mu ch more gene ral a ccess s tructure without posing any restrictions on what properties it must have. The results of this paper are general enough to cover most practical application scenarios. Note also that t he applicability of the model we use is not limited to s ymmetric or s hared key systems. For asy mmetric key systems, the model depicts the posse ssion of priv ate keys a nd the resources rep resent all a lgorithms req uiring a priv a te key input. For instanc e, a resource could rep resent the decryp tion a lgorithm of a certain public key cryptosystem and its keys represe nt the requ ired pri v ate keys to a chieve a su ccess ful decryption of a certain ciphertext en crypted using the corresponding pu blic key . The acces s control model we c onsider in this paper co uld cover a wide ran ge of actua l s ystems, inc luding those not designed for acces s c ontrol pu rposes. The con trib ution of this pape r is three-fold. First, we deriv e the lower b ound on key storage needed for a gene ral acce ss structure if key de penden cy is created be tween keys held by a user . This lower bound corresp onds to the theoretical limit on maximum key compression ac hiev a ble in an ide al ac cess structure without key comp romise. W e als o show that this bound is tight b y giving some con crete examp les in se nsor n etwork key pre-distribution, w hich a re either bo und-achieving or close to this bou nd. Second , we g i ve a practical, p rov ably secure key linking sc heme (for a general ac cess structure) ba sed on ps eudorand om functions (PRF). W e also provide a reduction proof of s ecurity for this construction. Third, we demons trate how to apply the ke y linking framew ork to red uce key storage in pairwise key p re-distrib ution sche mes for s ensor ne tworks. W e have to emphas ize that, un like the existing scheme s with key re-use s uch as [14], [6], the resulting key s torage reduction do es not come with a price o f lowering the resilience or s ecurity against c ompromised nodes. 2 The only trade-off is lo wering the security guarantee from the information-theoretic sense to the comp utational-complexity-theoretic s ense (du e to the us e of pseudo random functions ), which in e ssenc e makes n o dif ference in practice. In the next sec tion, we present the d efinitions of ac cess s tructures. In Sections III and V, we present the key storag e lo we r bound a nd the key linking cons truction ba sed o n pseudo- random functions resp ectiv ely . Then we co nsider applying the key linking framework to key pre-distrib ution for sensor networks in Sec tion VI. F inally , we have some discu ssions in Section VII and conc lude in Sec tion VIII. I I . A C C E S S S T RU C T U R E W e use an a ccess co ntrol system to mode l a se curity sys tem; a fairly wide ran ge of ap plications can be covered by this model. The a ccess structure of a typical s ystem d epicts the relations between users and keys/resources . A grap hical presentation is shown in Figure 1. Suppose U = { u 1 , u 2 , . . . , u n } is the s et of u sers and R = { r 1 , r 2 , . . . , r m } the s et of resou rces in a s ystem. Let 2 U be the s et of all subse ts of U a nd den ote the set of a ll possible secret keys 1 The access membership of a resource is the subset of legitimate users granted access ri ght to it. 2 In nearly all of the existing ke y pre-distribution schemes for sensor networks, i n order to lower the key storage requirement, the same k ey is used for links between sev eral pairs of node s. So when a ke y is ex posed to an adv ersary due to a compromised node, all these links will be compromised instead of one, thus lo wering the resilience of the network against compromised nodes. 3 u 1 u 2 u 3 r 1 r 2 r 3 r 4 r 5 r 6 r 7 u 4 Users Resource s Fig. 1. A T ypical Access Structure Graph by K . Each resource r j ∈ R is asso ciated with a key k j ∈ K a nd an ordered pair ( P j , F j ) with P j ⊆ U an d F j ⊂ 2 U ; P j is the subset o f privil eged users gran ted acce ss to r j whereas e ach element in F j correspond s to a forbidden subse t of use rs w hich should not b e able to access r j ev en if all o f them collude. Then the acces s structure of a system has the follo wing definition. Definition 1. The a cces s structure Γ of a secu rity syste m ( U , R , K ) is the follo wing set o f 4-tuples: { ( r j , k j , P j , F j ) : r j ∈ R , k j ∈ K , P j ⊆ U , F j ⊂ 2 U } . In the defi nition o f an acce ss structure, a sys tem is not required to g uard ag ainst a ll illegitimate users ou tside the pri vileged group of a resource from acce ssing it. In practical s cenarios, usu ally , only a bou nded n umber of illegitimate use rs in collus ion could be excluded; there is a trade off of sec urity for storage. Howe ver , this paper co nsiders an ideal acc ess structure w hich is the mos t desired se tting a s raised by Naor et. al. [18 ] in the con text of broadcas t enc ryption. An acc ess structure is idea l if a ll the illegitimate users to any resource in the system are excluded from acces sing it. Definition 2. An acces s structure Γ = { ( r j , k j , P j , F j ) } for a secu rity system ( U , R , K ) is ideal if U \ P j ∈ F j , ∀ r j ∈ R . In a se curity system, the acce ss structure is a ssociated with a key assignme nt sch eme. The set of keys held by a user ma y not be exactly the same as tha t o f the resou rces he c ould acce ss, but should a llo w h im to compu te all the resource keys he ne eds. An ac cess structure graph, whose definition is giv en be low , incorporates a key assign ment to an acce ss structure. Definition 3. Given a set of users U = { u 1 , u 2 , . . . , u n } , a se t of resou rces R = { r 1 , r 2 , . . . , r m } and a set of keys K , a n access structure graph G for the system is a bipa rtite graph with vertex set V ( G ) = U ∪ R and ed ge s et E ( G ) ⊆ U × R , and the following p roperties hold: • ( u i , r j ) ∈ E ( G ) if and only if u i can access r j . • Each resource vertex r j is associated with a pri vileged user subs et P j ⊆ U such that ( u i , r j ) ∈ E ( G ) if a nd o nly if u i ∈ P j . • Each resource vertex r j is assoc iated with a key k j ∈ K . The assoc iated key assignme nt of an access structure grap h is sa id to b e se cure a nd sound if the followi ng ho lds: a user u i can compute the key k j if and on ly if ( u i , r j ) ∈ E ( G ) for all 1 ≤ j ≤ m . Note that existing key pre-distribution s chemes for senso r ne tworks with key re-us e [14], [6] do not satisfy this requ irement o f security and soundn ess. I I I . A K E Y S T O R AG E L O W E R B O U N D W I T H K E Y D E P E N D E N C Y This sec tion uses the a ccess structure graph de fined in Section II to de ri ve a lower boun d on the key storage requiremen t if d epend ency is created be tween keys. 4 In a n acc ess s tructure graph, the degree o f ea ch use r vertex u i is the key storage req uirement at u i assuming the users store the resou rce keys directly and ea ch key has the sa me leng th, wherea s, the degree of eac h resource vertex r j is the number of pri vileged use rs who ca n ac cess it, which is the same as | P j | . Let the key storag e at user u i be d i , the goal is to minimize max u i ∈U { d i } . Usually the res ource keys should be picked independe ntly a t random to e nsure security . Howe ver , for some users, storing multiple keys may be redund ant. For instance, if a p ri vileged group P 1 is the subset of another s ay P 2 , that is, P 1 ⊂ P 2 , then it is red undant for a user in P 1 to store k 2 (the key for P 2 ) in addition to k 1 (the key for P 1 ). If k 2 can be d eri ved from k 1 , then the storage a t each u i ∈ P 1 would be red uced by one key 3 , eq ui valent to removing the edge ( u i , r 2 ) from G an d adding a new edge be tween r 1 and r 2 (the key depe ndency). Note that the resulting graph is no longe r bipa rtite. Gi ven two keys k j and k ′ j for privil eged subse ts P j and P ′ j , if k ′ j is derived from k j , all u sers in P j would have access to k ′ j . As a result, to en sure tha t the key linking doe s not c ompromise security , it is neces sary to make sure that P j \ P ′ j = φ (the emp ty set). In othe r words, P j ⊂ P ′ j if P ′ j 6 = P j . O therwise, a use r not in P ′ j (but in P j ) would have a ccess to k ′ j . S ubject to this constraint, the bes t ac hiev able key storage reduction is giv en by the follo wing the orem. Theorem 1 : If depend ency is created between keys while maintaining the ideal ac cess structure and sec urity of a s ystem, dep ending on the access structure, the be st ac hiev able maximum storage at ea ch use r is at leas t ⌈ m n ⌉ wh ere n is the total numbe r of u sers and m is the total numbe r of resources with distinct acce ss membe rship. Proof. T o maintain the s ecurity and a ccess structure, a key k ′ j can be d eri ved from an other key k j only if P j ⊂ P ′ j and the users in P ′ j \ P j need to s tore k ′ j while users in P j can generate k ′ j from k j . If a key k ′ j can be g enerated from k j , then | P ′ j \ P j | ≥ 1 since P j ⊂ P ′ j (Note that the m resources have distinct acc ess memb ership). That is, at least one us er in P ′ j needs to store k ′ j . In other words, after key linking, each res ource vertex in the a cces s structure graph should h av e at least o ne edge coming from the s et of us er vertices. If we denote the nu mber of ed ges coming from a user vertex to r j by y j ≥ 1 and the degree of a user u i by x i , then n X i =1 x i = m X j =1 y j ≥ m X j =1 1 = m. In the be st case , the degree s of any two users u i and u ′ i should not d if fer by more than 1. Henc e, the maximum user degree max u i ∈U deg ( u i ) ≥ ⌈ m n ⌉ . The result of Theorem 1 d oes not assume any co ncrete construction for crea ting the key depend ency . It is rather general, discussing whether a particular key could be derived f rom another while maintaining security and wh at the best achiev a ble key storage reduction w ould b e. In the be st sc enario, a 1 n reduction factor cou ld be achieved by eliminating all redunda ncy in the pri vileged group memberships of a s ystem. The lower bound in Theorem 1 is also tight as can be seen from the example b elow . Shown in Figure 2 is an examp le for the comp lete secure g roup co mmunication with 4 users. Originally , e ach user has to store 2 4 − 1 − 1 = 7 keys. Note tha t m = 11 a nd n = 4 , a nd hence ⌈ 11 4 ⌉ = 3 . After key linking 4 , the maximum numbe r of keys of a user is 4 > 3 . 3 Such a deri v ation is poss ible if k 2 would not leak out information about k 1 practically . W e show in the next section ho w such a derviation can be instantiated by a pseudorandom function. 4 Note t hat two fi ctitious nodes are added t o achiev e a lower storage; the lower bound stated in Theorem 1 holds here because the only effect of adding these fictiti ous nodes i s t hat t wo resource nodes are added to the original access structure graph, which in essence increases the v alue of m . 5 u 1 u 2 u 3 P 12 P 13 P 14 P 23 P 24 P 34 P 123 u 4 Users Resources P 134 P 124 P 234 P 1234 u 1 u 2 u 3 P 12 P 13 P 14 P 23 P 24 P 34 P 123 u 4 Users Resources P 134 P 124 P 234 P 1234 P 1 P 2 (a ) (b) Fig. 2. The Access Structure Graph of a Complete KPS Scheme (a) before K ey Linking and (b) after Ke y Linking u 1 u 2 u 3 r 1 r 2 r 3 r 4 u 4 Users Resources u 5 u 6 u 7 u 8 r 5 Fig. 3. An Example Access St ructure Graph that K ey Linking cannot lead to a Reduction on the Maximum Ke y Storage per User Clearly , as long as there exist reso urce n odes (in the acc ess s tructure graph) sh aring a non- empty interse ction betwee n their acces s memb ership sets , key linking c ould always be poss ible between them, resulting in storage redu ction at s ome use rs. Howe ver , it is not nec essarily true that max u i ∈U { d i } , the maximum of the key storage per us er (over a ll users), can always be red uced. W e may achieve storage reduction at all us ers but the one with ma ximum storage pa rticularly when the a ccess structure graph is very irregular . For ins tance, shown in Figure 3 is a case where key linking ca nnot lead to a red uction on the maximum of key storage per user (which is originally 3); no matter how key dep endency is created, the maximum key storage per user is still 3 while the lower bound sho uld be ⌈ 5 8 ⌉ = 1 . Whether the lower bound o n the maximum key 6 storage p er use r (as stated in Theorem 1) can b e ach iev ed and whether key linking can red uce the maximum key storage pe r us er d epend s on the acc ess structure. Loosely speaking, if the acc ess structure graph is d ense, it is likely that a reduc tion on the max imum key storag e pe r use r can be achieved through key linking; if the degrees of user nodes are regular (that is, eac h user has acces s to roughly the s ame n umber of resource s), an d the sequ ence o f the degrees o f the resource nodes (in asce nding order) doe s not have a sh arp d if ference be tween two co nsecu ti ve elements (that is, there does not exist a resource node having a con siderably larger ac cess membersh ip set tha n others), key linking is most effecti ve with the resulting ma ximum key storage pe r user closest to the lower bo und. A g eneral key linking algorithm is designed (giv en in the next s ection) to run experiments on dif ferent acces s structure graph s. The res ults a ctually agree with the above obse rvati ons. I V . A N A L G O R I T H M T O FI N D A K E Y L I N K I N G P A T T E R N Depicted below is a g eneral algorithm for finding a key linking p attern for any g i ven ac cess structure graph. This algorithm con verts an acces s structure graph into one with key linking. It runs as follo ws: An algorithm to find a key linking pattern. Input: an acces s structure graph Output: an acces s structure graph with key linking 1) Sort the resource nod es ac cording to the size of their privileged group s and assign an index (0,1 ,2, .....) to eac h nod e ac cordingly . 2) Pick the node with largest index to start with and set it as the cu rrent node. 3) From current nod e, pick a node with the next smaller ind ex an d se t its index a s the find-pointer . 4) Check if the nod e at fin d-pointer is a subse t of the cu rrent no de. a) If ye s, ma rk a link at the find-pointer node to the current node and go to step 5. b) If no, d ecrease the fin d-pointer by 1 and rep eat step 4 if the fin d- pointer is greater than zero, otherwise, go to step 5. 5) Decreas e the current no de index by 1. 6) Repeat 3-5 until the current nod e index is 0. V . A K E Y D E R I V A T I O N S C H E M E B A S E D O N P S E U D O R A N D O M F U N C T I O N S In order to genera te a key k ′ from an other key k , we cou ld conside r k a s a se ed to some ps eu- dorandom gene rator g which outputs k ′ . 5 The requirement of a s uitable gene rator is tha t,without the knowledge of the seed k , to any computationa lly ef ficient algorithm (i.e. polynomial-time), the output of g is indistinguisha ble from any random numb er picked uniformly from the key s pace. This would ensure that the view to anyone (co mputationally bounded and without the knowledge of the s eed) is a lmost ide ntical to that without key linking, thus guaranteeing that nob ody could lea rn any information abou t the s eed key from the ge nerated keys. This c omputational indistinguishability requirement is es sential to ens uring the sec urity of the whole system. Th e 5 The output space of g should be the same as the ke y space. 7 explanation is as follows: No te that the resulting keys from the generator is to be used as a n input key to a c ertain cryptographic a lgorithm or protoc ol whos e s ecurity gua rantee is us ually based on the as sumption that the inp ut key is uniformly picked from the key space. In fact, it c an be shown that, if the d istrib ution o f the key generator o utput is co mputationally ind istinguishable 6 from a uniform distrib ution over the key space, the secu rity gua rantee of cryptographic primiti ves like e ncryption and message authentica tion code s ho lds. Although one-way func tions or pre-image resistant h ash fun ctions have a long history of being used for linking mess ages in me ssage authentication [5], [16], it shou ld be n oted tha t the direct application of a one-way fun ction as the key ge nerator is no t s uf ficient to ac hiev e the g oal of key secrecy here . 7 A more careful composition of o ne-way functions is n eeded for linking keys together , na mely , a pseud orandom function (PRF) whos e de finition is as follo ws. Definition 4. Let f : { 0 , 1 } l s × { 0 , 1 } l i → { 0 , 1 } l o be a fun ction which ta kes a se ed key s ∈ { 0 , 1 } l s and an input string x ∈ { 0 , 1 } l i and outputs another s tring y ∈ { 0 , 1 } l o (i.e. y = f s ( x ) ). f s ( · ) is is said to be taken from a pseudoran dom function ensemble 8 with index s if it satisfies that, with s u niformly picked from { 0 , 1 } l s and kept sec ret, all computationa lly efficient algorithms A given a set Z = { ( x ′ , y ′ ) : y ′ = f s ( x ′ ) } of evaluations of f s at x ′ ∈ X of his choice could tell whether a given y is the output of f s ( · ) on input x 6∈ X or randomly picked form { 0 , 1 } l o with a negligible advantage in l s for all x , whe re the a dvantage of an algorithm A for a giv en x is defined as follows: P r [ s ← { 0 , 1 } l s ; y = f s ( x ) : A ( Z, x, y ) = 1] − P r [ y ← { 0 , 1 } l o : A ( Z, x, y ) = 1] . Suppose f is a PRF . T o gen erate a key k ′ for a resou rce (or p ri vileged g roup) with label r ′ from anothe r key k for a resource with lab el r , we could conside r the conc atenation of the labels r || r ′ as an inpu t string to f and generate k ′ as k ′ = f k ( r || r ′ ) . In the next s ection, p ri vileged group identities in a senso r network are used as resou rce labels. The property of f ensures tha t nobody (co mputationally bo unded), without the knowledge o f k , would be able to distinguish k ′ from a key directly p icked from the key spac e with a non -negligible advantage. This a lso guarantees that nobod y could extract k from k ′ . If there is a PPT algorithm A which c an extract k from k ′ , then it could be used to tell whether a giv en k ′ is generated form f or randomly picked as follows: run A on k ′ to extract k and che ck if k ′ ? = f k ( r || r ′ ) ; k ′ is a g enerated from f if and o nly if k ′ = f k ( r || r ′ ) ; othe rwise, flip a co in to make a rand om/wild gues s. Hence, the key extraction p roblem is at leas t a s dif ficult as solving the decisional p roblem non -negligibly better tha n a wild gu ess. Conje ctured ps eudorand om functions which are e f ficient for the purpose here include AES -OMA C [2] and SHA-HMA C [15]. For example, if h ( · ) denotes the HMA C function, f k ( x ) can simply be implemented a s h ( k || x ) where k || x deno tes the c oncaten ation of the secret key k a nd the public input x . It is natural to worry about whethe r such indistinguisha bility preserves if f is used to generate a series of keys, that is, whe ther k t is still co mputationally indistinguis hable from a random 6 T wo probability distri butions are said to be computationally indistinguishable when no polynomial-time distin- guishing procedure can tell them apart. In other words, giv en a sample which could be picked fr om either of the two distributions, no sufficiently efficient algorithm can tell whether the sample is from the first distribution or the second. 7 Recall that a one-way function is one which is easy to e v aluate in one direction but hard in the rev erse. In some implementation, the output of a one-way function may leak a significant fraction of t he input bits. For example, suppose f : { 0 , 1 } l → { 0 , 1 } l is a one-way function leaking no input bit, we could construct another one-way function f ′ : { 0 , 1 } 2 l → { 0 , 1 } 2 l in the following way: f ′ ( x 1 || x 2 ) = x 1 || f ( x 2 ) where x 1 , x 2 ∈ { 0 , 1 } l . This is still a one-way function but leaks half of the i nput bit s. Consequently , one might be able to distinguish between i ts output and a uniformly picked random number . 8 W e will call f s a pseudorandom function for the sake of simplicity despite the loss of rigor . 8 key if it is generated from k in the follo wing series: k 1 = f k ( r || r 1 ) ; k 2 = f k 1 ( r 1 || r 2 ) ; . . . ; k t = f k t − 1 ( r t − 1 || r t ) . The follo wing theorem would be useful in answe ring this que stion. Theorem 2 : Suppose f : { 0 , 1 } l k × { 0 , 1 } ∗ → { 0 , 1 } l k is a PRF , k is u niformly picked from { 0 , 1 } l k , and k 1 = f k ( r || r 1 ) ; k 2 = f k 1 ( r 1 || r 2 ) ; . . . ; k t = f k t − 1 ( r t − 1 || r t ) . If t is polynomially many in l k , then { k t } ∼ = U l k (denoting the two distrib u tions are compu tationally indistinguisha ble 9 ) where { k t } is the distributi on o f k t and U l k is the uniform distribution over { 0 , 1 } l k . Proof. Suppose we look at the generation of k i from k i − 1 and a ssume that { k i − 1 } ∼ = U l k with an indistinguishability coefficient ǫ i − 1 (defined as the maximum indistingu ishability ad- vantage ac hiev a ble by any poly-time algo rithm); that is, ǫ i − 1 is negligible. W e know that k i = f k i − 1 ( r i − 1 || r i ) and wish to show that { k i } ∼ = U l k . W e use the s tandard hybrid a r gument with the hybrid distributi on K ′ i = { k ′ i : s i ← { 0 , 1 } l k ; k ′ i = f s i ( r i − 1 || r i ) } . From the prope rty of the PR F , K ′ i ∼ = U l k with an indistinguish ability c oefficient ǫ f (negligible). W e argue that K ′ i ∼ = { k i } by contradiction. Suppos e the re is a PPT algorithm A which ca n distinguish betwee n K ′ i and { k i } with a distinguishab ility ad vantage ǫ ′ i , then it can be u sed to distinguish between { k i − 1 } and U l k . The construction is as follo ws: for a gi ven s ∈ { 0 , 1 } l k , c ompute k = f s ( r i − 1 || r i ) a nd run A on k . If s ∈ { k i − 1 } , then k ∈ { k i } , whe reas, if s ∈ U l k , then k ∈ K ′ i . Thus this perfectly simulates the ch allenge of A in a real attack and could be used to dis tinguish b etween { k i − 1 } and U l k (a contradiction to our as sumption). He nce, ǫ ′ i ≤ ǫ i − 1 . Overall, { k i } ∼ = U l k with an indistinguish ability coefficient ǫ i ≤ ǫ ′ i + ǫ f = ǫ i − 1 + ǫ f . Note that w hen i = 1 , ǫ 0 = 0 since k 0 = k ∈ U l k . Summing over i , we have ǫ t ≤ tǫ f . Since ǫ f is negligible in l k , if t is polyno mially many , then ǫ t remains negligible in l k . This c onclude s the proof. Since the sec urity gua rantee o f a p seudoran dom fun ction is computationally complexity ba sed, key linking base d on a pseudoran dom function is compu tationally sec ure. V I . K E Y L I N K I N G F O R P A I RW I S E K E Y P R E - D I S T R I B U T I O N I N S E N S O R N E T W O R K S In this sec tion, we look a t three examples of applying key linking to sensor ne twork key pre- distrib ution (KPS). In a senso r network, eac h node is preload ed with a se t of keys in its key ring in suc h a way that it can e stablish a p airwise key with ano ther no de in its phys ical n eighborhoo d with rea sonably high prob ability (mainly for mutual en tity au thentication); the model considered here is the same a s that in [14 ], [6], [4], [12], [11]. In pairwise KPS, each privileged group consists of two u sers o r nodes . W e will ignore the repeated us age of keys, wh ich trades off security for reduce d key storag e; b ut the discus sion below s hould also apply to that case. A. A Graph-theoretic Rep r esentation of KPS for Sens or N etworks When two sensor nodes share a common key , they can mutually authenticate each other . W e c an e asily rep resent this keying or trust relationship in a g raph; that is, the se nsor node s a re represented a s vertices a nd an edge exists between two vertices if the correspond ing se nsor n odes share a common key . Th is g raph is called a keying relations hip graph in the followi ng discussion . Note that the keying relationship graph is a logical graph and do es not refle ct the actual network topology of the senso r ne twork during deployment. W e as sume there a re n senso rs. 9 That is, no polynomial time algorithm can distinguish whether a giv en sample is from the former or latter distributions. 9 B. K e y Link ing for KPS in Sensor Network s a) Example 1 — KPS for se nsor networ ks with o ne o r mu ltiple bas e stations [19]: In [19 ], the base station of a senso r network (with n nodes) has a ma ster key which is used (with PRF) to derive diff erent keys, with each one b eing shared betwe en the base station and a dif ferent sensor n ode. That is, each se nsor node an d the base station only needs to store a single key . The keying relationship graph is simply a s tar with the ba se s tation at the centre. This is ind eed a special instance of the ac cess structure graph discu ssed in S ection II; here, the n umber of users is ( n + 1) (including the base station) and the n umber o f res ources is n . Applying Theo rem 1, the maximum key storage in the best case is ⌈ n n +1 ⌉ = 1 . He nce, the design in [19] is indeed optimal in its c ontext. By a similar token, we co uld apply Theore m 1 to cas es with multiple bas e stations. b) Example 2 — KPS with perfec t co nnectivity in the ke y relationship graph: Ideally , to ensure any pa ir of physical ne ighboring n odes in the de ployed n etwork to be able to fi nd a sha red key , each node n eeds to store ( n − 1) keys (without key linking) if there are n nodes labe led from 0 to ( n − 1) . That is, the keying relationship grap h G is a complete graph . This storage requirement is trivi ally impractical. Since the re are n 2 possible groups , if key linking is applied, the maximum key s torage in the bes t ca se is ⌈ n 2 /n ⌉ = ⌈ n ( n − 1) 2 n ⌉ = ⌈ n − 1 2 ⌉ (Theorem 1);the maximum possible reduction factor is 1 2 (still not good enough). The implementation of the linking c ould b e d one as follows. W ithout loss o f gene rality , ass ume n is odd. A user i need s to s tore one seed key k i and n − 1 2 other deri ved keys { k j i = f k j ( j || i ) : j = ( i − d ) mod n, d ∈ [1 , n − 1 2 ] } where k j i is the pairwise key b etween node j (where j = ( i − d ) mod n, d ∈ [1 , n − 1 2 ] ) and node i . For the p airwise key betwee n node i an d node j ′ (where j ′ = ( i + d ) mod n, d ∈ [1 , n − 1 2 ] ), k ij ′ = f k i ( i || j ′ ) . That is, for the n − 1 2 nodes in front of n ode i , node i has to store the de ri ved keys, whereas , for the n − 1 2 nodes beh ind it, it can deriv e the pairwise key from k i . As a result, the overall key storag e per node is n − 1 2 + 1 . c) Example 3 — KPS with bound ed conn ectivity in the ke y r elationship graph : In many cases , due to s torage con straint, each nod e can o nly share a c ommon key with ano ther c n odes with c < n . Tha t is, e ach vertex in the keying relationship g raph has a bounded degree. W ithout loss of generality , assume c is even. The total number of edg es of the resulting keying relations hip grap h G ′ is nc 2 which is the total nu mber of possible groups . If key linking is applied, the maximum key storage per no de in the be st case is ⌈ nc 2 n ⌉ = ⌈ c 2 ⌉ ; the max imum reduction factor is again 1 2 . In the best possible case, a node i would only ne ed to store one key k i and c 2 other de ri ved keys k j i . The problem of determining wh ich half of the c pairwise keys are derived from k i and which half are o btained from other c 2 nodes cou ld be solved by finding an Eulerian tour over G ′ . An E ulerian tour over a graph G is a tour along the e dges of G so that each edge is pas sed exactly once . Suc h a tou r exists in a graph G if G has at mos t two vertices with an od d degree; this is fulfilled for G ′ in question. The Fleury’ s algorithm (sh own in Ap pendix) with running time O ( | E ( G ) | ) (whe re | E ( G ) | is the total number o f edge s in G ) c an be used for finding a n Eulerian tour [8] a nd the set of ed ges o f each vertex would be pa rtitioned by the tour into two h alves, one marked as incoming edg es and the other as outgoing e dges. Now we co uld deriv e all pa irwise keys on a n outgoing edg e of node i u sing k i and set the keys o f the incoming edg es as k j i deriv ed from k j of another node j . Regarding the c ase with an o dd nu mber of edges in a conn ectivit y graph , ed ges co uld be added to make the graph Eulerian. If there are vertices in a connectivity graph G with an odd number of edges, the total number o f s uch vertices sh ould be even. 10 W e could simply p artition su ch a 10 The sum of the degrees of all vertices of a graph is e ven. If a vertex has an odd degree, then t here must exist another vertex wit h an odd degree to make the total sum e ven . That i s, vertices with an odd degree come in pairs. 10 subset o f vertices into pairs and assign an edge to each pair , then the resulting g raph is Eulerian. While a re gular keying relationship graph i s considered in t his example, the result and technique apply t o a more general keying relationship graph as long as one can partition the edge s connec ting each vertex into two parts. Reduction on maximum key storag e co uld alw ays be achieved. Recall that giv en any key of a node on a pa rticular ou tgoing ed ge of the key relationship graph, it is computationa lly infeasible to find the keys on other ou tgoing e dges of the n ode, thus guaranteeing the resilience of co mpromised nodes. Any co llusion of compromised nodes would not threat the sec urity of the remaining node s since we have conside red an idea l acc ess structure and it is computationally hard for the collusion to find any key not originally he ld by the m if a pseudo random function is use d. V I I . D I S C U S S I O N S While there is always reduction in the average storage whene ver there i s redundant membership, key linking may not lea d to reduction on the maximum key storage per use r in some ac cess structure. Und er the framew ork of constraints c onsidered in this pa per , it cou ld be dif ficult to achieve reduction on the ma ximum storage in those ca ses. An analog y to this situation is wh en Huff man encod ing for the equ iprobable cas e. This se ts the limits of any s cheme if trading off security is not cons idered. If further reduction on the maximum key storage is neces sary , trading off the ide al acc ess structure is one p ossible solution an d comb inatorial techniqu es cou ld apply a s in [3], [1], [17], [13]. Alternati vely , we could c onsider a set of keys as a lon g bit string (instea d of a se t of individual keys) and crea te the linking on a bit-by-bit basis us ing the tec hnique of correlated ps eudoran domness [9]; howev er , the gain a lso co mes as a result of trading off security; now a non-privile ged user ma y learn s ome o f the b its of a resou rce key h e is not s uppos ed to whereas the key linking technique conside red in this paper would n ot leak out information that can be efficiently extracted by a non-privil eged us er . V I I I . C O N C L U S I O N As applications in volving low co st devices like se nsor networks a nd RF ID e merge, memory cost (for s ecure key s torage) which is us ually not a con cern h as be come an e ssential c onstraint to designing s ecurity s ystems. T o alleviate this, the key storage req uirement co uld pos sibly reduce d by creating depe ndency among secret keys s tored in a user d evice, that is, key linking. Key linking exploits redundancy in privil eged group memberships for key compres sion. W e deriv e a n uppe r bound for max imum ach iev a ble key compression in a sys tem w ith idea l, general acces s structure. This b ound is tight an d ca n somehow be treated as a n egati ve result, which de monstrates that wit hout trading off security , cons iderable key storage reduc tion may not be achiev able. W e a lso show a provably secure instantiation of key linking sch eme u sing pesudo random fun ctions. W e show how to a pply the key linking tec hnique to red uce key storage in pairwise key pre-distrib u tion in wireless sensor ne tworks; the storag e reduction is still n ot sufficient to giv e efficient s chemes which ag ain demonstrate the c ost in efficiency los s we have to p ay if no security tradeoff is considere d. The results actually provide ground for proposals which trade off se curity for efficiency . R E F E R E N C E S [1] A. Beimel and B. Chor . Communication in key distri bution schemes. IEEE T ransactions on Information Theory , 42(1):19–28 , 1996. [2] M. Bell are, R. Canetti, and H. Krawczyk. Ke ying hash functions for message authentication. In Advances in Cryptology — CRYPTO 1996, Springer-V erla g LNCS vol. 1109 , pages 1–15. 11 [3] C. Blundo, A. De Santi, A. Herzberg, U. V accaro, and M. Y ung. P erfectly-secure key distribution for dynamic conferences. In Advances in Cryptology — CRYPTO 1992, Spring er-V erla g LNCS vol. 740 , pages 471–486, 1993. [4] S. A. C amtepe and B. Y ener . C ombinatorial design of key distribution f or wi reless sensor networks. In Computer Security - ESORICS, Springer -V erlag LNCS vol. 3193 , pages 293–308, 2004. [5] A. C-F . Chan. A graph-theoretical analysis of multicast authentication. In 23r d I EEE International Confer ence on D istributed Computing Systems (ICDCS’03) , pages 155–1 62, May 2003. [6] H. Chan, A. P errig, and D. Song. Random key predistribution schemes f or sensor networks. In the Pr oceedings of IE EE Symposium on Security and Pri vacy 2003 , pages 197–21 3, May 2003. [7] H. Y . Chien. Efficient time-bound hierarchical ke y assignment scheme. IEEE T rans. on Know . and Data Eng. , 16(10):1301 –1304 , 2004. [8] T . H. Cormen, C. E. Leiserson, R . L. Riv est, and C. Stein. Intr oduc tion to Algorithms . McGraw Hil l, 2nd edition, 2001. [9] R. Cramer , I. Damg ˚ ard, and Y . Ishai. Share con v ersion, pseudo randomness secret-sharing and applications to secure computation. In TCC 2005, Springer -V erlag LNCS vol. 3378 , pages 342–362, 2005. [10] A. De S antis, A. L. Ferrara, and B. Masucci. Unconditionally secure ke y assignment schemes. Discret Applied Math. , 154(2):234–252, 2006. [11] W . Du, J. Deng, Y . S . Han, S . Chen, and P . V arshney . A ke y management scheme for wireless sensor network s using deployment kno wledge. In the Pr oceed ings of IEEE INFO COM’04 , pages 586–597 , March 2004. [12] W . Du, J. Deng, Y . S . Han, and P . V arshney . A pairwise key pre-distribution scheme for wireless sensor networks. In the Procee dings of ACM Confer ence on Computer and C ommunication Security (CCS 2003) , pages 42–51 , Nov ember 2003. [13] M. Dyer , T . F enner , A. Frieze, and A. Thomason. On ke y storage in secure networks. Journ al of Cryptology , 8(4):189–20 0, 1995. [14] L. E schenauer and V . D. Gilgor . A key management scheme for distributed sensor networks. In the Proceed ings of ACM Conferen ce on Computer and Communication Security (CCS 2002) , pages 41–47, Nov ember 2002. [15] T . Iwata and K. Kurosaw a. OMAC: One-ke y CBC MAC. In F ast Softwar e Encryption (FSE 2003), Springer- V erlag LNCS vol. 2887 , pages 129–153, 2003. [16] R. C. Merkle. A certifi ed digital signature. In Advances i n Cryptology — CRYPT O 1989, Springer-V erlag LNC S vol. 435 , pages 218–238 , 1990. [17] C. J. Mitchell and F . C . Piper . Ke y storage i n secure networks. Discr ete Applied Mathematics , 21:215–228 , 1988. [18] D. Naor , M. Naor, and J. Lotspiech. Revoc ation and tracing schemes for stateless receiv ers. In A dvances in Cryptology — CRYPTO 2001, Springer-V erlag LNCS vol. 2139 , pages 41–62, 2001. [19] R. S ze wczyk, V . W en, D. Culler, and D. T ygar . SPIN S: Security protocols for sensor networks. In P r oceedin gs ACM MOBICOM 2001 , pages 189–199 , July 2001. [20] T . W u and C. Chang. Cr yptograph ic ke y assignment scheme for hierarchical access control. Int. Journ al of Comput. Syst. Sci. and Eng. , 1(1):25–28, 2001. A P P E N D I X Fleury’ s Algor ithm Fleury’ s algorithm constructs an Euler circuit in a g raph (if it’ s po ssible). Th e algorithm runs as follo ws: 1) Pick any verte x to start. 2) From that vertex pick a n edge to traverse, con sidering following rule: never c ross a bridge of the reduce d grap h 11 unless there is no other choice. 3) Darken that edge, as a reminder that you can’t traverse it again. 4) T ra vel that edg e, c oming to the next vertex. 5) Repeat Step s 2-4 until all ed ges have been tra versed, and you are back at the starting vertex. 11 By ”reduced graph” we mean t he original graph minus t he darkened (already used) edge.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment