Energy Efficiency of Opportunistic Device-to-Device Relaying Under Lognormal Shadowing
Energy consumption is a major limitation of low power and mobile devices. Efficient transmission protocols are required to minimize an energy consumption of the mobile devices for ubiquitous connectivity in the next generation wireless networks. Oppo…
Authors: S. M. Zafaruddin, Jan Plachy, Zdenek Becvar
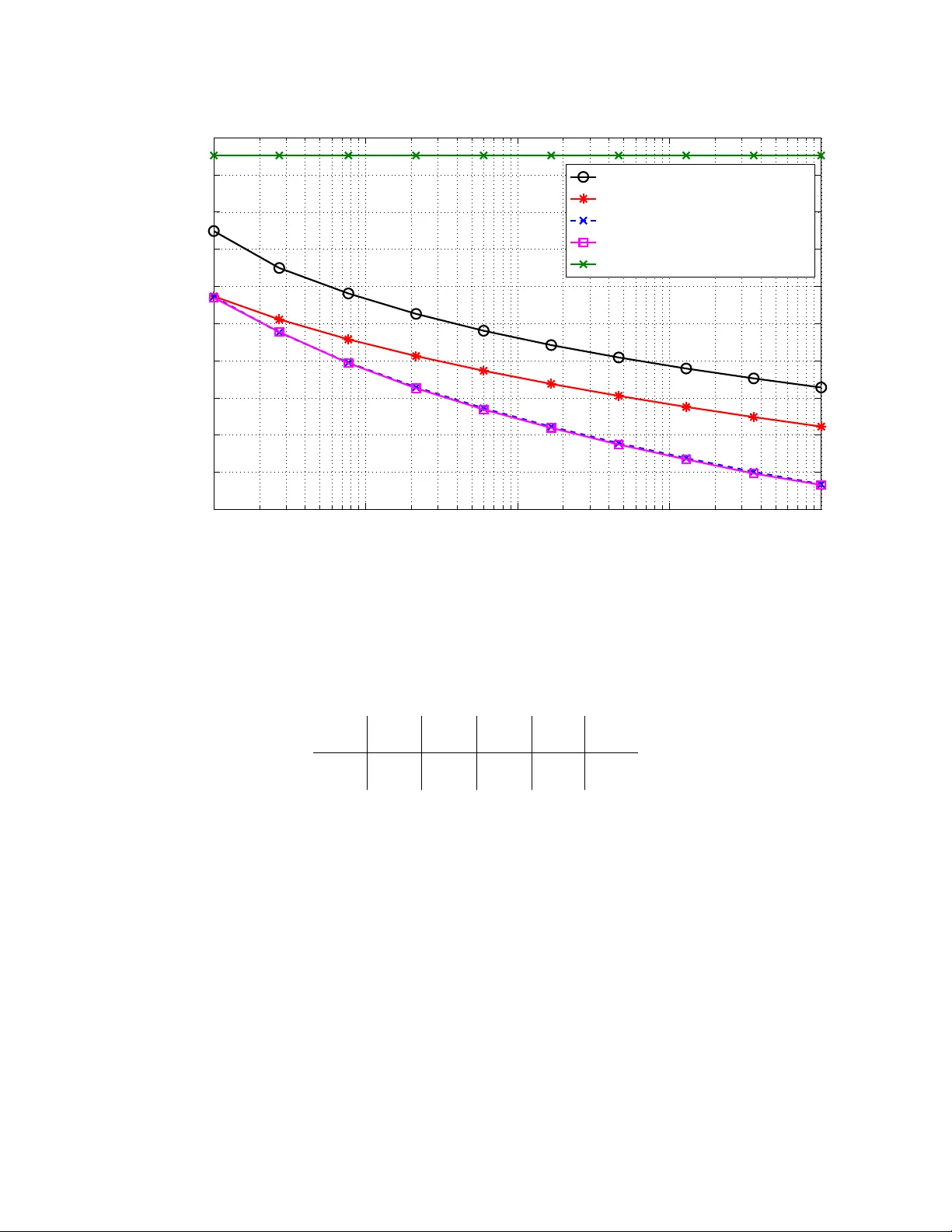
1 Ener gy Ef ficienc y of Opportunistic De vice-to-De vice Relaying Under Lognormal Shado wing S. M. Zafaruddin, Member , IEEE, Jan Plachy , Student Member , IEEE, Zdenek Becv ar , Senior Member , IEEE, and Amir Leshem, Senior Member , IEEE Abstract Energy consumption is a major limitation of lo w po wer and mobile de vices. Ef ficient transmission protocols are required to minimize an energy consumption of the mobile de vices for ubiquitous con- nectivity in the next generation wireless networks. Opportunistic schemes select a single relay using the criteria of the best channel and achiev e a near-optimal di versity performance in a cooperativ e wireless system. In this paper , we study the energy ef ficiency of the opportunistic schemes for device- to-device communication. In the opportunistic approach, an energy consumed by devices is minimized by selecting a single neighboring device as a relay using the criteria of minimum consumed ener gy in each transmission in the uplink of a wireless network. W e deri ve analytical bounds and scaling laws on the expected ener gy consumption when the de vices experience log-normal shado wing with respect to a base station considering both the transmission as well as circuit energy consumptions. W e show that the protocol improves the energy efficienc y of the network comparing to the direct transmission e ven if only a few de vices are considered for relaying. W e also demonstrate the effecti veness of the protocol by means of simulations in realistic scenarios of the wireless network. Index T erms S. M. Zafaruddin and Amir Leshem are with Faculty of Engineering, Bar-Ilan Univ ersity , Ramat Gan 52900, Israel (email: { smzafar , leshema } @biu.ac.il ). Jan Plachy and Zdenek Becvar are with Dpt. of T elecommunication Eng., Faculty of Electrical Engineering, Czech T echnical University in Prague, Czech Republic (email: { jan.plachy , zdenek.becvar } @fel.cvut.cz). This work was supported by Grant No. 8G15008 funded by MEYS in the framework of the Czech-Israel project MSMT - 10795/2015-1 and by the Israeli Ministry of Science and T echnology under grant 3-13038 for cooperation with the Czech Republic, and by ISF grant 903/2013. S. M. Zafaruddin was partially funded by the Israeli Planning and Budget Committee (PBC) post-doctoral fellowship. 2 5G, device to de vice (D2D) communications, energy efficienc y (EE), log-normal shadowing, op- portunistic carrier sensing, relaying. I . I N T RO D U C T I O N The upcoming 5G technology is expected to deli ver high-speed data transmission in order of tens of Gbps [1], [2]. This will improve the quality of service of existing multimedia applications and will pav e the way for more ambitious applications such as T actical Internet, Internet of Things (IoT), Internet of vehicles (IoV), Machine to Machine (M2M) communications, and e- healthcare [3]. These rate-demanding services are highly energy-consuming and would increase run-time usage of devices. The devices are equipped with batteries of a limited capacity , which can quickly run down if the energy consumption is not addressed properly . Ef ficient transmission protocols are needed to reduce the ener gy consumption of mobile de vices since improvement in battery capacity is unable to keep pace with increasing power dissipation of signal processing and transmission circuits. In addition to con ventional quality of service parameters, such as spectral ef ficiency and latency , also energy ef ficiency (measured in bits/Joule) has become an important feature of wireless networks [4], [5], [6]. Optimized allocation of resources (typically bandwidth and po wer) provides substantial energy ef ficiency gains, ho wev er , at the cost of throughput reduction for various wireless systems [7]– [11]. T o improv e the energy efficienc y of wireless networks, cooperativ e relaying techniques hav e been in vestigated (see, e.g., [12]–[14]) and energy-ef ficient multi-relay selection schemes with po wer control hav e been proposed (see, e.g., [15]–[17]). Ho we ver , the ener gy ef ficiency in cooperati ve communication can degrade as the number of cooperators rises [18]. In this paper , we focus on analyzing a protocol with a single-relay selection that minimizes the transmission energy and increase the energy ef ficiency of all de vices in a wireless network. The single relay-based cooperati ve transmission pro vides significant performance impro vement by exploiting div ersity from spatially distrib uted nodes in a wireless network [19]–[25]. The criteria for relay selection is based on the quality of channel or the signal to noise ratio (SNR) at the relays. This scheme is very popular when attempting to minimize transmission energy and maximize the lifetime of wireless sensor networks in particular [26]–[32]. It is noted that the state of the art cooperativ e schemes select a single device from the whole network which increases ov erhead energy and latency of the network, especially in a large network setup. Further , low 3 complexity distributed relay selection protocols are desirable since computational comple xity and the ov erhead of the optimal centralized scheduling are extremely high. In recent years, distrib uted solutions for resource allocation problems hav e been proposed using opportunistic carrier sensing [27], [29], [30], [33]–[37]. In [32], a power allocation is used to optimize either the energy consumption per bit or the lifetime of the network. The distributed implementation of this protocol exploits the timer-based relay selection proportional to the instantaneous channel [19]. It should be noted that a relay scheduling scheme with po wer control requires a solution in volving linear programs at each node. Moreover , the circuit po wer consumption is not considered in these papers, so that the solution may be sub-optimal. It is noted that when the operating transmission range is relati vely small, the po wer consumed in the baseband processor and in other components in the RF chain might be much greater than the po wer consumed by the transmitter po wer amplifier . Moreov er , minimizing transmission po wer does not correspond directly to reduction in energy consumption due to energy consumption in the circuitry of the device [6]. De vice to device (D2D) communication has emerged as a potential technique to reduce the energy consumption of mobile networks and is considered as one of the ke y techniques for the L TE (Long T erm Evolution) based cellular networks [38]–[41]. The D2D communication enables de vices to directly communicate with each other without transversing the data through a base station (BS). Recent works [42]–[46] sho w that the de vices can work as relays to av oid deplo yment and maintenance of con ventional relays. Relay assisted D2D can lev erage maximum potential of the D2D communication in v arious practical scenarios, such as when the distances between D2D pairs are longer or when the de vices experience strong fading. In this context, an opportunistic scheduling of de vices is shown to perform well for impro ved spectral ef ficiency [42]. The authors in [45] provide a geometrical zone for ener gy efficient D2D relaying. Furthermore, an experimental analysis of out-band D2D relaying scheme is presented to integrate D2D communications in cellular network [46]. Performance for D2D communication under dif ferent fading en vironments is recently in vestig ated (see [47], [48], and references therein). In [49], the author in vestigated the performance of opportunistic techniques for a verage signal- to-noise ratio improvements in wireless sensor network under large scale channel effects. The log-normal shado wing en vironment is common in various practical scenarios including shopping malls, offices, univ ersity b uilding [50]. In this paper , we analyze the opportunistic relaying in the paradigm of D2D communication and 4 study the opportunistic schemes with a single relay selection to minimize ener gy consumption of the de vices in a wireless network. The D2D communication ensures that the energy consumed for the data relaying is ne gligible, and that the selection of the relaying device e xploits the di versity from neighboring devices in order to minimize the energy consumed by the de vices for forwarding the data to the BS. The opportunistic device-select relaying (DSR) protocol selects a single device based on an instantaneous transmission energy including the energy consumed in the circuitry of the de vices and overhead energies required for relay selection. The DSR is implemented in a distributed way using the opportunistic carrier sensing algorithm for the selection of the device. This builds on the single hop protocol developed in [30], with a proper adaptation to the two-hop case as well as an adaptation of the opportunistic scheduling considering the transmission energy . W e deriv e closed form analytical bounds law on the expected energy consumption of the DSR protocol where the devices experience log-normal shadowing as well as path loss inside a b uilding or densely populated areas with respect to the BS whereas the devices close to the source device experiences strong signal under Rayleigh fading channel. W e also deri ve a scaling law on the expected energy consumption with respect to the number of devices, and show that the proposed scheme improves the ener gy ef ficiency of the network comparing to the direct communication using only fe w de vices of the network. A simple po wer control at the relays is presented to minimize the transmission energy . Finally , we demonstrate the effecti veness of the protocols with a numerical analysis, using parameters from realistic mobile networks, and we compare it to state of the art solutions. The rest of this paper is org anized as follows. Section II defines the system model. The proposed protocol for D2D relaying is described in Section III. Performance analysis of the DSR protocol is presented in Section IV . Section V provides performance e valuation using common scenarios considered for cellular networks. Section VI concludes the paper . I I . S Y S T E M M O D E L W e consider a single-cell network in which a BS serv es N single-antenna de vices, which are uniformly distrib uted in the network. W e consider data transmission to the BS in the uplink direction. W e consider the wireless network where the devices experience log-normal shado wing as well as path loss inside a building or densely populated areas with respect to the BS. This type of fading en vironment is common in v arious practical scenarios including shopping malls, 5 i j B S ℎ 𝑛 n ℎ 𝑖 ( 𝑑 ) D 2 D R e l a y i n g ℎ 𝑖 ℎ 𝑗 S o u r c e D e v i c e D 2 B S C h a n n e l L o g - N o r m a l S h a d o w i n g D 2 D C h a n n e l R a y l e i g h F a d i n g D i r e c t T r a n s m i s s i o n R e l a y e d T r a n s m m i s i o n Fig. 1. D2D relaying in the uplink communication of a single cell network. of fices, uni versity b uilding, etc. These scenarios impose significant constrains and limitations on communication with the far away destination, because of the signal attenuation due to walls. This drawback becomes much more pronounced at high frequencies, such as millimeter-wa ve communications (a ke y enabler for next generation networks [51]), where quality of direct transmission is weak. W e focus on a two-hop transmission model, where a source device can either transmit data directly to the BS or relay the data to a nearby device, which forwards the data to the BS, as depicted in Fig. 1. In a transmission slot, all de vices are allocated with a unique resource block (RB) by the BS to av oid inter -carrier interference between devices. In the direct transmission, the receiv ed signal at the BS from the i -th source device is giv en as: y BS = √ P h i x i + w , (1) where P is the transmit po wer , h i is the channel response between the i -th device and the BS, x i is the transmitted signal with unit power E [ | x i | 2 ] = 1 , and w ∼ C N (0 , N 0 ) is the zero-mean additi ve white Gaussian noise (A WGN) with power N 0 . The additi ve noise contains thermal noise and other interference terms (if any) which may increase the background noise lev el of the BS. 6 Since long term path loss dominates the short term fading, and ov er longer time scales Rayleigh fading is a veraged out, we model the amplitude po wer | h i | 2 as log-normal distributed: | h i | 2 = GR − α i i · 10 S i 10 , i = { 1 , 2 , · · · N } (2) where R i is the distance from the i -th device to the BS, and α i is the path loss coef ficient. The term S i ∼ N (0 , σ 2 ) is normal such that 10 S i 10 is log-normally distributed. The parameter σ is known as the dB spread or the shadowing factor . The term G is the normalizing factor for the path loss. Using (2), we can represent the log-normal fading channel as normal taking the logarithm of channel gain as: 10 log 10 | h i | 2 = X i ∼ N (10 log 10 R − α i + 10 log 10 G, σ 2 ) . If the direct transmission is not ener gy-efficient (e.g. due to shado wing ef fect reflected in the channel h i ) the source de vice sends data to a relay de vice using D2D communication. The recei ved signal at the n -th relay de vice is giv en as y (d) n = √ P h (d) i x i + v , (3) where h (d) i is the channel response between the i -th source de vice and the selected relay device, and v is A WGN with power N 0 including interference at the relay de vice. Since the quality of signal receiv ed at the relay is high, a DF protocol is used at the relay to transmit the data from the source device to the BS. It is noted that all de vices use different RBs separated in time and frequency , and thus there is no interference ev en if a single relay device receives signal from multiple source devices as these are sent at different RBs. W e assume fading amplitude | h (d) i | between the i -th source device and the relay device as Rayleigh distributed such that | h (d) i | 2 = r − α (d) i · F i , (4) where F i follo ws the exponential distribution, r i is the distance from the i -th source de vice to the selected relay device, and α (d) is the path loss exponent between them. Since de vices are close each other in D2D communication, the relay devices receiv e signal at a very high SNR, and thus consume negligible energy compared with the direct transmission. I I I . D E S C R I P T I O N O F T H E P R OT O C O L In this section, we describe the proposed protocol and the criteria used in which devices cooperate with each other to minimize transmission energy and to impro ve energy ef ficienc y of the network. Although the description of the protocol can fit in many source-relay-destination 7 frame works, we focus on an uplink communication of the wireless network. W ithout loss of generality , we assume that there is a single source de vice in ev ery transmission slot. A. Ener gy Consumption W e assume transmissions of packets with a fixed length of L bits in a RB transmitted by the de vice to the BS in each transmission slot. W e assume that the fading channel is constant for the duration of the RB of the source device. W e assume that all de vices transmit with equal po wer P . W e denote the circuit power by P ckt i for the i -th de vice. Since the po wer dissipated in the transmitter and recei ver circuits is different for different de vices, we assume that the circuit po wer transmission of the de vices is uniformly distributed between P ckt min and P ckt max . W e denote the initial energy of the i -th device by E in i . Using (1), the energy consumed by the i -th source device to transmit its data directly to the BS is: E i = ( P + P ckt i ) · L B log 2 (1 + γ i ) = η 1 10 log 10 (1 + γ i ) + η 2 P ckt i 10 log 10 (1 + γ i ) (5) where B is the transmission channel bandwidth, η 1 = 10 log 10 (2) P L/B , η 2 = η 1 /P , and γ i = | h i | 2 P N 0 is the recei ved signal-to-noise-ratio (SNR) at the BS when the signal is transmitted from the i -th de vice. Note, that as we assume the DF relaying, the energy is computed based on optimal coding scheme between the source and the relay , and a different rate is used for the second hop. From (5), it can be seen that a minimization of the transmit power does not correspond to the minimum energy transmission. Here, we provide a simple optimal transmit power control strategy using local measurements. Using first order deriv ati ve of (5) with respect to P , an optimal transmit power P ∗ can be obtained using the solution of the follo wing logarithmic equation: (1 + | h i | 2 N 0 P ∗ ) log(1 + | h i | 2 N 0 P ∗ ) = | h i | 2 N 0 ( P ∗ + P ckt i ) (6) This optimal transmit power minimizes the transmission energy in the presence of circuit po wer . Using (3), the energy consumed by the D2D communication to relay a data of L bits is: E (d) i = η (d) 1 log e (1 + γ (d) i ) + η (d) 2 P ckt i log e (1 + γ (d) i ) (7) where η (d) 1 = log e (2) P d L/B , η (d) 2 = η (d) 1 /P (d) , and γ (d) i = | h (d) i | 2 P (d) N (d) 0 is the SNR at the relay de vice when the signal is transmitted from the i -th source de vice. Similarly , an optimal transmit po wer can be obtained for the relaying phase in the D2D communication. 8 B. Device Selection Metric For the relay selection, we consider tw o main components of the energy consumption: energy E (d) i computed in (7) for the D2D communication and energy E i computed in (5) to transmit the data to the BS from the i -th relay de vice. In contrast to the con ventional relay selection schemes based on the SNR or fading channels [19], [52], the relay selection criteria for the proposed protocol is based on the total consumed energy as: n = argmin 1 ≤ i ≤ N { E i + E (d) i + E RELA Y ov } , (8) where E RELA Y ov is the o verhead energy required for relay selection in the case of D2D communi- cation. The dual-hop DSR selection criteria in (8) is useful when both hops are symmetric and consumes a similar amount of energy . Howe ver , the scenario considered in this paper is highly imbalanced in both the hops because the ener gy consumption of the D2D relaying (strong signal due to proximity of the de vices) is lower than the energy consumed in the second hop (users are generally at a larger distance from the BS). Hence, the selection criteria in (8) is reduced to relay selection based on the energy consumption of the second hop only: n = argmin 1 ≤ i ≤ N { E i } . (9) W e define the single-hop selection criteria in (9) as the DSR. Since we use D2D communication in the first hop, the single hop relay selection in (9) is near-optimal and depends only on the channel quality between de vices and the BS (which is av ailable for the existing operation of the mobile netw ork). This a voids energy o verhead to estimate the channel using the request-to-send (R TS) signal in the first hop and clear-to-send (CTS) signal in the second hop as required in [32]. In what follows, we describe a low complexity implementation of DSR protocol since a centralized implementation of the protocols would be consuming lar ge energy ov erhead due to control signaling. C. Distributed Pr otocol For distributed implementation of the proposed protocols, we use the back-off principle of the carrier sensing multiple access (CSMA) in the TCP/IP MAC layer supported with the transmission ener gy from the PHY . W e define an increasing function f ( E ) designed judiciously 9 𝜏 𝑛 = 𝑓 ( 𝐸 𝑛 ) 𝑡 0 𝑡 0 + 𝜏 𝑛 + 𝑡 𝑝 , 𝑛 𝜏 𝑖 = 𝑓 ( 𝐸 𝑖 ) 𝜏 𝑗 𝑅 𝑇 𝑅 ( 𝐿 ( 𝑑 ) ) 𝑡 0 + 𝜏 + 𝑡 𝑝 R e l a y i n g D e l a y C T R C T R 𝐿 𝐿 D F D e l a y P r o p a g a t i o n D e l a y S o u r c e D e v i c e , D e v i c e n D e v i c e j 𝑡 𝑝 , 𝑛 𝑡 𝑝 , 𝑗 𝜏 𝑡 ℎ 𝒊 R e l a y S e l e c t i o n R e l a y S e l e c t i o n R e l a y S e l e c t i o n D e v i c e n D e v i c e j D e v i c e i R e l a y N o D a t a N o D a t a R e l a y i n g N o D a t a DT F r e q u e n c y T i m e B S (a) T iming diagram and resource block allocation. E 𝐸 1 𝐸 2 𝜏 2 𝜏 1 𝜏 = 𝑓 ( 𝐸 ) 𝐸 1 < 𝐸 2 < 𝐸 𝑠 𝐸 𝑠 𝜏 𝑠 (b) Function f ( E ) . Fig. 2. Schematic diagram of the DSR protocol for three devices with transmission energy E n < E j < E i . (see Fig. 2a) such that back-off time τ i = f ( E i ) , i = 1 · · · N of the devices computed with distinct energy index E i , i = 1 · · · N (gi ven in equation (5)) provides enough back-of f range to minimize collisions without incurring high delay by the use of τ . In the seminal paper , Blestsas 10 et. al [19] describe a timer-based distributed protocol for relay selection (controlled by the BS with R TS and CTS signals) using instantaneous channel information of both hops. Zhou et. al [32] use the protocol in [19] for the relay selection using power control at each relays for energy-ef ficient transmissions. Our protocol differs from [19], [32] as follows: (i) our protocol directly minimizes energy at each transmission instead of div ersity gain for rate performance using the instantaneous channel [19] or po wer control [32]; (ii) no control signaling from the BS for relay selection is needed; (iii) our proposed protocol reduces hidden node problem due to the D2D communication. The developed DSR protocol is implemented in follo wing steps (see Fig. 2): 1) Request to Relaying (R TR): First, the i -th source device sets its back-off time to τ i = f ( E i ) and broadcasts an R TR message (with fields such as user ID) with a transmit power to be receiv ed by the devices in close proximity . The transmit power for the R TR message can be controlled to minimize the ov erhead energy and a void selecting relays incurring high energy consumption in relaying. It is noted that structure of R TR is quite dif ferent from R TS which contains many control bits. All the de vices are capable to decode the R TR message with the CSI estimated using the R TR message if not kno wn. The CSE is known if de vices are already in the discov ery mode complaint with the proximity services of 3GPP-L TE [53]. The R TR transmission costs an ener gy consumption E R TR tx to the source device. The energy ov erhead in decoding the R TR per device is E R TR rx . The source de vice w aits for a reply from a potential relay for a duration of τ i + τ th , where τ th is an additional delay to compensate for the propagation delays in D2D communication. This delay corresponds to relay selection overhead, as depicted in Fig. 2. If the device does not recei ve a reply from an y device for relaying in the time limit of τ i + τ th , it directly transmits to the BS (step 4), otherwise the data is transmitted through a relay . 2) Distributed Relay Selection: Upon the receipt of a R TR message from the source, each de vice sets its back-off time to τ j = f ( E j ) , j · · · N − 1 . In the opportunistic DSR scheme, the n -th device selected using the criteria in (9) has the lo west back-of f time, and hence occupies the channel first by responding to the source with a CTR message after a waiting period τ n < τ j , n 6 = j . Once the selected device transmits the CTR message to the source, all other de vices ov erhear the CTR message (or just a b usy tone), and quit the process of relay selection for the giv en request from the i -th source device. The overhead energies for a response from relay de vice are: transmission of CTR message E CTR tx and reception of CTR message E CTR tx . 11 3) Source to Relay T ransmission: Upon the successful decoding of the CTR message, the source device sends the data packet L to the selected relay device with a transmit energy cost E d i as computed in (7). Using the DF protocol, the selected relay device decodes the data from the source device, encodes it, and transmits to the BS. The DF protocol requires the CSI at the relay device. This can be estimated using the R TR message from the source de vice after the decision on relay selection. The energy ov erhead at this stage is: CSI estimation energy E CSI , transmit energy cost E d i , decoding energy E DEC , and encoding energy E ENC . 4) Data T ransmission: Finally , transmission of data is accomplished by direct transmission from the source or by the relay de vice. The energy consumption in this phase is E i as computed in (5). D. Challenges of Distributed Implementation Although distributed implementation simplifies the relay selection and transmission comparing to the centralized method, it poses few challenges that needs consideration. W e no w describe some practical challenges, which may impact the distributed implementation, and their solutions as follows: 1) Coexistence of direct and r elay tr ansmission: All de vices have unique RB assigned by the eNB and relay devices use the RB of the source device for both D2D communication and data transmission. If a single device happens to act as the source for its own data and as the relay for other source, the data transmission can be done simultaneously . 2) Multiple users with same back-of f time: As described in [19], the probability that two users hav e equal back-off time is zero. Ho wev er , there might be scenarios where dif ference between the multiple back-off time can be lower causing collision of CTR messages at the source device. Ho wev er due to dif ferent propagation delays probability of this case is very low . In any case, the source device directly transmits after waiting for a specified time. 3) Hidden node pr oblem: The broadcast of R TR message informs de vices in proximity about relay selection. Ho wev er , some de vices o verhearing R TR can be hidden from other relay devices. Hence, a hidden device from already selected relay device may still be in the contention for the channel and sends CTR to the source device after its back-off time. This is a voided by the transmission of data from the source de vice which is ov erheard by all devices in proximity . 4) T ransmission delay: The relay selection based on CSMA increases an additional delay corresponding to the back-off time τ . In order to limit the additional delay in the relay selection 12 process or delay due to unsuccessful reception of CTR (in case two devices hav e almost the same back-off time τ ), the source de vice transmits its data directly to the eNB after waiting τ i + τ th , where τ i is the back-of f time of the source device and τ th is an additional delay to wait for successful reception of a CTR message. Ho wev er , a use of the relay with best channel significantly reduces time to transmit the data to the BS (higher throughput) and thus leads to a reduced transmission time, compared to the direct transmission. In the following sections, we analyze the performance of the proposed scheme by deriving bounds on the expected energy consumption, and by means of simulation results in a scenario of a realistic mobile network. I V . P E R F O R M A N C E B O U N D S O F O P P O RT U N I S T I C D S R In this section, we discuss v arious components of the consumed energy , deri ve bounds on expected ener gy consumption of direct transmission and relay transmission, and perform an analysis on ov erhead energy of D2D relaying. A. Ener gy Consumption of DSR Gi ven the steps of distributed relaying described in the pre vious section, the total energy consumption using the DSR protocol is: E DSR = p ( E RELA Y + E D2D + E RELA Y ov ) + (1 − p )( E DT + E DT ov ) (10) where p is the probability of the relay-assisted data transmission, E RELA Y is the energy consumed by the selected relay to transmit the data packet to the BS, E D2D is the data transmission energy by the source device to another relay in D2D communication, E RELA Y ov = E R TR tx + ( N − 1) E R TR rx + E CTR tx + E CTR rx + E CSI + E DEC + E ENC is the ov erhead ener gy required for relay selection in the case of D2D communication, E DT denotes the ener gy consumed for data transmission directly to the BS when the direct transmission is found to be more energy-ef ficient than the relay-assisted transmission, and E DT ov = E R TR tx + ( N − 1) E R TR rx is ov erhead energy for the relay selection. It is noted that the direct transmission without DSR protocol does not incur any ov erhead energies. Ho wev er , the ov erhead energies in the DSR protocol are low since the signaling in volv ed is very short and the signaling messages are sent to other local devices with very lo w power or at a very high data rate. 13 W e compare the transmission energy of the DSR protocol E DSR with the component of the transmission energy for only the direct transmission E DT . W e analyze the components of energy consumption in (10), and demonstrate that the DSR protocol consumes less ener gy than the direct transmission. B. Expected Ener gy Consumption of Dir ect T r ansmission W e deri ve an e xpression on the e xpected consumed energy without D2D relaying. In this scenario, each device transmits its o wn data to the BS. Using a simple inequality , 10 log 10 ( γ ) ≤ 10 log 10 (1 + γ ) ≤ 1 + 10 log 10 ( γ ) in (5), we get bounds on energy consumption for the direct transmission as η 1 + η 2 P ckt 1 + X ≤ E DT ≤ η 1 + η 2 P ckt X , (11) where X = 10 log 10 ( γ ) . Since γ is log-normal distributed with a spreading parameter σ 2 in dB, X ∼ N ( ¯ γ , σ 2 ) with ¯ γ = 10 log 10 R − α + 10 log 10 G + 10 log 10 P / N 0 is the a verage SNR per de vice in dB. Considering different types of user de vices in a network, we model the circuit po wer to be uniformly distributed between P ckt min and P ckt max representing minimum and maximum circuit transmit powers, respecti v ely . W e assume circuit transmit power independent of transmit po wer since the v ariation on the circuit transmit power with the transmit power is insignificant. W e compute the upper bound, b ut similar e xpression hold for the lo wer bound, replacing ¯ γ with ¯ γ + 1 . T aking expectation in (11) and noting the independence between numerator and denominator terms, we get an upper bound on the expected energy consumption with direct transmission defined as ¯ E DT ≤ E [ η 1 + η 2 P ckt ] E [ 1 X ] = η 1 + η 2 E [ P ckt ] 1 √ 2 π σ Z ∞ γ th 1 x e − ( x − ¯ γ ) 2 2 σ 2 d x (12) where γ th in dB is a SNR threshold above which the communication occurs. The threshold SNR is selected to achiev e a minimum data rate requirement belo w which communication is possible. Theor em 1: If P ckt min and P ckt max are minimum and maximum circuit transmit power of all devices, respecti vely , γ th is the threshold SNR in dB, and η 1 = 10 log 10 (2) P L/B , η 2 = η 1 /P , then bounds on the expected energy with direct transmission in a log-normal fading channel with average SNR ¯ γ and v ariation σ in dB are gi ven as ( η 1 + 0 . 5 η 2 ( P ckt max + P ckt min )) ( ¯ γ + 1) exp ( σ 2 2( ¯ γ + 1) 2 ) Q ( σ ( ¯ γ + 1) + ( γ th − ¯ γ − 1) σ ) ≤ ¯ E DT ≤ ( η 1 + 0 . 5 η 2 ( P ckt max + P ckt min ))[ I DT 1 ( ¯ γ , σ ) + I DT 2 ( ¯ γ , σ )] , (13) 14 where I DT 1 ( σ ) = σ √ 2 π (2 σ 2 + ¯ γ 2 ) h 2 √ 2 σ log e ( ¯ γ γ th ) log e (1 + ( ¯ γ − γ th √ 2 σ ) 2 ) + arctan ( ¯ γ − γ th √ 2 σ ) 2 i I DT 2 ( σ ) = exp[ − ¯ γ 2 / 2 σ 2 ] 4 √ 2 π σ [2 π Erfi( ¯ γ √ 2 σ ) − 2 E 1 ( ¯ γ 2 2 σ 2 ) + log e ( ¯ γ 2 2 σ 2 ) + 4 log e ( √ 2 σ ¯ γ ) − log e ( σ 2 ¯ γ )] (14) Pr oof: The proof is presented in Appendix A. It can be seen from the bounds in (13) that a higher av erage SNR reduces the ener gy consumption of the direct transmission. The deri ved expressions are computable in terms of kno wn functions. No w , we analyze the relaying protocol where a best relay is selected to minimize consumed energy , and sho w that the proposed scheme consumes less energy than the direct transmission and the energy gain increases with the number of participating relay devices. C. Expected Ener gy Consumption for Relay Selection T o simplify the model, we assume that the relaying de vices are in the vicinity of the source, so that the path loss of all possible relays are similar , b ut spread enough to experience independent shado wing. T o compute energy consumed by the relaying, we deriv e expression for the expected energy consumed E RELA Y by the device to the BS in log-normal fading with the selection criteria defined in (9). Using the selection criteria in (9) for the log-normal shadowing (de vice to eNB transmission) in (11), we get: E RELA Y ≤ η 1 + η 2 P ckt (1) X ( n ) (15) where X ( n ) = max( X 1 , X 2 , X 3 , · · · , X N ) , X i = 10 log 10 ( γ i ) , and P ckt (1) = min( P ckt 1 , P ckt 2 , P ckt 3 , · · · , P ckt N ) Since we assume similar path loss for all device (i.e., relays are in the vicinity of the source) the X i are i.i.d.; it follo ws from standard order statistics that the CDF of X ( n ) is gi ven as F X ( n ) ( x ) = [ F X ( x )] N , where F X ( x ) = [1 / 2 + 1 / 2erf ( x − ¯ γ √ 2 σ 2 )] is the CDF of normal distribution. The PDF of the maximum X ( n ) is f X ( n ) ( x ) = N [ F X ( x )] N − 1 [ f X ( x )] where f X ( x ) = 1 √ 2 π σ 2 e − ( x − ¯ γ ) 2 2 σ 2 is the PDF of normal distribution. The expected consumed energy with the best select relay scheme ¯ E RELA Y = E [ E RELA Y ] is expressed as: ¯ E RELA Y ≤ E [ η 1 + η 2 P ckt (1) ] Z ∞ γ th N x [ F X ( x )] N − 1 [ f X ( x )]d x, (16) 15 Using integration in parts and F X ( x ) = Q ( ¯ γ − γ th σ ) , we can represent (16) as: ¯ E RELA Y ≤ E [ η 1 + η 2 P ckt (1) ] I RELA Y 1 ( N , σ ) + I RELA Y 2 ( N , σ ) − 1 γ th Q N ( ¯ γ − γ th σ ) (17) where I RELA Y 1 ( N , σ ) = Z 0 γ th − µ σ 1 ( xσ + ¯ γ ) 2 (1 − Q ( x )) N d x I RELA Y 2 ( N , σ ) = Z ∞ 0 1 ( xσ + ¯ γ ) 2 (1 − Q ( x )) N d x (18) Computable bounds and analytical expressions can be obtained from (17) using Chernoff bounds (upper and lo wer as giv en in [54]) on the Q-function that makes integration tractable and in a closed form. Theor em 2: If P ckt min and P ckt max are minimum and maximum circuit transmit power of all devices, respecti vely , γ th is the threshold SNR in dB, and η 1 = 10 log 10 (2) P L/B , η 2 = η 1 /P , then the expected ener gy consumption with a single relay selection from N devices in a log-normal fading channel with average SNR ¯ γ and v ariation σ in dB is gi ven as ¯ E RELA Y ≤ ( η 1 + η 2 ( P ckt max + N P ckt min ) N + 1 ) I RELA Y 1 ( N , σ ) + I 2 RELA Y (N , σ ) − 1 γ th Q N ( ¯ γ − γ th σ ) (19) where Q denotes the standard Gaussian Q function, and I RELA Y 1 ( N , σ ) ≤ σ (2) N (2 σ 2 + N ¯ γ 2 ) 2 " 2 σ 2 (2 σ 2 + N ¯ γ 2 ) 1 γ th − 1 ¯ γ + 4 N σ 2 ¯ γ log γ th ¯ γ + 2 N σ µ log 1 + N 2 ( ¯ γ − γ th σ ) + √ 2 N ( N ¯ γ 2 − 2 σ 2 ) arctan p N / 2( ¯ γ − γ th σ ) # (20) I RELA Y 2 ( N , σ ) ≤ σ N X r =0 N / 2 2 r 1 4 r Ψ( r , σ, ¯ γ ) − N X r =0 N / 2 2 r + 1 [ f ( κ )] 2 r +1 Ψ((2 r + 1) κ, σ , ¯ γ ) , where f ( κ ) ≤ p e/ 2 π ( √ κ − 1) /κ, and Ψ( r, σ, ¯ γ ) is giv en in (33) Appendix B . (21) Pr oof: The proof is presented in Appendix B. The numerical analysis shows that I RELA Y 2 ( N , σ ) is dominant and bounds on the Q-function are not always accurate. W e improv e the accuracy of analysis in Theorem 2 by using an approximation on the Q-function in the follo wing corollary . 16 Cor ollary 1: Approximating the Q-function, a closed form e xpression on I RELA Y 2 ( N , σ ) is: I RELA Y 2 ( N , σ ) ≈ σ N X k =0 N k ( − 1) k A ( k ) γ max ¯ γ 2 + ¯ γ σ γ max + B ( k ) ¯ γ log(1 + σ γ max ¯ γ ) + C ( k ) log | 1 + γ max α ( k ) | + D ( k ) log | 1 + γ max β ( k ) | ! A ( k ) = σ 2 ( ¯ γ − α ( k ) σ )( ¯ γ − β ( k ) σ ) , B ( k ) = σ 2 ( α ( k ) σ + β ( k ) σ − 2 ¯ γ ) ( ¯ γ − α ( k ) σ ) 2 ( ¯ γ − β ( k ) σ ) 2 , C ( k ) = 1 ( α ( k ) − β ( k ))( α ( k ) σ − ¯ γ ) 2 , D ( k ) = 1 ( α ( k ) − β ( k ))( β ( k ) σ − ¯ γ ) 2 , { α ( k ) , β ( k ) } = − k q 2 ± q k 2 q 2 2 − 4 k q 1 q 2 − 4 k q 1 / 2 k q 1 q 1 = − 0 . 4920 , q 2 = − 0 . 2287 , q 3 = − 1 . 1893 . (22) Pr oof: The proof is presented in Appendix C. Finally , we deriv e an upper bound on the ener gy consumption and provide a scaling law for the reduction of energy with the number of de vices. Theor em 3: If P ckt min and P ckt max are minimum and maximum circuit transmit power of all devices, respecti vely , γ th is the threshold SNR in dB, and η 1 = 10 log 10 (2) P L/B , η 2 = η 1 /P , then the expected energy with a single relay selection from N devices in a log-normal shadow fading channel with av erage SNR ¯ γ and v ariation σ in dB is upper bounded as: ¯ E RELA Y ≤ η 1 + η 2 ( P ckt max + N P ckt min ) N + 1 1 2 N 1 γ th + 1 σ 1 ¯ γ + σ p c M ln( N ) + M − 1 X m =1 ( 1 1 + κN (1 − c m ) )( 1 ¯ γ + σ p c m − 1 ln( N ) (23) where M is a positi ve inte ger , κ = 0 . 3885 is a constant, and 0 ≤ c m ≤ 1 , c 0 = 0 , m = 1 , 2 , · · · M . Further , energy consumption scales as ¯ E RELA Y = O η 1 + η 2 P ckt min ¯ γ + σ p c M ln( N ) . (24) Pr oof: The proof is presented in Appendix D. From the scaling law in (24), it can be seen that the number of de vices improves the energy consumption. D. Expected Ener gy Consumption for D2D Relaying As discussed in the protocol description (Section III), the signaling in v olved in the relay selec- tion is very short and incurs negligible energy overhead. This is illustrated through simulations in realistic scenarios in the next section. Ho we ver , the ener gy ov erhead due to the data forwarding to the selected relay de vice in a fading en vironment and far apart from the source devices may increase the energy consumption significantly . This energy ov erhead can be minimized if the selection of relay is confined only to the de vices nearby to the source devices. In what follo ws, 17 we analyze this energy consumption under Rayleigh fading channel, and sho w that the energy consumed by relaying is also negligible in the D2D communication range. Under the Rayleigh fading channel model, the SNR γ ( d ) in (7) is exponential distributed with PDF f ( γ (d) ) = 1 ¯ γ (d) e − γ (d) / ¯ γ (d) where ¯ γ (d) is the average SNR. Using (7), the expected energy for D2D relaying: ¯ E D2D = η (d) 1 + η (d) 2 E [ P ckt ] 1 ¯ γ (d) Z ∞ γ (d) th 1 log e (1 + x ) e − x/ ¯ γ (d) d x (25) where γ (d) th is the threshold SNR in linear scale for D2D communication. Using the series expansion of exponential function in (25), we get an exact expression of the expected energy consumption in D2D relaying ¯ E D2D = ( η d 1 + 0 . 5 η (d) 2 ( P ckt max + P ckt min )) × ∞ X k =0 ( − 1) k k ! 1 ( ¯ γ (d) ) k +1 [ E i ( γ max + k γ max ) − E i ( γ (d) th + k γ (d) th )] . (26) W e also pro vide simple bounds on (25) in the follo wing Theorem: Theor em 4: If P ckt min and P ckt max are minimum and maximum circuit transmit power of all devices, respecti vely , γ th is the threshold SNR, and η (d) 1 = 10 log e (2) P (d) L/B , η (d) 2 = η (d) 1 /P (d) , then the expected energy consumption in D2D relaying under Rayleigh fading channel with average SNR ¯ γ (d) satisfies ( η (d) 1 + 0 . 5 η (d) 2 ( P ckt max + P ckt min )) 1 ¯ γ (d) log e (1 + ¯ γ (d) γ (d) th ) − 1 ( ¯ γ (d) ) 2 log e (1 + ¯ γ (d) γ (d) th ) ≤ ¯ E D2D ≤ ( η (d) 1 + 0 . 5 η (d) 2 ( P ckt max + P ckt min )) ¯ γ (d) ¯ γ (d) + γ (d) th + 1 ¯ γ (d) + γ (d) th log e (1 + ¯ γ (d) γ (d) th ) (27) Pr oof: The proof is giv en in Appendix E. From (26) and (27), it can be seen that the expected energy decreases with an increase in the av erage SNR at the relaying de vice. Since the relay devices have high SNR due to close proximity with the source de vice in the D2D communication, the energy overhead of the relaying among de vices is negligible as compared with the transmission of data to the BS. V . S I M U L A T I O N A N D N U M E R I C A L A N A L Y S I S In this section, we demonstrate the effecti veness of the proposed protocol through numerical analysis and simulations carried out in MA TLAB. First, we verify the analytical bounds and scaling law deri ved in this paper by considering a simplified transmission model and without overhead energies, as depicted in Fig. 3. For each 18 10 1 10 2 10 3 10 4 10 5 11.5 12 12.5 13 13.5 14 14.5 15 15.5 16 16.5 Number of Devices (N) Expected Energy Consumption (Joule) DSR Upper Bound, Eq. (19) DSR Scaling Law, Eq. (24) DSR Numerical DSR Simulation Direct Fig. 3. V erification of scaling law and bounds. T ABLE I A V E R A G E E N E R G Y C O N S U M P T I O N ( I N µ J ) O F V A R I O U S O V E R H E A D S O B TA I N E D U S I N G S I M U L A T I O N U N D E R 3 G P P M O D E L . ¯ E R TR tx ¯ E R TR rx ¯ E CTR tx ¯ E CTR rx ¯ E D2D tx ¯ E D2D rx 11.60 4.50 3.35 1.30 350.5 135.4 transmission, a packet length of L = 2 MB is considered. W e consider channel between devices to the BS to be log-normal distributed with a spreading factor of 4 dB and a path loss exponent α = 4 . The channel between de vices is assumed to be Rayleigh fading with a path loss exponent α = 3 . The transmit power for each de vice is set to 23 dBm. For scaling law verification, we consider M = 4 , c M = 0 . 99 , δ M = ln( N ) , δ 1 = δ M / 4 , δ 2 = δ M / 2 and δ 3 = 3 δ M / 4 . Fig. 3 verifies the analytical bounds and the deriv ed scaling law on the expected consumed ener gy in a network of 10 to 10 5 de vices situated uniformly at a distance of 300 m from the BS, situated in the center . Next, we demonstrate the proposed schemes under a more realistic scenario using the 3GPP 19 D2D channel model and simulation parameters in line with 3GPP recommendations [55]. W e emulate a single cell network with up to 150 de vices distrib uted uniformly in a radius of 50 m to 500 m with a BS in the center . The background noise for each de vice and the BS is taken as − 174 dBm/HZ. W e consider 20 dB of interference at the BS. W e assume equal transmit po wer ( 23 dBm) and equal initial energy of 0 . 72 mWh for all de vices. W e use the ener gy model presented in [56] to compute the energy consumption of the devices for communication with the BS or D2D communication. W e assume that the communication range for D2D relaying is 50 m. The transmission bandwidth for each device is 200 KHz. The channel between the device and the BS is urban macro log-normal shadowing (spreading factor 4 dB) while the channel between de vices is modeled as Rayleigh fading using Winner II [57]. For each transmission, a data packet length of L = 1024 bytes is considered, and the size of D2D request/reply data is L ( d ) = 10 bytes. In contrast to the existing performance ev aluations for relaying schemes, we also include the ov erhead ener gy into our simulation model. W e present the components of a verage consumed ener gy for various ov erheads in T able I. This is obtained using the realistic simulation in line with 3GPP recommendations and the 3GPP D2D channel model. W e compare the proposed algorithms with the opportunistic relaying (OR) selection criterion using the channel statistics for both hops [19] and the single hop (devices to the BS) [20]. These opportunistic schemes are fundamental in wireless networks to harness the multi-user di versity . For a comparison, we use the same network scenario i.e., selection of de vices within D2D range in contrast to the state of art procedure of selecting a relay device from the whole network. Ho wev er , we also demonstrate (in Fig. 8) the adv antage of selecting few nearby de vices to achie ve the near-optimal performance. In Fig. 4, we plot the expected consumed energy of the network by the DSR protocols and compare the performance with SNR-based opportunistic schemes. The figure sho ws that the DSR based schemes provide significant performance improvement in terms of the expected consumed ener gy compared to the direct communication with a fe w relaying de vices i.e, within N = 15 , as shown in Fig. 4. This happens because the log-normal shado wing of the second hop provides sufficient div ersity to achiev e the near-optimal performance with a fe w relaying de vices. Although the DSR selection criteria is based on the total consumed energy in contrast to the earlier SNR based OR scheme, the DSR achie ves the similar performance to the OR since the impact of overhead energies and energy consumed in the circuitry is insignificant in 20 10 20 30 40 50 60 70 80 5 10 15 20 25 30 Network size (N) Expected consumed energy [mJ] Direct OR (Both Hops)[19] OR (Single Hop)[20] DSR DSR (Both Hops) 16 16.02 16.04 16.06 16.08 16.1 6.76 6.77 6.78 6.79 6.8 6.81 Fig. 4. Expected consumed energy by the D2D opportunistic relaying schemes. the considered scenario. Fig. 4 also sho ws that the selection based on both hops performs very similar to the single hop schemes. The energy efficienc y of the network is depicted in Fig. 5. It can be seen that the network ef ficiency is increased by more than 4 times than the direct transmissions when N > 30 . As expected, the DSR achie ves the similar performance to the other opportunistic schemes. It can also be seen that the performance dif ference between the single-hop and the dual-hop is indistinguishable. This happens because the energy consumed by the devices in the second hop is dominant than the first hop (the second hop is limited by the log-normal shadowing and the BS is assumed to have an additional 20 dB of interference). T o this end, we compare the energy ef ficiency of the dual-hop schemes with the single-hop by neglecting the 20 dB of interference at the BS, as shown in Fig. 6. It can be seen that the DSR based on both hops achiev es the best performance with an increase of 50 Kbits/Joule comparing to the other schemes. Further , we analyze the expected number of transmissions before the battery of the first device is depleted, as sho wn in Fig. 7. It can be seen that the DSR (with both hops) outperform the 21 10 20 30 40 50 60 70 80 0.2 0.4 0.6 0.8 1 1.2 1.4 1.6 Network size (N) Network energy efficiency [Mbits/J] Direct OR (Both Hops)[19] OR (Single Hop)[20] DSR DSR (Both Hops) 16 16.02 16.04 16.06 16.08 16.1 1.206 1.207 1.208 1.209 1.21 1.211 Fig. 5. Network energy efficienc y of the D2D relaying schemes. other techniques, since it consumes the least energy for forw arding the data to the BS. The significant gain in the expected number of transmissions (in contrast to the other performance metrics such as expected energy consumption and ener gy ef ficiency) is due to the fact the small decrease in the transmission energy results into a significant cumulati ve gain in the number of transmissions by the dual-hop DSR when the first de vice depletes its energy . Finally , we demonstrate the use of D2D communication while selection of the relaying devices is limited to only nearby devices (considered in the range of 50 m). W e show the performance for the DSR and compare it with the existing methods of relay selection from the whole network, as depicted in Fig. 8. As demonstrated in Fig. 4 and Fig. 5, the DSR achiev es the near - optimal div ersity performance using fe w de vices only due to the log-normal shadowing. Thus, it is imperativ e to limit the relay selection to only fe w de vices since it reduces latency and minimizes the ov erhead required for the selection of relay . Fig. 8 sho ws that the performance of the DSR scheme is higher for lar ge networks when the relay is selected from only nearby de vices (considered in the range of 50 m). In case of relay selection from whole network, the overhead 22 5 10 15 20 25 30 35 40 1.6 1.65 1.7 1.75 1.8 1.85 1.9 1.95 2 2.05 2.1 Network size (N) Network energy efficiency [Mbits/J] OR (Both Hops) [19] OR (Single Hop) [20] DSR DSR (Both Hops) Fig. 6. Energy efficiency performance of the relaying schemes by neglecting the interference at the BS. in terms of energy increases due to a higher density of de vices (more devices out of which the relay can be selected). It is noted that the performance degradation due to the overhead energy depends on the size of R TS/CTS ov erhead message which is considered 1 % of the data length. Thus, in comparison to the existing protocol, the DSR has a higher performance gain in terms of energy efficiency for large networks, as depicted in Fig. 8. V I . C O N C L U S I O N W e ha ve studied opportunistic relaying schemes for D2D communication and we ha ve analyzed the energy consumed by the devices in a wireless netw ork. W e ha ve deri ved closed form expressions and analytical bounds on D2D relaying protocols under log-normal shadowing for both direct and relayed transmissions. The analytical expressions show that the opportunistic schemes can achieve significant performance gain when the devices are in heavy shadowing area with respect to the BS while the devices enjoy strong channel for inter -user D2D communication with ne gligible energy overhead. Further , the deri ved scaling law on the consumed energy 23 10 20 30 40 50 60 70 80 2400 2600 2800 Network size (N) Expected number of transmissions OR (Both Hops)[19] OR (Single Hop) [20] DSR (Both Hops) DSR Fig. 7. Expected number of transmissions of each devices until a device depletes its energy . sho w that a near-optimal performance can be achie ved in log-normal shado wing with a fe w de vices only . This reduces the latency and overhead energy consumed by the de vices in the selection of relays. W e consider a realistic cellular en vironment and show that the opportunistic D2D-relaying schemes improv es the energy efficienc y of the network comparing to the direct communication using only fe w de vices in the network. The results will be useful for millimeter - wa ve communications where non-line-of-sight communication can be very hard. A P P E N D I X A T H E O R E M 1 : E N E R G Y C O N S U M P T I O N I N D I R E C T T R A N S M I S S I O N First we prov e the upper bound. The integral in (12) can be represented as a sum of two integrals: I ub = 1 √ π h Z ¯ γ − γ th σ √ 2 0 1 ¯ γ − √ 2 tσ e − t 2 d t + Z ∞ 0 1 ¯ γ + √ 2 tσ e − t 2 d t i (28) Using exp[ − x 2 ] ≤ 1 1+ x 2 in the first integral, an upper bound on the integral I DT 1 ( ¯ γ , σ ) can be obtained by the partial fraction method. This has been presented in (14). Using standard 24 20 40 60 80 100 120 140 0.5 0.6 0.7 0.8 0.9 1 1.1 1.2 1.3 1.4 Network size (N) Network energy efficiency [Mbits/J] OR (All Devices) DSR (D2D<50m) Fig. 8. Performance comparison of single-hop DSR (relay devices under the range of 50 m with the source) with the opportunistic scheme (single hop) based on relay selection from the whole network. mathematical procedure, an exact solution of the second integral I DT 2 ( ¯ γ , σ ) is also presented in (14). Using these, and av erage of uniform random variable, we get the upper bound (13) of Theorem 1. For the lo wer bound, we use (11) and 1 + z ≤ e z to get the integral as I lb = 1 √ 2 π ( ¯ γ + 1) Z ∞ ( γ th − ¯ γ − 1) σ e − x 2 2 − σ ¯ γ +1 x d x (29) Completing the square in the exponential function and representing the integral into Gaussian Q-function with simple substitution, we get the lower bound (13) of Theorem 1. A P P E N D I X B T H E O R E M 2 : E N E R G Y C O N S U M P T I O N I N R E L A Y T R A N S M I S S I O N First, we deri ve an e xpression on energy consumed due the circuit po wer using the order statistics on the uniform random variable in the following lemma. 25 Lemma 1: Let Z 1 , Z 2 , · · · Z N are N i.i.d uniform random variables in the interv al [ a, b ] , and Z (1) = min { Z 1 , Z 2 , · · · Z N } . The expected value of the minimum of a uniform random v ariable is E [ Z (1) ] = b + N a 1 + N . (30) The proof follows standard procedure and has been omitted. Using Lemma 1, E [ P ckt (1) ] can be deri ved. An upper bound on I RELA Y 1 ( N , σ ) in (18) can be obtained using Q ( t ) = 1 − Q ( − t ) and Chernoff bound Q ( t ) ≤ 1 2 exp[ − t 2 / 2] , and exp[ − z ] < 1 1+ z to conv ert into polynomial function: I RELA Y 1 ( N , σ ) ≤ 1 (2) N Z ¯ γ − γ th σ 0 1 ( ¯ γ − tσ ) 2 (1 + N 2 t 2 ) d t (31) W e use partial fraction to solve the integral in (31) in an exact form, as giv en in (20). T o analyze I RELA Y 2 ( N , σ ) , we use the binomial e xpansion of (1 − Q ( x )) N and interchange the summation and the integration to get I RELA Y 2 ( N , σ ) = N X k =0 N k ( − 1) k Z ∞ 0 [ Q ( x )] k ( xσ + ¯ γ ) 2 d x = N X r =0 N / 2 2 r Z ∞ 0 [ Q ( x )] 2 r ( xσ + ¯ γ ) 2 d x − N X r =0 N / 2 2 r + 1 Z ∞ 0 [ Q ( x )] 2 r +1 ( xσ + ¯ γ ) 2 d x (32) Using standard mathematical procedure, we present a solution to the integral gi ven in the follo wing preposition. Pr oposition B1: If a, b, N > 0 Z ∞ 0 exp[ − N x 2 ] ( ax + b ) 2 d x = Ψ( N , a, b ) = 1 2 a 3 b e − nb 2 a 2 2 π b 2 N erfi b √ N a ! − 2 b 2 N Ei b 2 N a 2 + 2 a 2 e b 2 N a 2 − 2 √ π ab √ N e b 2 N a 2 − b 2 N log a 2 b 2 N + b 2 N log b 2 N a 2 + 4 b 2 N log a b − 2 b 2 N log ( N ) ! (33) W e use Chernoff bounds: f ( κ ) exp[ − κx 2 ] ≤ Q ( x ) ≤ 1 2 exp[ − x 2 / 2] in (32), and then use the result of (33) to get an upper bound on I RELA Y 2 ( N , σ ) in (21). Using Lemma 1, and (20), (21) in (17) completes the proof the Theorem 2. 26 A P P E N D I X C C O RO L L A RY 1 : A P P R OX I M A T I O N O N I RELA Y 2 ( N , σ ) T o deri ve an approximate expression on I RELA Y 2 ( N , σ ) , we use an approximation on Q ( x ) ≈ exp[ − ( q 1 x 2 + q 2 x + q 3 )] and e − z ≤ 1 1+ z , ∀ z ≤ 0 in (32) to represent the integral I RELA Y 2 ( N , σ ) ≈ Z γ max 0 d x ( xσ + ¯ γ ) 2 (1 + k ( q 1 x 2 + q 2 x + q 3 )) (34) where γ max < ∞ is chosen to av oid the diver gence of the integral. The integration in (34) is deri ved in exact form as presented in (22). This completes the proof of Corollary 1. A P P E N D I X D T H E O R E M 3 : S C A L I N G L AW O N E N E R G Y C O N S U M P T I O N W e use Q (0) = 1 / 2 to get an upper bound on the integral I RELA Y 1 ( N , σ ) in (18): I RELA Y 1 ( N , σ ) ≤ 1 2 N ( 1 γ th − 1 ¯ γ ) (35) where the equality is achie ved when γ th = ¯ γ . The integral I RELA Y 2 ( N , σ ) in (18) can be decomposed: I RELA Y 2 ( N , σ ) = Z δ 1 0 1 ( xσ + ¯ γ ) 2 (1 − Q ( x )) N d x + Z δ 2 δ 1 1 ( xσ + ¯ γ ) 2 (1 − Q ( x )) N d x + · · · + Z ∞ δ M 1 ( xσ + ¯ γ ) 2 (1 − Q ( x )) N d x (36) where δ m > δ m − 1 > 0 , m = 1 , 2 , · · · M . Since Q ( δ m ) < Q ( δ m − 1 ) , we use the minimum of Q-function in each interv al of integration to get an upper bound (36): I RELA Y 2 ( N , σ ) ≤ (1 − Q ( δ 1 )) N 1 σ ( 1 ¯ γ − 1 σ δ 1 + ¯ γ ) + (1 − Q ( δ 2 )) N 1 σ ( 1 σ δ 1 + ¯ γ − 1 σ δ 2 + ¯ γ ) + · · · + 1 σ ( 1 σ δ M + ¯ γ ) (37) W e use δ m = p c m ln( N ) where 0 ≤ c m ≤ 1 , inequality (1 − x ) N ≤ 1 1+ N x , and a lower bound on Q-function Q ( x ) ≥ κe − x 2 , where κ = 0 . 3885 to bound (1 − Q ( δ m )) N : (1 − Q ( δ m )) N ≤ 1 1 + κN 1 − c m (38) Using (38) in (37), we get I RELA Y 2 ( N , σ ) ≤ 1 σ h 1 ¯ γ + σ p c M ln( N ) + M − 1 X m =1 ( 1 1 + κN (1 − c m ) )( 1 ¯ γ + σ p c m − 1 ln( N ) − 1 ¯ γ + σ p c m ln( N ) ) i , (39) where c 0 = 0 . Using Lemma 1, and (35), (39) in (17), and neglecting negati ve terms, we get (23). When N → ∞ , we get the scaling law for energy consumption of Theorem 3. 27 A P P E N D I X E T H E O R E M 4 : E N E R G Y O V E R H E A D O F D 2 D R E L A Y I N G Using (30) and logarithm inequality x x +1 ≤ log e (1 + x ) ≤ x , the integral in (25) for expected energy in D2D relaying can be represented in terms of e xponential integral: ( η (d) 1 + 0 . 5 η (d) 2 ( P ckt max + P ckt min )) 1 ¯ γ d E 1 ( γ (d) th ¯ γ d ) ≤ ¯ E D2D ≤ ( η (d) 1 + 0 . 5 η (d) 2 ( P ckt max + P ckt min )) exp( − γ (d) th γ d ) + 1 ¯ γ (d) E 1 ( γ (d) th ¯ γ (d) ) (40) Further , we use the inequality on exponential integral 0 . 5 exp( − x ) log e (1 + 2 /x ) < E 1 ( x ) < exp( − x ) log e (1 + 1 /x ) and exp( x ) > 1 + x to get (27) of Theorem 4. R E F E R E N C E S [1] J. Andre ws, S. Buzzi, W . Choi, S. Hanly , A. Lozano, A. Soong, and J. Zhang, “What will 5G be?” IEEE J ournal on Selected Ar eas in Communications , vol. 32, no. 6, pp. 1065–1082, June 2014. [2] M. Shafi, A. Molisch, P . Smith, T . Haustein, P . Zhu, P . D. Silv a, F . T ufvesson, A. Benjebbour , and G. W under, “5G: A tutorial ov erview of standards, trials, challenges, deployment, and practice, ” IEEE Journal on Selected Ar eas in Communications , vol. 35, no. 6, pp. 1201–1221, June 2017. [3] M. Agiwal, A. Roy , and N. Saxena, “Next generation 5G wireless networks: A comprehensive survey , ” IEEE Communi- cations Surveys T utorials , vol. 18, no. 3, pp. 1617–1655, thirdquarter 2016. [4] G. Li, Z. Xu, C. Xiong, C. Y ang, S. Zhang, Y . Chen, and S. Xu, “Energy-efficient wireless communications: tutorial, surve y , and open issues, ” IEEE Wir eless Communications , vol. 18, no. 6, pp. 28–35, December 2011. [5] D. Feng, C. Jiang, G. Lim, L. J. Cimini, G. Feng, and G. Y . Li, “ A survey of energy-efficient wireless communications, ” IEEE Communications Surveys T utorials , vol. 15, no. 1, pp. 167–178, First 2013. [6] S. Buzzi, Chih-Lin I, T . Klein, H. V . Poor, C. Y ang, and A. Zappone, “ A survey of energy-efficient techniques for 5G networks and challenges ahead, ” IEEE J ournal on Selected Ar eas in Communications , vol. 34, no. 4, pp. 697–709, April 2016. [7] S. Buzzi and H. V . Poor , “Joint receiver and transmitter optimization for energy-ef ficient CDMA communications, ” IEEE Journal on Selected Areas in Communications , vol. 26, no. 3, pp. 459–472, April 2008. [8] G. Miao, N. Himayat, G. Li, and S. T alwar , “Distributed interference-aware energy-ef ficient power optimization, ” IEEE T ransactions on W ir eless Communications , vol. 10, no. 4, pp. 1323–1333, April 2011. [9] A. Zappone, E. Jorswieck, and A. Leshem, “Distributed resource allocation for energy efficienc y in MIMO OFDMA wireless networks, ” IEEE Journal on Selected Areas in Communications , vol. 34, no. 12, pp. 3451–3465, Dec 2016. [10] ——, “Distributed assignment and resource allocation for energy efficienc y in MIMO wireless networks, ” in WSA 2016; 20th International ITG W orkshop on Smart Antennas , March 2016, pp. 1–5. [11] ——, “Distributed fractional programming in matched multiple access channels, ” in 2016 IEEE Sensor Array and Multichannel Signal Processing W orkshop (SAM) , July 2016, pp. 1–5. [12] C. Sun, Y . Cen, and C. Y ang, “Ener gy efficient OFDM relay systems, ” IEEE T ransactions on Communications , vol. 61, no. 5, pp. 1797–1809, May 2013. 28 [13] A. Zappone, P . Cao, and E. Jorswieck, “Energy efficiency optimization in relay-assisted MIMO systems with perfect and statistical CSI, ” IEEE T ransactions on Signal Pr ocessing , vol. 62, no. 2, pp. 443–457, Jan 2014. [14] K. Cheung, S. Y ang, and L. Hanzo, “ Achieving maximum ener gy-efficiency in multi-relay OFDMA cellular networks: A fractional programming approach, ” IEEE T ransactions on Communications , vol. 61, no. 7, pp. 2746–2757, July 2013. [15] T . Himsoon, W . Siriwongpairat, Z. Han, and K. Liu, “Lifetime maximization via cooperative nodes and relay deployment in wireless networks, ” IEEE Journal on Selected Areas in Communications , vol. 25, no. 2, pp. 306–317, February 2007. [16] R. Madan, N. Mehta, A. Molisch, and J. Zhang, “Energy-ef ficient cooperative relaying ov er fading channels with simple relay selection, ” IEEE T ransactions on W ir eless Communications , vol. 7, no. 8, pp. 3013–3025, August 2008. [17] G. Lim and L. Cimini, “Energy-ef ficient cooperativ e beamforming in clustered wireless networks, ” IEEE T ransactions on W ir eless Communications , vol. 12, no. 3, pp. 1376–1385, March 2013. [18] Z. Zhou, S. Zhou, S. Cui, and J. Cui, “Energy-ef ficient cooperativ e communication in a clustered wireless sensor network, ” IEEE T ransactions on V ehicular T echnology , vol. 57, no. 6, pp. 3618–3628, Nov 2008. [19] A. Bletsas, A. Khisti, D. Reed, and A. Lippman, “ A simple cooperative div ersity method based on network path selection, ” IEEE Journal on Selected Areas in Communications , vol. 24, no. 3, pp. 659–672, March 2006. [20] I. Krikidis, J. Thompson, S. Mclaughlin, and N. Goertz, “ Amplify-and-forward with partial relay selection, ” IEEE Communications Letters , vol. 12, no. 4, pp. 235–237, April 2008. [21] Y . Jing and H. Jafarkhani, “Network beamforming using relays with perfect channel information, ” IEEE T ransactions on Information Theory , vol. 55, no. 6, pp. 2499–2517, June 2009. [22] S. Ikki and M. Ahmed, “Performance analysis of adaptive decode-and-forward cooperati ve diversity networks with best- relay selection, ” IEEE T ransactions on Communications , vol. 58, no. 1, pp. 68–72, January 2010. [23] A. Kalantari, M. Mohammadi, and M. Ardebilipour, “Performance analysis of opportunistic relaying over imperfect non- identical log-normal fading channels, ” in 2011 IEEE 22nd International Symposium on P ersonal, Indoor and Mobile Radio Communications , Sept 2011, pp. 1909–1913. [24] A. Nosratinia, T . Hunter, and A. Hedayat, “Cooperativ e communication in wireless networks, ” IEEE Communications Magazine , vol. 42, no. 10, pp. 74–80, Oct 2004. [25] Q. Li, R. Hu, Y . Qian, and G. Wu, “Cooperative communications for wireless networks: techniques and applications in L TE-adv anced systems, ” IEEE W ireless Communications , vol. 19, no. 2, April 2012. [26] Y . Chen and Q. Zhao, “On the lifetime of wireless sensor networks, ” IEEE Communications Letters , vol. 9, no. 11, pp. 976–978, Nov 2005. [27] Q. Zhao and L. T ong, “Opportunistic carrier sensing for ener gy-efficient information retrie v al in sensor networks, ” EURASIP Journal on W ir eless Communications and Networking , vol. 2005, no. 2, p. 125040, Apr 2005. [28] Y . Chen, Q. Zhao, V . Krishnamurthy , and D. Djonin, “Transmission scheduling for optimizing sensor network lifetime: A stochastic shortest path approach, ” IEEE T ransactions on Signal Pr ocessing , vol. 55, no. 5, pp. 2294–2309, 2007. [29] Y . Chen and Q. Zhao, “ An integrated approach to energy-aw are medium access for wireless sensor networks, ” IEEE T ransactions on Signal Pr ocessing , vol. 55, no. 7, pp. 3429–3444, 2007. [30] K. Cohen and A. Leshem, “ A time-varying opportunistic approach to lifetime maximization of wireless sensor networks, ” IEEE T ransactions on Signal Pr ocessing , vol. 58, no. 10, pp. 5307–5319, Oct 2010. [31] W . Huang, Y . Hong, and C. Kuo, “Lifetime maximization for amplify-and-forward cooperative networks, ” IEEE T ransactions on W ir eless Communications , vol. 7, no. 5, pp. 1800–1805, May 2008. [32] Z. Zhou, S. Zhou, J. Cui, and S. Cui, “Energy-efficient cooperative communication based on power control and selecti ve single-relay in wireless sensor networks, ” IEEE transactions on W ir eless Communications , vol. 7, no. 8, 2008. 29 [33] K. Cohen and A. Leshem, “Time-v arying opportunistic protocol for maximizing sensor networks lifetime, ” in 2009 IEEE International Confer ence on Acoustics, Speech and Signal Pr ocessing , April 2009, pp. 2421–2424. [34] Y . Y af fe, A. Leshem, and E. Zehavi, “Stable matching for channel access control in cogniti ve radio systems, ” in 2010 2nd International W orkshop on Cognitive Information Pr ocessing , June 2010, pp. 470–475. [35] A. Leshem, E. Zehavi, and Y . Y affe, “Multichannel opportunistic carrier sensing for stable channel access control in cognitiv e radio systems, ” IEEE Journal on Selected Areas in Communications , vol. 30, no. 1, pp. 82–95, January 2012. [36] O. Naparstek and A. Leshem, “ A fast matching algorithm for asymptotically optimal distrib uted channel assignment, ” in 2013 18th International Confer ence on Digital Signal Processing (DSP) , July 2013, pp. 1–6. [37] ——, “Fully distributed optimal channel assignment for open spectrum access, ” IEEE T ransactions on Signal Processing , vol. 62, no. 2, pp. 283–294, Jan 2014. [38] D. Feng, L. Lu, Y . Y uan-W u, G. Y . Li, G. Feng, and S. Li, “Device-to-device communications underlaying cellular networks, ” IEEE T ransactions on Communications , vol. 61, no. 8, pp. 3541–3551, August 2013. [39] A. Asadi, Q. W ang, and V . Mancuso, “ A surve y on device-to-device communication in cellular networks, ” IEEE Communications Surveys T utorials , vol. 16, no. 4, pp. 1801–1819, Fourthquarter 2014. [40] M. N. T ehrani, M. Uysal, and H. Y anikomeroglu, “Device-to-device communication in 5G cellular networks: challenges, solutions, and future directions, ” IEEE Communications Magazine , vol. 52, no. 5, pp. 86–92, May 2014. [41] P . Mach, Z. Becvar , and T . V anek, “In-band device-to-de vice communication in OFDMA cellular networks: A survey and challenges, ” IEEE Communications Surveys & T utorials , vol. 17, no. 4, 2015. [42] J. H. Song, H.-T . Roh, and J.-W . Lee, “Opportunistic scheduling and incentiv e mechanism for OFDMA networks with D2D relaying, ” Computer Networks , vol. 91, pp. 772–787, Oct 2010. [43] J. Deng, A. A. Dowhuszko, R. Freij, and O. Tirkk onen, “Relay selection and resource allocation for D2D-relaying under uplink cellular power control, ” in 2015 IEEE Globecom W orkshops (GC Wkshps) , Dec 2015, pp. 1–6. [44] A. Chaaban and A. Sezgin, “Device-relaying in cellular D2D networks: A fairness perspective, ” CoRR , vol. abs/1505.00114, 2015. [Online]. A vailable: http://arxiv .org/abs/1505.00114 [45] A. Al-Hourani, S. Kandeepan, and E. Hossain, “Relay-assisted de vice-to-device communication: A stochastic analysis of energy saving, ” IEEE T ransactions on Mobile Computing , v ol. 15, no. 12, pp. 3129–3141, Dec 2016. [46] A. Asadi, V . Mancuso, and R. Gupta, “DORE: An experimental framework to enable outband D2D relay in cellular networks, ” IEEE/ACM T ransactions on Networking , vol. PP , no. 99, pp. 1–14, 2017. [47] Y . Li, J. Li, J. Jiang, and M. Peng, “Performance analysis of de vice-to-device underlay communication in Rician fading channels, ” in 2013 IEEE Global Communications Confer ence (GLOBECOM) , Dec 2013, pp. 4465–4470. [48] Y . J. Chun, S. L. Cotton, H. S. Dhillon, A. Ghrayeb, and M. O. Hasna, “ A stochastic geometric analysis of device-to-de vice communications operating over generalized f ading channels, ” IEEE T ransactions on W ireless Communications , v ol. 16, no. 7, pp. 4151–4165, July 2017. [49] G. G. Messier , “Opportunistic transmission using large scale channel effects, ” IEEE T ransactions on Communications , vol. 58, no. 11, pp. 3110–3114, November 2010. [50] X. Liu, Q. He, Y . Li, and J. W ang, “Large-scale fading based power allocation for device-to-de vice underlay cellular communication, ” in 2015 IEEE 81st V ehicular T echnolo gy Conference (VTC Spring) , May 2015, pp. 1–5. [51] J. Qiao, X. Shen, J. Mark, Q. Shen, Y . He, and L. Lei, “Enabling de vice-to-device communications in millimeter-wa ve 5G cellular networks, ” IEEE Communications Magazine , vol. 53, no. 1, pp. 209–215, January 2015. [52] C. de Lima, H. Alves, P . Nardelli, and M. Latv a-aho, “Effects of relay selection strategies on the spectral ef ficiency of wireless systems with half- and full-duple x nodes, ” IEEE T ransactions on V ehicular T echnolo gy , v ol. 66, no. 8, pp. 7578–7583, Aug 2017. 30 [53] X. Lin, J. Andrews, A. Ghosh, and R. Ratasuk, “ An overvie w of 3GPP device-to-device proximity services, ” IEEE Communications Magazine , vol. 52, no. 4, pp. 40–48, April 2014. [54] S. Chang, P . Cosman, and L. Milstein, “Chernof f-type bounds for the Gaussian error function, ” IEEE T ransactions on Communications , vol. 59, no. 11, pp. 2939–2944, November 2011. [55] 3GPP , “ Study on L TE Device to Device Proximity Services; Radio Aspects, ” 3rd Generation Partnership Project (3GPP), TR 36.843, 3 2014. [Online]. A vailable: http://www .3gpp.org/dynareport/36843.htm [56] M. Lauridsen, L. No ¨ el, T . B. Sørensen, and P . Mogensen, “ An empirical L TE smartphone po wer model with a view to energy efficiency ev olution, ” Intel T echnology Journal , vol. 18, no. 1, pp. 172–193, 2014. [57] Y . J. Bultitude and T . Rautiainen, “IST -4-027756 WINNER II D1. 1.2 V1. 2 WINNER II channel models, ” EBITG, TUI, UOULU, CU/CRC, NOKIA, T ech. Rep., T ech. Rep., 2007.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment