Biometric and Physical Identifiers with Correlated Noise for Controllable Private Authentication
The problem of secret-key based authentication under privacy and storage constraints on the source sequence is considered. The identifier measurement channels during authentication are assumed to be controllable via a cost-constrained action sequence…
Authors: Onur Günlü, Rafael F. Schaefer, H. Vincent Poor
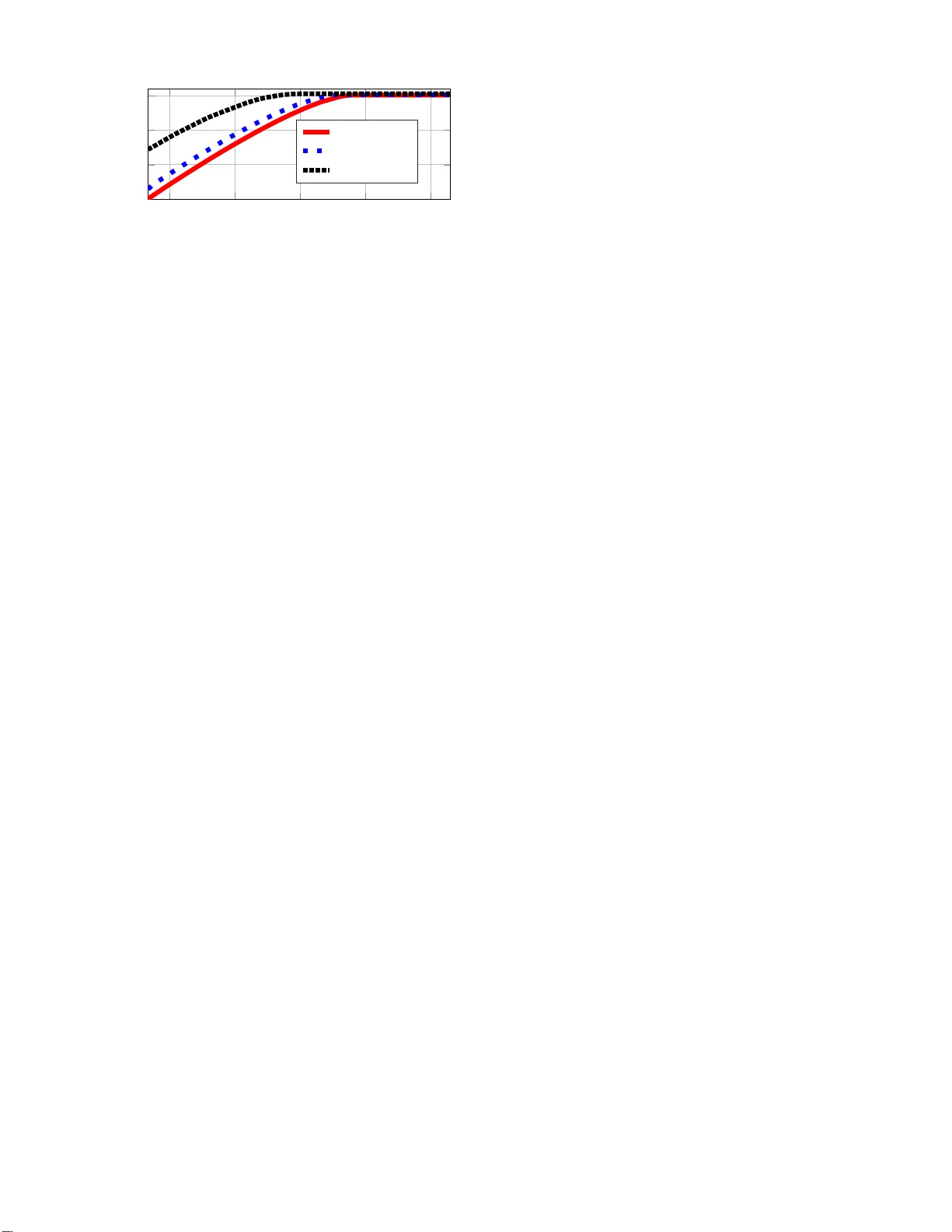
Biometric and Physical Identifiers with Co rrelat ed Noise for Co ntrollable Pri v ate Authentication Onur G ¨ unl ¨ u 1 , Rafael F . Schaefer 1 , and H. V incent Poor 2 1 Information Theory and Applications Chair , T echnisch e Uni versit ¨ at Berlin, { guenlue, raf ael.sch aefer } @tu-berlin.de 2 Department of Electrical Engineering, Pri nceton Univ ersity , poor@princeton.e du Abstract —The problem of secr et-key based authentication under priva cy and storage constraints on the sour ce sequence is consid ered. The ident ifier measureme nt channels du ri n g au- thentication are a ssumed to be controllable via a cost-constrained action sequence. Single-letter inner and outer bounds f or the key- leakage-storage-co st regions are deriv ed for a generalization of a classic two-terminal key agreem ent model with an ea vesdr opper that ob serves a sequence th at is correlated with the sequ en ces observ ed by the legitimate terminals. The additions to th e model are that t h e encoder observe s a n oisy versio n of a r emote source, and the noisy outpu t and the rem ote source output together with an action sequence are giv en as inputs to the measurement channel at the decoder . Thu s, correlation is i n troduced between the noise components on the encoder and decoder measurements. The model with a secret key generated by an encoder is extend ed to the randomized models, where a secr et-key is embedded to the e ncoder . The results ar e relev ant f or sev eral u ser and device authen tication scenarios includ ing p hysical and biometric identifiers with multiple measur ements that pro vide div ersity and multiplexing gains. T o illu strate the b eh a vior of the rate region, achiev able (secret-key rate, storage-rate, cost) tuples ar e gi ven fo r binary identifiers and measureme nt channels that can be repre sented as a mixture of b inary symmetric su bchannels. The gains fr om u sing an action sequence such as a large sec ret-key rate at a significantly small hardwa re co st, are illustrated to motiv ate the use of low-complexity transfor m-coding algorithms with cost-constrained actions. I . I N T RO D U C T I O N A trad itional method for secur ity is to store secret keys used for, e.g., device authentication in a hard ware- p rotected non-volatile mem o ry (NVM ). Biom etric identifiers such as fingerpr in ts and physical iden tifiers such as r a n dom and uniq ue oscillation freq uencies of r ing oscillators (ROs) are secur e and cheap altern ativ es to key storag e in an NVM. Physical unclona b le function s (PUFs) are p hysical iden tifiers th at ar e challenge respon se mappings such that it is easy to ev aluate the r e sponse to a gi ven challenge and hard to guess th e response to a rand omly chosen challeng e [1]. PUFs can be used as a source of local rando mness for the wiretap chan nel (WTC) [2], where the optimal coding scheme requ ires rand om sequences at the WTC encoder . Other applicatio ns of PUFs are Internet- o f-Thin g s (Io T ) de vice security , intellectual property (IP) pro tection in a field prog rammab le gate arr a y (FPGA), and non -repud iation [3, Chap ter 1]. W e extend the sour ce m odel f o r ke y ag reement from [4] , [5] to co nsider mu ltiple imp rovements to priv ate authen tication with PUFs a nd biometr ics. T he orig inal mo del considers that an en coder observes a source outpu t to gen erate a key and to send public in f ormation , called helper data , to a decode r . Ke y agreemen t at the decoder is successful when the de coder observes a noisy source o utput and enough amount of h elper data to recon struct the same key . The secrecy measure u sed is the amount of information the helper data lea ks about the secret key , i.e., secr ecy leakage , which should be negligible. Similarly , [6], [7] argue that the informa tion leaked about the source output should b e also sm a ll to keep privacy leakage as small as possible, which ca n not be made negligible f or g eneral cases. Th e am o unt o f public storage should also be kept small to limit the h ardware co st [8], [9]. Biometric and physical identifier outpu ts are noisy . Suppo se we have multip le m easurements of an identifier so urce at the encoder, which assumes th at th e source is hidd e n or rem ote [10]. The source, noisy iden tifier , and measur e ment symbol strings are pr o posed in [11] to be related b y a bro adcast channel (BC) with one input and two ou tp uts to capture the effects of correlated noise in the measurem ents. For in stance, the surro unding hardware logic is the main reason for th e noise components on encoder a n d decoder measurem ents of the same RO to be corr elated [ 12]. Motiv ated by the u se of dif - ferent id entifier-measurement for ms, e.g. , th e u se of multiple measuremen ts or variations in the qu ality of the measurem ent process [13], we e xtend a private auth e ntication model fro m [14]. I n this model, iden tifier measur ements a re represented by a co st-constrained action- depend ent side information acquisi- tion wh ere an action seque n ce determin es the measurem e n t channel at the dec o der . A high cost for an action represents, e.g., the use of a hig h q uality measurement device that results in a small error proba b ility . W e comb in e the BC measuremen t model with the action -depen d ent priv ate authentication model to consider th e c o rrelated n o ise on encod er and decode r measuremen ts such that the deco d er me a surement channel can be ad a pted to the variations in the amb ient temperatu re, su p ply voltage, and surr oundin g logic. Suppose the encoder gen erates a ke y fro m a no isy identifier output. W e call this mode l the generated- secr et (GS) mo del. Similarly , for the chosen- secr e t (CS) model, a chosen key and noisy identifier measuremen ts are combined to generate the he lp er data. W e co nsider also the CS model to addr ess the cases where the enc o der, e.g. , a hardware man ufacturer (for PUFs) or a trusted entity (f or biometrics), pre-deter mines the secret key for prac tical reasons. Ke y agreemen t with correlated side infor mation at the eavesdropper (E VE) is considered in, e.g., [15]–[19]. This assumption is r ealistic fo r key agreeme n t with biometr ic iden tifiers since an eavesdropper can ob tain side informatio n fr o m, e.g., any ob ject touch ed by a n ind i vidual. PUF outpu ts are perman ently changed by in vasi ve attacks [2 0], so no n -inv asive attacks to the devices that emb ody the PUF shou ld be co nsidered to m ake this model realistic for ph ysical iden tifier s. W e allow side inf o rmation at the ea vesdropper to consider both biometric and physical identifier models. Fu r thermor e, we stu d y in depend ent and identically distributed (i.i.d.) source outputs and mem oryless measuremen t channels. Th ese mod els are rea listic if one uses transform -coding algorithms from [2 1], [22] to extract almost i.i.d. sequen c es fr om PUFs or b iometric identifiers. W e der iv e ach iev a b le key-leakage- storage-co st regions fo r a decod er measuremen t chan n el with th ree inp u ts an d two outputs f or a strong secrecy metric. T he m odel of the separate encoder and d ecoder measurem e n ts in [14] corr esponds to a physically-d egraded measur ement channel for a weak secrecy metric. T o provid e strong secr ecy , th ere is a “priv ate” key assumption, e . g., in [6], [7] , [2 3], where they c onsider that the key is available to the en coder an d deco der and is hidden from an ea vesdr opper . This assumption is unrealistic because if a priv ate-key protectio n against attac kers is feasib le, then there is no need fo r key ag reement with identifiers. W e do not make such un realistic assumptions to provid e strong secrecy and we u se the output statistics of random b inning (OSRB) method from [24], which req uires on ly local ran domne ss. Our rate regions recover pr evious rate region s in the literatur e for hidden and visible sour ces. W e establish o u ter bounds for condition ally less-noisy (CLN) channels defined in [25 ]. The inner boun ds and outer boun d s for the GS models are extend ed to the ran domized m odels, i.e., CS models. This pap er is organized as follows. In Section II, we describe our models and the prob lem. W e give a chiev able key-leakage-storag e-cost regions for the GS and CS mo d els in Section III. W e define CLN chann els and show o uter bound s fo r the key-leakage- sto rage-cost regions in Section IV if tw o CLN conditions are satisfied. W e g i ve an e xample in Section V to illustra te the gains from having a larger hardware area av ailable f or p ublic stor age in com bination with a co st-constrained actio n sequen ce for a practical PUF design. Achiev ability proo fs for the inner bound s an d outer boun ds fo r CLN ch annels are given in Section s VI an d VII, respectively . Section VIII con cludes th e paper . I I . P RO B L E M D E FI N I T I O N S Consider the GS mod e l in Fig. 1 ( a ) , wher e a key is generated from a hidden source. T he source X , measur e m ent e X , Y , Z , and action A alphabets are finite sets. The encoder observes uncontrollab le noisy measurem ents e X n of the i.i.d. P X ( W , S ) ( a ) = f 1 ( e X n ) W ( b ) = f 2 ( e X n , S ) P Y Z | X e X A P e X | X A n = f a ( W ) ˆ S = g ( W , Y n ) EVE W X n Y n e X n X n A n Z n S ˆ S ( b ) ( a ) W e X n Fig. 1. A hidden id entifier source : ( a ) re presents t he GS model with the encode r f 1 ( · ) and ( b ) represents the CS model with the enc oder f 2 ( · , · ) . hidden source outp uts X n throug h a me moryless channe l P e X | X . The encoder comp utes a secret key S and pub lic helpe r data W as ( W , S ) = f 1 ( e X n ) . During au thentication , the action encoder o b serves the helper data W and comp utes an action sequenc e A n as A n = f a ( W ) . Then , the d ecoder, g iv en ( X n , e X n , A n ) , observes cost-constrain ed controllable sou rce measuremen ts Y n throug h a memo ryless channel P Y Z | X e X A together with the helper data W and estimates th e secret key as ˆ S = g ( W , Y n ) . The eavesdropper ob serves Z n as the o utput of the same memory le ss ch annel in addition to the public helper d ata W . Similarly , Fig. 1 ( b ) shows the CS mod el, where a secret key S that is ind ependen t of ( X n , e X n , Y n , Z n ) is embedd e d into the helper d a ta as W = f 2 ( e X n , S ) . The a c tio n encoder and the de coder for the CS mo del are ap plied in a similar way to the GS m odel. Definition 1. A key-leakage-storag e-cost tuple ( R s , R ℓ , R w , C ) is a chievable for the GS o r CS m odel if, gi ven δ > 0 , there is some n ≥ 1 , an encod er , and a decoder such that R s = log |S | n and Pr[ ˆ S 6 = S ] ≤ δ ( reliability ) (1) I ( S ; W , Z n ) ≤ δ ( strong secrecy ) (2) 1 n H ( S ) ≥ R s − δ ( uniform ity ) (3) 1 n I ( X n ; W, Z n ) ≤ R ℓ + δ ( priv acy ) (4) 1 n log W ≤ R w + δ ( storage ) (5) E [Γ( A n )] ≤ C + δ ( action co st ) (6) where we have Γ( A n ) = 1 n P n i =1 Γ( A i ) . The ke y-leakage- storag e-cost re gion s R gs and R cs for the GS an d CS mo d els, respectively , are the closures of th e sets of all achiev able tup les for the corr espondin g models. ♦ I I I . I N N E R B O U N D S W e are interested in ch aracterizing the optima l trad e-off among the secret-key rate, privac y-leakage ra te, storage rate, and action cost with stron g secrecy for correla ted noise on the encoder and decoder measurements. W e give achiev able rate region s for the GS and CS mode ls in Theo rem 1. See Section VI fo r proof s. Define R ℓ, 1 = I ( V , X ; Z | A ) + I ( X ; A, V , Y ) − I ( V , X ; Y | A ) R ℓ, 2 = I ( V , X ; Z | A, U ) + I ( X ; A, V , Y ) − I ( V , X ; Y | A, U ) R ℓ, 3 = I ( X ; A, U, Z ) . Theorem 1 (In ner Bounds for GS and CS Models) . A n inner bound fo r the rate r e gion R gs for the GS model is the set o f all tuples ( R s , R ℓ , R w , C ) satisfying 0 ≤ R s ≤ I ( V ; Y | A, U ) − I ( V ; Z | A, U ) (7) R ℓ ≥ max R ℓ, 1 , R ℓ, 2 , R ℓ, 3 (8) R w ≥ I ( e X ; A ) + I ( V ; e X | A, Y ) (9) for some P X P e X | X P A | e X P Y Z | X e X A P V | e X A P U | V such that E [Γ( A )] ≤ C . Similarly , an inner bou nd for the rate re gion R cs for the CS model is the set of all tup les ( R s , R ℓ , R w , C ) satisfying (7), (8), an d R w ≥ I ( e X ; A, V ) − I ( U ; Y | A ) − I ( V ; Z | A, U ) (10) for some P X P e X | X P A | e X P Y Z | X e X A P V | e X A P U | V such that E [Γ( A )] ≤ C . Pr oo f Sketch: The proof for the GS mod el uses the OSRB metho d that assigns rand om bin indices to sequences a n , u n , and v n to obtain stron g secrecy . Using the OSRB method consecutively , nin e cases are analy zed, resulting in six d ifferent terms who se maxim um is used in ( 8). The proo f for the CS model uses the key g enerated by using the proof for the GS m odel and applies a one- tim e p adding step to the embedd e d secret key an d the ke y generated by the GS model. The main effect is the increase in the stora ge rate as com pared to the GS m odel by th e amou nt equ al to the boun d in (7). In [14], separate measureme nts P X e X AY Z = P A | e X P e X | X P X P Y Z | X A and a weak secrecy constraint such that (2 ) is replac e d with 1 n I ( S ; W , Z n ) ≤ δ , are considered . The model in Fig. 1 extends [14] by co nsidering correlation in the n oise comp onents on the enco der and decoder measurements with strong secr ecy . Such a correlation is con sidered in [1 1] fo r a mod el with out cost-co nstrained action-dep endent measure ments at the decode r and with o ut correlated side in f ormation Z n at the e avesdropper . Bro adcast channel (BC) measurements are considered in [11] to model the cor relation in the noise compon ents. Du e to th e causal depend ence o f A n on e X n , one canno t mode l e X n as an outp ut of the action -depen dent m easuremen t channel, so Fig. 1 considers the enco d er measurem ent e X n as an input to the measuremen t ch a nnel P Y Z | X e X A . This model is the case, e.g., if the decod er and enco der m easurements are ma de within a co herence time, in an a logy to w ir eless com munication systems, so the en coder measurem ents e X n affect R O outp u ts at the decoder due to r emanining temperatu re an d curren t effects on digital circu its. A similar model is con sidered in [13, Fig. 9] for a source coding with sid e information p roblem without secrecy , priv acy , and secret-key rate co nstraints. Remark 1. The b ound s in Th eorem 1 recover the key- leakage-stor age-cost regions given in [14, T h eorems 3 and 4] for the separ ate-measurem ent model such tha t P X e X AY Z = P A | e X P e X | X P X P Y Z | X A since we h av e R ℓ, 2 ( a ) = I ( X ; Z | A, U ) + I ( X ; A, V , Y ) − I ( X ; Y | A, U ) (11) where ( a ) fo llows for the sep arate-measur ement mod el be- cause ( U, V ) − ( A, X ) − ( Z, Y ) form a Markov chain fo r this model. Similarly , the ke y-leakage - storage rate r egions giv en in [10] fo r measur ement chann els such that P X e X Y = P X P e X | X P Y | X are recovered by the bounds in Th e orem 1 if we choose ( Z , U , A ) as constan ts. Theo r em 1 b ound s recover the key-leakage and key-leakage-stor a g e regions f or visible source models, where encoder measurements are noiseless such th a t e X n = X n , giv en in [6], [7], [14, The o rems 1 an d 2] . I V . O U T E R B O U N D S W e give o uter bounds for CLN ch a nnels, defined in Defini- tion 2, for the model dep icted in Fig. 1. Definition 2 ([2 5]) . X is conditionally less-noisy (CLN) than Z g iv en ( A, Y ) if I ( L ; X | A, Y ) ≥ I ( L ; Z | A, Y ) (12) holds for any ran dom variable L such that L − ( A, e X , Y ) − ( X, Z ) form a Mar kov chain and we denote this r elation as ( X ≥ Z | A, Y ) . The set of CLN channels is shown in [25] to be larger th a n the set of physically de graded chan nels. W e gi ve o uter boun ds for the ra te regions R gs and R cs in Theo rem 2 when two CLN condition s are satisfied. See Section VII for pro ofs. Theorem 2 (Outer Bounds fo r GS an d CS Mo dels) . An ou ter bound for the rate re gion R gs for a ll CLN channels such that ( X ≥ Z | A, Y ) and ( Z ≥ Y | A, X ) is the set of all tu ples ( R s , R ℓ , R w , C ) satisfying 0 ≤ R s ≤ I ( V ; Y | A, U ) − I ( V ; Z | A, U ) (13) R ℓ ≥ I ( X ; A, V , Y ) − I ( X ; Y | A ) + I ( X ; Z | A ) + I ( U ; Y | A ) − I ( U ; Z | A ) (14) R w ≥ I ( e X ; A ) + I ( V ; e X | A, Y ) (15) such that U − V − ( A, e X ) − ( A, e X , X ) − ( Y , Z ) form a Markov chain an d E [Γ( A )] ≤ C . Similarly , a n outer boun d for the rate r e g ion R cs for all CLN channels such that ( X ≥ Z | A, Y ) and ( Z ≥ Y | A, X ) is the set o f a ll tu ples ( R s , R ℓ , R w , C ) satisfying (1 3), (14), a nd R w ≥ I ( e X ; A, V ) − I ( U ; Y | A ) − I ( V ; Z | A, U ) (16) such that U − V − ( A, e X ) − ( A, e X , X ) − ( Y , Z ) form a Ma rkov chain and E [Γ( A )] ≤ C . It su ffices to limit the ca r d inalities to |U | ≤ |A|| e X | + 3 and |V | ≤ ( |A|| e X | + 3)( |A|| e X | + 2) . Pr oo f Sketch: The pr o of for the priv acy-leakage r ate R ℓ bound u ses an inequality that we prove for the CLN channel ( X ≥ Z | A, Y ) , which might be useful also for other p roblems. W e also assume an other CLN conditio n ( Z ≥ Y | A, X ) and prove the existence of a single-letter r e presentation of a subtraction o f condition al entropies to fin d a lower b ound for the subtr a ction ter m by applyin g the p roperties of the seco nd CLN conditio n. Th e p roofs for the secret-key rate, stor age rate, and ac tio n cost follow by using standard pro p erties of the Shan n on entro py . Remark 2. The b ound s in Th eorem 2 r ecover the key- leakage-stor age-cost regions giv en for the mo re re stricti ve case considered in [14] with the Markov chain e X − ( A, X ) − ( Y , Z ) since we h av e in (14) for th e more restrictiv e case th at R ℓ ≥ I ( X ; A, V , Y ) − I ( X ; Y | A ) + I ( X ; Z | A ) + I ( U ; Y | A ) − I ( U ; Z | A ) ( a ) = I ( X ; A, V , Y ) − I ( X ; Y | A, U ) + I ( X ; Z | A, U ) (17) where ( a ) fo llows from the Mar kov chain U − ( A, X ) − ( Y , Z ) , which is v alid on ly f or the m ore restricti ve case. It is straigh t- forward to show that th e bou nds in The o rem 2 re c over th e outer bou nds g iv en in [6 ], [7], [9], [1 1]. V . E X A M P L E W e illu stra te the e ffects of th e storag e rate o n the achievable secret-key rate an d expected action cost. An achie vable key- leakage-stor age-cost tr adeoff with ad ditional assumptions for the a u xiliary r andom variables and with realistic measureme n t channel pa r ameters suffices to mo tiv ate th e use of an action in prac tica l b iometric secrecy sy stem s and PUFs. Suppose the hid den iden tifier outp uts X n are un iformly d is- tributed bit sequences, the eav esdropp er side information Z n is a physically-degraded version of the decoder m easurements Y n , i.e., ( A, e X , X ) − Y − Z form a Markov ch a in, an d we have binary sy mmetric chann els (BSCs) with crossover probab ilities p , den oted as BS C ( p ) , such th at P e X | X ( ·|· ) ∼ BSC ( p enc ) (18) P Z | Y ( ·|· ) ∼ BSC ( p eve ) (19) P Y | X e X A ( ·|· , e x, a ) ∼ BSC ( q e xa ) fo r all e x, a ∈ { 0 , 1 } . (20) Consider ph y sical identifiers like start-u p values of static random access m emories (SRAM) or RO outpu ts. Symmetr ic source outputs and BSCs ar e realistic source and chan n el models for such id entifiers [21], [ 26]. W e can therefore use the ch a nnel param eters ob tained in the literatu re fo r real R Os and SRAMs. Decoder measuremen ts with smaller crossover pr obability can be obtaine d by applying additional post-pr ocessing steps, which incr eases the h a rdware cost [27]. Suppose th a t the actio n A = a ch ooses BSCs such that q e x 0 < q e x 1 for all e x ∈ { 0 , 1 } , i.e., A = 0 cho o ses more r eliable measure m ent channels with higher co st. Similarly , assume q 0 a < q 1 a for all a ∈ { 0 , 1 } , i.e., e X = 0 ch o oses mor e reliable m easurement chann els with h igher cost. Th is assump tion is realistic if the ambien t temperatur e increases dur in g encoder measure ments since th e oscillation freq uency of an RO dec r eases with incr e a sing temperatur e [28], wh ich results in a bias towards th e bit 0 after quantization. In such a case, the decod er measureme nt channels sho u ld b e chosen to be more reliab le to com pensate for the performan ce lo ss due to the tempe r ature in crease. Moreover , th e action cost should be hig her for the cases with higher hardware cost. W e thus cho ose the costs of ac tions as Γ(0) = q 01 + q 11 q 01 + q 11 + q 10 + q 00 , Γ(1) = 1 − Γ(0) (21) where q 00 , q 01 , q 10 , q 11 are as defin ed in (20). W e use r eal- istic crossover p robab ilities for R O PUFs comb in ed with the transform -coding algo rithm giv en in [3] and satisfy the as- sumptions giv en above by choo sing p enc = 0 . 05 , q 00 = 0 . 01 0 , q 10 = 0 . 0 30 , q 01 = 0 . 0 50 , q 11 = 0 . 0 60 , and p eve ≈ 0 . 1 02 such that p eve ∗ q 11 = 0 . 150 , wh ere ∗ - operator is defined a s p ∗ q = (1 − 2 q ) p + q . The crossover prob ability of 0 . 1 50 correspo n ds to the case that the eavesdropper observes no isy PUF ouputs but cannot control the en vironm ental variations as a passiv e attacker [ 28]. Furtherm ore, these values result in Γ(0) ≈ 0 . 733 units and Γ(1) ≈ 0 . 267 units by ( 2 1). Let th e auxiliar y rando m v ariable U be co nstant, so from Theorem 1 we ha ve an inner bound for th e GS model that is the set of a ll tuples ( R s , R ℓ , R w , C ) satisfying 0 ≤ R s ≤ I ( V ; Y | A ) − I ( V ; Z | A ) (22) R ℓ ≥ max n I ( V , X ; Z | A ) + I ( X ; A, V , Y ) − I ( V , X ; Y | A ) , I ( X ; A, Z ) o (23) R w ≥ I ( e X ; A ) + I ( V ; e X | A, Y ) (24) for some P X P e X | X P A | e X P Y Z | X e X A P V | e X A such th a t E [Γ( A )] ≤ C . Let P A | e X be a binary chan nel and P V | A e X ( ·| a, · ) be a BSC ( p a ) f o r a = 0 , 1 . W e evaluate an ac h iev a b le key- leakage-stor age-cost region for all possible P A | e X and plot the (cost vs. secret-key rate) pro jection of the bo undary tuples ( R s , R ℓ , R w , C ) for different storage rates R w bits/source- symbol in Fig. 2. Any secr e t-key rate less tha n the secre t- key r ates on the bo u ndary and any cost greater than the cost on the bou ndary are also achiev able. The minimum and maximum expected costs d e picted in Fig. 2 ar e Γ(1) an d Γ(0) , respe c ti vely , since these are costs of two p ossible actio n s A = a . Th e secret-key ra te R s in Fig. 2 does no t decre ase with increasing co st C because for a higher cost better set of channels, i.e., channels with smaller crosssov er p robab ilities, can be u sed f or decod er measurem ents. Fig. 2 shows that, for a gi ven cost C = c , the secr et-key rate R s increases fo r increasing storag e rate R w . Mor eover , the maximum secret-key rates, d enoted by R ∗ s , for different storage rates R w are different an d they ar e obtain ed at d ifferent minimum cost values, denoted by C ∗ . For instance, fo r R w = 0 . 3 0 . 4 0 . 5 0 . 6 0 . 7 0 0 . 1 0 . 2 0 . 3 Cost C Secret-key Rate R s R w = 0 . 00 1 R w = 0 . 05 0 R w = 0 . 25 0 Fig. 2. Cost vs. secret-k e y rate projection of the boundary tuples ( R s , R ℓ , R w , C ) for the GS model with storage rates R w of 0 . 001 , 0 . 050 , and 0 . 250 bits/source-symbol . 0 . 001 bits/sour ce-symbo l we ha ve ( C ∗ = 0 . 5 821 , R ∗ s = 0 . 3 021 bits/source-sym bol); whereas for R w = 0 . 250 bits/source- symbol we ob tain ( C ∗ = 0 . 5028 , R ∗ s = 0 . 3058 bits/source- symbol). T his illustrates that having a larger p ublic storag e av ailab le increases the max imum secret-key rate, e.g., for the given e xample by approx imately 1 . 22% , and significan tly decreases the req u ired expected action cost to ach iev e the maximum secret-key rate, e.g., for this example by app rox- imately 13 . 62% . Thus, a low-complexity PUF design with small h ardware area as in [21], should be used to a llo cate a large hard ware area fo r helpe r data stora g e, which pr ovid es significant gains in th e achieved rate tuples in combinatio n with an action seq uence. V I . P RO O F O F T H E O R E M 1 W e provide a proof that follows from the output statistics of ran dom binn ing (O SRB) method [24] b y app lying the steps in [29, Section 1 .6]. A. Pr oof for the GS Mo del Pr oo f Sketch: Fix P A | e X , P V | e X A , and P U | V such that E [Γ( A )] ≤ C + ǫ and let ( U n , V n , A n , e X n , X n , Y n , Z n ) be i.i. d . accord ing to P U V A e X X Y Z = P U | V P V | e X A P A | e X P e X | X P X P Y Z | X e X A . Suppose H ( V | U, A, Z ) − H ( V | U, A, Y ) > 0 . Assign two random bin indices ( F a , W a ) to each a n . Assume F a ∈ [1 : 2 n e R a ] and W a ∈ [1 : 2 nR a ] . Similarly , assign two indices ( F u , W u ) to each u n , where F u ∈ [1 : 2 n e R u ] and W u ∈ [1 : 2 nR u ] . Furth ermore, assign three ind ices ( F v , W v , S ) to each v n , wh ere F v ∈ [1 : 2 n e R v ] , W v ∈ [1 : 2 nR v ] , an d S ∈ [1 : 2 nR s ] . The helper data are W = ( W a , W u , W v ) , the public indices are F = ( F a , F u , F v ) , and the secret ke y is S . Reliable estimation of A n from ( F a , W a ) is possible if [24, Lemma 1] e R a + R a > H ( A ) . (25) Using a Slep ian -W o lf (SW) [ 30] decod er , one can r eliably estimate U n from ( F u , W u , A n , Y n ) if [2 4, Lem ma 1] e R u + R u > H ( U | Y , A ) . (26) Similarly , one can reliably estimate V n from ( F v , W v , A n , Y n , U n ) by using a SW decoder if [24, Lemma 1] e R v + R v > H ( V | U, Y , A ) . (27) Thus, th e r e liability con straint in (1) is satisfied if (25)-(27) are satisfied. The strong secrecy (2) and key unif o rmity (3) constraints are satisfied if [2 4, Theor em 1] R s + e R v + R v < H ( V | U, A, Z ) (2 8) since (28) ensu res that the three random indices ( S, F v , W v ) are almost independent of ( U n , A n , Z n ) and are almo st mu- tually indepe n dent and u niform ly distributed. The pub lic in dex F a is almo st indep endent of e X n , so it is almost ind ependen t of ( e X n , X n , Y n , Z n ) , if we have [2 4, Theorem 1] e R a < H ( A | e X ) . (29) Similarly , the public index F u is almost independ ent of ( A n , e X n ) , so it is almost independent of ( A n , e X n , X n , Y n , Z n ) , if we ha ve [24, The o rem 1] e R u < H ( U | A, e X ) . ( 3 0) Furthermo re, the public index F v is almost indep e n- dent of ( U n , A n , e X n ) , so it is almost in depend ent o f ( U n , A n , e X n , X n , Y n , Z n ) , if we have [2 4, Theor em 1] e R v < H ( V | U, A, e X ) . (31) Thus, the public indices F can be fixed by generating them unifor m ly at random. The encoder can generate ( A n , U n , V n ) accordin g to P A n U n V n | e X n F a F u F v obtained from the binnin g scheme a b ove to comp ute the b ins W a from A n , W u from U n , and ( W v , S ) from V n . This procedu re indu c es a join t probab ility distribution that is almost equal to P U V A e X X Y Z fixed ab ove [29, Section 1.6 ]. T o satisfy the constraints (25)-(31), we fix the r ates to e R a = H ( A | e X ) − ǫ (32) R a = I ( A ; e X ) + 2 ǫ (33) e R u = H ( U | A, e X ) − ǫ (34) R u = I ( U ; e X | A ) − I ( U ; Y | A ) + 2 ǫ (35) e R v = H ( V | U, A, e X ) − ǫ (36) R v = I ( V ; e X | A, U ) − I ( V ; Y | A, U ) + 2 ǫ (37) R s = I ( V ; Y | A, U ) − I ( V ; Z | A, U ) − 2 ǫ (38) for some ǫ > 0 such th at ǫ → 0 when n → ∞ . T his results in a storage (h elper-data) rate R w of R w = R a + R u + R v = I ( A ; e X ) + I ( U, V ; e X | A ) − I ( U, V ; Y | A ) + 6 ǫ ( a ) = I ( A ; e X ) + I ( V ; e X | A ) − I ( V ; Y | A ) + 6 ǫ ( b ) = I ( A ; e X ) + I ( V ; e X | A, Y ) + 6 ǫ (39) where ( a ) fo llows because U − ( V , A ) − ( e X , Y ) form a Markov chain an d ( b ) f ollows since V − ( A, e X ) − Y for m a Markov chain. Furthermor e, since e ach action sequ ence a n is in th e typical set with hig h probab ility , b y the typ ica l average lemm a [31, pp . 26] , the expected c ost constrain t in ( 6) is satisfied. Since F is public, we can bound the p r iv acy leakage as follows. I ( X n ; W, Z n , F ) ( a ) ≤ I ( X n ; W, Z n | F ) + 3 ǫ n ( b ) ≤ H ( X n | F ) − H ( X n , W, Z n | F ) + H ( W | F ) + H ( Z n | A n , U n ) + I ( A n , U n ; Z n | W a , F a , W u , F u ) + 4 ǫ n ( c ) ≤ − H ( Z n | X n , F ) − H ( W , A n | X n , Z n , F ) + H ( W | F ) + H ( A n | W , X n , Z n , F ) + H ( Z n | A n , U n ) + 4 ǫ n + nǫ ′ n + I ( U n ; Z n | A n , W u , F u ) ( d ) ≤ − H ( A n | X n , F a ) + I ( F u , F v ; A n | X n , F a ) − H ( Z n | A n , X n ) + I ( Z n ; F u , F v | A n , X n ) − H ( W | A n , X n , Z n , F ) + 2 nǫ ′ n + 4 ǫ n + H ( W | F ) + H ( Z n | A n , U n ) + I ( U n ; Z n | A n , W u , F u ) ( e ) ≤ − H ( A n | X n ) + H ( F a | X n ) − H ( Z n | A n , X n ) + 2 nǫ ′ n + 8 ǫ n − H ( W u , V n | A n , X n , Z n , F ) + H ( V n | W , A n , X n , Z n , F ) + H ( W | F ) + H ( Z n | A n , U n ) + I ( U n ; Z n | A n , W u , F u ) ( f ) ≤ − H ( A n | X n ) + nH ( A | e X ) − H ( Z n | A n , X n ) + 2 nǫ ′ n + 8 ǫ n − H ( V n | A n , e X n , F ) − I ( V n ; e X n | A n , X n , Z n , F ) + H ( V n | W , A n , X n , Z n , F ) + H ( W | F ) + H ( Z n | A n , U n ) + nI ( U ; Y | A ) + 5 ǫ n − H ( U n | Z n , A n , W u , F u ) ( g ) ≤ − H ( A n | X n ) + nH ( A | e X ) − H ( Z n | A n , X n , U n ) − I ( U n ; Z n | A n , X n ) + 2 nǫ ′ n + 15 ǫ n − H ( e X n | A n , X n , Z n ) + H ( e X n | A n , X n , Z n , V n ) + H ( V n | W , A n , X n , Z n , F ) + H ( W a ) + H ( W u ) + H ( W v ) + H ( Z n | A n , U n ) + nI ( U ; Y | A ) − H ( U n | Z n , A n , W u , F u ) ( h ) ≤ n − H ( A | X ) + H ( A | e X ) + I ( X ; Z | A, U ) − I ( U ; Z | A, X ) − nI ( e X ; V | A, X , Z ) + 2 nǫ ′ n + 15 ǫ n + n I ( e X ; A, V ) − I ( U ; Y | A ) − I ( V ; Y | A, U ) + 6 ǫ + nI ( U ; Y | A ) − H ( U n | Z n , A n , W u , F u ) + H ( V n | W , A n , X n , Z n , F ) ( i ) ≤ n I ( X ; Z | A, U ) − I ( U ; Z | A, X ) + 2 nǫ ′ n + 15 ǫ n + 6 nǫ + n − H ( V , A | X ) + I ( V ; Z | A, X ) + H ( V , A | e X ) + n I ( e X ; A, V ) − I ( V ; Y | A, U ) − H ( U n | Z n , A n , W u , F u ) + H ( V n | W , A n , X n , Z n , F ) ( j ) = n I ( X ; Z | A, U ) + I ( X ; A, V ) − I ( V ; Y | A, U ) + 2 nǫ ′ n + 15 ǫ n + 6 nǫ + nI ( V ; Z | A, X , U ) − H ( U n | Z n , A n , W u , F u ) + H ( V n | W , A n , X n , Z n , F ) ( k ) = n I ( X ; Z | A, U ) + I ( X ; A, V , Y ) − I ( X , V ; Y | A, U ) + 2 nǫ ′ n + 15 ǫ n + 6 nǫ + nI ( V ; Z | A, X , U ) − H ( U n | Z n , A n , W u , F u ) + H ( V n | W , A n , X n , Z n , F ) = n I ( X ; Z | A, U ) + I ( X ; A, V , Y ) − I ( X ; Y | A, U ) + 2 nǫ ′ n + 15 ǫ n + 6 nǫ + nI ( V ; Z | A, X , U ) − H ( U n | Z n , A n , W u , F u ) − nI ( V ; Y | A, X , U ) + H ( V n | W , A n , X n , Z n , F ) (40) where ( a ) follows f rom [24, Theore m 1] such that we ha ve th a t F is almo st inde penden t of ( e X n , X n ) due to the Ma r kov ch a in X n − e X n − F . W e ha ve I ( X n ; F ) = I ( X n ; F a ) + I ( X n ; F u | F a ) + I ( X n ; F v | F a , F u ) ( a. 1) ≤ 3 ǫ n (41) where ( a. 1 ) follows by (3 2), (34), an d (36), and from the facts that A n determines F a and U n determines F u , for some ǫ n > 0 with ǫ n → 0 wh e n n → ∞ ; ( b ) follows because ( F v , W v ) are almost indepe n dent o f ( U n , A n , Z n ) by (28), A n determines ( W a , F a ) , and U n determines ( W u , F u ) ; ( c ) fo llows since A n determines ( F a , W a ) , a n d from (25) an d [24, Lem ma 1] we ha ve H ( A n | W a , F a ) ≤ nǫ ′ n for so me ǫ ′ n → 0 when n → ∞ ; ( d ) fo llows because b y (25) such that H ( A n | W , X n , Z n , F ) ≤ nǫ ′ n for some ǫ ′ n → 0 when n → ∞ an d A n determines F a ; ( e ) follows by (30) and (31), and because A n determines W a , V n determines W v , and we obtain I ( F u , F v ; A n | X n , F a ) = I ( F u ; A n | X n , F a ) + I ( F v ; A n | X n , F a , F u ) ≤ 2 ǫ n and I ( Z n ; F u , F v | A n , X n ) = I ( Z n ; F u | A n , X n ) + I ( Z n ; F v | A n , X n , F u ) ≤ 2 ǫ n since F u is almost indepen dent of ( A n , X n , Z n ) , U n deter- mines F u , and F v is almost indepen dent of ( U n , A n , X n , Z n ) ; ( f ) f ollows by (32), from the Markov chain V n − ( A n , e X n , F ) − ( X n , Z n ) , and fr o m the following inequality H ( U n | A n , W u , F u ) ( f . 1) = H ( U n | A n ) − H ( W u , F u | A n ) ( f . 2) ≤ H ( U n | A n ) − ( H ( W u | A n ) + H ( F u | A n ) − ǫ n ) ( f . 3) ≤ H ( U n | A n ) − ( H ( W u ) − ǫ n ) − ( H ( F u ) − ǫ n ) + ǫ n ( f . 4) ≤ H ( U n | A n ) − ( nR u − ǫ n ) − ( n e R u − ǫ n ) + 3 ǫ n ( f . 5) ≤ nI ( U ; Y | A ) + 5 ǫ n (42) where ( f . 1) fo llows because U n determines ( W u , F u ) , ( f . 2) follows fro m R u + e R u < H ( U | A ) for some ǫ n > 0 such that ǫ n → 0 when n → ∞ , ( f . 3) follows because W u is almost indepe n dent of A n due to R u < H ( U | A ) whe n n → ∞ and F u is almost in depend ent of A n due to e R u < H ( U | A ) when n → ∞ fo r some ǫ n > 0 such th at ǫ n → 0 when n → ∞ , ( f . 4) follows because ( W u , F u ) are almost u niformly distributed due to R u + e R u < H ( U ) , and ( f . 5) follows by ( 3 4) and (35); ( g ) follows since A n determines F a and by (3 0) and (31), an d we obtain I ( F u , F v ; e X n | A n , X n , Z n ) = I ( F u ; e X n | A n , X n , Z n ) + I ( F v ; e X n | A n , X n , Z n , F u ) ≤ 2 ǫ n since F u is almost in depend ent of ( A n , X n , Z n , e X n ) , U n determines F u , and F v is almost independen t o f ( U n , A n , X n , Z n , e X n ) ; ( h ) follows by (3 3), ( 35), and (37), and fr om th e M a r kov chains A − e X − X and U − ( V , A ) − e X ; ( i ) follows fr om the Markov ch ain V − ( A, e X ) − ( X , Z ) ; ( j ) follows fr om th e Markov chain Z − ( A, X , V ) − U ; ( k ) follows from the Mar kov chain U − ( V , A ) − ( Y , X ) . Consider multi-letter terms in (40), i.e., − H ( U n | Z n , A n , W u , F u ) + H ( V n | W , A n , X n , Z n , F ) . There are nin e ca ses we have to analyze for th is sum. Case 1 : Sup pose we have R u + e R u < H ( U | Z , A, X ) (43) R v + e R v ≥ H ( V | Z, A, X ) . (44) Then, W u , F u , and ( Z n , A n , X n ) ar e almost mutu a lly in- depend ent, and W u and F u are almost uniformly distrib uted by [24, Theorem 1]. Fur thermor e , we can r ecover V n from ( F v , W v , Z n , A n , X n ) by usin g a SW decoder [24, Lemma 1]. W e obtain − H ( U n | Z n , A n , W u , F u ) + H ( V n | W , A n , X n , Z n , F ) ( a ) ≤ − H ( U n | Z n , A n ) + H ( W u , F u | Z n , A n ) + H ( V n | W v , A n , X n , Z n , F v ) ( b ) ≤ − H ( U n | Z n , A n ) + H ( W u ) + H ( F u ) + nǫ ′ n ( c ) ≤ n ( − H ( U | Z, A ) + H ( U | Y , A ) + ǫ + ǫ ′ n ) (45) where ( a ) follows becau se U n determines ( F u , W u ) , ( b ) fol- lows b y (44) such that H ( V n | F v , W v , Z n , A n , X n ) ≤ nǫ ′ n for some ǫ ′ n > 0 such that ǫ ′ n → 0 when n → ∞ , and ( c ) fo llows by (34) and (3 5). Combining (40) and ( 45), we obta in f or Case 1 I ( X n ; W, Z n , F ) ( a ) ≤ n I ( X ; Z | A, U ) + I ( X ; A, V , Y ) − I ( X ; Y | A, U ) + n I ( V ; Z | A, X , U ) − I ( V ; Y | A, X , U ) + n ( I ( U ; Z | A ) − I ( U ; Y | A ) + ǫ ′′ ) ( b ) = n I ( V , X ; Z | A ) + I ( X ; A, V , Y ) − I ( V , X ; Y | A ) + nǫ ′′ (46) where ( a ) follo ws for some ǫ ′′ > 0 such that ǫ ′′ → 0 when n → ∞ a n d ( b ) fo llows f rom the Ma r kov chain U − V − ( A, X , Z , Y ) . Case 2 : Sup pose we have R u + e R u < H ( U | Z, A, X ) (47) R v + e R v < H ( V | Z , A, X ) (48) R v + e R v ≥ H ( V | U , Z, A, X ) . (49 ) Then, W u , F u , and ( Z n , A n , X n ) a r e almo st mutu ally indep e n - dent, and W u and F u are almost uniform ly distributed by [2 4, Theorem 1]. Similarly , W v , F v , and ( Z n , A n , X n ) are almost mutually ind epende n t [24, T h eorem 1 ] , but we can recover V n from ( U n , Z n , A n , X n ) [2 4, Lemm a 1 ]. Mo reover , W v and F v are almost un iformly d istributed [24, Th eorem 1]. W e h av e − H ( U n | Z n , A n , W u , F u ) + H ( V n | W , A n , X n , Z n , F ) ( a ) ≤ − nH ( U | Z, A ) + H ( W u , F u | Z n , A n ) + nH ( V | A, X , Z ) − H ( W u , F u | A n , X n , Z n ) − H ( W v , F v | A n , X n , Z n , W u , F u ) + nH ( U | A, X , Z , V ) ( b ) ≤ − nH ( U | Z, A ) + H ( W u ) + H ( F u ) + nH ( U, V | A, X , Z ) − ( H ( W u | A n , X n , Z n ) + H ( F u | A n , X n , Z n ) − ǫ n ) − H ( F v | A n , X n , Z n , W u , F u ) − H ( W v | A n , X n , Z n , W u , F u , F v ) ( c ) ≤ − nH ( U | Z, A ) + H ( W u ) + H ( F u ) + nH ( U, V | A, X , Z ) − ( H ( W u ) − ǫ n ) − ( H ( F u ) − ǫ n ) + ǫ n − ( H ( F v ) − ǫ n ) − H ( W v | A n , X n , Z n , U n , F v ) ( d ) ≤ − nH ( U | Z , A ) + nH ( U, V | A, X , Z ) + 4 ǫ n − H ( F v ) − H ( V n | A n , X n , Z n , U n , F v ) + nǫ ′ n ( e ) ≤ − nH ( U | Z , A ) + nH ( U, V | A, X , Z ) + 4 ǫ n − H ( V n | A n , X n , Z n , U n ) + nǫ ′ n = − nI ( U ; X | Z, A ) + 4 ǫ n + nǫ ′ n (50) where ( a ) follows be c ause U n determines ( F u , W u ) , A n determines ( F a , W a ) , an d V n determines ( F v , W v ) , ( b ) follows by (47) such that W u and F u are almost inde penden t giv en ( A n , X n , Z n ) , ( c ) follows by (4 7) such th at W u and F u are almost indepen dent of ( A n , X n , Z n ) and by (31) such that F v is almost indep endent of ( A n , X n , Z n , U n ) and U n determines W u and F u , ( d ) fo llows b ecause V n determines W v and by (49 ), and ( e ) follows sinc e V n determines F v . Combining (40) and ( 50), we obta in for Case 2 I ( X n ; W, Z n , F ) ( a ) ≤ n I ( X ; Z | A, U ) + I ( X ; A, V , Y ) − I ( X ; Y | A, U ) + n I ( V ; Z | A, X , U ) − I ( V ; Y | A, X , U ) − n ( I ( U ; X | Z, A ) + ǫ ′′ ) = n I ( V , X ; Z | A, U ) + I ( X ; A, V , Y ) − I ( V , X ; Y | A, U ) − n ( I ( U ; X | Z, A ) + ǫ ′′ ) (51) where ( a ) follo ws for some ǫ ′′ > 0 such that ǫ ′′ → 0 when n → ∞ . Case 3 : Sup pose we have R u + e R u < H ( U | Z, A, X ) (52) R v + e R v < H ( V | U , Z, A, X ) . (53 ) Then, W u , F u , and ( Z n , A n , X n ) are almost mutually inde- penden t, and W u and F u are almost un iformly d istributed by [24, Th eorem 1]. Similarly , W v , F v , and ( U, n Z n , A n , X n ) are almost mutually independen t, and W v and F v are almost unifor m ly distributed by [24, Theo r em 1 ] . W e ha ve − H ( U n | Z n , A n , W u , F u ) + H ( V n | W , A n , X n , Z n , F ) ( a ) ≤ − nH ( U | Z , A ) + H ( W u , F u | Z n , A n ) + nH ( V | A, X , Z ) − H ( W u , F u | A n , X n , Z n ) − H ( W v , F v | A n , X n , Z n , W u , F u ) + nH ( U | A, X , Z, V ) ( b ) ≤ − nH ( U | Z, A ) + H ( W u ) + H ( F u ) + nH ( U, V | A, X , Z ) − ( H ( W u | A n , X n , Z n ) + H ( F u | A n , X n , Z n ) − ǫ n ) − H ( F v | A n , X n , Z n , W u , F u ) − H ( W v | A n , X n , Z n , W u , F u , F v ) ( c ) ≤ − nH ( U | Z, A ) + H ( W u ) + H ( F u ) + nH ( U, V | A, X , Z ) − ( H ( W u ) − ǫ n ) − ( H ( F u ) − ǫ n ) + ǫ n − ( H ( F v ) − ǫ n ) − H ( W v | A n , X n , Z n , U n , F v ) = − nH ( U | Z , A ) + nH ( U , V | A, X , Z ) + 4 ǫ n − H ( F v ) − H ( V n | A n , X n , Z n , U n , F v ) + H ( V n | A n , X n , Z n , U n ) − I ( V n ; W v , F v | A n , X n , Z n , U n ) ( d ) ≤ − nH ( U | Z , A ) + nH ( U, V | A, X , Z ) + 4 ǫ n − H ( F v ) − H ( V n | A n , X n , Z n , U n ) + H ( F v ) + H ( V n | A n , X n , Z n , U n ) − ( H ( W v | A n , X n , Z n , U n ) + H ( F v | A n , X n , Z n , U n ) − ǫ n ) ( e ) ≤ − nH ( U | Z , A ) + nH ( U, V | A, X , Z ) + 4 ǫ n − ( nR v − 2 ǫ n ) − ( n e R v − 2 ǫ n ) + ǫ n ( f ) ≤ − nI ( U ; X | Z, A ) + 9 ǫ n + n ( I ( V ; Y | A, U ) − I ( V ; X , Z | A, U )) (54) where ( a ) follows be c ause U n determines ( F u , W u ) , A n determines ( F a , W a ) , and V n determines ( F v , W v ) , ( b ) follows by (47) such that W u and F u are almost inde penden t gi ven ( A n , X n , Z n ) , ( c ) follows by (4 7) such th at W u and F u are almost inde p endent of ( A n , X n , Z n ) and by (31) such that F v is almost indep endent of ( A n , X n , Z n , U n ) and U n determines W u and F u , ( d ) follows by (53) and since V n de- termines ( W v , F v ) , ( e ) follows beca use W v and F v are almost indepen d ent of ( A n , X n , Z n , U n ) and ar e almost unifo rmly distributed, and ( f ) follows by ( 36) and (37). Combining (40) and ( 54), we obta in for Case 3 I ( X n ; W, Z n , F ) ( a ) ≤ n I ( X ; Z | A, U ) + I ( X ; A, V , Y ) − I ( X ; Y | A, U ) + n I ( V ; Z | A, X , U ) − I ( V ; Y | A, X , U ) + ǫ ′′ ) + n ( − I ( U ; X | Z, A ) + I ( V ; Y | A, U ) − I ( V ; X , Z | A, U )) = n I ( V , X ; Z | A, U ) + I ( X ; A, V , Y ) − I ( V , X ; Y | A, U ) + n ( − I ( U ; X | Z, A ) + I ( V ; Y | A, U ) − I ( V ; X , Z | A, U ) + ǫ ′′ ) ( b ) = n ( I ( V ; Z | A, U ) + I ( X ; Z | A, V ) + I ( X ; A, V , Y )) + n ( − I ( X ; Y | A, V ) − I ( U ; X | Z, A ) − I ( V ; Z | A, U )) − nI ( V ; X | A, U, Z ) + nǫ ′′ ( c ) = nI ( X ; A, V , Z ) − nI ( V ; X | Z, A ) + n ǫ ′′ = nI ( X ; A, Z ) + nǫ ′′ (55) where ( a ) follows for some ǫ ′′ > 0 such that ǫ ′′ → 0 when n → ∞ , ( b ) follows from the Markov chain U − V − ( A, X , Y , Z ) , an d ( c ) follows from the Markov chain U − V − ( X , A, Z ) . Case 4 : Sup pose we have R u + e R u ≥ H ( U | Z , A, X ) (56) R u + e R u < H ( U | Z , A ) (57) R v + e R v ≥ H ( V | U, Z, A, X ) (58) R v + e R v < H ( V | Z, A, X ) . (59) Then, W u , F u , and ( Z n , A n ) are almost mutually in depend ent, and W u and F u are almost un if ormly distributed b y [24, Theo - rem 1] and we can recover U n from ( F u , W u , Z n , A n , X n ) by using a SW deco der [ 24, Lemma 1] . Mor eover , we can rec over V n from ( F v , W v , U n , Z n , A n , X n ) by using a SW decod er [24, Lem ma 1], but F v , W v , and ( Z n , A n , X n ) ar e almost indepen d ent, and F v and W v are almo st unifo rmly distributed by [24, Theo rem 1 ]. W e obtain − H ( U n | Z n , A n , W u , F u ) + H ( V n | W , A n , X n , Z n , F ) ( a ) ≤ − H ( U n | Z n , A n ) + H ( W u , F u | Z n , A n ) + H ( V n | W v , U n , A n , X n , Z n , F v ) + H ( U n | W u , F u , A n , X n , Z n ) ( b ) ≤ − H ( U n | Z n , A n ) + H ( W u ) + H ( F u ) + 2 n ǫ ′ n ( c ) ≤ n ( − H ( U | Z, A ) + H ( U | Y , A ) + ǫ + 2 ǫ ′ n ) (60) where ( a ) follo ws because U n determines ( F u , W u ) an d A n determines ( F a , W a ) , ( b ) fo llows by (56) and (5 8) fo r so me ǫ ′ n > 0 such that ǫ ′ n → 0 when n → ∞ , and ( c ) follows b y (34) and (35). Combining (40) and ( 60), we obta in f or Case 4 I ( X n ; W, Z n , F ) ( a ) ≤ n I ( X ; Z | A, U ) + I ( X ; A, V , Y ) − I ( X ; Y | A, U ) + n I ( V ; Z | A, X , U ) − I ( V ; Y | A, X , U ) + n ( I ( U ; Z | A ) − I ( U ; Y | A ) + ǫ ′′ ) ( b ) = n I ( V , X ; Z | A ) + I ( X ; A, V , Y ) − I ( V , X ; Y | A ) + nǫ ′′ (61) where ( a ) is for some ǫ ′′ > 0 such that ǫ ′′ → 0 when n → ∞ and ( b ) follows from the Markov ch a in U − V − ( A, X , Z, Y ) . Case 5 : Sup pose we have R u + e R u ≥ H ( U | Z, A, X ) (62) R u + e R u < H ( U | Z, A ) (63) R v + e R v < H ( V | U , Z, A, X ) . (64 ) Then, W u , F u , and ( Z n , A n ) are almost mutually indep e ndent, and W u and F u are almo st unifo rmly distributed by [24, Th e- orem 1] and we can re c over U n from ( F u , W u , Z n , A n , X n ) by using a SW decoder [24, Lemma 1]. Mo reover , W v , F v , and ( U n , Z n , A n , X n ) are almost mutually independent, and W v and F v are almost uniform ly d istributed [24, Theorem 1]. W e ha ve − H ( U n | Z n , A n , W u , F u ) + H ( V n | W , A n , X n , Z n , F ) ( a ) ≤ − H ( U n | Z n , A n ) + H ( W u , F u | Z n , A n ) + nH ( V | A, X , Z ) − H ( W u , F u | A n , X n , Z n ) − H ( W v , F v | A n , X n , Z n , W u , F u ) + nH ( U | A, X , Z , V ) ( b ) ≤ − H ( U n | Z n , A n ) + H ( W u ) + H ( F u ) + nH ( U, V | A, X , Z ) − H ( U n | A n , X n , Z n ) + nǫ ′ n − H ( F v | A n , X n , Z n , W u , F u ) − H ( W v | A n , X n , Z n , W u , F u , F v ) ( c ) ≤ n ( − H ( U | Z, A ) + H ( U | Y , A ) + ǫ ) + nH ( V | U, A, X , Z ) + nǫ ′ n − ( H ( F v ) − ǫ n ) − H ( V n | A n , X n , Z n , U n , F v ) + H ( V n | A n , X n , Z n , U n ) − I ( V n ; W v , F v | A n , X n , Z n , U n ) ( d ) ≤ n ( − H ( U | Z , A ) + H ( U | Y , A ) + ǫ ) + nH ( V | U, A, X , Z ) + nǫ ′ n − H ( F v ) + ǫ n − H ( V n | A n , X n , Z n , U n ) + H ( F v ) + H ( V n | A n , X n , Z n , U n ) − ( H ( W v | A n , X n , Z n , U n ) + H ( F v | A n , X n , Z n , U n ) − ǫ n ) ( e ) ≤ n ( − H ( U | Z, A ) + H ( U | Y , A ) + ǫ ) + nH ( V | U, A, X , Z ) + nǫ ′ n + 2 ǫ n − ( nR v − 2 ǫ n ) − ( n e R v − 2 ǫ n ) ( f ) = n ( I ( U ; Z | A ) − I ( U ; Y | A ) + ǫ ) + 6 ǫ n + n ( I ( V ; Y | A, U ) − I ( V ; X , Z | A, U ) + ǫ ′ n + ǫ ) (65) where ( a ) follows becau se U n determines ( W u , F u ) , ( b ) fol- lows by (62) for some ǫ ′ n → 0 when n → ∞ , ( c ) f ollows by (34), (35), and (31), and b e c ause W u and F u are de te r mined by U n , ( d ) follows because V n determines ( F v , W v ) , and W v and F v are almost ind ependen t given ( A n , X n , Z n , U n ) by (64), ( e ) f ollows because W v and F v are almost indepen dent o f ( A n , X n , Z n , U n ) an d almost unifo rmly distrib uted by (64), and ( f ) follo ws b y (36) and (3 7). Combining (40) and ( 65), we obta in for Case 5 I ( X n ; W, Z n , F ) ≤ n I ( X ; Z | A, U ) + I ( X ; A, V , Y ) − I ( X ; Y | A, U ) + n I ( V ; Z | A, X , U ) − I ( V ; Y | A, X , U ) + n ( I ( V ; Y | A, U ) − I ( V ; X , Z | A, U ) + ǫ ′′ ) + nI ( U ; Z | A ) − nI ( U ; Y | A ) ( a ) = n I ( X , V ; Z | A, U ) + I ( X ; A, V , Y ) − I ( X ; Y | A, V ) − nI ( V ; Z | A, U ) − nI ( V ; X | A, U, Z ) + n ǫ ′′ + nI ( U ; Z | A ) − nI ( U ; Y | A ) ( b ) = n I ( X ; Z | A, V ) + I ( X ; A, V , Y ) − I ( X ; Y | A, V ) − nI ( V ; X | A, U, Z ) + nǫ ′′ + nI ( U ; Z | A ) − nI ( U ; Y | A ) ( c ) = n I ( X ; A, U, Z ) + I ( U ; Z | A ) − I ( U ; Y | A ) + ǫ ′′ ) (66) where ( a ) f ollows fro m the Markov chain U − V − ( X , Y , A ) and for some ǫ ′′ > 0 such that ǫ ′′ → 0 wh en n → ∞ , and ( b ) and ( c ) follow from the Markov chain U − V − ( X , Z , A ) . Case 6 : Sup pose we have R u + e R u ≥ H ( U | Z , A, X ) (67) R u + e R u < H ( U | Z , A ) (68 ) R v + e R v ≥ H ( V | Z, A, X ) . (69) Then, we ca n recover U n from ( F u , W u , Z n , A n , X n ) b y u sing a SW de c oder [24, Lemma 1], but F u , W u , and ( Z n , A n ) are almo st indep endent, and F u and W u are almo st unifo rmly distributed b y [24, T h eorem 1]. Mo reover , we can r ecover V n from ( F v , W v , Z n , A n , X n ) by u sing a SW decoder [24 , Lemma 1]. W e obtain − H ( U n | Z n , A n , W u , F u ) + H ( V n | W , A n , X n , Z n , F ) ( a ) ≤ − H ( U n | Z n , A n ) + H ( W u , F u | Z n , A n ) + H ( V n | W v , A n , X n , Z n , F v ) ( b ) ≤ − H ( U n | Z n , A n ) + H ( W u ) + H ( F u ) + nǫ ′ n ( c ) ≤ n ( − H ( U | Z, A ) + H ( U | Y , A ) + ǫ + ǫ ′ n ) (70) where ( a ) follows becau se U n determines ( F u , W u ) , ( b ) fol- lows by ( 69) for som e ǫ ′ n > 0 such that ǫ ′ n → 0 when n → ∞ , and ( c ) follows b y (34) an d (35). Combining (40) and ( 70), we obta in f or Case 6 I ( X n ; W, Z n , F ) ( a ) ≤ n I ( X ; Z | A, U ) + I ( X ; A, V , Y ) − I ( X ; Y | A, U ) + n I ( V ; Z | A, X , U ) − I ( V ; Y | A, X , U ) + n ( I ( U ; Z | A ) − I ( U ; Y | A ) + ǫ ′′ ) ( b ) = n I ( V , X ; Z | A ) + I ( X ; A, V , Y ) − I ( V , X ; Y | A ) + nǫ ′′ (71) where ( a ) follo ws for some ǫ ′′ > 0 such that ǫ ′′ → 0 when n → ∞ a n d ( b ) fo llows f rom the Ma r kov chain U − V − ( A, X , Z , Y ) . Case 7 : Sup pose we have R u + e R u ≥ H ( U | Z , A ) (72) R v + e R v ≥ H ( V | U, Z, A, X ) (73) R v + e R v < H ( V | Z, A, X ) . (74) Then, we can recover U n from ( F u , W u , Z n , A n ) b y using a SW deco der [2 4, Lemma 1]. Moreover, we can recover V n from ( F v , W v , U n , Z n , A n , X n ) by using a SW decod er [24, Lem ma 1], but F v , W v , and ( Z n , A n , X n ) ar e almost indepen d ent, and F v and W v are almost uniform ly distributed by [24, Th eorem 1 ]. W e obtain − H ( U n | Z n , A n , W u , F u ) + H ( V n | W , A n , X n , Z n , F ) ( a ) ≤ H ( V n | W v , U n , A n , X n , Z n , F v ) + H ( U n | W u , F u , A n , Z n ) ( b ) ≤ 2 nǫ ′ n (75) where ( a ) follows becau se U n determines ( F u , W u ) and ( b ) follows by (72) and (73) for som e ǫ ′ n > 0 such that ǫ ′ n → 0 when n → ∞ . Combining (40) and ( 75), we obta in f or Case 7 I ( X n ; W, Z n , F ) ≤ n I ( X ; Z | A, U ) + I ( X ; A, V , Y ) − I ( X ; Y | A, U ) + n I ( V ; Z | A, X , U ) − I ( V ; Y | A, X , U ) + ǫ ′′ ≤ n I ( V , X ; Z | A, U ) + I ( X ; A, V , Y ) − nI ( V , X ; Y | A, U ) + nǫ ′′ (76) for some ǫ ′′ > 0 su ch that ǫ ′′ → 0 when n → ∞ . Case 8 : Sup pose we have R u + e R u ≥ H ( U | Z , A ) (77 ) R v + e R v ≥ H ( V | Z, A, X ) . (78) Then, we can recover U n from ( F u , W u , Z n , A n ) and V n from ( F v , W v , Z n , A n , X n ) by using a SW d ecoder [24, Lemm a 1]. W e obtain − H ( U n | Z n , A n , W u , F u ) + H ( V n | W , A n , X n , Z n , F ) ≤ H ( V n | W v , A n , X n , Z n , F v ) ( a ) ≤ nǫ ′ n (79) where ( a ) follows by ( 78) for some ǫ ′ n > 0 such that ǫ ′ n → 0 when n → ∞ . Combining (40) and ( 79), we obta in for Case 8 I ( X n ; W, Z n , F ) ≤ n I ( X ; Z | A, U ) + I ( X ; A, V , Y ) − I ( X ; Y | A, U ) + n I ( V ; Z | A, X , U ) − I ( V ; Y | A, X , U ) + ǫ ′′ ≤ n I ( V , X ; Z | A, U ) + I ( X ; A, V , Y ) − nI ( V , X ; Y | A, U ) + nǫ ′′ (80) for some ǫ ′′ > 0 such that ǫ ′′ → 0 wh e n n → ∞ . Case 9 : Sup pose we have R u + e R u ≥ H ( U | Z, A ) (81) R v + e R v < H ( V | U , Z, A, X ) . (82 ) Then, we can recover U n from ( F u , W u , Z n , A n ) b y using a SW decod er [24, Lemma 1]. Moreover, F v , W v , and ( U n , Z n , A n , X n ) are almo st ind ependen t, an d F v and W v are almost unifor mly distributed by [24, T heorem 1 ]. W e obtain − H ( U n | Z n , A n , W u , F u ) + H ( V n | W , A n , X n , Z n , F ) ( a ) ≤ nH ( V | A, X , Z ) − H ( W u , F u | A n , X n , Z n ) − H ( W v , F v | A n , X n , Z n , W u , F u ) + nH ( U | A, X , Z , V ) ( b ) ≤ nH ( U, V | A, X , Z ) − H ( U n | A n , X n , Z n ) + nǫ ′ n − H ( F v | A n , X n , Z n , W u , F u ) − H ( W v | A n , X n , Z n , W u , F u , F v ) ( c ) ≤ nH ( V | U, A, X , Z ) + nǫ ′ n − ( H ( F v ) − ǫ n ) − H ( V n | A n , X n , Z n , U n , F v ) + H ( V n | A n , X n , Z n , U n ) − I ( V n ; W v , F v | A n , X n , Z n , U n ) ( d ) ≤ nH ( V | U, A, X , Z ) + nǫ ′ n − H ( F v ) + ǫ n − H ( V n | A n , X n , Z n , U n ) + H ( F v ) + H ( V n | A n , X n , Z n , U n ) − ( H ( W v | A n , X n , Z n , U n ) + H ( F v | A n , X n , Z n , U n ) − ǫ n ) ( e ) ≤ nH ( V | U, A, X , Z ) + nǫ ′ n + 2 ǫ n − ( nR v − 2 ǫ n ) − ( n e R v − 2 ǫ n ) ( f ) = n ( I ( V ; Y | A, U ) − I ( V ; X , Z | A, U ) + ǫ ′ n + ǫ ) + 6 ǫ n (83) where ( a ) follows becau se U n determines ( W u , F u ) , ( b ) fol- lows b y (81) for some ǫ ′ n → 0 whe n n → ∞ , ( c ) follows by (31) and beca u se W u and F u are d etermined by U n , ( d ) follows because V n determines ( F v , W v ) , and W v and F v are almost ind ependen t given ( A n , X n , Z n , U n ) by (82), ( e ) f ollows because W v and F v are almost indepen dent o f ( A n , X n , Z n , U n ) an d almost unifo rmly distrib uted by (82), and ( f ) follo ws b y (36) and (3 7). Combining (40) and ( 83), we obta in f or Case 9 I ( X n ; W, Z n , F ) ( a ) ≤ n I ( X ; Z | A, U ) + I ( X ; A, V , Y ) − I ( X ; Y | A, U ) + n I ( V ; Z | A, X , U ) − I ( V ; Y | A, X , U ) + ǫ ′′ + n ( I ( V ; Y | A, U ) − I ( V ; X , Z | A, U )) ( b ) = n ( I ( V ; Z | A, U ) + I ( X ; Z | A, V ) + I ( X ; A, V , Y )) − nI ( V ; Y | A, U ) − nI ( X ; Y | A, V ) + nI ( V ; Y | A, U ) − nI ( V ; Z | A, U ) − nI ( V ; X | A, U, Z ) + nǫ ′′ ( c ) = nI ( X ; A, U, Z ) + nǫ ′′ (84) where ( a ) follo ws for some ǫ ′′ > 0 such that ǫ ′′ → 0 when n → ∞ a n d ( b ) fo llows f rom the Ma r kov chain U − V − ( A, X , Z , Y ) . Combining all cases a n d applying the selection lemm a [32, Lemma 2.2] , ther e exists a binnin g that ach ieves all rate tu ples ( R s , R ℓ , R w , C ) in the inner boun d g iven in Theo rem 1 fo r the key-leakage-storag e-cost region R gs for the GS model with strong secrecy when n → ∞ . B. Pr oof for the CS Model W e use the achiev ab ility pro of for the GS model. Su ppose the key S ′ , g enerated in the GS model tog ether with the helper data W ′ = ( W ′ a , W ′ u , W ′ v ) an d public indices F ′ = ( F ′ a , F ′ u , F ′ v ) , ha ve the same cardin ality a s an emb edded secret key S , i.e., |S ′ | = |S | , so th at we achiev e the same secret-key rate R s as in the GS model. The encode r f 2 ( · , · ) has inputs ( e X n , S ) and outputs W = ( S ′ + S, W ′ ) . The decoder g ( · , · ) has inpu ts ( W , Y n ) an d output ˆ S = S ′ + S − ˆ S ′ , wh ere all addition and su b traction opera tions are mod ulo- |S | . W e use the deco der of the GS mo del to ob tain ˆ S ′ . W e ha ve th e er ror probab ility Pr[ S 6 = ˆ S ] = Pr[ S ′ 6 = ˆ S ′ ] (85) which is small due to the achiev ability p roof for the GS mod e l. Using the one-tim e p adding o peration ap plied ab ove, (38), and (39), we can achieve a storag e r a te of R w ≥ I ( e X ; A, V ) − I ( U ; Y | A ) − I ( V ; Z | A, U ) + 4 ǫ (86) for the CS m odel. Similar to the GS mo del, one can sho w that th e expected cost constraint is satisfied with h igh p r obability by using the typical average lemma. W e ha ve th e secr e cy leaka g e of I ( S ; W , Z n , F ) ( a ) = I ( S ; W, Z n | F ′ ) = I ( S ; W ′ , Z n | F ′ ) + I ( S ; S ′ + S, Z n | W ′ , F ′ ) ( b ) = H ( S ′ + S, Z n | W ′ , F ′ ) − H ( S ′ , Z n | W ′ , F ′ ) = H ( S ′ + S | Z n , W ′ , F ′ ) + H ( Z n | W ′ , F ′ ) − H ( S ′ | W ′ , F ′ ) − H ( Z n | W ′ , F ′ , S ′ ) ( c ) ≤ nR s − H ( S ′ | W ′ , F ′ ) + I ( S ′ ; W ′ , Z n | F ′ ) ( d ) ≤ nR s − ( nR s − 2 ǫ n ) + I ( S ′ ; W ′ , Z n | F ′ ) ( e ) ≤ 3 ǫ n (87) where ( a ) follows beca u se F = F ′ and S is ind ependen t of F ′ ; ( b ) follows be c a use S is in depend ent of ( W ′ , F ′ , Z n , S ′ ) ; ( c ) follows beca u se |S ′ | = |S | ; ( d ) follows by ( 28) since ( S ′ , F v , W v ) are a lmost mutu- ally ind ependen t, un if ormly distributed, and indepen dent o f ( U n , A n , Z n ) so th at S ′ is almo st independ ent of ( F ′ , W ′ ) and unifo rmly distributed; ( e ) follows because the GS mod el satisfies the strong secrecy constraint (2) by ( 28) for some ǫ n > 0 suc h that ǫ n → 0 when n → ∞ . W e o btain the p riv acy-leakage of I ( X n ; W, Z n , F ) ( a ) ≤ I ( X n ; W, Z n | F ′ ) + 3 ǫ n ≤ I ( X n ; W ′ , Z n | F ′ ) + H ( S + S ′ | Z n , W ′ , F ′ ) − H ( S + S ′ | Z n , X n , W ′ , F ′ , S ′ ) + 3 ǫ n ( b ) ≤ I ( X n ; W ′ , Z n | F ′ ) + log ( |S | ) − H ( S ) + 3 ǫ n ( c ) = I ( X n ; W ′ , Z n | F ′ ) + 3 ǫ n (88) where ( a ) fo llows by (41), ( b ) follows becau se S is indepen - dent o f ( X n , Z n , W ′ , S ′ , F ′ ) and |S ′ | = |S | , and ( c ) follo ws from the u niform ity of S . W e theref o re hav e the f ollowing results for nine dif ferent cases. Case 1 : Suppo se (43) an d (44). By com bining ( 46) an d (88), we obtain I ( X n ; W, Z n , F ) ≤ n I ( V , X ; Z | A ) + I ( X ; A, V , Y ) − I ( V , X ; Y | A ) + nǫ (3) (89) for some ǫ (3) > 0 such that ǫ (3) → 0 when n → ∞ . Case 2 : Suppose (47)-( 49). By comb in ing (51) and (88), we have I ( X n ; W, Z n , F ) ≤ n I ( V , X ; Z | A, U ) + I ( X ; A, V , Y ) − I ( V , X ; Y | A, U ) − nI ( U ; X | Z, A ) + nǫ (3) (90) for some ǫ (3) > 0 such that ǫ (3) → 0 when n → ∞ . Case 3 : Suppose (52) an d (53). Com bining (55) an d (88), we have I ( X n ; W, Z n , F ) ≤ n ( I ( X ; A, Z ) + ǫ (3) ) (91) for some ǫ (3) > 0 such that ǫ (3) → 0 when n → ∞ . Case 4 : Suppose ( 56)-(59). Combining (61) and (88), we obtain I ( X n ; W, Z n , F ) ≤ n I ( V , X ; Z | A ) + I ( X ; A, V , Y ) − I ( V , X ; Y | A ) + nǫ (3) (92) for some ǫ (3) > 0 such that ǫ (3) → 0 when n → ∞ . Case 5 : Suppose ( 62)-(64). By comb in ing (66) and (88), we have I ( X n ; W, Z n , F ) ≤ n I ( X ; A, U, Z ) + I ( U ; Z | A ) − I ( U ; Y | A ) + ǫ (3) (93) for some ǫ (3) > 0 such that ǫ (3) → 0 wh e n n → ∞ . Case 6 : Suppose ( 67)-(69). By comb in ing (71) and (88), we obtain I ( X n ; W, Z n , F ) ≤ n I ( V , X ; Z | A ) + I ( X ; A, V , Y ) − I ( V , X ; Y | A ) + nǫ (3) (94) for some ǫ (3) > 0 such that ǫ (3) → 0 wh e n n → ∞ . Case 7 : Suppose ( 72)-(74). Combining (76) and (88 ), we obtain I ( X n ; W, Z n , F ) ≤ n I ( V , X ; Z | A, U ) + I ( X ; A, V , Y ) − I ( V , X ; Y | A, U ) + nǫ (3) (95) for some ǫ (3) > 0 such that ǫ (3) → 0 wh e n n → ∞ . Case 8 : Suppose (77) and (7 8). Com bining (80) an d (88), we obtain I ( X n ; W, Z n , F ) ≤ n I ( V , X ; Z | A, U ) + I ( X ; A, V , Y ) − I ( V , X ; Y | A, U ) + nǫ (3) (96) for some ǫ (3) > 0 such that ǫ (3) → 0 wh e n n → ∞ . Case 9 : Sup pose (81) and (82). By com bining ( 84) and (88), we obtain I ( X n ; W, Z n , F ) ≤ nI ( X ; A, U, Z ) + nǫ (3) (97) for some ǫ (3) > 0 such that ǫ (3) → 0 wh e n n → ∞ . Using the selection lem ma, there exists a b inning that achieves all rate tup les ( R s , R ℓ , R w , C ) in the inner boun d giv en in The o rem 1 fo r the key-leaka g e-storage- cost region R cs for the CS m odel with strong secr ecy wh en n → ∞ . V I I . O U T E R B O U N D S F O R C L N C H A N N E L S W e use the f o llowing lemma, which is an extension of [3 3, Lemma 1] proved f or less-no isy BCs, to bound the pri vac y- leakage rate fo r CLN channels. Lemma 1. For a C LN chan nel ( X ≥ Z | A, Y ) , we ha ve I ( X i ; X i − 1 | W , S , A n , Y n ) ≥ I ( X i ; Z i − 1 | W , S , A n , Y n ) , (98) I ( Z i ; X i − 1 | W , S , A n , Y n ) ≥ I ( Z i ; Z i − 1 | W , S , A n , Y n ) (99) for i = 1 , 2 , . . . , n if ( S, W ) − ( e X n , Y n , A n ) − ( X n , Z n ) form a Markov ch ain. Pr oo f: Consider f o r any 1 ≤ j ≤ i − 1 and i = 1 , 2 , . . . , n I ( Z j − 1 , X i − 1 j ; X i | W , S , A n , Y n ) = I ( Z j − 1 , X i − 1 j +1 ; X i | W , S , A n , Y n ) + I ( X j ; X i | W , S , A n , Y n , Z j − 1 , X i − 1 j +1 ) ( a ) ≥ I ( Z j − 1 , X i − 1 j +1 ; X i | W , S , A n , Y n ) + I ( Z j ; X i | W , S , A n , Y n , Z j − 1 , X i − 1 j +1 ) = I ( Z j , X i − 1 j +1 ; X i | W , S , A n , Y n ) (100) where X i − 1 i and Z 0 are co nsidered to b e constant an d ( a ) follows from the inequality I ( X i ; X j | Y j , A j , W, S, Z j − 1 , X i − 1 j +1 , Y n \ j , A n \ j ) ( a. 1) ≥ I ( X i ; Z j | Y j , A j , W, S, Z j − 1 , X i − 1 j +1 , Y n \ j , A n \ j ) (10 1) where Y n \ j is the set of rand o m variables { Y 1 , Y 2 , . . . , Y j − 1 , Y j +1 , . . . , Y n } and ( a. 1) follows for a CLN chan nel such that ( X ≥ Z | A, Y ) by ( 12) an d since ( W , S, Z j − 1 , X i − 1 j +1 , Y n \ j , A n \ j , X i ) − ( A j , e X j , Y j ) − ( X j , Z j ) form a Markov ch ain. Apply (100) repetitively for j = 1 , 2 , . . . , i − 1 such that I ( X i − 1 ; X i | W , S , A n , Y n ) ≥ I ( Z 1 , X i − 1 2 ; X i | W , S , A n , Y n ) ≥ I ( Z 2 , X i − 1 3 ; X i | W , S , A n , Y n ) ≥ . . . ≥ I ( Z i − 1 ; X i | W , S , A n , Y n ) (102) which is the pro of for (98). Th e p roof of (99) follows by replacing X i with Z i in (100), (101), and (1 02) sin c e ( W , S, Z j − 1 , X i − 1 j +1 , Y n \ j , A n \ j , Z i ) − ( A j , e X j , Y j ) − ( X j , Z j ) also form a Ma rkov chain. A. Pr oofs of Outer Bo unds Suppose fo r som e δ n > 0 and n ≥ 1 , there is a p air of encoder s and decoders such that (1)-(6) ar e satisfied for all CLN ch annels such that ( X ≥ Z | A, Y ) and ( Z ≥ Y | A, X ) by some key-leakage - storage-co st tuple ( R s , R ℓ , R w , C ) . If ( X ≥ Z | A, Y ) and ( Z ≥ Y | A, X ) , we also have ( X ≥ Y | A, Z ) . Using (1) and Fano’ s ineq uality , we obtain H ( S | W, Y n ) ( a ) ≤ H ( S | ˆ S ) ≤ nǫ n (103) where ( a ) p ermits random ized decod ing, ǫ n = δ n R s + H b ( δ n ) /n , where H b ( δ ) = − δ log δ − (1 − δ ) log (1 − δ ) is the binary en tropy func tio n, an d ǫ n → 0 if δ n → 0 . Let U i , ( W, A n \ i , Y n i +1 , Z i − 1 ) and V i , ( S, W, A n \ i , Y n i +1 , Z i − 1 ) , which satisfy the Markov chain U i − V i − ( A i , e X i ) − ( A i , e X i , X i ) − ( Y i , Z i ) for all i = 1 , 2 , . . . , n . Secr et-ke y Rate : W e obtain fo r the GS an d CS models n ( R s − δ n ) ( a ) ≤ H ( S ) ( b ) ≤ H ( S | W , Z n ) + δ n ( c ) = H ( S | W , A n , Z n ) + δ n ( d ) ≤ H ( S | W , A n , Z n ) − H ( S | W , A n , Y n ) + nǫ n + δ n = n X i =1 I ( S ; Y i | W , A n , Y n i +1 ) − I ( S ; Z i | W , A n , Z i − 1 ) + nǫ n + δ n ( e ) = n X i =1 h I ( S ; Y i | W , A n , Y n i +1 , Z i − 1 ) − I ( S ; Z i | W , A n , Y n i +1 , Z i − 1 ) i + nǫ n + δ n ( f ) = n X i =1 I ( V i ; Y i | A i , U i ) − I ( V i ; Z i | A i , U i ) + ǫ n + δ n (104) where ( a ) follows b y (3), ( b ) follows b y (2), ( c ) follows from the determ inistic a ction enco der, ( d ) follows by ( 103), ( e ) follows fro m Csisz ´ ar ’ s sum identity [3 4], and ( f ) fo llows from the defin itio ns of U i and V i . Storage Rate : W e o btain for the GS model n ( R w + δ n ) ( a ) ≥ log |W | ≥ H ( W ) ( b ) = H ( A n ) + H ( W | A n ) ≥ [ H ( A n ) − H ( A n | e X n , Z n )] + [ H ( W | A n , Y n ) − H ( W | A n , e X n , Y n , Z n )] = H ( e X n , Z n ) − H ( e X n , Z n | A n ) + H ( e X n , Z n | A n , Y n ) − H ( e X n , Z n | A n , Y n , W ) = H ( e X n ) + H ( Z n | e X n ) − H ( Y n | A n ) + H ( Y n , Z n | e X n , A n ) − H ( Z n | e X n , A n ) − H ( e X n , Z n | A n , Y n , W, S ) − I ( e X n , Z n ; S | A n , Y n , W ) ≥ H ( e X n ) − H ( Y n | A n ) + H ( Y n , Z n | e X n , A n ) − H ( e X n , Z n | A n , Y n , W, S ) − H ( S | A n , Y n , W ) ( c ) ≥ n X i =1 h H ( e X i ) − H ( Y i | A i ) + H ( Y i , Z i | e X i , A i ) − H ( e X i , Z i | A n , Y n , W, S, e X i − 1 , Z i − 1 ) i − nǫ n ( d ) ≥ n X i =1 h H ( e X i ) − H ( Y i | A i ) + H ( Y i | e X i , A i , Z i ) + H ( Z i | e X i , A i ) − H ( e X i , Z i | A i , Y i , V i ) i − nǫ n ≥ n X i =1 h I ( e X i ; A i ) + I ( V i ; e X i | A i , Y i ) − ǫ n i (105) where ( a ) follows b y (5), ( b ) follows from the determ inistic action en coder, ( c ) follows by (1 03), and ( d ) follows fr om the definition of V i . W e o btain for the CS model n ( R w + δ n ) ( a ) ≥ log |W | ≥ H ( W ) ( b ) = H ( A n ) + H ( W | A n ) ( c ) ≥ H ( A n ) − H ( A n | e X n , Z n ) + H ( A n | e X n , Z n ) + H ( W | A n , Y n ) − H ( W | A n , e X n , Y n , Z n ) + H ( W | A n , e X n ) = H ( e X n , Z n ) − H ( e X n , Z n | A n ) + H ( A n | e X n , Z n ) + H ( e X n , Z n | A n , Y n ) − H ( e X n , Z n | A n , Y n , W ) + H ( W | A n , e X n ) = H ( e X n ) + H ( Z n | e X n ) − H ( Y n | A n ) + H ( Y n , Z n | e X n , A n ) − H ( Z n | e X n , A n ) + H ( A n | e X n , Z n ) − H ( e X n , Z n | A n , Y n , W, S ) − I ( e X n , Z n ; S | A n , Y n , W ) + H ( W | A n , e X n ) = H ( e X n ) + I ( Z n ; A n | e X n ) − H ( Y n | A n ) + H ( Y n , Z n | e X n , A n ) + H ( A n | e X n , Z n ) − H ( e X n , Z n | A n , Y n , W, S ) − H ( S | A n , Y n , W ) + H ( S | A n , Y n , W, e X n , Z n ) + H ( W | A n , e X n ) ( d ) = H ( e X n ) + H ( W, A n , S | e X n ) − H ( Y n | A n ) + H ( Y n , Z n | e X n , A n ) − H ( e X n , Z n | A n , Y n , W, S ) − H ( S | A n , Y n , W ) ( e ) ≥ H ( e X n ) + H ( S ) − H ( Y n | A n ) + H ( Y n , Z n | e X n , A n ) − H ( e X n , Z n | A n , Y n , W, S ) − H ( S | A n , Y n , W ) ≥ H ( e X n ) − H ( Y n | A n ) + H ( Y n , Z n | e X n , A n ) − H ( e X n , Z n | A n , Y n , W, S ) + H ( S | A n , Z n , W ) − H ( S | A n , Y n , W ) ( f ) = n X i =1 h H ( e X i ) − H ( Y i | A i ) + H ( Y i , Z i | e X i , A i ) − H ( e X i , Z i | A n , Y n , W, S, e X i − 1 , Z i − 1 ) + I ( S ; Y i | W , A n , Y n i +1 ) − I ( S ; Z i | W , A n , Z i − 1 ) i ( g ) = n X i =1 h H ( e X i ) − H ( Y i | A i ) + H ( Y i , Z i | e X i , A i ) − H ( e X i , Z i | A n , Y n , W, S, e X i − 1 , Z i − 1 ) + I ( S ; Y i | W , A n , Y n i +1 , Z i − 1 ) − I ( S ; Z i | W , A n , Y n i +1 , Z i − 1 ) i ( h ) ≥ n X i =1 h H ( e X i ) − H ( Y i | A i ) + H ( Y i | e X i , A i , Z i ) + H ( Z i | e X i , A i ) − H ( e X i , Z i | A i , Y i , V i ) + I ( V i ; Y i | A i , U i ) − I ( V i ; Z i | A i , U i ) i ≥ n X i =1 h I ( e X i ; A i ) + I ( V i ; e X i | Y i , A i ) + I ( V i ; Y i | A i , U i ) − I ( V i ; Z i | A i , U i ) i ( i ) = n X i =1 h I ( e X i ; A i , V i ) − I ( U i ; Y i | A i ) − I ( V i ; Z i | A i , U i ) i (106) where ( a ) follows by (5), ( b ) fo llows fr om the deter min- istic action e ncoder, ( c ) fo llows from the Markov chain W − ( A n , e X n ) − ( Y n , Z n ) , ( d ) follows from the Markov chain S − ( A n , e X n , W ) − ( Y n , Z n ) , ( e ) fo llows becau se th e embedd e d key S is inde penden t o f e X n , ( f ) follows when Y n n +1 and Z 0 are co nsidered to be constant, ( g ) follows from Csisz ´ ar’ s sum identity . W e use the definitions of U i and V i in ( h ) , a n d ( i ) fo llows becau se U i − V i − ( A i , e X i ) − ( Y i , Z i ) form a Markov chain for all i = 1 , 2 , . . . , n . Privacy-leakage Rate : W e h av e for GS and CS models that n ( R ℓ + δ n ) ( a ) ≥ I ( X n ; W, A, Z n ) = H ( X n ) − H ( X n | W , S , A n , Y n ) − I ( X n ; S | W, A n , Y n ) − I ( X n ; Y n | W , A n ) + I ( X n ; Z n | W , A n ) ( b ) ≥ n X i =1 h H ( X i ) − H ( X i | W , S , A n , Y n , X i − 1 ) − ǫ n − H ( Y i | W , A n , Y n i +1 ) + H ( Y i | X i , A i ) + H ( Z i | W , A n , Z i − 1 ) − H ( Z i | X i , A i ) i − I ( Y n ; W | A n , X n ) + I ( Z n ; W | A n , X n ) ( c ) ≥ n X i =1 h H ( X i ) − H ( X i | W , S , A n , Y n , Z i − 1 ) − I ( X i ; Y i | A i ) + H ( Y i | A i ) + I ( X i ; Z i | A i ) − H ( Z i | A i ) − H ( Y i | W , A n , Y n i +1 ) + H ( Z i | W , A n , Z i − 1 ) − ǫ n i − I ( Y n ; W | A n , X n ) + I ( Z n ; W | A n , X n ) ( d ) ≥ n X i =1 h H ( X i ) − H ( X i | V i , A i , Y i ) − I ( X i ; Y i | A i ) + I ( W, Y n i +1 , A n \ i ; Y i | A i ) + I ( X i ; Z i | A i ) − I ( W, Z i − 1 , A n \ i ; Z i | A i ) − ǫ n i − I ( Y n ; W | A n , X n ) + I ( Z n ; W | A n , X n ) ( e ) = n X i =1 h I ( X i ; A i , V i , Y i ) − I ( X i ; Y i | A i ) + I ( X i ; Z i | A i ) − ǫ n + I ( W, Y n i +1 , Z i − 1 , A n \ i ; Y i | A i ) − I ( W, Z i − 1 , Y n i +1 , A n \ i ; Z i | A i ) i − I ( Y n ; W | A n , X n ) + I ( Z n ; W | A n , X n ) ( f ) = n X i =1 h I ( X i ; A i , V i , Y i ) − I ( X i ; Y i | A i ) + I ( X i ; Z i | A i ) − ǫ n + I ( U i ; Y i | A i ) − I ( U i ; Z i | A i ) i − I ( Y n ; W | A n , X n ) + I ( Z n ; W | A n , X n ) (107) where ( a ) follows by (4) an d from the d e terministic action encoder, ( b ) f o llows by (103), ( c ) follows by (98) for CLN channels ( X ≥ Z | A, Y ) , ( d ) follows f rom the definition of V i and th e deterministic actio n encoder, ( e ) follows from Csisz ´ ar’ s sum iden tity , and ( f ) fo llows fro m the defin ition of U i . Consider the extra terms − I ( Y n ; W | A n , X n ) + I ( Z n ; W | A n , X n ) = H ( W | A n , X n , Y n ) − H ( W | A n , X n , Z n ) (108) in (107). W e can not apply Csisz ´ ar ’ s sum iden tity to the term s in (10 8) due to the c ondition in g on X n , so one should find another method to have a single-letter expression fo r (108). W e use the following lemma to replace the term s in (10 8) with single- letter expression s and make f urther assumptio n s to bound the e xtra ter m . Lemma 2. Consider the model given in F ig. 1. Ther e e xists a random variable Ď W such that ( Ď W n , A n , e X n , X n , Y n , Z n ) ar e i.i.d ., Ď W − ( A, e X ) − ( A, e X , X ) − ( Y , Z ) form a Markov chain, a nd H ( W | A n , X n , Y n ) − H ( W | A n , X n , Z n ) = n H ( Ď W | A, X , Y ) − H ( Ď W | A, X , Z ) (109) when n → ∞ . Pr oo f Sketch: Consider the en coder f s ( · ) an d decod e r g s ( · ) of a lossless sou r ce c ode such that W = f s ( Ď W n ) and c Ď W n = g ( W ) , where c Ď W n is an estima te of Ď W n . Supp ose the lossless source co d e achiev es the optimal comp r ession rate of R = H ( Ď W ) = H ( W ) n when n → ∞ . W e th us o btain H ( W | Ď W n ) = H ( W ) − nH ( Ď W ) + H ( Ď W n | W ) = H ( Ď W n | W ) ( a ) ≤ H ( Ď W n | c Ď W n ) ( b ) ≤ nǫ n (110) where ( a ) fo llows from the data processing in e q uality applied to the Mar kov chain Ď W n − W − c Ď W n and ( b ) f ollows from Fano’ s inequality for some ǫ n > 0 such th at ǫ n → 0 when n → ∞ . Since c Ď W n − W − ( A n , e X n ) − ( A n , e X n , X n ) − ( Y n , Z n ) f o rm a Markov chain , the proof of L emma 2 follows b y (110). Suppose the joint pr o bability distribution P X e X AY Z satisfies also the condition to be a CLN channel ( Z ≥ Y | A, X ) . For the rando m variable Ď W defined in Lemma 2, w e th en have H ( Ď W | A, X , Y ) ≥ H ( Ď W | A, X , Z ) . (111) Thus, by com b ining (107), (108), (109), and (1 11) for a CLN channel ( Z ≥ Y | A, X ) , we obta in n ( R ℓ + δ n ) ≥ n X i =1 h I ( X i ; A i , V i , Y i ) − I ( X i ; Y i | A i ) + I ( X i ; Z i | A i ) − ǫ n + I ( U i ; Y i | A i ) − I ( U i ; Z i | A i ) i (112) when n → ∞ . Expected Action Cost : W e ha ve C + δ n ( a ) ≥ E Γ ( n ) ( A n ) = 1 n n X i =1 E Γ( A i ) (113) where ( a ) follows b y (6). Introd u ce a u niform ly distributed tim e -sharing rando m vari- able Q ∼ Unif [1 : n ] indep endent of other random v ariables. Define X = X Q , e X = e X Q , Y = Y Q , Z = Z Q , A = A Q , U = ( U Q ,Q ) , and V = ( V Q ,Q ) so that U − V − ( A, e X ) − ( A, e X , X ) − ( Y , Z ) f orm a Markov chain. The o u ter bo und fo r all CLN channe ls such th at ( X ≥ Z | A, Y ) and ( Z ≥ Y | A, X ) for th e GS mode l follows by u sing th e introd uced ran d om variables in (104), (105), (112), and (113), and letting δ n → 0 . Similarly , the ou ter boun d for the sam e class of ch a nnels for th e CS model f ollows by using the introd uced rand om variables in (104), (106), (112), and (113), and letting δ n → 0 . Car d inality B ounds : W e use the supp ort lemma [34, Lemma 15.4]. The bou nd in (1 6) can be written as the sum o f the bound s in (13) and (15). T herefor e, the same cardina lity bound s can be used f o r the ou ter boun ds of the GS and CS models. On e c an p reserve P A e X by using |A|| e X |− 1 real- valued continuo us fu n ctions. W e have to preserve fou r mor e expr es- sions, i.e., H ( V | A, U, Z ) − H ( V | A, U, Y ) , H ( X | U, V , A, Y ) , H ( e X | U, V , A, Y ) , and H ( Y | A, U ) − H ( Z | A, U ) . Thus, one can limit the cardinality |U | of U to |U | ≤ |A|| e X | + 3 . Similarly , in ad dition to the |A|| e X | − 1 real-valued con tin- uous f unctions, on e sh o uld p reserve three m o re expression s, i.e., H ( X | A, V , Y ) , H ( e X | A, V , Y ) , and H ( Y | A, U , V ) − H ( Z | A, U, V ) for the auxiliary random variable V . Further- more, to satisfy th e Markov cond ition U − V − ( A, e X ) − ( A, e X , X ) − ( Y , Z ) , one can lim it the cardin ality |V | of V to |V | ≤ ( |A|| e X | + 3 )( |A|| e X | + 2) . V I I I . C O N C L U S I O N W e derived inner and outer bo unds for the key-leakage - storage-co st region s fo r a hidde n ( noisy) identifier sou rce with correlated noise co mponen ts at th e e n coder and d ecoder to generate or emb e d secrets when a cost-con strained action sequence contro ls the decod er measurem ents. Th e c orrelation between the noise compo nents is provid ed by a mod el wher e the en c oder measurem e n t is an input to the decod e r measure- ment channel, as an extension of a BC mo d el. Side informa tio n at the eavesdropper that is co rrelated with the enco der and decoder measureme n ts is also con sidered since it is a realistic assumption fo r biom etric identifiers. Th e achievability pro ofs of th e inn er bou n ds in volve a rando m enc o ding step using the OSRB meth od that provides stron g secrecy . Th e main difference between the boun ds f or the GS and CS mod els is the increased storage rate for the CS model as comp ared to the GS model. The outer boun d s are given for CLN chan nels, for which impo rtant inequalities are derived. The inner and outer bound terms match f or th e secret-key rate, storage r a te, and cost, an d ar e dif ferent for the privac y-leakag e rate. W e illustrated achievable co st vs. secret-key rate p airs for a set of storage rates with an examp le, where source and channel param eters were m otiv a te d by realistic authentication scenarios th at use R O PUFs. W e showed that an action sequence significan tly decrea ses the n ecessity of reliable mea- surement chann els to achieve the maximum secret- key ra te. This reductio n in the requir e d reliability allows to have a larger hardware area a vailable f or pu blic storage , which is illustrated to fur ther increase the secret-key rate achieved for the same expected ac tio n cost. In futur e work, we will study the possibility of intro d ucing a third aux iliary rando m variable as it m ight be po ssible to find single-letter expression s for th e extra multi-letter terms in the outer bound s by defin ing anoth e r aux iliary ra ndom variable. A C K N OW L E D G M E N T O. G ¨ unl ¨ u and R. F . Scha efer were sup ported b y the German Federal Ministry of Edu c ation and Research (BMBF) within the nationa l initiative fo r “Post Shanno n Communicatio n (NewCom)” und er the Grant 1 6KIS100 4 . The work of H. V . Poor was supp orted by the U.S. National Science Foun- dation und er Grants CCF-093 9370 , CCF-151391 5, an d CCF- 19083 08. O. G ¨ unl ¨ u thanks Gerhar d Kramer fo r his previous suggestions that ind irectly helpe d to obtain Lemma 2 an d Matthieu Bloch for h is insightfu l comme nts. R E F E R E N C E S [1] B. Gassend, “Physica l random function s, ” Master’ s thesis, M.I.T ., Cam- bridge, MA, Jan. 2003. [2] A. D. W yner , “The wire-tap channel, ” Bell Labs T ech. J. , vol. 54, no. 8, pp. 1355–1387, Oct. 1975. [3] O. G ¨ unl ¨ u, “K ey agreement with physical unclonable functio ns and biometri c ident ifiers, ” Ph.D. dissertation, TU Munich, Germany , No v . 2018, published by Dr. Hut V erlag. [4] R. Ahlswede and I. Csisz´ ar, “Co mmon ran domness in informatio n theory and cryp tography - Part I: Secret sharing, ” IEEE T rans. Inf . Theory , vol. 39, no. 4, pp. 1121–1132, July 1993. [5] U. M. Maurer , “Secre t k ey agreement by public discussion from common informati on, ” IEE E T rans. Inf. Theory , vol. 39, no. 3, pp. 2733–2742, May 1993. [6] T . Ignate nko and F . M. J. W illems, “Biomet ric systems: Priv acy and secrec y aspects, ” IEEE T rans. Inf. F ore nsics Security , vol. 4, no. 4, pp. 956–973, Dec. 2009. [7] L. Lai, S.-W . Ho, and H. V . Poor , “Pri va cy-se curity trade-of fs in biometri c security systems - Part I: Single use case, ” IEEE T rans. Inf . F orensics Security , vo l. 6, no. 1, pp. 122–139, Mar . 2011. [8] I. Csisz ´ ar and P . Narayan, “Common randomness and secret ke y generat ion with a helper , ” IEEE T rans. Inf . Theory , vo l. 46, no. 2, pp. 344–366, Mar . 2000. [9] O. G ¨ unl ¨ u, O. ˙ Is ¸can, V . Sidorenko , and G. Kramer , “Code constructions for physical unclonable functions and biometric secrec y systems, ” IEE E T rans. Inf. F orensics Sec urity , vol. 14, no. 11, pp. 2848–285 8, No v . 2019. [10] O. G ¨ unl ¨ u and G. Kramer , “Priv acy , secrecy , and storage wit h multiple noisy measurements of identi fiers, ” IEE E T rans. Inf. F oren sics Security , vol. 13, no. 11, pp. 2872–2883, Nov . 2018. [11] O. G ¨ unl ¨ u, R. F . Scha efer , and G. Kramer , “Pri v ate authenti cation with physical identifiers through broadcast cha nnel measuremen ts, ” in IEE E Inf. Theory W orkshop , V isby , Sweden, Aug. 2019, pp. 1–5. [12] D. Merli, F . Stumpf, and C. Eckert, “Improvi ng the qualit y of ring oscilla tor PUFs on FPGAs, ” in ACM W orkshop Embedded Sys. Security , Ne w Y ork, NY , Oct. 2010, pp. 9:1–9:9. [13] H. Permuter and T . W eissman, “Source co ding with a side informati on “Vending Machine”, ” IEEE T rans. Inf. Theory , vol. 57, no. 7, pp. 4530– 4544, July 2011. [14] O. G ¨ unl ¨ u, K. Kittic hoke chai, R. F . Schaefer , and G. Caire, “Control lable identi fier measurements for pri v ate authentica tion with secret ke ys, ” IEEE T rans. Inf. F or ensics Security , vol. 13, no. 8, pp. 1945–1959, Aug. 2018. [15] V . M. Prabhak aran, K. Eswaran, and K. Ra mchandran, “Secrec y via sources an d cha nnels, ” IEEE T rans. Inf. Theory , vol. 58, no. 11, pp. 6747–6765, Nov . 2012. [16] R. A. Chou and M. R . Bloc h, “Separatio n of reliabil ity and secrec y in rate-l imited secret-ke y generation, ” IEEE T rans. Inf. Theory , vol. 60, no. 8, pp. 4941–4 957, Aug. 2014. [17] A. Khisti, S. N. Diggavi, and G. W . W ornel l, “Se cret-k ey gen eration using corre lated sources and channels, ” IEEE T rans. Inf. Theory , v ol. 58, no. 2, pp. 652–67 0, Feb. 2012. [18] A. Gohari, O. G ¨ unl ¨ u, and G. Kramer , “Coding for posit i ve rate in the source model key agreemen t probl em, ” May 2019, [Online ]. A v ailab le: arxi v .org/pdf/ 1709.05174.pdf. [19] H. T yagi and S. W ata nabe, “Co n ve rses for secret k ey agreement and secure computi ng, ” IEEE T rans. Inf . Theory , vol. 61, no. 9, pp. 4809– 4827, Sep. 2015. [20] R. Pappu, “Physical one-wa y functions, ” Ph.D. dissertation, M. I.T ., Cambridge , MA, Oct. 2001. [21] O. G ¨ unl ¨ u, T . Ke rnetzk y , O . ˙ Is ¸can, V . Sidorenk o, G. Kramer , and R. F . Schaefe r , “Secure and reliable key agreement wit h physical uncl onable functio ns, ” Entr opy , vol. 20, no. 5, May 2018. [22] J. W ayman, A. Jain, D. Malton i, and D. M. (Eds), Biometric Systems: T ec hnolo gy , Design and P erformance Evaluation . London, U. K . : Springer V erla g, Feb . 2005 . [23] R. A. Chou, M. R. Bloch, and E. Abbe, “Polar coding for secret-ke y generat ion, ” IE E E T rans. Inf. Theory , vol. 61, no. 11, pp. 6213–6237, Nov . 2015. [24] M. H. Y assaee, M. R. Aref, and A. Gohar i, “ A chiev ability proof via output stati stics of random binning, ” IE EE T rans. Inf. Theory , v ol. 60, no. 11, pp. 6760– 6786, No v . 2014. [25] R. Timo, T . J. Oechtering , and M. Wigger , “ Source coding pr oblems with conditi onally less noisy side information, ” IEE E T rans. Inf . Theory , vol. 60, no. 9, pp. 5516–5532, Sep. 2014. [26] R. Mae s, P . T uyls, and I. V erbauwhede, “ A soft decisio n helpe r data algorit hm for S RAM PUFs, ” in IEE E Int. Sy mp. Inf. Theory , Se oul, South Kore a, June 2009 , pp. 2101–2105. [27] O. G ¨ unl ¨ u and O. ˙ Is ¸can, “DCT based ring oscillator physical unclonable functio ns, ” in IEEE Int. Conf. A coust., Sp eec h Sign. Pr oc. , Floren ce, Italy , May 2014, pp. 8198–8201. [28] O. G ¨ unl ¨ u, O. ˙ Is ¸can, and G. Kramer , “Reliabl e s ecret key generation from physical unclonable functions under va rying en vironmental conditions, ” in IEEE Int. W orkshop Inf. F or ensics Security , Rome, Italy , Nov . 2015, pp. 1–6. [29] M. Bloch, Lectur e Notes in Information- Theor etic Security . Atla nta, GA: Georgia Inst. T echnol., July 2018. [30] D. Slepian and J. W olf, “Noiseless coding of correlate d informati on sources, ” IEEE T rans. Inf. T heory , vol. 19, no. 4, pp. 471–480, July 1973. [31] A. E. Gamal and Y .-H. Kim, Network Information Theory . Cambridge, U.K.: Cambridge Univ ersity Press, 2011. [32] M. Bloch and J. Barros, Physic al-laye r Securit y . Cambridge , U.K.: Cambridge Univ ersity Press, 2011. [33] Z. V . W ang and C. Nair , “The capaci ty region of a cla ss of broadca st channe ls with a s equence of less noisy receiv ers, ” in IEEE Int. Symp. Inf. Theory , Austin, TX, June 2010, pp. 595–598. [34] I. Csisz ´ ar and J. K ¨ orner , Information Theory : Codin g Theor ems for Discr ete Memoryless Systems , 2nd ed. Cambridge, U. K.: Cambridge Uni versi ty Press, 2011.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment