Control Challenges for Resilient Control Systems
In this chapter, we introduce methods to address resiliency issues for control systems. The main challenge for control systems is its cyber-physical system nature which strongly couples the cyber systems with physical layer dynamics. Hence the resili…
Authors: Quanyan Zhu
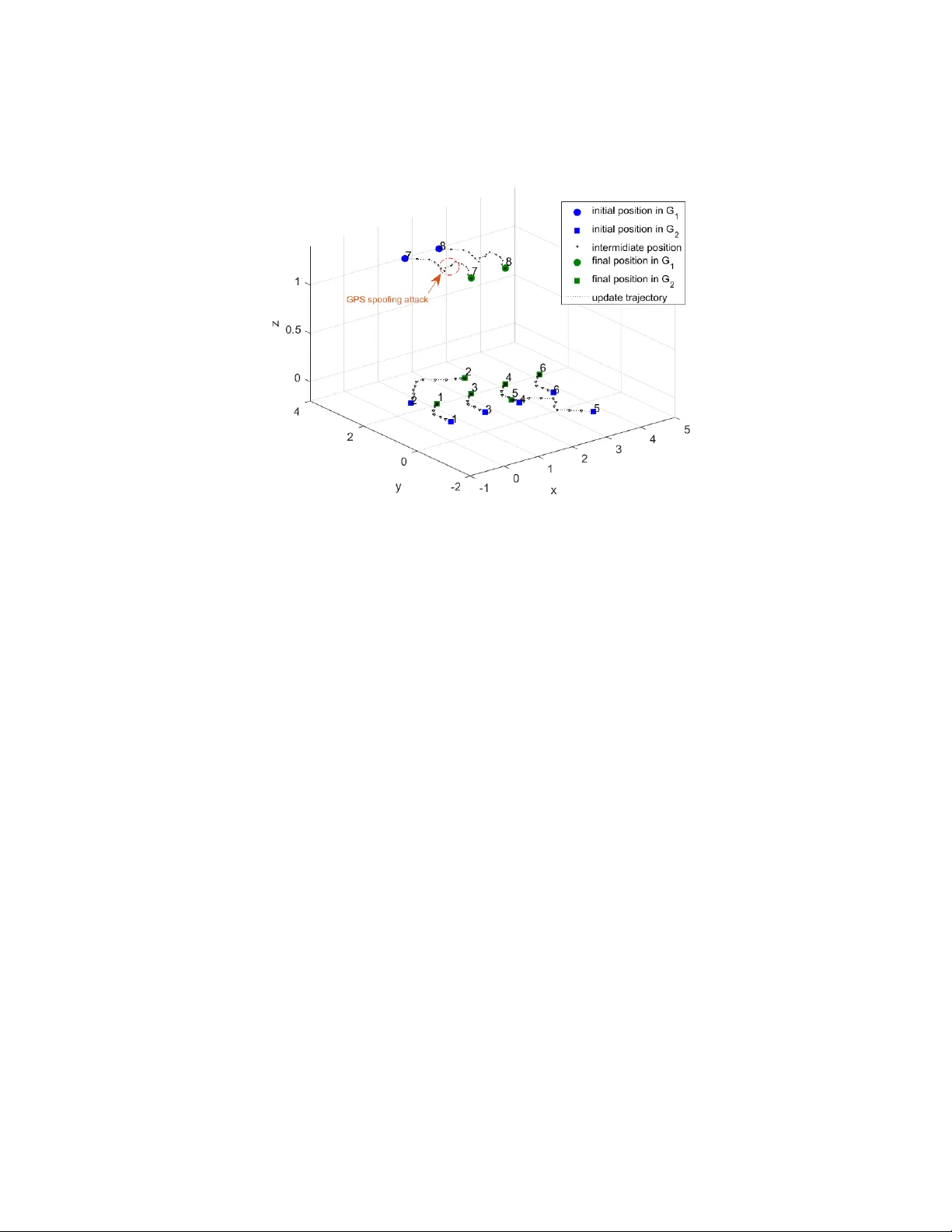
Chapter 14 Con trol Challenges Quan y an Zh u T andon Sc ho ol of Engineering New Y ork Universit y E-mail: qz494@n yu.edu Abstract In this chapter, w e introduce metho ds to address resiliency issues for control systems. The main challenge for control systems is its cyb er-ph ysical system nature that strongly couples the cyber systems with ph ysical la yer dynamics. Hence, the resiliency issues for control systems need to b e addressed by in tegrating the cyb er resiliency with the ph ysical lay er resiliency . W e introduce framew orks that can provide a holistic view of the con trol system resiliency and a quan titative design paradigm that can enable an optimal cross-la y er and cross-stage design at the planning, op eration, and recov ery stage of control systems. The con trol systems are often large-scale systems in industrial application and critical infrastruc- tures. Decen tralized con trol of suc h systems is indispensable. W e extended the resiliency framew ork to address distributed and collab orativ e resiliency among decen tralized con trol agen ts. 1 2 CHAPTER 14. CONTR OL CHALLENGES Ob jectiv es The ob jectives of this c hapter is to pro vide an o verview of resilien t control systems, including understanding: 1. Cross-lay er tradeoffs b et ween securit y at the cyb er lay er and resiliency at the ph ysical la yer. 2. Cross-stage resiliency design, including ex-an te planning, in terim operation, and ex- p ost reco very . 3. Games-in-games design paradigm for the m ulti-stage and m ulti-lay er design of resilient con trol systems. 4. Control c hallenges for distributed control systems. 14.1 Resiliency Challenges in Con trol Systems Mo dern control systems are equipp ed with information system technologies (ICTs) that can pro vide situational aw areness of the plant and enable a fast response to emergency and securit y breac hes. As the con trol systems b enefit from the enhanced functionalities and autonom y , the cyb ersecurit y vulnerabilities b ecome prominen t issues to resolv e. Adversaries can tak e a sequence of mov es and launc h m ulti-phase and m ulti-stage attac ks from the early reconnaissance to the ob jectiv e of data e xfiltration. This structure of attacks is kno wn as the cyber kill c hain. The defense against suc h attac ks includes detection of an adv ersary , disruption of the netw ork system, cyb er deception to create uncertain ties and costs for the attac ker, and many other techniques (see [30, 31, 40, 67]). Despite the effort in developing cyb er defense for control systems, the p erfect security is not alw a ys achiev able. Achieving p erfect security would either require a cost-prohibitiv e amoun t of resources to main tain the securit y or lead to a degradation of system operability and usabilit y . Hence, it is imp ortan t to shift the fo cus from securit y-centered design to the paradigm of secure and resilience design of con trol systems. Adding resiliency as an additional dimension to the new paradigm complements the sole reliance on ex-an te perfect security tec hnologies as a solution with interim and ex-p ost resiliency mec hanisms as solutions when the ex-ante securit y mec hanism fails to protect the con trol system. Resiliency is a key system concept that fo cuses on the p ost-ev ent b eha viors of a system. F or example, when a cyb er attac k has successfully reached its target, any s ecurit y mec h- anism b ecomes futile at this point. Reliance should be on resiliency mec hanisms that can reduce the impact of this successful attac k and enable a fast recov ery to restore the op era- tions to their normal state. On the con trary , securit y mec hanisms are often used as to ols to prev ent successful attac ks or attack ers from ac hieving their ob jectiv es. Hence securit y and resilience are dual concepts and there are fundamen tal relationships b et ween them. First, there exists a tradeoff betw een security and resiliency . When there is p erfect securit y , resiliency b ecomes unnecessary . The need for r esiliency is high when the securit y is p oor. Second, security and resiliency resolutions ha ve to b e implemen ted jointly . One cannot coun t on either securit y or resiliency solutions to safeguard the system from adv ersarial 14.1. RESILIENCY CHALLENGES IN CONTROL SYSTEMS 3 b eha viors. The cost for security and resiliency solutions are often different. The level of securit y and resiliency implemen ted in the system should b e optimized together. Understanding these relationships pro vides a fundamen tal understanding tow ard de- signing secure and resilient systems. There are tw o key c hallenges to design secure and resilien t systems. One is the cross-lay e r c hallenge and the other is the cross-stage c hallenge. Cross-la yer challenges refer to the fact that the securit y issues often reside at the cyber la yer of the system while the resiliency often deals with the last-mile issue and in the context of control systems, the resiliency issues sit at the physical la y er of the systems. In other w ords, the failure in the protection at the cyb er la yer can lead to malfunctioning of the ph ysical system p erformance. The join t design of secure and resilient solutions is naturally cross-la yered. It would require understanding the dep endency and in terdep endency among h uman, cyb er, and ph ysical la yers of the con trol system. F or example, the failure of cy- b er defense against an adv anced persistent threat w ould lead to data injection on sensors and the manipulation of the controller of the ph ysical plan t. Human negligence in system configurations w ould lead to cyber vulnerabilities that can b e exploited by the attac k ers to reac h targeted physical assets. The second challenge of resilient control systems arises from the fact that resiliency is a dynamical system concept. Impro ving resiliency in v olves multi-stage planning and design, including ex-ante planning, in terim execution, and ex-p ost recov ery . The ex-ante stage refers to the planning stage b efore the con trol system starts to run. At this stage, one needs to in vest resources and plan contingencies to provide information and physical resources to enable fast reco very at later stages. F or example, one can add redundancies such as sensors and pow er generators to prepare for an attack on sensors and attac k-induced loss of p o w er. One can also design secure and switc hing con trollers in adv ance to prepare for the worst- case op erational en vironment and provide a con tingency controller when the control system encoun ters failures. The offline design of such controller at the ex-an te stage prepares for a set of anticipated attac ks in later stages. How ev er, unan ticipated attacks can still o ccur. In addition, the preparation for a large set of even ts can b e exp ensive. There is a tradeoff b et w een what ev ents should b e prepared for at the ex-an te stage and what ev en ts should b e dealt with in later stages. Hence, from the set of an ticipated even ts, the high-impact and high-frequency ev ents should b e selected first. The in terim stage refers to the op eration stage of the control systems. By running the con troller that prepares for a selected set of anticipated ev en ts, the control system can run smo othly and in telligently when it encoun ters these prepared ev en ts. The con trol system can switc h to a differen t control logic or leverage built-in resources to handle ev ents that o ccurred. In Figure 14.1, at time t 1 , an anticipated ev ent has o ccurred; for example, there is a loss of a sensor. By switching to a redundant sensor, the in terim stage op eration do es not suffer an y loss of system p erformance. The ex-p ost stage refers to the stage where unan ticipated ev en t occurs and the reco v ery pro cess kic ks off. The probabilit y of running in to an unan ticipated even t depends on the set of ev ents prepared for by the ex-an te controller. In Figure 14.1, the unanticipated ev ent a o ccurs at t 2 . The exp ected v alue of t 2 w ould dep end on the frequency of Even t A and whether the ex-an te stage has b een taken in to accoun t. Since no con tingency plan has b een made for Ev en t A , the system will suffer a performance degradation. The ex-post resiliency design aims to detect the even t quickly and find a self-healing mec hanism that can restore the 4 CHAPTER 14. CONTR OL CHALLENGES Figure 14.1: Multi-stage planning and design for resilient control systems: ex-ante stage plans resiliency . In terim stage executes resilient con trol. Ex-p ost stage restores system p erformance after unanticipated attac ks. system to its normal op eration or an acceptable performance level. Depicted in Figure 14.1, the system p erformance degrades to its maxim um difference M and then gradually reco vers to the lev el D at time t 3 . The ex-p ost resiliency is measured b y the total p erformance loss after the ev en t. The goal of ex-post resiliency is to minimize this loss b y resp onding fast to the even t and dev eloping an effective restoration plan. The restoration plan would dep end on the configurable resources a v ailable to the system and the ex-an te resource inv estmen t made for the control system . F or example, when an attac k has successfully compromised a cen trifuge control system, the system can detect and reb o ot. The cost for reb o ot dep ends on whether the control system is w ell equipp ed with computational resources and h uman resources to enable the fast resp onse. It is clear that the concept of resiliency spans three stages of the con trol systems. The planning of ex-ante resiliency affects the resource av ailabilit y of and the need for ex-p ost resiliency . Hence, the ex-ante resiliency planning and the ex post resiliency mec hanism hav e to be jointly designed. This c hapter will in tro duce a games-in-games framework to dev elop a cross-lay er cross-stage design framew ork. W e will use examples from unmanned v ehicles to illustrate the games-in-games framew ork. 14.2 Resiliency Design F ramew ork A natural framew ork to enable the cross-lay er design is to use the games-in-games framew ork in tro duced in [64]. Game-theoretic metho ds hav e b een used to capture differen t cyb er-attack scenarios and models including jamming (see [49, 71, 73, 73]), sp oofing (see [52, 62]), and net work configurations (see [25, 27, 46, 65, 75]). Interested readers can refer to [34] and [40] for recen t surv eys. Each game can be used to mo del a cyb er-attac k scenario. Composing these games together forms a set of an ticipated adversarial b eha viors at the cyb er lay er to 14.2. RESILIENCY DESIGN FRAMEWORK 5 b e considered. Similarly , the attack behaviors at the ph ysical la yer can also be mo deled b y a set of ph ysical la yer games. F or example, the attack er can choose to inject bad data into sensors while the defender can c ho ose which sensors to use. The defender can determine the switc hing p olicy of the con trollers while the attac ker can determine how to compromise the logic of one of the con trol laws. Comp osing the physical la yer games together pro vides a framework to design ex-ante and ex-p ost resiliency mec hanisms. The cyb er games and the ph ysical la yer games are in terdep enden t. The outcome of one game would lead to a new game. The games-in-games framework is illustrated in Figure 14.2. Cyb er games G 2 , 1 and G 2 , 2 are composed together to form G 2 . The physical la y er games G 1 , 1 and G 1 , 2 are comp osed to form G 1 . G 1 and G 2 are interconnected to form a larger game G . Figure 14.2: Comp osition of cyb er games and physical lay er games together to form a cross-la yer adv ersarial mo del. A natural con trol framew ork to capture the multi-stage features of resilien t control sys- tems is mo del-predictiv e con trol or moving-horizon tec hniques. The mo ving-horizon control lo oks N steps in to the future, prepares for p ossible ev ents, and finds optimal control strate- gies to b e implemen ted at the current stage. The ex-an te control design tak es into accoun t a credible set of an ticipated adv ersarial models. This design process can be form ulated as a game b et w een the control designer and adv ersaries. The game mo del can be chosen to capture the cross-la yer nature of the control system as illustrated in Figure 14.2. The ex-ante control is implemen ted immediately after the design. If no unan tic- ipated behaviors o ccur, this game-based mo ving-horizon con trol con tin ues. When unan tici- pated adversarial b eha vior happ ens in the next mo ving horizon, the control design not only prepares for the anticipated adversarial b eha viors but also determines wa ys to reco ver from the unanticipated attac k. The moving-horizon tec hnique directly incorp orates the ex-ante planning by lo oking into p ossible future even ts and the ex-p ost recov ery by immediately reconfiguring the system in the next mo ving horizon. 14.2.1 Con trol of Autonomous Systems in Adversarial En vironment T o illustrate the mo ving-horizon resilient con trol design paradigm, we presen t a case study of con trol for mobile autonomous systems in adv ersarial en vironment. The ob jective of the con trol is to main tain the connectivity of the autonomous system in an en vironment where an attac k er can jam the communications among the autonomous systems. The op erator 6 CHAPTER 14. CONTR OL CHALLENGES do es not kno w the capability of the attac k er (i.e., ho w man y links the attack er can jam, and where and when the attac ker will jam the communications). The op erator prepares for the an ticipated lev el of attac ks and plans the con trol in a mo ving-horizon w a y . At every time k , the op erator solves the following problem: Q k : max x ( k + c ) min e ∈ E λ 2 ( e, x ( k + c )) . (14.1) Here x ( k ) is the configuration of the mobile netw ork at time k (i.e., the p osition of the mobile agen ts). Two mobile agents can form a link when they are sufficiently close within a desirable range of comm unications. Hence, the configuration x ( k ) includes a netw ork whose connectivity is describ ed b y the algebraic connectivity of the netw ork, denoted by λ 2 (i.e., the second-smallest eigen v alue of the associated Laplacian matrix). A t eac h time step k , the op erator determines where the agents should mov e to in the next time step x ( k + c ), where c is a time interv al. The con trol is constrained b y the physical dynamics of autonomous systems. T o main tain connectivit y , the op erator aims to maximize the lev el of connectivit y as m uch as p ossible at time k + c b y an ticipating the w orst-case adversarial b eha viors giv en a certain lev el of attac ks, describ ed b y the set E . F or example, the op erator can an ticipate one-link remov al and determine how agents can mo ve and main tain connected secure to suc h one-link remov al. On one hand, when the capability of the attac ker is higher, it b ecomes more difficult for the op erator to find a controller to b e secure to the attac k lev el. On the other hand, if the op erator underestimates the attack er, his con trol strategies will not ac hiev e a desirable connectivit y . Hence, the op erator should an ticipate a reasonable lev el of attac ks and design an ex-an te controller that will be implemen ted at the interim stage. When the attack er’s capability do es not exceed the attack level anticipated by the ex-an te con troller, the netw ork connectivit y is main tained as expected. When the attac ker’s capabilit y exceeds the an ticipated level, the netw ork connectivit y may not b e ac hieved and the ex-post resiliency mec hanism will b e designed at time k + c . In other words, the problem for the op erator at k + c , Q k + c includes ho w to react to the failure of netw ork connectivit y and ho w to design new con trol la ws to heal the broken links while an ticipating new attacks at time k + c . The anticipation of attack lev els can b e adjusted from time k to k + c . This mo ving-horizon framework has b een shown to b e effective in obtaining the self- adaptabilit y , self-healing, and resilience of the In ternet of Battlefield Things (IoBTs) (see [6, 15, 19]). Sp ecifically , the unmanned ground vehicle (UGV) net work should coordinate its actions with the unmanned aerial vehicle (UA V) net work and the soldier netw ork to ac hieve a highly connected global netw ork. The designed decentralized algorithm yields an intelligen t control of each agen t to resp ond to others to optimize real-time connectivit y under adversaries. Figure 14.3 sho ws an example of a tw o-la yer rob otic net work that is robust to jamming attack at every step. Figure 14.4 shows the algebraic connectivity ov er time asso ciated with the t wo-la y er netw ork. F urthermore, the agen ts can resp ond to the sp oofing attac k quickly , whic h sho ws the resilience of the con trol strategy . The dev elop ed mo ving-horizon framework can b e further adopted to address the mosaic control design as the framew ork provides built-in securit y and resilience for each comp onen t in the system, whic h guaran tee the p erformance of the integrated system. 14.2. RESILIENCY DESIGN FRAMEWORK 7 Figure 14.3: Netw ork connectivity: dynamic configuration of secure rob otic netw ork. The GPS sp o ofing attac k is introduced at time Step 9, and it lasts for 5 steps. 14.2.2 Cross-La y er Defense for Cloud-Enabled In ternet of Con trolled Things T o illustrate games-in-games framework, we c onsider the Internet of Controlled Things (IoCT) that integrates computing, con trol, sensing, and net working. The IoCT relies on lo cal clouds to in terface b et ween heterogeneous comp onen ts. The cloud-enabled IoCT is comp osed of three interacting lay ers: a cloud la yer, a comm unication lay er, and a ph ysical la yer. In the first lay er, the cloud-services are threatened by attac kers capable of APTs and defended by netw ork administrators (or “defenders”). The in teraction at each cloud- service is mo deled using the FlipIt game recen tly prop osed by [2] and [51]. W e use one FlipIt game per cloud-service. In the comm unication lay er, the cloud services, which ma y b e con trolled by the attack er or defender according to the outcome of the FlipIt game– transmit information to a device that decides whether to trust the cloud-services. This in teraction is captured using a signaling game. At the physical la yer, the utility parameters for the signaling game are determined using optimal con trol. The cloud, communication, and ph ysical la yers are in terdep endent. This motiv ates an ov erall equilibrium concept called Gestalt Nash equilibrium (GNE). GNE requires each game to b e solved optimally giv en the results of the other games. Because this is a similar idea to the concept of b est resp onse in Nash equilibrium, w e call the m ulti-game framew ork a game-of-games. A comp osition of a FlipIt game G 1 (e.g., [2, 51]) and a signaling game G 2 (e.g., [1, 50]), depicted in Figure 14.5, has b een used to provide a strategic trust management in Internet of things (IoT) netw orks vulnerable to adv anced persistent threats. The game G 1 describ es the strategic in teractions b etw een an attac ker and a cloud service provider where the attac k er aims to gain con trol of the computing resources and the cloud service pro vider protects and audits the system. The game G 2 describ es the information asymmetry b et ween the sender 8 CHAPTER 14. CONTR OL CHALLENGES Figure 14.4: The net work connectivit y o ver time. of the message (i.e., the computational results) and the IoT as the receiver of the message. G 1 and G 2 are composed sequen tially as in Figure 14.5. An attack er and a defender play the FlipIt game for con trol of the cloud. Then, the winner sends a command to the device in the signaling game. The Gestalt Nash equilibrium of the meta-game predicts the risk of sequential adv ersarial interactions. As sho wn in Figure 14.6, the equilibrium can b e computed as the in tersection of blue and red curves in an iterative manner within a finite n umber of steps. 14.3 Resiliency for Decen tralized Con trol Systems Resilien t design for distributed systems requires engineering agen ts with flexible interoper- abilit y and the capability of self-adaptability , self-healing, and resiliency . It is important that systems can ac hieve its ob jective when one no de go es a wa y or fails. In addition, a subsystem can resp ond to other subsystems in a non-deterministic/sto c hastic wa y . Suc h a design increases the comp osabilit y and modularity of the system design. F or example, agen ts can randomly arriv e and resp ond in a sto c hastic but structured w ay to other agents in an uncertain en vironmen t. Ho wev er, the structured randomness leads to emerging system b eha viors that manifest desirable prop erties for the ob jective of the en tire mission. Systems that hav e suc h prop erties are easily comp osable and resilien t-b y-design. With- out a pre-planned integration among agen ts, the agents can adapt their resp onses and reconfigure their own systems based on the type of agents with whom they interact. Agen ts can be easily comp osed to achiev e a prescrib ed ob jective through an unprescribed path. In adv ersarial en vironments, the agents can reconfigure their resp onses and roles to achiev e the global mission in spite of the failures of nodes and links. The system can still operate when one piece is missing. It is the epicenter of the mosaic designs. W e can leverage the games-in-games principle as discussed in [64] and [28] to provide a theoretical underpinning and a guideline for distributed resilien t control designs. The 14.3. RESILIENCY FOR DECENTRALIZED CONTR OL SYSTEMS 9 F lipI t G ame Sig naling G ame D move Control time type message message message message action action action action A move D move D move A move A move A move Figure 14.5: Conceptual mo del of the comp osed G 1 and G 2 . games-in-games approac h integrates three lay ers of design for eac h agent: strategic lay er, tactical lay er, and mission la yer. A t the strategic la yer, the agen ts learn and resp ond to their environmen t quickly to unan ticipated even ts such as attac ks, disruptions, and c hanges of other agen ts. A t the tactical lay er, the agen ts plan for a more extended p eriod of time b y taking in to accoun t the long-term interactions with the en vironmen t and other agents. The agents can mak e goal-orien ted planning at each stage. At the mission la yer, the agen ts dev elop stage-b y-stage planning of multi-stage ob jec tiv es to ac hieve the mission despite the uncertain ties and online c hanges. Eac h lay er corresp onds to a game of a different scale. F or example, at the tactical la yer, a game asso ciated with an agen t describes its interaction with an adversary (e.g., a jammer, a sp o ofer, or a sudden loss of a neigh b oring no de). Solutions to this game can prepare nodes for unan ticipated attacks and secure the agen ts. At the strategic la yer, an N -p erson dynamic game describ es the longer-term interactions among co operative agents, eac h seeking control p olicies to achiev e individual stage ob jectiv es. The individual control w ould lead to achievin g global ob jectiv es (such as connectivity and netw ork formation). A t the mission la y er, eac h agen t plans their stage ob jectives for each stage at the tactical la yer. This planning is ob viously under a lot of uncertainties and needs to b e ac hieved in a mo ving-horizon w ay . The games-in-games framework enables securit y and resilience by design. F rom the p er- sp ectiv e of security , the framework anticipates the attack b eha vior and designs a control p olicy that w ould prepare to defend against the anticipated attacks. The framew ork pro- vides a clean-slate design and built-in security for each system comp onen t that w ould lead to the securit y of the integrated system. F rom the p erspective of resiliency , the framework enables each system to resp ond to the unan ticipated even ts at each time instan t. Each 10 CHAPTER 14. CONTR OL CHALLENGES 0 0.05 0.1 0.15 0.2 p 0 1 2 3 4 5 6 7 ¯ u S A / D ˜ T F , ˜ T S , and Itera tive 1 p, ¯ u S A / D 2 Iter ative 1 p, ¯ u S A / D 2 Sig naling G ame Flip It Gam e Figure 14.6: Iterations to compute a Gestalt Nash equilibrium. agen t can resp ond to even ts that inflict damages on the agent and go through a self-healing pro cess that can recov er itself from the attacks and failures if p ossible. If the full recov- ery is not achiev able, the agen ts will develop con trol strategies that will allow a graceful p erformance degradation. 14.4 Conclusions and New Challenges This c hapter has introduced tw o key challenges for resilient con trol systems. One is the cross-la yer c hallenge requiring an in tegrated cyber-physical p ersp ectiv e. The optimal design piv ots on the understanding of the tradeoffs b et w een the security at the cyb er la yer and the res iliency at the ph ysical lay er. The other is the cross-stage resiliency mechanism that requires three stage resiliency design including ex-ante planning, in terim op eration, and ex-p ost reco very . The games-in-games framework pro vides a design paradigm for the multi- stage and multi-la y er design of resilient control systems. The framew ork is particularly useful for distributed con trol systems b y designing mo dular agen ts that can w ork together. The chapter has presented t wo applications. One is the control of autonomous vehicles in adversarial environmen t and the other one is the cross-lay er defense for cloud-enabled IoCTs. The metho dology presented in these tw o case studies can b e further generalized and made applicable to other systems, including smart grids, transportation systems, and man ufacturing systems. The new challenge with these large-scale systems is the scalability of the solutions and the incompleteness of the situational aw areness. The resiliency design w ould need mechanisms that can achiev e scalable y et suboptimal resiliency and deal with time delay and non-global system state information. 14.5. FUR THER READING 11 14.5 F urther Reading Game-theoretic metho ds hav e b een widely used to model adversarial b eha viors in wireless comm unications (See [18, 62, 71, 73, 74, 78, 79]), netw ork configuration (See [20, 34, 70, 76]), and con trol systems (See [35, 47, 52, 64, 66, 68]). The applications of security games hav e addressed the critical infrastructure protection (See [3, 11, 26, 45, 72]), cyb er insurance (See [14, 58, 60, 61]), cyb er deception (See [21, 27, 39, 40, 63, 69]), adversarial machine learning (See [29, 42, 57, 59]), and net work systems (See [7, 12, 17, 43, 56]). Game-theoretic approaches ha ve also addressed the resilient design of con trol systems. Games-in-games approach has been proposed Section 14.2.1 is based on the work of [9, 15] in whic h tw o lay ers of mobile agents are controlled to main tain net work connectivit y . Section 14.2.2 is based on the work of [38, 41]. The Internet of Con trolled Things (IoCTs) extends the concept of Internet of Things (IoTs) and studies a cloud-enabled sensing and actuation arc hitecture with three lay ers of in teracting systems including the cloud, communication net works, and sensor-actuator netw orks. The games-in-games principle was first discussed in [64] and has b een used for addressing applications of multi-la y er netw orks (See [6, 37, 52, 53, 54, 55]) and trust management (See [38, 41, 43]). The recent b ook [77] has provided a comprehensiv e introduction to game- and control-theoretic tec hniques for cross-lay er cyb er- ph ysical systems. One imp ortant application of resilient control systems is critical infrastructures, includ- ing p o w er grids, transp ortation, and manufacturing systems. They are often legacy systems that mo dern ICT tec hnologies build on to impro v e their efficiency and expand their func- tionalities. Due to the large-scale nature of critical infrastructures, their resilience has to b e designed in a decen tralized manner. It is critical to understand and capture the interconnec- tions b et ween components within the infrastructure as well as the interdependencies among differen t infrastructures. Netw ork mo deling and design approaches (e.g., [48, 80, 81, 82]) ha ve been used to provide a holistic framew ork for understanding cyb er-ph ysical interde- p endencies in infrastructure systems. Readers can refer to [16, 22, 23, 24, 44] for further materials on the topic of resilient in terdep enden t infrastructures. Resiliency for decentralized systems is a fundamen tal challenge for increasingly complex and connected systems. Recen t works [3, 4, 5, 6, 7] hav e addressed this issue from the p erspective of netw ork science. They hav e provided a design metho dology to create netw orks that are resistant to link remov als. In particular, [5] has provided a trade-off analysis b et w een the ex-an te robustness and the ex-p ost recov ery of the net w ork. This framew ork has also b een recently extended to the con text of multi-agen t systems, where multiple mobile agents comm unicate lo cally to accomplish a mission (e.g., rendezvous and formation). In terested readers can refer to [8, 10, 13, 36, 36, 37] for recent dev elopment on this topic. Chapter 12 of this b o ok introduces Grid Game, a simulation and learning platform for the electric grid and resilien t controls. It is a useful to ol to sim ulate and understand the m ulti-agent b eha viors describ ed in this c hapter in the context of electric p ow er systems. F or example, a multipla y er microgrid game has b een form ulated in [32] and its related extensions to m ulti-lay er games ha ve b een in tro duced in [10, 13, 33]. The decentralized arc hitecture of the multipla y er microgrids impro ves the resiliency of lo cal microgrids when they are sub ject to attac ks or natural failures. Readers can refer to Problem 14.3 for an exercise problem that builds on the Grid Game platform. 12 CHAPTER 14. CONTR OL CHALLENGES 14.6 Though tful Questions to Ensure Comprehension Problem 14.1 Consider a smart electric p ow er system, discuss the cross-lay er control c hallenges of the cyb er-enabled p o wer systems. Present metho ds to improv e the resiliency of the p o wer systems. Discuss ho w to scale the resiliency solutions when the size distribution and transmission net work increases. Hint: The r e aders c an r efer to the c ase studies in [64]. Problem 14.2 W rite down the dynamics of the unmanned aerial vehicles (UA Vs) and create a case study of a netw ork of five UA Vs. Simulate three steps by solving a sequence of three optimization problems (14.1). Use MA TLAB R ○ to presen t the sim ulation results. Hint: The c omplete description of the algorithm c an b e found in [15]. Problem 14.3 In this problem, w e will in v estigate the game-theoretic algorithms for dis- tributed energy systems. W e consider an energy system that consists of multiple microgrids that are mo deled as self-in terested play ers that can op erate, communicate, and interact autonomously to efficiently deliv er p o wer and electricity to their consumers. Consider a t wo-microgrid case where each of them aims to minimize the cost of pro duction and maxi- mize the qualit y of the p o wer qualit y . The utility function of this game has been describ ed in [10]. Use GridGame introduced in Chapter 12 to create a sim ulation platform of tw o pla yers. Implemen t the distributed algorithm in (11) in [10] for each microgrid and observe the behavior of the grid. Discuss the resiliency of the grid un der the follo wing t wo scenarios: (a) there is a false data injection attack on the PMU angle measuremen t; (b) One microgrid suddenly fails and cannot generate p o wer to meet the demand. Hint: The r e aders c an r efer to the c ase studies in Se ction IV-B of [10]. Bibliograph y [1] J. S. Banks and J. Sob el. Equilibrium selection in signaling games. Ec onometric a: Journal of the Ec onometric So ciety , pages 647–661, 1987. [2] K. D. Bo w ers, M. v an Dijk, R. Griffin, A. Juels, A. Oprea, R. L. Rivest, and N. T rian- dop oulos. Defending against the unknown enemy: Applying flipit to system security . In De cision and Game The ory for Se curity , pages 248–263. Springer, 2012. [3] J. Chen, C. T ouati, and Q. Zhu. A dynamic game analysis and design of infrastructure net work protection and recov ery: 125. ACM SIGMETRICS Performanc e Evaluation R eview , 45(2):128, 2017. [4] J. Chen, C. T ouati, and Q. Zh u. Heterogeneous multi-la yer adversarial netw ork design for the iot-enabled infrastructures. In GLOBECOM 2017-2017 IEEE Glob al Commu- nic ations Confer enc e , pages 1–6. IEEE, 2017. [5] J. Chen, C. T ouati, and Q. Zh u. A dynamic game approac h to strategic design of secure and resilient infrastructure net work. IEEE T r ansactions on Information F or ensics and Se curity , 15:462–474, 2019. [6] J. Chen, C. T ouati, and Q. Zh u. Optimal secure tw o-la yer iot netw ork design. IEEE T r ansactions on Contr ol of Network Systems , 7(1):398–409, 2019. [7] J. Chen, C. T ouati, and Q. Zhu. Optimal secure t wo-la y er IoT net work design. IEEE T r ansactions on Contr ol of Network Systems , 2019. [8] J. Chen, L. Zhou, and Q. Zh u. Resilien t con trol design for wind turbines using marko v jump linear system mo del with l ´ evy noise. In 2015 IEEE International Confer enc e on Smart Grid Communic ations (SmartGridComm) , pages 828–833. IEEE, 2015. [9] J. Chen and Q. Zh u. Resilien t and decentralized con trol of multi-lev el co operative mobile netw orks to maintain connectivity under adv ersarial environmen t. In IEEE Confer enc e on De cision and Contr ol (CDC) , pages 5183–5188, 2016. [10] J. Chen and Q. Zhu. A game-theoretic framew ork for resilient and distributed gener- ation con trol of renewable energies in microgrids. IEEE T r ansactions on Smart Grid , 8(1):285–295, 2017. [11] J. Chen and Q. Zhu. In terdep enden t strategic cyb er defense and robust switc hing con trol design for wind energy systems. In Power & Ener gy So ciety Gener al Me eting, 2017 IEEE , pages 1–5. IEEE, 2017. 13 14 BIBLIOGRAPHY [12] J. Chen and Q. Zhu. Security as a service for cloud-enabled internet of controlled things under adv anced p ersisten t threats: a contract design approac h. IEEE T r ansactions on Information F or ensics and Se curity , 12(11):2736–2750, 2017. [13] J. Chen and Q. Zh u. A stac kelberg game approach for tw o-lev el distributed energy managemen t in smart grids. IEEE T r ansactions on Smart Grid , 9(6):6554–6565, 2017. [14] J. Chen and Q. Zh u. A linear quadratic differen tial game approach to dynamic con tract design for systemic cyb er risk management under asymmetric information. In 2018 56th A nnual Al lerton Confer enc e on Communic ation, Contr ol, and Computing (Al lerton) , pages 575–582. IEEE, 2018. [15] J. Chen and Q. Zhu. Control of multi-la y er mobile autonomous systems in adversarial en vironments: A games-in-games approach. IEEE T r ansactions on Contr ol of Network Systems , pages 1–1, 2019. [16] J. Chen and Q. Zh u. A Game-and De cision-The or etic Appr o ach to R esilient Inter de- p endent Network A nalysis and Design . Springer, 2019. [17] J. Chen and Q. Zhu. Interdependent strategic security risk management with b ounded rationalit y in the In ternet of things. IEEE T r ansactions on Information F or ensics and Se curity , 14(11):2958 – 2971, 2019. [18] S. F arhang, Y. Ha yel, and Q. Zhu. Phy-la yer lo cation priv acy-preserving access p oint selection mechanism in next-generation wireless netw orks. In Communic ations and Network Se curity (CNS), 2015 IEEE Confer enc e on , pages 263–271. IEEE, 2015. [19] M. J. F aro oq and Q. Zhu. On the secure and reconfigurable multi-la yer net w ork design for critical information dissemination in the internet of battlefield things (iobt). IEEE T r ansactions on Wir eless Communic ations , 17(4):2618–2632, 2018. [20] C. J. F ung and Q. Zhu. F A CID: A trust-based collab orative decision framew ork for in trusion detection netw orks. A d Ho c Networks , 53:17–31, 2016. [21] K. Hor´ ak, Q. Zhu, and B. Bo ˇ sansk` y. Manipulating adversary’s b elief: A dynamic game approac h to deception by design for proactive netw ork securit y . In International Confer enc e on De cision and Game The ory for Se curity , pages 273–294. Springer, 2017. [22] L. Huang, J. Chen, and Q. Zhu. A large-scale marko v game approach to dynamic protection of in terdep enden t infrastructure net w orks. In International Confer enc e on De cision and Game The ory for Se curity , pages 357–376. Springer, 2017. [23] L. Huang, J. Chen, and Q. Zh u. Distributed and optimal resilient planning of large- scale in terdep enden t critical infrastructures. In 2018 Winter Simulation Confer enc e (WSC) , pages 1096–1107. IEEE, 2018. [24] L. Huang, J. Chen, and Q. Zhu. F actored mark ov game theory for secure in terdep enden t infrastructure netw orks. In Game The ory for Se curity and R isk Management , pages 99–126. Springer, 2018. BIBLIOGRAPHY 15 [25] L. Huang and Q. Zh u. Adaptive honeyp ot engagement through reinforcement learning of semi-marko v decision pro cesses. In International Confer enc e on De cision and Game The ory for Se curity , pages 196–216. Springer, 2019. [26] L. Huang and Q. Zhu. A dynamic games approach to proactive defense strategies against adv anced p ersisten t threats in cyber-physical systems. CoRR , abs/1906.09687, 2019. [27] L. Huang and Q. Zhu. A dynamic games approach to proactive defense strategies against adv anced p ersisten t threats in cyb er-ph ysical systems. Computers & Se curity , 89:101660, 2020. [28] Y. Huang, J. Chen, L. Huang, and Q. Zh u. Dynamic games for secure and resilient con trol system design. National Scienc e R eview , page to app ear, 2020. [29] Y. Huang and Q. Zhu. Dec eptiv e reinforcemen t learning under adversarial manipula- tions on cost signals. arXiv pr eprint arXiv:1906.10571 , 2019. [30] S. Ja jo dia, A. K. Ghosh, V. Swarup, C. W ang, and X. S. W ang. Moving tar get de- fense: cr e ating asymmetric unc ertainty for cyb er thr e ats , volume 54. Springer Science & Business Media, 2011. [31] S. Ja jodia, V. Subrahmanian, V. Sw arup, and C. W ang. Cyb er de c eption . Springer, 2016. [32] S. Maharjan, Q. Zh u, Y. Zhang, S. Gjessing, and T. Basar. Dependable demand resp onse management in the smart grid: A stack elb erg game approach. IEEE T r ans- actions on Smart Grid , 4(1):120–132, 2013. [33] S. Maharjan, Q. Zhu, Y. Zhang, S. Gjessing, and T. Ba¸ sar. Demand resp onse man- agemen t in the smart grid in a large p opulation regime. IEEE T r ansactions on Smart Grid , 7(1):189–199, 2015. [34] M. H. Manshaei, Q. Zhu, T. Alp can, T. Bac¸ sar, and J.-P . Hubaux. Game theory meets net work securit y and priv acy . ACM Computing Surveys (CSUR) , 45(3):25, 2013. [35] F. Miao, Q. Zh u, M. Pa jic, and G. J. P appas. A h ybrid sto c hastic game for secure con trol of cyb er-ph ysical systems. A utomatic a , 93:55–63, 2018. [36] Y. Nugraha, A. Cetink ay a, T. Hay ak aw a, H. Ishii, and Q. Zh u. Dynamic resilient net- w ork games with applications to m ultiagent consensus. IEEE T r ansactions on Contr ol of Network Systems , 8(1):246–259, 2021. [37] Y. Nugraha, T. Hay ak aw a, A. Cetink ay a, H. Ishii, and Q. Zh u. Subgame p erfect equilibrium analysis for jamming attacks on resilien t graphs. In 2019 Americ an Contr ol Confer enc e (ACC) , pages 2060–2065. IEEE, 2019. [38] J. Pa wlic k, J. Chen, and Q. Zhu. iSTRICT: An in terdep enden t strategic trust mec ha- nism for the cloud-enabled In ternet of controlled things. IEEE T r ansactions on Infor- mation F or ensics and Se curity , 14(6):1654–1669, 2018. 16 BIBLIOGRAPHY [39] J. Pa wlic k, E. Colb ert, and Q. Zhu. Mo deling and analysis of leaky deception us- ing signaling games with evidence. IEEE T r ansactions on Information F or ensics and Se curity , 14(7):1871–1886, 2018. [40] J. Pa wlic k, E. Colb ert, and Q. Zhu. A game-theoretic taxonom y and survey of defensiv e deception for cyb ersecurit y and priv acy . ACM Computing Surveys (CSUR) , 52(4):82, 2019. [41] J. P awlic k, S. F arhang, and Q. Zh u. Flip the cloud: Cyb er-ph ysical signaling games in the presence of adv anced persistent threats. In International Confer enc e on De cision and Game The ory for Se curity , pages 289–308. Springer, 2015. [42] J. P awlic k and Q. Zhu. A Mean-Field Stac kelberg Game Approach for Obfuscation Adoption in Empirical Risk Minimization. arXiv pr eprint arXiv:1706.02693 , 2017. [43] J. P awlic k and Q. Zhu. Strategic trust in cloud-enabled cyb er-ph ysical systems with an application to glucose con trol. IEEE T r ansactions on Information F or ensics and Se curity , 12(12):2906–2919, 2017. [44] G. Peng, J. Chen, and Q. Zhu. Distributed stabilization of tw o interdependent mark ov jump linear systems with partial information. IEEE Contr ol Systems L etters , 5(2):713– 718, 2020. [45] S. Rass, S. Sc hauer, S. K¨ onig, and Q. Zh u. Cyb er-Se curity in Critic al Infr astructur es: A Game-The or etic Appr o ach . Adv anced Sciences and T echnologies for Security Appli- cations. Springer, 2020. [46] S. Rass and Q. Zhu. GADAPT: a sequential game-theoretic framework for design- ing defense-in-depth strategies against adv anced p ersisten t threats. In International Confer enc e on De cision and Game The ory for Se curity , pages 314–326. Springer Inter- national Publishing, 2016. [47] C. Rieger, I. Ray , Q. Zhu, and M. Haney . Industrial Contr ol Systems Se curity and R esiliency: Pr actic e and The ory . Adv ances in Information Security . Springer, 2019. [48] S. M. Rinaldi, J. P . Peeren b oom, and T. K. Kelly . Iden tifying, understanding, and analyzing critical infrastructure interdependencies. IEEE c ontr ol systems magazine , 21(6):11–25, 2001. [49] J. B. Song and Q. Zhu. P erformance of dynamic secure routing game. In Game The ory for Networking Applic ations , pages 37–56. Springer, 2019. [50] M. Sp ence. Job market signaling. In Unc ertainty in e c onomics , pages 281–306. Elsevier, 1978. [51] M. V an Dijk, A. Juels, A. Oprea, and R. L. Rivest. Flipit: The game of “stealthy tak eov er”. Journal of Cryptolo gy , 26(4):655–713, 2013. [52] Z. Xu and Q. Zhu. A cyb er-ph ysical game framework for secure and resilien t multi- agen t autonomous systems. In 2015 54th IEEE Confer enc e on De cision and Contr ol (CDC) , pages 5156–5161. IEEE, 2015. BIBLIOGRAPHY 17 [53] Z. Xu and Q. Zh u. Cross-lay er secure c yber-physical control system design for net- w orked 3d printers. In 2016 Americ an Contr ol Confer enc e (ACC) , pages 1191–1196. IEEE, 2016. [54] Z. Xu and Q. Zhu. A game-theoretic approach to secure control of comm unication-based train con trol systems under jamming attac ks. In Pr o c e e dings of the 1st International Workshop on Safe Contr ol of Conne cte d and Autonomous V ehicles , pages 27–34. ACM, 2017. [55] Z. Xu and Q. Zhu. Cross-la yer secure and resilien t control of delay-sensitiv e netw ork ed rob ot operating systems. In 2018 IEEE Confer enc e on Contr ol T e chnolo gy and Appli- c ations (CCT A) , pages 1712–1717. IEEE, 2018. [56] H. Y unhan and Z. Quan yan. A differential game approach to decen tralized virus- resistan t w eight adaptation p olicy ov er complex net works. IEEE T r ansactions on Contr ol of Network Systems , pages 1–1, 2019. [57] R. Zhang and Q. Zhu. Secure and resilient distributed machine learning under ad- v ersarial environmen ts. In 2015 18th International Confer enc e on Information F usion (F usion) , pages 644–651. IEEE, 2015. [58] R. Zhang and Q. Zh u. A ttack-a w are cyb er insurance of in terdep enden t computer net works. 2016. [59] R. Zhang and Q. Zh u. A game-theoretic approac h to design secure and resilien t dis- tributed supp ort v ector mac hines. IEEE T r ansactions on Neur al Networks and L e arn- ing Systems , 2018. [60] R. Zhang and Q. Zh u. Flipin: A game-theoretic cyb er insurance framework for incen tive-compatible cyber risk management of in ternet of things. IEEE T r ansactions on Information F or ensics and Se curity , 2019. [61] R. Zhang, Q. Zhu, and Y. Ha yel. A bi-level game approach to attack-a w are cyb er insurance of computer netw orks. IEEE Journal on Sele cte d A r e as in Communic ations , 35(3):779–794, 2017. [62] T. Zhang and Q. Zh u. Strategic defense against deceptiv e civilian gps sp o ofing of unmanned aerial vehicles. In International Confer enc e on De cision and Game The ory for Se curity , pages 213–233. Springer, 2017. [63] J. Zheng and D. A. Casta ˜ n´ on. Dynamic netw ork in terdiction games with imp erfect information and deception. In 2012 IEEE 51st IEEE Confer enc e on De cision and Contr ol (CDC) , pages 7758–7763. IEEE, 2012. [64] Q. Zhu and T. Ba¸ sar. Game-theoretic metho ds for robustness, securit y , and resilience of cyb erph ysical control systems: games-in-games principle for optimal cross-lay er re- silien t con trol systems. Contr ol Systems, IEEE , 35(1):46–65, 2015. [65] Q. Zh u and T. Ba ¸ sar. Indices of p ow er in optimal ids default configuration: theory and examples. In De cision and Game The ory for Se curity , pages 7–21. Springer, 2011. 18 BIBLIOGRAPHY [66] Q. Zh u and T. Ba¸ sar. Robust and resilien t con trol design for cyber-physical systems with an application to p o w er systems. In 2011 50th IEEE Confer enc e on De cision and Contr ol and Eur op e an Contr ol Confer enc e , pages 4066–4071. IEEE, 2011. [67] Q. Zhu and T. Ba¸ sar. Game-theoretic approac h to feedback-driv en multi-stage mo ving target defense. In International Confer enc e on De cision and Game The ory for Se curity , pages 246–263. Springer, 2013. [68] Q. Zhu, L. Bushnell, and T. Ba¸ sar. Resilient distributed control of multi-agen t cyb er- ph ysical systems. In Contr ol of Cyb er-Physic al Systems , pages 301–316. Springer, 2013. [69] Q. Zhu, A. Clark, R. P o o vendran, and T. Ba¸ sar. Deceptive routing games. In 2012 IEEE 51st IEEE Confer enc e on De cision and Contr ol (CDC) , pages 2704–2711. IEEE, 2012. [70] Q. Zh u, C. F ung, R. Boutaba, and T. Ba ¸ sar. Guidex: A game-theoretic incen tive-based mec hanism for intrusion detection netw orks. Sele cte d A r e as in Communic ations, IEEE Journal on , 30(11):2220–2230, 2012. [71] Q. Zh u, H. Li, Z. Han, and T. Ba¸ sar. A sto c hastic game mo del for jamming in multi- c hannel cognitive radio systems. In 2010 IEEE International Confer enc e on Commu- nic ations , pages 1–6. IEEE, 2010. [72] Q. Zhu and S. Rass. On multi-phase and m ulti-stage game-theoretic mo deling of adv anced p ersisten t threats. IEEE A c c ess , 6:13958–13971, 2018. [73] Q. Zhu, W. Saad, Z. Han, H. V. P o or, and T. Ba¸ sar. Ea vesdropping and jamming in next-generation wireless netw orks: A game-theoretic approac h. In Military Communi- c ations Confer enc e (MILCOM), 2011 , pages 119–124. IEEE, 2011. [74] Q. Zhu, J. B. Song, and T. Ba¸ sar. Dynamic secure routing game in distributed cognitiv e radio net works. In Glob al T ele c ommunic ations Confer enc e (GLOBECOM 2011), 2011 IEEE , pages 1–6. IEEE, 2011. [75] Q. Zh u, H. T embine, and T. Ba ¸ sar. Net work security configurations: A nonzero-sum sto c hastic game approach. In Americ an Contr ol Confer enc e (A CC), 2010 , pages 1059– 1064. IEEE, 2010. [76] Q. Zh u, H. T embine, and T. Ba ¸ sar. Net work security configurations: A nonzero-sum sto c hastic game approach. In Pr o c e e dings of the 2010 Americ an Contr ol Confer enc e , pages 1059–1064. IEEE, 2010. [77] Q. Zhu and Z. Xu. Cr oss-L ayer Design for Se cur e and R esilient Cyb er-Physic al Systems: A De cision and Game The or etic Appr o ach . Springer Nature, 2020. [78] Q. Zh u, Z. Y uan, J. B. Song, Z. Han, and T. Ba¸ sar. Dynamic in terference minimization routing game for on-demand cognitive pilot channel. In Glob al T ele c ommunic ations Confer enc e (GLOBECOM 2010), 2010 IEEE , pages 1–6. IEEE, 2010. BIBLIOGRAPHY 19 [79] Q. Zh u, Z. Y uan, J. B. Song, Z. Han, and T. Ba ¸ sar. Interference a ware routing game for cognitiv e radio multi-hop netw orks. Sele cte d Ar e as in Communic ations, IEEE Journal on , 30(10):2006–2015, 2012. [80] R. Zimmerman, Q. Zhu, F. De Leon, and Z. Guo. Conceptual mo deling framework to in tegrate resilien t and in terdep enden t infrastructure in extreme w eather. Journal of Infr astructur e Systems , 23(4):04017034, 2017. [81] R. Zimmerman, Q. Zhu, and C. Dimitri. Promoting resilience for foo d, energy , and w ater in terdependencies. Journal of Envir onmental Studies and Scienc es , 6(1):50–61, 2016. [82] R. Zimmerman, Q. Zhu, and C. Dimitri. A net work framew ork for dynamic mo dels of urban foo d, energy and w ater systems (FEWS). Envir onmental Pr o gr ess & Sustainable Ener gy , 37(1):122–131, 2018.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment