A Fundamental Bound on Performance of Non-Intrusive Load Monitoring with Application to Smart Meter Privacy
We prove that the expected estimation error of non-intrusive load monitoring algorithms is lower bounded by the trace of the inverse of the cross-correlation matrix between the derivatives of the load profiles of the appliances. We use this fundament…
Authors: Farhad Farokhi
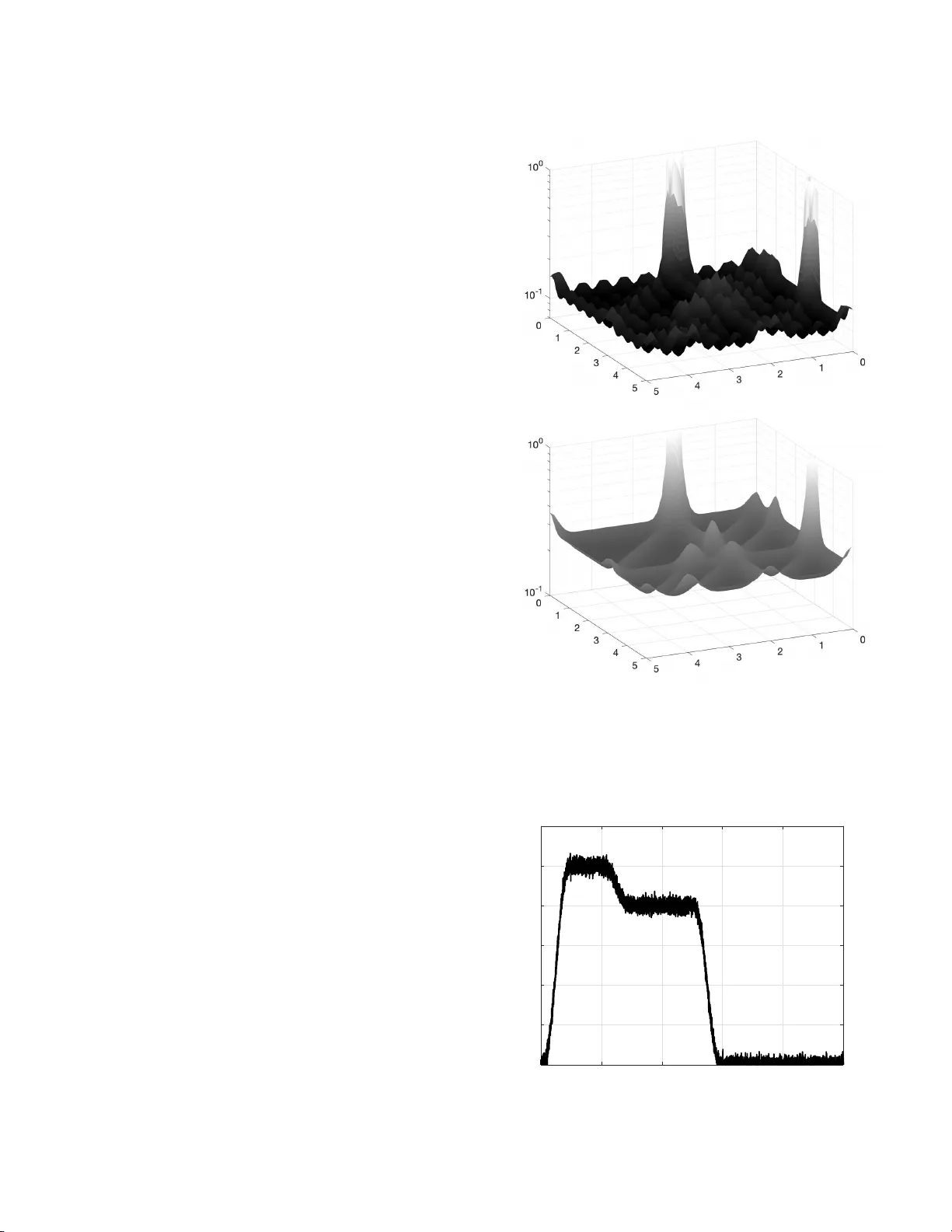
1 A Fundamental Bound on Per formance of Non-Intrusi v e Load Monitoring with Application to Smart Meter Pri v ac y Farhad Farokhi Abstract —W e prov e that the expected estimation error of non- intrusive load monitoring algorithms is lower bounded by the trace of the in ver se of the cr oss-corr elation matrix between the deriva tiv es of th e load profiles of the appliances. W e use this fundamental bound to develop pri vac y-preser ving policies. Particularly , we devise a load-scheduling policy by maximizing the lower bound on the expected estimation err or of non-intrusive load monitoring algorithms. Index T er ms —Non-intrusive l oad monitoring; Smart meter; Fisher infor mation; Priva cy . I . I N T RO D U C T I O N Non-intru si ve load monitor ing r esearch is dedicated to de- velopment o f algorithms for dis-ag gregating overall energy consump tion of househo lds measure d by s mart meters t o estimate timin g o f indi v idual appliance s, such as fridge or air- condition ing un its [3]–[8]. Th e research is of ten motiv ated b y the inter e st in pr ovid ing consumers with en e rgy-saving tips to lo wer bills or counter clima te change, perfor ming fault detection, and accommodatin g electricity grid tr ansformatio ns due to integration of r enew able energy . Although an important area of research, little is done in under standing fun damental bound s on the achiev able perfor mance o f non- intrusive load monitorin g algor ithms. Ther e f ore, in th is paper, we prove that the expected estimation err or of non- intrusive load monitoring algorithms is lo wer boun ded by th e trace of the in ve rse of th e cr oss-corr elation ma trix between the deriva tives of the lo ad pr ofiles o f the applian c es . Energy data, collected by smar t meters, is known to leak priv a te info rmation of ho useholds, su c h as occupan cy and appliance usage [1]. This sensiti ve data can be accessed by third-pa r ty data- analytic co mpanies 1 throug h electricity retailers or u tility comp anies. For instanc e , in Australia, an electricity retailer r equired its customer s to consent to sharing their da ta with th ird parties in the United St ates b efore permitting them to use an online web po rtal [2]. Th e refore, non-in trusiv e load monitorin g can be used for gaining pri vac y- intrusive in sights. Th is is evident from th e patents o n the technolog y expressing its use in targeted advertising [9], [10]. Also, non -intrusive load monito r ing has been proved to be commercia lly v ia b le an d attractive. Similar tech nologies ar e currently being used (albeit ba sed on water smart mete r s) F . Farokhi is with the CSIR O’ s Data61 and the Unive rsity of Mel- bourne. The work of F . Farokh i was, in part, fu nded by the of fice of the Deputy V ice-Cha ncell or (Researc h) at the Uni versity of Melbourn e. e-mail: farha d.farok hi@unimel b .edu.au 1 See http:// bidgel y .com and https://pl otwa tt.com/ as example s. to track elder ly behaviour and help those in distress [ 1 1] with similar ap plications to mo nitoring patien ts [12], which is a double- edged sword th at can be used by bo th he althcare profession a ls and insurance age ncies. This h as motiv ated the development o f priv acy-preserving polices f or smart m eters; see [1 3]– [20] and ref erences ther e -in. Therefo re, in this p aper, we use the afo remention ed fun damental bou nd on estimation err or of non -intrusive lo ad mo nitoring algorithms to develop privacy-preserving p olicies . Particularly , we devise a load - scheduling p o licy by max imizing the tra ce of the in verse of the cross-corre lation matrix between the d eriv atives of th e loa d profiles of th e app lian ces. I I . N O N - I N T RU S I V E L O A D M O N I T O R I N G Consider a ho use with n ∈ N applian ces. Applian c e i ∈ [ n ] := { 1 , . . . , n } h as a load signa tu re o f f i : R → R , i.e., its uniq ue en ergy consu mption p attern. The lo a d’ s signatu re is such tha t f i ( t ) = 0 for all t < 0 (befor e starting to work) and t > T (after finishin g its work) for some large eno ugh T . Appliance i ∈ [ n ] is sched uled to start at τ i ∈ R . Th erefore, the total con su mption o f the hou se at a ny given time t ∈ R is P i ∈ [ n ] f i ( t − τ i ) . W e assume that a non-in tr usiv e load mo nitoring algorithm can access noisy mea su rements of th e total consum ption at dis- crete times ( t ℓ ) ℓ ∈ [ k ] ⊆ [0 , T ] . The n oise models measurem ent noise, p riv acy-pr eserving additive noises (e.g., d ifferential- priv a cy no ise), and consumption of small loads that the non-in trusiv e load mon itoring algorith m is not interested in identifyin g . Th e measuremen t y ℓ at time t ℓ is the n given by y ℓ = X i ∈ [ n ] f i ( t ℓ − τ i ) + w ℓ , (1) where w := ( w ℓ ) ℓ ∈ [ k ] is a sequen ce of i.i.d . 2 noises. T he non- intrusive lo ad monito ring algo rithm is interested in estimatin g τ := ( τ i ) i ∈ [ n ] ∈ R n from the measurem e nts y := ( y ℓ ) ℓ ∈ [ k ] ∈ R k using a family of arbitrary estimator s denoted by ˆ τ i : R k → R for all i ∈ [ n ] . W e are interested for finding a lower bou nd on X i ∈ [ n ] π i E { ( ˆ τ i ( y ) − τ i ) 2 } = E {k Π 1 / 2 ( ˆ τ ( y ) − τ ) k 2 2 } , (2) where ˆ τ := ( ˆ τ i ) i ∈ [ n ] and Π := diag( π 1 , . . . , π n ) . W e make the following standing assump tion. 2 i.i.d. stands for independent ly and identicall y distrib uted. 2 Assumption 1 (Regular ity ) . p ( w ) is con tinuously d iffer en- tiable; p ( w ) = 0 , ∀ w ∈ ∂ supp( p ) . The regular ity co ndition in Assum ption 1 is a basic assum p- tion that is commo n in signal p r ocessing results, suc h as the Cram ´ er-Rao bou nd [21, p. 16 9]. Th is a ssumption h olds fo r Gaussian an d L aplace distributions, and many o ther den sity function s. In fact, any den sity f u nction with an unbo unded support au to matically satisfies this cond ition. W e can p rove the following fu ndamenta l bo und on the p erform a n ce o f unbiased non-in trusiv e load monitorin g algo rithms. Theorem 1. F or any unbia sed estimator ˆ τ , i.e., E { ˆ τ } = τ , we get E {k Π 1 / 2 ( ˆ τ ( y ) − τ ) k 2 2 } ≥ 1 I w trace(Π R d ( τ ) − 1 ) , wher e I w = E w { ( p ′ ( w ) /p ( w )) 2 } is the F isher in formation of the additive noise and R d ( τ ) is the discr e te cr o ss-corr elatio n matrix function for the derivatives of the load signatur e s with entry in i -the r ow and j -the c o lumn defi ned as [ R d ] ij ( τ i , τ j ) := X ℓ ∈ [ k ] f ′ i ( t ℓ − τ i ) f ′ j ( t ℓ − τ j ) . Pr oof: The con ditional p robability den sity of o bserving y g iv en τ is equ al to p ( y | τ ) = Y ℓ ∈ [ k ] p y ℓ − X i ∈ [ n ] f i ( t ℓ − τ i ) . Differentiating lo garithm of the conditio nal density p ( y | τ ) results in ∂ log( p ( y | τ )) ∂ τ i = X j ∈ [ k ] p ′ y j − X i ∈ [ n ] f i ( t j − τ i ) p y j − X i ∈ [ n ] f i ( t j − τ i ) f ′ i ( t j − τ i ) . Follo wing this, we can co mpute th e entry in i -th r ow and q -th column of th e Fisher inf ormation matrix as I iq := E y ∂ ∂ τ i log( p ( y | τ )) ∂ ∂ τ q log( p ( y | τ )) = E w ( X j ∈ [ k ] p ′ ( w j ) p ( w j ) f ′ i ( t j − τ i ) ! × X j ∈ [ k ] p ′ ( w j ) p ( w j ) f ′ q ( t j − τ q ) !) = X j 1 ,j 2 ∈ [ k ] E w ( p ′ ( w j 1 ) p ( w j 1 ) p ′ ( w j 2 ) p ( w j 2 ) ) × f ′ i ( t j 1 − τ i ) f ′ q ( t j 2 − τ q ) = I w X j ∈ [ k ] f ′ i ( t j − τ i ) f ′ q ( t j − τ q ) = I w [ R d ] iq ( τ i , τ q ) . Therefo re, the Fisher info rmation matrix is equal to I := E y ∇ τ p ( y | τ ) ∇ τ p ( y | τ ) ⊤ = I w R d ( τ ) . Finally , we get E {k Π 1 / 2 ( ˆ τ ( y ) − τ ) k 2 2 } = tr ace( E { Π 1 / 2 ( ˆ τ − τ )( ˆ τ − τ ) ⊤ Π 1 / 2 } ) = tr ace(Π 1 / 2 E { ( ˆ τ − τ )( ˆ τ − τ ) ⊤ } Π 1 / 2 ) ≥ tr ace(Π 1 / 2 ( I w R d ( τ )) − 1 Π 1 / 2 ) = tr ace(Π 1 / 2 R d ( τ ) − 1 Π 1 / 2 ) / I w = tr ace(Π R d ( τ ) − 1 ) / I w . This conclu d es the proo f. If we assume tha t w ℓ is a zero- mean Gaussian r andom variable with variance σ 2 w > 0 for a ll ℓ ∈ [ k ] , we can simplify the boun d in Theo rem 1 by noting that I w = σ − 2 w . Note th at the bo und in Th eorem 1 is only valid for un biased estimators. W e gen eralize this boun d to u n biased estimators in the next theore m. Theorem 2. F or any estimato r ˆ τ , we get E {k Π 1 / 2 ( ˆ τ ( y ) − τ ) k 2 2 } ≥ 1 I w trace Π ∂ µ ( τ ) ∂ τ R d ( τ ) − 1 ∂ µ ( τ ) ∂ τ ⊤ ! + k Π 1 / 2 µ ( τ ) k 2 2 , wher e µ ( τ ) := E { ˆ τ ( y ) } . Pr oof: T he proo f follows fro m that E {k Π 1 / 2 ( ˆ τ ( y ) − τ ) k 2 2 } ≥ tr ace Π 1 / 2 ∂ µ ( τ ) ∂ τ ( I w R d ( τ )) − 1 ∂ µ ( τ ) ∂ τ ⊤ + µ ( τ ) µ ( τ ) ⊤ ! Π 1 / 2 ! = 1 I w trace Π ∂ µ ( τ ) ∂ τ R d ( τ ) − 1 ∂ µ ( τ ) ∂ τ ⊤ ! + k Π 1 / 2 µ ( τ ) k 2 2 . This conclu d es the proo f. W e can further simplify the lower bound in Th eorem 2. Corollary 1. F or any estimato r ˆ τ , we get E {k Π 1 / 2 ( ˆ τ ( y ) − τ ) k 2 2 } ≥ c 1 ( τ ) I w trace(Π R d ( τ ) − 1 ) + c 2 ( τ ) , wher e c 1 ( τ ) := λ min Π − 1 / 2 ∂ µ ( τ ) ∂ τ ⊤ Π ∂ µ ( τ ) ∂ τ Π − 1 / 2 ! ≥ 0 , c 2 ( τ ) := k Π 1 / 2 µ ( τ ) k 2 2 ≥ 0 . 3 t f i ( t ) Fig. 1. Examples of three generic loads. Pr oof: No te that trace Π ∂ µ ( τ ) ∂ τ R d ( τ ) − 1 ∂ µ ( τ ) ∂ τ ⊤ ! = trace Π − 1 / 2 ∂ µ ( τ ) ∂ τ ⊤ Π ∂ µ ( τ ) ∂ τ Π − 1 / 2 × Π 1 / 2 R d ( τ ) − 1 Π 1 / 2 ! ≥ λ min Π − 1 / 2 ∂ µ ( τ ) ∂ τ ⊤ Π ∂ µ ( τ ) ∂ τ Π − 1 / 2 ! × trace(Π 1 / 2 R d ( τ ) − 1 Π 1 / 2 ) , where the ineq u ality follows fr om the inequality on traces of p ositi ve semi-defin ite matrices in [2 2]. Comb ining this in- equality with trace(Π 1 / 2 R d ( τ ) − 1 Π 1 / 2 ) = tra ce(Π R d ( τ ) − 1 ) conclud e s the proo f. Note that R d ( τ ) in T h eorems 1 and 2 is a fun ction of the sampling tim e s ( t ℓ ) ℓ ∈ [ k ] . However , as k increases, th is depend ence d isappears. Th is is discussed in th e following corollary . Corollary 2. F or an y u n biased estimator ˆ τ , i.e., E { ˆ τ } = τ , we get lim k →∞ k E {k Π 1 / 2 ( ˆ τ − τ ) k 2 2 } ≥ 1 I w trace(Π R c ( τ ) − 1 ) , wher e R c ( τ ) is the continu ous cr oss-corr elation matrix func- tion for the derivatives of the lo ad signa tur es with entry on i -the r o w and j -th e column defin ed as [ R c ] ij ( τ i , τ j ) := Z + ∞ −∞ f ′ i ( t − τ i ) f ′ j ( t − τ j )d t. Pr oof: The proof follows from th e co n vergence of the Riemann integral. T h e bou n ds of the integral can be pushed from [0 , T ] to ( −∞ , + ∞ ) d ue to the fact that the load pro files are equal to zero o utside [0 , T ] . I I I . S M A RT - M E T E R P R I V A C Y B Y L O A D S C H E D U L I N G In this section, we prop ose an ap proach fo r smart meter priv a cy b ased o n loa d sched uling. Clear ly , the lower bou nd on the per f ormance of an ad versary employin g a non-in trusiv e load m onitorin g algorithm for prying into a h o usehold in Theorem 1 an d Corollary 1 is a f unction o f the sch eduling time of th e appliance s τ . Th is motiv ate us to solve the fol- lowing optimization p roblem for finding the op timal privac y- preserving schedulin g: max τ ∈ T trace(Π R d ( τ ) − 1 ) , (3) where T denote s th e set o f feasible sch edules. The c ost function of this optimization prob lem is howe ver non-co n vex. Therefo re, the r e are many local optima that c a n be recovered using numerica l algor ith ms, such as the gradien t descent. For this, we no te that ∂ trace(Π R d ( τ ) − 1 ) ∂ τ i = tr ace Π ∂ R d ( τ ) − 1 ∂ τ i !! = − trace R d ( τ ) − 1 Π R d ( τ ) − 1 ∂ R d ( τ ) ∂ τ i ! ! , where ∂ R d ( τ ) ∂ τ i j i = ∂ R d ( τ ) ∂ τ i ij = − 2 X j ∈ [ k ] f ′′ i ( t j − τ i ) f ′ i ( t j − τ i ) , i = j, − X j ∈ [ k ] f ′′ i ( t j − τ i ) f ′ j ( t j − τ j ) , i 6 = j, and ∂ R d ( τ ) ∂ τ i qℓ = 0 , ∀ q , ℓ 6 = i. Therefo re, we can use the projected g radient ascent to solve (3) by following τ k +1 = P T τ k + µ k ∂ ∂ τ trace(Π R d ( τ ) − 1 ) , (4) where µ k > 0 de n otes the step size an d P T [ · ] den o tes projection into the set T . For large k , we can replace R d ( τ ) with R c ( τ ) w h ile noting that ∂ R c ( τ ) ∂ τ i j i = ∂ R c ( τ ) ∂ τ i ij = − 2 Z ∞ −∞ f ′′ i ( t − τ i ) f ′ i ( t − τ i )d t, i = j, − Z ∞ −∞ f ′′ i ( t − τ i ) f ′ j ( t − τ j )d t, i 6 = j, and, similarly , ∂ R c ( τ ) ∂ τ i qℓ = 0 , ∀ q , ℓ 6 = i . 4 I V . N U M E R I C A L E X A M P L E In this sectio n, we use an illustrativ e example to demo nstrate the results of this paper . For this purp o se, let u s con sider th ree generic loads depicted in Fig ure 1. The se load s possess simple forms for ease of dem onstration. Assume that th e ad ditiv e noise is Ga u ssian with z e r o mean and standard deviation σ w = 0 . 1 . Assume that the n on-intr usi ve lo ad monitor ing algorith m has access to the total measuremen ts at { 0 , 0 . 5 , . . . , 9 . 5 , 10 } . Figure 2 [top] illustrates the lo wer boun d on th e estima- tion error of any n on-intru si ve load mo nitoring algorith m in Theorem 1 versus schedu ling delays o f the first two loads τ 1 , τ 2 when fixin g τ 3 = 0 . Figure 2 [bottom ] illustrate s the lower bo und on the estimation erro r o f any non- intrusive lo ad monitorin g algorith m in Corollary 2 versus schedu ling delay s of the fir st two loads. Clearly , these two boun ds ar e very close to each other due to the high numb er of measureme nts in the discrete case. Furthermo re, as expected, the lower boun ds in Theo rem 1 and Corollary 2 are no n -conve x in the decision variables of the schedu ling problem τ an d possess m any loc a l optim a. Howe ver, there are two p oints fo r which the lower boun ds become very large, in fact these points are th e g lobally- optimal priv acy-preserving schedu les when fixing τ 3 = 0 . They cor respond s to sch e dules for which its is impo ssible to determine if the second load is sch e duled first or the third load. Therefo re, the estimation erro r of any non- intrusive load monitorin g algorithm is large. Therefo re, these ar e the mo st priv a cy-p reserving sched u les. V . C O N C L U S I O N S A N D F U T U R E R E S E A R C H W e proved that the expected estimation error o f no n - intrusive lo a d monitoring algorithm s is lower bounded by the trace of the inverse of the cross-corr e la tio n m atrix betwee n the deriv ati ves o f th e loa d pro files of the app liances. W e developed priv a cy-p reserving load sched u ling policies by maximizing the lower bou nd on the expected estimation error o f non- intrusive load mo nitoring alg orithms. Future work can focus on experimental demon stra tion and validations of these results with off-the-she lf no n -intrusive load monitorin g algo rithms. R E F E R E N C E S [1] P . McDaniel and S. McLaughlin, “Securit y and priv acy challenges in the smart grid, ” IEE E Security & Privacy , vol. 7, no. 3, pp. 75–77, 2009. [2] V . Chadwick , C. Butt, and H. Cook, “Smart meter data shared far and wide. ” The Age, Australia, Sep. 2012. [Online]. A vail able: http:/ /www .theage.com.au/ it- pro/government- it/smart- m eter- data- sha red- far- a n d - w i d e - 2 0 1 2 0 9 2 2 - 2 6 d v p . h t m l . [3] S. S. Hosseini, K. Agbossou, S. Kelouw ani, and A. Cardena s, “Non- intrusi ve load monitoring through home ener gy management systems: A comprehensi ve revi e w , ” Renewa ble and Sustainable Energy R evi ews , vol. 79, pp. 1266–1274, 2017. [4] A. Zoha, A. Gluhak, M. Im ran, and S. Rajase garar , “Non-intrusi ve load monitoring approac hes for disaggre gated energy sensing: A surve y , ” Sensors , vol. 12, no. 12, pp. 16838–16866, 2012. [5] P . Davies, J. Dennis, J . Hansom, W . Martin, A. Stanke vicius, and L. W ard, “Deep neural netw orks for appli ance transient classific ation , ” in ICASSP 2019-2019 IEEE Internati onal Confer ence on A coustic s, Speec h and Signal Proce ssing (ICASSP) , pp. 8320–8324, IEEE, 2019. [6] Y . Jin, E. T ebekaemi , M. Berges, and L. Soibelman, “Robu st adapti ve e ven t detection in non-intrusi ve load m onitoring for energy aware sm art fac iliti es, ” in 2011 IEEE International Confere nce on Acoustics, Speec h and Signal Proce ssing (ICASSP) , pp. 4340–4343, IEEE, 2011. τ 2 τ 1 trace( R d ( τ ) − 1 ) τ 2 τ 1 trace( R c ( τ ) − 1 ) Fig. 2. L o wer bound on the estimatio n error of any non-intrusi ve load monitoring algorithm in Theorem 1 [top] and Corollary 2 [bottom] versus scheduli ng delays of the first two loads. 0 2 4 6 8 10 0 1 2 3 4 5 6 t P i ∈ [ n ] f i ( t − τ i ) + w Fig. 3. T otal noisy consumption for the pri vac y-preservi ng schedule. 5 [7] B. Zhao, L . Stank ovic , and V . Stanko vic, “Blind non-intrusi ve applia nce load monitoring using graph-base d signal processing, ” in 2015 IEE E Global Confer ence on Signal and Information Pr ocessing (GlobalSIP) , pp. 68–72, IEEE , 2015. [8] H. Rashid, V . Stanko vic, L. S tankovi c, and P . Singh, “Eva luatio n of non-intru si ve load monitoring algorithms for appliance-l e ve l anomaly detec tion, ” in ICASSP 2019-2019 IEEE Internati onal Confer ence on Acoustics, Speech and Signal Proce ssing (ICASSP) , pp. 8325–8329, IEEE, 2019. [9] S. B. Leeb and J. L. Kirtle y Jr , “Transient ev ent detector for use in nonintrusi ve load monitoring systems, ” Jan. 9 1996. US Patent 5,483,153. [10] A. Haghigha t-kashani , J. T . -N. Cheam, and J. M. Hallam, “System and method of compiling and organizi ng po wer consumption data and con vertin g such data into one or more user actionable formats, ” Jan. 8 2015. US Patent App. 14/372,056. [11] S. Corner , “The a ussie co mpany metering south koreas wate r: Freestyle t echnolo gy highly c ommended in iot aw ards. ” IoT HUB, June 2018. [Online]. A vaila ble: https:/ /www .iothub .com.au/ne w s /the- aussie- company- metering- south- koreas- w ater- 49 2482 . [12] C. Chalmers, W . Hurst, M. Mackay , P . Fergus, D. Al-Jumeily , and B. Ke ndall, “Intel ligen t health monitoring using smart meters, ” in Scienc e and Information Conferen ce , pp. 1104–1113, Springer , 2018. [13] J . Y ao and P . V enkitasubra maniam, “Priv acy aw are stochasti c games for distribu ted end-user energy storage sharing, ” IE E E T ransactions on Signal and Information P r ocessing over Networks , vol. 4, no. 1, pp. 82– 95, 2017. [14] K. -H. Cho, S. -H. Lee, and A. Khisti, “Effec t of user cooperat ion on smart m eter priv acy with rechargea ble batteri es, ” IEEE Signal Pr ocess- ing Letter s , vol. 26, no. 7, pp. 971–975, 2019. [15] Y . H. Liu, S.-H. L ee, and A. Khisti, “Informati on-theor etic priv acy in smart metering systems using cascaded recharge able batteries, ” IEEE Signal Proc essing Letters , vol. 24, no. 3, pp. 314–318, 2017. [16] L . Sankar , S . R. Rajagopala n, S. Mohajer , and H. V . Poor, “Smart m eter pri vac y: A theoreti cal framew ork, ” IEEE T ransact ions on Smart Grid , vol. 4, no. 2, pp. 837–846, 2012. [17] G. E ibl and D. Engel, “Influence of data granularity on smart meter pri vac y , ” IEEE T ransact ions on Smart Grid , vol. 6, no. 2, pp. 930–939, 2014. [18] F . Farokhi and H. Sandber g, “Fisher information as a measure of priv acy: Preserving priv acy of households with smart meters using batteri es, ” IEEE T ransactions on Smart Grid , vol. 9, no. 5, pp. 4726–4734, 2017. [19] G. Giaconi, D. G ¨ und ¨ uz, and H. V . Poor , “Smart meter priv acy with rene wable energy and an energy storage de vice, ” IEEE T ransactions on Informatio n F orensic s and Security , vol. 13, no. 1, pp. 129–142, 2017. [20] E . Liu and P . Cheng, “ Achie ving priv acy protection using distribute d load scheduli ng: A randomized approach, ” IEEE T ransaction s on Smart Grid , vol. 8, no. 5, pp. 2460–2473, 2017. [21] J . Shao, Mathematica l Statistics . Springer T exts in Statistics, Springer- V erlag New Y ork, 2003. [22] D. Kleinman and M. Athans, “The design of suboptimal linear time- v arying systems, ” IEEE T ransactio ns on Automati c Contr ol , vol. 13, no. 2, pp. 150–159, 1968.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment