Fog Computing Systems: State of the Art, Research Issues and Future Trends, with a Focus on Resilience
Many future innovative computing services will use Fog Computing Systems (FCS), integrated with Internet of Things (IoT) resources. These new services, built on the convergence of several distinct technologies, need to fulfil time-sensitive functions…
Authors: Jose Moura, David Hutchison
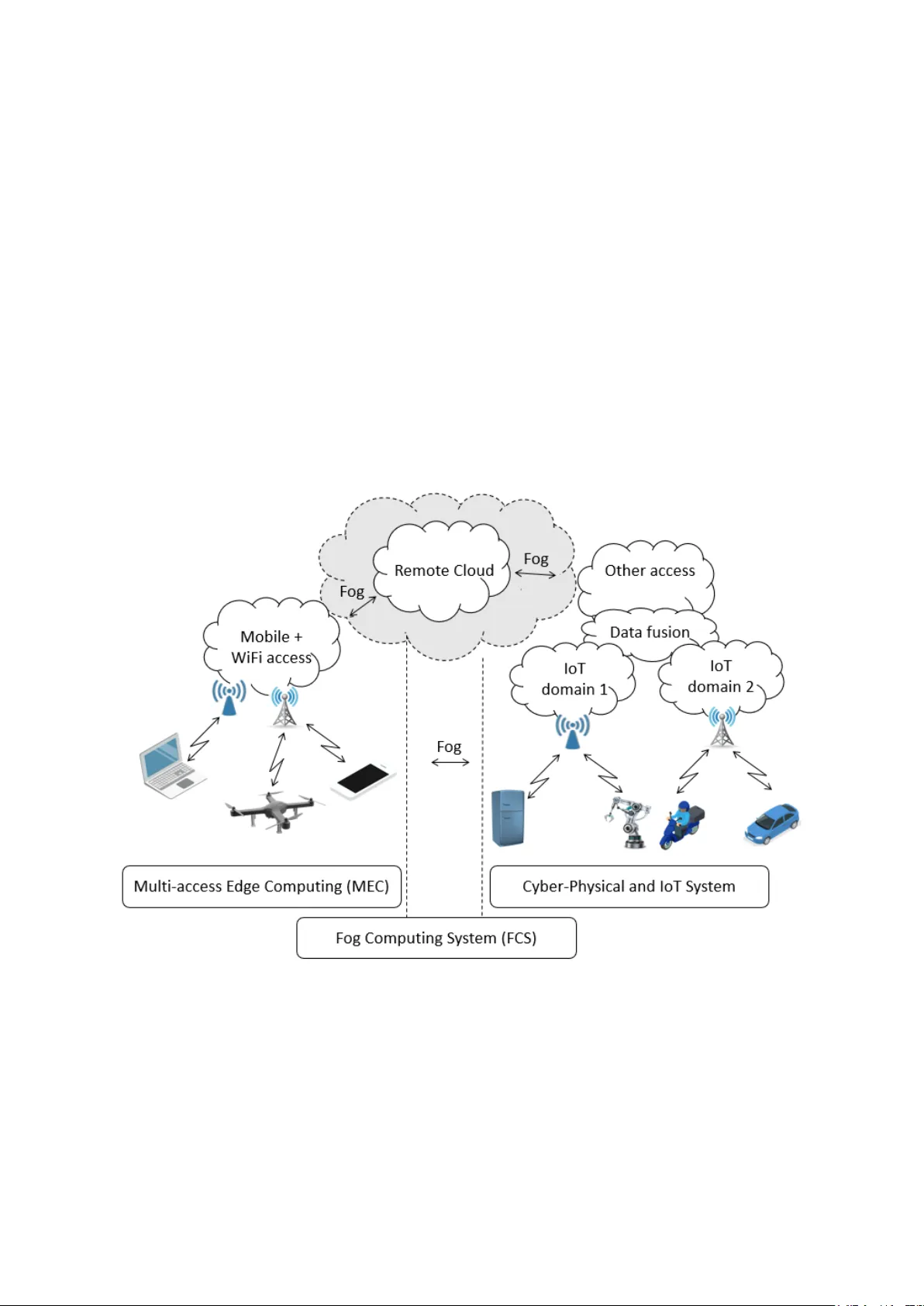
Review Fog Computing Systems : State of the Art, Research Issues and Future Trends, with a Focus on Resilience Jose Moura 1* and David Hutchison 2 1 School of Technology and Architecture, ISCTE-Instituto Universitário de Lisboa, 1649-026 Lisbon, Portugal, and Instituto de Telecomunicações, 1649-026 Lisbon, Port ugal (e -mail: jose.moura@iscte-iul.pt) 2 School of Computing and Communications, InfoLab21, Lan caster University, Lancaster LA1 4W A, U.K. (e -mail: d.hutchison@lancaster.ac.uk) * Correspondence: jose.moura@iscte-iul.pt Received: date; Accepted: date; Published: date Abstract: Many future innovative co mputing services will use Fog Co mputing System s ( FC S) , integrated with Internet of Things (IoT) resources. The se new ser vices , bui lt o n th e convergence of several distinct techn ologies , need to fulfil time-sen sitive functions, provide v ariable levels of integration with the ir environment, and incorporate data sto rage, computation, communications, sensing, and control. There are, ho wever, significant problems to be solved before such systems can be considered fit for purpose . The high heterogeneit y, complexity, a nd dynamics of these resource- constrained systems br ing new challe nges to their robust and reliable operati on, which implies the need for integral resilience management strateg ies. Th is paper surveys the state of the a rt in the relevant fields , and discusses the researc h issues and future trends that are emerging . We envi sage future applications that h ave very stringent requirement s, notably high-precis ion latency and synchronization betwee n a large set of flows, where FCSs a re key to supportin g them . Thus, we hope to provide new insigh ts into the desi gn and mana gement of resi lient FCSs that are formed by IoT devices , edge co mputer servers and wireles s sens or networ ks; these syste ms ca n be model led using Game Theory, and fle xibly progra mmed with the latest software and virtuali zation platf orms. Keywords: Fog Computi ng ; Internet of Things / IoT; edge computi ng; cyber-physic al systems / CPS ; Software Defined Network s / SDN ; c hallenges; ga me theory ; Net work Fu nction Virtualiza tion / NFV ; cyber-attacks; re silient systems; self-awareness; network slicing 1. Introduction The digit ization a nd interconnectio n of al most ev erything are together making an enor mous impact on all a spects of our daily lives . The Internet of Things ( I oT ) [1] is a very important underpinning tec hnology f or Fog Computing S ystems (FCSs) [2] that can of fer, at the net work edge, embedded intelligence and smart actuation/c ontrol of peripheral actuators. Prominent examples of an FCS include the i ntelligent grid, s mart building s , and next generati on mobile sy stems . Because of the in cr easing importance of FC S in our society, these systems require strong protection against threats that can under mine their normal o peration and consequently t he quality of our liv es [3] [4] . Figure 1 v isualizes our vie w of the fast e volution of networked sys tems towards the emergin g FCS. It a lso shows tw o design convergence moveme nts. The first of these occurs at the lower part of Figure 1, and is about the convergence of acc ess technologies. The second convergence occurs at the top part of Fig ure 1, which is relat ed to ser vice a ccess (i.e. remote c loud v s. ed ge cl oud). Our worki ng definition of FCS, particularly t he notion of “fog”, assumes that t he computation al resources can be delivered by either remote cloud or edge cl oud, depending on each depl oyment scenario. That is why, in Figure 1, we have the bidirectional arrow between the t wo top clouds w ith distinct co ve rage, and the a rrow is labe lled with the term “fog”. In addition, there are severa l options f or each end device to have access t o the Internet. Thus, Figure 1 s hows two possible options in ter ms of access 2 o f 38 technology, which are Multi-access Edge Computing (MEC) on one side and Cyber-Physical and IoT Systems on the other . Similarly, to the two options for delivery of computatio nal resources, there are also choices for t he access technology that will be u sed for the deployment of a ser vice. We illustrate this second option with the two vertical dotted lines of Figure 1, which are con nected by a ho rizontal bidirectional arrow, a lso labelled “fog”. Another vision of an FCS aligned to ours is in [ 5], where the low-delay distr ibution of fog services to end -users uses the cloud- to -things continuum infrastruc ture. This vision is equivalent to the top part of Figure 1, associated with the resources (fog vs. edge) used to compute the tasks of eac h service. The FCS vision that we dep ict c omplements the vision in [5 ]: h ere (in Figure 1) we are adding the new a spect concer ning the heteroge neity of network acc ess. The previously refer red FCS threa ts ca n be grouped in two classes , viz. un planned and planned. The unplan ned system threats are typicall y due to n atural disasters (e.g. earthquake s) or non- intentional faults or human errors. Planned sys tem threats are typically associated with cyber -attacks. Whatever the origin of the threa t, it is vitally important to deploy appropria te resilie nce strategie s and mechanisms to mitigate threa ts. A list of relevant system weak nesses against threats is a vailable in [5 ]. This list includes low-level vulnerabilitie s in physi cal n etw orking equi pment using field programmable gate array (FPGA) devices, which may allow, as an exa mple, an attacker to install and boot a malicious software image in a huge diversity of networking devices, such as routers, switches and firewalls [6] . Figure 1. Evoluti on of Networked Sys tems to Fog Computi ng Systems FCS is about a physical facility with embedded sensors and actuators that can be remotely monitored a nd controlled by co mputerized s ystems [7] . The monitoring a nd control are ma de by logical control loops over p hysical c ommunicati on c hannels. These c hannels are established between the sensors/actuators and the computers that ma nage them. The channel s transfer both data representing the facility status and control messages to chan ge the operation m ode of that facility. FCS threats can ad versely impact both system mo nitoring and control tasks. The Oxford English dictionary defines resilience as “ the capacity to recover quickly from difficulties”. This suggests tha t a resilient system in t he face of some eit her know n o r unk nown threa t should contain features t o mitigate or even preve nt that thre at ; typically, these features will be to detect, absorb, re cover and a dapt [8 ] . After succe ssfully dete cting a threat, t he system s hould have 3 o f 38 the ‘ absorb ’ feature to diminish the negative i mpact induced by that threat . Followi ng the threat occurrence, the system should recover its operation as quickly as possible to an acceptable level. Then, after the system threat has finished, the system should ada pt its manageme nt po licies and diminish even more than before the negative impact on the system in any future repe tition of that t hreat or even pr event it. During the current paper resilience and robustness are considered as synonyms. Nevertheless, [9] differ entiates these terms. They argue that, after a system threat , a resilient system shows a temporarily degra dation on its performance. A lternatively, a robust system does not have any degra dation. In additi on, [9] discusses a ttributes closely related to re silience s uch as reliab ility, agility, f lexibility, am ong others, which are not c overed here. We also co nsider that resilienc e is related to both phy sical system infra structure and data (logical) analysis [7] . The high levels of heterogeneity, co mplexity, a nd dynamics of re source constrain ed FCS s bring new challenges t o t heir reli able operation, w hich imply the nee d for n ovel management strategies , using distinct tec hnologies. These technologie s are Game Theory ( GT), Software -Defined Networking (SDN), Network Funct ion Virtua lization (NFV) and Machine Learning (M L). As a n example, GT is a fundamen tal to ol for modeling the threats and their interactions wi th the se systems, enabling the de sign of automated protecti on mechanism s [10] . GT has been used to study mechanisms in the area of Advanced Persistent Threat s (APTs) [11] a s well as for enabling both safety and security in cyber-ph ysical and IoT systems [1 2]. In the co ntext of a n APT, a well -provided resource atta cker establi shes a long-ter m, illegal, and o bfuscated infi ltration i n a network d omain to steal confide ntial data. GT can model and a nalyze the interactions bet ween thre ating entities and system defenders to pro tect the data privacy and enable the resilie nt operation of FCSs. The emerging FCS fea tures [8] of dete ct, absorb, recove r, and a dapt are like t h e diverse stages of a theoretical game model that run s in a sequential way, mediating t he interaction s among opponent players. Examples of opponent players a re cyber -attacker s versus aut omated def ense mec hanisms , or nature ver sus self-hea ling mechanisms. We a rgue that an effective way to fulfil the challenging requirements imposed by the successful managemen t of resili ent FCSs is to orchestrate diverse technologies, such as GT, S DN, NFV, and ML. Previous work in the secur ity area has investigated privacy on IoT systems [1], and saf ety [ 12] or resilience [ 13] for Cyber- Physical Systems (CPSs) w ith embedded IoT device s. Our contributi on in this paper is to refre sh and advance the literature by investigating effective management soluti ons to the n ovel requirements of a n ew generation o f Cyber-Physical Systems (CPSs) a ugmented with oth er technologies, such as I oT. All these techn ologies are converging int o a co mmon platform, often labelled as Edge (Fog) Computing. This new version of CPSs we ca ll FCSs. In the current work, w e discuss the available literat ure , h ighlight th e a dvantages th at the surveyed resea rch areas could bring to FCSs for enhancing their resilience , and outline some f uture re search areas . As a primary case study, we investigate h ow an FCS system can detect, absorb and recover from, a nd adapt to, threats. These goals s hould be achie ved using available system resources for lim iting the sy stem deployment and maintenance cost s. Despite th ese considerable constrai nts , FCS should fulfil time- sensitive functions with variable levels o f integration with t he environment, in tegrating distributed data storage, pa rallel computati on, proficient communications , ubiquitous sensi ng, and efficient control of system resource s used by machines, agent s (algor ithms) or e nd-user devices. Our work is mai nly concerned with FCSs . However, the entire discussion throughout the paper is by no means re stricted to FCSs. In fact, the main f indings of our work can be also applied to more general scenarios, such as wireless/IoT networks. Th is paper has the following structure . Section 2 discusses related work. Section 3 describes some ba ckground to the re maining part of pa per, namely pertinen t scenarios i n FCSs and relevant aspects to be aware of whe n t he goal is to enhance t he resilie nce of FCSs . Section 4 presents a four- layered design for res ilient Fog C omputing and IoT syst ems . Section 5 outli nes open researc h directions. Sectio n 6 concludes the paper. The paper ’s logical or ganization is visua lized in Figure 2. 4 o f 38 Figure 2 . Logical Roadma p Behind the Paper 2. Related Work This Section compare s known re lated work at th e time of writing . We discuss relevant associated technologies , inc luding Ga me Theory ( GT ) , SDN, NFV, and Machine Learning ( ML ). We also envisage GT as compleme ntary techn ology to the o ther technologies disc ussed in our pape r. All these technologies could have a n important role in efficiently managing fog computin g systems. In our view, the technologies mentioned above will be of para mount importance to support new applications t hat will appea r in the next d ecade. T he se emerging appl ications will dema nd much beyond the best-effort service offered by the current Inter net. These new services ne ed the Internet to offer strict pa cket latenc y , t o provide exact coordinatio n among many packet flows across multiple communication chan nels , and to assure connectiv ity service immune to the negative impairments of any Internet threat. Th is paper is focused on th e last of th ese capabilities , viz. resilienc e, in the context of Fog Computi ng. We have surveyed the releva nt literature as discussed bel ow. However, first a clarification about the network/comp uting architecture scope of fog c omputi ng system s: our architectural vie w of a FCS is like a bidirectional conver gent move ment of technologies a nd computational resources (see Fig. 1) not only from the cloud to the edge devices, i.e. the decentralized cloud discussed in [14] , but a lso from the edge d evices to the cloud , wh ich was de bated in [15 ] . That is , the fog edge is a moving border, dependi ng on the perspective initiall y analyzed ( i.e. cloud or mobile ad hoc acc ess ). From t he literature analysis , we can conclude that a vast amount of work , e.g. [16][17][18] has been done on s tudying and cla ssifying published cont ributions i n the securit y a rea , but they la ck a more holist ic and complete re vision than the security perspective by re viewing some other important areas, such as software-defined solutions for resilient FC Systems (FCSs) operating in diverse emerging use cases. Consi dering that resilience incor porates security a s a sub-capa bility, w e justify the classification of so me of the surveys a s constraine d literature overview s , because (for ex ample) some [16] present techniques f or detection of DDoS att acks, while others [17] study machine learning solutions for intrusion detection. Also, [18] is focused on security control and attack detection but only for industrial FCSs . Further releva nt and a ssociated work [19] is focused on the oretical management models for networked syste ms, co nsidering t he need of t he diverse pla yers of t he network t o coopera te among them selves t o enforce the optimum usage of the available network resources. The auth ors of [ 13] review dependa bility and security for detection, dia gnosis, and mitigation. Nevertheless, they do not cover enabling technologies, nor a pplications , in their discussion. Clearly, further work is necessary for investigatin g proposals which can enforce not only a particular security aspect but a more generic resilience framework to immunize network operation against the negative ef fects of serious threa ts. The authors of [20] argue that the manage ment of networked systems should al so have self - adaptability cha racteristics in the presence of seriou s system t hreats . In t his way, the system s tructure 5 o f 38 as well as its o peration can become m ore resilient against seriou s and persistent m enaces against the ir normal operation. Aligned with this set of system self- capabilities, there are a set of work proposing ML techniques [17] [21][22]. In a more detail way, [22] investigates how ML a lgorithms can be used in applica tions i nvolving NFV and SDN. NFV virtualizes network functions and decouples t hese from the hardware. The m ain goal of NFV-ba sed solutions is t o automate networ k configuration as well as to provide system services in a n elastic and adaptive wa ys. On the other hand, SDN can be very useful in Edge Computing scenarios to program, with s ome abstraction of the physic al devices, the way the netw orking-based system is expected to operate. SDN-based solutions can divert co mputational-i ntensive tas ks fro m res ource-constrai ned mobile devices to more po werful servers located at the network edge. Hence, the battery autonomy of mobile devices is increased, and the results of the computational - intensive tasks a re more quickly obtained. In addition, there are several important contributions a lso aligned with our current proposal but a pplied to a m ore specific use case, namely, n etwork resource allocation for ultra-dense networking [2 3] , mobile network plan ning with small cells [ 24] , optimiz ation of hybrid SDN networks [25], and management of faults in SDN- based [26] or vehicular networ ks with a utonomous cars [27] . In addition, we have found valid contributions in sens ing manageme nt for smart city monitori ng [28] , mobility of things or devices using several standa rds of low-power wide a rea networks [29] , studying novel business models for resource ma nagement i n 5G wireless networks [ 30], a nd analyzing datasets to pr edict and prevent securit y incidents [31] . From all the surveys we are aware of a t the time of writi ng , we c learly identif y [32] , which broadly rev iews the litera ture in terms of c ontributions to resilience applied to FCSs. The a uthors argue according to their experience that the most challenging issue for designi ng a resilient FCS is to deploy a real -time, closed -loop, networked control system complete ly immune a gainst serious threats. These t hreats are c aused by natura l noi se, which induces in the system p acket loss and bit errors, as well as some internal or external cyber-attacks. They also discuss two medical case studies. The first is about the resilient integration of virtual realit y and a robot device for restoring the corporal coordination and flexibility of persons with disabilities. The second stud y is about the design of a robust implantable medical dev ice f or physica l- to -cybe r health se nsing and cyber - to -physical organ control. This survey published in 2 016, it is naturally outdated, missing last releva nt a nd related literature work. Our paper tries t o overcome these shortcomings, a nd looks anew at the literature on rel iable and flexible soft ware-def ined management solutions for resi lient FCS s. The current work adopt s a set of management fea tures [8 ] (i.e. detect, absorb, recove r, and adapt) to supp ort the resilience of FCS s. Neve rtheless, there are other alternative s, suc h a s in [4] where the authors propose two types of management features; the first type is formed by sh ort -term or re active management activities, viz . defend, detect, remediate and recover. The second type is formed by long-term or proa ctive management activi ties, viz. diagnose and ref ine. The next Section offer s a background discussion on th ese technologies, as well as on FCS scenarios and resilie nce requirements in systems for med by either physica l or virt ualized resources . 3 . Background on Software- Defined Resi lient Fog Computing Systems The paper ’s content is ba sed on our outline of a software-defined re silient F og Computing System shown in Figure 3 . It shows the two major goa ls of the pape r. The fir st g oal i s to investiga te how GT ca n model an FCS wi th IoT applied t o edge computing use cases. The second goal is to study how SDN-based solutions can empower FCSs with embe dded IoT devices com municating via wireless sen sor net works with extra capabilities , such as programmi ng of ma nagement policies t hat enforce the system resilienc e against diverse threats, includi ng system node failures . For that, our current view is about SDN -based solutions that orchestrate other technolo gies su ch as NFV or ML. In this way, there is a viable solutio n to support dynamic cross -layer resilience decision making for FCSs us ing heter ogeneous IoT devices . I n t he su bsections below, the l iterature within the maj or area s evidenced in Figure 3 a re discussed, as follows: i) resilience definition and backgr ound; ii) scenarios of Fog Computing Systems ( FCS s) ; i i i) analysis of FCS s ; iv) novel programming mo dels for FCSs. 6 o f 38 Figure 3. Outli ne of a Software -Defined Resilient Fog C omputing Syste m 3.1. Resilience Definition and Novel Manag ement Challenge s The NIST 1 definition of a Cyber -Physical System (CPS) is a commonly accepted one. According to that definition, CPS s are engin eering-ba sed system s offering a functio nality st rongly depende nt on the intera ction a mong computational and physica l processe s. Thi s integr ation e nables the deployment of emerging systems that our society can use in different ways. The literature also offe rs several definitions of resilience. Our paper adopts the definition of re silience as the system’s capability to maintain an acceptable level of service to its users despite the eventual occurrence of various fault s and c hallenges to the system’s nor mal operati on, where some issues could be completely ne w to the system architect [4] . So , a resilient fog system should offer a satisfactory leve l of service desp ite the vario us challenge s t o whic h it is exposed, whether t hese be natura l disaster s, weather events, co mponent failures ( in hardware or s oftware), misconfigura tions / human errors, or malicious offensives such a s cyber -attacks. FCSs show co mpletely novel ca pabilities, includin g p ervasiveness a nd in telligence. I n parallel with the new be nefits offered by FCSs, these systems also beco me more attractiv e to cyber -a ttackers because if the attacks are succe ssful t hen important sectors of society c ould s uffer significant losses. Considering security as one of the relevant aspects of resilience, we have found s everal publications that d iscuss the use of public-key solutions in secure fog computing scenarios, e.g. involving IoT devices [33][34] . We think that public-key solut ions b ased on hierarchica l centra lized design (e. g. Public Ke y Infrastructure – PKI) can have scalability is sues, robustness problems due to their single point of failure, or be especia lly attractive to cyber-atta ckers due to their centralized operation . In addition, given the limited computational resources in edge/ fog/IoT scenarios tha t we recognize in this paper, it is genera lly d ifficult (and thus s ometimes neglected) to apply pub lic-key crypto in FC Ss , sensor networks or other systems. But these security services need to be used, without doubt . At this point, a pertinent question arises: are there good solutions to ha ndle the cost s of cryptographic certificates in FC Ss ? The research community surely has an important role in successfully ans wering that question . F or this, GT (discussed in s ubsection 3.3) , the nove l programming approaches (debated in subsectio n 3.4 ), or our hierarchical design of a resilient FCS (discussed in Sec tion 4) may eventually be useful to answer t his qu estion. In addition, we have found some alternatives to PKI models with a more decentralized design [35 ][36]. Clearly, further work is required in all these security aspects to successfully deploy them in FCSs. 1 NIST stan ds for National In stitute of Standards an d Technolog y, available in https://www.nist.g ov/ (verified in 21/02/2019) 7 o f 38 The research community has ded icated recent notable efforts to addre ss the novel threats aga inst FCS s [18] by enhancing the management of resilience [37] [38]. In addition, the relevant interplay between resilience and self -orga nization for the design of critical net worked systems has been als o investigated [20] . A potential outcome from all these eff orts is to obtain a robust FCS , whic h shoul d have a system design orie nted for the a spects of stability, security, a nd ‘ systematicness ’ [ 32] . By ‘ systematicness ’ they mea n a system that has a seamless integration of sensors an d a ctuators. Please consult [32] for further details on these design aspects . Acc ording to an ITU recent deliverable [39] , the resilience is a very re levant networ k capability to maintain the high quality, availability, and reliability of the upc oming networking services and th eir related user applications. The literature have a few contributions related wit h FCS s that i mmunize these systems against either already identified or potential threats in distinct usage scenarios. The next subsection prese nts a literature revision of FCS using a ta xonomy based on some relevant use cases. 3.2. Scenarios of Fog Computing Systems We start this sub section trying to clarif y the Fog C omputing (FC) pa radigm. The authors of [40][41][42 ] consider that FC is no t a substitute for Cloud Computing but a pow er ful complement. In this way, FC enables elastic process ing a t the net work edge a nd low-la tency user access to t he data output from t hat proce ssing, or even da ta st ored at t he net work per iphery. Nevertheless, it is still possible, if necessary, to connect remote cloud applica tions to the end- users. In additio n, FC serves as a key enabler [43] for many fu ture technologie s like 5 G [44][ 45], Internet of Things (IoT) [46][47][48 ], B lockchain [49] , or even applica tions re quiring co mputation offloa ding [5 0]. The FC paradigm besides providin g local proce ssing/storage and low lat ency, it also supports mobility and location awareness for specific applications requiring those requi rements for their normal operation. Th en, the current subsec tion discusses below some rele vant use cases in Fog Co mputing Systems (F CS s) enhanced with the ever-developing model of the Internet o f Th ings ( IoT). It provides a con cise and precise description of these scenario s, their ba sic requirements, a nd the novel challenges tha t these use cases present to the research and standardiz ation communities. The s ce narios discussed below involve power gri ds [51], smart buildings [5 2], next-generation mobil e communication sys tems [53] , healthcare systems [54], a nd Industry 4.0 (Industrial I oT) [5 5]. Intelligent Power Grid Systems Power syste ms are changing f rom centralized large facilities to fully dis tributed micro -size facilities, such a s domestic electrical appliances composed by ph otovoltaic panels and DC/AC power inverters. At the same time, the full opera tion of the latest ge neration of m icrogrids depends massively on co mputerized systems. Consequently, that situation makes these systems increasin gly exposed to cyber-atta cks [51 ][56], which could crea te huge problems in our ever yday lives. Smart grids present great ch allenges to their efficient manageme nt due to the unpredictability of demand load a nd the reliability of data communicat ions. The unpredictability of demand load is caused by many factors, not least to domestic electrical energy variation and most re cently to the charging of electrical vehicles [57]. In addition, the reli ability of data communicati ons in smart grids could be adversel y affected by per turbations that occ ur on some links, mai nly on wireless links [58] . These perturba tions ca n be induced by either cyber - attacks [5 9][60] or impairments on the communications medium [6 1][62][63] . The a uthors of [61] study the outage proba bility of a wire less link, considering the multipath fading, shadowing, and random path loss given the location distribution of s mart mete rs. In [62] , they prioritize the data transfer within a smart grid using a position-based quality- of - service (QoS)-aware routing protoc ol. Furt her, they propose a load - balancing mechanism t o mitigate network congesti on induced by many critical event messages. As an example, these event me ssages can be related to the high number of damages on the electrica l physical infrastructure a big storm can ca use. Paper [64] proposes an incentive-based demand respo nse algorithm for smart grids, which uses a deep neural network to overcome system uncerta inties by finding out the i nitial unknown both 8 o f 38 prices and energy demands. In a ddition, the same al gorithm also uses re inforcement learni ng to obtain the optimal i ncentive ra tes, considering the prof its of both service provider and customers . In a smart grid, severa l devices use wireless co mmunications to transfer da ta. Most of these use industrial, scientific, and medical (ISM ) radio ba nd f or ch a nnel c ommunication. Since the ISM band is license-fre e, attackers can easily have access to that fre quency band, tryi ng to initi ate a cyber -attack. A potential attack is the jamming attack t hat can discon nect important s ystem devices such as smart meters, collectors of meter data, remotely controlled distribution automation devices, and GPS antennas of phasor measur ement units. Therefore, m ore work is needed to create resilient wireless communications am ong the diverse comp onents of a smart grid. The a uthors of [65] are concerned with the resilience of network control systems under communication delay attacks. These attacks force two wrong operatio nal si tuations on t he controlled system (e. g. power pla nt) due to either missing data or delayed data from the power plant status. In addition, this a ttack type ca n be made over encr ypted messages by jamm ing t he w ireless communications used by the syste m control l oop. So, the a uthors of [65] propose a solution to countermeasure a time delay atta ck. To implement that protection, their solution has a system state estimator. Then, the state predicted can be compare d with the reported state of the power plant. In the case the two states show significant changes, then the controller uses the predicted state until the reported state is similar to the predicted one, when t he controller use s again the reported state. Further aspects t hat need m ore work in smart grids are anomaly dete ction systems and intrusion detection system s, particu larly from insider attacke rs [51] . In ad dition, more investigation on coordinated cyber-attacks needs to be ca rried out. During a cyber -atta ck bogus data that is enf orced by the attacker s can affect the normal opera tion of a power plant. So, it is neces sary to detect and remove as quickly as p ossible from the p ower grid s upervision system all the bogus power plan t status inserted by false data injection attacks [66] [67]. The authors of [68] provide a detailed discussion of impr ovement strategies f or the resilie nce of power systems. These strategies a re classified based on tw o distinct perspectives . The firs t perspective a nalyzes the resilience of po wer systems cons idering the t ime- dimension. The second pe rspective enforce s the r obust operation of power systems, choosi ng adequate control actions. Additional d iscussion on these topics is in [68 ]. Smart Building S ystems Considering the substantia l price reduction i n sensor nodes, these now ca n be used in novel applications, as is the case, for example, in modern smart building s. The author s of [5 2][69] argue that IoT can be a ca talyzer of a full i ntegration of build ing i ntelligent mechani sms with the system grids that connect ea ch building. Hence, the people living within th ose buildings could benefit from greater comfort without p aying m ore to the diverse utilities, e. g. ele ctricity, gas, water, or even healthcare [69] . To achieve this, and particula rly for th e electrical scenario, all the intelligent control mechanisms existing within a building should operate in a completely c o ordinated way with the smart power grid suppl ying that building. To make that coordination possible, open networking protocols sh ould be used [52 ]. By open, we mean standard solutions t hat enable u niversal exc hange of data over heterogene ous technological system s to fulfil a set of commo n goals. The authors of [70] propose a population based algorithm f or deciding ab out the places where sensors should be located to monitor the various pipes within a large building. Their results sho w that the proposed algorithm demonstrates good perfo rmance in relati on t o other algorithms inspired in nature. The results obtained also suggest t hat the system lifeti me can be impro ved. In [7 1] the a uthors pr opose a smart solution for buildings that learns and predicts opti mum individual user-pref erences toward s the efficient ene rgy contro l of personalized lig ht. They argue that their proposal can achi eve energy savings up t o 72% when compared t o the conventional lightin g systems. Aligned with prev ious work, [7 2] proposes a flexible a pproach supported by deep learning that offers aut omatic adjustment s to syste m / en vironment variations. The same approach a lso has an incentive mec hanism based on gamification f or i mprovin g t he interaction be tween the bui lding inhabitants and the buildi ng system that supe rvises and controls the infra structure. In [73] the authors propose a platform -based methodology for smart buildin g d esign. The la st platform reu ses hardware and soft ware on shared in frastructures, ena bles the fast pr ototyping of 9 o f 38 applications, a nd allows exploration of the design spa ce to optimize the design perf ormance. The paper illustrates the usage of the propo sed pla tform v ia a ca se study on the design of on -demand heating, ventilation, and a ir conditioning sys tems. More work is necessary in the area of smart buildin g systems. In fact, the livin g comfort characteristics (temperature, humidity, air quality), energy (electrical or gas) efficiency, and building safety require the existence wi thin each building of a software-defined management service responsible to satisf y the new challe nges imposed by modern buildings wit h a myriad of embedded sensors a nd actuators. This management service should be responsible for local control loops, send automatic mes sages to ex ternal pub lic en tities (e.g. in case of ga s leakage or fire alar m), and re cording the occ urred buil ding events f or future analysis. After analyzing the data extra cted from the buildin g events, the ma nagement service, in a proactive wa y, could reco mmend so me ma intena nce tasks in the building t o i mprove th e living comf ort, re duce the energy consumption, increase the safety, or reduce the false -negative statistics of re porting failures. Next Generation Mob ile Systems Considering the ra pid evolution of mob ile cellula r technologies, incl uding smart personal wireless device s, a set of new mob ile applica tions i s appearing [53] . These novel applications are mainly focused on fulfillin g the require ments of user s. For ensuri ng more positive usage experiences to end -users, service provi ders are moving their focus from Quality of Service (Qo S) to Quality of Experience (QoE) in the way the y aim to eff iciently manage the available resources fr om their network infrastructures. O bviously, QoS is related with technical metri c s such as packet loss, loss rate, delay, and jitter, wherea s QoE try to balance in t he more positive way what the user expects from th e network-based application and w hat the same user ef fectively gets from that application. In addition, one ca n see QoE [53] requirement s as an evolution from t he t hose of QoS [74 ][75]. For next generation mobile systems (e.g. 5G), the a uthors of [53] comprehensively discuss the literature in terms of enhancin g the user experience by means of supporti ng advances in t he methods t hat assess the video quality and reflecting on how the QoE reported from users should be conven iently managed in upc oming usa ge scenari os. For further e nhancements in QoE, t he managemen t of bot h network resources and offered services needs to be evolved by adop ting s olutions based on self - organization optimiz ation. In addition, SDN and cl oud technologies ca n be useful to allocate the required services to t he be st possible available s ystem re sources , enabling a more dense net work management with smaller cells than before, and a more holistic manageme nt co nsidering the cross - layer aspect o f SDN opera tion [7 6]. The authors of [77 ] propose a potential ga me for sh aring spectrum in 5G networks i n a decentra lized way and based on user QoE. The w ork in [7 8] discuss es the major challenges and f uture devel opments on FCSs in ve hicular networks, healthcare sy stems, and mobile education. T he contributi on in [79] considers the scenario of a vehicular ad h oc network formed by vehicles on the road with some co mmon interest s w hich can form a platoon -based driving pattern. They co mprehensively dis cuss the novel manage ment challenges induced by th e platoon -based driving in the efficien t operation of the vehicular netw ork. Further work is needed to manage the continuou s converge nce betwee n the network operat ors and the cl oud providers formin g a common meet- in -the-middle p lace currently designated a s edge (fog) computing. This c onvergence scenario is a win-wi n situati on for all the players involve d, including the end -users, as we now explain . The network operators need more se rvices, processing, and storage resources from the cloud providers, i ncluding their experience i n satisfying high v olumes of da ta pr ocessing with a minimum set of computing/network ing re sources b y orc hestrating all these (physical/virtualized ) resourc es in an e lastic way . In the opposite directi on, the cloud providers a re interested in supp lying the end-users with customized applications and with the highest possible quality. To satisfy these requi rements, the proactive data caching at the network edge based on historical data popularity can be very useful to diminish the d ata access latency/jitter . E nd -users want ubiquitous and re liable acc ess to all the services they need in each of their daily tas ks. If the end-users are served adeq uately then they will be sa tisfied, rewarding bot h network operators and service providers. Here, novel busi ness models can give t he right incentives towards the g oal of being offered applications with a q uality much higher than t he curre nt bes t-ef fort model. The network provider 10 of 38 should re ceive t he a dequate in ce ntive to supply the us er with the right amount of network resources . On the other hand, the netw ork should have a n appropriate accounting mechanism to verif y the exact amount of network resourc es that have been used by each user application. This is to ensure so me fairness among the divers e users ’ payme nts. GT can enh ance such b usiness models by solving eventua l conflicts a mong the self-expectations of the diverse pla yers. Healthcare Systems A large a nd ra pidly growing percentage of people in most countries is elder ly. There is huge pressure to dev ote enough med ical a nd human resources to ensure a good qua lity of life. However, the commit ment of enough resources is pro ving i mpossible by reason of bo th hu man and financial constraints. A popular appr oach to a lleviate these pressures is to explore the adoption of IoT in medical service s ystems, ena bling innovative so lutions in healthcare [54]. There are important potential advantages of deploying IoT -based healthcare sys tems, namely: i) extra ct useful information for raw -data; ii) automation in terms of either improve patient health or pr omote preventive care; iii) en hance patient sa tisfaction a nd engageme nt with their treat ment pr ocedures; and iv) enhance the management of popula tion health in a large scale with a suitable amount of resources. However, obsta cles for adopting IoT in he althcare systems include i ssues with security and performance. A s an example, for deploying IoT -ba sed healthcare systems with excellen t performance, there is a strong need to supp ort real -time requirements. The a uthors of [8 0] propose a fog computing implementa tion to decrease la tency substantially. T his occurs because the d ata processing is made as clo se to the end -consumers as possible by leveraging virtualized containers on the networ k edge such as mobile base stat ions, gate ways, netw ork switches and routers. Additional deployment challenges of IoT-based healthcare systems are discussed in [81]. In a ddition, based on a thoroughly rev ision of t he literature, [82] discusses the major a dvances h ealthcare syste ms embedding IoT-ba sed smart devices. They also address the intelligent tre nd a nd f uture re search directions in the field of IoT-ba sed healthcare solutions. The authors of [83] proposed a smart health sys tem which includes a u nified da ta collection layer for the integration of public medical resource s and pe rsonal health devices . In addition, the same system has a cloud- enabled and data -driven platform for multis ource heterogeneou s healthcare data storage and a nalysis. Then , the s ystem offers acc ess interfaces for sy stem developers and user s. A compre hensive analy sis of authenticati on protocols which address t he trad e-off betwee n securing implantable medic al devices in terms of access rights and the safety of the patient in case of emergency is available in [ 84] . Moreover, they contrast the authentication protocols w ith respect to the cryptographic and sec urity mec hanisms implemented on the implant. Healthcare applications can benefit from the deployment of the f og c omputing parad igm [ 85] . This could be aided by appropriate design innovations i n the way the networked s ystems interoperate [86 ]. In addition, hea lthcare applica tions ca n off er low la tency, distributed process ing, context awareness, better sca lability, fault tolerance, better security and priva cy [8 0]. Cloud-based IoT systems [87] , or fog-based [8 5] to reduce the access delay, see m to be promising solutions in healthcare due to the huge ava ilable capacity in da ta storage and data processing ; the offloading of computationally i ntensive data a nalysis tasks from bo dy sensor devices to fo g servers, which could be containers, is feasible. In this way, the autonomy of battery -operated body sensors i s increased, lessening the burden on patients as they will not so of ten need to recharge their body sens ors. The use of remote-locatio n healthcare has also become via ble with the recently proposed Internet of Medical Things (IoMT) [88 ]. The IoMT approach can e nable the diagnosis and trea tment of pa tients to give a higher lev el of sa tisfaction, especially during pandemic periods or even i n cases of patients with mobility impair ments . A taxonomy of FCS s for healthcare is available in [89] . They identify as open research challen ges the issues related with secu rity and privacy, autonomic decisions for lo op control, and event predicti on. 11 of 38 In dustry 4.0 The term “Industry 4.0” , the f ourth revol ution in th e f ield of manufacturin g , was coined i n November 201 1 under a governmental initiative to enhance the Ger man comp etitiveness in the manufacturing i ndustry [90] . Industry 4.0 is als o more rece ntly desig nated a s “Industria l Intern et of Things (IIoT)” or “S mart Factories” . I t is a new sort of industrial revolution that not only guarantee s communication and interconnec tion among distinct indust rial systems, but also analyzes the information obtained from it, and use that in f ormation to create a more h olistic and better-connected ecosystem for the industri es [ 55] . In addition, the automati on offered by the deployment of IIoT makes the industrial plants more auton omous and efficient, but it is still possible to have remotely operated industrial processes. However, the capabilities of reliability and sta bility for cr itical communication, with short and predictable latency, are re quired to offer remote services to the se Industrial fa ctories. In add ition, to diminish t he deployme nt cost of the communicat ions infrastructure in side each industrial plant, the communication should be sup ported by wireless networks. In this perspecti ve, 5G is a superb candidate to support the co mmunication i n Industria l networks, because it supports thre e esse ntial communication types, i.e. deterministic low-late ncy, massive machine- to -machi ne communication, and enhanced mobile broad band [ 91] . It is expected t hat ultra-reli able wireless co mmunications, suppor ting mas sive communications among the industrial machines, devices, and robo tized actuators , will enable t he development and transformation in smart f actories, while contribu ting to the gro wth of social and economic aspects. However, the engagement of many sensors and other industrial equipment will increa se the amount of data to be capture d, stored, and pr ocessed. This pervasive and exponentially increasing wireles s data traffic is usually char acterized as “big da ta” [92]. Here, an SDN-based architectu re c ombined with a “ big data” engine ca n offer a da ta-driven intelligent net working infrastructure to enable the processing of ma ssive amounts of da ta to obtain usef ul knowledge about each In dustrial process. The data-intensive transfor mation expected to occur in future indu stries will generate not only large amounts of data to be processed but also most of th ose data a re not organized in a clear structure. All t hese facts bring a huge difficulty to h umans who pr ocess th is data in order to obtain useful information t o supervise and manage t he industrial processes. A possible s olution for the las t problem is t o create an autonomous data -driven decision mak ing syste m, using S DN, NFV, a nd ML [93]. In a ddition, ML can be also used to en hance the w ireless broadband acc ess in order to the strict requirements imposed by industrial communicatio ns can be supported in a satisfactory way [94][95]. The role of human-computer interaction in future industries will also incorporate virtual/augmented reality enhanced wi t h h aptic technologies [55]. The se haptic technologies provide the remote human o perator with a true immersive experience on the indust ry plant ’s physical context, with the final g oal of obtainin g a more ef ficient re mote control of th e plant. The haptic information is based on se nsors typ ically physica l object harness, we ight, inertia, and positioning awareness , as well as surface contact geometr y, smoothness, slippage a nd tem perature [55] . In this context, the network needs to support a new type of haptic communicatio n that transmits to t he remote operator correc t and complete f eedback a bout the industry plant status. In this way, the network should offer a medium to transfer in real- time the se nse of touc h ( haptic) and actuation (kinesthetic). Other relevant require ments of the se forms of commu nications include low latency, high throughput, reliability, and intelligent precise coordination (synchroniza tion) among t he diverse flows [96] . Summary of Open Is sues in Analyzed Scenarios of Fog Computing Systems Table I su mmarizes some prominent funct ional aspects from the analyzed FCS scenarios that require further work from the a ssociated research co mmunity. Table I. Summ ary of Open Issues in Analyzed Scenarios of Fog Computin g Syste ms FCS Scenario Open Issue Intelligent Power Grid Systems Anomaly detectio n from insider attackers; protecti on against coordinated cyber-attacks; immunization against data injection attacks in t he control loop 12 of 38 Smart Building Syste ms Deployment of a software -defined management service to enhance t he livi ng c omfort and safety as well as a pr oactive recommendation ser vice for buildin g maintenance tasks Next Generation Mob ile Systems Proactive data caching at t he network ed ge based on several data dimensions: popu larity; spatial; temp oral; energy to data storage, processing, or transfer. Healthcare Systems Offloading of computa tionally intensive data analysis tasks from battery-opera ted embedded devices to fog servers a iming to enhance the batter y autonomy of t hose devices Industry 4.0 (IIoT or Smart Factories) Ultrareliable wireless com munications, supporti ng massive data communications ; autonomous data -driven decision making ; haptic com munications 3.3. Modeling of Fog Computing Sy stems The modeling of a Fog Co mputing System is made using a theoret ical model. A very popula r tool to model and perform syste m analysis is Game theory (GT) . It is a fundamen tal mechan ism to study the various cha llenges and fa ults t hat could aff ect the system n ormal operation. GT ca n a lso enable the design of a utomated mechanis ms t o pr otect the major functi onalities of the system [10]. Nevertheless, theoretical ga me model s may need a significant amo unt of ti me for discovering stable and optimum system co nfigurations. Thi s extra delay introduced by GT may not me et the low latency needs of fog sy stems . We think one way to cope with that problem is to deploy the theoretical model running in the backe nd of the f og system, where the theoretical model acts as a northbound SDN application (SDN is disc ussed in subsection 3.4) . In this way, the theoretical model has an active role in the system operation only in those instants of time where the model potential ly converge s to a viable system configurati on. When the theoretical m odel is running in the backend it will be the SDN controller’s role to ma nage online the CPS’s context . Literature Revi ew for T heoretical Models We have revi ew ed the literature for theoretical m odels in Fog Computing Syste ms distributed in the f ollowing aspects: system resource allocation [19] [23], system reso urce offloading [97][ 98] , system energy efficie ncy [72] [99], and system security [100][101] . A brief ba ckground in GT (non-cooperative, cooperative, and evolutionary ga mes) applied to edge computing is availa ble in [19]. It includes a comprehensive review of game theoretical contributions to wireless commun ication networks. They also discu ss diverse issues t hat ca n be addressed by th eoretical game models to optimize the network performance i n some emerging multi - access ed ge computing sce narios. The a uthors of [23] offer ed a n alternative literature revision in coalitional games am ong o ther alternative techniques, such a s la rge- scale con vex optimization, m ean field game, stochas tic geometry, a nd stochastic optimization. All t hese techni ques can enable a n optimized system resource allocation . In particular , th e mean field games can be applied to analyze scenarios with ma ny resources, devices a nd user types. The authors of [63] proposes a non- cooperative game theoretic model for the management of a smart grid's demand considering the packet error ra te in the game formulati on. In [102 ] is the authors describe a mod el for determining optimal resource a llocation by combini ng GT with a mult i-attribute uti lity model. It allows optimal allocation of the def ender’s budget across potential identified syste m targets and, conside ring different types of countermeasures. The a uthors of [103] pr opose a h ierarchical model betwee n mobile operators and users . They offer a management solut ion for effective ba ndwidth sl icing in software-defined 5G sy stems. Other releva nt functi onal aspect s in FCSs are data offloading [9 7] or computation offloading [98][104][ 105] . In [ 97] the authors outli ne a SDN- based c ontroller enhanced with a game model based on a single leader and multiple followers for a 5G -ba sed vehicular network. This solution a ims to deal with high speed and traf fic congestion wit hin th at network. It enables the v ehicles to perf orm intelligent decisions for data offloading by using the network services of priority manager and load 13 of 38 balancer, which route the traf fic load in an efficient way even within a large netw ork. An other contribution [98] considers a scenario of a heterogeneous cellular network . The authors propose a solution ba sed on a two -stage auction to perform task transfer fro m macr o cell users to small cell s , which are re lay network nodes for task ex ecution. This alleviates the hea vy bur den of macro base stations b y off loading c omputation from macro cell user equipment to s mall c ell ba se s tations or remote cloud . The work in [ 104] offload s user processing tasks f rom the user devices to the network edge. Then, at the network edge the offloaded tasks are scheduled between the remote cloud and edge servers. This task scheduling is performed by an evolutionary algorithm , which aims to protect the quality needs of applica tions a nd their computation-intensive resources. In th ese cases, the available computati onal resources in MEC servers may not be enough to fulfil the computation delay, and conseque ntly the tasks need to be proce ssed in t he cloud servers. In [ 105] the authors pr opose a non-cooperative and distributed game a mong Industrial IoT devices with the assistance of Blockchain. Using Blockchain, the IoT devices could se curely trade distributed res ources wi th other untrusted peers. Their solution transfers heavy resource demanding tasks such as data processing as well as mining fro m IoT devices to the ed ge/cloud servers. There are some literature contributions focused in eith er re ducing the energy consumptio n [72] [99] or def eating jamming attacks [106]. The authors of [72] propose a social ga me aiming to incentivize bu ilding occup ants to m odify their behavior so that the overa ll energy consumption in their roo m is reduced . Aligned with this, [9 9] pr oposes a social game to guarantee energy efficiency for buildings. I nterestingly , [106] uses energy harvest ing as a countermea sure against a po tential jamming attack. The harve sted energy is extracted f rom the ener gy used by t he attacker to jam the channel, and the former is c onsumed to increase the tra nsmission power of benign traf fic. A significant amount of work was made to e nhance the security of FCS s. The au thors of [100] classifies the literature into two classes, viz. security and privacy. Then the y discuss the wo r k in ter ms of the GT model that each contributi on has pr oposed to def eat the va rious cyber -security problems. The a uthors of [101] propose a hierarchical model that a djusts t he strategie s for enabling the selection of wireless channels in such a way that jamming attac ks are avoided. T he work in [107] investigates how a game- of -game c oncept formed by two intert wined games can study the tradeoff between robustness, secur ity, and re silience of a cyber -physical control syste m. The first game is a zero -sum differential game for robust control desig n at the phy sical layer. T he seco nd ga me is a stochastic (explained below) z ero-sum game between an administrator and an attacker for the design of a n effective defense mechanism. By using this game - of -g ame framework, the authors aim to defeat the potential threats originated by attackers exploring the vulnerabili ties not only from the physical part (i.e. the physical plant and control layer) of the system but also from the cyber elements (i.e. communication and network layers) that ena ble adva nced system monitoring a nd intelligent control. Another contribution [ 108] proposes st ochastic gam es for protecting microgrids agai nst cyber- attacks. In a stochastic m odel a dynamic game is pla yed with probabilistic tra nsitions and in a sequence of system steps. Such games start in a given state, a nd then the players select a ctions according to their own status at the time of each system phase. The players receive an immediate payoff according to their status and the actions selected in a probabilistic way. This procedure is repeated through a sequen ce of system steps with each pla yer aiming to obtain t he maximum total utility from the i nteraction with the syste m and wit h others. T he a uthors of [10 9] apply a d ynamic Bayesian game of inco mplete informati on to imple ment cybe r deception b y mea ns of Hone ypot devices in IoT usage sce narios. Honeypots are virtual or physical network devices th at emulate exact network nodes to attract to them potential malign traffic. In this way, two positive outcomes for the network securit y are guaranteed. The first one is to star ve the resources and ti me of the attackers by deviating the bad traf fic from the init ial targets of the atta cks, i.e., the real network nodes, whic h become protec ted from the negative impa ct of th ose att acks. The second ad vantage is to analyze the behavior of each atta ck, including a completely new one, learning fro m the a nalyzed trend of ea ch attack how to develop fut ure eff ective countermeasures to mitigate that attack. 14 of 38 Comparison among M odeling Techniques for Fog Com puting Systems Table II compares FCS mo deling tec hniques i n terms of their strengths a nd weaknesses. T he modeling tec hniques under comparison, in our opinion, a re re levant f or di scovering su itable management decisions to counteract the negative effects of various threats to t he normal operation of an FCS. In addition, [110] discusses further theoretical games in the network/cyber-securit y domain, suc h a s, trust assignment, resource allocation, anomaly detection , information leakage , as well as the decepti on of attackers, network jamming, o r communications eave sdropping. Table II . Comparison of diverse FCS mode ling techniques Modeling Technique Advantage Disadvanta ge Hierarchical Model (e.g. Stackelberg) Can optimize simultaneously diverse system parameters Exposures private data Evolutionary Model Suitable for systems i n which players via tria l and error learn that some strategies are better than others; this process i s repeated until the evolution converges to a stable state amo ng the players of a specific generation ; this stable state represents the be st response for each pla yer. High convergence ti me to reach a stable system state Cluster-Based Model Reward is shared a mong the elements of the same cluster Not suitable for dyna mic systems due to t he high complexity to ma nage clusters Differential Model Suitable for dynamic systems, meaning the players ’ incentives t o make their choices (i.e. , select their actions) change during the t ime the game is played ; the model optimizatio n is done using a group of differential equa tions. For games with m ore of two player s, it could be difficult to evalua te the conditions u nder which such games have a Nash Equilibrium i n the given class of player strategies, because each player la cks complete infor mation about how the game was pla yed (i.e. the game trajectory, the payoff s received) by the other players ; consequently, th e optimiza tion of differential games w ith N players with incomplete informa tion needs more researc h. Potential Game Model The same function runs in each node to optim ize system configurati on A local optimum could b e found instead of the expected global optim um Mean Field Model Can address large -scale and heterogeneous scenarios Players are ra tional, indistinguishable, and influenced only by t he average behavior of others Stochastic Model Dynamic repeated games that allow players to learn reinforced strategie s towards system goals It is very challenging t o timely discover t he equilibria of a stochastic ga me due to its random characteristics a nd large model dimensionality Games- of -game s Model Cross-layered model design where in each New utility functions are needed to represe nt in a formal and realistic ways the 15 of 38 system layer is played a game with features be tter adjusted to both the mai n functionality expected and the involved players in terdependency a mong the diver se games; other open issue is to disc over the holistic equilibria of the ga mes- of -g ames model, considering the bounded rationality of player s, similar to what was prop osed in [111] Non-Cooperative Model Highly suitable for dynamic distributed systems with incomplete information Players cannot learn (wi th no game repeti tion nor cooperation ince ntive) from past acti ons Auction Model Low convergence time because the solution space is further reduced than in the case of GT Every player should trut hfully tell the syste m designer its intent; other wise the model re sult is negatively affec ted Gamification Provides immediate feedback to ai d players adjust their learned skil ls about a specific contex t Replaces other learni ng activities such as simulations, creatin g uniform learned skills, reducing the diversit y and eventually impairing the “ Darw in evolutio n of skills ” Performance Metrics for Fog Computi ng Systems Table III summarizes a sele ction of performance m etrics (or data labels in the c ontext o f machine learning) for FCS s, which dea l with a heterogeneous resource set formed by computati onal, communications, storage, and ener gy assets . These FC S performance metrics ca n be classified in to several types such as data, control, energy, resource allocati on, proces sing, a nd business. All these metrics can be als o analyzed a nd optimized by theoretica l a lgorithms , among ot her possible ways , such as [112] . Table III . Summ ary of selected performance me trics (or data labels) for FCSs Metric (or Data label) Main goal Rate Maximizes the acc ess rate for a dataflow Edge/fog caching Proactive ca ching based on data/service popularity to minimize the access delay to data /service Privacy Level of data /service disclosure to unknown recipie nts Trust Deg ree of confidence in a d ata block /service by non-s ource recipients Localization Data/service d elivery based on consu mer localization Fusion Level of data aggregation and summariz ation Reasoning Level ok knowledge (labels) extracted from da ta features Control delay Selects the controller for an SDN-ba sed node that mi nimizes the delay on the control loop Energy Ma ximizes the energy eff iciency Distributed resource scheduling Allocates in a fair way s carce resources among c ompetitors with distinct requirement s Computation offloadi ng Decision o n deviati ng heavy processing ta sks fr om constrained end- devices to more po werful edge servers Parallel processing Allows the div ision of an original high-complexity processing task into distinct subtasks, w hich are executed in parallel by edge servers 16 of 38 Processing delay Mi nimizes the processing d elay of a computational task CPU/GPU capacity How many operatio ns CPU/GPU can process in a time interval Processing cost Minimizes the proce ssing cost of a computati onal task Virtual micropayme nt Anonymous dynamic payments to incentivize the sh are of heterogeneous re sources among players in distinct ne twork settings 3.4. Novel Prog ramming Approaches to Enhance the Mana gement of Fog Computing Systems This subsecti on discuss es releva nt work associated with some recent approac hes, such as S DN, NFV, or M L, which can enhance the manageme nt of an FCS. A n FCS require s the deployment of sensors, actuators, a nd computing devices at the network edge. FCSs also need to be supervised and controlled de -centrally because of their co mplexity, heterogeneity, and geographica l dispersion. To ensure network- wide resilience, it is funda mental to study the eff icient orchestration [11 3] of a set of SDN applica tions that mu st cooperate amo ng them to f ulfil the global re silience r equi rement s [11 4] . These have distinct goals includin g traffic classificatio n, anomaly detection, or traffic shaping [ 114]. Software-Defined Networking / Netw ork Function Vir tualization for Fog C omputing Systems In para llel, the Quality of Experience (QoE) o f end-use r (or end -machine) service s sho uld be also supported end- to -end, among diverse network domains. To a ddress these requi rements, within each network domain, a Software -Defined Networking (SDN) [1 15] system with thre e levels can be deployed. The top level is formed by Networ k Function Virtua lization (NFV) services and a northbound Application Progra mming Interface (API). The intermedia te leve l is comp osed by an SDN controller or multipl e SDN controllers a nd Southbound API. T he bottom level incorporates networking devices and a gents associated wit h end-us er terminals or end- ‘things’. The SDN controllers can support Quality o f Service (QoS) only within a network domain. Although the SDN contr oller alrea dy has some abstra ction from the hardwa re, that a bstraction is limited, because the S DN contr oller t ypically contact s the Ope nFlow switch-ba sed devices a nd n ot the end-devices. Therefore, in these conditions it is very hard to support user-perceive d QoE. Considering these li mitations, the commu nication ove r the network domains should be made at the top leve l, by means of east-west APIs used by either SDN controller s or NFVs. In a ddition, the end- devices should re port to t he upper sy stem layers (e.g. control and/or m anageme nt) relevant statist ical information about the services in operati on within those devices. I n this way, using the top-level, there is a higher a bstraction level from the network infrastructure and t he end -devices, and it enables powerful manageme nt in teractions among the d omains t o a ssure a re liable end- to -end QoE. We argue that this kind of a pplication-leve l programmabl e inter-domain envir onment is like the one previously proposed in [7 4]. Nevertheless, there is at lea st an important differ ence in the ser vice needs between the previous work and future scenarios. In fact, the former is focused in objective QoS requirements [74 ][75] and the latter is m ore focused on subjective Q oE requirem ents [53]. Thus, the service providers are now shifting their attention from intra- domain QoS fulfil ment to e nd- to -end (and inter-domai n) customer- perceived quality (i.e., QoE). The literature offers severa l pieces of work tha t appl y S DN for Moving Target Defense (MTD) network protection [1 16] in Fog C omputing System s. If a Fog Computing System is protected via MTD, then t hat system re currently modifies its configuration to deter potenti al inspections by attackers into the wa ys the system is configured and operated . The authors of [117] propose to enhance S DN with NFV against penetration attacks. A penetratio n attack is perpet rated by a delive ry method that tra nsports a malign payload to the ta rget system device. Th is m align payload can trigger on the targe t system device the execution of compr omised code which can jeopardize the system normal operatio n. To circu mvent the occurrence of a penetration a ttack on a specific syste m, that system should be compre hensively assessed to ide ntify weaknes ses t hat a n atta cker could expl oit. This verif ication of potent ial system vul nerabilities is designated as pe netration t esting. In addition, the literature has a considerable number of SDN-based solutions to enhance diverse network features, 17 of 38 such as network security [118] [119][120], network communicatio ns [121][122] [123], energy efficiency [124] and network lifet ime [1 25]. The authors of [126] abstract the complexity of the physical world and present to a programmer an abstracted view of that phys ical world. Thus, the programmer can more easily create a system model, pe rform system de bugging or explore the d esign space of various IoT application s. The abstracted view of the physical world is made by using the composition of several “a ccessors”, which are design patter ns that serve as proxies for a ny ‘thing’ or service that may be eit her local or re mote. The accessors offer a similar functionality to t hat offered by a web pr oxy, w hen a client, instea d of downloading a web page from the remote web serve r, alternatively downloads it directly fro m the web proxy. The w ork in [9 3] re views and discusses a daptation features for dep loying scalable and autonomous commun ication systems by mea ns of SDN and NFV, both enhanced by ML . Artificial Intelligence f or Fog Computi ng Systems FCSs are cha llenging to manage because of their high complexity. The complexity is due to both the internal opera tion of each system and the interdependence among systems. A possible way of managing these systems effi ciently is to adopt some aut omatic control functions fro m natural systems that evolved to optimum operation modes with m inimum energy con sumption, ensurin g the survivability of the species coevolv ing in those natural systems . A ligned with these important goals, artificial li fe (AL) is a research are a tha t investi gates natural systems related to c hemistry and biology fields. Acc ording to the tool type used to perform the i nvestigation in t his are a, there are three main types of AL : i) soft via simulation; ii) hard via actua tors or senso rs; iii) wet via biochemistry. We think AL techniques can be very powerful for evaluati ng and manage cyber-resilience in FCSs that show a highly dynamic behavior. A comprehensive coverage of AL techniques combined with self- organization system capabilities is in [1 27] . The evo lutionary trend of AL is d iscussed in [128] and its relevant open issue s are covered by [129]. Another area that can be easily associated with AL is artificial intelligence (AI) , including d eep learning [13 0][131] , random neural networks [13 2] or deep learning with reinforcemen t learning [133] , h ierarchical learning models [101] or a very recent mo del d esignated as brain intelligence [134] . These contributions propose d eep learning and other machine learning (ML ) techniques to autonomously and optimally configure future wirel ess networking environments based on the information learned from network system behaviors . Those ML techniques optimize the model performance of hi gh-complex ity systems in a more ef ficient way t han other legacy a lternatives. Th is efficiency gain occurs beca use ML techn iques discover the optimu m re sults of a system model with small er convergence time, high er accura cy, and are better adjusted to significant system variations than o ther legacy techniq ues that optimize the same system. Another limitation of a legacy technique is it does no t support lea rning, in oppo sition to wha t ML meth ods guarantee [130] . The authors of [133] propose a secure and intelligent architecture for 5G mobile net works and beyond to enable flexible and secure resource sharing. Then, they suggest a Blockchain emp owered content cachi ng problem to maximize system utility a nd they develop a new caching scheme by utilizi ng deep reinforcement learning. A comprehensive survey on deep learning proposals f or m obile and wireless networking is available i n [13 1] . The authors of [135] surveyed the state- of -the-a rt applications o f ML in wireless communication and they pointed out seve ral unsolved issues. T hey divided the body of kn owledge into resource management in t he MA C layer, networking and mobility manage ment in the network la yer, a nd localization in the applica tion layer. In addition, they identified several conditions for applying ML to wire less c ommunication f or a iding interested re searchers decide whether to use M L a nd whic h kind of ML techniques to use. Further, the authors summarized traditional a pproaches together with their performance comparison with ML based approaches, based on which the motivations of previous work to a dopt ML become more evident. For example, ML enables adaptive learning and intelligent decision maki ng in mobile wirele ss networks , due to the ML capability to achieve the convergence the automatic processi ng of ve ry large a nd complex i nput da ta sets a nd the s ystematic enhancement of self -adaptive a lgorithms [13 1][135] . All this i s obtained b y avoidin g t he ma nual preprocessing code obliged by rule -based and legacy tec hniques based on non- learning algorith ms. 18 of 38 A tutorial on artificial neural networks- based ML for wireless networks is available in [136] . They discuss ML solutions to provide intelligent wireless n etworks and realize the full potential of 5G (and beyond) mobile netw orks. Th e learning based on M L techniques in how to i mprove the syste m pe rformance is normall y obtained incrementa ll y , during a considera ble long-term period, and using methods that do no t take in considerati on the und erlying engineerin g principles in arriving at t heir final decisions . Considering what the algorithms have learned (i.e. a set of weights to take the more suitable final decision) to improve the system pe rformance, we ca n designate it as artificial intelligence that can automatically manage t hat system but, in a way, that it could be supervised b y humans. In t his area , the a uthors of [ 134] suggest brain intelligence ( BI) as a new tec hnique in AI to solve some optimization problems that ca nnot be solved by ot her, weak er AI algorithms. They discuss BI usage on scenarios such as a utonomous vehicles, healthcare, and industrial a utomatio n. The authors of [132] investigated the routing opt imization f or software def ined networks ev en in severe use ca ses. They aim t o optimize the QoS of da ta f lows using a cognitive routing engine . Nevertheless, the satisfaction of Q oS requi rements ca n be je opardized when system res ilience / security is miss ing, or even wh en the system has ot her limitations such as limited resources of energy, which is ve ry relevant for scenarios involving I oT devices . A new decentralized ra ndom-access algorithm is i ntroduced in [55] to schedule the Plug-i n Hybrid Electrical Ve hicles (PHEV) charging to protect the d istribution grid from bus co ngestion and voltage d rop, a nd improve the grid efficiency. Ano ther way to deploy learni ng is via either a hierarchical model using S tackelberg g ames [101] or dee p-learning [137]. Further work is clearly ne eded in this field. The current sub section highlights t he grea t impor tance of investigating intelligen t mechani sms to enhance the next ge neration of FCS [138] with new capabilities, e.g. self-awareness of resilienc e against threa ts . T hese new system capa bilities can guara ntee appr opriate performance level s in dynamic scenarios, offer energy harvesting, diminish the consumption of energy , detect and recover from system errors , and pr otect against cybe r-attack s. Th e self-aware management we have just discussed is like the aut onomic (self-orga nized) management of ne tworked systems, which is investigated in [1 39]. The next subsecti on discusses relevant fa ctors for enhancing the re silience of FCSs . 3.5. Key Aspect s for the Resilience of Fog Comp uting Syste ms FCS resilience depends on several key aspects [140] . These are managing complexity, choosin g the correct topology, a dding redundant resources, des igning for ra pid recovery from f ailures in a distributed system, control ling failures and threats, providing adeq uate information buffering, deploying agents to e nforce resilience , and analyzi ng system menace s. Managing Complex ity As network complexity increases , then t he network ’s resilience may be reduced , be cause the failure of a specific network component may cause the failure of other compo nents in a completely unexpected way. The last unpredictable network behavior may be caused by so me unplanned paths within the network that were not reco gnized by the netw ork administrator or designer . Such unexpected behavior is particularly relevant in mu lti-genre or interdependen t networks. These networks have also distinct roles suc h as data communication, computing, data storage, or extract knowledge from ra w data . Therefore, unless a high level o f complexity is need ed to support re silience functions directly, the network complex ity level should be controlled or even reduced . Aligned with this context, the authors of [1 41] discuss the existence of dependencies in comple x syste ms and h ow the ef fect of those depend encies i n systems operation should be characterized and analyzed . The authors o f [1 42] present a metho dology to assess the cyber resilience of a system controlling a specific geographical region. Their methodology can perform a sy stem functional diagnosis identifyi ng system parts that must be protected against cyber -threats, such a s datacente rs and communications networks. Otherwise, i n the case when any of these system parts become exposed to a serious menace , the system perfor mance can be seriou sly undermined. 19 of 38 Choosing the Correc t Topology The choice of t he most ad equate network t opology used wi thin a system can enhance the system ’s resilience [143]. In addition, there are tw o types o f network topol ogies, acc ording to the used node degree distribution in each network. The first type of network topol ogy i s exponential node degree distribution; the second type is scale -free network. So me exa mples of the former type are wireless networks and mesh net works a nd, of the latter type , the World Wide W eb (WWW) a nd power grids. Compa ring the two previous types of net work topol ogies, one can conclude: i) on the one hand, sca le-free gra phs are much more robust to ra ndom node errors t han gra phs w ith an exponential degree d istribution ; ii) while , on the o ther h and, scale-free graphs are muc h more vulnerable to cyber -attacks targeted to some high-degr ee nodes. Adding Redundant Reso urces Providing crucia l additional resources can improve the resilience of a system. As an example, within a power generation plant, when we increa se the number of system nodes, the probability of a system failure ca n be reduced a s well as a quicker service restoration a fter a system proble m. In addition, the additiona l resources should have some distinct chara cteristics among t hem to create diversity wi thin the system, avoiding the ad ditional res ources bei ng affected exactly in the same way by a cyber-a ttack (e.g. a worm attack). S o, combining new but slightly d ifferentiated resources could create a more re silient system [ 144] but the system desi gner s hould be aware of the amount o f sy stem resources (e.g. energy, network nodes) being used to a chieve t he aimed level of system resilie nce . Considering again the energy consumption, the a uthors in [1 45] study a scena rio of a vehicular wireless net work with th e g oal of di minishing the energy consumptio n. To achiev e this, they prop ose a solution that orga nizes t he vehicles and ot her mobile nodes into cluster s. In a ddition, to enhance further the energy efficie ncy they assume some collaboration among the nodes. Nevertheless, cooperating nodes may need to disclose sensitive information to others. This is a n open issue that should be addressed in future work. In addition, [146] explore s t he controller placement problem in the co ntext of software -defined Interne t of Auton omous Vehic les to minimize en ergy consu mption and support load ba lancing under latency limitat ions. Designing for Rapid Recovery from Failure s in a Distributed System The correc tness a nd pe rformance of a fault- tolerant system depend on its underlying rep lication protocols. The authors of [147] propose a hybrid replication protocol that provide s t he h igh performance o f memory- durable techniques w hile offering st rong gua rantees including disk- durable approaches. The key idea of their replicati on protocol is that the repl ication mod e should depend upon t he state t he distri buted system is in at a gi ven time. In t he common case, with ma ny ( or all) nodes up and r unning, th e last solut ion runs in memory- durable mode, thus achieving excelle nt throughput a nd low latenc y; when n odes crash or become partiti oned, the same soluti on transiti ons to disk-dura ble operation , prefera bly flash-based solid-state drive ( SSD ) disks, thus ensuri ng safety at a lower performance lev el. Controlling Failures and T hreats The designer o f a system should protect the sy stem against ca scaded failures. Such failures occur when a node failure triggers a neighbor node failure and so on. To avoid these sequential (cascading) failures, the dep endencies among nodes should be planned to minimize the chance o f a fa ilure easily propagating via n eighboring nodes [143] . In addition, the effect of h uman action s in the way a failure could pr opagate within a system should be also stud ied [148] . The work in [149] evalua tes so me state of the art anomaly detection mechanisms to assess their monit oring a nd dete ction feature s of a challenge or threat to the normal opera tion i n multi-tenant cloud i nfrastructures . They have concluded that elasticity an d live migration of cloud ser vices impair the detection of the tra ffic normal behavior, and conseque ntly its correct isolation fro m the traffic associated to an y anomalous incidents that are likely to be ini tiated. 20 of 38 Providing Adequate Information Buffering To offer robust and timely data access, despite scarce network resources, s ome resilient sol utions based on network bufferin g are very attractive . A s an example, network bufferin g has been used to restore li nk c onnectivity a nd network performa nce fol lowing topological changes in mobile ad hoc networks [150], as well as to diminish the data a ccess delay in disrupti ve -toler ant networks [151]. A major o rigi n of packet loss is related to the cl assical problem of congestion and limitations in network resources (e.g., link bandwidth, router buffers) . In order to pr event network congestion, the network administrator co uld decide on the proactive oversubscription of network resources. However, this strategy resul ts in a signific ant amou nt of net work res ources not be ing used when the networ k load is low, increasing the co st of the network operati on, whi ch in some cases will not be acceptable. Thus , there is a tradeoff between management actions to avoid loss of m essages and the associated costs. A possible wa y ahead is to us e machine learning techniques [1 36] to dete ct the possibility of net work resource contention a s ea rly a s possible. If the resource contention ca n be ide ntified early enough , then packet f orwarding throug h the network can be dynamicall y adjusted so that congestion and thus message losses a re avoided ev en at high network loads. Deploying Agent s to Enforce Resilience To allow a system to absor b a specific failure or a ttack, re cover from that issue, and adapt the system for mitigatin g that problem in the ca se it occurs again, it is necessary t o deploy active agents, either human or artificial. When the active a gents enforcing the sy stem’s resilie nce are humans , they should be trai ned, prepa red, and motiva ted to perfor m the functio ns of absorbing, recover ing, a nd adapting from an eventual failure , as efficiently as possible [148] . Alternatively, artificial intelligence techniques [152] ca n be use d to deploy artificial agents th at, on one hand, carry action s to enforce the problem mitigation and th e system recovery and, on the o ther hand, the same artificial agents maintain a require d level of concealment, exercising a self-defense strategy against the adve rsaries, e.g. malware that aims to discover and destroy the artif icial agents of a system. Increasing the functiona l re dundancy within the agents that manage a network can significa ntly enhance the resilience of network functions in case of a network perturba tion, e.g. loss of some agen ts . Using functional redunda ncy, the system roles ma de by the lost a gents a re reallocated to others. Another advantage of having several agents pe rforming the same fu nction is i ncreasing the system’s scalability against high levels of syst em demand. The authors of [153] describe a distributed decision algorithm supported by diverse S DN controllers to enha nce the recover y mechanism from a problem. The authors of [1 54] review compre hensively the ma jor pri nciples and challeng es for the design of smart Fog Computing Systems that ca n recover at run -time from unexpected faults or threats . Analyzing System Menace s The system atta cker specif ically tries to def eat the absorption a nd recover y efforts of th e resilience stra tegies in order to perpetra te the worst impa ct possible on the system ’s normal operation. In this way, the system designer should pr otect the processes of absorptio n and recovery after a threat so that these processes are less penalized by malicious actions. The wor k in [155][156] [144] propose GT to identify effective strategies a gainst cyber-threats. Any resilience-enhancing measure ca n cause unanticipated effects , leading to a n overa ll reduction in system re silience. Therefore, each resilie nce -enhancing mea sure should be analyzed to check if it could have a potential negative effec t on the system operation. Thus, compara tive analytical studies should be made with and without t he me asure being investigated. Ref. [ 157] offers a numeric al re silience definition t hat allows syste m designers to assess in a more formal way how much the system resilience could change a fter a set of syst em altera tions a re performed. It can also compare the resilience between either distinct systems or various design options of the same system. In addition to the releva nt f actors to enhance the resilience of Fog Comp uting Systems, w hich were discussed in the curr ent subsection , the re ader can consult [13] to obtain an alternative set of attributes that a system s hould satisfy in order to be come more resilient agai nst diverse kinds of system f aults namely errors, failures or attacks. Further , [26] classifies typical faults present in a SDN - based system. 21 of 38 The following S ection discusses a proposed design to enhance the operation of lega cy Cypher - Physical Systems ( CPSs) by deploying the tec hnologies and other aspects previously discussed in the current Section to wards a new generation of more resil ient CPSs, which we generica lly designate in this paper as Fog Co mputing Systems . 4 . Hierarchica l Design of a Resil ient Fog Computing and IoT System Th is Section di scusses desig n aspects t hat are im portant to consider in a re silient Fo g Computing and IoT System . Ta ble IV presents a four- layered h ierarchical architecture that ca n detect, absorb and recover, and ada pt to threats against Fog Computing a nd IoT Systems [8 ]. The bottom layer of Table IV measures, collects (typically inside a lo ca l IoT domain), and stores data obtained via either physical or virtualiz ed devices. T he detection and absorbing of threats a gainst a Fog Computing Sy stem ( FCS) is made via interface chip programming. The second layer of the architecture visualized in Table IV aims t o distribute a common pool of available resources, such as, communications, storage, processing, or services. Thi s layer is typicall y responsible for a si ngle intra -domain usi ng devices that excha nge dat a using a single communications protoc ol. The exchange of da ta is controlled by flow rules stored within local device s and queues to give differentiated QoS to flows. Alternatively, th e QoS support can be deployed based on flow type (e.g. video strea ming , interactive, best effort), enhancing the system scalability, because the same flow type can a ggregate many individual traff ic flows. The third layer of Ta ble IV aims to c ontrol the data pla ne topology and how the tra ffic should be transferr ed throug h the available topological links. This la yer is a lso essential to support the feedback loop bet ween the cyber and physical worlds. Th e curre nt layer uses S DN -based solutions to contr ol a heteroge neous int ra -domain c ommunicat ions infrastructure , forme d by diverse area networks with disti nct networking ra nges, such as home, large buildin g, or corporative enter prise. The normal operation o f e ach area network ca n be protected via an SDN-based framework a s suggested in [158 ]. This framewor k creates a secur e perimeter a round a network domain, pr otecting it in a completely d istributed way from the negative impact induced by several types of cyber-atta cks. A possible enha ncement on this framewor k ca n be achieved by modifying it to also detect and mitigate any funct ional failure or even functional degr adation on the net work topolog y. The fourth and topmost layer of Table IV is the management layer. It supports service discovery , service compositi on , service ma nagement , a nd service interfa ces. Fir st , the service d iscovery aim s to verify if a required service is available within a specific system . Second, the service compo sition aggregates diver se services, coordinating among them , as if these services operate has only a single service. Th e service integra tion is useful in a scenario where to sati sfy a specific system re quest then several system services need to be processed for that request in a pre-defined o rder . Third, t he service management manage s and determines the trust mecha nisms to satisfy in a resilient way the service requests involving diver se internal services . Fourth and finally, the serv ice interface s are used to support interactions among a ll the provided services within the management layer . Th e last layer aggregates severa l approa ches, such as NFV a nd SDN . Th e current la yer also deploys a heterogeneous in ter-domain co mmunications infrastr ucture, formed by diverse area networks with distinct networking ran ges, such as street, digital city, or wide area. The topmost layer (Cyber, Social) of our proposed architecture supports the f unctional requirements of eit her huma n users or age nts. The applica tion layer support s applicatio ns used within FCSs with embedded sensors and actuators including smart grid, smart transportation, smart cities, smart homes, smart farming, smart health ca re, smart l ogistics, or smart i ndustries . Most of these applications are completely distributed , among diverse netw orking domains , which brings new security challenges. To addre ss these security cha llenges, we envision sev eral ways, usin g middleware [159] [160] along with other more recent options, such as Bloc kchain s mart co ntracts [161][162] . These solutions should offer a secure management fu nctionality to en sure a resilient and well-coordinated FCS operation. Using smart contracts , it is possible to deploy trustful roaming (peer to peer) services among nodes belonging to dis tinct n etwork domai ns, avoidi ng the use of externa l communication entities to enforce security, such as key distribut ion centers. Another adva ntage of 22 of 38 using distributed smart co ntracts is hig her resilience against net work failures. The a uthors of [163 ] proposes a smart contra ct for collab orative edge learning , ensuring authentic and correct message exchange during the tra ining process , a nd d etouring the behavior of malign entities. The mode lling of Blockchain-based proposals is comprehensively disc ussed in [164 ]. The require ments of emer ging appl ications ca n be s pecified in YAN G service modules [165] , including a description of how each applica tion is expecte d to be experie nced by the customer . To give an example, a service model can be associated w ith vide o traffic . Then, YAN G service modules are processed to ide ntify the (network, proce ssing, storage, etc .) intents [166] [167]. For example, a network i nt ent could be “optimize my network for enhancing vide o QoE”. Then, the intent is translated to a ma nagement policy. This specifies a logical (Boolean) condition to fire an action. Th e action is defined independ ently of the networking device that will be deploying that action. This action co uld be “ send the re ceived message to the more suitable next-hop int erface to the final destination ” . The next an d final step is to convert the management policy to specific device rules . Performing this final conversion, the ma nagement pol icy action “ send the received message to the more suitable next-hop inte rface to the final destination ” is converted to some specific a ctions on the data plane device. In this case, supposing a dev ice such as an SDN -based switch, the f ield action of th at device rule could be , “ Output: port 2 ” , where “ po rt 2 ” is the switc h port number two. The initia l managemen t inten ts and/or policies can be adjusted (or indeed augmented) by Machine L earning ( ML) [168] algorithms. These a lgorithms learn from the system operati on and build a sort of Artificia l I ntelligence (AI). This self-a wareness capa bility is p ossible a fter a set of consecutive successful adjustments on the s ystem configura tion. A syste m configuration adjus tment could occur after the sy stem being in operation, during a specific time interval (i.e., epoch), using the previous sy stem configurati on. In this way, the to p-level layer can collect the system stati stics, durin g the previous time interval, and deliver th e statist ics (e.g., using input attribute weights) to ML/A I algorithm . Th en , th is alg orithm for indirect ly i mproving t he video QoE (e.g., the video Qo E is represented via a function output) ca n decide to notify the Intent Engine (e.g., using output attribute weights). Thu s, the Intent E ngine changes from the current ma nagement p olicy to an other one. Thi s new manage ment polic y is then converted by the S DN Controller to a set of novel rules, whic h are pushed via a Southbound API to the da ta plane d evices being used by t he optimum video data pat h through the network infra structure. The functionality whic h we have just described can be summarized such as a n ob servation (i.e., collect of sta tistics) – action (i.e., set of novel rule s for the data plane devices) loop. T his new type of ob servation -action control loop, made possible via the SDN paradigm, ca n be seen as a promising ba sis for inc orporating in the man agement of futur e networks s ome p owerful se lf-driving capabilities [93]. This new manage ment of future networks will be completel y opposed to the closed -for m models of i ndividual pro tocols [169 ], such as the control of networ k conge stion by active queue management [170 ]. In fact, the management of a self -driving network, in opposition to the lega cy management o f network reso urces, implies the n ext new aspects [169]: i) the network mea surement is ta sk-drive n and tightly integrated wi th t he contro l of the network; ii) the network control relie s on large -scale analysis over the acquired data from the global operation of the networke d system ; a nd iii) the major outcomes from th e last analysi s form an important system learn ing asset to orche strate and effic iently control the network available resources. Table IV. Hie rarchical Design of a Resilie nt Fog Computing and IoT System Layer Plane Domain FCS Activity [8] Goals Tools 4 In telligent management (Cyber, Social) Inter/Intra Adapt Reasoning, orchestration, full abstra ction, Yang service models , intents , management policies NFV, SDN, Intent Engine , ML /AI 23 of 38 3 Control Intra Adapt, recover Partial abstraction, topology, traff ic, control actions, system status Software-Defined Controller with link layer discovery, forwarding, and feedback loop 2 Switching Edge Detect, absorb, recover Decision about next link decision, traffic mirroring, discard packet OpenFlow rules in local device tables, queue s 1 Sensors, A ctuators (Physical , Virtualized) IoT Detect, absorb Accept or discard received message Interface Chip programming The next S ec tion deba tes the lessons learned along the curre nt paper and open research issues. 5 . Lessons Learned and Open Issues This S ection summarizes and highlights the mai n f indings fro m the analysis and reflection in our pape r. We start b y deba ting in ter esting ways to enhance th e management of resilient FCSs. Then , in subsection 5.2 we discuss the deployment of network sl ici ng proposals to empower resilient FCSs. Subsection 5.3 deals with the promising area of data fusion for resilient FCSs. In addition, subsection 5.4 discusses literature wo rk related to proactive and pr eventive mainte nance o f systems that we envision co uld be also applied with great succe ss to resilie nt FCSs. Then s ubsection 5 .5 debates the relevant future need to efficiently disseminate data in re silient FCSs. Fi nally, subsection 5.6 investigates the integra tion of Blockc hain and Machine Lea rning for resi lient FCSs. 5.1. Interesting Prop ects on the Enhance d Management of Resilient Fog Computing Systems We consider now interesting aspects for further improvement on the management of FCSs in hazard scenarios. We envision the desig n and programming of intelligent solutions that provide and optimize the autonomic management of interconnected heterogeneous FCSs , orchestrating the available system res ources in an a bstracted, elastic, flexible, and stable ways . This new co ntext ca n support the model of dete ct-absorb-re cover-adapt discussed i n Section 4 [8], which ca n be use d towards a resi lient systems - of -systems [9]. This ca n be successfully appl ied to va rious FCS scenarios with networking infrastructure s (see Table V ) for fulfilling the goals of energy efficiency [124] , quality provision [171] , computation offloading [105] , mobility support [17 2] , data fusion [173 ] , data offloading [17 4], threat ma nagement [17 5], and onlin e optimizatio n for di stributed fog ne tworks [176]. We detail be low t hese r elevant g oals to e nhance the rob ustness of FCS s and consequently enhance their performance in adverse situations. Considering that many d evices in FCSs are ba ttery- operated, then the aspect of increasing the energy efficiency in those system s becomes very relevant. When the ava ilable energy in each batter y is used in a more eff icient way the sy stem operational lifetime is increased. In a ddition, the system sustai nability is improved . Table V. Applying the model of de tect/absorb an d recover/adapt [8] to various FCS scena rios Scenario Goal Detect (even t- based) Absorb and Recover (Control) Adapt (Learn) Mesh network formed by IoT battery- operated devices Routing with energy efficiency Detect netw ork devices with a low-level of battery via associated events Do not select routing paths using network devices with lo w energy in their batteries Balance the tra ffic load through diverse pa ths to guarantee a f air depletion of battery among all the network devices 24 of 38 Quality provided by network slicing To guara ntee the delay of a specific flow type is constrained to a maximum Event originated by a high packet delay Select a lternative path or discard some packets Based on historical data analysis performs a proactive load rout ing Computation offloading from end-user devices to edge servers Efficient usage of end-user device with limitations on computational resources Events originated by high CPU utilization a t en d-user devices End-user device with maximu m CPU uti lization during a specifie d time a lleviates its burden by mov ing the execution o f some tasks to servers at the network edge Based on historical data analysis , performs proactive actions of computation offloading Mobility support Guarantee a pervasive access to data and services Events originated by end-user mobility, active message flows, and a vailable resources Offer a sea mless flow handover among distinct mobile access networks Based on previous learne d mobility behavior s , disseminates in advance through the edge of the network infrastructur e several replicas of message flows and/or services Data fusion To shrink t he high data volume from IoT devices to a much lower data volume, and reduce resources Events from heterogeneous sensors transport raw data Edge network devices aggregate and synthetize useful information from the received ra w data Based on historical data analysis, opti mizes th e methods to mer ge and extract useful k nowledge from the received IoT data Data offloading Edge data caching ba sed on spatio- temporal popularity Events originated by high end to end Round Trip Time between a request and its reply Stores data replicas at diverse edge network nodes Based on historical data analysis, perfor ms a proactive data replication at selected network nodes Threat management Mitigation of system threats Events originated by threat detection ; events are classified as “malign traffic” or “packet is lost” If threat is “malign traffic” then “d iscard malign pa ckets” elseif threat is “packet is lost ” then “select an alternative and more robu st path” Based on historical data, th e FCS can a utonomously adjust the previous acti on against a future occurrence of the same (or similar) incident, and a trust indicator; t he value of this trust indica tor shows how well that action coul d mitigate the associated incident. Computation offloading Jointly optimize the formation of Fog nodes events originated by Offloading computational tasks to selected To minimize the maximum latency when computing a new task that arrives a t a fog 25 of 38 among fog and cloud servers fog net works and the distribution of computational tasks in a hybrid fog- cloud system with dyna mic fog nodes their arrival , their mobility pattern , their localization, their local ca pabilities, their support o f micropayments neighboring fog nodes and the cloud node under uncertain behavior of other fog nodes 5.2. Network Slicing for Resilient Fog Comp uting Systems IoT devices pr oduce a lot of data demanding a large amount of network resources, and the best - effort a llocation of networ k resources may not be eff icient. To overco me this, it will be interesting to investigate novel wa ys to manage system resources, such a s network slicing [171]. Network sl icing is a technique that allocates to each data flow a dedicated set of network resources, according to the specific QoS/QoE requirements of that flow. To scale out the system management solution instead of allocating network resourc es to individual data flows, the resources should be allocated to data flow types (e.g. video, gaming, best -effort). This is like the classic DiffSer v QoS strategy that (per domain) classifies, marks, polices, and shapes the incoming traffi c class. In contrast to DiffServ , network slicing can be used to meet the dema nds of vertical applications in 5G net works , across multiple d omains , end- to - en d , as discussed in [177] . To realize the network slicing goals, we need software that automat es t he crea tion, supervision, and deployment of resources and services in the underl ying virtualized context . This software is normally an orchestrator of both services and system resources . Ref. [177] discusses open source orchestrators for network slicing, such as Ope nMANO, Ope nBaton, OPNFV, M-COR D, or ONAP, among other s. En d-user dev ices ha ve se rious limitations on co mputational resources . In this way, s ome im portant system pe rformance gains can be obtained as some heavy- processing tasks are moved from the resourc e-constrained end-user devices to mor e powerful serve rs at the network edge [105] . This distributed management of tasks offers the simult aneous advantages of finalizing quickly those tasks and increasing th e b attery autonomy of ba ttery-opera ted end-user devices. In the opposite direction o f what we hav e just dis cussed, [178] debates future directions i n networked control systems, where the execution of dela y-sensitive tasks, such as the control of robotiz ed arms, can be automatically offloaded fro m re mote systems t o f og c ontroller nodes, giving significant gains in the control accuracy of field devices. The authors of [172] propose a soluti on based on n etwork slic ing to supp ort seamless flow handover among mobile acc ess networks . Neverthel ess, they a cknowledge tha t further research work is necessa ry in pr oviding end- to -end network slicing to address the f ollowing ope n issues: network reconstruction ov er heterogeneous technologies , the high complexity and difficulty of slicing management, and the lack of cooperati on with other 5G technologies such as C-RAN, SDN, and NFV. Further rela ted research directions a re in [179] . As these open issues will be succes sfully endorsed, some interest ing and relevant fun ctional o utcomes can be obtained namely sea mless mobility, high transmiss ion rate , ultra- low guaranteed latency and jitter. These aspects are essen tial to supp ort robus t loop controls through the future data communica tions i nfrastructures, which should support both a reliable, efficient, and timely exchange of da ta among machines, a gents (algorithms) or e nd-user devices. A very recent tech nology d esignated as Segment Routing for IPv6 (SRv6) has be en invest igated in bot h the standardiz ation and research communities to build novel distributed processing mo del s on top of the network layer , a nd for various networking deployme nt scenarios [1 80] . The authors comprehensively survey and discuss segme nt routi ng, including SRv6. They also point out possible future re search dire ctions, and d omains in wh ich seg ment rou ting wo uld bring benefits , namely: i) service functi on chaini ng support; ii) srv6 end-h ost implementat ion aspects; iii) cloud orchestration; iv) mobile 5G; a nd v) IoT. 26 of 38 5.3. Data Fusion for Resilient Fog Comp uting Systems Due to the high level of heterogeneity and complex ity of diverse Fog Computing systems as well as the need for a hig h- level of interoperability, ma nagement solutions with “fusion - enabled” capabilities [86] [181][173] have been re cently proposed . These use distinct system arc hitectures such as the Internet and Information C entric Networkin g (ICN) for efficiently sharing common resource s via interoperability entities [86] . Alternatively, the same fusion -enabled capabili ty ca n be applied to merge and process hetero geneous data from mul tiple sources , leading to better estimation a ccuracy of the status of managed physi cal syste ms [18 1][173]. T he da ta fusion met hods can be classified based on the data space of each use case, namely Fog Computin g space fusion, Cyber -Social space fusion, or Cyber-Physical-S ocial space fusion [181] . Considering t he most complex ca se, the auth ors of [ 181] discuss a Cyber-Phy sical-Social S ystem that aims t o pre dict multi - users’ mobility pattern by solving a cubica l User- Spatio-Temporal pr obability arising from heterogeneous sensor data. To solve the stationary probabilit y map, they refer to a tensor -based iterative algorithm to merge and process sensor data from m ultiple sources, namely time, space, and social network. The algorithm seems promising for the prediction accuracy and associated c onverge nce time. In a dditio n, other important aims are to perform data fusion securely as well a s preserving data privacy [173 ]. 5.4. Proact ive and Preventive Maintenance of Resilient Fog Computing Systems Future resea rch in high -level prepa redness against threats to FCSs s hould cert ainly include proactive and prev entive maintenance using ei ther discrete -time [182 ] or continuous- time control [175] of IoT systems, incident protection [111], short mitigation times, a nd fast reco very. It i s also ve r y important to pay more att ention t o the sce nario of mult iple t hreats simultane ously affecting the normal operation of an FCS. The diverse aspects to be e nhanced s hould be studied no t o nly a t s ystem runtime but initially at its d esign [12 ], including the protecti on of the physical infr astructure aga inst weaknesses recently rep orted [6 ]. Moreover, the FCS design enhancement s hould not only c onsider the protec tion again st thre ats but other relevan t aspe cts such as t he qua lity of service offer ed to system clients and the e nergy consumed by sy stem [18 3]. 5 .5. Efficent Data Dissemination in Resilient Fog Computing Systems The data transfer is exp onentially increasi ng through the c ommunications infrastructure of FCSs. Nevertheless, the fa st transfer of data can be adversely affected by high mobility a nd congestion , essentially in mobile networks . To diminish the data transfer time, the author s of [174] propose a solution that est imates the c ontent popular ity. The n , that content pop ularity i s used to decide about which conten t i s offloaded from remote clouds a nd cached at Base S tations to achieve higher user satisfacti on and backhaul offloadin g. As future work, the c ontent popularity can be evaluated combining several da ta-related dimensions such as spatial, temporal, mobility behavior and resource ava ilability, including energ y [184] . Future networks shou ld provide on-time delive ry of flow pa ckets, respecting latenc y constraints , i.e. delay al ways in the range, [dela y_min, delay_max] , for ea ch application [39 ]. This new behavior should be a distinc t improvement on current network services where service qua lity may va ry according to the networ k load . The TCP transport protocol s hould be also revisited , specifically its algorithm for control ling end- to -end congest ion together with the right buffer size for ro uting devices [185 ]. Emerging applications will req uire the simultaneous satisfaction of severa l requirements , in very precise and sca lable ways, especia lly those of throughput and la tency. However, resilience should also be fundamental ly guaranteed for applications that demand it, spec ifically for remote sur gery or autonomous vehicle drivi ng applicatio ns. Further, urgent, investigati on is required in these are as. 5.6 . Blockchain and Machine Learning Integ rated Solutio ns for Resilient Fog Computing Systems As was discussed in subse ction 3. 1 , PKI is a hierarchical centra lized model that validates the authenticity of digital certificates. This centralized mana gement of net worked resources presen ts 27 of 38 several limitations including the low level of offered resilie nce against system thre ats. Alternativel y, management solutions tha t rely on more decentralized a nd distributed operating modes seem preferable than the ir centralized coun terparts for managing resilient com putational resources of both remote and fog networked infrastructures. To guarantee all these conditions in a scalable way, the deployment of solutions involving Blockchai n seem pr omising [186] . Nevertheless, p opular Blockchain solutions such as Bitcoin a nd Ethereum, which are da ta-ba sed, are often limited by scalability challe nges a nd latency in tra nsaction processing , due to the scarcen ess of computi ng resources at the network edge to guarantee a universal conse nsus among miners to wards the final decision about how to update the centralized chain. T o mitigate the li mitations of da ta-ba sed virtual currencies , t here are other alternatives based on age nt-centric architectures such as Holochain [187] . It enables a ny device to have its own cha in-based ledger system. T his allows every device on a sy stem to func tion i ndependently, and requires data synchronization only when necessa ry, e. g. to supp ort data redundancy which is usef ul to give resilience agai nst an agent failure . The sharing of data among agents is made via a distributed hash tab le. In this way, Holochai n ca n supp ort m ore scalable distributed applications with data integrity that can run in mobile battery-operate d terminals, which are normally constrained in ter ms of computationa l c apabilities and available energy . In addition, other possible s olutions in the literature for h ow th e system should be managed in a resili ent manner are auctions [188 ] or innovative business models [ 189]. Other work [190 ][191] proposes not only Bl ockchain but its c ombination with machine learning to manage edge com puting scena rios with IoT devices more scalably and efficiently. The convergence of edge computing and dee p learning is c omprehensively investigated in [19 2]. The a uthors discuss the scenario o f dep loying d eep-learning algorithms at the netw ork edge to enforce intelligent ways to manage the re sources a vailable at the ne twork peripher y am ong the diverse system nodes . In addition, Blockchain (or Holocha in) can be used to su pport trus t a mong t he ed ge devices as well a s giving enough incentives t o the ir coopera tion towards com mon system objective s. Further research is needed to find so lutions for the goals of [ 192]: i) e xecuti ng complex d eep lea rning computation s ; ii) supporting the live offloading of microservices t o reduce service latency, energy cons umption, or service unavailabili ty; and iii) orche strating assets am ong t he cloud and distrib uted ed ge servers to achieve better network operation al performa nce. 6. Conclusion Th is paper has explored the provision of future Fog Computing Systems (FCSs) from the perspective of the litera ture on resilience properties for moder n Cyber-Ph ysical Systems supported by IoT a nd edge c omputing elastic re sources . Our discussions covered key use cases, notably t hose of pow er grids, smart bui ldings, mobile networks, h ealthcare , and Industria l IoT . We reviewed w ork that aggregates GT , SDN/NFV, and multi-access ed ge computing for enhancing system re silience and maintaining normal system operation under d istinct and serious t hreats. We a lso discuss ed system design a nd how SDN-based theoretical model algorithms can be used to opti mize system operation with respect to well-identi fied goals such as energy efficiency, computation and data offloading, management of flow qualit y, and IoT data fidelity. A long the wa y, relevant topics for further research in this increasingly importa nt resea rch area have been identified. Funding: Th e work of Jose Moura is funded by FCT/MCTES through n ational funds and when a pplicable co - funded EU funds under the project UIDB/EEA/50008/2020. Acknowledgments: Jose Moura acknowledges the support given by Instituto de Telecomunicações, Lisbon , Portugal . Jose Moura is grateful to Beatriz Moura for her initial work on the pa per figures . David Hutchison is grateful t o m any colleagues in the EU COST Action RECODIS (CA15127) for discussions on the resilience of communication systems. We thank the reviewers very much for the ir constructive and positive c omments, which have help ed improve the quality of th is pa per. References [1] J. Lin, W. Yu, N. Zhang, X. Yang, H. Zhang, and W. Zhao, “A Survey on Internet of Things: Architecture, Enabling 28 of 38 Technologies, Secur i ty and Privacy , and Applications, ” IEEE Interne t Thi ngs J. , vol. 4, no. 5, pp. 1125 – 1142, 2017, do i: 10.1109/JIOT.2 017.2683200. [2] B. Bordel, R. Alcarria, T. Robles, a nd D. Martín, “Cybe r – physical systems : Extending perv a sive sensi ng from c ontrol theory to the Internet of Things, ” Pervasive Mob. Comput. , vol. 40 , pp. 156 – 184, 2017, doi: 10.101 6 /J.PMCJ. 2 017.06.01 1 . [3] J. Qin, M. Li, L. Shi, and X. Yu, “Optimal Denial - of -Se rvice Attack Scheduling With Energy Constraint Over Packet- Dropping Netwo r ks,” IEEE Trans. Automat. Contr. , vol. 63, no. 6, pp. 1648 – 1663, Jun. 2018, doi: 10.1109/TAC.2 0 17.2756259. [4] J. P. G. S ter benz et al. , “R esilien c e and surv i vability in communicati on netw orks: St r ategies, p rinciples, and su rvey of disciplines,” Com p ut. Networ ks , vol. 54, no. 8, pp . 1245 – 1265, Jun. 2010, d oi: 10.1016/j.c omnet.2010.03. 005. [5] Carnegie Mellon University, “CERT Vulnerab i lity Notes Database.” Accessed: Aug. 10, 2019. [Online]. Ava i lable: https://www.kb.ce r t.org/vuls /bypublished/desc/. [6] Ci sco, “Cisc o Secure Boot Hardware Tampering Vulner a bility.” Accessed: Aug. 10, 2019. [Online]. Available: https://tools.cisc o .com/secu rit y/center/c ontent/CiscoSecu rityAdviso ry/cisco - sa -20190513-secureboot. [7] L. Da Xu and L . Duan, “ Big da ta for cybe r physical systems i n indus tr y 4.0: a survey,” Enterp. Inf. Syst. , v o l. 13, no . 2, pp. 148 – 169, 20 19, doi: 10.108 0 /17517575.2 018.1442934. [8] E. B. Connelly, C. R . Allen, K. Hatfield, J. M. Palma - Oliveira, D. D. Woods, a nd I. Linkov, “ Featu r es of resilience,” Environ. Syst. Decis. , vol. 37, no. 1, pp. 46 – 50, Ma r. 2017, doi: 10.1007/s10669-017-96 3 4- 9. [9] P. Uday and K. Marais, “Designing Resilien t Systems- of - Sys tems: A Survey of Metrics, Methods, a nd C hallenges, ” Syst. Eng. , vo l. 18, no. 5, pp. 4 9 1 – 510, 2015, do i : 10.100 2/sys.21325. [10] S. Rass, A. Alshawish, M. A. Abid, S. Schauer, Q. Z hu, a nd H. De Meer, “Physical Intrusion Games — Optimizing Sur veillance by Simulation and Game Theory,” IEEE Access , vol. 5, pp. 8394 – 8407, 2017, doi: 10.1109/ACCESS. 2017.2693425. [11] A. Alshamrani, S. Myneni , A. Chowdh a ry, and D. Huang, “ A Survey on Advanced Persistent Threats: Techniques, Solutions, C hallenges, an d Re search Opportun ities,” IEEE C ommun. Surv. Tutorials , p. 1, 2019, doi : 10.1109/COMST .2019.28918 91. [12] M. Wolf and D. Serpanos, “Safety and Security in Cyber -Physical Systems and Internet- of - Things Systems,” Proc. IEEE , vol. 106, n o. 1, pp. 9 – 20, Jan . 2018, doi: 10. 1109/JPROC. 2017.2781198. [13] D. Ra tasich, F. K halid, F. Geissler, R. Grosu, M. Shafique, and E. Bartocci, “A R oadmap T oward the R esilient In ternet of Things for Cyber- Physica l Systems ,” IE EE Access , vol. 7, pp. 13260 – 13283, 2019, doi: 10.1109/ACCESS.2019. 2891969. [14] A. J. Fe rrer, J. M. Ma rquès, and J. Jorb a, “Towards the decentra lised cloud: Su r vey on appr oaches and challenges for mobile, ad hoc , and edge compu ting,” ACM Com p ut. Sur v. , vol. 51, no. 6, pp . 1 – 36, Jan. 2019, d oi: 10.1145/3243929. [15] M. Mehrabi, D. You, V. Latzko, H. Sal ah, M. Reisslein, and F. H. P. Fitzek, “Device -Enhanced MEC: Multi-Access Edge Computing ( MEC) Ai ded by End Dev i ce Computation and Caching: A Su rvey,” I EEE Access , vol. 7, pp. 1 66079 – 166108, 2019, d oi: 10.1109/A CCESS.2019.2953172. [16] A. P raseed and P. S. Thilagam, “DDoS Attacks a t the Application La yer: Challenges and Research Perspectives for Safeguarding Web Applications ,” IEE E Commun. Surv. Tutorials , vol. 21, no. 1, pp. 661 – 685, 2019, doi: 10.1109/COMST .2018.28706 5 8. [17] P. Mishra, V. Varadhar a jan, U. Tupakula, and E. S. Pilli, “A Detaile d Investigation and Analysis of Using Machine Learning Techniques for Intrusio n Detection,” IEEE Commun. Surv. Tutorials , vol. 21, no. 1, pp. 686 – 728, 2019, doi: 10.1109/COMST .2018.2847722. [18] R. Alguliyev, Y. Imamverdiyev, and L. Sukhostat, “Cyber - physic a l systems a nd their security issues,” Comput. Ind. , vol. 100, pp. 2 12 – 223, 2018, doi : 10.1016/J.C O MPIND. 2018.04.017. [19] J. Moura and D. H utchison, “Game Theory for Multi -Access Edge Computing: Survey , Use Cases, and Future 29 of 38 Trends,” IEEE Com mun. Surv. Tutorials , vol. 2 1 , no. 1, pp. 260 – 288, 2019, doi: 1 0.1109/COMST .2018.2863030. [20] S. Dobson, D. Hutchison, A. Mauthe, A. Schaeffer - Filho, P. Smith, and J. P. G. Sterbenz, “Self - Or ganiz ation and Resilience fo r Netw o rked Sy stems: Desi gn P rinciples a nd Open Research Issues, ” Proc. IEEE , vo l . 107, no. 4, pp. 819 – 834, 2019, doi: 1 0.1109/J PROC.2019. 2894512. [21] E. O ’ Dwyer, I. Pan, S. Acha, a nd N. Shah, “Smart energy systems for sustaina ble smart cities: Current d evelopments, trends and future direct ions,” Appl. Energ y , vol. 237, pp. 58 1 – 597, Ma r. 2019, doi: 10. 1016/J.APE NERGY.2019.01.0 24. [22] J. Xie et al. , “A Survey of Machine Learning Techniques Applied to Software Defined N etwork i ng (SDN): Research Issues and Challenges,” IEEE Commun. Surv. Tutoria ls , vol. 21, no. 1, pp. 393 – 430, 2019, doi: 10.1109/COMST .2018.28669 42. [23] Y. Teng, M. Liu, F. R. Yu, V. C. M. Leung, M. Song, and Y. Zhang, “Resource Allocation for Ultra -Den se Networks: A Survey, Some Research Issues and Challenges,” IEEE Commun. Surv. Tutorials , p. 1, 2018, doi: 10.1109/COMST .2018.28672 68. [24] F. Al- Turjm a n, E. Ever, and H. Zahmatkesh , “ Sma l l Cells in the Forthcoming 5G/IoT: Traffic M o delling an d Deployment Overview,” IEEE Commun. Surv. Tutorials , vol. 21, no. 1, pp . 28 – 65, 2019, doi: 10.1109/COMST .2018.28647 79. [25] X. Huang, S. Cheng, K. Cao, P . Cong, T. Wei, and S. Hu, “A Surv ey of Deployment So l utions and Optimization Strategies for Hy brid SDN Networks,” IEEE Commun. Surv. Tutorials , p. 1, 20 1 8, doi: 10.1 109/COMST.2 018.2871061. [26] Y. Yu et al. , “ Fault Management in Software - Defined Networking: A Survey,” IEEE C ommun. Surv. Tutorials , p. 1 , 2018, doi: 10.11 09/COMST. 2018.2868922. [27] R. Hussain and S. Zeadally, “ Autonomous Cars: Rese arch Results, Issues and Future Challenges,” IEEE Commun. Surv. Tutorials , p. 1, 2018, doi: 1 0.1109/COMST. 2018.2869360. [28] R. Du, P. Santi, M. X iao, A . V Vasilakos, and C. Fischione, “The sensable city: A survey on the deployment and management for smart city monitoring ,” IEEE Commun. Surv. Tut orials , p. 1, 2018, doi: 10.1109/COMST. 2018.2881008. [29] W. Ay oub, A. E. S amhat, F. Nouvel, M. Mr oue, and J. P r evotet, “In ternet of Mob ile Things: Ove rview of LoRa WAN, DASH7, and NB- IoT in LPWANs standards and Supported Mobilit y,” IEEE Commun. Surv. Tutorials , p. 1, 2018, doi: 10.1109/COMST .2018.28773 82. [30] N. C. Luong, P. Wang, D. Niyato, Y.- C. Liang, Z. Han, a nd F. Hou, “Applications of Economic and Pricing Models for Resource Management in 5G Wireless Networks: A Survey,” I EEE Commun. Surv. Tutorials , p. 1, 2 018, doi: 10.1109/COMST .2018.28709 96. [31] N. Sun, J. Zhang, P. Rimba, S. Ga o, Y. Xiang, and L. Y. Zhang, “Data -driven cyber secu rity incident prediction: A survey,” IEEE Comm un. Surv. Tut orials , p. 1, 201 8, doi: 10.1109/C O MST .2018.2885561. [32] F. Hu et al. , “Robust Cyber–Physical Systems: Concept, models, and implementation,” Futur. Gener. Comput. Syst. , vol. 56, pp. 44 9 – 475, Mar. 201 6 , doi: 10. 1016/J.FUTURE.2 015.06.006. [33] S. Sicari, A. Rizzardi, L. A. Griec o, and A. Coen - Porisini, “Survey P aper Security , privacy and trust i n Internet of Things: The road ahead, ” Elsevier , 2015, do i: 10.1016/j.com net.2014.11.008. [34] W. Du, J. Deng , Y. S. Han, P. K . Varshney, J. Ka tz, a nd A. Kh alili, “A pairwise key p r edist ribution sche me f or wireless sensor networks, ” AC M Transacti ons on Information and System Security , vol. 8 , no. 2. pp. 228 – 258, May 2005 , doi: 10.1145/106554 5 .1065548. [35] D. Li u, P. Ning, an d R. Li, “Establishing P airwise K eys i n Distributed Sensor Networks ,” ACM Tr ans. In f. Syst. Secur. , vol. 8, no. 1, pp . 41 – 77, 2005, do i : 10.114 5/1053283.1053 287. [36] M. S. Ali, M. Vecchio, M. Pincheira, K. Dolui , F. Antonelli, and M. H. Rehmani, “Applications of Blockchains in the Internet of Things: A C omprehens i ve Survey,” IEEE Communications Surveys and Tutorials , vol. 21, no. 2. I nstitute of Electrical and Ele ctronics Engineers Inc., pp. 1676 – 1717, Apr. 01, 2 019, doi: 10.1109 / COMST .2018.2886932. 30 of 38 [37] Y. Ashiban i and Q. H. Mahmoud, “Cyber physical systems security: Analysis, c hallenges and solutions,” Comput. Secu r. , vol. 68, pp. 81 – 97, Jul. 2 017, doi: 10.101 6/J.COSE.2017. 04.005. [38] S. F. Mihalache , E. Pricop, and J. Fattah i, “Resilience Enhancemen t of Cyber - Physical Systems: A Review,” Springer, Cham, 2019, pp. 269 – 287. [39] Focus Group on Technolog i es for Netwo rk 2030, “New Se r vices and Capabilities for Network 2030: Descript ion, Technical Gap and Performance Target Analysis,” ITU-T, https://www.itu.int/en/I TU- T/focusgroups/net 2 030/Document s/Deli verable_NET2 030.pdf , p p. 1 – 45, 2018, [ Online]. Available: https://www.itu.in t/ en/ITU-T/f ocusgroups/ne t2030/Documen ts/ Deli verable_NET2 0 30.pdf. [40] C. Mouradi an, D. Naboulsi, S. Yangui, R. H. Glitho, M. J. Morrow, and P. A. Polakos, “A Comp rehensive Survey on Fog C o mputing: State- of -the- Art and Resea rch Ch all enges,” IEEE Communications Su rveys and Tutorials , vol. 20, no. 1. Institute of Elect rical and Elec tronics Engi neers Inc., pp . 416 – 464, Jan. 2018, d oi: 10.1109/COMST. 2017.2771153. [41] S. Wang, X. Zhang, Y. Zhang , L. Wang, J. YANG, a nd W. W ang, “A Survey o n Mobile Edge Networks: Conve rgence of Computing, Caching and Communications, ” IEEE Access , vol. 5, pp. 6757 – 6779, 2017, doi: 10.1109/ACCESS. 2017.2685434. [42] A. Yousefpour et al. , “All one needs to know about fog computing and related edge computing paradigms: A compl ete survey, ” Journal of S ystems Architectu re . 2019, doi: 10.1 016/j.sys a rc.2019.02.0 0 9. [43] W. Z. Khan, E. Ahmed, S. Hakak, I. Yaqoob, and A. Ahmed, “Edge computing: A sur vey,” Futur. Gener. Comput. S yst. , vol. 97, pp. 21 9 – 235, 2019, doi: 1 0 .1016/J.FUTU RE.2019.02.050. [44] Y. Mao, C. You, J. Zhang, K. Huang, and K . B. Letaief, “A Survey on Mobile Edge Computing: The Commu nication Perspective,” IE EE Commun. Surv . Tutorials , vol. 19, no. 4, pp . 2322 – 2358, 2017, d o i: 10.11 09/COMST.20 17.2745201. [45] T. Taleb , K. Samdan is, B. Mada, H. Flinck, S. Du tt a, and D. S abella, “On Mul ti -Access Edge Computing: A Survey of the Emerging 5 G Network Edge Ar chitectur e & Orchestration,” IEEE Commun. Surv. Tutorials , vol. PP, no. 99, p. 1, 2017, doi: 10.11 09/COMST. 2017.2705720. [46] W. Yu et al. , “A Survey on the Edge Computing for the Internet of Things,” IEEE Access , vol. 6. Institute of Electrica l and Electroni cs Engineers In c., pp. 6900 – 6919, Nov. 2017, doi: 1 0.1109/ACCESS .2017.2778504. [47] Y. Ai, M. Peng, and K. Zhang, “Edge computing technologies for Internet of Things: a primer,” Digit. Commun . Networks , vol. 4, n o . 2, pp. 77 – 86, 2018, doi: 1 0.1016/J.DCA N .2017.07 .001. [48] I. Yaqoob, I. A. T. Hashem, A. Ah med, S. M. A . Kazmi, a nd C. S. Hong, “I nternet of things forens ic s: Recent a dvances, taxonomy, requirements, and o pen challenges, ” Futur. Gener. Comput. Syst. , vol. 92, pp. 265 – 275, Mar. 2019, doi : 10.1016/J.FUTU RE.2018.09. 058. [49] R. Yang, F . R. Yu, P. S i, Z. Yang, and Y. Zhang, “Integrated Blockchain and Edge Computing Systems: A Survey, Some Research Issues and Ch allenges,” IEEE Communicat ions Surveys and Tutoria l s , vol. 21, no. 2. Institute of Elect r ical and Electroni cs Engineers In c., pp. 1508 – 1532, 2019, doi: 10.110 9 /COM ST.2019.289472 7. [50] P. Mach and Z. Becvar, “Mobile Edge Computing: A Survey on Architecture a nd Computation Offloading,” IEEE Commun. Surv. Tutor ials , vol. 1 9, no. 3, pp. 1 628 – 1656, 20 17, doi: 10.1 1 09/COMST. 2017.2682318. [51] C. C. Sun, A. Hahn, and C. C. Liu, “Cyber secur ity of a power grid: State- of -the- art,” International Journal of Electrical Power and Energ y Systems . 2018, d oi: 10.1016/j. i jepes.2017. 12.020. [52] D. Kolokotsa, “The role of smart gri ds in the building sector,” Energy Build. , vol. 116, pp. 703 – 708, Mar. 2016, doi: 10.1016/J.ENBU ILD.2015. 12.033. [53] M. Agiwal, A. Roy, a nd N. Saxena, “Next Generation 5G Wireless Networks: A Comprehensive Su rvey,” I EEE Commun. Surv. Tutor ials , vol. 1 8, no. 3, pp. 1 617 – 1655, 20 16, doi: 10.1 1 09/COMST. 2016.2532458. [54] Boyi X u, L i Da Xu, Hongming Cai, Cheng X ie, Jingyuan Hu, and Feng lin Bu, “Ub iquitous Data Access ing Method in IoT - Based Information Syste m for Emergen cy Med ical Services, ” IEEE Trans. Ind. Informatics , v ol. 10, no. 2, p p. 1 578 – 31 of 38 1586, 2014, d oi: 10.1109/TII. 2014.2306382. [55] G. Aceto, V. Persico, and A. Pescape, “A survey on I nformation and Commun ication Technologies for Industry 4.0: state o f the a rt, taxonomies, perspectives, and challenges,” IE EE Commun. S urv. Tutorials , vol. 21, no. 4, pp . 34 6 7 – 3501, 2019, doi: 10.11 09/comst.2019.29 38259. [56] P. Eder- Neuhauser, T. Zseby, and J. Fabini, “Resilience and Secur ity: A Qualitative Survey of Urban Smart Grid Architectures,” IEEE Access , vo l. 4, pp. 839 – 848, 201 6 , doi: 10. 1109/ACCESS. 2016.2531279. [57] K. Zhou and L. Cai, “Randomized PHEV Charging Under Di stribution Grid Constraints,” IEEE Trans. Smart Grid , vol. 5, no. 2, pp . 879 – 887, M ar. 2014, doi: 1 0.1109/TSG. 2013.2293733. [58] P. - Y . Kong, “Wireless Neigh borhood Area Netwo rks With QoS Sup port for Demand Respo nse in Smart Grid,” IEEE Trans. Smart Gri d , vol. 7, no. 4, pp . 1913 – 1923, J ul. 2016, doi : 10.1109/TSG.2 015.2421991. [59] I. Stellios, P. Kotzanikolaou, M. Ps arakis, C. Alcar a z, and J. Lopez, “A Survey of I o T -Enabled Cyberattacks: Assessing Attack Paths to Critical Infrastruc tures and Services,” IEEE Commun. Surv. Tuto rials , vol. 20, no. 4, pp. 3453 – 3495, 2018, doi: 10.11 09/COMST. 2018.2855563. [60] E. Benkhelifa, T. Wel sh, and W. Hamouda, “A C ritical R eview o f P ractices and Challenges in Intru si on Detection Systems for IoT: To ward Univers al and Resilient Systems,” IEEE Commun. Surv. Tutorials , vol. 20, no. 4, pp. 3496 – 3509, 2018, d oi: 10.1109/COMST. 2018.2844742. [61] L. Zheng, N. Lu, and L. Cai, “Reliable Wireless Communicat i on Networks for Demand Response Control,” IEEE Trans. Smart Grid , vol. 4, no. 1, pp . 133 – 140, M ar. 2013, doi: 1 0.1109/TSG .2012.2224892. [62] A. Abdrabou, “A W i reless Communicat ion A rc hitecture for Smart G r id Distribution Networks,” IEEE Syst. J . , vol. 10, no. 1, pp. 251 – 261, Mar. 2016, d o i: 10.11 09/JSYST.2014.2304291. [63] S. Belhaiza and U. Baroudi, “A Game Theoret ic Model for Smart Grids Demand Management,” IEEE Tra ns. Smart Grid , vol. 6, no. 3, pp. 1386 – 139 3, 2015, doi: 10. 1109/TSG.201 4.2376632. [64] R. Lu and S . H. Hong, “Incentive -based demand response for smart grid with reinforcement learning and deep neural network,” Appl. Ener gy , vol. 2 3 6, pp. 93 7 – 949, 2019, do i : 10.101 6/J.APENERGY.2 018.12.061. [65] A. Sargol z aei, K. K. Yen, M. N. Abdelghan i , S. Sargolzae i , and B. Carbu na r, “Resilient Des i gn of Netw or ked Control Systems Under Time Delay Switch Attacks, Application in Smart Grid,” IEEE Access , vol. 5, pp. 15901 – 15912, 2017, doi: 10.1109/A CCESS.2017.2 7 31780. [66] G. Liang, J. Zhao, F. Luo, S. R. Weller, and Z. Y. Dong, “A Review of False Data Injection A ttacks Against Modern Power Systems, ” IEEE Trans. Sm art Grid , vol. 8, no. 4, pp. 1630 – 1638, Jul. 201 7 , doi: 10. 1109/TSG.201 5.2495133. [67] Q. Wang, W. Tai, Y. Tang, M. Ni, and S. You, “ A two -layer game theoretical attack -defense model for a false dat a inje ction attack against p o wer systems ,” Int. J. Electr . Power Energy Syst. , vol. 1 0 4, pp. 169 – 177, Jan. 2 019, doi: 10.1016/J.IJEPES. 2 018.07.0 07. [68] A. Gholami, T. Shekari, M. H. Amirioun, F. Aminifar, M. H. Amini, and A. Sargolzaei, “Toward a Consensu s on the Definition and Taxonomy of Power System Resilience,” IEEE Access , vol. 6, pp. 32035 – 32053, 2018, doi: 10.1109/ACCESS. 2018.2845378. [69] A. Kumar , A. Singh, A. Kuma r, M. K. Si ngh, P. Mahanta, and S. C. Mukhopadhyay , “Sensing Technologies for Monitoring Intelligent Buildings: A Review,” IEEE Sens. J. , vol. 18, no. 12, pp. 4847 – 4860, Jun. 2018, doi: 10.1109/JSEN. 2018.2829268. [70] S. Varshney et al. , “Energy Eff icient Manageme nt of Pipelines in Bu i ldings Us i ng Linea r Wireless Sens or Networks ,” Sensors , vol. 1 8, no. 8, 2018, do i : 10.3390/s 1 8082618. [71] P. K ar, A. Shareef, A. Kum ar, K. T. Harn, B. Kallu r i, and S . K. Panda, “ReViCEE: A recommendation b a sed approach for pers o nalized control, visual comfort & energy efficiency in buildings,” Build. Environ. , vol. 152, pp. 135 – 14 4, 2019 , doi: 10.1016/J.BUIL DENV.2019.01.035. 32 of 38 [72] I. C. Konstant akopoulos, A. R. Barkan, S. He, T. Veer a valli, H. Liu, and C. Spa nos, “A deep learning and g amification approach t o improving human- building interact i on and energy eff i ciency in smart i nfrastructure ,” Appl. Energy , v o l. 237, pp. 810 – 821, M ar. 2019, doi: 10.101 6/J.APENERG Y .2018.12.0 65. [73] R. Jia et al. , “Desi gn Automation for Smart Building Systems, ” Proc. IEEE , vol. 106, no. 9 , pp. 1680 – 1699, 2018, doi: 10.1109/JPROC .2018.2856932 . [74] I. W. Marshall et al. , “Application - level Programmable Internetwork Environment, ” BT Technol. J. , vol. 17, no. 2, pp. 82 – 94, 1999, doi: 10.102 3/A:100968990 0 903. [75] N. Y eadon, A. Mauthe, F. García, a nd D. Hutchis o n, “QoS filters: A ddressing the heterogeneity gap,” in Lecture N otes in Computer Science (includin g subseries Lecture Notes in Artificial Intelli gence and Lecture Notes in Bioin formatics) , 1996, vol. 1045, pp. 227 – 243, doi: 10. 1007/3-540-60938- 5_16. [76] M. Arslan, K. Sundaresan, and S. Rangarajan, “Software -defined networking in cellular radio access networks: potential and challenges,” IEEE Commun. Mag. , vol. 5 3, no. 1, pp. 150 – 156, Jan. 2015, doi: 10.1109/MCOM. 2015.7010528. [77] N. Zhang, S. Zhang, J. Zheng , X. Fang, J. W. M a rk, and X. Shen , “QoE Drive n Decent ralized Spectrum Sharing in 5G Networks: Potential Game Approach,” IEEE Trans. Veh. Technol. , vol. 66, no. 9, pp. 7797 – 7808, 2017, doi: 10.1109/TVT.2 017.2682236. [78] Y. Guo, X. Hu, B. Hu, J. Cheng, M. Zhou, and R. Y . K. Kwok, “Mobile Cyber Physical Systems: Current Challenges and Future Networking Applications,” IEEE Access , vol. 6, pp. 12360 – 12368, 2018, doi: 10.1109/ACCESS.2017.278 2881. [79] D. J ia, K. Lu, J. Wa ng, X. Zhang, and X. Shen, “A Su rvey on Plat o on -Based Vehicular C yber- Physica l Systems ,” IEEE Commun. Surv. Tutor ials , vol. 1 8, no. 1, pp. 2 63 – 284, 2016, d oi: 10.1109/COMST.201 5 .241083 1. [80] A. A. Mutlag, M. K. Ab d Ghani, N. Arunkumar, M. A. Mohammed, and O. Mohd, “Enabling technologies for fog computing in healthcare IoT systems,” Futur. Gener. Comput. Syst. , vol. 90, pp. 62 – 78, Jan. 2019, doi: 10.1016/J.FUTU RE.2018.07. 049. [81] F. Firouzi, B. Farahani, M. Ibrahim , and K. Chakrabarty, “Keynote Paper: From EDA to IoT eHealth: Promises, Challenges, and Solutions,” IEEE Trans. Comput. Des. Integr. C ircuits Syst. , vol. 37, no. 12, pp. 2965 – 2978, 2018, doi: 10.1109/TCAD.2 018.2801227. [82] Y. YIN, Y. Zeng, X. Chen, and Y. Fa n, “ The i nternet of things in healthcare: An overview,” J. Ind. Inf. Integr. , vol. 1, pp. 3 – 13, Mar. 2 016, doi: 10. 1 016/J.JII.2 016.03.004. [83] Y. Zhang, M . Qiu, C.- W. Tsai, M. M. Hassan , and A. Alamri, “Health -CPS: Healthc a re Cyber-Physic al System Assiste d by Cloud and B ig Data,” IEEE Syst . J. , vol. 11, no. 1, pp. 88 – 95, Mar. 2017, doi: 10.1109 /JSYST.2015.24 6 0747. [84] R. Altawy and A. M. Youssef , “ Security Tradeoffs in Cyber Physical Systems: A Case Study Survey on Impla ntable Medical Devices,” IEEE Access , vo l. 4, pp. 959 – 979, 2016, do i: 10.1109/AC CESS.2016.2521 727. [85] F. A. Kraemer, A. E. Braten, N. Tamkittikhun, and D. P alma, “Fog Compu ting i n Hea l thcare– A Review and Discussion,” IEEE A ccess , vol. 5, p p. 9206 – 9222, 2017, doi: 10.1 1 09/ACCESS .2017.270 4100. [86] C. Guimarães, J . Q uevedo , R . Ferreira, D. Coru j o, and R. L. Aguiar, “Exploring interoperability assessment for Futur e Internet A rchitectures r oll out,” J. Netw. Comput. Appl. , v ol. 1 36, pp . 38 – 56, Jun. 2019, doi: 10.1016/J.JN CA.2019.04. 008. [87] S. B. Baker, W. Xiang, and I . Atkinson, “Internet of Things for Sm a rt Healthcare: Technolog i es, Challenges, and Opportunities,” IEEE Access , vol. 5, pp. 26521 – 26544, 2017, do i: 10.1109/A CCESS.2017.2775180. [88] R. Prat ap Singh, M. J a vaid, A. H aleem, R. Va i shya, and S. Ali, “Inte rnet of Medical Things ( I oMT) fo r orthopaedic i n COVID- 19 pandemic: R oles, challenges, a nd applications,” Journal of Clinical Orthopae dics and Trauma . Elsevier B.V., pp. 1 – 5, May 15, 2020, doi: 1 0.1016/j.jcot. 2020.05.011. [89] S. A. Haque, S. M. Aziz, and M. Rahman, “Review of Cyber -Physi cal System in Healthcare,” Int. J. Distrib. Sens. Networks , vol. 10, no. 4, pp . 1 – 20, 2014, doi: 1 0.1155/2014/ 217415. 33 of 38 [90] M. Brettel, N. Friederichsen, M. Keller, and M. Rosenberg, “How Virtualization, Decentralization a nd Network Building Change the Manufacturing Land scape : An Industry 4 .0 Perspective,” Int. J. Mech. aerospace, Ind. mechatronic s Eng. , vol. 8, no . 1, pp. 37 – 44, 2014 , [Online]. Av a ilable: https ://publications.rw th -aachen.de/rec ord/465283. [91] T. Taleb, I. Afo labi, and M. Baga a, “Orchestrating 5G Network Slices to Support Industrial Internet and to Shape Next- Generati on Sm a rt Factories,” IEEE Netw. , vol. 33, n o. 4, pp. 146 – 154, Ju l. 2019, doi: 10.1109/MNET.201 8.1800129. [92] C. Fang, S. Guo, Z. Wang, H . Huang, H. Yao, and Y. Liu, “Data -driv en intelligent future network: Archite cture, use cases, and cha l lenges,” IEEE Co mmun. Ma g. , vol. 57, no. 7, pp. 34 – 40, Jul. 2019, doi: 10.1109/MCOM. 2019.18007 69. [93] W. Kellere r , P. Kalmbach , A. Blenk, A. Basta, M. Re isslein, and S. Schmid , “Adaptab l e and Data -Drive n Softwarized Networks: Review, Opportun i ties, and Challenges,” Proc. IEEE , vol. 107, no. 4, pp. 711 – 731, 2019, doi: 10.1109/JPROC .2019.2895553 . [94] M. Yao, M. Sohul, V. Ma rojevic, and J. H. R eed, “Artificia l Intelligence Defined 5G Radio Access Networks,” IE EE Commun. Mag. , v o l. 57, no. 3, pp. 14 – 20, Ma r. 2019, doi: 10. 1109/MCOM . 2019.1800 629. [95] E. A. Mazied et al. , “The wireless control plane: An overview and directions for future research,” J. Netw. Co mput. Appl. , vol. 126, pp. 104 – 122, Jan. 2 019, doi: 10.1016 /J.JNCA.2018 .09.017. [96] M. T. Vega, T. Mehmli, J. V a n Der Hoof t, T. Wa uters, and F. De Turck, “Enabling Virtual Rea l ity for the Tactile Internet: Hur dles and Opportuni ties,” in 14th I nternational Conference on Networ k and Service Management, CNSM 20 18 and Workshops, 1st International Workshop on High-Precision Networks Operations and Control, HiPNet 2018 a nd 1st Workshop on Seg ment Routing and Service Function Chain i ng, SR+SFC 2 , Nov. 2018, pp. 3 78 – 383. [97] G. S. Aujla, R. Chaudhary, N. K umar, J. J. P. C. Rodrigues, and A. Vinel, “Data Offloading in 5G -Enabled So ftwa re- Defined Vehicular Networks: A St a ckelberg-Game- B a sed Approach,” IEEE Commun. M ag. , vol. 55, no. 8, pp. 100 – 108, 2017, doi: 10.11 09/MCOM. 2017.1601224. [98] L. Chen, J. Wu, X.-X. Zhang, a nd G. Zhou, “T ARCO: Tw o -Stage Auction for D 2D Relay Aided Computation Resource Allocation in HetNet,” IEEE Trans. Serv. Comput . , p. 1, 201 8, doi: 10.1109 / TSC.201 8.2792024. [99] I. C. Konstantakopou l os, L. J. Ratliff, M. Jin, C. Spanos, and S. S. Sastry, “ Smart buildi ng energy efficiency via social game: a robust utility learning frame work f or closing – the –loop, ” in 2016 1st In ternational Workshop on S cience of Smart City Operations and Platforms Engineering (SCOPE) in partnership with Global City Teams Chal lenge (GCTC) (SCOPE - GCTC) , 2016, pp. 1 – 6, doi: 10. 1109/SCOPE.20 16.7515054. [100] C. T. Do et al. , “Game Th eory for Cyber Security a nd Pr ivacy,” ACM Comput. Su rv. , vol. 50, n o. 2, pp. 1 – 37, 2017, do i : 10.1145/305726 8 . [101] F. Yao, L. Jia, Y. Sun, Y. Xu, S. Feng, and Y. Zhu, “A hierarchic al le arning a pproach to anti -jamming channel s election strategies,” Wirel. Net works , vol. 25 , no. 1, pp . 201 – 213, Jan. 20 1 9, doi: 10.1 007/s11276- 017 -1551- 9. [102] E. C. Paulson, I. Linkov, and J. M. Keis ler, “A game theoretic model for resource allocation among cou nter measures with multiple attributes,” Eur. J. O per. Res. , vol. 2 52, no. 2, pp. 6 1 0 – 622, Jul. 2016, doi: 10.1016 /J.EJOR.2016 .01.026. [103] Z. Zhou, L. Ta n, B. Gu, Y. Zhang, and J. Wu, “Bandwidth Slicing in Softwa r e -Defined 5G: A Stackelberg Game Approach,” IEEE Veh. Technol. Mag. , vol. 13, n o. 2, pp. 102 – 109, Jun . 2018, doi: 1 0 .1109/MVT . 2018.28 14022. [104] L. Wa n, L. Sun, X. Kong, Y . Yua n, K . Su n, and F . X ia, “T a sk -Driven Resource Ass ignment in Mobi le Ed ge Computing Exploiting Evolutionary Computation,” IEEE Wirel. Commun. , vol. 2 6, no. 6, pp. 94 – 101, 2019, doi: 10.1109/MWC. 001.1800582. [105] W. Chen et al. , “ Cooperative and Distributed Computation Offloadi ng for Blockch ain -Emp owered Industrial Internet of Things,” IEEE I nternet Thin g s J. , p. 1, 201 9, doi: 10.110 9/JIOT.2019.2918 2 96. [106] G. Rezgui, E. V. Belmega, a nd A. Chorti, “Mitigating Jamming Attacks Using Energy Harvesting,” IEEE Wirel. Commun. Lett. , p . 1, 2018, doi: 1 0.1109/LWC. 2018.2871152. [107] Q. Zhu and T. Basar, “Game -Theoretic Methods for Robustness, Security, and Resilience of Cyberphysical C ontrol 34 of 38 Systems: Games- in - Games Princip le for Optimal Cross- Layer Resilient Control Systems, ” IEEE Control Syst. , vol. 35, no. 1, pp. 46 – 65, 2015, doi: 10.1 1 09/M CS.2014.236471 0. [108] L. Wei, A. I. Sarwat, W. Saad, an d S. Biswas, “Stochast i c G ames for Power Grid Protection Against Coordinated Cyber- Physical Attacks, ” IEEE T rans. Smart Gr i d , v ol. 9, no. 2, pp. 684 – 694, Mar. 2018, doi: 10.1 1 09/TSG.201 6 .2561266. [109] Q. D. La, T. Q. S. Quek, J. Lee, S. Jin, and H. Zhu, “Deceptive Attack and Defens e Game i n Honeypot -Enable d Networks for the Internet of Thi ngs,” IEEE Internet Thin gs J. , vol. 3, no. 6, pp. 1025 – 1035, 2016, doi: 10.1109/JIOT.2 016.2547994. [110] A. Iqbal, L . J. Gunn, M. Guo, M. Ali Babar, a nd D. Abbott, “Game theoretical modelling of network/cy bersecurity,” IEEE Access , vol. 7, pp. 154167 – 154 1 79, 2019, d o i: 10.1109 /ACCESS.2 019.2948356. [111] J. C hen and Q. Zhu, “Interdependent Strategic Security Risk Managem ent with Bounded Rationality in the Internet of Things,” IEEE Tr ans. Inf. Forensics Secur. , vo l. 14, no. 11, pp. 2958 – 2971, Nov . 2019, doi: 1 0.1109/TIFS.2 0 19.2911 112. [112] H. Liao, Z. Zhou, B. Ai, a nd M. Guizani, “Learning -Based Energy-E fficient Channel Selection for Edge Computing- Empowered Cognitive Machine- to - Machine Communications,” in 2 020 IEEE 91st Vehicular Technolo gy Conference (VTC2020-Sprin g) , May 2020, p p. 1 – 6, doi: 10.11 0 9/VTC20 20-Spring48590.2 020.9128780. [113] C. Rots os et al. , “Network s er vice orches tration sta ndardization: A t echnology survey,” Comput . Stand. Interfaces , vol. 54, pp. 203 – 215, N o v. 201 7, doi: 10.1016/J. CSI.2016.12 .006. [114] P. Smith, A. Sc ha effer- Filho, D . Hutchison, an d A. Mauthe, “Management p a tterns: SDN -enabled network resilienc e management,” i n IEEE/IFIP NOMS 2014 - IEEE/IFI P Network Operati ons and Mana gement Symp osi um: M anag ement in a Software Defined World , 2014, pp. 1 – 9, doi: 10.1109/ N OMS.20 1 4.6838323. [115] E. Molina a nd E. Jacob, “Software -defined networking in cyber- physical systems: A sur vey,” Comput. Electr. Eng. , vol. 66, pp. 407 – 419, 2 018, doi: 1 0.1016/J.COMPE LECENG.201 7 .05.013. [116] P. Kampanakis , H. Perros, and T . Beyene, “SDN - based solut i ons for Moving Ta rget Defense netwo r k protect ion,” in Proceeding of IEEE International Symposium on a World of Wireless, Mobile and Multime dia Networ ks 2014 , Jun. 2014, pp. 1 – 6, doi: 10.110 9/WoWMoM.2 014.691897 9 . [117] Q. Zhao, C. Zhang, and Z. Zhao, “ A decoy chain deployme nt method based on SDN a nd N FV against penetration att ack.,” PLoS One , vol. 12, no. 1 2, pp. 1 – 23, 20 17, doi: 10.137 1 /journ al.pone.018909 5 . [118] N. Sultana, N. Chilamkurt i, W. Peng, and R. Alhadad, “Survey on SDN based network intrusion detection system using machine learning app r oache s,” Peer- to -Peer Netw. Appl. , pp. 1 – 9, Jan. 2018, doi: 10.100 7 /s12083-017-0630- 0. [119] Z. Fan, Y. Xiao, A. Nayak, a nd C. Tan, “An improved network security situation assessment approach in softwa re defined networks ,” Peer- to -Peer Net w. Appl. , pp. 1 – 15, 2 017, doi: 1 0.1007/s12083- 017 -0604- 2. [120] X. Xu, S. Wang, and Y. Li, “Identificat ion and predication of netwo r k attack patter ns in software- defined netwo rking,” Peer- to -Peer Netw. Ap p l. , pp. 1 – 11, J a n. 2018, d o i: 10.10 07/s12083- 017 -0629- 6. [121] X. Yin, L. Wang, a nd S . J i ang, “ A h ierarchical m obility management scheme based on software def ine d netw orking,” Peer- to -Peer Netw. Ap p l. , pp. 1 – 16, J a n. 2018, d o i: 10.10 07/s12083- 017 -0615- z. [122] J. Xiao, S. Chen, and M. Sui, “The strategy of path determination and traffic scheduling in private campu s networks based on SDN,” Peer- to -Peer Netw. A ppl. , pp. 1 – 10, 2017, doi: 10.10 07/s12083-017-0623- z. [123] Z. Zh ang, L. Ge, P. Wang, and X. Zhou, “Beh avior Re co nstruct ion M odels f or Large - scale Network Se rvice Systems, ” Peer- to -Peer Netw. Ap p l. , pp. 1 – 12, J a n. 2018, d o i: 10.10 07/s12083- 017 -0625- x. [124] S. Din, A. Paul, A. Ahmad, and J. H. Kim, “Energy efficient topology managemen t scheme based on clustering technique for software defined wireless sensor network, ” Peer- to -Peer Netw. Appl. , vol. 12, no. 2, pp. 348 – 356, Mar. 2019, doi: 10.10 07/s12083-017-060 7- z. [125] T. Bai et al. , “An optimized protocol for QoS and ene rgy efficiency on wireless body area networks,” Peer - to -Peer Netw. Appl. , pp. 1 – 11, 2 017, doi: 10.1 007/s12083-017-06 02- 4. 35 of 38 [126] C. Brooks et al. , “A Component Architecture for the Internet of Things,” Proc. IEEE , vol. 106, no. 9 , pp. 1527 – 1542, 2018, doi: 10.11 09/JPROC. 2018.2812598. [127] C. Gershenson, V. Trianni, J. Werfe l , and H. Sayama, “Self - Organization and Artifi cial Life: A Review,” 2018, [On line]. Available: http:/ / arxiv.org /abs/1804.01 144. [128] W. Aguilar, G. Santamaría- Bonf il, T. Froese, and C. Gershenson , “ The Past, Present, and Future of Artificial Life,” Front. Robot. AI , v ol. 1, p. 8, 2 014, doi: 10.3 389/frobt.2014 .00008. [129] M. A. Bedau et al. , “Open Problems in Artificial Life,” Artif. Life , vol. 6, no. 4, pp. 363 – 376, 2000, doi: 10.1162/106454 6 00300103 683. [130] Z. M. Fadlullah et al. , “State - of -the- Art Deep Learning: Evolving Mach ine I ntelligence Toward Tomorrow’s Intel ligent Network Traffic Control System s,” IEEE Commun. Surv. Tutorials , vol. 1 9 , no. 4, pp. 2432 – 2455, 2017, doi: 10.1109/COMST .2017.27071 40. [131] C. Zhang, P. Patras, and H. Haddadi, “Deep Learning i n Mobi le a nd Wireless Networking: A Su rvey,” IEEE Commun. Surv. Tutorials , v ol. 21, no. 3, pp . 2224 – 2287, 201 9, doi: 10.1109/C O MST.2 019.2904897. [132] F. Francois and E. Gelenbe, “Towards a cognitive routing engine for software defined networks,” i n 2016 IEEE International Con ference on Commun ications (ICC) , 2016, pp. 1 – 6, do i: 10.1109/ICC .2016.7511138. [133] Y. Dai, D . Xu, S. Maharjan, Z. Chen, Q. He, and Y. Zhang, “Blockcha i n and Deep Reinforcement Learn ing Empowered Intelligent 5G beyo nd,” IEEE Netw . , vol. 3 3 , no. 3, pp. 10 – 17, 2019, do i : 10.1109/M N ET.2019. 1800376. [134] H. Lu, Y. Li, M. Chen, H. Kim, and S. Se ri kawa , “Brain Intell igence: G o bey o nd A rtificial Intel l igence,” Mob. Net works Appl. , vol. 23, n o . 2, pp. 368 – 375, 2018, doi: 10. 1007/s11036- 017 -0932- 8. [135] Y. Sun, M. Peng, Y. Zhou, Y. Huang, and S. Mao, “Applicat ion of Mac hine Learning in Wireless Networks : Key Techniques and Open Issues,” IEEE Commun. Surv. Tutorials , vol. 21, no. 4, pp. 3072 – 3108, 2019, doi: 10.1109/COMST .2019.29242 43. [136] M. C hen, U. Chall ita, W. Saad, C. Yin, and M. Debba h, “Artificial N eural Networks -Based Machine Learning fo r Wireless Networks: A Tutorial, ” IEEE Commun. Sur v. Tutorials , vol. 21, no . 4 , pp. 3039 – 307 1, 2019, doi: 10.1109/COMST .2019.29266 25. [137] H. Li, K. Ota, an d M. Dong, “Lear ning IoT in Edge: Deep Lea rning f o r the Internet of Things with Edge Computing,” IEEE Netw. , vol. 3 2, no. 1, pp . 96 – 101, Jan. 2 018, doi: 10.110 9/MNET.2 018.1700202. [138] S. Ozawa, “Computational Intellig ence in the Ti me of Cybe r -Phy sical Systems and the Internet of Things,” in Artificial Intelligence in the A ge of Neural Networks an d Brain Com puting , Academic Press, 2 019, pp. 2 45 – 263. [139] M. A. Khan and H. Tembine, “Meta -Learning for Realizing Self - x Management of Future Networks,” IEEE Access , vol. 5, pp. 190 72 – 19083, 2017, do i : 10.1109/A CCESS.2017. 2745999. [140] I. Linkov and A. Kott, “Fundamen tal Concepts of Cyber Resilience: Introduction and Overview,” in C yber Resilience of Systems and Net works , Cham: Sp r inger Intern a tional Publish ing, 2019, pp. 1 – 25. [141] N. Evans and W. Horsthemke, “Ana l ysis of Dependencies,” in C y ber Resilience of S ystems and Networks , Cham: Springer Intern ational Publish i ng, 2019, pp . 93 – 106. [142] N. Evans and W. Horsthemke, “Regional Critical I nfrast ructure,” in Cyber Resilience of Systems and Networks , Cham: Springer Intern ational Publish i ng, 2019, pp . 355 – 380. [143] T. J . M oore and J.- H. Cho, “Applying P erco lation T heory,” in Cyber R esilience of Systems and Networks , Cham: Springer International P ublishing, 201 9, pp. 107 – 133. [144] D. J. Bodeau and R. D. Graubart, “Systems Engineering App roaches,” in Cyber Resil ience of Systems and Networks , Cham: Springer Internation al Publishing , 2019, pp. 19 7 – 220. [145] I. Al Ridhawi, M. Aloqaily, and A. Bo ukerche, “Co mparing Fog Solutions for Energy Efficiency in Wireless Networks: Challenges and Opportunities, ” IEEE Wirel. C ommun. , vol. 26 , no. 6, pp . 80 – 86, 2019, doi: 10.1109/MWC. 001.1900077. 36 of 38 [146] K. Kaur, S. G arg, G. Kaddoum, N. Kumar, and F. Gagn on, “ SDN -Based Internet of Au tonomous Vehicl es: An Energy- Efficient Approach for Controll er Placement,” IEEE Wirel. Commun. , vol. 26, no. 6, pp. 72 – 79, 2019, doi: 10.1109/MWC. 001.1900112. [147] A. R a mnatthan, A. G anesan, J. L i u, A. C. Ar paci-Dusseau, and R . H. Arpaci-Duss ea u, “F a ult -tolerance, fast an d s low: exploiting failure a synchrony in di stribute d systems,” in Proceedings of the 12th USENIX conference on Operating Systems Design a nd Implementation , 2 018, pp. 391 – 408, [Online]. A vailable: https://d l.acm.org/c itation.cfm ?i d=329 1197. [148] G. Giacomello and G. Pescaroli, “Managing Human Factors,” in Cy ber Resilience of Systems and Networks , Cham: Springer Intern ational Publish i ng, 2019, pp . 247 – 263. [149] N. U. H. Shirazi, S. Simpson, A. K. Marnerides, M. Watson, A. Maut he, and D. Hutchison, “Assessing the impact of intra- cloud live migration on anomaly detection ,” i n 2014 IEEE 3rd International Conference on Cloud Networking , CloudNet 2014 , N ov. 2014, pp. 52 – 57, doi: 10.1109/C l oudNet.2 014.696896 8. [150] Shengbo Yang, Chai Kiat Yeo, and Bu- Sung Lee, “Toward Reliable Data Delivery for Hi ghly Dynamic Mobile Ad Hoc Networks,” I EEE Trans. Mob . Comput. , vol. 11, no. 1, pp . 111 – 124, Jan. 2 012, doi: 1 0.1109/TMC.2 011.55. [151] W. Gao, G. Cao, A. Iyengar, and M. Srivats a, “Cooperative Caching for Efficient Data Access in Disr uptio n Toleran t Networks,” IEEE Trans. Mob. Comput. , vol. 13, no. 3 , pp. 61 1 – 625, Mar. 2014, d oi : 10.1109 / TMC.20 13.33. [152] N. Tandiya, E. J. M. Colbert, V. Marojevic, and J. H . Reed, “Biologically Inspired Artificial Intelligence Techniques,” in Cyber Resilience of Systems a nd N etworks , Cham: Springe r Intern ational Publishing , 2019, pp. 287 – 313. [153] M. Curado et al. , “Internet of Things,” in Cyber Resilience o f Systems and Networks , Cham: Springer Internationa l Publishing, 201 9, pp. 381 – 401. [154] J. Tavcar and I. Horvath, “A Review of the Principles of Design ing Smart C yber -Physical Systems for Run -Tim e Adaptation: Learned Lessons and Open Issues,” IEEE Trans. Syst. Man, Cybern. Syst. , vol. 49, no. 1, pp. 145 – 158, Jan. 2019, doi: 10.11 09/TSMC.20 1 8.2814539. [155] E. J. M. Colbert, A. Kott, and L. P. Knachel, “The game -theoretic mo del and expe r iment al investigation of cyber wargaming,” J. De f . Model. Simul. Appl. Met h odol. Techn ol. , pp. 1 – 18, 201 8, doi: 10.1177/1 548512918795 061. [156] I. Kotenko, I. Saenko, and O. Lauta, “Modeling the Impact of Cyber Attacks,” in C y ber Resilience of Systems a n d Networks , Cham: Springer Inte r nationa l Publishing, 201 9 , pp. 135 – 169. [157] S. Musman, S. Agbolosu-Amison, an d K. Crowther, “Metrics Based on the Mission Risk Perspective,” in Cyber Resilience of Systems and Networks , Cham: Springer Internation al Publishing, 2 019, pp. 41 – 65. [158] A. Moubayed , A. Refaey, and A. Shami, “Software -Defined Perimeter (SDP): State o f the Art Secure Solution for Modern Netwo r ks,” IEEE Netw . , vol. 33, no. 5, pp. 226 – 23 3, 2019, doi: 10. 1109/MNET. 2 019.18003 24. [159] J. Rodriguez- Mol ina and D. M. Kammen, “Middleware Architectures for the Smart Grid: A Survey on the State - of - the-Art, Taxonomy and Main Open Issues,” IEEE Commun. Surv. Tutorials , vol. 20, no. 4 , pp. 2992 – 3033, 2018, doi: 10.1109/COMST .2018.28462 84. [160] A. Farahz adi, P. Sha ms, J. Rezazadeh, a nd R. Farahb akhsh, “Mid dleware techno logies for cloud o f thing s: a su rvey,” Digit. Commun. Netw o rks , vol. 4, no. 3, pp. 176 – 188, 2018, doi : 10.1016/J.D CAN.2017.04.005. [161] K. Wang, H. Yin, W. Quan, and G. Min, “Enabling Collaborative Edge Comput ing for So ftw a re Defined Vehicular Networks,” IEEE Netw. , vol. 32, no . 5, pp. 112 – 117, 2018, doi: 10. 1109/MNET.201 8.1700364. [162] J. Xu, S. Wang, B. K. Bha rgava, and F. Yang, “ A Blockch a in -Enabled Trustless Crowd-I ntelligence Eco system on Mobile Edge Computing,” IEEE Tr a ns. In d. Informatics , vol. 15, no. 6, pp. 3538 – 3547, Jun. 2019, doi: 10.1109/TII.20 19.2896965. [163] Z. Zhang et al. , “Sec CL: Securing Col laborative Learning Sys tems via Trusted Bulletin Boards, ” IEEE Commu n. Mag. , vol. 58, no. 1, pp. 47 – 53, Jan. 2 020, doi: 10.1 109/MCOM.0 01.1900130. [164] Z. Liu et al. , “ A Survey on Blockchain: A Game Theoret ical P erspec ti ve,” IEEE Access , vol. 7, pp. 47615 – 47643, 2019, 37 of 38 doi: 10.1109/A CCESS.2019.2 9 09924. [165] Q. Wu, W . Liu, a nd A . Farrel, “ RFC 8 309: Service Models Ex plained, ” IETF, https://too l s.ietf.org/htm l/rfc8309 , pp. 1 – 23, 2018, [Online]. Av ailable: https://tools.ietf. org/html/rfc8309. [166] ONF_TR- 523, “Intent N BI – Definition a nd Principles,” Open Netw. Found. https//www.opennet working.org/wp- content/uploa ds/2014/10/TR-523_In tent_Definition_ Pri nciples. p df , pp . 1 – 20, 2016, [Online]. Available: https://www.openn etworking.org/wp-content/upl oads/2014/1 0/TR-523_Intent_Definit i on_Princip l es.pdf. [167] A. Clemm, L. Ciavaglia, L. Granville, a nd J. Tantsura, “ Intent -Based Networking - Concepts and Overview,” IETF, https://tools.ietf.or g /id/draft-clemm-n mrg-dist-intent-03.html#T R523 , pp. 1 – 21, 2 019. [168] F. Hussain, S. A. Hassan, R. Hussain, and E. Hossain, “Machine Learning for Resource Managemen t in Cellular and IoT Networks: Potentials, C urrent Solutions, and Open Challen ges,” IEEE Commun. Surv. Tut orials , p p. 1 – 1, Jan. 2020 , doi: 10.1109/comst .2020.2964534. [169] N. Feamster and J. Rexf ord, “Why (and How) Netw o rks Shou l d Run Them selves,” arXiv:1710.1158 3 , pp. 1 – 7, 2017. [170] C. V. Hollot, V. Misra, D. Towsley , and W. B. Gong, “A control theoretic a nalys is of RED,” in Proceedings - IEEE INFOCOM , 2001, vol. 3, pp. 1 510 – 1519, doi: 10. 1109/infcom.2 001.916647. [171] Y. Yiakoum i s, K.- K. Yap, S. Katti, G. Parulkar, and N. McKe own, “Sl i cing H ome Netw orks,” in Proceedings of t he 2Nd ACM SIGCOMM Workshop on Home Netw orks , 2011, pp. 1 – 6, doi: 10.1145/20 18567.2018569. [172] H. Zhang, N. Li u, X. Chu, K. Long, A. -H. Aghvami, a nd V. C . M. Leung, “Network Slicing Based 5G a nd Future Mobile Networks: Mobility, Resource Management, and Challenges,” IEEE Commun. Mag. , vol. 55, no. 8, pp. 138 – 145, 2017, doi: 10.11 09/MCOM. 2017.1600940. [173] W. Ding, X. Jing, Z. Y a n, a nd L. T. Yang, “ A survey on data fus ion in internet of things: Towards secure and privacy- preserving fus i on,” Inf. Fusion , v o l. 51, pp. 129 – 144, 2019, d oi: 10.1016/j. i nffus.2018. 12.001. [174] E. Zeydan et al. , “Big data caching for networking: moving from cloud to edge,” IEEE Commun. Mag. , vol. 54, no. 9 , pp. 36 – 42, 2016, d oi: 10.1109/MCOM.2016. 7565185. [175] R. Casado- Var a, P. Novais, A. B. Gil, J. P rieto, and J. M. Corchado, “Distributed Continuous -Time Fault Estimatio n Control for Multiple Devices in IoT Networks,” IEEE Access , vol. 7, pp. 11972 – 11984, 2019, doi: 10.1109/ACCESS. 2019.2892905. [176] G. Lee, W. Saad, a nd M. Bennis, “An online optimization framewo rk for distributed fog network format i on with minimal latency,” IEEE Trans. Wirel. Commun. , vol. 18, no. 4 , pp. 22 44 – 2258, Apr. 2019, doi: 10.1109/TWC.2 019.2901850. [177] A. A. Barakabitze, A. Ahmad, R. Mijumb i, and A. Hines, “5G network slicing using SDN a nd NFV: A survey of taxonomy, architectures and future c hallenges, ” Comput. Networks , vo l. 167, p. 106984, Feb. 2020, d oi: 10.1016/j.comnet . 2019.10 6984. [178] Y. Z han, Y. Xi a , and A. V Vas ilakos, “Future d irections of networked control s ystems: A combi nation of cloud control and fog contr ol approach, ” Comput. Networks , v ol. 161, pp. 2 35 – 248, 2019, doi: 10. 1016/J.COMNET.2019.07.004. [179] M. Richart, J. Baliosian, J. Serrat, and J.- L. Gorricho, “Resource S lici ng in Virtual Wireless Net works: A Survey,” IEEE Trans. Netw. Ser v . Manag. , vol. 1 3, no. 3, pp . 462 – 476, 20 16, doi: 10.1109/T N SM.201 6.2597295. [180] P. L. Ventre et al. , “ Segment Routing: a Comprehensive Survey of Research Activities, Standardization Efforts and Implementation Results,” arXiv: cs .NI/1904.03471 , pp. 1 – 38, 2 020. [181] P. Wang, L. T . Yang, J. Li, J. Chen, and S. Hu, “Data fusion in cyber -physical-social systems: State- of -the-art and perspectives,” Inf . Fusion , vol. 51, pp. 42 – 57, 2 019, doi: 10.1 016/j.inffus . 2018.11.002. [182] R. C asado-Va r a, F. Pri eto- Cast rillo, an d J. M . Corchado, “A g a me theory approach for coope rative control to imp r ove data qualit y and false data detection in WSN,” Int. J. Robust Nonlinear Control , vol. 28, no. 16, pp. 5087 – 5102, Nov. 2018, doi: 10.10 02/rnc.4306. 38 of 38 [183] P. Mishr a, D. Puth al, M. T i wary, a nd S. P. Mohanty, “ Softw a re Defin ed IoT Systems: P roperties, St a te o f the Art, a nd Future Research, ” IEEE Wirel. Commun. , vol. 26, n o. 6, pp. 64 – 71, 2 019, doi: 10.1109/M WC.001.1900083. [184] R. V a les, J. Mou ra, and R. Marin heiro, “Energy -aware and a dapti ve fog storage mechanism wit h dat a replication ruled by spatio-temp oral content po pularity,” J. Netw. Comput. Appl. , vol. 135, pp. 84 – 96, 2019, doi: 10.1016/j.jnca.2 019.03.001. [185] Geoff Hust on, “What’s the R ight Netwo r k Buffer Si z e?,” The Interne t Protocol Journ a l , vol. 23, n o. 1, pp. 2 – 20, 2020. [186] Z. Xiong, Y. Zhang, D. Niyato, P. Wang, and Z. Han, “When mo bile blockchain meets edge computing,” IEEE Commun. Mag. , v o l. 56, no. 8, pp. 33 – 39, Aug . 2018, doi: 1 0.1109/MCOM. 2018.1701095. [187] M. F. Zia, M. Benbouz id, E. Elbouchikhi, S. M. Muyeen , K. Techato, a nd J. M. Guerrero, “Micro grid transactive energy : Review, architectures, distributed ledger technologies, and market analysis,” IEEE Access , vol. 8. Institu te of Electrical and Electroni cs Engineers In c., pp. 1941 0 – 19432, 2020, doi: 10.1 1 09/ACCESS .2020.296 8402. [188] Y. Jiao, P. Wang, D. Ni yato, and K. Suankaewman ee, “Auction Mechanisms in Clo ud/F o g Computing Resource Allocation for Pub l ic Blockchain Networks,” IEEE Trans. Pa rallel Distr ib. Syst. , vol. 3 0, no. 9, pp. 1975 – 1989, M ar. 2019, doi: 10.1109/tp ds.2019.29002 38. [189] Z. Xiong , S. Feng , W. Wang, D. Niyato, P. Wang, and Z. Han, “Clo ud/fog computing r esource management and pricing for blockchain networks,” IEEE Internet Things J. , vol. 6, no. 3 , pp. 4585 – 4600, Jun. 2019, doi: 10.1109/JIOT.2 018.2871706. [190] Y. Liu, F. R. Yu, X. Li, H. Ji, and V. C. M. Leung, “Blockch a in and Machine Learning for Communicat i ons and Networking Systems,” IEEE Commun. Surv. Tutorials , vol. 22, no. 2, pp. 1392 – 1431, Apr. 2020, doi: 10.1109/COMST .2020.29759 11. [191] Y. Sun, H. S ong, A . J. Jara, and R. B ie, “Internet of Things and Big Data An a lytics for Sma rt and Connected Communities,” IE EE Access , v o l. 4, pp. 7 66 – 773, 2016, doi: 10.1109 /ACCESS.201 6 .2529723. [192] X. Wang, Y. Han, V. C. M. Leung, D. Niyato, X. Yan, and X. Chen, “Conv er gence o f Edge Computi ng a nd Deep Learning: A Comprehens ive Surv ey,” IEEE Communicati ons Surveys and Tutor ials , vol. 22, no. 2. Institute of Electrical and Electroni cs Engineers In c., pp. 869 – 904, Apr . 01, 2020, do i: 10.1109/COM ST.2020.297 0550.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment