Novel Stealthy Attack and Defense Strategies for Networked Control Systems
This paper studies novel attack and defense strategies, based on a class of stealthy attacks, namely the zero-dynamics attack (ZDA), for multi-agent control systems. ZDA poses a formidable security challenge since its attack signal is hidden in the n…
Authors: Yanbing Mao, Hamidreza Jafarnejadsani, Pan Zhao
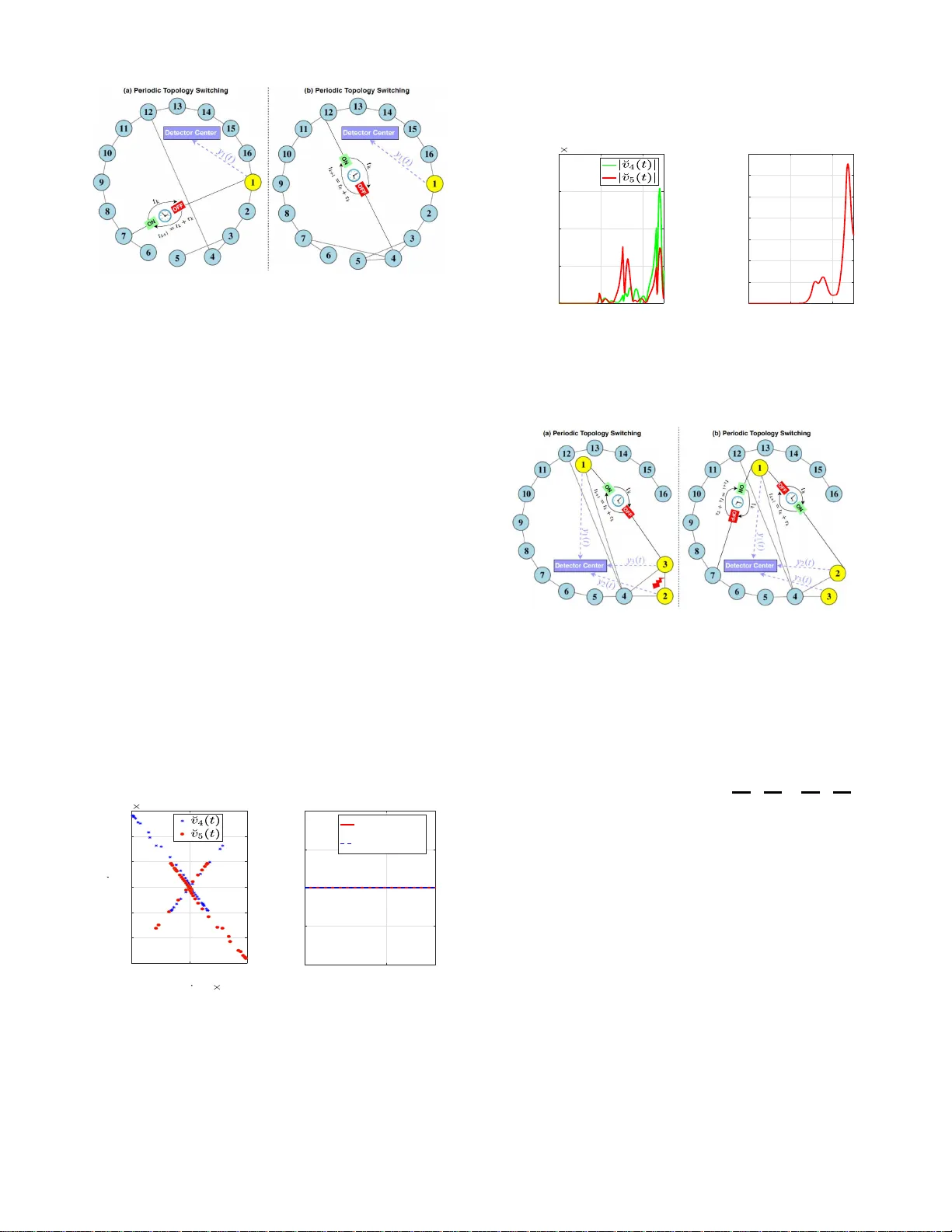
1 No v el Stealth y Attack and Defense Strate gies for Netw orke d Co n trol Systems Y anbing Mao, Hamidreza Ja farnejadsani, P an Zhao, Emrah Akyol, and Naira Hovakimyan Abstract —This paper studies nov el attac k and defense strate- gies, based on a cla ss of stealthy a ttacks, namely the zero - dynamics attack (ZD A), f or multi-agent control systems. ZD A poses a fo rmidable security challenge since its attack signal is hidden in the null-space of th e state-space repre sentation of th e control system and hence i t can evade conv entional detection methods. An intuitive defense strategy builds on changing t he af orementioned represe ntation via switching through a set of carefully crafted topologies. In this paper , we pro pose realistic ZD A variations where the attacker is aware of thi s t opology- switching strategy , and hence employs the fo llowing policies to a void detection: (i) pause, update and resume ZDA according to the knowledge of switching topologies; (ii) cooperate with a concurrent stealthy topology attack that alters network topology at switch ing times, such t h at the original ZD A is feasible u nder the corrupted topology . W e first systematically study the proposed ZD A variations, and then d ev elop defense strategies against them un der the realistic assump t i on that th e defend er has no knowledge of attack starting, pausing, an d resuming times and the numb er of misb eha ving agents. Particularly , we characterize conditions for d etectability of the p roposed ZD A variations, in terms of the network topologies to be maintained, the set of agents to b e monitored, and t h e measurements of the monitored agents that should be extracted, while simultaneously p reser ving the priva cy of the states of the non-monitored agents. W e then propose an attack detection algorithm based on the Luenberger observ er , using the characterized detectability cond itions. W e prov ide numerical simulation results to demonstrate our theo- retical findi n gs. Index T erms —M ulti-agent systems, security , privacy , zero- dynamics attack, topology attack, attack d etection. I . I N T RO D U C T I O N C OORDIN A TION and co ntrol of n etworked systems is a well-stu died theo retical pro blem (see e.g ., [2] , [3]) with many p ractical ap plications inclu d ing distributed opti- mization [4], power sharing fo r dr o op-co n trolled inverters in island ed micro g rids [5], cloc k synchr onization for sensor networks [6 ] , as well as connected veh ic le s [7], spa c ecrafts [8], and electrical power n etworks [9] . Security co ncerns regarding the afore mentioned networked systems pose a formid able threat to their wide deploym ent, Y . Mao, P . Zhao and N. Hov akimyan are with the Depart ment of Mechanica l Science and Enginee ring, Uni versit y of Illinois at Urbana–Cha mpaign, Ur- bana, IL , 61801 USA (e-mail: { ybmao, panzhao2 , nhov akim } @illinoi s.edu). H. Jafarne jadsani is with the Department of Mechanic al Engineeri ng, Ste ve ns Institute of T echnology , Hoboken, NJ, 07310 USA (e-mail: hja- farne @ste ve ns.edu). E. Akyol is with the Department of Electrical and Comput er Engineer- ing, Binghamton Univ ersity –SUNY , Binghamton, NY , 13902 USA (e-mail: eak yol@bingha mton.edu). Parts of this paper were presented at the 58th IE EE Confere nce on Decision and Control, 2019 [1]. This work is supported in part by NSF (awa rd numbers CMMI-1663460 and ECCS-1739732 ), and Binghamt on Uni versi ty–SUNY , Center for Colle cti v e Dynamics of Complex Systems ORC grant. as high lighted by the recent incid ents includin g distributed denial-of -service ( D DO S) attack on Eston ian web sites [10 ] and Maroo chy w ater breach [1 1]. The “networked” a sp ect exacerbates the difficulty of secu ring these systems, since centralized m easurement (sensing ) and control are not f easible for such large-scale systems [12], and he nce r e q uire the development of decentra lized app r oaches, which are inherently prone to attacks. Particularly , a special class of stealthy attacks, namely the “zero- dynamics attack ” (ZDA), poses a significant security challenge [13 ]–[15 ]. The main idea behin d ZDA is to hide the attack sign a l in th e null-sp a ce of the state- space r epresentation of the contr o l system so that it cannot be d etected by applying conventional detection methods on the observation signal. The objectiv e of such an attac k can vary from ma n ipulating th e controller to accep t false data that would yield the system towards a desired (e.g., un stab le) state to maliciously altering sy stem dynamics (top ology attack) to affect the system trajec to ry . Recent research efforts have focu sed on variations o f ZD A for systems with distinct properties. For stochastic cyber - physical systems, Park et a l. [16] designed a r obust ZD A, where the attack-detection sign al is gu aranteed to stay below a thresho ld over a finite horizo n . In [17] , Kim et al. p roposed a discretized ZD A for th e sampled-da ta con tr ol systems, where th e attack- d etection signal is constant zero at the sampling times. Another intere sting line o f r esearch pertain s to developing def ense strategies [1 2], [ 1 8]–[2 1]. For example, Jafarnejadsani et al. [ 14] propo sed a multi-r ate L 1 adaptive controller th at can detec t ZDA in sampled-da ta co ntrol system s by removing certain u n stable zero s of discrete-time systems. Back et al. [22] used generalized hold strategy to mitigate the impact of ZD A. Most of the prio r work on de f ense strategies for th e o r ig- inal ZD A in networked systems builds on rather r estrictiv e assumptions regar d ing the con nectivity o f ne twork topolo gy and the num b er o f the misbehaving ag ents (i.e . , the agents under attack ) [1 2], [ 1 8]–[2 0]. T eixeira et al. [23 ] showed that the strategic chang es in system d ynamics co uld be u sed by defend e r to detect ZD A. But th e defense strategy r equires the attack- starting times to be the initial time and known to defender, and the attacker has no capab ility of inferring the chang ed system dynamics. In o ther words, the defen se strategy fails to work if the stealthy attack strategy is based on the newly inferred system dynamics. As a first step towards a practical ZD A defense strategy , in [24] , strategic topology switching is prop osed. This strategy is motivated b y the feasibility of co ntrolling com munication to pology dr iv en due to re c ent developments in mobile c o mputing , wir eless com- 2 munication a n d sensing [25] , [ 26]. W e note, in passing, that the idea of u sing the chan ges in the state-space d y namics to detect ZD A first a p peared in [23 ], albeit a re alistic me c h anism (e.g., switching the system topo logy) to achieve that objectiv e was only very recently studied in [24]. Howe ver , the defense strategy in [24 ] still re lies on a naive attacker that does not take the topo logy switching strategy of the def ender into account. In this p aper, we systematically address this practically importan t pro blem: wh at kind of Z D A strategies ca n an informe d attacker design ag a inst a topolog y-switching system and wh at ar e the optimal defense strategies, b eyond switching the topology , against such intelligen t attacks? W e note that we study th e se questions under re a listic assum ptions on the capabilities of th e d efender, i.e., we assume that the defend er does not know the start, pau se an d resume times of the attack or th e number of m isbehaving agents. W e also assume that the attacker is aware of the strategic cha nges in system d ynamics. Moreover , we a ssum e that th e defend er has to preserve the priv acy of the outp u ts of the non-mo nitored ag ents, since it is assumed that the attacker h as access to the sensor o utputs. The following example from co ordinatio n control illustra te s our motiv ation to im pose this priv acy constrain t. For the coor dination co n trol of multi-age n t systems, e.g., the connected au tonomo us vehicles, the data of initial po sitions and velocities ca n be u sed by the ad versary to estimate target location [27], and the indi vidual initial positions in- clude individual home-base locations. Once the attac ker has access to the ou tputs of monitored agents and the system is observable, the attacker can use curre n t avail able data to infer the global initial con dition and g lobal real-time system state. From a perspec tive o f stealthy to p ology attack design (e.g., top ology attack in smart grids [28] and software-defined networks [29]), the attacker needs (estimate d ) real-tim e d a ta of some agents’ state to decide the target conn ection links to attack. Un f ortunately , th e inferr ed g lobal real-time system state implies the largest scope of attackable conn ection link s is exposed to the attacker . T o red uce th e f easible area of target links for Z DA in cooperatio n with a stealthy topolog y attack, monitore d outputs have to b e co nstrained to be u nobservable to preserve the privac y of non-mo nitored agen ts’ real-time states, co nsequently , the g lobal system state and global initial condition . Throu g hout this pa p er , we fo cus on the following policies which can be used b y the attacker to ev ade d e tection: 1) interm ittently pau se attack if the incoming to pology is unknown, and update (if necessary) an d resume attack after the newly activ ated topolo gy is inferred (in termit- tent ZDA). 2) coop eratively work with a stealthy topolog y attack, such that the orig inal ZDA policy continu es to be f easible under the cor rupted top ology ( c ooperative ZD A). In this paper, we d ev elop integrated def ense stra tegies for both inter mittent and co operative ZD As, in th e presen ce of priv acy con siderations. More specifically , we d ev elop defense strategies to address the fo llowing qu estions: wha t n etwork topolog y shou ld be m a in tained, which agen ts should be mo n- itored and what measuremen ts the mo nitored agen ts sho uld output, such that the intermittent and co o perative ZD A variants are detectab le, and at the same tim e , the priv acy o f non - monitore d agents’ real-time states are preserved? Based on the answers of the que stion s above, we next pro pose a strategic topolog y-switching algor ith m to detect the Z D A. The contributions ar e su mmarized as follows. • T o ev ade conventional detection method s th at r ely on naive attacker, we pro p ose two ZD A variations: inter mit- tent and co operative Z D As, where the attac ker is aw are of the def ense strategy and has prac tical capability of inferring switching topolo g ies. • W e systematically study th e policies of ZDA variations that the attacker follows to devise stealthy attacks that lay the found ation for the novel def ense strategies. • W e char acterize cond itions for detec tab ility of the pr o - posed ZDA variations, in terms of the n e twork topolog ies to be maintain e d, the set of agen ts to b e monito r ed, and the measu rements of the m o nitored agents that sho uld b e extracted. • Und e r th e pri vacy-preserving constraint of non-mo nitored agents’ states, we propose a strategic to pology -switching algorithm for attack detection th at is b ased on the de- tectability of Z D A variations using the Luenb erger o b- server . The advantages of this approach include: – in ach ieving consensus and tr acking real systems in the absence of attacks, it ha s n o constrain t on the magnitud es of cou pling weigh ts and observer gains; – in detectin g ZD A v ariations, it allows the defender to be un aware of attack star tin g, pausing , and r esuming times and the n umber o f misbehaving agents; – in d etecting ZD A variations, o nly one mon itored agent is sufficient for inter m ittent ZD A and only two monitore d agents are sufficient fo r coo perative ZD A. This paper is organized as fo llows. W e present the prelim- inaries and th e problem fo rmulation in Section s I I and II I , respectively . In Sectio n IV , we analy z e the propo sed ZD A variations. I n Section V , we ch aracterize the co nditions fo r detectability of these ZD A variations. Based on this charac- terization, we d evelop an attack d etection algo rithm in Section VI. Num erical simulation r e su lts are provided in Section VII, and the conclud ing remar k s an d the future research direction s are discussed in Section VIII . I I . P R E L I M I N A R I E S A. Notatio n W e let R n and R m × n denote the set of n -d imensional real vectors and the set of m × n -dimension al real m a tr ices, respectively . Let C denote the set of co mplex numbers. N represents the set o f the natural number s and N 0 = N ∪ { 0 } . Let 1 n × n and 0 n × n be the n × n -d im ensional iden- tity matr ix and zer o matr ix, respectively . 1 n ∈ R n and 0 n ∈ R n denote the vector with all ones and the vector with all zeros, r espectively . Th e supe r script ‘ ⊤ ’ stands for matrix transp o se. µ P ( A ) den otes the induced P -norm matrix measure of A ∈ R n × n , with P > 0 , i.e. , µ P ( A ) = 1 2 max i =1 ,...,n λ i P 1 / 2 AP − 1 / 2 + P − 1 / 2 A ⊤ P 1 / 2 . ker ( Q ) , { y : Q y = 0 n , Q ∈ R n × n } , A − 1 F , { y : Ay ∈ F } . Also, |·| 3 denotes th e cardinality of a set, or th e modulus of a num ber . V \ K describes the com plement set of K with respect to V . λ i ( M ) is i th eigenv alue of matrix M . x ( b ) ( t ) stands for the b th -order time d eriv ati ve o f x ( t ) . For a matr ix W ∈ R n × n , W k , [ W ] i,j , [ W ] i, : , and [ W ] a : b,c : d denote th e k th power o f W , the elemen t in row i an d column j , the b th row , and the sub-matrix forme d by the en tr ies in the a th throug h b th row and the c th throug h d th column of W , respectively . The interaction among n ag ents is mo deled b y an undirected graph G , ( V , E ) , wh ere V , { 1 , 2 , . . . , n } is the set of vertices tha t rep resents n a g ents and E ⊆ V × V is the set of edges of the graph G . The weighted adjacency matrix A = [ a ij ] ∈ R n × n of the gr aph G is defined as a ij = a j i > 0 if ( i, j ) ∈ E , and a ij = a j i = 0 otherwise. Assum e that ther e are n o self - loops, i.e., for any i ∈ V , a ii = 0 . Th e Laplacian matrix of gra ph G is defined as L , [ l ij ] ∈ R n × n , where l ii , n P j =1 a ij , an d l ij , − a ij for i 6 = j . T he d iameter m of a grap h is th e longest shortest unweighted path between any two vertices in the graph. B. Defi nitions A second-o rder system con sists of a population of n agents whose dynam ics are governed by th e following equatio ns: ˙ x i ( t ) = v i ( t ) , (1a) ˙ v i ( t ) = u i ( t ) , i = 1 , . . . , n (1b) where x i ( t ) ∈ R is the position, v i ( t ) ∈ R is th e veloc ity , and u i ( t ) ∈ R is the local control inp ut. Th e broad applications of its coordin a tion c o ntrol is th e main m otiv ation of this paper considerin g the m o del (1 ), see e.g., [30]–[3 3]. For coo rdination control, we consider the more rep r esentativ e av erage consen- sus. W e recall th e definitions of consensus and ZDA to revie w the contr ol ob je c ti ve and the attack p olicy . Definition 1: [34] The agents in the system (1) are said to ach iev e the asympto tic consensu s w ith fin al zero com m on velocity if f or any initial condition : lim t →∞ | x i ( t ) − x j ( t ) | = 0 and lim t →∞ | v i ( t ) | = 0 , ∀ i, j ∈ V . (2 ) Definition 2: [1 2], [35] Consider the system (with proper dimension) in the pr esence of attack signal ˘ g ( t ) : ˙ ˘ z ( t ) = A ˘ z ( t ) + B ˘ g ( t ) , (3a) ˘ y ( t ) = C ˘ z ( t ) + D ˘ g ( t ) . (3b) The a ttac k signal ˘ g ( t ) = g e ηt is a zer o-dynamics attack if there exist a scalar η ∈ C , an d nonze r o vectors z 0 and g , that satisfy z 0 − g ∈ ker η 1 n × n − A B − C D . (4) Moreover , the states and observed outputs o f system (7) satisfy ˘ y ( t ) = y ( t ) , t ≥ 0 (5) ˘ z ( t ) = z ( t ) + z 0 e ηt , (6) where y ( t ) an d z ( t ) are the output and state of th e system (3) in the absen c e o f attacks, i.e., the dyn amics: ˙ z ( t ) = Az ( t ) , (7a) y ( t ) = C z ( t ) . (7b) C. Contr ol Pr otocol W e borr ow a contr ol protocol that inv olves topo logy switch- ing from [ 34], [36] to achieve the consen sus ( 2) for the agents in system (1): u i ( t ) = − v i ( t ) + X j ∈ V a σ ( t ) ij ( x j ( t ) − x i ( t )) , i ∈ V (8) where σ ( t ) : [ t 0 , ∞ ) → S , { 1 , . . . , s } , is the switching signal of the interaction topo logy of the communicatio n network; a σ ( t ) ij is the entry o f the weig hted adjac e ncy matrix that describes the activ ated to pology of commun ication grap h. I I I . P RO B L E M F O R M U L A T I O N W e let K ⊆ V de n ote the set of misbehaving agents, i.e., the agents whose local control in puts are under attack. For simplicity , we let th e in creasingly ordered set M , { 1 , 2 , . . . } ⊆ V d enote the set o f m o nitored ag ents for attack detec tion. W e make the f ollowing assumptio n s o n the attacker and defend e r through out this pap er . Assumption 1: The attacker 1) is aware that the changes in system dynam ics are used by the defend er (system op erator); 2) knows the initial topolo gy , output matrix and switchin g times; 3) need s a non- ne gligible time to exactly infer the ne wly activ ated topolo gy , c ompute and upd a te attack strategy; 4) recor ds the n ewly inferr ed topolo g y into me mory; 5) knows th e o utputs of mon ito red agen ts in M . Assumption 2: The def ender 1) design s the switching time s and switching topolog ies; 2) choo ses can didate agents to mon itor , i. e ., the monito red agent set M , for attack de te c tio n; 3) has no knowledge of the attack starting, pausing and resuming times, and the misbeh aving agents. Remark 1: In Assump tion 1 , the assumed attacker’ s ca- pability 2) is motiv ated by recent inciden ts, see e.g., the revenge sew age attack (cyber attack) that led to the Maroochy water breach, wh ere the attacker h ad previously installed the in dustrial con tr ol systems for the water service network (consequ ently , h e knew the control proto col and the locations of sensors) [37] . Remark 2 : Strategically ch anging the system dynam ics has b een demonstrated to be an e ffective appr oach to detect system-based stealthy attack s, see e . g., ZD A [23 ], [2 4] and C k / C stealthy attack s [38]. The core idea beh ind this defen se strategy is the intention al gene r ation of mismatch between the models of th e attacker and the def ender . Sp ecifically , the attacker uses the original system dynamics to make the stealthy attack decision (i.e., the co mputation (4)) before the system starts to o perate, while the defender strategically change s the system dynamics at some operating p oint in time. H owever , 4 from the attacker’ s perspective, it is prac tica l to b ecome aware of th is d efense strategy , and hence try to infer th e changed system dynamics to update the stealthy attack strategy and ev ade d e tection. T h is motiv ates the awareness c a pability 1 ) in Assumption 1. Remark 3 : Altho ugh the switching top o logies are kept confidential fro m attackers, the dev eloped topolog y inf erence algorithm s [3 9], [4 0] enable the attacker to exactly infer the switching topolo gies f rom observation sig nals. Even with the global ability of observin g all age n ts’ states, the in ference algorithm s need to collect the state data over a time interval to obtain an exact top ology so lu tion, which explains the imp osed non-n e gligible time in capability 3) in A ssum ption 1. Remark 4: Since th e sensor devices ar e embedd ed within an en vironmen t, they are frequently v ulnerab le to local ea ves- dropp ing, which is the m otiv ation of cap a bility 5) in As- sumption 1 . The ZDA policy (4) shows that th e attacker do es not need the capability 5) to obtain a feasible attack strategy consisting of the false d ata z 0 , and the p arameters g a n d η of attack signal ˘ g ( t ) . However , when ZD A seeks co operation w ith a stealthy to pology attack in r e sponse to strategic topolog y switching d efense, th e n the attacker needs the real-time ou tp uts indicated by th e capab ility to identify the ta rget links to attack. Remark 5: As analyzed in [1], the defense strategy of strate- gically chan ging sy stem dynamic s [23 ] imp licitly assumes that the attack - starting time m ust be the initial time and k n own to the def e nder . The capab ility 3) of de f ender in Assump tio n 2 removes this unr ealistic assump tion. A. T opology S witching Strategy The building block of o ur defense strategy is pe riodic topolog y switching, i.e., there exists a per iod τ such that σ ( t ) = σ ( t + τ ) ∈ S . (9) • W e n ote that (9) implies the building blo c k belongs to the time-depen dent top ology switching. The critical reason that we do n ot c onsider state-depend ent switching is th e attack signals in jected into control in put may g enerate a Zeno behavior [41] that r enders the co ntrol protoco l (8 ) infeasible. • If the top ology switching is random , the defender needs to often send th e generated “rando m” info rmation of network topology to th e detector/estimator/o bserver in the cyber layer as well, wh ich will be sub jec t to a cyber to pology attack (inc orrect informatio n o f network topolog y is transmitted) [28], [29 ], [ 4 2]. T o a void this type of cyber attack, the defend er chooses her e period ic topolog y switching, an d pre p rogram the (repeated) p eri- odic switching seque n ce into the co ntrolled links, and hence av oids sending the topology informatio n to the cyber laye r d uring the system opera tion. For our defe n se strategy based on the periodic topolog y switching (9), we defin e the following per iodic sequ ence with length of l : L , σ ( t 0 ) | {z } τ 0 , σ ( t 1 ) | {z } τ 1 , . . . , σ ( t l − 2 ) | {z } τ l − 2 , σ ( t l − 1 ) | {z } τ l − 1 , (10) where τ k denotes the dwell time o f the activ ated topology indexed by σ ( t k ) , i.e., τ k = t k +1 − t k . Next, we study wh ether the age n ts in the system (1) using control inp ut (8 ) can re ach con sensus un d er period ic topo logy switching. W e first recall the well-known p roperty of Lapla- cian matrix L r of a connecte d undir ected grap h f rom [43]: Q ⊤ r = Q − 1 r , (11a) [ Q r ] 1 , 1 = [ Q r ] 2 , 1 = . . . = [ Q r ] | V | , 1 , (11b) Q ⊤ r L r Q r = diag { 0 , λ 2 ( L r ) , . . . , λ n ( L r ) } , Λ r , (11c) based on which, we d efine: Υ r s , Q ⊤ r L s Q r , (12a) A s , 0 ( | V |− 1) × ( | V |− 1) 1 ( | V |− 1) × ( | V |− 1) − [Υ r s ] 2: | V | , 2: | V | − 1 ( | V |− 1) × ( | V |− 1) . (12b) Pr o position 1: Consider th e seco nd-ord er m ulti-agent sys- tem (1) with co ntrol inpu t (8). If the sequen ce L in (10 ) in- cludes on e co nnected top ology , there exists a per iodic top ology sequence that satisfies l − 1 X s =0 ν s µ P ( A s ) < 0 , (13) where ν s = τ s τ with τ = l − 1 P i =0 τ i . Moreover , un der th at periodic topolog y switching, the consen sus (2 ) can be achieved. Pr o of: See Appen dix B. Remark 6: Prop osition 1 imp lies that periodic topolog y switching has no constraint on the magnitu des of cou pling weights in ach ieving co nsensus, i.e. , f or any couplin g weights there exists a feasible p eriodic topolo gy switchin g sequenc e for con sensus. This is in sharp con trast with the arbitrary topolog y switching that imposes a strict cond ition on the magnitud es of coup ling weig hts in achieving consensus [36] . B. Sy stem Description Under perio dic top ology switching, the multi-ag ent system in (1), with the control inpu t given by (8) and the o utputs of monitore d agen ts in M subject to the a ttack signal g i ( t ) , can be written as ˙ ˘ x i ( t ) = ˘ v i ( t ) (14a) ˙ ˘ v i ( t ) = − ˘ v i ( t ) + X j ∈ V a σ ( t ) ij ( ˘ x j ( t ) − ˘ x i ( t )) + g i ( t ) , i ∈ K 0 , i ∈ V \ K (14b) ˘ y i ( t ) = c i 1 ˘ x i ( t ) + c i 2 ˘ v i ( t ) + d i g i ( t ) , i ∈ M (14c) where c i 1 and c i 2 are constant coefficients de sig ned by the defend e r (system operato r ), wh ile constant coefficient d i is designed by the attacker . Remark 7: The m odel in (14b ) with (1b) implies that there are two practical app roaches to attack the local contro l inputs: (i) the attacker directly injects the attack sig n al to the control arch itectures of misbeh aving age n ts (target agents) in K ; (ii) possibly throug h b reaking the encry ption algorithm that protects th e commu nication channels with misbe having agents, the attacker injects attack signals to the data sent to controller . 5 The system in (14 ) can be equ ivalently expressed as a switched system und er attack : ˙ ˘ z ( t ) = A σ ( t ) ˘ z ( t ) + ˘ g ( t ) (15a) ˘ y ( t ) = C ˘ z ( t ) + D ˘ g ( t ) , (15b) where we define : ˘ z ( t ) , ˘ x 1 ( t ) . . . ˘ x | V | ( t ) ˘ v 1 ( t ) . . . ˘ v | V | ( t ) ⊤ , (16a) A σ ( t ) , 0 | V |×| V | 1 | V |×| V | −L σ ( t ) − 1 | V |×| V | , (16b) C , C 1 C 2 , (16c) C j , diag c 1 j , . . . , c | M | j 0 | M |× ( | V |−| M | ) , j = 1 , 2 (16d) D , 0 | M |×| V | diag d 1 , . . . , d | M | 0 | M |× ( | V |−| M | ) , (16e) ˘ g ( t ) , h 0 ⊤ | V | ¯ g ⊤ ( t ) i ⊤ , (16f) ¯ g i ( t ) , g i ( t ) , i ∈ K 0 , i ∈ V \ K . (16g) In ad dition, we c o nsider the sy stem (15) in the a b sence of attacks, which is given by ˙ z ( t ) = A σ ( t ) z ( t ) , (17a) y ( t ) = C z ( t ) . (17b) C. P riva cy o f Initial Conditio n an d Globa l S ystem State T o fully secure multi-agent systems, e.g., connected au- tonomo us veh icle s, the initial cond itio ns should be k ept confidential from an adversary since the initial da ta co uld be u tilized to estimate the target lo cations [27] . Moreover , individual in itial positions contain the informatio n of hom e- base locatio ns. The f ollowing two examples illustrate that the global initial conditio n as well as the globa l system state play an importan t role in stealthy attack s. Example 1 (Attack Objective) : Th e state solution un der attack ( 6 ) implies that if η = 0 , a ttacker’ s o bjective is to modify the steady-state value. If the attack objective is to modify the target location to a new lo cation that the attacker desires, the attacker mu st know the original target loc a tion in the absen ce of attacks. Under un d irected communica tio n, it is straightfo rward to verify from the system (1) with its control input (8) tha t th e average p osition ¯ x ( t ) ∆ = 1 | V | P i ∈ V x i ( t ) proceed s with the average veloc ity ¯ v ( t ) ∆ = 1 | V | P i ∈ V v i ( t ) = e − t ¯ v ( t 0 ) , which indicates that when the consensu s is achieved, all of the ind i vidual agents sync h ronize to th e target location: x ∗ = lim t →∞ ¯ x ( t 0 ) + 1 − e − t ¯ v ( t 0 ) = ¯ x ( t 0 ) + ¯ v ( t 0 ) . (18) Unfortu n ately , (1 8) shows that o n ce the global initial cond ition is known (i.e., initial position s and velocities of all age nts), the origina l target location can simply be co mputed through a simple mean compu tation. Example 2 (Stea lthy T op ology Attack Design): Stealthy topolog y attack design, as in smart grids [28] and power networks [42], requ ires (estimated) real-tim e data of system states to choose the target connection links to maliciously alter . Since attacker c an record the newly ob tained kn owledge of the network topolog y , the attacker has the mem ory of the p ast topolog y sequ ence. Whenever the data o n the g lobal initial condition z ( t 0 ) (or real-tim e glo bal state z ( t ) ) is available, the attacker c a n in fer the exact re al-time glo bal state z ( t ) (or global initial conditio n z ( t 0 ) ) throu gh z ( t ) = e A σ ( t k ) ( t − t k ) k − 1 Y l =0 e A σ ( t l ) ( t l +1 − t l ) z ( t 0 ) , t ∈ [ t k , t k +1 ) which ind ica tes whenever ZDA seeks a co operation with stealthy topolo gy attack to e vade detection , the attacker would have th e largest scope of attackable link s since th e attacker knows all of agen ts’ real-time state data. Ther efore, the pr i vate global in itial cond itio n or system state can reduce th e scope of target lin ks f or stealthy topolog y attack. W e next imp o se the fo llowing un observability co ndition on the monitored ou tputs to preserve th e p riv acy o f n on- monitore d agents, such that the attacker cannot use the av ail- able (monitor ed) outpu ts to in fer any n on-mo n itored agen t’ s full state ( and conseq uently , th e glob a l system state and initial condition ). Lemma 1: For the system (17 ), x i ( t ) and v i ( t ) , ∀ i ∈ V \ M , are not simultan eously o bservable for any t ∈ [ t 0 , t + m ) , if and only if ∃ p ∈ N m 0 : | p i | + p i + | V | 6 = 0 , ∀ i ∈ V \ M (19) where N m m = ker ( O m ) , (20) N m q = ker( O q ) \ e − A σ ( t q ) τ q N m q +1 , 0 ≤ q ≤ m − 1 (21) O q = h C ⊤ ( C A σ ( t q ) ) ⊤ . . . ( C A 2 | V |− 1 σ ( t q ) ) ⊤ i ⊤ . (22) Pr o of: The conditio n in (1 9) im plies th at N m 0 6 = 0 2 | V | . Using Theorem 1 in [44 ], it follows th at the system in (17) is unobservable for any t ∈ [ t 0 , t + m ) . Also, (1 9 ) implies that p i 6 = 0 , and ( o r) p i + | V | 6 = 0 , and therefore the agen t i ’ s po sition and (or) velocity are (is) not par tially o bservable. Remark 8: Altho ugh th e selection of the monito red output coefficients in (14c) subje c t to ( 19) render s the system (17) unobser vable to preserve privac y , we will show that the propo sed ZDA variations become detectab le u sing the outputs y i ( t ) ’ s by careful selection of switchin g top ologies and the set of monitor ed agents. I V . S T E A LT H Y A T TAC K M O D E L In the scenario where the attacker is aware of the detection purpo se of strategic changes in system dyn amics indu ced b y topolog y switching [24] , the attacker can ev olve the attack policies in respo n se to the strategic chang es at switch ing times to stay stealthy: • “pau se attack” befo re topo logy switchin g wh e n the in- coming topology is unknown or the attack policy (4) is infeasible u nder the k nown in c oming topolo gy , and “resume a ttac k ” after the feasibility of (u pdated if needed) attack policy und er the inferr e d activ ated top o logy is verified; • coo perate with a topo logy attack that maliciously alters network to pology at switching times, such that the orig- inal attack po licy (4) co ntinues to be f easible under the corrup ted topolo g y . 6 In the following subsection s, we pre sen t a systematic study on these ZDA variations. A. In termittent Zer o-Dyna m ic s Attack For convenience, we refer to T as the set of topologies un der which the attacker injects attack signals to contro l inputs, and we r e f er to ξ k and ζ k as the attack- r esuming and attack- pausing time s over the acti ve topolog y intervals [ t k , t k +1 ) , k ∈ N 0 , r espectively . The ZD A signals injected into th e control input and m on- itored output of system (14) with interm ittent pausing an d resuming behaviors are described as g i ( t ) = g σ ( t k ) i e η σ ( t k ) ( t − ξ k ) , t ∈ [ ξ k , ζ k ) ⊆ [ t k , t k +1 ) 0 , other wise . (23) T o an alyze this ZD A, we review the m onitored output (14c ) at the first “p a u sing” time ζ 0 : ˘ y i ζ − 0 = c i 1 ˘ x i ( ζ − 0 ) + c i 2 ˘ v i ( ζ − 0 ) + d i g i ζ − 0 , ∀ i ∈ M which implies that ˘ y i ζ − 0 = ˘ y i ( ζ 0 ) if and only if g i ζ − 0 = g i ( ζ 0 ) , since ˘ v i ζ − 0 = ˘ v i ( ζ 0 ) and ˘ x i ζ − 0 = ˘ x i ( ζ 0 ) . Me an- while, the velocity and p osition states are always co ntinuou s with respect to time, and hence the mon itored o utputs must be continu o us as well. Therefo re, to avoid the “jump” on monitore d outputs to maintain the stealth y prop erty (5), th e attacker cannot co mpletely pause the attack, i.e., whenev er the attacker pauses injecting ZDA signals to co ntrol inputs at pausing tim e ζ k , simu ltan eously co ntinues to inject the same attack signals to mo nitored o utputs (14c): ˘ y i ( t ) = c i 1 ˘ x i ( t ) + c i 2 ˘ v i ( t ) + d i k X m =0 g i ζ − m , t ∈ [ ζ k , ξ k +1 ) (24) or equiv alently , ˘ y ( t ) = C ˘ z ( t ) + D k X m =0 ˘ g ζ − m , t ∈ [ ζ k , ξ k +1 ) . (25) Based on the above analysis, for ZD A po licy consisting of “p ause attack” an d “resu me attack ” beh aviors to remain stealthy , it sho u ld satisfy ( 25) and z ( t 0 ) ∈ b N k 0 \ e N k 0 , (26a) z ( ξ k ) − ˘ g ( ξ k ) ∈ ker ( P r ) , ∀ σ ( ξ k ) ∈ T (26b) where b N k k = ker( O k ) , (27) b N k q = ker( O q ) \ e − A σ ( t q ) ( τ q − ( ζ q − ξ q )) N k q +1 , 0 ≤ q ≤ k − 1 (28) e N k k = ker( e O k ) , (29) e N k q = ker( e O q ) \ e − A σ ( t q ) ( τ q − ( ζ q − ξ q )) N k q +1 , 0 ≤ q ≤ k − 1 (30) e O r , h ( C A r ) ⊤ ( C A 2 r ) ⊤ . . . ( C A 2 | V | r ) ⊤ i ⊤ , (31) P r , η r 1 2 | V |× 2 | V | − A r 1 2 | V |× 2 | V | − C D , (32) z = x ⊤ v ⊤ ⊤ , ˘ z − z = ˘ x ⊤ − x ⊤ ˘ v ⊤ − v ⊤ ⊤ , (33) and O r is giv en b y (22). Pr o position 2: Und er the stealthy attack p olicy consisting of (25) and (26), th e states and monitored outp u ts o f the systems (17) and (15) in the presence o f attack signal (23 ) satisfy ˘ y ( t ) = y ( t ) , t ∈ [ t 0 , t k +1 ) , (34) ˘ z ( t ) = z ( t ) + e η σ ( t k ) ( t − ξ k ) z ( ξ k ) , t ∈ [ ξ k , ζ k ) . (35) Pr o of: See Appen dix C. Remark 9: At first glance, it might seem that the intermittent ZD A is an asynch ronou s attack respon se to the strategic topol- ogy switching, wh ich is due to th e imposed n on-negligible time on capability 3 ) in Assumption 1 . W e n ote however that the attacker can record the newly obtained topology knowledge into th e memory . Since the defend er switches topolog ies p eriodically , if the r ecorded length of to pology sequence is sufficiently lo ng, the attacker can learn from the recorded memory the (recurrin g) period ic sequ ence, i.e., the attac ker knows all fu tu re switching topologies and times. The correspon d ing future synchron ous attack policies can be obtained off-line. Therefo re, a synchron ous attack response is possible o nly a f ter the attacker obtains th e (re c urring) per iodic topolog y sequence from mem ory . B. Coo p erative Zer o-Dynamics Attack The objective o f co operation with stealthy topo logy attac k is to make the ZD A policy (4) con tinue to hold under the corrup ted to p ology . Stealthy to pology attack can be o f two types: • Physical T o pology A ttac k : th e attac ker maliciously alters the status of target conn ection links of physical systems, e.g., the bus intera ction breaks in power networks [42] and link fabrication in software-defined n etworks [29]. • Cyber T op ology Attack: the attacker malicio usly alters the inform a tion of network topolog y sent to the estima- tor/observer/d etector in cyber layer [2 8], [ 45]. As stated in Subsection I I I-A, the basis of our defen se strategy is th e perio d ic top ology switching , an d the defend er (system oper ator) would prep rogram the r e peated switching times an d topo logies into the contro lled links of the real system and observer/detector . In this case, th e operator o f the real system do e s not need to sen d the top ology info r mation to the observer/detecto r when the system op erates. Th erefore , the system un der ou r defen se strategy is not subject to a cyber topolog y attack, albeit it is subject to a ph ysical top ology attack. W e let t k +1 denote th e switching tim e whe n ZD A coope r- ates with top ology attack . The multi-age nt system (15) in the presence of such coo perative attack s is described b y ˙ ˘ z ( t ) = b A σ ( t ) ˘ z ( t ) + ˘ g ( t ) , t ∈ [ t k +1 , t k +2 ) (36a) ˘ y ( t ) = C ˘ z ( t ) + D ˘ g ( t ) , (36b) where b A σ ( t ) is defined as b A σ ( t ) , 0 | V |×| V | 1 | V |×| V | − b L σ ( t ) − 1 | V |×| V | , (37) with b L σ ( t k +1 ) denoting the Laplacian ma trix of the corr upted topolog y . W e describe its corr espondin g system in the absence 7 of Z D A, i.e., in the pre sence of the only p hysical topo logy attack, as ˙ b z ( t ) = b A σ ( t ) b z ( t ) , t ∈ [ t k +1 , t k +2 ) (38a) b y ( t ) = C b z ( t ) . (38b) If ˘ g ( t ) is a ZD A signa l in systems (15) an d (36) at times t − k +1 and t k +1 , by (6) we h av e ˘ z ( t k +1 ) = ˘ z t − k +1 = z t − k +1 + z 0 e ηt k +1 and ˘ z t − k +1 = ˘ z ( t k +1 ) = b z ( t k +1 ) + z 0 e ηt k +1 . Here, we con clude that b z ( t k +1 ) = z t − k +1 = z ( t k +1 ) , (39) otherwise, the system state ˘ z ( t k +1 ) has “jump” behavior , which contrad icts with the fact that ˘ z ( · ) is continuo u s. The equation ( 39) and the stealthy prop erty (5 ) imp ly th at C ˘ z ( t k +1 ) = C z ( t k +1 ) = C b z ( t k +1 ) , based on which , a necessary condition for the existence of ZD A und er cor r upted topolog y is stated for m ally in the following propo sition. Pr o position 3: Consider the systems in (38) and (17). W e have y ( t ) = b y ( t ) for any t ∈ [ t k +1 , t k +2 ) , if and on ly if d X l =0 C b A l σ ( t k +1 ) ( b A σ ( t k +1 ) − A σ ( t k +1 ) ) z ( d − l ) ( t k +1 ) = 0 | M | , ∀ d ∈ N 0 . (40) Pr o of: See Appen dix D. W e set d = 0 , 1 and expand (4 0) out to ob ta in : C 2 ( b L σ ( t k +1 ) − L σ ( t k +1 ) ) x ( t k +1 ) = 0 | M | , (41a) C 2 ( b L σ ( t k +1 ) − L σ ( t k +1 ) ) v ( t k +1 ) = 0 | M | . (41b) The result (41 ) shows that like the stealthy topo logy attacks in smar t grids [2 8], [45] and software-defined n etworks [ 29], the attacker need s some a g ents’ rea l-time state data to decide the target lin ks to attack, wh ile acco rding to Lemma 1 , the attacker canno t simultaneo usly infer x i ( t k +1 ) and v i ( t k +1 ) , ∀ i ∈ V \ M . Th erefore , there should b e a scop e o f attackab le connectio n links und er the strategy (19). W ithout loss o f generality , we express the difference o f Laplacian matrices in the fo rm: b L σ ( t k +1 ) − L σ ( t k +1 ) = L σ ( t k +1 ) 0 | D | × ( | V |−| D | ) 0 ( | V |−| D | ) × | D | 0 ( | V |−| D | ) × ( | V |−| D | ) , (42) where D d enotes the set of agents in the sub-graph formed by the target links to be p ossibly attacked, L σ ( t k +1 ) ∈ R | D |×| D | is the elementary row transfor m ation o f the Laplacian matrix of a subgrap h G in the difference gr a ph, wh ich is gener ated by the corrup ted graph b G t k +1 of the topolog y attacker and can didate graph G t k +1 of the defe nder at time t k +1 . Since C 2 ∈ R | M |×| V | and L σ ( t k +1 ) ∈ R | D |×| D | , th e relations in (19), (41), and (42) imply that the attacker can devise a stealthy topolo g y a ttac k (witho u t kn owing the m easuremen ts of the agents in V \ M which are unavailable) only wh en the scope of target links satisfies: D ⊆ M . (43) V . D E T E C TA B I L I T Y O F S T E A L T H Y A T TAC K S Based on the systematic study o f the attac k behaviors an d policies in Section IV , in this section, we in vestigate th e detectability of the pro posed ZD A variations. A. Detecta bility of I ntermittent Zer o- Dynamics Attack W e fir st define U r i , diag n [ Q r ] i, 1 , . . . , [ Q r ] i, | V | o Q ⊤ r , (44) F , n i | [ Q r ] i,j 6 = 0 , i ∈ M , ∀ j ∈ V , ∀ r ∈ L o , (45) where Q r satisfies (11). Strategy on switching to pologies: L r has distinct eigenv alues for ∀ r ∈ L . Strategy on mo nitored- a gent locations: F 6 = ∅ . Defense Strategy Against Intermittent ZD A (46) (47) Theor em 1: Consider the sy stem (14) in the p resence of attack signals (23). Under the defense strategy against inter- mittent ZD A, • if the monitore d agents ou tput the fu ll observations of their velocities (i.e., c i 1 = 0 and c i 2 6 = 0 for ∀ i ∈ M ), the intermittent ZDA is detectable and N ∞ 0 = 0 2 | V | , h 1 ⊤ | V | 0 ⊤ | V | i ⊤ ; (48 ) • if the monitore d agents ou tput the fu ll observations of their po sitions (i.e., c i 1 6 = 0 and c i 2 = 0 f or ∀ i ∈ M ), the intermittent ZD A is detectable but N ∞ 0 = 0 2 | V | ; (49) • if the monitore d agents ou tput th e partial ob ser vations (i.e., c i 1 6 = 0 an d c i 2 6 = 0 for ∀ i ∈ M ), and c i 1 = c i 2 , ∀ i ∈ M , the kernel of the obser vability m atrix satisfies N ∞ 0 = 0 2 | V | , h 1 ⊤ | V | − 1 ⊤ | V | i ⊤ ; (50) and the intermittent ZDA is detectable if ξ 0 > t 0 , or D = 0 | M |× 2 | V | , (51) where N ∞ 0 is computed recur si vely by (20) and ( 21). Pr o of: See Appen dix E. Under the defen se strategy consisting of (46) and (4 7), th e result (49) im p lies tha t if the monitor ed agents o utput full o b- servations of p osition, the condition (19) is not satisfied. While the results (48 ) an d (5 0) show that if the mo nitored a g ents output f u ll obser vations of velocity or p artial ob servations, the cond itio n (1 9) is satisfied, and according to Lemma 1, the priv acy of all states of non -monito red a g ents is preserved, which further implies that using the av ailable d a ta ( 5), the attacker can not infer the glob al system state an d the glo bal initial conditio n . T herefor e, for the p urpose of priv acy preserv - ing of non-m o nitored agents’ states, consequen tly , r estricting the scope of attack able link s to deri ve the de f ense strategies against the coo p erative Z D A, we abandon full ob servation of position. B. Detecta bility of Coo perative Zer o-Dynam ic s Attack Considering th e m atrix Q r satisfying ( 11), we d escribe th e defense strategy as f ollows: Strategy on switching topolo gies: (46) . Strategy on monitore d-agent outpu ts: c i 2 > 0 , ∀ i ∈ M . Strategy on monitore d-agent location s: [ Q r ] i,m − [ Q r ] j,m 6 = 0 , ∀ m ∈ V \{ 1 } , ∀ r ∈ L , ∀ i 6 = j ∈ M . Defense Strategy Against Cooperativ e ZD A (52) (53) 8 Theor em 2: Conside r the sy stem ( 36) in the presence o f zero-dy namics attack in cooperatio n with topolog y attack under (43). Under the d e f ense strategy against cooperative ZD A, th e attack is detectable. Pr o of: See Appen dix F . Remark 10: The common critical requiremen t of o ur def ense strategies is that the c o mmunica tio n n e twork has distinct Laplacian eigen values. There indeed exist many to pologies whose associated La placian matrice s h av e distinct eig en val- ues. Th e following lemm a pr ovides a guide to design such topolog ies: Lemma 2 (Pr o position 1.3 .3 in [43]): L et G be a connected graph with diameter m . Then , G ha s at least m + 1 distinc t Laplace eigenv alues. V I . A T TAC K D E T E C T I O N A L G O R I T H M Using the p roposed defen se strategies and the detectab ility condition s in Section V , this section f ocuses on the attack detection algorithm that is based on a Luenberger o bserver . A. Luen ber ger Observer un der Switching T o pology W e now pre sen t a Lue n berger obser ver [46]: q i ( t ) = w i ( t ) (54a) ˙ w i ( t ) = − w i ( t ) + X i ∈ V a σ ( t ) ij ( q j ( t ) − q i ( t )) − r i ( t ) , c i 1 6 = 0 , i ∈ M R t t 0 r i ( b )d b, c i 1 = 0 , i ∈ M 0 , i ∈ V \ M (54b) r i ( t ) = c i 1 q i ( t ) + c i 2 w i ( t ) − ˘ y i ( t ) , i ∈ M (54c) where ˘ y i ( t ) is the monitored o utput o f agent i in system (14 ), r i ( t ) is the attack -detection sig n al. W e next consider a system matrix related to the system (54) in the absence of attack s: b A r , 0 | V |×| V | 1 | V |×| V | −L r − b C − 1 | V |×| V | , (55) where b C , C 1 0 ( | V |−| M | ) ×| V | or C 2 0 ( | V |−| M | ) ×| V | (56) with C 1 and C 2 giv en by (16d). I t is straightfor ward to obtain the following result regar ding the matrix stability . Lemma 3: The matrix b A r defined by (55) is Hurwitz, if L r is the Laplacian matrix of a connected graph and 0 | V |×| V | 6 = b C ≥ 0 . (57) If the sequence (10) has one connected graph and gain ma- trix b C (56) satisfies (57 ), it follows from Lemma 3 that there exists a P > 0 , such that un der con vex linear combinatio n, the matrix measure satisfies l − 1 X s =0 ν s µ P b A s < 0 . ( 58) Algorithm 1: Strategic T opology Switch ing Input: Initial index k = 0, initial time t k = 0 , observer gains satisfying (57), perio dic sequ e n ce L (10) with length of l satisfying (13 ) and (5 8). 1 Run th e system (14) and the ob server (54 ); 2 Up date dwell time: τ σ ( t k ) ← τ σ ( t mod ( k,L +1) ) ; 3 Switch top ology of system (14) and o bserver (54) at time t k + τ σ ( t k ) : σ ( t k + τ σ ( t k ) ) ← L ( mod ( k + 1 , L )) ; 4 Up date switching time: t k ← t k + τ σ ( t k ) ; 5 Up date index: k ← k + 1 ; 6 Go to Step 2. B. Strategic T opology- Switching A lgorithm W e next prop ose Algorithm 1 that d escribes whe n and which topolog y to switch to detec t the ZD A variations. Theor em 3 : I f th e m o nitored ag ents satisfy (47), (52) an d (53), and the switching topo logies in L satisfy (46), • withou t req u iring the k nowledge of the misbeh aving agents and the start, p ause, and re su me times of the attack, 1) with c i 1 = 0 , ∀ i ∈ M , the ob server (54) is able to detect the interm ittent and co o perative ZDAs; 2) with c i 1 = c i 2 , ∀ i ∈ M , the o bserver (5 4 ) is able to detect th e coope r ativ e ZD A and in termittent ZDA under (51); • in the absen ce of a ttacks, the agents in system (14) achieve the asymp totic consensus, and the observer (54) asymptotically tracks the real system (1 5) if c i 1 = c i 2 , ∀ i ∈ M , or c i 1 = 0 , ∀ i ∈ M . Pr o of: See Appen dix G. Remark 1 1 : Th e modulo o perations in steps 2 and 3 of Algorithm 1 descr ibe the building block of our defense strategy , that is p eriodic topolo g y switching . Gi ven the length of topology switchin g sequ ence, i.e. , l , and the length of the runnin g tim e of th e system (14) and the o bserver (54), denoted by t f − t 0 , the total n umber of top ology switchings can rou ghly be computed as t f − t 0 τ l . V I I . S I M U L A T I O N S W e consider a system with n = 16 agents. The initial position and veloc ity c onditions are ch osen as x ( t 0 ) = 2 × 1 ⊤ 8 , 4 × 1 ⊤ 8 ⊤ and v ( t 0 ) = 6 × 1 ⊤ 8 , 8 × 1 ⊤ 8 ⊤ . Th e coupling weights an d observer gain s are unifo rmly set to one. The conside r ed network topologies are given in the following Figures 1 and 4 where the ye llow no des den o te the monitor ed agents that outp ut fu ll ob servations of individual velocities. A. Detectio n of I ntermittent ZD A W e first co nsider the per io dic topolog y switching scheme in Figure 1 (a). W e denote the topo logies with the contr o lled links a σ ( t ) 17 in “On” and “Off” by 1 and 2, respectively . The considere d corr esponding period ic switching sequ e n ce is L = σ ( t 0 ) = 1 | {z } τ 0 =3 , σ ( t 1 ) = 2 | {z } τ 1 =6 . It can be verified that with 9 Figure 1. T wo periodic topology switching schemes for intermitt ent ZD A. y 1 ( t ) = v 1 ( t ) , n e ither of the switch ing to p ologies in Figure 1 (a) has distinct eigenv alues and F = ∅ , such that the d efense strategy con sisting of (46) and (4 7) does not hold. Th erefore , the attacker can de sign a n undetectable intermittent ZDA as follows: • inject false data z ( t 0 ) = 0 ⊤ 3 , − 1 , 1 , 0 ⊤ 14 , − 0 . 08 − 2 i , 0 . 08 + 2i , 0 ⊤ 11 ⊤ to the data of initial condition sent to the observer ( 54); • inject ZDA signals ˘ g 4 ( t ) = (2 . 9136 + 2 . 32i) e (0 . 08 − 2i)( t − 0 . 2) and ˘ g 5 ( t ) = ( − 2 . 913 6 − 2 . 32i) e (0 . 08 − 2i)( t − 0 . 2) to the lo c al control inputs of agents 4 and 5 fo r th e initial T opology 1 at ξ 0 = 0 . 2 ; • pau se the ZDA if the in coming topolog y is un known; • up d ate the attack strategy if n ecessary , and resum e the feasible attack after newly switche d top ology is in ferred; • iterate the last two steps. Some agents’ veloc ities and the attack-detection sign als in Figure 2 show th at with y 1 ( t ) = v 1 ( t ) , when the def e n se strategy con sisting of (46) and ( 4 7) does not hold , the attacker can design an intermitten t ZDA th a t c a nnot be d etected by the observer (5 4) under Algo rithm 1 (constant zero d etection signal), a n d the stealthy attack r e nders the system un stable (in the absence of attack s, lim t →∞ | v i ( t ) | = 0 , ∀ i ∈ V ). -5 0 5 Imag( ) 10 38 -3 -2 -1 0 1 2 3 Real( ) 10 39 (a) 0 50 80 Time -1 -0.5 0 0.5 1 Detection Signal r 1 (t) (b) Imag(r 1 (t)) Real(r 1 (t)) Figure 2. Indi vidual velociti es (a) and atta ck-dete ction signal (b). The switchin g topolog ies in Figure 1 (b ) satisfy th e defen se strategy co n sisting o f (4 6) and ( 47). Hen ce, according to the first statement in Th eorem 1, with y 1 ( t ) = v 1 ( t ) , i.e. , c 11 = 0 , we can turn to the switching scheme at some time to detect the stealthy attack . Und e r the topo logy switching scheme in Figu r e 1 (b), the trajectory of attac k-detection signal in Figure 3 (b) shows th e observer (5 4) succeed s in detecting the intermitten t ZD A (n o nzero detection signal), which also demonstra te s the first statement in T heorem 3 . 0 10 20 Time 0 0.5 1 1.5 2 Individual Velocities 10 4 (a) 0 10 20 Time 0 2000 4000 6000 8000 10000 12000 14000 Detection Signal |r 1 (t)| (b) Figure 3. Tra jectori es of velocit ies (a) and attac k-detec tion signal (b). B. Detectio n of Coo perative ZDA Figure 4. Netwo rk topologies for cooperati ve Z D A. W e d enote the switch in g to pologies in Figur e 4 (a) by 3 and 4, in Figur e 4 (b) by 5 and 6, respecti vely . It can be verified that with y i ( t ) = v i ( t ) , i ∈ M = { 1 , 2 , 3 } , neither T opology 3 nor T opology 4 satisfies the defen se strategy consisting of (46), (52 ) and (5 3). Therefo re, under the per iodic topolog y switching sequ ence L = σ ( t 0 ) = 3 | {z } τ 0 =3 , σ ( t 1 ) = 4 | {z } τ 1 =1 , it is possible to design stealthy co operative Z D A as follows: • inject false data z ( t 0 ) = [0 , 0 , 0 , 1 , 1 , 1 , 0 , 0 , 0 , 0 , 0 , 0 , 0 , 0 , 0 , 0 , 0 , 0 , 0 , 1 , 1 , 1 , 0 , 0 , 0 , 0 , 0 , 0 , 0 , 0 , 0 , 0 ] ⊤ to the data of initial cond ition sent to o bserver (5 4); • inject ZDA signals ˘ g 1 ( t ) = ˘ g 3 ( t ) = ˘ g 7 ( t ) = − e t , ˘ g 4 ( t ) = 5 e t , ˘ g 5 ( t ) = 2 e t and ˘ g 6 ( t ) = 3 e t to the local control inputs of agents 1, 3 , 7, 4, 5 and 6, respectiv ely , at initial time for T opolo gy 3; • inject false data − e t to the monito red o utputs; • maliciou sly c ontrol the conn ection b etween agents 2 and 3, such that the orig inal ZD A policy maintains its feasi- bility under the cor rupted topology at incoming switching times. The trajectories of velo c ities and attack-d etection sign a ls in Figure 5 show that the designed attack makes system un stable without being detected (co nstant zero d etection signals). The switching topologies in Figu re 4 (b ) satisfy th e defense strategy consisting of (46 ), (52) and (53). Theref ore, w ith y i ( t ) = v i ( t ) , i.e., c i 1 = 0 , i ∈ M = { 1 , 2 , 3 } , accor ding to 10 0 5 10 15 Time 0 0.5 1 1.5 2 2.5 3 3.5 Individual Positions 10 6 (a) 0 5 10 15 Time -1 -0.5 0 0.5 1 Detection Signals (b) Figure 5. Traje ctorie s of veloc ities (a) and attack-det ection signals (b). Theorem 2, to detect th e cooper ativ e ZDA we can co nsider the perio dic topology switching sequence in Figure 4 (b): L = σ ( t 0 ) = 5 | {z } τ 0 =3 , σ ( t 1 ) = 6 | {z } τ 1 =1 . W e assume that the attacker can modify any con n ection in the scop e of attack a ble lin ks. The trajectorie s of attack- d etection signals in Figure 6 d emon- strate that the observer (54 ) under Alg o rithm 1 succeeds in detecting the coop erative ZDA (nonz ero detection sign als). 0 5 8 Time 0 500 1000 1500 2000 2500 3000 Individual Velocities (a) 0 5 8 Time -0.2 -0.1 0 0.1 0.2 Detection Signals (b) Figure 6. Traje ctorie s of veloc ities (a) and attack-det ection signals (b). C. Comp arison with Existing W orks The existing results on the detection of ZDA are summa- rized in T able I. Since | M | = 1 in Figu re 1 and | K | = 1 fo r intermittent ZD A, | M | = 3 in Figure 4 and | K | = 6 for cooper- ativ e ZD A, and th e conn ectivity o f all network topolo gies a r e the same as 1 , which violate the conditio n s in T able I. D e fense strategies that rely on o n ly strategically c hanging system dynamics [2 3], [24], while are ef fective ag ainst conv entional ZD A an d inspired us to analy z e m ore sophisticated scenarios in this paper, implicitly a ssum e that the attacker has no aware- ness of the af o remention ed defense. He n ce, th e intermittent ZD A (when the system is un o bservable) or cooperative ZD A (when the system is observable) canno t be detected by these methods. W e also note that none o f th e pr ior work explicitly takes the issue of p riv acy/observability o f initial/fin a l states into account as we h av e pu rsued in this work. V I I I . C O N C L U S I O N In this pa per , we have first introdu c e d two ZDA variations for a scen ario where th e attacker is inf ormed abou t th e switching strategy of the d efender : interm ittent ZDA wher e T able I C O N D I T I O N S F O R D E T E C T I O N O F Z DA Refer ence Conditions Dynamics [12] size of input-o utput linking is smaller than | K | Continuous Time [18] conne cti vity is not smaller than 2 | K | + 1 Discrete Time [19] | K | is smalle r than conn ecti vity Discret e Time [20] the minimum verte x separator is lar ger than | K | + 1 Discr ete Time [21] single attack, i.e., | K | = 1 Continuous Time the attacker pauses, updates and r esumes ZD A in con junction with the k nowledge of switching topologies, and c ooperative ZD A where the attacker em p loys a stealthy topolog y attack to render the switching topolo g y defense ineffectiv e. W e have then stud ied co n ditions for a defe n der to detect these a ttac ks, and subsequen tly based on these co nditions, we have proposed an a ttac k detection alg orithm. The p r oposed defense strategy can detect both of the p roposed ZD A variations, withou t requirin g any kn owledge of the set of misbe h aving ag e nts or the start, pause and resume times o f the attack. Mor eover , this strategy achieves asym p totic consensus and tr acking in the absence of an attack without limiting the magnitudes of the coupling weights or the n umber o f monitored agents. Our analysis sugg ests an inter e sting trade-off a m ong the switching cost, the d uration o f an undetected attack, the conv ergence speed to consensus and tracking. Analy z ing this fundam ental tr a de-off throug h the lens of game theory and multi-objec ti ve optimization con stitutes a p art o f ou r future research. A P P E N D I X A : A U X I L I A RY L E M M A S In this section, we p resent au xiliary lemmas th at ar e used in the proo fs of the main results of this paper . Lemma 4: [47] Consider the switched system s: ˙ x ( t ) = A σ ( t ) x ( t ) under p eriodic switching , i.e., σ ( t ) = σ ( t + τ ) ∈ S . If th ere exists a conve x co mbination of some matrix measur e th a t satisfies l − 1 X m =0 ν m µ ( A m ) < 0 , (59) where ν m = τ m l − 1 P i =0 τ i ; then the switched system system is unifor m ly asymptotically stable for ev ery positiv e τ = l − 1 P i =0 τ i . Lemma 5: [48] Consider the V ander monde matrix: H , 1 1 · · · 1 a 1 a 2 · · · a n a 2 1 a 2 2 · · · a 2 n . . . . . . · · · . . . a n − 1 1 a n − 1 2 · · · a n − 1 n ∈ R n × n . Its determin ant is det ( H ) = ( − 1) n 2 − n 2 Q i 0 , th e n ker Q ⊤ r 2: | V | , : = 1 | V | , 0 | V | . (60) 11 Pr o of: The pr oof follows from a contradiction argument. W e assume that (6 0 ) does not hold, i.e., there exists a vector ψ = [ ϕ 1 , . . . , ϕ | V | ] ⊤ such that ψ / ∈ span 1 | V | , 0 | V | , (61) and Q ⊤ r 2: | V | , : ψ = 0 | V |− 1 . Then, it follows fr om (11) that L r ψ = Q r Λ r Q ⊤ r ψ = Q r 0 | V | = 0 | V | . (62) From [ 43], we k now that an undirected g raph is connected if an d only if λ 2 ( L r ) > 0 , an d further the null space o f the Laplacian m atrix L r of a co nnected graph is spanned by the vector 1 | V | . W e o b tain from (62 ) that ϕ 1 = . . . = ϕ | V | , which contradicts with (61). Thu s, (60 ) ho lds. Th is conclu des the proof . A P P E N D I X B : P RO O F O F P R O P O S I T I O N 1 Based o n average variables ¯ x ( t ) ∆ = 1 | V | P i ∈ V x i ( t ) and ¯ v ( t ) ∆ = 1 | V | P i ∈ V v i ( t ) , we define the following fluctuation terms: ˜ x i ( t ) , x i ( t ) − ¯ x ( t ) , (63a) ˜ v i ( t ) , v i ( t ) − ¯ v ( t ) , (63b) which implies that 1 ⊤ | V | ˜ x ( t ) = 0 , for t ≥ t 0 (64a) 1 ⊤ | V | ˜ v ( t ) = 0 , for t ≥ t 0 . (64b ) Considering (1b), (8) and a σ ( t ) ij = a σ ( t ) j i , we have ˙ ¯ v ( t ) = 1 | V | X i ∈ V ˙ v i ( t ) = 1 | V | X i ∈ V u i ( t ) = 1 | V | X i ∈ V ( − v i ( t ) + X j ∈ V a σ ( t ) ij ( x j ( t ) − x i ( t ))) = − 1 | V | X i ∈ V v i ( t ) = − ¯ v ( t ) , which, in conjun ction with (6 3b), leads to ˙ ˜ v i ( t ) = ˙ v i ( t ) − ˙ ¯ v ( t ) = u i ( t ) + ¯ v ( t ) = − v i ( t ) + X j ∈ V a σ ( t ) ij ( x j ( t ) − x i ( t )) + ¯ v ( t ) = − ( v i ( t ) − ¯ v ( t )) + X j ∈ V a σ ( t ) ij (( x j ( t ) − ¯ x ( t )) − ( x i ( t ) − ¯ x ( t ))) = − ˜ v i ( t ) + X j ∈ V a σ ( t ) ij ( ˜ x j ( t ) − ˜ x i ( t )) , i ∈ V . (65) The dy n amics o f the second- order multi-agent system (1) with contr o l inpu t (8 ) can now be expressed equiv alently as ˙ ˜ x ( t ) = ˜ v ( t ) (66a) ˙ ˜ v ( t ) = − ˜ v ( t ) − L σ ( t ) ˜ x ( t ) , (66b) where (66b ) con siders its e q uiv alent for m (65 ). Let us define ˆ x , Q ⊤ r ˜ x an d ˆ v , Q ⊤ r ˜ v . Noting (11), the dynamics (66) can equ iv alently transform to ˙ ˆ x ( t ) = ˆ v ( t ) (67a) ˙ ˆ v ( t ) = − ˆ v ( t ) − Υ r s ˆ x ( t ) , r, s ∈ S (6 7b) where Υ r s is defined in (12a ). W e note that it fol- lows from (64) and (11b ) that ˆ x 1 ( t ) = ˆ v 1 ( t ) = 0 , [Υ r s ] 1 , : = 0 ⊤ | V | and [Υ r s ] : , 1 = 0 | V | . Let us define θ , [ ˆ x 2 . . . ˆ x | V | ˆ v 2 . . . ˆ v | V | ] ⊤ . T hus, the system (67) equiv- alently reduce s to ˙ θ ( t ) = A s θ ( t ) , s ∈ S (68) with A s giv en in ( 12b). Mean wh ile, it is straightfo r ward to verify that when r = s , A s is Hurwitz. Therefo re, the exists a P > 0 suc h tha t µ P ( A r ) < 0 . Throug h setting o n the dwell time of th e topo logy ind exed by r , (59) can be satisfied. By Lemm a 4, th e system (68) is uniformly asympto tically stable, i.e., f or any initial condition , lim t →∞ θ ( t ) = 0 2 | V |− 2 , which imp lies that lim t →∞ Q ⊤ ˜ x ( t ) = lim t →∞ Q ⊤ ˜ v ( t ) = 0 | V | . Since Q is fu ll-rank, we have lim t →∞ ˜ x ( t ) = lim t →∞ ˜ v ( t ) = 0 | V | . The n , (63) implies that lim t →∞ ˜ x i ( t ) = lim t →∞ ˜ x j ( t ) an d lim t →∞ ˜ v i ( t ) = lim t →∞ ˜ v j ( t ) , ∀ i 6 = j ∈ V . Here, we con c lude that the second-o rder co nsensus is achiev ed, and we define v ∗ = lim t →∞ ˜ v i ( t ) , ∀ i ∈ V . Th e n, substituting the seco nd-or der consensus into the system (1) with contro l inpu t (8) yie ld s the dynamics ˙ v ∗ = − v ∗ , which implies a com mon zer o velocity at steady state. A P P E N D I X C : P RO O F O F P RO P O S I T I O N 2 Let us first defin e: y ∆ = ˘ y − y . (69) It is straightfo rward to obtain dyn amics f rom (3) and (7) as ˙ z ( t ) = A σ ( t ) z ( t ) + ˘ g ( t ) (70a) y ( t ) = C z ( t ) + D ˘ g ( t ) , (70b) where z ( t ) is defined in (33). 1) P roof of (3 5) : Since [ ξ k , ζ k ) ⊆ [ t k , t k +1 ) , σ ( t ) = r for t ∈ [ ξ k , ζ k ) . W e d enote Ξ ( s ) , L { z ( t ) } , where L ( · ) stands fo r the Laplac e transform o perator . It follows from the attack signal (2 3) that L { ˘ g ( t ) } = ( e − ξ k s − e − ζ k s ) ˘ g ( ξ k ) s − η r , t ∈ [ ξ k , ζ k ) . W ith out loss of generality , we let σ ( t ) = r for t ∈ [ t k , t k +1 ) . Then, the L aplace transform of the dy namics in (7 0) is obtained as ( e − ξ k s − e − ζ k s )( s Ξ ( s ) − z ( ξ k )) = ( e − ξ k s − e − ζ k s ) A r Ξ ( s ) + ( e − ξ k s − e − ζ k s ) ˘ g ( ξ k ) s − η r , which is equivalent to ( e − ξ k s − e − ζ k s )Ξ( s ) = ( e − ξ k s − e − ζ k s ) s 1 2 | V |× 2 | V | − A r z ( ξ k ) + ˘ g ( ξ k ) s − η r . (7 1) Expand ing (26b ) ou t y ields C z ( ξ k ) + D ˘ g ( ξ k ) = 0 | M | , (72 ) η r z ( ξ k ) − A r z ( ξ k ) = ˘ g ( ξ k ) , r ∈ T . (73) Substituting (73 ) into (7 1) yields ( e − ξ k s − e − ζ k s )Ξ ( s ) = ( e − ξ k s − e − ζ k s ) s − η r z ( ξ k ) , and the inverse Lapla c e tran sform of it giv es ( 35). 12 2) P roof of (34) : It f ollows from (35) and ( 7 0) th at y ( t ) = e η r ( t − ξ k ) ( C z ( ξ k ) + D ˘ g ( ξ k )) , t ∈ [ ξ k , ζ k ) , k ∈ N 0 (74) which com bined with (72 ) results in y ( t ) = 0 | M | , or equ iva- lently , ˘ y ( t ) = y ( t ) , for any t ∈ [ ξ k , ζ k ) . W e next prove (5) o ver non- attack interval o f ZD A [ ζ k , ξ k +1 ) . From (2 3 ) and (25 ), th e dynamics (70 ) over such non-attack intervals of ZDA ( su bject to the mon ito red o utput attack as (2 5 )) is d escribed b y ˙ z ( t ) = A σ ( t ) z ( t ) (75a) y ( t ) = C z ( t ) + D k X m =0 ˘ g ζ − m , t ∈ [ ζ k , ξ k +1 ) . (75b) It follows fr o m (3 5) and (75a) that z ( t ) (76) = e A σ ( t k ) ( t − t k ) z ( t k ) , t ∈ [ t k , ξ k ) e 1 2 | V |× 2 | V | η r ( t − ξ k )+ A σ ( t k ) ( ξ k − t k ) z ( t k ) , t ∈ [ ξ k , ζ k ) e A σ ( t k ) ( t − t k − ( ζ k − ξ k ) )+ 1 2 | V |× 2 | V | η r ( ζ k − ξ k ) z ( t k ) , t ∈ [ ζ k , t k +1 ) . W e conclud e from (69 ) that ( 34) is equivalent to y ( t ) ≡ 0 | M | on [ t 0 , t k +1 ) . (77) For D = 0 | M |× 2 | V | , we note that (7 7 ) implies that the system (75) is unobservable fo r any t ∈ [ t 0 , t k +1 ) , k ∈ N 0 . It is immediate that z ( t k ) ∈ k er( O k ) = b N k k , k ∈ N 0 . (7 8) W e next show that z ( t q − 1 ) ∈ b N k q − 1 for 0 ≤ q − 1 ≤ k , throug h inductive argu ment. Let u s suppo se z ( t q ) ∈ b N k q . W e obtain from (76) that z ( t q ) = z ( t − q ) = e η σ ( t q − 1 ) ( ζ q − 1 − ξ q − 1 ) e A σ ( t q − 1 ) ( τ q − 1 − ( ζ q − 1 − ξ q − 1 )) z ( t q − 1 ) , which, in conju nction with the fact of e η σ ( t q − 1 ) ( ζ q − 1 − ξ q − 1 ) 6 = 0 , leads to z ( t q − 1 ) ∈ e − A σ ( t q − 1 ) ( τ q − 1 − ( ζ q − 1 − ξ q − 1 )) b N k q . Moreover , we note tha t (78) implies that z ( t q − 1 ) ∈ ker( O q − 1 ) . Therefo re, z ( t q − 1 ) ∈ e − A σ ( t q − 1 ) ( τ q − 1 − ( ζ q − 1 − ξ q − 1 )) b N k q ∩ k er( O q − 1 ) , (79 ) where the right-ha n d expression is, in fact, th e compu tation of b N k q − 1 , i.e., th e unobservable space g iv en by (28). Let q = 1 , we have z ( t 0 ) ∈ b N k 0 . Th en, following the sam e steps in the proo f of ne cessary co ndition in Theorem 1 of [44], we conclud e that (3 4 ) holds if and on ly if there exists a non -zero vector z ( t 0 ) such that z ( t 0 ) ∈ b N k 0 . (80) For D 6 = 0 | M |× 2 | V | , it follows fro m (72) and (75b) that y ( ζ k ) = y ζ − k = 0 | M | . The r efore, in this scenario, (77) holds only when ˙ y ( t ) ≡ 0 | M | on [ t 0 , t k +1 ) . Updating the observability matrix O q in ( 2 2) by e O q in ( 3 1) and following the sam e steps to deriv e (80), we co nclude that (34) holds if and only if z ( t 0 ) ∈ e N k 0 , (81) where e N k 0 is recursively computed by (29) and (30) . In addition to (80 ) and ( 8 1), we conclud e that if (2 6a) an d (72) ho ld, regardless of D k P m =0 ˘ g ( ζ − m ) 6 = 0 | M | or = 0 | M | , ( 34) always ho lds. A P P E N D I X D : P RO O F O F P R O P O S I T I O N 3 Let us d efine ˜ e , ˜ e ⊤ x ˜ e ⊤ v ⊤ , b z − z . W ithout loss o f generality , we let σ ( t k +1 ) = s . Noticing (39), we obtain from the dynamics (38 ) and (1 7) th at ˙ ˜ e ( t ) = b A s ˜ e ( t ) + ( b A s − A s ) z ( t ) , t ∈ [ t k +1 , t k +2 ) ( 82a) b y ( t ) − y ( t ) = C ˜ e ( t ) , (82b) ˜ e ( t k +1 ) = 0 | M | , (82c) from which we have b y ( t ) − y ( t ) = C e b A s ( t − t k +1 ) Z t t k +1 e − b A s ( τ − t k +1 ) (( b A s − A s ) z ( τ ))d τ , and the correspo nding derivati ves b y ( d ) ( t ) − y ( d ) ( t ) = C b A d s e b A s ( t − t k +1 ) Z t t k +1 e − b A s ( τ − t k +1 ) ( b A s − A s ) z ( τ )d τ + d − 1 X l =0 C b A l s (( b A s − A s ) z ( d − 1 − l ) ( t )) . (83) W e note tha t u nder corru pted topology , the stealth y prop erty b y ( t ) − y ( t ) = 0 | M | for any t ∈ [ t k +1 , t k +2 ) is eq uiv alent to b y ( d ) ( t k +1 ) − y ( d ) ( t k +1 ) = 0 | M | for ∀ d ∈ N 0 , wh ich is further equiv alent to (40 ) by considerin g the solutio n (83 ). A P P E N D I X E : P RO O F O F T H E O R E M 1 W ithout loss of g enerality , we let σ ( ζ k ) = r ∈ T , an d ζ k < t k +1 , k ∈ N , i.e., attacker “pauses” ZD A at ζ k . W e n ow prove this theorem via a c ontradictio n . W e assume that the attack is not detec ta b le in [ ζ − k , ξ k +1 ) , which is equivalent to y ( t ) = 0 | M | for any t ∈ [ ζ − k , ξ k +1 ) , (84) where y ( t ) is de fin ed in (69). Considering the fact that giv en a differentiable functio n f ( t ) , f ( t ) = 0 f or any t ∈ [ a, b ] , if and only if f ( a ) = 0 and f ( d ) ( a ) = 0 , ∀ d ∈ N . W e conclud e from (75) that ( 84) at time ζ k is equiv alent to y ( d ) ( ζ k ) = C z ( ζ k ) + D k P m =0 ˘ g ( ζ − m ) = 0 | M | , d = 0 C A d r z ( ζ k ) = 0 | M | , ∀ d ∈ N . (85) W ith the definition s of A r , C , D and z ( · ) in (16 b ), (1 6c), (16e) and (3 3), the relation ( 85) can be f urther rewritten und er different for ms of o bservation as follows: • Full Ob servation of V elocity , i.e., c i 1 = 0 , ∀ i ∈ M , C 2 v ( ζ k ) + D k X m =0 ˘ g ζ − m = 0 | M | (86a) C 2 v ( ζ k ) + C 2 L r x ( ζ k ) = 0 | M | (86b) C 2 L e r v ( ζ k ) = 0 | M | , ∀ e ∈ N (86c) C 2 L d r x ( ζ k ) = 0 | M | , ∀ d ∈ N ≥ 2 (86d) 13 • Full Ob servation of Position, i.e., c i 2 = 0 , ∀ i ∈ M , C 1 x ( ζ k ) + D k X m =0 ˘ g ζ − m = 0 | M | (87a) C 1 L e r x ( ζ k ) = 0 | M | , ∀ e ∈ N (87 b) C 1 L d r v ( ζ k ) = 0 | M | , ∀ d ∈ N 0 (87c) • Partial Observation, i.e., c i 1 6 = 0 and c i 2 6 = 0 , ∀ i ∈ M , C 1 x ( ζ k ) + C 2 v ( ζ k ) + D k X m =0 ˘ g ζ − m = 0 | M | , (88a) C 1 L e r x ( ζ k ) + C 2 L e r v ( ζ k ) = 0 | M | , ∀ e ∈ N ( 88b) ( C 1 − C 2 ) L d r v ( ζ k ) − C 2 L d +1 r x ( ζ k ) = 0 | M | , ∀ d ∈ N 0 . (88c) Considering the definitio n o f the vector z ( t ) in (3 3), and its continu ity with respect to time, i.e., z ζ − k = z ( ζ k ) , it follows from (3 5) an d (23) that at time ζ − k , z ( ζ k ) − ˘ g ζ − k = e η r ( ζ − k − ξ k ) z ( ξ k ) − ˘ g ( ξ k ) , (89) which, in conjunction with the fact of e η r ( ζ − k − ξ k ) 6 = 0 and th e condition (26b ), results in z ( ζ k ) − ˘ g ζ − k ∈ ker ( P k ) . (90) W ith variables ˘ g ( ζ − k ) , ¯ g ( ζ − k ) , z ( ζ k ) , A r and P k defined in (16f), (16 g) , (3 3), ( 16b) and (32), respec tively , expand ing (90 ) yields η r x ( ζ k ) − v ( ζ k ) = 0 | V | , (91 ) − ¯ g ζ − k + v ( ζ k ) + L r x ( ζ k ) + η r v ( ζ k ) = 0 | V | . (92 ) Before pro ceeding the re st of proof , we define the variables: H i , [ U r i x ( ζ k )] 2: | V | , (93a) D r , dia g n λ 2 2 ( L r ) , . . . , λ 2 | V | ( L r ) o , (93b) e H r , λ 2 2 ( L r ) · · · λ 2 | V | ( L r ) λ 3 2 ( L r ) · · · λ 3 | V | ( L r ) . . . · · · . . . λ | V | 2 ( L r ) · · · λ | V | | V | ( L r ) , (93 c ) H r , 1 · · · 1 λ 2 ( L r ) · · · λ | V | ( L r ) . . . · · · . . . λ | V |− 2 2 ( L r ) · · · λ | V |− 2 | V | ( L r ) , (93d ) where U r i is given in (44). A. Und er F u ll Observation of P osition or V elocity Let us start with fu ll observation of velocity . It follows from (11) that L d r = Q r Λ d r Q ⊤ r with Λ r giv en in (1 1). Thu s, (8 6d) is equiv alent to C 2 Q r Λ d r Q ⊤ r x ( ζ k ) = 0 | M | , ∀ d ∈ N ≥ 2 , which is further equivalent to | V | X l =1 λ d l ( L r )[ Q r ] i,l Q ⊤ r l, : x ( ζ k ) = 0 , ∀ d ∈ N , ∀ i ∈ M (94) with the consideratio n of the matr ix C 2 defined in (16d) with c i 2 6 = 0 , ∀ i ∈ M . Furthe r, recalling e H r , H i and U r i from (93c), (93a) and (44), fro m ( 9 4) we hav e e H r H i = 0 | V |− 1 , ∀ i ∈ M . (95) It ca n be verified from (93 b )–(93d) that e H r = H r D r , from which we h av e det( e H r ) = det( H r ) det( D r ) . The m atrix defined in (93 b ) shows if L r has d istinct eig en values, D r is full-rank . In addition, by Lemma 5, the V an dermon de matrix H r is f ull-rank ; thu s, e H r is f ull-rank . Theref ore, the solu tio n of (95) is H i = 0 | V |− 1 , ∀ i ∈ M . (96) W ith the definitions in (44 ) and (93a), the equation (96) indicates that for ∀ i ∈ M , diag n [ Q r ] i, 2 , . . . , [ Q r ] i, | V | o Q ⊤ r 2: | V | , : x ( ζ k ) = 0 | V |− 1 . (97) W e no te th at ( 44), (4 5) a n d (47) im ply th at ∃ i ∈ M : diag n [ Q r ] i, 2 , . . . , [ Q r ] i, | V | o is f ull-rank . Th us, from (97) we have Q ⊤ r 2: | V | , : x ( ζ k ) = 0 | V |− 1 . By Lemma 6, the solution of (97) is x 1 ( ζ k ) = . . . = x | V | ( ζ k ) . (98) Considering (86c), using the same meth o d to deriv e (98), we obtain v 1 ( ζ k ) = . . . = v | V | ( ζ k ) . (99) Substituting (98 ) into (86b) yields C 2 v ( ζ k ) = 0 | M | , which together with (99 ) results in v 1 ( ζ k ) = . . . = v | V | ( ζ k ) = 0 . (100) For the full observation o f p osition, using nearly th e same analysis metho d employed above, we obtain the same results as (98) and (100 ). Substituting (98 ) and (100) into ( 9 2) yields ¯ g ζ − k = 0 | V | , and co nsequen tly , ˘ g ζ − k = 0 2 | V | . T his means that th e re is no ZD A on th e system at ζ − k , which contrad icts the assump tion that the attack is ap plied un til ζ k . The r efore, we c o nclude that under the f ull observation of position or velocity , th e intermittent ZD A is detectable. 1) Full Observation of V elocity : T o p roceed with the pr oof of (48), we first n e ed to obtain ker ( O k ) of the system (17) giv en in (2 2). The analysis of the kernel of th e o bservability matrix O k can follow th e relation (85) with th e setting of D = 0 | M |× 2 | V | . W e no te that (8 5) is equiv alently represented by (86 ), (87) an d (88). Th e results ( 98) and (99) are obtained without c onsidering ( 86a), (87a) and (88a) which are the only terms in volving D . Then, results similar to (98) and (99 ) can be obtained for the system in (17) a s x 1 ( ζ k ) = . . . = x | V | ( ζ k ) and v 1 ( ζ k ) = . . . = v | V | ( ζ k ) . (101) Further, with D = 0 | M |× 2 | V | , f rom (86 a) with v ( ζ k ) re p laced by v ( ζ k ) , we have C 2 v ( ζ k ) = 0 | M | , which combin ed with (101) yields x 1 ( ζ k ) = . . . = x | V | ( ζ k ) and v 1 ( ζ k ) = . . . = v | V | ( ζ k ) = 0 . Th us, ker( O k ) = 0 2 | V | , h 1 ⊤ | V | 0 ⊤ | V | i ⊤ . Since all of the elements in k er( O k ) are the equilibriu m poin ts of the system ( 17), throu gh the recur si ve computation of (20) and (21), we arrive at (48). 14 2) Full Observatio n of P osition : T o obtain ker( O k ) u n- der f ull ob servation of position, we can co n sider ( 87) with D = 0 | M |× 2 | V | . From (87a) and (98) we have x 1 ( ζ k ) = . . . = x | V | ( ζ k ) = 0 . Then, we o btain from ( 1 00) (replace v i ( ζ k ) by v i ( ζ k ) ) that ker( O k ) = 0 2 | V | , which means that if the mo n itored agents outp ut f ull observation of positions, the system (17 ) is ob servable a t t k ; thus (4 9) is obtain ed b y the recur si ve comp u tation of (20 ) and (2 1). B. Und er P artial Ob servation The ana lysis of ob servability fo llows the same steps of that un der fu ll observation. With C 1 = C 2 , fro m ( 8 8c) we have C 2 L d +1 r x ( ζ k ) = 0 , ∀ d ∈ N 0 . Employing the same step s to derive (98) u nder f u ll ob ser vation of velocity , we ob tain (98) as well u n der p artial observation. Mo reover , substituting (98) into (88b) and repeating the same steps, we arri ve at (99). It is straightf orward to verify fr om th e dy namics ( 17) that x 1 ( t ) = . . . = x | V | ( t ) and v 1 ( t ) = . . . = v | V | ( t ) for any t ≥ t 0 , if an d only if (99 ) and (98) ho ld. Fina lly , considerin g (88a) with the setting of D = 0 | M |× 2 | V | , we have C 1 x ( ζ k ) + C 2 v ( ζ k ) = 0 | M | , fro m wh ic h we h av e ker( O k ) = 0 2 | V | , h 1 ⊤ | V | − 1 ⊤ | V | i ⊤ , ∀ k ∈ N 0 , an d then (50) is obtained by co mputation of (20) and (21). Under the con dition (5 1), z ( ζ k ) ∈ N k 0 , which in co n junc- tion with (91) implies η r = − 1 . Substituting (98), (99) and η r = − 1 in to (92) yield s ¯ g ζ − k = 0 | V | , and co nsequently , ˘ g ζ − k = 0 2 | V | . This means th at there is no ZD A on the system at ζ − k , which contr adicts the assumption that the attack is applied until ζ k . A P P E N D I X F : P R O O F O F T H E O R E M 2 W ith the definition o f C j , j = 1 , 2 , in (16d ), we can rewrite (82) as ˙ ˜ e x ( t ) = ˜ e v ( t ) , (102a) ˙ ˜ e v ( t ) = − ˜ e v ( t ) − b L s ˜ e x ( t ) − b L s − L s x ( t ) , (10 2b) b y ( t ) − y ( t ) = C 1 ˜ e x ( t ) + C 2 ˜ e v ( t ) , t ∈ [ t k +1 , t k +2 ) ( 102c) ˜ e x ( t k +1 ) = 0 | V | , ˜ e v ( t k +1 ) = 0 | V | . (102d ) W e define C , diag c 12 , . . . , c | D | 2 , where the diagonal entries are from C 2 defined in (16d). Accord ing to (5 2) and | D | ≤ | M | (implied by (43)), the matr ix C is in vertible. Now , considerin g (42), we have C 2 b L s − L s = C L s 0 | D | × ( | M |−| D | ) 0 ( | M |−| D | ) × | D | 0 ( | M |−| D | ) × ( | M |−| D | ) , (10 3) which, in c o njunction with invertible ma tr ix C and the def - initions of A s in (16b) and b A s in (3 7 ), im plies that if C 2 b L s − L s x ( d ) ( t k +1 ) = 0 | M | , ∀ d ∈ N 0 , th en b A s − A s z ( d ) ( t k +1 ) = 0 2 | V | , ∀ d ∈ N 0 . (104 ) Under the dyna mics (10 2) and the relation (104), th e necessary co ndition (40 ) of g uaranteein g stealthy property of cooper a tive ZD A is e quiv alently written as C 2 b L s − L s L d s x ( t k +1 ) = 0 | M | , ∀ d ∈ N 0 (105a) C 2 b L s − L s L d s v ( t k +1 ) = 0 | M | , ∀ d ∈ N 0 . (105b) W e assume that the top ology attack in system (36 ) can ensure that the stealthy prop erty (5) o f ZD A holds. Noticing (103) and the d ynamics (17 ), the eq uation (1 05) is eq u iv alent to C L σ ( t k +1 ) χ ( m ) ( t k +1 ) = 0 | D | , ∀ m ∈ N 0 , where χ ( t k +1 ) , x 1 ( t k +1 ) . . . x | D | ( t k +1 ) ⊤ . Since C is in vertible, we have L σ ( t k +1 ) χ ( m ) ( t k +1 ) = 0 | D | , ∀ m ∈ N 0 . (1 06) As L σ ( t k +1 ) is th e elemen tary row transfo rmation of a Laplacian matrix, there exists an eleme ntary r ow operator E ∈ R | D |×| D | such that b L σ ( t k +1 ) , E L σ ( t k +1 ) is a Laplacian matrix. Pre-multiplyin g both sides of (1 06) by E yields b L σ ( t k +1 ) χ ( m ) ( t k +1 ) = 0 | D | , ∀ m ∈ N 0 . (1 07) It is well-known that the null space of the Lap lacian matrix of a connected gr aph is spann e d by the vector with all ones. From (107 ) we conclude that ∃ i, j ∈ D : x ( m ) i ( t k +1 ) = x ( m ) j ( t k +1 ) , t k +1 ≥ t 0 , ∀ m ∈ N 0 , which can be rewritten as e ⊤ i − e ⊤ j x ( m ) ( t k +1 ) = 0 , ∀ m ∈ N 0 (108) where e i denotes a vector of leng th | D | with a sing le non zero entry with value 1 in its i th position. Due to the dyn a mics ( 17), the equation (108) leads to e ⊤ i − e ⊤ j L m r x ( t k +1 ) = 0 , ∀ m ∈ N 0 (109a) e ⊤ i − e ⊤ j L m r v ( t k +1 ) = 0 , ∀ m ∈ N 0 . (109b) It follows from ( 11) that L d r = Q r Λ d r Q ⊤ r with Λ r giv en in (11c), substituting which into ( 109) yield s that for ∀ m ∈ N , | V | X l =2 λ m l ( L r ) [ Q r ] i,l − [ Q r ] j,l Q ⊤ r l, : x ( t k +1 ) = 0 , (110a) | V | X l =2 λ m l ( L r ) [ Q r ] i,l − [ Q r ] j,l Q ⊤ r l, : v ( t k +1 ) = 0 . (110b) Then, with the definition s D ij , diag n [ Q r ] i, 2 − [ Q r ] j, 2 , . . . , [ Q r ] i, | V | − [ Q r ] j, | V | o , (111) f , [ Q r ] ⊤ 2: | V | , : x ( t k +1 ) , (112) following the same de r iv ations from (94 ) to (9 5), we ar riv e a t e H r D ij f = 0 | V |− 1 , ∀ i ∈ M , (113) where e H r is gi ven in (93c). Using the same analysis to derive (96), we conclud e th at under the condition (46), the solution of (113) is D ij f = 0 | V |− 1 . Since D ij giv en by (111) is full-ran k under the con dition (53), we h av e f = 0 | V |− 1 . Then , noticing (112), by Lemm a 6 we arriv e at x 1 ( t k +1 ) = . . . = x | V | ( t k +1 ) . (114 ) Repeating the sam e p rocedu re of deriving (114 ) from (11 0a), we conclude v 1 ( t k +1 ) = . . . = v | V | ( t k +1 ) from ( 110b), which means that the second- order consensu s is a chieved at t k +1 , i.e., x i ( t k +1 ) = x j ( t k +1 ) and v i ( t k +1 ) = v j ( t k +1 ) , ∀ i 6 = j ∈ V . It is straig htforward to verify from the dynamics (66) that the second-o rder co nsensus is achieved at some time t < ∞ if and on ly if the individual initial conditions ar e identical, i.e., x i ( t 0 ) = x j ( t 0 ) and v i ( t 0 ) = v j ( t 0 ) . Hence, the cooper a tive ZDA is u ndetectable o nly in the case of identical initial cond ition that cor responds to the stead y state. 15 A P P E N D I X G : P RO O F O F T H E O R E M 3 W e define e x ( t ) , q ( t ) − ˘ x ( t ) an d e v ( t ) , w ( t ) − ˘ v ( t ) . The dynam ics of tracking err ors in the p resence of the attack obtained from (54) and ( 14) a re given as: ˙ e x i ( t ) = e v i ( t ) , (115a) ˙ e v i ( t ) = − e v i ( t ) + X i ∈ V a σ ( t ) ij e x j ( t ) − e x i ( t ) − ˘ g i ( t ) , i ∈ K 0 , i ∈ V \ K − r i ( t ) , c i 1 6 = 0 ,i ∈ M R t t 0 r i ( b )d b, c i 1 = 0 ,i ∈ M 0 , i ∈ V \ M (115b ) r i ( t ) = c i 1 e x i ( t ) + c i 2 e v i ( t ) − d i ˘ g i ( t ) , i ∈ M . (115c) The attack is no t detected by the o b server (54 ) means that r i ( t ) = 0 , i ∈ M , for a ny t ≥ t 0 . Sub stitutin g it into th e above equation results in ˙ e x i ( t ) = e v i ( t ) ˙ e v i ( t ) = − e v i ( t ) + X i ∈ V a σ ( t ) ij e x j ( t ) − e x i ( t ) − ˘ g i ( t ) , i ∈ K 0 , i ∈ V \ K r i ( t ) = c i 1 e x i ( t ) + c i 2 e v i ( t ) − d i ˘ g i ( t ) , i ∈ M which has th e sam e f orm o f dynamics as that of (14). Therefo re, the analy sis of ZDA v ariations in the observer (54) follows th e same analy sis o f the system (1 4). Moreover, the requ ired conditio n (52 ) im plies that the monito red ag ents output f u ll observations of velocity or partial obser vations: either (48) or (5 0) imp lies (19). Hence, the to pology attacker cannot infer the real-time full states of the n on-mo n itored agents, and the top o logy attacker has to co nsider the scope of the target connections implied by (43). Th e refore, the proof of the first statemen t fo llows f rom Theor ems 1 and 2. In th e absen c e of attac ks, the system matrix o f system (115 ) is b A σ ( t ) defined in (55). Since the con dition (46) imp lies that all of the switching topolog ies provided to Algor ithm 1 are connected g raphs and co ndition (5 2 ) implies ( 5 7), the matr ix b A σ ( t ) is Hurwitz b y Lemma 3. Thus, the re exists a P > 0 such that both ( 59) and (58) hold. Hence, the proo f o f the second statement follows fr om Pro position 1 and Lemm a 3 . R E F E R E N C E S [1] Y . Mao, H. Jafarn ejadsani , P . Zhao, E . Akyol, and N. Hova kimyan, “Detec tabili ty of int ermitten t zero-dynamics attac k in netw orke d control systems, ” in Proc eedings of the 58th IEEE Conf ere nce on Decision and Contr ol , pp. 5605–5610, 2019. [2] A. Jadbabaie , J. Lin, and A. S. Morse, “Coordi nation of groups of mobile autonomous agents using nearest neighbor rule s, ” IEEE T ransactions on Automat ic Contr ol , vol. 48, no. 6, pp. 988–1001, 2003. [3] J. A. Fax and R. M. Murray , “Info rmation flow and coopera ti ve control of vehicle formations, ” IEEE T ransac tions on Automat ic Contr ol , vol. 49, no. 9, pp. 1465–1476, 2004. [4] A. Nedi ´ c and A. Ozdaglar , “Distrib uted subgradient methods for multi- agent optimizati on, ” IEEE T ransac tions on Automatic Contr ol , vol. 54, no. 1, pp. 48–61, 2009. [5] L. -Y . Lu and C.-C. Chu, “Conse nsus-based droop contr ol synthesi s for multiple dics in isolated micro-grid s, ” IEE E T ransactions on P ower Systems , vol. 30, no. 5, pp. 2243–2256, 2015. [6] Q. Li and D. Rus, “Globa l clock synchroniza tion in sensor netw orks, ” IEEE T ransactions on Computers , vol. 55, no. 2, pp. 214–226, 2006. [7] W . Ren and E. Atkins, “Distrib uted m ulti-v ehic le coordinate d control via local information e xchange, ” Internatio nal Journa l of Robust and Nonline ar Contr ol , vol . 17, no. 10-11, pp. 1002–1033, 2007. [8] A. Abdessameud and A. T ayebi , “ Attitude synchroniza tion of a group of spacecraft without v elocit y measurements, ” IEEE T ransactions on Automat ic Contr ol , vol. 54, no. 11, pp. 2642–2648, 2009. [9] B. B. Johnson, S. V . Dhople, A. O. Hamadeh, and P . T . Krein, “Synchroni zatio n of nonl inear oscillators in an L TI electric al power netw ork, ” IEEE T ransact ions on Circu its and Systems I: Re gular P aper s , vol. 61, no. 3, pp. 834–844, 2014. [10] J. Nazario, “Polit ically moti va ted denial of service attacks, ” The V irtual Battlefie ld: P erspec tives on Cyber W arfare , pp. 163–181, 2009. [11] J. Slay and M. Miller , “Lessons learned from the maroochy water breach, ” in Internat ional Confere nce on Critical Infrastructu re Pr otec- tion , pp. 73–82, 2007. [12] F . Pasquale tti, F . D ¨ orfler , and F . Bullo, “ Attack detecti on and identi- fication in cyber -physical systems, ” IEEE T ransac tions on Automatic Contr ol , vol. 58, no. 11, pp. 2715–2729, 2013. [13] M. Naghnaeia n, N. Hirzal lah, and P . G. V oulgaris, “Dural rate control for security in cybe r-physi cal systems, ” in Pr ocee dings of the 54th IEEE Confer enc e on Decision and Contro l , pp. 1415–1420, 2015. [14] H. Jafa rnejadsa ni, H. Lee, N. Hov akimyan , and P . V oulgaris, “ A multirate adapti ve control for MIMO systems with appli cation to cybe r-physi cal security , ” in Proc eedings of the 57th IEE E Confe re nce on Decisi on and Contr ol , pp. 6620–6625, 2018. [15] N. H. Hirzallah and P . G. V oulgaris, “On the computa tion of worst attac ks: a LP frame work, ” in Annual American Contr ol Confer ence , pp. 4527–4532, 2018. [16] G. Park, H. Shim, C. Lee, Y . E un, and K. H. Johansson, “When adve rsary encounters uncertain cyber -physical systems: Robust zero - dynamics attack with disclosure resource s, ” in P r oceed ings of the 55th IEEE Confer enc e on Decision and Contr ol , pp. 5085–5090, 2016. [17] J. Kim, G. Park , H. Shim, and Y . Eun, “Zero-steal thy attack for sampled- data contro l systems: The case of fa ster actuat ion than sensing, ” in Pr oceedi ngs of the 55th IE EE Confer ence on Decision and Contr ol , pp. 5956–5961, 2016. [18] S. Sundaram and C. N. Hadjic ostis, “Distribut ed function calcul ation via linea r itera ti ve strate gies in the presence of malicious agents, ” IEEE T ransactions on Automatic Contr ol , vol. 56, no. 7, pp. 1495–1508, 2011. [19] F . Pasqu aletti , A. Bicchi, and F . Bullo , “Consensus computati on in unrelia ble networks: A system theoretic approac h, ” IEE E T ra nsactions on Automati c Contr ol , vol. 57, no. 1, pp. 90–104, 2012. [20] S. W eerakkod y , X. Liu, and B. Sinopoli, “Rob ust structu ral analysis and design of distri buted control systems to pre ve nt zero dynamics atta cks, ” in Pr oceedi ngs of the 56th IEEE Confere nce on Decision and Contr ol , pp. 1356–1361, 2017. [21] J. Chen, J. W ei , W . Chen, H. Sandberg, K. H. J ohansson, and J. Chen, “Protec ting positi ve and seco nd-order systems against undetec table attac ks, ” IF AC-P apersOnLine , vol. 50, no. 1, pp. 8373–8378, 2017. [22] J. Back, J. Kim, C. Lee, G. Park, and H. Shim, “Enhancement of securit y against zero dynamics attack via general ized hold, ” in Pr oceedi ngs of the 56th IEEE Confe re nce on Decision and Contr ol , pp. 1350–1355, 2017. [23] A. T eix eira, I. Shames, H. Sandber g, and K. H. Johansson, “Re v ealing stealt hy attacks in control systems, ” in 50th Allerton Confere nce on Communicat ion, Contr ol, and Computing , pp. 1806–1813, 2012. [24] Y . Mao, E. A kyol, and Z. Zhang, “Nov el defense strategy against zero- dynamics attac k in multi-age nt systems, ” in Proce edings of the 58th IEEE Confer enc e on Decision and Contr ol , pp. 3563–3568, 2019. [25] H. Hartenstein, K. P . Laberteaux et al. , “ A tutoria l surve y on vehicu lar ad hoc networks, ” IEEE Communicat ions Ma gazine , vol. 46, no. 6, pp. 164–171, 2008. [26] S. K. Mazumder , W ir ele ss netw orking based contr ol . Springer , 2011. [27] M. Xue, W . W ang, and S. Roy , “Security concepts for the dynamics of autonomous vehicle networks, ” Automatica , vol. 50, no. 3, pp. 852–857 , 2014. [28] J. Kim and L . T ong, “On topology attack of a smart grid: Undetecta ble attac ks and countermeasures, ” IEEE J ournal on Sele cted Ar eas in Communicat ions , vol . 31, no. 7, pp. 1294–1305, 2013. [29] R. Sko wyra, L. Xu, G. Gu, V . Dedhia, T . Hobson, H. Okhravi, and J. Landry , “Ef fecti ve topology tampering attack s and defenses in softwar e-defined networks, ” in 48th IEEE /IFIP Internat ional Confer ence on Dependabl e Systems and Networks , pp. 374–385, 2018. [30] H. G. T anner , A. Jadbabaie, and G. J. Pappas, “Flocki ng in fixed and switchin g networks, ” IEEE T r ansactions on Automatic contr ol , vol. 52, no. 5, pp. 863–868, 2007. [31] S. Rah ili and W . Ren, “Distri bute d continuous-ti me con ve x opti mization with time-v aryi ng cost functions, ” IEEE Tr ansacti ons on Automatic Contr ol , vol. 62, no. 4, pp. 1590–1605, 2017. 16 [32] R. O lfati-Sabe r , “Flocking for multi-a gent dyna mic systems: Algorithms and theory , ” IEEE Tr ansacti ons on Automati c Contr ol , vol. 51, no. 3, pp. 401–420, 2006. [33] J. R. Lawton, R. W . Beard, and B. J. Y oung, “ A decentrali zed approach to formation maneuv ers, ” IEEE T ra nsactions on Robotics and Automa- tion , vol. 19, no. 6, pp. 933–941, 2003. [34] J. Mei, W . Ren, and J. Chen, “Distri buted consensus of second-order multi-ag ent systems with heteroge neous unkno wn inert ias and control gains under a directe d graph, ” IEEE T ra nsactions on Automat ic Contr ol , vol. 61, no. 8, pp. 2019–2034, 2016. [35] A. T eixeira, D. P ´ erez, H. Sandberg, and K. H. Johansson, “ Attack models and scenario s for network ed control s ystems, ” in Pr ocee dings of the 1st internat ional confer ence on High Confiden ce Network ed Systems , pp. 55–64, 2012. [36] G. Xie and L. W ang , “Consensus control for a class of networks of dynamic agents: switching topology , ” in A nnual American Contr ol Confer enc e , pp. 1382–1387, 2006. [37] T . Smi th, “Hack er jaile d for re ven ge sew age att acks, ” https:/ /www . there gister .co.uk/2001/10/31/hacker jaile d for re v enge se wage/ , accessed 2001-10-31. [38] A. T eixeira , G. D ´ an, H. Sandber g, R. Berthier , R. B. Bobba, and A. V alde s, “Security of smart distrib ution grids: Data integrit y attacks on integrate d v olt/v ar control and countermea sures, ” in Annual American Contr ol Confer enc e , pp. 4372–4378, 2014. [39] H. J. van W aarde, P . T esi, and M. K. Camlibel , “T opology reconst ruction of dynamica l network s via constrain ed L yapunov equations, ” IEEE T ransactions on Automati c Contr ol , v ol. 64, no. 10, pp. 4300–4 306, 2019. [40] Y . Mao and E. Akyol , “On inference of netw ork topology and confir- mation bias in cyber -social networks, ” to appear in IEEE T ransact ions on Signal and Information Proce ssing over Networks (Special Issue on Network T opology Inferenc e), [41] A. D. Am es and S. Sastry , “Characteri zation of Zeno beha vior in hybrid systems using homological methods, ” in Annual American Contr ol Confer enc e , pp. 1160–1165, 2005. [42] J. W eimer , S. Kar , and K. H. Johansson, “Distribute d detecti on and isolati on of topology attacks in power networks, ” in P r oceed ings of the 1st international confer ence on High Confidence Networked Systems , pp. 65–72, 2012. [43] A. E. Brouwer and W . H. Haemers, Spectra of graphs . Springer Science & Business Media, 2011. [44] A. T anwani , H . Shim, and D. Liberzon , “Observ abil ity for switched linea r systems: chara cteriz ation and observer design, ” IEEE T ransactions on Automati c Contr ol , vol. 58, no. 4, pp. 891–904 , 2013. [45] J. Z hang and L. Sankar , “Implementat ion of unobserv able state- preservin g topology at tacks, ” in North America n P ower Symposium , pp. 1–6, 2015. [46] D. G. Luenberg er , “Observing the state of a linear system, ” IEEE T ransactions on Military Electr onics , vol. 8, no. 2, pp. 74–80, 1964. [47] M. Porfiri, D. G. Roberson, and D. J. Stilwell, “Fast switchin g analysis of linear switche d systems using exponent ial splitting, ” SIAM J ournal on Contr ol and Optimizati on , vol. 47, no. 5, pp. 2582–2597, 2008. [48] R. A. Horn and C. R. Johnson, “T opic s in matrix analysis, ” Cambridge UP , New Y ork , 1991.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment