Online detection of cascading change-points
We propose an online detection procedure for cascading failures in the network from sequential data, which can be modeled as multiple correlated change-points happening during a short period. We consider a temporal diffusion network model to capture …
Authors: Rui Zhang, Yao Xie, Rui Yao
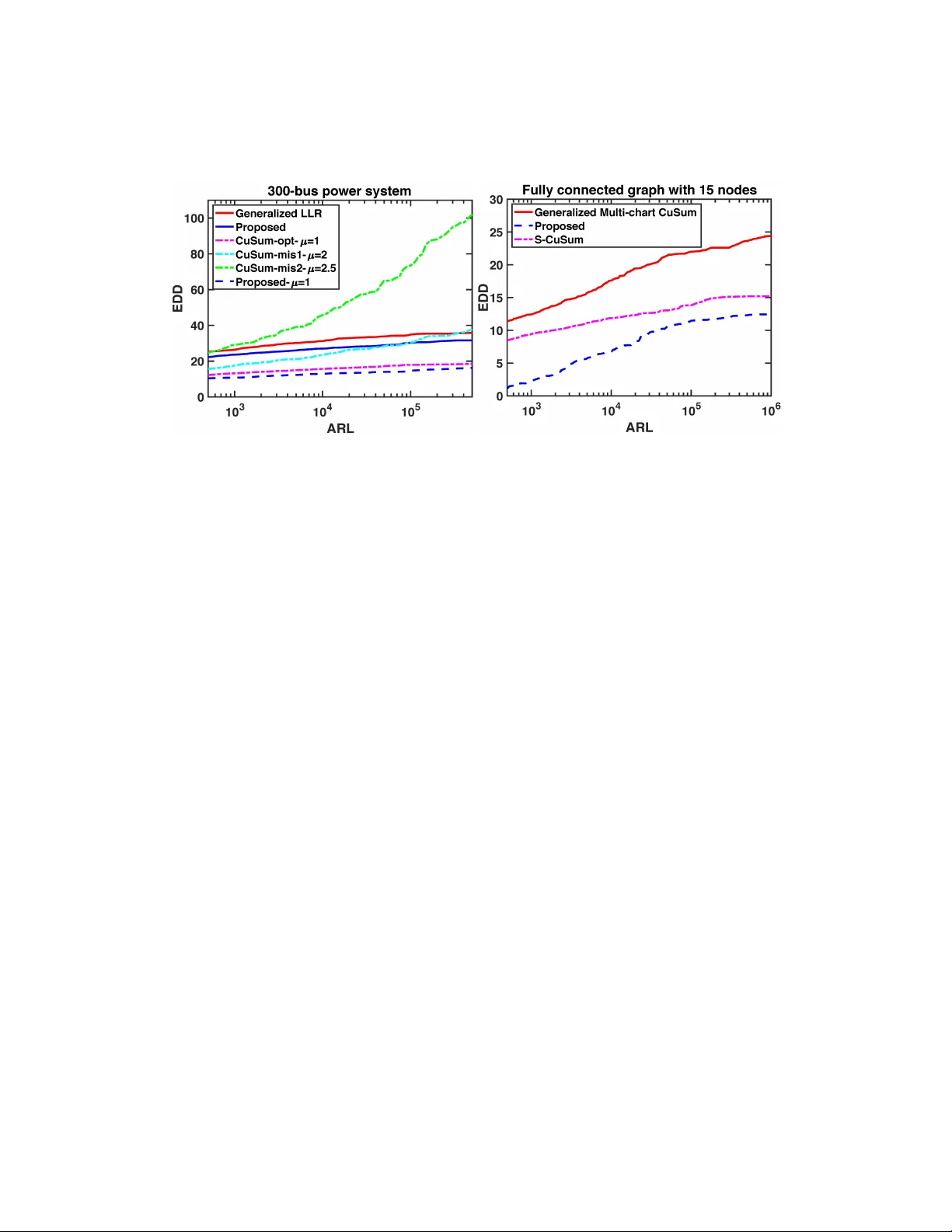
Online detection of cascading c hange-p oin ts Rui Zhang, Y ao Xie, Rui Y ao, F eng Qiu F ebruary 9, 2021 Abstract W e prop ose an online detection pro cedure for cascading failures in the net- w ork from sequen tial data, whic h can b e modeled as multiple correlated c hange- p oin ts happ ening during a short perio d. W e consider a temp oral diffusion net- w ork mo del to capture the temporal dynamic structure of m ultiple c hange- p oin ts and dev elop a sequential Shewhart pro cedure based on the generalized lik eliho o d ratio statistics based on the diffusion net work mo del assuming un- kno wn p ost-change distribution parameters. W e also tackle the computational complexit y p osed by the unknown propagation. Numerical exp eriments demon- strate the goo d performance for detecting cascade failures. 1 In tro duction Cascading failure is a critical problem for p o w er systems. A p o w er system consists of a large n umber of buses connected b y lines, so a failure or anomaly in one com- p onen t w eakens the whole system, mak es other components more vulnerable and increases their risk of malfunctioning. Cascading failure is the pro cess caused b y the initial failure of one component, which propagates to cause the consecutiv e failure of other components [1]. Cascading failures can often lead to ma jor blac k outs, and it is essen tial to deploy fast detection and effective mitigation. Online detection of cascading failure is a challenging task. In some cases, we can- not directly monitor a comp onen t’s failure but rather use indirect measuremen ts to detect the system’s c hanges and infer the failure. F or instance, [2] uses the difference b et w een the true and the estimated voltage angle, [3] uses the area angle to moni- tor the outage in the p o wer netw ork, and [4] uses auto-correlation in the frequency signal increases as the system is getting close to a critical slowdo wn and applies this prop ert y to detect a failure b efore it o ccurs. These studies demonstrate the v alue of measuremen ts in system monitoring and ev ent detection, but there has been little w ork on using measurements for the online detection of failures. A path forw ard for mo deling cascading failure is that the propagation of failures in a pow er system can b e mo deled as diffusion netw orks [5], whic h is popular for 1 transmission disease mo deling [6] and information diffusion in so cial net works [7]. Prior work [8, 9] also studied estimating the latent net w ork using multiple cascading cascade ev en ts p o wer systems. T o p erform online detection, w e assume that the underlying net w ork and the propagation mo del are giv en. But since the propagation is typically unkno wn since they can b e arbitrary and due to anomaly , we ha ve to infer the propagation of the net work’s failure using real-time measurements. This pap er dev elops an online change-point detection pro cedure for p ow er sys- tem’s cascading failure using multi-dimensional measuremen ts o ver the net works. W e incorp orate the cascading failure’s c haracteristic in to the detection procedure and mo del multiple changes caused by cascading failures using a diffusion pro cess ov er net works [10]. The mo del captures the prop ert y that the risk of comp onent failing increases as more comp onen ts around it fail. Our c hange-p oin t detection pro cedure using the generalized likelihoo d ratio statistics assuming unkno wn p ost-change pa- rameters of the measuremen ts and the true failure time (c hange-p oints) at eac h no de. Closely related works in the literature include the follo wing. Since a failure in the p o w er system can b e mo deled as a change-point when the distribution of measure- men ts changes, [11] examines a general setting with multiple c hange-p oints in m ultiple data streams without utilizing the graph top ology of the data streams. Several works consider the propagation of change-points: [12] considers change-point propagation in a line-type net w ork, [13] assumes that all p ossible propagation paths are equally lik ely , both of which prop osed a propagation mo del only dep ends on the last change- p oin ts. Ho wev er, multiple failure no des may influence the neighboring no des, suc h as outages in p ow er systems; [14] applies fuzzy neural net works to detect changes in measuremen ts and identify anomaly types. Recen t seminal work [15] studies a general c hange-p oin t detection framew ork while considering the ev en t propagation dynamics is unknown; in contrast, w e consider a sp ecific diffusion mo del for cascading failures motiv ated by pow er systems applications. 2 Problem Setup Consider a graph G = ( V , E ) , which is formed b y a set of no des V = { 1 , 2 , 3 , . . . , N } and a set of edges E ⊂ V × V . Here V corresp onds to the set of components in the p o wer netw ork, and E can b e constructed according to the ph ysical netw ork or in teraction graph [16, 17]. Assume G is undirected; X i,t ∈ R is the measuremen t of i th no de at time t , t = 1 , . . . , T . W e mak e the following assumptions ab out the c hange p oints, which corresp ond to the failure times at each no de. Assume the true failure time of the i th no de is τ ∗ i ∈ R + ∪ {∞} , and τ ∗ ( i ) denotes the corresp onding ordered failure time. When τ ∗ i = ∞ , it means that there is no failure on the i th no de. Let τ ∗ = ( τ ∗ 1 , τ ∗ 2 , . . . , τ ∗ N ) denote the v ector of all true failure times, whic h is unknown. 2 2.1 F ailure (c hange-p oint) propagation mo del Consider the follo wing cascading mo del for the propagation pro cess of the net work’s failures. W e assume that whenever a failure o ccurs on a node, it increases the neigh- b oring no des’ tendency to fail. Mathematically , we define the influence of no de i on no de j as α i,j > 0 . W e assume α j,i are kno wn since they can b e typically estimated b eforehand using historical and simulation data giv en on the top ology of the p ow er grid and p ow er flo w. W e do not know the distribution for the first failure. After the o ccurrence of the first failure, the distribution of the subsequen t failures is determined b y the conditional hazard rate (in tensit y function) λ i ( t ) : λ i ( t ) = ( P j :( j,i ) ∈E ,τ ∗ j t } ∆ t . The distribution of τ ∗ is uniquely define d by the c onditional hazar d r ate [10]. 2.2 Measuremen t mo del T o simplify the study , we assume that the measurements at each no de are indep en- den t, conditioned on the failure time. Before a c hange, they follow an i.i.d. standard normal distribution, and after a change they follow an i.i.d. normal distribution with an unkno wn mean and v ariance. That is, X i,t i . i . d ∼ ( N (0 , 1) , t < τ ∗ i , N ( µ i , σ 2 i ) , t ≥ τ ∗ i . (2) Since we can t ypically use a certain length of data as a warm start to estimate the sample mean and v ariance of the pre-c hange distribution, therefore we assume that the pre-c hange distribution is known and can b e standardized. 3 3 4 2 1 3 1 2 4 3 4 1 2 𝑇 𝜆 ! 𝜏 " ∗ 𝜏 $ ∗ 𝜏 % ∗ 𝛼 " ,! 𝛼 % ,! + 𝛼 " ,! 𝛼 $ ,! + 𝛼 % ,! + 𝛼 " ,! 𝛼 " , ! 𝛼 " , ! 𝛼 % , ! 𝛼 " , ! 𝛼 % , ! 𝛼 $ , ! Figure 1: Example of how cascading failure propagates o ver net works. The failure initiate at no de one, then all the neighbors of no de one are affected, and no de t wo and no de four fail ev en tually . As the failure propagates, no de three is surrounded b y more and more failed no des, and its hazard rate contin ues to increase. Here, red circles corresp ond to failed no des, solid y ellow lines are p ossible paths for failures to diffusion, dashed yello w lines corresp ond to paths with failed no des at b oth ends, y ellow circles are nodes affected b y failed neigh b ors. 2.3 Lik eliho o d function A ccording to the abov e mo dels, in a time window [0 , T ] , giv en measurements and failure times, prop osition 2.1 is the lik eliho o d function. Prop osition 2.1. A c c or ding to the mo del define d by Equation (1) and Equation (2), the likeliho o d function for a given τ ∗ and X i,t in [0 , T ] c an b e expr esse d as the fol lowing: f ( τ ∗ i , X i,t , ∀ i = 1 , . . . , N , t = 1 , . . . , T ) = N Y i =2 f ( τ ∗ ( i ) | τ ∗ (1) · · · τ ∗ ( i − 1) ) | {z } ( a ) · N Y i =1 T Y t =1 f ( X i,t | τ ∗ i ) | {z } ( b ) (3) wher e the term (a) c aptur es the failur e pr op agation mo del and term (b) c aptur es the me asur ement mo del. Pr o of. A ccording to mo del (2), giv en change-points τ ∗ , X i,t are indep enden t. i.e. f ( X i,t , i = 1 , . . . , N , t = 1 , . . . , T | τ ∗ ) = N Y i =1 T Y t =1 f ( X i,t | τ ∗ i ) (4) A ccording to [10], the lik eliho o d of a failure no des is the pro duct of the surviv al probabilit y up to the failure time and the hazard rate at the failure time, i.e. for 4 τ ∗ i < T f ( τ ∗ i |{ τ ∗ 1 , . . . , τ ∗ N } \ τ ∗ i ) = λ i ( τ ∗ i ) exp − Z τ ∗ i 0 λ i ( t ) dt . (5) F or a no de which has no failure b efore time T , the likelihoo d of it is the surviv al function up to time T , i.e. for τ ∗ i > T : f ( τ ∗ i |{ τ ∗ 1 , . . . , τ ∗ N } \ τ ∗ i ) = exp − Z T 0 λ i ( t ) dt . (6) A ccording to the definition of hazard rate (1), λ i ( t ) only dep ends on the change-points b efore time t . Therefore, we hav e f ( τ ∗ 1 , . . . , τ ∗ N ) = N Y i =2 f ( τ ∗ ( i ) | τ ∗ (1) . . . , τ ∗ ( i − 1) ) . (7) Com bine the ab ov e and (4), w e hav e the follo wing: f ( τ ∗ i , X i,t , i = 1 , . . . , N , t = 1 , . . . , T ) = f ( τ ∗ 1 , . . . , τ ∗ N ) f ( X 1 , 1 , . . . , X N ,T | τ ∗ 1 , τ ∗ 2 , . . . , τ ∗ N ) = N Y i =2 f ( τ ∗ ( i ) | τ ∗ (1) . . . , τ ∗ ( i − 1) ) N Y i =1 T Y t =1 f ( X i,t | τ ∗ i ) . (8) Our metho d can b e extended in a more general setting. F or the failure propagation mo del, one can c ho ose differen t hazard functions. Three mo dels are pro vided in [10]. In our study , we c ho ose to use the exp onential mo del. F or the measurement mo del, one can select the differen t distribution, and the measuremen t can b e a high dimension. 3 Detection Pro cedure Consider the following sequential h yp othesis test for detecting a dynamic change. An alarm is raised when there are at least η change-points. T o p erform the online detection, at eac h time instance T w e consider the following hypothesis test: H 0 ,η ,T : τ ∗ ( η ) > T , H 1 ,η ,T : 0 ≤ τ ∗ ( η ) ≤ T . W e consider a Shewhart chart type pro cedure: at each time, w e ev aluate a general lik eliho o d ratio (GLR) statistics ov er a sliding windo w. The GLR statistic can handle the mean, and p ost-c hange distribution v ariance are unknown. As shown in (3), giv en the failure time and the measuremen ts, the likelihoo d can b e decoupled into tw o parts: the likelihoo d of the failure propagation mo del and the likelihoo d of measurement mo del, resp ectively . 5 3.1 Log lik eliho o d of failure propagation mo del Define C ( i ) = { j ∈ V | ( j, i ) ∈ E } to b e the set of the i th no de’s neighbors. Given τ , the log-lik eliho o d function for [0 , T ] is shown in prop osition 3.1: Prop osition 3.1. Given T , a set of failur e times τ = ( τ 1 , . . . , τ N ) , gr aph G , and p ar ameters α i,j ∀ i, j ∈ V , the lo g-likeliho o d function of the failur e pr op agation mo del is given by ` 1 ,T = log f ( τ 1 , τ 2 , . . . , τ N |{ α i,j } ) = X i : τ i ≤ T , τ i 6 = τ (1) n log X j ∈C ( i ) α j,i I ( τ j < τ i ) − X j ∈C ( i ) α j,i ( τ i − τ j ) + o − X i : τ i >T X j ∈C ( i ) α j,i ( T − τ j ) + , (9) wher e ( · ) + = max( · , 0) , and I ( · ) is the indic ator function. Pr o of. Com bine the mo del (1), equations (5) and (6), the log lik eliho o d of a failure no de is, ∀ τ i < T , log f ( τ i |{ τ 1 , . . . , τ N } \ τ i ) = log λ i ( τ i ) − Z τ i 0 λ i ( t ) dt = log X j ∈C ( i ) ,τ j <τ i α j,i − X j ∈C ( i ) ,τ j <τ i α j,i ( τ i − τ j ) . (10) The log-lik eliho o d function of a no de without failure b efore time T is, ∀ τ i > T , can b e written as log f ( τ i |{ τ 1 , . . . , τ N } \ τ i ) = − Z T 0 λ i ( t ) dt = − X j ∈C ( i ) ,τ j T for all i , Equation (9) equals 0 and ` T is the sum of log likelihoo ds of standard normal distribution for the measuremen ts on eac h no de, according to Equation (12). T o p erform the hypothesis test b etw een H 0 ,η ,T and H 1 ,η ,T , we need to search for τ such that the log-likelihoo d in (13) is maximized. Define U ( η ) = { τ : N X i =1 I ( τ i ≤ T ) ≥ η } , and L ( η ) = { τ : N X i =1 I ( τ i ≤ T ) ≤ η − 1 } . W e consider a Shewhart t yp e of detection pro cedure, and we ev aluate the test statis- tics with the data ov er a sliding windo w [ T − L + 1 , T ] , where L is the length of the windo w. T o detect a change for at least η c hange-p oints, we apply the follo wing GLR test statistics ∀ η = 1 , . . . , N : S η ,T = max τ ∈ U ( η ) ` T ( τ ) − max τ ∈ L ( η ) ` T ( τ ) . The corresp onding stopping time is Γ = inf { T > 0 : S η ,T > b } , for some preset threshold b . 7 4 Computationally Efficien t Algorithm W e would like to implement change detection online and detect the cascading changes as quickly as p ossible in practice. Th us, w e need a lo w-complexity algorithm and only searc h for propagation paths with at most m no des affected b y the failure. The computation cost of the maxim um likelihoo d under the alternative h yp othesis is high. F or instance, for a fully connected graph with N nodes with observ ations in time horizon T , the computation cost is O ( T m N ! / (( N − m )! m !) . W e aim to dev elop a computationally efficien t algorithm based on a pruning strategy (similar to the ideas in [18, 19]). Our prop osed algorithm is describ ed as in Algorithm 1, whic h w e describe b elo w in more details. T o reduce the computation cost, we prop ose a r andom sampling str ate gy as follows. Since the num b er of p ossible propagation paths in a fully connected net work gro ws exp onen tially as the n umber of no des increases. Define F as the failure set that con tains the failed no des, and R = { j / ∈ F : ∃ i ∈ F , α i,j > 0 } , as the risk set. Then, w e generate the next p ossible failure p oints b y randomly pic king P p oin ts in R without replacement with probability v ector p = ( p i ) i ∈R , where p i = ˜ p i ( X j ∈R ˜ p j ) − 1 , ˜ p i = X j ∈F α j,i . (14) With this sc heme, we reduce the num b er of paths to O ( N P m ) . T o further reduce computational complexity , w e also com bine the ab ov e with a Thinning algorithm b y exploiting the monotonicit y of e − x in volv ed in the likelihoo d function, whic h is summarize in Algorithm 3. Consider the likelihoo d T = e ` T , 2 ,i,T = e ` 2 ,i,T , 2 ,T = e ` 2 ,T , 1 ,T = e ` 1 ,T . Giv en a propagation path, w e need to compute the maximum T ( τ ) , which is the pro duct of 1 ,T and 2 ,T . Define the q th p ercen tile of the i th no de to b e l 2 ,i,q . Also define a lo w er bound l 1 for 1 ,T . Instead of maximizing T ( τ ) ov er all the possible c hoices, we maximize it only in a thinned set { τ : 2 ,i,T ( τ i ) ≥ l 2 ,i,q , ∀ i = 1 , . . . , N } ∩ { τ : 1 ,T ( τ ) ≥ l 1 } . Sp ecifically , given τ i , w e consider τ j ∈ { τ i + 1 , τ i + 2 . . . } ∪ { τ j : 2 ,j,T ( τ j ) ≥ l 2 ,j,q } , from the smallest to the largest un til 1 ,T < l 1 as shown in Figure 2. The computation cost of this step is O ( h ) , where h depends on the top ology of G , as w ell as parameters α i,j , l 1 and q . Moreo v er, we can show that h ≤ [ L (1 − q )] m . 8 0 5 10 15 20 25 30 35 40 45 𝝉 𝒊 𝝉 𝒊 + 𝟓 ℒ ",$ 𝑙 " Figure 2: Illustration of the searc hing strategy for τ j giv en the previous failure p oin t τ i . When searching τ j from τ i + 1 , we ha ve 1 ,T ( τ i + 4) > l 1 and 1 ,T ( τ i + 5) < l 1 ; by the monotonicit y of e − x , w e can stop searching at τ i + 5 . With the ab ov e strategies, w e can reduce the computation cost to O ( N P m h ) , whic h is linear to N , the netw ork’s size. As shown in the following n umerical examples, w e can no w efficiently compute the test statistics for a 300-bus p o w er system. W e com bine r andom sampling str ate gy and thinning to reduce the computation cost using a recursion function genNext as sho wn in Algorithm 2. 5 Numerical Examples In this section, w e p erform several n umerical examples to demonstrate our prop osed metho d’s p erformance and compare it to existing metho ds. W e consider tw o com- monly used p erformance metrics in c hange-p oin t detection: the av erage run length (ARL) (a large ARL means a lo w false alarm rate) and the expected detection dela y (EDD). More sp ecifically , for a stopping time Γ , w e define ARL as E 0 [Γ] , and we use E 1 [(Γ − τ ∗ (1) ) + ] as a measure for EDD (whic h is a common practice in literature (see, e.g., [20]), where E i denotes the exp ectation with the probabilit y measure under h yp othesis H i . As we increase the threshold, ARL t ypically increases exp onentially , whereas the EDD will increase linearly . A go o d change-point detection pro cedure should ha ve a small EDD, given the same ARL. W e consider t wo case studies: one is to detect the very first c hange in the netw ork, and the other is to detect the change when there are at least η change-points. In Case I, we compare our metho ds with generalized lik eliho o d ratio (GLR) and (CuSum), since CuSum is the optimal pro cedure when the parameter is known [21]) and GLR is a natural generalization of CuSum when the p ost-change parameter is unknown [22]. In Case I I, w e compare our metho d with the state-of-the-art, including the S-CuSum [15] 9 Algorithm 1: Cascading change-point detection Input : Data X i,T − L +1 , . . . X i,T , i = 1 , . . . N V ariables: • m : the maximal n umber of c hange-p oin ts • ` : log lik eliho o d given a set of change-points • τ : a set of change-points • r : path of c hange-p oints (sorted) • ` max , τ max , r max : b est log lik eliho o d and parameters • J : sets of p otential change-points of each no des • j : current depth of recursion • q : p ercentile to threshold the measuremen t likelihoo d • l 1 : threshold of failure propagation likelihoo d 1. j = 1 2. J ← compute p otential c hange-p oints using Thinning ( j , m , r , τ , q , l 1 , { X i,t } ) for x = 1 : N do for t in J ( x ) do p 1 = x , τ 1 = t `, r, τ = genNext ( j + 1 , m, r, τ , { X i,t } ) if ` > ` max then ` max = ` , r max = r , τ max = τ end end end 4. Return ( ` max , r max , τ max ) 10 Algorithm 2: genNext function Input : j , m , r , τ , Data { X i,t } V ariable K : a set of p oten tial nodes with change-point if j > m then ` ← compute log-lik eliho o d return( `, r, τ ) end J ← Thinning ( j , m , r , τ , q , l 1 , Data) K ← sample no des with the probabilit y as (14) for x in K do for t in J ( x ) do r j = x , τ j = t , `, r, τ = genNext ( j + 1 , m , r , τ , { X i,t } ) if ` > ` max then ` max = ` , r max = r , τ max = τ end end end Return ( ` max , r max , τ max ) Algorithm 3: Thinning function Input : j , m , r , τ , q , l 1 , Data { X i,t } 1. J = ∅ 2. compute l 2 ,x,q , ∀ x = 1 , . . . , N using giv en Data. for x = 1 : N \ r do for t = τ j : T do Giv en t and τ , compute L 2 ,x,T and L 1 ,T . if L 2 ,x,T > l 2 ,x,q then J ( x ) = J ( x ) ∪ t end if L 1 ,T < l 1 then exit for end end end 4. Return ( J ) 11 Figure 3: (Left) Comparison of CuSum, generalized lik eliho o d ratio, and the prop osed metho d. (Righ t) Comparison of generalized multi-c hart CuSum, S-CuSum, and the prop osed metho d. and a traditional metho d, Generalized Multi-char CuSum, b oth of which are suitable for Case II. Belo w the pre-c hange distribution is N (0 , 1) and p ost-c hange distribution is N (1 , 1) . Case I: Dete ct the first change-p oint. In Figure 3 (left), we sho w the results in a 300- bus p ow er system (see MA TPO WER [23]). In this relativ ely large system, w e apply our algorithm with L = 100 , q = 0 . 8 , P = 1 , l 1 = e − 5 , and m = 5 . Our detection statistic can b e computed quite efficien tly: the av erage computation time for each time step is less than 3 seconds. Dashed lines are the results when parameters are kno wn. In this scenario, w e compare our prop osed metho d with the exact CuSum and t wo missp ecified CuSum ( µ = 2 , 2 . 5 ). Solid lines are the results when parameters are unkno wn. In this scenario, w e compare our prop osed method with GLR. Ov erall, our metho d shows the best p erformance, whic h is reasonable because our metho d is not only based on the likelihoo d ratio but also considers the likelihoo d of failure propagation. Case II: Dete ct when ther e ar e at le ast η change-p oints. Here we compare our prop osed metho d with generalized multi-c hart CuSum, and S-CuSum [15], b ecause these are the most well-kno wn algorithms for tackling such problems. In this exp eriment, the graph is fully connected with 15 no d es. The parameters for the algorithm are L = 100 , q = 0 . 8 , P = 1 , l 1 = e − 7 , and m = 5 . W e set η = 3 . T o compute the ARL, we generate data with η − 1 affected nodes. The result in Figure 3 (righ t) sho ws that our method outp erforms b oth generalized m ulti-chart CuSum and S-CuSum. 12 6 Conclusion W e prop osed a computationally efficient algorithm to p erform the c hange-p oin t de- tection by mo deling the cascading failure as a temp oral diffusion pro cess in a net work. Numerical exp erimen ts show that our prop osed metho d demonstrates go o d p erfor- mance; for an IEEE 300-bus system, which is considered relatively large, our results sho w that the prop osed algorithm can scale up to larger systems. A c kno wledgemen t The work of Rui Zhang and Y ao Xie is supp orted by an NSF CAREER A w ard CCF- 1650913, and NSF CMMI-2015787, DMS-1938106, DMS-1830210. 13 References [1] R. Y ao, S. Huang, K. Sun, F. Liu, X. Zhang, and S. Mei, “A m ulti-timescale quasi-dynamic mo del for simulation of cascading outages,” IEEE T r ans. Power Syst. , v ol. 31, no. 4, pp. 3189–3201, July 2016. [2] R. A. Wiltshire, G. Ledwic h, and P . O’Shea, “A k alman filtering approach to rapidly detecting mo dal c hanges in p ow er systems,” IEEE T r ansactions on Power Systems , v ol. 22, no. 4, pp. 1698–1706, 2007. [3] I. Dobson, “New angles for monitoring areas,” in 2010 IREP Symp osium Bulk Power System Dynamics and Contr ol-VIII (IREP) . IEEE, 2010, pp. 1–13. [4] P . D. Hines, E. Cotilla-Sanchez, B. O’Hara, and C. Danforth, “Estimating dy- namic instabil it y risk by measuring critical slowing do wn,” in 2011 IEEE Power and Ener gy So ciety Gener al Me eti ng . IEEE, 2011, pp. 1–5. [5] J. Cao, D. Duan, L. Y ang, Q. Zhang, S. W ang, and F. W ang, So cial influenc e analysis in the big data er a: a r eview . Cam bridge Univ ersity Press, 2016, pp. 301–334. [6] E. A. Meirom, C. Caramanis, S. Mannor, A. Orda, and S. Shakk ottai, “Detecting cascades from w eak signatures,” IEEE T r ansactions on Network Scienc e and Engine ering , v ol. 5, no. 4, pp. 313–325, 2017. [7] S.-H. Y ang and H. Zha, “Mixture of mutually exciting pro cesses for viral diffu- sion,” in International Confer enc e on Machine L e arning , 2013, pp. 1–9. [8] I. Dobson, “Estimating the propagation and exten t of cascading line outages from utilit y data with a branching pro cess,” IEEE T r ansactions on Power Systems , v ol. 27, no. 4, pp. 2146–2155, 2012. [9] H. Ren and I. Dobson, “Using transmission line outage data to estimate cascading failure propagation in an electric p ow er system,” IEEE T r ansactions on Cir cuits and Systems II: Expr ess Briefs , v ol. 55, no. 9, pp. 927–931, 2008. [10] M. Gomez-Ro driguez, E. D. Balduzzi, M. DE, and B. Schölk opf, “Uncov ering the temp oral dynamics of diffusion net works,” in International Confer enc e on Machine L e arning , 2011. [11] Y. Chen and X. Li, “Comp ound sequen tial c hange p oin t detection in m ultiple data streams,” arXiv pr eprint arXiv:1909.05903 , 2019. [12] V. Ragha v an and V. V. V eerav alli, “Quic kest c hange detection of a mark ov pro- cess across a sensor array ,” IEEE T r ansactions on Information The ory , v ol. 56, no. 4, pp. 1961–1981, 2010. 14 [13] M. N. Kurt and X. W ang, “Multi-sensor sequen tial c hange detection with un- kno wn change propagation pattern,” IEEE T r ansactions on A er osp ac e and Ele c- tr onic Systems , 2018. [14] G. Rigatos, P . Siano, and A. Piccolo, “Neural netw ork-based approach for early detection of cascading ev ents in electric p ow er systems,” IET Gener ation, T r ans- mission & Distribution , vol. 3, no. 7, pp. 650–665, 2009. [15] S. Zou, V. V. V eera v alli, J. Li, and D. T o wsley, “Quick est detection of dynamic ev ents in netw orks,” IEEE T r ansactions on Information The ory , vol. 66, no. 4, pp. 2280–2295, 2020. [16] P . D. Hines, I. Dobson, E. Cotilla-Sanchez, and M. Eppstein, “D ual graph and random chemistry metho ds for cascading failure analysis,” in 2013 46th Hawaii International Confer enc e on System Scienc es . IEEE, 2013, pp. 2141–2150. [17] J. Qi, K. Sun, and S. Mei, “An interaction model for sim ulation and mitigation of cascading failures,” IEEE T r ansactions on Power Systems , vol. 30, no. 2, pp. 804–819, 2014. [18] G. Rigaill, “A pruned dynamic programming algorithm to recov er the b est seg- men tations with 1 to k_max change-points.” Journal de la So ciété F r ançaise de Statistique , v ol. 156, no. 4, pp. 180–205, 2015. [19] O. H. M. P adilla, Y. Y u, D. W ang, and A. Rinaldo, “Optimal nonparametric c hange p oin t detection and lo calization,” arXiv pr eprint arXiv:1905.10019 , 2019. [20] Y. Xie and D. Siegmund, “Sequential multi-sensor c hange-p oin t detection1,” The A nnals of Statistics , vol. 41, no. 2, pp. 670–692, 2013. [21] G. Lorden et al. , “Procedures for reacting to a c hange in distribution,” The A nnals of Mathematic al Statistics , v ol. 42, no. 6, pp. 1897–1908, 1971. [22] T. L. Lai, “Sequen tial analysis: some classical problems and new challenges,” Statistic a Sinic a , pp. 303–351, 2001. [23] R. D. Zimmerman, C. E. Murillo-Sánc hez, and R. J. Thomas, “Matp ow er: Steady-state op erations, planning, and analysis tools for pow er systems researc h and education,” IEEE T r ansactions on p ower systems , vol. 26, no. 1, pp. 12–19, 2010. 15
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment