Resilient Coordinated Movement of Connected Autonomous Vehicles
In this paper, we consider coordinated movement of a network of vehicles consisting of a bounded number of malicious agents, that is, vehicles must reach consensus in longitudinal position and a common predefined velocity. The motions of vehicles are…
Authors: Mostafa Safi, Seyed Mehran Dibaji, Mohammad Pirani
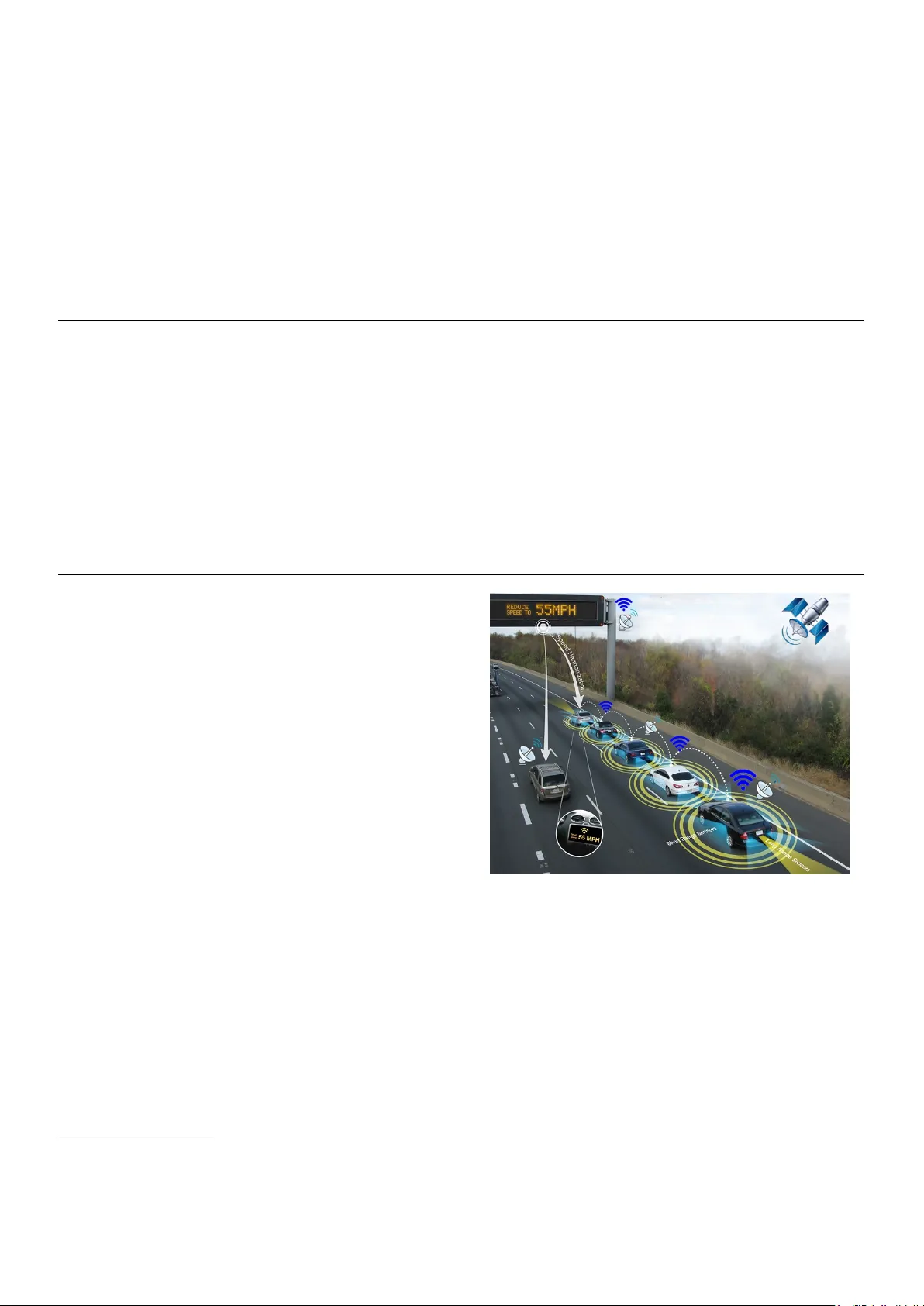
Resilient Coordinated Mov ement of Connected Autonomous V ehicles Mostafa Safi a, ∗ , Seyed Mehran Dibaji b , Mohammad Pirani c a Aer ospace Engineering Department, Amirkabir Univer sity of T echnology , T ehran, Ir an b Mechanical Engineering Department, Massachusetts Institute of T echnology , Cambridge, MA, USA c University of T or onto, T or onto, Canada Abstract In this paper, we consider coordinated movement of a network of v ehicles consisting of a bounded number of malicious agents, that is, vehicles must reach consensus in longitudinal position and a common predefined velocity . The motions of v ehicles are modeled by double-integrator dynamics and communications ov er the network are asynchronous with delays. Each normal vehicle updates its states by utilizing the information it receiv es from vehicles in its vicinity . On the other hand, misbehaving vehicles make updates arbitrarily and might threaten the consensus within the network by intentionally changing their moving direction or broadcasting faulty information in their neighborhood. W e propose an asynchronous updating strategy for normal vehicles, based on filtering extreme v alues received from neighboring vehicles, to sa ve them from being misguided by malicious vehicles. W e show that there exist topological constraints on the network in terms of graph robustness under which the vehicles resiliently achiev e coordinated mov ement. Numerical simulations are provided to e valuate the results. K eywor ds: Cooperativ e adaptiv e cruise control, autonomous vehicles, resilient consensus, graph rob ustness 1. Introduction Modern intelligent vehicles are not only used for driving but are processors that can perform complicated tasks and connect to their surroundings [1]. The advent of ever -gro wing Internet of V ehicles, along with cloud services, enables v ehicles to com- municate important information which can potentially be used for management of the network ed vehicles or increasing the re- liability of each vehicle’ s estimation and control indi vidually [2, 3]. Ho wev er , as the vehicles become more connected, they become more prone to adversarial actions and cyber -attacks. T o this end, devising defense mechanisms, to increase the security for both intra-vehicle networking and inter -vehicular communi- cations, is of great importance [4, 5, 6, 7]. An e ffi cient defense mechanism must be able to prev ent the attack as much as pos- sible, detect the attack in case of happening, and satisfy a le vel of resilience in performing tasks despite the existence of an at- tack [8]. The focus of the current paper is the application of resilience methods to a Cooperati ve Adaptive Cruise Control (CA CC) strategy (Fig. 1). V ehicle-to-vehicle (V2V) communications can provide di- rect data transfer which possess a much lo wer delay compared to radars [9] and enable vehicles to mov e close together , while collision av oidance algorithms and congestion control proto- cols assist this strate gy [10, 11, 12]. This will increase the amount of road throughput and reduce the need for de velop- ing more road networks. Cooperativ e adaptiv e cruise control, as one of the applications of V2V communications, is among ∗ Corresponding author Email addresses: halebi@aut.ac.ir (Mostafa Safi), dibaji@mit.edu (Seyed Mehran Dibaji), pirani@kth.se (Mohammad Pirani) Figure 1: Cooperativ e adapti ve cruise control in a network of vehicles with activ e and / or passive sensing systems, photo source (with some edits): US De- partment of T ransportation. the widely used methods in controlling highway tra ffi c systems [13]. In this approach, vehicles tend to follo w specific speeds while maintaining a safe distance from each other and at the same time consume as little space as possible in the highway to facilitate the tra ffi c flo w [14]. Since wireless communica- tion plays piv otal roles in CACC, we must make it resilient to malicious actions [15]. Attack-resilient algorithms in CA CC context refer to a class of actions taken to bypass the attacker or mitigate its e ff ects in order to impro ve performance in vehicle formation and velocity tracking. Similarly , in multi-agent sys- Pr eprint submitted to European Journal of Control J uly 30, 2021 tems, v arious consensus setups have been widely studied in the past decade [16, 17], where locally connected agents interact to achiev e agreement by reaching a common state. In this litera- ture, r esilient consensus expresses the situation where some of the agents in the network take some actions to decei ve the oth- ers, are possibly crashed, or intentionally ev ade ex ecuting the local state updating rule. These types of consensus problems are frequently studied in the computer science field by design- ing distributed control algorithms(see, e.g., [18]). There are v arious techniques to reliev e or counteract the ef- fects of cyber attacks in multi-agent systems. In some solutions, each agent identifies the adversarial agents of the network by observing their information history – a sort of fault detection and isolation strategy [19, 20, 21]. Howev er , usually in these techniques, each agent needs global knowledge of the network such as topology , which is neither desirable in distributed algo- rithms nor scalable. It is shown that to o vercome the misbehav- ing of f malicious vehicles, the topology is required to be at least (2 f + 1)-connected [19, 21]. In another type of distrib uted algorithms for resilient con- sensus, each agent utilizes a kind of filtering of the information packets delivered from the agents in its neighborhood contain- ing extreme or inv alid values at each time step. This class of algorithms are often called Mean Subsequence Reduced (MSR) algorithms, which was firstly introduced in [22] and ha ve been extensi vely used in the literature of computer science [23, 24, 25, 18, 26, 27] as well as estimation and control [28, 29, 30, 31, 32]. W ith MSR-type algorithms, there is no need to kno w the entire topology of the network; instead, a parameter f is con- sidered to secure the consensus in the worst case scenario, in which f is an upper bound for the number of malicious nodes. That means there is no need that the agents know f accurately . In fact, each node considers that there are at most f malicious nodes within the neighborhood (or within the entire network). These types of assumptions are common in the literature of ro- bust control. In this literature, conv ergence of these algorithms is guaranteed by some constraints on the topology . While the traditional connectivity constraints are not enough for conv er- gence of these algorithms, as is stated in [32], graph r obustness has been recently used as a successful connecti vity measure for di ff erent consensus problems to ensure that a network achiev es agreement [33, 34]. Our contributions in this paper are threefold: • Modeling and formulation of resilient longitudinal co- ordinated movement of autonomous vehicles: we use resilient consensus notions introduced in computer sci- ence literature [33] to solve a real world problem in multi- vehicle coordinated movement. W e consider longitudi- nal cooperativ e cruise control in the presence of some malicious vehicles in the network. Therefore, we as- sume that the vehicles move in parallel or each vehicle is equipped with a Collision A voidance System (CAS) to prev ent colliding with its neighbors and can switch its lane to overtak e frontier vehicles if required. W e use the typical second-order dynamics to model each autonomous vehicle within the network. Also, each vehicle makes up- dates based on its current position and velocity and those most recently recei ved from its neighbors. The control input of each vehicle is applied through its acceleration. • Developing distrib uted algorithm and update rule f or each vehicle to reach agreement considering asynchrony and delays in communications: W e develop our dis- tributed algorithms in an asynchronous setting, where each normal vehicle may decide to update from time to time with possibly delayed data packets receiv ed from the agents in its neighborhood. This is a susceptible situation which allows the malicious vehicles to take advantage and broad- cast di ff erent information, including their states, in dif- ferent time intervals to reachable vehicles or change their mov ement quickly to appear in di ff erent states in perspec- tiv e of the other vehicles. W e suppose that the worst-case scenario may happen, where the malicious vehicles hav e global knowledge about the topology , updating times, the transmitted data packets by normal vehicles, and e ven delays of communications. On the other hand, the nor- mal vehicles only have access to the data directly re- ceiv ed from their neighbors; thus they cannot predict ad- versaries’ beha vior . • Analyzing the topology constraint r equired for the r e- silient cooperative cruise control: The proposed algo- rithm and update rule cannot immediately lead to the suc- cess of the resilient coordinated mov ement. There must be specific constraints on the topology to guarantee the con ver gence. W e analyze these topology constraints based on robustness notions de veloped in the literature. The outline of this paper is as follows. In Section 2, we introduce the preliminaries and problem setup. Our main re- sults including the update rule, the filtering algorithm, and the required topology constraints are presented in Section 3. W e show the e ff ecti veness of our strategy by simulation examples in Section 4. Finally , Section 5 concludes the paper . 2. Preliminaries 2.1. Graph Theory Notions According to [16], we recall some preliminary concepts on graphs. A digraph with n nodes ( n > 1) is defined as G [ k ] = ( V [ k ] , E [ k ] ) , k ∈ Z + , with the set of nodes V = { 1 , . . . , n } and the set of edges E ⊆ V × V . W e sometimes drop do wn the step time k for the sake of simplicity . An incoming link from node j to node i is denoted by ( j , i ) ∈ E . The adjacency matrix corresponding to G [ k ] is defined by A [ k ] ∈ R n × n . A graph is called complete if ∀ i , j ∈ V , i , j : ( i , j ) ∈ E . For node i , the set of its neighbors is denoted by N i = { j | ( j , i ) ∈ E} and the number of its neighbors, i.e. its degree, is denoted by d i = |N i | . A path is a subset of nodes P = { i | ( i + 1 , i ) ∈ E , i = 1 , . . . , p − 1 , p > 1 } . If there is a path between each pair of nodes in the directed graph G , it is said to be strongly connected. The verte x connectivity K ( G ) of the graph G is the minimum number of nodes such that by removing them and all associated edges, the 2 graph is not strongly connected anymore. Then, the graph is said to be κ -connected if K ( G ) ≥ κ . A directed graph is said to have a directed spanning tree if there exists a node in the graph from which there is a path to e very other node. Note that we will use the terms node and vehicle interchangeably in this paper . Among connectivity measures of a graph, robustness is the critical topological notion for the MSR-type algorithms to achieve resilient consensus. Robust graphs were coined in [32] for the analysis of resiliency of consensus in multi-agent systems against cyber -attacks. Definition 1. (( r , s )-robust) The digraph G = ( V , E ) is ( r , s )- robust ( r , s < n ) if for ev ery pair of nonempty disjoint subsets V 1 , V 2 ⊂ V , at least one of the following conditions is satis- fied: 1. X r V 1 = V 1 , 2. X r V 2 = V 2 , 3. |X r V 1 | + |X r V 2 | ≥ s , where X r V ` is the set of all nodes in V ` which have at least r incoming edges from outside of V ` . In particular , graphs which are ( r , 1)-robust are called r -robust. T o have a better understanding of the notions of robustness, refer to Appendix A. 2.2. Physics of the System Consider a network of vehicles driving in a road whose communications are through the directed graph G . Each ve- hicle i ∈ V has a second-order dynamic system given by ˙ x i ( t ) = v i ( t ) , ˙ v i ( t ) = u i ( t ) , i = 1 , . . . , n , (1) where x i ( t ) ∈ R and v i ( t ) ∈ R are the longitudinal position and velocity of the i th vehicle, respecti vely , and u i ( t ) is its control input at time t ≥ 0. The discrete form of the dynamic system (1) with sampling period T is represented as x i [ k + 1] = x i [ k ] + T v i [ k ] + T 2 2 u i [ k ] , v i [ k + 1] = v i [ k ] + T u i [ k ] , i = 1 , . . . , n , (2) where x i [ k ], v i [ k ], and u i [ k ] are, respectively , the position, the velocity , and the control input of the i th vehicle at t = kT for k ∈ Z + , where T is the sampling period [17]. 2.3. Pr oblem Setup In this paper , we inv estigate the coordinated movement of networked vehicles in the sense that they reach a same fixed velocity asymptotically leading to a formation with a predefined (safe) inter-v ehicular distance: x i [ k ] − x j [ k ] → δ i j , v i [ k ] → r as k → ∞ , ∀ i , j ∈ V , where δ i j is the desired relative position of node i with respect to j and r is the desired velocity of the networked vehicles which is assumed to be known for all. W e intentionally defined δ i j as a distributed parameter because of two reasons: i) we aimed to minimum the global information known by the agents in the network, ii) it gi ves the vehicles the opportunity to set the inter-vehicular distances based on their size and sensing systems. For example, it would be safer for two trucks to ha ve a longer relati ve distance. In this work, we inv estigate the case where some vehicles misbehav e because of damage, disturbances, or various cyber attacks. Note that we focus on the consequences of such attacks or failures in consensus of the network, not the source of attacks (or failures). For example, some malicious vehicles might in- tentionally send false data to their neighbors in the network or, alternativ ely , some vehicles might suddenly crash and lose their control. In other words, nature of failures makes no di ff erence in our problem setup. In order to formulate the problem, we elaborate on some notions regarding the communications in the network and consensus in the presence of malicious vehicles. There are two possible situations in which malicious vehi- cles might deceive the normal vehicles and prev ent them from reaching consensus based on their equipment (refer to Fig. 1), described below: i) V ehicles use an activ e sensing system: they can estimate the state of their neighbors on their o wn (for e xample us- ing their 3D camera or LiD AR system. ii) V ehicles use a passi ve sensing system: they trust the in- formation the y recei ve from their neighbors (for e xample using their GPS recei ver or wireless communication sys- tem which are susceptible to cyber attacks). In the first case, malicious vehicles can intentionally change their moving direction or oscillate by av oiding any prescribed update rule and choosing arbitrary control inputs. Accordingly , all normal vehicles are supposed to follow . In the second case, malicious vehicles can arbitrarily broadcast any information in their neighborhood to deceive their neighbors. Note that the dynamics for all vehicles still remain the same as (2). Accordingly , we divide the v ehicles into two groups of ma- licious and normal vehicles as follo ws. Definition 2. (Malicious and Normal V ehicles) V ehicle i is called malicious if it can e vade following any prescribed algorithm for updating its control input or broadcast false state feedback to its neighbors. The malicious vehicles are assumed to be om- niscient, i.e. they have full kno wledge of the topology , updat- ing times, the transmitted data packets by normal vehicles, and ev en delays for all communication links and all k ≥ 0 – this is a reasonable assumption as it takes the worst case scenarios. Otherwise, it is called normal. The set of malicious vehicles is denoted by M ⊂ V . Furthermore, we assume that the number of malicious ve- hicles, all ov er the network or at least in the neighborhood of each normal vehicle, is upper bounded. Definition 3. ( f -total Malicious Model) The netw ork is f -total malicious if the number of malicious vehicles in the whole net- work is at most f . Definition 4. ( f -local Malicious Model) The network is f -local malicious if the number of malicious vehicles in the neighbor- hood of each normal vehicle i is bounded by f , i.e., |N i ∩ M| ≤ f , i ∈ V / M . 3 Now , we formally define the concept of resilient coordi- nated mov ement for the proposed network of vehicles as fol- lows. Definition 5. (Resilient Coordinated Movement) For any possi- ble set of malicious vehicles and their arbitrarily chosen inputs, the network of normal vehicles is said to achie ve resilient coor- dinated mov ement if it holds that x j [ k ] − x i [ k ] → δ i j , v i [ k ] → r as k → ∞ , ∀ i , j ∈ V \ M , where δ i j is a predefined (safe) inter - vehicular distance between the nodes i and j and r is the desired velocity of the network ed normal vehicles. In practice, the parameter δ i j can be properly set by the CAS of each vehicle to keep a safe distance with the other vehicles in the ego lane a voiding any collision. Furthermore, the vehi- cles might not have synchronous and delay-free communica- tions with all the neighbors simultaneously . Thus, the solution must be robust against both delays and asynchrony which are very important in real world applications. Finally , the main problem which we consider in this paper is as follows: Problem 1. Under the f -total / f -local malicious model, find a condition on the network topology so that the normal vehi- cles reach the resilient coordinated mov ement using an asyn- chronous update rule. 3. Main Results In this section, we propose the update rule and MSR-type algorithm by which the normal vehicles are able to reach the coordinated movement in the presence of misbehaving vehicles. W e present the updating strategy compatible with communica- tion delays and asynchrony . Therefore, the vehicles are allowed to update occasionally using delayed data packets. Note that the updating strategies that are developed here must be enhanced with the constraints on the topology of the network which will be discussed in the next section. 3.1. Update Rule W e modified the algorithm and update rule proposed in [30] to ADP-MSR (Asynchronous Double-integrator Position-based Mean Subsequence Reduced), which suits the problem of re- silient coordinated mo vement. Each normal vehicle distribu- tiv ely uses the relative position to its neighbors and its o wn ve- locity as the feedback. T o develop the update rule for coordinated mov ement, first we use a change of variables as follo ws: x i [ k ] = p i [ k ] + kT r v i [ k ] = q i [ k ] + r , (3) where, p i [ k ] and q i [ k ] are the transformed variables and r is the desired velocity of the networked v ehicles based on Def. 5. Substituting the new variables into the dynamic system (2), we hav e: p i [ k + 1] = p i [ k ] + T q i [ k ] + T 2 2 u i [ k ] q i [ k + 1] = q i [ k ] + T u i [ k ] . (4) Interestingly , the form of the transformed dynamic system (4) is the same as (2). Based on Theorem 4.2 in [30], the system dynamic (2) asymptotically reaches consensus (in the sense that lim k →∞ x j [ k ] − x i [ k ] = δ i j ) in a network with communication delays and asynchrony with the control input: u i [ k ] = X j ∈N i a i j [ k ] x j [ k − τ i j [ k ]] − x i [ k ] − δ i j − α i v i [ k ] . Equiv alently , the transformed dynamic system (4) asymp- totically reaches consensus (in the sense that lim k →∞ p j [ k ] − p i [ k ] = δ i j , q i [ k ] → 0 as k → ∞ , ∀ i , j ∈ V ) in a network with communication delays and asynchrony with the control input: u i [ k ] = X j ∈N i a i j [ k ] p j [ k − τ i j [ k ]] − p i [ k ] − δ i j − α i q i [ k ] , (5) where a i j [ k ] is the ( i , j ) entry of the adjacency matrix A [ k ] ∈ R n × n associated with G , τ i j [ k ] ∈ Z + denotes the time delay cor - responding to the edge ( j , i ) at time k and α i is a positi ve scalar . For the sake of simplicity , p j [ k − τ i j [ k ]] − p i [ k ] is called the relativ e position of vehicle j to vehicle i in the rest of the paper . Recalling the variable change of (3), from the viewpoint of ve- hicle i , the most recent information regarding vehicle j at time k is the position of j at time k − τ i j [ k ] relativ e to its own cur- rent position. While the communications delays are assumed to hav e the common upper bound τ , they can be di ff erent at each edge and ev en time varying defined as 0 ≤ τ i j [ k ] ≤ τ , ( j , i ) ∈ E , k ∈ Z + . (6) Using transformation (3), the e xpressions of lim k →∞ p j [ k ] − p i [ k ] = δ i j and lim k →∞ q i [ k ] = 0, can be transformed to the expressions of lim k →∞ x j [ k ] − x i [ k ] = δ i j and lim k →∞ v i [ k ] = r , ∀ i , j ∈ V \ M which represent what we called “resilient coordinated mov ement” in Definition 5. According to (5) and (6), note that each normal vehicle re- ceiv es the position v alue of its neighbors at least once in τ time steps, but possibly in an asynchronous manner . Also, vehicle i uses its own velocity without delay in the update rule. The value of τ is not required to be known to the vehicles as it is not uti- lized in the update rule. W e also emphasize that, in fully asynchronous settings, ve- hicles must also be f acilitated with their o wn clocks [35]. How- ev er , we consider the so-called partially asynchr onous updating setting in this paper . This is a common term in the literature for those update protocols with both delay and di ff erent update times [36] and in fact contains some lev el of synchrony mean- ing that all vehicles use the same clock. Considering delays in communicated data packets to address partial asynchrony has been studied in [37, 38, 35]. 4 The malicious vehicles are assumed to be omniscient, i.e. they have full kno wledge of the topology , updating times, the transmitted data packets by normal vehicles, and even delays τ i j [ k ] for all communications and for k ≥ 0. The malicious ve- hicles can take advantage of this knowledge to make deceiving back and forth movements or broadcast faulty data packets to confound and prev ent the normal vehicles to reach consensus. Howe ver , any misbehavior by malicious vehicles might only make the con vergence time longer and cannot a ff ect the main outcome of our method, i.e. prevent the vehicles from reaching consensus. The ADP-MSR algorithm which is executed by each vehi- cle at each time step k is outlined in Algorithm 1. The simplicity of this algorithm is its main feature. Each normal vehicle dis- regards the misleading information – e xtreme v alues – received from its neighbors by neglecting the incoming edges from those suspicious neighbors. Then, the remaining edges determine the underlying graph G [ k ]. In this algorithm, there is no need to know the entire topology of the netw ork; instead, we consider a parameter f to secure the consensus in the worst case scenario, in which f is an upper bound for the number of malicious ve- hicles. That means the normal vehicles do not need to know f accurately . In fact, each vehicle considers that there are at most f malicious nodes within the neighborhood (or within the entire network). Note that these types of assumptions are common in the literature of robust control. Theorem 1. Under the f -total malicious model, the network of vehicles with second-order dynamics utilizing the control input (5) and the ADP-MSR algorithm comes to resilient co- ordinated mov ement with an exponential con ver gence rate, if the underlying graph is (2 f + 1)-rob ust, and if it comes to re- silient coordinated mov ement, the underlying graph is at least ( f + 1 , f + 1)-robust. Pr oof. (Su ffi ciency) The proof is similar to what is presented in Theorem 4.2 of [33]. The proof there is presented for the position consensus of the original dynamic system (1). Here, the dynamic system is replaced with (4) and the result is v alid for p [ k ] and q [ k ], i.e. p j [ k ] − p i [ k ] → δ i j , q i [ k ] → 0, ∀ i , j ∈ V \ M as k → ∞ . Equi valently , according to (3), x j [ k ] − x i [ k ] → δ i j , v i [ k ] → r as k → ∞ , ∀ i , j ∈ V \ M . Thus, all the normal vehicles asymptotically reach a same velocity of r and meet a formation with the distrib uted inter -vehicular distance of δ i j , which is the resilient coordinated mov ement. (Necessity) W e consider the synchronous networks without communication delays as the proof of necessity is also valid for the more general case of partially asynchronous networks with communication delays. Contradiction is used for the proof. Suppose that the network is not ( f + 1 , f + 1)-robust. Then, there are nonempty disjoint sets V 1 , V 2 ⊂ V such that none of the conditions 1–3 in Definition 1 are held, i.e. 1. |X f + 1 V 1 | < |V 1 | , 2. |X f + 1 V 2 | < |V 2 | , 3. |X f + 1 V 1 | + |X f + 1 V 2 | ≤ f , Algorithm 1: ADP-MSR At each step time k , if vehicle i decides to mak e an update then for j ∈ N i The vehicle i calculates p j [ k − τ i j [ k ]] − p i [ k ] − δ i j based on the most recent position values. end V ehicle i sorts the calculated values from the largest to the smallest. if there ar e less than f vehicles that p j [ k − τ i j [ k ]] − p i [ k ] − δ i j ≥ 0 then The normal vehicle i ignores the incoming edges from those vehicles. else The normal vehicle i ignores the incoming edges of f vehicles, which ha ve the largest relativ e position values. end if there ar e less than f vehicles that p j [ k − τ i j [ k ]] − p i [ k ] − δ i j ≤ 0 then The normal vehicle i ignores the incoming edges from those vehicles. else The normal vehicle i ignores the incoming edges of f vehicles, which ha ve the smallest relativ e position values. end V ehicle i applies the control input (5) by the substitution a i j [ k ] = 0 for edges ( j , i ) which are ignored. else V ehicle i applies the control (5) where the position values of its neighbors remain the same as time step k − 1. end Result: u i [ k ] where by the definition X f + 1 V 1 and X f + 1 V 2 are the subsets of V 1 and V 2 whose their nodes hav e at least f + 1 incoming links. W e assume that p i [0] = a , ∀ i ∈ V 1 and p j [0] = b , ∀ j ∈ V 2 , where a < b . Let p ` [0] = c , where a ≤ c ≤ b , ∀ ` ∈ V \ ( V 1 ∪ V 2 ). W e also assume that q i [0] = 0, ∀ i ∈ V . From condition 3, we hav e |X f + 1 V 1 | + |X f + 1 V 2 | ≤ f . Also, we suppose that all vehicles in X f + 1 V 1 and X f + 1 V 2 are malicious and hold on to the constant values. Therefore, since the condition 1 and 2 are not held, i.e. |X f + 1 V 1 | < |V 1 | and |X f + 1 V 2 | < |V 2 | , we can conclude that there exist at least one normal vehicle in V 1 and one normal vehicle in V 2 which have f or fewer incoming neighbors outside of their own sets as they are not in X f + 1 V 1 and X f + 1 V 2 . Consequently , these normal vehicles in V 1 and V 2 update based only on the values inside V 1 and V 2 by remo ving the v alues receiv ed from outside of their sets. This makes their values unchanged at a and b . Thus, the normal vehicles do not come into agreement. In our problem setup, we aim to find topological conditions 5 G 1 G 3 G 2 G 4 Figure 2: A 2 f -rob ust network in which vehicles fail to reach coordinated movement with partial asynchrony and delayed information (each vehicle in this figure is representative for a set of f vehicles that are strongly connected). Note that the focus of this paper is on the longitudinal motion of vehicles. that for any set of malicious nodes and any malicious behavior , resilient coordinated mov ement is achie ved. For example, what we pro ved in the necessary condition is that for any topological condition less restrictiv e than a ( f + 1 , f + 1)-robust, there is a set of malicious nodes or behaviors that fail the normal vehi- cles to achie ve the resilient coordinated movement. T o elabo- rate more on this, consider a spanning tree which is the neces- sary condition for the resilient consensus if the malicious nodes take no misleading behavior regardless of the delayed and asyn- chronous communications. Ho wever , the malicious v ehicles will hav e more freedom to decei ve more normal vehicles in a network with communication delays and asynchrony . So, the necessary condition for the synchronous case (( f + 1 , f + 1)- robustness) is also a necessary condition for the asynchronous case. Also, note that authors in [33] ha ve considered the case where all normal agents agree on their positions and then stop. This paper pushes the previous research one step forw ard in the sense that the positions and velocities of the networked agents reach consensus simultaneously – the problem whose solution was non-tri vial after [33]. Furthermore, in Theorem 1, we observe a gap between the su ffi ciency and the necessity conditions. This point is illustrated by a 2 f -robust graph in Fig. 2, which is not resilient to f totally bounded adversarial vehicles as we will discuss in what follows. This graph is composed of four subgraphs G i , i = 1 , . . . , 4, and each of them is a complete graph – each vehicle in this figure is representative for a set of f vehicles that are strongly connected. The graph G 1 consists of 4 f vehicles and the rest hav e f vehicles. Each v ehicle in G 4 has incoming links from 2 f vehicles of G 1 . Every vehicle in G 3 has f links from G 1 and f links from G 4 . Like wise, each vehicle of G 2 has f link from G 1 and f incoming links from G 4 . Note that the minimum degree for a 2 f -robust graph is 2 f . Howe ver for this graph, the minimum degree of the vehicles is 2 f + 1 or greater . This is an important point for the follo wing reason. If a normal vehicle has only 2 f neighbors, it will keep its current state since it might ignore all of the v alues received from its neighbors under the ADP-MSR algorithm. It is clear that coordinated movement cannot tak e place if this happens for more than two vehicles in the network. The following proposi- tion formally states our claim. Proposition 1. There exists a 2 f -robust netw ork with the min- imum degree 2 f + 1 under which normal vehicles might not reach resilient consensus by the ADP-MSR algorithm. Pr oof. W e suppose that the network in Fig. 2 is both 2 f -robust and ( f + 1 , f + 1)-robust, but resilient coordinated movement cannot be achiev ed under the ADP-MSR. Assume that all vehi- cles in G 2 are malicious. W e sho w a scenario in which by the ADP-MSR algorithm, the position values of the vehicles in G 3 and G 4 nev er concur . Note that G 1 is 2 f -robust because of Lemma 1 (v) (see Ap- pendix A). By (iv) of this lemma, the graph obtained by adding G 2 is still 2 f -robust, since there are 2 f edges from G 1 . Simi- larly , adding G 3 and G 4 and the required edges based on (iv) of Lemma 1 also keeps the graph to be 2 f -robust. W e assume vehicles ha ve the following initial states for k = 0 and the prior τ steps: p i [0] = a − δ i ` 2 , q i [0] = 0 , ∀ i ∈ V 3 , p ` [0] = b + δ i ` 2 , q ` [0] = 0 , ∀ ` ∈ V 2 , p h [0] = c , q h [0] = 0 , ∀ h ∈ V 1 , where a − δ i ` 2 < c < b + δ i ` 2 . Also, the malicious vehicles set the following values as their states: p j [2 m ] = a − δ i ` 2 , p j [2 m + 1] = b + δ i ` 2 , ∀ j ∈ V 4 and the time delays are chosen by the following scenario: τ i j [2 m + 1] = 1 , ∀ j ∈ V 2 , i ∈ V 3 , ( j , i ) ∈ E , τ ` j [2 m + 1] = 0 , ∀ j ∈ V 2 , ` ∈ V 2 , ( j , ` ) ∈ E , τ i j [2 m ] = 0 , τ ` j [2 m ] = 1 , where m ∈ Z + . All other links ha ve no delay . Then, to the vehicles in G 3 , the malicious vehicles appear to be stationary at the state value a − δ i ` 2 and to the vehicles in G 4 at the state v alue b + δ i ` 2 . By ex ecuting the ADP-MSR at k = 0, the vehicles in G 3 will remov e the position values of all neighbors in G 1 since a − δ i ` 2 < c . Thus, for i ∈ V 3 , p i [1] = a − δ i ` 2 . At k = 1, the same happens for the vehicles ` ∈ V 4 and they stay at b + δ i ` 2 . Since the vehicles in G 3 are not a ff ected by an y vehicles with state values larger than a − δ i ` 2 , they remain at their state value for all future steps. The same holds among the normal vehicles in the network, therefore, p i [ k ] = a − δ i ` 2 and p ` [ k ] = b + δ i ` 2 for all i ∈ V 3 and ` ∈ V 4 . This shows failure in agreement of all vehicles as lim k →∞ p ` [ k ] − p i [ k ] = δ i ` + ( b − a ) , δ i ` . 3.2. Further Discussions and Results Here, we provide some e xtensions to the discussions and results so far proposed in the paper . 6 1 2 3 4 5 Figure 3: A graph that is (2 , 2)-robust but not 3-rob ust. First, note that only the number of malicious vehicles in each normal vehicle’ s neighborhood plays a role in the proof of Theorem 1. Therefore, the result is also valid for the f -local malicious model leading to the following corollary . Corollary 1. Consider the network of vehicles with second- order dynamics using the control input proposed in (5) and the ADP-MSR algorithm. The network achieves resilient coordi- nated movement under the f -local malicious model if the un- derlying graph is (2 f + 1)-robust. Note that the results in this paper are all valid for the second- order networks whose underlying graphs are fixed, i.e. with time-in variant E . In [31], for the first-order synchronous vehicle networks, there is a natural e xtension for the time-v arying G [ k ] and based on that G [ k ] = ( V , E [ k ]) is enough to be ( f + 1 , f + 1)- robust at each time k . The same condition is valid here, again for second-order synchronous networks. Howe ver , the assump- tion on robustness of the graph at each time k is quite conserva- tiv e and might bring di ffi culties in practice. Here, we would like to state a new relaxed condition for the partially asynchronous time-varying netw orks. The following definition has a key role for this purpose: Definition 6. (Jointly r -robust) The time-varying graph G [ k ] = ( V , E [ k ]) is jointly r -robust if there exists a fix ed ` such that the union of G [ k ] over each consecuti ve ` steps is r -robust. In a time-varying network, each normal vehicle i can use the outdated links from τ time steps back whene ver some informa- tion is not av ailable. Thus, the su ffi cient condition is obtained with the following additional assumptions: ` ≤ τ . (7) By the above discussions, the su ffi cient condition is presented as below . Corollary 2. Under the f -total / f -local malicious model, the time-varying network of vehicles with second-order dynamics utilizing control input (5) and ADP-MSR algorithm achieves resilient coordinated movement, if the underlying graph is jointly (2 f + 1)-robust under condition (7). Now , we discuss the relation between the graph properties proposed here for the resilient coordinated movement problem and those used in standard consensus problems without any ma- licious agents [39, 40, 35, 41]. In this paper , it is assumed that the number of adversarial vehicles is upper bounded by f . By removing all edges connected to malicious v ehicles, we can ob- tain a subgraph of G consisting of only the normal vehicles. By (vi) of Lemma 1 (see Appendix A), this network becomes (1 , f + 1)-robust. Now , the obtained graph has a spanning tree according to (iv) of the same lemma. W e know that consen- sus can be achiev ed under such a graph. It is also interesting that the su ffi cient condition in Corollary 2 is consistent with the consensus condition on time-varying networks kno wn as ha v- ing jointly spanning tree [42]. It is further noted that [23, 43, 22, 31, 26, 27] consider the so-called omissiv e faults, where malicious nodes can deny mak- ing any transmissions. Therefore, the normal vehicle i would wait to receiv e the position v alues of at least d i − f neigh- bors before making an update. It should be noted that omissiv e faults can also be tolerated by the MSR-type algorithms. The malicious vehicles kno wing that the normal vehicles apply the ADP-MSR algorithm might attempt to make this kind of attack to cause denial of information for filtering the received values in Algorithm 1. In such cases, if vehicle i does not receiv e the data packets from m i [ k ] incoming neighbors at time k , then the pa- rameter of the ADP-MSR for that vehicle can be changed from 2 f to 2( f − m i [ k ]) assuming that vehicle i is a ware of d i [ k ]. The topology analysis remains mostly the same. Besides, the ADP-MSR algorithms for f -total malicious models are resilient against another type of adversaries studied in [44]. There, the adversarial agents can extend the network by adding extra links. Howe ver , this does not change the value of f in the network. For example, in our problem, this can happen in a highway when some additional vehicles are passing by the connected vehicles network. Howe ver , note that the situation is subtly di ff erent in the case with the f -local model. Adding an extra link might increase the number of malicious vehicles in a neighborhood of some normal vehicles. Accordingly , the vehi- cles must kno w which links are newly created so as to remove them along with the edges ignored in the ADP-MSR algorithm. 4. Numerical Example Suppose a network of vehicles connected together on the network illustrated in Fig. 3 with partially asynchronous de- layed settings. This graph is (2 , 2)-robust (refer to Appendix A for more discussion). This network is considered to contain only one malicious vehicle, i.e. f = 1. The sampling period is set to be T = 0 . 01. Note that we set δ i j = 0 in this ex- ample, thus the vehicles come to consensus in parallel lanes with no relati ve longitudinal distances. Also, remember that we only consider longitudinal motion of the vehicles. Therefore, in this example, we assume that they move in parallel or each vehicle utilizes a CAS to overtak e frontier vehicles if required. W e consider two di ff erent scenarios to sho w the e ff ectiv eness of our method in the presence of acti ve and passiv e sensing systems. In both scenarios, four normal vehicles periodically make updates within each 12 time steps with various timings. Specifically , vehicles 1, 2, 3, and 5 make updates at time steps 7 0 5000 10000 15000 0 500 1000 1500 Figure 4: Position-time history of v ehicles under (2 , 2)-robust graph - coordi- nated movement f ailed. 0 5000 10000 15000 0 20 40 60 80 100 120 140 160 Figure 5: V elocity-time history of vehicles under (2 , 2)-robust graph - coordi- nated movement f ailed. k = 12 ` + 6 , 12 ` + 9 , 12 ` + 11 , 12 ` + 4 for ` ∈ Z + , respecti vely . W e assume that at these time steps, their updates are made with- out any delays. Ho wev er, each vehicle deals with nonuniform time-varying delays ( τ = 11) since the normal vehicles do not receiv e new information at other time steps. Setting 1: All the normal vehicles are assumed to hav e pas- siv e sensing systems, e.g. GPS recei ver , for navig ation. Thus, the malicious vehicle can misbehav e them by easily sending in- correct information to them instead of its actual position and velocity , and is free to mov e in its own way . It can be e ven stopped somewhere on the road and broadcast its false infor- mation. T o simulate this scenario, the initial states of the vehicles are gi ven by h x T [0] v T [0] i = 4 250 150 8 0 50 70 70 60 10 . The parameters α i in (5) are e v aluated as α 1 = α 5 = 2 and α 2 = α 3 = 3. The desired target velocity of the network of vehicles is set as r = 100. In this network, the malicious vehicle 4 misguide the normal ones and divide them into multiple groups to prevent them from coming to a single agreement. T o this end, vehicle 4 incorrectly send its positions as: x 4 [2 k ] = 2 + k T r and 0 5000 10000 15000 0 200 400 600 800 1000 1200 1400 Figure 6: Position-time history of vehicles under 3-robust graph - coordinated movement succeeded. 0 5000 10000 15000 0 20 40 60 80 100 120 140 160 180 200 Figure 7: V elocity-time history of vehicles under 3-robust graph - coordinated movement succeeded. x 4 [2 k + 1] = 200 for all k ≥ 0. Figs. 4 and 5 illustrate the time history of the positions and velocities of the normal vehicles. As expected, the positions of the normal vehicles do not reach consensus although the underlying network is (2 , 2)-robust, as a necessary condition. In fact, the ADP-MSR cannot stop the malicious vehicle from misguiding the normal vehicles. Fig. 4 indicates that in fact vehicles are divided into two groups and mov e with a relati ve distance because of the malicious behavior of vehicle 4, sending the false data to the normal v ehicles. Next, we obtain a 3-robust graph (which is 2 f + 1-robust in this case) by adding enough edges. As illustrated in Fig. 6 and 7, the same simulation with the complete graph with 5 nodes (the only 3-rob ust graph with 5 nodes) verifies the su ffi cient condition of Theorem 1 for the partially asynchronous setting. Setting 2: Normal vehicles 2 and 3 are assumed to ha ve ac- tiv e sensing systems and vehicles 1 and 5 are assumed to have passiv e sensing systems for navigation. As a result, the mali- cious vehicle faces a more challenging situation rather than the first setting 1 . If the malicious vehicle wants to misguide vehi- 1 Note that more complicated situations in which actions and reactions of the 8 Figure 8: Position-time history of v ehicles under (2 , 2)-robust graph - coordi- nated movement failed e ven when vehicles 2 and 3 ha ve active sensing systems. cles 2 and 3, it has to appear around them. Ho wever , as vehicles 1 and 5 each has a passive sensing system, the malicious vehicle can still use broadcasting false information to av oid them reach- ing consensus with the other two vehicles. As shown in Fig. 8, the malicious v ehicle can a ff ect the consensus and misguide the vehicles into two groups e ven when 2 of the vehicles have ac- tiv e sensing systems. On the other hand, as shown in Fig. 9, the su ffi cient graph condition, (2 f + 1)-robustness, guarantee the longitudinal coordinated movement of the vehicles. It is clear that the cyber attack for the malicious vehicle could be more di ffi cult (yet possible) if all the vehicles are equipped with ac- tiv e sensing systems. Theoretically , the malicious vehicle can- not pre vent consensus e ven if all the vehicles are equipped with activ e sensing systems. Howe ver , finding a practical scenario for this case would be tricky . In this setting, the initial states of the vehicles are gi ven by h x T [0] v T [0] i = 100 400 500 10 0 50 70 70 60 10 . The parameters α i in (5) are ev aluated as α 1 = α 5 = 2 and α 2 = α 3 = 10. Also, vehicle 4 incorrectly send its positions to vehicle 1 and 5 as: x 4 [2 k + 1] = 200 for all k ≥ 0, while it moves closer to vehicle 2 and 3 most of the time and appears as: x 4 [ k ] = 0 . 1 k + 5 √ k . 5. Conclusion In this paper , we studied the problem of resilient coordi- nated movement of a network of connected vehicles with second- order longitudinal dynamics, where the number of malicious vehicles in the network is bounded by a parameter f , known to the vehicles. W e ha ve proposed a distributi ve strategy for the normal vehicles to achie ve resilient consensus on their po- sitions with a safe inter-v ehicular distance and a predefined tar - get velocity . The necessary and su ffi cient graph conditions are respectiv ely ( f + 1 , f + 1)-rob ustness and (2 f + 1)-robustness for resilient coordinated movement of the network of vehicles normal and malicious vehicles are tak en into account are out of scope of this paper . Game theoretic approaches will address them. Figure 9: Position-time history of vehicles under 3-robust graph - coordinated movement succeeded. V ehicles 2 and 3 have acti ve sensing systems. under the f -total malicious model. Each vehicle performs the proposed update rule and ADP-MSR algorithm to achiev e the agreement with an exponential con ver gence rate. Communica- tions in the network are partially asynchronous with bounded delays. Future research trend can be possibly inv estigations in the following two main directions: i) considering 2D coordinated mov ement of connected vehicles and dev elop appropriate up- dating algorithms, ii) finding a necessary and su ffi cient topol- ogy condition for the con ver gence. Appendix A. T o ha ve a better understanding of ( r , s )-robust graphs [45], the following lemma is presented. Lemma 1. For an ( r , s )-robust graph G , the follo wings hold: (i) G is ( r 0 , s 0 )-robust, where 0 ≤ r 0 ≤ r and 1 ≤ s 0 ≤ s , and in particular , it is r -rob ust. (ii) G is ( r − 1 , s + 1)-robust. (iii) G is at least r -connected, but an r -connected graph is not necessarily r -robust. (iv) G has a directed spanning tree. (v) r ≤ d n / 2 e . Also, if G is a complete graph, then it is ( r 0 , s )- robust for all 0 < r 0 ≤ d n / 2 e and 1 ≤ s ≤ n . (vi) The graph G 0 = ( V , E 0 ) is ( r − w , s )-robust, when G 0 is formed by removing at most w edges from neighbors of each node in V , where w < r . (vii) The graph G 0 = ( V ∪ { v 0 } , E ∪ E 0 ), where v 0 is a node added to G and E 0 is the edge set related to v 0 , is r -robust if d v 0 ≥ r + s − 1. Moreov er , a graph is ( r , s )-robust if it is ( r + s − 1)-robust. Generally , it is clear that ( r , s )-robustness is more restrictive than r -robustness. The 5 nodes graph in Fig. 3 can be sho wn to be (2 , 2)-robust, but not 3-robust. From computational point of view , checking rob ustness properties is di ffi cult since the problem needs combinatorial calculations. Howe ver , tending the size of random graphs to infinity makes them rob ust [46]. 9 References [1] N. Lu, N. Cheng, N. Zhang, X. Shen, J. W . Mark, Connected vehicles: Solutions and challenges, IEEE Internet Things J. 1 (2014) 289–299. [2] B. Besselink, V . T urri, S. H. van de Hoef, K. Y . Liang, A. Alam, J. Martensson, K. H. Johansson, Cyber–physical control of road freight transport, IEEE Trans. Control Syst. T echnol. 104 (2016) 1128–1141. [3] K. Y . Liang, J. Martensson, K. H. Johansson, Heavy-duty vehicle platoon formation for fuel e ffi ciency , IEEE Trans. Intell. Transp. Syst. 17 (2016) 1051–1061. [4] D. Jia, K. Lu, J. W ang, X. Zhang, X. Shen, A survey on platoon-based ve- hicular cyber-ph ysical systems, IEEE Commun. Surveys T uts. 18 (2016) 263–284. [5] A. Alipour-Fanid, M. Dabaghchian, K. Zeng, Impact of jamming attacks on vehicular cooperative adapti ve cruise control systems, IEEE Transac- tions on V ehicular T echnology (2020). [6] A. Greenber g, Hackers remotely kill a jeep on the high- way—with me in it, https://www.wired.com/2015/07/ hackers- remotely- kill- jeep- highway/ , 2015. Accessed: 2018-12-16. [7] K. K oscher , A. Czeskis, F . Roesner, S. Patel, T . K ohno, S. Checko way , D. McCoy , B. Kantor, D. Anderson, H. Shacham, S. Sav age, Experi- mental security analysis of a modern automobile, IEEE Symposium on Security and Priv acy (2010) 447–462. [8] S. M. Dibaji, M. Pirani, D. B. Flamholz, A. M. Annaswamy , K. H. Jo- hansson, A. Chakrabortty , A systems and control perspective of CPS security , Annual Re views in Control 47 (2019) 394 – 411. [9] B. V an Arem, C. J. V an Driel, R. Visser , The impact of cooperativ e adaptiv e cruise control on tra ffi c-flow characteristics, IEEE Trans. Intell. T ransp. Syst. 7 (2006) 429–436. [10] Y . Y uan, R. T asik, S. S. Adhatarao, Y . Y uan, Z. Liu, X. Fu, Race: rein- forced cooperativ e autonomous vehicle collision a voidance, IEEE T rans- actions on V ehicular T echnology (2020). [11] M. Forghani, J. M. McNew , D. Hoehener , D. Del V ecchio, Safety con- trol of a class of stochastic order preserving systems with application to collision avoidance near stop signs, in: Proc. of American Control Con- ference, 2015, pp. 507–514. [12] S. A. Ahmad, A. Hajisami, H. Krishnan, F . Ahmed-Zaid, E. Moradi-Pari, V2v system congestion control v alidation and performance, IEEE Trans- actions on V ehicular T echnology 68 (2019) 2102–2110. [13] V . Turri, B. Besselink, K. H. Johansson, Cooperativ e look-ahead control for fuel-e ffi cient and safe heavy-duty vehicle platooning, IEEE Trans. Control Syst. T echnol. 25 (2017) 12–28. [14] A. Spiliopoulou, D. Manolis, M. P . F . V andorou, Adaptive cruise control operation for improved motorway tra ffi c flow , Transportation Research Record: Journal of the Transportation Research Board 2672 (2018). [15] M. Amoozadeh, A. Raghuramu, C. Chuah, D. Ghosal, H. M. Zhang, J. Rowe, K. Levitt, Security vulnerabilities of connected vehicle streams and their impact on cooperati ve driving, IEEE Communications Maga- zine 53 (2010) 126–132. [16] M. Mesbahi, M. Egerstedt, Graph Theoretic Methods in Multiagent Net- works, Princeton Uni versity Press, 2010. [17] W . Ren, Y . Cao, Distributed Coordination of Multi-agent Networks, Springer , 2011. [18] N. A. L ynch, Distributed Algorithms, Mor gan Kaufmann, 1996. [19] F . Pasqualetti, A. Bicchi, F . Bullo, Consensus computation in unreliable networks: A system theoretic approach, IEEE Trans. Autom. Control 57 (2012) 90–104. [20] I. Shames, A. M. H. T eixeira, H. Sandberg, K. H. Johansson, Distributed fault detection for interconnected second-order systems, Automatica 47 (2011) 2757–2764. [21] S. Sundaram, C. N. Hadjicostis, Distributed function calculation and con- sensus using linear iterative strategies, IEEE J. Sel. Areas Commun. 26 (2008) 650–660. [22] R. M. Kieckhafer , M. H. Azadmanesh, Low cost approximate agreement in partially connected networks, Journal of Computing and Information 3 (1993) 53–85. [23] M. H. Azadmanesh, R. M. Kieckhafer , Asynchronous approximate agree- ment in partially connected networks, International Journal of Parallel and Distributed Systems and Networks 5 (2002) 26–34. [24] M. M. Azev edo, D. M. Blough, Multistep interactiv e con ver gence: An e ffi cient approach to the fault-tolerant clock synchronization of large mul- ticomputers, IEEE Trans. P arallel Distrib. Syst. 9 (1998) 1195–1212. [25] Z. Bouzid, M. G. Potop-Butucaru, S. Tix euil, Optimal Byzantine-resilient con vergence in uni-dimensional robot networks, Theoretical Computer Science 411 (2010) 3154–3168. [26] R. Plunkett, A. Fekete, Optimal approximate agreement with omission faults, in: International Symposium on Algorithms and Computation, 1998, pp. 468–475. [27] N. H. V aidya, L. Tseng, G. Liang, Iterati ve approximate Byzantine con- sensus in arbitrary directed graphs, in: Proc. of A CM Symposium on Principles of Distributed Computing, 2012, pp. 365–374. [28] M. Safi, A filtering approach for resiliency of distributed observers against smart spoofers, arXiv preprint arXi v:1909.04172 (2020). [29] S. M. Dibaji, H. Ishii, Resilient multi-agent consensus with asynchrony and delayed information, Proc. of IF A C W orkshop on Distributed and Networked 48 (2015) 28–33. [30] S. M. Dibaji, H. Ishii, Consensus of second-order multi-agent systems in the presence of locally bounded faults, Systems & Control Letters 79 (2015) 23–29. [31] H. J. LeBlanc, X. Koutsouk os, Resilient asymptotic consensus in asyn- chronous robust networks, in: Proc. of Conference on Communication, Control, and Computing, 2012, pp. 1742–1749. [32] H. J. LeBlanc, H. Zhang, X. Koutsouk os, S. Sundaram, Resilient asymp- totic consensus in robust networks, IEEE J. Sel. Areas Commun. 31 (2013) 766–781. [33] S. M. Dibaji, H. Ishii, Resilient consensus of second-order agent net- works: Asynchronous update rules with delays, Automatica 81 (2017) 123–132. [34] S. M. Dibaji, M. Safi, H. Ishii, Resilient distributed averaging, in: Proc. of American Control Conference, 2019, pp. 96–101. [35] J. Qin, C. Y u, S. Hirche, Stationary consensus of asynchronous discrete- time second-order multi-agent systems under switching topology , IEEE T rans. Ind. Informat. 8 (2012) 986–994. [36] D. P . Bertsekas, J. N. Tsitsiklis, Parallel and Distributed Computation: Numerical Methods, volume 23, Prentice Hall, 1989. [37] Y . Gao, L. W ang, Consensus of multiple double-integrator agents with intermittent measurement, International Journal of Rob ust and Nonlinear Control 20 (2010) 1140–1155. [38] C. L. Liu, F . Liu, Dynamical consensus seeking of second-order multi- agent systems based on delayed state compensation, Systems & Control Letters 61 (2012) 1235–1241. [39] M. Cao, A. S. Morse, B. D. O. Anderson, Reaching a consensus in a dynamically changing environment: A graphical approach, SIAM Journal on Control and Optimization 47 (2008) 575–600. [40] J. Qin, H. Gao, A su ffi cient condition for con vergence of sampled-data consensus for double-integrator dynamics with nonuniform and time- varying communication delays, IEEE Trans. Autom. Control 57 (2012) 2417–2422. [41] F . Xiao, L. W ang, State consensus for multi-agent systems with switching topologies and time-varying delays, International Journal of Control 79 (2006) 1277–1284. [42] L. Xiao, S. Boyd, S. Lall, A scheme for robust distributed sensor fusion based on av erage consensus, in: Proc. of International Symposium on Information Processing in Sensor Networks, 2005, pp. 63–70. [43] A. Khanafer, B. T ouri, T . Bas ¸ar, Consensus in the presence of an adver - sary , Proc. of IF A C W orkshop on Distributed Estimation and Control in Networked Systems 45 (2012) 276–281. [44] Z. Feng, G. Hu, G. W en, Distributed consensus tracking for multi-agent systems under two types of attacks, International Journal of Robust and Nonlinear Control 26 (2016) 896–918. [45] H. J. LeBlanc, Resilient Cooperative Control of Networked Multi-Agent Systems, Ph.D. thesis, V anderbilt University , 2012. [46] H. Zhang, E. Fata, S. Sundaram, A notion of robustness in complex net- works, IEEE Control Netw . Syst. 2 (2015) 310–320. 10
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment