Aggregating Privacy-Conscious Distributed Energy Resources for Grid Service Provision
The increasing adoption of advanced metering infrastructure has led to growing concerns regarding privacy risks stemming from the high resolution measurements. This has given rise to privacy protection techniques that physically alter the consumer's …
Authors: Jun-Xing Chin, Andrey Bernstein, Gabriela Hug
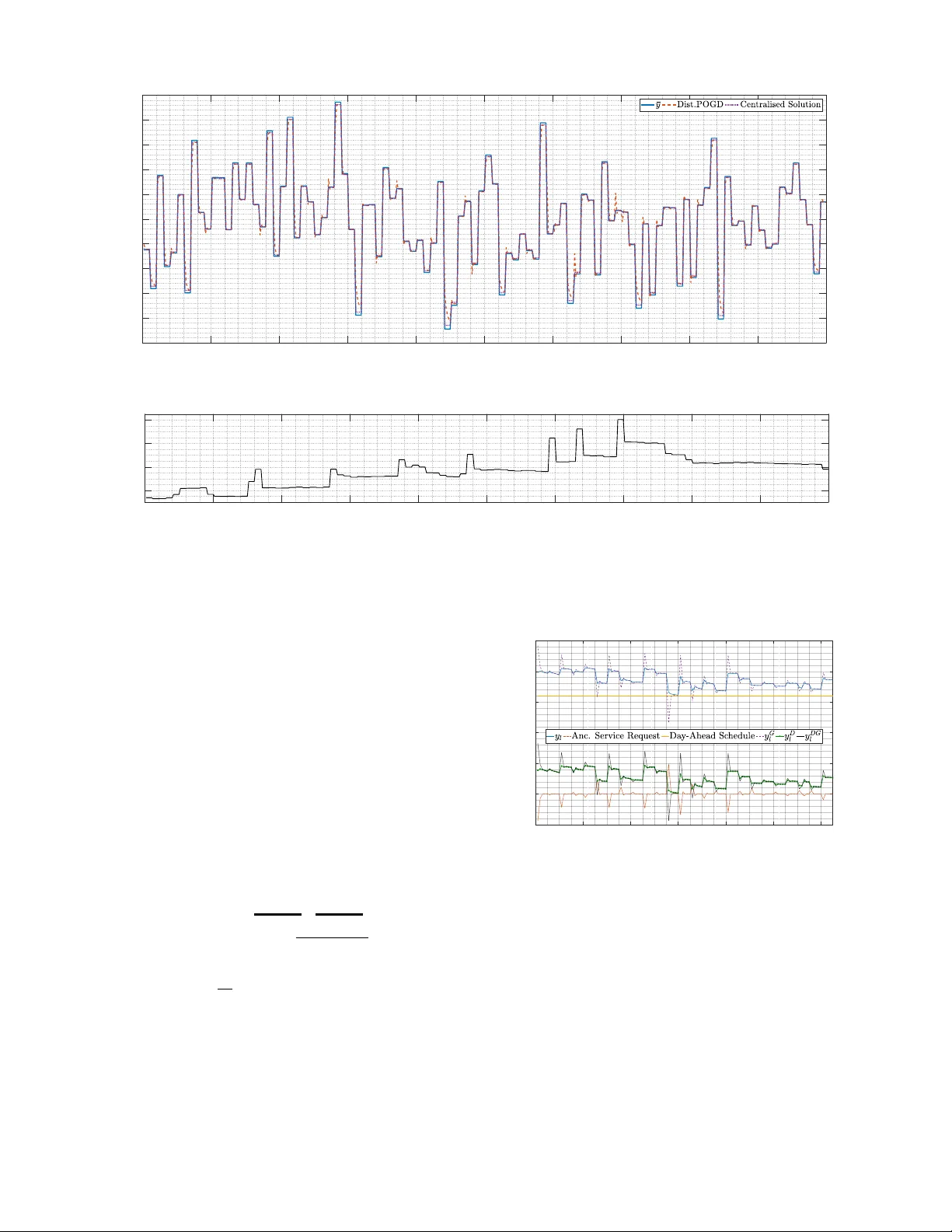
PREPRINT 1 Aggre gating Pri v ac y-Conscious Distrib uted Ener gy Resources for Grid Service Provision Jun-Xing Chin, Member , IEEE, Andrey Bernstein, Member , IEEE, and Gabriela Hug, Senior Member , IEEE Abstract —The increasing adoption of advanced metering in- frastructure has led to growing concerns regarding privacy risks stemming fr om the high resolution measurements. This has given rise to privacy pr otection techniques that physically alter the consumer’ s energy load profile, masking private information by using localised devices, e.g. batteries or flexible loads. Mean- while, there has also been increasing interest in aggregating the distributed energy resources (DERs) of residential consumers to pro vide services to the grid. In this paper , we propose an online distributed algorithm to aggregate the DERs of privacy-conscious consumers to pro vide services to the grid, whilst preserving their privacy . Results show that the optimisation solution from the distributed method con verges to one close to the optimum computed using an ideal centralised solution method, balancing between grid ser vice pro vision, consumer prefer ences and pri vacy protection. More importantly , the distributed method preser ves consumer priv acy , and does not r equire high-bandwidth two-way communications infrastructure. Index T erms —Ancillary Services, Consumer Privacy , Online Gradient Descent, Mutual Information, Optimisation Methods, Smart Meter , Advanced Metering Infrastructure I . I N T RO D U C T I O N In recent years, the adoption rate of advanced metering in- frastructure (AMI) using smart meters (SMs) has risen steadily across the globe as part of grid modernisation ef forts. As of January 2017, 52% of the 150 million electricity consumers in the US have AMI [1], while in Europe, 13 member states are expected to hav e AMI adoption rates of over 95% by 2020 [2]. In Switzerland, 80% of all electricity meters are to be replaced with SMs by 2027 [3]. AMI pro vides high-frequency energy consumption measurements to utility operators, allowing for data-driv en grid management and planning techniques that promise to improve grid efficienc y and transparency . Howe ver , this data also entails serious priv ac y risks for consumers, as it rev eals their detailed electricity consumption profiles. Recent studies have shown that potential illnesses, religious practices, socio-demographic profile, and even appliances used can be inferred from AMI data through data analytics and non- intrusiv e load monitoring techniques [4]–[8]. A. Smart Meter Consumer Privacy These risks and recent dev elopments in consumer priv acy protection laws such as the European Union’ s General Data This work was supported in part by the Swiss National Science F oundation for the COPES project under the CHIST -ERA Resilient Trustworth y Cyber- Physical Systems (R TCPS) initiative. J.X. Chin, and G. Hug are with the Po wer Systems Laboratory , ETH Zurich, 8092 Zurich, Switzerland. Email: { chin | hug } @eeh.ee.ethz.ch. A. Bernstein is with the National Renewable Energy Laboratory , Golden, CO 80401, USA. Email: Andrey .Bernstein@nrel.go v Protection Regulation [9], hav e spurred the de velopment of priv ac y-enhancing methods for consumers with AMI, which can be split into two cate gories: smart meter data manipulation (SMDM) and user demand shaping (UDS) [10]. SMDM in volv es pre-processing the AMI data before it is reported, e.g., data aggregation, data anonymisation, and data obfus- cation. UDS, on the other hand, entails physically shaping the consumer demand such that the grid-visible load, i.e . , the grid load no longer reveals pri vate information present in the actual priv acy-sensiti ve consumer load . This is achieved by using behind-the-meter resources such as energy storage devices, flexible loads, and distributed energy sources. While the former may be cheaper to implement, they may impact the utility of the AMI data due to the distortion in the meter readings or may require trusted third parties, e.g, as proposed in [11], [12]. Moreover , as they do not tackle the issue on the physical lev el, i.e . , the actual energy flow , it might be possible to still decipher the actual consumption depending on the protection used [13]. One of the first UDS schemes is described in [14], where the authors implement a best ef fort scheme to keep the grid load constant. Howe ver , this has been shown to leak information whenev er there is a change in grid load [15], and has since been followed up by more complex schemes such as [16]– [19]. In [16], the authors propose a differential-pri v acy based protection scheme using an ideal battery to mask the on/off status of appliances while being cost-friendly . Using a model- distribution predicti ve control (MDPC) scheme that balances between minimising ener gy cost and a proxy for pri v acy loss, the authors in [17] show that a home energy controller can be designed to directly minimise an approximate of mutual information between the grid and consumer loads. And in [18], the authors propose Q-learning based pri vac y-enhancing control policies using electric vehicles (EVs), flexible thermal loads, and energy storage de vices to ov ercome limitations in modelling consumer load statistics. The control policies are tested on simulated load profiles with an ideal battery and a linearised thermal load model, and sho w that reasonable priv ac y-cost trade-off can be achie ved by combining a small battery with EVs and an air conditioning device. The authors in [19] deri ved fundamental bounds on mutual information priv ac y for consumers with rene wable energy sources (RES), both with and without an infinite battery , and proposed a sub- optimal priv acy-enhancing scheme for realistic cases (finite battery) based on stochastic gradient descent. Note that in the absence of a battery , priv acy can be enhanced through the curtailment of the available RES production. PREPRINT 2 B. Residential Demand Side Aggr e gation and UDS Schemes Meanwhile, the increasing av ailability of behind-the-meter resources, a.k.a. distributed energy resources (DERs), coupled with the roll-out of smart grid communications infrastructure has spurred the de velopment of demand-side management for smaller loads. Residential consumers, which have traditionally been neglected due to their size, are being aggregated in order to provide services to the grid. Residential demand side aggre- gation (RDSA) schemes can be divided into two main classes: direct load control, and incentiv e (signal) based schemes. The authors in [20] provide an ov erview of incentive based RDSA literature, and propose a multi-agent non-cooperati ve game framew ork for integrating RDSA schemes with home ener gy management systems (HEMSs). Nonetheless, limitations in communications infrastructure remain a challenge for most RDSA schemes [21]. One possible solution is the broadcast of a common signal as suggested in [22], though the design of the signal is still an activ e field of research; see, e.g., [23] and pertinent references therein. UDS priv acy protection methods, by their nature, lend themselves well to being a part of an RDSA scheme gi ven their inherent flexibility to alter grid load. Moreo ver , it is intuitiv e that priv acy-conscious consumers with UDS protection be considered potential DERs that can be aggregated to provide services to the grid. Howe ver , there are only few works on the design of priv acy-centric HEMSs for RDSA schemes, with most works focusing solely on the auction activ ation, or (and) accounting mechanisms, e.g., [24]–[26]. These works employ different cryptographic techniques in the RDSA mechanism in order ensure pri vac y while being able to attrib ute re wards to demand response participants, but do not provide designs for the automated HEMSs. C. Contrib utions and Outline In this paper , we design a HEMS for RDSA that also considers the consumers’ preferences and priv acy loss due to high-frequency SM measurements (SM priv acy), without the need for pervasi ve real-time AMI metering, a trusted third- party , nor two-w ay high-bandwidth communications infras- tructure to each consumer . Using an online projected gradient descent approach based on the framew ork in [27] and the SM priv ac y protection scheme in [17], the proposed RDSA scheme preserves the SM priv acy of consumers through UDS and omits the need for real-time information from each consumer . It is important to note that the allocation of re wards in RDSA schemes that do not directly control consumer loads typically rely on benchmarking metered consumption against historical records. Howe ver , in pri vate-by-design RDSA algo- rithms, save for a totally flat profile, individual benchmark profiles should not be discernible from measured grid-visible consumer load profiles. Otherwise, pri vate information could be inferred from repeated disclosures of a pri vate, but static grid-visible load profile. Hence, rewards for participation in a priv ate-by-design RDSA scheme in the absence of any trusted party can only be allocated based on the individual consumer’ s resource commitment. While this could result in a free-loader problem, such as those explored in game theoretic works, the resolution of this is outside the scope of this paper . The rest of this paper is organised as follo ws: Section II details the problem considered, Section III introduces the distributed solution method, Section IV presents and discusses simulation results and Section V concludes the paper , and presents an outlook for future work. I I . P RO B L E M F O R M U L A T I O N A N D S Y S T E M D E S C R I P T I O N W e consider the problem of a HEMS that is part of an RDSA scheme and is required to consider the consumer’ s pref- erences, and also priv acy-loss stemming from high-frequency smart meter measurements. Each consumer household consists of a DER, an HEMS controller , and a smart meter that is able to provide high-frequency measurements locally , but unable or unwilling to provide r eal-time high-frequency remote mea- surements to the utility provider or aggregator . The aggregator could be a distribution system operator or a third-party energy services provider that has the capability to broadcast high- speed uni-directional signals to each consumer , and is able to measure the real-time aggregated energy consumption of its consumers, e.g., at the sub-station or transformer . The general aggregator system setup is illustrated in Fig. 1(a). On the other hand, the adversary considered in the priv acy problem is assumed to be an y entity (including an untrusted utility provider) that has access to the high-frequency smart meter measurements, i.e. , there are no assumed trustworthy parties to which unprotected data is directly disclosed to. An ideal solution to the considered problem would directly disclose only the following data to third-parties: i. time-delayed high-frequency SM measurements from in- dividual consumers that are priv ac y-protected; ii. real-time high-frequency aggreg ated consumer consump- tion measurements at points-of-common-coupling. Additionally , we consider the case of the DER being a battery in this paper , but the proposed method can easily be extended to incorporate other DERs with con vex models. Fig. 1(b) illustrates the system considered at each consumer house- hold. The problem can be framed as solving the following optimisation program: minimise y l N X l =1 { Λ( y l ) + µ l Φ( y l ) } + ρ Γ( y ) subject to y l ∈ F l , l = 1 , . . . , N , (1) where N is the number of consumers in the aggregation, y l and µ l are the grid load and price of pri vac y loss for consumer l , respecti vely , Λ( y l ) is the consumer’ s utility (preference) function, Φ( y l ) is a measure of real time pri vac y-loss, ρ is the coefficient for grid service provision, Γ( y ) giv es a measure of the grid service provided (e.g., tar get load or ancillary service tracking signal), and y := [ y 1 , y 2 , · · · , y N ] T is a v ector of consumer grid loads. The set F l , defined by the constraints: 0 ≤ s + l ≤ s + ,max l (2) 0 ≤ s − l ≤ s − ,max l (3) 0 ≤ e l + ∆ t ( η l s + l − 1 η l s − l ) ≤ e cap l (4) PREPRINT 3 Ag grega tor Real - t ime Inf ormation Fl ow Energy Flow Privacy Awa re Consumers (a) RDSA Aggregator System S m a rt Me t e r S y s te m H E MS C o n t r o l l e r E n e r g y St o r ag e L o a d A g g r e g a t o r Re a l - t i me In f o r ma t i o n F l o w En e r gy F l o w (b) Setup at Consumer Household Fig. 1. System setup at consumer households and the aggregator system y l = x l + s + l − s − l (5) y min l ≤ y l ≤ y max l (6) enforces the system constraints for consumer l . Here, s + l , s − l denote the battery’ s charging and discharging po wer; s − ,max l , s + ,max l denote the battery’ s maximum discharging and charg- ing po wer rating; η l denotes the battery’ s charge/discharge efficienc y; e l is the battery state of charge; e cap l is the battery capacity; y min l and y max l are the minimum and maximum allow able grid loads; x l denotes the instantaneous consumer load; and ∆ t is the time interval between each control action. For the rest of the paper , A l denotes a random variable, a l denotes its realisation, log is the base-2 logarithm, A t denotes the sequence ( A 1 , A 2 , · · · , A t ), A is the range space for variable A , and p A ( a ) is the probability of A = a . The functions Λ( y l ) , Φ( y l ) and Γ( y ) are described in the following. A. Consumer Pr efer ences The function Λ( y l ) can be any con vex utility function that reflects the consumer’ s preferences. For simplicity , we con- sider a function that penalises deviations from the consumer’ s day-ahead grid-load schedule, given by Λ( y l ) := k y l − y r ef l k 2 2 , (7) where y r ef l is the day-ahead planned consumption. This sched- ule can include the consumer’ s preferences on a grid visible load profile, energy cost optimisation and battery state-of- charge requirements. B. Privacy Loss Pr oxy There has yet to be a consensus amongst researchers on the best measure of priv acy loss for consumers with AMI. The authors in [28] found that the percei ved levels of SM priv acy are greatly affected by the different priv acy measurement methods, and that the priv acy guarantees giv en by protection schemes based on these various methods are also highly dependent upon the underlying load profiles. Ne vertheless, one widely accepted measure for priv acy loss stemming from an adversary that has access to the individual grid-visible load profiles captured by the SMs is mutual information (MI) [10], [15]. A method to tractably approximate MI in an optimisation problem for a single consumer is proposed in [17]. In this work, we adapt the MI approximate dev eloped in [17] as the pri vac y loss objecti ve for multiple priv acy-conscious con- sumers in the RDSA scheme. Let X l ∈ X l and Y l ∈ Y l denote the random v ariables modelling the instantaneous consumer load and the total grid load, respectively . For the purpose of estimating the MI only , we assume that these random variables are discrete and ha ve finite support. In particular, ˜ X l = { x 0 l , x 1 l , · · · , x m l } , ˜ Y l = { y 0 l , y 1 l , · · · , y n l } , where m and n are the number of bins used to quantise the consumer and grid loads, respectiv ely , and I ( X l ; Y l ) ≈ I ( ˜ X l ; ˜ Y l ) . The MI function for discrete random v ariables is given by I ( ˜ X l ; ˜ Y l ) := X x l ∈ ˜ X l X y l ∈ ˜ Y l p ˜ X l , ˜ Y l ( x l , y l ) log p ˜ X l , ˜ Y l ( x l , y l ) p ˜ X l ( x l ) p ˜ Y l ( y l ) , where p ˜ X l , ˜ Y l , p ˜ X l , and p ˜ Y l are the approximated joint and marginal probability distribution functions (PDFs) of the random v ariables. In order to formulate MI as a function of the next grid load realisations, binary variables z l = { z ij l } m,n i =1 ,j =1 ∈ Z l = { 0 , 1 } m × n are introduced in [17] to relate the grid load v ariable, y l to its statistics. More specifically , the variables z ij l count the frequenc y of y l when estimating its statistics using the histogram method. Giv en that the value of x l falls in the i -th bin, for each v alue of y l , there exists exactly one non-zero z ij l representing the bin where y l falls. Using z l as the optimisation variables, an approximation of the MI function, ˜ I ( z l ) is then formulated as an optimisation objectiv e [17]. A brief summary on the deri vation of ˜ I ( z l ) is provided in online Appendix A [29]; further details can be found in [17]. Here, we relax the binary constraints on z l , i.e. z l ∈ Z 0 l = [0 , 1] m × n and allow that for each value of y l , there exists a set of non-zero z ij l within the feasible set. Effecti v ely , this relaxes the constraints imposed on y l by z l , thereby af fecting the statistics percei ved by the controller , and hence, its priv acy protection performance [30]. Define then the set F 0 l as the set of all ( y l , z l ) that satisfies the constraints (2) to (6), in addition to the following constraints: n X j =1 z i ∗ j l = 1 (8) z ij l = 0 , ∀ i 6 = i ∗ (9) n X j =1 z i ∗ j l y j − 1 l ≤ y l < n X j =1 z i ∗ j l y j l , (10) where i ∗ is the index corresponding to the gi ven value of x l . Constraint (10) links the grid load to its PDF estimate. Furthermore, let Φ( y l ) = ˜ I ( z l ) for any z l satisfying ( y l , z l ) ∈ PREPRINT 4 F 0 l . ˜ I ( z l ) is a quadratic form that is strongly con ve x for m > 1 . This can be implied from [17] by relaxing the binary constraints and limiting the optimisation program to a single time step, and can be shown by analysing its algebraically manipulated form (see online Appendix B [29]). Note that ˜ I ( z l ) is only strongly conv ex for m > 1 . Furthermore, the gradient of ˜ I ( z l ) is bounded, thereby making ˜ I ( z l ) Lipschitz continuous. These properties will be used later to apply the online gradient descent method to solve (1). C. Ancillary Service Pr ovision W e consider the tracking of a target aggregate real power load profile as the ancillary service objectiv e, and penalise deviations from this target profile, i.e . , Γ( y ) := N X l =1 y l ! − ¯ y 2 2 , (11) where ¯ y is the target profile, and y = { y 1 , y 2 , . . . , y l } . This target profile can be shaped to provide services such as peak shaving, grid balancing, and congestion alleviation, or simply just to follo w a planned consumption profile. Moreover , in well designed systems, po wer flow constraints arising from the provision of ancillary services by DERs are considered during their pre-qualification stage. These constraints are then taken into account when aggregating them for service pro- vision; i.e. , the aggregation groups can be defined such that participants within a group face similar constraints, which are then accounted for when sending out service requests. Note that one could also track an additional target reactiv e power profile in order to provide voltage support, but this is left as the subject of future work. I I I . P RO J E C T E D O N L I N E G R A D I E N T D E S C E N T The overall optimisation problem is now gi ven by minimise y l , z l ,s + l ,s − l N X l =1 n Λ( y l ) + µ l ˜ I ( z l ) o + ρ Γ( y ) subject to ( y l , z l , s + l , s − l ) ∈ F 0 l , l = 1 , . . . , N , (12) which can be solved optimally using an of fline centralised controller by the aggregator if real-time high-resolution SM measurements and high-bandwidth communication links are av ailable. Howe v er , giv en that current AMI deployments poll for readings at intermittent intervals due to communication infrastructure bandwidth constraints, this solution method re- mains impractical. Moreover , this would also require that priv ate information from all consumers, i.e , their actual con- sumer load, priv acy preferences and day-ahead schedules, be rev ealed to the aggre gator , in validating the pri vac y protection objectiv e. Alternati vely , (12) can be solved using an of fline dis- tributed algorithm in the presence of two-way high-bandwidth communications infrastructure between scheme participants, which is again impractical for current grids. Therefore, we propose solving (12) using a distributed feedback-based online gradient descent solution method based on the general real- time feedback-based optimisation frame work proposed in [27]. The algorithm replaces the coupling of the grid load variables across consumers in (11) with the latest real-time aggre gated consumption measurement ˆ y at the point of common coupling: N X l =1 y l ≈ ˆ y . Hence, only the value k ˆ y − ¯ y k 2 2 is communicated in real- time, and is treated as a constant when computing the gra- dients. This makes (12) separable and solv able locally , over - coming the lack of real-time SM data and mitigating priv acy concerns. The av ailability of ˆ y can readily be assumed given the increasing adoption of phasor measurement units (PMUs), and that transformers or b usbars can easily be outfitted with a high-frequency measurement device. The use of ˆ y leads to a lagged and sub-optimal solution at each time step. Howe ver , by assuming that high-speed control actions can be actuated faster than the time-varying nature of (12), the distributed algorithm is shown to con ver ge to a centralised solution in [27], provided that the optimisation problem is strongly con ve x. Recall that (12) is strongly conv ex for m > 1 . Nev ertheless, we add a regularisation term k h k 2 2 with a small coefficient σ 2 / 2 , where h is the vector of all the optimisation v ariables; this ensures that (12) is at least σ 2 -strongly con ve x in all cases (e.g., when m = 1 , or when extending the algorithm to multiple time steps). It is easy to see that k h k 2 2 , which is the sum of the squares of the variables, is separable. Accordingly , let 1 ρ = σ 1 / 2 , and f ( y l , z l ) = N X l =1 n Λ( y l ) + µ l ˜ I ( z l ) o + σ 1 2 Γ( y ) + σ 2 2 k h k 2 2 . W e now solve the follo wing quadratic program, minimise y l , z l ,s + l ,s − l f ( y l , z l ) subject to ( y l , z l , s + l , s − l ) ∈ F 0 l , (13) locally at each HEMS by first taking a gradient descent step: ˜ s + l,t = s + l,t − 1 − r ∇ s + l,t f ( y l , z l ) (14) ˜ s − l,t = s − l,t − 1 − r ∇ s − l,t f ( y l , z l ) (15) ˜ z i ∗ j l,t = z i ∗ j l,t − 1 − r ∇ z i ∗ j l,t f ( y l , z l ) , j = 1 , . . . , n, (16) where r is the gradient descent step size, and ∇ A is the gradient with respect to A . The final solution is then obtained by projecting the interim solution onto the feasible set, i.e . , [ s + l,t , s − l,t , z i ∗ j l,t ] T = proj F 0 l [ ˜ s + l,t , ˜ s − l,t , ˜ z i ∗ j l,t ] T . (17) Only variables z i ∗ j l are updated at each time step, with variables z ij l for i 6 = i ∗ being treated as zero when computing the gradients for z i ∗ j l . Note that the actual v alues of z ij l , i 6 = i ∗ are not re-initialised as zero, and are kept for future time steps in order to ensure conv ergence. The gradients ∇ s + l,t f ( y l , z l ) , ∇ s − l,t f ( y l , z l ) , and ∇ z i ∗ j l,t f ( y l , z l ) are deriv ed from (5) and (13), then computed by substituting for ˆ y ; see online Appendix B for the details on the gradients [29]. 1 for simplicity in deriving the gradient PREPRINT 5 A. Battery Modelling The con ve x modelling of realistic batteries while av oiding physically infeasible but optimal decisions due to simultaneous charging and discharging remains a research challenge. There are numerous modelling methods, e.g., using binary v ariables, quadratic constraints, or penalising battery use, but they are either non-con ve x, or are inapplicable because simultaneous charging and discharging is allowed and is optimal for (12) in some scenarios. T o circumvent this issue, we assume that the battery is unable to go directly from charging to discharging, i.e , it must go through “zero”, ( s + > 0 , s − = 0) → ( s + = 0 , s − = 0) → ( s + = 0 , s − > 0) , and vice versa. This is a reasonable assumption giv en suffi- ciently fast control actions and limitations on certain power con verter designs. The proposed distributed projected online gradient descent algorithm incorporating this battery modelling work-around is summarised in Algorithm 1. W e note that the conv ergence of this algorithm is guaranteed provided that the step size r in (14) - (16) is small enough, as the optimisation problem defined by (13) satisfies the conditions identified in [27]; see [27] for details. The feasibility of the optimisation problem is also guaranteed as priv ac y requirements are formulated as a term in the objective function instead of a hard constraint. Algorithm 1 algorithm for solving (13) at time t 1: obtain aggregated load measurement ˆ y t − 1 2: obtain target load ¯ y t 3: compute k ˆ y t − 1 − ¯ y t k 2 2 and broadcast to consumers 4: f or consumer 1 to N do 5: obtain load forecast x l,t and battery state e l,t 6: if charge flag = true then 7: compute s + l,t and z i ∗ j l,t using (14), (16) and (17) 8: if s + l,t ≥ 0 then 9: actuate s + l,t and update z i ∗ j l,t 10: else 11: charge flag = false 12: actuate s + l,t = 0 and update z i ∗ j l,t 13: else 14: compute s − l,t and z i ∗ j l,t using (15), (16) and (17) 15: if s − l,t ≥ 0 then 16: actuate s − l,t and update z i ∗ j l,t 17: else 18: charge flag = true 19: actuate s − l,t = 0 and update z i ∗ j l,t 20: update constants ( a ij l , b j l , c i l ) used in the MI 21: approximation (see Appendix A in [29] for details) 22: advance to t + 1 I V . N U M E R I C A L E X P E R I M E N T S The proposed scheme is tested using 1 Hz smart meter data taken from the ECO dataset [31]. As there are only six houses in this dataset, we emulated more consumers in the RDSA scheme by drawing data from multiple days over the period between 26 August and 9 September , 2012 from the six households. This results in a dataset with homogeneous load profiles, which may decrease target aggregate load tracking performance. Giv en more heterogeneous load profiles (as in reality), the resultant aggregate load would likely be smoother as load peaks are compensated by load troughs, allo wing for better tracking. A. Simulation Setup Each household in the RDSA scheme was assigned a random price of priv acy loss, 1 ≤ µ l ≤ 9 , to mimic the beha viour of multiple real households. T o enforce the assumption that control actions are actuated faster than the time varying nature of (13), we assume that the local high frequency SM measurements have a resolution of 0.2 Hz, and that the target grid signal also v aries every 5 seconds, while the aggregated load measurements are av ailable ev ery second. These are realistic assumptions, as local HEMS controllers obtain measurements from smart meters deployed locally at each household, which have the ability to sample at 2kHz or higher; and aggregators receiving continuous real-time reserve provision signals may choose to broadcast a more stable signal, so long as they meet the requirements in their service contracts with the grid operator . Each household tracks an arbitrary day-ahead schedule, y r ef l , computed using a single multi-time step optimisation for energy costs and MI priv acy , at half-hourly resolution with the MDPC algorithm described in [17], and on a two-tier time-of-use energy tariff. Here, we define ˆ y = P N l =1 y l for simplicity , omitting grid losses, and assume that grid in-feed is not allo wed, i.e , y min l = 0 . Depending on network topology and size, the grid losses may impact the RDSA scheme’ s performance in reality , but this is outside the scope of this paper . The general system setup at each consumer household is summarised in T able I, where battery parameters were taken from the T esla Po werwall v1. The target aggregate load ¯ y is generated using the aggre- gated day-ahead consumer schedules as a base, considering total RDSA reserve capacity ¯ γ = N γ . For ease of assessment, this is designed such that the target load is energy neutral with respect to the aggreg ate day-ahead schedule within each half- hourly interval. When generating such a reference curve, we took into account battery losses (max bias of 0.1% of reserve capacity), and ensured that the aggre gate reserv es are sufficient to meet the ancillary service requests approximately 99.7% of the time. Unless otherwise stated, the simulation parameters are as listed in T able II where applicable. For ease of comparison and simplicity , we set aside battery energy capacity corresponding to γ at each consumer household in their day-ahead schedules, and assume that the battery model in the optimisation problem is accurate. The proposed distrib uted algorithm (abbreviated as Dist.POGD in this section) is compared against an ideal centralised solution for (13), both with and without relaxing the binary constraints on z l by modelling it in Y ALMIP [32], PREPRINT 6 T ABLE I I N DI V I D UA L H O U SE H O LD S Y S T EM P A R AM E T ER S Real-T ime PDF Estimation Sample Size, K + 1 901 Number of X Bins, m 15 Number of Y Bins, n 15 Additiv e Smoothing, ε 0 . 1 Battery Capacity 6 . 4 kWh Battery Power 3 . 3 kW One-way Battery Efficiency , η 96 % RDSA Reserve Capacity , γ 0 . 15 kW T ABLE II G E NE R A L S I M UL ATI O N P AR A M ET E R S Initial Battery State of Charge 3 . 2 kWh Ancillary Service Coefficient, σ 1 5 Regularisation Coefficient, σ 2 1 e − 4 Descent Step Size, r 0 . 012 No. of Consumers, N 20 and solving it with the Gurobi solv er . F or the distrib uted algorithm, we assume a persistent (rather than perfect) forecast for x l , i.e. , use the latest high-frequency SM measurement for computing the gradient step. For the centralised solution, a perfect forecast was used instead in order to provide a better benchmark. Note that P N l =1 y l is not substituted with ˆ y in the centralised solution. T able III summarises the information used in the respective solution methods at time t . B. V isualisation of Aggr e gate Loads Fig. 2 illustrates the target aggregate load profile, the aggregated grid loads from Dist.POGD and a centralised solution with relaxed binary constraints, and the total con- sumer load. Within the specific illustrated period, the batteries are dischar ging, resulting in grid loads less than the total consumer load; but the conv erse can be true in other periods. Using the parameters in T able II and the selected ener gy and pri vac y loss prices, the Dist.POGD solution conv erges close to the ideal centralised solution, as seen in Fig. 2, and ov ershoots only when there is a significant consumer load change. The performance of Dist.POGD is affected by the choice of parameters in T able II. These parameters hav e to be chosen empirically in a real system, as consumer pri vac y preferences would be unknown to the aggregator . C. Evaluation Metrics Numerically , we ev aluate the performance of the algorithms ov er a period of three and a half hours (number of samples K s = 12600 ; simulate four hours, discard the first half-hour for initialisation purposes) with the follo wing metrics. For T ABLE III V AR I A B LE S U S ED I N T H E O P T I MI S A T I ON P RO B L E M AT T I ME t Distributed Centralised Load Forecast x l,t − 1 x l,t T arget Aggregate Load ¯ y l,t ¯ y l,t Day-Ahead Schedule y ref l,t y ref l,t Aggregate Load ˆ y l,t − 1 P N l =1 y l,t ancillary service provision, the algorithms are ev aluated based on the normalised root mean square error (NRMSE) between ˆ y and ¯ y , giv en by NRMSE := q 1 K s P K s k =1 ( ˆ y k − ¯ y k ) 2 ¯ y mean × 100% , ¯ y mean = 1 K s K s X k =1 ¯ y k , and the mean absolute percentage error (MAPE), MAPE := 100% K s K s X k =1 ˆ y k − ¯ y k ¯ y k . MAPE gives the av erage of the errors at each time t , while NRMSE emphasises large de viations from the tar get load, which are undesirable, and reflects the target load tracking error relative to the overall mean. The consumer preference (day-ahead schedule tracking) is ev aluated by computing its normalised mean absolute error (NMAE), i.e . , the absolute error as a percentage of the maximum grid load, NMAE := 100% K s y max l K s X k =1 y l,k − y ref l,k . W e used an approximate MI function in the objectiv e func- tion of the optimisation problem. Howe v er , for ev aluation purposes we estimate the average MI, assuming identical and independently distributed random variables (denoted as I iid ), and stationary first-order Markov processes (denoted as I mk ), as described in [33], [34]. Such ev aluation requires the computation of p X,Y ( x, y ) log[ p X,Y ( x, y ) /p X ( x ) p Y ( y )] , which in the case of p X,Y ( x, y ) being zero, is set to zero to avoid computing log 0 . The I mk captures some of the time correlation between the consumer and grid loads, which is neglected when calculating the I iid [34]. Note that while modelling the X l and Y l as time-varying Markov processes would yield more accurate MI estimates, there are insufficient samples from this simulation for its application. The information that is contained within a consumer’ s load profile has been shown to be dependent on the measurement frequency [35]. Thus, the pri vac y risks stemming from high- frequency SM measurements are also time resolution depen- dent, i.e , the resolution at which consumers are metered influ- ences their priv acy risks [36]. Giv en that 1-minute metering resolution is more likely to be deplo yed than the 1-second time resolution of the controller , the MI is also assessed at this lower time resolution to better understand the realistic SM priv acy loss. While there is a lack of literature that studies SM priv ac y protection considering access to side information, the presence of such information should not be ignored due to its potential impact on the performance of priv acy protection schemes. In a recent preliminary work, e ven the presence of mundane side information (day of the week) has been sho wn to degrade the performance of two different learning-based SMDM priv acy protection mechanisms [37]. While adversarial attack models are not the focus of this paper , for the sake of completeness, PREPRINT 7 13500 13550 13600 13650 13700 13750 13800 13850 13900 13950 14000 Simulation Time [s] 6 6.5 7 7.5 8 8.5 9 9.5 10 10.5 11 Aggregate Load [kW] (a) T ar get grid load and aggregated grid loads 13500 13550 13600 13650 13700 13750 13800 13850 13900 13950 14000 Simulation Time [s] 12.8 13 13.2 13.4 Aggregate Load [kW] 0 50 100 150 200 250 300 350 400 450 500 12.8 13 13.2 13.4 (b) Aggregated consumer load Fig. 2. T arget grid load, and aggregated grid and consumer loads we also considered priv acy loss in the presence of some simple side information, which may increase the information leakage to the adversary . In our case study , one could rea- sonably assume that an adversary (possibly the aggregator) may ha ve the following side information: the ancillary service provision signal k ˆ y t − 1 − ¯ y t k 2 2 , and each consumer’ s day-ahead schedule y r ef l . Each consumer’ s grid load on the other hand is composed of their day-ahead schedule, deviations due to priv ac y-protection, ancillary service request, and consumer load de viations from day-ahead forecasts. Hence, a naive, but simple assessment of such risk is conducted by estimating the MI of the grid load profiles with the ancillary service portion remov ed (denoted as GS or y G l ), with the day-ahead schedule remov ed (dentoed as D A or y D l ), and with both subtracted (denoted as DA GS or y DG l ): y G l = y l − ancillary service request z }| { ( ˆ y − ¯ y ) y mean l P N l =1 y mean l , y mean l = 1 k s k s X k =1 y l,k , y D l = y l − y ref l y DG l = y G l − y ref l . Fig. 3 illustrates the original and adjusted grid loads for consumer 1 . Note that the ancillary service request does not equal the ancillary service provision, and that y DG l is the adversary’ s guess that does not reflect the actual pri vac y sensitiv e consumer load. The number of bins, m and n , are 1800 1820 1840 1860 1880 1900 1920 Simulation Time [s] -0.1 0 0.1 0.2 0.3 0.4 0.5 Load [kW] Fig. 3. Grid load for consumer 1 kept the same as in the optimisation problem when computing the MI between x l and y l . Ho wev er , n is adjusted when computing the MI for y G l , y D l and y DG l to account for the increased range space; in order to keep a similar quantisation resolution. The increase in range space for y G l and y DG l can be seen in Fig. 3; while the range space increase for y D l occurs whenev er there is a change in the day-ahead schedule (e.g., ev ery half hourly in our case study). All else being equal, increasing the quantisation resolution generally leads to an increase in the MI estimate as discussed in [17]. PREPRINT 8 D. Results and Discussion T ables VI and VII summarise the performance of Dist.POGD with dif ferent parameters, and the two centralised solutions. While the Dist.POGD solution con ver ges close to the ideal centralised solution as seen in Fig. 2, there is a dete- rioration in the overall performance due to the time required for con ver gence, forecast error , and the replacement of ˆ y l,t − 1 for P N l =1 y l,t . For the simulations, a persistent forecast was used in Dist.POGD instead of a perfect forecast. This allo ws for a better analysis of its performance if deployed in reality . Moreov er , relaxing the binary constraints on z l marginally improv es the NRMSE, MAPE, av erage NMAE, and most of the MI estimates, showing that this relaxation does not significantly impact the performance of the MI approximate in the objective function for a single control action. Note, howe v er , that this may not be true in general; in fact, the opposite might occur as sho wn in [30]. One can also see an increase in information leakage if MI is assessed at a resolution lower than the controller’ s, e.g., at one minute instead of one second. Howe ver , this increase might not pertain to information that is masked by the controller at higher resolutions, e.g., information on the type of de vice (contained in lo w time resolution data) versus a de vice’ s condition (inferable from high frequency data). By definition mutual information measures the general interdependence between two statistical distributions. As such, it is immune to post-processing for the information it is designed to hide. Howe ver , this does not mean that the grid load does not carry different (unprotected) information about the consumer load that is inferable from lower time resolution (aggregated) data . Recall that time aggregation has significant impact on SM load profile characteristics and by extension, also on the information contained within them [35]. T o gain a better understand the effect of time resolution (aggregation) on the priv ac y le vels attained by pri vac y mecha- nism employed in this paper, Houses 1 and 11 were simulated and ev aluated at different time resolutions, with the controller objectiv e set to only protect priv acy . T ables IV and V show the results of the different MI estimates. Assuming that the battery controller is able to maintain a fixed value across higher time resolutions ( i.e. , hold a fixed grid load ov er the control action interval), it can be seen that ev aluating priv acy loss at time resolutions higher than those used for the control actions always led to less priv acy-loss. This is intuiti ve as it is akin to load-lev elling across the ev aluation time interval. Howe v er , it is inconclusiv e to state that aggregating high time resolution measurements always leads to more priv acy- loss; e.g., there is less IID MI when ev aluating 1-minute simulations for House 1 at 5-minute resolutions. W e believ e that the ef fects on time aggregation during e valuation may be dependent on the amount of time-correlated information present in the underlying consumer load, but the in vestigation of this is left for future work. Note also that the 1-sec I mk values are very small because the measure is unable to fully capture the time-correlated priv ac y leakage that it was designed for . The time-correlation of the load profiles is at least 5 seconds (5 sample intervals), T ABLE IV H O US E 1 P R I V A CY P RO T EC T I ON O N LY Evaluation Resolution IID MI Markov MI Sim. Reso. 1 Sec 1 Min 5 Min 1 Sec 1 min 5 Min 1 Second 0 . 068 0 . 067 0 . 092 0 . 011 0 . 102 0 . 393 1 Minute 0 . 412 0 . 437 0 . 358 0 . 0030 0 . 220 0 . 522 5 Minutes 0 . 074 0 . 079 0 . 105 6 . 95 e -4 0 . 038 0 . 195 T ABLE V H O US E 1 1 P R IV AC Y P RO TE C T I ON O N L Y Evaluation Resolution IID MI Markov MI Sim. Reso. 1 Sec 1 Min 5 Min 1 Sec 1 min 5 Min 1 Second 0 . 681 0 . 689 0 . 736 0 . 031 0 . 232 0 . 309 1 Minute 0 . 446 0 . 579 0 . 571 0 . 006 0 . 216 0 . 320 5 Minutes 0 . 361 0 . 414 0 . 552 0 . 004 0 . 099 0 . 318 which cannot be captured by modelling the loads as first-order Markov processes, a drawback that was previously highlighted in [34]. T able VIII summarises the MI estimates for the compen- sated grid loads using the reference Dist.POGD setup. In analysing the ef fects of the simple grid load compensation using the possible side information, we consider only added information leakage as this illustrates the loss of priv acy in the presence of such information. Comparing T ables VII and VIII, one can see that correcting for ancillary service request results in higher 1-sec I mk , and 1-min I mk estimates, thus resulting in more leakage of time-correlated pri vate information. While there is a slight increase in 1-min I iid , the results are inconclu- siv e. Ha ving the day-ahead consumer schedule does not appear to increase information leakage in our experiments. This can be seen as there is no marked increase in information leakage when compensating for the day-ahead schedule alone (D A), or further compensating for it after removing the grid service request (DA GS). This shows that the ancillary service request signal constitutes sensitiv e side-information, while additional information on the day-ahead schedule may not exacerbate consumer priv acy loss. Note that the day-ahead schedules in this case study are optimised for half-hourly priv acy protection in addition to energy cost, which may explain the lack of sensitiv e information deriv able from them. Further study on ways of incorporating the day-ahead schedules are needed for a conclusiv e verdict on their priv acy sensitivity . As discussed, the RDSA parameters are setup-dependent, and changing the number of consumers in the RDSA while keeping all else constant affects the con ver gence rates and performance. This is illustrated for 25 and 15 consumers in Fig. 4. The choice of gradient descent step size r affects the con ver gence rate of Dist.POGD; too high a value for r leads to overshoots and instability , while too low a v alue hinders con v ergence to the optimal solution before the problem changes, as seen in Fig. 5. 1-Sec I mk increases with larger step sizes (see T able VII), showing an increase in the leakage of time-correlated priv ate information with larger r v alues. On the other hand, the overall tracking performance improves and I iid decreases as the rate of con ver gence (and overshoots) increases (see T able VI and Fig. 5). An ideal value for the PREPRINT 9 T ABLE VI P E RF O R M AN C E O F D I FF ER E N T S O L U TI O N M E T H OD S A N D P A RA M E T ER S NRMSE MAPE A vg. NMAE Reference Dist.POGD 1 . 694% 0 . 7878% 4 . 699% Centralised, binary 0 . 336% 0 . 295% 3 . 71% Centralised, relaxed 0 . 322% 0 . 283% 3 . 53% 15 Consumers 2 . 69% 1 . 61% 5 . 42% 25 Consumers 1 . 51% 0 . 827% 4 . 32% r = 0 . 008 2 . 80% 1 . 63% 5 . 13% r = 0 . 016 1 . 56% 0 . 914% 4 . 41% σ 2 = 0 1 . 691% 0 . 7873% 4 . 695% σ 2 = 0 . 001 1 . 694% 0 . 7883% 4 . 703% µ l = 0 1 . 68% 0 . 777% 4 . 61% 11 ≤ µ l ≤ 19 1 . 78% 0 . 866% 5 . 21% K = 600 1 . 70% 0 . 796% 4 . 71% K = 1200 1 . 69% 0 . 785% 4 . 69% σ 1 = 3 3 . 17% 2 . 05% 4 . 41% σ 1 = 7 1 . 65% 0 . 978% 4 . 86% T ABLE VII M I E S T I MATE S F O R D I FF E RE N T S O L U TI O N M E TH O D S A N D S E T T IN G S A vg. 1 sec A vg. 1 min I iid I mk I iid I mk Reference Dist.POGD 0 . 248 0 . 020 0 . 280 0 . 193 Centralised, binary 0 . 236 0 . 018 0 . 277 0 . 140 Centralised, relaxed 0 . 221 0 . 015 0 . 270 0 . 147 15 Consumers 0 . 301 0 . 018 0 . 354 0 . 228 25 Consumers 0 . 223 0 . 020 0 . 244 0 . 164 r g = 0 . 008 0 . 256 0 . 019 0 . 300 0 . 194 r g = 0 . 016 0 . 247 0 . 022 0 . 279 0 . 184 σ agg , 2 = 0 0 . 248 0 . 020 0 . 281 0 . 192 σ agg , 2 = 0 . 001 0 . 247 0 . 020 0 . 281 0 . 192 µ l = 0 0 . 254 0 . 020 0 . 287 0 . 194 11 ≤ µ l ≤ 19 0 . 237 0 . 020 0 . 269 0 . 196 K = 600 0 . 247 0 . 020 0 . 276 0 . 196 K = 1200 0 . 248 0 . 020 0 . 282 0 . 196 σ agg , 1 = 3 0 . 253 0 . 018 0 . 294 0 . 189 σ agg , 1 = 7 0 . 250 0 . 023 0 . 285 0 . 204 coefficient σ 2 for the regularisation term k h k 2 2 would result in minimal impact on the performance of the algorithm. As seen in T ables VI and VII, Dist.POGD with σ 2 = 1 e − 4 has similar performance to an algorithm without regularisation. As expected, increasing σ 1 reduces the ancillary service provision NRMSE at the expense of increasing the day-ahead tracking NMAE and most MI estimates. Howe ver , a decrease in σ 1 does not necessarily lead to a decrease in I iid due to a slower con ver gence rate (see Fig. 6). Surprisingly , increasing σ 1 could also lead to an increase in ancillary service provision MAPE due to tracking o vershoots as illustrated in Fig. 6. Increasing µ l decreases I iid , but increases ancillary service provision NRMSE and MAPE, and the av erage NMAE for tracking the day-ahead schedule. Changing the sample size K T ABLE VIII M I E S T I MATE S F O R T H E C O MP E N S A TE D G R I D L OA D Reference Dist.POGD A vg. 1 sec A vg. 1 min I iid I mk I iid I mk GS 0 . 236 0 . 039 0 . 306 0 . 249 D A 0 . 102 0 . 022 0 . 139 0 . 224 D A GS 0 . 086 0 . 033 0 . 138 0 . 225 13500 13520 13540 13560 13580 13600 13620 Simulation Time [s] 6.5 7 7.5 8 8.5 9 9.5 10 Aggregate Load [kW] (a) 15 consumers 13500 13520 13540 13560 13580 13600 13620 Simulation Time [s] 11 12 13 14 15 16 17 Aggregate Load [kW] (b) 25 consumers Fig. 4. Tracking performance with different aggregation sizes 13500 13520 13540 13560 13580 13600 13620 Simulation Time [s] 7 8 9 10 11 Aggregate Load [kW] Fig. 5. Comparison between different step sizes, r in the objective function has a similar effect to changing µ l as it increases the importance of the current control action in estimating the PDF of ( X l , Y l ) . Howe ver , their effects are not equiv alent as reducing K could lead to ov erfitting the PDF . V . C O N C L U S I O N In this paper, a distributed projected online gradient de- scent algorithm for providing ancillary services to the grid by aggregating priv acy-conscious residential consumers was presented. A balance between the different objectives can be 13500 13520 13540 13560 13580 13600 13620 Simulation Time [s] 7 8 9 10 Aggregate Load [kW] Fig. 6. Comparison between different tracking coefficients, σ 1 PREPRINT 10 achiev ed by adjusting their weights. Despite minor perfor - mance de gradation when compared to an ideal centralised aggregation scheme, the proposed algorithm does not require high-bandwidth communications infrastructure. Moreov er , it allows for the preservation of consumer pri vac y as the actual consumer load does not need to be re vealed to the aggre gator . Future work will focus on the provision of other grid services such as voltage support, incorporating DERs with uncertainty or more complex constraints, and considering grid constraints in the formulation of the optimisation problem. R E F E R E N C E S [1] U.S. Energy Information Administration, “Annual electric power industry report, form EIA-861, ” 2017. [Online]. A vailable: https: //www .eia.go v/electricity/annual/html/epa 10 10.html [2] European Commission, “Cost-benefit analyses & state of play of smart metering deployment in the EU-27, ” 2014. [Online]. A vailable: https://eur - lex.europa.eu/legal- content/EN/TXT/ PDF/?uri=CELEX:52014SC0189&from=EN [3] Swiss Federal Office of Energy , “Wichtigste Neuerungen im Energierecht ab 2018, ” 2017. [Online]. A v ailable: https: //www .ne wsd.admin.ch/newsd/message/attachments/50166.pdf [4] T . Hargreav es, M. Nye, and J. Burgess, “Making energy visible: A qualitativ e field study of how householders interact with feedback from smart energy monitors, ” Ener gy P olicy , vol. 38, no. 10, 2010. [5] A. Molina-Markham, P . Shenoy , K. Fu, E. Cecchet, and D. Irwin, “Priv ate memoirs of a smart meter , ” in Pr oceedings of the 2nd A CM W orkshop on Embedded Sensing Systems for Ener gy-Efficiency in Build- ing , Zurich, Switzerland, Nov . 2010, pp. 61–66. [6] P . McDaniel and S. McLaughlin, “Security and privac y challenges in the smart grid, ” IEEE Security and Privacy , vol. 7, no. 3, 2009. [7] V . Becker and W . Kleiminger , “Exploring zero-training algorithms for occupancy detection based on smart meter measurements, ” Computer Science - Research and Development , vol. 33, no. 1-2, 2018. [8] Y . W ang, Q. Chen, D. Gan, J. Y ang, D. S. Kirschen, and C. Kang, “Deep learning-based socio-demographic information identification from smart meter data, ” IEEE Tr ans. on Smart Grid , vol. 10, no. 3, pp. 2593–2602, 2019. [9] European Union, “Regulation (EU) 2016/679 of the European Parlia- ment and of the Council of 27 April 2016 on the protection of natural persons with regard to the processing of personal data and on the free movement of such data, and repealing Directive 95/46/EC (General Data Protection Regulation), ” Official J. of the European Union , May 2016. [10] G. Giaconi, D. G ¨ und ¨ uz, and H. V . Poor, “Priv acy-aware smart metering: Progress and challenges, ” IEEE Signal Processing Magazine , vol. 35, no. 6, pp. 59–78, Nov . 2018. [11] C. Efthymiou and G. Kalogridis, “Smart grid privac y via anonymization of smart metering data, ” in 2010 Fir st IEEE International Confer ence on Smart Grid Communications , Gaithersburg, MD, USA, Oct. 2010. [12] C. Rottondi, G. Mauri, and G. V erticale, “ A data pseudonymization protocol for smart grids, ” in 2012 IEEE Online Conference on Green Communications (GreenCom) , Sept. 2012. [13] M. Jawurek, M. Johns, and K. Rieck, “Smart metering de- pseudonymization, ” in 27th Annual Computer Security Applications Confer ence on - ACSA C ’11 , Orlando, FL, USA, Dec. 2011. [14] G. Kalogridis, C. Efthymiou, S. Z. Denic, T . A. Lewis, and R. Cepeda, “Priv acy for Smart Meters: T owards Undetectable Appliance Load Signatures, ” in F irst IEEE International Conference on Smart Grid Communications (SmartGridComm) , 2010, pp. 232–237. [15] W . Y ang, N. Li, Y . Qi, W . Qardaji, S. McLaughlin, and P . McDaniel, “Minimizing priv ate data disclosures in the smart grid, ” in Proceedings of the 19th ACM conference on computer and communications security (CCS ’12) , Raleigh, North Carolina, USA, Oct. 2012. [16] Z. Zhang, Z. Qin, L. Zhu, J. W eng, and K. Ren, “Cost-friendly differential pri vac y for smart meters: Exploiting the dual roles of the noise, ” IEEE T rans. on Smart Grid , vol. 8, no. 2, pp. 619–626, 2017. [17] J. X. Chin, T . Tinoco De Rubira, and G. Hug, “Priv acy-protecting ener gy management unit through model-distribution predicti ve control, ” IEEE T rans. on Smart Grid , vol. 8, no. 6, pp. 3084–3093, 2017. [18] Y . Sun, L. Lampe, and V . W . S. W ong, “Smart meter priv acy: Exploiting the potential of household energy storage units, ” IEEE Internet of Things Journal , vol. 5, no. 1, pp. 69–78, 2018. [19] G. Giaconi, D. G ¨ und ¨ uz, and H. V . Poor , “Smart meter priv acy with renew able energy and an energy storage device, ” IEEE T rans. on Information F orensics and Security , vol. 13, no. 1, pp. 129–142, 2018. [20] A. C. Chapman, G. V erbic, and D. J. Hill, “ Algorithmic and strategic aspects to integrating demand-side aggregation and energy management methods, ” IEEE T rans. on Smart Grid , vol. 7, no. 6, 2016. [21] A. Rajabi, L. Li, J. Zhang, and J. Zhu, “ Aggre gation of small loads for demand response programs — implementation and challenges: A revie w , ” in 2017 IEEE Intl. Conference on Envir onment and Electrical Engineering and 2017 IEEE Industrial and Commer cial P ower Systems Eur ope (EEEIC / I&CPS Eur ope 2017) , Milan, Italy , June 2017. [22] D. S. Callaway and I. A. Hiskens, “ Achieving controllability of electric loads, ” Proceedings of the IEEE , vol. 99, no. 1, pp. 184–199, 2011. [23] A. Bernstein and E. Dall’Anese, “Real-time feedback-based optimization of distribution grids: A unified approach, ” IEEE T ransactions on Contr ol of Network Systems , vol. 6, no. 3, pp. 1197–1209, 2019. [24] H. Li, X. Lin, H. Y ang, X. Liang, R. Lu, and X. Shen, “EPPDR: An efficient priv acy-preserving demand response scheme with adaptiv e key evolution in smart grid, ” IEEE Tr ans. on P arallel and Distributed Systems , vol. 25, no. 8, pp. 2053–2064, 2014. [25] Y . Gong, Y . Cai, Y . Guo, and Y . Fang, “ A priv acy-preserving scheme for incentiv e-based demand response in the smart grid, ” IEEE Tr ans. on Smart Grid , vol. 7, no. 3, pp. 1304–1313, 2016. [26] M. F . Balli, S. Uludag, A. A. Selcuk, and B. T avli, “Distributed multi- unit priv acy assured bidding (P AB) for smart grid demand response programs, ” IEEE T rans. on Smart Grid , vol. 9, no. 5, 2018. [27] E. Dall’Anese, A. Bernstein, and A. Simonetto, “Feedback-based projected-gradient method for real-time optimization of aggregations of energy resources, ” in 2017 IEEE Global Confer ence on Signal and Information Pr ocessing (GlobalSIP) , Montreal, Canada, Nov . 2017. [28] V . Arzamasov , R. Schwerdt, S. Karrari, K. B ¨ ohm, and T . B. Nguyen, “Priv acy measures and storage technologies for battery-based load hiding - an ov erview and experimental study , ” in Pr oceedings of the Eleventh ACM International Conference on Futur e Energy Systems , ser . e-Energy ’20, V irtual Event, Australia, 2020, pp. 178–195. [29] J. X. Chin, A. Bernstein, and G. Hug, “Online appendix for aggregating priv acy-conscious DERs for grid service provision, ” 2019. [Online]. A vailable: https://doi.org/10.5281/zenodo.3384771 [30] J. X. Chin, “Consumer priv acy and smart distribution grids: A cyber -physical ecosystem, ” Ph.D. dissertation, ETH Zurich, 2020. [Online]. A v ailable: https://doi.org/10.3929/ethz- b- 000406297 [31] W . Kleiminger , C. Beckel, and S. Santini, “Household occupancy monitoring using electricity meters, ” in Proceedings of the 2015 ACM International Joint Conference on P ervasive and Ubiquitous Computing (UbiComp 2015) , Osaka, Japan, Sept. 2015. [32] J. Lofberg, “Y ALMIP : a toolbox for modeling and optimization in MA TLAB, ” in 2004 IEEE International Confer ence on Computer Aided Contr ol Systems Design , New Orleans, LA, USA, Sept. 2004. [33] O. T an, J. Gomez-V ilardebo, and D. G ¨ und ¨ uz, “Priv acy-cost trade-offs in demand-side management with storage, ” IEEE T rans. on Information F or ensics and Security , vol. 12, no. 6, pp. 1458–1469, 2017. [34] J. X. Chin, G. Giaconi, T . T inoco De Rubira, G. Hug, and D. G ¨ und ¨ uz, “Considering time correlation in the estimation of priv acy loss for consumers with smart meters, ” in 2018 P ower System Computation Confer ence (PSCC) , Dublin, Ireland, June 2018. [35] J. Rousseau, “Impact of time and spatial aggregation of smart meter data, ” Semester Thesis, ETH Zurich, June 2020. [36] G. Eibl and D. Engel, “Influence of data granularity on smart meter priv acy , ” IEEE Tr ans. on Smart Grid , vol. 6, no. 2, pp. 930–939, 2015. [37] M. Shateri, F . Messina, P . Piantanida, and F . Labeau, “On the impact of side information on smart meter privac y-preserving methods, ” 2020, to be published. [Online]. A v ailable: https://arxiv .org/abs/2006.16062
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment