Microgrid Resilience: A holistic approach for assessing threats, identifying vulnerabilities, and designing corresponding mitigation strategies
Microgrids are being increasing deployed to improve the operational flexibility, resilience, coordinated-energy management capabilities, self-adequacy, and increased reliability of power systems. This strong market growth is also driven by advances i…
Authors: Sakshi Mishra, Kate Anderson, Brian Miller
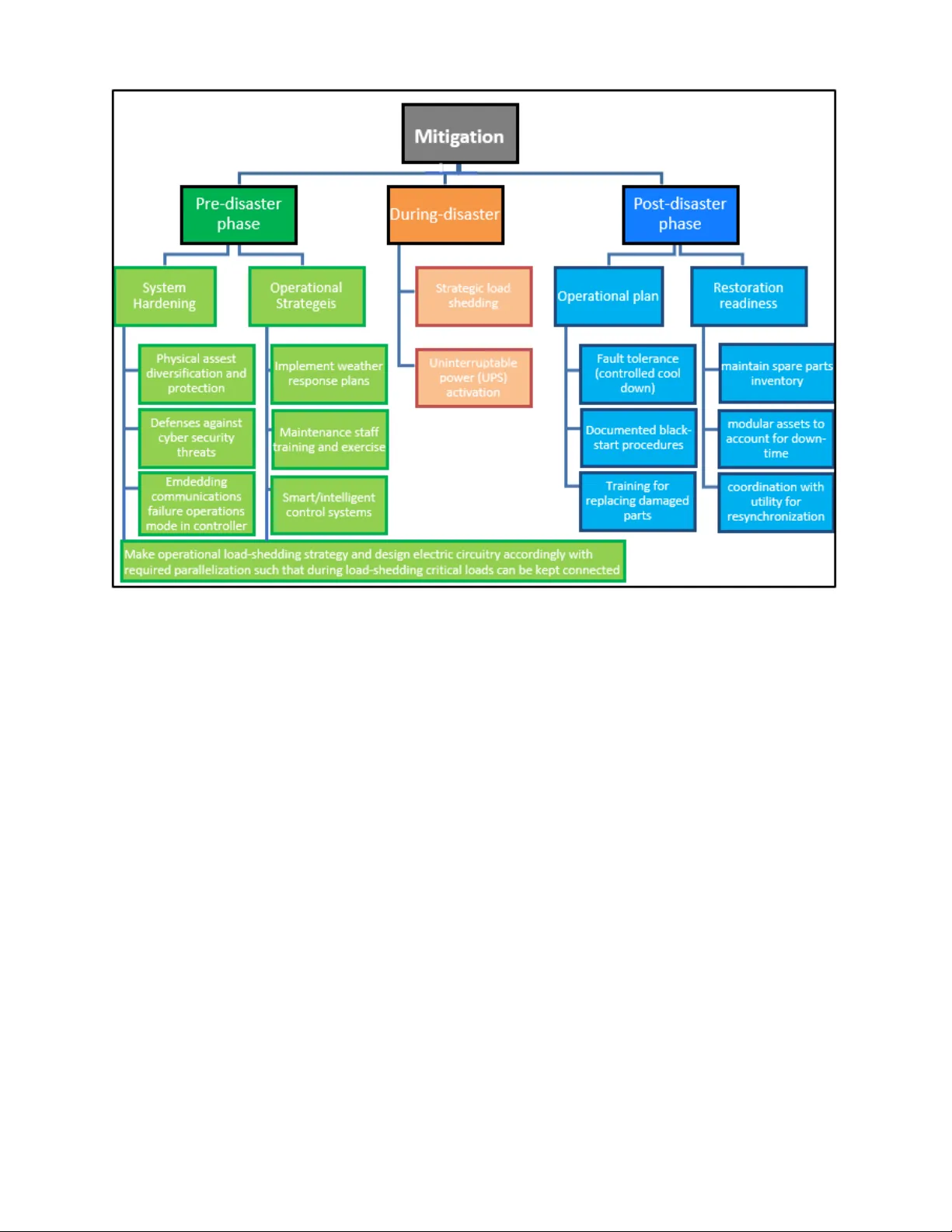
Microgrid Resilience: A holistic approach for assessing threats, identifying vulnerabilities, and designing corresponding mitigation strategies Sakshi Mishra * , Kate Anderson, B rian Miller, Kyle B oyer, Adam War ren National Renewable Energy Laboratory, Golden, CO *corresponding author Emails: Sakshi.Mishra@nrel.gov , Kate.And erson@nrel.gov , Brian.Miller@nrel.gov , Kyle.Boyer@nrel.gov , Adam.Warren@nrel.gov Abstract — Microgrid s are being increasing deployed to impro ve the operational flexibility, resilience, coordinated-energy management capabilities, self-adequacy, and inc reased reliability of power systems. This strong market growth is also driven by advances in power electronics , improved control systems, and the rapidly falling price and incre ased adoption of distributed energy generation technologies, like solar photovoltaics and st orage. In the event of grid outages , micro grids can provide a backup source of power; providing resilience to t he critical loads ; however, th is req uires that the microgrid itself is resilient to physical and cyber threats. Build ing highly resilient microgrids requires a methodological assess ment of potential threats, identification of vuln erabilities, and de sign of mitigation stra tegies . This paper provides a comprehensive review of threats, vulnerabilities, an d mitigation strategies a nd develops a definition f or m icrogrid resilience. The paper also develops a methodology for designing resilient microg rids by considering how microgrid designers and site owners evaluate threats, vulnerabilities, and consequences and choose the microgrid features required to address these threats under different situations. Keywords — Microgrid, Resilience, Reliability, Risk Assessment, Cyber-physical microgrid, Resilience Metric, DERs I. I NTRODUCTIO N A. Motivation a nd Background In a develo ped co untry like the United States, w ith an in creasing shift towar d an electrified an d dig ital econ omy, many cr itical infrastructur e sectors (e.g., communi cations, wate r, food , defense, healthcare) rely d irectly or indirectly up on the electric po wer supply. Thus, an unin terrupted and continuous supply of p ower is an essential compo nent of co ntinued well -being and sustainab le developm ent o f the n ation. For coun tries in the developin g wor ld , basic electrificatio n plays a critical role in ad vancing economic developm ent, which requires reliable power infrastructure . As decen tralized gener ation sources are proliferating around the world, microgrids ar e becoming an effective means of generating and utilizing power locally. The energy sector has been designated as a uniquely critical infrastructure “due to the enabling function [the energy sector] provide[s] acro ss all infrastructure sector s” by Presidential Policy Dir ective 21 (PPD -21) [1]. R ecen t wea ther-related even ts and cyberattacks have brought the resilience of the energy sector to the forefront of the national research priorities . As stated by the Executive Office of the Presid ent , “ the resilience of the U.S. electric grid is a key part o f the natio n’s defen se against severe wea ther ” [2] . The eco nomic and security imp act of such ev ents can be widespread beyon d the stricken area . Natural and hu man-induced disasters can result in lo ss of electricity , causing large financial lo sses that span multiple sectors and various service types, negatively impacting the day- to -day lives of thousands, if not millions, of residents during each incident. For example, water infrastructu re (water treatment plants and pumps), as well as the transportation sector (traffic signals), are impacted when electricity supply is interrup ted . Such interdependencies worsen the impact of an electricity o utage o n the ec onomy as a whole. A 2012 Congression al Research Service stud y fo u nd that the inflatio n-adjusted co st o f weath er-relate d outages in 2 012 is $25 - billion to $70-billion annually [2] . The frequency and severity of power outages caused b y e xtreme weather h ave b een incre asing [3] . A tropical storm can impo se three phases of impacts on power in frastructure : 1) initial impac t o f wind an d rain (Hurricane Hermine in 2016, which struck Florida.); 2) storm surge in co astal areas and near major inla nd waters (Hurrican e Katrina in 2005, Lake Pontchartrain, Louisiana.) ; and 3 ) flooding due to precipitation (Hu rricane Sandy in 2012, which struck the eastern United States) [4] . In the first phase, hig h- speed wind s can bring d own the o v erhead wires, wh ereas the storm surge in second phase can cause con siderable damage to generation and storage assets of the microgrid which are located close to the coastline. The next phase o f flooding after storm sur ge hampers the restoration process. 2 Other natur al hazards such as earthqu akes also have dev asting impact on the grid. The potential for ea rthquake disruption of major power system equipm ent is significant. The 201 8 Hokkaido Eastern earthquake knocked out power to 5 million people in H okkaido , Japan. A 1.6 5-gigawatt po wer p lant that supplies mo re than half o f the power of th e largest Japan ese main island s was shu t down following a magnitude 6.7 quake . In 2018, at least 80 reports of weather-rel ated power o utages were reported in the United States, which affected at least 50,000 customers [5]. In 2013, the E xecutive O ffice o f the Presi dent published a report [2] pointing to seve re weathe r as the single most common cause of power outages in the United States, representin g over half of all outages and 87% of all outages that affecte d 50,000 or more cust omers from 2002- 2012 . [2]. Hurricane Sandy caused powe r outages to which 50 deaths are attr ibuted [2] . In 2008, over 129 line faults in Southern China occurr ed due to a snowstor m [6] . Beyond we ather e vents, human-ind uced outa ges a re als o a c oncern. A gunman in Metc alf C alifornia hit 17 trans formers, resultin g in $15 mil lion in equipment damage [6] [7] . A 2015 cyberatta ck on t he Ukrain ian g rid caused a powe r outage for si x hour s and le ft approxima tely 225,000 peopl e without power. The BlackE nergy malware attack infect ed a utilit y’s netw ork through spear-phishi ng email, the n harvest ed the credent ials requi red to gain acc ess to their Super visory Control and Data Acquisiti on (SCADA) system operatio n. The attacker then opened breakers to bring more th an 30 substations offline [8]. More recently, a cyber event within the power grid was reported in the United St ates in 2019 [9]. Thes e cy be r eve nts i n the Ukraine and in small U.S. util ities may be an indicatio n of advers arial preparatio ns, increasin g their r eadiness to conduc t larger-s cale atta cks, if needed, at a strate gic time. Given a host of natural and human -induced threats an d the complexity of power systems, building resilience in energy infrastructure is a ch allenging task. Power system resilience has b een defined as “a grid wh ich h as f our f und amental properties of resilience, namely anticipation, absorption, r ecovery, and adaptability after th e damaging events” [10]. A recent review p aper on power grid resilience [10 ] look ed at how sev eral organ izations defin e resilience. While ev ery organ ization has its own d efinition of resilience, there are some co mmonalities. In g eneral, resilience is ch aracterized b y resistance to damaging events, th e ability to ab sorb th e impact of events without loss of service to customers, the recovery capabilities after an event, and the adaptive ability of the s ystem to learn from an ev ent and p repare more effectively for the next on e . The damaging events ar e typically ch aracterized as low- probability, hig h-impact that affect large regions over long duration s. Planning for and build ing resilience solution s in power systems require a com prehensive evaluation framework. The steps inclu d e: 1) und erstanding the types an d severity o f the ev ent for a given geograph ical area ; 2) defining resilience metrics relevan t to the situation; 3 ) identifying a suitable m ethodology f or system assessment d uring and after the event; an d 4) calculating th e fault consequen ces, including estimating the true cost of the lost load. Building resilience is ca tegorized into two major ways: system hardening and o perational strategies for r esilience [6] . Based on the type of natural disaster to which a given geograp hic area is p rone, various system hard ening approaches can be employed, including upgrading po les with rob ust materials, elevating substation s, m anaging veg etation, and undergro unding distribution lines. Building redundancy (meshed networks instead of radial on es) is another syste m-har dening practice that h as bee n widely ado pted for decades by u tilities as a reliability mea sure for cr itical loads , such as hospitals . However , redundancy is ineffective against certain events (e.g., a fire in an underground vault can destro y both sets o f redundant p ower lines co ntained therein). Moreover, redundancy for large proportions of a n etwork may be uneconomical. A major bottleneck with em ployin g system-hard ening strategies is capital investment. Valuing the benefits of resilience can help i n understand ing the c ost-b enefit implications of hardening the s ystem and potentially strengthen the business case to do so. Operational strategies present an alternat ive to capital investments and present a wid e range of opportunities for building g rid resilience. From a utility perspective, approac hes such as adv anced co ntrol and pro tection schemes, automated f ault location , isolation using Ad vanced Metering Infrastructu re (AMI), and demand-side -management can b e employed to mak e the grid more resilient. Dense in terconnection of transmission systems stren gthens power networks because these networ ks en able the movement o f economically generated power from generatio n to load while o ffering redund ancy. However, during a sev ere event, th ese interconnec tions can lead to ca scading blackouts or load-shed ding . Intact portions of the grid are often connected radially to impacted or dam aged p arts, spreading the impact of the fault. In rad ial netwo rks, the power cannot be rerou ted fr om the point of generation to the intact portions of th e grid if a connecting co mponent such as a transmission line is damag ed. Grid hardening strategies, such as underg rounding lines, will n ot help with such cascading failures. Althou gh underground lines avoid trees an d wind fau lts, they can be damaged by floods or earthquakes an d are more difficult to repair than aerial lines . Localized resilience solutions, such as microgrids, are less vulnerable to cascading power system black outs . The U.S. Dep artment of Energy ( DOE ) defines the microgrid as “a group of interconnected loads and distributed energy resources within clearly d efined electrical b oundaries th at acts as a single controllable en tity with respect to the grid. A microgr id can co nnect and disconnec t from the gr id to enable it to o perate in both grid -con nected and islan d- mode” [2 ]. Microgr ids are incr easingly being u tilized as backup systems for reliability and r esilience solu tions. Microgrid s have largely been adopted by m ilitary b ases, h ospitals, academic institutions, cities, an d po rts. According to a market study report b y Wood Mack enzie [11], th e cum ulative cap acity of micr ogrid installations is forecasted to reach 8 .8 GW by 2024 due to favorable market factors. 3 Microgrids can play a key role in providing resilience at the community or neighborhood level . Microgrids are unique among other gr id -hardening measures and techno logies, in that they can be installed by the customer, rather than requiring deployment by t he utility . Sign ificant savings through risk reduction and expeditious rec overy can be achieved by build ing resilience in comm unity - level gen eration and storage infrastru cture [12]. Alo ng with boosting resilience, benefits of micr ogrid to the local co mmunity includ e potentially reduced cost, as the microgrid can reduce demand on the grid during pea k hours an d also participate in markets by do ing energy arbitrag e. As stated in [2] , “A key f eature of a microgrid is its ab ility dur ing a utility grid disturbance to separate and isolate itsel f fr om the utility seamlessly with little or no disruption to the loads with in the microgrid .” The ability to operate independen tly from the grid is par ticularly important d uring weather -related gri d outages, wh en the lo ss of power lines or substations may prevent the restoration of power , even after the utility’s gen eration capab ilities are back o nline [2]. During post -event gr id-connected operational m ode, a microgrid’s surplus electricity generatio n capability can b e used for pro viding a n ew reliability service aimed at accelerating the restoration of supply to neighbo ring customers [13] . Strate gic installation o f networked m icrogrids in wea k regions of the po wer system has been shown to help with the post-d isaster recovery of the utility grid [3] [14]. While microgrids are increasingly being adopted as a resilie nce and reliability solution, their own vulnerabilities cannot be ignored. The physical v ulnerabilities of distributed gen eration -based microgrids are relatively lower fo r weath er-related ev ents compared to the u tility grid , as no tr ansmission and f ewer distribu tion lines are involved. The microgrid may be impacted by a weather event if it is in close pro ximity to the epicenter of the event , but there is lower probability of inter ruption of supply due to a natu ral disaster or a human-induced attack h appening somewhere else in the utility grid . But im properly d esigned micr ogrids can be more vulnerable to com munication s f ailures and cybersecurity- related events. For ex ample, power substations are designed with dual redundant communication networks, but many m icrogrid s have not been so design ed to m itigate single po ints of failure . Therefore, it is essential to identify th e risks, u nderstand the vulnerabilities, and design the microgrid s with mitigatio n measures that assuredly make them resilient against physical, communications, and cybersecurity -related threats. Systematically addressing these vulnerab ilities du ring the d esign phase o f the m icrogrid along with disaster preparedness to op erate th e microgrid during the most needed times will make microgrids a truly reliable, resilient, and enduring solu tion. B. Literature Review Many studies have been conducted in the literature of power systems (utility grid) resilienc e . A r eport from the Executive Office of the President describes the economic benefits of increasi ng the resilience of power systems to outages caused by weather events in the context of US crit ical infrastr ucture enhancem ent [2]. Jufira e t al. prese nt a review of power sys tems resilien ce def initions a nd quantitati ve assessment methodol ogies for measuri ng resilience [10] . A d etaile d descri ption of the damage caused by weather related- events to power systems infrastructu re and its impact on bulk power system energy sup ply capabilit y is presented in [15] . A nother report fr om the US Departme nt of Energy em phasizes the be nefits of int egrating dist ributed e nergy res ources to inc rease infras tructure resilienc e [16] . Key strategi es for realizing power systems r esilie nce are discussed in [1 7]. Ouyang et at. focus on a resilienc e assessme nt of power systems with res pect t o hurric anes [18] . A me thodolog y for deter mining optimal p ower syste ms investm ent for buildin g resilience is prese nted in [19]. A framewor k for load restorati on in the u tilit y grid is propos ed in [6], and strategies for modelin g large-scale energ y infrastr ucture from a resilie nce pe rspective have been explored in th e literat ure [20] . Powe r system’s infrast ructure resil ience has ther efore been stu died extensive ly; b ut microgri d resilience remai ns relatively unexplored. There is a need for understa nding an d measuri ng the resilie nce of mic rogrids (in isl anded mode or as s tandal one entities in developing nations) against v arious t ypes of th reats to ma ke them e ffective backup s ystems. The p rocess of d esigning resilien ce micro grids start s with a risk assessment. A risk assessm ent is a systematic way of identifying possible threats an d estimating the severity of the corresponding vulnerabilities. A variety of risk assessment m ethodologies are used in industry, including Preliminar y Hazard Analy sis (PHA), What - if, Hazar d an d Operability (Hazop) stud ies, Failure Model and Eff ect Analysis (FME A), Fault T ree Analy sis (FTA), Expected Damag e-Cost An alysis (E DCA), and Quantitative Risk Analy sis (QRA) [21]. For microgrid-deploy ment projects, several approaches have been tak en. Williams et al . present a case study of assessing risks to a micro grid for rur al electrificatio n in developing n ation s [22]. A risk-based per formance analysis of m icrogrids with d istributed energy generation is presented in [23] . A risk assessmen t fo r in corporating mitigation measures to make a micr ogrid resilient with cybersecurity perspective is presented in [24 ] . Risk analysis for micro grid deploymen t, therefore, is a multifaceted process where f irst th e business risks associated with economic operations are analy zed, and then the next step is to id entif y and quantify the risks associated with the r esilience of the micro grid. A q ua ntitative fram ework for a micro grid resilience assessmen t against windsto rms is presented in [25] . An o perational strategy to cope with the adverse impacts of extreme windstor m are presented in [26] . In this work , when the windstorm forecast aler t or a flooding alert is r eceived, the microg rid’s operational strategy is modified through network reco nfiguration, demand -side resources, generation reschedule, optimal param eter settings of d roop -contro lled units (such as Combined Heat and Power), and conservati ve voltage r egulation to help it ride through the event . Likewise, an oper ational strategy to sustain op erations during flooding is presented in [27 ] . A similar proactive op erational scheduling for buildin g operational resilience against hurrican es for multi -carrier 4 microgrids is presented in [28] . Liang et al . [29] pr opose a control strategy for electric spr ings 1 to enhance the op erational resilience of microgrids. Recently, Liu et a l. hav e resear ched the cybersecurity aspect of m icrogrid r esilience an d an alyzed DC microgrid resilience un der a denial- of -service th reat [30] . These works have focus ed on one specific aspect of microgrid resilience at a time , includin g physical sturdiness from natu ral disasters and maintaining cybersecurity. Th e work presented in this paper encomp asses a h olistic qualitative appro ach for ass essing the external threats and associated v ulnerabilities to a microgrid , and provid es desig n and o perational strateg ies tailored for mitigating the risk associated with identified threats. This w ork details both p hysical (hardware) and controls (software) dimensions of the m icrogrid to design a strategy for building microgrids capab le of addressing threats in p hysical, cyber, and communicatio ns dimensions. The specific contributions of this work ar e as follows: • We id entify and categorize various th reats to power systems and microgrid operations , includ ing p hysical, cyber, and communications th reats. We also p resent a quantitative th reat-m odeling metho dology. • We determine microgrid vulnerab ilities associated with the threats id entified in th e previous step. • We propo se variou s mitigation strategies for enh ancing th e microgrid design to be resilien t in bo th the physical and contro ls dimensions. We also recommend operational strategies f or minimizing d amage during the dis aster and for faster recovery of the microgr id afterward. • As an ex tension of resilience, we also brief ly cover the reliability asp ects of microg rid performan ce and differentiate between the two . C. Article Structure With Section I .A layin g o ut the motiv ation b ehind this work an d a d etailed review of the m icrogrid resilience literature in I.B, the rest of the pap er is org anized as fo llows : Section II intr oduces the prelimin aries of reliab ility and resilience in the context of a microgrid. The risk assessment metho dology is def ined in Section III . Section III.C.2) delin eates the threats to the r esilient performance of p ower systems, includ ing microgr id operations , and iden tifies the v ulnerabilities associated with th e threa ts. An example case study for risk factor calculatio n is p resented in Section V. Section VI presents various mitigation measures, which can be employed for p rotecting the microgrid against different kind of th reats as a preventive measure and various strategies for decreasing post -disaster recovery time. Th e article is concluded in Section VII where future resear ch directions are iden tified. II. R ESILIEN CE A ND RELIABILI TY Power system reliability has been s tudied in detail in t he literature . Standardized metrics are u sed across the industry t o measure the reliability o f electricity supply from th e utility . However, the dev elopment of resilience metric s is an active research area , and industry -accepted metrics fo r measuring the r esilience of microgr id s (or the utility grid ) do not yet exist . I t is essential t o descr ibe the d ifference b etween resilience an d r eliability of a microgrid to make effectiv e design ch oices ad dressing the two aspects appropriately. A. Reliability Billinton et al. describe reliability in power systems as covering “all aspects of the ability of the po wer system to perform its in tended function of providing an adequate supp ly of electrical energy to customers efficiently with a reasonable assurance of continuity and quality” [31] . DOE ’s definition of reliability focuses on the ability of the systems to withstan d sudden disturbances , such as electr ic short circuits or unanticipated loss of system com ponents [32] . Reliab ility concerns of the utility grid can b e divided into two m ain categories: system adequacy and system security. T he sufficiency of generation, transmi ssion, and distribution resources is required for m aintaining system adequacy — th e assessmen t is as sociated with static sys tem con ditions. On the other hand, system security relates to the ability of the system to maintain the continuity of the supply by responding to perturbations arising within th e system, which include transient and dynamic disturbance s. System security also concerns the ability of co mponents or eq uipment t o p erform efficiently for a particular period, under a specified condition. Events un dermining the reliability o f power systems typ ically last seconds (tran sient or dynamics disturb ances) or hours ( an unplanned o utage of a g eneration unit o r a major tr ansmission line) an d are cau sed by N -1 or N-1 - 1 contingency conditions. Th ere are standardized metrics, such as System Av erage Interruption Duration I ndex ( SAIDI) , System Av erage Interruption Frequency Index (SAIFI), and Customer Average Interruption Duration Index ( CAIDI), developed b y the North Amer ican Reliability Corporation (NERC) for assessing the reliability performance of the u tility grid at the individual utility level . Tradition al solutions used for ensuring th e reliability of the u tility g rid include meshed gr ids on the distribution side (alter native feeders to restore the supply, components in par allel) and adv anced p rotection devices . Distributed energy resour ces (DERs) and other smart grid technolog ies are providing new opportu nities for maintaining system r eliability in the grid context. Similar aspects are associated with reliability for microgrids; ho wever, the solu tions to ensure reliability in the microgrid are not the same as the solutions typically employed for the utility grid. A microgrid has a constrained amount of generation resources, and 1 electric springs is a new smart grid technology introduced in [59]. 5 there may not be redundancies in components for economic r easons . To increase its reliability, a h eavy emphasis needs to be placed on the reliable operation of the componen ts in the microgrid (i.e., testing and preventative mainten ance). Considering t he case of resilience, r eliable op eration of the microgrid comp onents (without any external threat) is a necessary b ut no t sufficient condition to endur e an external thr eat. On the other head, if the reliabili ty of the components is already weak, then add ing mitigation measure s to increase resilience o f the microgrid is of little use since the foundation of the m icrogrid ’ s operatio nal performance (i.e. reliability) is itself weak . As discussed in the p revious paragraph, u nderstanding the reliability of the c omponen ts of the microgrid is also an aspect of the resilient perf ormance. However, it is a small subset o f the lar ge resilience performan ce equation. Reliability can loosely be correlated with the probability of vulnerability of system componen ts ( vulnerability is described in detail in Section III.B) by asking the following question: how likely is it that compon ents forming both p hysical an d cyber layers of the m icrogrid will accomplish the functional objectives in the face of an ex ternal threat ? Apart from the probability of componen t failure , the contingencies that may cause reliability co ncerns in the micr ogrid are: 1) communications f ailure on the utility grid during gr id-connected operations; 2 ) internal communications failures causing a disconn ect between th e master microgrid controller and physical assets, for ce ntralized microgrid topology; and 3) disconnect between the distributed con trollers cau sing u ncoordinated oper ation of various physical assets in a decentralize d microgrid to pology . B. Resilience Resilience, on the other hand , is th e ability of a sy stem (and its components) to adapt to changing conditions ; and withstand and recover f rom disrup tive events. It is a wide -reaching con cept that does not just imp act one com ponent at a time. Instead , resilience is the sy stem ’ s ability to endure an d recover from low- probability , high-impact events, such as natural disasters and human-in duced attacks, that m ay impact la rge geographic region s over longer dur ations . Figure 1 shows the process diag ram of resilience analy sis an d deployment . Building resilient micr ogrids is an iterative process. A microgrid can be designed with fea tures that ad dress the ide n tified threats and v ulnerabilities; ho wever, n ew threats o r vulnerabilities may be revealed over time, particularly when the microgrid is tested during an actual disaster. Depending on its performance during and after th e disaster, the microgr id design ca n be upgraded to adap t to newly identified threats and vulner abilities . This cyclic model is especially relevant for cyb erthreats becau se the attack surf aces and mediu ms th rough which th e cyber infrastructure o f a microgrid can be damaged ar e growing with increasing interconnectivity of th e electrical and smart communication s systems. Therefore, wh en the prev iously unknown vulnerabilities in t he cyber -analytics layers ar e exp osed through either an ex ternal attack or an internal awar eness, the micr ogrid sho uld adapt to enhance resilien ce towar d the newly id entified cyberthreats and minimize or eliminate its associated vu lnerabilities. T he five attributes sho wn in green ar e exp lained in detail in Tab le 11 . Figure 1 Process of building a resilient microgrid Resilience can be long er-term ad aptability to with stand or rap idly recover from u nusual and extrem e events. Unlike reliability, resilience is no t just about restoring power ( to mor e cu stomers and in less time) after an ou tage. Resilience can fo cus more on critical power and leave noncritical customers off f or longer durations to preserve limited lo cal ener gy. Resilience is also fo cused on longer duration events where the outa ge impacts can grow exponen tially over days and weeks. Thus, simple metr ics like reliability, fail to capture the entire concept. 6 In the cyber dimension, it is also importan t to d ifferentiate between cy bersecurity and cyb er -resilience with respect to energy systems operation s . Cybersecur ity refers to the process and meth ods for protecting the data (wh ich could be voltage, frequen cy, price sig nals, fr equency regulation signals, etc.), including clear inform ation about where th e data reside s and how it is ex changed between various components of the microgrid and the utility grid [33] [34]. Cyber-resilience, on the other hand, refers to the ability of the energy system to maintain its operatio n in the event of a threat, and if impacted, th e ability to quick ly recover after the even t has passed [28] [30] . Gener ally, cybersecurity’ s central fo cus is vuln erability reduction. On the other hand, cyber -resilience tak es an integ rated app roach to minimize the risk, which is a combination of threat, vu lnerability, and impact (d etails in Section III.C ). The rest of th is article delineates thr eats, vulnerab ility, and mitigation strategies fo r microgrid resilience — u nderstanding and quantification of these three aspects lay th e groundwork for defining an effectiv e resilience metric for a microgrid . III. M ETHODOLOGY FOR ASSESSI NG THREATS AND ASSOCI ATED V ULNERABILI TIES It is essential to enhance the ability of decision makers to ass ess and manage risks associated with microgrids that may change over time and vary geograph ically. Therefore, clear identificatio n o f threats and vulnerabilities and the ir likelih ood and impac t is the first step in building resilient microgrids . This section describes how to identify the highest risks to a microgrid by assessing threats and vulnerab ilities specific the location or situation in which th e microgrid will be installed . A. Threats Threats are anything that can damage, destroy, or disrupt utility grid or microgrid operation. In other words, threats are what we are trying to p rotect microgrid against. They are typically natu ral or human -induced hazar ds that are no t within the site’s co ntr ol , such as wildfire, hurricane, cyber attacks, or physical attacks. Threats are identified throu gh the rev iew of clim ate data and state hazard assessments, and stakeholder interviews with s ite staff or emergen cy man agement teams f rom the sur rounding commun ity . Example microgrid threats to be considered are outlined in Table 1. Table 1. Types of Threats Natural Ha zards Technological H azards Adversarial H azards Hurricanes Grid outag e Inside b ad actor Flooding Water- and wastewate r- line disrup tion Outside bad ac tor Earthquakes Pumping system failure on water - and wastewater- lines Act of terror Severe winter sto rms Water damage to solar panels causing internal sho rt-circuit Cyber attack Wildfire Battery stored in extreme temperatures Political upheav al Hailstorms Internal Combustion Eng ine based g en sets located in ar eas with flammable vapor s or gases War B. Vulnerabilities Vulnerabilities are weaknesses within the microgrid eith er in infrastructure or processes. Unlike threats, t h ey are within th e site’s control and can be mod ified or mitig ated to prevent o r reduce the impact of a disruption. Vulnerabilities are iden tified through stakeholder interviews with energy man agers, electrical engineers, maintenance staff, emergency managers, utilities, m icrogrid designers, operator s, and en d-users. They can also be identified through a review of contingency response plans an d after-ac tion reports follo wing disasters or disruption s. Examples of microgrid vulner abilities to be co nsidered are outlined in Table 2. Table 2. Types of Vulnerabilities Type of Vulnera bilities Examples Physical • Lack of red undant backup systems • Lack of acce ssible spare part s • Single po ints of failure in electrical lines or generation sou rces. Natural • Equipmen t location pron e to flooding, fire, winds, earth quakes and oth er natural disasters. Cyber • Lack of cyber security defenses • Communication with e xternal networks or the internet • Data and co mmunication l eaks between inform ation network, operational n etwork, and other networks o r the op en internet. Communication • Single communicatio ns paths • Dependen ce on digital networks • Lack of red undant network components. Human • Lack of trained staff to operate the micr ogrid 7 • Inability of trained staff to access the site and the microgrid equipmen t during an emergency • Lack of wr itten procedures or training for oper ating microgrid . Communication s an d in formation technologies are i ncreasingly tightly integ rated with th e electric system and , in extension , with microgrids. Numerous advan tages are offered by greater connectivity and au tomated commun ications in terms of reliable and efficient grid operations. These technologies have also increased customer participation by p roviding a new medium for microgr ids and consumers to interact with the utility grid. On the flip side, they also expand the vulnera ble cyber surfac es by offering ad ditional vectors for intrusions and breaches. Ex ternal sources of information ex change for a microgrid include weather forecasts, pricing signals, Internet- of -Things (IoT)-connected appliance s (smart ap pliances which provide access to d ata/controls via the internet ) , frequency -regulation signals, peer- to -peer transaction s th rough public netwo rks, and so on . The more capabilities to i ntake and process v arious ty pes of information from external sources is ad ded, the more vulnerable th e micro grid is to cyberthreats. Th is i s because smart meters and other advan ced communications technologies are exposed surfaces for attacks if vulnerable parts such as control interfaces, data buses, d ata communicatio n channels, and remote debug ports are not protected well. I oT devices connec ted to a public netwo rk and electrical systems netwo rk simultaneo usly can be condu its through which cyberattack s can be executed . C. Risk and its A ssessment Assessing the risk essentially means fin ding a way to quantify th e relative potential of d amage t hat various th reats in the environment can cause to the microgrid. Risk, ther efore, i s a function of threats exploiting vulnerabilities to impac t the operations, and d amage or d estroy the assets. Thus , we def ine th e risk factor m etric based on the prob ability of a threat, th e prob ability of a vulnerability ’s exploitation given that th reat, and the imp act of the vuln erability. This d efinition of risk factor has bee n extensively used in the literature [3 5] [36] [37] [references]. A m icrogrid’s system -level risk assessment is th e first step in building resilient m icrogrids . 2 1) Ph ysical Threats are scored based on their likelihood of occurrence using a low-med ium-high qualitative scale, or a numerical scale ( e.g., 1- 10 , with 1 being very u nlikely and 10 b eing very likely ). Natu ral hazard threats are typically scored using do cumented natur al hazards, clim ate projections, and professional judgment . Non-nat ural hazard thr eats are scored based on information collected during stak eholder interviews. Vulnerab ilities are scored based on pro bability of exp loitation from a given threat, and the potential severity o f their im pact. Similar to threats, vulnerab ility scores can use a low -medium-h igh qualitative scale, or a numerical scale (e.g., 1- 10 , with 1 being low impact and 10 being high impact). Vulner ability probability scores shou ld consider the likelihood that a system will be compromised if th e threa t is real ized . Th is score is typically based on expert in terviews with staff familiar with the site, such as energy m anagers, electrical eng ineers, m aintenance staff, emergency managers, u tilities, an d m icrogrid oper ators. The sco re may be in formed by d ata in afte r- action reports fro m past ev ents and main tenance logs but is often based on expert judgment. For example, the probability of vuln erability of generation units, with respect to the threat of flood, would be high er for a site located in a co astal area with its assets placed on the ground -level, and lower for a site with elevated assets . Vul nerability impact sco res shou ld co nsider the geog raphic area of impact, the numb er of end -users affected , co st, safety, and environmental impacts. Vulnerability scores are based on the stakeholder in terviews and document review and are inherently m ore subjective than threat scores bec ause there is typically less d ata available to inform them. To evaluate the relationship between threats and vuln erabilities, th e threat lik elihood score is mu ltiplied by the vulnerability probability and impact scores to create a risk score for each specific threat -vuln erability combination. Risk is created when a threat can exploit an already present vu lnerability in the microgrid. The magni tude of the risk is determined by t he likelihood of the threat and vulnerability, as well as the scale of d amage the vulnerability could cause if exploited. T herefore, risk factor is calcu lated as intersection of these three f actors, as sho wn in Error! Reference source not fo und. . The risk score enables analysis and ranking of the risks to p rioritize m itigation actions. Threats an d hazards change over tim e, so the risk assessment should be updated on a regular basis. 2 Risks for a microgrid can be assessed for both individual compone nts , as well as at the system level. The risk associated with the failure of individual components in the microgrid, in lack of an external threat, will get categorized as a reliability concern. Whereas the system-level risk assessment, with respect to external threats, is a crucial step in gauging the resilience of the micro grid. 8 Figure 2 Risk Factor Metric - Venn Diagram 𝑅𝑖𝑠𝑘 𝑓𝑎𝑐𝑡𝑜𝑟 ≡ (𝑝𝑟𝑜𝑏𝑎𝑏𝑖𝑙𝑖𝑡𝑦 𝑜𝑓 𝑡ℎ𝑟𝑒𝑎𝑡 ) 𝑥 ( 𝑝𝑟𝑜𝑏𝑎𝑏𝑖𝑙𝑖 𝑡𝑦 𝑜𝑓 𝑣𝑢𝑙𝑛𝑒𝑟𝑎𝑏𝑖𝑙𝑖𝑡𝑦 ) 𝑥 (𝑖𝑚𝑝𝑎𝑐𝑡 𝑜𝑓 𝑣𝑢𝑙𝑛𝑒𝑟𝑎𝑏𝑖𝑙𝑖𝑡𝑦 ) (1) 2) Cyb er Models fo r cyber - security threat analy sis have b een dev eloped and stud ied by v arious techno logy companies’ research teams. STRIDE [38] is one such model of threa ts develop ed b y Microsoft for id entifying computer security threats, which is commonly used. It is a mnemon ic for the things that can go wrong in a cyber system, and stands fo r Spoofin g, Tam pering, Rep udiation, Information Disclosure, Denial of Service, and Elevation of Privileg e [39] . STRID E mod el, howev er, do esn’t yield a r isk score as it is primarily fo cused on calculating th reat scores. The DREAD mod el scores a potential threat on five metrics (Damage Potential, Reproducibility, Exploitability, Affected Users, and Disco verability), and averages th e scores to create numerical risk score. Ta ble 3 provides the d escription and scoring method for the attributes o f the DREAD model. Table 3. DREAD model attribute and associated scores Category Description Scoring Damage Potential How much damage is can be done? 0: No adv erse consequences 10: Total system failure Reproducib ility How reliably d oes the attack work? 0: Unlikely to succeed even with full access to the sy stem 10: Wo rks consistently and requires at most the level of acce ss available to th e general public Exploitability How easy is it to p erform the attack? 0: N/A; by d efinition, every vu lnerability must be exploitable in some way 1: Difficult for even an expert on the affected system and vulnerab ility to exploit 10: Minimal sk ill and no prior system access req uired Affected Users Scale of users af fected 0: No users aff ected 5: Issue contain ed to a subset of users 10: All users aff ected Discoverability How easy is it for an atta cker to discover the vu lnerability? 0: Nearly impo ssible to discover, even with full source code and access to runn ing system 10: Readily v isible to passive observer NOTE: In pr actice, d iscoverability is assumed to be 10 fo r any specific vulnerability which is already known to the system owner/operator . This follows the logic that if you know about th e vulnerab ility, it is likely that someon e else does too [40] . The analogy b etween the physical threat model and cy ber threat model can be established by loosely co mparing the attributes as follows: • probability of threat ≡ average of reproducibility + exploitability • probability of vuln erability ≡ disco verability • impact of vuln erability ≡ average of damage + affected users 9 IV. T HREATS TO MICRO ( AND MA CRO ) GRIDS AND ASSOCI ATED VULNERABILI TIES Threat modeling fo r complex systems is a four -stage process that begins with d efining and diagramming the system, then i dentifying things th at can go wrong, after wh ich mitig ation strateg ies can be developed . The entire p rocess is validated to ensure accur ate conclusions . For a complex cyber-physical system like a micr ogrid, there are multiple d imensions of resilience . They can be classified into three domains: • Physical resilience : Su staining physical infra structure (which includes assets and electrical cab les connecting the assets) during a disru ptive event and co ntinuing o r restoring oper ations rapidly after the event is over . • Cyber resilien ce : Id entifying and defending against various types o f cyberattacks and maintain ing safe p erformance during the occu rrence of such an ev ent. • Communication s resilience : Maintaining safe and stable operational performance during commu nications f ailures from the utility grid end or internal microgrids comm unications. The following sub sections discuss these threats in more detail. A. Physical Threats Physical threats include natural hazards ( wildfires, hurricanes, floods), changing climate (more extreme temperatures), and human- induced attac ks (including terrorist attacks , such as shooting substations ). • Natural h azards : Weath er events like t ropical cyclones, hurricanes, floods, ea rthquakes, and wildfires can ca use dam age to the utility grid, and if th e epicenter of the impact is geographically close to th e microgrid , then th e impact ca n be of eq uivalent order. Examples of vulnerab ilities resulting from natural hazards includ e : • Flooding can inundate eq uipment on or near the ground, cause gen erators to stop o perating, and cau se permanent damage; • Strong wind s can cause m icrogrid co mponents to fly away or topple overhead power lines; • Earthquakes can shatter the physical infrastru cture of the m icrogrid, causing d amage to assets; • Lightning strikes to elec trical components or cables in the microgrid can burn the components ; and • Wildfires can destro y generation, distribution, and controls equip ment . • Changing climate : increasingly extreme temp eratures caused by the changing climate can put undue strain on a microgrid especially wh en it is oper ating in islan ded mode. The spike in coo ling and h eating loads can ca use harm in two potential ways: 1 ) excessive power d emand can cause equipmen t and d evices to operate above their rated capac ity , resultin g in permanen t d amage; and 2 ) increased demand can cause load-shedding in the microgrid. If load -shed ding strategies are not automated, then there is an increased risk of a site-wide outage. Example vulnerab ilities resu lting from changing climate include: • He atwaves can cause an abr upt rise in air-co nditionin g loads, and if generation can not match the demand, site- wide outages or load-shedding can happen; • Winter storms and blizza rds can bring extreme cold, snow, hail, ice, an d h igh winds, and equipmen t ov erload due to prolonged perio ds of electric heating load s which can dam age equipment permanently ; and • During winter storms lasting sev eral days, maintenan ce of th e assets (damaged cables or generators located ou tdoors) becomes very d ifficult and increases the pro bability of a microgrid-wide outage. • Human- induced attacks : Phy sical attacks, such as bombings or shootings of major microgrid compon ents like g enerators and storage assets, cou ld cause seriou s damage and disable a microgrid . Electromagnetic pu lse attacks can also take o ut generatio n assets and controllers in the microgrid [41] [42] . The attack s can be from on e gunman shooting a specific equipmen t to a massive bombing that can d estroy the whole site. B. Cyber Threats Cyberattack s on microg rids can be classified into the following three types [43] [ 44]: attacks o n availability, in tegrity, and confiden tiality. • Availability: Attacks on availability attempt to limit or delay access to data. In a microgrid, this may be ex tended to include availability of power in addition to data. Attacks ag ainst availability are g enerally ref erred to as Den ial of Service (DoS) attacks. DoS attacks in m icrogrids g enerally include not only blocking resource access b ut also d elaying the timing of critical message exch ange . F or examp le, jamming communications ch annels between various par ts of th e microgrid. • Integrity: Attacks on integrity interfere with the ac curacy or t rustworthin ess of data. Spoofing, tampering, and elevation of privilege ar e all integrity violations. For the microgrid , interference with the qu ality of power mig ht also be consid ered a violation of integrity. For example, an attacker uses a Domain Name System (DNS) hijack to feed inaccurate pr ice data to the contro ller, showing diesel as cheaper than natural gas. The result is that the micro grid uses diesel instead of natural gas, costing the operato r m oney. Fa king a microgrid disconnect from the grid si gnal compromises the integrity. Othe r examples of integrity attacks include sending false co mmand s to the microgrid controller, causing unwanted or premature islanding; and changin g the setting groups of p rotection relays in a microg rid , causing the relays to trip err oneously . 10 • Confidentiality: Attacks o n conf identiality ar e attem pts to gain access to privileged information . This might include operational or b illing data, or any other in formation that should not be accessible to un authorized entities. For microgr ids participating in markets, the biddin g price data can be stolen. The example microgrid (shown in Figure 3) is a cyber-physical s ystem containing physical infrastructure (generation , sto rage, local distribution and transmission, loads) equ ipped with electronic con trols and sen sors as illu strated. These electronic devices are then connected via a n etwork to a super visory contro l system, which monito rs all systems in re al -time and coor dinates th e operatio n of the various physical systems. This supervisor y control system receives input from and reports back to the microgrid control s ystem, which is gener ally a n ear re al -time sof tware system that perfor ms optimization and resource sched uling. The microgrid contro l system is also connec ted to the utility, an y other external d ata sources, and the human -machine inter face (HMI) . In this system, each interface or trust boun d ary represents a poten tial attack su rface that must be analyze d for vulnerabilities. As methods for identifying specifi c threats are ex tensively well-docu mented elsewhere, we will focus here on tho se attack s urfaces that are common to microgrid systems in general, rather than on specific attacks, which must necessarily be identified on a case - by -case basis. Table 4 summar izes the vulner able attacks surfaces along with th e types of threats that can impact the operations of microgrids. Figure 3. Microgrid diagram with cyber-physical layers and associated trust bounda ries Table 4. Cybersecurity Risk Analysis Attack Surfac e Examples Threats/Vulner abilities Potential Impac t Wired Links Ethernet, Phone lines, RS -232, RS -422, RS-485, I2C (often used fo r sensors) Line may b e cut or unplugged, causing Do S. An attacker m ay splice into the wires and eavesd rop, tamper with , and inject data in to the medium . Blocking resou rces Delaying the timing of critical message exchan ge Wireless Links IEEE 802.11 (WiFi), Cellular network s, ZigBee/XBee The broadcast n ature of the medium enables any one to listen to communications . Signals may b e jammed, resulting in DoS. Confidentiality lo st With jammed signals, SCADA system loses connec tion with microgrid’s analy sis layer , causing sub-optimal operation . Unencryp ted Communication s Most low-level serial protocols in cluding I2C and SPI Unencapsulated TCP and UDP, inclu ding HTTP, FTP, Telnet An attacker wh o can access the medium can view, modify, and send meaningful data . Data confiden tiality lost — m arket participation bidding strategy compromised . Unauthenticated Communication s DNS, HTTP, most low - level serial pro tocols Attacker can p retend to be legitimate data source or user. Can cause unwan ted islanding of microgrid o r unwanted chang e to grid-conn ected mode during island (can be a life-threating issue if 11 maintenance workers are working on electrical compo nents). Exposed Endpoints Sensors, HMI, Remo te Servers, Anyth ing the attacker can g ain physical or virtu al access to Attacker cou ld falsify actionable data . Attacker cou ld damage interface, causi ng DoS. Wrong price -signal or wea ther data will cause subop timal and noneconom ic operational dispatch strategy of th e microgrid . Human Technicians, administrators, contractors, any user with the system or network acce ss Attacker gain s real credentials fro m a legitimate user an d can then access normally restricted systems. Insider threa t – a legitimate u ser exploits their ac cess to cause damag e Unwanted island ing Dispatch strategy caus es economics losses in operation s. Unwanted o utages For microgr ids with advanced contro ls an d analytics cap abilities, main taining cyb er -reliability is a matter of concer n as well. The more complex the control algorithm, the higher the risk associated with havin g unfo reseen/blinding scenarios making it behav e in an unintended manner. Moreover, the higher the sophistication of the so ftware stack, the greater the risk of injecting unintende d bugs wh ile dev eloping the stack f urther. Since these challenges ar e no t imposed by an ex ternal entity, they are not categorized a s threats against wh ich resilience solution s should be bu ilt in the microgrid. But th ey do p ose a ch allenge for maintaining the reliability of microgrid, which is a significant aspect as well. C. Communication s Failure Th reats The modern g rid is envisioned to b e highly integrated with multidirectional data ex change a nd information communication between all its p arts. The vision is co nsistent with m icro grids as well for deploying a more active and responsive infrastructure for faster demand r espon se an d more exhau stive energy management capab ilities. It is indispensabl e for a n intelligen t microgr id to require a dependenc e on communication network s. On th e other hand, using sophisticated co mmunicatio n schema make s the micr ogrid vulnerab le, due to the increased risk of communication failure, along with the micro grid’s growing depend ence on electric systems and public communication networks. An example of the severity of impact that a communication failure ca n have is 2013 Northeast blackout in the United States an d Canada. It was primarily caused by commun ication failure when a small tran smission disturbance failed to send out the alar m , making the o perators unaware of the need to redistribute power flo w. This initial trigger co uld have been controlled without causing a widespread o utage; h owever, because of the delay in r eacting to the over loaded transmission lines, a m anageable lo cal blackout cascaded into grid failure in the entire No rth east, leaving m ost of the region witho ut access to power for two days to a we ek [45]. In the case of microgrid s, if the communication failure happens d uring grid -connected operation, the microgrid’s co ntroller will lose access to grid-side information , resu lting i n its inability to maintain the commanded po wer and p ower-factor at the point- of - interconnec tion. The microgrid should b e able to maintain stable operations and stop feeding the power to the grid if it has been doing demand management before th e communication failure. In worst case scenarios, the microgrid needs to h ave the ability to island itself safely. Co mmunication failur e intern al to th e micro grid is more of a reliability co ncern, as it is not impos ed b y an external en tity. If not addressed appropriately, it ca n adver sely im pact the operation of the micro grid and damage the assets if left unattended fo r longer durations esp ecially when o perating in islanded mode . D. Threats Due to Interdepen dencies Between Variou s Systems Electricity, oil, natural gas, tra nsportation , telecomm unications, and water systems are all i nterdep endent critical infrastructure (CI) systems. The operations of power sy stems are in constant exchange with o ther CI systems. On one level, electric power systems support other CI systems in th eir o perations , wherea s, on the other level, elec tric po wer system s depend on other CI systems to b e able to op erate. The interdep endencies between all CI sectors is thorough ly mapped in [6 ]. Power systems pro vide electricity to: • Natural gas system s for op erating their control sy stems and storage • Oil industry f or pumping, control systems, an d lift stations • Telecom systems fo r switches and sig naling • Water infrastructu re for pur ification and pumping . On the reverse side, other CI systems prov ide the following material and services to facilitate utility grid and microgrid operatio ns: • Natural gas an d oil industries pro vide fuel for generators ; • Transportatio n industry tran sports operators an d sometimes diesel f uel to power p lants and generators ; • Telecom systems p rovide a communication layer and SCADA systems for cy ber layers ; and • Water is required for construction and infrastructure recovery o f power plants, as well as o perations including cooling, productions, and so on [4 6]. 12 These tightly inter twined in terdependencies between other CI systems and electric p ower systems increase their vulner abilitie s by exposing them to second -order and thir d-order threats. Microgrids are also equ ally, if not more, vuln erable to the threats p osed b y such interdep endencies. Microg rids operate as integrated energ y systems where gas, wate r, distributed g eneration, and utility grid supplies are coordinated to supply var ious kinds of loads , as depicted in Figure 4 . The electric energy supp ly ( shown in gr een) is partly d ependent on the electric energ y supp lied from the CHP unit; the CHP unit, in turn, relies on natur al gas and water inpu ts . Similarly, to serv e the heating load , the boiler needs bo th water an d natural gas. Sup ply of the water load requires both electricity (to operate the pump) and water itself. Ther efore, interrup tion in the supply of any of the se critical utilities (electricity, n atural gas, water, or heat) ca n negatively impact the ab ility o f the in tegrated en ergy system to meet loads and affect the operational econo my of the microgr id. The threats, vulnerabilities, and potential impacts of different CI system failure s on the microgrid are described in Table 5. The risk score methodology for this kind of threat is similar to ph ysical threat risk sco re calculation method d escribed in section III.C.1) , where the r isk factor is a mu ltiplication of the probability of threat, prob ability of vulnerability, and impact of vulnerability. Figure 4 Microgrid operation as an integrated energy system 3 Table 5. CI Systems Interdependencies Risk Analysis Threat Vulnerability Potential Imp act Natural gas sup ply interruption No input fuel f or heating system -Heating load can not be served -If microgrid also has electric h eating system pair ed with gas heating then undue load o n electric heating system, which m ay cause componen t failures. Water supply in terruption CHP and boiler need water, the operation of which can be halted -Not enough energy production to sup p ly electric and heating load Utility grid o utage No external electricity supply source -If microgrid is not design ed to sustain a 10 0% load in isolated-o perational mode , then unintended load shedding . - If microgr id is not designed for bump - less transfer or black star ts, then powering it up with out grid- supply is no t possible 3 Diagram adapted from [6]. 13 V. C A SE STUDY : EXAMPLE RI SK SCORE CAL CULATION In this section, we f irst in troduce an example microgrid. The ph ysical and cyber risk factors are then calculated in su bsecti ons A and B. Since a microgr id is inher ently a cyber-physical system [47] [48], it is important to integrate the risk assessments of these two layers to holistically evalu ate microgrid resilience. The combined risk assessment results provide an effective way to prioritize which mitigation measures will have maximum impact on increasing th e resilience of the microg rid. A. Physical To illustrate an example o f quantifying a risk facto r , Table 6 lists the three attribu tes of risk factor ca lculation . Th e test microgr id is as sumed to b e located o n Flor ida’s coast , an d a hurricane is the threa t b eing asses sed. Th e probability of a hurricane hitting the location is 90%, based on historic and projected climate data. If a hurrican e does hit the site, there is a 70 % prob ability that the generator s (includin g ground-mou nted so lar and electric battery stor age ) wi ll be flooded, based o n expected storm surg e lev els at the g enerator locations. If the generator s are flooded, the expected impact is severe (scored a 9 o ut of 10), because th e flo od ed generator s will not function and the m icrogrid will not be able to serv e critical loads. The total risk score is 9 x 7 x 9 = 5 67 . Th is is a high-risk scen ario, as bo th the likelihood of the hurricane and the potential dam age is high. Table 6. Physical Threat and Vulnerability Scores Category Score Reason Probability o f threat 9 90% likelihoo d of hurricane occurrin g in F lorida Probability o f vulnerability occurring (g iven the threat) 7 70% probab ility that generators (solar panels an d battery) will be flooded with muddy waters if hurr icane occurs Impact of vu lnerability 9 90% impact ( because flooded gener ators will almost certain ly cause the microgrid to no longer b e able to serve critical load s as well a s the generator th emselves will be damaged and will need repair/replacem ent based on th e degree of damage ) Risk Score: 9 x 7 x 9 = 567 B. Cyber To illustrate one method of quan tifying the severity of a vulnerab ility, we will look at a (simplified) example system shown in Figure 5 . The system con sists of a single inverter-based generatio n u nit that delivers power to sever al load s. The lo ads co ntain sensors, which report input voltage an d fr equency information b ack to the supervisory controller, wh ich in turn provides feed back to the inverter controls of the generatio n unit so that it can adjust its output to ensure the correct voltag e and frequency arrive at the loads. For this scen ario, we assume the sensors co mmunicate to the controller via an unencry pted ZigBee link . 4 Using the DREAD model ( explained in section III.C.2), we can q uantify the severity of various attacks ag ainst this system. Th e vulnerability we will specifically exam ine is the unencrypted wireless link . Figure 5. Test microgrid for cyber risk assessment example For the first attack (Tab le 7) , the attac ker is assum ed to b e passively observing the network. Because vo ltage an d f requency in electric grids are standardized, it wou ld be simple f or an eavesdropper to g uess the nature of the communication s. Ha ving don e this, 4 This examp le system is deliberately un secure to make scoring simple. 14 the eavesdropper can then extract the detailed frequency a nd voltage information, and learn the exact d ata f ormat being us ed (which is n ot necessarily damaging by itself but enables attack number three below). Eavesdropping of th is n ature d oes require some equipmen t, b ut all the r equired equipment is readily available at low cost. The data gathering itself can be performed by an unauthenticated user, but this is partially offset by the significant knowledge required to a nalyze the data. If t he attacker i s assumed to be placed nea r the supervisory contro ller’s receiver, then all loads’ data is compromised. Table 7. Cyber Threat Score: Data-Sniffing Attack (Attack 1 — Sniffing) Category Score Reason Damage 2 The attacker receives detailed informatio n about voltage and frequency, as well as the data format. Some usage inf ormation could be extrapolated. No direct harm is done to in frastructure. Reproducib ility 5 Some tools req uired, but all required tools are readily available at low co st . Exploitability 5 Can be don e by an unauth enticated user, but req uires significant kn owledge to use re sults. Affected Users 10 All loads’ power consumption com promised . Discoverability 10 By co nvention, discoverability is norm ally assumed to be 10 for any critical system, b ased on the assumption that if you can discover the vulnerability, so can someo ne else. Risk Score: 2+5 +5+10+10 / 5 = 6.4 This is a moderate threat, but since the dam age potential is very low and the knowledge required to perform the attack is hig h, th is is unlikely to b e a high priority. In the second attack (Table 8), the attacker perfo rms a DoS attack against the wireless netwo rk by jamming the s uperviso ry controller’s receiver. This ca uses a co mplete loss of v isibility f o r the con troller and reduces the ability of the controller to handle unforeseen events, but does n ot d irectly cause any permanent dam age to the system (It is assumed for th is example that the fe edback provided by the lo ads is n ot critical to system stability under n ormal co nditions.) . Th is attack can be ca rried o ut very reliably but requires either specialized hardware or a readily available device specifically prog rammed for the task. All technical knowle dge required to perform th is attack is available o n the internet, and n o authen tication is required. Exploitab ility is downgraded from 10 to 7 because of the need to place har dware near the target. Assuming the stability of the system is affected at all, all lo ad s are affected. With jam ming in particular, t h e vulnerability of wireless sy stems is widely k nown — ev en appearing in internet comics [49]. Table 8. Cyber Threat Score: DoS Attack (Attack 2 — Signal Jamming) Category Score Reason Damage 7 Complete loss of visibility, b ut n o (direct) permanent damage (assuming system can still operate in an open loop configuration) . Reproducib ility 5 A compatible device on the same ch annel can trivially and reliably inject gar bage data . Exploitability 7 Minimal kno wledge required, no au thentication . Affected Users 10 All loads ’ p ower supply stability decreased . Discoverability 10 By co nvention, discoverability is norm ally assumed to be 10 for any critical system, b ased on the assumptio n that if you can discover the vulnerability, so can someone else . Risk Score: 7+5 +7+10+10 / 5 = 7.8 This is a much more severe threat than just eavesdropp ing. The attack is r elatively easy to carry out and requires minimal k nowledge of the actual system. It a lso has a much higher impact. For Attack 3 (Table 9), t he attacker is assumed to have already performed Attack 1 and has detailed knowledg e of the loads and the general stability of the network. By sen ding inaccurate frequency and voltage feedback to the controller, the attac ker can cau se the controller to change its b ehavior in such a way as to damage lo ads or cause the generator to shut down. Th is attack is fairl y well understood but requires sig nificant and complex tooling to fun ction beyond a simple denial of service attack. While no authentication is req uired to perf orm the attac k, advanced skills and specific knowledge o f the exac t system ar e required to accomplish th e attack. If successful, the attack affects all users of the system, as well as the system itself. T he vulnerability o f the system is assumed to be known, so d iscoverability is assumed to be 10. Table 9. Cyber Threat Score: Tampering, Data Injection Attack (Attack 3 — Incorrect Frequency/Voltage Data) Category Score Reason Damage 10 Incorrect frequen cy or voltage can cause to tal shutdown or perman ently damage loads . Reproducib ility 3 This attack is well-u nderstood but r equires significan t and complex tooling to function beyond a simple DoS attack. 15 Exploitability 3 No authen tication required, but advance d skills required to accomplish . Affected Users 10 All loads and generation node poten tially damaged . Discoverability 10 By co nventio n, disco verability is normally assum ed to be 10 fo r any known vulnerability in a critical system, based on the assum ption that if you can discover the vuln erability, so can someone else . Risk Score: 10+3 +3+10+10 / 5 = 7.2 This th reat is also m oderate to h igh severity because, while it potentially has ca tastrophic ef fects, it has a low probability of functioning, and requires significant resour ces to accomplish. Since all three of these th reats target the same vulnerability — the un encrypted wir eless link — we assign the highest sco re to the discoverability attribute (which is equivalen t to probability of vulner ability attribute, as explained in the end of Section II I.C.2). Figure 6 shows a radar plot of the three threats and th eir corresponding five attr ibute sco res based on the DREAD mod el. Figure 6 DREAD Scores for 3 Cyber Threat Examples C. Overall Risk Facto r Calculatio n : Cyber-Ph ysical System To conduct a comprehensive risk analysis for making design decisions geared toward resilience, this section pr esents a n overall r isk factor calculatio n fo r the m icrogrid in our use -case ( a detail ed description ca n be found in sub-sections A and B) . Tab le 10 sho ws example risk scores (function of pr obability o f threat, p robability of vulnerability, and impact of v ulnerability) f or variou s combination s o f input threats and vu lnerabilities for the test microgrid assumed in sub-section A . For the cy ber threats, the three attributes of the risk score are calculated based on the analogy between the DREAD mo del an d risk assessment methodolog y for physical threa ts, which is covered in section III.C . Table 10 . Example Risk Score Calculation for Example Test Site 5 Threat Type of Threat Vulnerability Probability of Threat Probability of Vulnerability Impact of Vulnerability Risk Score Higher storm surge due to hurricanes (storm) Physical Generators, solar panels, and battery are at ground lev el in areas prone to floodin g 9 7 9 567 Increased numb er of days with thunderstorms/lightn ing (lightning) Physical Lack of acce ssible spare parts 8 8 7 448 Increase in co astal land loss Physical Critical microgrid infrastructur e near coast 7 5 5 175 5 These numbers are approximate and are only intended for showing examples, not to be used as risk factor s for actual microgrid design. 0 2 4 6 8 10 Damage Potential Reproducibility Exploitability Affected Users Discoverability Sniffing Denial of Service (DoS) Tampering 16 (land-lo ss) Increase in m agnitude of hottest annual temperature (heatwave) Physical Lack of redundan t backup systems 6 4 6 144 Increase in the number of tornados (tornados) Physical Equipmen t is outside in an unprotecte d area 4 3 2 24 Earthquake Physical Lack of staff trained to operate the microgrid 2 4 8 64 Data sniffing Cyber Unencryp ted wireless connection 5 10 6 300 DoS Cyber Unencryp ted wireless connection 6 10 8 480 Data Tamper ing Cyber Unencryp ted/unauthenti cated wireless connection 3 10 10 300 Figure 7 shows the r isk scores in a 3D bar plot where t he th reat probability is depicted by th e colors of the b ars (also shown in upper left legend). The data set is fou r-dimensional where the r isk sco re (the dependent variable) is a fun ction of the probability of the threat, probability of v ulnerability, and imp act of vulnerability ( th ree independent variables). To visualize the information in three dimensions, the probab ility of threat v ariable is qua litatively shown by the colors o f bars ; h owever, the plot is effectively showing the relative d ifference between the r isk score for different ki nd of physical an d cyber threats . Based on the calculated r isk factors for different kind s of threats and their impac t on the microgr id, the mitigation strategy sho uld prioritize the f looding protection (incr easing elevation of generators ) and storm preparedness ( keepin g inven tory of spare parts ) measures over the seismic design to make it resilient against hurrican es. Also, for this test microgrid system, the cyber risks are relatively higher. Therefore, the mitigation strategy should also make it a prio rity to build software features capab le of d e fen ding against such th reats. Figure 7 Risk scores for various kind of threats to example microgrid 17 VI. M I TIGATION STRATEGI ES After un derstanding the risks, the next step is to identify mitigation options th at reduce th e probability or imp act of each vulnerab ility to respectiv e threats. Each mitigation strategy is then evaluated b ased on its po tential to reduce the risks ag ainst its complexity and cost o f its adoption. When developin g mitigation mea sures, actions and measures that reduce risk in a ran ge of way s should be co nsidered . Table 11 delineates a useful way of assessing the stren gth of resilient microgrids through five attr ibutes (also called 5R) and prov ides examples of how these attrib utes increase resilien ce in differ ent ways . Th is 5R approach o f classification does not encompass various phases of resilience modeling, as depicted in Figure 1 , nor does it provide precise actionable mitigation strategies targeted for the pre-disaster and post-disaster p hase s’ operations and r ecovery, as depicted in Figure 8. Table 11 . Resilience Characteristics and Example Mitigations 6 Attribute Qualities Examples Robustness • Physically secure • Cyber secure • Hardened infrastructure • Performance monitoring • Risk Management Framework (RMF) 7 -compliant control systems • Active vs. passive performance monitoring • Maintenance schedule and checklist • Physically enclose microgrid equipment inside mechanical rooms to protect from elements and unauthorized persons; • Seismic design in earthquake zones; elevated platforms in floodplains • Cyber-secure access to controls and networks. Redundancy • Eliminate single points of failure • Modular units of accounting for maintenance and downtime • Redundant lines (power and comm) and equipment • Backup staff (microgrid operator). Resourcefulness • Available power generation • Energy storage • Diversified generation sources including generators, renewable energy, and storage; • Load shedding to prioritize more critical loa ds • Uninterruptable power supply (UPS). Response • Automated • Self-healing • Forecasting/threat assessment • Performance indicators • Training and exercises • Maintenance staff training and exercise • Data collection and predictive analytics • Fault tolerance (failover or failsafe) • Inclement weather response plans • Smart control systems • Documented procedures available during an emergency. Recovery • Standardized components • Spare parts inventory • Damage Assessment • Prioritization of re-powering • Maintain spare parts inventory, preferably using commercial off-the- shelf parts; • Utility coordination and agreements • Black start sequence. 6 Adapted from Air Force Civil Engineer Center. 7 Risk Management Framework (RMF) [50] 18 Figure 8. Comparison of resilient and traditional microgrid operations through disruptive eve nt 8 Therefore, in this work, we p ropose a comprehensive mitigation strategy encompassing both infrastru ctural and o peration al measures to make the microgrid resilient during pre- , d uring-, and post- disaster p hases. As illu strated in Figure 9 , mitigatio n strategies can be broadly classified in to pre-d isaster planning , during-disaster m easures, and post- disaster recovery and restoration. The p re -d isaster planning phase includ es asse ssment of threa ts, associate d vulnerab ility , an d implemen tation of system -harden ing measures (both physical hardening as well as cyber strengthen ing) to m inimize th e prob ability o f d amage to th e microgr id. Preparation can also include restocking supplies, relocating vehicles, etc. just prior to extreme wea ther or b ased on high threat level. Actions during -disaster could inclu de d eliberate de -energization, isolation o f dam aged lines, and status ch ecks o f esse ntial staff (recall alternate individuals if p rimary is u navailable) . Post-disaster recovery mitigation strategies focus on speedy recovery actions a nd restoration of energy sup ply. The following two sections discuss these mitig ation m easures in detail. 8 Diagram adapted from [6]. 19 Figure 9. Infrastructure and operational mitigation strategies for a resilient microgrid A. Designing and Building Resilient Microgrids In the plannin g phase of microgrid design (depicte d by the Original Operati onal M ode section of Figure 8), a set of mitigatio n measures must be considere d for making microgrids resilient during a disruptive eve nt (i.e., increasing micro grids’ robust ness or resista nce and maintaining supply) . Therefore, these mitigation measures are aimed at minimizi ng the damage and a ttempti ng to keep the supply (at le ast the critica l loads) uninterrupt ed during the event. The m easur es primarily make physical assets and contro ls software less vulner able to at tacks and are categorize d as sy stem-ha rdening mitigatio n options, whereas day- to -day o peratio nal procedur es and on- site staff’s competen ce in operati ng the micr ogrid in resp onse to disrupt ive events come under operational strategies . Coo rdination o f both S ystem Hardening and Operational Str ategies is required for the measure where strategic load shedding c apabilities are desig ned and constr ucted. The ele ctric circ uitry of the mi crogrid gri d should c onsider modul ar and/or parallel design f or enabli ng strate gic-load sheddi ng. 1) S ystem Hardening System-hard ening methodo logies are as follo ws: • Diversifying the generatio n sources, in cluding generator s, renewable energy, and storage. For micro grids located on islands, diversification of gener ation resources with r enewable energy also may decrease the co st of oper ation ; generator fuel can be costly in remote p laces, pr imarily d ue to cost and r isk associated with its transpor tation over long distances. For microgrids serving critical serv ices, such as defense bases and financial institutions , incorporating a UPS is another way of increasing resourcefulness. • Protecting assets fro m se ve re weather disrup tions b y implementing system-hardening measures , such as b olting down th e equipmen t (to p rotect fro m strong winds), elevating the equipment ab ove the floodplain, or enclosing equipment in side mechanical r ooms (to protect from b ad actor or other disruptive elements). • Designing cr itical electrical circuits to avoid any sing le point of failu re and modularizing the connectio ns to acco unt for the maintenance and downtime of the assets . • For a certain category of threats ( i.e., unusual fault cu rrent from the utility grid side), the comp onent sho uld be design ed to operate under a range of current an d voltage conditions. • Installing a co ntrol system that is RMF compliant [5 0] can harden or strengthen the microgrid to improve infor mation security and resilience against cyberattac k s. 20 • The cyber layer of the microgrid can be m ade more resilient to DoS and loss of c ommu nication by increasing the sophistication of the control systems and analytics software implem ented on top of the control systems. o In the event o f loss of communication with the utility, switch to island mode and a lert user; o In the event o f total communication loss (i.e. , between microgrid contr ol system and SCADA), all n odes should hav e a default b ehavior. • The cyb er layer can be hardened against DoS and intrusion by ad ding a firewall between the microgrid control s ystem and the internet • Looking bac k at the threat assessment examp les presented previo usly , each attack surface can be hardened to reduce th e ease of exp loitation. o Wired connec tions can be buried or other wise made inacce ssible to attackers ; o Wireless links can b e made directional an d support multiple band s to reduce the impact o f jamming and interference; o Redundant ph ysical connections (wired, wireless, or both) r educes chances of total lo ss of communication ; o All commun ications can be encryp ted and signed to mitigate eavesdr opping, tampering, and sp oofing ; o Restricting access to ph ysical infrastructu re reduces attack surface ; and o Training users to follow strong o perational security practices reduces op portunities f or attackers to ob tain legitimate credentials. 2) Op erational Strategies Day - to -d ay operational strategies th at can mak e microgrid s more resilient inclu de: • Performan ce monitoring of the microg rid assets (both hardware and software platform s) for preventive mainten ance of the assets. • Predictive an d condition-b ased maintenan ce using data analytics and p redictive modeling can h elp , as this process helps with increasing the reliability of co mponents ; fault-prone equipment is flagg ed with pr edictive maintenance and can be repaired or replaced; • A maintenan ce schedule (with check list) must be followed ; this schedule can be assisted by performance mon itoring and predictive maintenance software ; • Maintenance staff must be trained and prepared to respond to extreme events and be able to operate the microgrid in manual mode if th e need arise s; • When weather conditions deteriorate ( or extreme weather alerts are relea sed), r esponse plans must be in p lace that can shut down the vuln erable elements and y et sustain critical load s (e.g ., with the help of UPS) ; and • Documen ting procedures for mainten ance and response d uring the disruptive event is very important. Also, equally importan t is the easy accessibility o f the documents (fo r example , hard co pies instead of an electro nic cop y). B. Response Du ring-Disaster Even t These mitigation strategies a pply to the section depicted b y the Operation al Resilience section of Figure 8 . For enabling the microgrid to oper ate during a disruptive event (for the cases when the disrup tive even is predictable , such as windstorm alert or flood warnin g) to serve cr itical loads (at the minimum ), the following operation al steps can be taken : • Demand- side resources: load-shedding strategy in place that lets the controller turn off the non -critical loads during the event and switch on the UPS resources; • Switch UPS on : switching UPS on sho uld be a semi- automated p rocess that k icks off as s oon as dem and -side measu res ar e activated; • Generation rescheduling: for grid-connected microgrids, the on-site generation can be rescheduled to dispatch at a later point in time, as the utility grid o utage is a high -probable threat after th e disaster has hit ; • Network reconfiguration : if the electric circuitry design allows, the network can be reconfigured to connect generation and storage with cr itical loads o nly (as opposed to normal operations , where all critical and non -critical loads ar e connected), for avoiding the situation where the radial nature of cables running through critical and non -critical cause the critical load to be shed becau se of a fault in the non -critical load pathway ; and • Optimal param eter settings of dro op- controlled units ( i.e., generato rs): the par ameters should be set to sup port c onserv ative voltage regulation to help survive the event . In other words, th e r elaxed parameter limits will allow low-amplitud e voltage fluctuations with out tripped the micr ogrid. C. Post-Disaster Readin ess Once th e disruptive event has p assed, the characteristic of a resilient system is to be ab le to respond to the damage proactively an d recover faster. Th is requires the site to have sufficien t redundancy , as we ll as operational plans for rapid restoration. 1) S ystem Restoration For rapid sy stem restoration , the following measu res can be taken : 21 • Maintain a spar e parts inventory ; • As much as p ossible, use commercial off -the-shelf parts an d equipm ent for con structing the microgr id so that b uying spare parts is not a ch allenge; and • Follow mod ularized circuit design such that a subset o f assets can be brought on line without replacing a ll damaged p arts. 2) Op erational p lan • Staff must be trained for executing b lack starts, and the process should also be do cumented well ; • In the case o f electric system f aults, the assets must be equipped with a p rocess for con trolled co ol -down for safe recover y ; and • For grid -connected microgrids, the resy nchronization of the microgrid with the utility grid must be coordinated. D. Deployment Considerations Though a range of mitigation strategies are available and technically feasible, there are some challenges that make it difficu lt to justify the capital investment i n implementing these strategies. Moreover, inadequate infor mation -sharing processes between utility and microgrid own ers can hamper th e microgr id’s cyber lay er f rom def ending and mitigati ng certain types of cyber th reats, due to lack of visibility into the utility’s state . In real-life micr ogrid deployment scen arios, resources and budget are largely, if not always, con strained. In suc h cases, it is very important to prioritize the mit igat ion measures presented in this section . The criterion of prioritization includes: 1) r isk redu ction capability; 2 ) d ifficulty of adaption and/o r dep loyment; and 3) c apital investment cost . As an example, if a microgrid is located in a woodlan d in a geogr aphically dry area ( e.g., California) and is installed f or a military base, then the most effec tive mitigation strategies would b e: • Physical hardening: keeping the k ey assets, including generators, fuel -tanks, an d batteries, in a m echanical ro om (to p revent direct sh ooting), which h as its walls coated by a fire-resistant material (to p reven t wildfires fro m setting assets, including a flammable liqu id tank, on fire). Seismic design o f the mechanical roo m for earthquake prevent ion . • Cyber hardening: being a highly suscep tible lo cation , the military microg rid’s cy ber layer should be hardened ag ainst confiden tiality and integrity attacks by building software stacks equipped to defend against such attacks, or , at the very least, id entify t he attac ks befo re larger d amage is done. The h ardwired communication lines s hould b e grounded with water resistant covering s. In the microgrid design and deplo yment process, after the risk -analysis, identification and prioritization of mitigatio n strategies, then the next step s are: 1) developmen t of an action p lan; 2) implementatio n or deployment o f the action plan ; 3 ) validation (i.e., not waiting t o test the e ffectiveness of mitigation measures for the first time when a d isaster hits); and 4) re -assessing the plan based on the validation test results. As described in Section II.B, building resilient m icrogrids is an iterative process ( Figure 1). The above four steps must be continually re -assessed period ically to ensur e the resilience of the microgrid with ch anging external circumstances. VII. S UMMARY AND OUTLOOK As th e risks associate d natural an d human -induced threats co ntinue to gro w, power system resilience has b ecome an imp ortant requirement for ensuring th e continued supply of electricity. Microgrid s are emerging as an effectiv e solutions for supporting power system resilience wh ile prov iding oppor tunities to integ rate distribu ted renewab le energy generatio n efficiently into the utility grid during normal operations . The r esilience of microgrids ag ainst physical, cyber, and communications threats must b e ensured by proactively addressing th ese threats in a ho listic way . This work is fo cused on dev eloping a quantitativ e, holistic ap proach to id entify threats to a m icrogrid, determine vulnerabilities associated with iden tified th reats, an d emp loy m itigation strategies to ensure resilient perfo rmance of the microgrid in grid - connected and islanded modes of operation . Physical threa ts to which microgr ids are typically vulnerable includ e n atural hazards, changing climate, and h uman-induce d attacks. Commu nications threat s pertain to an op erating conditio n when the com munication between microgrid and utility gr id o r with in a microgrid is u nintentionally broken. Threats posed by cyberattack s can range from unintended islan ding to t riggering out- of -phase r eclosing in a microgrid to dam age the rotating machines . Due to the highly interdependen t nature of Critical Infrastructur e ( CI ) systems, there are threat s posed to the microgrid operation fro m event s including interruption in n atural gas and/or water supply . The discussion o f in terdependen cies between CI systems and their impac t on resilience modelin g of microgrid is also presented. The q uantitative th reat modelin g approach is pr esented to calcu late the risk factor. This paper discusses var ious mitigation strateg ies are proposed for pre -, during-, and after-disaster recovery modes. The proposed mitigation strategies include s ystem hardening and oper ational ef fectiveness measures. Mitigation strateg ies are also classified to assist the enh ancement of different attributes o f the microgrid , including ro bustness, redundancy, r esourcefulness, respon se, and recovery. Practical consider ation in pr ioritizing the mitigation strategic most im pactful fo r a microg rid in a giv en situation are also discussed with an example. 22 The future work will includ e the development of metrics to quantify the resilience of microgrids to various threats. By quantifying the resilience of d ifferent tactics, d ecision -maker s will be able to assess th e economic feasibility of technology and operational options and to ans wer the question, ‘is the capital inv estment requ ired to build r esilient microgr id worth the ben efits reaped dur ing a probable d isruptive event in the fu ture? ’ . These cost-benefit an alyses will aide in th e develop ment of policies and p ractices to guiding m icrogrid developm ent and deployment. VIII. A CKNOWLEDG MENTS This wo rk was auth ored by th e National R enewable Energy Laborato ry (NREL) , o perated by Alliance for Sustainable Energy, LLC, for the U.S. Departmen t of Energy (DOE) under Contract No. DE -AC36-08GO28308. Th is work was supported by the Laboratory Directed Research and Develo pment (LDRD) Program at NREL. Au thors wish to thank Bob Wood an d Mau rice Mar tin (NREL) for providing u seful suggestions to r efine the m anuscript. The views expressed in the article do n ot n ecessarily repr esent the views of the DOE or the U.S. Government. The U.S. Go vernment retains and th e pu blisher, by accep ting th e article for publication, acknowledg es that the U.S. Government retains a nonexclusive, paid -up, irrevocable, wo rldwide license to p ublish or reproduce the published form of this work, or allow oth ers to do so, for U.S. Gov ernment purposes. IX. R EFERENCES [1] P. P. D. -. 2 1, "Critical Infrastructure Security and Resilience," T he While House - Office of the Press secretary , Washington DC, 20 13. [2] Executive Of fice of the President, "Eco nomic Benefits of Increasing Electric Grid Resilience to Weather Outag es," 2013. [3] Z. Li, M. Shah idehpour, F. Aminifar, A. Alabdulwahab and Y. Al -Turki, "Networked Microgrids for Enhancing the Power System Resilience," Proceeding s of IEEE, vol. 105, no. 7, pp. 1289 - 1310, 2017. [4] National Academ ies of Sciences, Engin eering, and Medicine, "Chap ter 3 The Many Causes of Grid Failure," in Enhancing the Resilience of th e Nation's Electricity System , Washing ton, DC: The National Academ ies Press, 2017. [5] U.S. Departmen t of Energy, "E lectric Disturbance Events (OE -417) Annu al Summaries," [Online]. Av ailable: https://www.oe.netl.d oe.gov/OE41 7_annual_summar y.aspx. [Accessed 5 7 2019]. [6] Z. Bie, Y. Lin, G. Li and F. Li, "Battling the Extr eme: A Study on the Po wer System Resilience," Proceed ings of the IEEE, vol. 105, no. 7, 2 017. [7] P. W. Parfomak, "Physical Security Of The U.S. Power Gr id: High -Vo ltage Transformer Substations," Co ngressional Research Service, 2 014. [8] J. E. Sullivana an d D. Kamensky, "How cyber -attacks in Ukraine sh ow the vulnerab ility of the U.S. power grid," The Electricity Journal, vol. 30, pp. 30-35 , 2017. [9] DOE, "OE-4 17 Electric Emergency and Disturbance Repo rt - Calendar Year 2019," 2019. [10] F. H. Jufria, V. Widiputrab and J. Jung, "State - of -the-art review on po wer grid resilience to ex treme weather even ts: Definitions, fram eworks, quantitative assessment m ethodologies, an d enhancem ent strategies," Ap plied Energy, vol. 239, pp. 1049-1 065, 2019 . [11] W. Mackenzie, "US microgrid for ecast: H1 2019," 20 19. [12] B. M. Ayyub , "Systems Resilience for Multihazard Environments: Definition, Metr ics, and Valuation for Decision Making," Risk Analysis, v ol. 34, p. 340 – 3 55, 2013. [13] E. A. Ceseña, N . Good, A. L. Syrri an d P. Mancarella, "T echno -econom ic and business case assessment o f multi -energy microgrids with co-optimization of energy, reserve and reliability serv ices," Applied Energy, v ol. 210, pp. 896 -913, August 2018. [14] R. Eskandarp our, H. Lotfi and A. Kho daei, "Optimal microgrid placement for enhancing power system resilien ce in response to wea ther events," in North American Power S ymposium (NAPS) , Denver, CO, USA, 2016. [15] R. J. Campbell, "Weather -Related Power Outag es and Electric System Resiliency," Congressional Research Service, 2012 . [16] U.S. Departmen t of Energy, "The Poten tial Benefits of Distribu ted Generation an d Rate -Related I ssues That May Im pede Their Expansion ," U.S. Department of Energ y, 2007. [17] Y. Lin, Z. Bie an d A. Qiu, "A review of key strategies in realizing p ower system resilien ce," Glob al Energy Interco nnection Development a nd Cooperation Organ ization, vol. 1, no. 1, 201 8. [18] M. Ouyang an d L. Duenas -Osorio, "Mu lti-dimensional hur ricane resilience assessment of electric power systems," Structural Sa fety, vol. 48, pp. 15 -24, 2014. 23 [19] Y. Fang and G. Sansavini, "Optimizing p ower system investmen ts and resilience ag ainst attack s," Reliability Engin eering and System Safety, vol. 159, pp. 161-173 , 2017. [20] J. Wang, W. Zuo, L. Rhode -Barbarigo s, X. Lu, J. Wang and Y. Lin, "L iterature review on modelin g and simulation of energy infrastru ctures from a resilience perspec tive," Reliab ility Engineering and S ystem Safety, vol. 183, pp. 360 -373, 2019. [21] K. Alverbo, B. Nevhage and R. Erdeniz, "Methods for Risk Analsysis," Stock holm,Sweden , 2010. [22] N. J. Williams, P. Jaram illo and J. Tan eja, "An investmen t risk assessment of m icrogrid utilities for rural electrif ication using the stoch astic techno-econ omic microgrid model: A ca se study in Rwand a," Applied Energy, vol. 42, pp . 87-96, 2018. [23] H. A. Gabbar , R. Islam, M. U. Islam an d V. Trivedi, "Risk -based performance analysis of microg rid topology with distributed gen eration," Internation al Journal of E lectrical Power & Energy S ystems, vol. 43, no. 1 , pp. 1363 -1375, 2012. [24] X. Liu, M. Sha hidehpour, Y. Cao, L. Wu, W. Wei and X. Liu, "Micro grid Risk Analysis Considerin g the Impact o f Cyber Attacks on Solar PV and ESS Control System s," IEEE Transactions on Smart Grid, vol. 8, no. 3, pp. 1330-1 339, 2016. [25] M. Amirioun , F. Aminifar, L. H. and S. M., "Metrics and quantitative f ramework for assessing microgr id resilience against windstorms," International Journa l of Electrical Po wer & Energy Systems, vol. 104, pp. 716- 723, 2019. [26] M. H. Amiriou n, F. Aminifar and H. Lesani, "Resilience -Or iented Proac tive Management of Micr ogrids Against Windstorms," IE EE Transactions o n Power Systems, vol. 33, no . 4, pp. 4275 -4284, 2017. [27] M. H. Amiriou n, F. Aminifar and H. Lesani, "Towards Pro active Scheduling of Microgrids Against Extrem e Floods, " IEEE Transactions on Smart Grid, vol. 9, no. 4, pp. 3900 -3902, 2017. [28] M. H. Amiriou n, F. Aminifar and M. Shahidehpour, "Resilience -Promoting Proactive Scheduling Against Hurr icanes in Multiple Energ y Carrier Microgrids," IE EE Transactions on Power Systems, vol. 34, no. 3, pp . 2160 - 2168, 2019. [29] L. Liang, Y. Hou , D. J. Hill and S. Y. R. Hu i, "Enhancing Resilience of Microgrid s With Electric Springs," Liang Liang ; Yunhe Hou ; David J. Hill ; Shu Yuen Ron Hui, vol. 9, no. 3, p p. 2235- 2247, 2018. [30] J. Liu, X. Lu and J. Wang, "Resilience Analysis of DC Micr ogr ids Under Denial of Service Threats," IEEE Transactions on Power Systems, vol. 34, no. 4, pp . 3199 - 3208, 2019. [31] R. A. R. a. S. L. Billinton , Applied reliab ility assessment in electric power systems, New York: IEEE Press, 1991. [32] U. D. o. En ergy, "Staff Report to the Secretar y on Electricity Markets an d Reliability," 2 017. [33] J. Stamp, C. K. Veitch , J. Henr y, D. H. Har t and B. T. Richardson, "M icrogrid Cyber Security Referen ce Architectu re (V2)," Sand ia National Lab, 2015. [34] X. Zhong, L. Yu, R. Brooks and G. K. Ven ayagamoorthy, "Cyber Secu rity in smart DC microg rid operations," in 2015 IEEE First Intern ational Con ference on DC Microgrids (IC DCM) , Atlanta, GA, 2 015. [35] J. Moteff, "Risk Man agement and Critical Infrastructure Protectio n: Assessing, In tegrating, and Managing Threats, Vulnerabilities and Consequences," CRS Report for Congress, 2005. [36 ] ITI -RAMC, All-Hazards Ri sk and Resilience: Prio ritizing Critical Inf rastructures Using the RAMCAP Plus Appro ach, ASME Innov ative Technologies Institute, LLC, 2 009. [37] U. D. o. E. O. o. E. Assurance, "[DRAFT] Vu lnerability Ass essment Meth odology - Electric Power In frastructure," 200 2. [38] S. Hernan, S. Lambert, T. Ostwalk and A. Shostack, "Uncover Security Design Flaws Usin g The STRIDE Ap proach". [39] S. Hernan, S. Lambert, T. Ostwald and A. Shostack, "Uncover Security Design Flaw s Using The STRIDE Ap proach," MSDN Magazine, 2015. [40] "Security/OSSA-Metrics," Open Stack, [Online] . Available: https://wiki.openstack .org/wiki/Security/OSSA -Metrics. [Accessed 31 7 2019]. [41] J. S. Foster, E. Gjelde, W. R. Graham, R. J. Hermann, H. M. Kluepfel, R. L. Lawso n, G. K. Soper, L. L. Wood and J. B. Woodard, "Rep ort of the Commission to Assess the Threat to the United States from Electromagnetic Pulse (EMP) Attack," 2004. [42] K. Maize, "EMP: Th e Biggest Unadd ressed Threat to the Grid," P OWER, 2013 . [Online]. Available: https://www.powerm ag.com/emp -the-bigg est-unaddressed- threat- to -the-gr id/. [Accessed 29 12 2019]. [43] W. Wang and Z . Lu, "Cyber security in th e Smart Grid: Survey and ch allenges," Computer Networks, vol. 57, p. 1344 – 1371, 2013. [44] z. Li, M. Shah idehpour and F. Aminifar, "Cybersecurity in Distributed Po wer Systems," Proceedings of th e IEEe, vol. 105, no. 7, pp. 1367 -1388, 2017. 24 [45] R. A. Shuvro , Z. Wang, P. Das, M. R. Naeini an d M. M. Hayat, "M odeling impact of co mmunication networ k failures on power gr id reliability," in North American Power Symp osium (NAPS), 2017 IEEE , Morgantown, WV, 2017. [46] A. M. Carpenter , "Water conservat ion in coal-fired power plants," IEA CLEAN COAL CENTRE, 2 017. [47] A. Cagnano, E. D. Tuglie and P. Mancar ella, "Microgr ids: Overview and guid elines for practical implementation s and operation, " Applied Energy, vol. 2 58, 2019. [48] M. F. Zia, E. Elbou chikhi and M. Benbouzid , "Microgrids energy m anagement systems: A critical rev iew on method s, solutions, and prospects," A pplied Energy, vol. 222, pp. 1033 -1055, 2018. [49] x. (https://xkcd.co m/654/), "Internet com ic". [50] G. Locke and P. D. Gallagh er, "Guide for Applying the Risk Managemen t Framework to Federal Information Systems," National Institute o f Standards and Technology, U.S. Dep artment of Com merce, Gaithersburg, MD, 2010. [51] A. Bridam and A. Savoudi, "Hierarch ical Structure of Microgrids Control Sy stem," I EEE Transactions on Smart Grid, vol. 3, no. 4, pp. 1963 -1976, 2012. [52] O. Palizban an d K. Kauhaniemi, "Hierar chical Contro l Structure in Microgrid s with Distributed Gen e ration: Island and Grid-Conn ected Mode," Renewable and Sustainab le Energy Reviews, v ol. 44, pp. 797-813, 20 15. [53] D. T. Ton and M. A. Smith, The U.S. Depar tment of Energy's Microg rid Initiative, vo l. 25, The Electricity Jou rnal, 2012, pp. 84-94. [54] NBC DFW, "Oncor E xpects Vast Majority of Customers to Have Power Wed nesday Night," NBC DF W, Dallas - Fort Worth, 2019. [55] City of Dallas, "Imp ortant storm up date information," City of Dallas, Dallas, 2019. [56] J. D. Dickson an d H. Fournier, "73 0K re main without po wer after Michigan wind storm," The Detro it News, Detroit, 2 017. [57] U.S.-Canada Po wer System Outag e Task Force, "Fin al Report on the August 14, 2003 Blackout in the United States and Cananda: Causes and Recommend ations," 2004. [58] I. Maze-Roth stein, "U.S. microgrid forecast: H1 2019 - Ou tlook for sustained growth, " Wood Mackenzie, 2019 . [59] S. Y. Hui, C. K. Lee and F. F. Wu, "Electr ic Springs — A New Smart Grid Tech nology," IEEE Transactions on Smart Grid, vol. 3, no. 3, pp. 1552-1561 , 2012. [60] R. Munroe, "xkcd: Nachos," 26 10 2009. [Online]. Availab le: https://xkcd.com/654/.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment