An Image Identification Scheme of Encrypted JPEG Images for Privacy-Preserving Photo Sharing Services
We propose an image identification scheme for double-compressed encrypted JPEG images that aims to identify encrypted JPEG images that are generated from an original JPEG image. To store images without any visual sensitive information on photo sharin…
Authors: Kenta Iida, Hitoshi Kiya
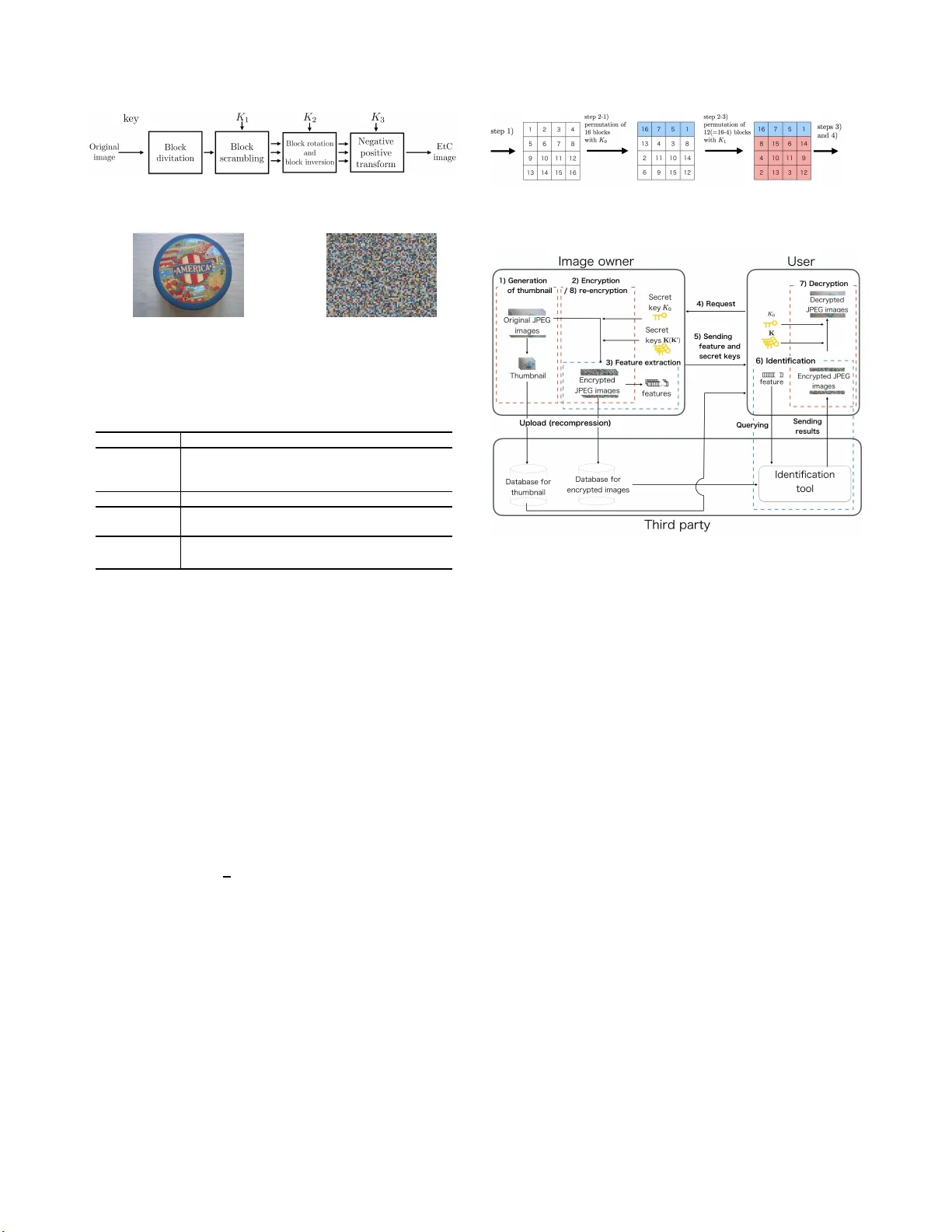
AN IMA GE IDENTIFICA TION SCHEME OF ENCR YPTED JPEG IMA GES FOR PRIV A CY -PRESER VING PHO T O SHARING S ER VICES K enta Iida and Hitoshi Kiya T o kyo Metropolitan Univ ersity , Asahigaoka, Hi no-shi, T okyo, Japan ABSTRA CT W e propo se an image identification scheme for double-compressed encrypted JPEG images that aims to identify encrypted JPE G images that are generated from an original JPEG image. T o store images without any visual sensitive information on photo sharing services, encrypted JPEG i mages are generated by using a block-scrambling- based encryption method that has been propo sed for E ncryption- then-Compression systems wit h JPEG compression. In addition, feature vectors robust against JP EG compression are extracted fr om encrypted JPEG images. The use of the image encryption and feature vectors allo ws us to identify encrypted images recompressed multi- ple times. Mo reov er , the proposed scheme is designed to identify images re-encrypted wit h different ke ys. The results of a simulation sho w that the i dentification performance of the scheme is high ev en when images are recompressed and re-encrypted. Index T erms — image identification, JPEG, Encryption-then- Compression system, priv acy-preserving 1. INTRODUCTION W ith the r apid gro wth of social networking services (SNSs) and cloud computing, photo sharing via various services has greatly in- creased. Generally , images are uploaded and stored in a compressed form to reduce the amount of data. In the uploading process for these SNSs, it is kno wn that service providers employ manipulation, such as recompression . In addition, most of the content includes sensi- tiv e information, such as personal data and copyrights. Thus, it is required t hat images on photo-sharing services be preve nted from leakage and unauthorized use by service providers. For priv acy-prese rving photo sharing on these services, t hree r e- quirements need to be satisfied: 1) protection of visual information, 2) tolerance for recompression after encryption, and 3) identifica- tion of encrypted images. In terms of requirement 1, a lot of studies on secure and efficient communications have been reported [1–15]. T o secure multimedia data, full encryption wi t h prov able security , such as RSA and AE S, is the most secure option. Howe ver , most schemes do not consider requirement 2, although requirement 3 is considered in sev eral schemes [13 –17] . As systems that satisfy both requirements 1 and 2, Encryption-then-Compression (EtC) systems hav e been dev eloped [6–10]. In this paper , we focus on a block- scrambling-based image encryption method that has been proposed for EtC systems. Regarding requirement 3, image retri e va l and t he identification of encrypted i mages hav e neve r been considered for EtC systems, although image i dentificati on and retriev al schemes that are robust against JPEG compression hav e been proposed for unencryp ted im- ages [18–22]. Ho wev er , the performance of these schemes is de- graded in the case of identification between encrypted images and correspondin g re-encrypted images, so, to satisfy all requirements, nov el image identification methods are required. Thus, we propose a nov el image identification scheme for en- crypted JPE G images comp ressed under variou s coding conditions. Image encryp tion is carried out by extending the method based on block-scrambling for EtC systems [6–10]. The extended method has steps for two-layer encryption. M oreov er, the feature vector used for identification is designed for images encrypted by the ex tended method. The use of t he t wo-layer encryption and features allows us t o i dentify re-encrypted images without re-calculating the fea- tures. Simulation results show that the proposed scheme has a high identification performance, ev en when images are recompressed and re-encrypted. 2. PRELIMINARIES 2.1. EtC image W e focus on EtC i mages which have been proposed for E ncryption- then-Compression (EtC) systems with JPE G compression [6–10]. EtC images have not only almost t he same compression performance as that of unencrypted images, but also enough robustness again v arious ciphertext-only attacks including jigsaw puzzle solver at- tacks [ 8]. The procedure of generating EtC images is conducted as belo w (see Figs. 1 and 2) [7]. 1) Di vide an image with X × Y pixels into non ove r-lapping 8 × 8 blocks. 2) Permute randomly M di vided blocks by using a random inte- ger secret key K 1 , where M = ⌊ X 8 ⌋ × ⌊ Y 8 ⌋ . 3) Rotate and in vert randomly each div ided block by using a ran- dom integer secret ke y K 2 . 4) Apply a negati ve-positi ve t ransform to each di vided block by using a random integer secret ke y K 3 . In this step, trans- formed pixel value at the position ( x , y ) in a block I np ( x, y ) is computed f r om the pixel value at the same position I ( x, y ) in a 8 × 8 block of an i mage applied step from 1 to 3 to by I np ( x, y ) = I ( x, y ) , b = 0 , 255 − I ( x, y ) , b = 1 , (1) where b is a random binary value generated by K 3 under the probability P ( b ) = 0 . 5 and 0 ≤ I ( x, y ) , I np ( x, y ) ≤ 255 . In this paper , images encrypted by using these steps are referred to “EtC images”. 2.2. Image Id entification for JPEG images Let us consider a situation in which there are t wo or more com- pressed images generated under different or t he same coding con- ditions. T hey originated from t he same image and were compressed Fig. 1 . Generation of EtC image (a) Original i mage (b) Encrypted image Fig. 2 . E xample of original image and encrypted image T able 1 . Notations used in this paper O i i th original JPEG image E ( j,k 0 ,k ) i i th encrypted JPEG image generated from O i with seeds k 0 and k and compressed j times (secret ke ys K 0 and K are generated from k 0 and k ) M number of 8 × 8 -blocks in image O i ( m ) DC coefficient of m th block in image O i ( 0 ≤ m < M ) E ( j,k 0 ,k ) i ( m ) DC coefficient of luminance in m t h block of image E ( j,k 0 ,k ) i ( 0 ≤ m < M ) under various coding conditions. W e refer to the identification of these images as “image identification. ” Note that the aim of the i m- age identification is not to retriev e visually similar images. The JPEG standard is the most widely used image compression standard. In the usual coding procedure, after color transformation from RGB space to YC b C r space and sub-samples C b and C r , an image is divided into non-ov erlapping consecuti ve 8 × 8-blocks. Al l pixel values in each block are shifted f r om [0,255] to [-128,127] by subtracting 128, and DCT is then applied to each block to obtain 8 × 8 DCT coef ficients. After that, the DCT coefficients are quantized, and the quantized coefficients are entropy-co ded. A DC coef ficient DC in each block is obtained by using the follo wing equation, where I ( x, y ) represents a pixel v alue at the po- sition ( x, y ) in a block. DC = 1 8 7 X x =0 7 X y =0 ( I ( x, y ) − 128) (2) The range of the DC coef ficients is [-1024,1016]. It has been re- ported that the features extracted from DC coef fi cients are effecti ve for recompression i n the con ventional schemes [18 , 19]. Therefore, the DC coefficients are used for the identification in this paper . 3. PROPOSED S CHEME In this section, a novel two-layer image encryption method and the proposed identification scheme are explained . The combination of them enables us to avoid the effects of not only recompression bu t also re-encryption. The notations used in the f ollo wing sections are sho wn in T ab. 1. Fig. 3 . Example of two-layer image encryption under M = 16 and N = 4 Fig. 4 . P riv acy-preserving photo-sharing 3.1. T wo-layer Image Encryption In the proposed scheme, the novel image encryption method, which is an extension of the method mentioned in Sec. 2.1 for the proposed identification scheme, is condu cted. The permutation process in step 2 is divided into two layers for identification. After dividing an im- age i nto 8 × 8 blocks, the following processes are performed, instead of st ep 2. 2-1) Permute randomly M divided blocks using a random integer secret key K 0 . 2-2) Select a positiv e integer value N . 2-3) Permute randomly the last M − N b locks using a random integer secret ke y K 1 again. After that, steps 3 and 4 are carried out. An example of the encryption process under M = 16 and N = 4 is sho wn in Fig. 3. It can be confirmed fr om F ig. 3 t hat t he first four blocks are not permuted in step 2-3. Thus, t he process in these steps does not change t he positions of the first N blocks under the same K 0 , e ven if K 1 is changed. This property will play an important role in the proposed identification scheme. 3.2. Over view of P h oto-sharing Services So that an image o wner shares JPEG images on an untrusted service without publishing the sensiti ve information of the original quality images, a scenario of t he proposed scheme is illustrated in Fig. 4. 1) An image o wner generates t humbnail JPEG images from original JPE G images, and the thumbnail images are then uploaded to a third party . 2) The image own er encrypts the original JPEG images with se- cret k eys K 0 and K = [ K 1 , K 2 , K 3 ] according to the two- layer image encryption. As shown in Fig. 3, the blocks of original JPEG images are permuted with the secret key K 0 , and encryption with K is t hen performed. After t hat, the compressed EtC images are uploaded to the third party . In this uploading process, these images may be recompressed. 3) The image o w ner extracts features from the encrypted JPEG images. The features are related to the uploaded thumbnail images. 4) A user selects a thumbnail image from those stored on the third party’ s storage, and then sends the selected images to the i mage owner . 5) The image own er sends the corresponding feature and the se- cret ke ys K 0 and K to the user . 6) The third party identifies the encrypted images correspondin g to the feature recei ved from the user, and sends the identified image to the user . 7) The user decrypts the encrypted image wi t h K 0 and K . 8) The i mage owner re-encrypts the identified image wit h K 0 and K ′ = [ K ′ 1 , K ′ 2 , K ′ 3 ] where K ′ 1 , K ′ 2 and K ′ 3 are differen t from K 1 , K 2 and K 3 . Thumbnail images are not tied to correspond ing encrypted images on the services because of the following two reasons. One is to pre vent j igsaw solver attacks done by using visual information of a thumbnail image, which a third party use to decrypt the correspond- ing encrypted image. The other is to preven t the unauthorized use of the user data. A third party makes it possib le to collect the data on users, such as their preferences, from a thumbnail image correspond- ing to an encrypted image. Therefore, identification using encrypted images without any visual sensitive information is required for the priv acy-preserv ing communications. It i s known that service providers usually employ manipulation such as recompression to uploaded images. The refore, recompres- sion is assumed in steps 1 and 2 of this scenario. The feature used in the proposed identification scheme is de- signed to identify images encrypted with the different ke y sets K and K ′ under the same K 0 . Thus, recalculation of features i s not needed, even when images are re-encrypted. 3.3. Pro posed Identification S cheme In the proposed identification scheme, the features extracted from the first N DC coefficients of Y compon ent in the encrypted images are used. The use of these features allow us to rob ustly i dentify images against recompression and re-encryption. Here, the feature extraction and the identification processes are explained. A. Feature extraction process In order to extract t he feature vector of E (1 ,k 0 ,k ) i , the following pro- cess is performed. (a) Set N . (b) Set n := 0 . (c) Extract the feature vector v E (1 ,k 0 ,k ) i from the n th DC coef fi - cient of Y component in E (1 ,k 0 ,k ) i as below . v E (1 ,k 0 ,k ) i ( n ) = | E (1 ,k 0 ,k ) i ( n ) | , (3) (d) Set n := n + 1 . If n < N , return to step (c). Otherwise, the image o wner halts the process for E (1 ,k 0 ,k ) i . In step (c), the feature is extracted from the absolute values of the DC coef fi cients of the Y component. It is kno wn that block rotation and in version in the DCT domain do not change the value of the DC coef ficient in each block [23]. In addition, from Eqs. (1) and (2), the absolute v alue of a DC coefficient is not greatly changed by a ne gative-po sitiv e transform. Thus, the use of DC coef ficients allows us to avoid not only the effect of recompression but also that of encryption. In the proposed scheme , when K 0 and N are not changed, the DC coef ficients t hat are mov ed to the first N blocks are the same as those of an i mage encrypted with different ke y sets. i.e., K 6 = K ′ . Therefore, it is exp ected that the absolute v alues of DC coef ficients in the first N blocks are close to those in the images encrypted with the different ke ys under t he same K 0 . This allows us to identify re-encrypted images wi thout re-calculating features. B. Id en tification process As shown in Fig. 4, a user obtains t he feature vector correspond- ing to a thumbnail image v E (1 ,k 0 ,k ) i from t he image o w ner, and then sends the vector to the third party . The third party performs the fol- lo wing process to identify E ( j,k 0 ,k ′ ) i ′ with E (1 ,k 0 ,k ) i , after extracting v E ( j,k 0 ,k ′ ) i ′ from E ( j,k 0 ,k ′ ) i ′ . (a) Set N and d , where d is a parameter that determines the ac- ceptance error . (b) Set n := 0 and i ′ = 0 . (c) If | v E (1 ,k 0 ,k ) i ( n ) − v E ( j,k 0 ,k ′ ) i ′ ( n ) | ≤ d , proceed to step (d). Otherwise, the third party judges t hat E ( j,k 0 ,k ′ ) i ′ is not gener- ated from O i and proceed to step (e). (d) Set n := n + 1 . If n < N , return to step (c). Otherwise, the third party j udges that E ( j,k 0 ,k ′ ) i ′ is generated from the same original image as that of E (1 ,k 0 ,k ) i , i.e., O i and the process for E (1 ,k 0 ,k ) i is halted. (e) Set i ′ := i ′ + 1 and n := 0 . If i ′ is not equal to the number of i mages stored in the database of the third party , return t o step (c). Otherwise, third party judges that there is no image correspondin g to E (1 ,k 0 ,k ) i . The distance between the absolute values of the features is used for identification under t he acceptance error d in step (c). As well as the con ventional schemes, this va lue was experimen tally determined in a pre-ex periment. 4. SIMULA TION A number of simulations were condu cted to ev aluate the perfor- mance of the proposed identification scheme. W e used images (size of 480 × 640 ) in UKbench dataset [24] and an encoder and a decoder from the IJG (Independent JPEG Group) [25] in the si mulations. T he dataset consists of 10,200 images (4 images per 2,520 objects), and 500 images from No.000 to No.499 were chosen from the 10,200 images (see Fig. 5). 4.1. Simulation Condi tions T able 2 summarizes the conditions for generating original JP EG im- ages and encrypted ones, where QF I indicates the quality factor (a) No.000 (b) No.001 (c) No.004 (d) No.005 Fig. 5 . Examples of images in UKbench T able 2 . Condition to generate original and encrypted JPEG images, where QF I indicates the quality factor generated for the JPEG image I , I ∈ { O i , E (1 ,k 0 ,k ) i , E (1 ,k 0 ,k ′ ) i , E (2 ,k 0 ,k ) i , E (2 ,k 0 ,k ′ ) i } . Condition QF O i = QF E (1 ,k 0 ,k ) i = QF E (2 ,k 0 ,k ) i = QF E (1 ,k 0 ,k ′ ) i = QF E (2 ,k 0 ,k ′ ) i = (1) 95 95 85,80,75,70 (2) 85 85 (3) 75 75 used for JPEG image I , I ∈ { O i , E (1 ,k 0 ,k ) i , E (1 ,k 0 ,k ′ ) i , E (2 ,k 0 ,k ) i , E (2 ,k 0 ,k ′ ) i } . Note that the sampling ratios for all compressions were 4:4:4. For instance, in the case of condition (1), 500 original JPEG images were generated with QF O i = 95 from the 500 UKbench i m- ages fi rst. T o generate E (1 ,k 0 ,k ) i , t he 500 original JPE G images were encrypted and compressed with QF E (1 ,k 0 ,k ) i = 95 . Next, these 500 single-compressed encrypted images were recompressed with QF E (2 ,k 0 ,k ′ ) i = 85 , 80 , 75 , 70 . As a result, 500 single-compressed and 2,000 double-compre ssed images encrypted wi t h k were gener- ated under each condition. As well as the generation of images en- crypted with k , there were 500 single-compressed and 2,000 double- compressed JPEG i mages encrypted with k ′ , QF E (1 ,k 0 ,k ′ ) i = 95 and QF E (2 ,k 0 ,k ′ ) i = 85 , 80 , 75 , 70 . I n the simulations, the iden- tification performances between 500 si ngle-compressed and 2,000 double-comp ressed images encrypted with k were ev aluated for each condition first. Also, identification between 500 single-compressed images wi th k and 2,000 double-compressed ones wi th k ′ was per- formed. As the parameters, N = 480 and d = 150 were selected. The UKbench images were di vided into 4800 8 × 8 blocks, i . e. M = 4800 , so that N = 480 was selected as 10 % of all blocks. T o determine d , identification between i mages generated under con- dition (2) and k 6 = k ′ from 885 UCID images [26] was carried out. As one of the best choices, d = 150 was selected. The proposed scheme was compared with four identifica- tion schem es (DC si gns-based [19], sparse codin g-based [20], quaternion-base d [21], and iterati ve quantization (ITQ)-based ones [22]). In the schemes [20–22], the Hamming distances between t he hash valu es of t he encrypted images were calculated, and images that had the smallest distance were then chosen as images generated from an original image after all images were decompressed. 4.2. Identification Performa nce T able 3 shows P r ecision value p and Recall v alue r , defined by p = T P T P + F P , r = T P T P + F N , (4) T able 3 . Identification performance for double-compressed en- crypted images scheme condition k = k ′ k 6 = k ′ p [%] r [%] p [%] r [%] proposed ( d = 150 ) (1) 100 100 100 100 (2) 100 100 100 100 (3) 100 100 100 100 DC sign [19] (1) 100 100 0 0 (2) 100 100 0 0 (3) 100 100 0 0 ITQ [22] (1) 100 100 3.45 3.45 (2) 100 100 3.25 3.25 (3) 100 100 3.6 3.6 Sparse coding [20] (1) 99.95 100 0.09 0.15 (2) 100 100 0.33 0.55 (3) 100 100 0.06 0.1 Quaternion [21] (1) 100 100 0.31 0.5 (2) 100 100 0.24 0.4 (3) 100 100 0.56 0.95 where T P , F P and F N represent t he number of true positiv e, false positi ve and false negati ve matches respectiv ely . Note that r = 100[%] means that there were no false negativ e matches, and p = 100[%] means that there were no false positi ve matches. It was confirmed that all schemes had high identification perfor- mances under k = k ′ . Howe ver , only the proposed scheme achieve d r = 100% and p = 100% under all conditions with k 6 = k ′ ; the other schemes did not. Moreov er , we confirmed that the identifica- tion results with N = 480 in T able 3 were the same as those eve n in the case N ≥ 160 . 5. CONCLUSION In this paper , a nove l identification scheme for encrypted images was proposed. T he image encryption is based on a block-scrambling method, and two-layer block permutation is performed in the en- crypted process. For t he identification, the feature vector used in the proposed scheme is extracted from t he D C coefficients of lumi- nance. The use of t he image encryption method and feature vectors allows us to avoid not only the effect of recompression but also that of re-encryption wi th different keys. Simulation results showed t he effe ctiv eness of the proposed scheme, ev en when images were re- compressed and re-encrypted by different keys for the second layer . Acknowledgeme nts This work was partially supported by Grant-in-Aid for Scientic Re- search(B), No.17H032 67, from t he Japan Society for the Promotion Science. 6. REFERENCES [1] C. T . Huang, L. Huangand Z. Qin, H. Y uan, L. Zhou, V . V arad- harajan, and C-C Jay Kuo, “Survey on securing data storage in the cloud, ” APSIP A Tr ans. Signal and Information Process ing , vol. 3, 2014. [2] R. Lagendijk, Z . Erkin, and M. Barni, “Encrypted signal pro- cessing for priv acy protection: Conv eying t he utility of homo- morphic encryption and multiparty computation, ” IEEE Signal Pr ocessing Magaz ine , vol. 30, no. 1, pp. 82–105, 2013. [3] R. Caldelli, R. Becarelli, and I. Amerini, “Image origin clas- sification based on social network prov enance, ” IEEE T rans. Information F or ensics and Security , vol. 12, no. 6, pp. 1299– 1308, 2017. [4] T . Chuman, K. Iida, W . S irichotedumrong , and H. Kiya, “Im- age manipulation specifications on social networking services for encryption-then-compression systems, ” IEICE T rans. on Info. and Sys. , vol. 102, no. 1, pp. 11–18, 2019. [5] V . Itier , P . Puteaux, and W . Puech, “Recompression of jpeg crypto-compressed images without a ke y , ” IEEE T rans. on Circu its and Systems for V ideo T echnolo gy , https://www .doi.org/10.11 09/ TCSVT . 2019.2894520, 2019. [6] J. Zhou, X. Liu, O. C. Au, and Y . Y . T ang, “Designing an ef- ficient image encryp tion-then-compression system via predic- tion error clustering and random permutation., ” I EEE T rans. information for ensics and security , vol. 9, no. 1, pp. 39–50 , 2014. [7] T . Chuman, W . Sirichotedumrong, and H. Kiya, “Encryption- then-compression systems using grayscale-base d image en- cryption for jpeg images, ” IEEE T rans. on I nformation F or en- sics and Security , vol. 14, no. 6, pp. 1515–152 5, 2019. [8] T . Chu man a nd H. Kiya, “Security ev aluation for block scrambling-based image encryption including jpeg distortion against jigsaw puzzle solver attacks, ” IEICE T rans. Funda- mentals , vol. E101-A, no. 12, pp. 2405–2408, 2018. [9] W . Sir ichotedumron g and H. Kiya, “Grayscale-based block scrambling image encryption using ycbcr color space for encryption-then -compression systems, ” APSIP A Tr ans. on Sig- nal and Information Pr ocessing, e7 , vol. 8, 2019. [10] K. Kurihara, S. Imaizumi, S. Shiota, and H. Kiya, “ An encryption-then -compression system for lossless image com- pression standards, ” IE ICE T rans. on Information and Systems , vol. E100-D, no. 1, pp. 52–56, 2017. [11] K. Munadi, F . Arnia, M. Syaryadhi, and H. Kiya, “ A content- based image retriev al system for visua lly protected image databases, ” in Proc. IEE E Asia P acific Confer ence on Mul- timedia and Bro adcasting , 2015, pp. 1–6. [12] M.R. R a, R. Govindan, and A. Orteg a, “ P3: T ow ard priv acy- preserving photo sharing, ” in P r oc. USENIX Symposium on Networked Systems Design and I m plementation , 2013, vol. 13, pp. 515–528. [13] A.A.A.M. Kamal, K. Iwamura, and H. Kang, “Searchable en- cryption of image based on secret sharing scheme, ” in Pr oc. APSIP A Annual Summit and Confer ence , 2017, pp. 1495– 1503. [14] H. Cheng, X. Zhang, and J. Y u, “ Ac-coefficient histogram- based retrie va l for encrypted jpeg images, ” Spring er Multime- dia T ools and Applications , vol. 75, no. 21, pp. 13791 –13803, 2016. [15] Y . Xu, J. Gong, L. Xiong, Z. Xu, J. W ang, and Y . Shi, “ A priv acy-preserv ing content-based image retri e va l method i n cloud en vironment, ” Elsevier J ournal of V isual Communica- tion and Image Repr esentation , vol. 43, pp. 164–1 72, 2017. [16] H. Cheng, X. Z hang, J. Y u, and F . Li, “Markov process-based retriev al for encrypted jpeg images, ” EURASIP J ournal on I n- formation Security , vol. 2016, no. 1, pp. 1, 2016. [17] Z. Xi a, N. N. Xiong, A.V . V asilakos, and X. Sun, “Epcbir: An efficien t and pri vac y-preserving content-based i mage retriev al scheme in cloud computing , ” Else vier Information Sciences , vol. 387, pp. 195–204, 2017. [18] K. Iida and H. Kiya, “Robust image identification wit h dc co- efficien ts for double-compresse d jpeg images, ” IEICE T rans. on Info. and Sys. , vol. 102, no. 1, pp. 2–10, 2019. [19] K. Iida and H. Kiya, “Robust image identification for double- compressed and resized jpeg images, ” in Proc. APSIP A A nnual Summit and Confer ence , 2018, pp. 1968–197 4. [20] Y . Li and P . W ang, “Robu st image hashing based on low- rank and sparse decomposition, ” in Pr oc. IEEE Int’l Conf . on A coustics, Speech and Signal P r ocessing , 2016, pp. 2154– 2158. [21] Y . N. Li, P . W ang, and Y . T . Su, “Robus t image hashing based on selectiv e quaternion in variance, ” IEEE Signal P r ocessing Letters , vol. 22, no. 12, pp. 2396–2400, 2015. [22] Y . Gong, S.Lazebnik, A. Gordo, and F . Perronnin, “Iterative quantization: A procrustean approach to learning binary codes for large-scale image retriev al, ” IEEE T rans. on P attern A nal- ysis and Machine Intelligence , vol. 35, no. 12, pp. 2916–2929, 2013. [23] R. L. De Queiroz, “Processing jpeg-compre ssed images and documents, ” IEEE Tr ans. on Image Processin g , vol. 7, no. 12, pp. 1661–1672, 1998. [24] “Ukbench dataset, ” ht tps://archive. org/details/u kbench . [25] “The independe nt jpeg group software jpeg cod ec, ” http://www.ij g.org/ . [26] G. Schaefer and M. Stich, “Ucid: An uncompressed color im- age database, ” in Electron ic Imaging 2004 , 2003, pp. 472–480.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment