Audio Watermarking with Error Correction
In recent times, communication through the internet has tremendously facilitated the distribution of multimedia data. Although this is indubitably a boon, one of its repercussions is that it has also given impetus to the notorious issue of online mus…
Authors: Aman Chadha, S, eep Gangundi
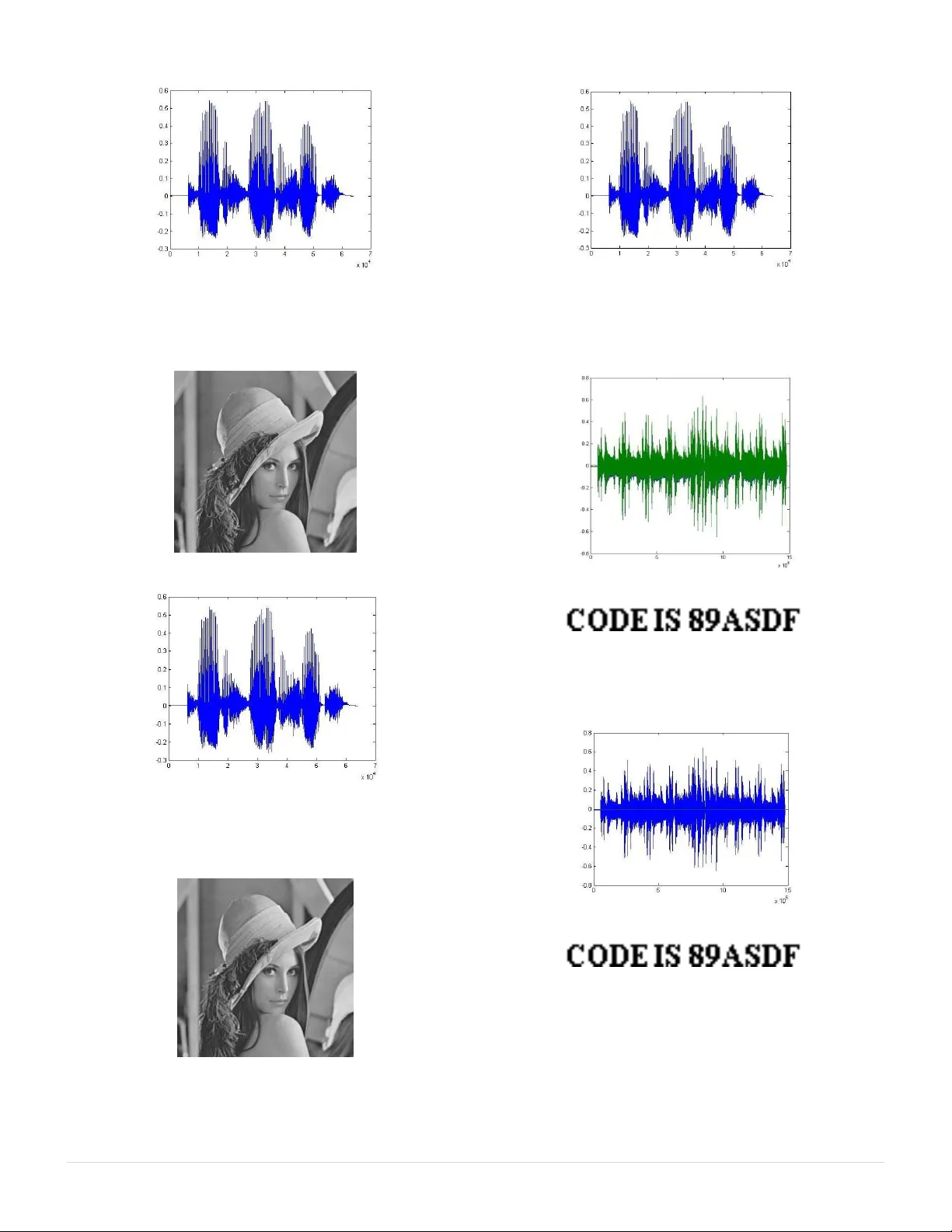
(IJACSA ) Intern ation al Journ al of Advan ced Comp uter Science and Applica tions , Vol. 2, No. 9, 201 1 113 | P a g e www .ijacsa.thesai.o rg Audio Watermarking with Error Correction Am a n C hadh a , San deep Gang undi, Rish abh Goel , Hiren Dave , M. Mani Roja Departme nt of E lec tr o n ics & Telec ommunicatio n Thadom al Shahani Engin ee ring Co ll ege Mumb ai , INDIA Abstrac t — In r ecent times , com munica ti on through th e inter net has trem endous ly f ac ilitated t h e distri bution of multim edia da ta. Although t h is is i n dubitab ly a boo n, one o f its reper cussio ns is that it has a lso g iven i mp etus to th e no torio us issue of on lin e music pi racy. Un ethical at tempts c an also be mad e to delibe rate ly alter such copy righted data and thus, misus e it. Co pyrig ht vio lati o n by me ans o f unautho rized dist ri bu tio n, as we ll as unautho riz ed tamper ing of co pyrighte d audio data is an impo rtant techno logical and res earch i ssue . Audio waterm arki ng has been p ropo sed a s a solutio n to tackle this issue. The main purpo se o f aud io waterma rk ing is to protect agains t possib le threat s to t h e audio da ta and i n c ase of co pyrigh t vio lation or unautho riz ed tampering , auth enticity of such data can be disputed by v irtue o f audio w atermark ing . Keywor ds- w ater marking; au dio wate rmarkin g; data h iding; da ta confide ntiality . I. I NTRODUCTIO N Ov er the y e ar s , th e re has be en tr e me n dous grow th i n co mputer n e two rks an d mo re spe cif ically , t h e inte rne t. T his phe nome n o n, co uple d w ith t h e expo nenti al i n c rease of co mputer pe r f orm ance, ha s faci lita ted the d is tribut ion of mult imed ia data s uc h as i mages, audio , v ideo etc. Data tra n s missio n has be en made ve ry simple , fast and accu rate using the inte rnet. How eve r , one of the mai n prob lems asso ciated w ith tra n s missio n of data ov er the inte rn et is th at it may po se a se cu rity thre at, i.e ., perso n al o r confide ntial da ta ca n be sto le n o r hacked in many way s. Pub lishe r s and artis ts, hence , may be r eluc tant t o dist ribu te d ata ov er th e Inte rn et due to l ack o f se curity ; co py r ighte d ma te rial ca n be easily duplic a te d and dis tribute d w itho ut the o wner‟s co n se nt. The r ef ore, it b eco mes ve r y i mpo rtant to take d ata sec uri ty into co nsidera tio n, as it i s o n e of the ess e n ti al f acto r s t hat ne ed atte ntio n du ring the p r o ces s o f data dist ribut io n . Wate rmarks have be e n propo sed a s a w ay to tack le this tou gh i ssue . This digi tal sig nat ure co uld disco urage co py r ight vio latio n, and may help dete r mine t h e authe ntici t y and o wne rship of an im age. Wate rma rking is “ the pract ice of impe r cep tibly alte ring a Wo rk to emb ed a me ssage abo ut that Wo r k ” [1]. Wate rmark ing ca n be used to secre tly transm it co n fide ntial mess ages , fo r e .g. , mil itary maps, wi thout the fact of suc h tra n sm issio n be ing disco ve red. Wa te r ma rking , bei n g ideal ly impe r cep t ible , ca n be ess entially use d to mask the ve r y exis te n ce of the sec ret messa ge [6 ]. In this manne r, w aterm arki ng is used t o crea te a cov ert c hanne l to tra ns mit co n fide n ti al i n f orm atio n [5] . Wa t e rma rking is an ef fe ctive me ans of hid ing dat a, there b y pro tecting the da ta f rom unau th o r ized o r u n wa nted v iew ing. Wate rma rking is be co min g increas ing ly popula r, es peci ally f or inse rtio n of undetec table identify ing marks , s uc h as autho r or co pyright info r matio n to the host sig nal. Wa terma rki n g may pro bab ly be bes t used in co n ju n c tio n with ano the r data- hiding metho d s uc h as stega n o gra phy , cry pt ograp hy etc. Such dat a- hidi ng sc h e mes, w h e n co up led wi th w ate r mark ing, c an b e a part of an exte n siv e lay ered sec urity a ppro a c h. To comb at o n li n e music p iracy , a digi tal wa te rmark coul d be added to all r ec o r d ings prio r to r e lease , sig nify in g n o t only the aut hor of th e wo r k, b ut also the use r who ha s purc ha sed a legit imate co py . Audio w aterm arki ng is defi n e d as “the impe r cept ible, r ob us t and se cure co mmu nicat io n of da ta r e late d to the h os t aud io signa l, w h ic h includes embe ddi ng into, and ext ractio n fro m, the hos t audio sig nal ” [4] . D igita l a ud io w aterma rking invo l ve s th e co n ce alme nt of data w ithi n a disc rete audio fi le. Intel lect ual prope rty prote ctio n is cu rr ent ly the m ai n d rivi ng fo r ce be h ind r esea rch in t his area . S ev eral othe r app licat io n s o f aud io wa term arki ng suc h as co py r ight pro tectio n, ow n e r ide ntific atio n, tampe r ing detect ion, finge r pri nti ng, copy and acce ss co ntr o l, annot atio n, and se c ret co mmunic atio n , a r e i n p ractic e. O ther r e lated us es f or w aterma rking incl ude e mbe dding aux ilia r y info rmatio n w h ich is rela ted to a pa rticul ar so n g , like ly ri cs , albu m info r matio n, or a h y perl ink etc . Wate rma rking co uld be used in vo ice co nfere n ci ng sy stems to indic ate to othe rs w hich party i s curre ntly speaki n g. A vide o appl icatio n of this tec hnolo gy w ould co n sist of e mbe dding subt itles o r c lose d c aptio ning info rmat io n as a wa te rmark [7] . II. I DEA OF T HE P ROPOS ED S OL UTION A. Pr oce ss of Watermarking The bloc k di agram fo r wate rma r ki ng is as s h ow n b elow : Figure 1. General watermarkin g block diagra m We ca n su mma rize the enti r e proce ss of h idi ng and ret rievi ng da ta as fo llow s: (IJACSA ) Intern ation al Journ al of Advan ced Comp uter Science and Applica tions , Vol. 2, No. 9, 201 1 114 | P a g e www . ijacsa.thesai.o rg Re ad the data t o be hidde n. Re ad the cov er , i.e ., hos t , in whic h data is to be hi dde n. App ly waterm arking me thods on t h e host . H ide the data in t h e host . Re trieve the o r igina l d ata at the rece iver e n d. B. Mean Squar e Error Mea n S qua re E rr o r (MS E) [2], f irs t int r oduc ed b y C. F. Gauss , se r ves as an impo rt ant p arame ter in gaug ing the perfo rma n ce of the w aterm arki ng sy stem. Th e fo llow ing fac tors jus tify the c h oic e of MSE as a co n ve nie n t and ex tensiv e stand ard fo r perfo rmance asses sme n t o f vario us tec hniques of audio wa terma rki n g: 1) Sim plici ty: It i s para mete r-f r ee and inexpe n s ive t o co mpute, wi th a co mplex ity of onl y one mult iply and two addi tio n s pe r sa mple . It is also me mory less , i.e., MSE ca n be ev aluated at e a c h samp le, i ndepe n de nt of ot h e r samp les . 2) Clear phys ical m e ani ng: It is the natu ral w ay t o def ine the ene r gy o f the e rror sig nal. Suc h an e n e r gy meas ure is prese rved ev e n afte r any ortho go nal o r unit ary linea r tra n sf orm atio n. The e n e rgy p r ese r vi ng prope rty gua rantees that the ene rgy of a sig nal disto rtio n in the tra n sf orm dom ain is the same as that in the s i gna l do main. 3) Exce llent metr ic in th e c o ntext of optim izat ion: The MSE po sses ses th e prope rties of co nvexi ty , sy mmetry , and diff ere n ti abili ty . 4) Used as a con venti on: It has be en ex te n siv ely emp loy ed fo r op timiz ing and asses sing a w ide v ariety of sig nal pro cess ing appl icatio n s, inc lud ing fil ter desi gn, sig nal co mpressio n, r es torat ion, r ec o nstruct io n , a nd c lassif icat io n . MSE is esse n tial ly a sig nal fide lity me asure [14] ,[15] . Th e goal of a sig nal fide lity meas ure i s t o comp are tw o sig nals by pro viding a q uanti tativ e sco r e that desc ri b es the degree of simi larity /fidelity o r , c onve r sely , the le ve l o f err o r/dis torti on be twee n t h e m. Us ually , it is assu med t hat o n e of the sig nals is a pris tine o r ig inal, w hi le t h e ot h e r is disto rted o r co n tami nated by erro rs. Suppo se tha t x = { x i | i = 1, 2, . . . , N} and y = { y i | i = 1, 2, . . . , N} are tw o f inite-le ngth, discre te sig nals, for e.g ., v isual image s o r a udio s ignals . The MSE betw een the sig nals i s giv en by the fo llow in g f ormu la: (1) Whe r e , N is t h e numb er of signal samp les. x i is th e value o f the i th sample in x. y i is th e v alue of th e i th sample in y . III. I MPLEMENT ATION S TE PS Aud io Wa terma rki ng ca n be imple me nted in 3 way s: Aud io in A udio Aud io in I m age Image in A udio A. Audio in Audio In this met h o d, bo th the cov er file and the wate rma rk fi le are aud io sig nals. The w ate rmark sig nal must ha v e fewe r samp les as co mpared to thos e of the cov er aud io sig nal. Fu r the r, this metho d can be im ple mente d w it h the h el p o f two techni ques , name ly , Inte rleaving and DCT . 1) Using Int erlea ving : It is a w a y to arrange data in a no n -co ntiguous way so as t o incre ase pe r f orm ance [3]. T h e fo l low ing exam ple illus trates the p r oc ess of inte rleavi ng: Original signal: AAAA BBBB CCCCDDD DEEE E Interleav ed signal: ABCD EABCDEAB CDEABCDE In this tec hnique , the sam ples of wate rmark audio are inse rted in be twe en the sa mples of the cov er audio fi le [9] ,[10] . In te rms of c omplex ity , this is the sim ples t met hod of audio w aterma rking . 2) Using Discr ete Cosin e Tr ansform: This tec hnique is bas ed on the D isc r ete Co sine Tra nsfo rm (D CT) [ 11 ]- [1 3]. In this tec hnique , we take t h e D CT of bo th th e cov er audio and the wate rmark a u dio s igna ls. U pon zigz ag scanni ng, the high freque n cy DCT co ef fic ients of the co ve r a ud io fi le are r epl aced w ith the low freque ncy DCT co ef ficie nts of the w aterm ark audio f ile . Du ring tra n s missio n, the I n ve r se Disc r e te Co sine Tra n sf orm (IDC T) of th e fi nal w ate rmarked D CT is take n. In this partic ular tec hni que , si n ce bot h the h o st, i.e., c ov er and w aterma rk sig nal are in the audio fo rmat , we im pleme n t this metho d us ing a 1D DC T w hic h is def ined by th e fo llow ing equa tion: 1 0 2 (2 1 ) ( ) ( ) co s ( ) 2 N i ui F u A i f i NN (2) Whe r e , 1 0 A (i) 2 1 for u othe rwise f(i) is t h e input sequence . B. Audio in Ima ge This wate rma rking imp leme ntatio n uses DCT fo r emb edding audio file in an ima ge. He r e we take DC T o f bot h the co ver im age and the w at e rma rk aud io file s. The low freque n cy coeff icie n ts of bo th the DCT ‟s are t ake n. The high freque n cy co eff icients o f the D CT of the im age are r ep lace d w ith the low freque n cy coe ffic ients of th e D CT of th e 2 1 1 ( , ) ( ) N ii i M SE x y x y N (IJACSA ) Intern ation al Journ al of Advan ced Comp uter Science and Applica tions , Vol. 2, No. 9, 201 1 115 | P a g e www . ijacsa.thesai.o rg w aterma rk aud i o fi le. Du ring tra n s missio n, the IDCT o f t h e fina l wate rma r ked DCT is take n. This tec hnique invo lves b oth an aud io sig nal (wate rmark) an d an image (host ). He n ce, we imple me nt this met h o d usi n g a 1D DCT fo r th e aud io sig nal and a 2D DC T f or the im age. Equatio n (2) def ines a 1D DCT w h ile the corre spo n di n g equ atio n fo r a 2 D DCT i s def in ed b y the fo ll o wing eq uat ion: 11 00 2 2 (2 1 ) (2 1 ) ( , ) ( ) c os ( ) cos ( , ) 22 NM ij u i v j F u v A i A j f i j N M N M (3) Whe r e , 1 0 A (i) 2 1 for u othe rwise 1 0 A (j) 2 1 for v othe rwise f(i, j) is the 2D input se que n ce . C. Image in Audio In this imple m e n ta tio n, a s deplo ye d p r ev iously , D CT is used f or embedd in g an i mage in an aud io f ile. He r e w e take the DCT of b ot h the co ve r audio and the wa terma rk image fi les . This is f ollow ed by zigz ag scanni ng so as to asce rtain the low freque n cy and high f r e que n cy DCT co eff icients . Th e hig h freque n cy DCT co eff icients of the audio signal are r ep lac ed w ith the low freque ncy DCT co ef fic ients o f the wate rma rk image f ile . W hile trans mitt ing, the IDCT o f the f inal w aterma rked DC T is take n. Since this me thod i s s imila r to th e „Aud io in Ima ge‟ techni que w ith re spec t to t he p ara mete r s invo lved, i.e ., this techni que also invo lve s bo th an aud io sig nal (wate rma rk) and an image (ho st) , hence , we may imple ment this me thod usi ng a 1D DCT f or the aud io sig nal and a 2D DCT f or the im age . Equa tio n ( 2) def ines a 1D DC T w hile, ( 3) def in es a 2D DC T. IV. R E SULTS A. Audio in Audio The spe ctra of the inpu t, i.e ., o rigina l co ve r and wate rmark audio sig nal are as show n b elow : Figure 2. Original c over audio signal Figure 3. Original watermark au dio signal 1) Using In terl eav ing: The s pect ra of th e ou tput, i.e . , w aterma rked audio si gnal and the r ec ov ered audio s ignal , ob t ained by interle avi ng a r e as s h o wn b elo w: Figure 4. Watermark ed audio signal Figure 5. Recover ed audio water mark sig nal 2) Us ing DCT: The spe ctra of the outpu t, i.e., w aterma rked audio si gnal and the r ec ov ered audio s ignal , ob t ained by DCT base d „Audio in Aud io‟ wate rmarki ng ar e as show n be low : Figure 6. Watermark ed audio signal (IJACSA ) Intern ation al Journ al of Advan ced Comp uter Science and Applica tions , Vol. 2, No. 9, 201 1 116 | P a g e www . ijacsa.thesai.o rg Figure 7. Recover ed audio wat ermark sig nal B. Audio in Ima ge The input , i.e., orig ina l co ve r image and spe ct r um o f the w aterma rk aud io si gna l is as show n be low : Figure 8. Original c over image Figure 9. Original wa termark aud io si gnal The ou tput, i.e., wa term arked im age and the spec tru m of the r ec ov ered audio sig nal , obta ined by „Au dio in Imag e‟ w aterma rking is as show n b elow : Figure 10. Watermark ed image Figure 11. Recovered au dio water mark sig nal C. Image in Audio The in p ut, i.e ., spe c trum of the origi nal cov er sig nal and th e w aterma rk im age is as show n be low : Figure 12. Original co ver audio signal Figure 13. Original wa termark i mage The output , i.e ., s pect r um of the w ate rmarke d sig nal and t h e reco ve r ed wate rma rk image , ob t aine d by „Image in Aud io ‟ w aterma rking is as show n b elow : Figure 14. Watermark ed image Figure 15. Recovered watermark Fo r all pract ical pu r pos es, it is p r ef e r able to have a quant itat ive m e asu r e me nt to prov ide an ob je ctive judgme nt of the ext racti ng f ideli ty . This is do n e by calcula ting the MSE in eac h c ase. Res ults , thus ob tained , have bee n t abulate d. (IJACSA ) Intern ation al Journ al of Advan ced Comp uter Science and Applica tions , Vol. 2, No. 9, 201 1 117 | P a g e www . ijacsa.thesai.o rg TABLE I. C ALCULATION OF MSE WITHOUT N O ISE Types MSE Wat ermarked sig nal Wat ermark Audio in Audio (Interlea ving) 3.5 10 -4 0 Audio in Audio (DCT) 3.4 10 -3 2.48 10 -9 Image in Audio 3.2 10 -3 0 Audio in I mage 23.3 2.47 10 -9 V. E RROR C ORRECT ION USING H AMMING C ODES Du r ing trans missio n, w h e n dat a trav els throug h a wi r eles s med ium ov er a lo ng dis t ance , it is hig hly prob able tha t it m ay get co rrupted due t o fl uctua tio n s in c hanne l cha racte ristics o r othe r e xt e rnal pa ram e te r s . He n ce , ham ming co des, w h ich are Fo r w ard Err o r Correc tio n (F EC) code s, may be use d f or the purpo se of e rr o r co rrec tion i n aud io w aterm arki ng. H amming co des can de tect u p to tw o simul ta n eo us bi t erro rs and co rr ec t sing le bit e rro r s ; thus , r el iable co mmunic atio n is poss ible w hen the “ ham ming dist anc e” be twee n the t ransmit ted and rece ive d bit patte rns is less tha n or equa l to o n e [8] . In cont rast, simple parity code s ca nn ot co rr e ct erro rs and c an o nly de tect an o dd numbe r o f erro r s. I n this appl icatio n, we are usi n g the (15 , 11) fo rm o f the ham mi ng co de. The imp r ov eme nt in the qua lity of r ece ived sig nal is clea rly visible fro m the fo ll o wing wav efo r ms : Figure 16. Desired audi o signal Figure 17. Recovered au dio signal without Ha mmin g Code Figure 18. Recovered au dio signal with Ha mming Cod e The co rr espo nding resu lt s fo r Audio W ate r marki ng w i th noise hav e be en tab ulate d as fo ll o ws : TABLE II. C ALCULAT I ON OF M SE W ITH N OISE Types MSE Wat ermarked with noi se Wat ermark wit h noise Audio in Audio (Interlea ving) 0.01 0 0.01 0 Audio in Audio (DCT) 0.00 2 0.00 8 Image in Audio 0.00 3 1.92 10 3 Audio in I mage 323 .3 0 VI. C ONCLUSION DCT is an eff ec tive an d rob ust algo r it hm f or audio w aterma rking as th e audio sig nal r etrie ve d is cle arly a ud ible . H amming Code s e nable dat a co rr ect io n in case of data co rruptio n duri ng trans mi ss io n and h e lp in r eco ve ring the origi nal audio sig nal. R EFERENCE S [1] I. J. C ox, M. L . Mill er, J. A . Bloom, J. Fridrich, an d T. Kalker, Di gital Watermarki ng an d Stegan ograph y, 2 nd Editi on, Mor gan Kaufma nn, 200 8, p. 31. [2] Z. Wang a nd A. C. Bovik, “Mean squared error: lov e it or leave i t? - A new lo ok at signal f i delity measure s ,” IEEE Signal Proce ssing Magazine, Vol. 26, No. 1, pp. 98 -117 , January 2009 . [3] S. Shiy a mala a n d Dr . V. Raja mani, “A Novel Area Effici ent Fol ded Modified Con volutional I nterleaving Arc hitecture for MA P Decoder ,” Internati on al Journal of Co mputer A pp l icati ons (IJC A), Vol. 9 , No. 9, p . 1, Novemb er 2 010 . [4] N. Cv ejic, Academic Di sserta tion, Fa culty o f T echnology, Universit y of Oulu, “Alg orithms for au dio wat ermarking a nd stegan ography ,” p. 5. [5] Shahr ez a S.S. an d Shalma ni M.T. M., “ Ad a ptive wa velet domain au dio steganograp hy with high ca pacity and low err or rate ,” Proc eedings of t he IEEE I nternational C onferen ce o n In formation a nd Emer ging Technolo gies, (ICIET„0 7), pp. 17 29 -1732 , 2007. [6] Dr. H . B. Kekre and A. A. Ar chana, “In formatio n hi ding u sin g LS B techniqu e with i ncr eased ca pacity ,” I nternati onal J ournal o f Cryptogra phy and Securit y, Vol. 1, No. 2, p. 1, Oct ober 200 8. [7] M. Ad ya, M.Tec h. Thesis, I ndian Institut e o f Te chnolo gy Kharagpur (IJACSA ) Intern ation al Journ al of Advan ced Comp uter Science and Applica tions , Vol. 2, No. 9, 201 1 118 | P a g e www . ijacsa.thesai.o rg (IIT -KGP) , “ Audio watermark resi stant to mp3 co mpre ssion ,” p. 13. [8] D. MacKa y, “ I nformati on Th eory, I nferen ce a nd L earning A l go r ithms ,” Cambridge U niversity Pr ess, Sept ember 2003 pp. 218 - 222. [9] C. Z eng a nd Y. Zhong, "An i nterlea ving -decompositi on ba sed digita l watermarkin g scheme i n wav elet domai n," 8t h I nternational C onferen ce on Signal Pro cessin g, Vol. 4, No v. 2 006 . [10] P. Agar wal and B. Pra bh ak aran , “R eliable T ran smission of Audio Streams i n Lossy Channe ls Using Application Lev el Da ta Hi ding ,” Journal o f Multi medi a, Vol. 3, No. 5, D ecember 20 08 , pp. 1 - 8. [11] J. Liu an d Z. Lu , “ A Multipurp ose Audio Watermarki ng Algorit hm Based on Vector Qua ntization i n DCT Domain ,” World Ac ade my of Science, E ngineering and T echnolog y (W ASET), I ssue 55 , Jul y 2009 , pp. 399- 404. [12] R. Ra vula, M.S . Th esis, D epart ment of El ectrical a nd C om puter Engineerin g, L ouisiana State Univer sity a nd Agricultural a n d Mechanical C ollege , “ Audio Watermark ing u sing T ransfor mation Techniqu es ,” pp. 8- 51 . [13] Y. Ya n, H. Ro ng, and X. Minta o, “A N ovel Audio Watermarki ng Algorith m for C opyright Prot ection Ba se d o n DCT D omai n ,” Se cond Internati on al Symposiu m on E lectro nic Commer ce and Se curity, China, May 2009 , pp. 184 - 188. [14] G. Casella and E.L. Lehmann, T heory o f Point Estimatio n. N ew Yo rk: Springer -Verlag, 199 9. [15] T. N. Pa pp a s, R . J. Safranek a nd J. Che n, “ Perc eptual criteria for i ma ge quality e valuation,” in H a ndbook of I ma ge and Video Processin g, 2nd ed., May 20 05.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment